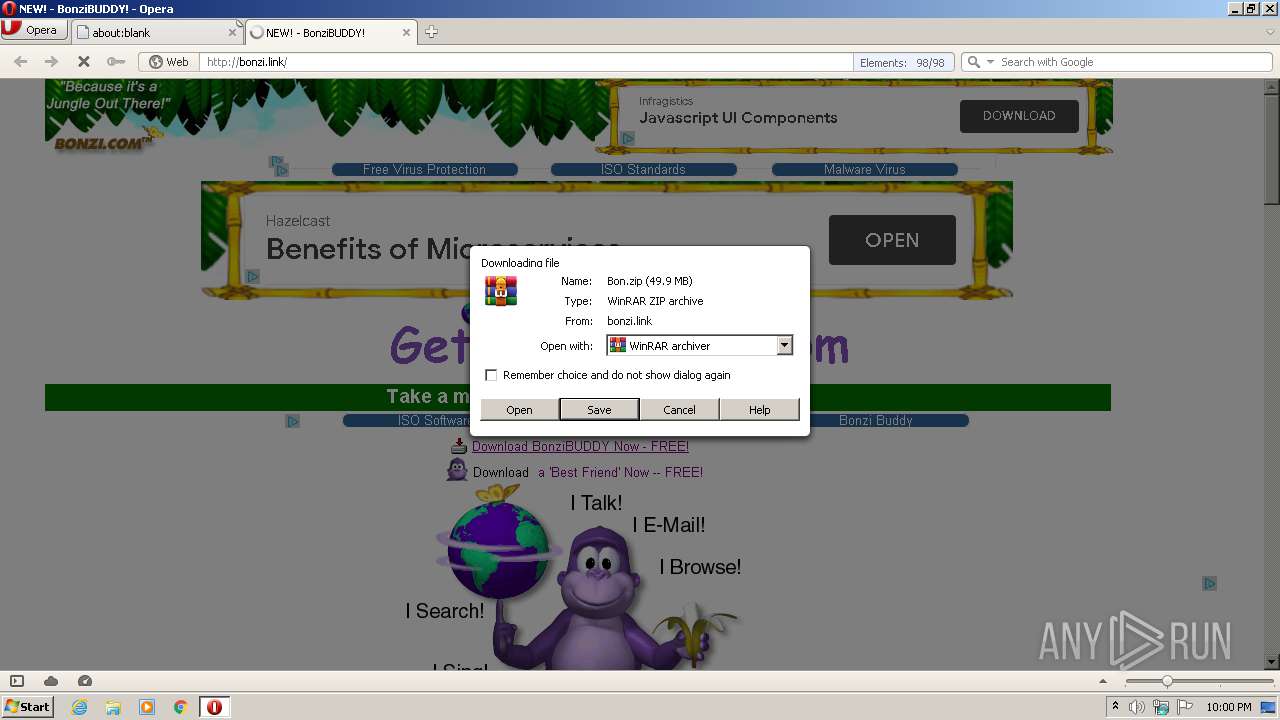
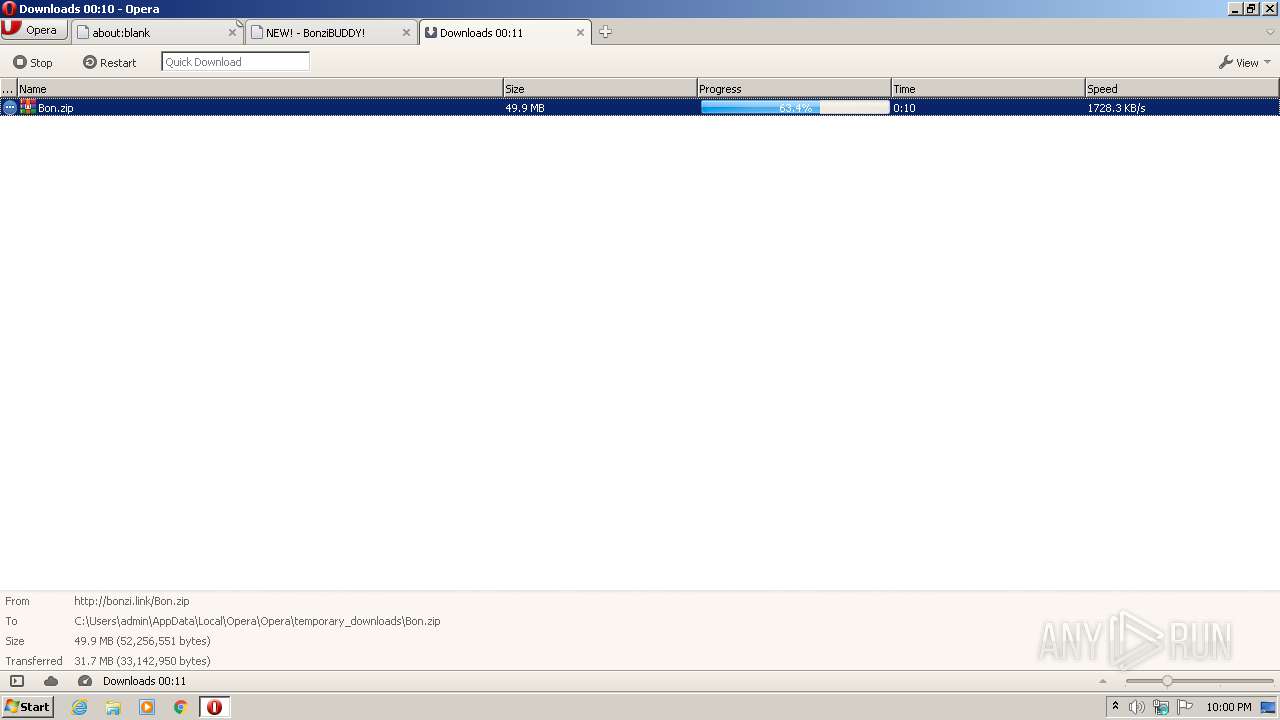
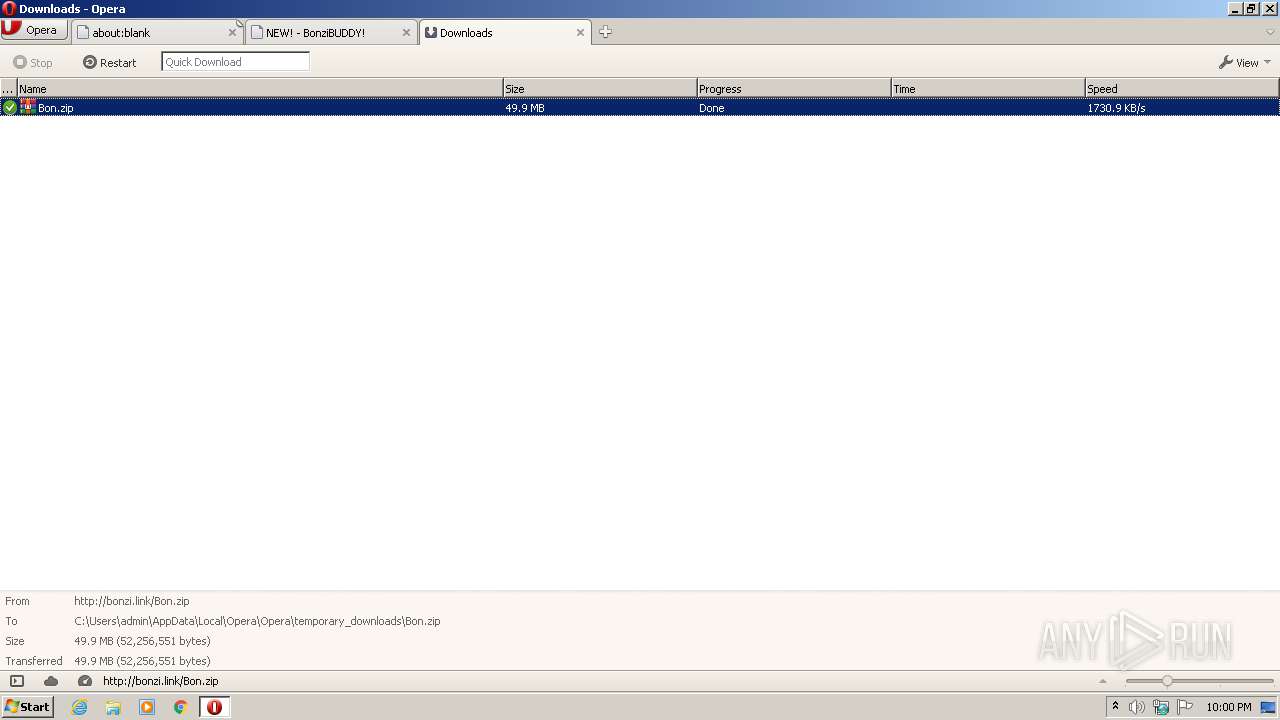
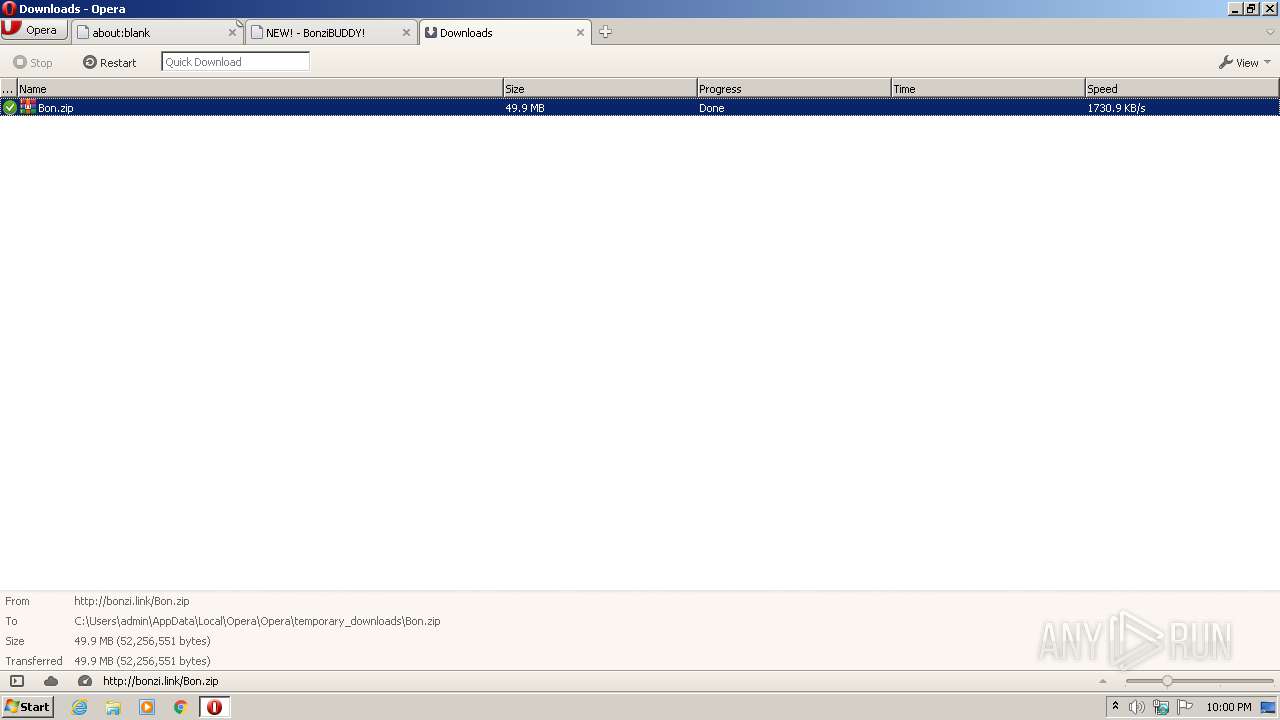
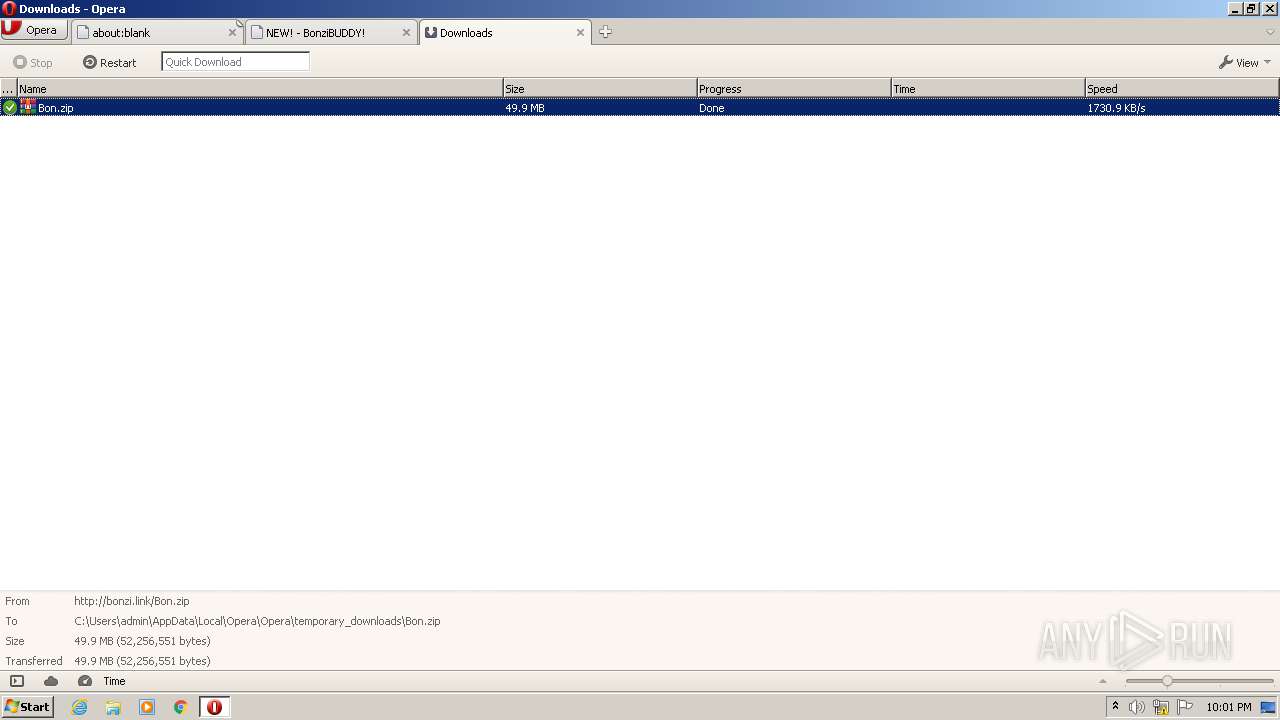
| URL: | http://bonzi.link/Bon.zip/ |
| Full analysis: | https://app.any.run/tasks/89bcc1e2-b09e-45f8-bb6a-e3cf7beca30e |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2020, 21:00:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B41B4EEADE670DA85C6B6A5E2C8D14B0 |
| SHA1: | D2934716E1B2BCA6D07004278F1DA72700E41548 |
| SHA256: | 53D7171C6392A61E8D44B95F332FC94C74E8B000C944044FCD0FFB4F30062589 |
| SSDEEP: | 3:N1KcX8KLH:CcX8KD |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 1936)
Creates files in the user directory
- opera.exe (PID: 1936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
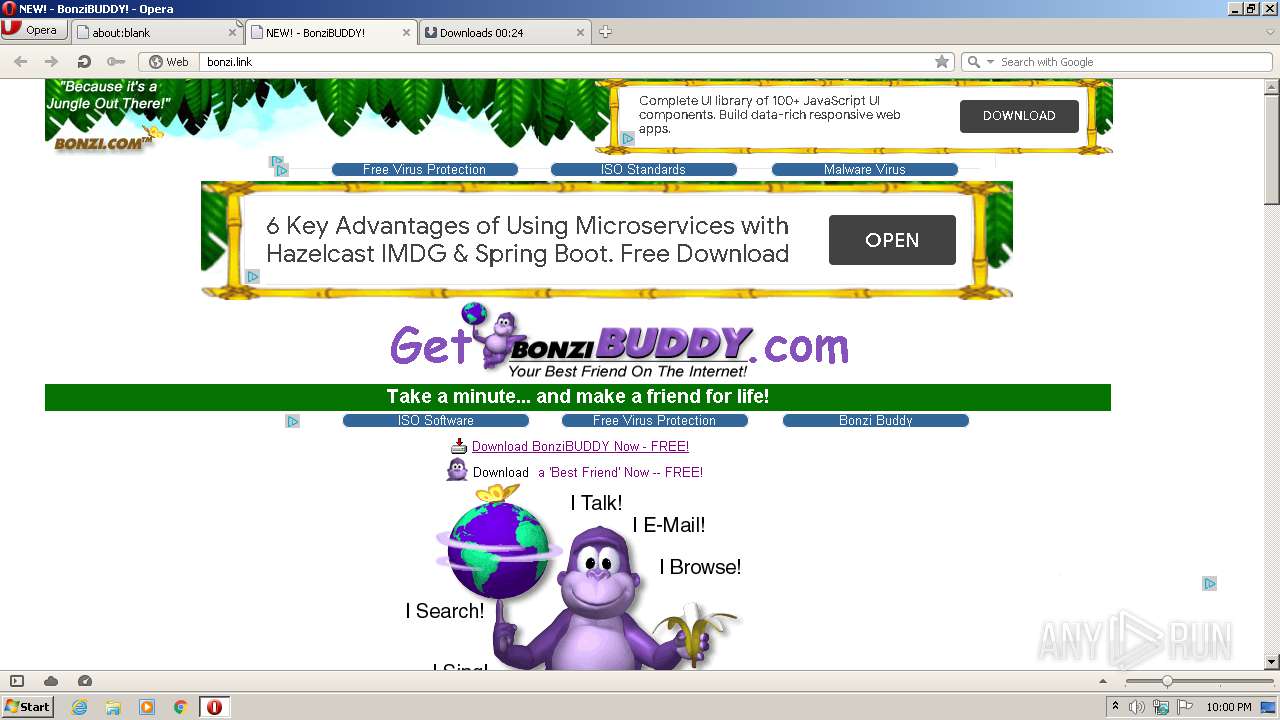
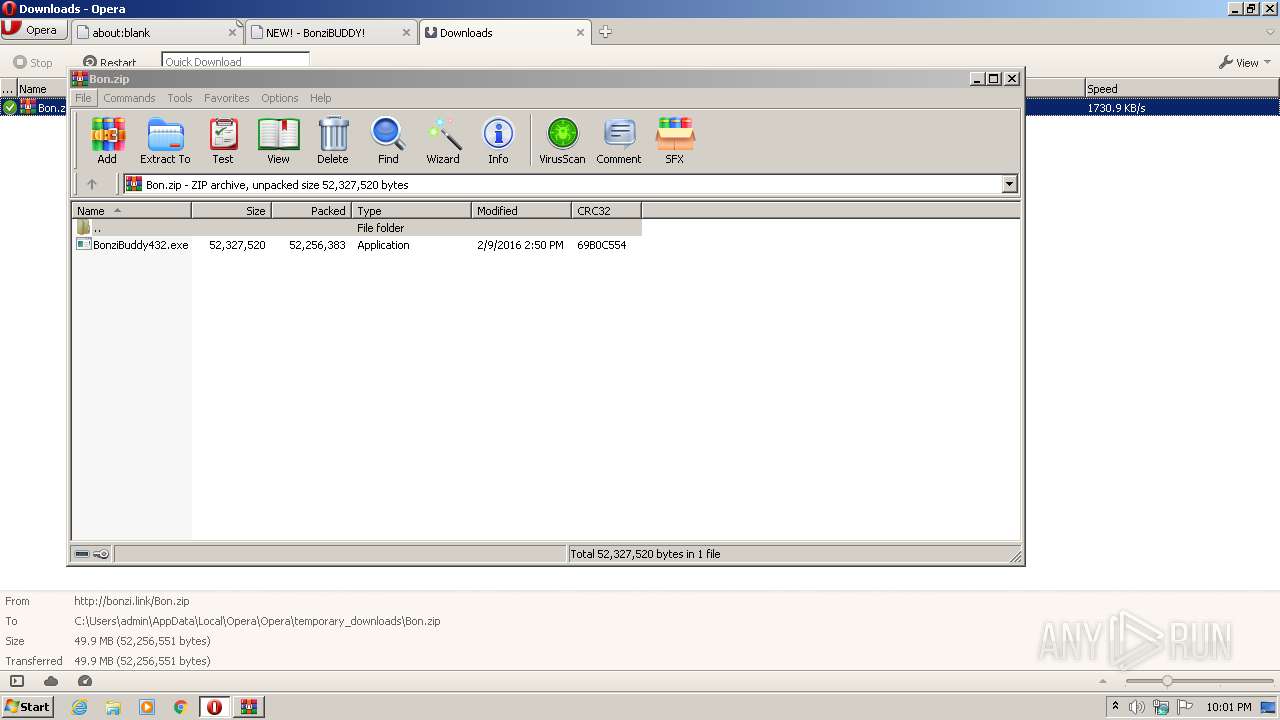
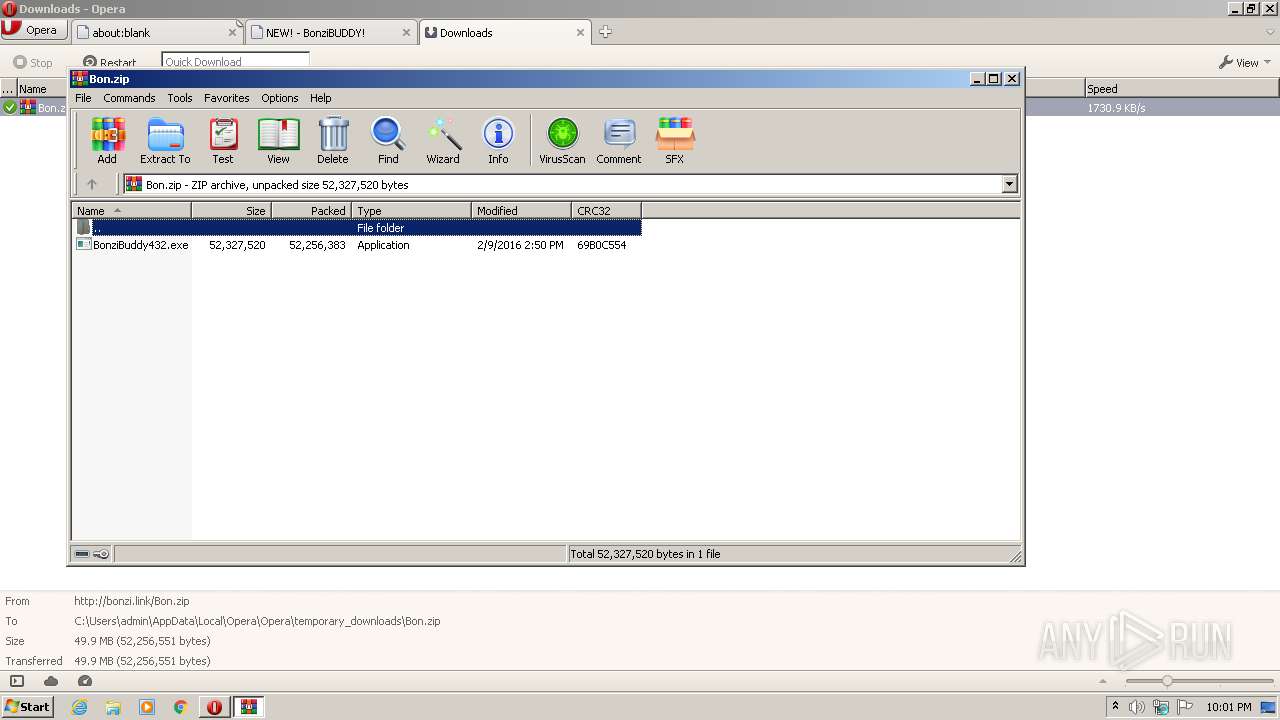
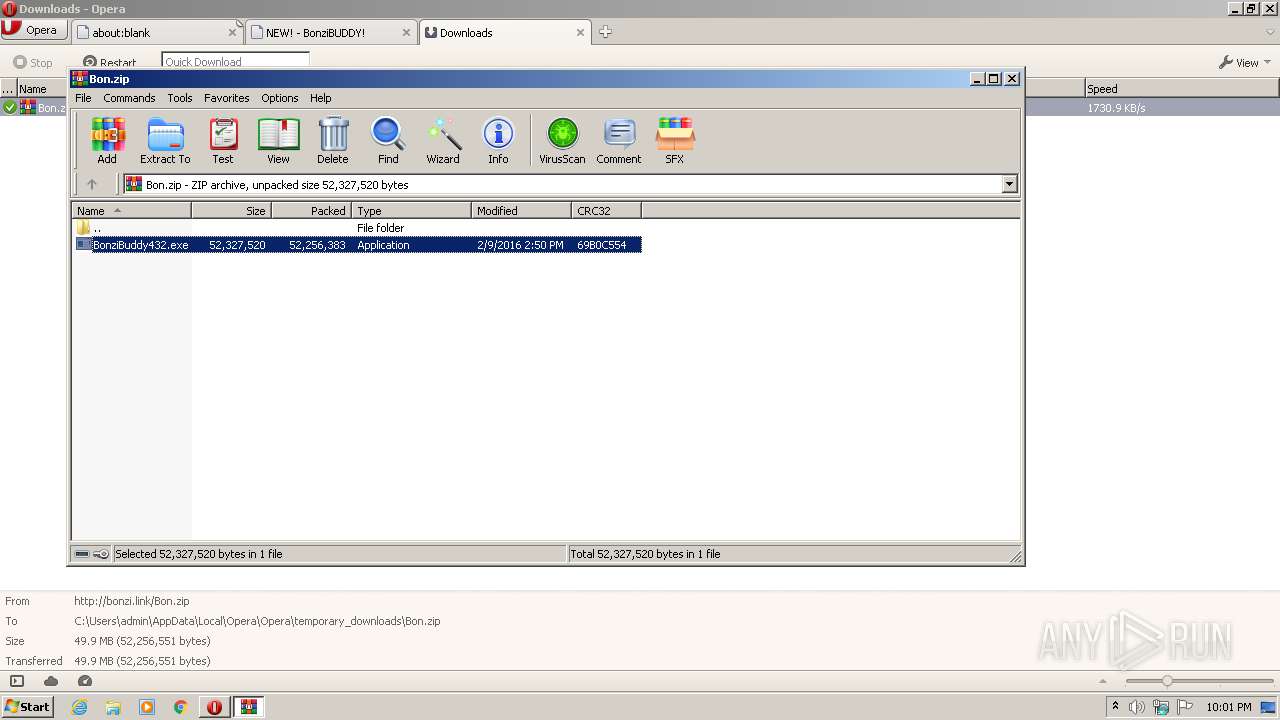
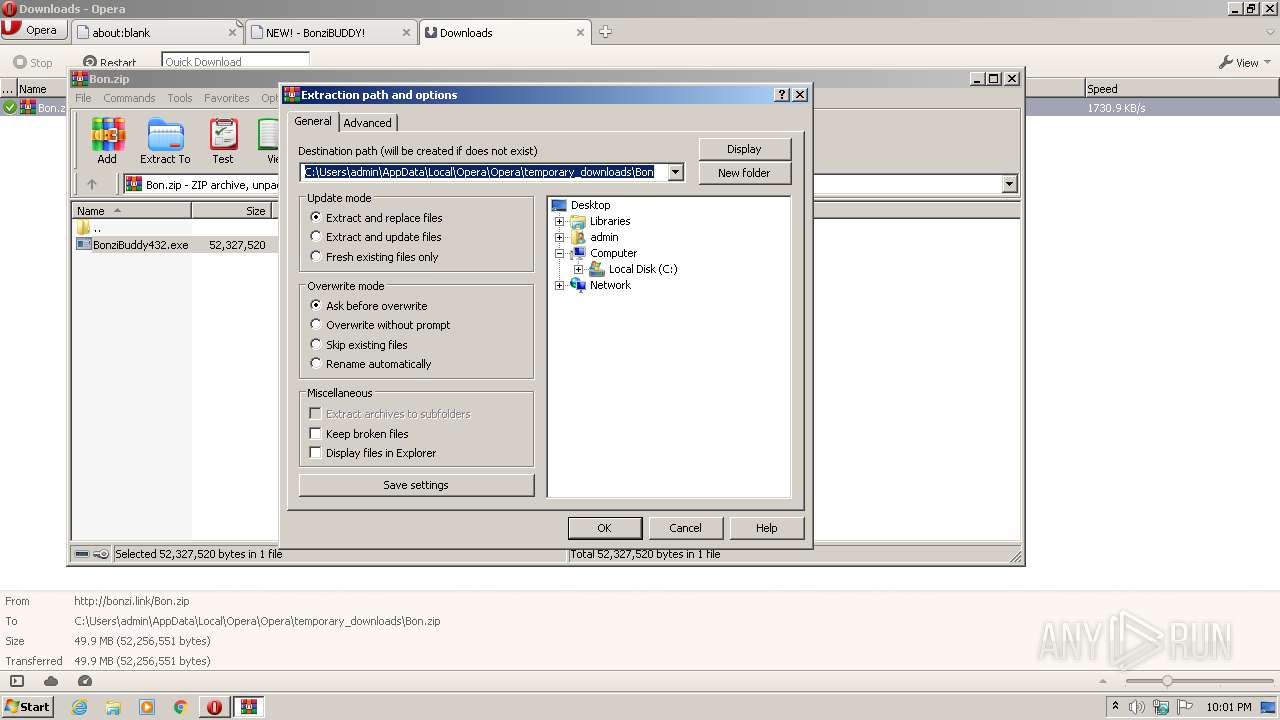
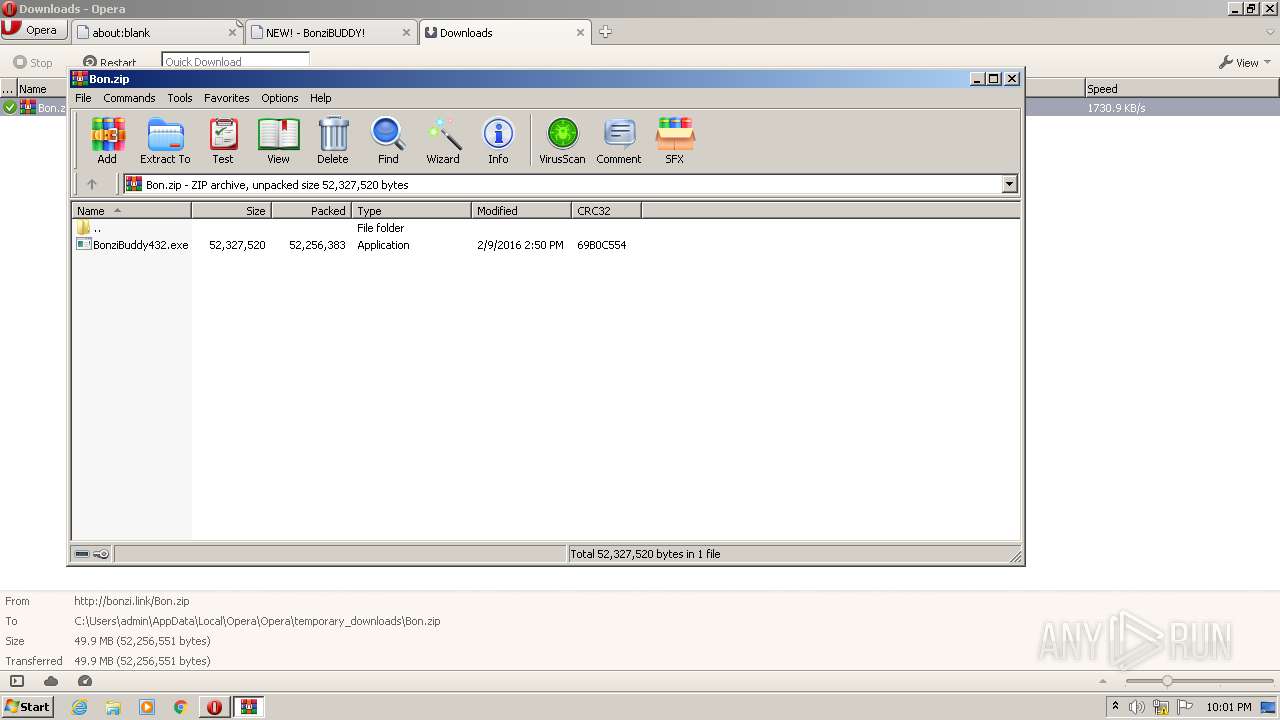
| 1868 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\Bon.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | opera.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Opera\opera.exe" "http://bonzi.link/Bon.zip/" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
983
Read events
897
Write events
86
Delete events
0
Modification events
| (PID) Process: | (1936) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "http://bonzi.link/Bon.zip/" | |||
| (PID) Process: | (1936) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1936) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1936) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1868) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1868) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\Bon.zip | |||
| (PID) Process: | (1868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
0
Suspicious files
71
Text files
42
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1936 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr6DC4.tmp | — | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr6DD5.tmp | — | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr6E14.tmp | — | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\00\17\opr7912.tmp | — | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\opr7922.tmp | — | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K1C2IJM48BB7A57KKGGU.temp | — | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr7A3D.tmp | — | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\assoc002\sesn\opr00004.000 | ttf | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\00\17\00000000 | text | |
MD5:— | SHA256:— | |||
| 1936 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\psindex.dat | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
74
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
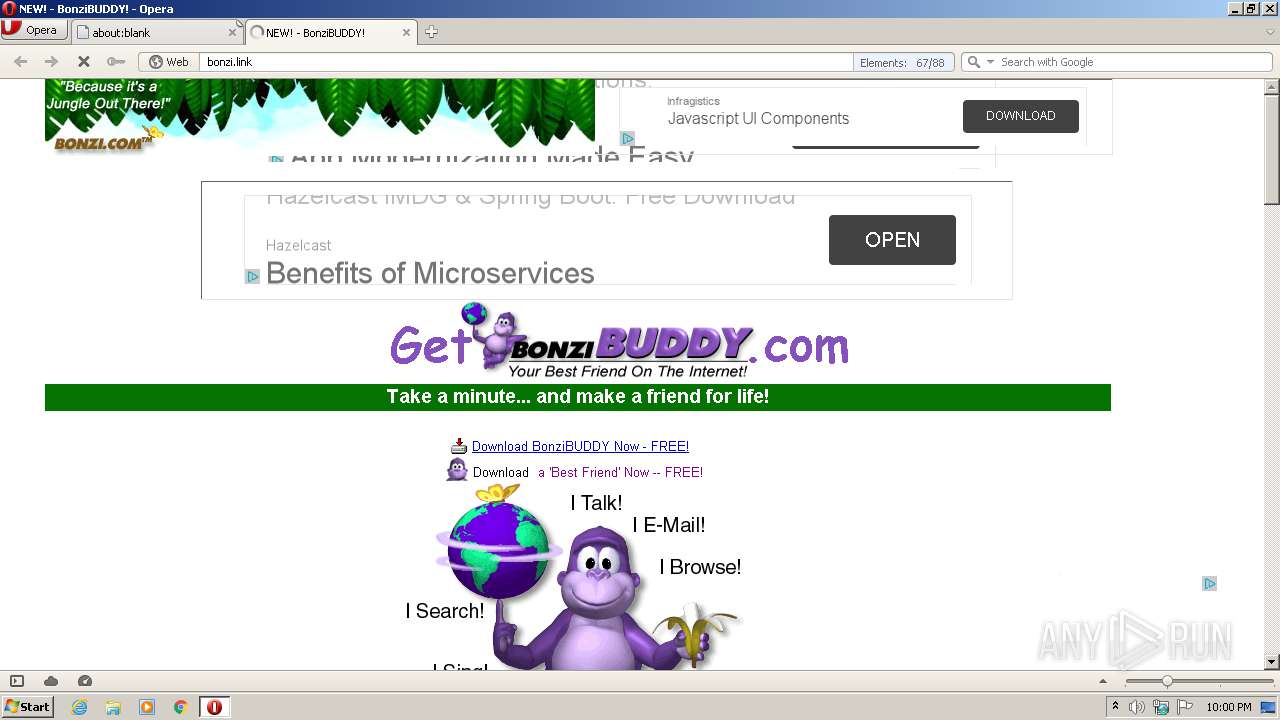
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/images/bbsearch.gif | GB | — | — | suspicious |
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/images/sepbar.jpg | GB | — | — | suspicious |
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/images/bbmail.gif | GB | — | — | suspicious |
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/images/meetyou.jpg | GB | — | — | suspicious |
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/images/bbabilities2.gif | GB | — | — | suspicious |
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/images/download.gif | GB | — | — | suspicious |
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/images/bbdownload.gif | GB | — | — | suspicious |
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/images/banana24.gif | GB | — | — | suspicious |
1936 | opera.exe | GET | — | 145.239.5.59:80 | http://bonzi.link/favicon.ico | GB | — | — | suspicious |
1936 | opera.exe | GET | 200 | 172.217.21.194:80 | http://pagead2.googlesyndication.com/pagead/show_ads.js | US | text | 30.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1936 | opera.exe | 185.26.182.93:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
1936 | opera.exe | 145.239.5.59:80 | bonzi.link | OVH SAS | GB | suspicious |
1936 | opera.exe | 185.26.182.118:80 | sitecheck2.opera.com | Opera Software AS | — | suspicious |
1936 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1936 | opera.exe | 172.217.22.34:443 | adservice.google.de | Google Inc. | US | whitelisted |
1936 | opera.exe | 172.217.16.129:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
1936 | opera.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1936 | opera.exe | 216.58.206.3:443 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1936 | opera.exe | 52.222.147.102:443 | d36ee2fcip1434.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
1936 | opera.exe | 185.64.190.78:443 | image6.pubmatic.com | PubMatic, Inc. | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bonzi.link |
| suspicious |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
adservice.google.de |
| whitelisted |
adservice.google.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crl.pki.goog |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |