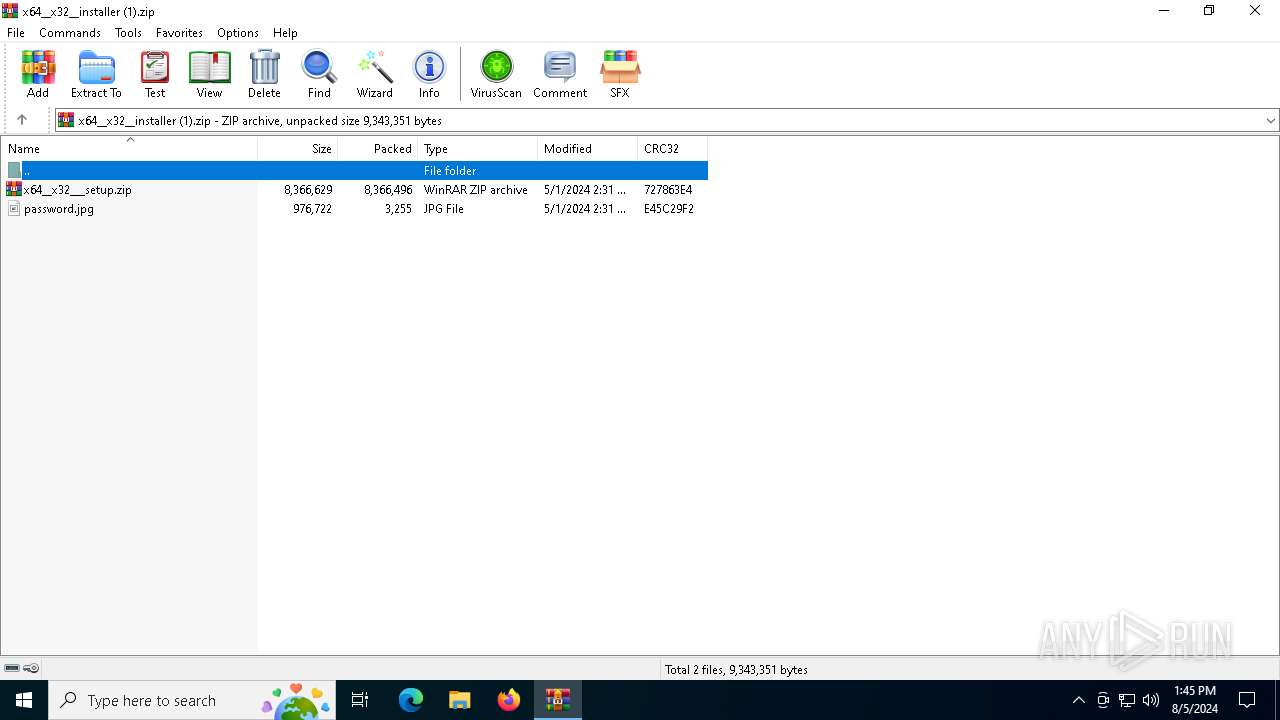
| File name: | x64__x32__installer (1).zip |
| Full analysis: | https://app.any.run/tasks/60da3e34-b176-4e48-ac1a-5b5658bf5623 |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2024, 13:45:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E5F53ECB931CEFEF3B66C8F08ED97B9A |
| SHA1: | D395E114E7A28FF8044C7552261D6D7DE49FAC26 |
| SHA256: | 53BFA98CB9BF49F55E670DAE62BC424D6910FAD1D85C48DA76E09148E64797E4 |
| SSDEEP: | 98304:F0Ih+J8ogLmnkDg7bjH+A+EvSCv/zLDf+71nc7jsQrvfqs8S2DC7Yi1vlvh4rHTU:YEfotEnjNUMyDb |
MALICIOUS
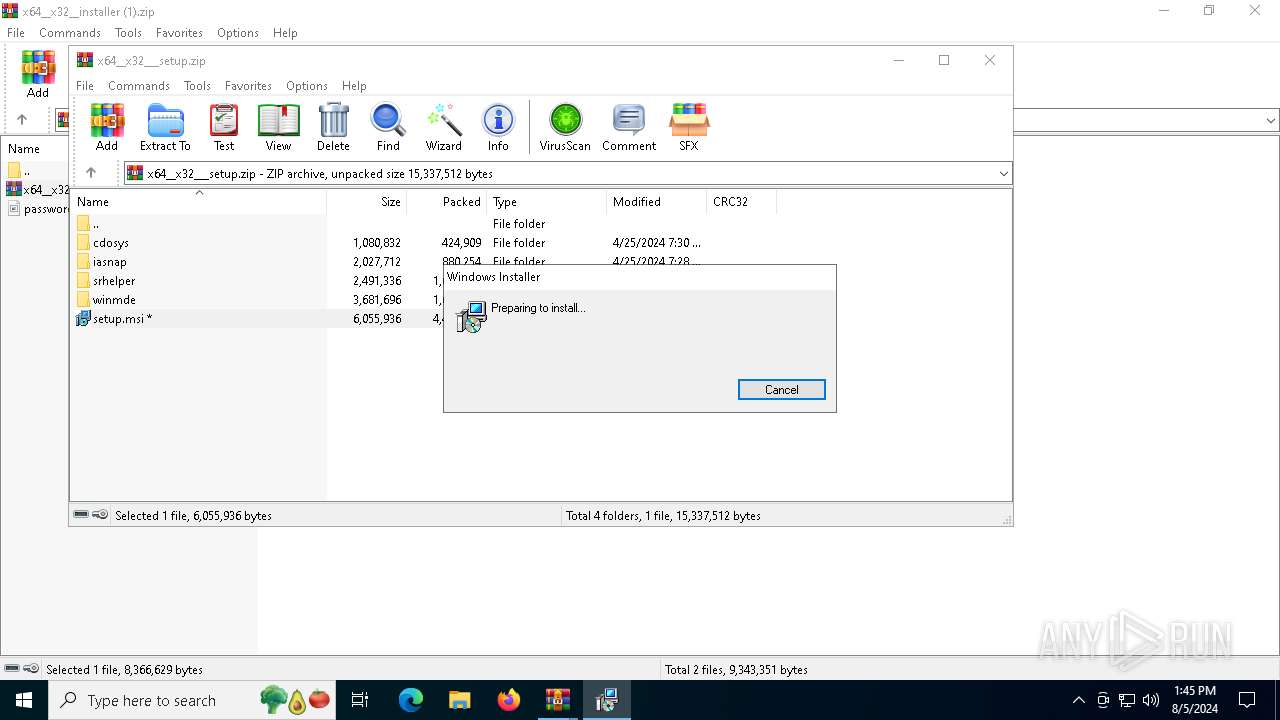
Drops the executable file immediately after the start
- msiexec.exe (PID: 7064)
Bypass execution policy to execute commands
- powershell.exe (PID: 4004)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 1664)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 2132)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6388)
- WinRAR.exe (PID: 2132)
Application launched itself
- WinRAR.exe (PID: 6388)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7064)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 1664)
The process executes Powershell scripts
- msiexec.exe (PID: 1664)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 1664)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1664)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7064)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2132)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2132)
Checks supported languages
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 1664)
- TextInputHost.exe (PID: 2064)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2132)
- msiexec.exe (PID: 7064)
Reads the computer name
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 1664)
- TextInputHost.exe (PID: 2064)
Reads Environment values
- msiexec.exe (PID: 1664)
Create files in a temporary directory
- msiexec.exe (PID: 1664)
- powershell.exe (PID: 4004)
Creates files or folders in the user directory
- msiexec.exe (PID: 7064)
Reads the software policy settings
- powershell.exe (PID: 4004)
Checks proxy server information
- powershell.exe (PID: 4004)
Reads security settings of Internet Explorer
- powershell.exe (PID: 4004)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4004)
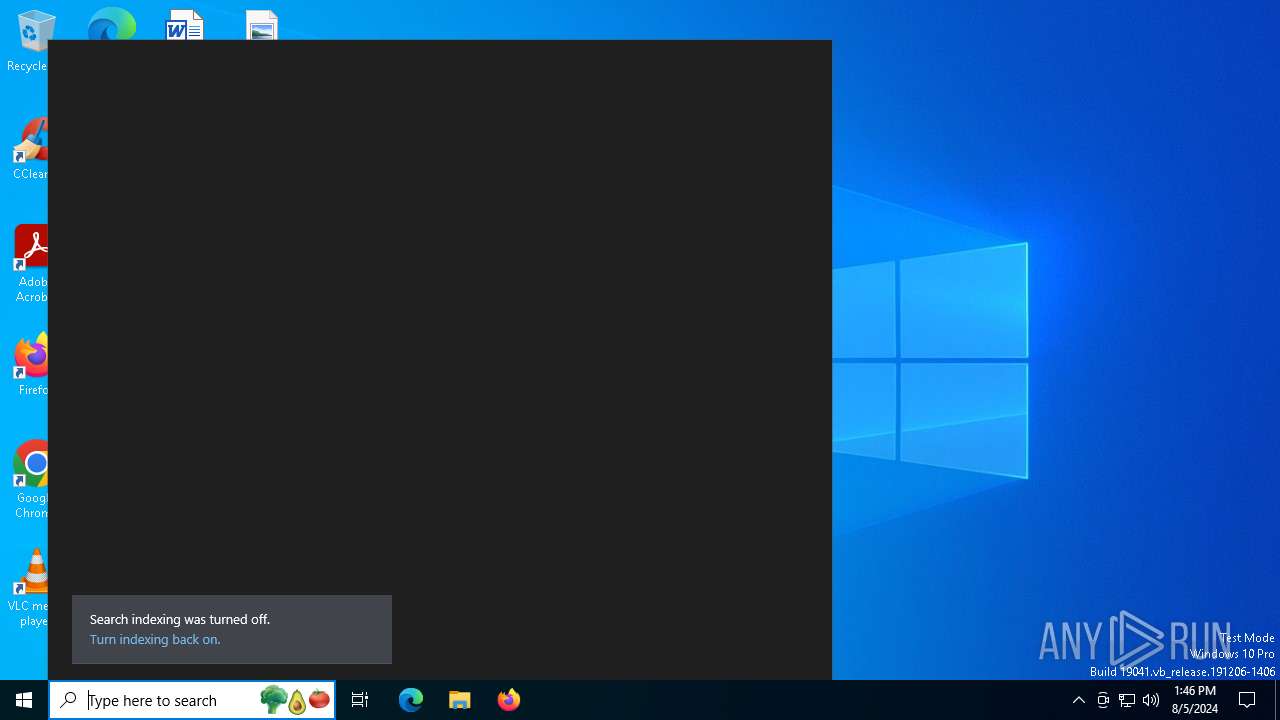
Disables trace logs
- powershell.exe (PID: 4004)
Creates a software uninstall entry
- msiexec.exe (PID: 7064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:05:01 17:31:36 |
| ZipCRC: | 0xe45c29f2 |
| ZipCompressedSize: | 3255 |
| ZipUncompressedSize: | 976722 |
| ZipFileName: | password.jpg |
Total processes
147
Monitored processes
8
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | C:\Windows\syswow64\MsiExec.exe -Embedding 45820014D2504098BF157208D335D668 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
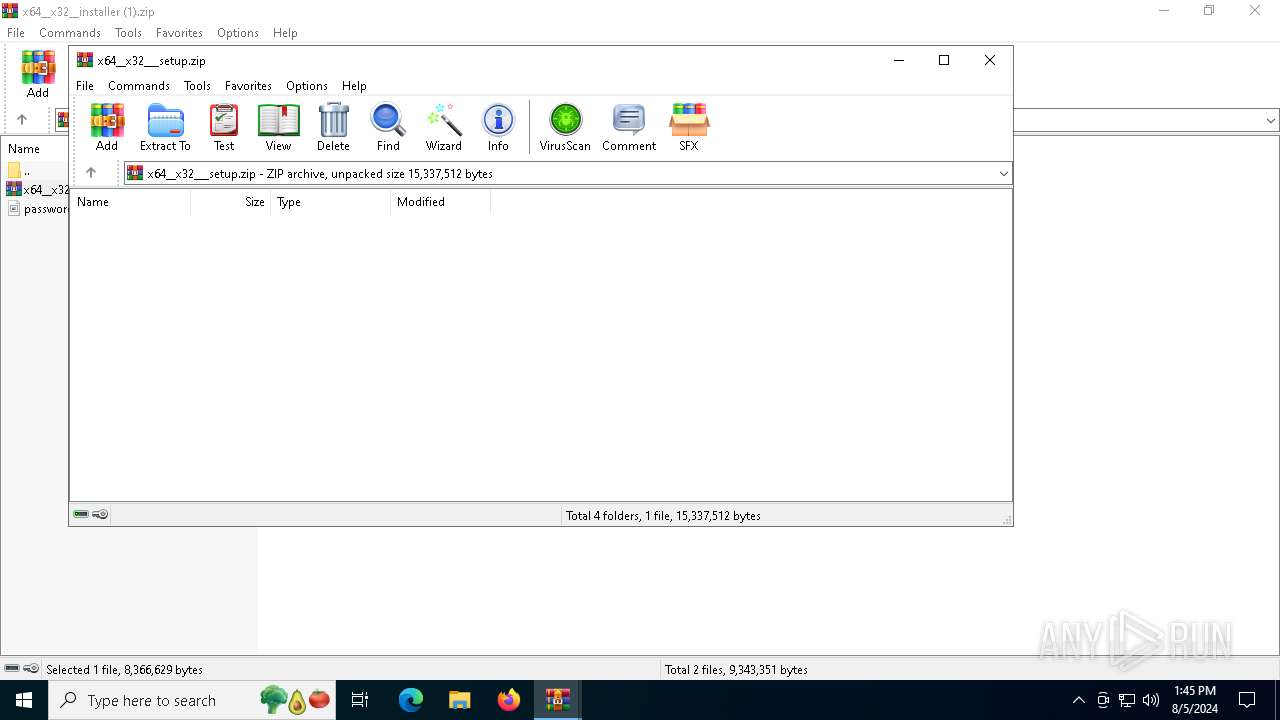
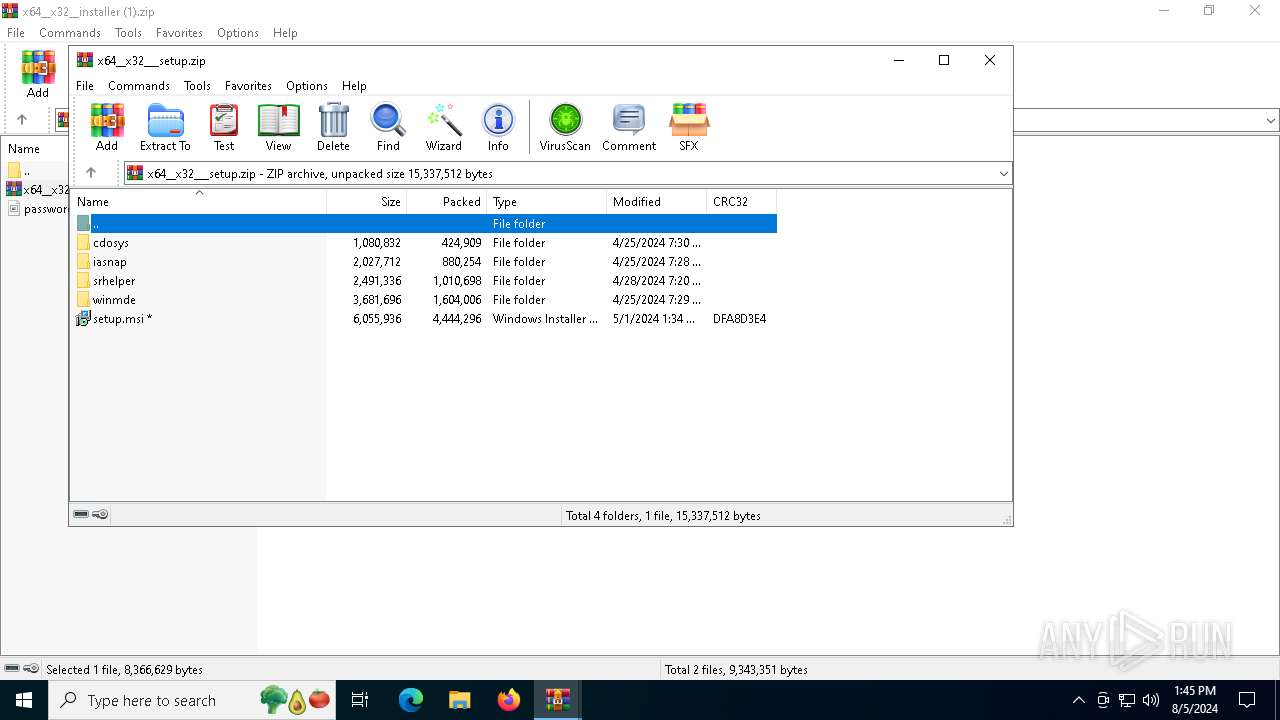
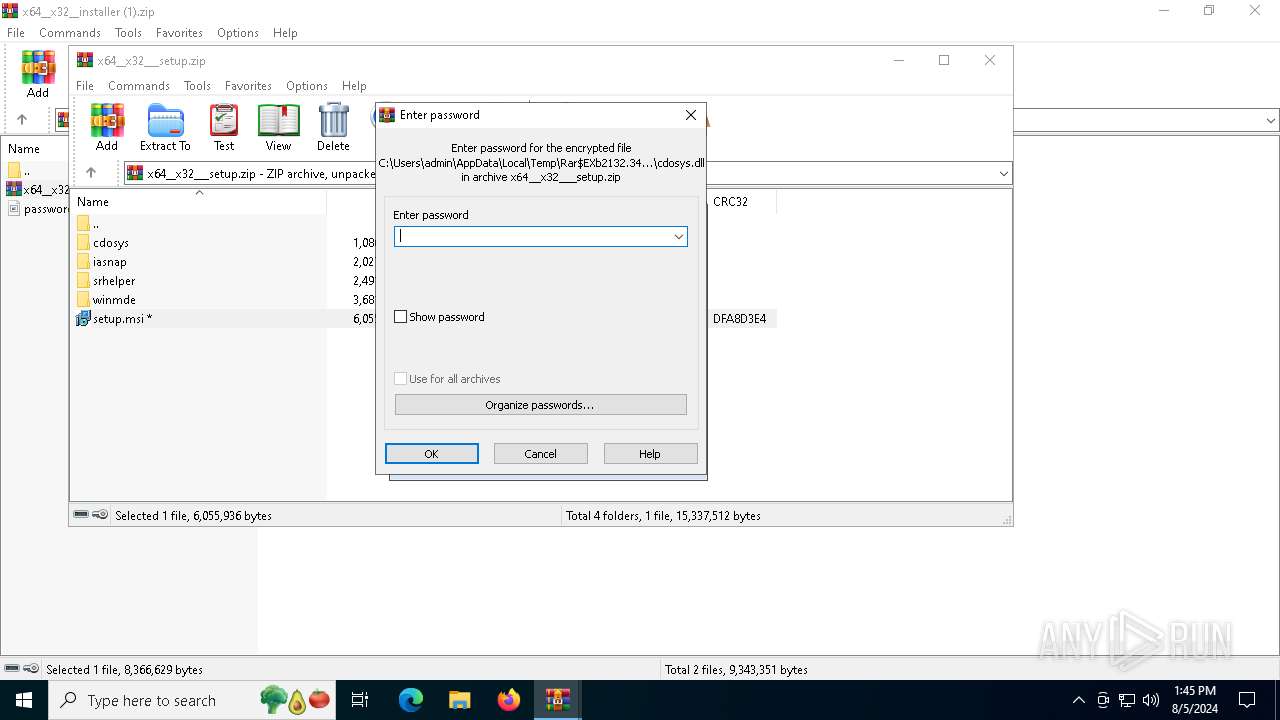
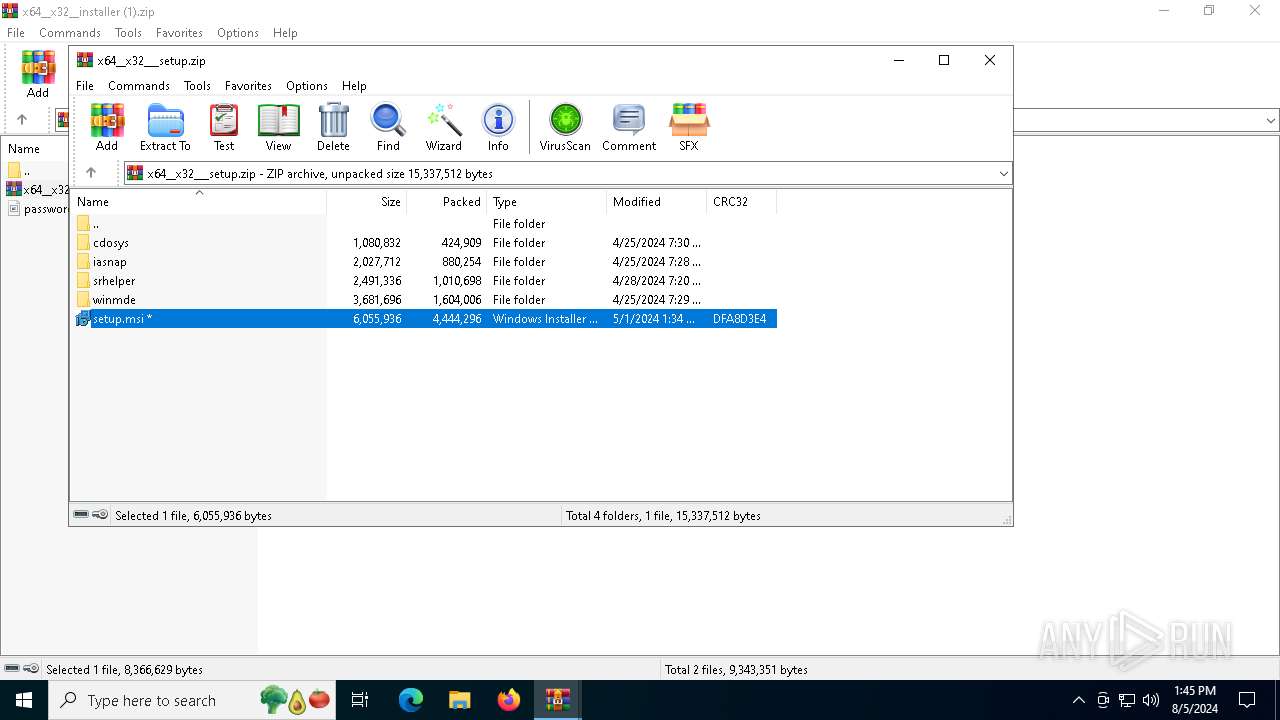
| 2132 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa6388.34664\x64__x32___setup.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4004 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssBFA5.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msiBFA2.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scrBFA3.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scrBFA4.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
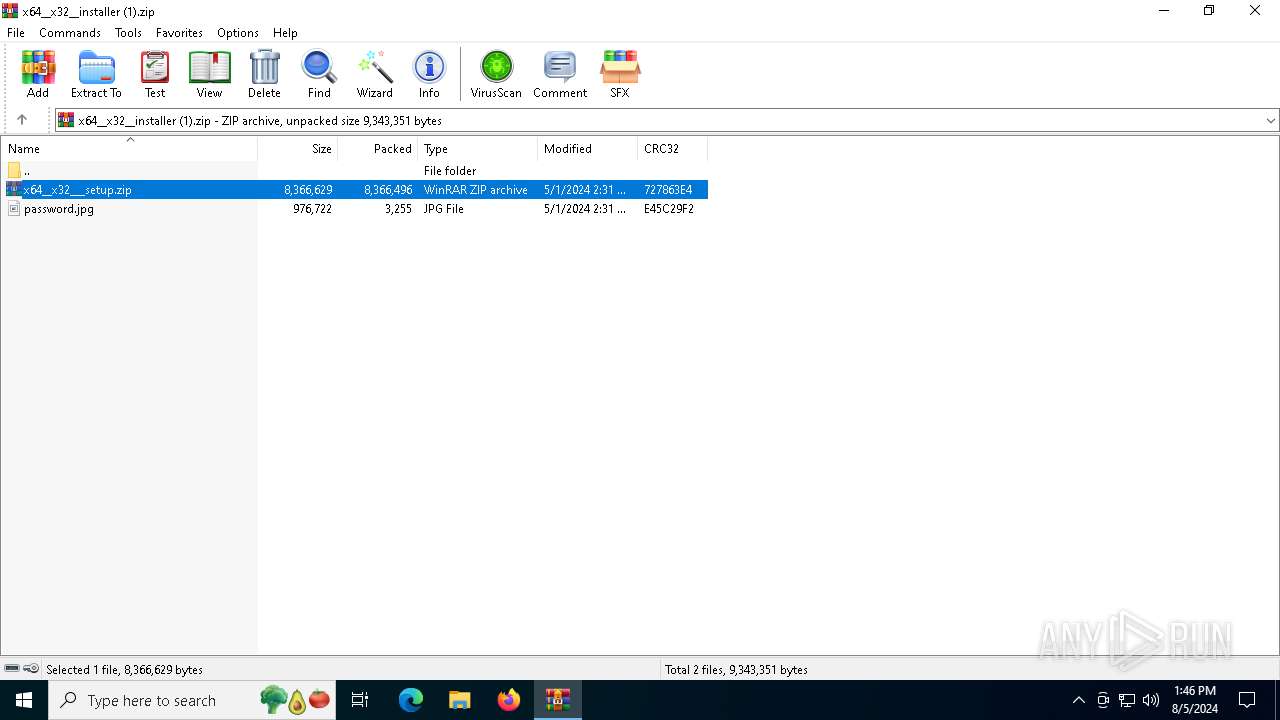
| 6388 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\x64__x32__installer (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7064 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7128 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rar$EXb2132.34912\setup.msi" | C:\Windows\System32\msiexec.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 095
Read events
20 890
Write events
196
Delete events
9
Modification events
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\x64__x32__installer (1).zip | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
44
Suspicious files
12
Text files
25
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2132.34912\setup.msi | — | |
MD5:— | SHA256:— | |||
| 7064 | msiexec.exe | C:\Windows\Installer\ebc27.msi | — | |
MD5:— | SHA256:— | |||
| 1664 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msiBFA2.txt | — | |
MD5:— | SHA256:— | |||
| 1664 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scrBFA3.ps1 | — | |
MD5:— | SHA256:— | |||
| 1664 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scrBFA4.txt | — | |
MD5:— | SHA256:— | |||
| 1664 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssBFA5.ps1 | — | |
MD5:— | SHA256:— | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6388.34664\x64__x32___setup.zip | compressed | |
MD5:B0B4C4963C55CCC44AAF4AC9CF891662 | SHA256:19C4AA78AA2D0B62A15DC3DFB6B289B8DAC22793DDCA068D568736B14258B659 | |||
| 2132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2132.34912\srhelper\srhelper.dll | executable | |
MD5:EF1C527CD3F8FD9DED04B9AC0E4F7C9E | SHA256:1A7B3DC6503FEC4A080DAE7AE59B4A2BEB2766326D148653C5E3DC3E05113415 | |||
| 2132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2132.34912\srhelper\PortableDeviceApi.dll | executable | |
MD5:E20900A32781F84278E98273C9318CEA | SHA256:153D94801C538EB820D2F721B80FB93C054E4A143B8544AD3EF6AC2EA794C1AA | |||
| 2132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2132.34912\srhelper\sppobjs.dll | executable | |
MD5:BF28019CD8187341479BBB4EFECC45D6 | SHA256:6B051B1D3E3E74201A97FED167AF3A10409237A275EFE514FDAD5EF4BFEA03F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
52
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6752 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6800 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2248 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4664 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4664 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 95.100.146.35:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
640 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |