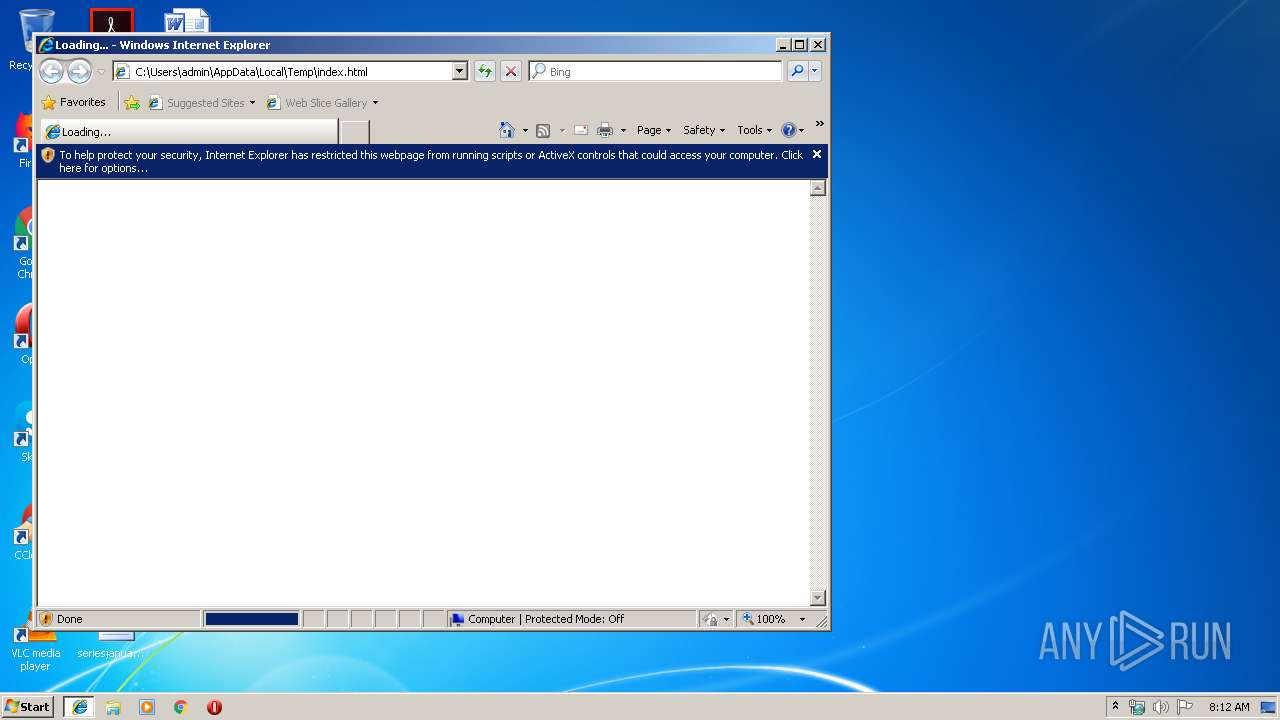
| download: | index.html |
| Full analysis: | https://app.any.run/tasks/12adc47b-699f-4498-bbcf-f00fc6bfc4cc |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 07:12:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with no line terminators |
| MD5: | 913E4B781503776F2142CED1E30CBDAB |
| SHA1: | 9E0A5C8792501856CB8E1A5F07F003D171D4A8BD |
| SHA256: | 53AAF4CAB735D16233720DDA7CDF5F006D464AC79CD23F266CED3D9F75F63268 |
| SSDEEP: | 12:kxvsCk9cE3MxB/X8KnbJZ9HUNkEI6bDYI:kbxxB/sKBHU0vI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 3544)
Reads Internet Cache Settings
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 3604)
Reads internet explorer settings
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 3604)
Application launched itself
- iexplore.exe (PID: 3544)
Creates files in the user directory
- iexplore.exe (PID: 3604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3544 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3604 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3544 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3972 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3544 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
566
Read events
463
Write events
101
Delete events
2
Modification events
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {DC0F0437-DAAC-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30709000400130007000C0026005702 | |||
Executable files
0
Suspicious files
1
Text files
30
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3544 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\IUQ2TTPG\ww1_yotube_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3544 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA5A42217E454AE0B.TMP | — | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019091920190920\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\D7JMX0LI\ww1_yotube_com[1].htm | html | |
MD5:— | SHA256:— | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\IUQ2TTPG\ww1_yotube_com[1].htm | html | |
MD5:— | SHA256:— | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\T2GYTV2H\min[1].js | text | |
MD5:— | SHA256:— | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
15
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3604 | iexplore.exe | GET | 200 | 2.16.186.64:80 | http://i2.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
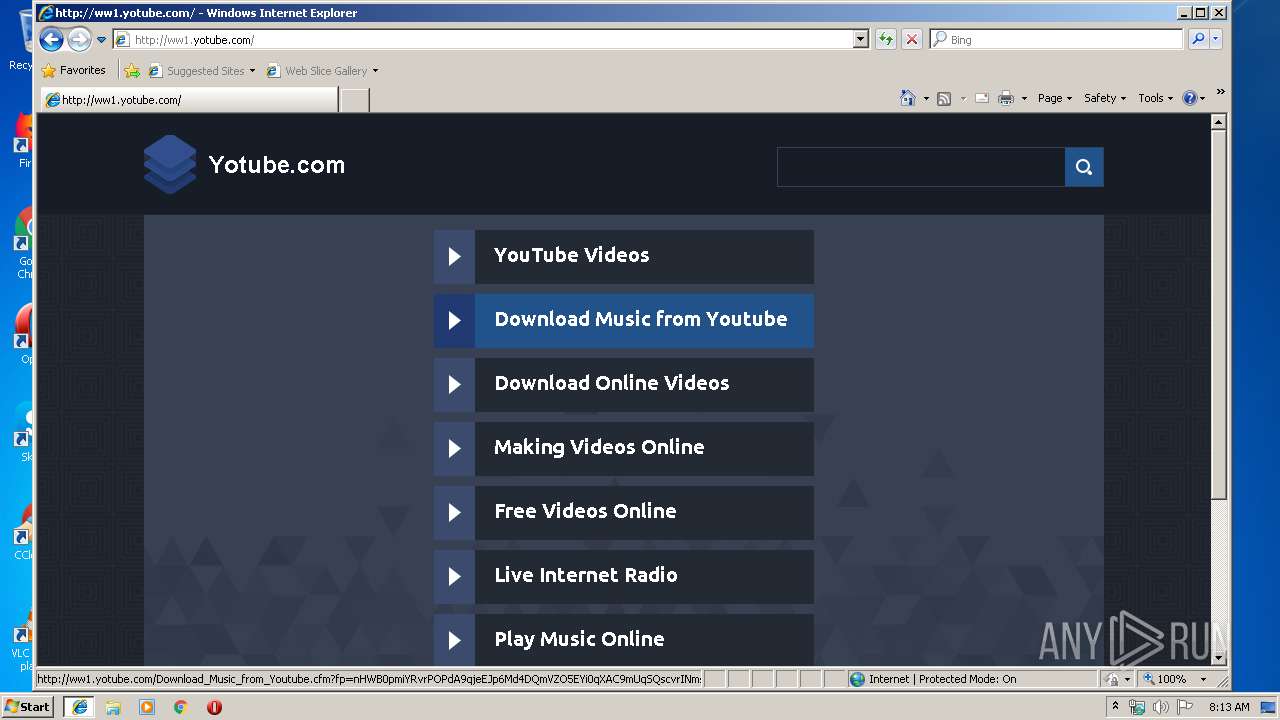
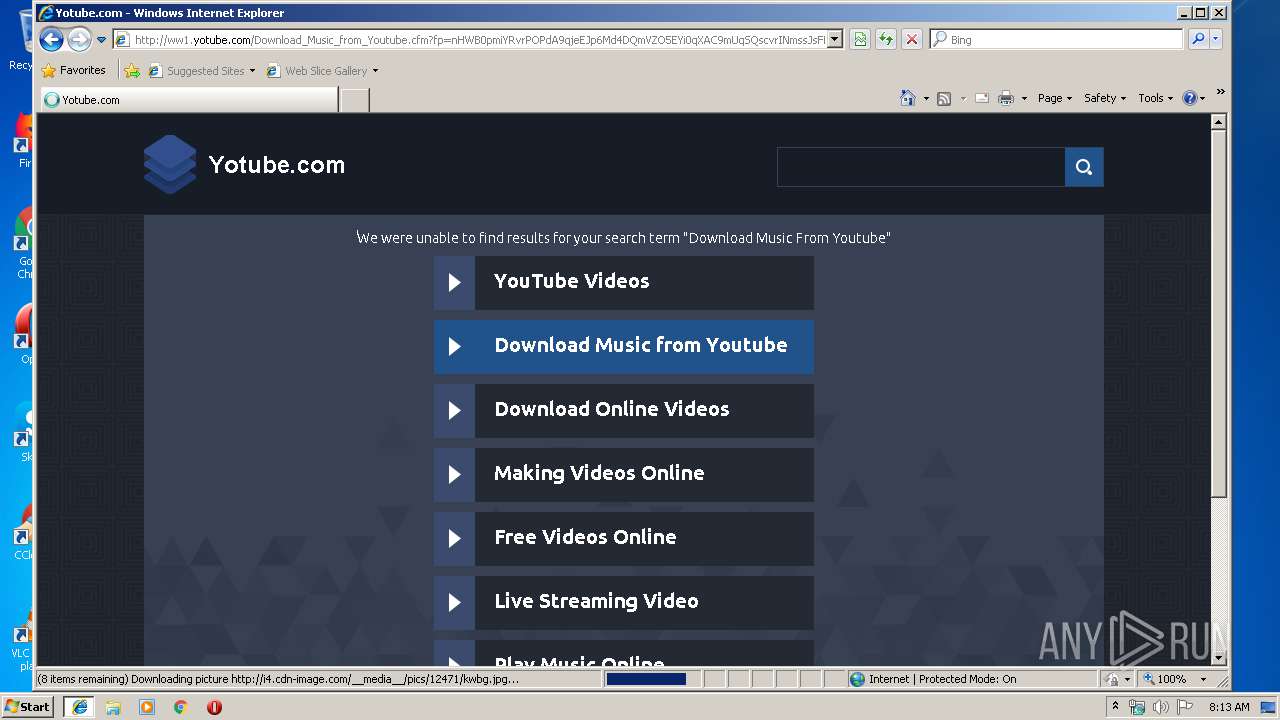
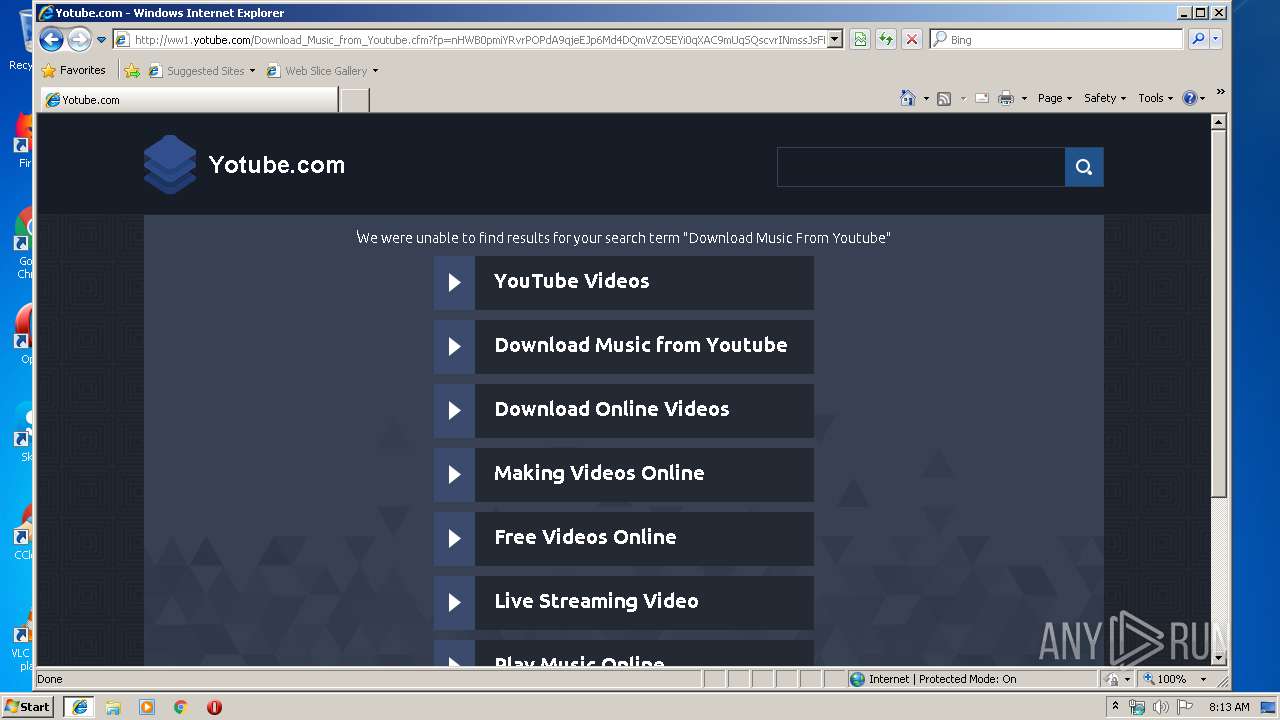
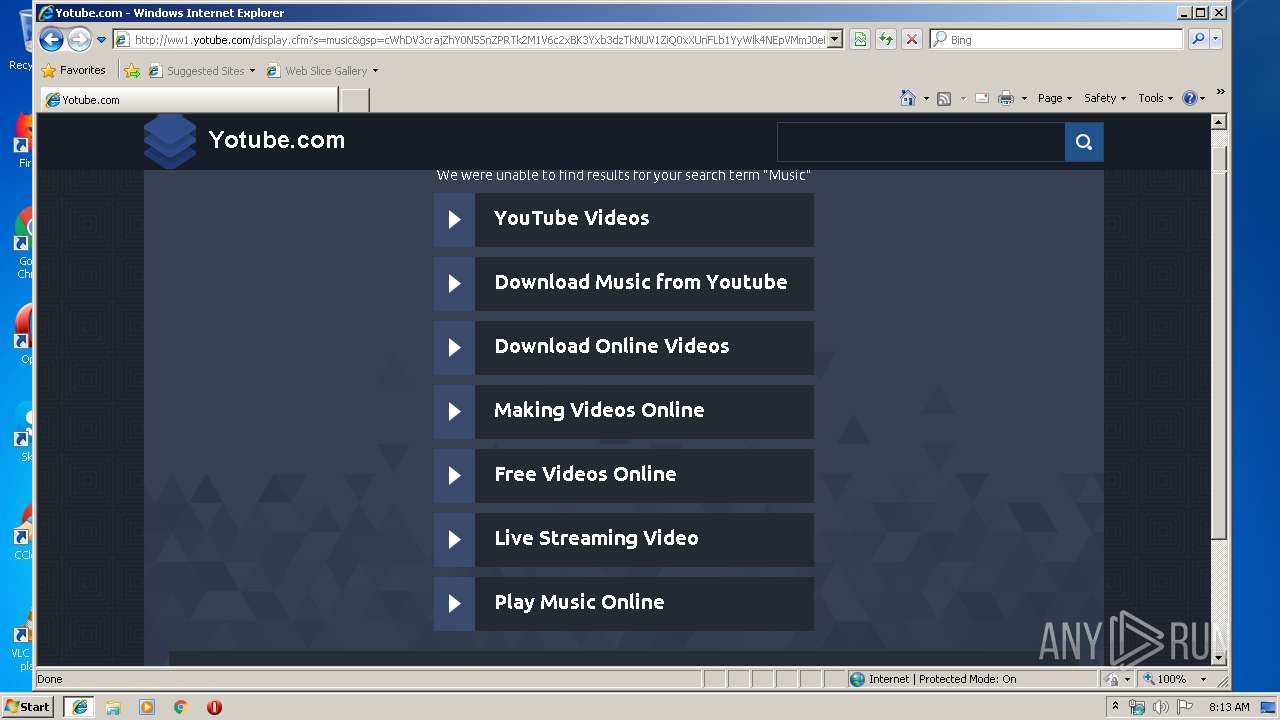
3604 | iexplore.exe | GET | 200 | 208.91.196.145:80 | http://ww1.yotube.com/Download_Music_from_Youtube.cfm?fp=nHWB0pmiYRvrPOPdA9qjeEJp6Md4DQmVZO5EYi0qXAC9mUqSQscvrINmssJsFMQY3JP94q0jjwSW8GZV0Sfc7fbIAMxU%2BrnL9waQjRJ7c3Da6MeTHEY7MDejj6aM4dRjTJuOCgnDy39t7PR7dkDx1w0r0%2BwU6ykLP9Ve9K5WPu9cA3axaV2a1jZnyVerL%2BY3uxXMFYHGiPYx11O%2BalzTjg%3D%3D&maxads=0&kld=1040&yprpnd=nk4IJq0HodZ6ZMzknNX0%2Biv%2FQFyxdGEiFtw3EM8WAvI%3D&prvtof=vzu%2BwqGvUoo2djOXmx4cHnvjS8v%2BvKtDM0pXzD5ZII0%3D&&&kt=320&&kbc=136983&ki=74402451&ktd=283674000162816&kld=1040&kp=2&bd=1%23720%231280%231%230%230%230 | VG | html | 5.11 Kb | malicious |
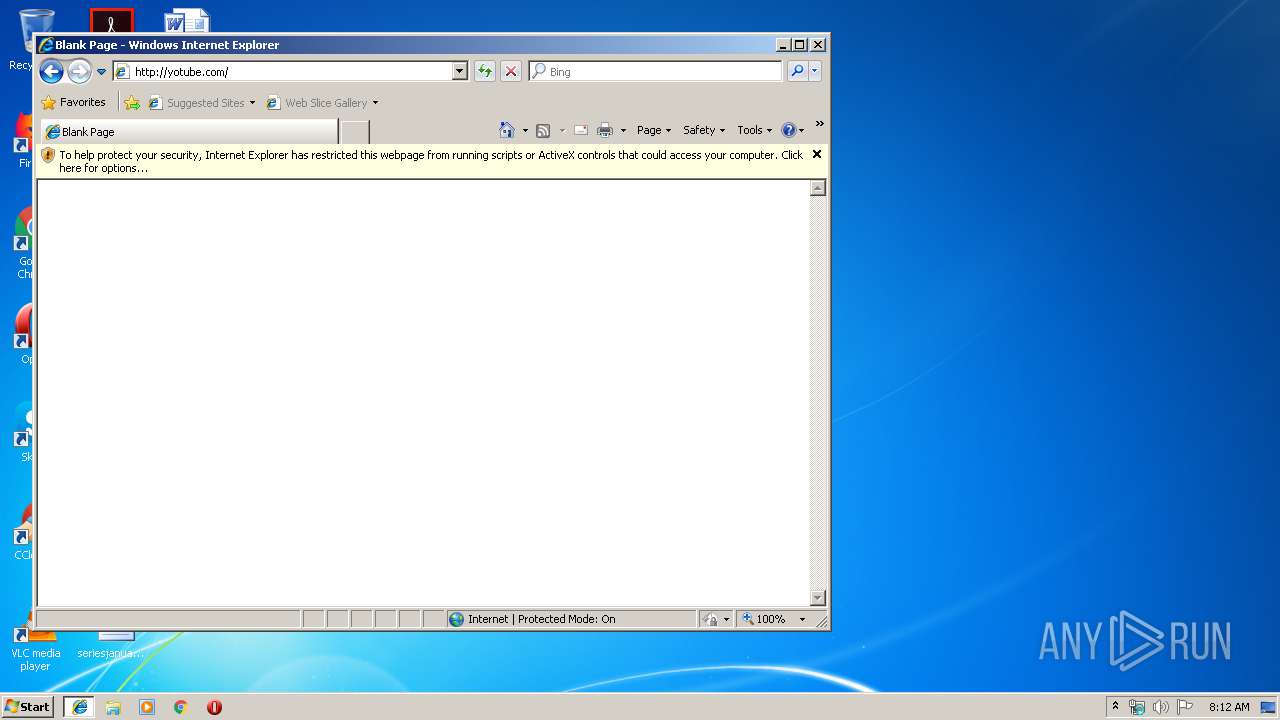
3604 | iexplore.exe | GET | 302 | 200.63.47.3:80 | http://yotube.com/ | PA | text | 11 b | malicious |
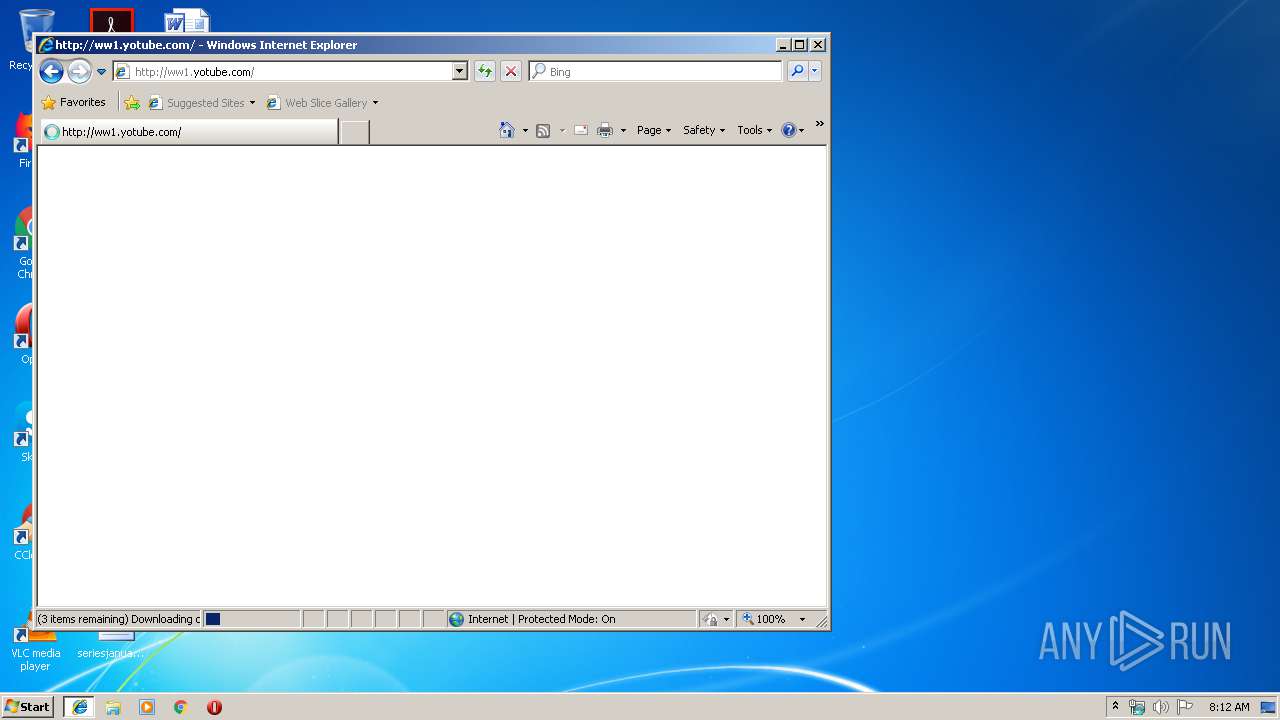
3604 | iexplore.exe | GET | 200 | 208.91.196.145:80 | http://ww1.yotube.com/px.js?ch=2 | VG | text | 346 b | malicious |
3604 | iexplore.exe | GET | 200 | 2.16.186.64:80 | http://i1.cdn-image.com/__media__/pics/12471/bodybg.png | unknown | image | 94.9 Kb | whitelisted |
3604 | iexplore.exe | GET | — | 2.16.186.64:80 | http://i2.cdn-image.com/__media__/pics/12471/libgh.png | unknown | — | — | whitelisted |
3604 | iexplore.exe | GET | 200 | 2.16.186.106:80 | http://i4.cdn-image.com/__media__/pics/12471/kwbg.jpg | unknown | image | 36.3 Kb | whitelisted |
3604 | iexplore.exe | GET | 200 | 2.16.186.106:80 | http://i4.cdn-image.com/__media__/pics/12471/libg.png | unknown | image | 1.07 Kb | whitelisted |
3544 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
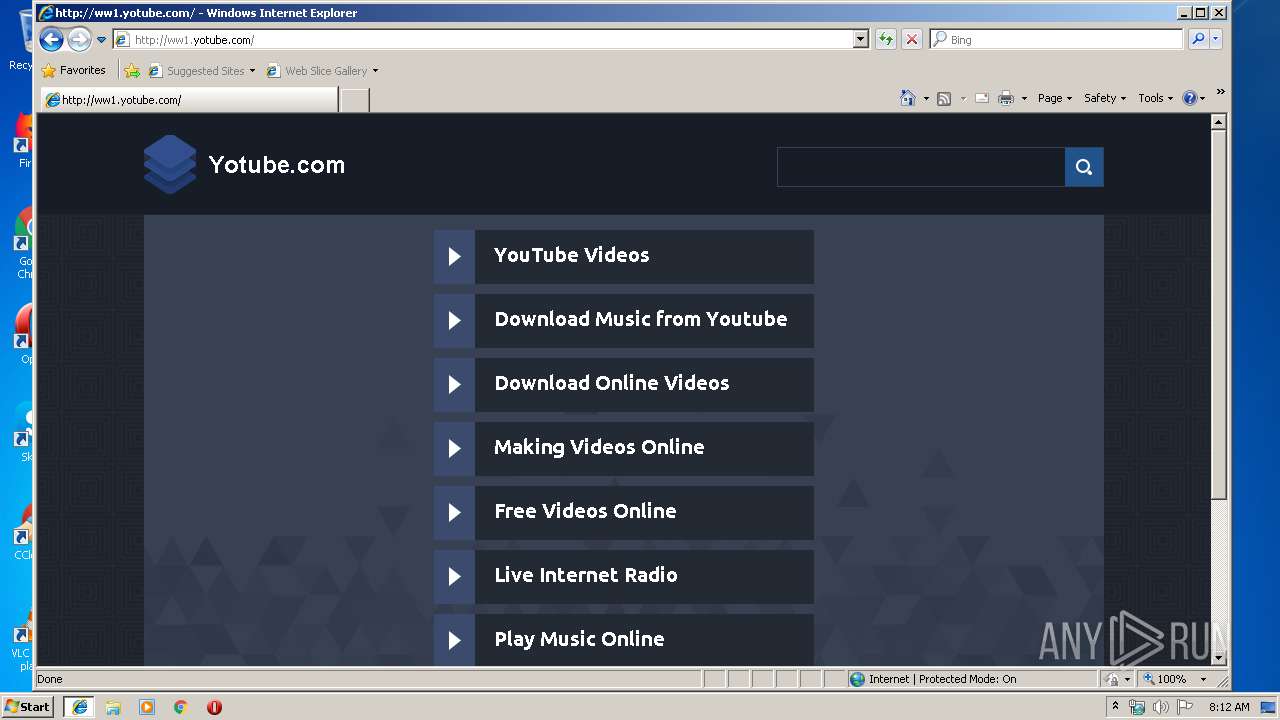
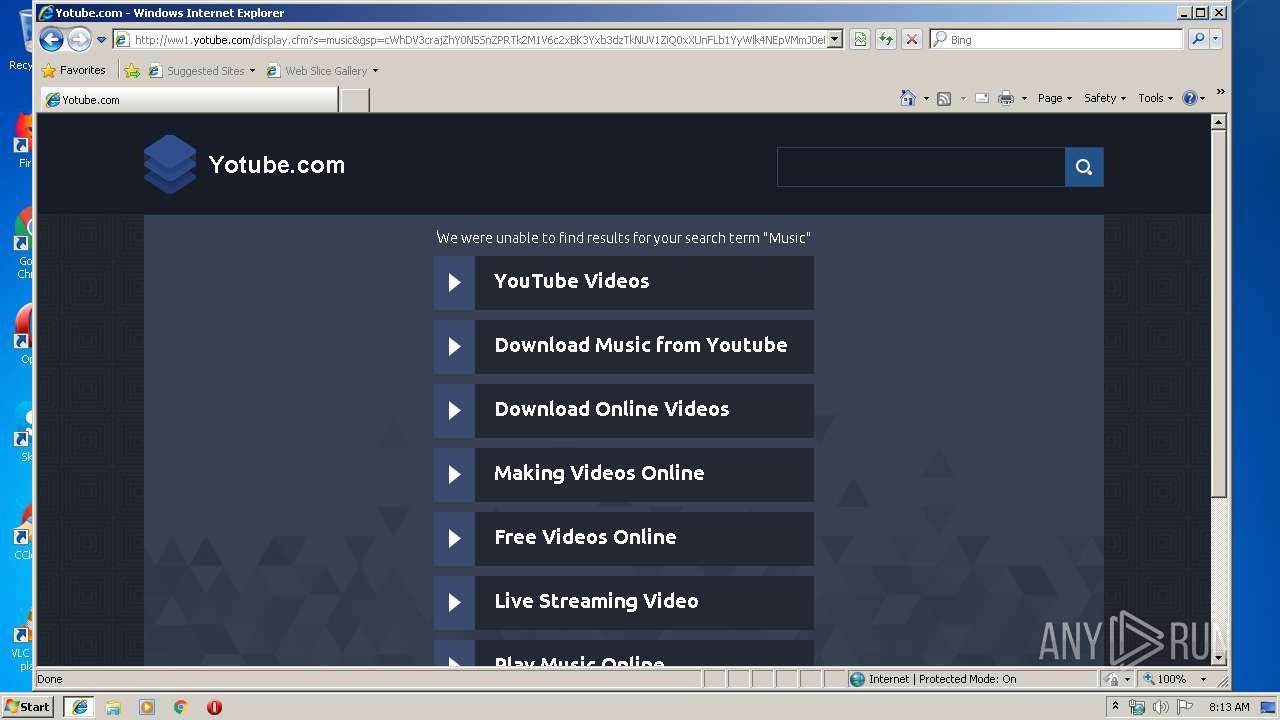
3604 | iexplore.exe | GET | 200 | 208.91.196.145:80 | http://ww1.yotube.com/ | VG | html | 1.05 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3544 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3604 | iexplore.exe | 208.91.196.145:80 | ww1.yotube.com | Confluence Networks Inc | VG | malicious |
3604 | iexplore.exe | 2.16.186.106:80 | i2.cdn-image.com | Akamai International B.V. | — | whitelisted |
3604 | iexplore.exe | 200.63.47.3:80 | yotube.com | Panamaserver.com | PA | malicious |
3604 | iexplore.exe | 2.16.186.64:80 | i2.cdn-image.com | Akamai International B.V. | — | whitelisted |
3544 | iexplore.exe | 208.91.196.145:80 | ww1.yotube.com | Confluence Networks Inc | VG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
yotube.com |
| malicious |
ww1.yotube.com |
| malicious |
i2.cdn-image.com |
| whitelisted |
i1.cdn-image.com |
| whitelisted |
i3.cdn-image.com |
| whitelisted |
i4.cdn-image.com |
| whitelisted |