| File name: | ClashRoyaleBot.exe |
| Full analysis: | https://app.any.run/tasks/87b6a370-a938-4d59-9745-169e43d417a6 |
| Verdict: | No threats detected |
| Analysis date: | March 24, 2020, 04:31:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 70921F7216CD688021623B388E405D9A |
| SHA1: | 77C558F084A62CABD11AE31313EE5D7FFD33AEF8 |
| SHA256: | 541E8CAC5B90003D553664D7D79A6A9DC1E3D5AA7C840B528DE978B83D54CD71 |
| SSDEEP: | 98304:NHCq9Vi9lpZ8aZ4VCgUa6qoG8Sjgl1ahFC7cFtUMOMKI68CJQ+pNIqkL+:klR4V0eoG8SjAaHC7cFtInI6VQ+HtkK |
MALICIOUS
No malicious indicators.SUSPICIOUS
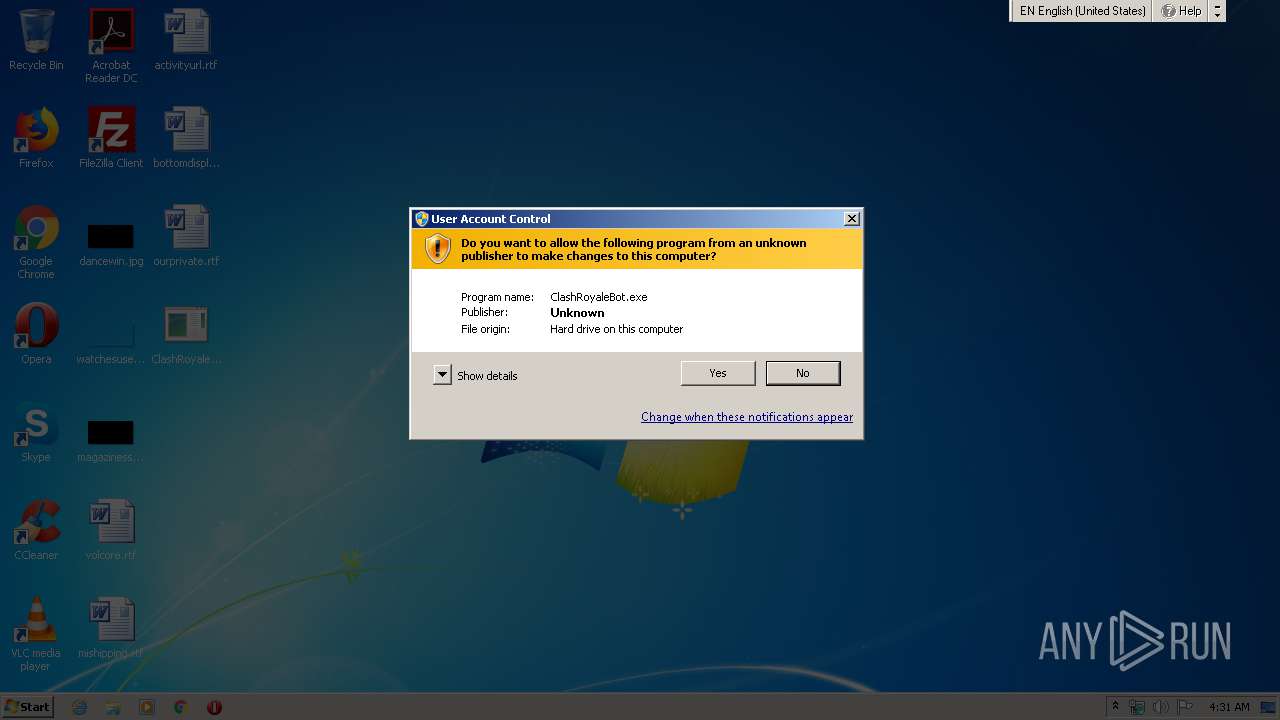
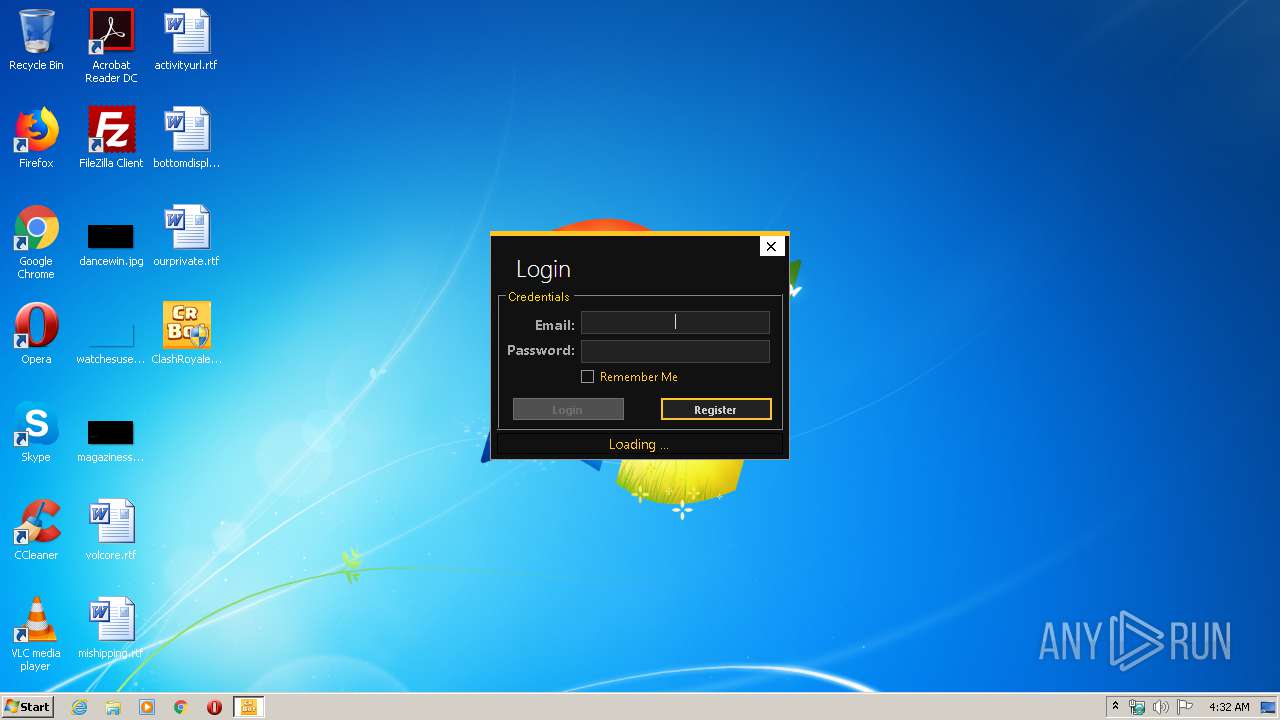
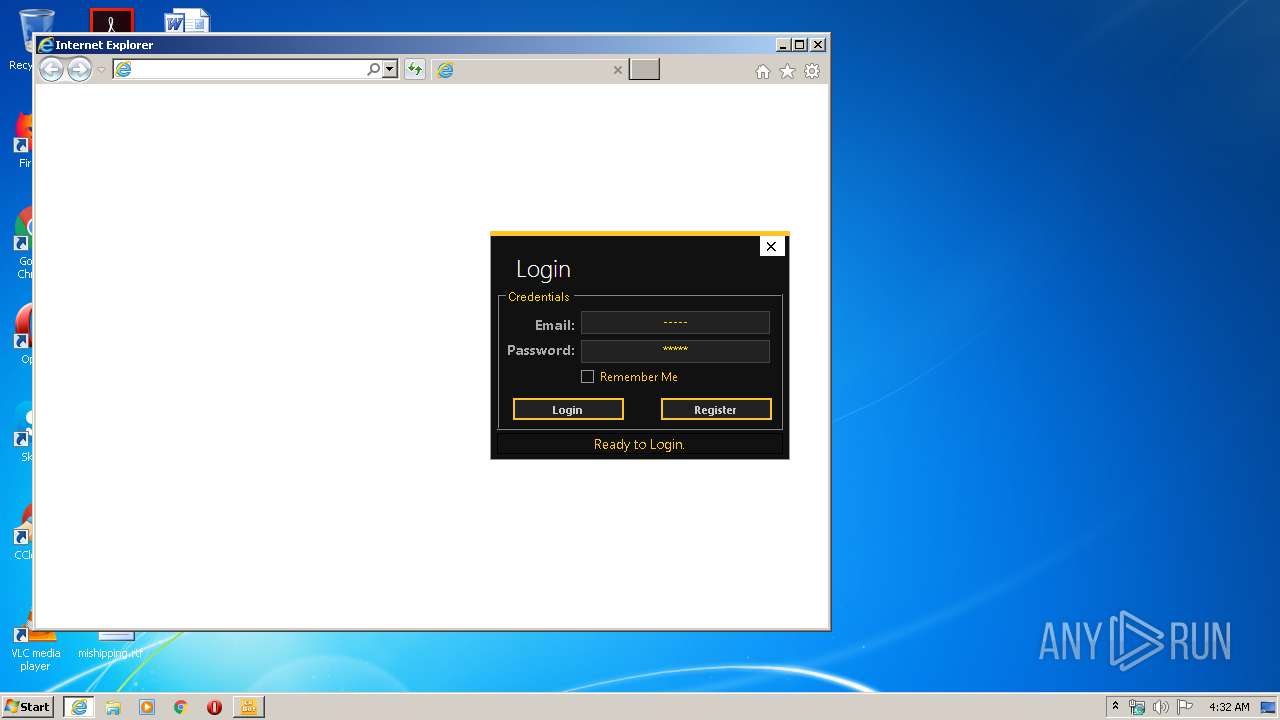
Starts Internet Explorer
- ClashRoyaleBot.exe (PID: 3556)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 4068)
Reads Internet Cache Settings
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 4068)
Changes internet zones settings
- iexplore.exe (PID: 2824)
Application launched itself
- iexplore.exe (PID: 2824)
Reads internet explorer settings
- iexplore.exe (PID: 4068)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4068)
Changes settings of System certificates
- iexplore.exe (PID: 4068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:12 02:00:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 397824 |
| InitializedDataSize: | 5500928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5a800a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.5.0 |
| ProductVersionNumber: | 1.6.5.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | RedSoft |
| FileDescription: | Clash Royale Bot |
| FileVersion: | 1.6.5.0 |
| InternalName: | ClashRoyaleBot.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | ClashRoyaleBot.exe |
| ProductName: | Clash Royale Bot |
| ProductVersion: | 1.6.5.0 |
| AssemblyVersion: | 1.6.5.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Dec-2019 01:00:57 |
| Comments: | - |
| CompanyName: | RedSoft |
| FileDescription: | Clash Royale Bot |
| FileVersion: | 1.6.5.0 |
| InternalName: | ClashRoyaleBot.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | ClashRoyaleBot.exe |
| ProductName: | Clash Royale Bot |
| ProductVersion: | 1.6.5.0 |
| Assembly Version: | 1.6.5.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Dec-2019 01:00:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
Vxj,7u\x03\x1e\xe4ES | 0x00002000 | 0x005345E4 | 0x00534600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99997 |
.text | 0x00538000 | 0x00060F98 | 0x00061000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36324 |
.rsrc | 0x0059A000 | 0x0000A640 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98069 |
.reloc | 0x005A6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x005A8000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.142636 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00397 | 3167 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.36467 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.20415 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.9428 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.92507 | 20480 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.70931 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
46
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2720 | "C:\Users\admin\Desktop\ClashRoyaleBot.exe" | C:\Users\admin\Desktop\ClashRoyaleBot.exe | — | explorer.exe | |||||||||||
User: admin Company: RedSoft Integrity Level: MEDIUM Description: Clash Royale Bot Exit code: 3221226540 Version: 1.6.5.0 Modules
| |||||||||||||||
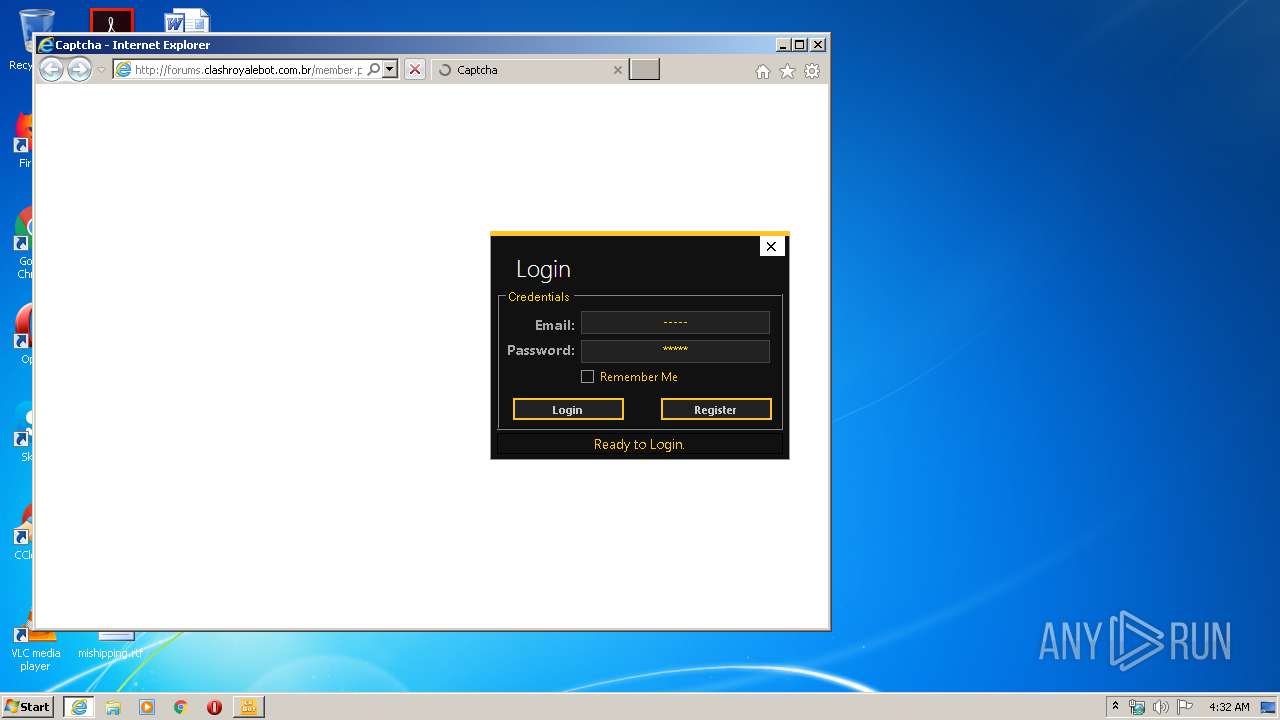
| 2824 | "C:\Program Files\Internet Explorer\iexplore.exe" http://forums.clashroyalebot.com.br/member.php?action=register | C:\Program Files\Internet Explorer\iexplore.exe | ClashRoyaleBot.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3556 | "C:\Users\admin\Desktop\ClashRoyaleBot.exe" | C:\Users\admin\Desktop\ClashRoyaleBot.exe | explorer.exe | ||||||||||||
User: admin Company: RedSoft Integrity Level: HIGH Description: Clash Royale Bot Exit code: 0 Version: 1.6.5.0 Modules
| |||||||||||||||
| 4068 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2824 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
7 676
Read events
2 787
Write events
4 888
Delete events
1
Modification events
| (PID) Process: | (3556) ClashRoyaleBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3556) ClashRoyaleBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1178032035 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30802325 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
38
Text files
6
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3DE7.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar3DE8.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\member[1].htm | html | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver5AF6.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB886.tmp | — | |
MD5:— | SHA256:— | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB896.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_B4E256AEE3EBA21D6B1078B3E1B79532 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
27
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4068 | iexplore.exe | GET | 200 | 154.16.125.51:80 | http://forums.clashroyalebot.com.br/member.php?action=register | US | html | 20.3 Kb | unknown |
4068 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
4068 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
4068 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
4068 | iexplore.exe | GET | 200 | 154.16.125.51:80 | http://forums.clashroyalebot.com.br/a9bc224bd710f56d27affffddc764239b58c3faa0/shield.png | US | image | 3.93 Kb | unknown |
4068 | iexplore.exe | GET | 200 | 172.217.168.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
4068 | iexplore.exe | GET | 200 | 172.217.168.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDy4NKedukSQwgAAAAAMgpY | US | der | 472 b | whitelisted |
4068 | iexplore.exe | GET | 200 | 172.217.168.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEC4G%2Bv2mHN8jAgAAAABcZ3g%3D | US | der | 471 b | whitelisted |
4068 | iexplore.exe | GET | 200 | 172.217.168.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
4068 | iexplore.exe | GET | 200 | 172.217.168.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4068 | iexplore.exe | 154.16.125.51:80 | forums.clashroyalebot.com.br | Digital Energy Technologies Chile SpA | US | unknown |
4068 | iexplore.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
4068 | iexplore.exe | 172.217.17.132:443 | www.google.com | Google Inc. | US | whitelisted |
2824 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4068 | iexplore.exe | 172.217.168.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
4068 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
4068 | iexplore.exe | 216.58.211.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
4068 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2824 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
forums.clashroyalebot.com.br |
| unknown |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |