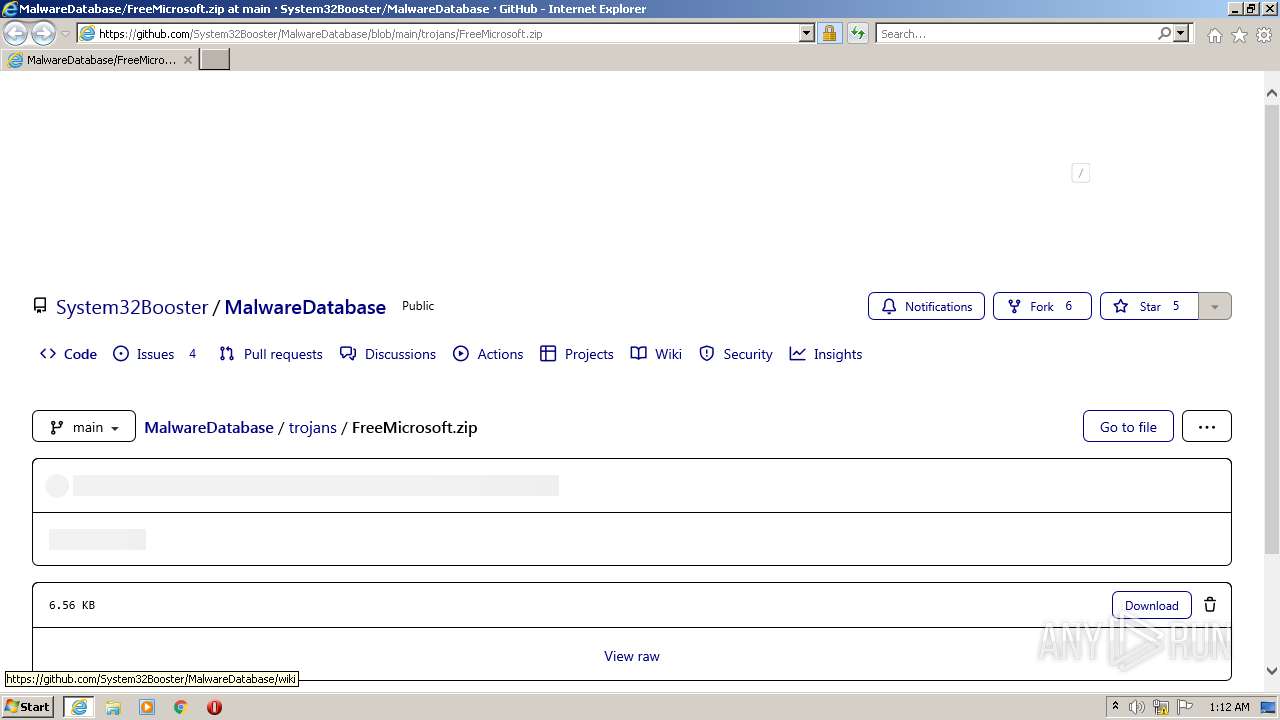
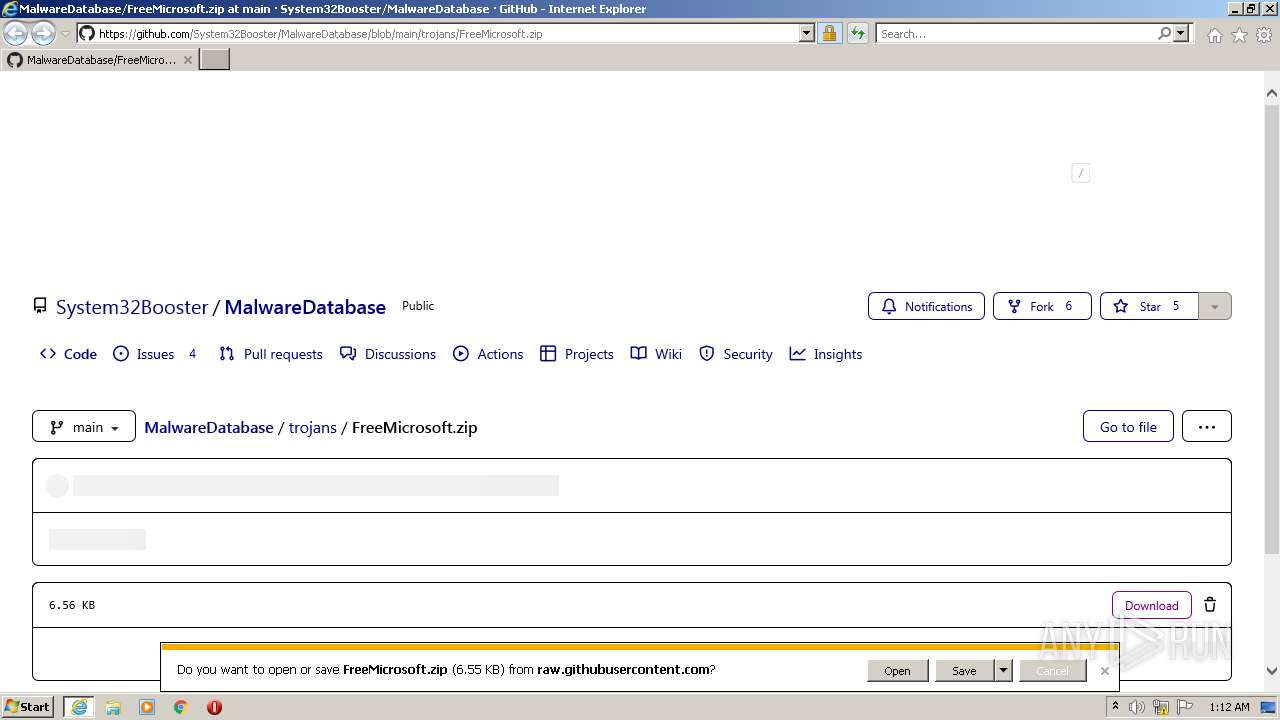
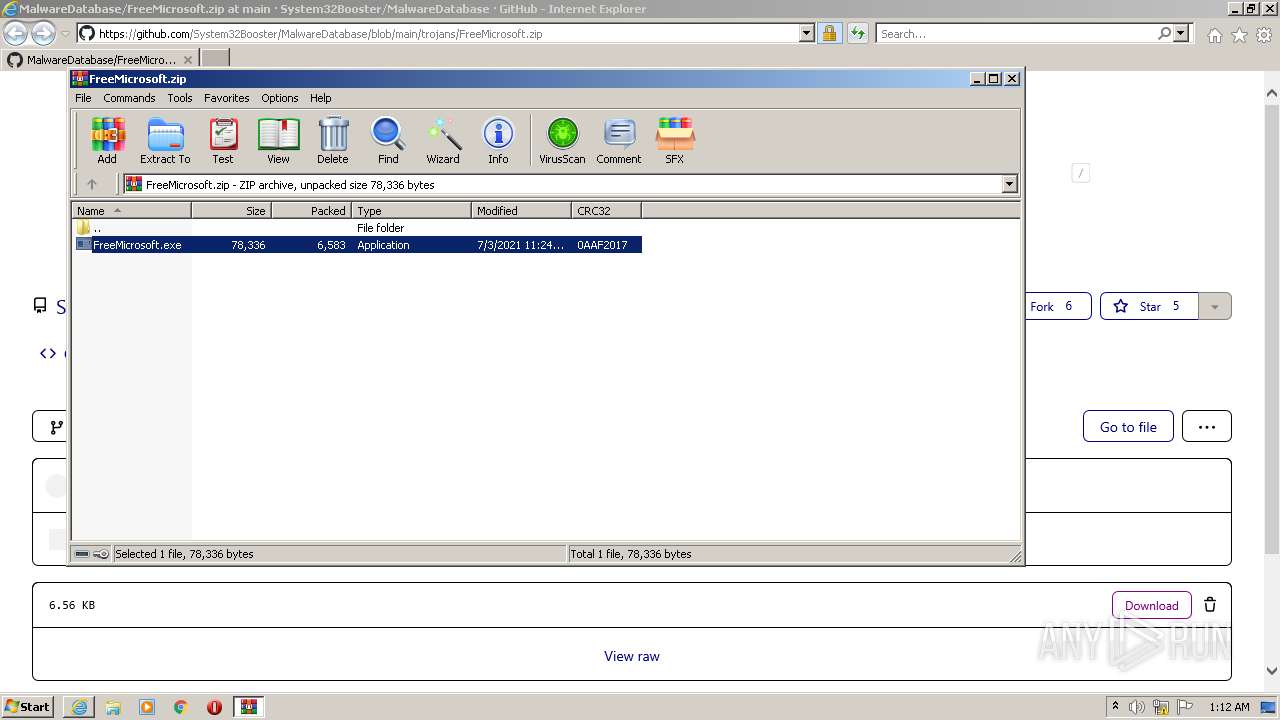
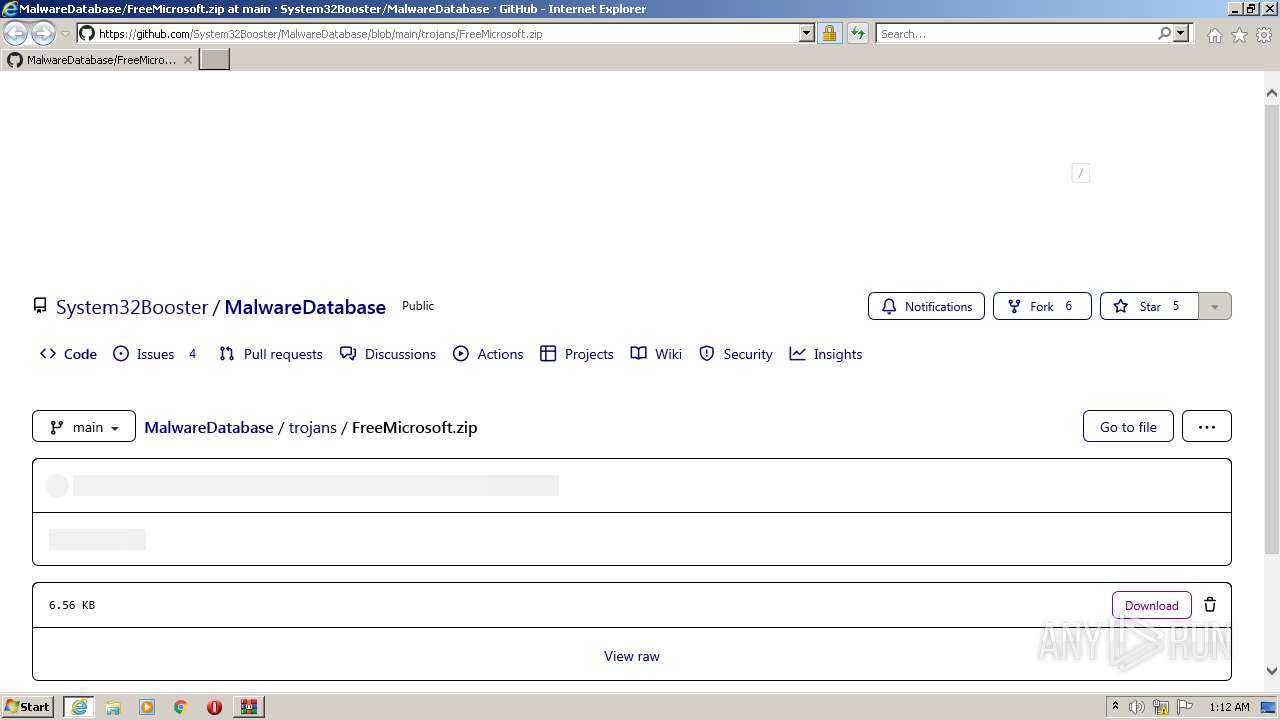
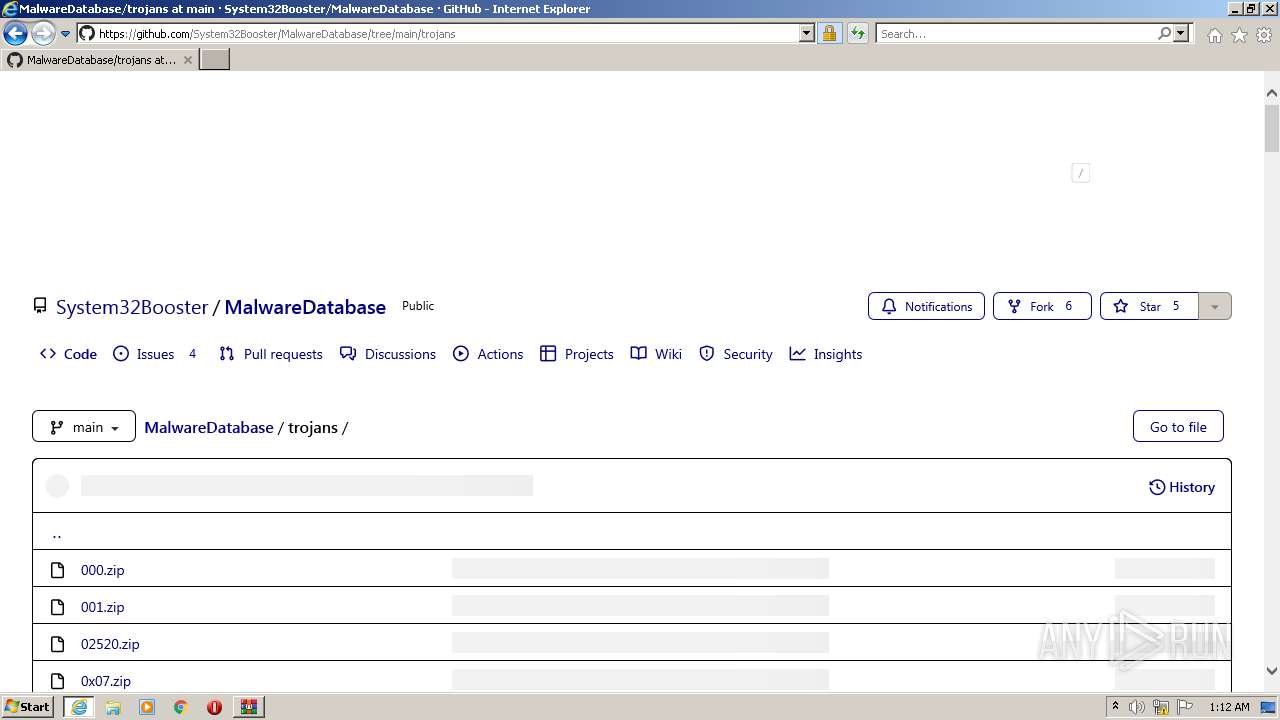
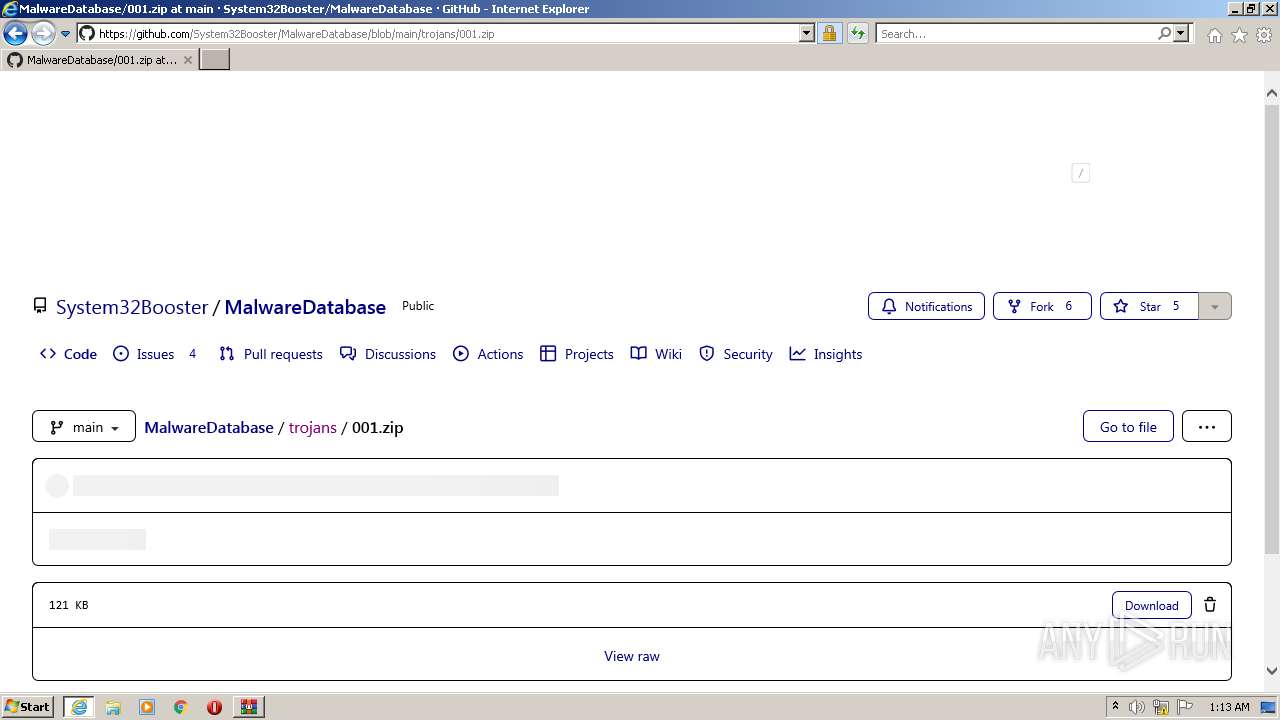
| URL: | https://github.com/System32Booster/MalwareDatabase/blob/main/trojans/FreeMicrosoft.zip |
| Full analysis: | https://app.any.run/tasks/bcd377af-4a2a-421f-95ae-007350931e7f |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2022, 00:12:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 794A9E5D9341B938610EF61A6BC825B0 |
| SHA1: | 0EBE70D5CD1E932F7475EC55645D0F38AC4CFCF6 |
| SHA256: | 5428CE1845F207BC1B0CA608A3187D7D56FDB4C92B817FEE04B922701F9359FB |
| SSDEEP: | 3:N8tEdyAr6DWENqkzEROAqYtc:2u8Ar6lnzsOaq |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 456)
- WinRAR.exe (PID: 2780)
- 001.exe (PID: 1124)
- cmd.exe (PID: 1564)
Application was dropped or rewritten from another process
- FreeMicrosoft.exe (PID: 2332)
- FreeMicrosoft.exe (PID: 2980)
- 001.exe (PID: 3828)
- 001.exe (PID: 1124)
Changes the login/logoff helper path in the registry
- 001.exe (PID: 1124)
Disables registry editing tools (regedit)
- 001.exe (PID: 1124)
Task Manager has been disabled (taskmgr)
- 001.exe (PID: 1124)
Writes to a start menu file
- cmd.exe (PID: 1564)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3744)
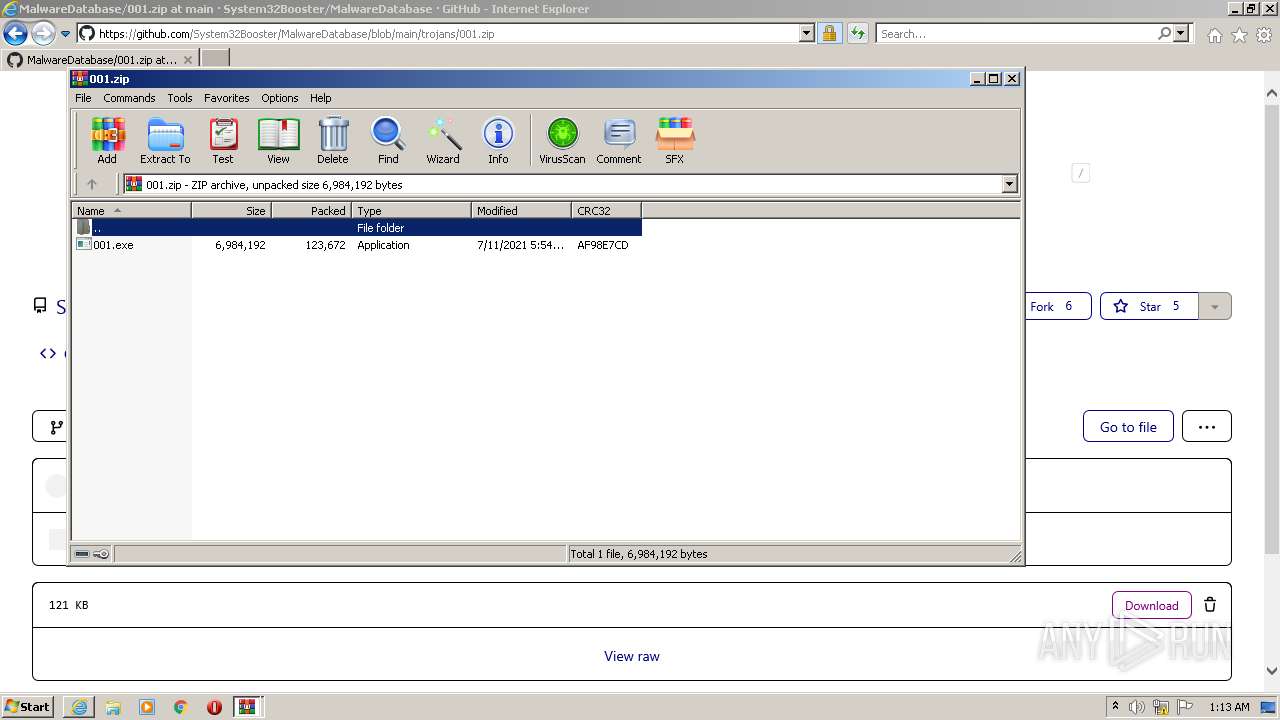
Drops a file with a compile date too recent
- WinRAR.exe (PID: 456)
- WinRAR.exe (PID: 2780)
- 001.exe (PID: 1124)
- cmd.exe (PID: 1564)
Checks supported languages
- WinRAR.exe (PID: 456)
- FreeMicrosoft.exe (PID: 2980)
- WinRAR.exe (PID: 2780)
- 001.exe (PID: 1124)
- cmd.exe (PID: 1564)
- WMIC.exe (PID: 3260)
- WMIC.exe (PID: 2352)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 456)
- WinRAR.exe (PID: 2780)
- 001.exe (PID: 1124)
- cmd.exe (PID: 1564)
Reads the computer name
- WinRAR.exe (PID: 456)
- WinRAR.exe (PID: 2780)
- 001.exe (PID: 1124)
- WMIC.exe (PID: 3260)
- WMIC.exe (PID: 2352)
Changes the desktop background image
- 001.exe (PID: 1124)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1564)
Starts CMD.EXE for commands execution
- 001.exe (PID: 1124)
Creates files in the program directory
- cmd.exe (PID: 1564)
INFO
Reads the computer name
- iexplore.exe (PID: 1332)
- iexplore.exe (PID: 3744)
- taskkill.exe (PID: 3044)
- taskkill.exe (PID: 1608)
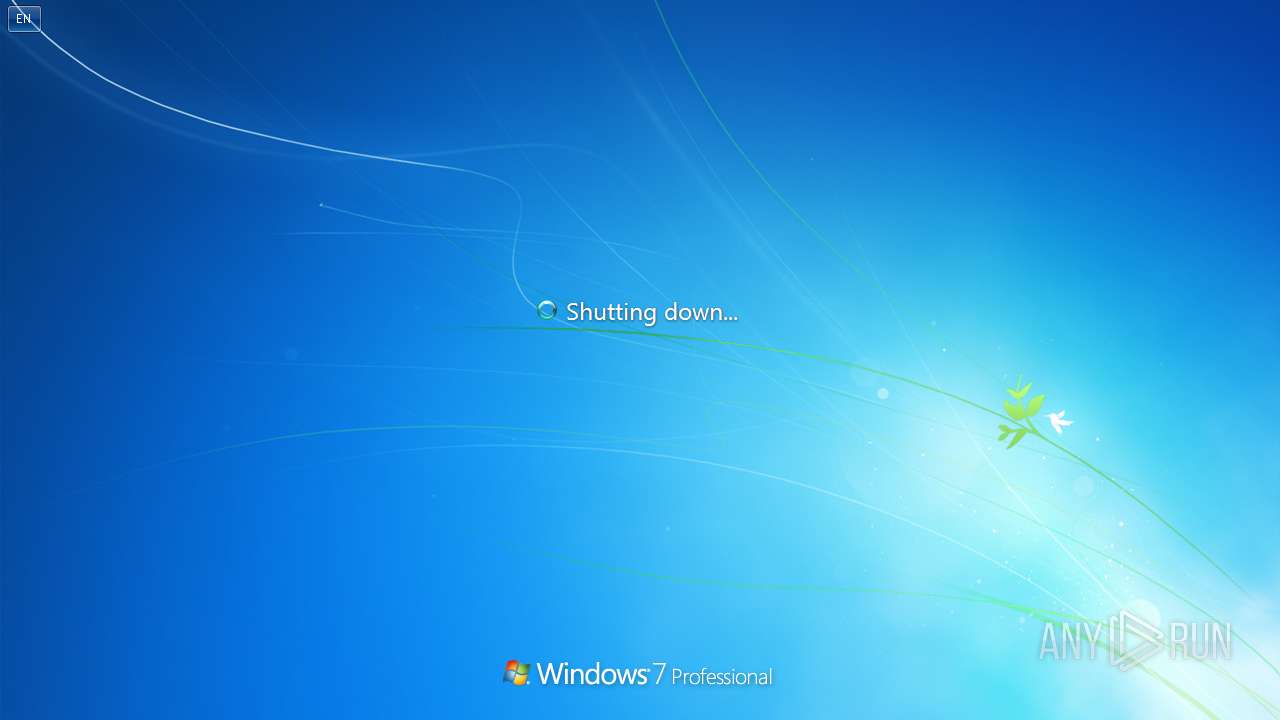
- shutdown.exe (PID: 4032)
- WISPTIS.EXE (PID: 2816)
Reads settings of System Certificates
- iexplore.exe (PID: 3744)
- iexplore.exe (PID: 1332)
Changes internet zones settings
- iexplore.exe (PID: 1332)
Reads internet explorer settings
- iexplore.exe (PID: 3744)
Checks supported languages
- iexplore.exe (PID: 1332)
- iexplore.exe (PID: 3744)
- taskkill.exe (PID: 3044)
- taskkill.exe (PID: 1608)
- WISPTIS.EXE (PID: 2816)
- shutdown.exe (PID: 4032)
Application launched itself
- iexplore.exe (PID: 1332)
Creates files in the user directory
- iexplore.exe (PID: 3744)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1332)
Checks Windows Trust Settings
- iexplore.exe (PID: 3744)
- iexplore.exe (PID: 1332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
16
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
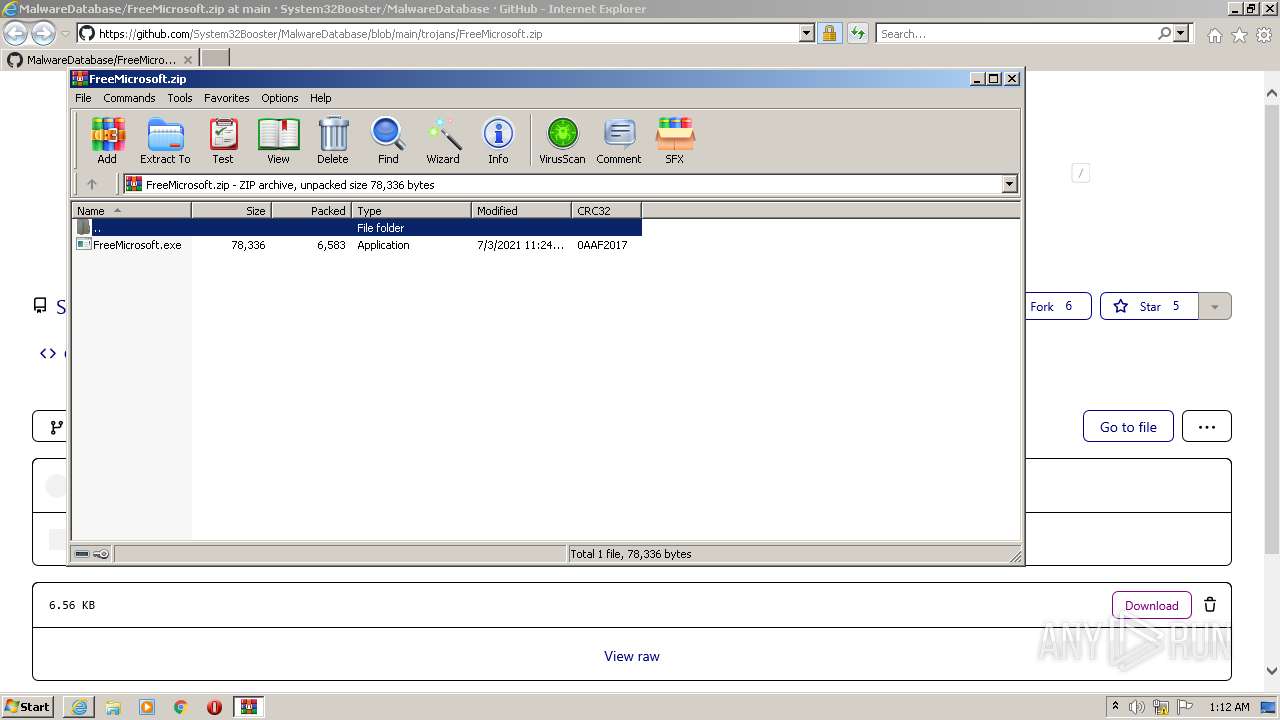
| 456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\FreeMicrosoft.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.91.0 Modules
| |||||||||||||||
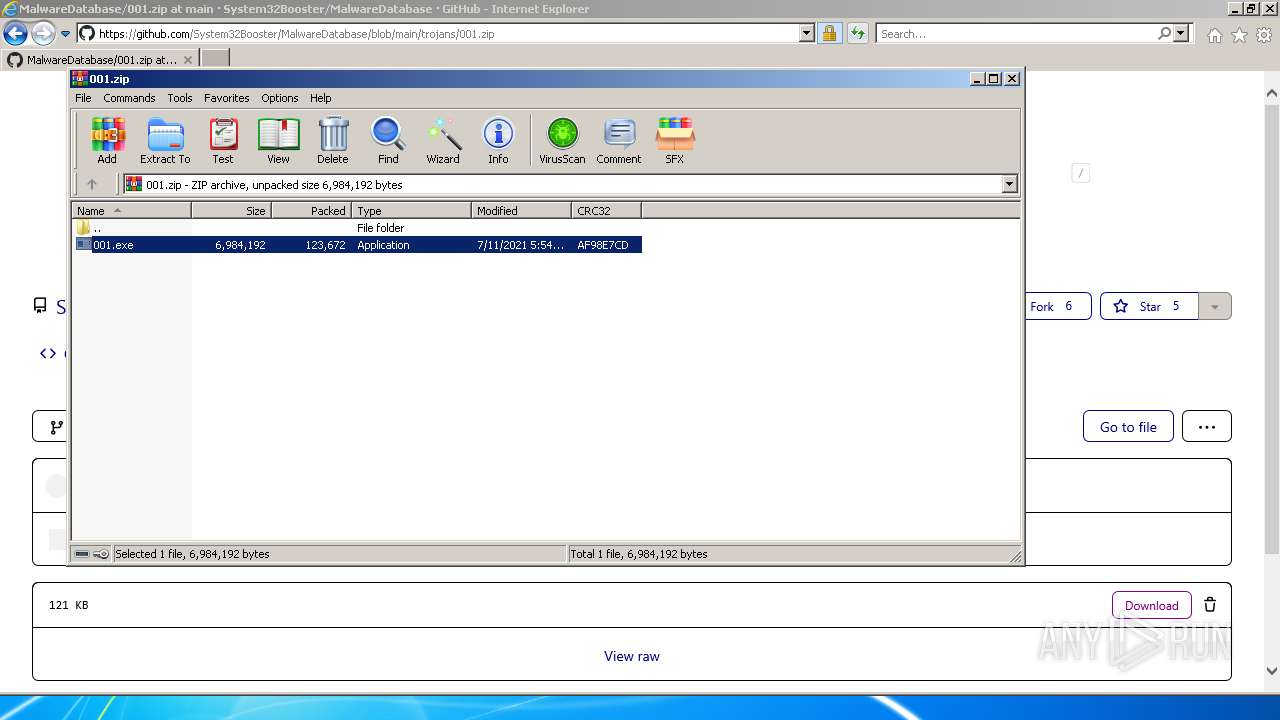
| 1124 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2780.44649\001.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2780.44649\001.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 000 Exit code: 1073807364 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/System32Booster/MalwareDatabase/blob/main/trojans/FreeMicrosoft.zip" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1073807364 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1564 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\windl.bat"" | C:\Windows\system32\cmd.exe | 001.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1608 | taskkill /f /im taskmgr.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa456.41582\FreeMicrosoft.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa456.41582\FreeMicrosoft.exe | — | WinRAR.exe | |||||||||||
User: admin Company: FreeMicrosoft Inc. Integrity Level: MEDIUM Description: Free Microsoft Products Activation Exit code: 3221226540 Version: 6.6.6.6 Modules
| |||||||||||||||
| 2352 | wmic useraccount where name='admin' rename 'ăé═é¿æOé╛üI Death' | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
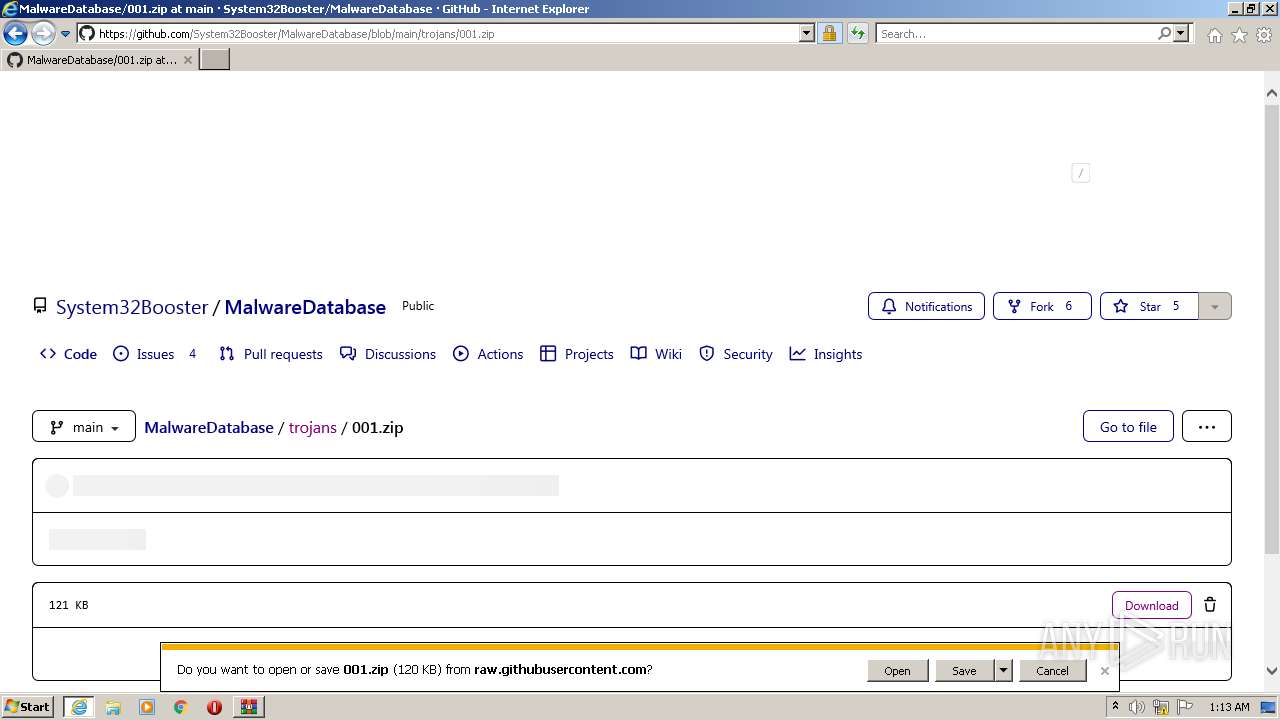
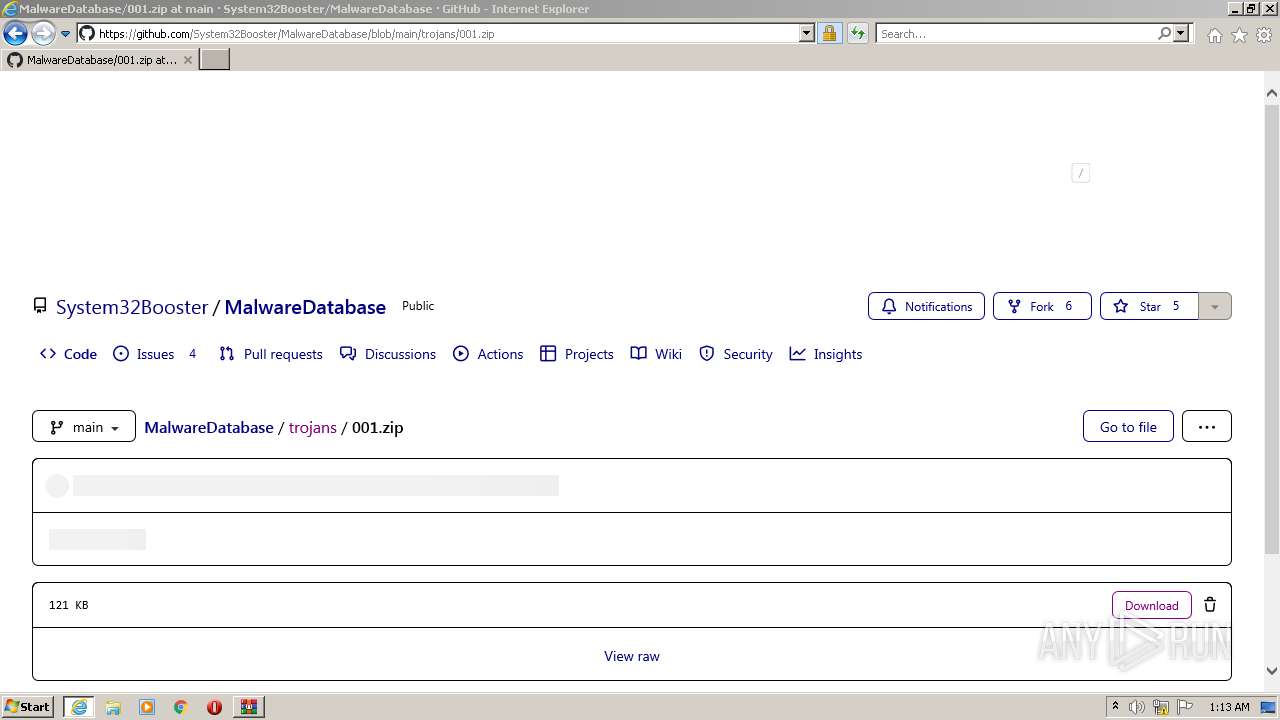
| 2780 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\001.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.91.0 Modules
| |||||||||||||||
| 2816 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | 001.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa456.41582\FreeMicrosoft.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa456.41582\FreeMicrosoft.exe | WinRAR.exe | ||||||||||||
User: admin Company: FreeMicrosoft Inc. Integrity Level: HIGH Description: Free Microsoft Products Activation Exit code: 0 Version: 6.6.6.6 Modules
| |||||||||||||||
Total events
18 272
Read events
18 048
Write events
224
Delete events
0
Modification events
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30972273 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30972273 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
15
Text files
58
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\github-fee1576e5bd2[1].css | text | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\environment-318014894642[1].js | text | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\vendors-node_modules_delegated-events_dist_index_js-node_modules_stacktrace-parser_dist_stack-74aed8-6575784e93e6[1].js | text | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\global-10fbf043e525[1].css | text | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\code-3d7b701fc6eb[1].css | text | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | der | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | binary | |
MD5:— | SHA256:— | |||
| 3744 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3744 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAUYmlTr6MfpA%2BCrDZJVRd4%3D | US | der | 313 b | whitelisted |
3744 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
1332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3744 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3744 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?99f7046d211feafd | US | compressed | 4.70 Kb | whitelisted |
3744 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53acdcc8e58d37ad | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3744 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3744 | iexplore.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
1332 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1332 | iexplore.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
1332 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3744 | iexplore.exe | 185.199.111.133:443 | avatars.githubusercontent.com | GitHub, Inc. | NL | suspicious |
3744 | iexplore.exe | 185.199.109.133:443 | avatars.githubusercontent.com | GitHub, Inc. | NL | malicious |
1332 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3744 | iexplore.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | Microsoft Corporation | US | whitelisted |
3744 | iexplore.exe | 140.82.121.4:443 | github.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
raw.githubusercontent.com |
| shared |