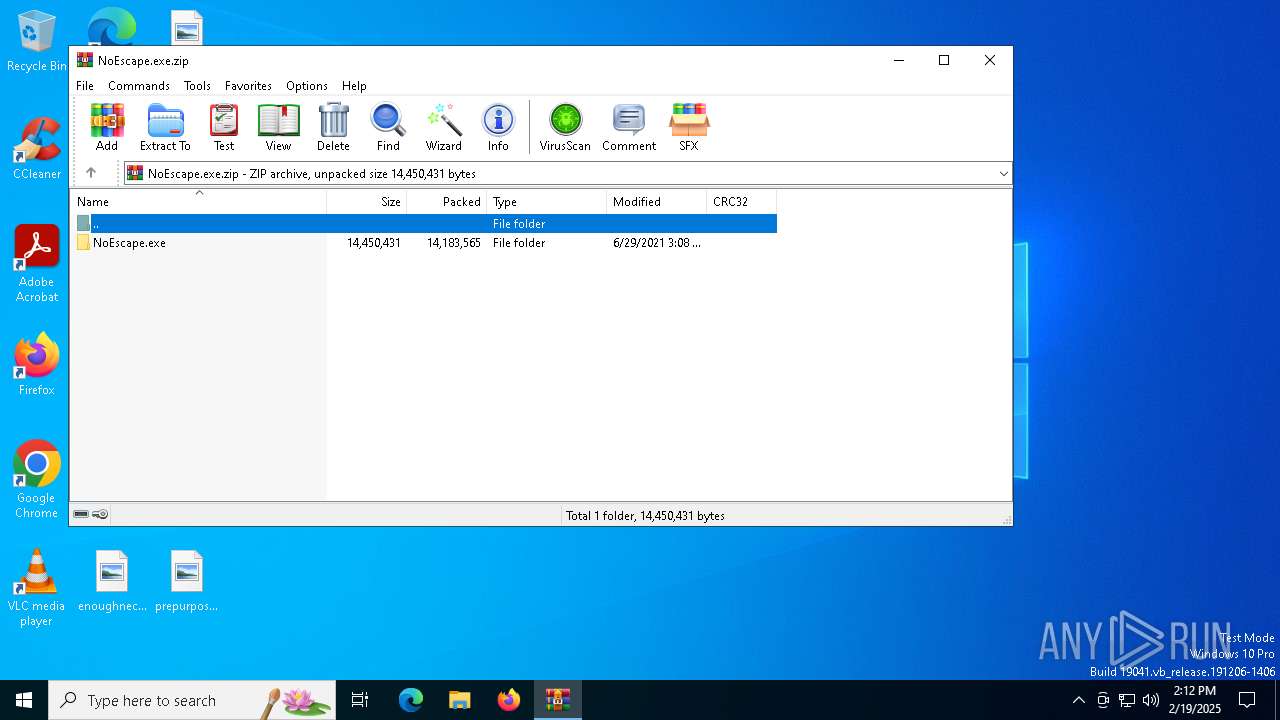
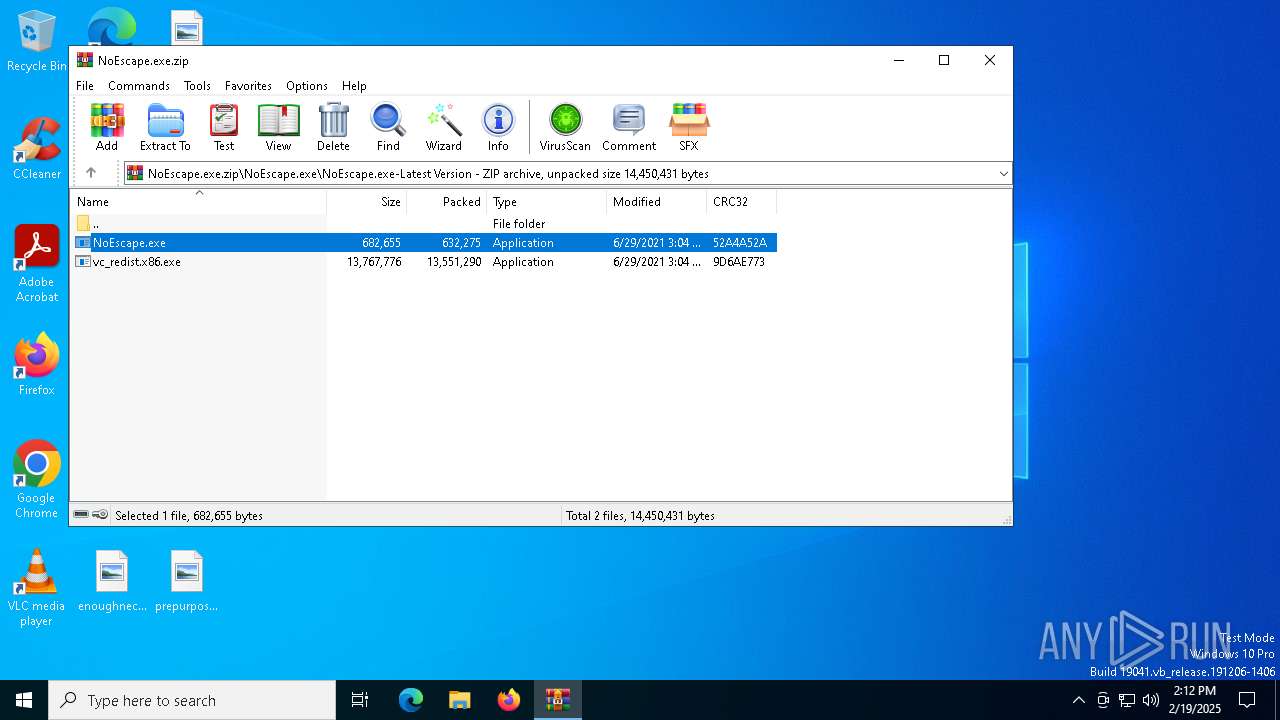
| download: | /Sn8ow/NoEscape.exe_Virus/releases/download/1.0.0/NoEscape.exe.zip |
| Full analysis: | https://app.any.run/tasks/c13b6f44-4069-4c3a-b876-8a9072a21f6a |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2025, 14:11:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 660708319A500F1865FA9D2FADFA712D |
| SHA1: | B2AE3AEF17095AB26410E0F1792A379A4A2966F8 |
| SHA256: | 542C2E1064BE8CD8393602F63B793E9D34EB81B1090A3C80623777F17FA25C6C |
| SSDEEP: | 393216:BATeK1bYlJbM9tAlAkRCnG7H+KlzMNCPm5lvvayDPk15DBJ:BoX16blXonYeKdKCPGayDPiJ |
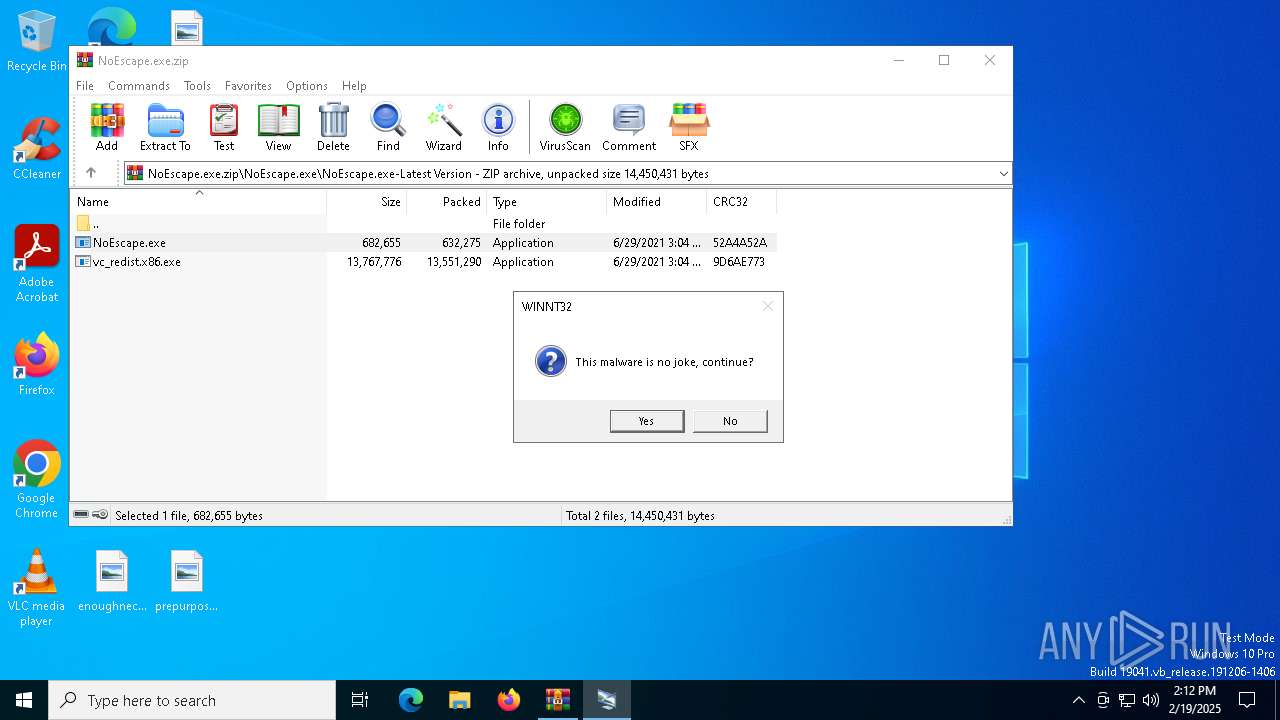
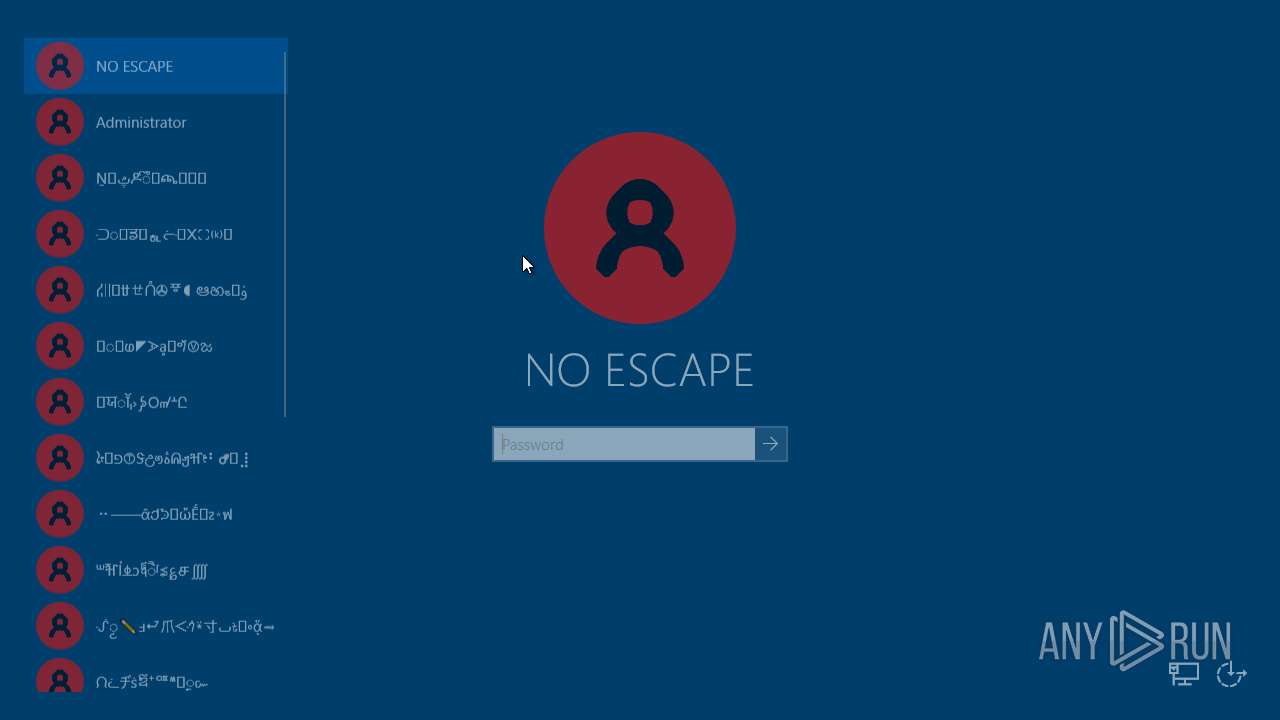
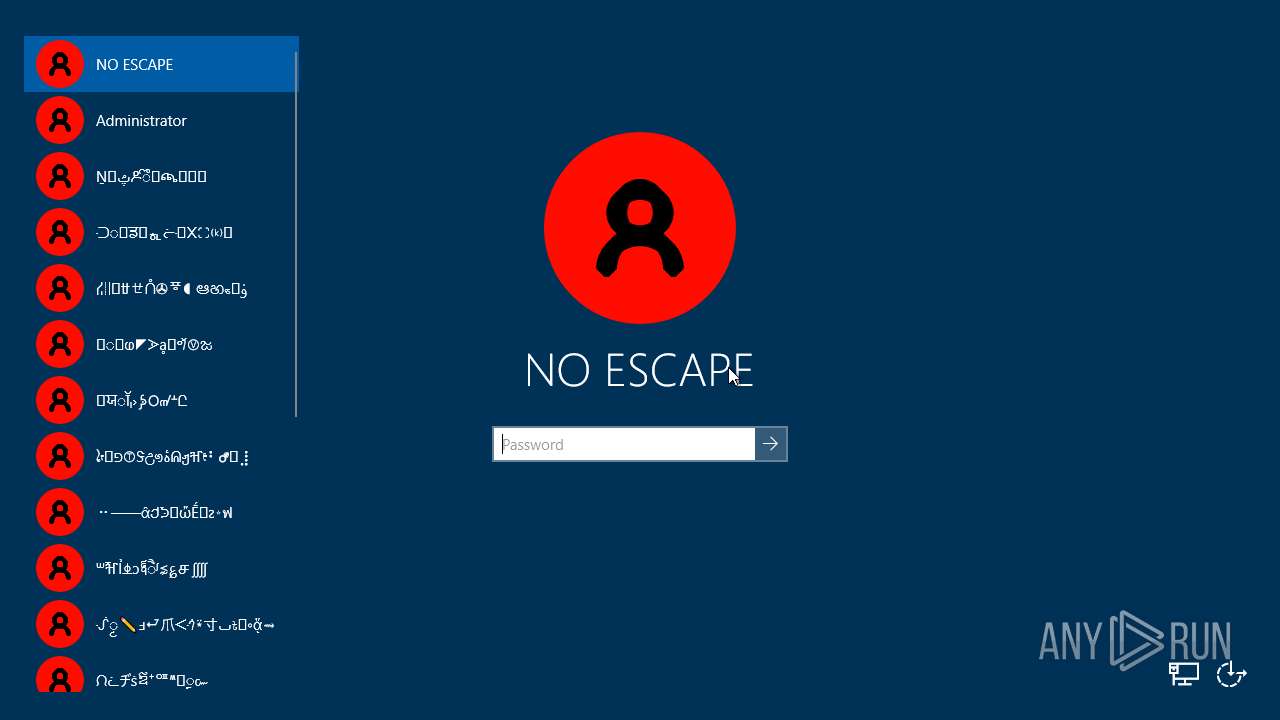
MALICIOUS
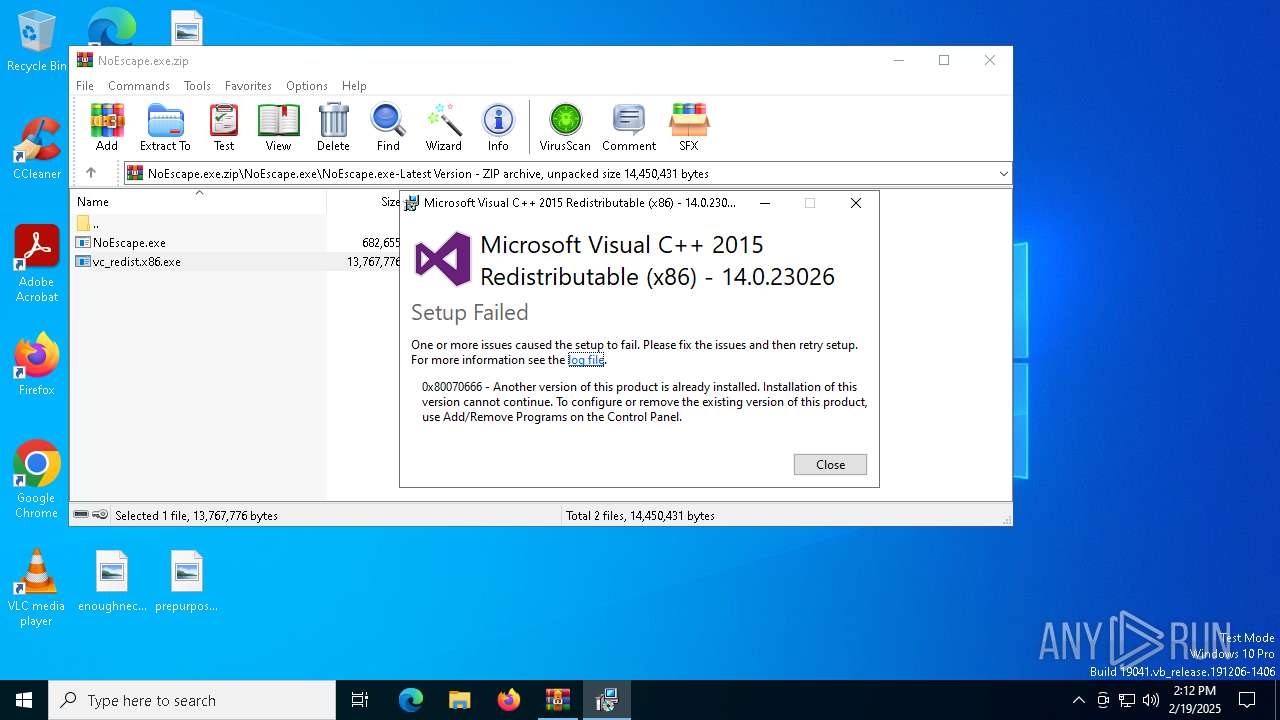
Executing a file with an untrusted certificate
- vc_redist.x86.exe (PID: 6952)
UAC/LUA settings modification
- NoEscape.exe (PID: 5460)
Changes the login/logoff helper path in the registry
- NoEscape.exe (PID: 5460)
NOESCAPE has been detected
- NoEscape.exe (PID: 5460)
Disables the Shutdown in the Start menu
- NoEscape.exe (PID: 5460)
SUSPICIOUS
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 6952)
Searches for installed software
- vc_redist.x86.exe (PID: 6952)
Executable content was dropped or overwritten
- vc_redist.x86.exe (PID: 6952)
- NoEscape.exe (PID: 5460)
Application launched itself
- NoEscape.exe (PID: 7144)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5696)
- NoEscape.exe (PID: 7144)
- ShellExperienceHost.exe (PID: 5540)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5696)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5696)
Checks supported languages
- vc_redist.x86.exe (PID: 6952)
- NoEscape.exe (PID: 7144)
- NoEscape.exe (PID: 5460)
- ShellExperienceHost.exe (PID: 5540)
Reads the computer name
- vc_redist.x86.exe (PID: 6952)
- NoEscape.exe (PID: 7144)
- NoEscape.exe (PID: 5460)
- ShellExperienceHost.exe (PID: 5540)
Create files in a temporary directory
- vc_redist.x86.exe (PID: 6952)
Process checks computer location settings
- NoEscape.exe (PID: 7144)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5696)
Creates files or folders in the user directory
- NoEscape.exe (PID: 5460)
Creates files in the program directory
- NoEscape.exe (PID: 5460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:06:29 17:08:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | NoEscape.exe/ |
Total processes
214
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
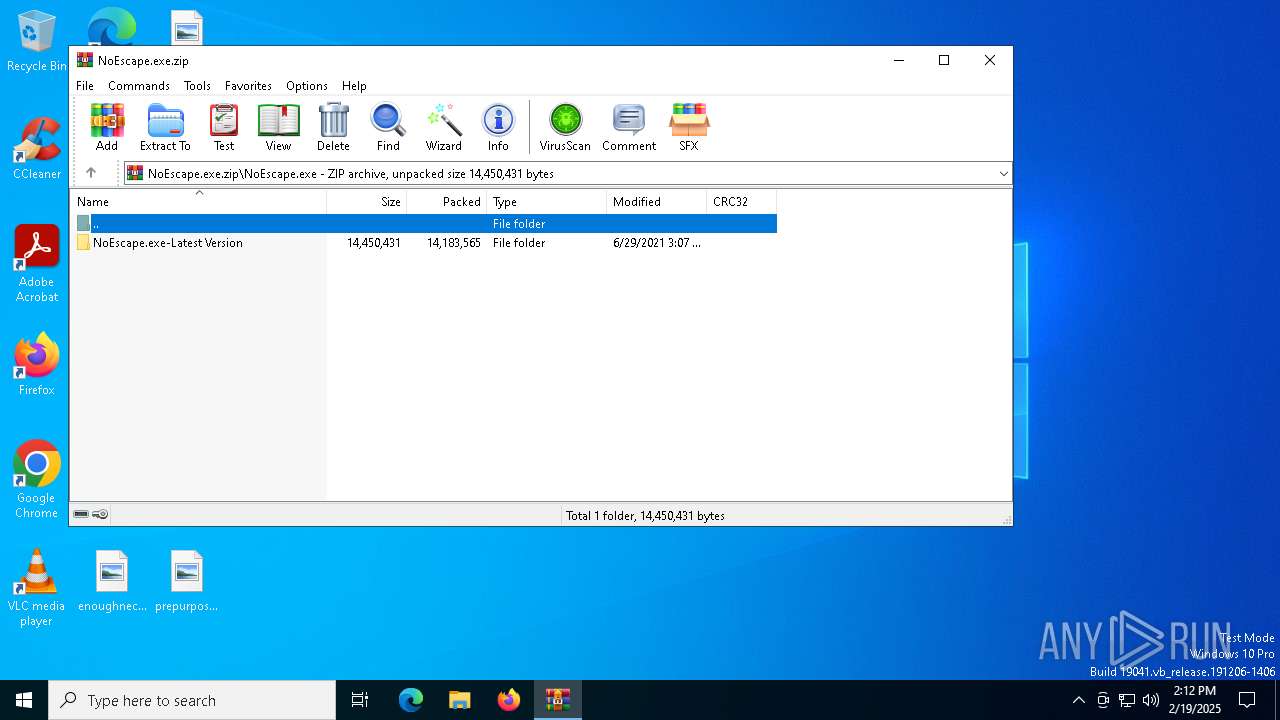
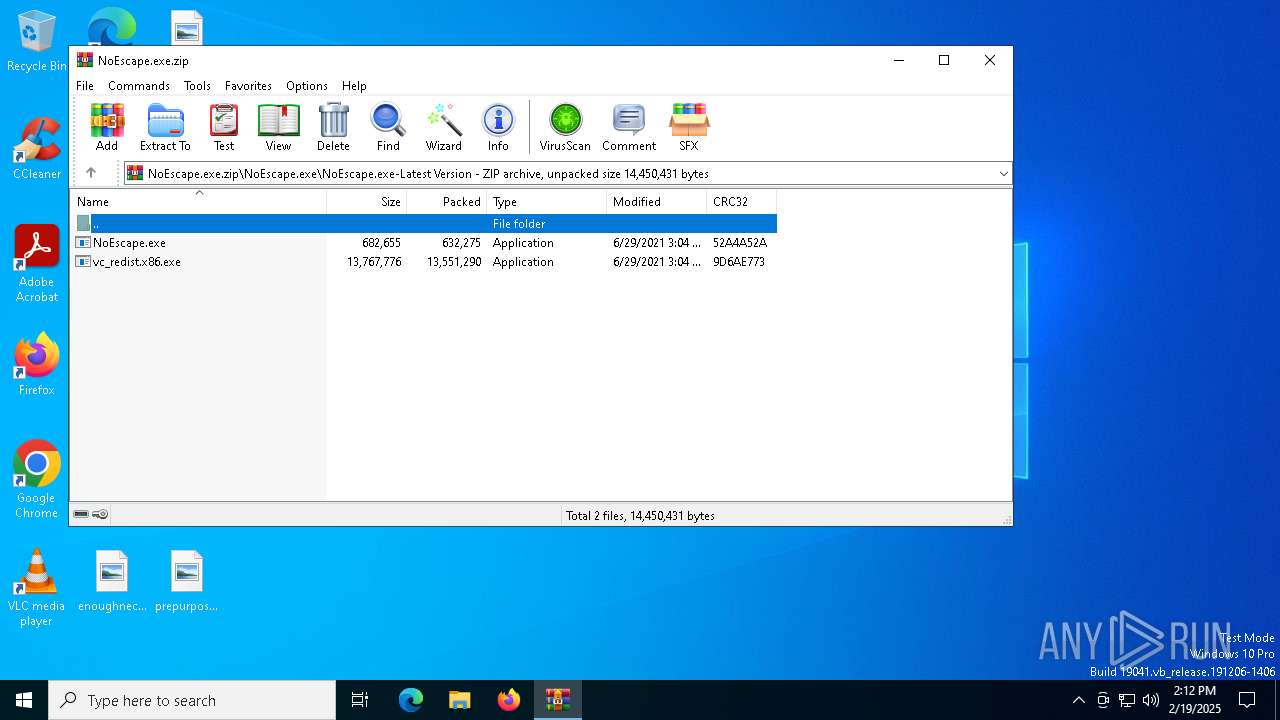
| 5460 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5696.15886\NoEscape.exe\NoEscape.exe-Latest Version\NoEscape.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5696.15886\NoEscape.exe\NoEscape.exe-Latest Version\NoEscape.exe | NoEscape.exe | ||||||||||||
User: admin Company: Endermanch Integrity Level: HIGH Description: Windows Customization Tool Exit code: 0 Version: 6.6.6.6 Modules
| |||||||||||||||
| 5540 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
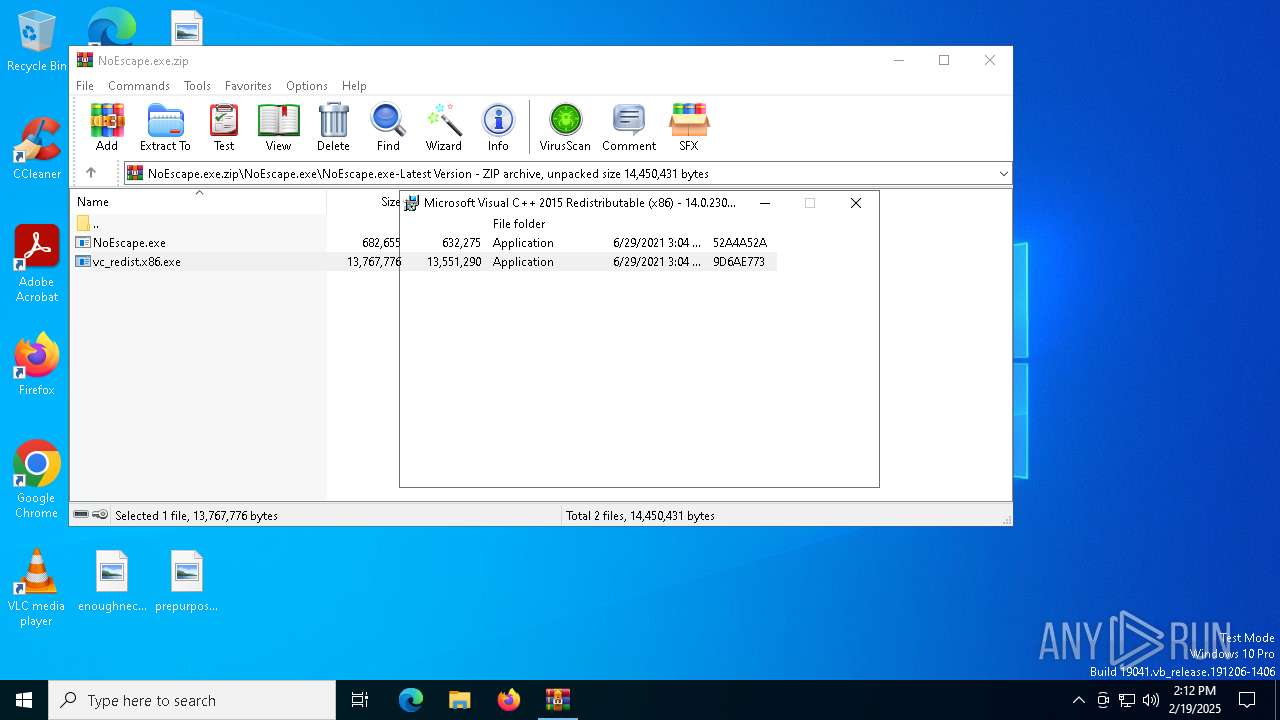
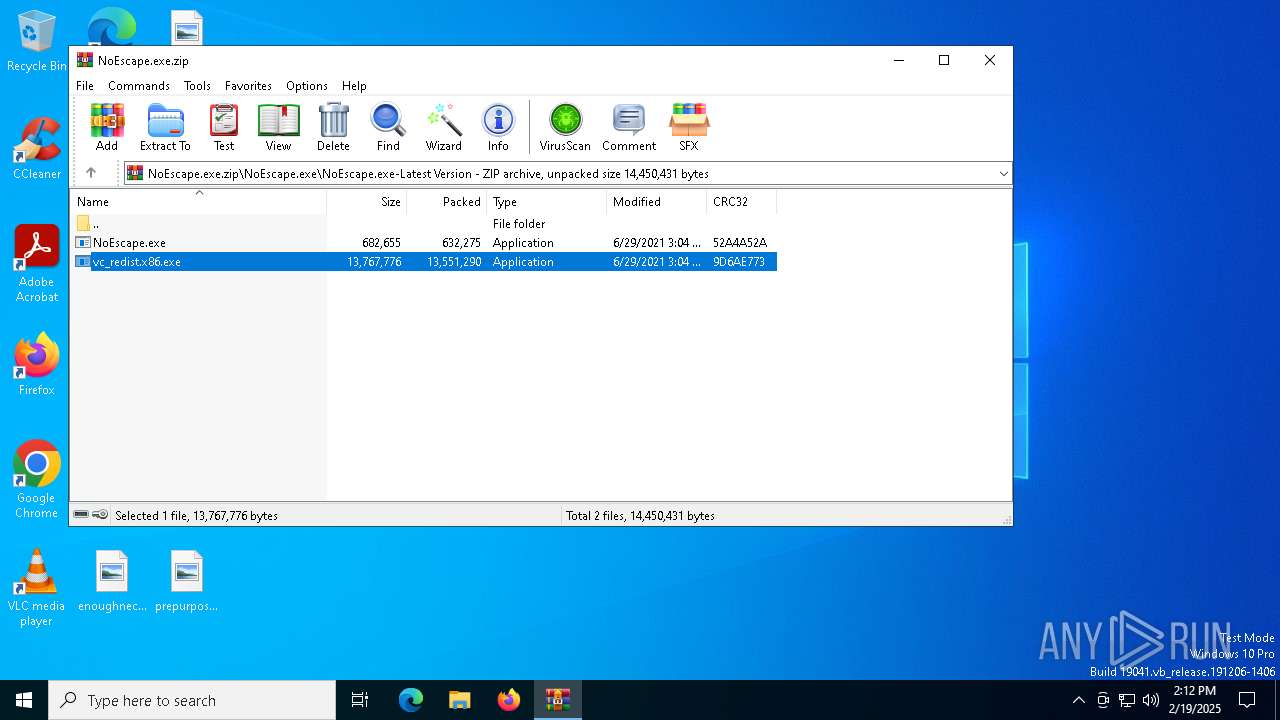
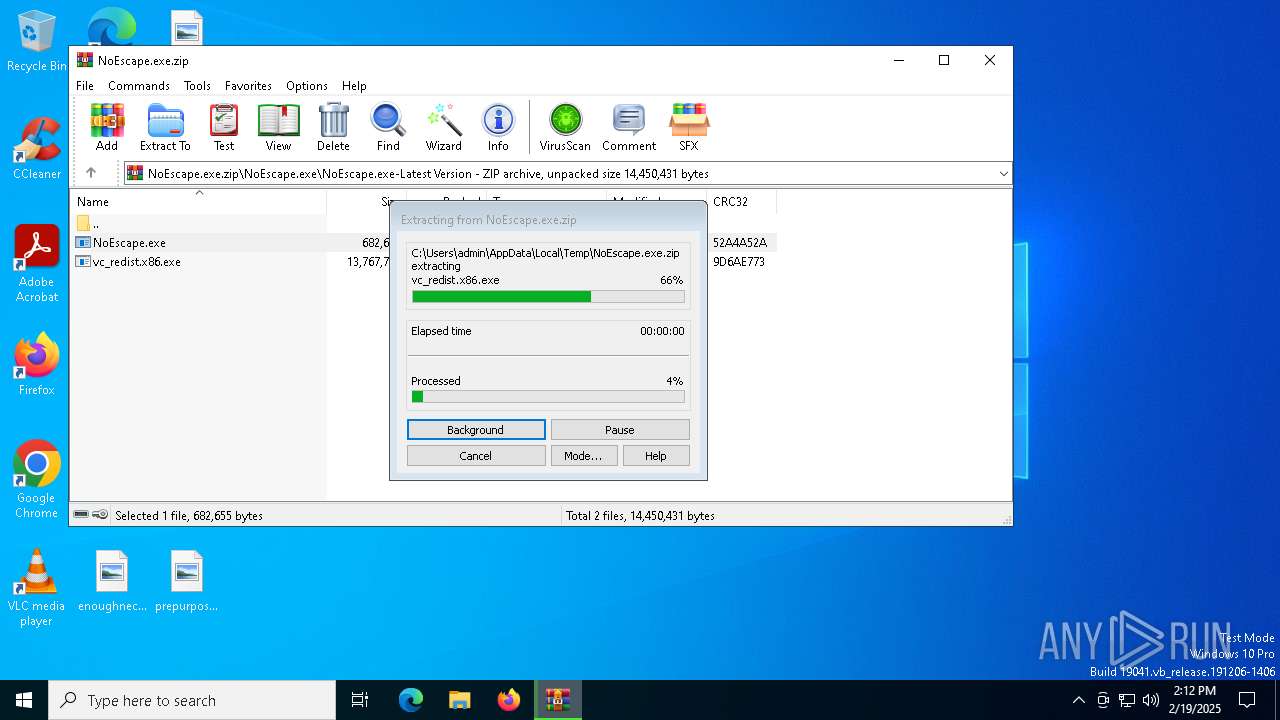
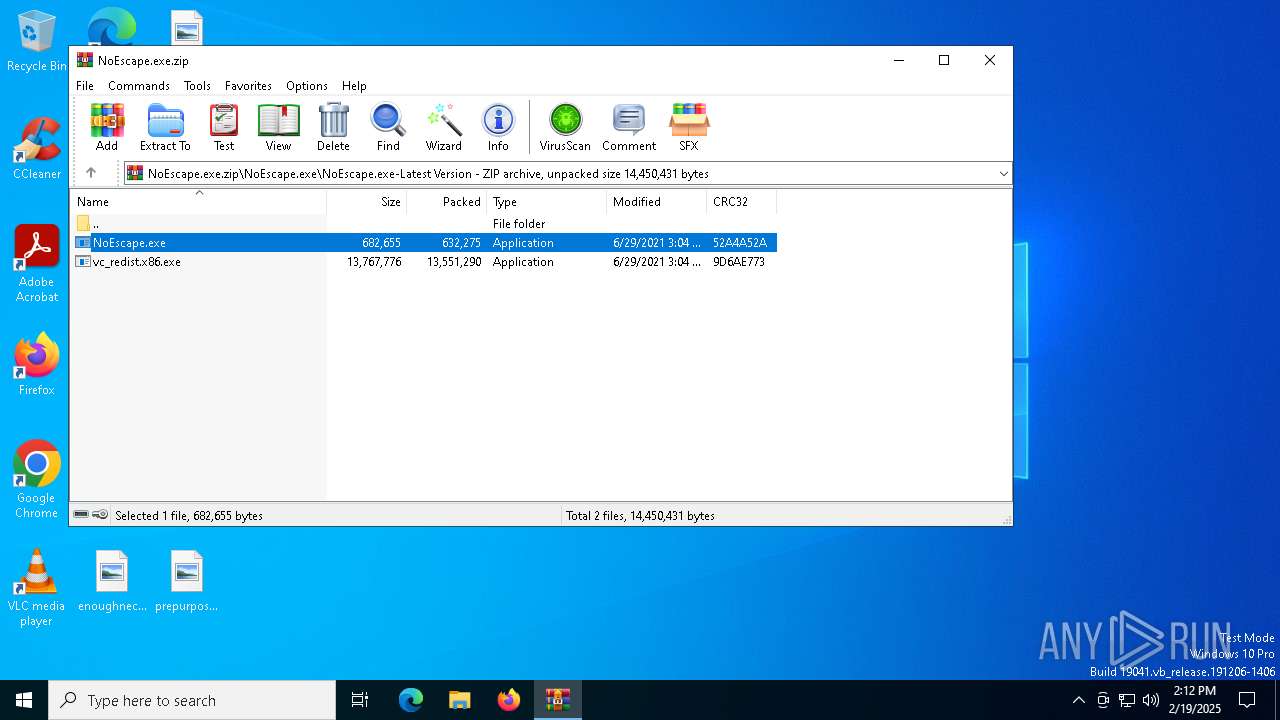
| 5696 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\NoEscape.exe.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.91.0 Modules
| |||||||||||||||
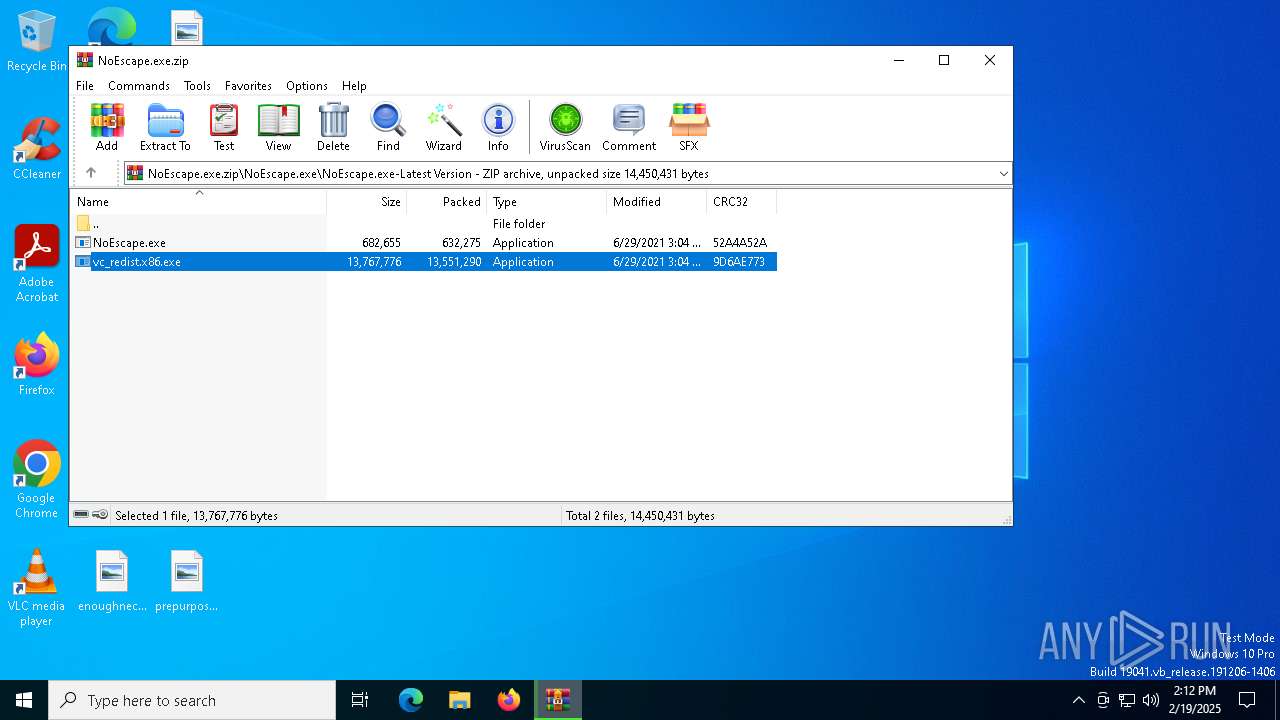
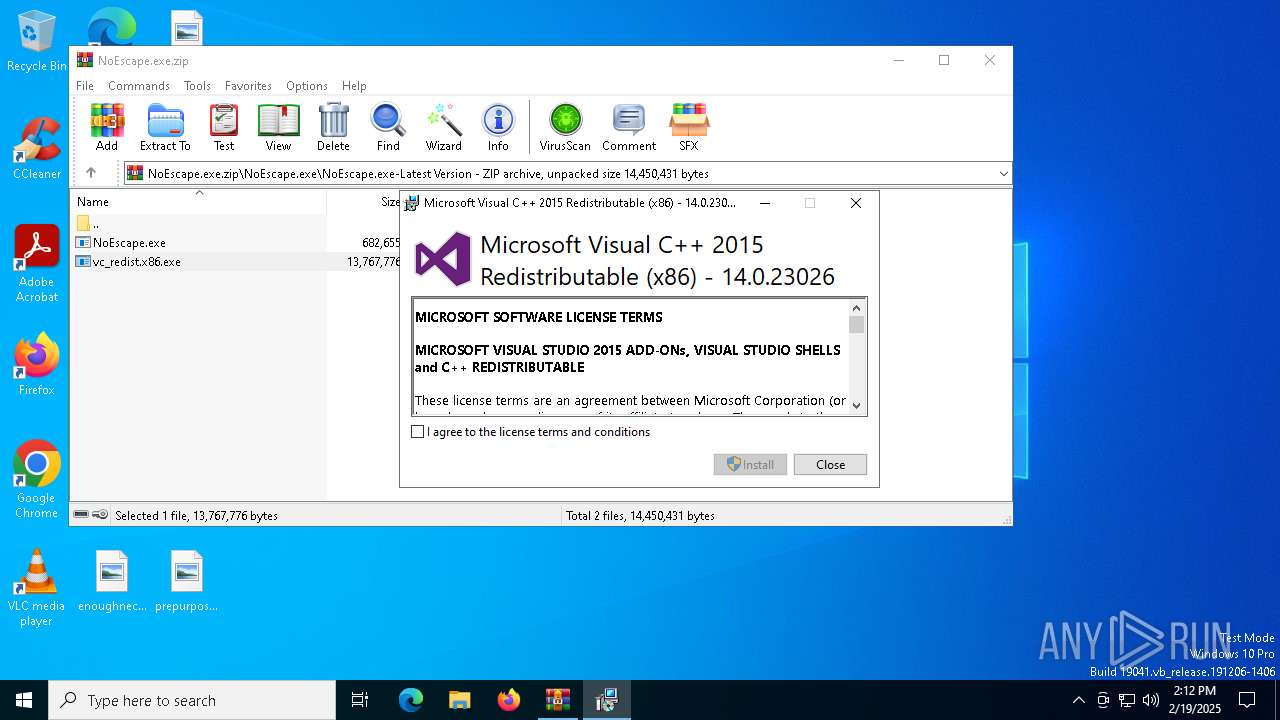
| 6952 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5696.14880\NoEscape.exe\NoEscape.exe-Latest Version\vc_redist.x86.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5696.14880\NoEscape.exe\NoEscape.exe-Latest Version\vc_redist.x86.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
| 7144 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5696.15886\NoEscape.exe\NoEscape.exe-Latest Version\NoEscape.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5696.15886\NoEscape.exe\NoEscape.exe-Latest Version\NoEscape.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Endermanch Integrity Level: MEDIUM Description: Windows Customization Tool Exit code: 0 Version: 6.6.6.6 Modules
| |||||||||||||||
Total events
4 111
Read events
4 088
Write events
23
Delete events
0
Modification events
| (PID) Process: | (5696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NoEscape.exe.zip | |||
| (PID) Process: | (5696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5460) NoEscape.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | AutoAdminLogon |
Value: 0 | |||
| (PID) Process: | (5460) NoEscape.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | DisableCAD |
Value: 1 | |||
Executable files
6
Suspicious files
166
Text files
39
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1029\license.rtf | text | |
MD5:FD8353F3BC88A47B8880B59A5DAD3F03 | SHA256:2428E8BA8FC9648422333B6B4B92FB476741FC1022DE7CB59D030EC35CC21AC7 | |||
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1042\license.rtf | text | |
MD5:F6E7A2A05EFB4413295C156A179578A3 | SHA256:DCEFD9B37D78F37ED8AAEF70AC2BFCDE441DCFB97469A6AA6AF89C1FFADBF814 | |||
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1040\license.rtf | text | |
MD5:1D07E27F97CE22A58780A04227BE6465 | SHA256:F1214784C57AA3323426AF64D132045970717994EBA500B25283684DC1ADEBAA | |||
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1041\license.rtf | text | |
MD5:0D9DD57746D5609494B35314FA88FD93 | SHA256:AC0D8E0EAAB1875909A6A6F106A37CD7468F87F71887A44263F5F0178F99C40B | |||
| 5696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5696.14880\NoEscape.exe\NoEscape.exe-Latest Version\vc_redist.x86.exe | executable | |
MD5:1A15E6606BAC9647E7AD3CAA543377CF | SHA256:FDD1E1F0DCAE2D0AA0720895EFF33B927D13076E64464BB7C7E5843B7667CD14 | |||
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1036\license.rtf | text | |
MD5:6F70759DF32F212DBB65464258ECEEAF | SHA256:C7F03DA5D9A7F689B8DCBD507FF0B3FA98DABA55616F902E5E47E9839B753E1F | |||
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1046\license.rtf | text | |
MD5:137A9579BA2E02EBB87817440FCBDCB9 | SHA256:42DC678EF9D5E4E147BF178FFE2FA3CD4BBBF9C904872B4E344D8BB22C473ED5 | |||
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1045\license.rtf | text | |
MD5:A0D88589A339E57E412AB01E763D6A27 | SHA256:898D5CA01A3271D97350D06A6CCDB8803A176BB42BAF7E2C8F76C9037235CA8E | |||
| 6952 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\thm.xml | xml | |
MD5:0056F10A42638EA8B4BEFC614741DDD6 | SHA256:6B1BA0DEA830E556A58C883290FAA5D49C064E546CBFCD0451596A10CC693F87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
42
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6996 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6996 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6392 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4040 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 184.86.251.27:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.79.89.142:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 184.86.251.27:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1076 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |