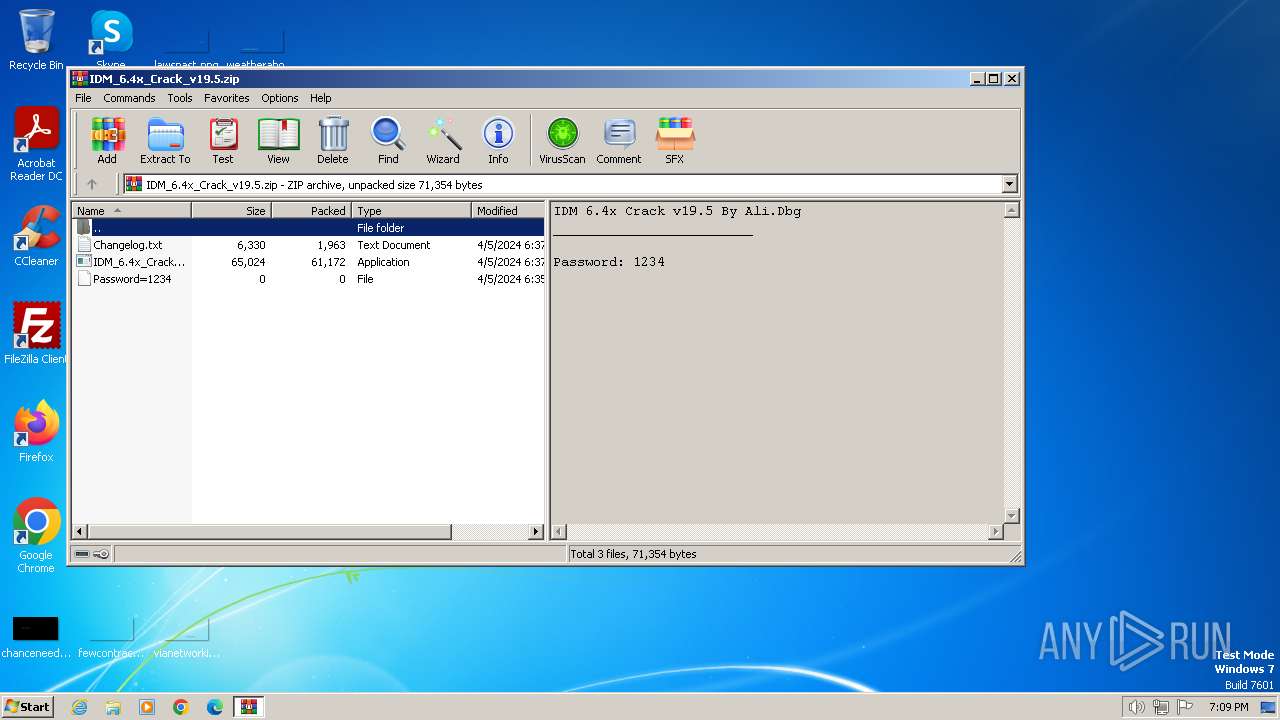
| File name: | IDM_6.4x_Crack_v19.5.zip |
| Full analysis: | https://app.any.run/tasks/3168e5e6-3137-40a0-9a55-e0ec73ca4ef5 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2024, 18:09:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
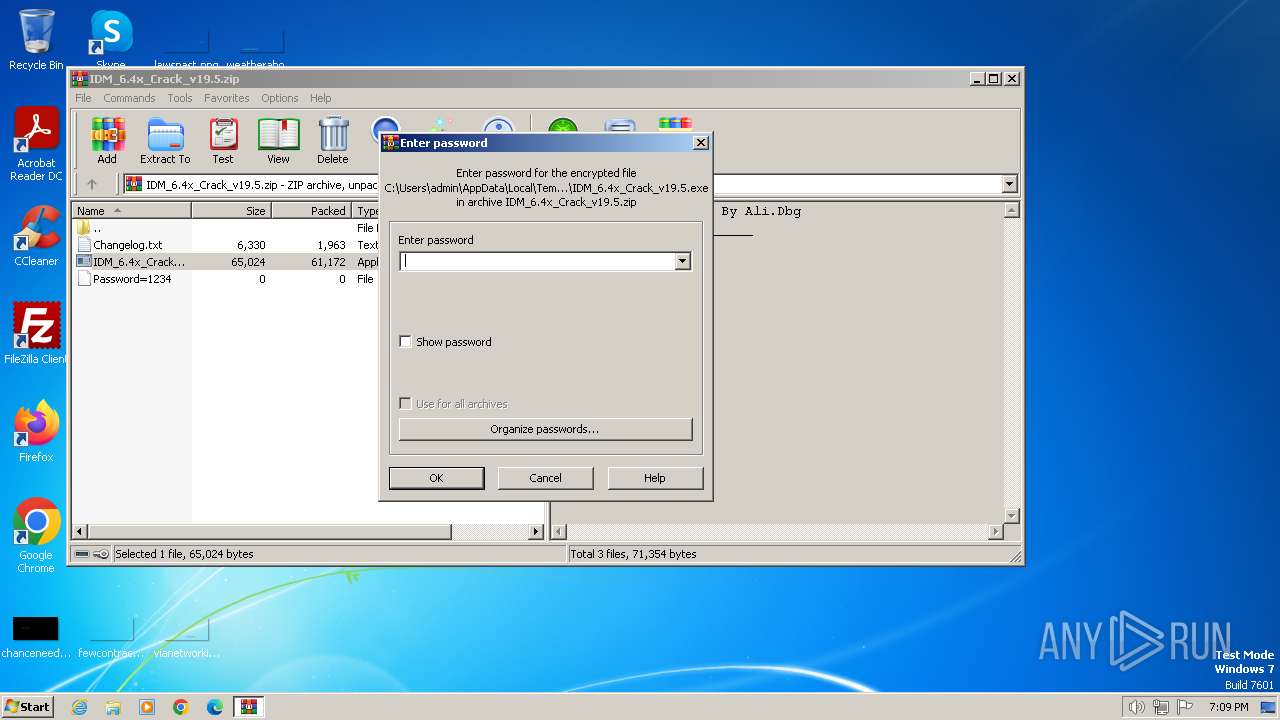
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | 3F2293323E03ABB2C628F952E71C36FB |
| SHA1: | 162B329CF46177303D68AECF74B2EB5717BF4B49 |
| SHA256: | 541ECED93017E619D5F1B7B61E24D02951E810BFAAF1D39F9873B9FAD508B6A0 |
| SSDEEP: | 1536:wN3pdvlPt4x3VB/y/jOiEnuWIZ/1CnWnCpaNGwLcvclib:wNZJFtETyrOxuWa/1CnzpaNGwLckkb |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3400)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3400)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 3400)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3400)
Unusual connection from system programs
- wscript.exe (PID: 3400)
Deletes a file (SCRIPT)
- wscript.exe (PID: 3400)
SUSPICIOUS
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3400)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3400)
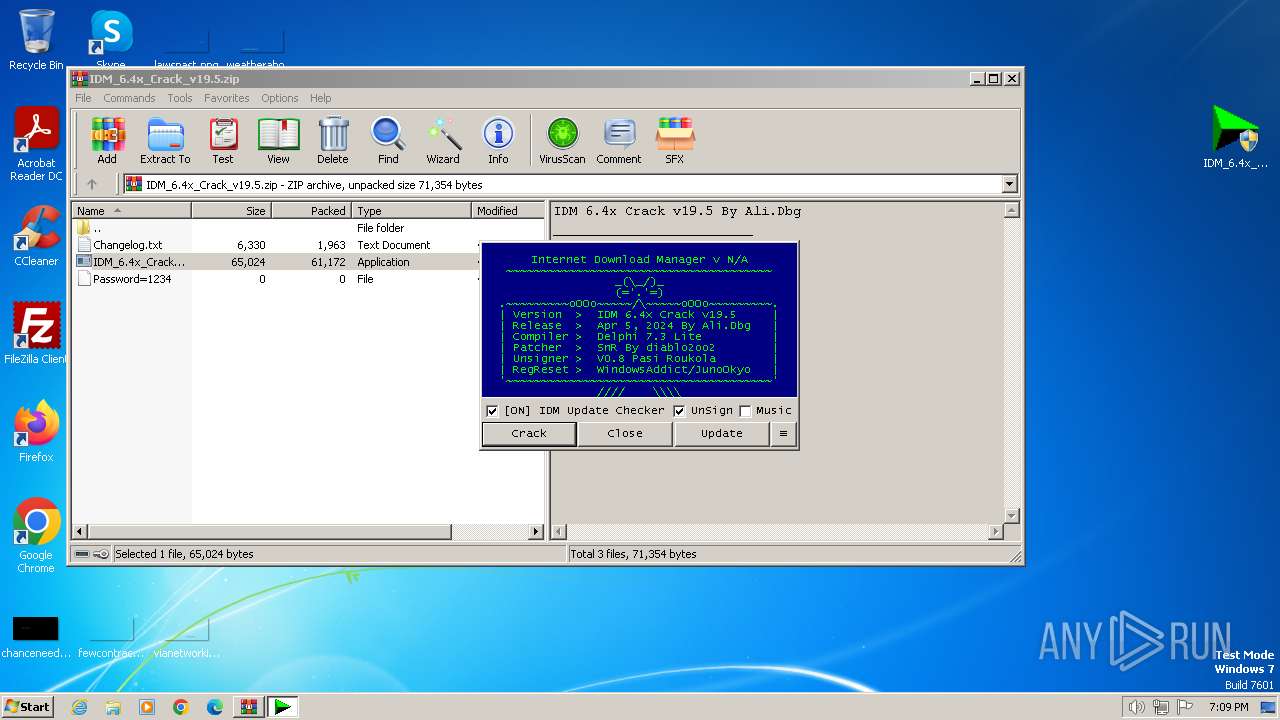
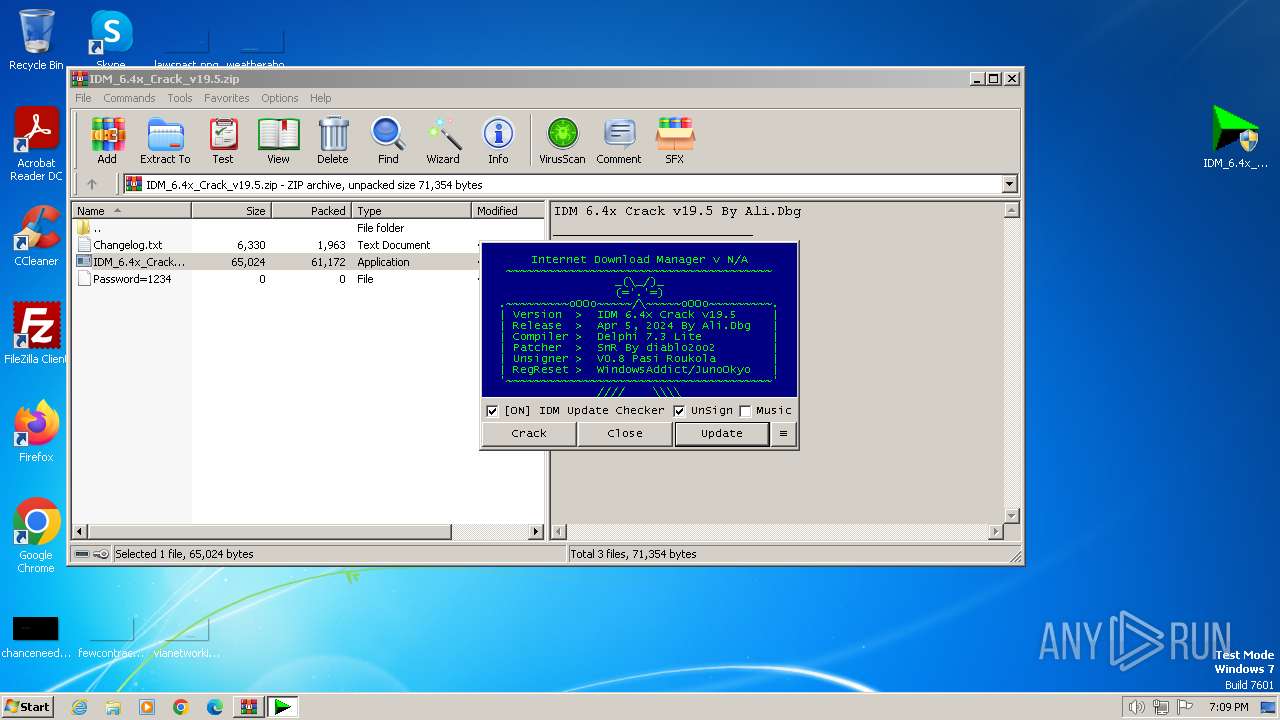
The process executes VB scripts
- IDM_6.4x_Crack_v19.5.exe (PID: 1860)
INFO
Create files in a temporary directory
- IDM_6.4x_Crack_v19.5.exe (PID: 1860)
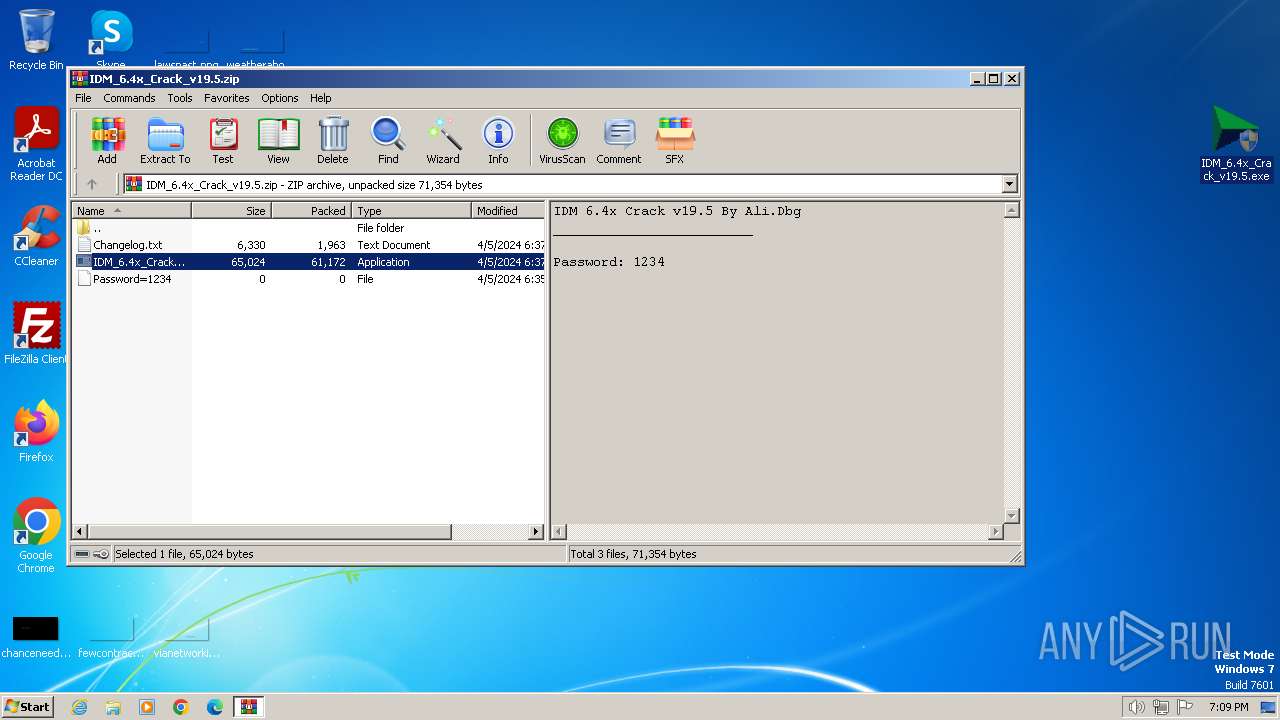
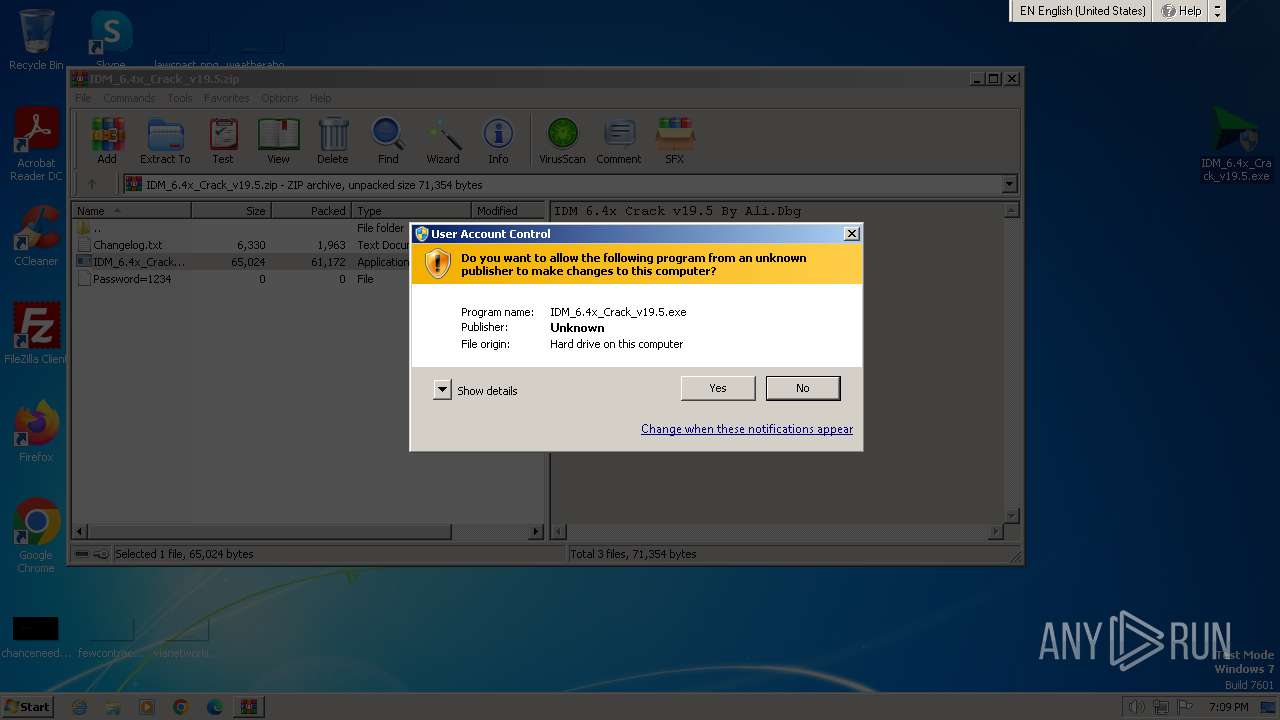
Manual execution by a user
- IDM_6.4x_Crack_v19.5.exe (PID: 2420)
- IDM_6.4x_Crack_v19.5.exe (PID: 1860)
Checks supported languages
- IDM_6.4x_Crack_v19.5.exe (PID: 1860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:04:05 21:07:14 |
| ZipCRC: | 0x72566dae |
| ZipCompressedSize: | 61172 |
| ZipUncompressedSize: | 65024 |
| ZipFileName: | IDM_6.4x_Crack_v19.5.exe |
Total processes
44
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1860 | "C:\Users\admin\Desktop\IDM_6.4x_Crack_v19.5.exe" | C:\Users\admin\Desktop\IDM_6.4x_Crack_v19.5.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\Desktop\IDM_6.4x_Crack_v19.5.exe" | C:\Users\admin\Desktop\IDM_6.4x_Crack_v19.5.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3400 | wscript.exe "C:\Users\admin\AppData\Local\Temp\\UPDT.vbs" /browser:"C:\Program Files\Google\Chrome\Application\chrome.exe" /crkver:"19.5" | C:\Windows\System32\wscript.exe | IDM_6.4x_Crack_v19.5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3500 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\IDM_6.4x_Crack_v19.5.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
5 998
Read events
5 953
Write events
42
Delete events
3
Modification events
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\IDM_6.4x_Crack_v19.5.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3500.4229\IDM_6.4x_Crack_v19.5.exe | — | |
MD5:— | SHA256:— | |||
| 1860 | IDM_6.4x_Crack_v19.5.exe | C:\Users\admin\AppData\Local\Temp\UPDT.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3400 | wscript.exe | 188.114.96.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idm.0dy.ir |
| unknown |