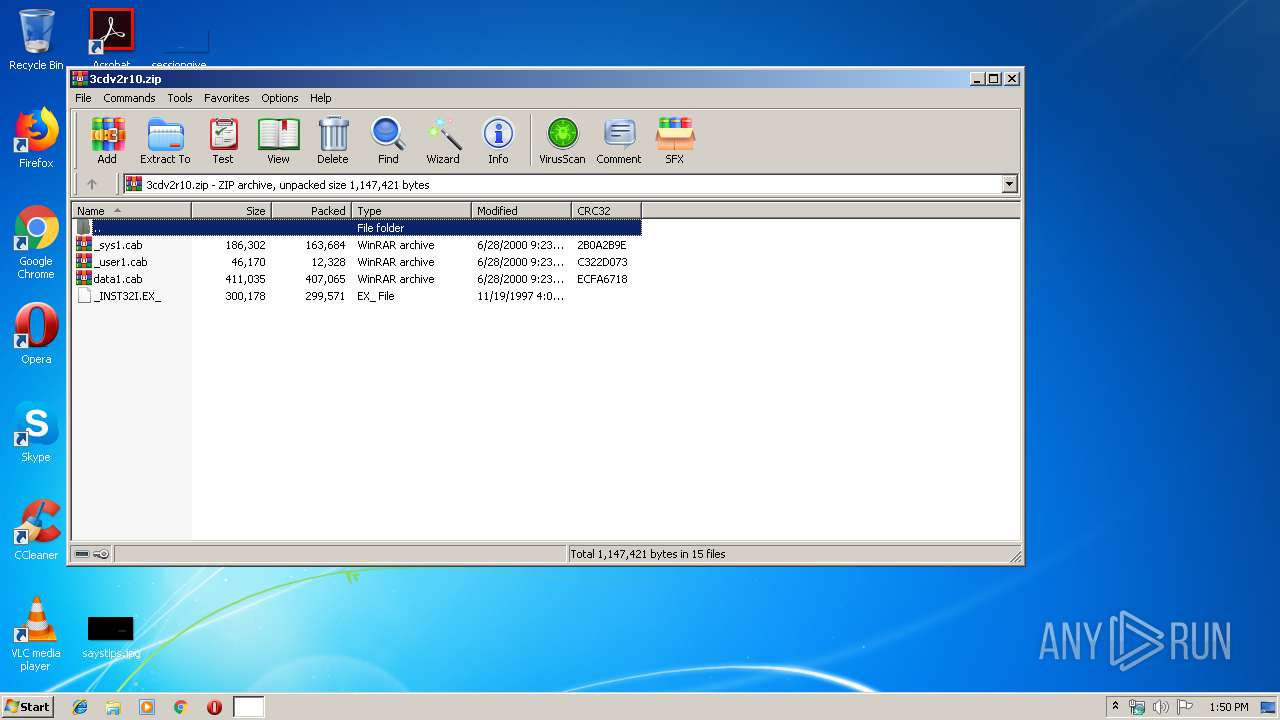
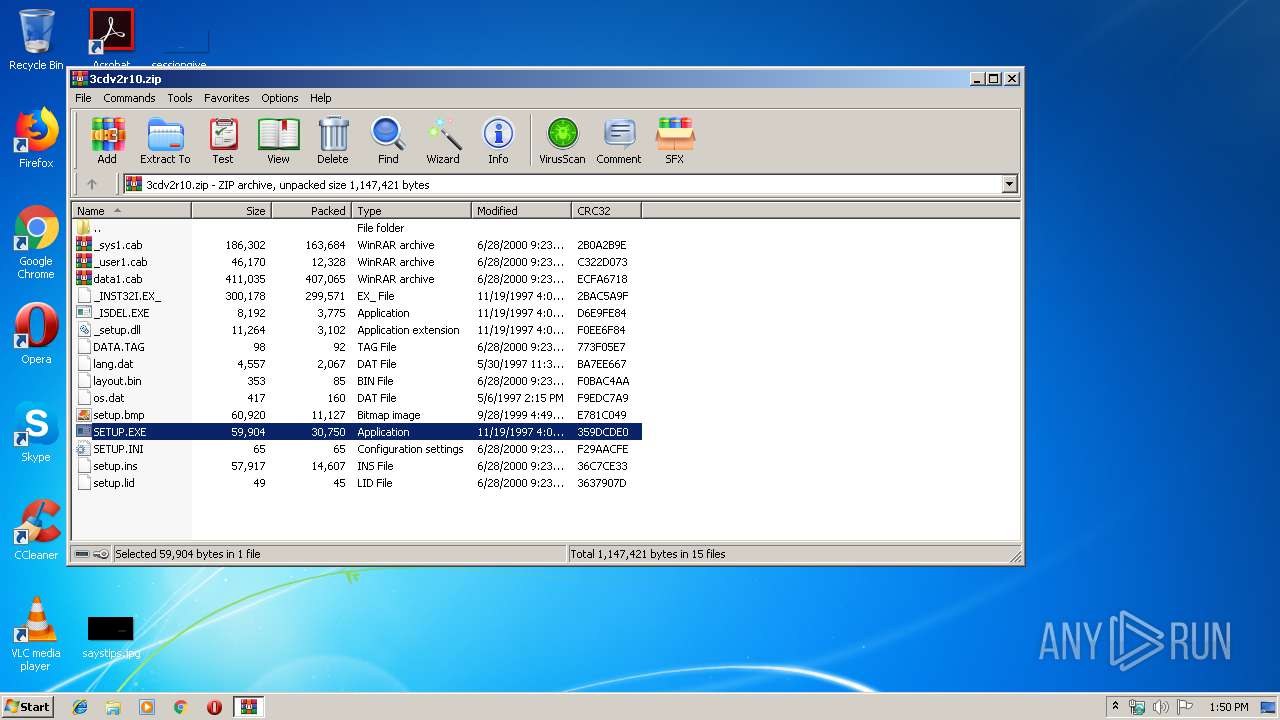
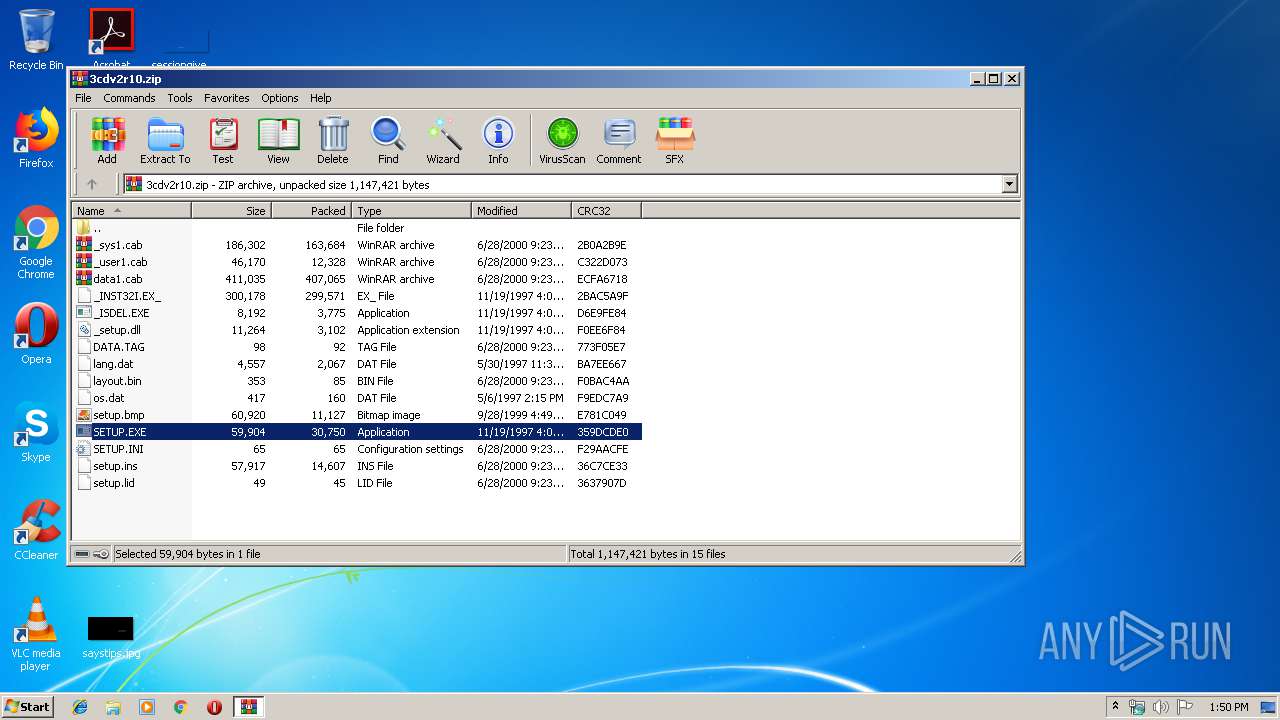
| File name: | 3cdv2r10.zip |
| Full analysis: | https://app.any.run/tasks/d2a1efd7-6549-4238-b68b-4aab15f9ffd1 |
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2019, 13:50:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0CB7E580B5B1C9454EC1FE36BBB7D141 |
| SHA1: | 4240D478E26B12424846B5EFF4B3BF9A099D5D4E |
| SHA256: | 53DD6DDDB1102A7075948DBC4D023C47F9A260CBB1658C37610141BD521C8B16 |
| SSDEEP: | 24576:AyIcn3vZpwXcG9+Zk/tQhbtA99JLclvW4BV7wwG:Bn/vwXVQ24RA9f4v/BV7wwG |
MALICIOUS
Loads dropped or rewritten executable
- _INS5176._MP (PID: 3824)
- ntvdm.exe (PID: 2952)
Application was dropped or rewritten from another process
- _INS5176._MP (PID: 3824)
- 3CDaemon.EXE (PID: 3756)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2644)
- ntvdm.exe (PID: 2952)
- _INS5176._MP (PID: 3824)
Executes application which crashes
- csrstub.exe (PID: 932)
Removes files from Windows directory
- _INS5176._MP (PID: 3824)
- ntvdm.exe (PID: 2952)
Creates files in the program directory
- _INS5176._MP (PID: 3824)
- 3CDaemon.EXE (PID: 3756)
Creates a software uninstall entry
- _INS5176._MP (PID: 3824)
Starts application with an unusual extension
- ntvdm.exe (PID: 2952)
Creates files in the Windows directory
- _INS5176._MP (PID: 3824)
- ntvdm.exe (PID: 2952)
INFO
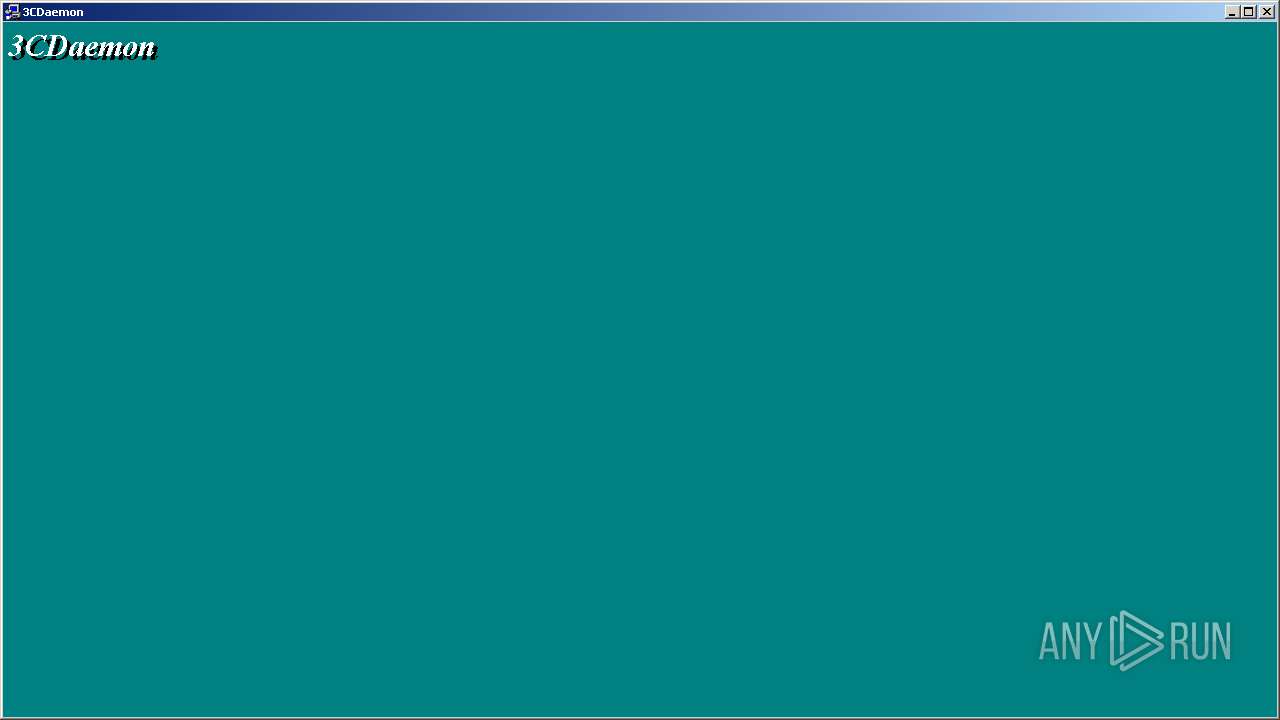
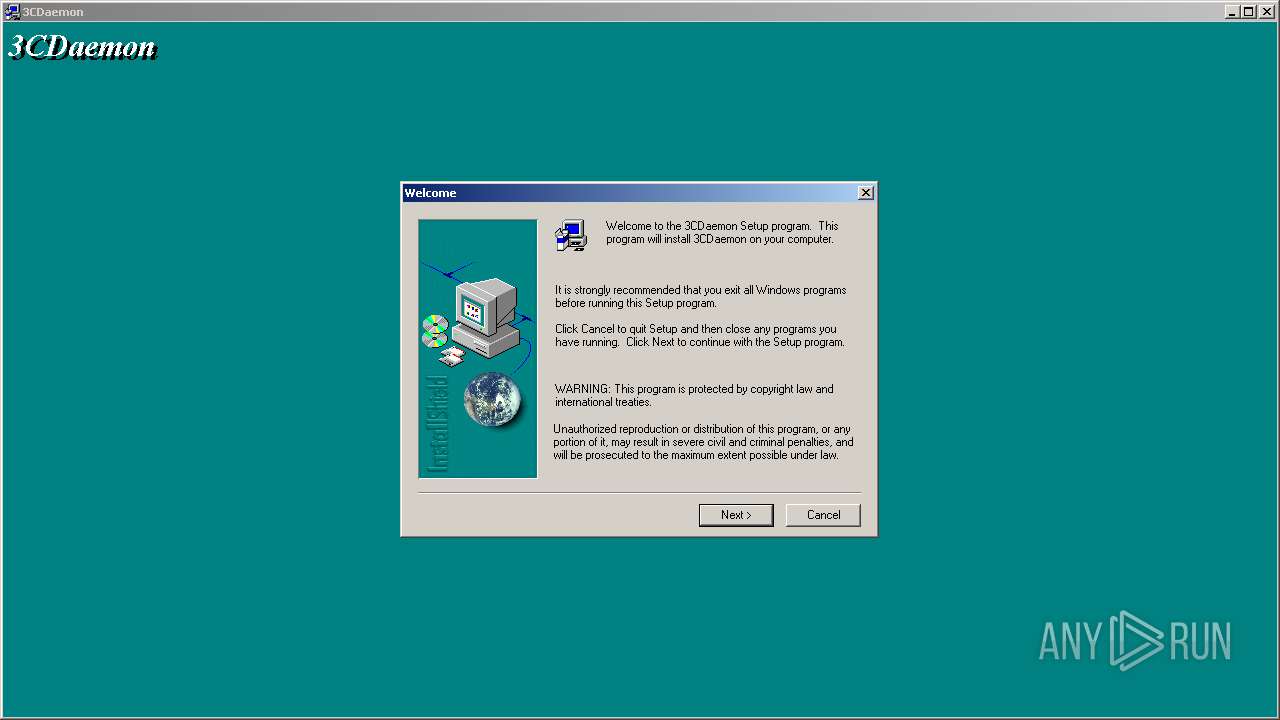
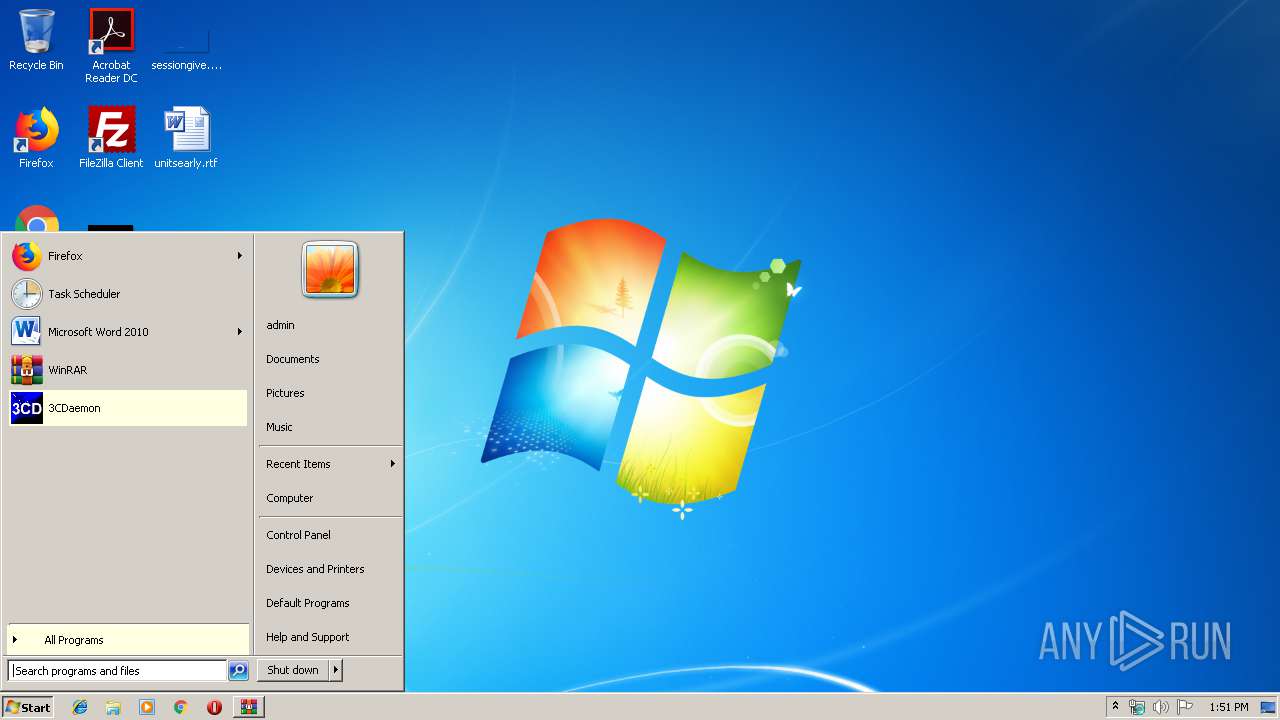
Manual execution by user
- 3CDaemon.EXE (PID: 3756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1997:11:19 16:05:25 |
| ZipCRC: | 0xd6e9fe84 |
| ZipCompressedSize: | 3775 |
| ZipUncompressedSize: | 8192 |
| ZipFileName: | _ISDEL.EXE |
Total processes
43
Monitored processes
5
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
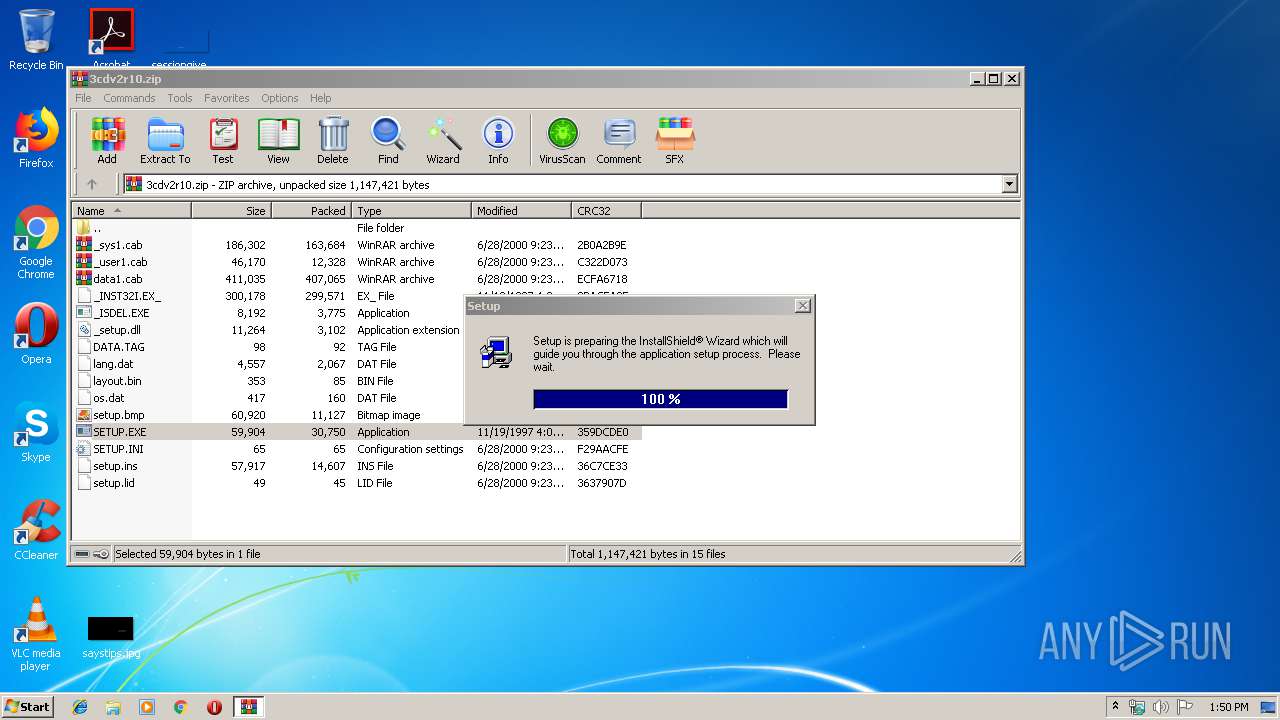
| 932 | csrstub.exe 67634196 -P "C:\Users\admin\AppData\Local\Temp\Rar$EXa2644.43362\SETUP.EXE" | C:\Windows\system32\csrstub.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: allows lua to launch 16-bit applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
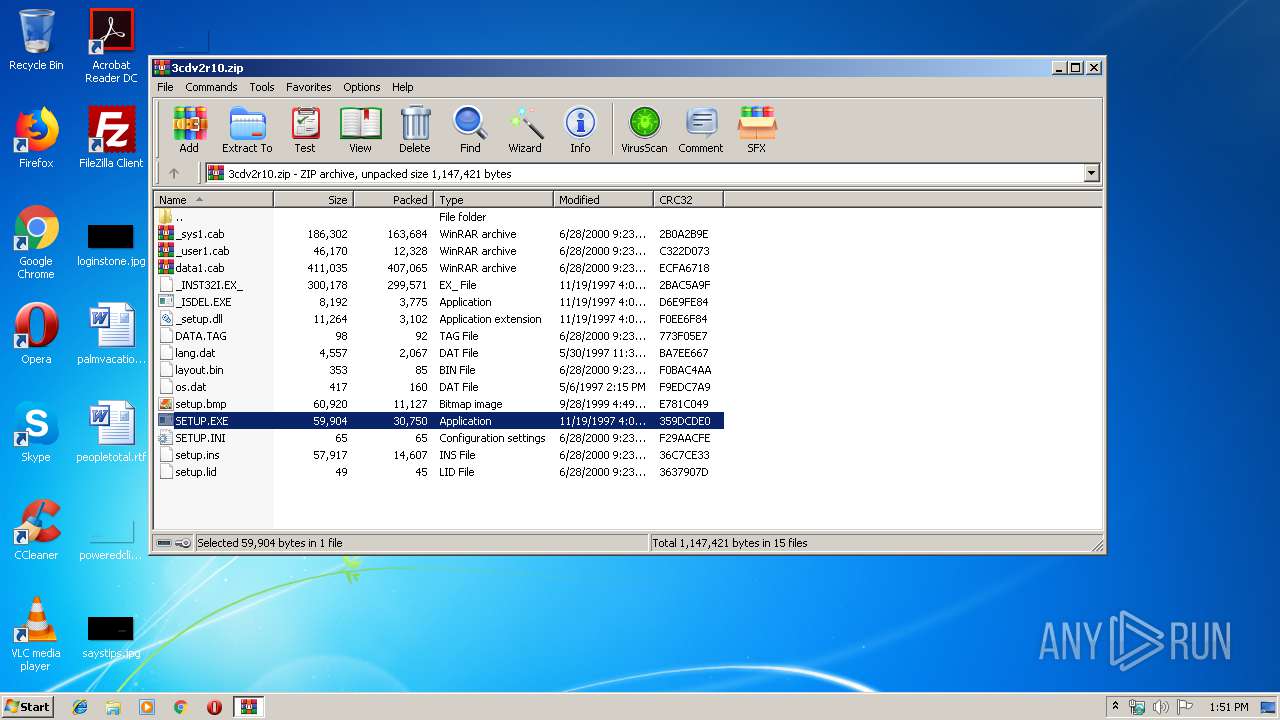
| 2644 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\3cdv2r10.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2952 | "C:\Windows\system32\ntvdm.exe" -i1 -ws | C:\Windows\system32\ntvdm.exe | csrstub.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
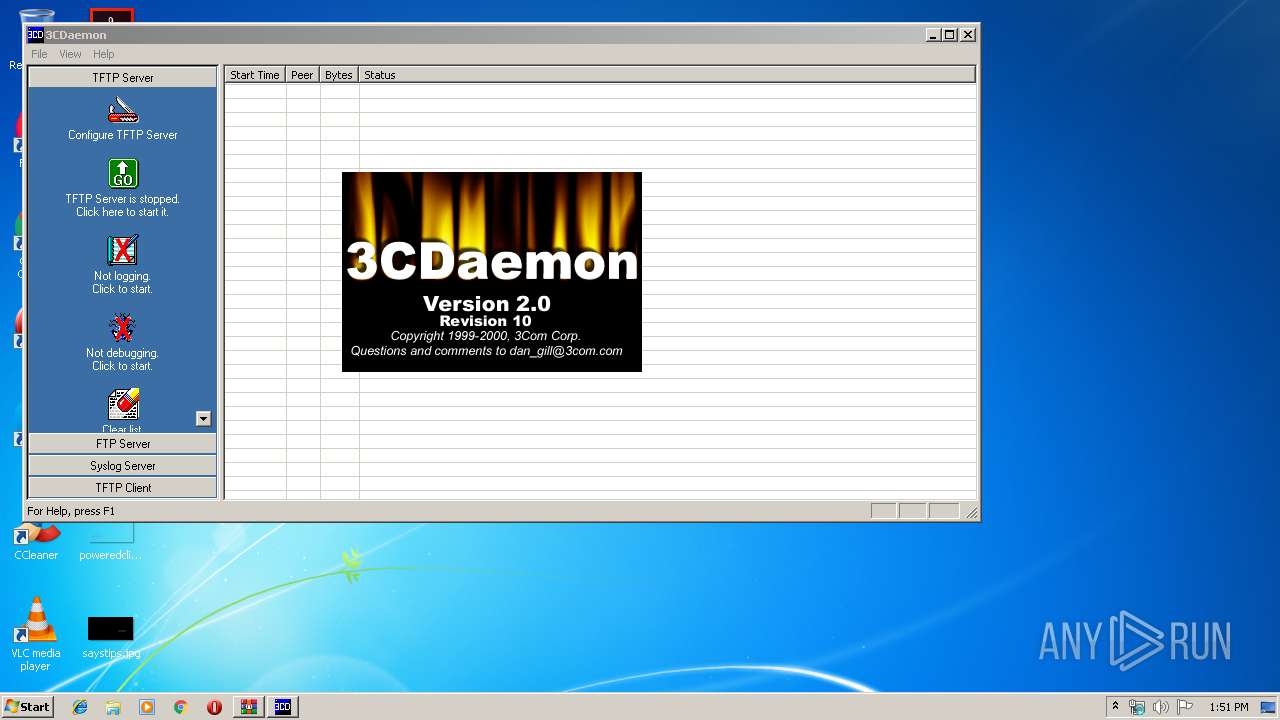
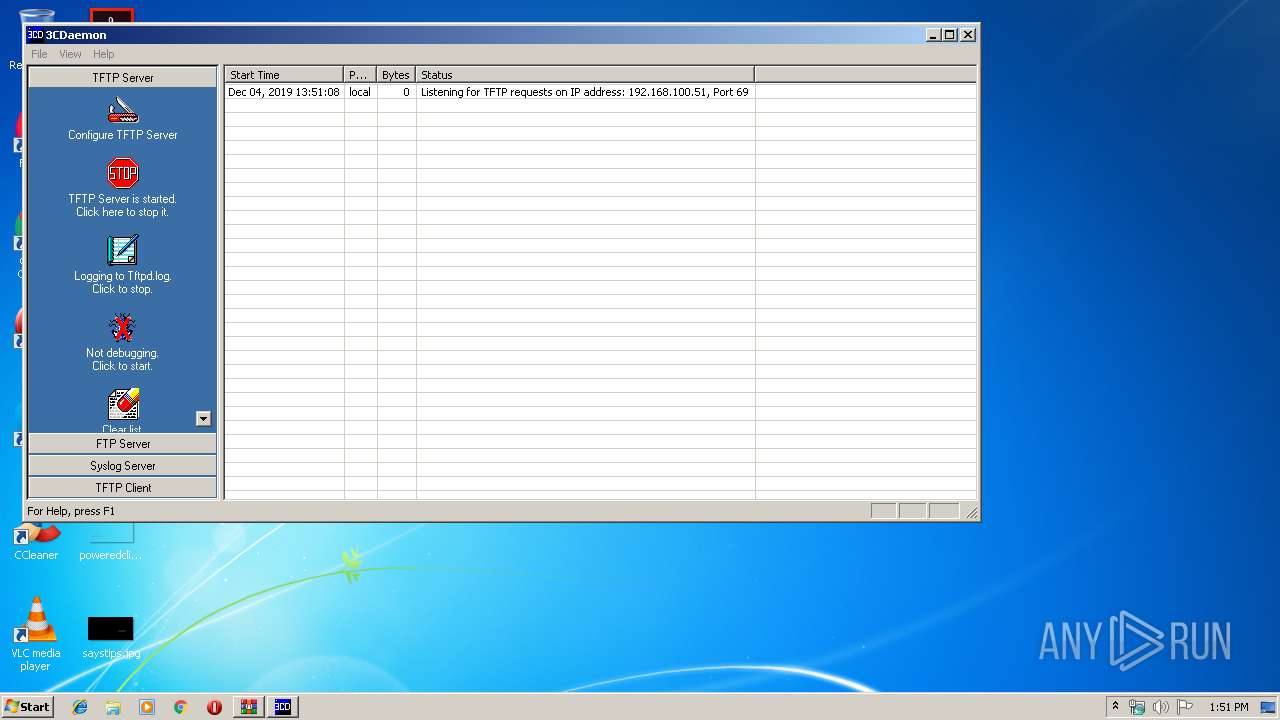
| 3756 | "C:\Program Files\3Com\3CDaemon\3CDaemon.EXE" | C:\Program Files\3Com\3CDaemon\3CDaemon.EXE | — | explorer.exe | |||||||||||
User: admin Company: 3Com Integrity Level: MEDIUM Description: 3CDaemon Application Exit code: 0 Version: 2, 0, 0, 10 Modules
| |||||||||||||||
| 3824 | C:\Users\admin\AppData\Local\Temp\_INS5176._MP | C:\Users\admin\AppData\Local\Temp\_INS5176._MP | ntvdm.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield Engine Exit code: 0 Version: 5.10.130.0 Modules
| |||||||||||||||
Total events
672
Read events
656
Write events
16
Delete events
0
Modification events
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3cdv2r10.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
10
Suspicious files
5
Text files
55
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsE634.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsE635.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | ntvdm.exe | C:\USERS\ADMIN\APPDATA\LOCAL\TEMP\_INS0432.INI | — | |
MD5:— | SHA256:— | |||
| 2952 | ntvdm.exe | C:\Windows\_delis43.ini | text | |
MD5:— | SHA256:— | |||
| 2952 | ntvdm.exe | C:\Windows\_iserr31.ini | text | |
MD5:— | SHA256:— | |||
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2644.43362\SETUP.EXE | executable | |
MD5:2E7BC5B75DF9C7BC2A53A32964C2D899 | SHA256:83441525FB5AEBE10892CFBC931395E2BB1F68C8720E49BB58749CB95981F06D | |||
| 3824 | _INS5176._MP | C:\Users\admin\AppData\Local\Temp\_ISTMP0.DIR\IsUninst.728 | — | |
MD5:— | SHA256:— | |||
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2644.43362\_INST32I.EX_ | ??_ | |
MD5:8D70C8885459CCFB5B8066C39E969699 | SHA256:C707F6BD6EEA954DDF0E8999ED949A506F915E4AE8237FBE52B3D548E68867B4 | |||
| 3824 | _INS5176._MP | C:\Users\admin\AppData\Local\Temp\_ISTMP0.DIR\_IsRes.Dll | — | |
MD5:— | SHA256:— | |||
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2644.43362\_setup.dll | executable | |
MD5:AF0F37E850846FA145BEF70474C5D214 | SHA256:2C294A582D85A39696025558AFA3B96376884BD1E95D37810422F8B2E4C2A224 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report