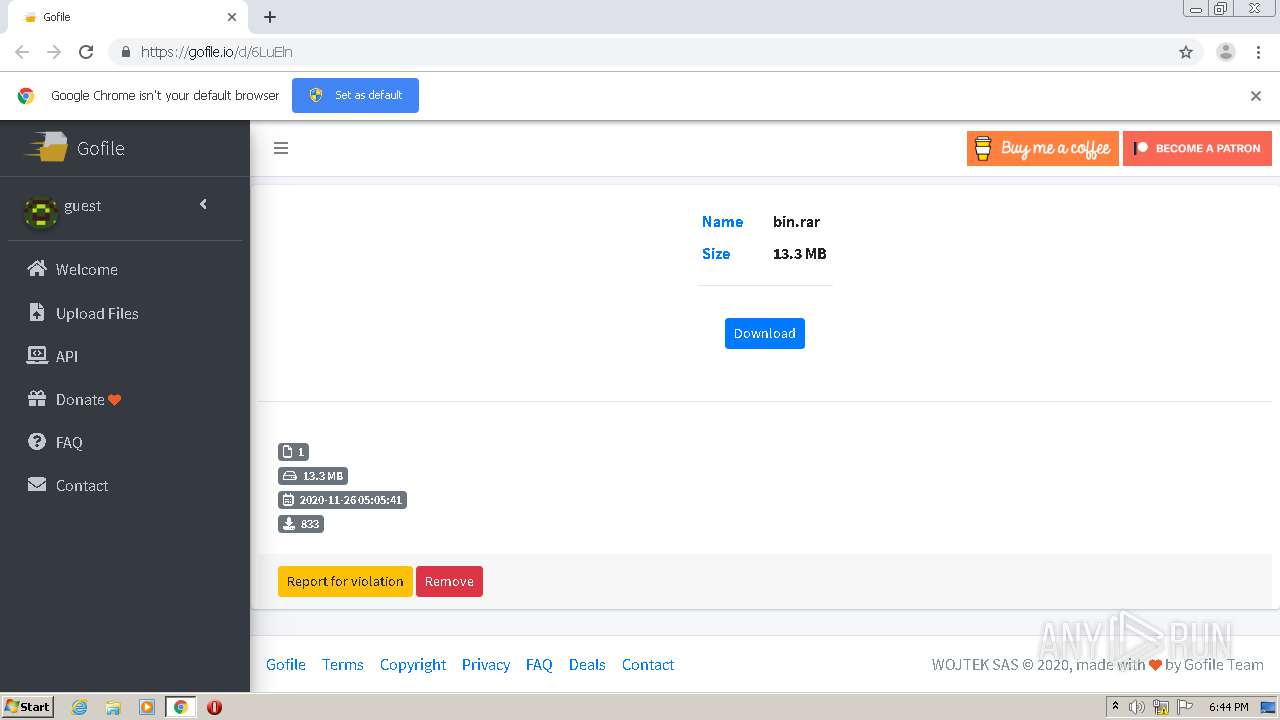
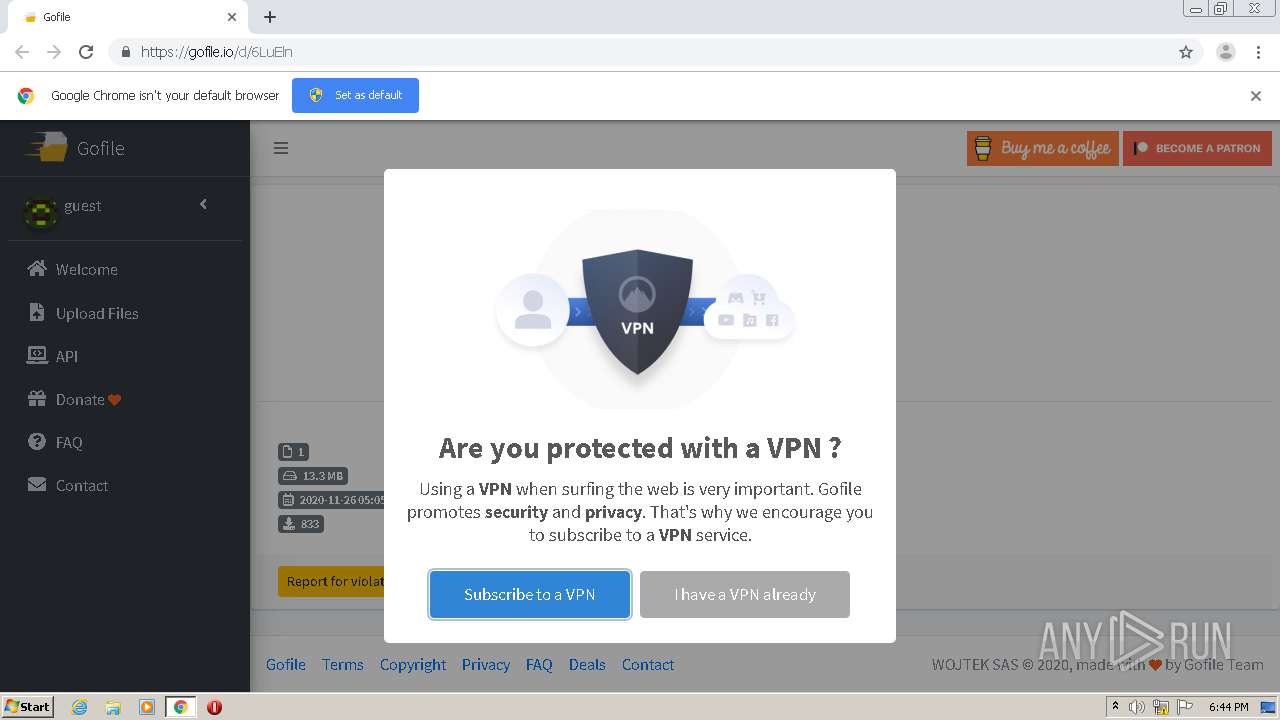
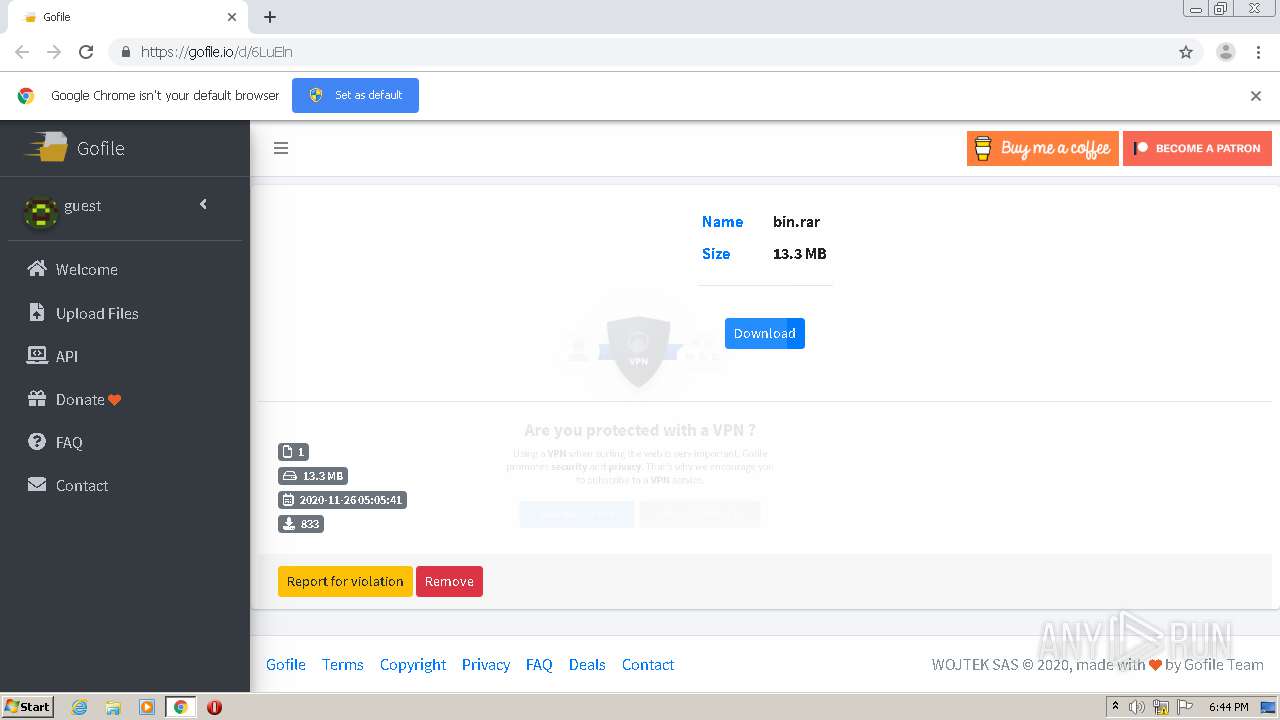
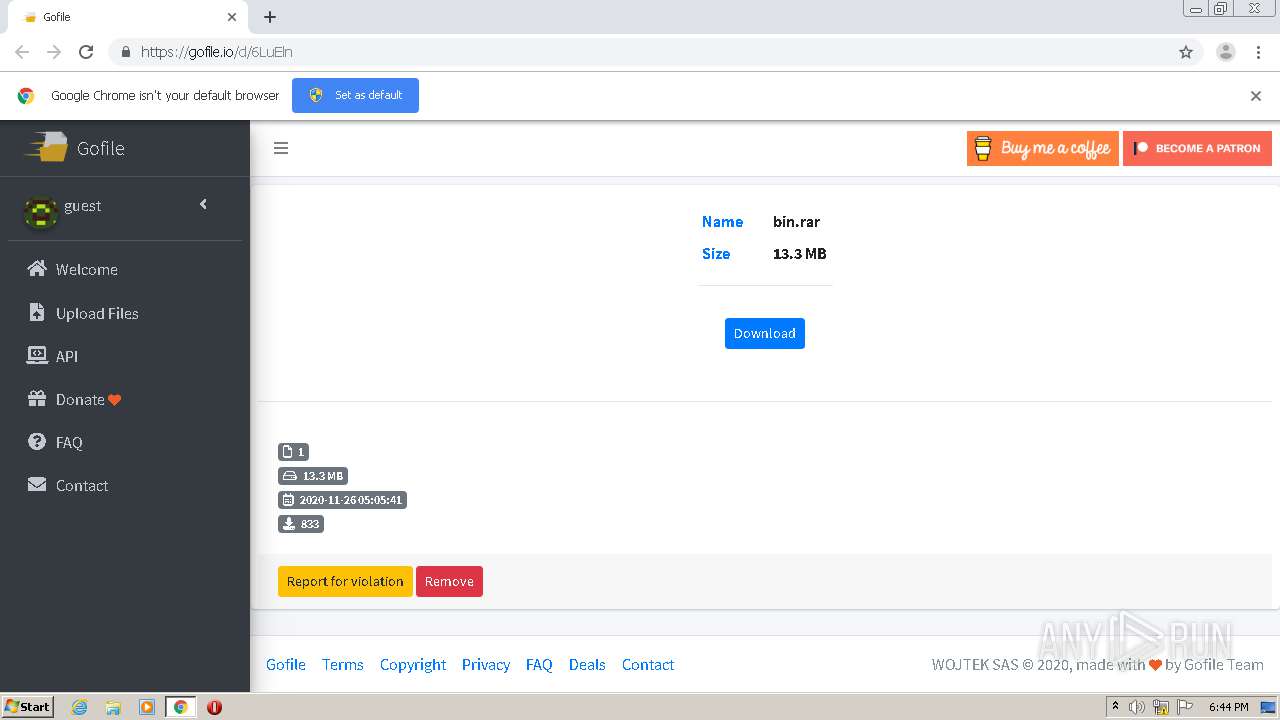
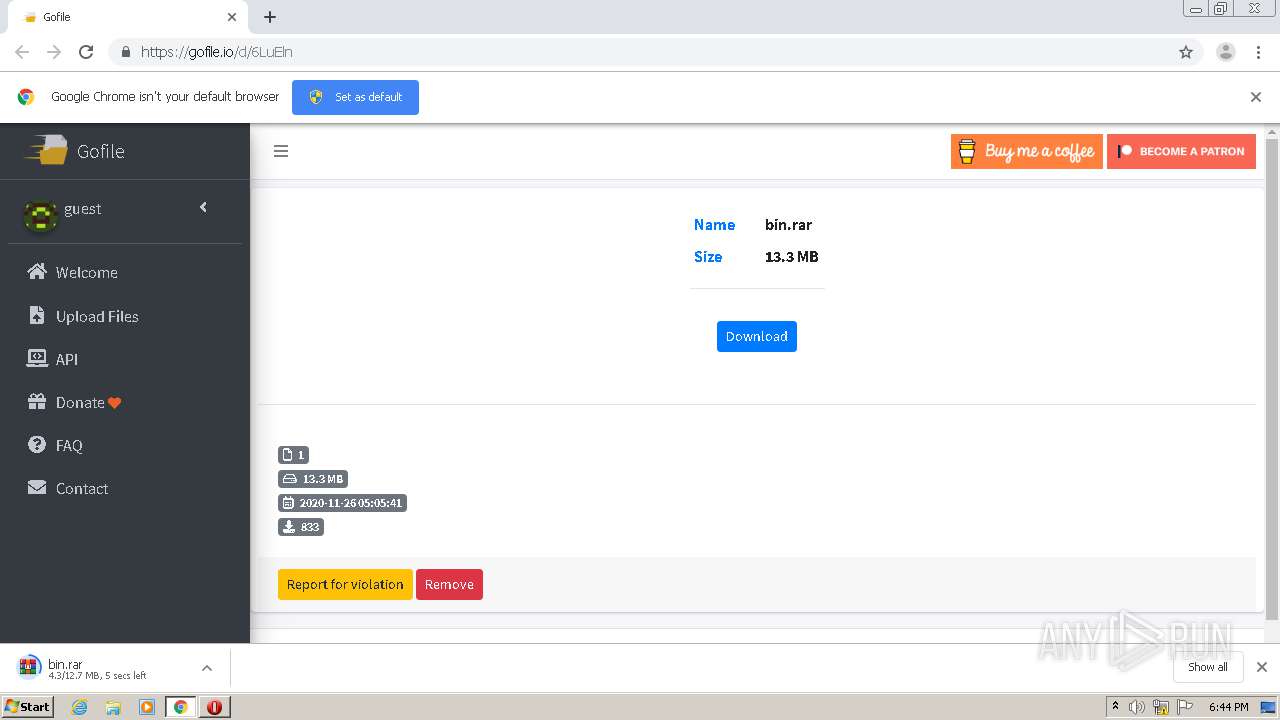
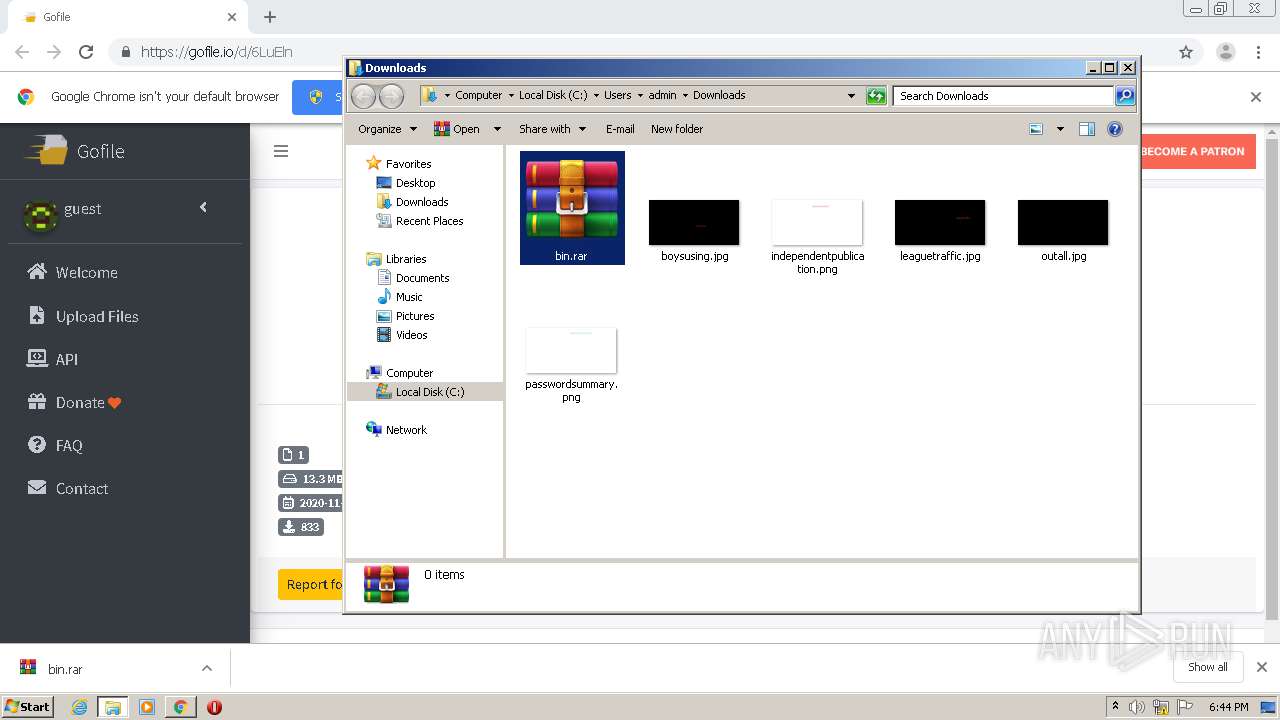
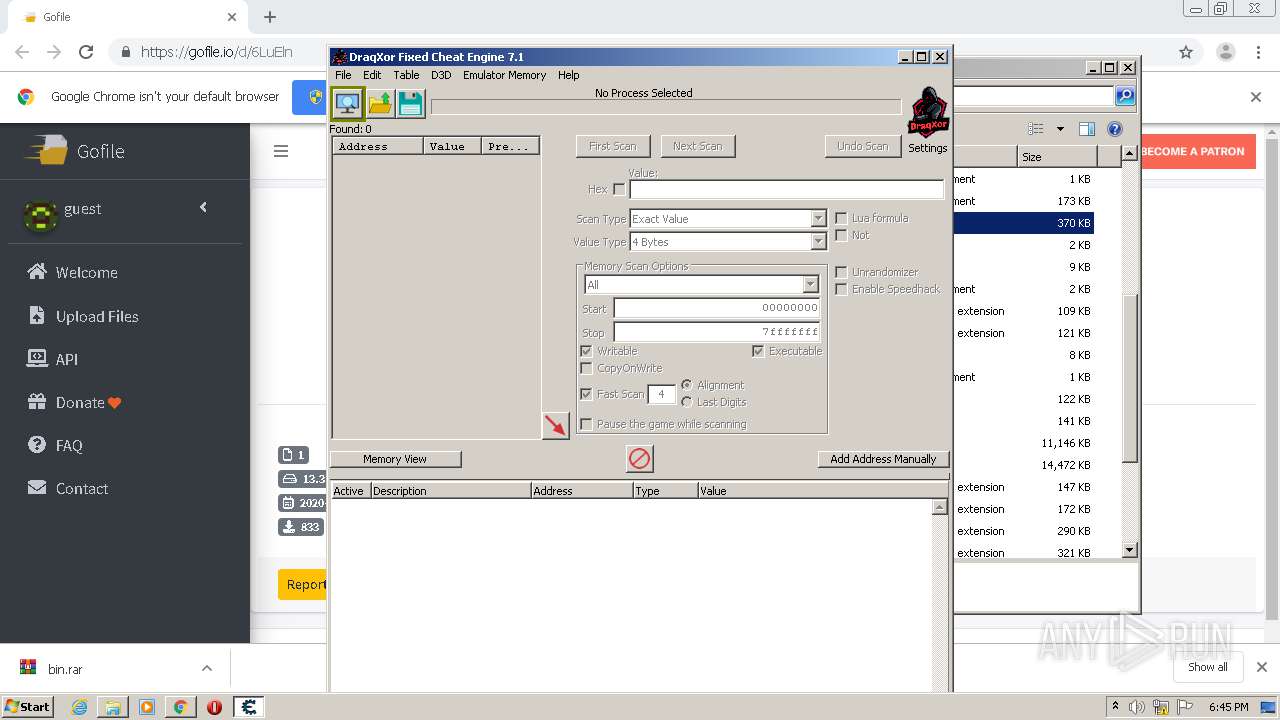
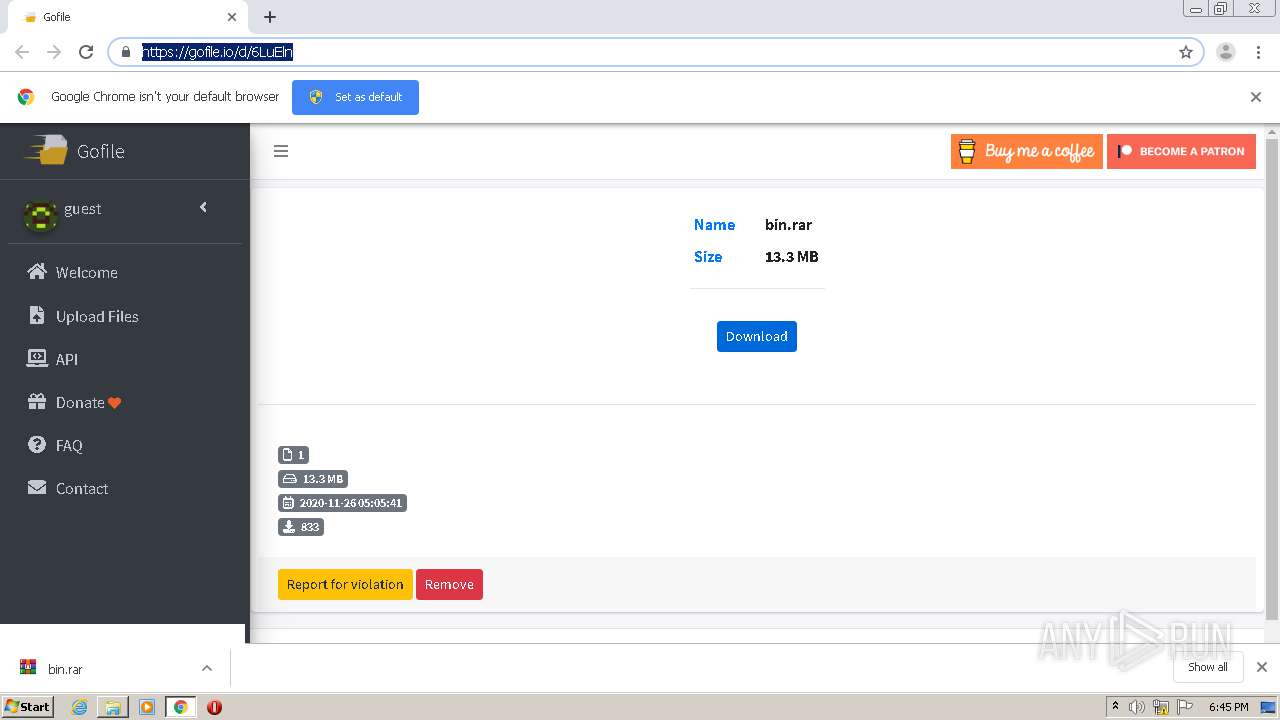
| URL: | https://gofile.io/d/6LuEln |
| Full analysis: | https://app.any.run/tasks/c9e28659-b1de-4d99-8df6-c3edaeea677f |
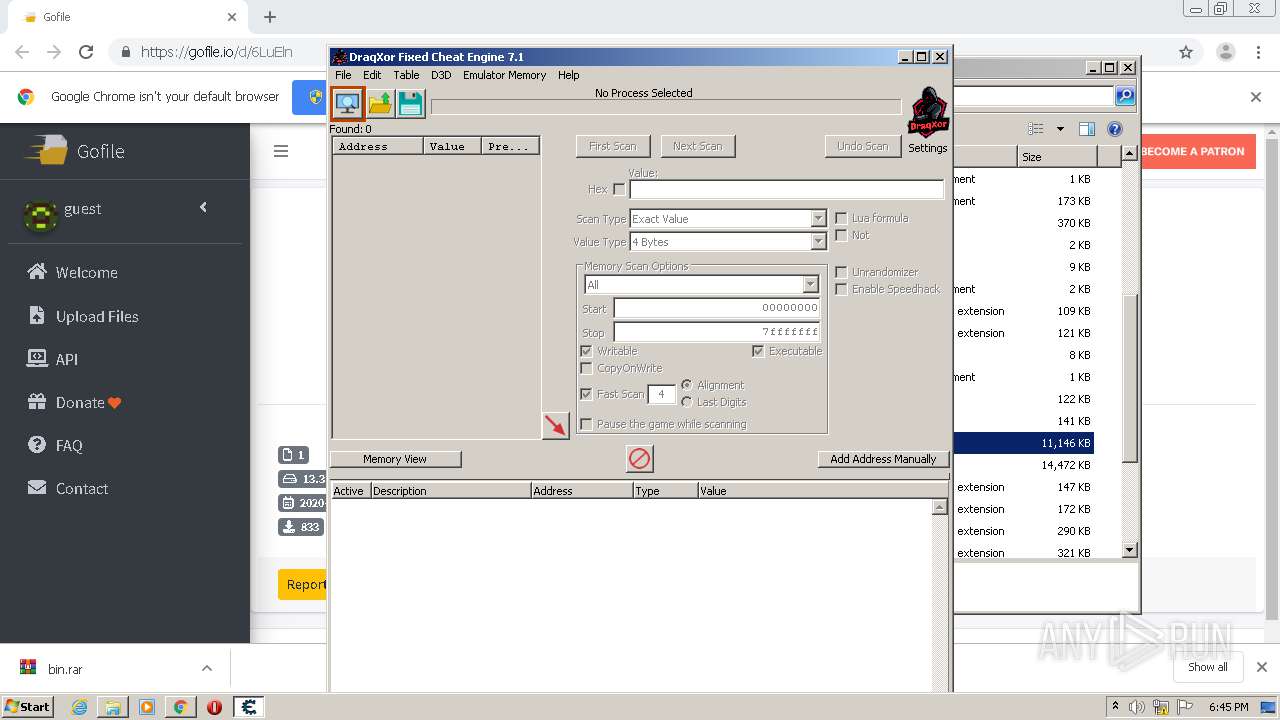
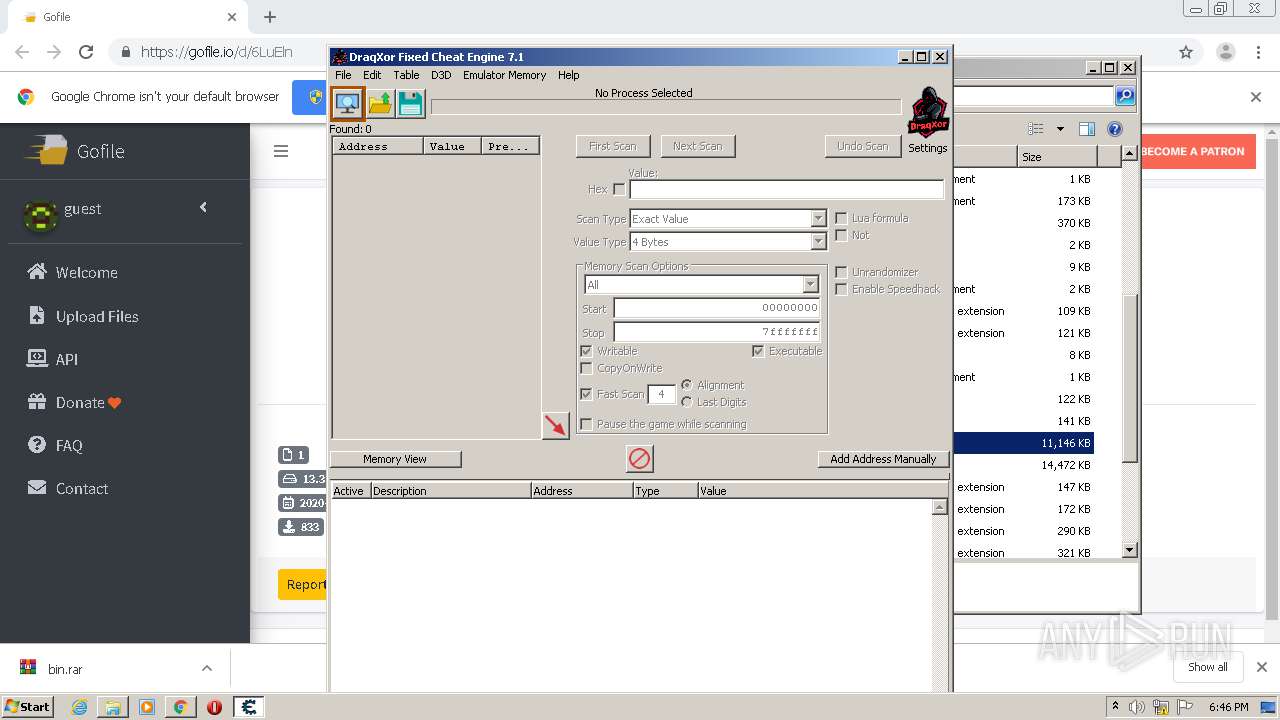
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 18:44:08 |
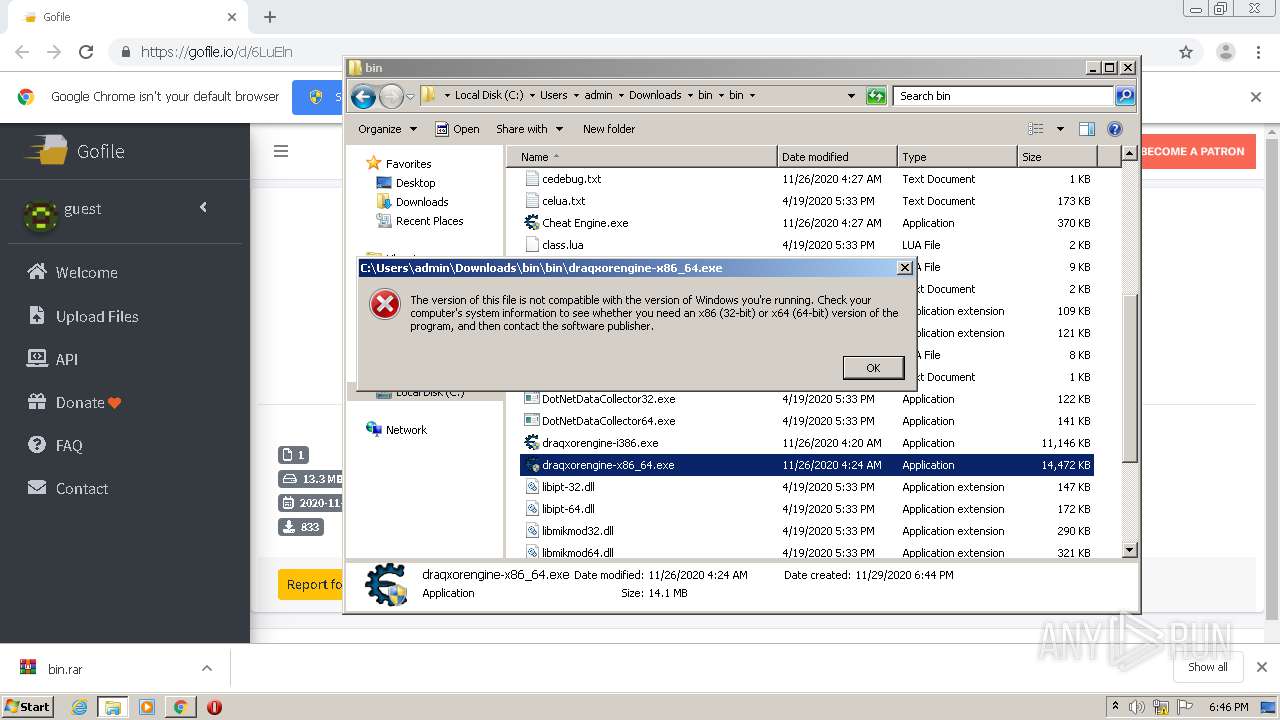
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 53B8D236D0125289E4B5D342264162BF |
| SHA1: | 56509117B267FC645DE123CA12BC8CC43C7BC40F |
| SHA256: | 5362AD68B64E82C9FB73341B55B19DF5473C98FE1B6DD9499ABC1121A5F7FD58 |
| SSDEEP: | 3:N8rxL1Td:2ZZd |
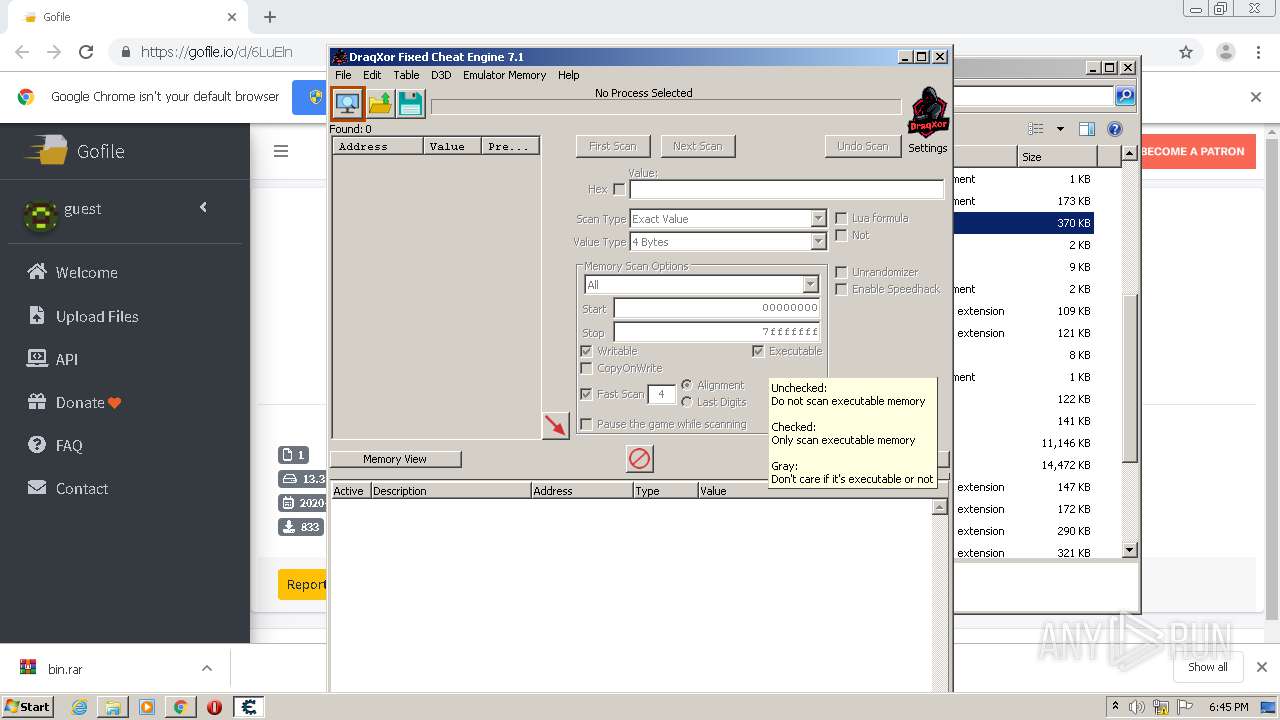
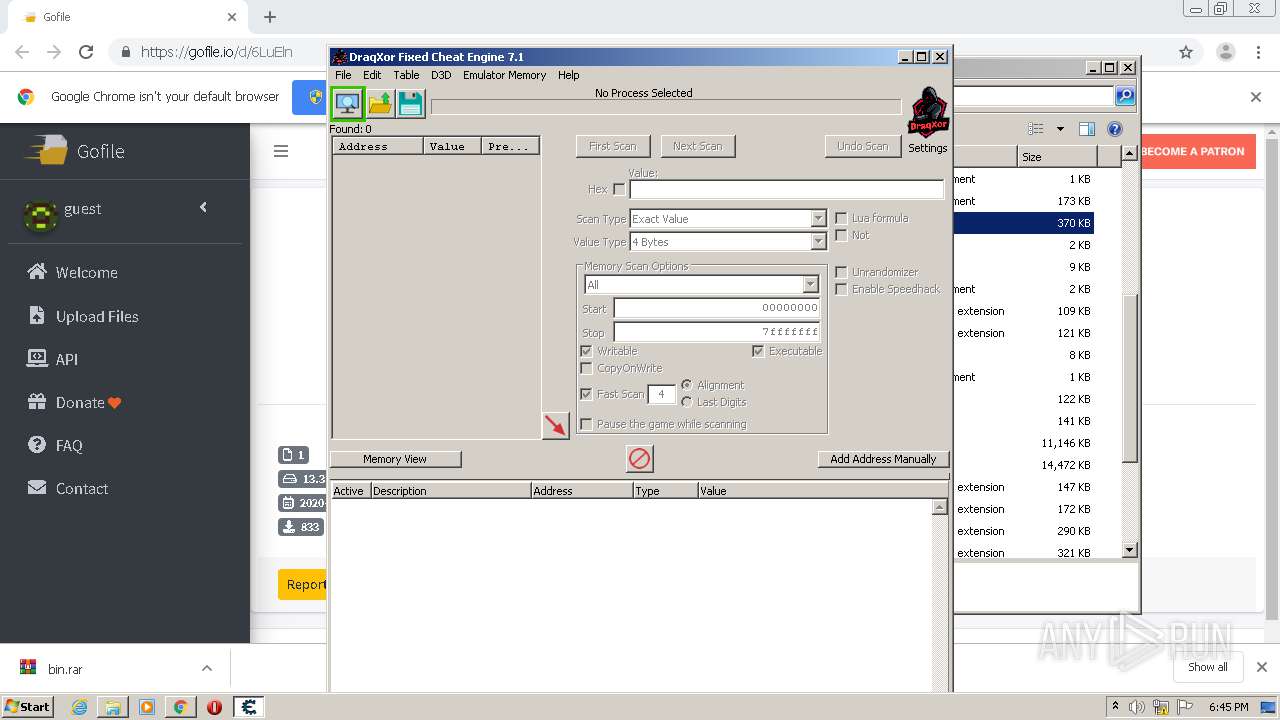
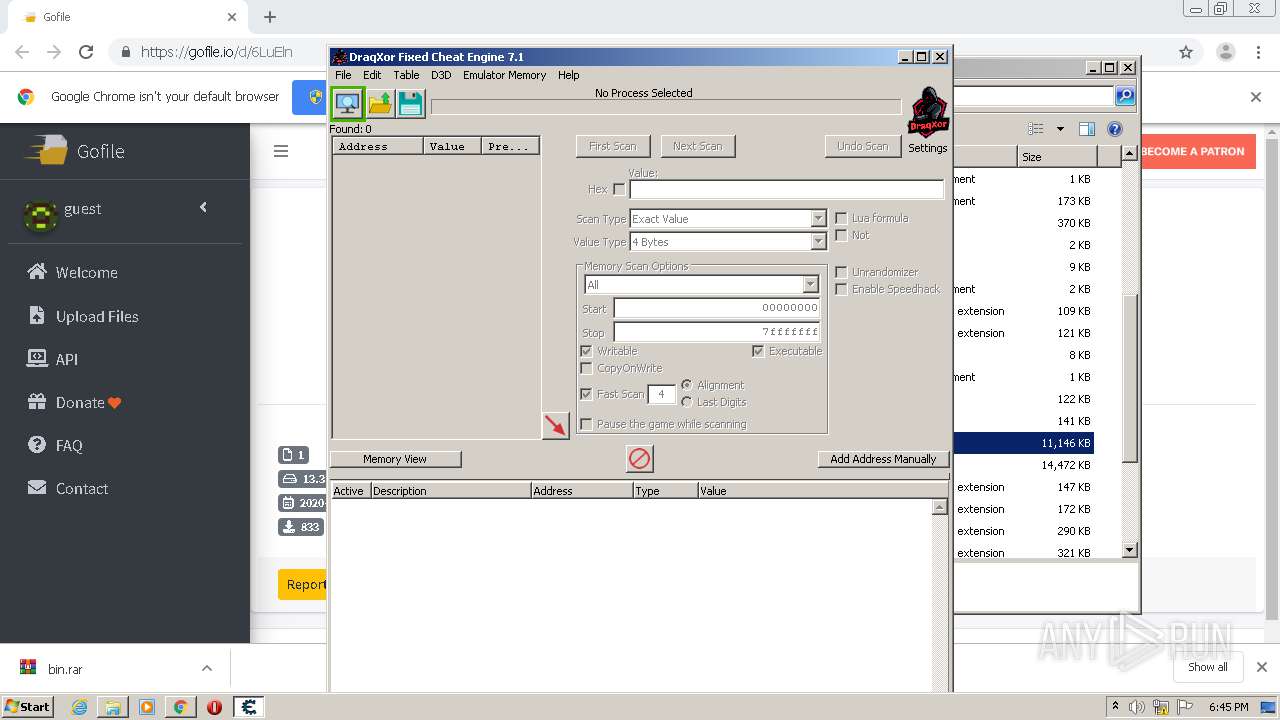
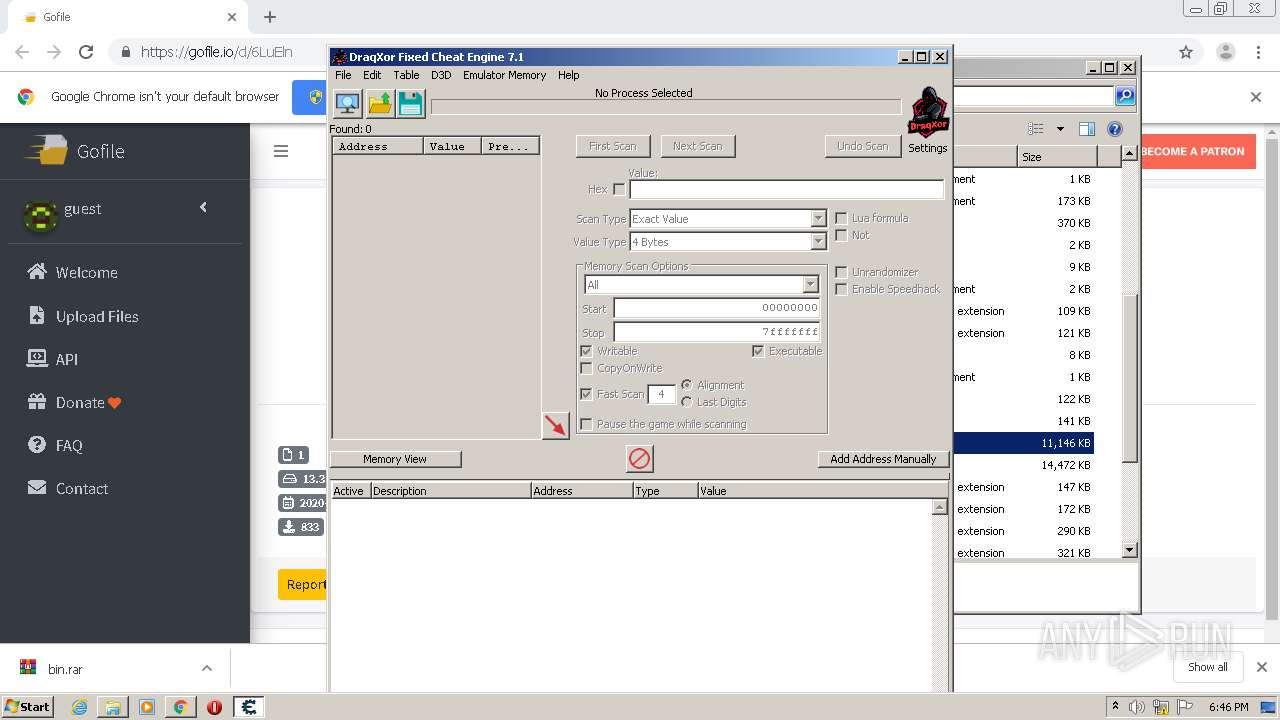
MALICIOUS
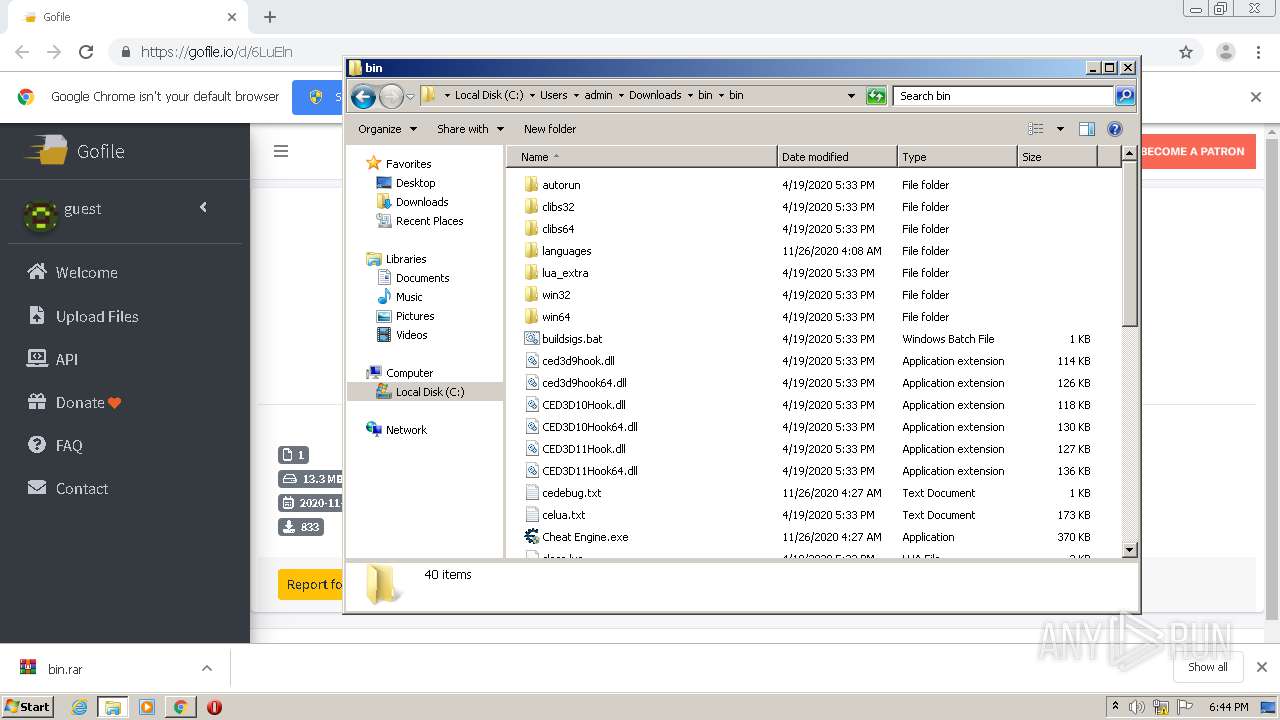
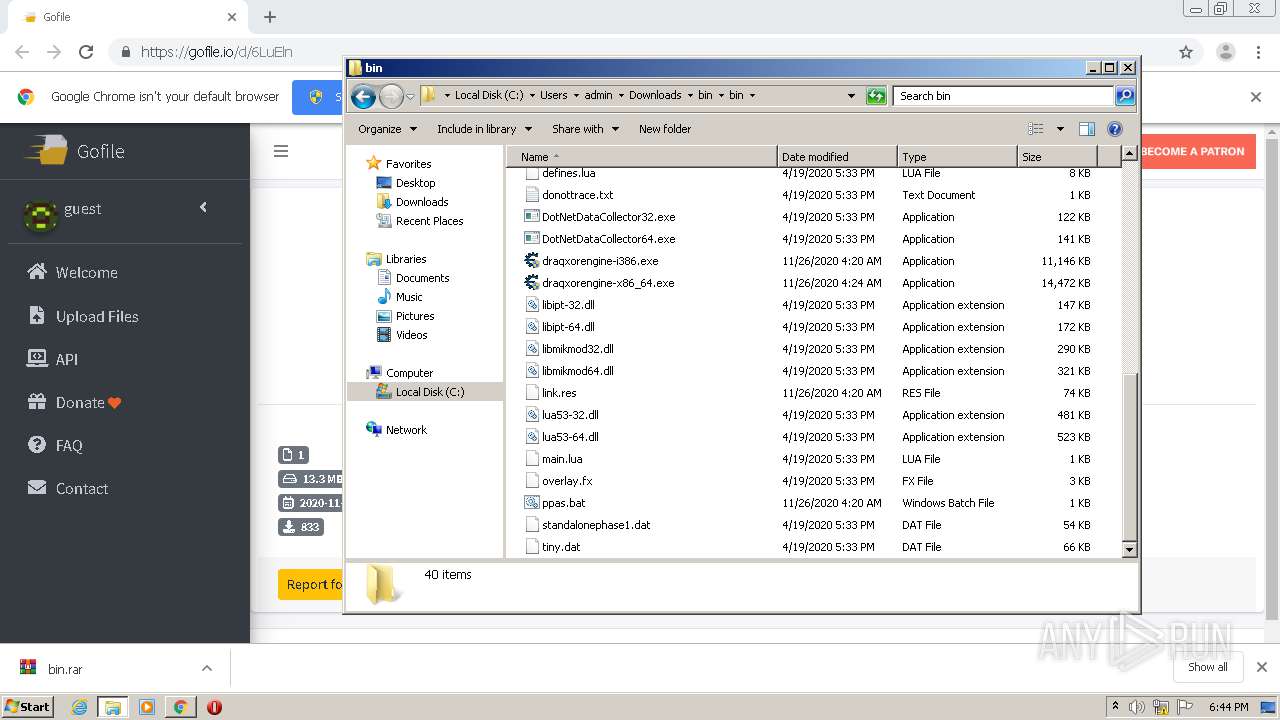
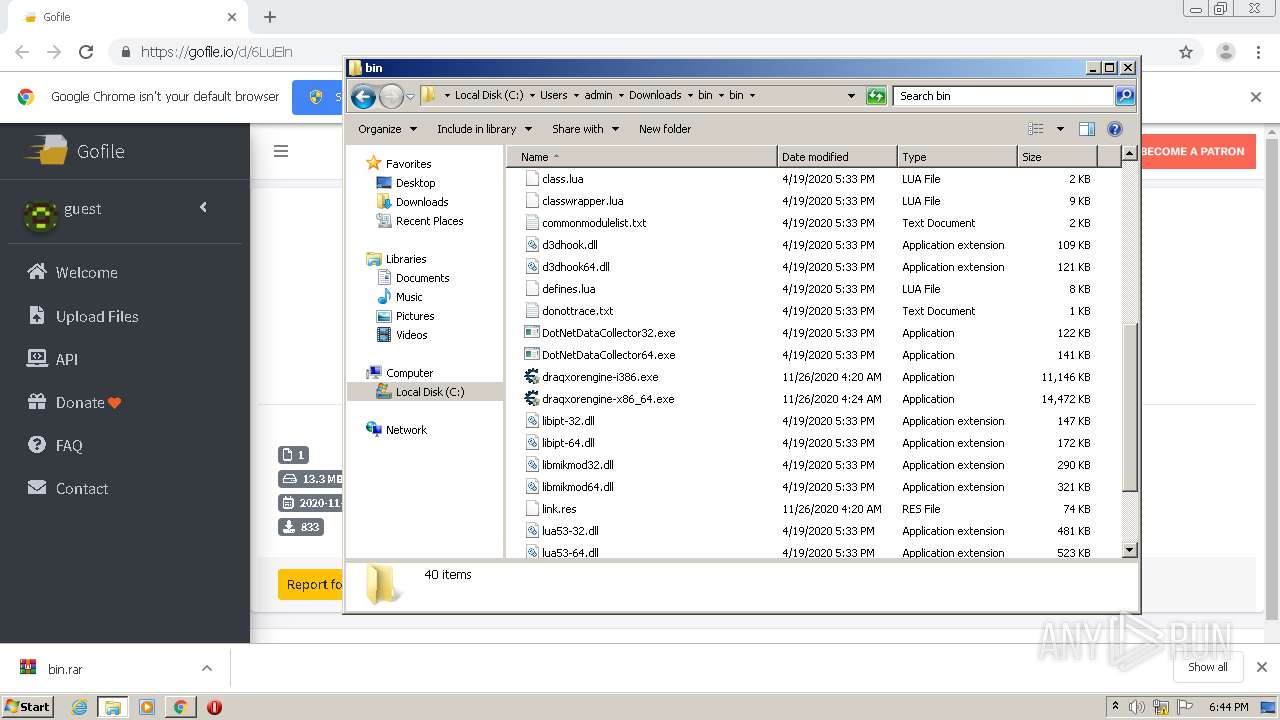
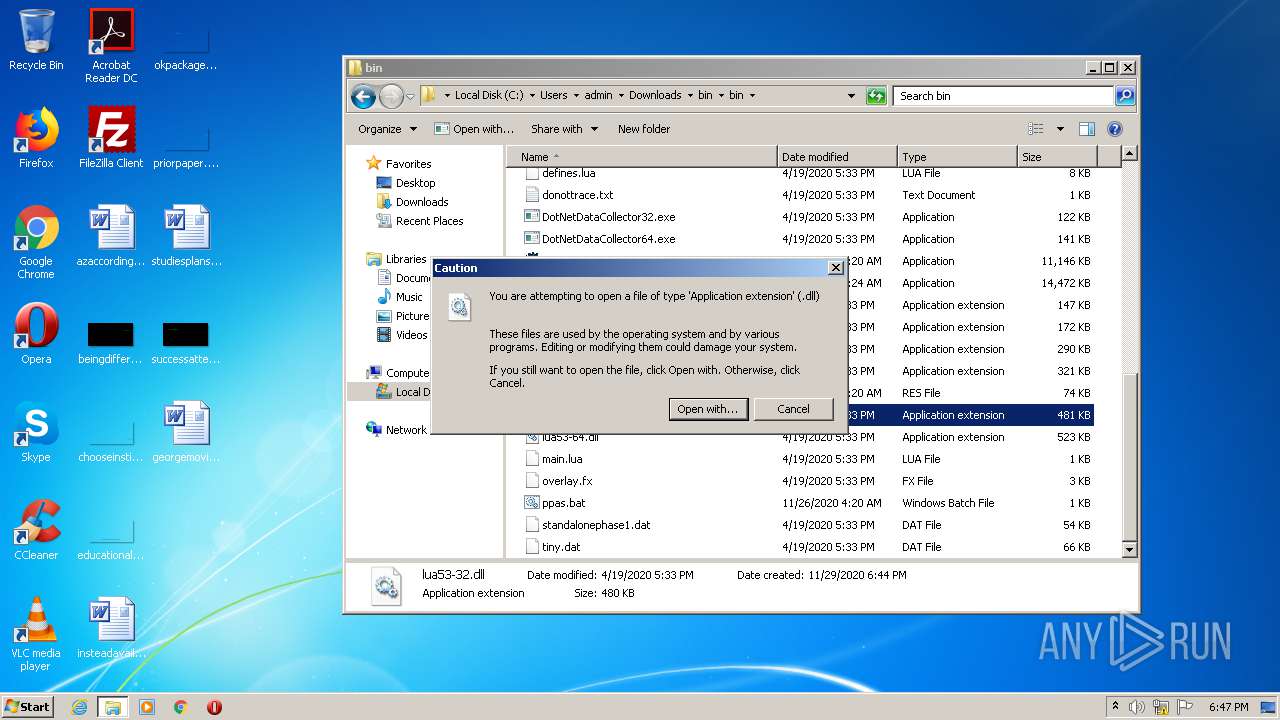
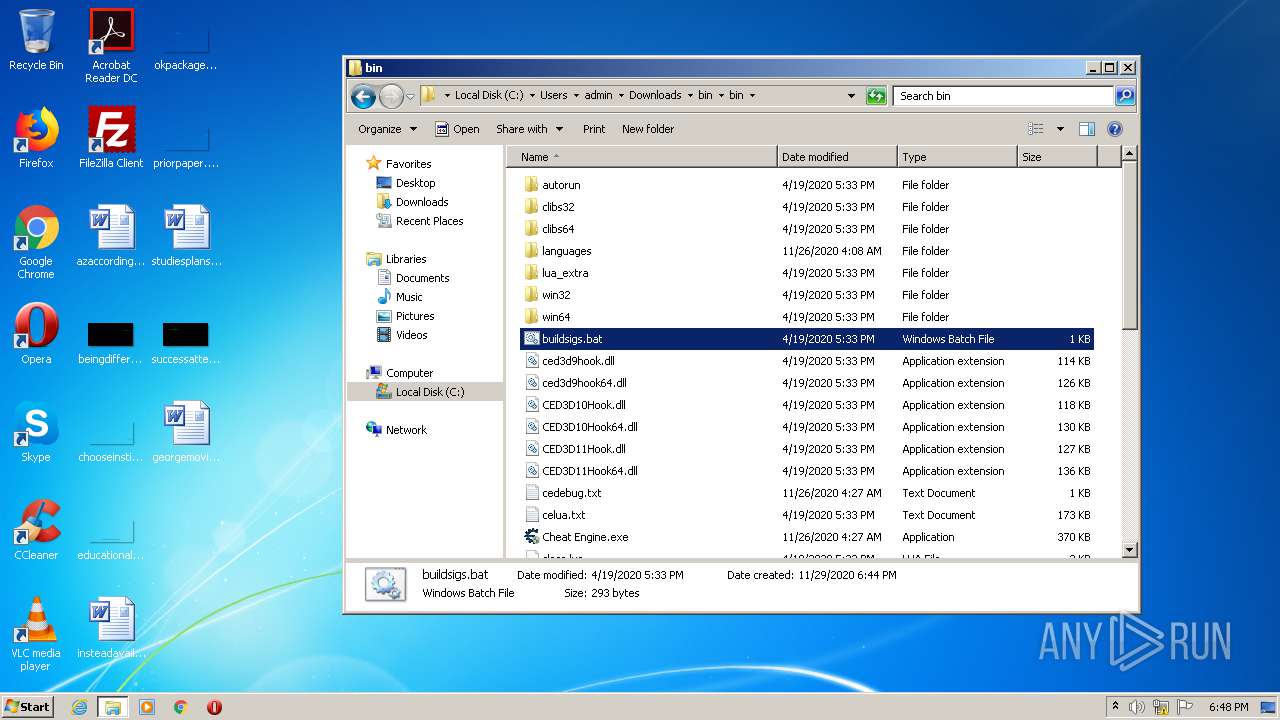
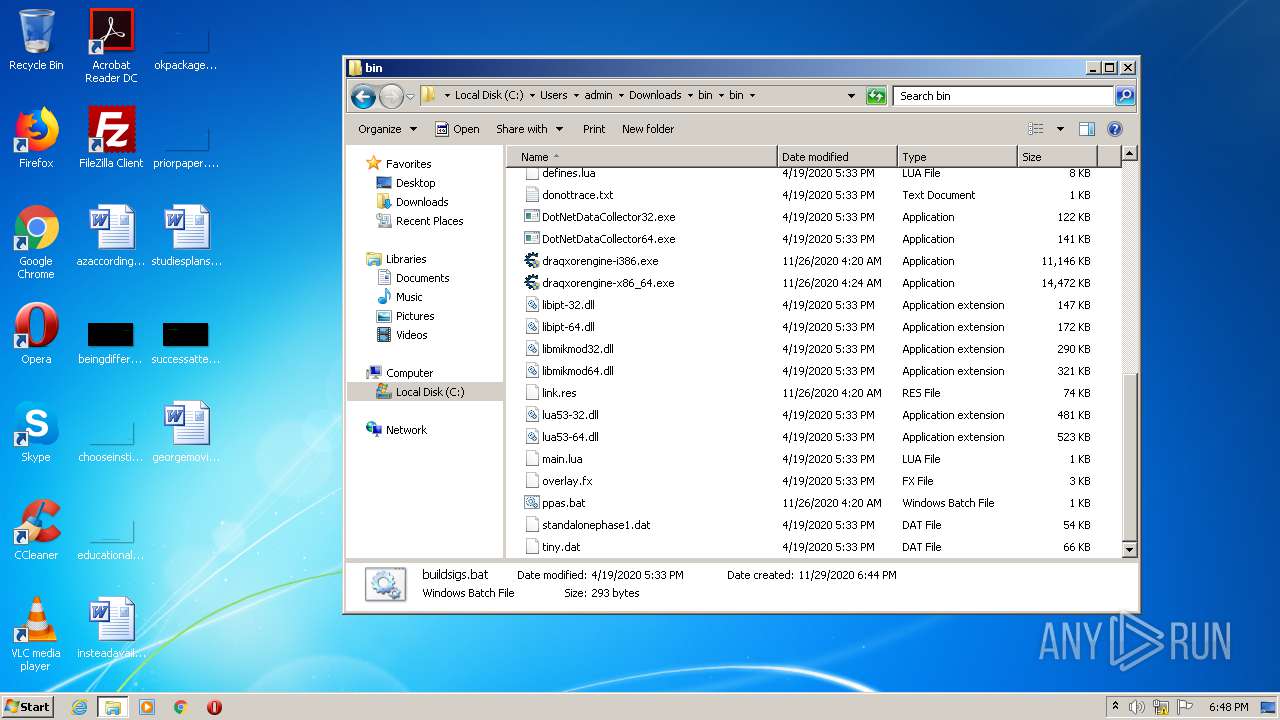
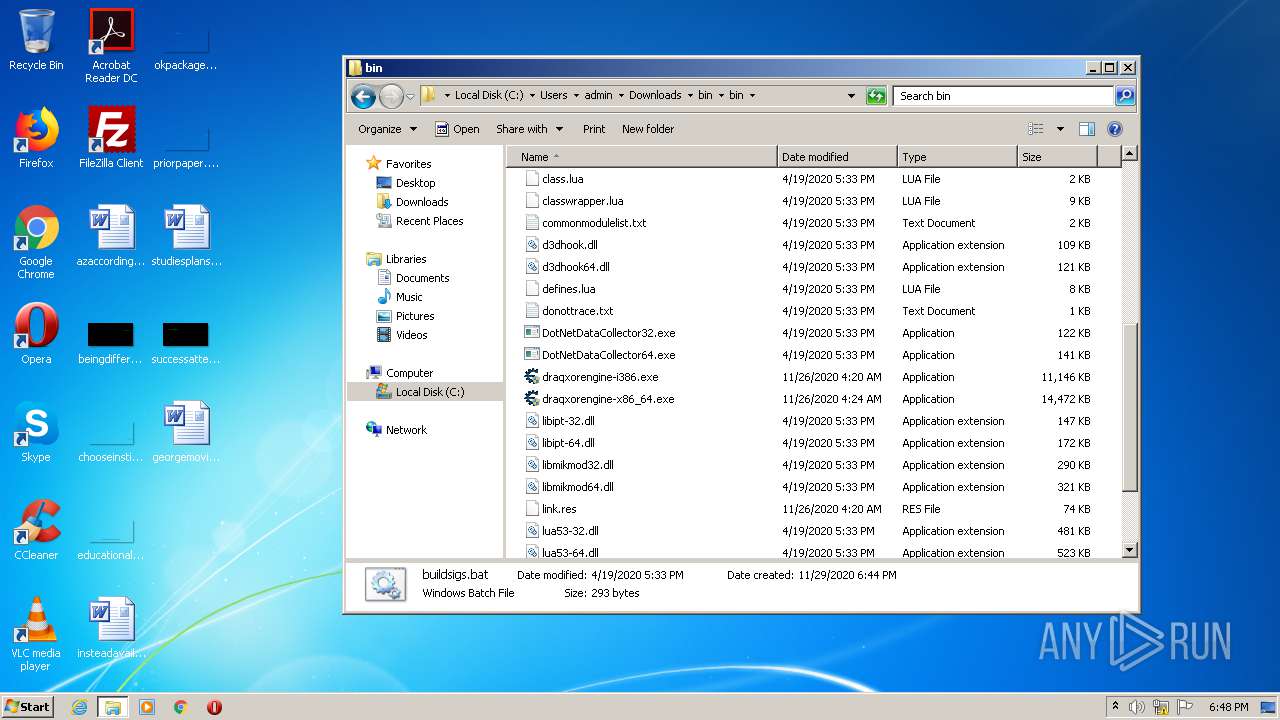
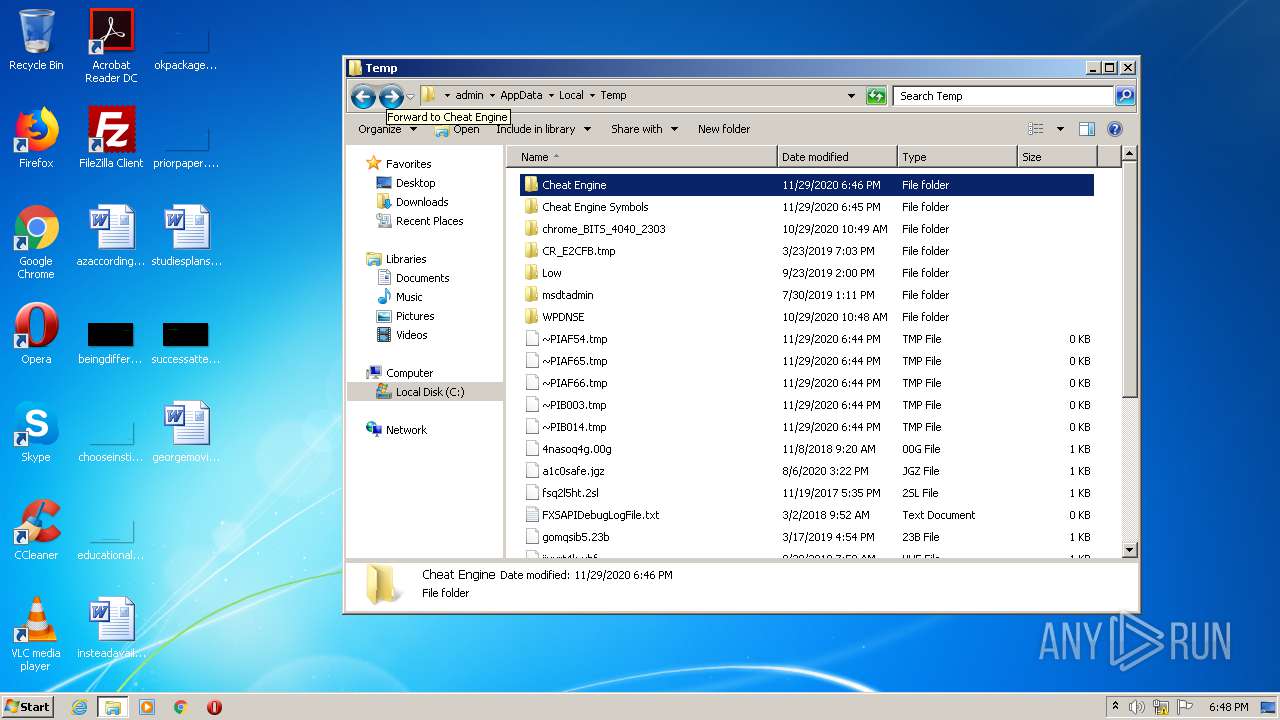
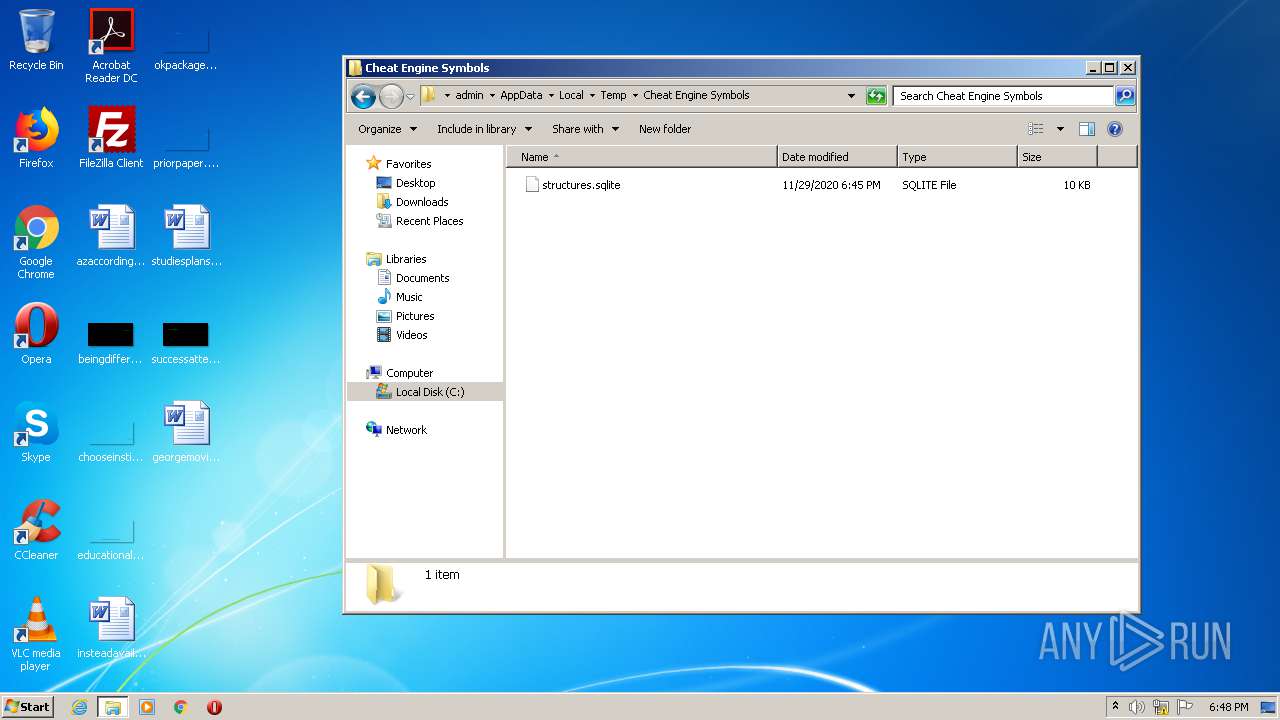
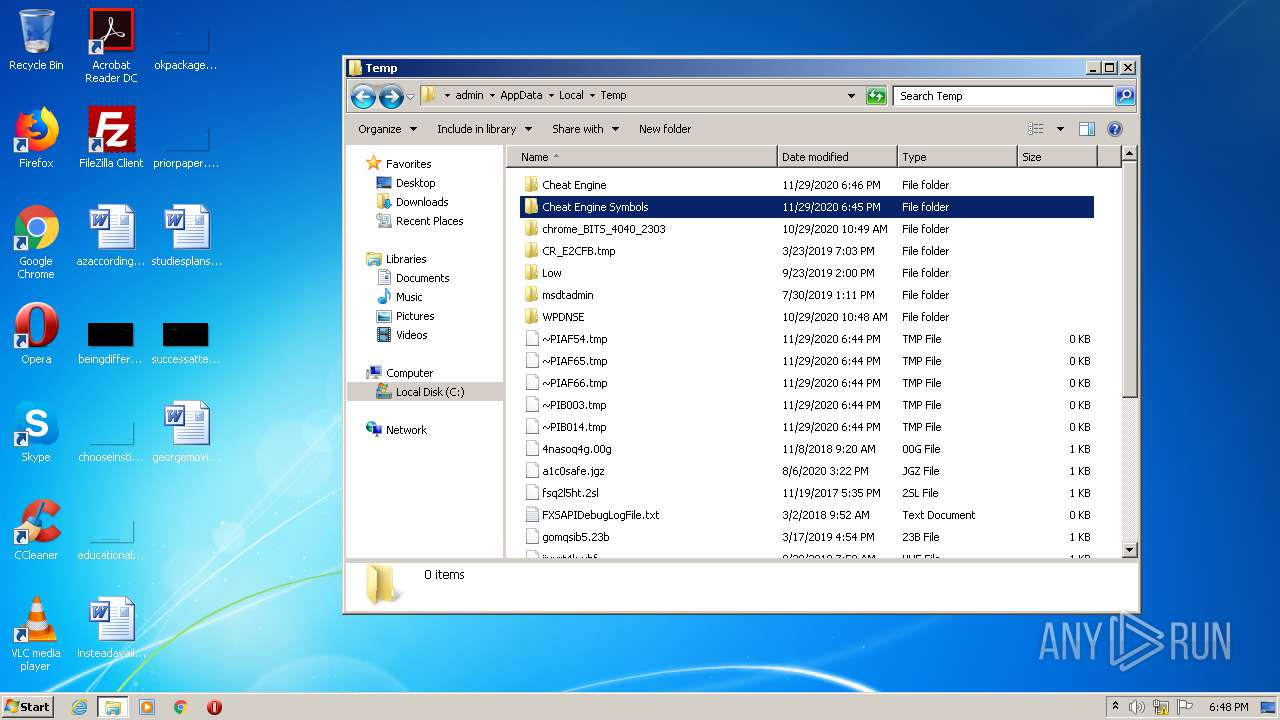
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3352)
- draqxorengine-i386.exe (PID: 3228)
- draqxorengine-i386.exe (PID: 2460)
- explorer.exe (PID: 356)
- draqxorengine-i386.exe (PID: 2860)
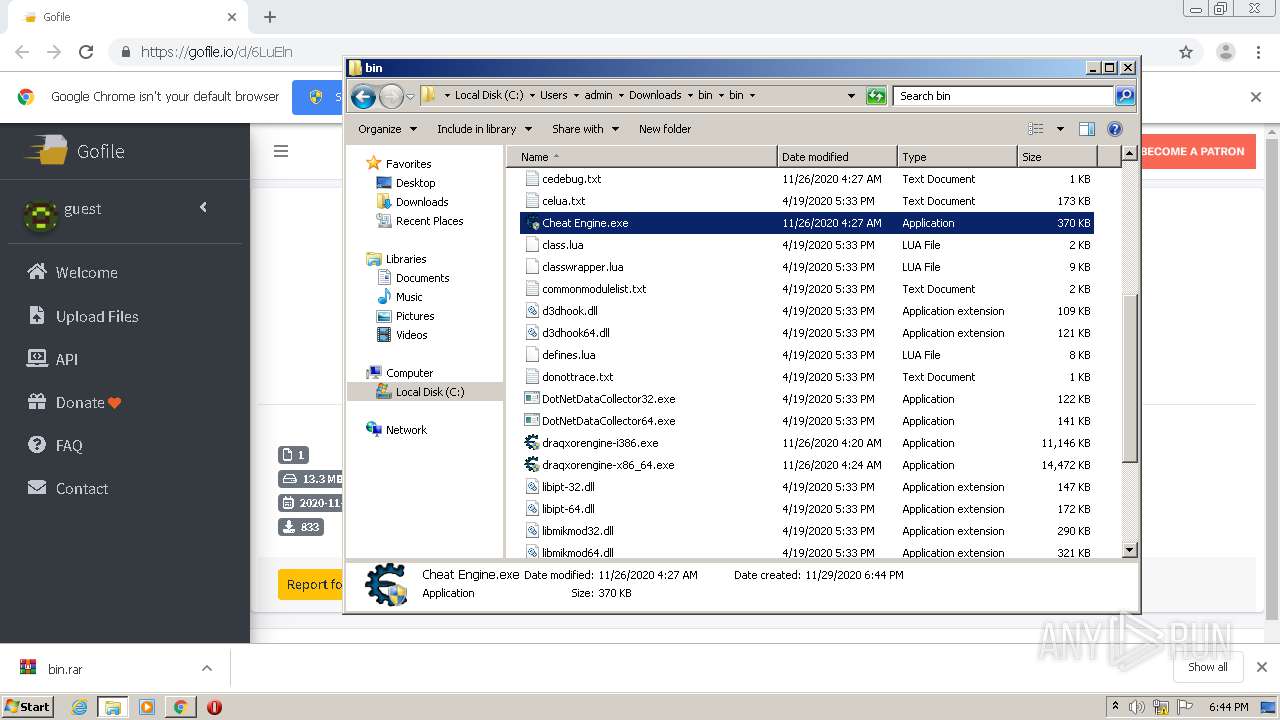
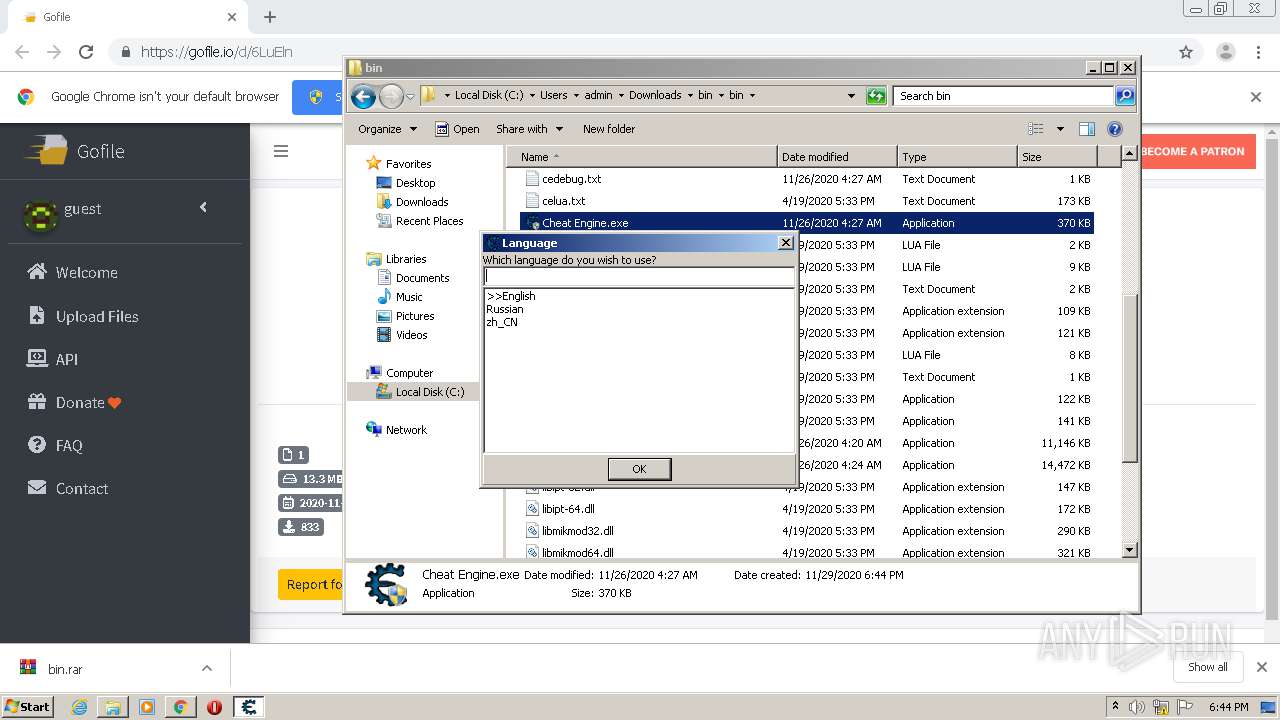
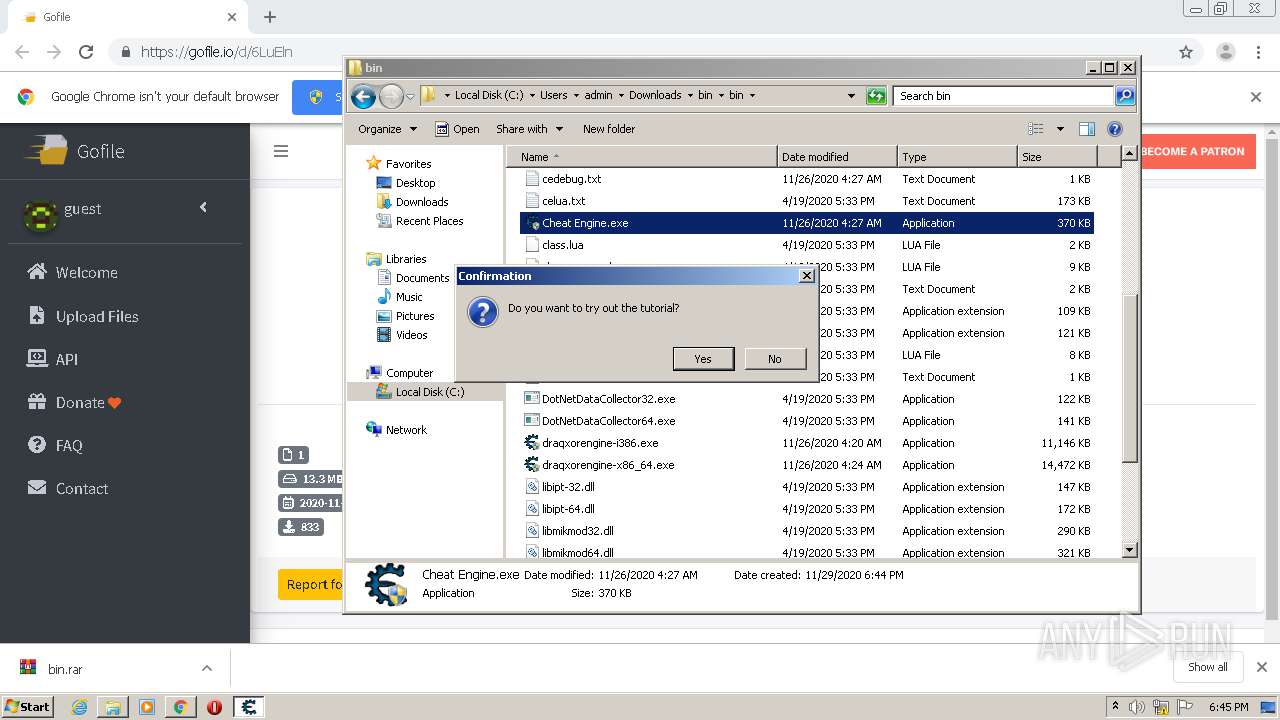
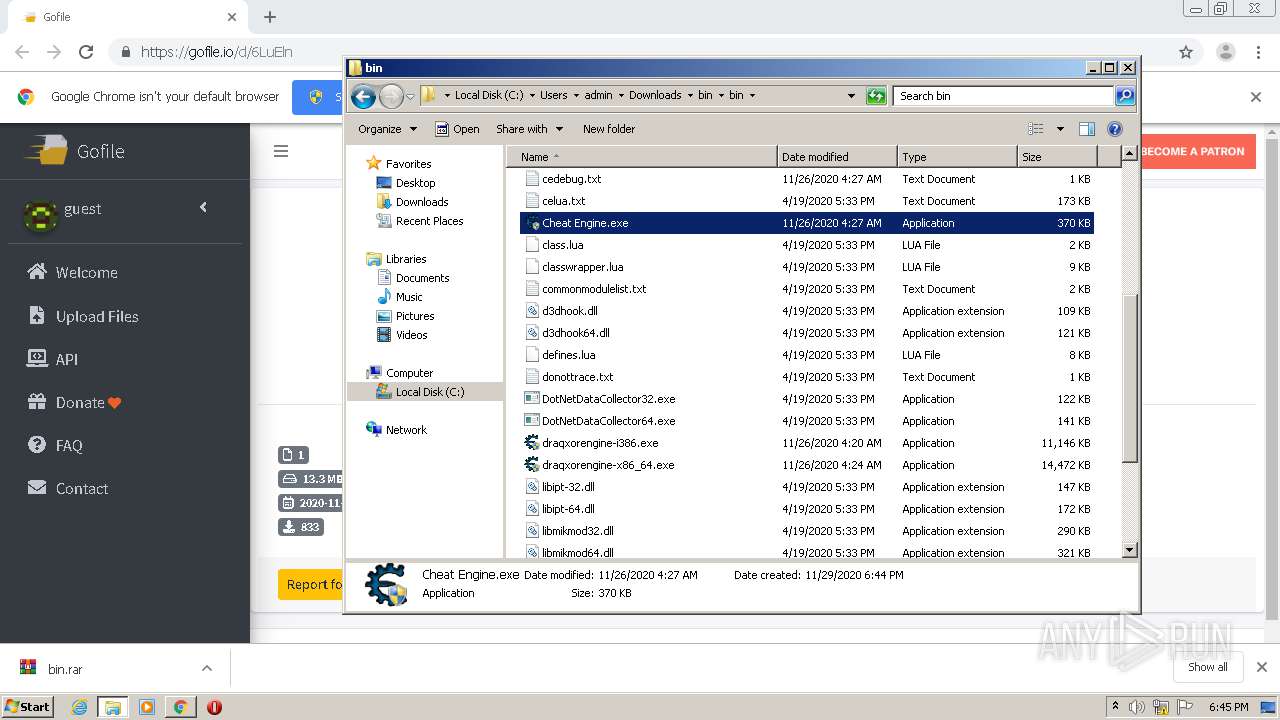
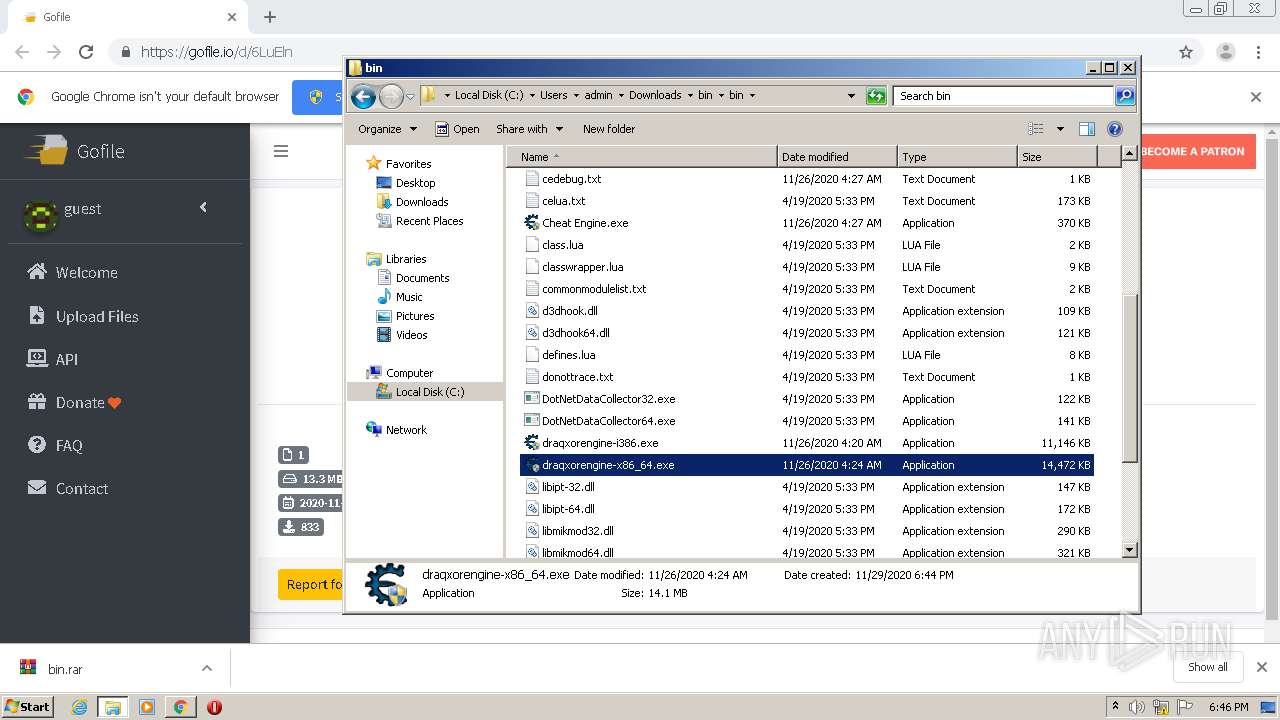
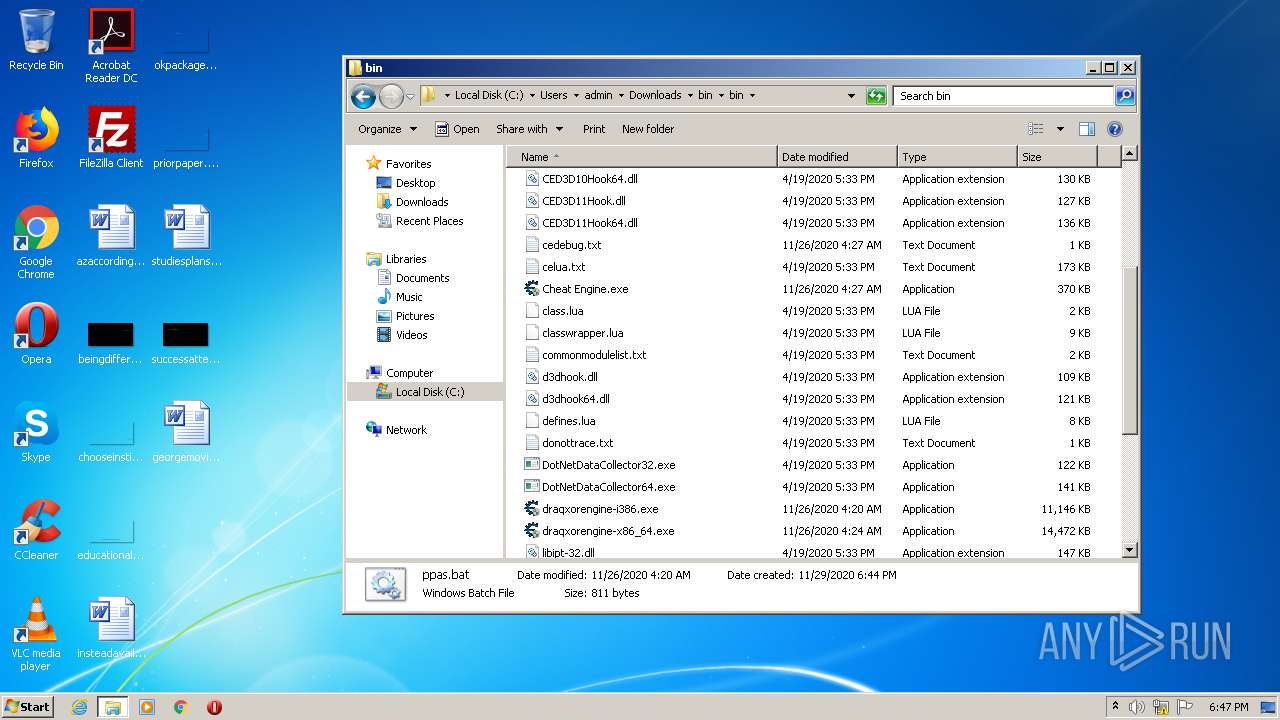
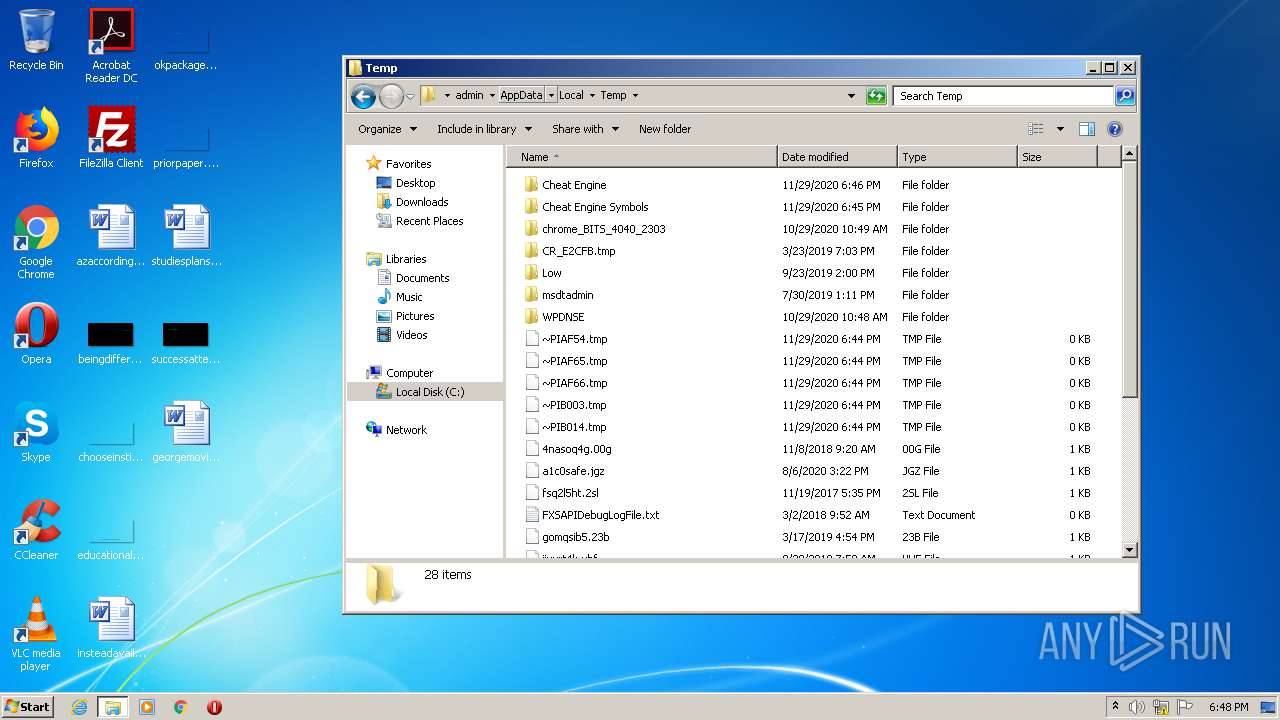
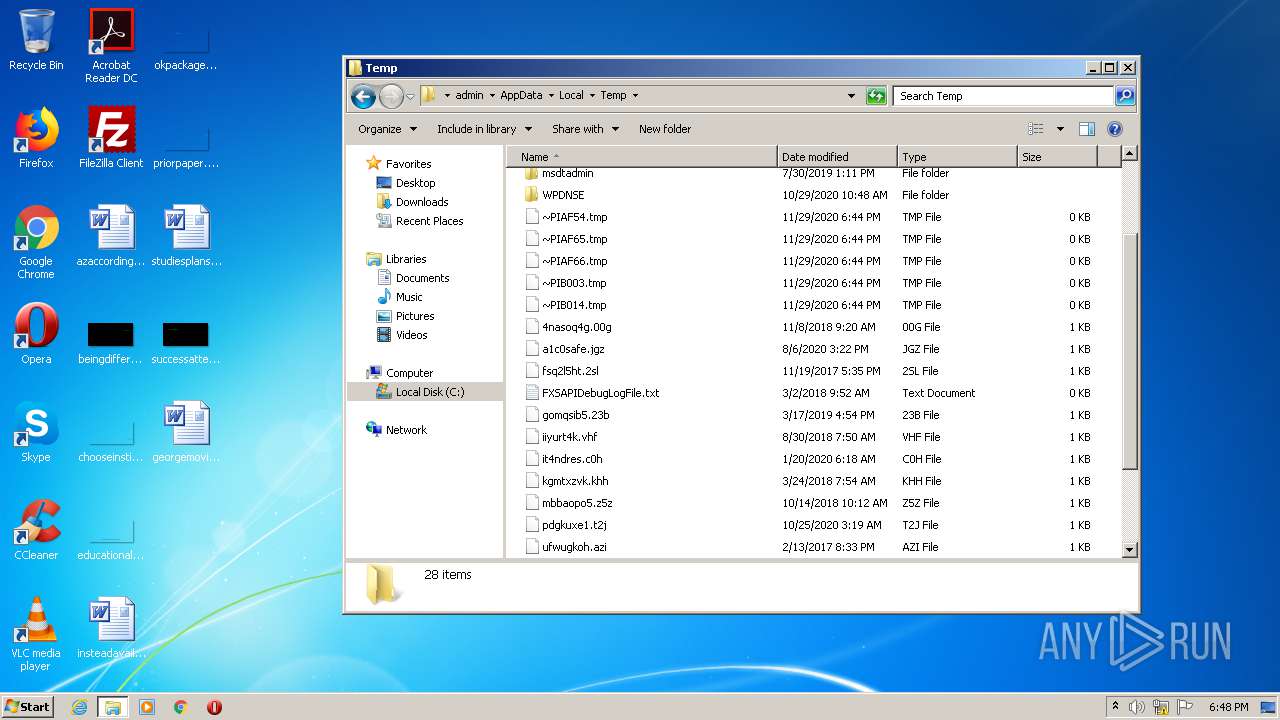
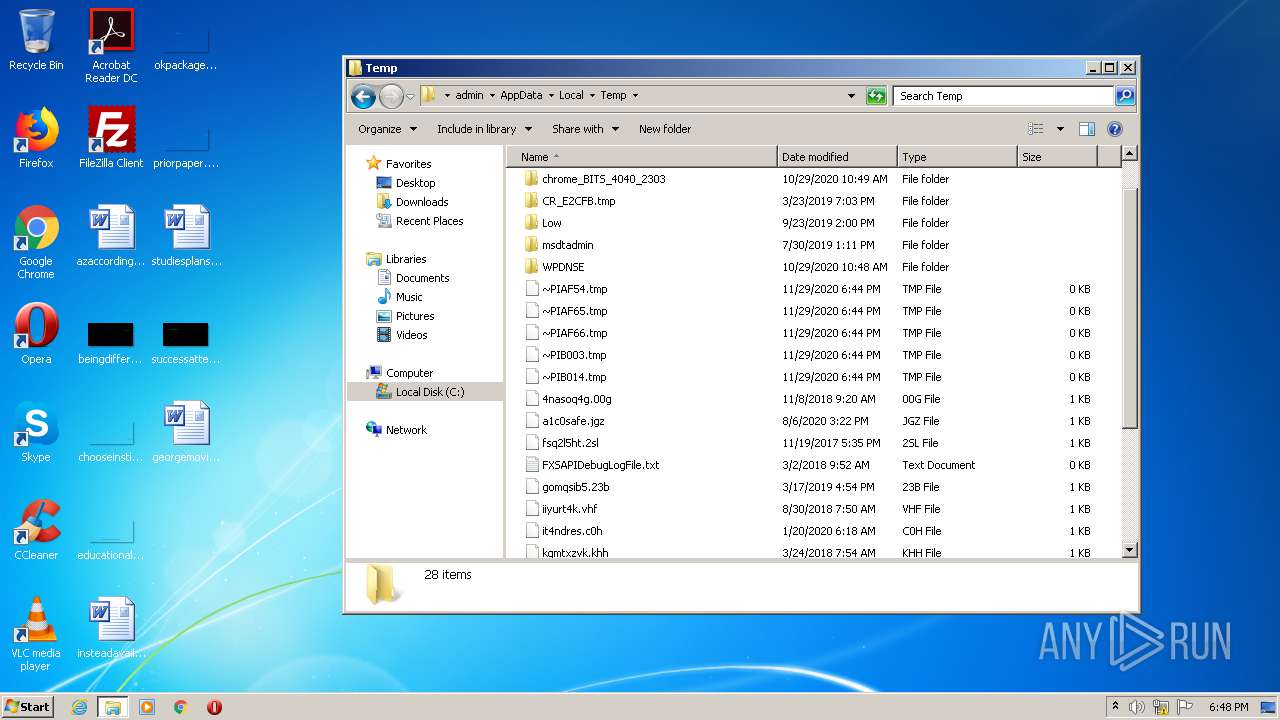
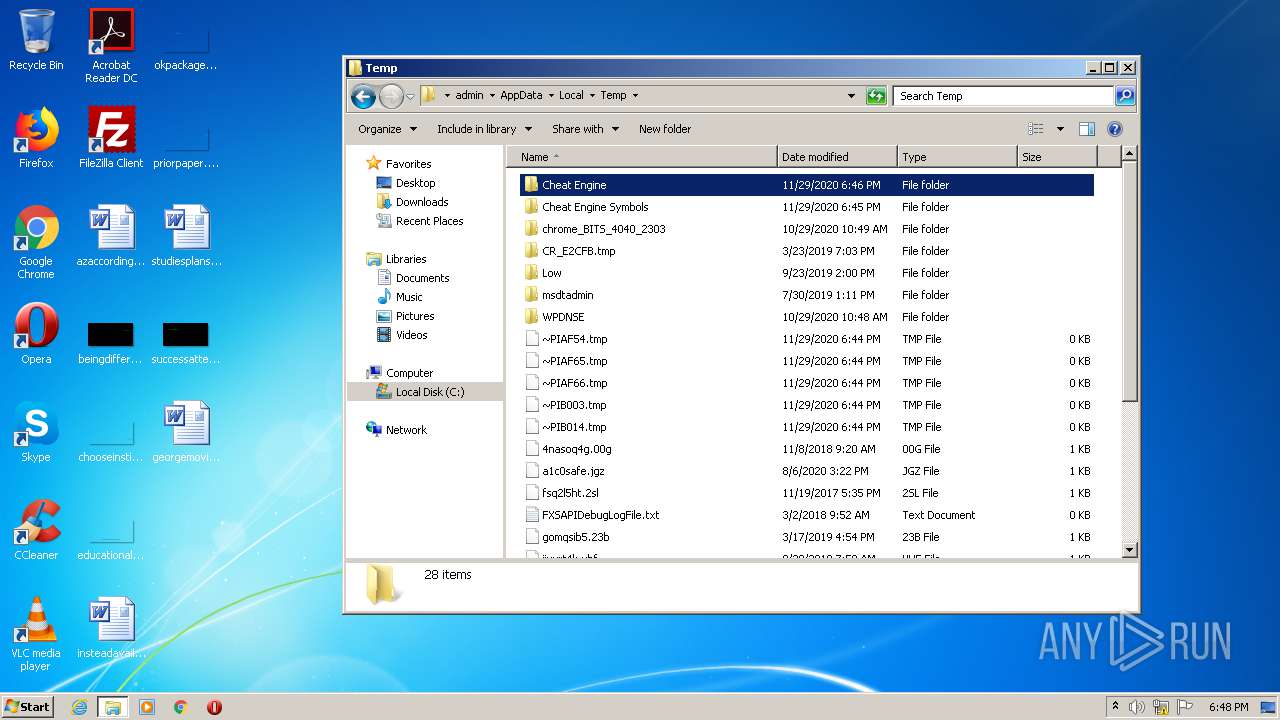
Application was dropped or rewritten from another process
- Cheat Engine.exe (PID: 2916)
- Cheat Engine.exe (PID: 2748)
- draqxorengine-i386.exe (PID: 3228)
- draqxorengine-i386.exe (PID: 2492)
- draqxorengine-i386.exe (PID: 2536)
- draqxorengine-i386.exe (PID: 2860)
- draqxorengine-i386.exe (PID: 2460)
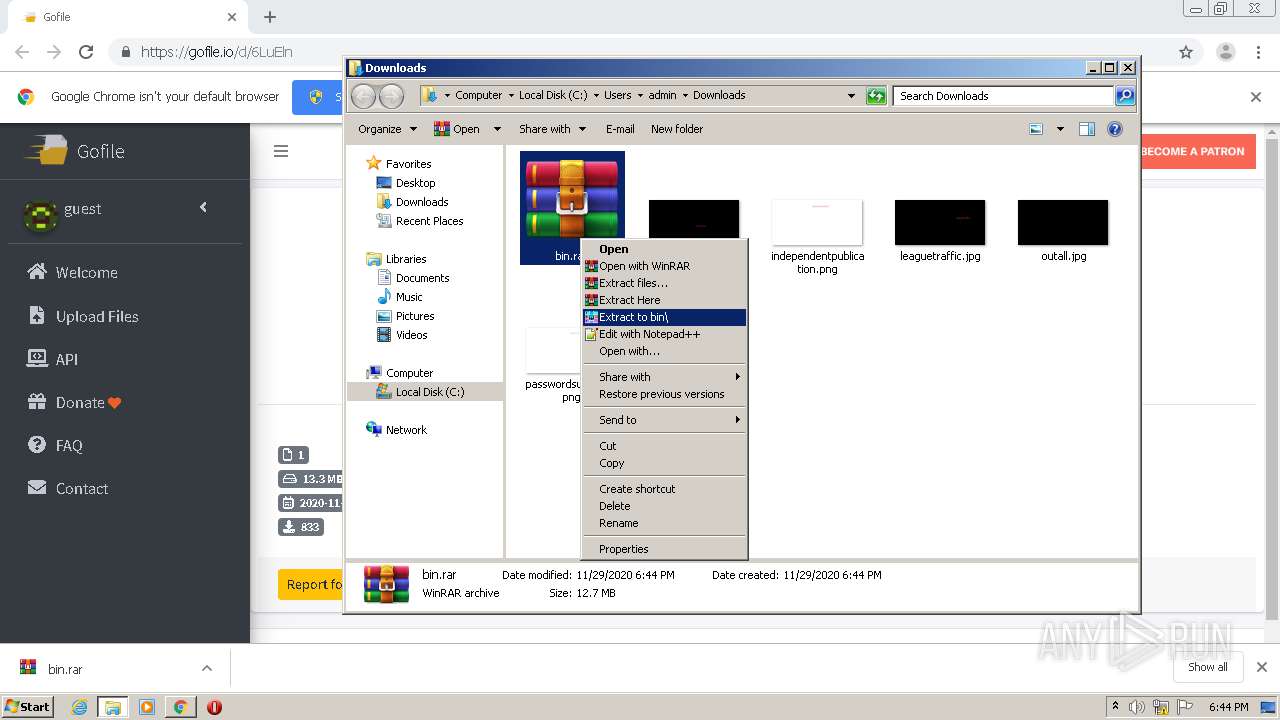
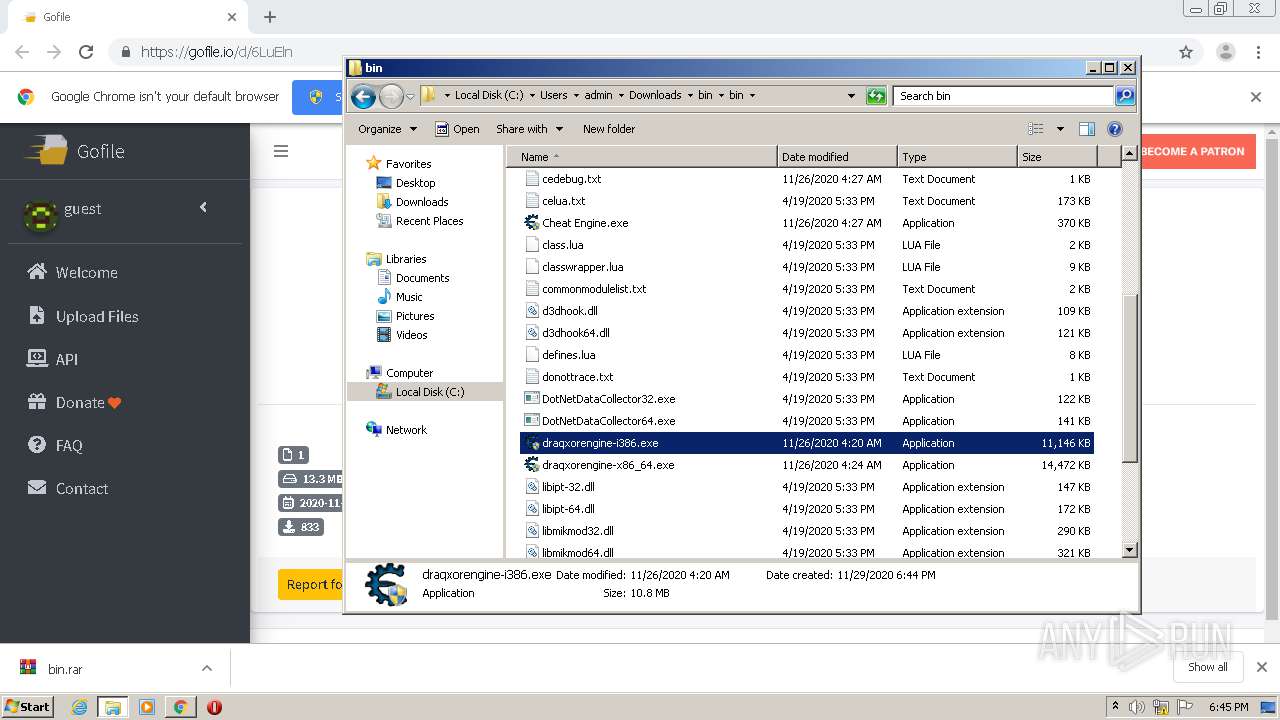
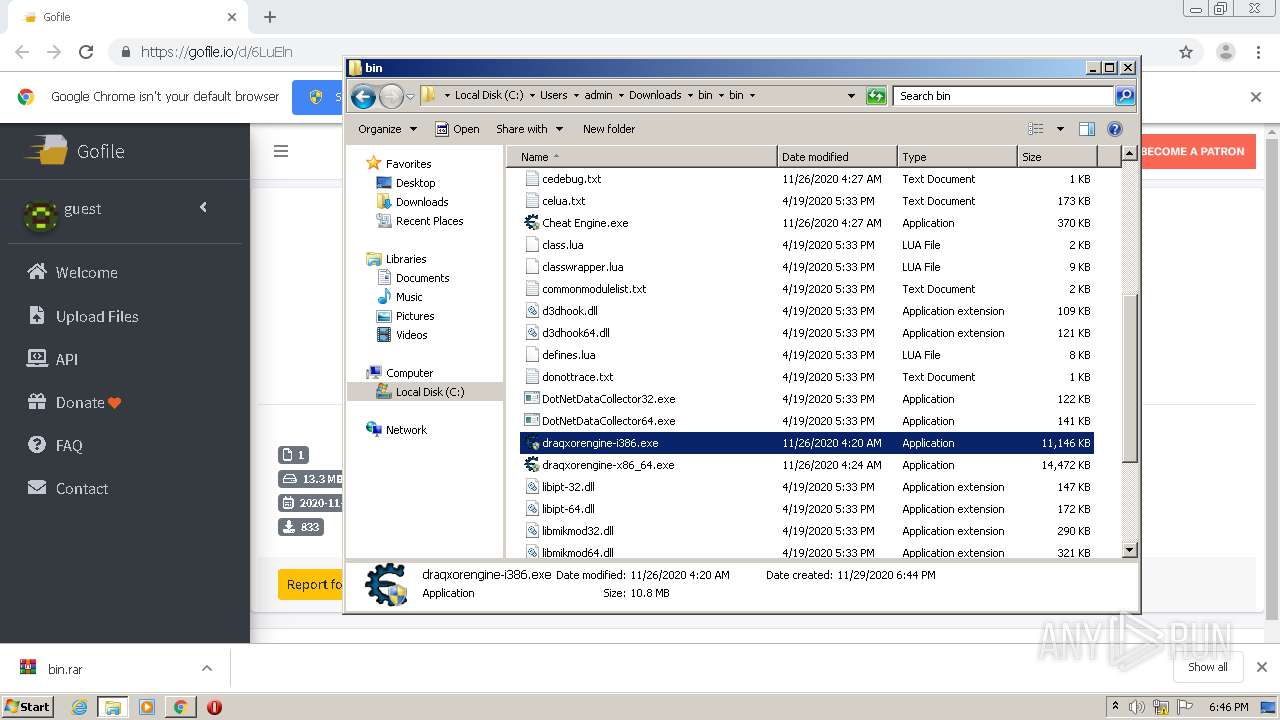
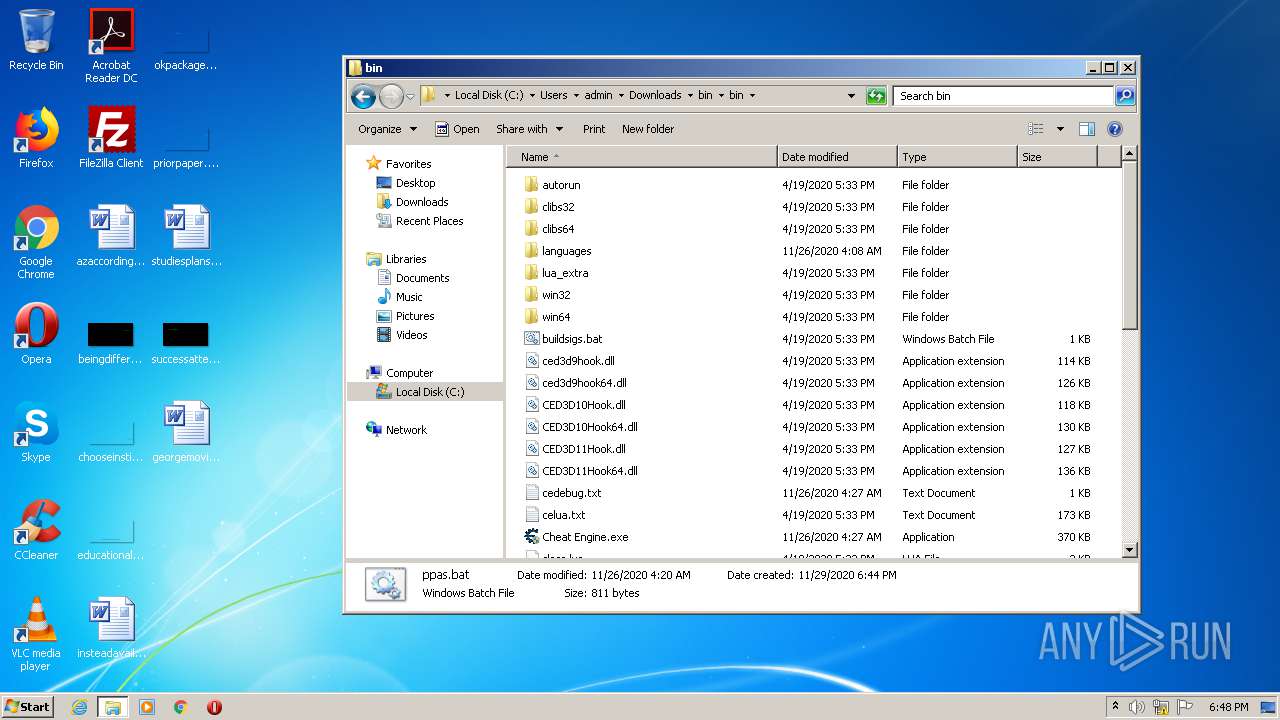
Drops executable file immediately after starts
- WinRAR.exe (PID: 784)
SUSPICIOUS
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 784)
Creates files in the user directory
- explorer.exe (PID: 356)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 784)
Drops a file with too old compile date
- WinRAR.exe (PID: 784)
Executed via COM
- DllHost.exe (PID: 2192)
- DllHost.exe (PID: 2884)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 356)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 356)
Reads default file associations for system extensions
- explorer.exe (PID: 356)
INFO
Application launched itself
- chrome.exe (PID: 2620)
Reads the hosts file
- chrome.exe (PID: 2620)
- chrome.exe (PID: 760)
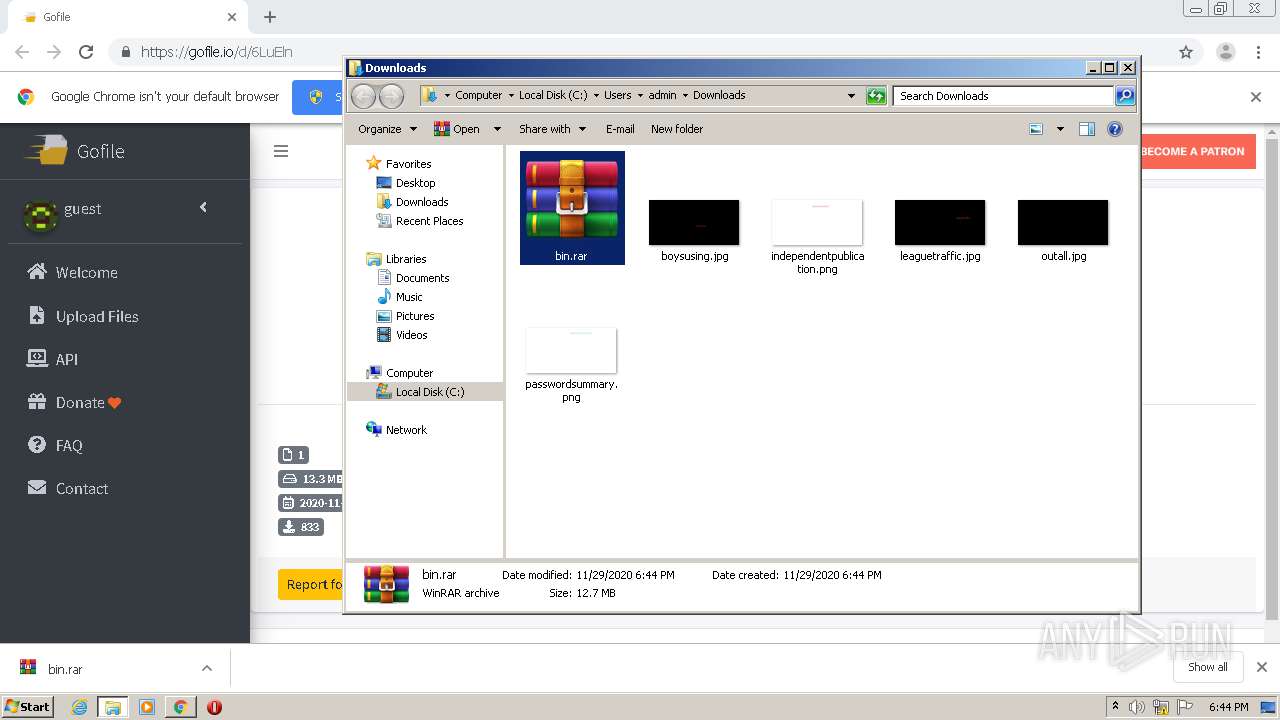
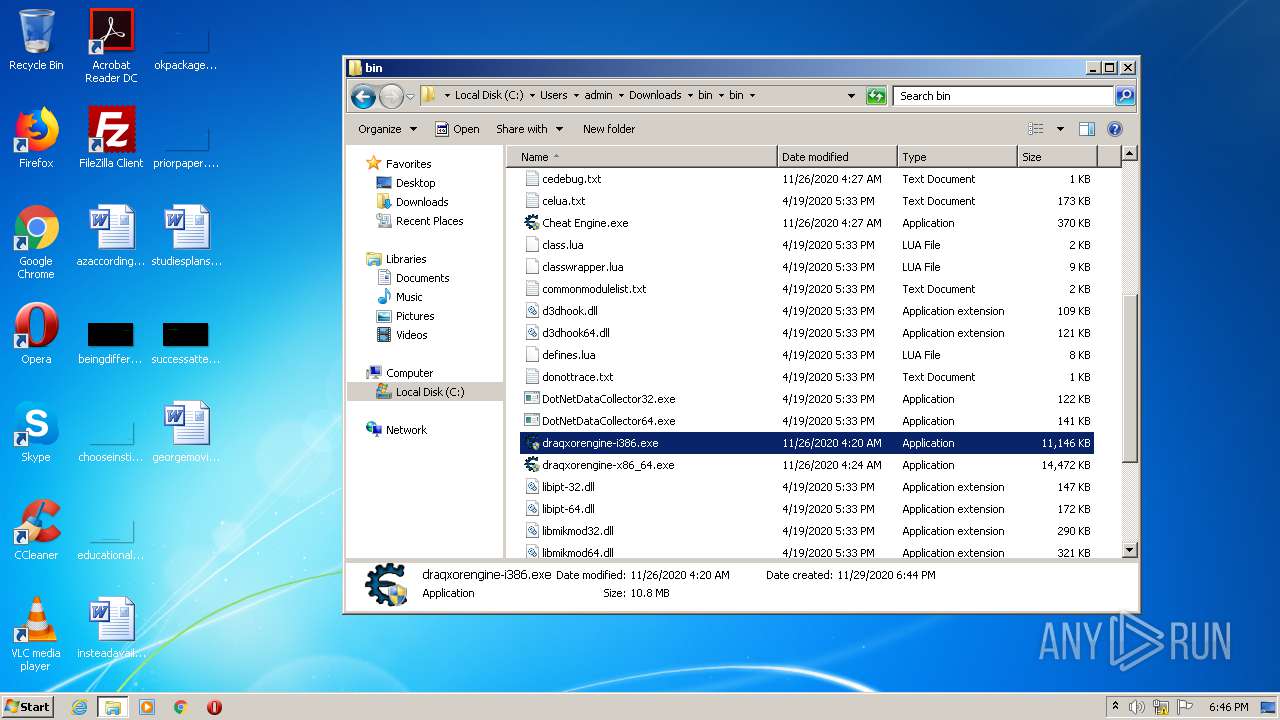
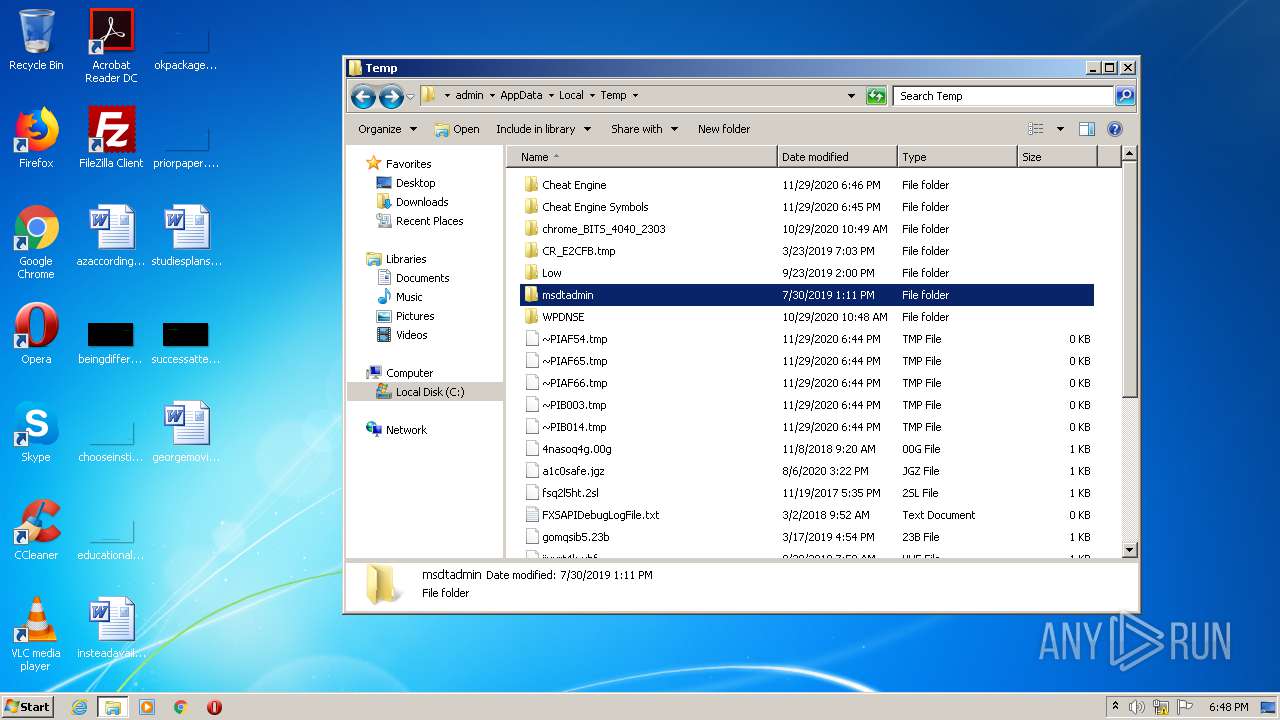
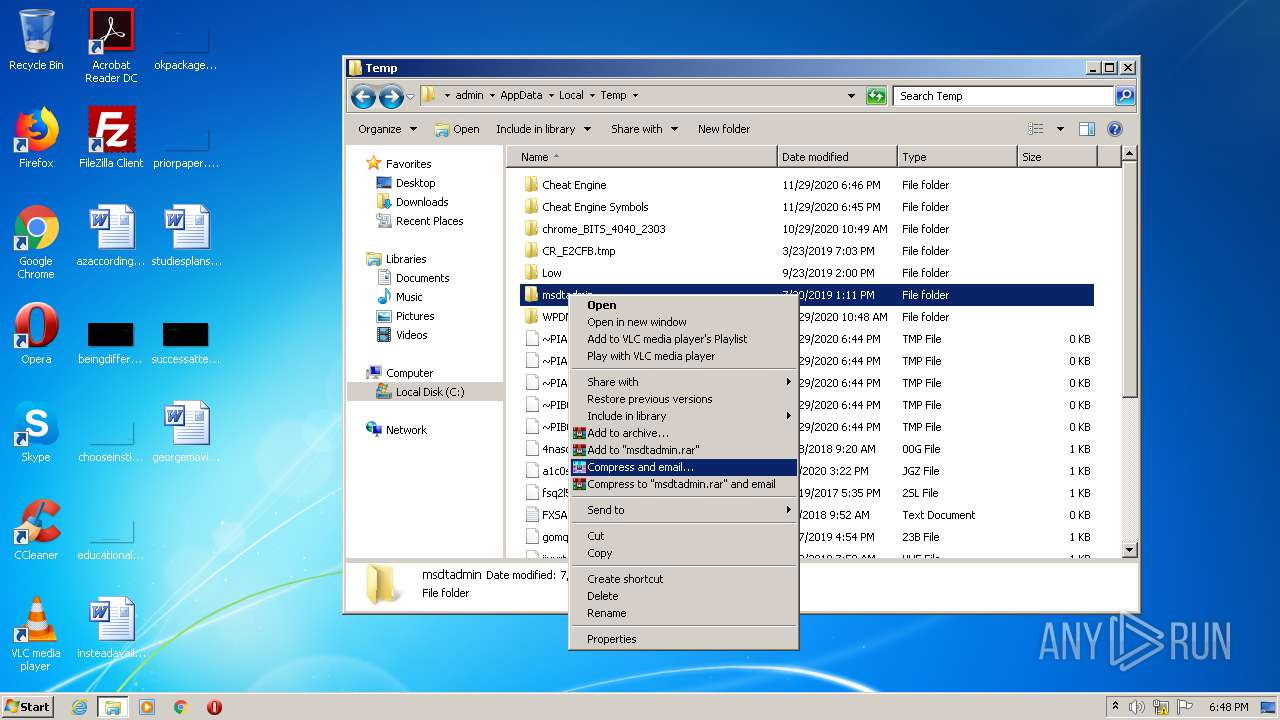
Manual execution by user
- WinRAR.exe (PID: 784)
- Cheat Engine.exe (PID: 2916)
- Cheat Engine.exe (PID: 2748)
- draqxorengine-i386.exe (PID: 2860)
- draqxorengine-i386.exe (PID: 2492)
- draqxorengine-i386.exe (PID: 2536)
- draqxorengine-i386.exe (PID: 2460)
- rundll32.exe (PID: 3052)
Reads settings of System Certificates
- chrome.exe (PID: 760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
31
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
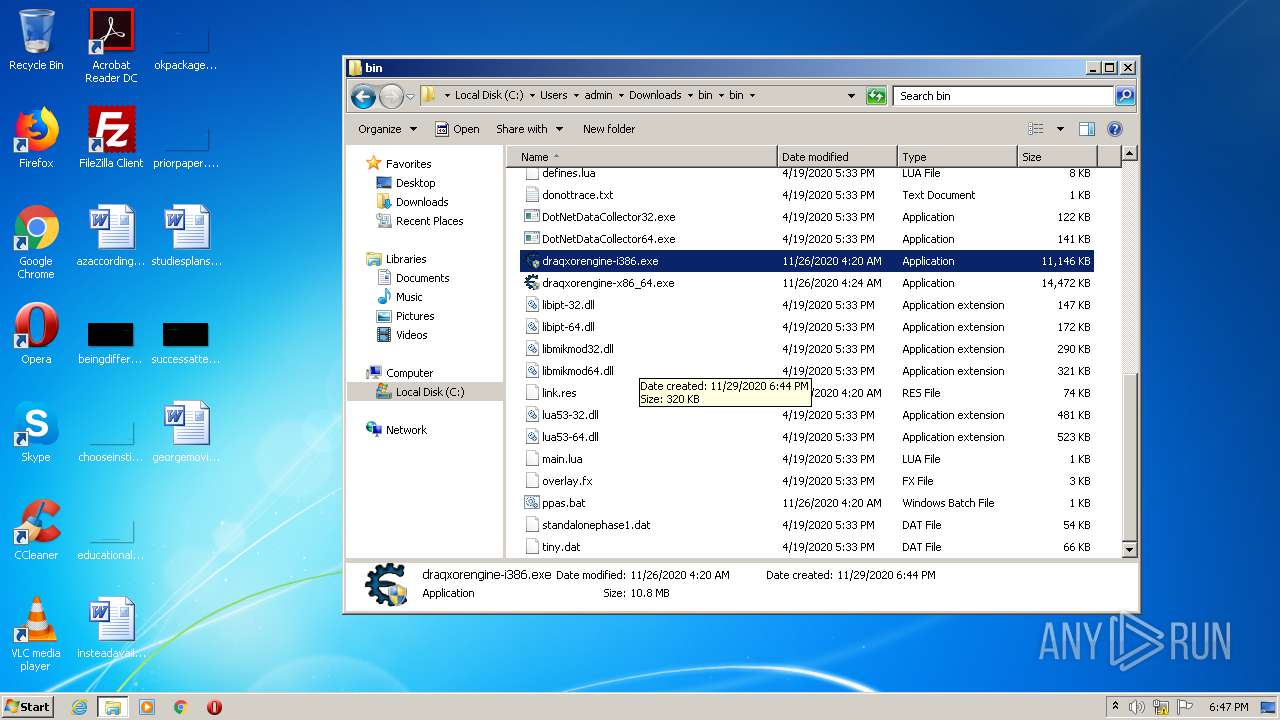
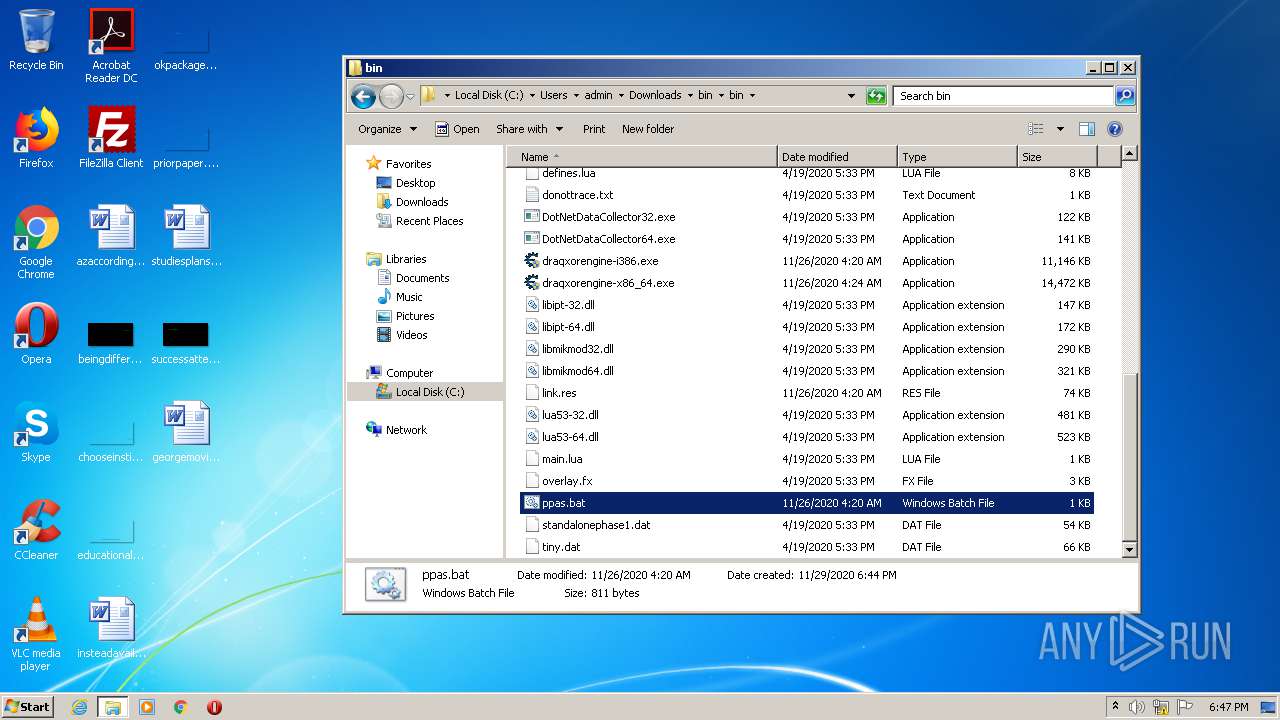
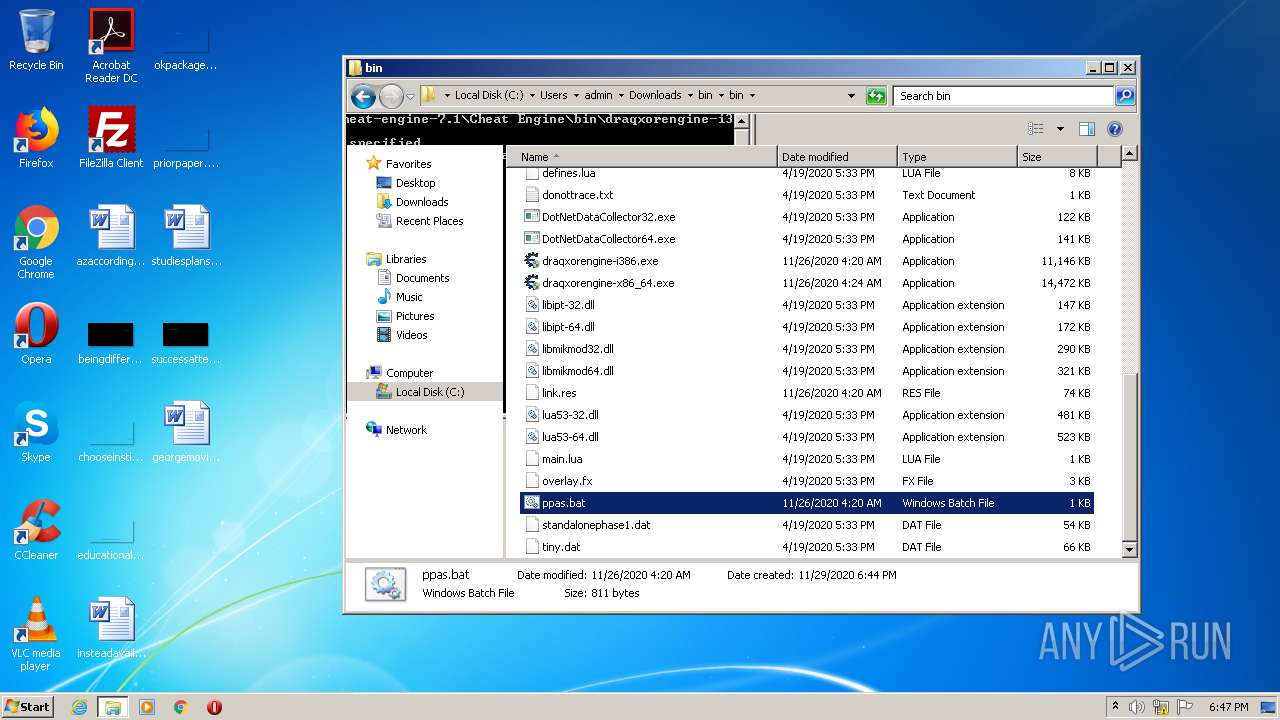
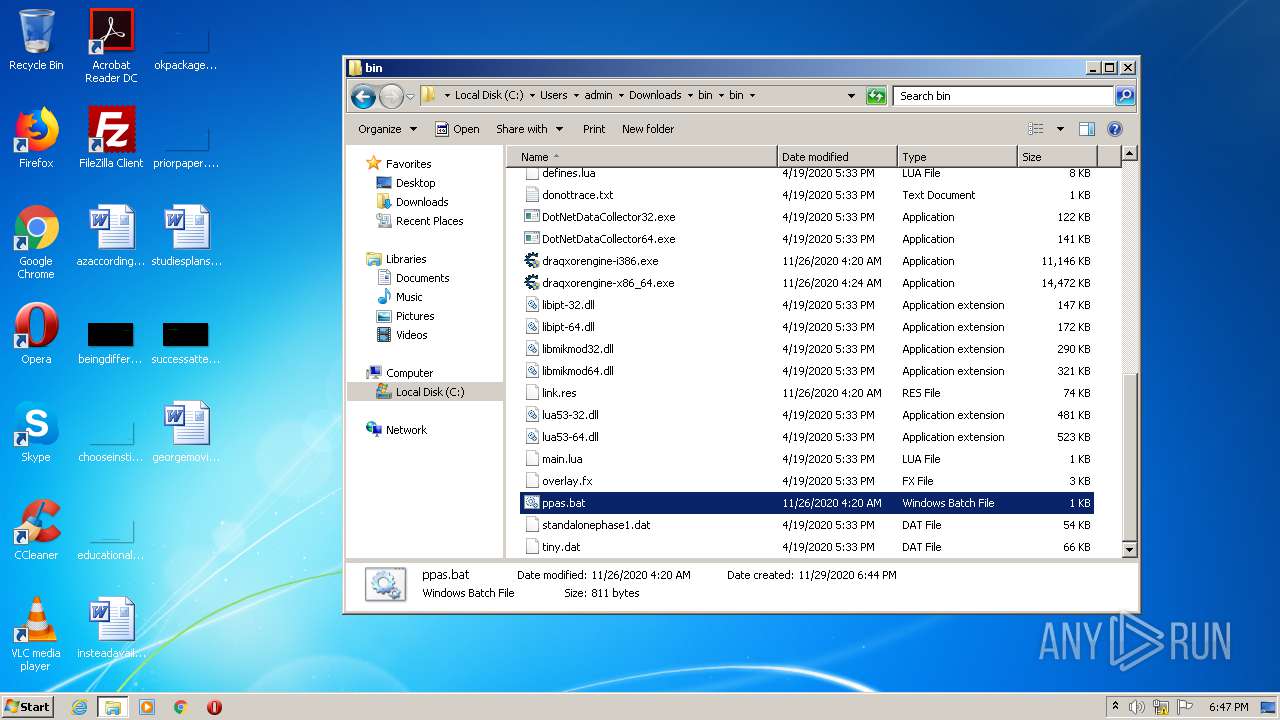
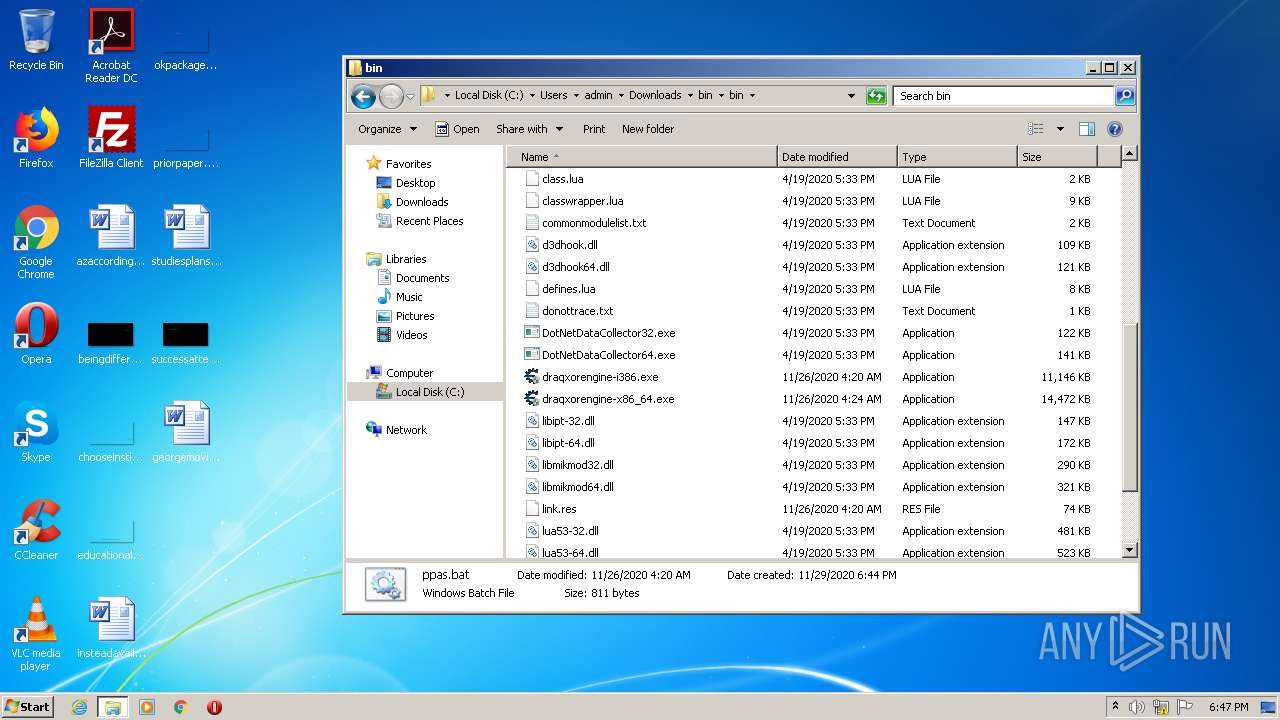
| 184 | cmd /c ""C:\Users\admin\Downloads\bin\bin\ppas.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 356 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
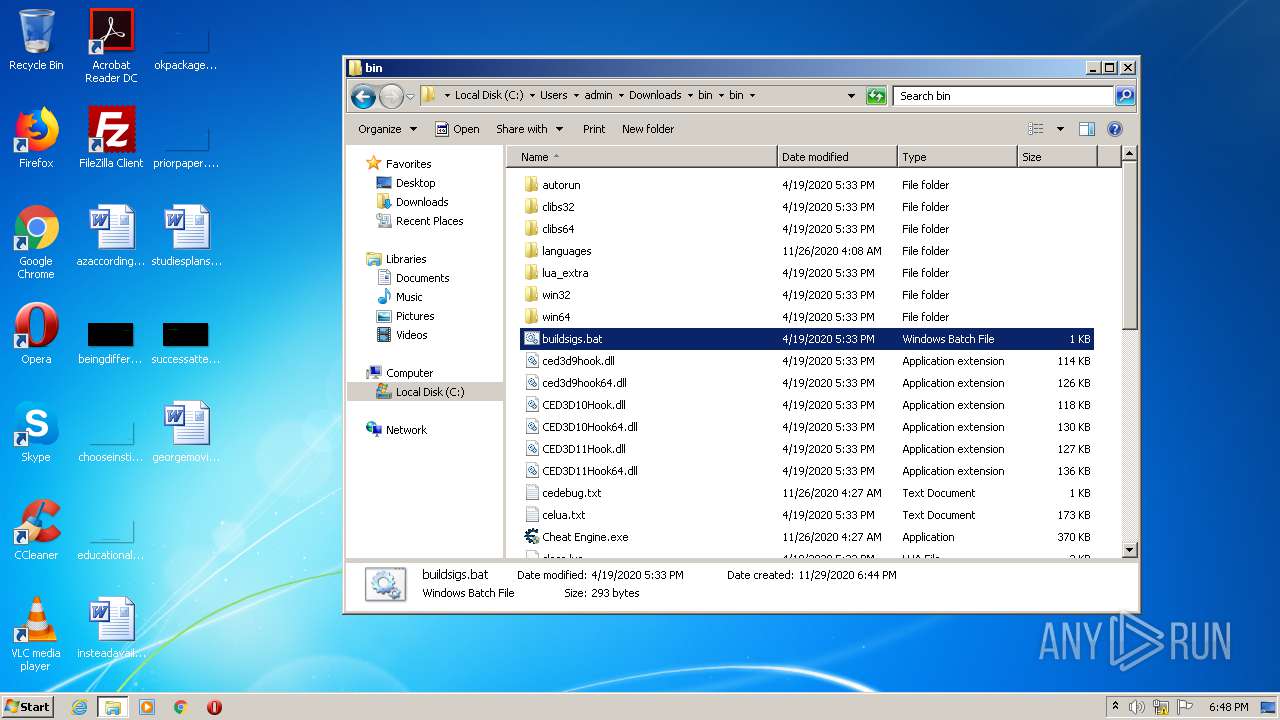
| 528 | cmd /c ""C:\Users\admin\Downloads\bin\bin\buildsigs.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1404517403138207911,16669990321483151499,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4999685849323200624 --mojo-platform-channel-handle=1448 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
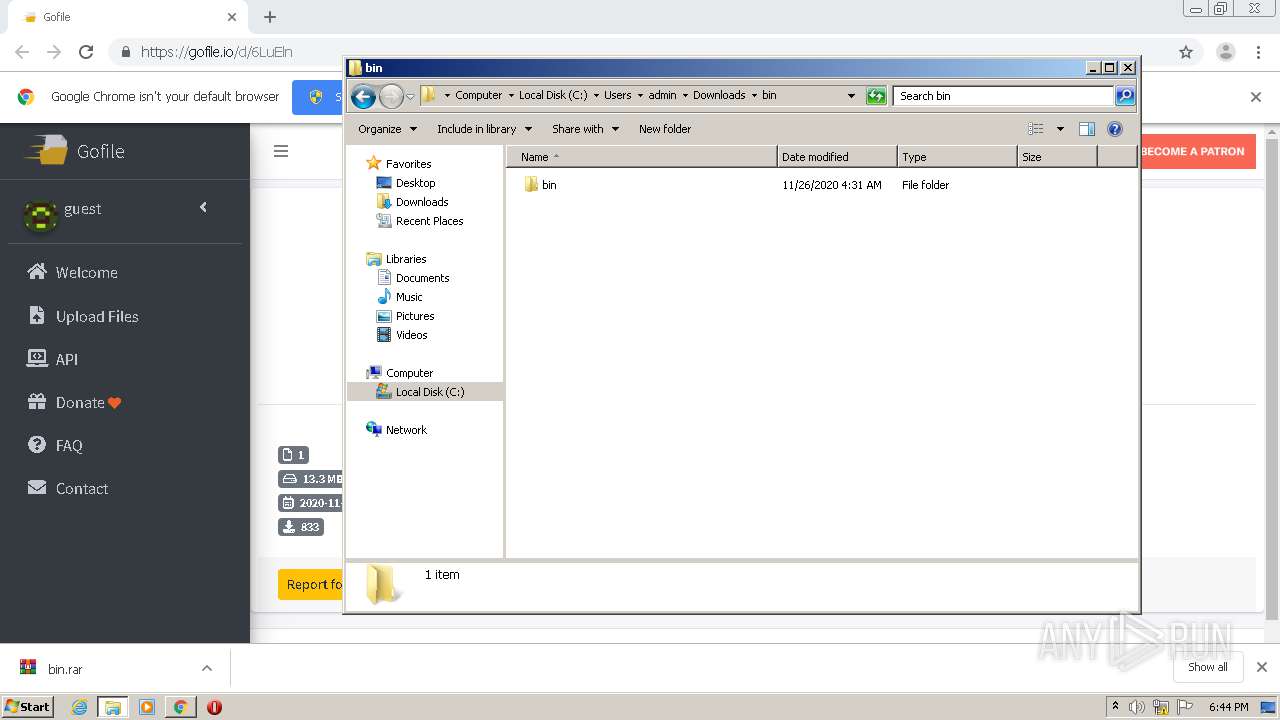
| 784 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\bin.rar" C:\Users\admin\Downloads\bin\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1404517403138207911,16669990321483151499,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14091552925736543018 --mojo-platform-channel-handle=2868 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,1404517403138207911,16669990321483151499,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10744336158567784804 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,1404517403138207911,16669990321483151499,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5617173459046517078 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | cmd /c ""C:\Users\admin\Downloads\bin\bin\buildsigs.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1916 | cmd /c ""C:\Users\admin\Downloads\bin\bin\buildsigs.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
5 579
Read events
4 556
Write events
1 017
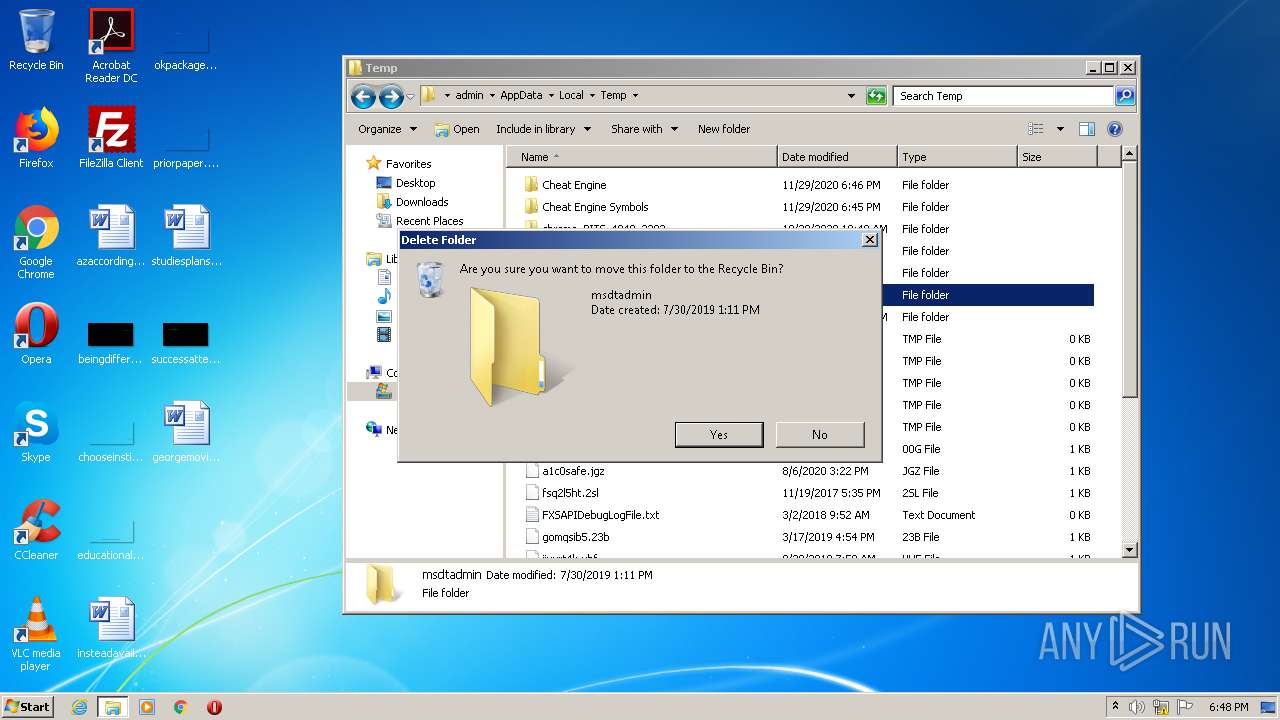
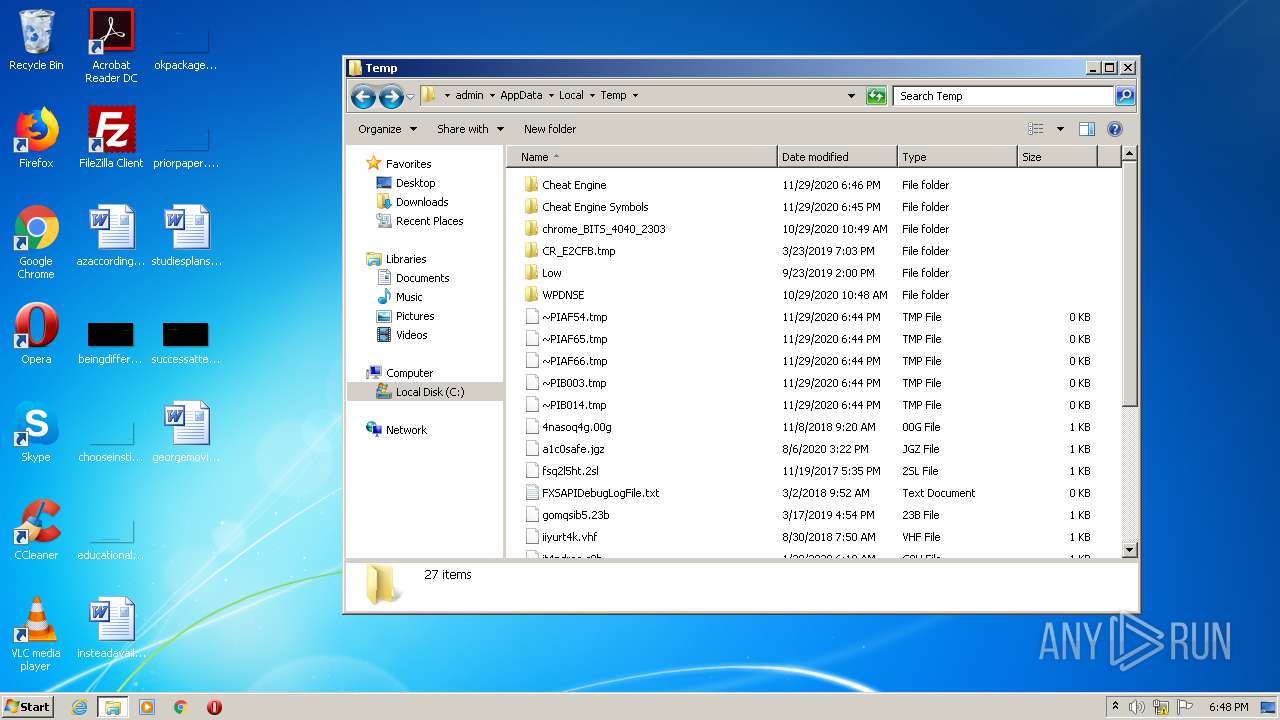
Delete events
6
Modification events
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2620-13251149058810625 |
Value: 259 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
36
Suspicious files
42
Text files
195
Unknown types
16
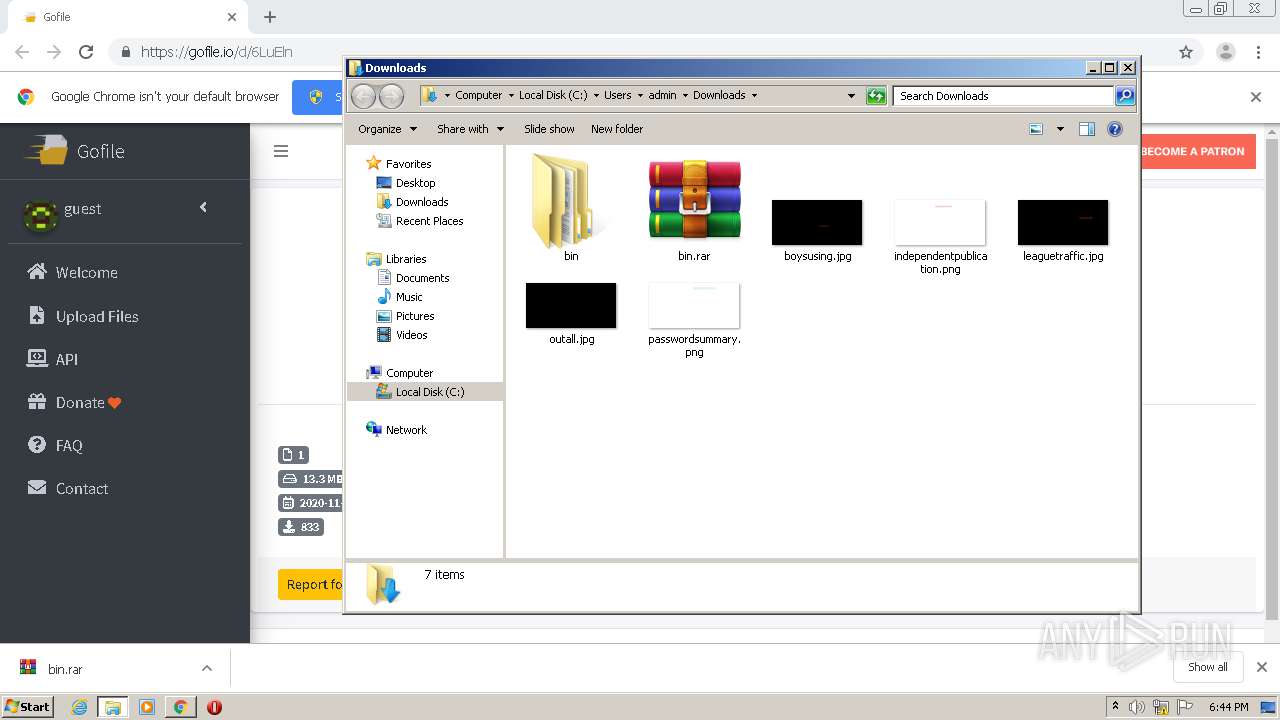
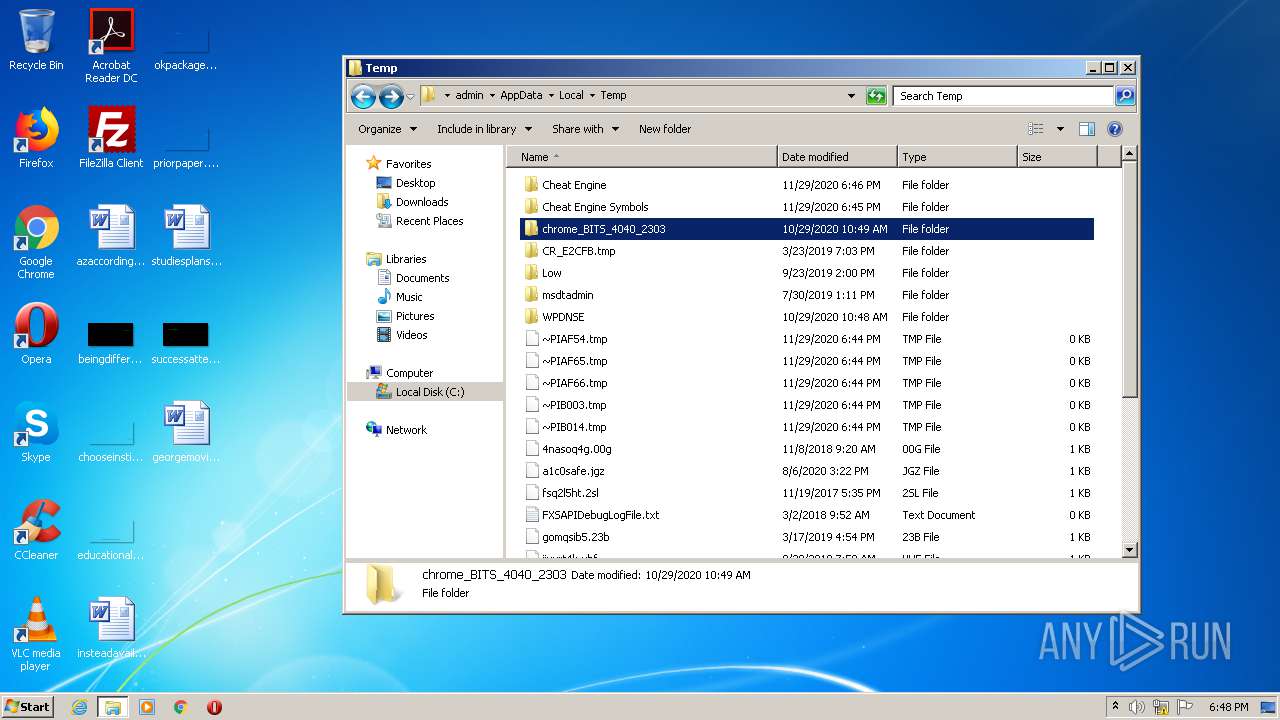
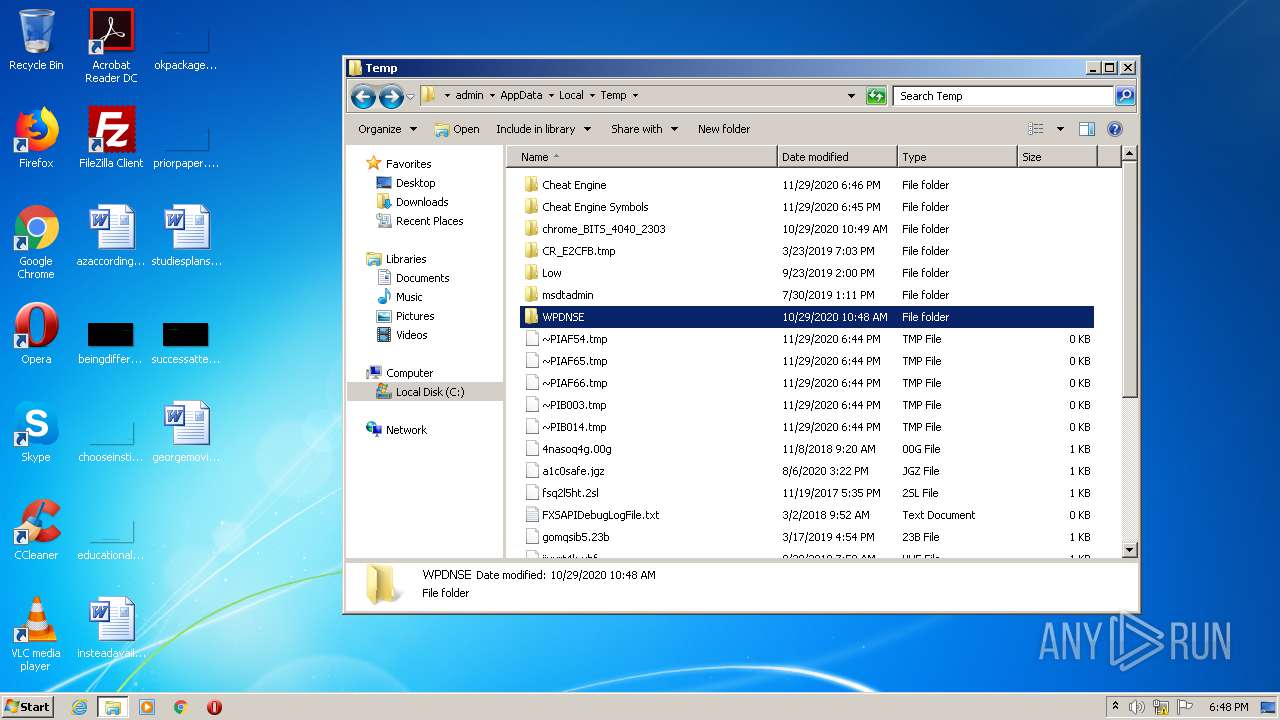
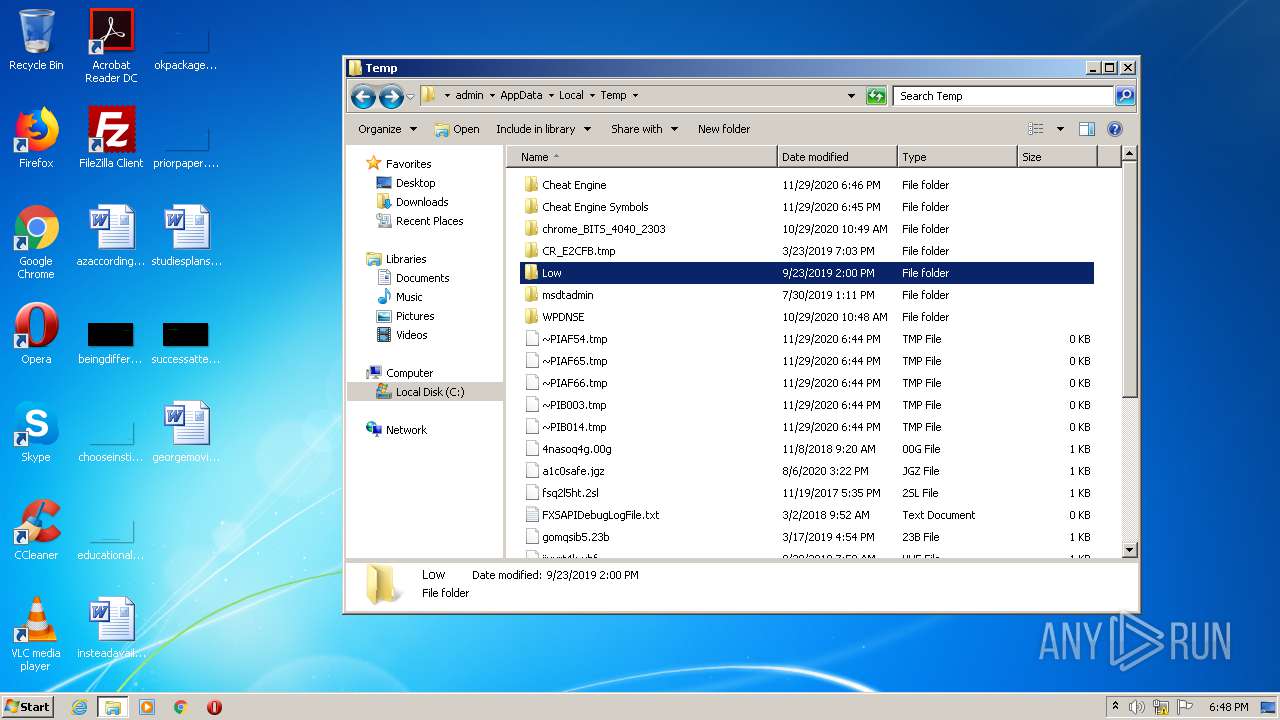
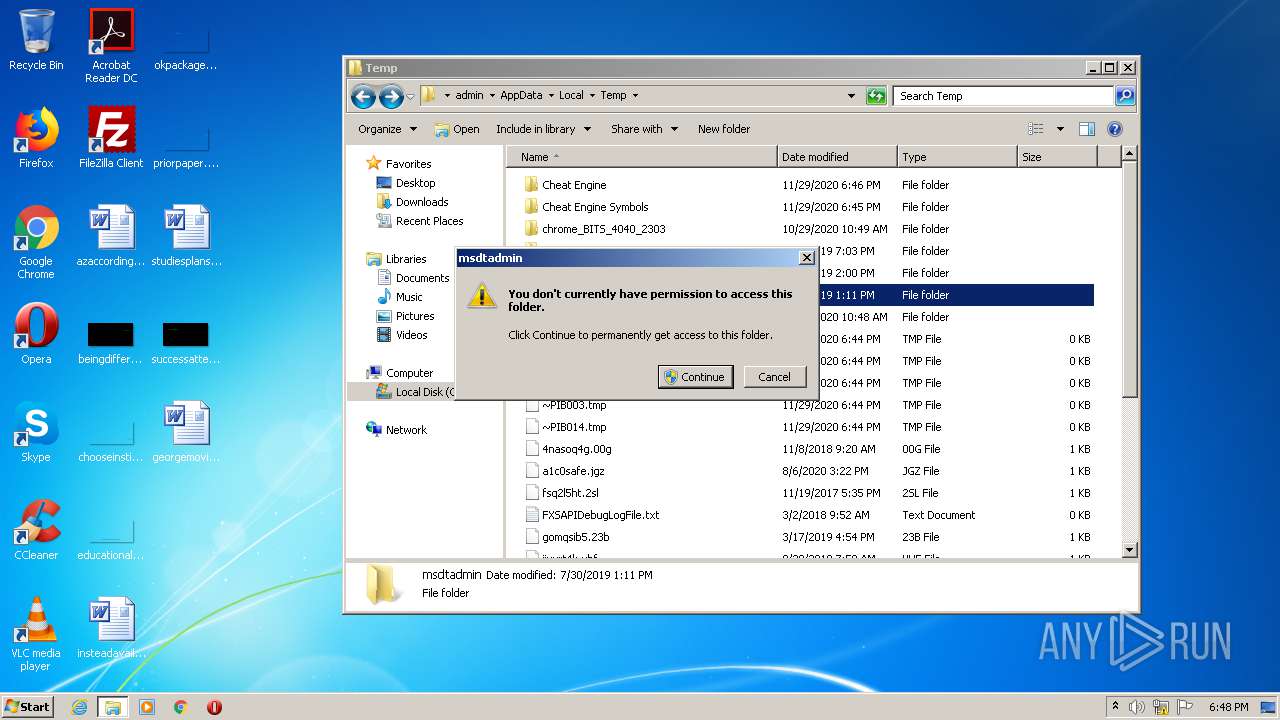
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3EC03-A3C.pma | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e80cf4b8-81d2-470a-802e-7d4ec54dc024.tmp | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF153571.TMP | text | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF15360d.TMP | text | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF153571.TMP | text | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF153736.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
23
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
760 | chrome.exe | 217.182.142.131:443 | gofile.io | OVH SAS | FR | unknown |
760 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
760 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
760 | chrome.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
760 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
760 | chrome.exe | 104.26.11.39:443 | cdn.buymeacoffee.com | Cloudflare Inc | US | suspicious |
760 | chrome.exe | 149.202.184.93:443 | matomo.gofile.io | OVH SAS | FR | unknown |
760 | chrome.exe | 217.182.142.52:443 | gofile.io | OVH SAS | FR | unknown |
760 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
760 | chrome.exe | 104.18.59.22:443 | piunikaweb.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gofile.io |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
cdn.buymeacoffee.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn.datatables.net |
| whitelisted |
cdn.rawgit.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
matomo.gofile.io |
| whitelisted |
Threats
Process | Message |
|---|---|
draqxorengine-i386.exe | p3 |
draqxorengine-i386.exe | p3 |
draqxorengine-i386.exe | arm disassembler |
draqxorengine-i386.exe | arm disassembler |
draqxorengine-i386.exe | MainUnit2 |
draqxorengine-i386.exe | sizeof fxstate = 512 |
draqxorengine-i386.exe | sizeof fxstate = 512 |
draqxorengine-i386.exe | start |
draqxorengine-i386.exe | TSymbolListHandler.create 2 |
draqxorengine-i386.exe | TSymbolListHandler.create 2 |