| File name: | Folder2Iso31.exe |
| Full analysis: | https://app.any.run/tasks/b11c2fed-7a5d-4214-bcfc-a0a86a50f5ec |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2019, 13:44:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DE8D912532E77D30DBB0932C49FD0981 |
| SHA1: | 93662EE7417AD23E3A4E5CB3BD3091F805DCB075 |
| SHA256: | 537800806FCA71B3D65F412DAE4AFFC1B846DDD69FA68145235F460AFEFD1AE2 |
| SSDEEP: | 49152:6UeOMAV94AHcOwRnmzesWYB5xV/jqzNi7rvGSBg1vhv2hCKK2oQ:6G5V94AHoRmzeNYBxEi2SBg15uhpKs |
MALICIOUS
Application was dropped or rewritten from another process
- Folder2Iso.exe (PID: 3884)
- mkisofs.exe (PID: 2864)
Detects Cygwin installation
- Folder2Iso.exe (PID: 3884)
Loads dropped or rewritten executable
- mkisofs.exe (PID: 2864)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Folder2Iso.exe (PID: 3884)
Executable content was dropped or overwritten
- Folder2Iso31.exe (PID: 3004)
- Folder2Iso.exe (PID: 3884)
Reads Internet Cache Settings
- Folder2Iso.exe (PID: 3884)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 17:27:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 127488 |
| InitializedDataSize: | 51200 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d262 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.20.0.0 |
| ProductVersionNumber: | 9.20.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
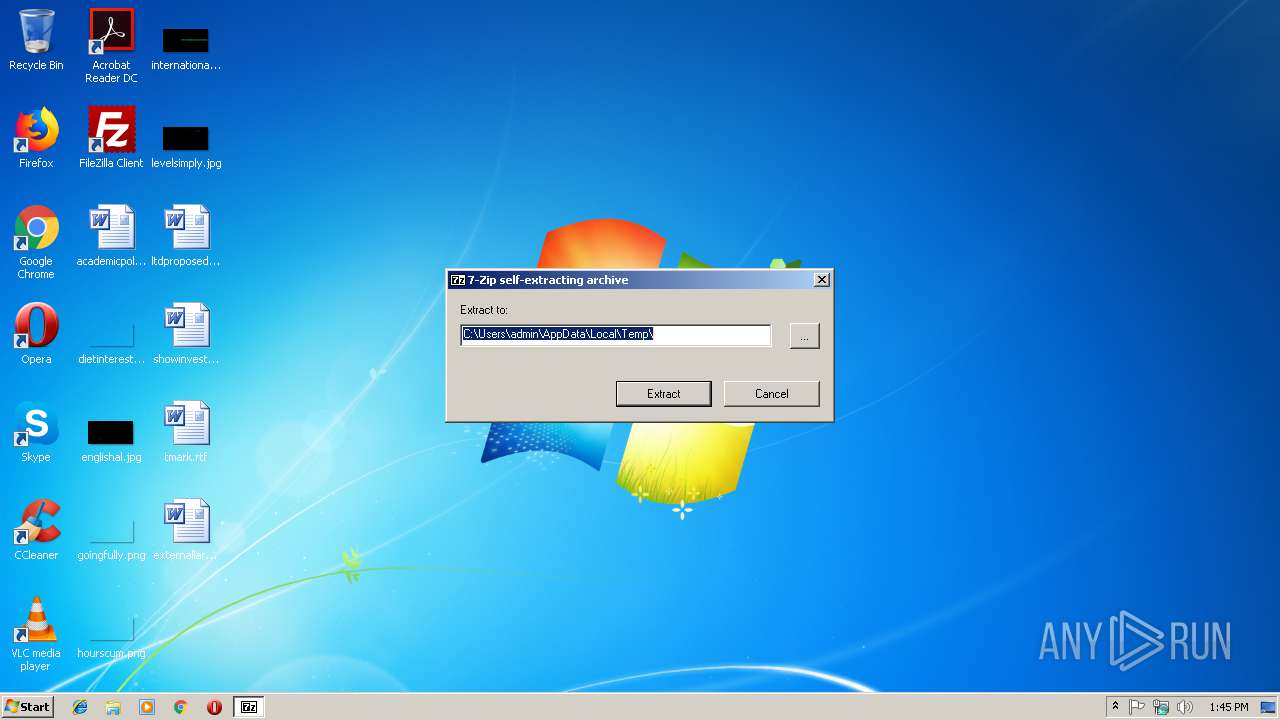
| FileDescription: | 7z SFX |
| FileVersion: | 9.2 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFileName: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2010 16:27:33 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z SFX |
| FileVersion: | 9.20 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFilename: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Nov-2010 16:27:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F01A | 0x0001F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59059 |
.rdata | 0x00021000 | 0x00005A5C | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.16805 |
.data | 0x00027000 | 0x00004D98 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.10058 |
.sxdata | 0x0002C000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0002D000 | 0x00001BC0 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.29296 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41402 | 688 | UNKNOWN | English - United States | RT_VERSION |
2 | 1.68942 | 296 | UNKNOWN | English - United States | RT_ICON |
7 | 3.16186 | 392 | UNKNOWN | English - United States | RT_STRING |
13 | 3.27682 | 756 | UNKNOWN | English - United States | RT_STRING |
14 | 2.58196 | 114 | UNKNOWN | English - United States | RT_STRING |
32 | 1.10136 | 46 | UNKNOWN | English - United States | RT_STRING |
38 | 2.11169 | 72 | UNKNOWN | English - United States | RT_STRING |
44 | 2.76378 | 148 | UNKNOWN | English - United States | RT_STRING |
45 | 1.07875 | 44 | UNKNOWN | English - United States | RT_STRING |
66 | 3.07708 | 244 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
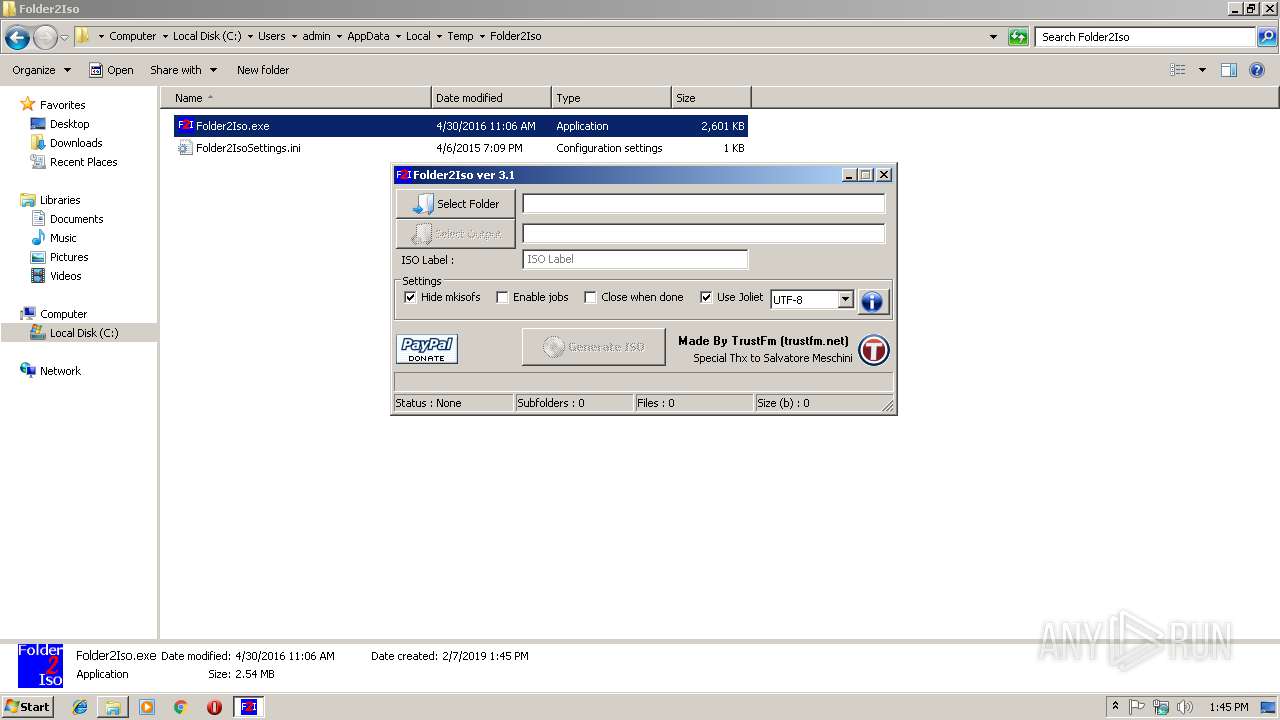
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2260 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
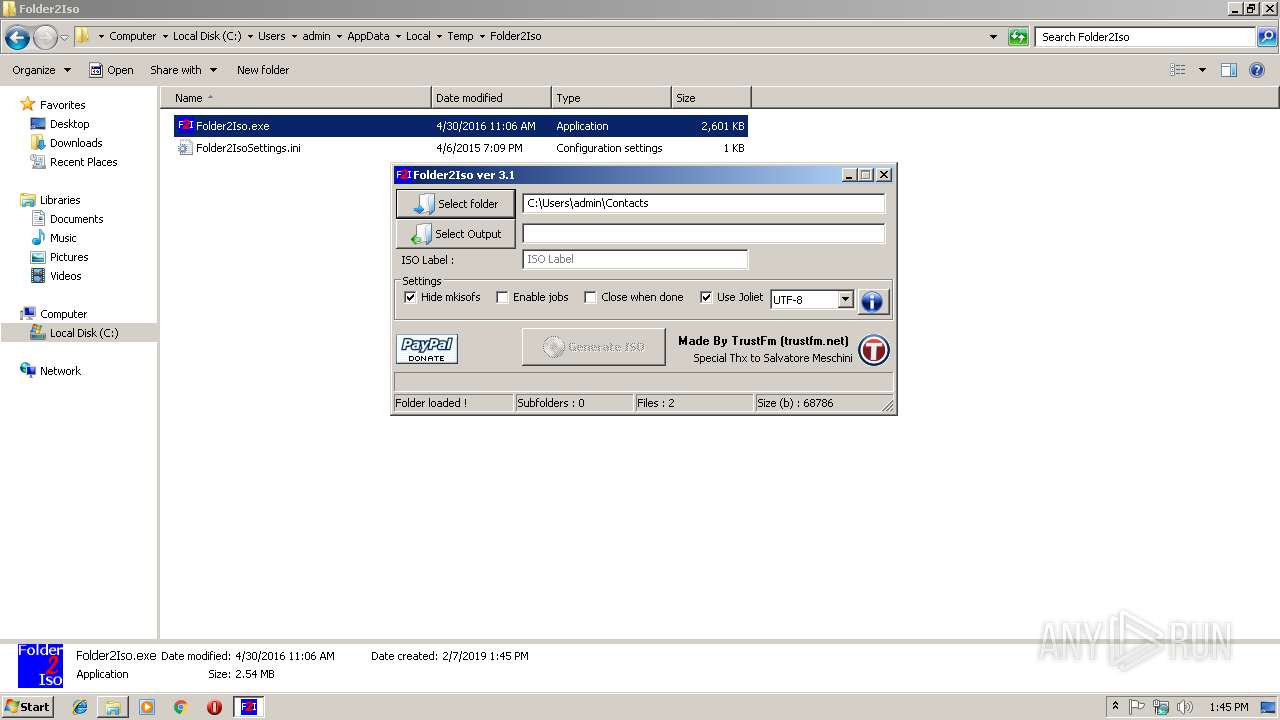
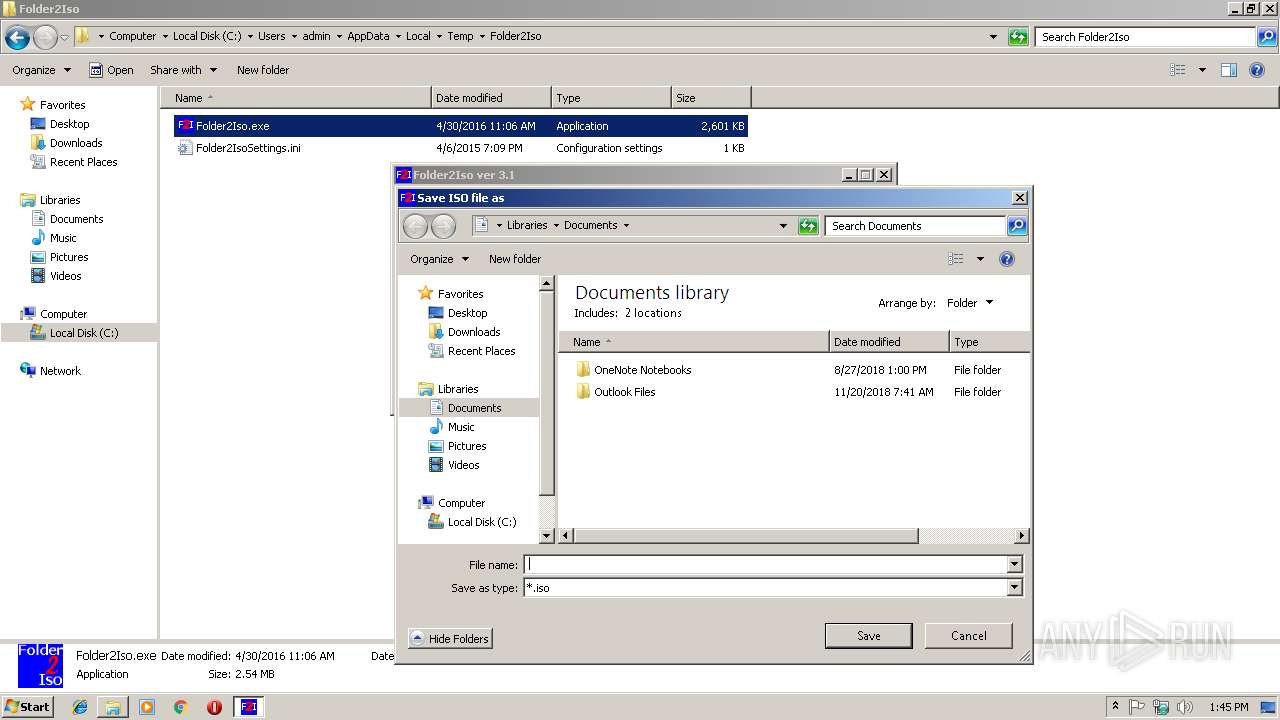
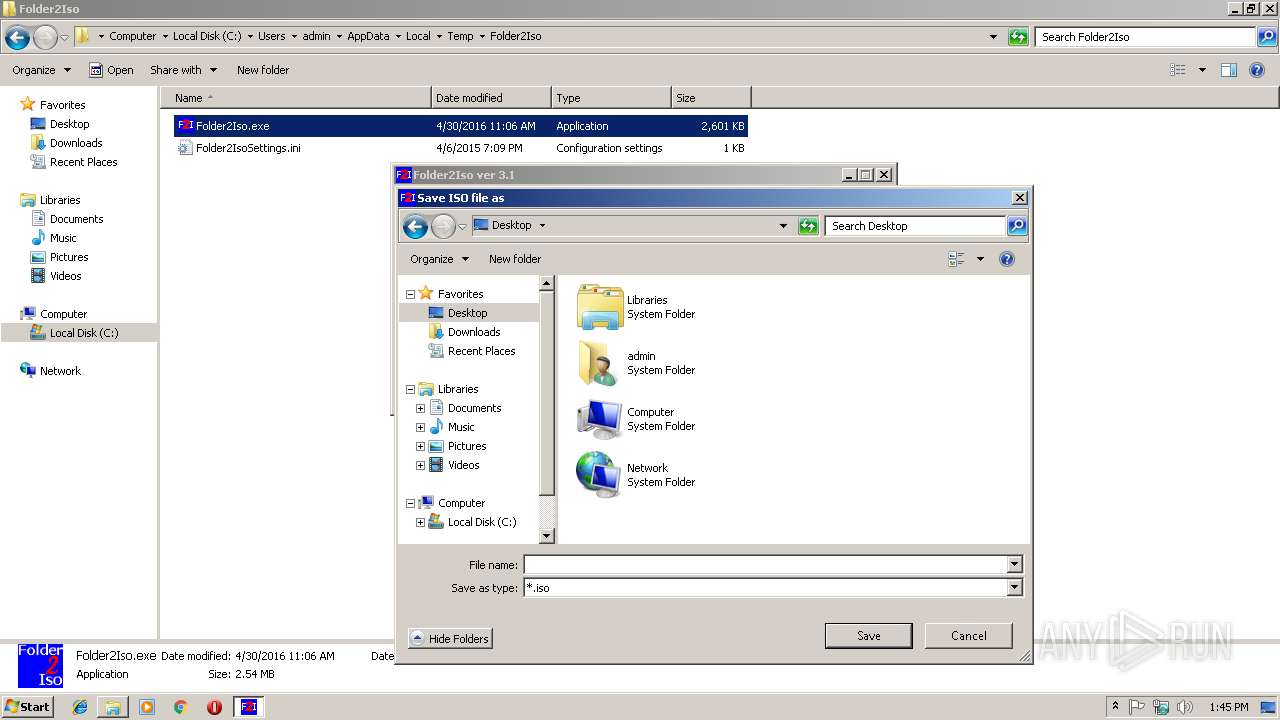
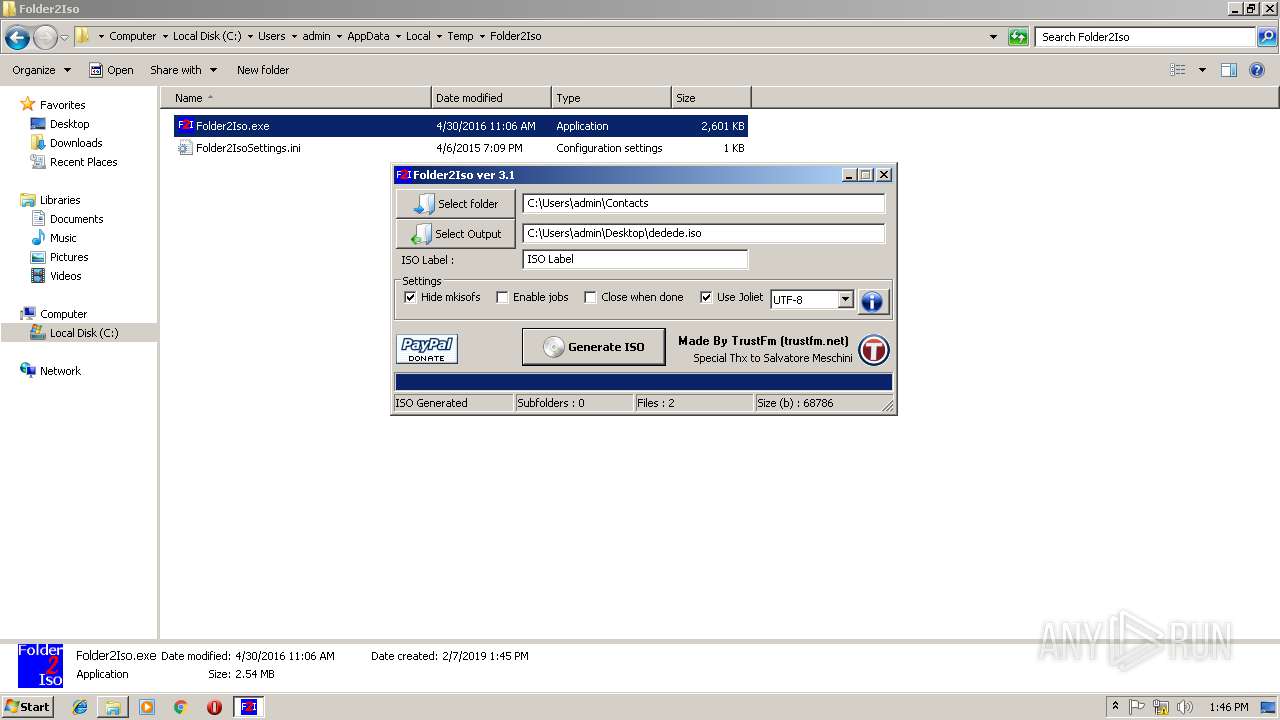
| 2356 | cmd.exe /C ""C:\Users\admin\AppData\Local\Temp\mkisofs.exe" "-J" "-joliet-long" "-jcharset" "UTF-8" "-l" "-r" "-V" "ISO Label" "-o" "C:\Users\admin\Desktop\dedede.iso" "C:\Users\admin\Contacts"" | C:\Windows\system32\cmd.exe | — | Folder2Iso.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2864 | "C:\Users\admin\AppData\Local\Temp\mkisofs.exe" "-J" "-joliet-long" "-jcharset" "UTF-8" "-l" "-r" "-V" "ISO Label" "-o" "C:\Users\admin\Desktop\dedede.iso" "C:\Users\admin\Contacts" | C:\Users\admin\AppData\Local\Temp\mkisofs.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
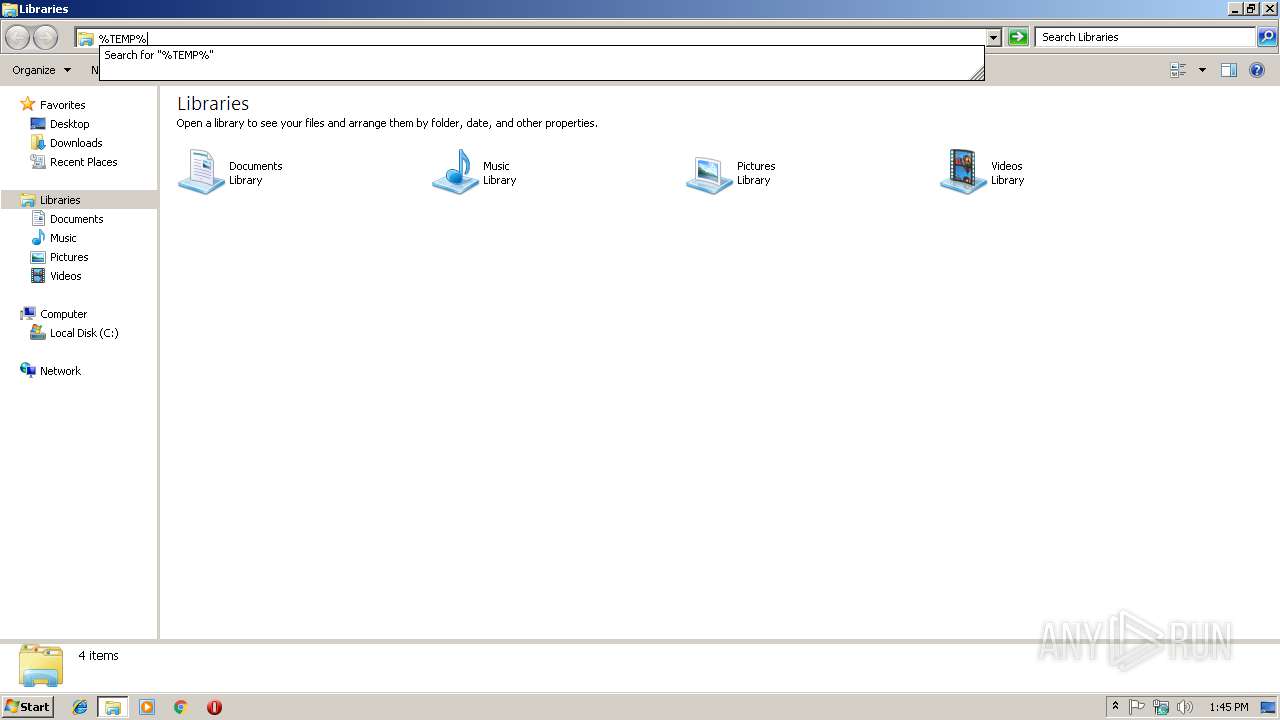
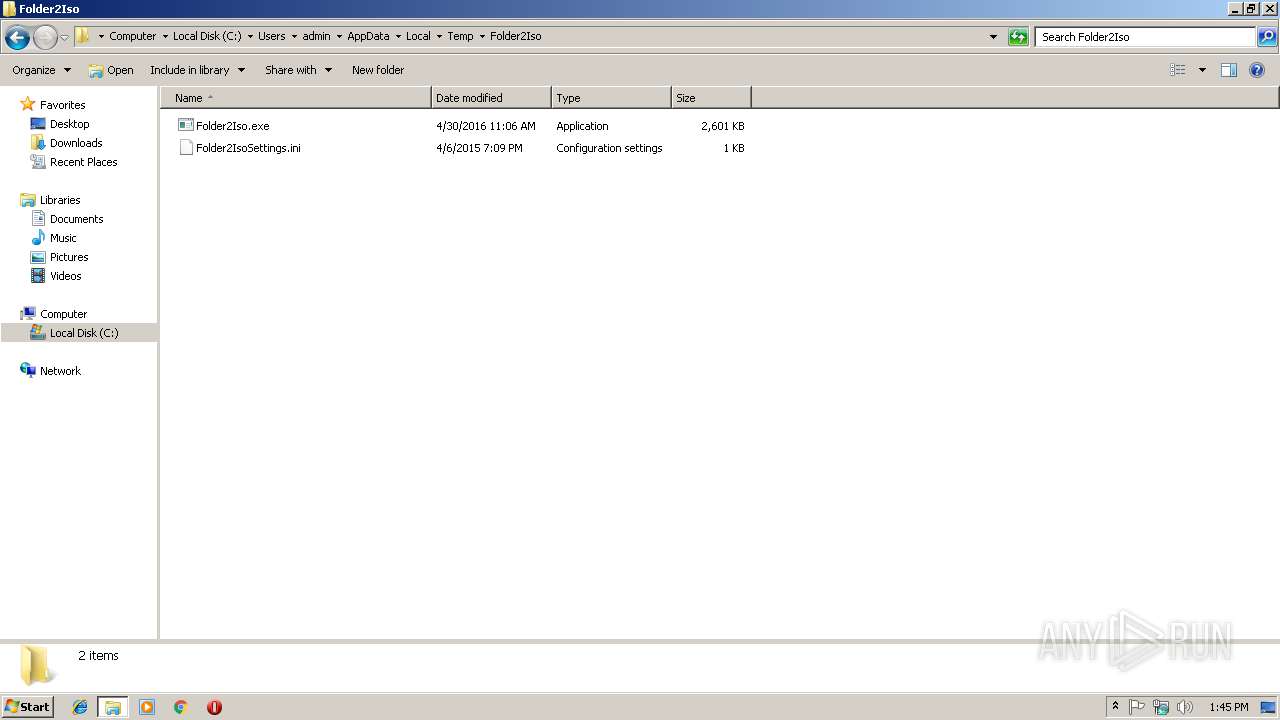
| 3004 | "C:\Users\admin\AppData\Local\Temp\Folder2Iso31.exe" | C:\Users\admin\AppData\Local\Temp\Folder2Iso31.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
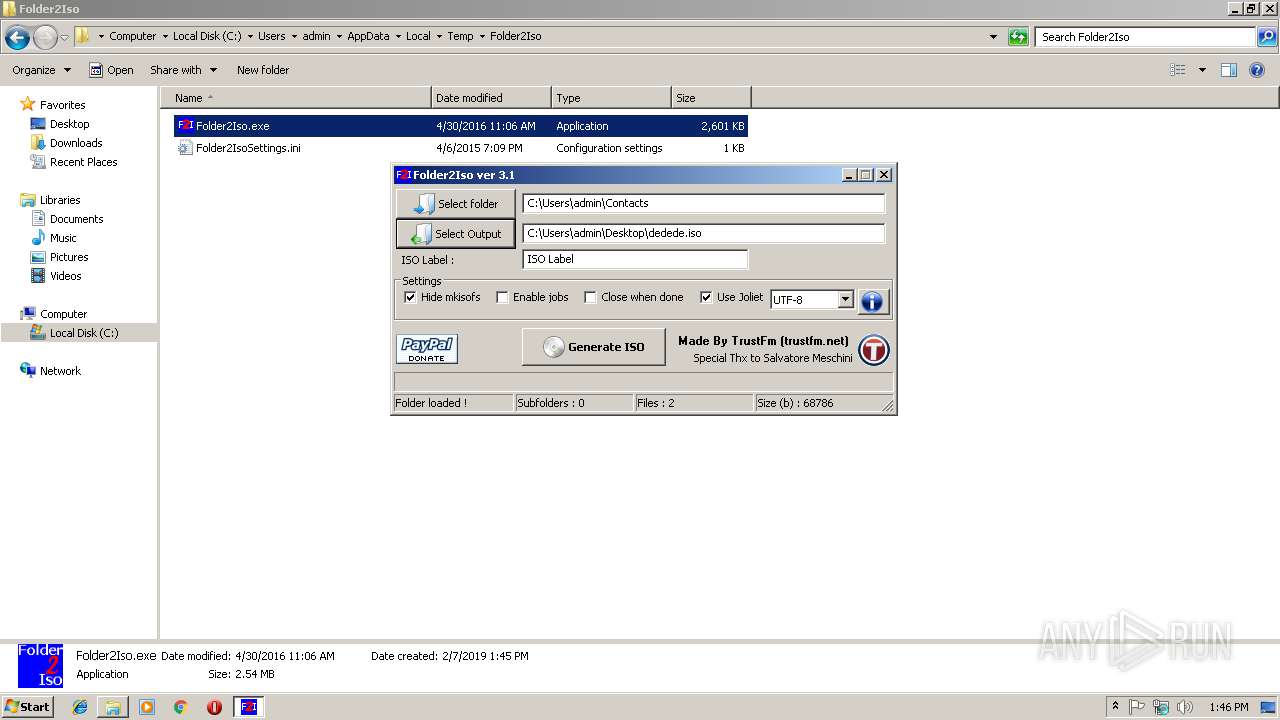
| 3884 | "C:\Users\admin\AppData\Local\Temp\Folder2Iso\Folder2Iso.exe" | C:\Users\admin\AppData\Local\Temp\Folder2Iso\Folder2Iso.exe | explorer.exe | ||||||||||||
User: admin Company: TrustFm Integrity Level: MEDIUM Description: Convert any folder to ISO Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
648
Read events
569
Write events
77
Delete events
2
Modification events
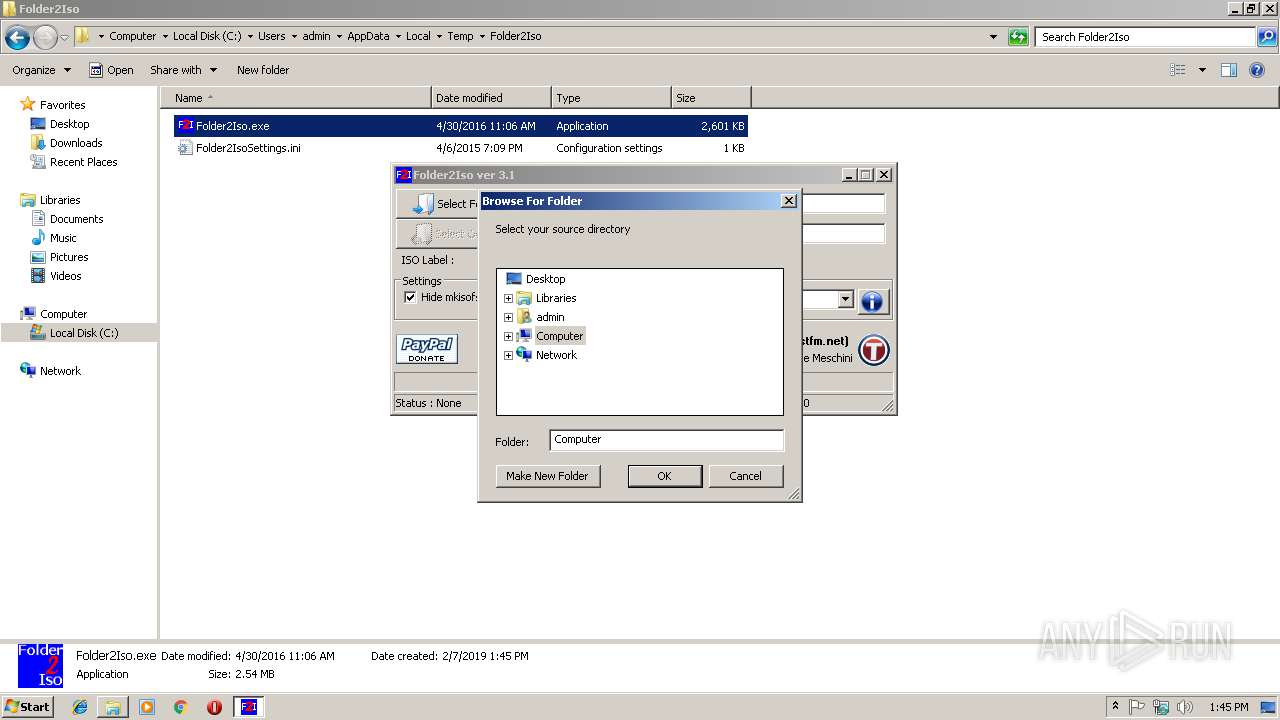
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%CommonProgramFiles%\system\wab32res.dll,-10200 |
Value: Contains Contact files. | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3884) Folder2Iso.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
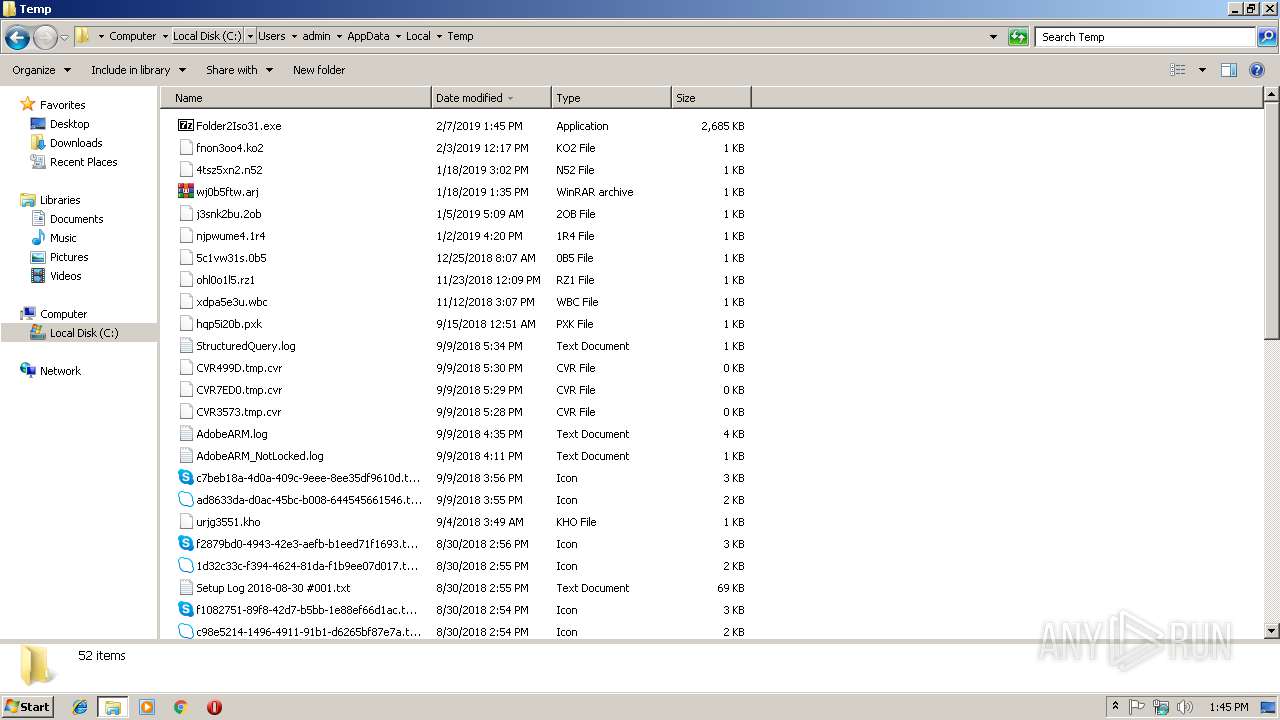
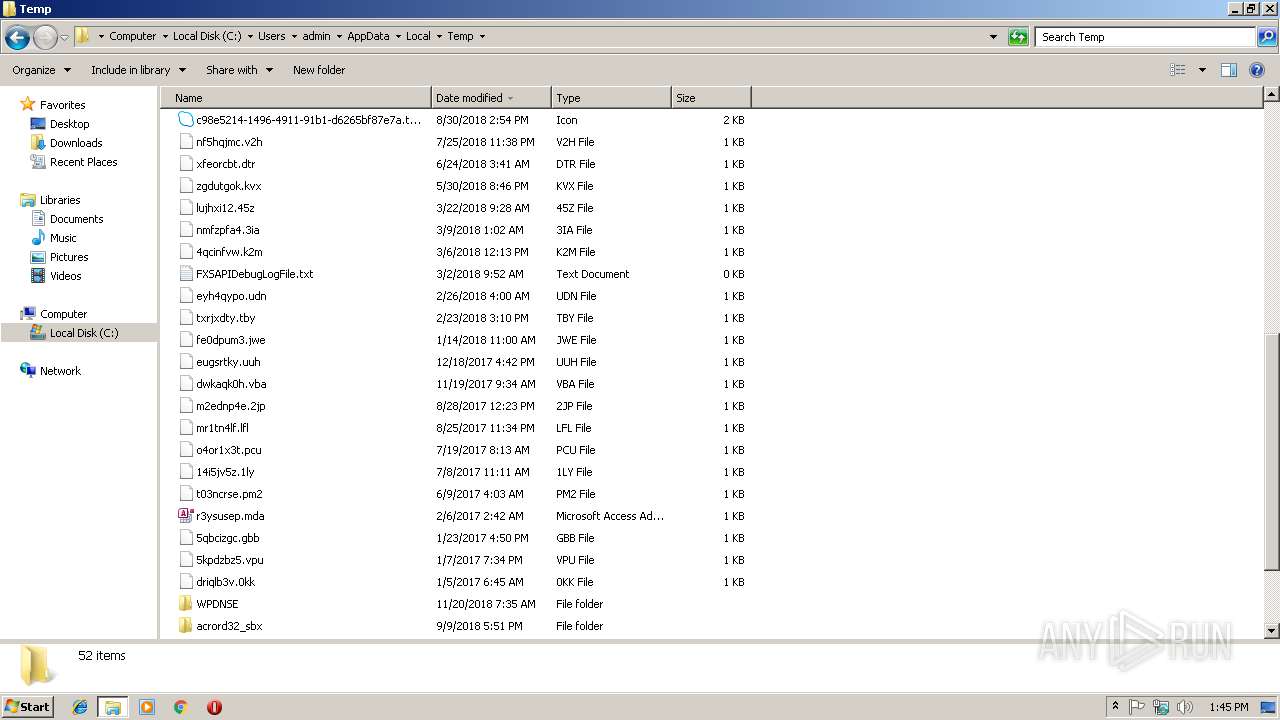
Executable files
6
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | mkisofs.exe | C:\Users\admin\Desktop\dedede.iso | compressed | |
MD5:— | SHA256:— | |||
| 3004 | Folder2Iso31.exe | C:\Users\admin\AppData\Local\Temp\Folder2Iso\Folder2Iso.exe | executable | |
MD5:— | SHA256:— | |||
| 3004 | Folder2Iso31.exe | C:\Users\admin\AppData\Local\Temp\Folder2Iso\Folder2IsoSettings.ini | text | |
MD5:73B77EDCE4D5E08E0CC00232F23D790C | SHA256:5082CE0D013AAA94BC391D0E629C0BDD1BC78321A2D0C70154BA3E1BFDE5F91F | |||
| 3884 | Folder2Iso.exe | C:\Users\admin\AppData\Local\Temp\cygiconv-2.dll | executable | |
MD5:A4459CBEC5BC43987B25435FC177B933 | SHA256:C78ECBA75AF82357E9BB985AB8DCFB9565D32CB374CB975D41383FBB58C2F6FB | |||
| 3884 | Folder2Iso.exe | C:\Users\admin\AppData\Local\Temp\mkisofs.exe | executable | |
MD5:7598261D1E05C1F97106B4F5E9E50CBE | SHA256:09211F1397C7760352E790D82EACF0281BC894343DB12D5A28A90B5A0663DE5A | |||
| 3884 | Folder2Iso.exe | C:\Users\admin\AppData\Local\Temp\cyggcc_s-1.dll | executable | |
MD5:A397DD11A6EB30E22D197B6FE2B126BE | SHA256:CB9324D76DC592FB61D12BF135401A8EF414C3E56CDB52EE388DBD7FFEE46A42 | |||
| 3884 | Folder2Iso.exe | C:\Users\admin\AppData\Local\Temp\cygintl-8.dll | executable | |
MD5:A5BC4683B537E09C124FB72D67A93BFF | SHA256:ED684929C3E23C8674CCEA3EFB81BB2E381691D2B7756F32AA3C11B2740AF165 | |||
| 3884 | Folder2Iso.exe | C:\Users\admin\AppData\Local\Temp\Folder2Iso\Folder2IsoSettings.ini | text | |
MD5:73B77EDCE4D5E08E0CC00232F23D790C | SHA256:5082CE0D013AAA94BC391D0E629C0BDD1BC78321A2D0C70154BA3E1BFDE5F91F | |||
| 3884 | Folder2Iso.exe | C:\Users\admin\AppData\Local\Temp\cygwin1.dll | executable | |
MD5:26864EDDD52804F3E0E260600D90B31C | SHA256:01653BB8B855B08D16044758C1D084CF45104F63B6805ADE4194BDF4F20EA971 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report