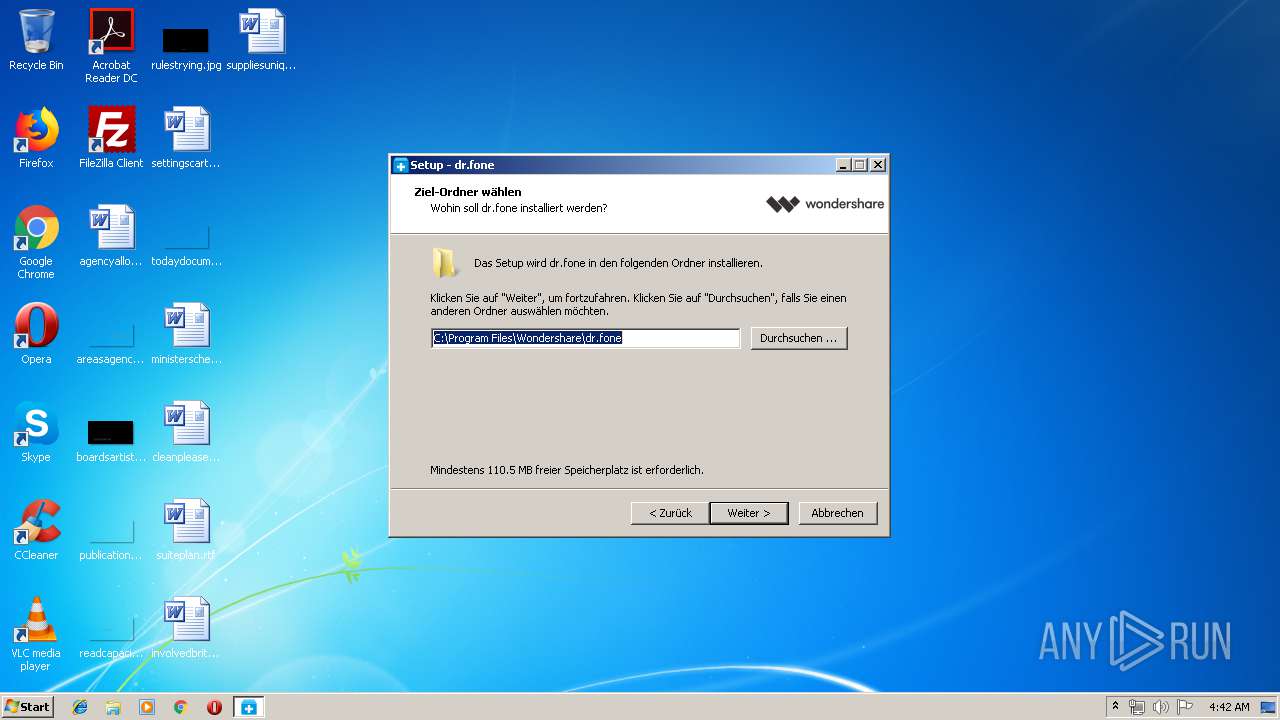
| File name: | http://download.wondershare.com/cbs_down/drfone_recover_full3366.exe |
| Full analysis: | https://app.any.run/tasks/b53fcda4-068c-4e0a-8c9c-25cfb73f206b |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2019, 03:41:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BADEB0C8A61D32E90B9BC43A47D77F4A |
| SHA1: | 99D66A546AB02A48247910853A6E7A027BE3AB3D |
| SHA256: | 543EBFDDC8F848509A1DF486B23FF6D016650D21688DA7DF69FDC6B41E339C1C |
| SSDEEP: | 1572864:MT93q91M3/DoRGvcR66+1sQZjs4i+6PskTVyrBA9zRnKq:ulqdG96FQOL/TVytA9 |
MALICIOUS
Changes settings of System certificates
- NFWCHk.exe (PID: 2584)
Application was dropped or rewritten from another process
- WAFSetup.exe (PID: 3364)
- WsAppService.exe (PID: 3172)
- devcon_x86.exe (PID: 3048)
- devcon_x86.exe (PID: 1456)
Loads dropped or rewritten executable
- RegAsm.exe (PID: 3564)
- RegAsm.exe (PID: 3960)
- RegAsm.exe (PID: 3248)
- RegAsm.exe (PID: 1360)
- RegAsm.exe (PID: 1288)
- RegAsm.exe (PID: 3908)
- WsAppService.exe (PID: 3172)
SUSPICIOUS
Executable content was dropped or overwritten
- drfone_recover_full3366.exe (PID: 1488)
- drfone_recover_full3366.exe (PID: 3204)
- drfone_recover_full3366.tmp (PID: 3992)
- NetFxLite.tmp (PID: 3360)
- WAFSetup.tmp (PID: 2648)
- devcon_x86.exe (PID: 1456)
- devcon_x86.exe (PID: 3048)
- DrvInst.exe (PID: 1504)
- WsAppService.exe (PID: 3172)
Reads the Windows organization settings
- drfone_recover_full3366.tmp (PID: 3992)
- NetFxLite.tmp (PID: 3360)
- WAFSetup.tmp (PID: 2648)
- DrFoneToolKit.tmp (PID: 2224)
Reads Windows owner or organization settings
- NetFxLite.tmp (PID: 3360)
- drfone_recover_full3366.tmp (PID: 3992)
- WAFSetup.tmp (PID: 2648)
- DrFoneToolKit.tmp (PID: 2224)
Creates files in the Windows directory
- NetFxLite.tmp (PID: 3360)
- drfone_recover_full3366.tmp (PID: 3992)
- WAFSetup.tmp (PID: 2648)
- devcon_x86.exe (PID: 3048)
- DrvInst.exe (PID: 4080)
- DrvInst.exe (PID: 1504)
Adds / modifies Windows certificates
- NFWCHk.exe (PID: 2584)
Modifies the open verb of a shell class
- RegAsm.exe (PID: 1288)
Creates COM task schedule object
- RegAsm.exe (PID: 3908)
- RegAsm.exe (PID: 1288)
Creates files in the program directory
- RegAsm.exe (PID: 3248)
- RegAsm.exe (PID: 3908)
- WsAppService.exe (PID: 3172)
- RegAsm.exe (PID: 1288)
Reads Environment values
- RegAsm.exe (PID: 3908)
- WsAppService.exe (PID: 3172)
Reads Internet Cache Settings
- RegAsm.exe (PID: 3908)
Executed as Windows Service
- WsAppService.exe (PID: 3172)
Creates or modifies windows services
- WAFSetup.tmp (PID: 2648)
Removes files from Windows directory
- DrvInst.exe (PID: 4080)
- DrvInst.exe (PID: 1504)
Executed via COM
- DrvInst.exe (PID: 4080)
- DrvInst.exe (PID: 1504)
Creates files in the driver directory
- DrvInst.exe (PID: 4080)
- DrvInst.exe (PID: 1504)
Searches for installed software
- WsAppService.exe (PID: 3172)
- RegAsm.exe (PID: 3908)
- DrFoneToolKit.tmp (PID: 2224)
INFO
Application was dropped or rewritten from another process
- drfone_recover_full3366.tmp (PID: 1256)
- drfone_recover_full3366.tmp (PID: 3992)
Creates a software uninstall entry
- drfone_recover_full3366.tmp (PID: 3992)
Dropped object may contain Bitcoin addresses
- drfone_recover_full3366.tmp (PID: 3992)
Loads dropped or rewritten executable
- drfone_recover_full3366.tmp (PID: 3992)
Creates files in the program directory
- WAFSetup.tmp (PID: 2648)
- drfone_recover_full3366.tmp (PID: 3992)
- DrFoneToolKit.tmp (PID: 2224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 66560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.9.5.38 |
| ProductVersionNumber: | 9.9.5.38 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
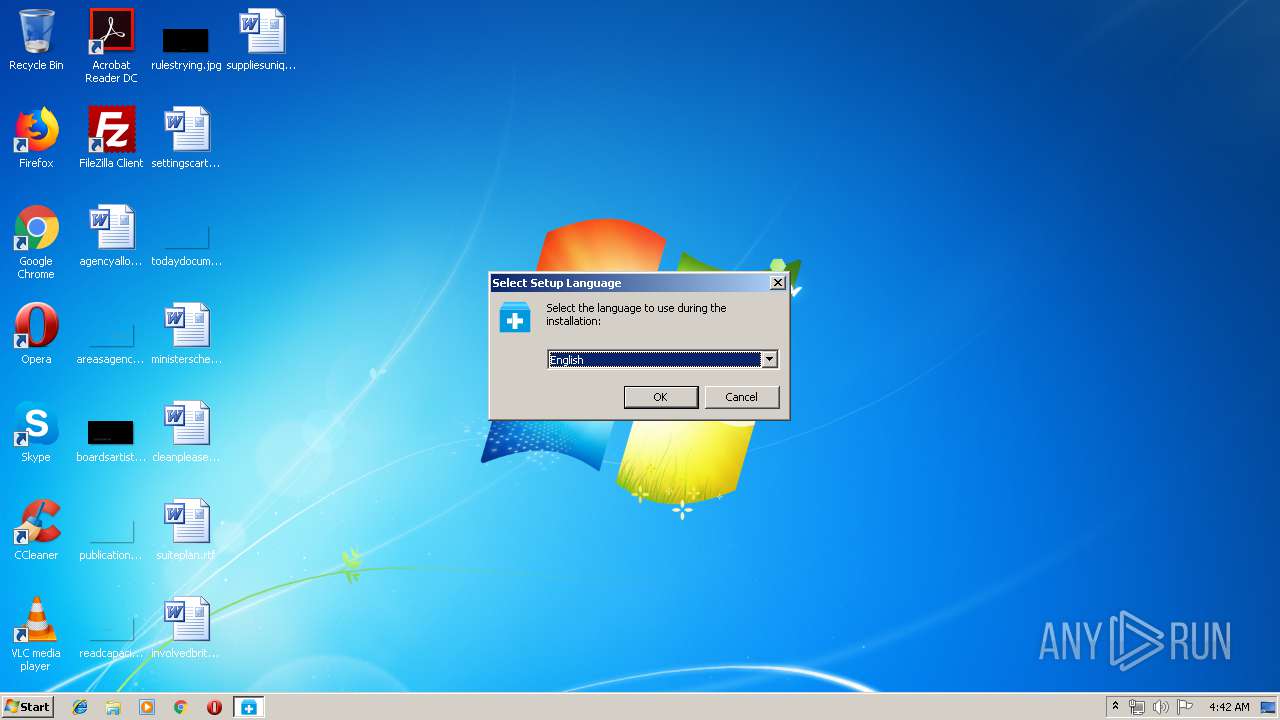
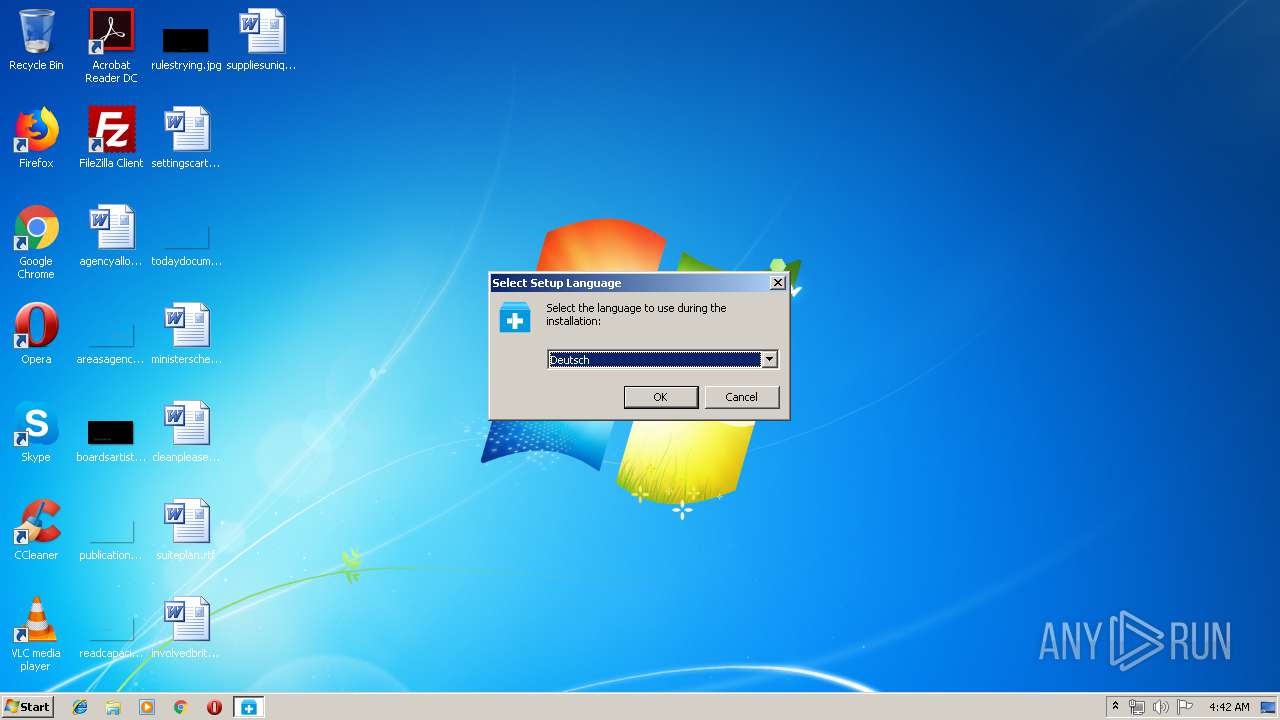
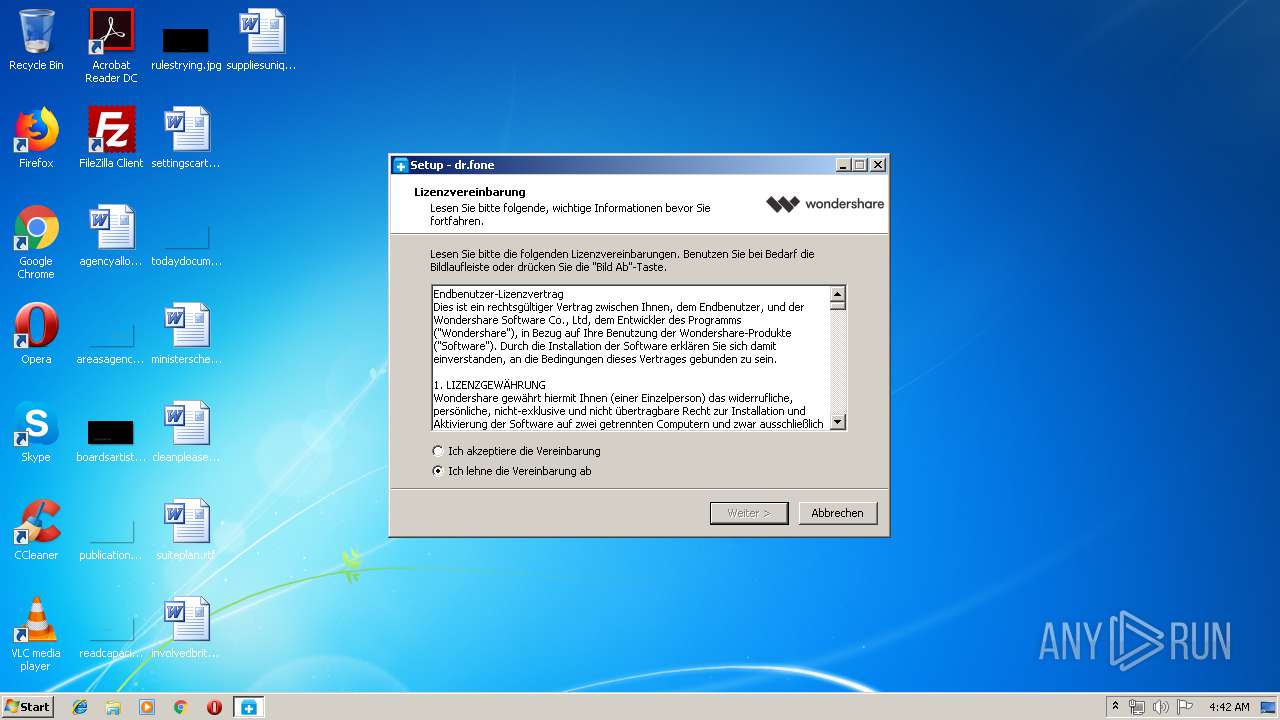
| CompanyName: | Wondershare |
| FileDescription: | dr.fone |
| FileVersion: | 9.9.5.38 |
| LegalCopyright: | Copyright © 2019 Wondershare. All rights reserved. |
| ProductName: | dr.fone |
| ProductVersion: | 9.9.5.38 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Wondershare |
| FileDescription: | dr.fone |
| FileVersion: | 9.9.5.38 |
| LegalCopyright: | Copyright © 2019 Wondershare. All rights reserved. |
| ProductName: | dr.fone |
| ProductVersion: | 9.9.5.38 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000E29C | 0x0000E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.38379 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.48302 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.69026 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.90084 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
68
Monitored processes
23
Malicious processes
13
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Users\admin\AppData\Local\Temp\is-83QPF.tmp\NetFxLite.exe" /verysilent /NORESTART | C:\Users\admin\AppData\Local\Temp\is-83QPF.tmp\NetFxLite.exe | — | drfone_recover_full3366.tmp | |||||||||||
User: admin Company: © Wondershare Corporation. All rights reserved. Integrity Level: HIGH Description: Microsoft .NET Framework 2.0 Client Profile Basic SP2 Exit code: 1 Version: 2.0.0.29 Modules
| |||||||||||||||
| 1256 | "C:\Users\admin\AppData\Local\Temp\is-4H184.tmp\drfone_recover_full3366.tmp" /SL5="$70256,62996796,134144,C:\Users\admin\AppData\Local\Temp\drfone_recover_full3366.exe" | C:\Users\admin\AppData\Local\Temp\is-4H184.tmp\drfone_recover_full3366.tmp | — | drfone_recover_full3366.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1288 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" "C:\Program Files\Wondershare\WAF\2.4.3.237\WsAppClient.exe" /codebase /tlb:"C:\Program Files\Wondershare\WAF\WsAppClient.tlb" /nologo | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | WAFSetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1360 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" "C:\Program Files\Wondershare\WAF\2.4.3.237\WsAppClient.exe" /u /nologo | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | WAFSetup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\AppData\Local\Temp\is-83QPF.tmp\DrFoneToolKit.exe" /SP- /silent /VERYSILENT /NoCustomize /LANG=DEU /Dir="C:\Program Files\Wondershare\dr.fone" /CreateDesktopIcon /CreateQuickLaunchIcon | C:\Users\admin\AppData\Local\Temp\is-83QPF.tmp\DrFoneToolKit.exe | — | drfone_recover_full3366.tmp | |||||||||||
User: admin Company: Wondershare Integrity Level: HIGH Description: Wondershare dr.fone Exit code: 0 Version: 9.8.2.9 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Wondershare\dr.fone\Library\RootRecovery\1.0.0\tools\devcon_x86.exe" dp_add "C:\Program Files\Wondershare\dr.fone\Library\RootRecovery\1.0.0\tools\driver\ssudbus.inf" | C:\Program Files\Wondershare\dr.fone\Library\RootRecovery\1.0.0\tools\devcon_x86.exe | drfone_recover_full3366.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 1488 | "C:\Users\admin\AppData\Local\Temp\drfone_recover_full3366.exe" | C:\Users\admin\AppData\Local\Temp\drfone_recover_full3366.exe | explorer.exe | ||||||||||||
User: admin Company: Wondershare Integrity Level: MEDIUM Description: dr.fone Exit code: 0 Version: 9.9.5.38 Modules
| |||||||||||||||
| 1504 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{480b5327-c6d5-79b5-cb95-1c138a52a31b}\ssudbus.inf" "0" "6a3d6d4ab" "000003D0" "WinSta0\Default" "00000578" "208" "C:\Program Files\Wondershare\dr.fone\Library\RootRecovery\1.0.0\tools\driver" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Local\Temp\is-PI5GM.tmp\DrFoneToolKit.tmp" /SL5="$9020A,726173,121344,C:\Users\admin\AppData\Local\Temp\is-83QPF.tmp\DrFoneToolKit.exe" /SP- /silent /VERYSILENT /NoCustomize /LANG=DEU /Dir="C:\Program Files\Wondershare\dr.fone" /CreateDesktopIcon /CreateQuickLaunchIcon | C:\Users\admin\AppData\Local\Temp\is-PI5GM.tmp\DrFoneToolKit.tmp | — | DrFoneToolKit.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2584 | C:\Users\admin\AppData\Local\Temp\is-4HO28.tmp\NFWCHk.exe | C:\Users\admin\AppData\Local\Temp\is-4HO28.tmp\NFWCHk.exe | NetFxLite.tmp | ||||||||||||
User: admin Company: Wondershare Integrity Level: HIGH Description: .NET Framework Checker Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 526
Read events
1 217
Write events
1 278
Delete events
31
Modification events
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 980F000094715825870FD501 | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C7C503FF9FB7F692FE9DD7552DBEB89D6AEC1D614ADC4F710304A073841512EB | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Wondershare\dr.fone\WSUtilities.dll | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 4D01B633FE35D8B65500B73C9138FF02F71FE4FF3AE517D7CE259E2AACA8C9D2 | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wondershare\com.wondershare.drfonewin |
| Operation: | write | Name: | RemindSwitch |
Value: 1 | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wondershare\com.wondershare.drfonewin |
| Operation: | write | Name: | TipsEnable |
Value: 1 | |||
| (PID) Process: | (3992) drfone_recover_full3366.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wondershare\3436 |
| Operation: | write | Name: | JumpType |
Value: 0 | |||
Executable files
80
Suspicious files
27
Text files
154
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\is-A624Q.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\is-LIBRN.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\Library\CBS\is-QRT5J.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\Library\ADB\is-V6VB4.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\Library\ADB\is-A3CC0.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\Library\ADB\is-5O0AN.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\Library\ADB\is-R2A7H.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\Library\ADB\is-QH27T.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\Library\MSVCRT\is-QR2QT.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | drfone_recover_full3366.tmp | C:\Program Files\Wondershare\dr.fone\Library\MSVCRT\is-P7OG7.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
12
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3908 | RegAsm.exe | GET | — | 203.130.48.151:80 | http://was.wondershare.com/v1/?app_id=com.wondershare.waf&app_ver=237&client_sign=%7BC4BA3647-FBFF-0005-06E3-5254004A04AF%7D&lang=en-US&method=app.info.modulelist&sku=sku-ween×tamp=1558410173&key=47342D1BEE153385294760BDDB8A7F49&vc=81269abae7a6523dfc2e3f424fc4d08b | CN | — | — | unknown |
3172 | WsAppService.exe | HEAD | 200 | 2.16.186.90:80 | http://download.wondershare.com/com.wondershare.waf/com.wondershare.waf.updater_sku-ween_173.zip | unknown | — | — | whitelisted |
2584 | NFWCHk.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
3908 | RegAsm.exe | GET | 200 | 203.130.48.151:80 | http://was.wondershare.com/v1/?client_sign=%7BC4BA3647-FBFF-0005-06E3-5254004A04AF%7D&lang=en-US&method=member.info.getTmpMemberId&sku=sku-ween×tamp=1558410172&key=47342D1BEE153385294760BDDB8A7F49&vc=b2307e1a1a5f453845d6b39fe87ce69b | CN | text | 141 b | unknown |
3908 | RegAsm.exe | GET | 200 | 203.130.48.151:80 | http://was.wondershare.com/v1/?app_id=com.wondershare.waf&app_ver=237&client_sign=%7BC4BA3647-FBFF-0005-06E3-5254004A04AF%7D&lang=en-US&member_id=&method=app.info.upgrade&sku=sku-ween×tamp=1558410173&wafver=237&key=47342D1BEE153385294760BDDB8A7F49&vc=91fa4cb1c1f9626bda226e8136ec7727 | CN | html | 2.02 Kb | unknown |
3172 | WsAppService.exe | GET | 200 | 63.159.217.174:80 | http://was-stats.wondershare.com/stats/?appid=com.wondershare.waf&client_sign=%7BC4BA3647-FBFF-0005-06E3-5254004A04AF%7D&error_info=&language=en-US&log_id=09c83a02-631a-4778-8ffe-2312d3ac911a&member_id=U653AAAB014A2010B9&os=Win&osv=7&screen_pixel=1024x768&source=sku-ween&start_status=0&start_time=1558410174×tamp=1558410174&timezone=1&track=start&user_type=0&vid=2.4.3.237&wafver=2.4.3.237&key=47342D1BEE153385294760BDDB8A7F49&vc=9e2d3eb3d462a2e566d86e6ba3b7a138 | US | text | 2 b | suspicious |
3908 | RegAsm.exe | POST | 200 | 203.130.48.151:80 | http://was.wondershare.com/v1/?client_sign=%7BC4BA3647-FBFF-0005-06E3-5254004A04AF%7D&lang=en-US&member_id=&method=common.init.get&sku=sku-ween×tamp=1558410172&wafver=2.4.3.237&key=47342D1BEE153385294760BDDB8A7F49&vc=56c367467318bf6f22b8bf3cbdd59c02 | CN | text | 2.47 Kb | unknown |
3908 | RegAsm.exe | GET | 200 | 63.159.217.174:80 | http://was-stats.wondershare.com/stats/?appid=com.wondershare.waf&client_sign=%7BC4BA3647-FBFF-0005-06E3-5254004A04AF%7D&error_info=&language=en-US&log_id=836645e7-e63b-4e63-8a32-463c42852e95&member_id=U653AAAB014A2010B9&os=Win&osv=7&screen_pixel=1280x720&source=sku-ween&start_status=0&start_time=1558410170×tamp=1558410173&timezone=1&track=start&user_type=0&vid=2.4.3.237&wafver=2.4.3.237&key=47342D1BEE153385294760BDDB8A7F49&vc=ea482bcecadc7be47def24e5f9cd57fc | US | text | 2 b | suspicious |
3172 | WsAppService.exe | GET | 200 | 63.159.217.174:80 | http://was-stats.wondershare.com/stats/?appid=com.wondershare.waf&client_sign=%7BC4BA3647-FBFF-0005-06E3-5254004A04AF%7D&download_fail_time=0&download_start_time=1558410175&download_success_time=1558410176&error_code=0&error_info=&language=en-US&log_id=09c83a02-631a-4778-8ffe-2312d3ac911a&member_id=U653AAAB014A2010B9&os=Win&osv=7&package_id=com.wondershare.waf.updater&package_versionname=2.1.6&screen_pixel=1024x768&source=sku-ween×tamp=1558410176&timezone=1&track=package_download&user_type=0&vid=2.4.3.237&wafver=2.4.3.237&key=47342D1BEE153385294760BDDB8A7F49&vc=34f9cdaf47c4eeef2798c71b42ff01eb | US | text | 2 b | suspicious |
3172 | WsAppService.exe | GET | 206 | 2.16.186.90:80 | http://download.wondershare.com/com.wondershare.waf/com.wondershare.waf.updater_sku-ween_173.zip | unknown | compressed | 25.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2584 | NFWCHk.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3172 | WsAppService.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
3172 | WsAppService.exe | 114.114.114.114:53 | — | Cogent Communications | CN | malicious |
3172 | WsAppService.exe | 208.67.222.222:53 | — | OpenDNS, LLC | US | malicious |
3172 | WsAppService.exe | 218.192.240.2:53 | — | China Education and Research Network Center | CN | unknown |
3172 | WsAppService.exe | 2.16.186.90:80 | download.wondershare.com | Akamai International B.V. | — | whitelisted |
3908 | RegAsm.exe | 203.130.48.151:80 | was.wondershare.com | QUANTIL, INC | CN | unknown |
3172 | WsAppService.exe | 63.159.217.174:80 | was-stats.wondershare.com | QUANTIL, INC | US | suspicious |
3908 | RegAsm.exe | 63.159.217.174:80 | was-stats.wondershare.com | QUANTIL, INC | US | suspicious |
3172 | WsAppService.exe | 203.130.48.151:80 | was.wondershare.com | QUANTIL, INC | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
us.wondershare.com |
| unknown |
was.wondershare.com |
| unknown |
was-stats.wondershare.com |
| suspicious |
download.wondershare.com |
| whitelisted |
Threats
Process | Message |
|---|---|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|