| download: | JRE%20-%20Flip%20Installer%20-%203.4.7.112.exe |
| Full analysis: | https://app.any.run/tasks/3626e669-325e-4ee8-9ef4-78443c7fcdb0 |
| Verdict: | Malicious activity |
| Analysis date: | June 07, 2018, 03:59:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 0C2E14DDA06687E7016100B34B92D9EA |
| SHA1: | 993817326406BFE03271D129313DE5132C76358B |
| SHA256: | 5404B843378344D1F054CFD3F069DD477BF2BC73CF04F3B36FA1A0E77D77F0D7 |
| SSDEEP: | 393216:CC+Ngzzyem2z1SRYfImyzx8ehWy4Xx5vmZLwUB2DEDZMcBTYF5MT5+TIHuW:Z+N6nRp7yzueYxRawUtMcoMXJ |
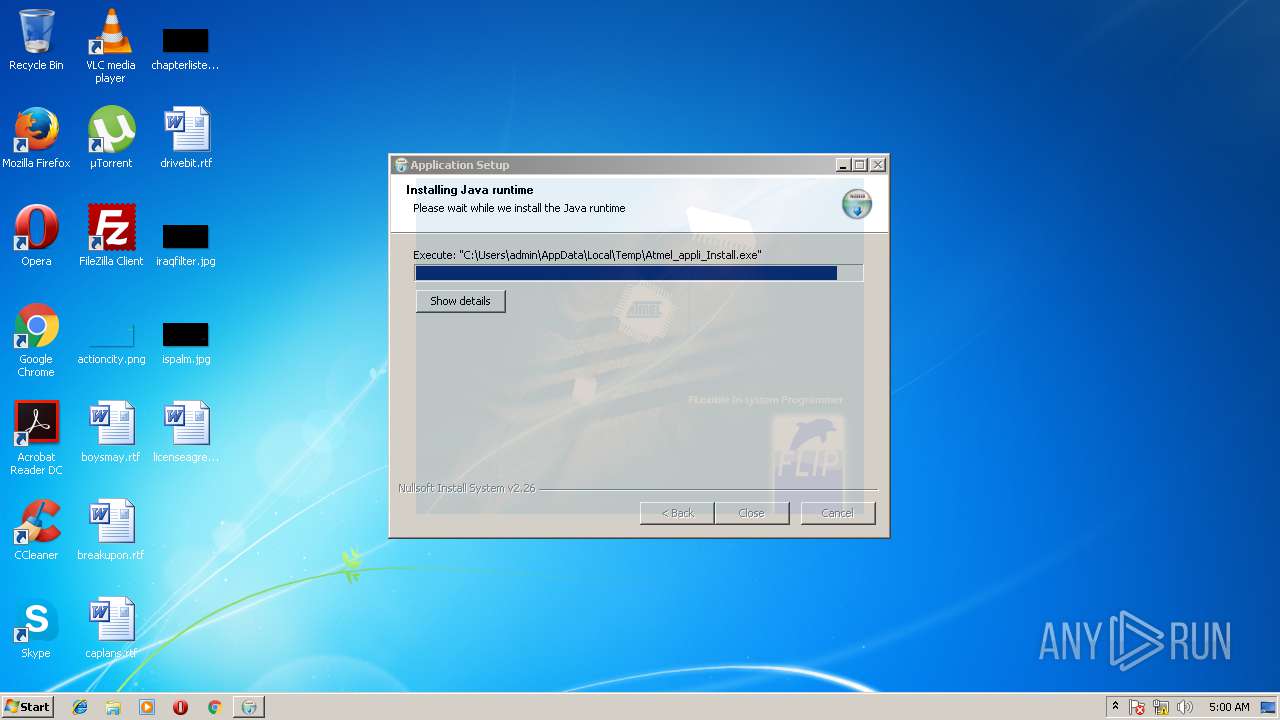
MALICIOUS
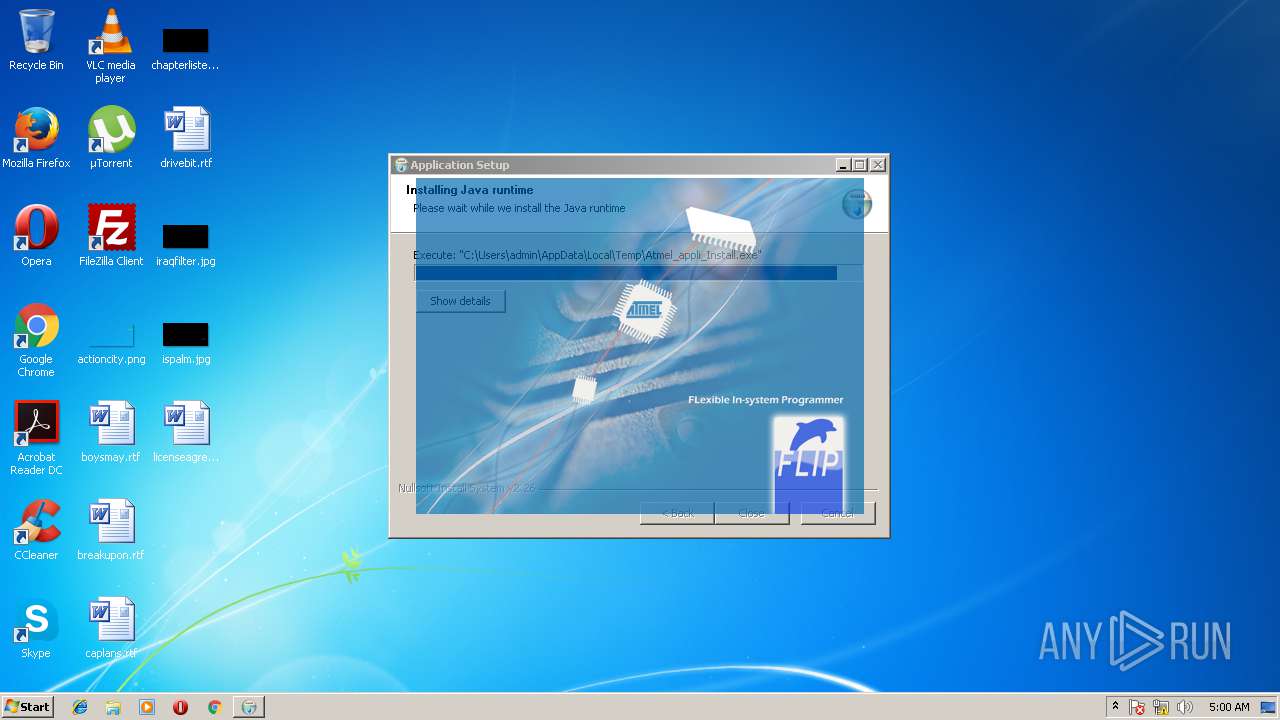
Loads dropped or rewritten executable
- Atmel_appli_Install.exe (PID: 1272)
- javaw.exe (PID: 1736)
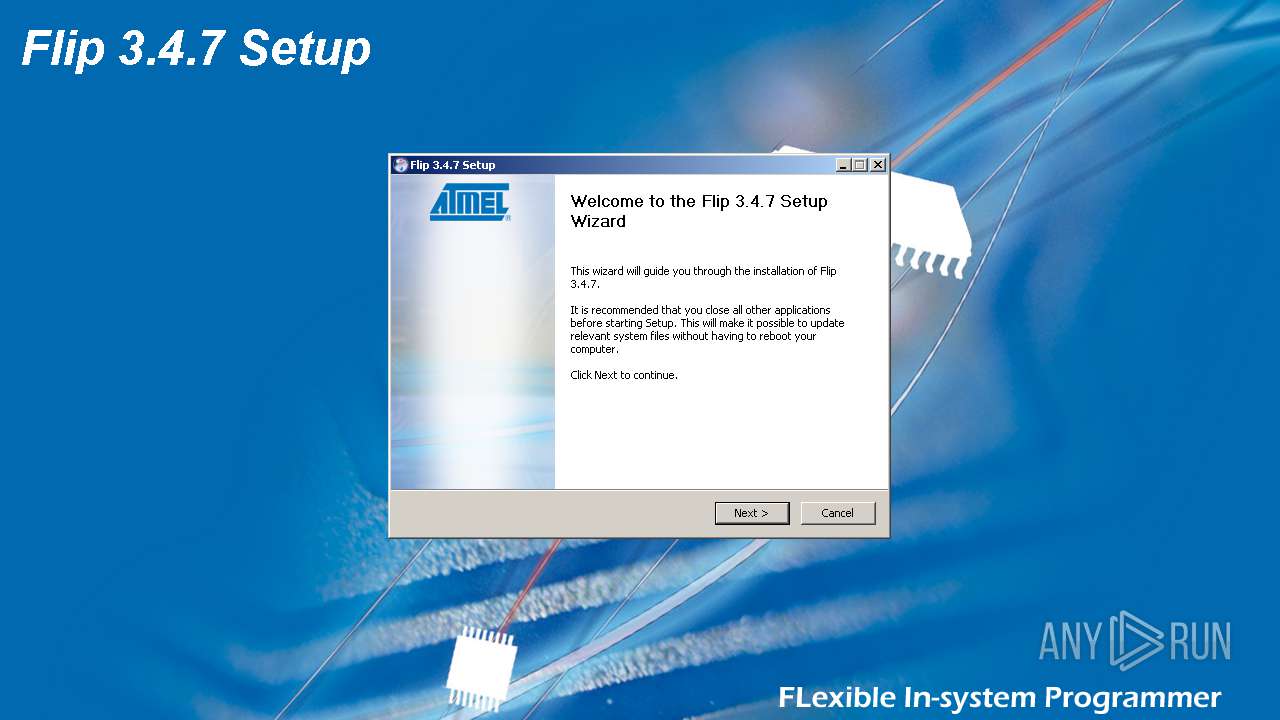
Application was dropped or rewritten from another process
- Atmel_appli_Install.exe (PID: 1272)
- flip.exe (PID: 3112)
SUSPICIOUS
Executable content was dropped or overwritten
- a80467a1-8cf9-435a-bf25-6210c2a6143d.exe (PID: 1692)
- Atmel_appli_Install.exe (PID: 1272)
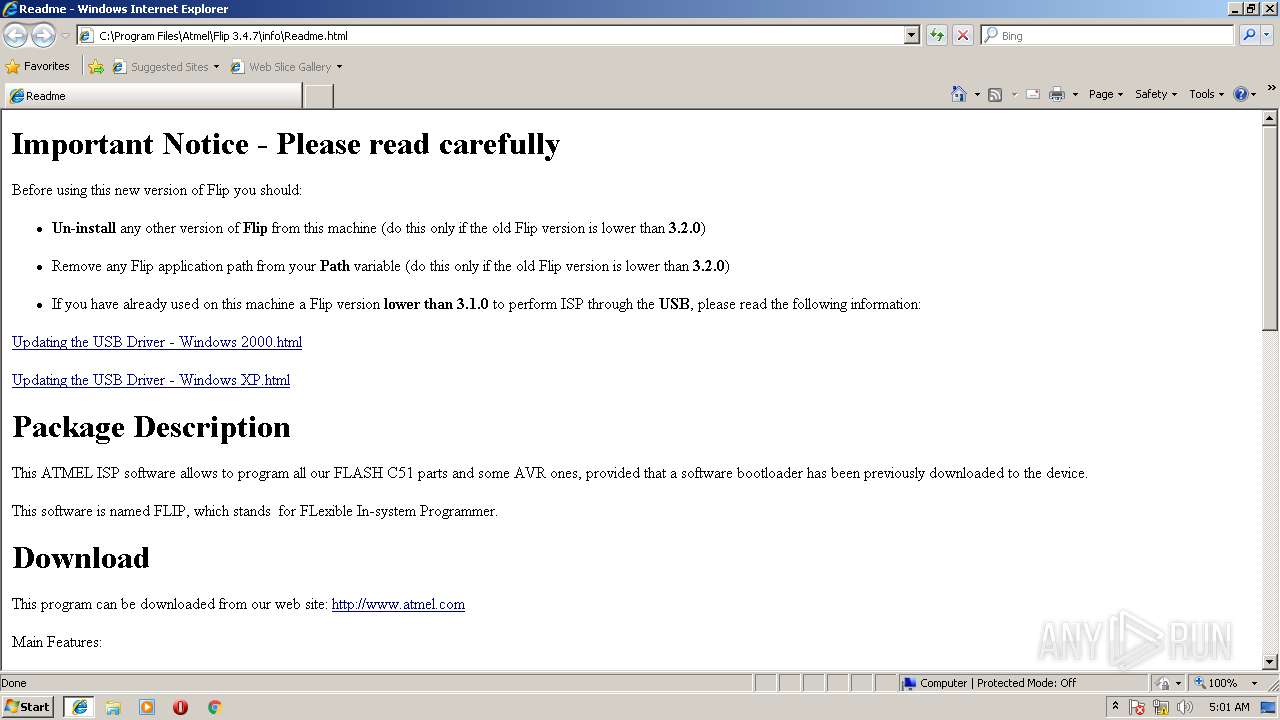
Starts Internet Explorer
- Atmel_appli_Install.exe (PID: 1272)
Creates a software uninstall entry
- Atmel_appli_Install.exe (PID: 1272)
Check for Java to be installed
- iexplore.exe (PID: 3084)
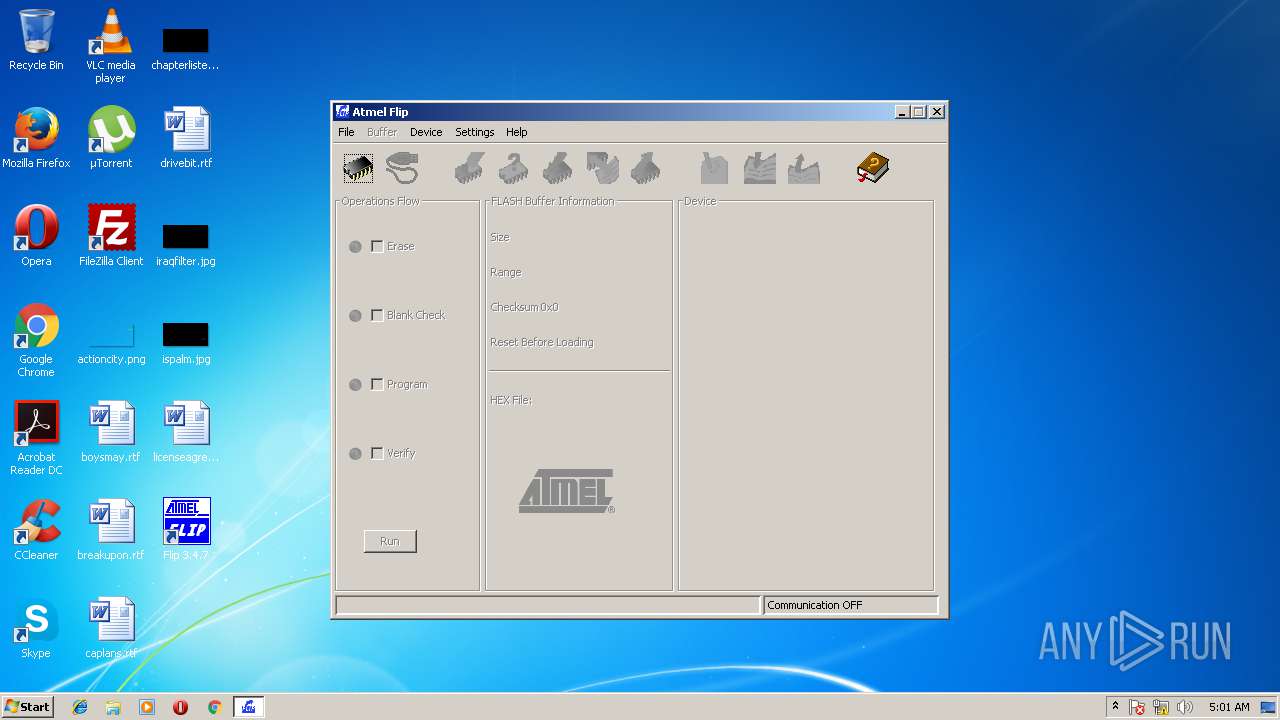
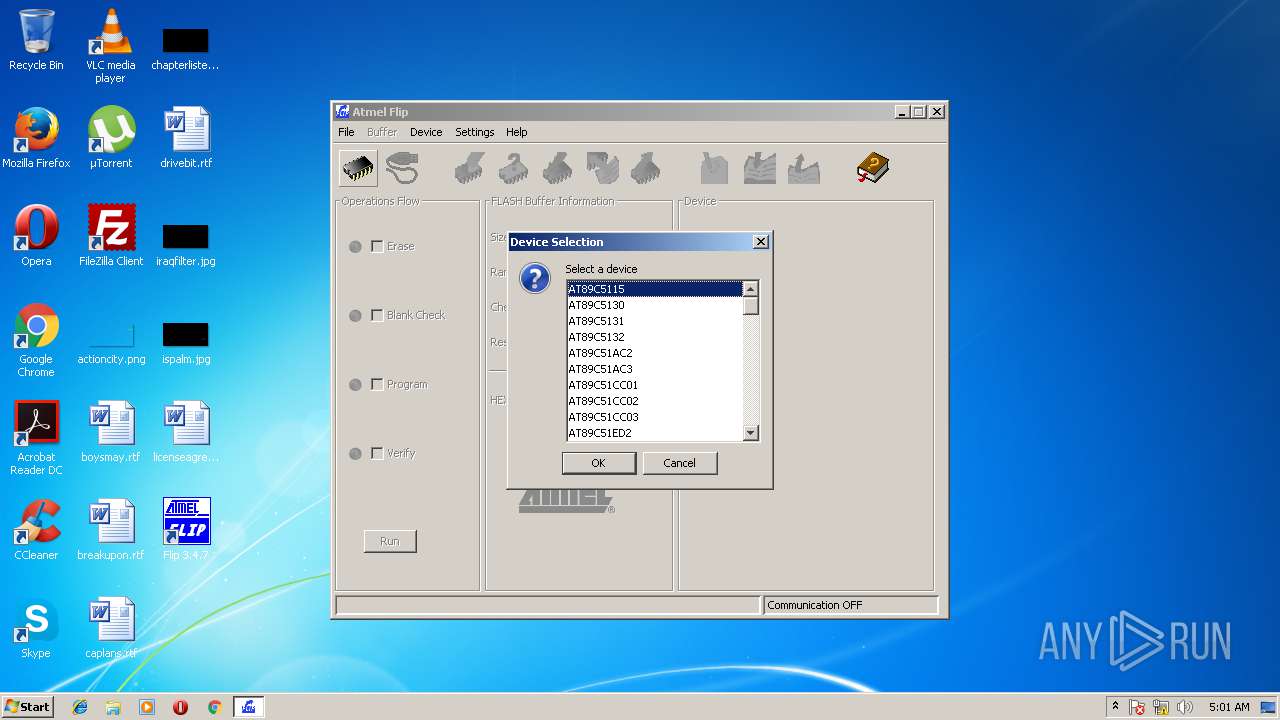
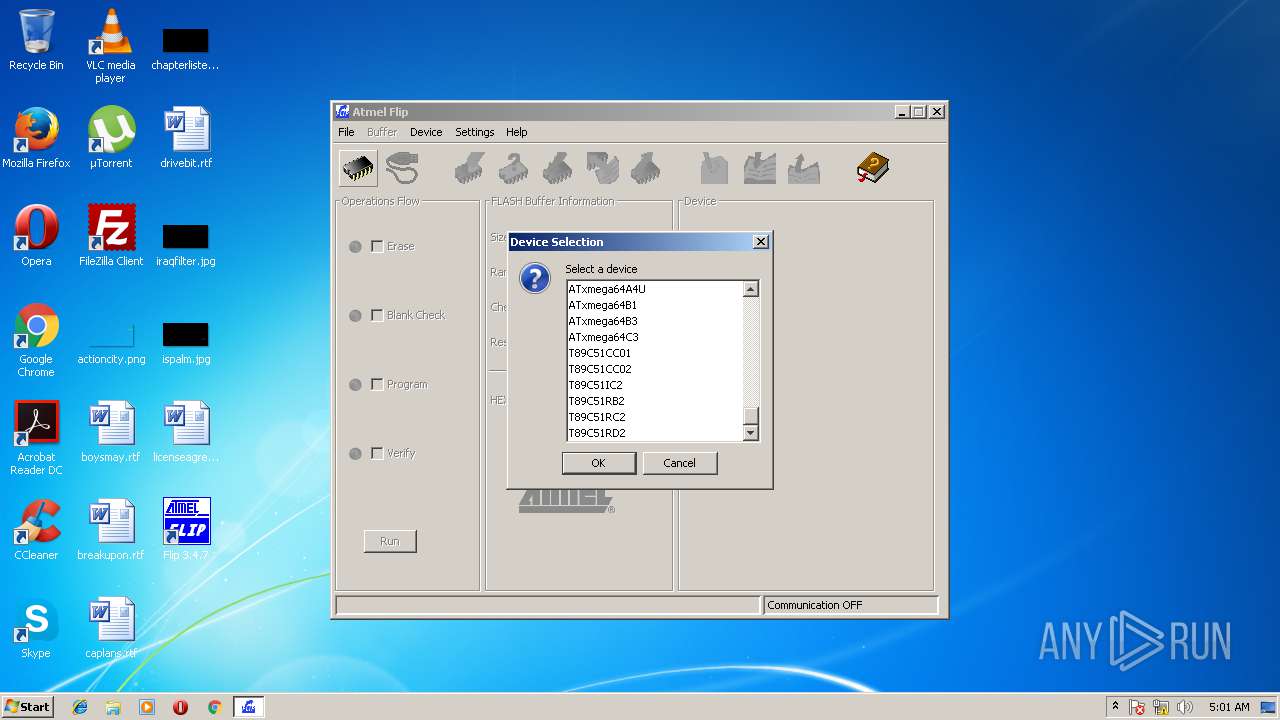
Executes JAVA applets
- flip.exe (PID: 3112)
Creates files in the program directory
- Atmel_appli_Install.exe (PID: 1272)
INFO
Application launched itself
- iexplore.exe (PID: 3084)
Changes internet zones settings
- iexplore.exe (PID: 3084)
Creates files in the user directory
- iexplore.exe (PID: 3988)
Reads internet explorer settings
- iexplore.exe (PID: 3988)
Reads Internet Cache Settings
- iexplore.exe (PID: 3988)
Dropped object may contain URL's
- iexplore.exe (PID: 3988)
- Atmel_appli_Install.exe (PID: 1272)
- iexplore.exe (PID: 3084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:04:27 21:59:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3190 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.7.0 |
| ProductVersionNumber: | 3.4.7.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | ASCII |
| CompanyName: | Atmel |
| CompanyWebsite: | www.atmel.com |
| FileDescription: | - |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | 3.4.7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2007 19:59:40 |
| Detected languages: |
|
| CompanyName: | Atmel |
| CompanyWebsite: | www.atmel.com |
| FileDescription: | - |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | 3.4.7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Apr-2007 19:59:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005B6E | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47324 |
.rdata | 0x00007000 | 0x00001286 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04135 |
.data | 0x00009000 | 0x00025CB8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.04684 |
.ndata | 0x0002F000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x00004158 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.88321 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 6.26612 | 4264 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
44
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1272 | "C:\Users\admin\AppData\Local\Temp\Atmel_appli_Install.exe" | C:\Users\admin\AppData\Local\Temp\Atmel_appli_Install.exe | a80467a1-8cf9-435a-bf25-6210c2a6143d.exe | ||||||||||||
User: admin Company: Atmel Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1692 | "C:\Users\admin\AppData\Local\Temp\a80467a1-8cf9-435a-bf25-6210c2a6143d.exe" | C:\Users\admin\AppData\Local\Temp\a80467a1-8cf9-435a-bf25-6210c2a6143d.exe | explorer.exe | ||||||||||||
User: admin Company: Atmel Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Program Files\Atmel\Flip 3.4.7\bin\flip.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | flip.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\Temp\a80467a1-8cf9-435a-bf25-6210c2a6143d.exe" | C:\Users\admin\AppData\Local\Temp\a80467a1-8cf9-435a-bf25-6210c2a6143d.exe | — | explorer.exe | |||||||||||
User: admin Company: Atmel Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 3084 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Atmel_appli_Install.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Atmel\Flip 3.4.7\bin\flip.exe" | C:\Program Files\Atmel\Flip 3.4.7\bin\flip.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3988 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3084 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 030
Read events
960
Write events
69
Delete events
1
Modification events
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Atmel\Flip 3.4.7\Components |
| Operation: | write | Name: | Main |
Value: 1 | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Atmel\Flip 3.4.7 |
| Operation: | write | Name: | Path |
Value: C:\Program Files\Atmel\Flip 3.4.7 | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Atmel\Flip 3.4.7 |
| Operation: | write | Name: | StartMenuGroup |
Value: Flip 3.4.7 | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\flip.exe |
| Operation: | write | Name: | DisplayName |
Value: Flip 3.4.7 | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\flip.exe |
| Operation: | write | Name: | DisplayVersion |
Value: 3.4.7 | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\flip.exe |
| Operation: | write | Name: | Publisher |
Value: Atmel | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\flip.exe |
| Operation: | write | Name: | URLInfoAbout |
Value: www.atmel.com | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\flip.exe |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Atmel\Flip 3.4.7\uninstall.exe | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\flip.exe |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Atmel\Flip 3.4.7\uninstall.exe | |||
| (PID) Process: | (1272) Atmel_appli_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\flip.exe |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
42
Suspicious files
4
Text files
552
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1692 | a80467a1-8cf9-435a-bf25-6210c2a6143d.exe | C:\Users\admin\AppData\Local\Temp\nsh27EA.tmp\jre.ini | text | |
MD5:— | SHA256:— | |||
| 1272 | Atmel_appli_Install.exe | C:\Users\admin\AppData\Local\Temp\nss29AF.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 1272 | Atmel_appli_Install.exe | C:\Users\admin\AppData\Local\Temp\nss29AF.tmp\AdvSplash.dll | executable | |
MD5:166F6790B14B42BF785F591C176A6517 | SHA256:DACBA23574C50255764909FEA1187A4B0227DFFF39CAA0D162D3496E76843644 | |||
| 1692 | a80467a1-8cf9-435a-bf25-6210c2a6143d.exe | C:\Users\admin\AppData\Local\Temp\Atmel_appli_Install.exe | executable | |
MD5:E4D4A87854F091F2BA56C84B3A263567 | SHA256:129CF866B949AF4AE315AA84E4A83EBD872C9AF08FBBC34F450B5625BC84E0D1 | |||
| 1272 | Atmel_appli_Install.exe | C:\Users\admin\AppData\Local\Temp\nss29AF.tmp\spltmp.bmp | image | |
MD5:3C01842C0025E111C262F10F6E224146 | SHA256:6C28EFEF7AD55AD74E481260DEB069ACBBFFB568186163350C3CFB887542ADF0 | |||
| 1272 | Atmel_appli_Install.exe | C:\Program Files\Atmel\Flip 3.4.7\bin\AtCanIxxat2.dll | executable | |
MD5:3E44DF692245BB278F37792342160B47 | SHA256:206309A886F3E842811B833EC2AFFEA95D2BA03A27C0D4D4C5747EE330B086C2 | |||
| 1272 | Atmel_appli_Install.exe | C:\Program Files\Atmel\Flip 3.4.7\bin\AtCanJanz.dll | executable | |
MD5:64D98E0ADFEA77361FDED360DF558242 | SHA256:4FE9D75B9F96C418EAAF8B8E27297457A873025428AD447394603D4CBFAD3359 | |||
| 1272 | Atmel_appli_Install.exe | C:\Users\admin\AppData\Local\Temp\nss29AF.tmp\StartMenu.dll | executable | |
MD5:EE388FDF6BF27673F7874D26F85724AC | SHA256:F31C16B1ECB01C7AA12F1893EC5935C1D9EDA7F5CACCF1616A0044BFBA4EE3A5 | |||
| 1272 | Atmel_appli_Install.exe | C:\Program Files\Atmel\Flip 3.4.7\COPYING_GPL.txt | text | |
MD5:FDAFC691AA5FB7F8E2A9E9521FEF771B | SHA256:19404E184CF45EC991B54E1E6F05F847AD8F13FEE2A51F3A2D9A960C8F7CB26B | |||
| 1272 | Atmel_appli_Install.exe | C:\Users\admin\AppData\Local\Temp\nss29AF.tmp\InstallOptions.dll | executable | |
MD5:7AF3EAD73BEDF48083D088228D99B200 | SHA256:75FF58404F0211A16341AEE2EEEB5C19AFC8D7827A79B27C5AA501F53A0BAD71 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3084 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3084 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |