| File name: | V2Injector.exe |
| Full analysis: | https://app.any.run/tasks/82191be9-3b2e-44bd-9ee3-85401bdd02c3 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2024, 10:49:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 13 sections |
| MD5: | D855E2CBDB9BA4EEBD6565BE67A02CFE |
| SHA1: | 3F471A7CE59D63F0322F2EEA8B4F36E149B49931 |
| SHA256: | 5415D24E56C7E6BB60BC14F205312A35B2FD2BBB89A0568D7FCFAB3F66DF5B89 |
| SSDEEP: | 98304:fsJuXM4GA4QqxrWljZPGJaiSsObepinQMc2qX12BJxOjsXG6sQR7YrsJIU5Ld8Ll:YGd5jW |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the BIOS version
- V2Injector.exe (PID: 5592)
Reads security settings of Internet Explorer
- V2Injector.exe (PID: 5592)
Checks Windows Trust Settings
- V2Injector.exe (PID: 5592)
Executable content was dropped or overwritten
- V2Injector.exe (PID: 5592)
- YhDSh.exe (PID: 5588)
Reads the date of Windows installation
- V2Injector.exe (PID: 5592)
Creates or modifies Windows services
- YhDSh.exe (PID: 5588)
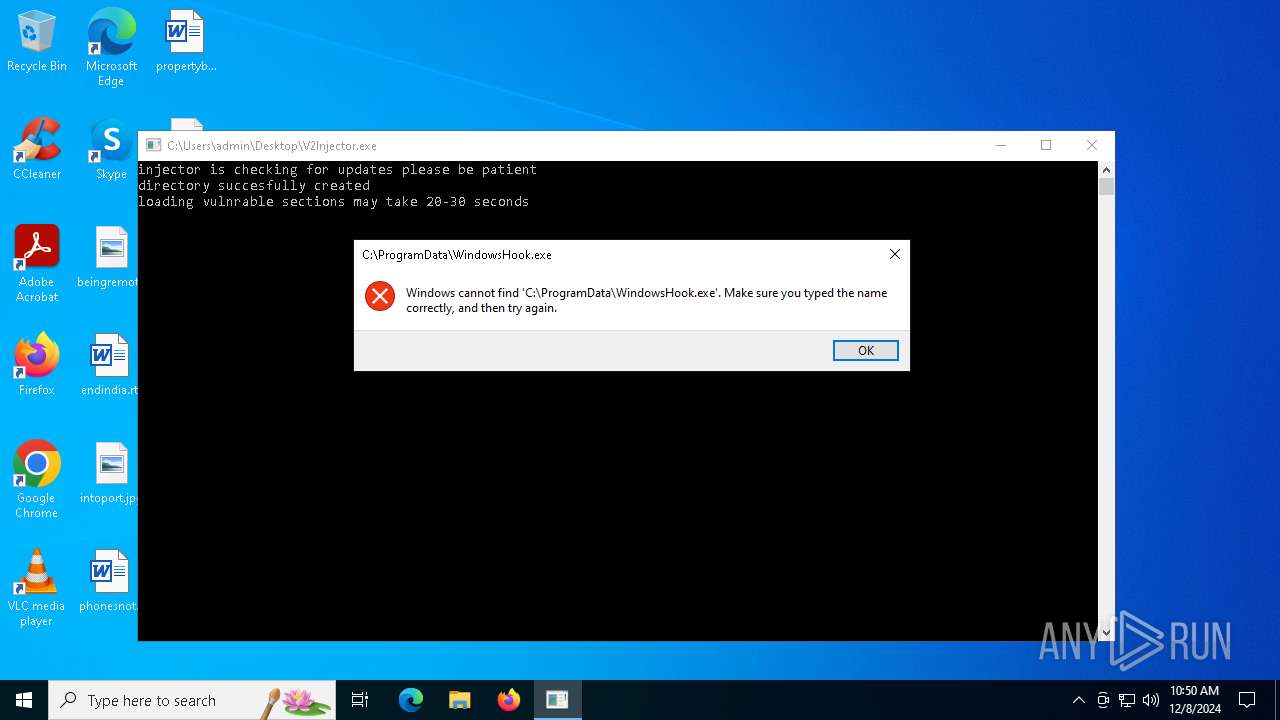
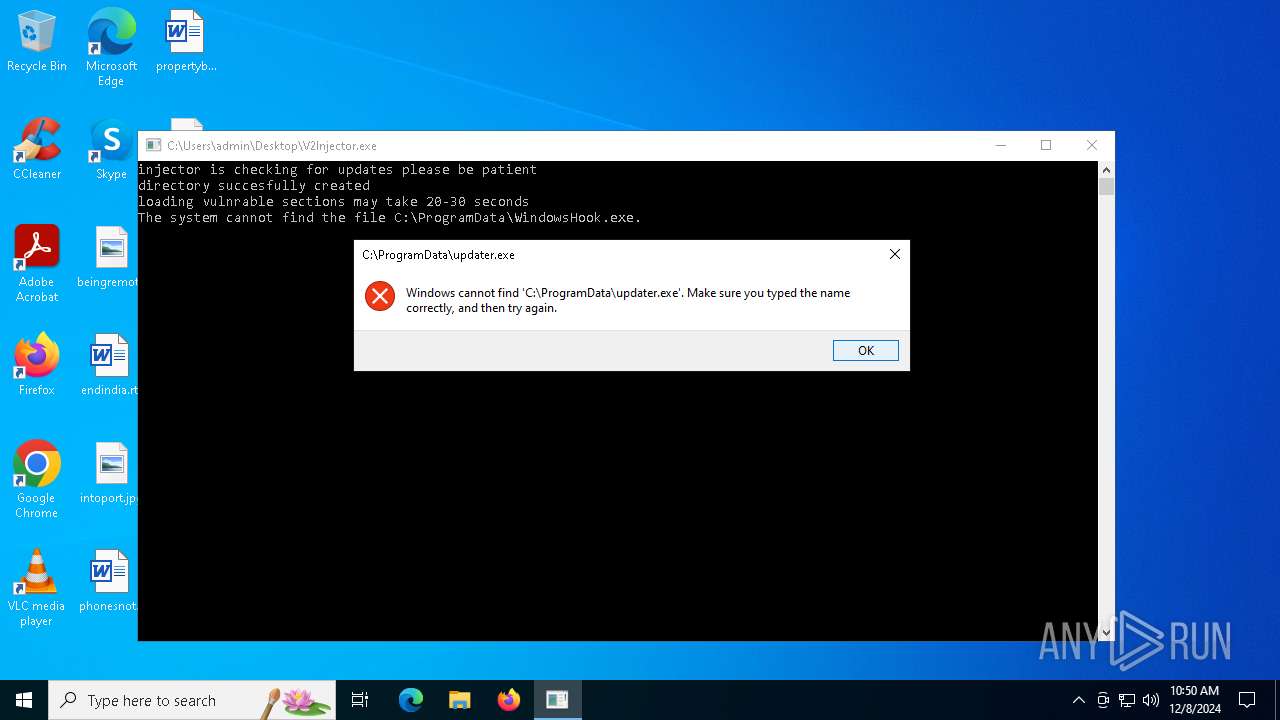
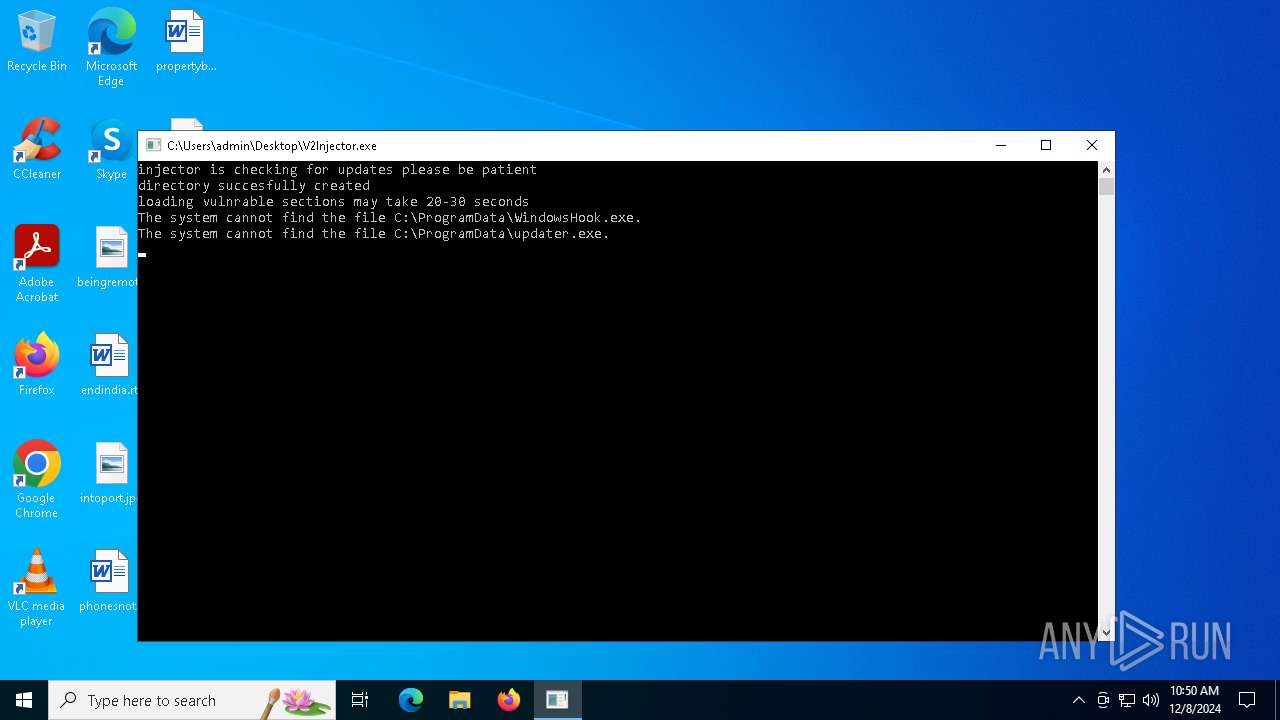
Starts CMD.EXE for commands execution
- V2Injector.exe (PID: 5592)
INFO
Process checks whether UAC notifications are on
- V2Injector.exe (PID: 5592)
Checks supported languages
- V2Injector.exe (PID: 5592)
- YhDSh.exe (PID: 5588)
Reads the machine GUID from the registry
- V2Injector.exe (PID: 5592)
Reads the computer name
- V2Injector.exe (PID: 5592)
Checks proxy server information
- V2Injector.exe (PID: 5592)
Reads the software policy settings
- V2Injector.exe (PID: 5592)
Themida protector has been detected
- V2Injector.exe (PID: 5592)
Process checks computer location settings
- V2Injector.exe (PID: 5592)
The process uses the downloaded file
- V2Injector.exe (PID: 5592)
Create files in a temporary directory
- YhDSh.exe (PID: 5588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2022:03:09 17:31:26+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.31 |
| CodeSize: | 213504 |
| InitializedDataSize: | 211456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5e8058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
126
Monitored processes
13
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
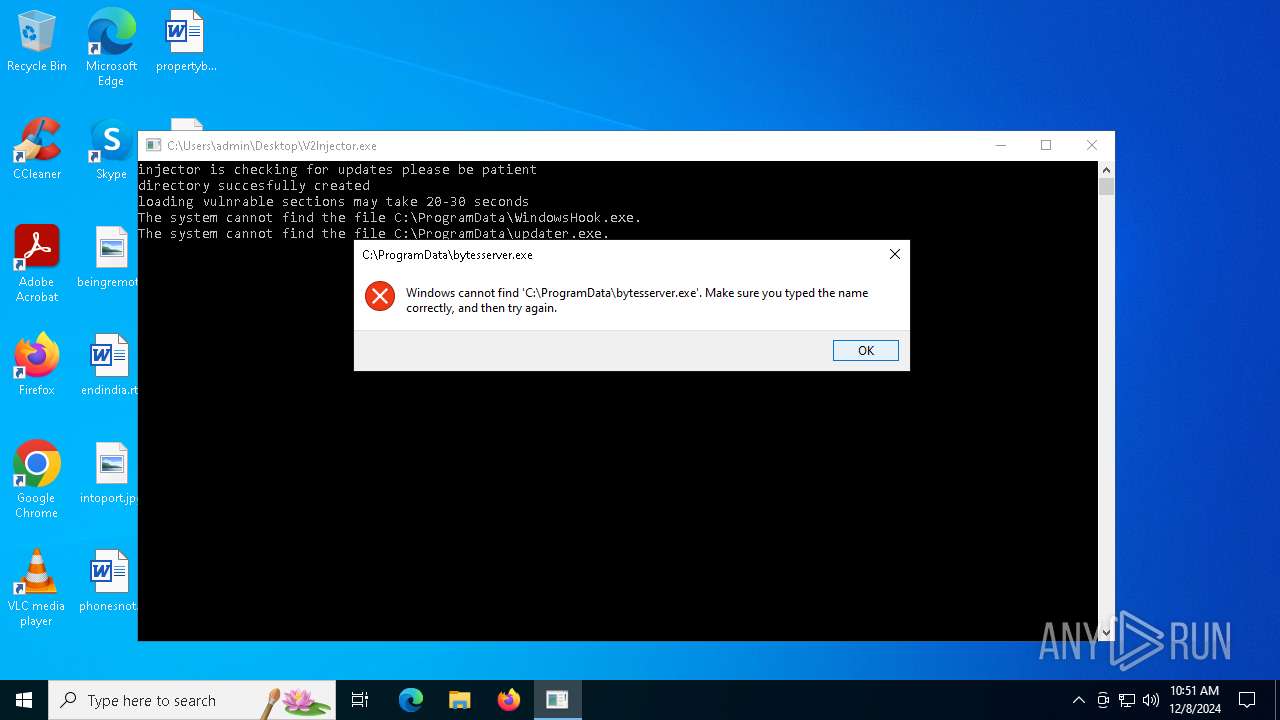
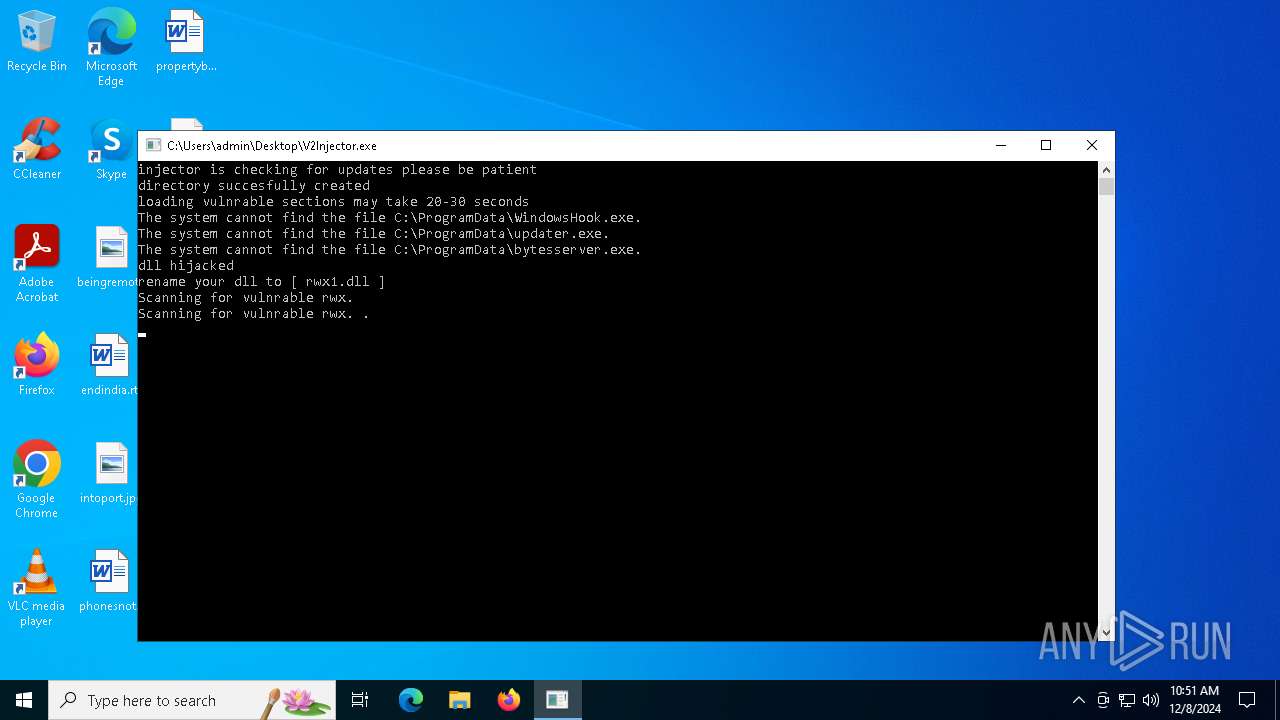
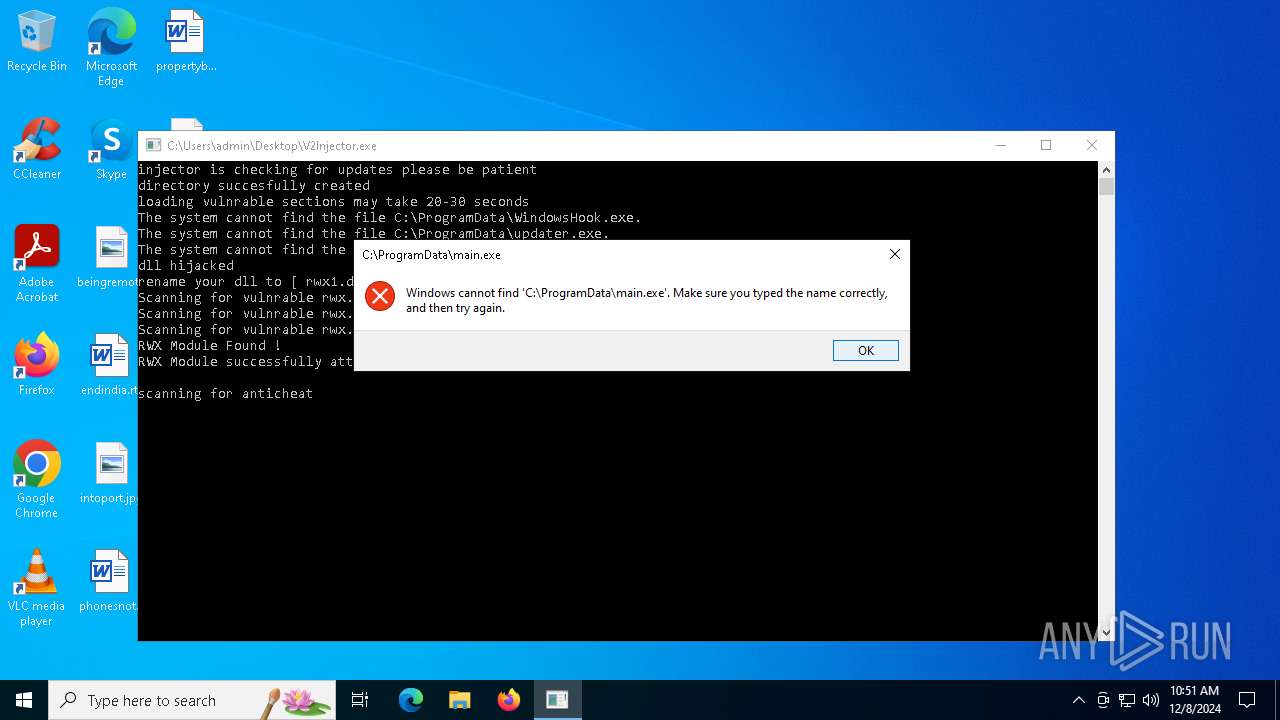
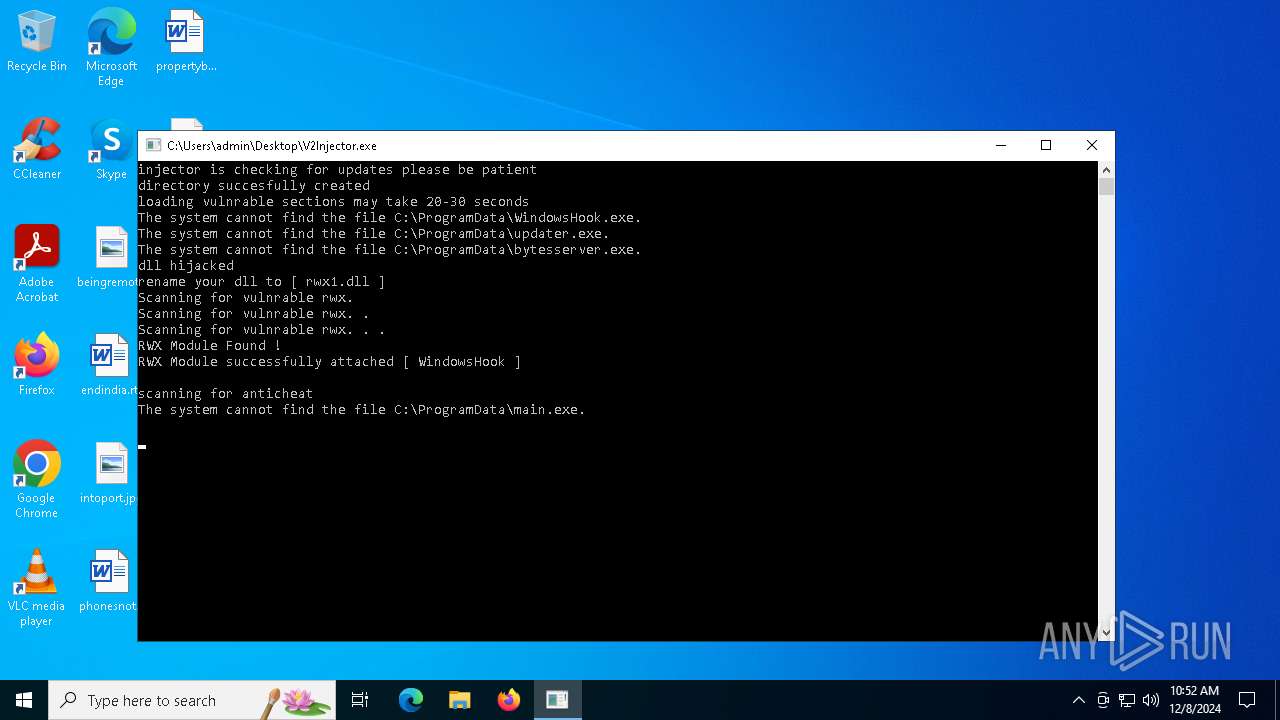
| 644 | C:\WINDOWS\system32\cmd.exe /c start C:\ProgramData\main.exe | C:\Windows\System32\cmd.exe | — | V2Injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1468 | C:\WINDOWS\system32\cmd.exe /c cd C:\ProgramData | C:\Windows\System32\cmd.exe | — | V2Injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | C:\WINDOWS\system32\cmd.exe /c start C:\ProgramData\bytesserver.exe | C:\Windows\System32\cmd.exe | — | V2Injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | C:\WINDOWS\system32\cmd.exe /c cd C:\ProgramData | C:\Windows\System32\cmd.exe | — | V2Injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | YhDSh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3928 | C:\WINDOWS\system32\cmd.exe /c cd C:\ProgramData | C:\Windows\System32\cmd.exe | — | V2Injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | V2Injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4132 | "C:\Users\admin\Desktop\V2Injector.exe" | C:\Users\admin\Desktop\V2Injector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5448 | C:\WINDOWS\system32\cmd.exe /c start C:\ProgramData\WindowsHook.exe | C:\Windows\System32\cmd.exe | — | V2Injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 091
Read events
4 085
Write events
5
Delete events
1
Modification events
| (PID) Process: | (5592) V2Injector.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5592) V2Injector.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5592) V2Injector.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5588) YhDSh.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IEYQQQohlcoxqwzwytml |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Users\admin\AppData\Local\Temp\IEYQQQohlcoxqwzwytml | |||
| (PID) Process: | (5588) YhDSh.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IEYQQQohlcoxqwzwytml |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (5588) YhDSh.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IEYQQQohlcoxqwzwytml |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5588 | YhDSh.exe | C:\Users\admin\AppData\Local\Temp\IEYQQQohlcoxqwzwytml | executable | |
MD5:1898CEDA3247213C084F43637EF163B3 | SHA256:4429F32DB1CC70567919D7D47B844A91CF1329A6CD116F582305F3B7B60CD60B | |||
| 5592 | V2Injector.exe | C:\Windows\SoftwareDistribution\Download\YhDSh.exe | executable | |
MD5:3F9AF39F8B7E0D314824CB101054D0DD | SHA256:939E6BCDE687D6ED9242F4C223B2D7255C767C0BFDAE3A3521718766103629BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 522 | 188.114.96.3:443 | https://havok.cc/WindowsHook.exe | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 522 | 188.114.97.3:443 | https://havok.cc/updater.exe | unknown | — | — | unknown |
— | — | GET | 522 | 188.114.96.3:443 | https://havok.cc/bytesserver.exe | unknown | — | — | unknown |
— | — | GET | 522 | 188.114.97.3:443 | https://havok.cc/main.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5592 | V2Injector.exe | 188.114.96.3:443 | havok.cc | CLOUDFLARENET | NL | unknown |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3976 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
havok.cc |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |