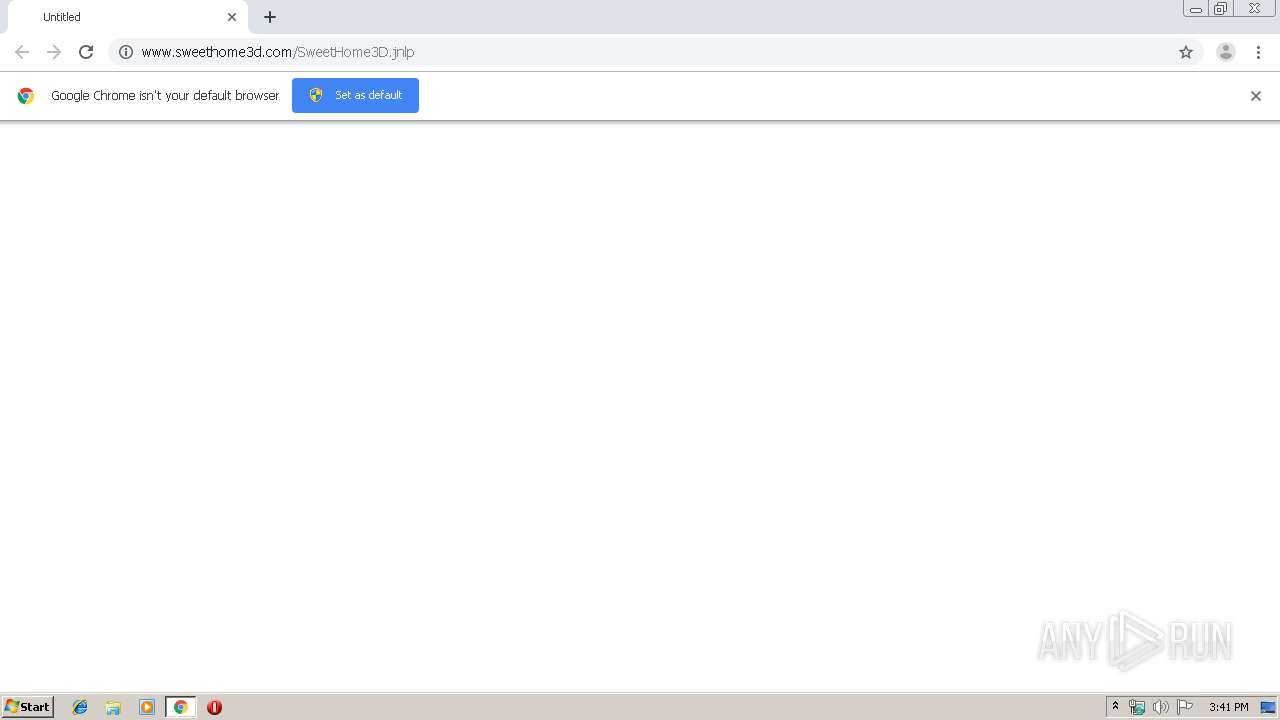
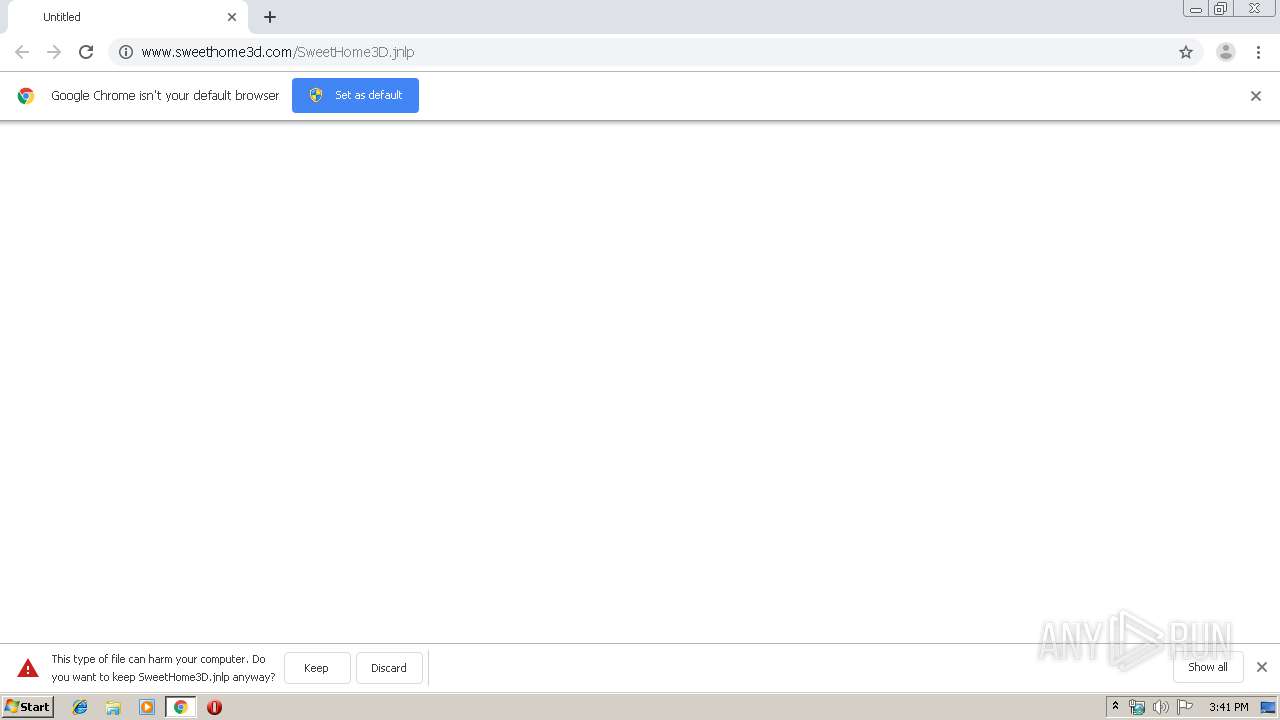
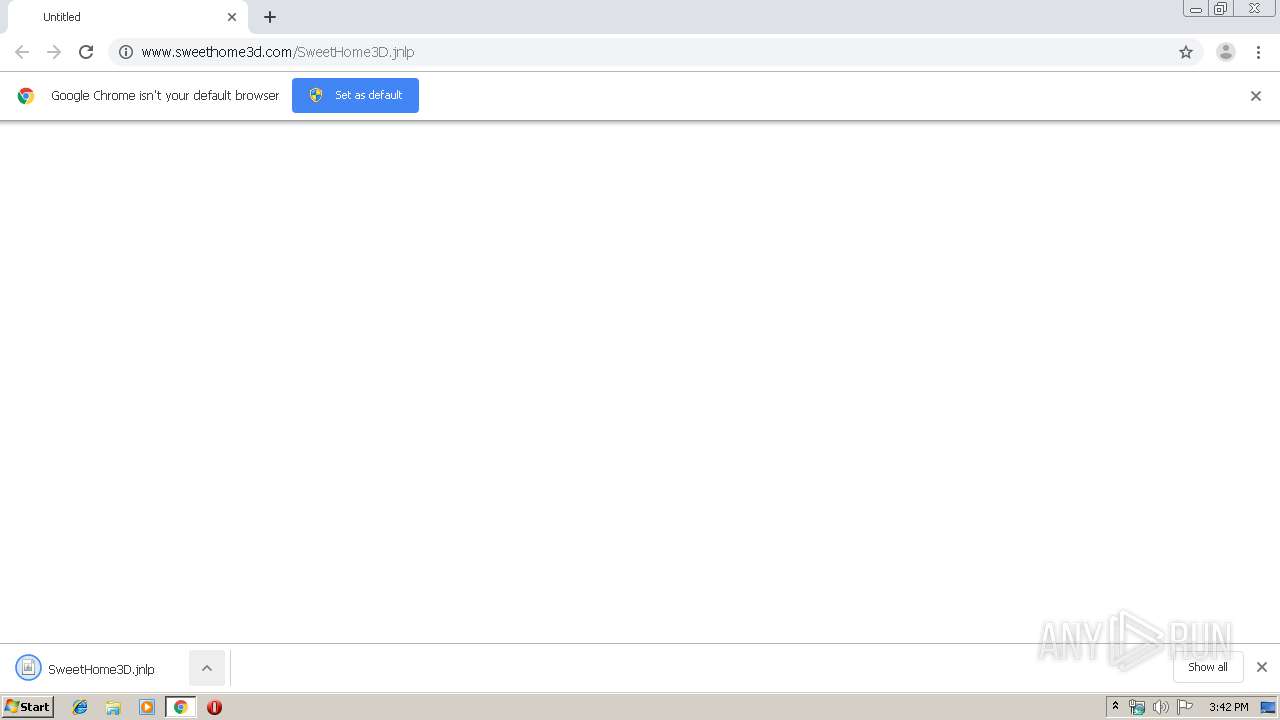
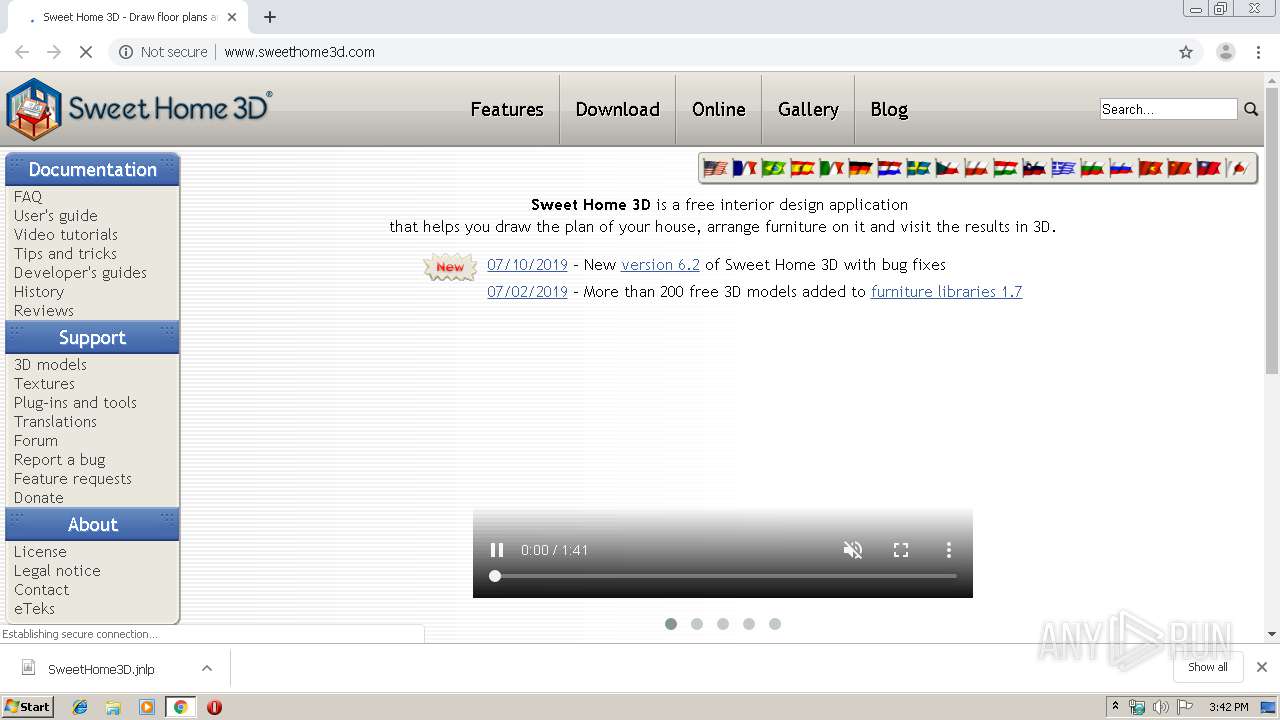
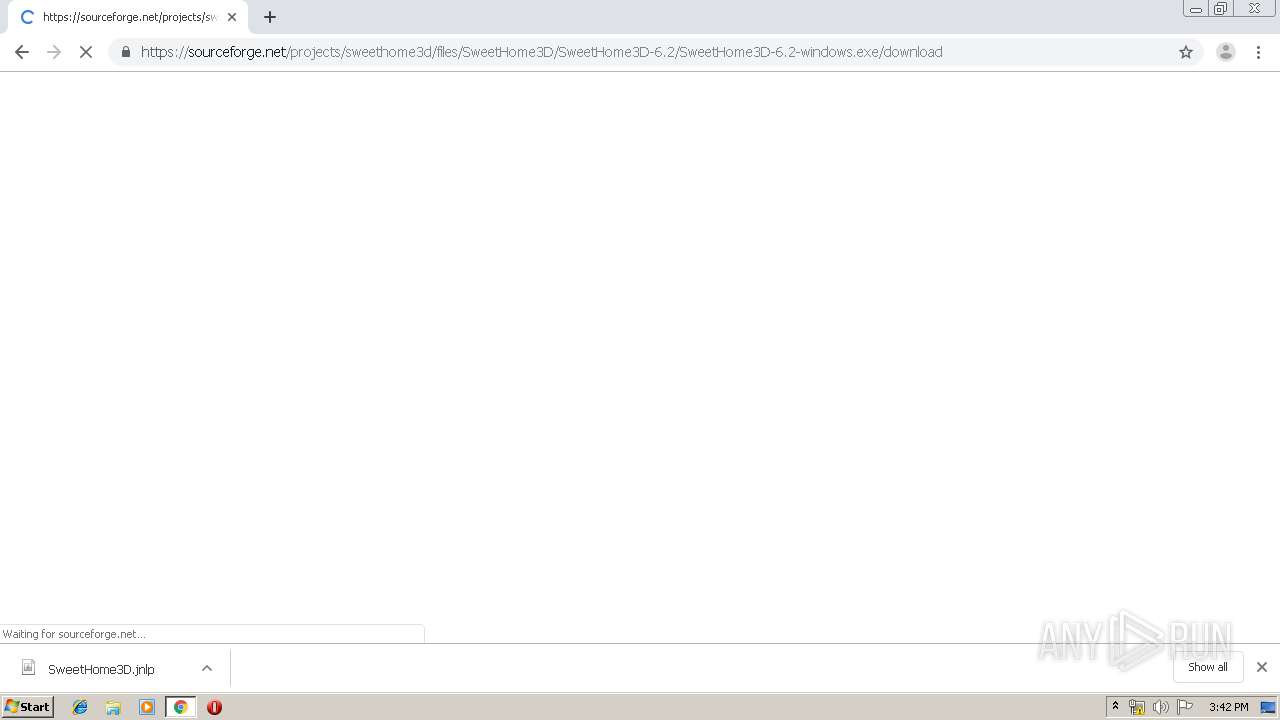
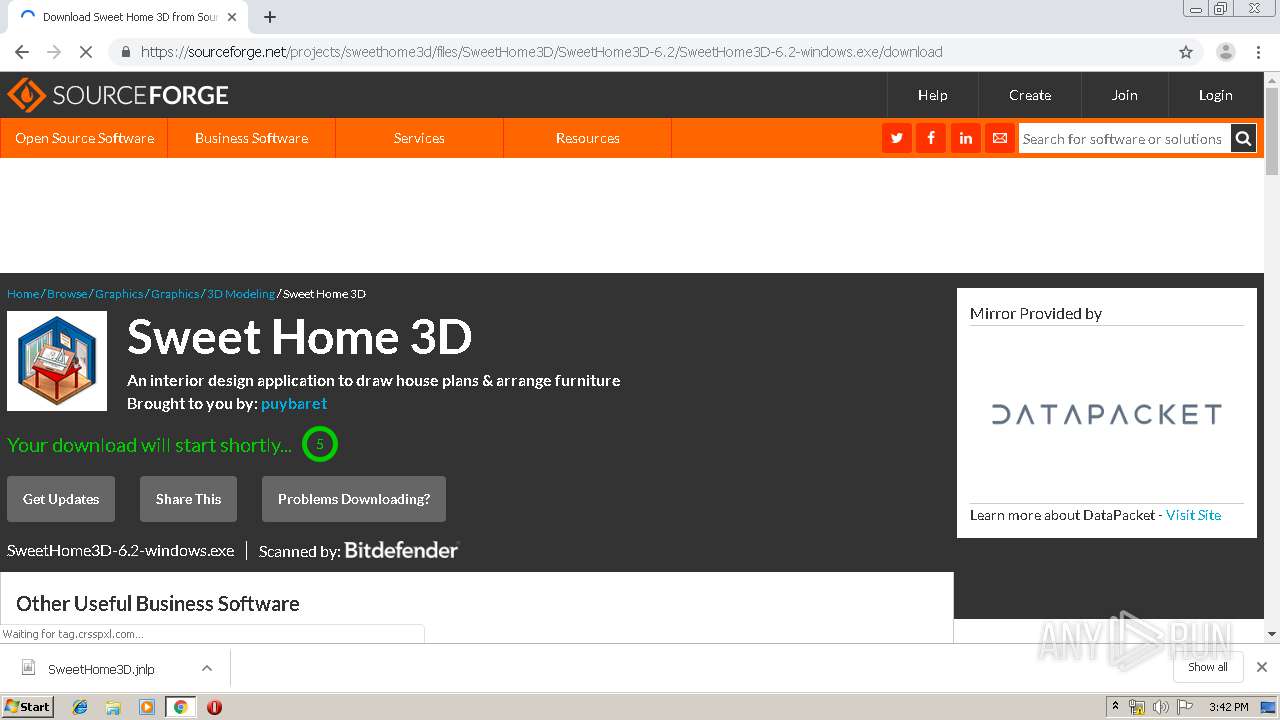
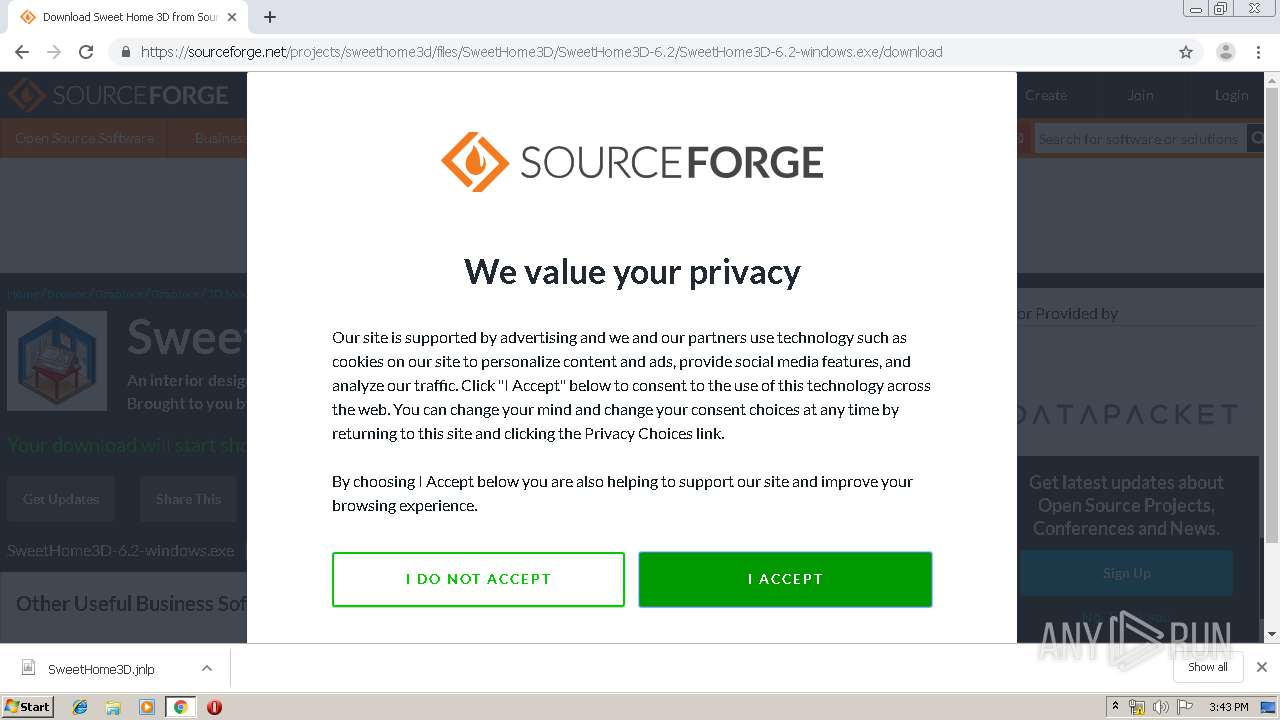
| URL: | http://www.sweethome3d.com/SweetHome3D.jnlp |
| Full analysis: | https://app.any.run/tasks/bc876836-720b-456b-8879-7ab3251adfd2 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 14:41:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E23FF898E2661D3A918F5B5EF807A80B |
| SHA1: | AADD1A635F2D1C180BC8E798E118EFE739147CBA |
| SHA256: | 536D7E0DDB772DB138258B8F6FE302352ACCF9E993D14E98DCCC783F2A8EF87A |
| SSDEEP: | 3:N1KJS4VY9GLGK32z0FzhxV:Cc4K93K32wFz3V |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3312)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3312)
Application launched itself
- chrome.exe (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6996739068592409488 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7406653660150439947 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6152751850938691141 --mojo-platform-channel-handle=3920 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4169478206022926949 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1378596046008952456 --mojo-platform-channel-handle=3496 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12703779999051201275 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10201893412579278430 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3944 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3192 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6434184960059598097 --mojo-platform-channel-handle=2712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,1479058739090607480,11838893811081791776,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1064755401027040463 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
998
Read events
900
Write events
94
Delete events
4
Modification events
| (PID) Process: | (1744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3312-13207329682163375 |
Value: 259 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3312-13207329682163375 |
Value: 259 | |||
Executable files
0
Suspicious files
130
Text files
202
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ae5c07c5-c559-4610-a92d-35aa8bbf9219.tmp | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF166c4b.TMP | text | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF166c4b.TMP | text | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF166ca9.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
162
TCP/UDP connections
141
DNS requests
118
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
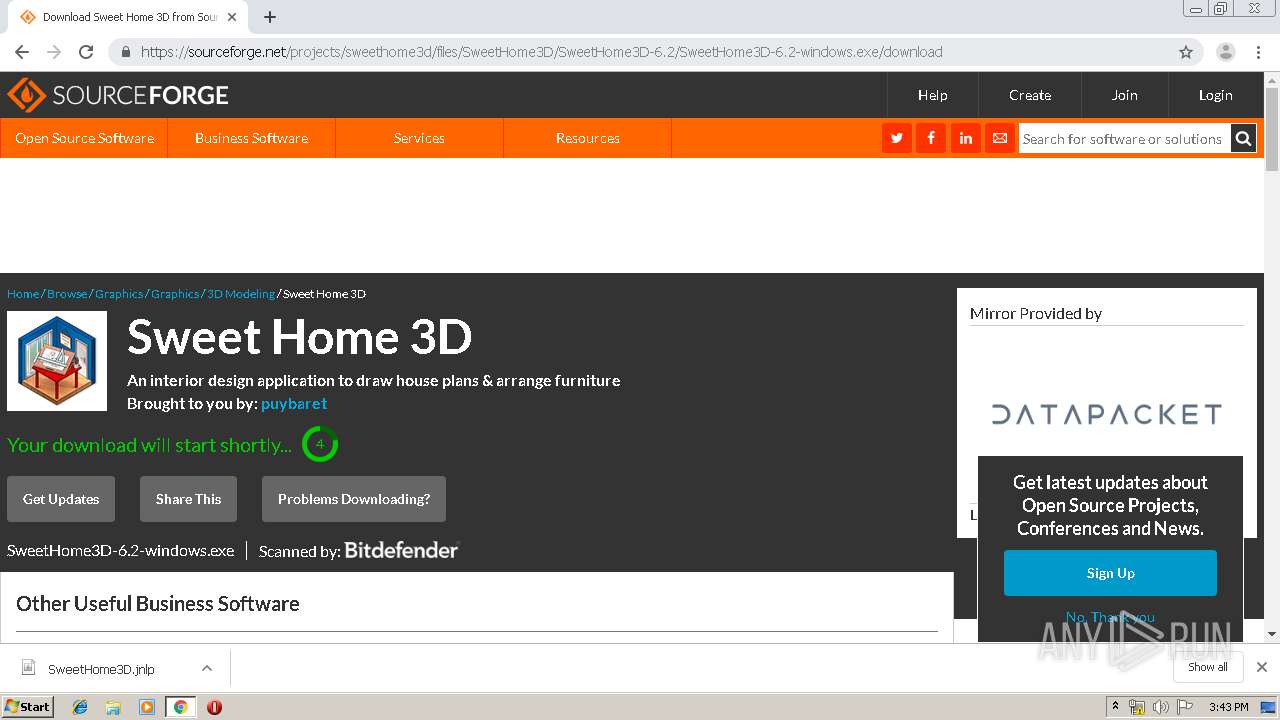
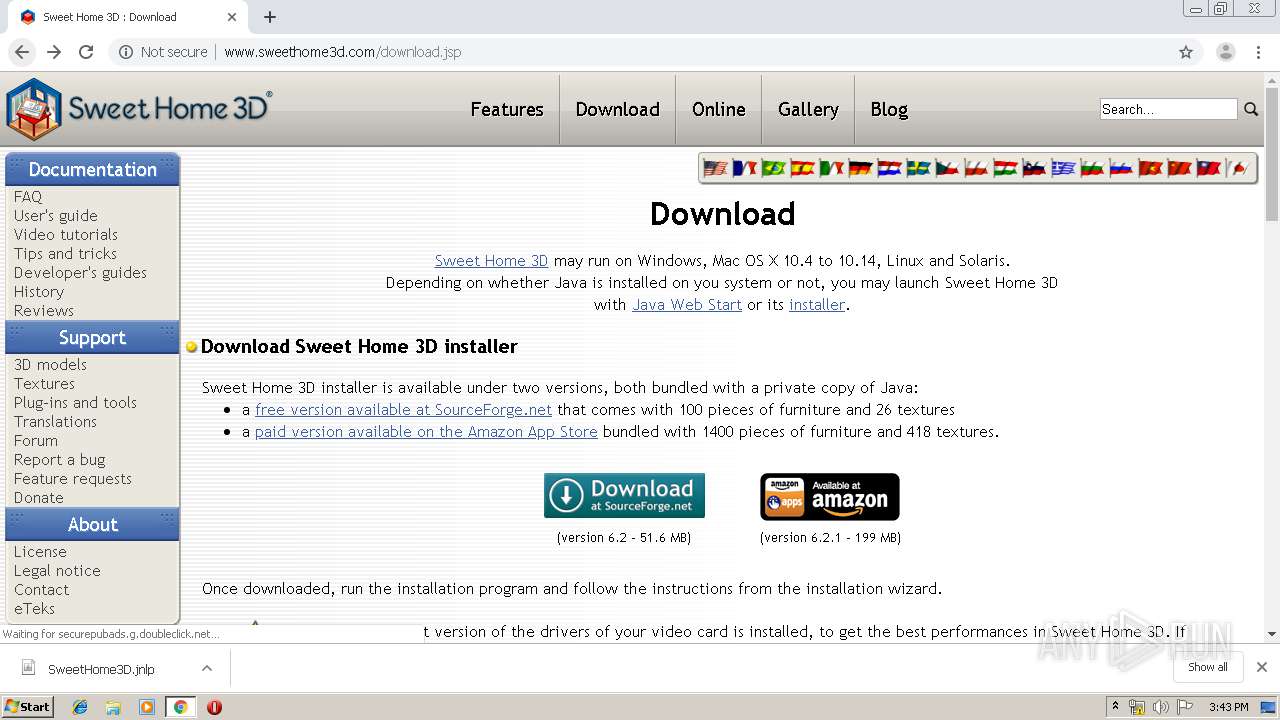
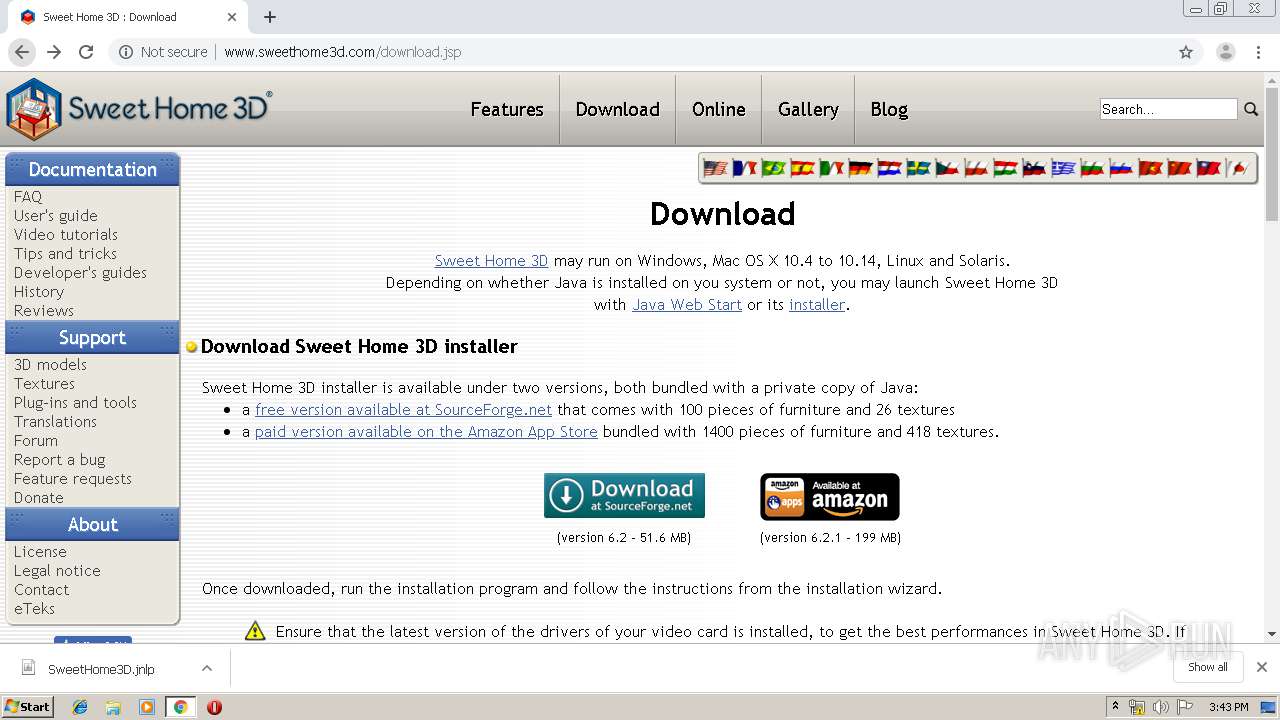
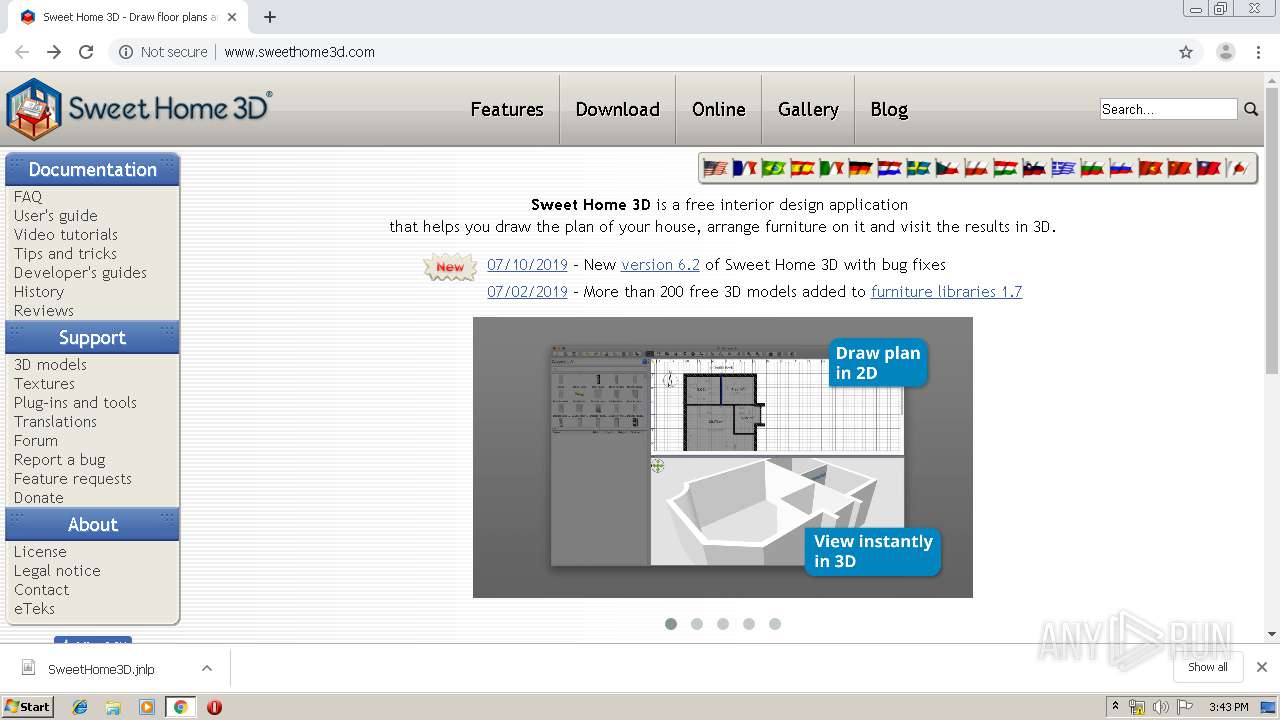
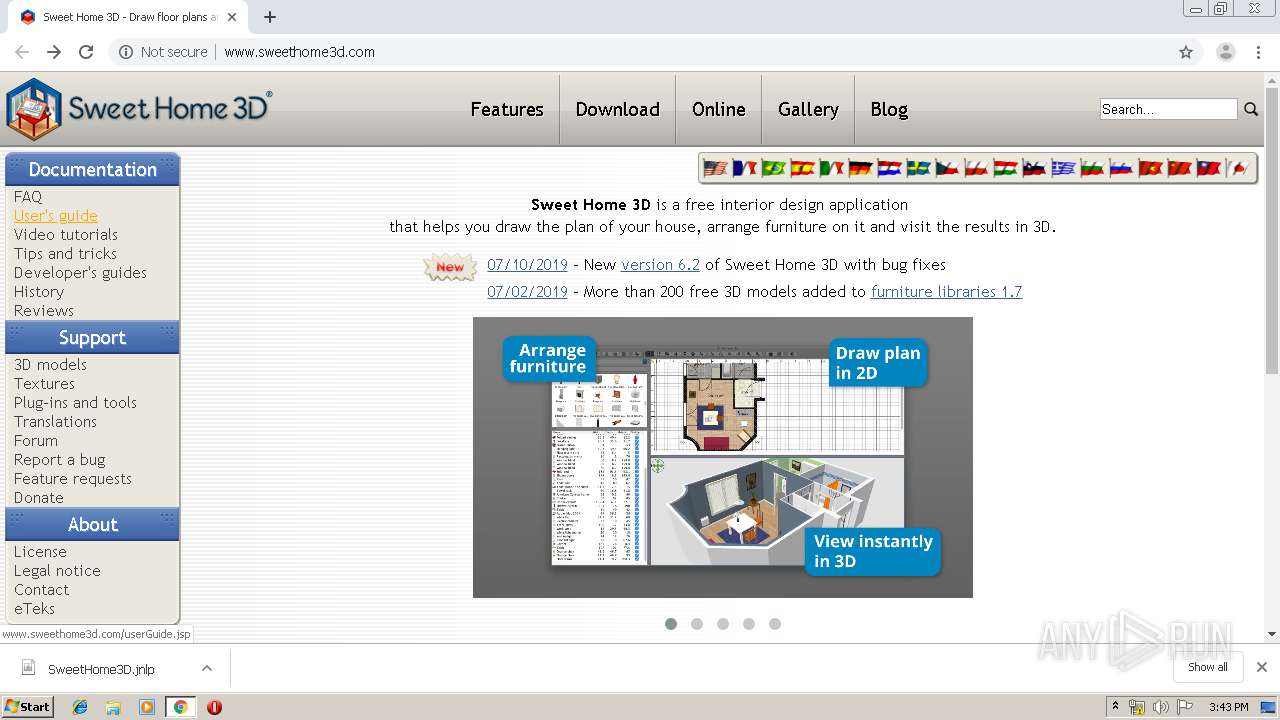
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/SweetHome3D.jnlp | FR | xml | 4.42 Kb | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/sweethome3d.css?version=2 | FR | text | 1.61 Kb | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/lightbox/lightbox.js | FR | text | 3.58 Kb | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/ | FR | html | 5.63 Kb | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/lightbox/lightbox.css | FR | text | 410 b | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/images/search.gif | FR | image | 358 b | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/videos/owl.carousel.css | FR | text | 528 b | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/videos/owl.theme.css | FR | text | 606 b | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/images/SweetHome3DLogoSmallScreen.png | FR | image | 15.2 Kb | suspicious |
2652 | chrome.exe | GET | 200 | 176.31.241.24:80 | http://www.sweethome3d.com/videos/owl.carousel.min.js | FR | text | 6.31 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2652 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2652 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2652 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
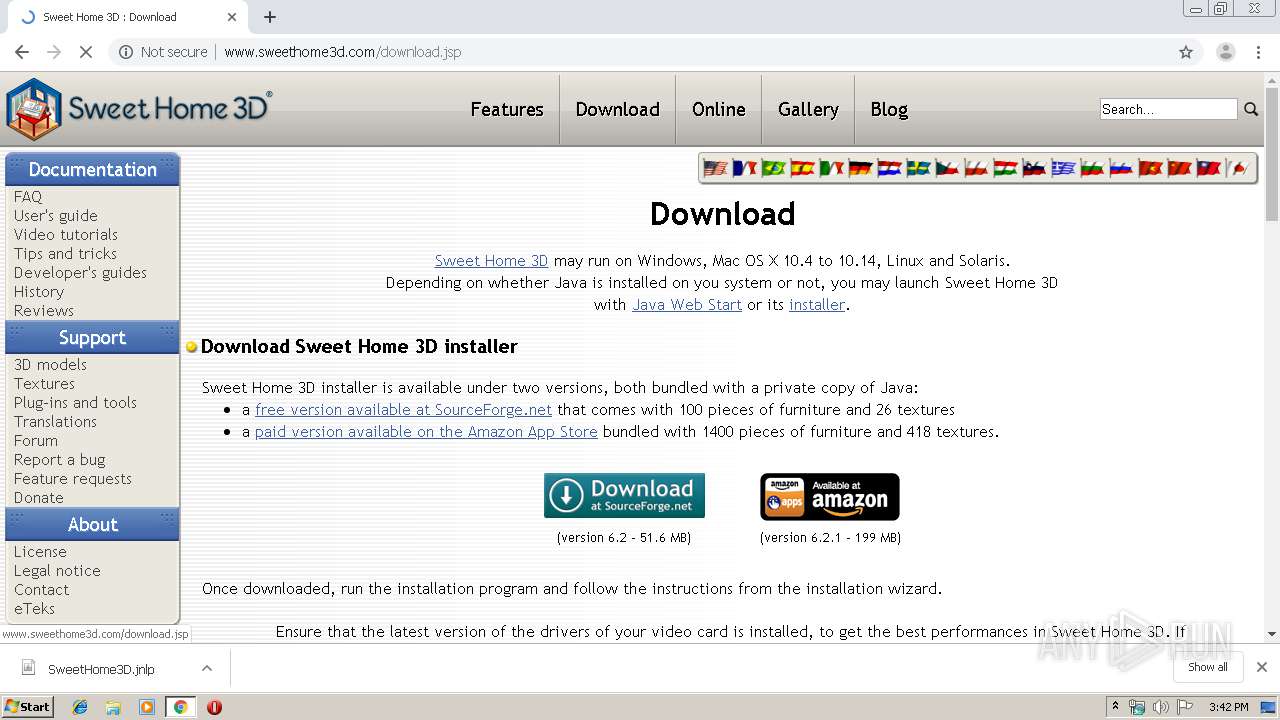
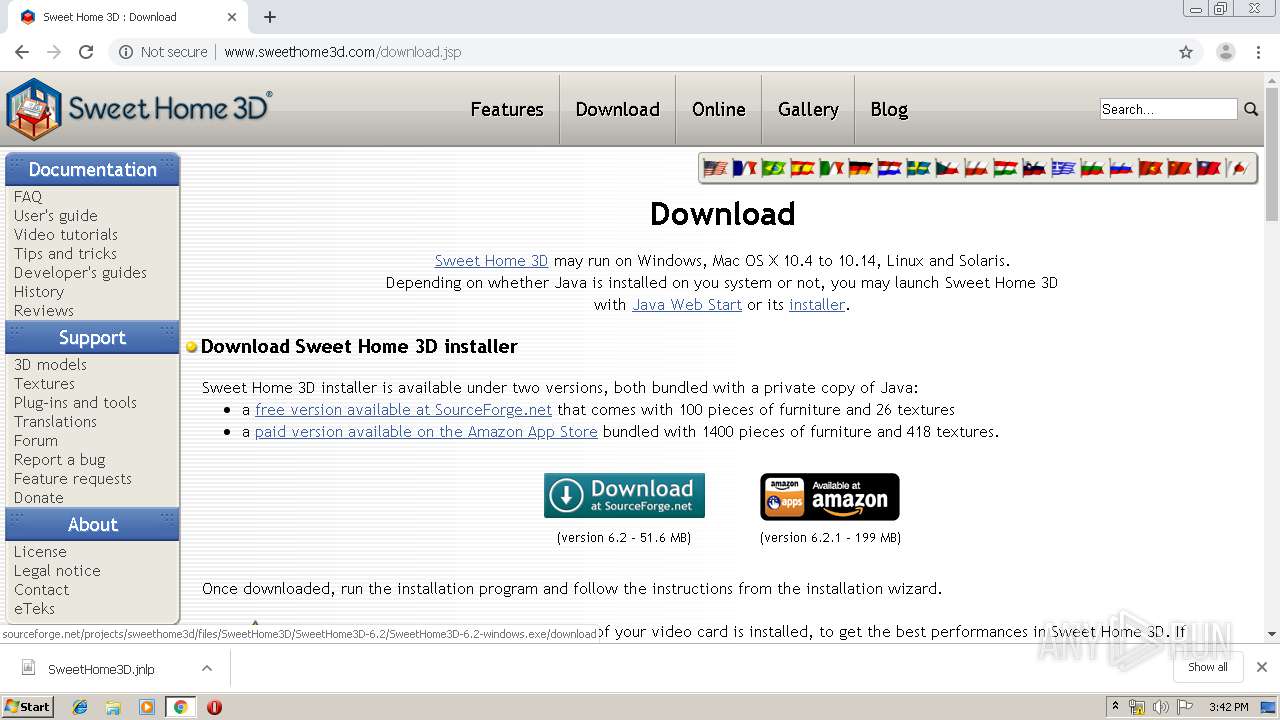
2652 | chrome.exe | 216.105.38.13:80 | sflogo.sourceforge.net | American Internet Services, LLC. | US | malicious |
2652 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2652 | chrome.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
2652 | chrome.exe | 31.13.92.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2652 | chrome.exe | 216.58.207.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2652 | chrome.exe | 31.13.92.14:443 | staticxx.facebook.com | Facebook, Inc. | IE | whitelisted |
2652 | chrome.exe | 172.217.22.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sweethome3d.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.at |
| whitelisted |
www.paypal.com |
| whitelisted |
sflogo.sourceforge.net |
| suspicious |
sourceforge.net |
| whitelisted |