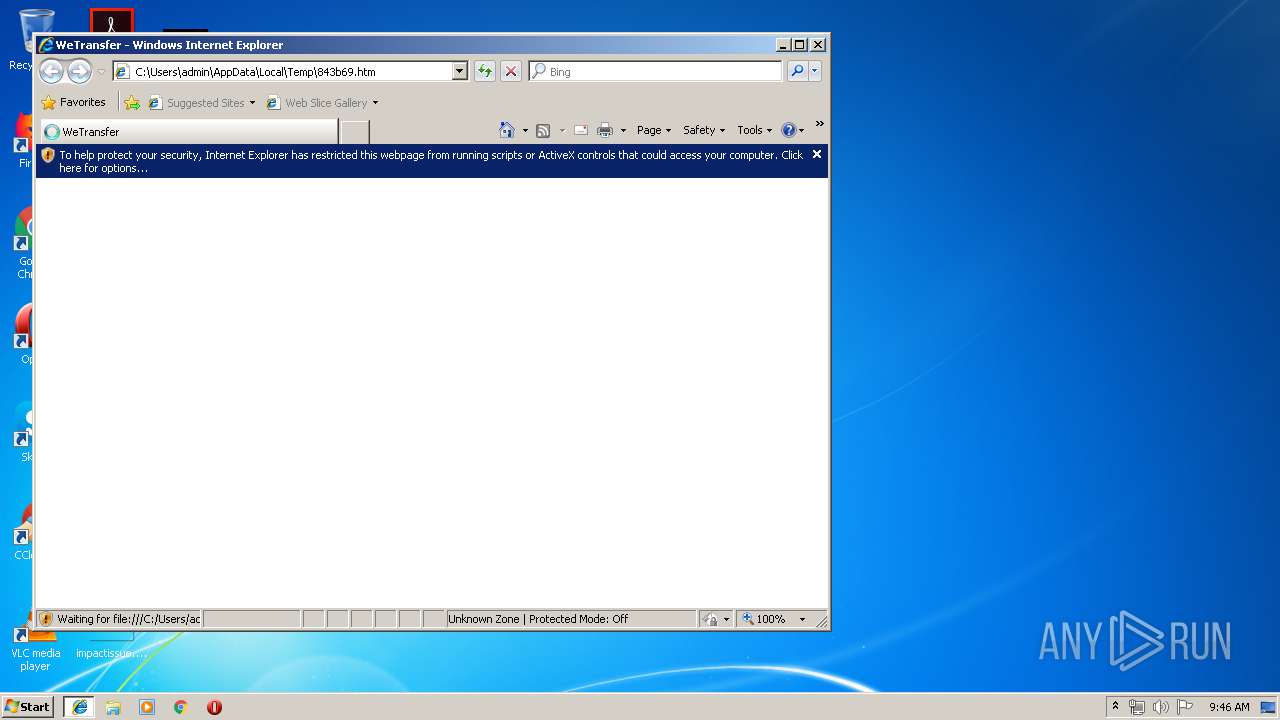
| download: | 843b69 |
| Full analysis: | https://app.any.run/tasks/cfe59e61-7098-43a3-8496-14c884ddc02b |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 08:45:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
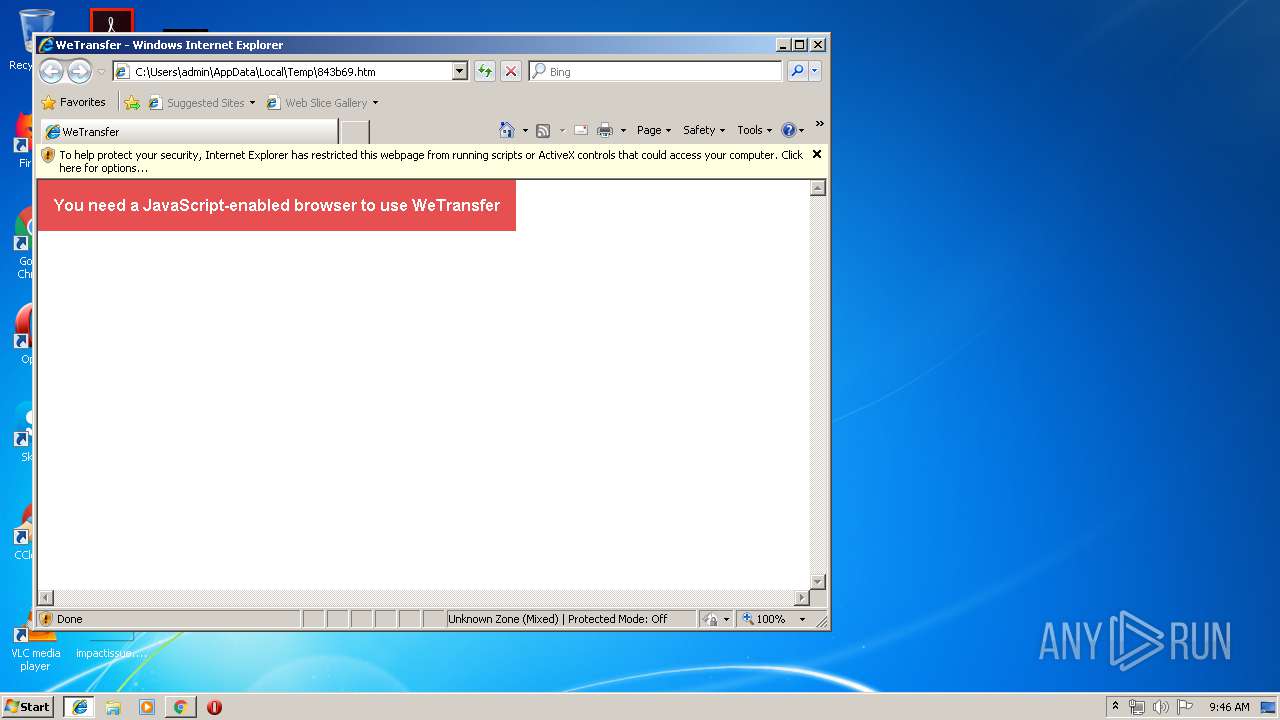
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 4091182CC69A407B6C325566BE651D84 |
| SHA1: | D6FA2A4BFD3389AED19185E958AA14B15801F71A |
| SHA256: | 541AC42A4299E9A54F9E4FD1084C31988EC9E0C52E438D50C561A3B9356B5F95 |
| SSDEEP: | 1536:UEEwa2W7flXB4eL2fCzbr2UdiUz70oD9H:UEEwax7daQ2crx9D9H |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3820)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 2856)
Changes internet zones settings
- iexplore.exe (PID: 2948)
Application launched itself
- iexplore.exe (PID: 2948)
- chrome.exe (PID: 3820)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2856)
Changes settings of System certificates
- iexplore.exe (PID: 2856)
Creates files in the user directory
- iexplore.exe (PID: 2856)
Reads Internet Cache Settings
- iexplore.exe (PID: 2856)
- iexplore.exe (PID: 2948)
Manual execution by user
- chrome.exe (PID: 3820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| viewport: | width=device-width, minimum-scale=1, initial-scale=1, user-scalable=no |
| pinterest: | nopin |
| referrer: | origin |
| Description: | WeTransfer is the simplest way to send your files around the world. Share large files up to 2GB for free. |
| Author: | WeTransfer |
| applicationName: | WeTransfer |
| csrfParam: | authenticity_token |
| csrfToken: | C1w8FP9dOSibxxIMDMrr1kOILzT0887uYcOlgxEToWLxIUun20H59I9PRoV72eMrO4U9ZZUbC+Pdc1WhQX/pjw== |
| Title: | WeTransfer |
Total processes
56
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1969834428318368833 --mojo-platform-channel-handle=4220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16795040407739571762 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16795040407739571762 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1022323420978891209 --mojo-platform-channel-handle=4880 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8734604966389185833 --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --service-pipe-token=2743314212089463606 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2743314212089463606 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15100750817931837029 --mojo-platform-channel-handle=4280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16319764763884558193 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16319764763884558193 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3696 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10320561461762442048 --mojo-platform-channel-handle=4604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,6417118361384947746,2395954465886875303,131072 --enable-features=PasswordImport --service-pipe-token=16813250761492637004 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16813250761492637004 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2948 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
548
Read events
402
Write events
136
Delete events
10
Modification events
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {B0EA39BF-7ADB-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30705000100140008002E0001002701 | |||
Executable files
0
Suspicious files
50
Text files
176
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab12A5.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar12A6.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab12C7.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar12C8.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab1346.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar1347.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94308059B57B3142E455B38A6EB92015 | compressed | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Feeds Cache\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
33
DNS requests
22
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | chrome.exe | GET | 200 | 173.194.5.220:80 | http://r6---sn-aigl6n7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.249.73.20&mm=28&mn=sn-aigl6n7d&ms=nvh&mt=1558341918&mv=m&pl=25&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2856 | iexplore.exe | OPTIONS | 400 | 172.217.21.200:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2856 | iexplore.exe | GET | 200 | 13.32.222.188:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2856 | iexplore.exe | OPTIONS | 400 | 172.217.21.200:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3820 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 503 b | whitelisted |
2856 | iexplore.exe | OPTIONS | 400 | 172.217.21.200:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2856 | iexplore.exe | OPTIONS | 400 | 172.217.21.200:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2856 | iexplore.exe | OPTIONS | 400 | 172.217.21.200:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2856 | iexplore.exe | OPTIONS | 400 | 172.217.21.200:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2856 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2856 | iexplore.exe | 13.32.223.128:443 | prod-cdn.wetransfer.net | Amazon.com, Inc. | US | unknown |
— | — | 13.32.222.188:80 | x.ss2.us | Amazon.com, Inc. | US | suspicious |
— | — | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2856 | iexplore.exe | 172.217.21.200:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3820 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3820 | chrome.exe | 172.217.22.35:443 | www.google.de | Google Inc. | US | whitelisted |
3820 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
3820 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
prod-cdn.wetransfer.net |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
10 ETPRO signatures available at the full report