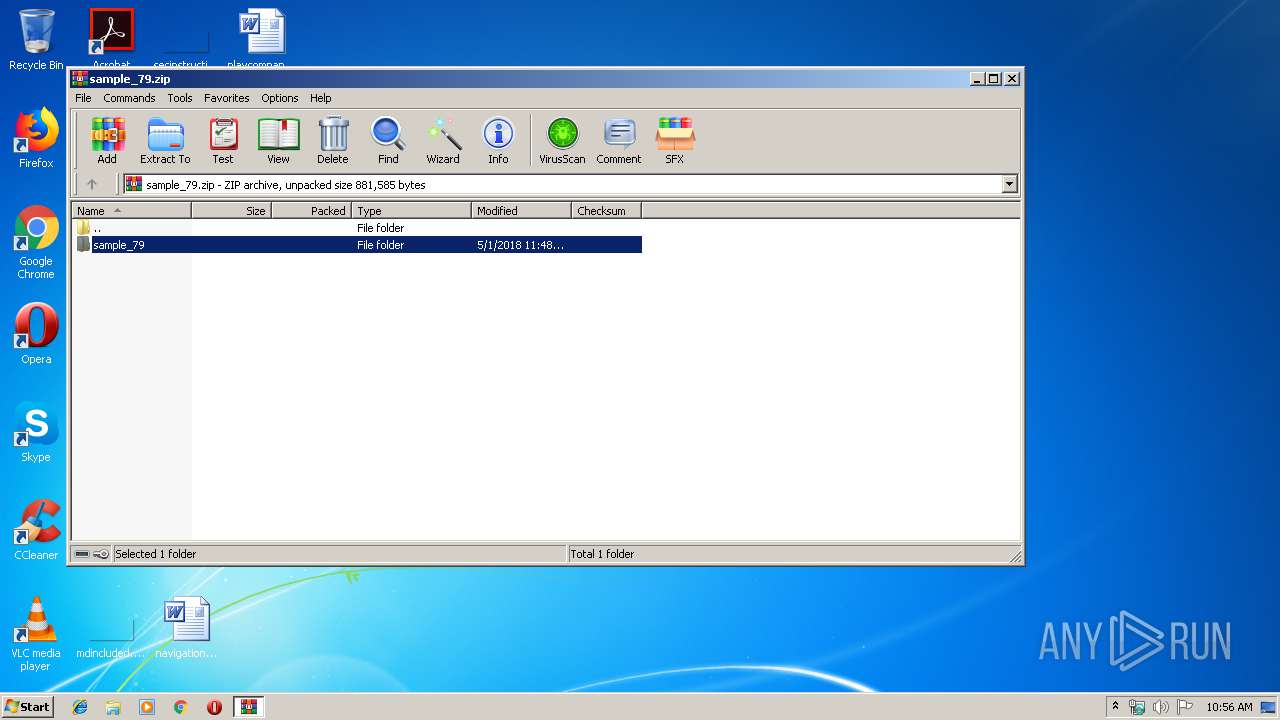
| File name: | sample_79.zip |
| Full analysis: | https://app.any.run/tasks/bf067706-510c-440d-84d2-111a1af73ae0 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 09:56:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E1CDDDFEE642CCBB4E5056C25B5E873C |
| SHA1: | 94246D6989D1C2C269489AACF730C6A68F0C5AD9 |
| SHA256: | 537008470A30DD496127B478B07E3FBDEE179825B338395BC792908584F5D39B |
| SSDEEP: | 12288:LntECo12yiQBNEQnpY2szmNhS1A81P4+I4YEUBePRfCC15OV69:uF1eQBOQnpbszQcAV+KEOelT15OE |
MALICIOUS
Application was dropped or rewritten from another process
- sample_79.exe (PID: 2672)
- sample_79.exe (PID: 2504)
Changes the autorun value in the registry
- sample_79.exe (PID: 2504)
Runs injected code in another process
- sample_79.exe (PID: 2504)
Application was injected by another process
- explorer.exe (PID: 252)
SUSPICIOUS
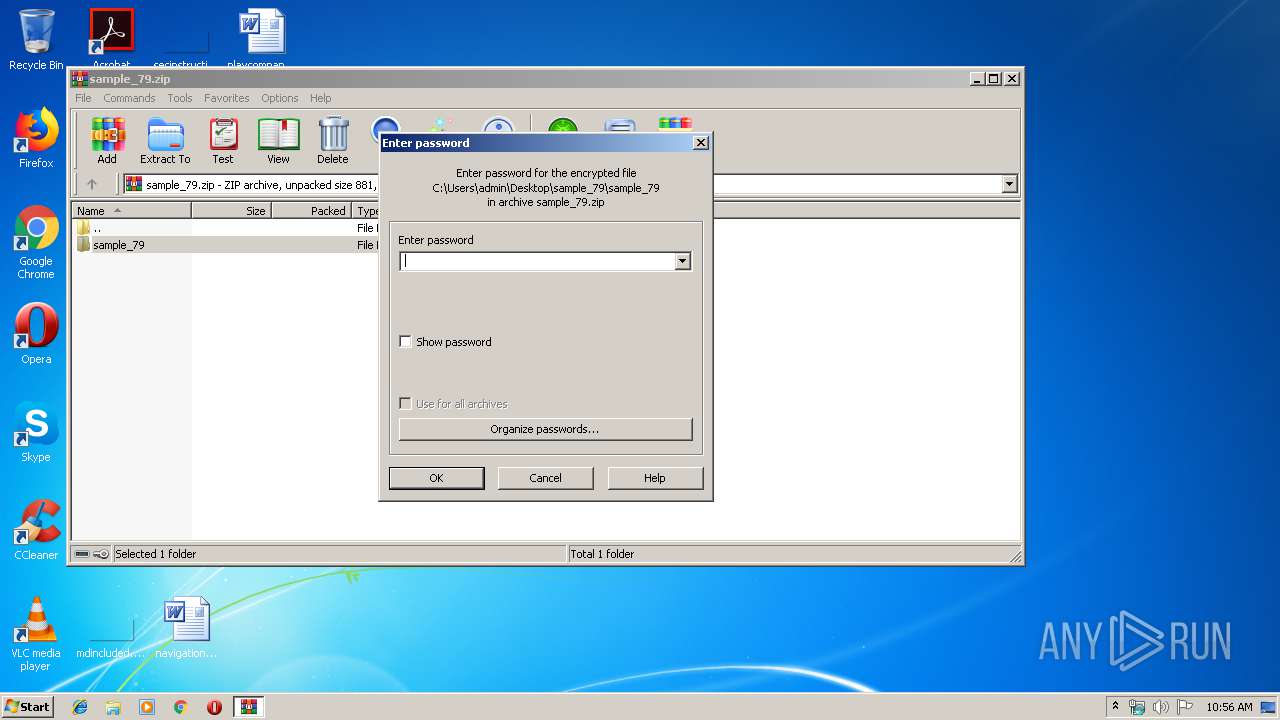
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2824)
- sample_79.exe (PID: 2504)
Application launched itself
- sample_79.exe (PID: 2672)
Starts Internet Explorer
- sample_79.exe (PID: 2504)
INFO
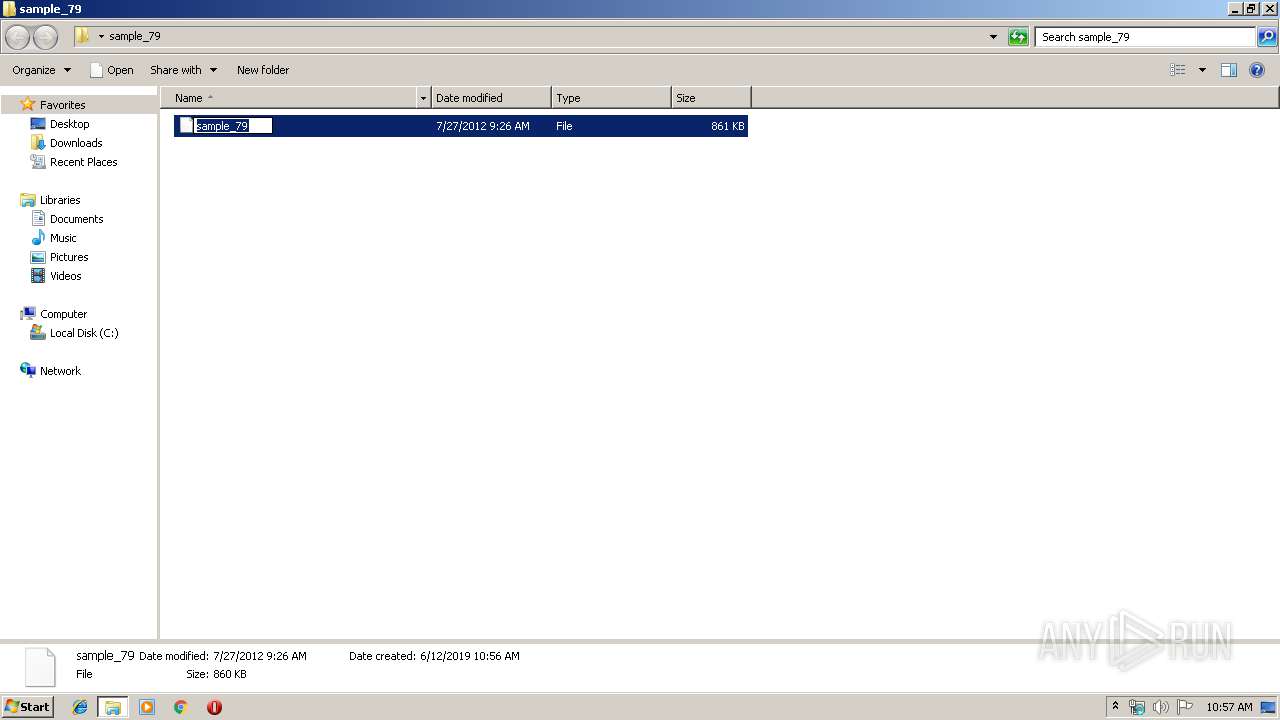
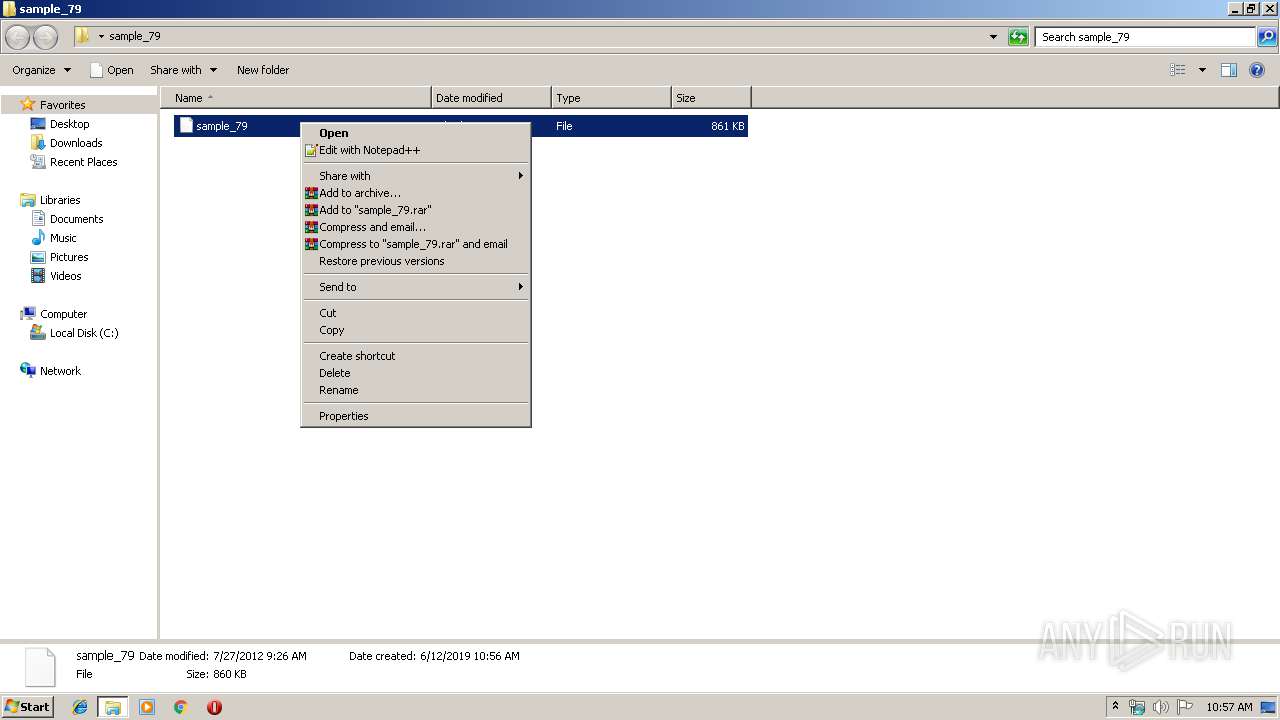
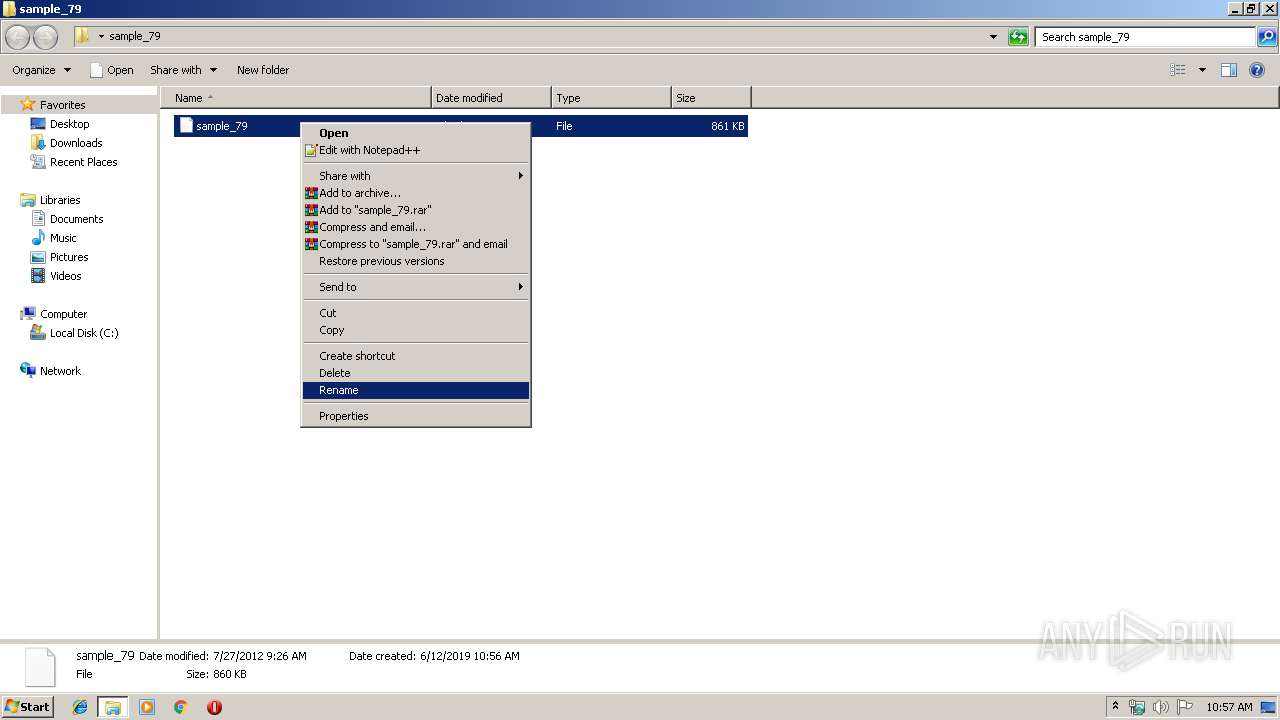
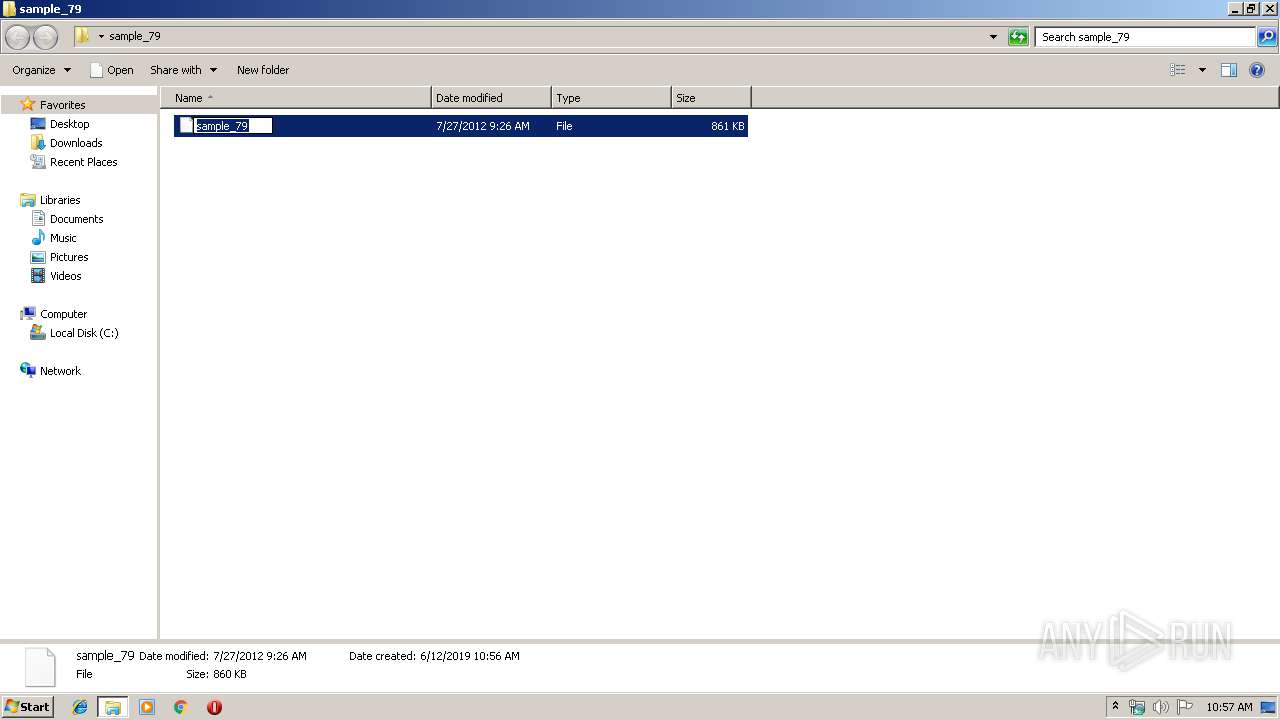
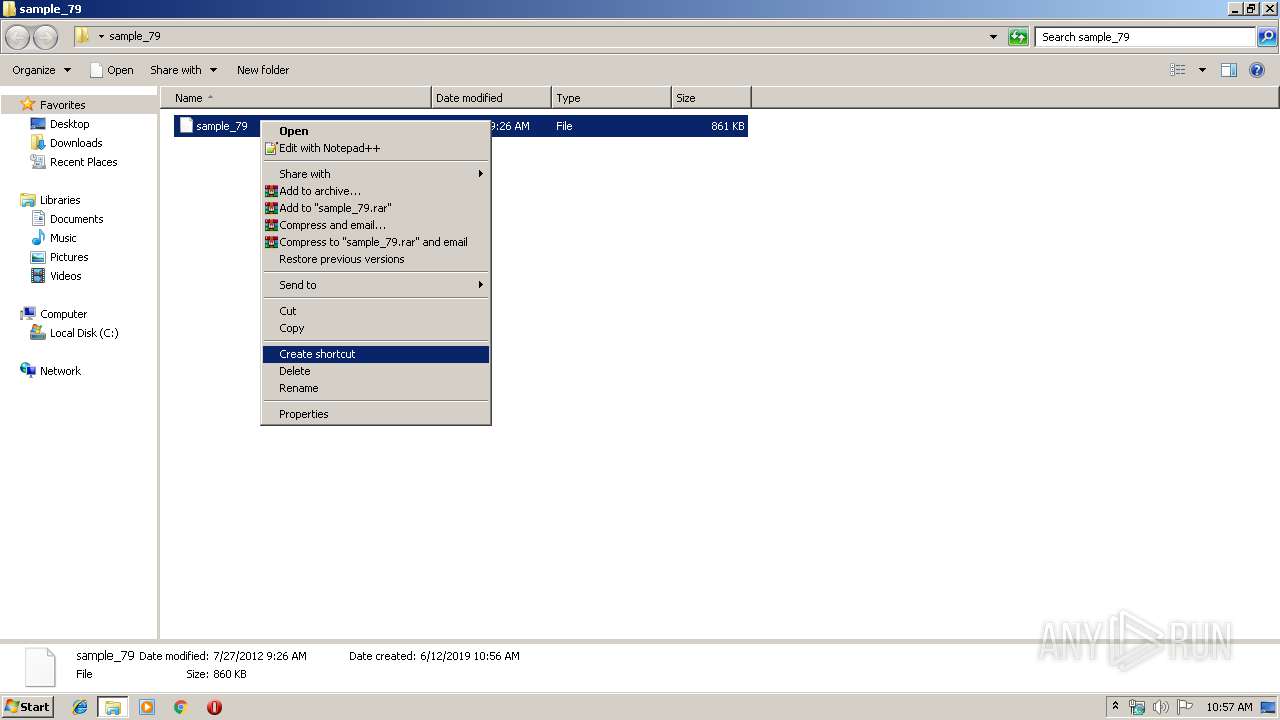
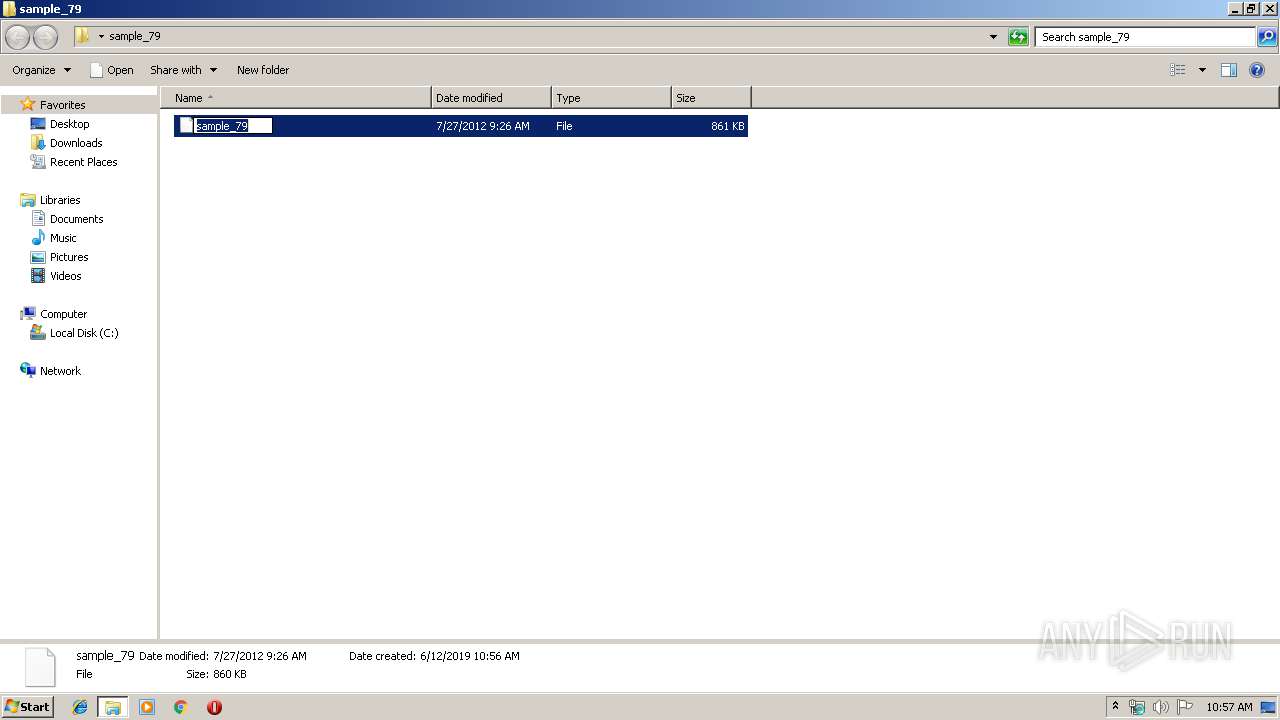
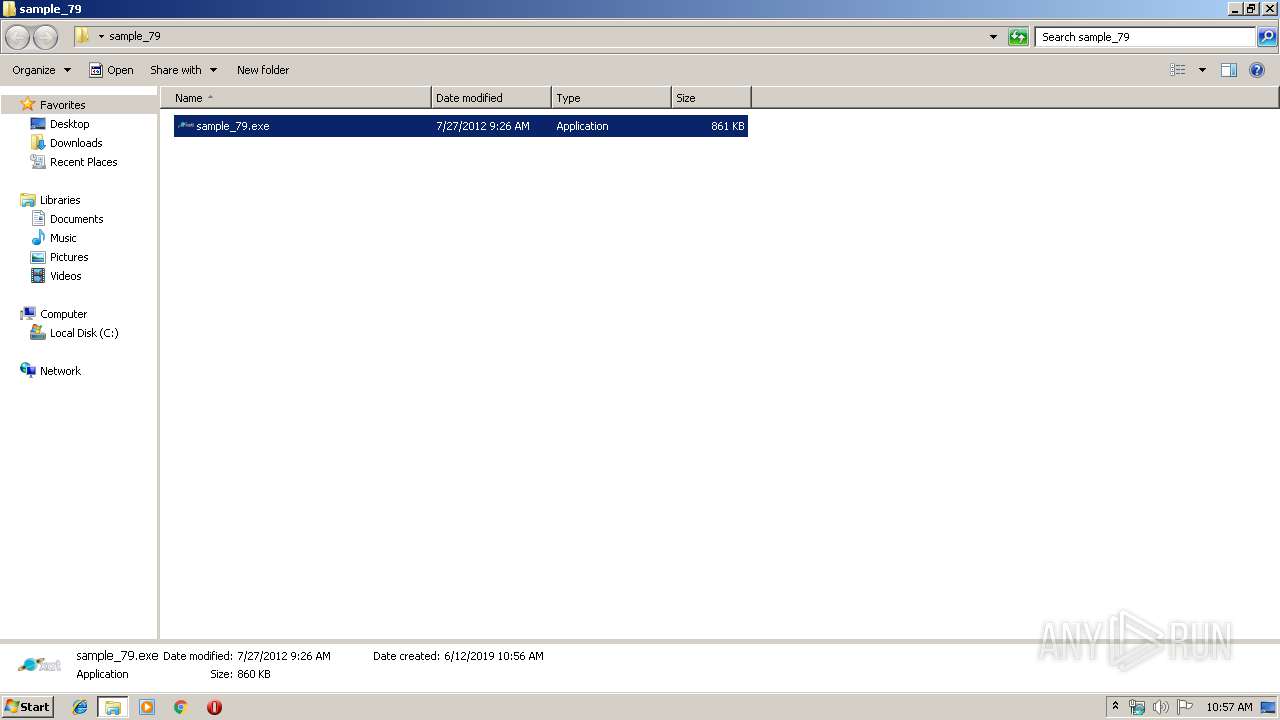
Manual execution by user
- sample_79.exe (PID: 2672)
Creates files in the user directory
- iexplore.exe (PID: 3504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
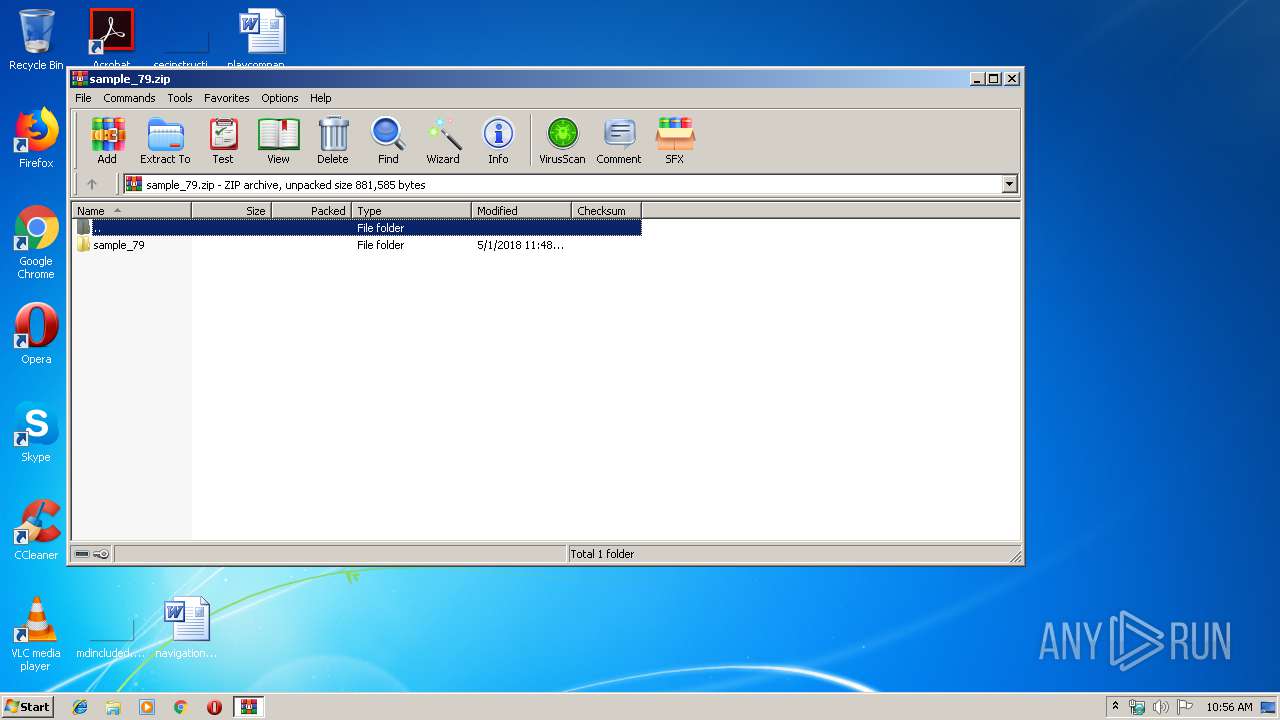
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_79/ |
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | ctfmon.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\Desktop\sample_79\sample_79.exe" | C:\Users\admin\Desktop\sample_79\sample_79.exe | sample_79.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\Desktop\sample_79\sample_79.exe" | C:\Users\admin\Desktop\sample_79\sample_79.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
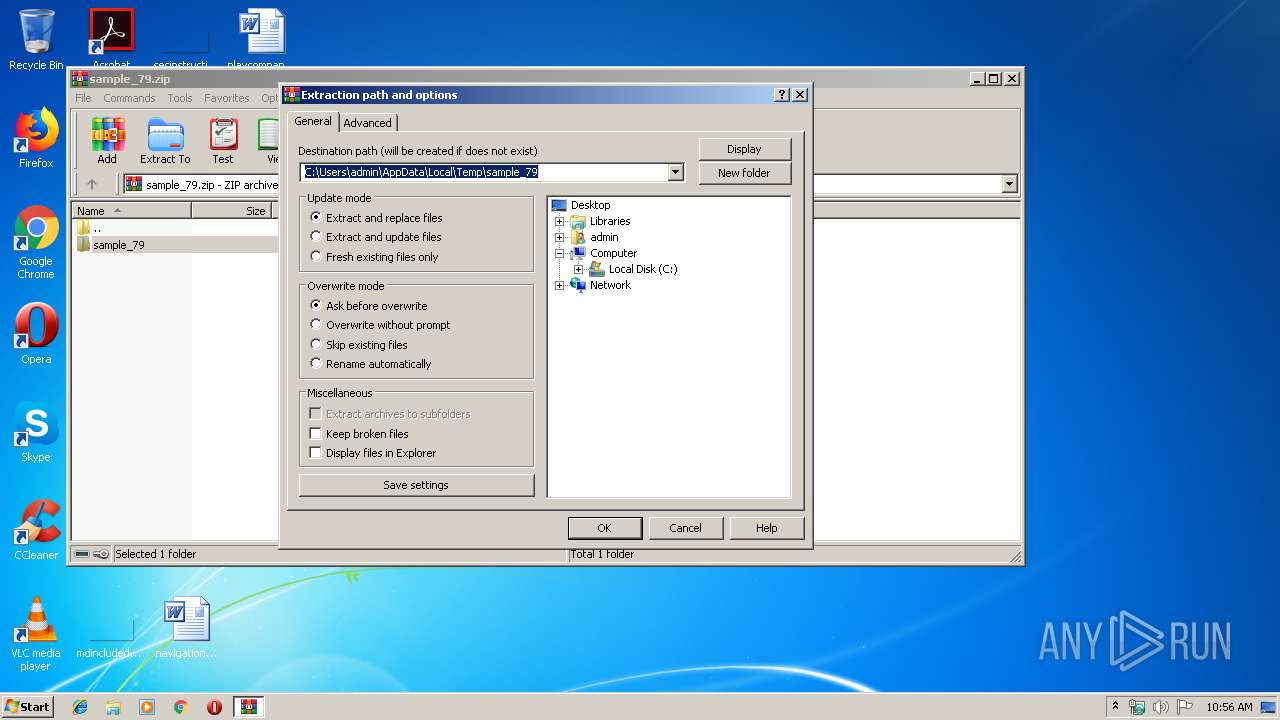
| 2824 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_79.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3504 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | sample_79.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 353
Read events
3 226
Write events
127
Delete events
0
Modification events
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_79.zip | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
3
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | sample_79.exe | C:\Users\admin\AppData\Local\Temp\XX--XX--XX.txt | binary | |
MD5:— | SHA256:— | |||
| 2504 | sample_79.exe | C:\dir\install\install\adobepdf.exe | executable | |
MD5:94C6CAAA60F2CF7EF94738C4D2A42603 | SHA256:12FF08802C6B7656F54FD73E9D6312F818BB4A34D459C3A87BAE53E5B40E2BE6 | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\UuU.uUu | text | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\XxX.xXx | text | |
MD5:— | SHA256:— | |||
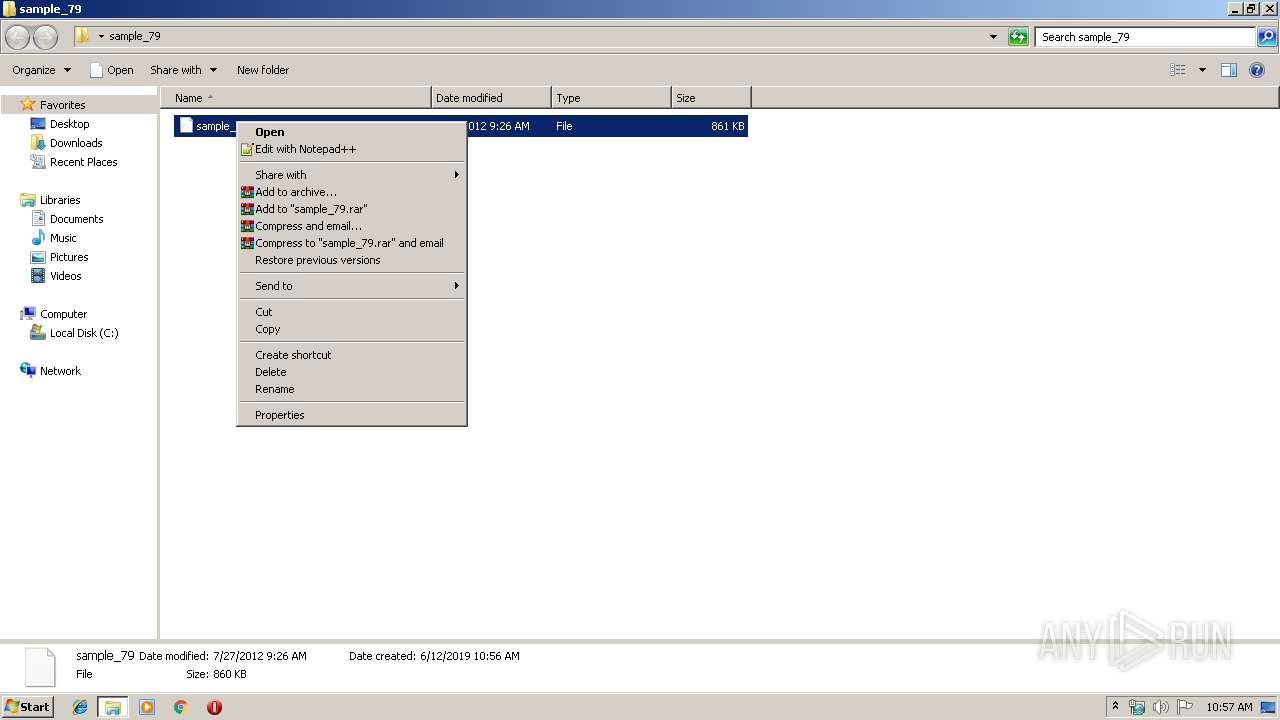
| 252 | explorer.exe | C:\Users\admin\Desktop\sample_79\sample_79.exe | executable | |
MD5:94C6CAAA60F2CF7EF94738C4D2A42603 | SHA256:12FF08802C6B7656F54FD73E9D6312F818BB4A34D459C3A87BAE53E5B40E2BE6 | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Roaming\logs.dat | text | |
MD5:4362E21AF8686F5EBBA224768D292A5B | SHA256:B1B2CC9A6BF77F9E56955ACBBCE253C70FC25B92D1E150D9928B9183B19B93B3 | |||
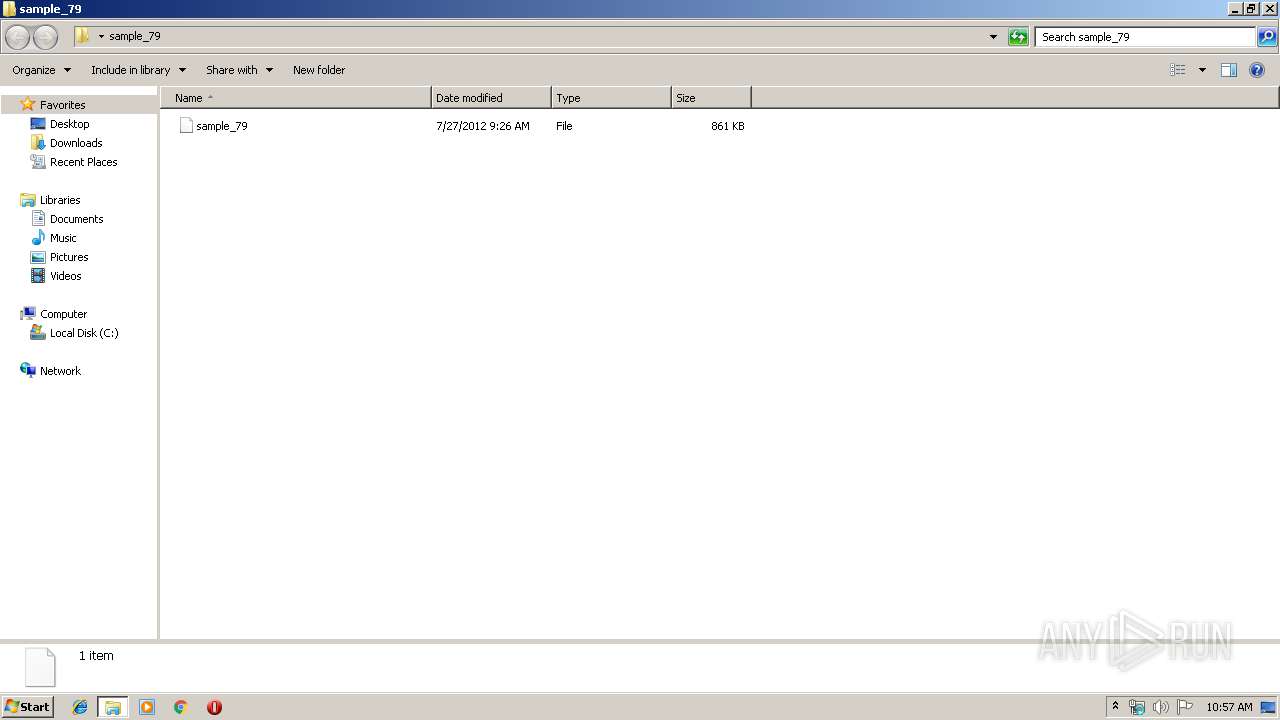
| 2824 | WinRAR.exe | C:\Users\admin\Desktop\sample_79\sample_79 | executable | |
MD5:94C6CAAA60F2CF7EF94738C4D2A42603 | SHA256:12FF08802C6B7656F54FD73E9D6312F818BB4A34D459C3A87BAE53E5B40E2BE6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.radioflogmix.com |
| unknown |
rpcodec.no-ip.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a Suspicious no-ip Domain |