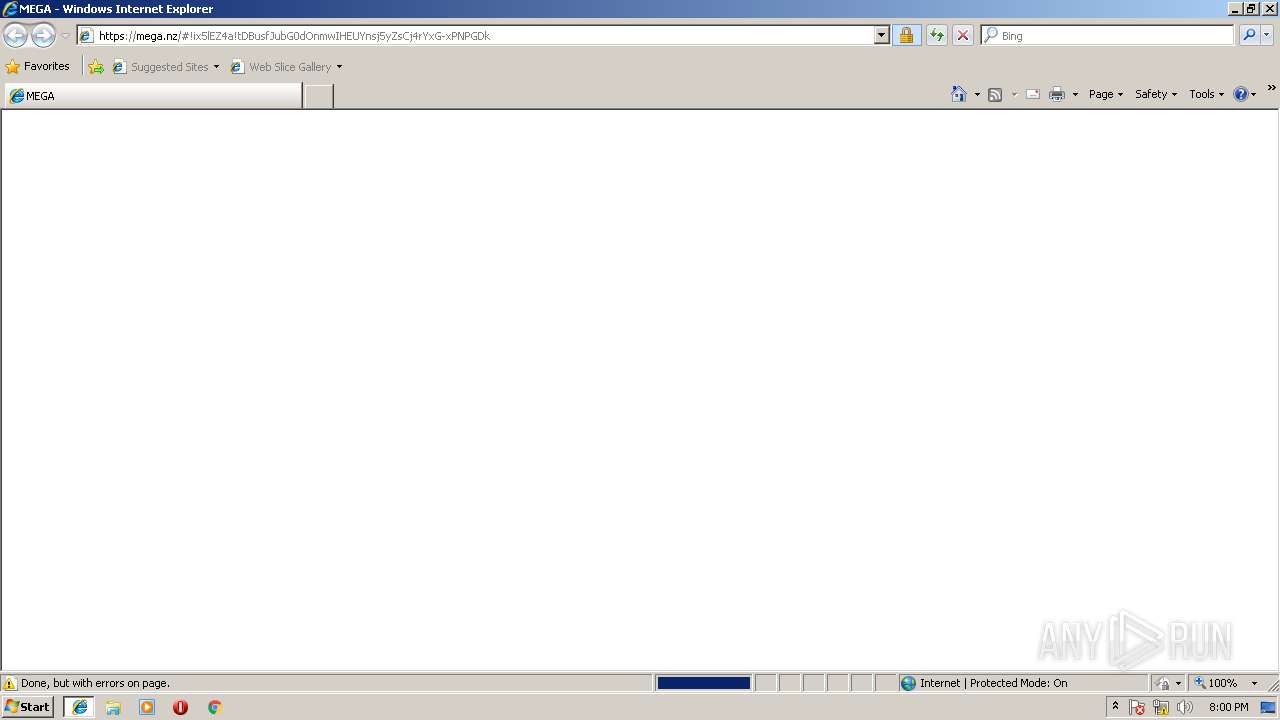
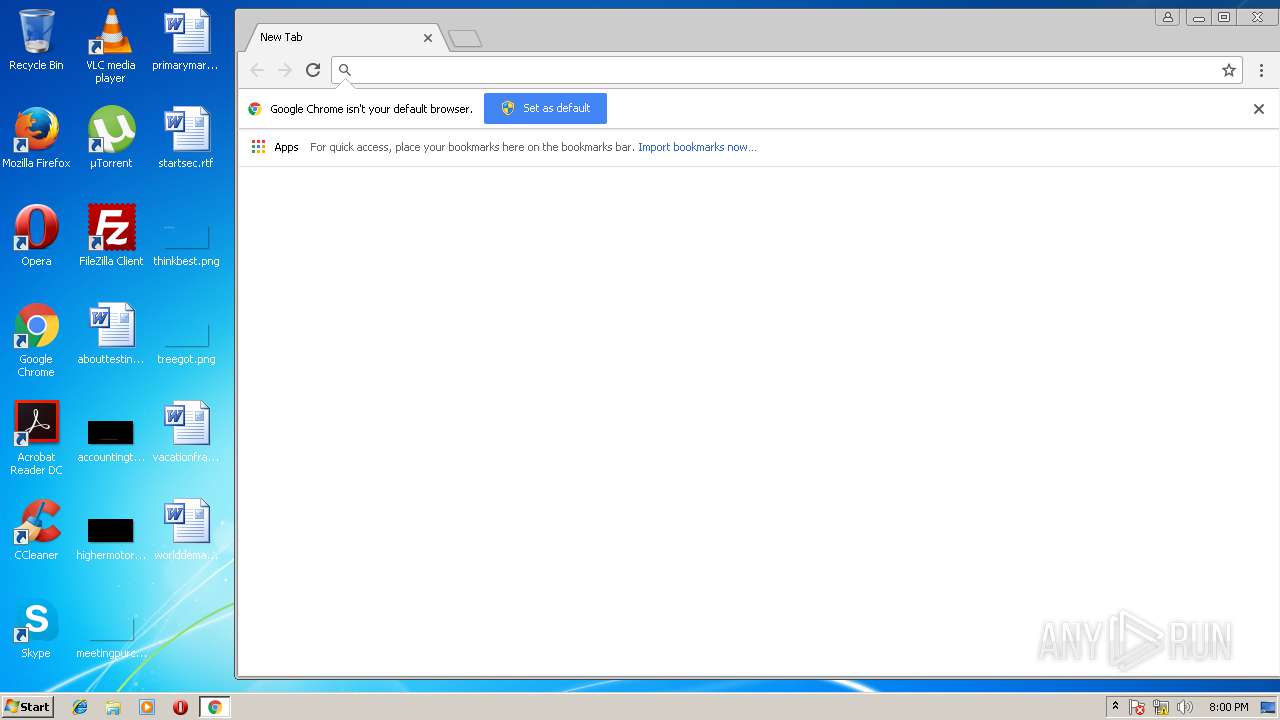
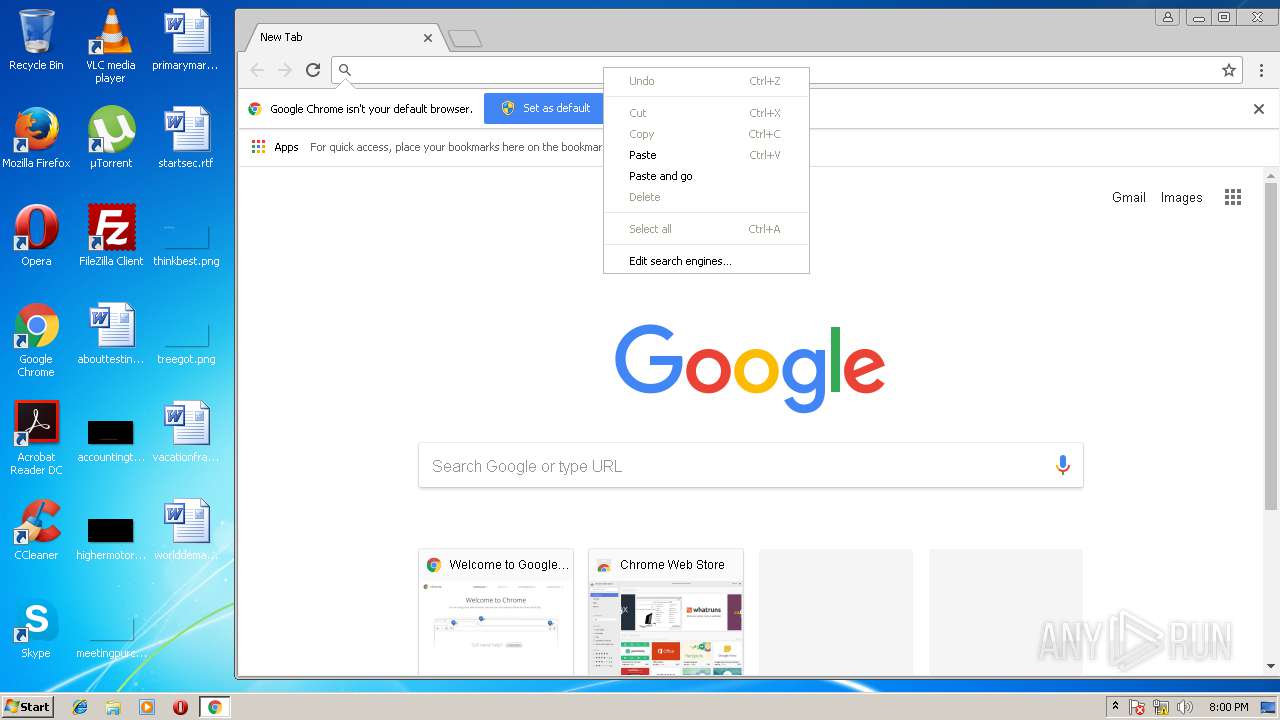
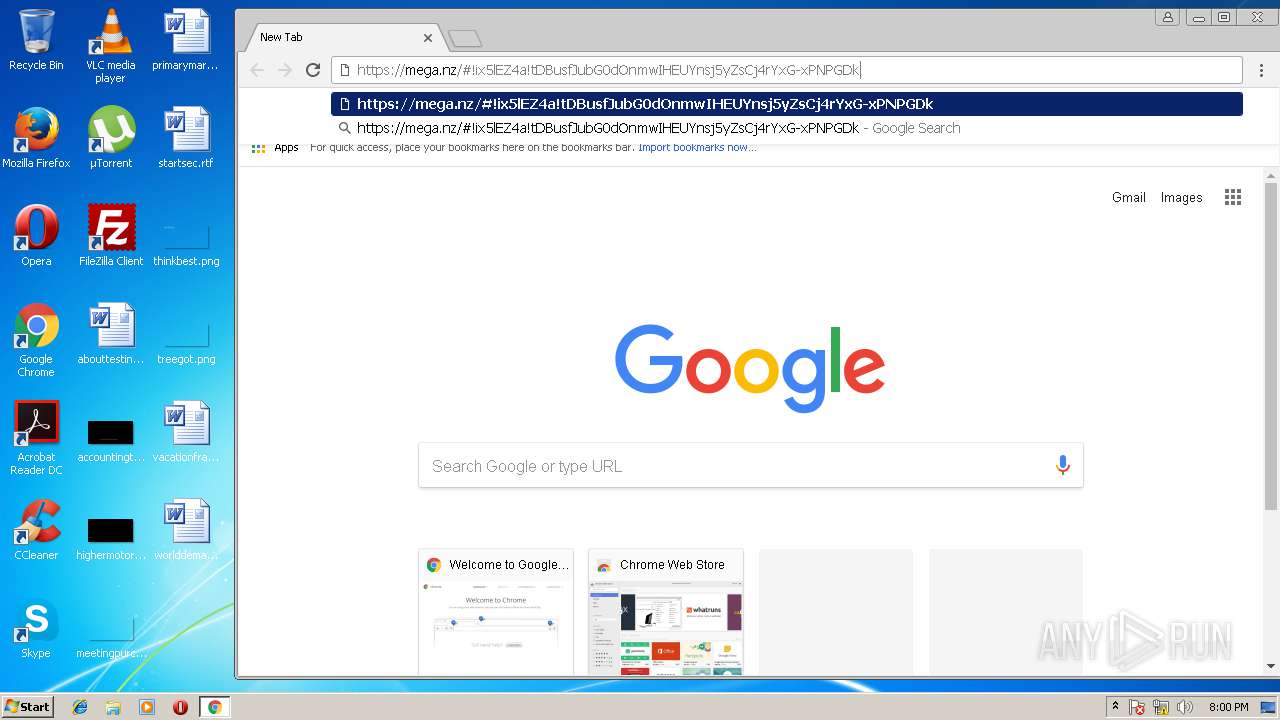
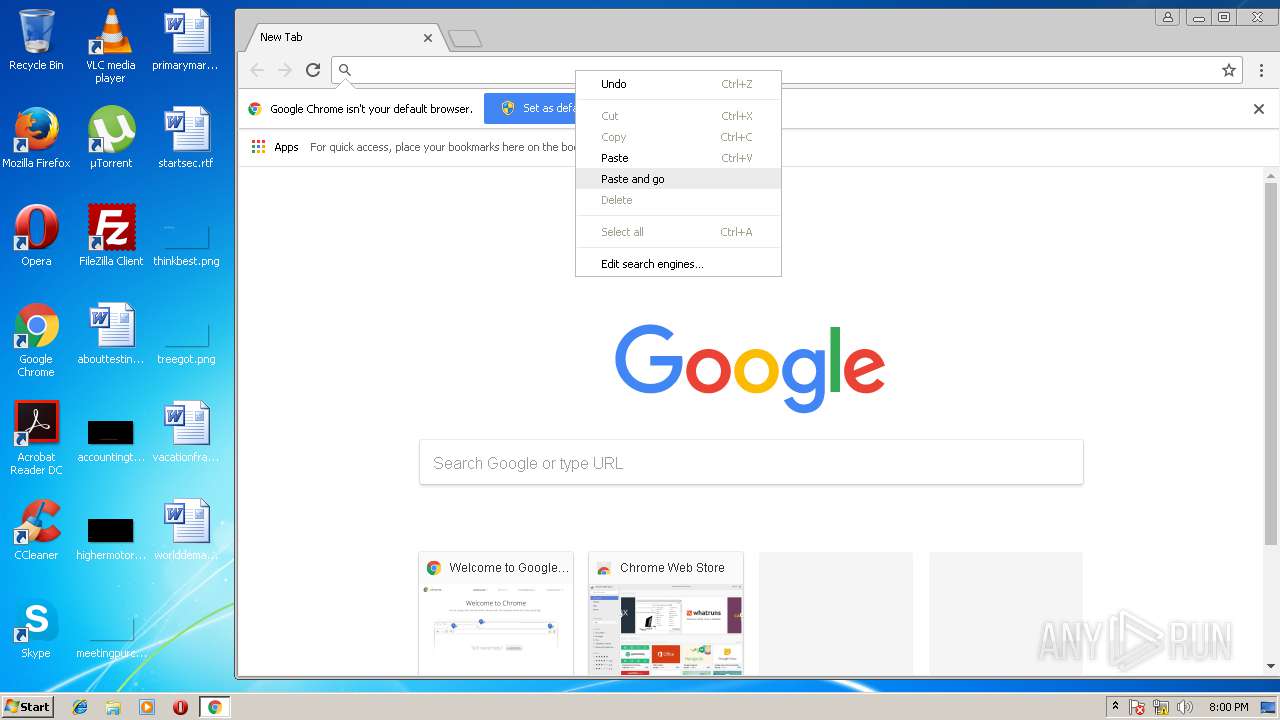
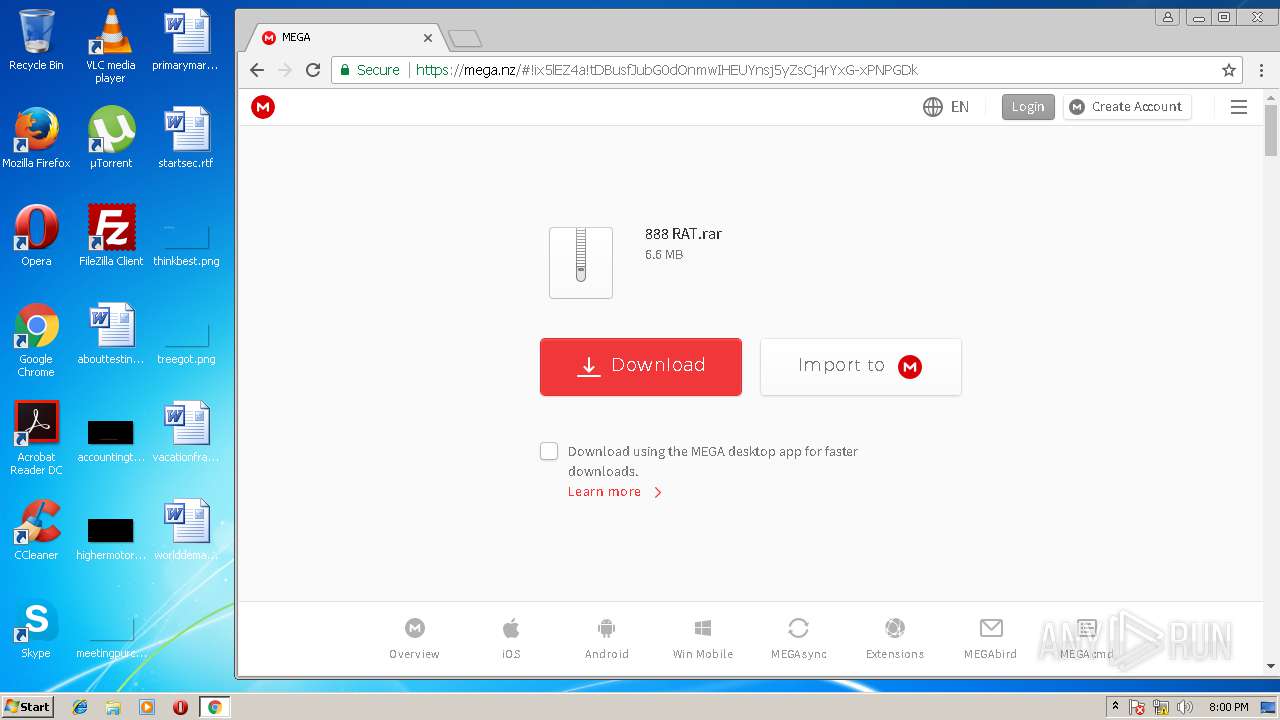
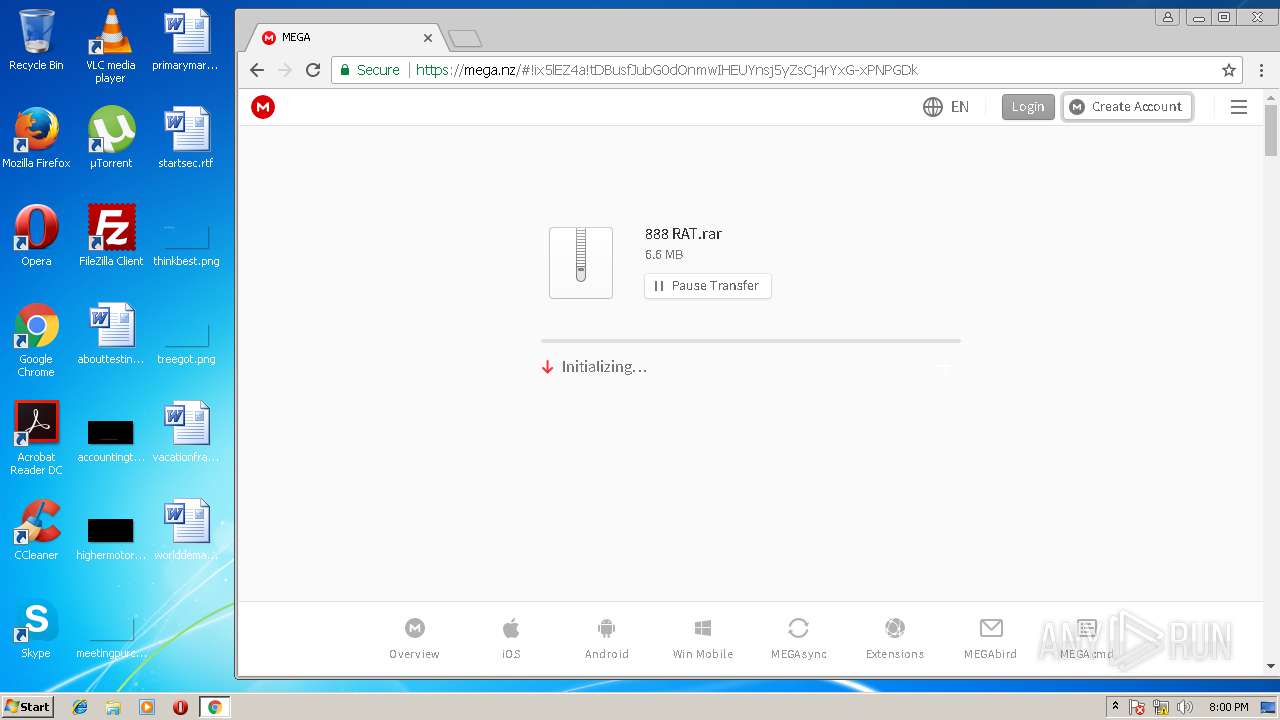
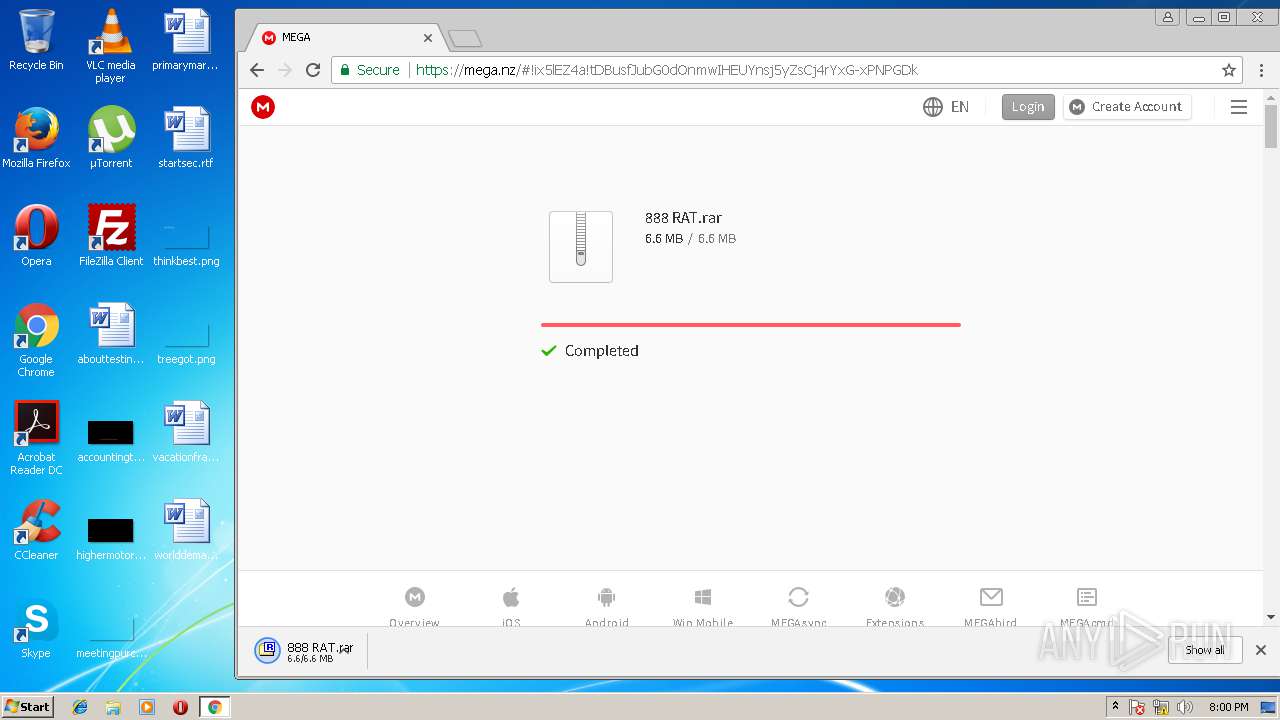
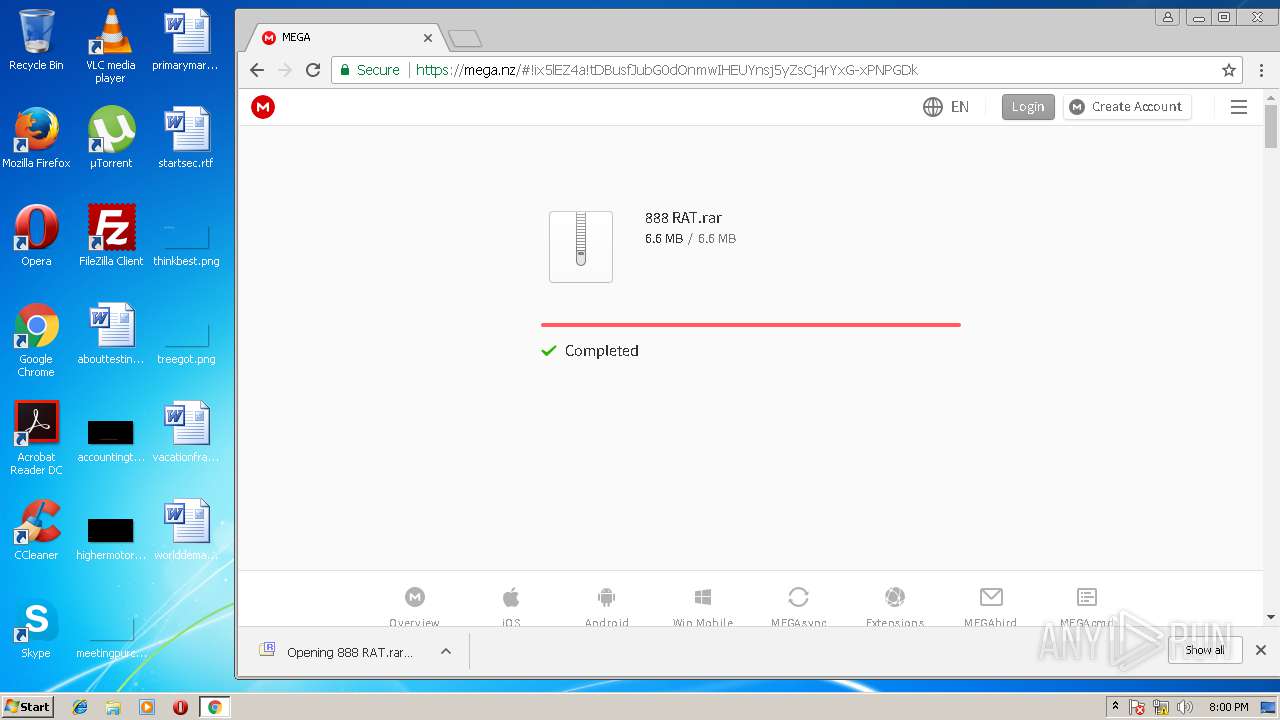
| URL: | https://mega.nz/#!ix5lEZ4a!tDBusfJubG0dOnmwIHEUYnsj5yZsCj4rYxG-xPNPGDk |
| Full analysis: | https://app.any.run/tasks/6edcc35f-6c4e-49f1-bec4-3273df6411e8 |
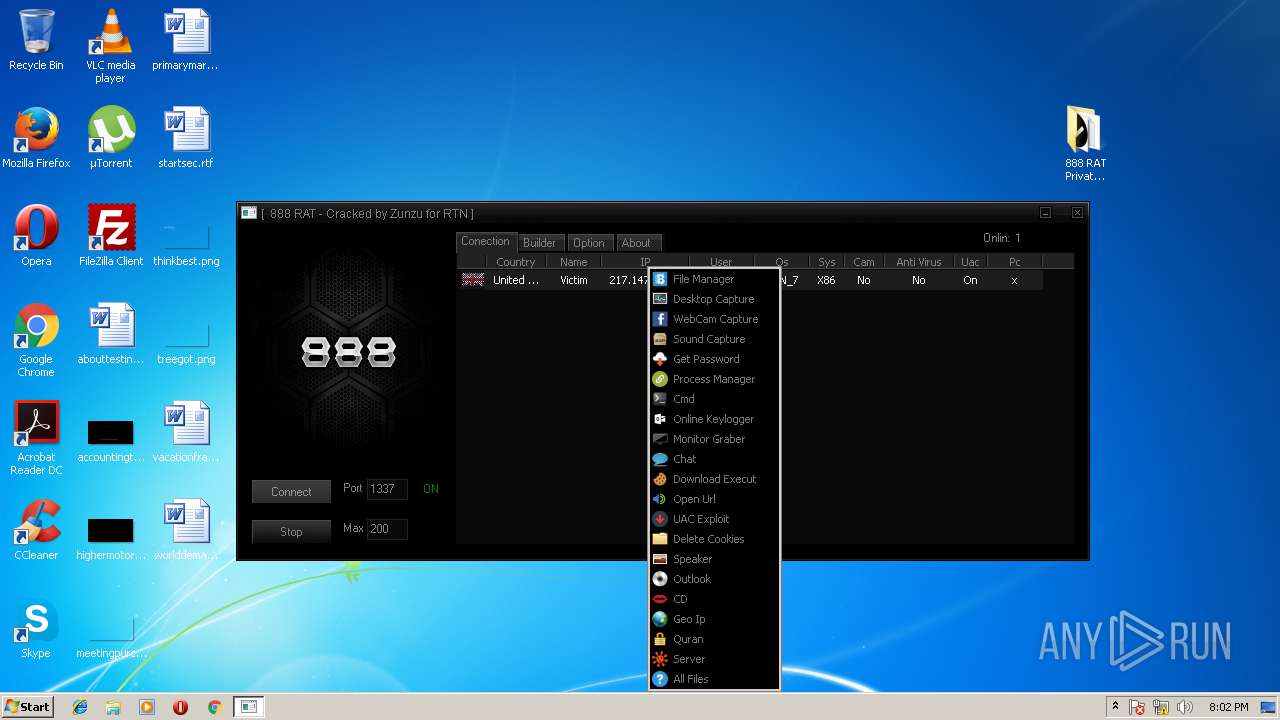
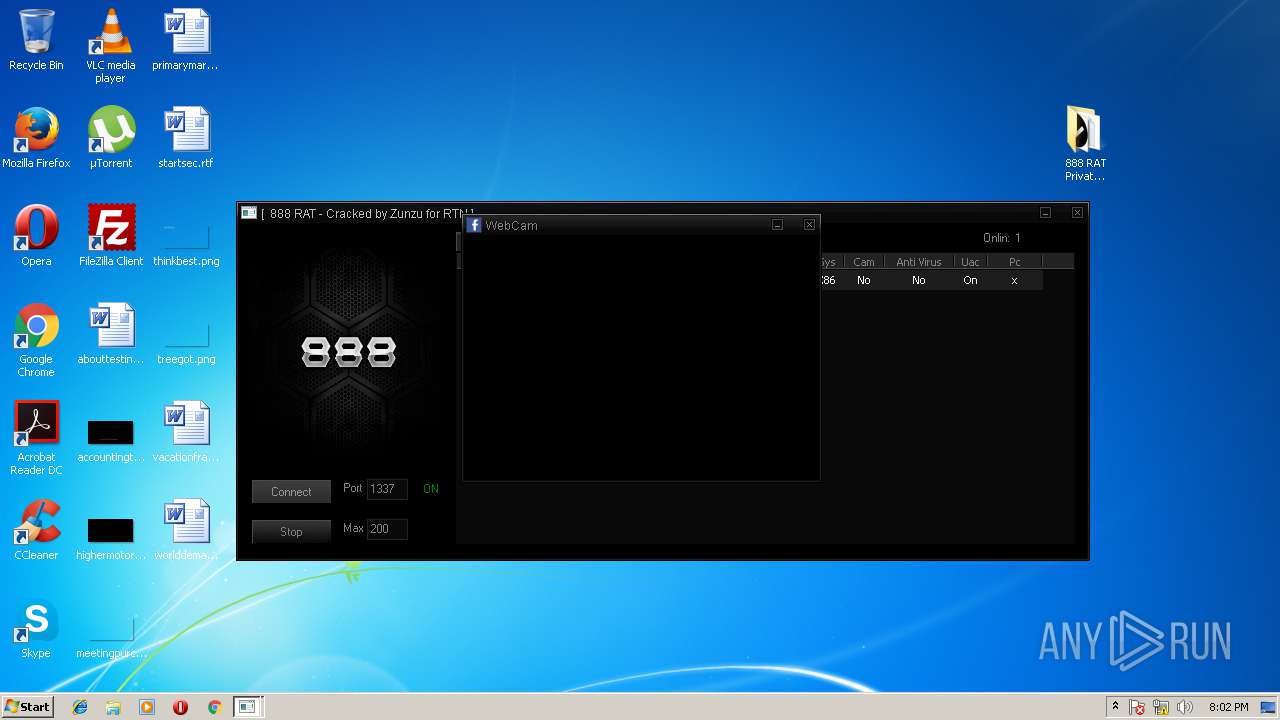
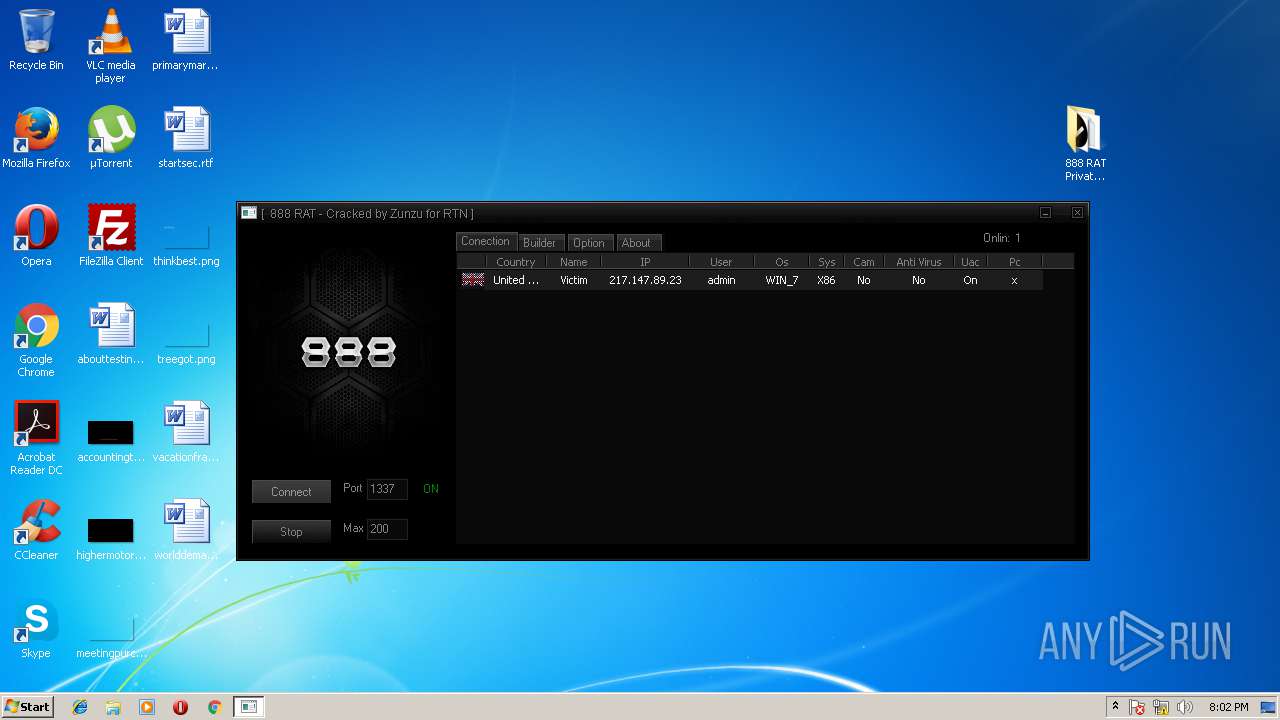
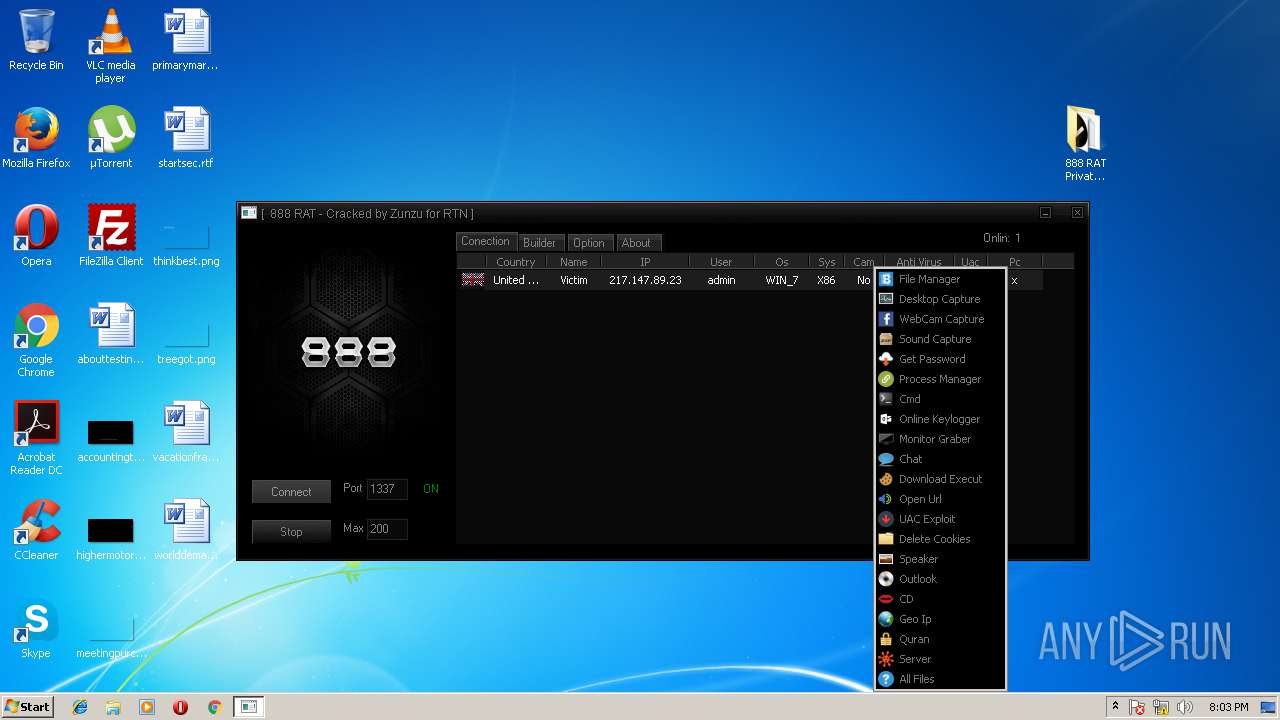
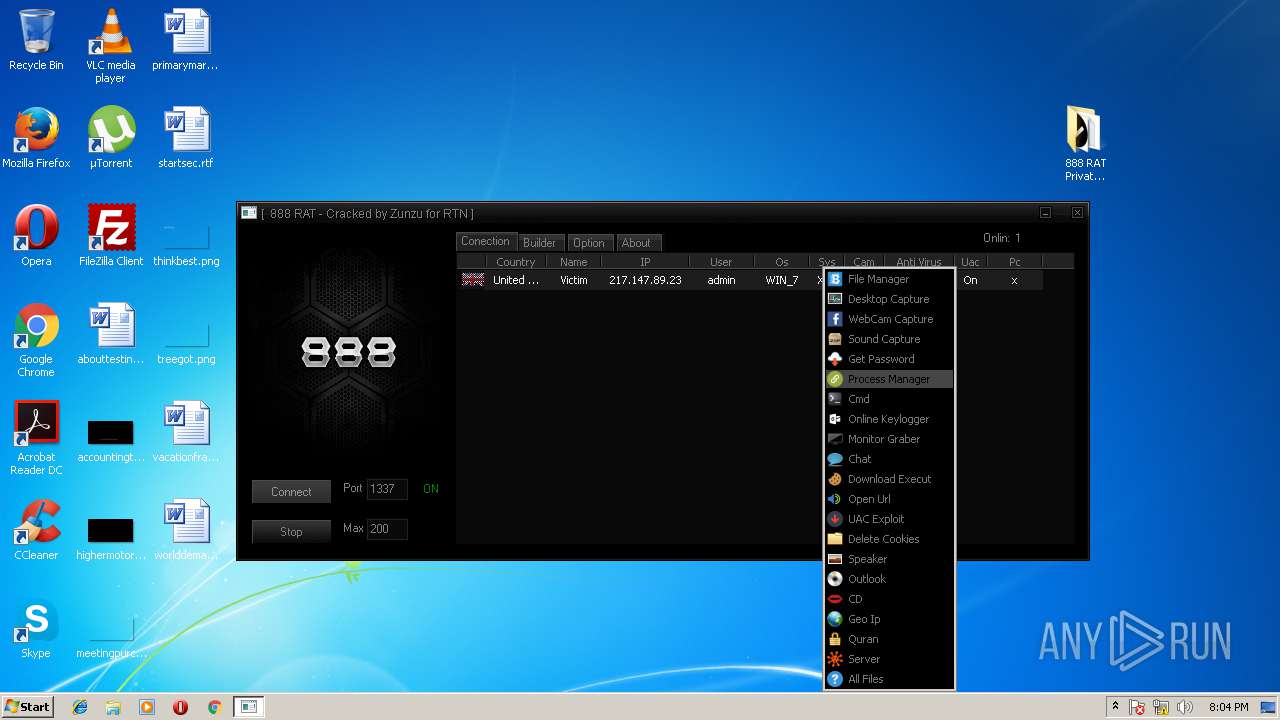
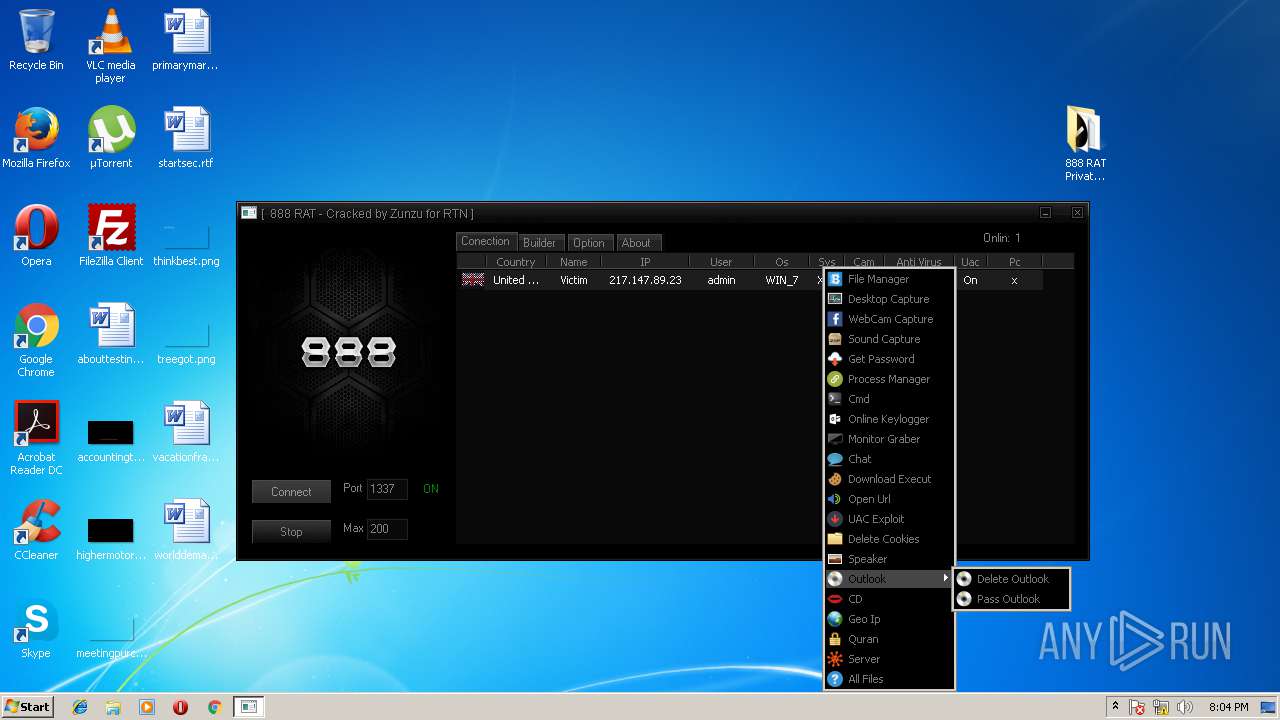
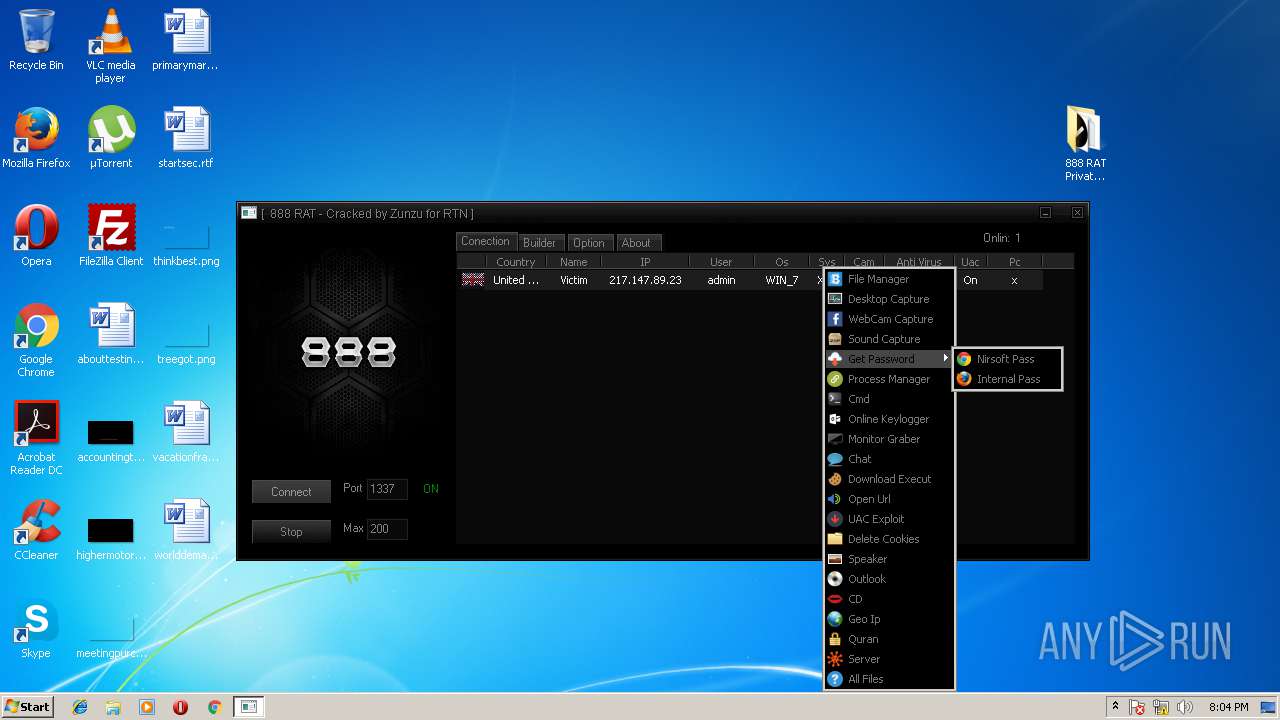
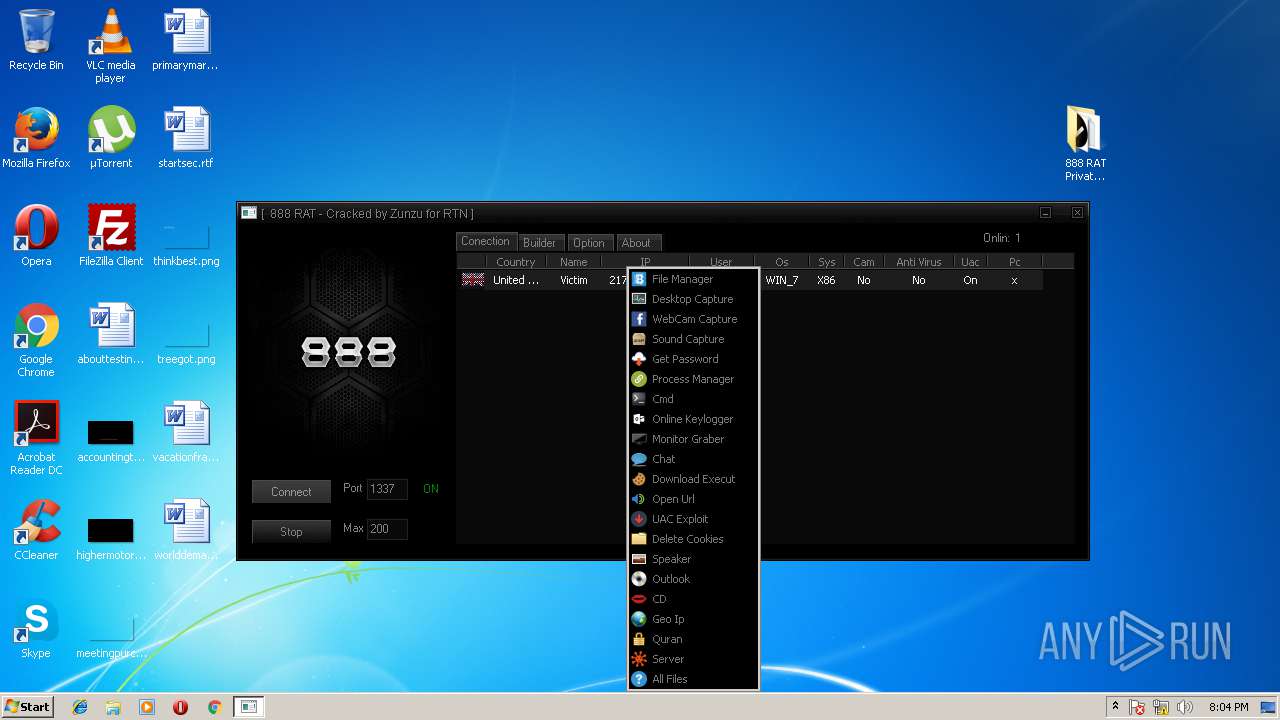
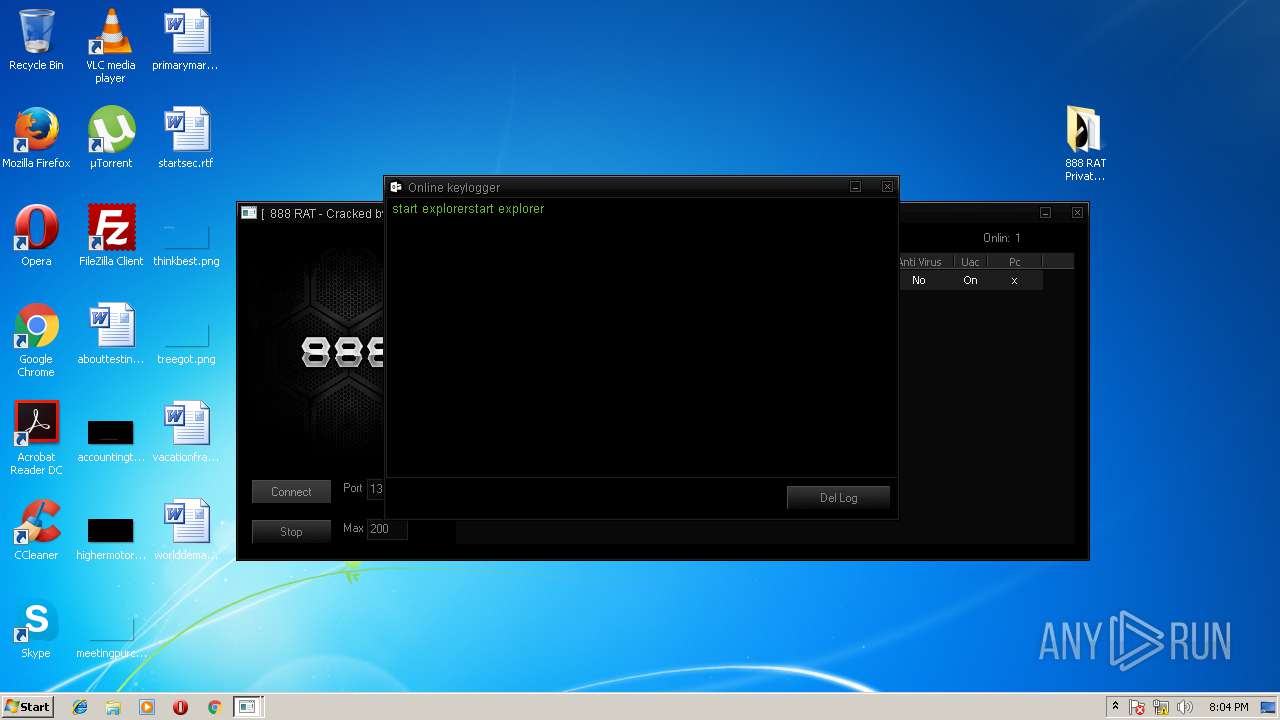
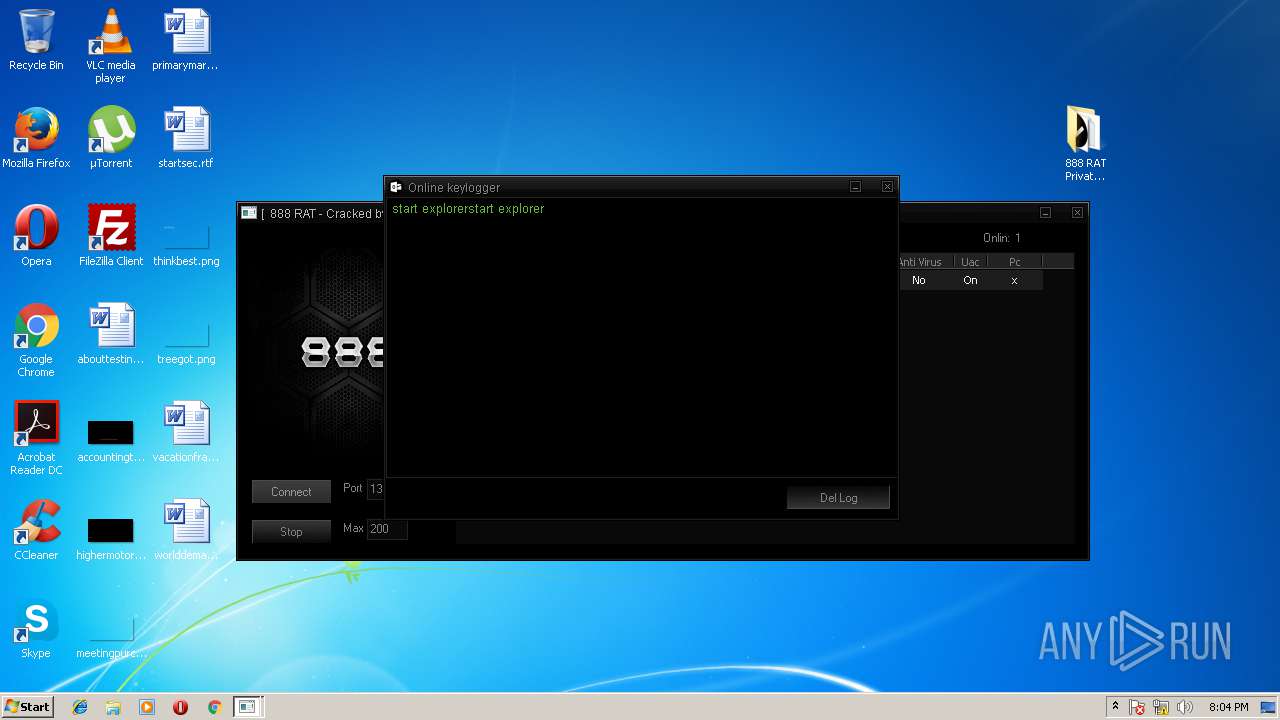
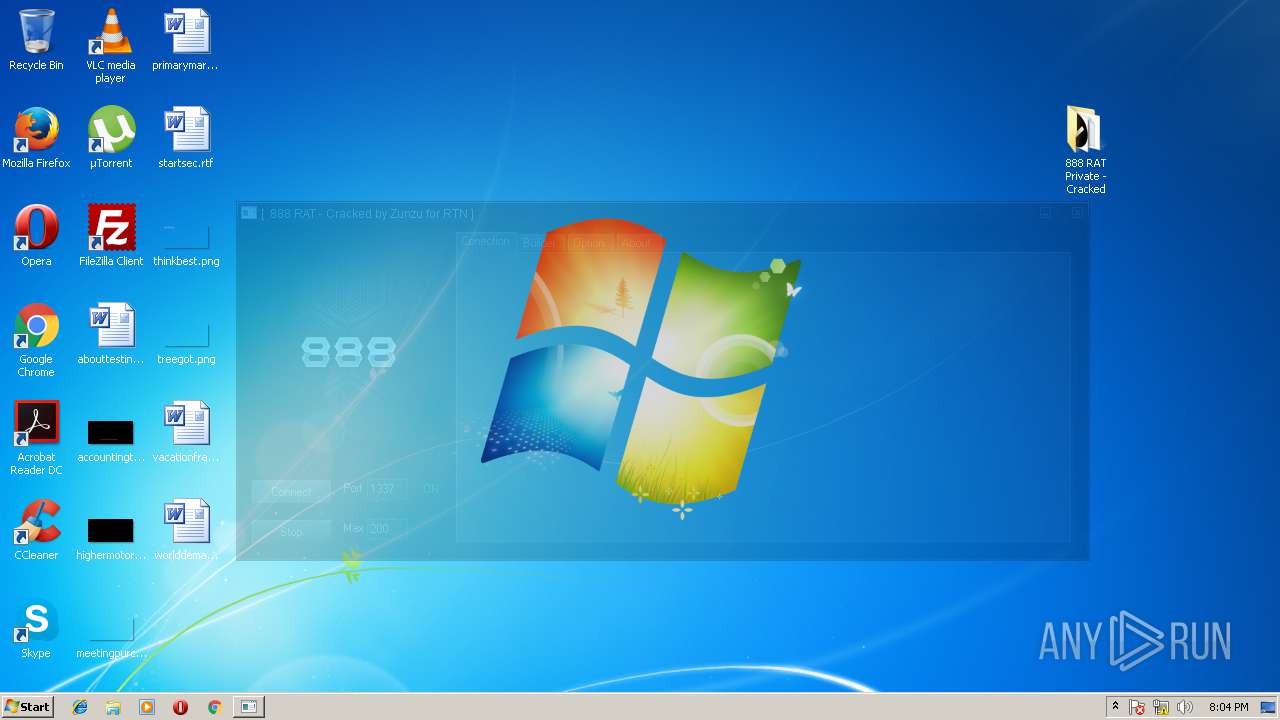
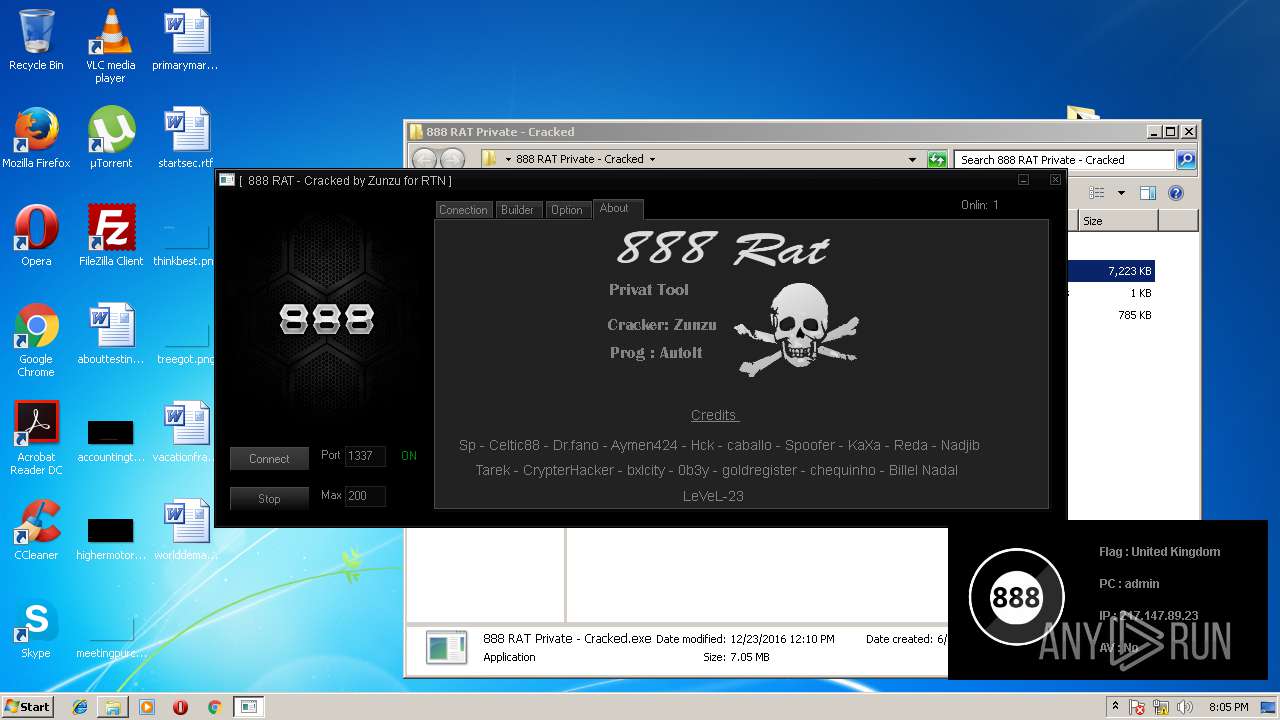
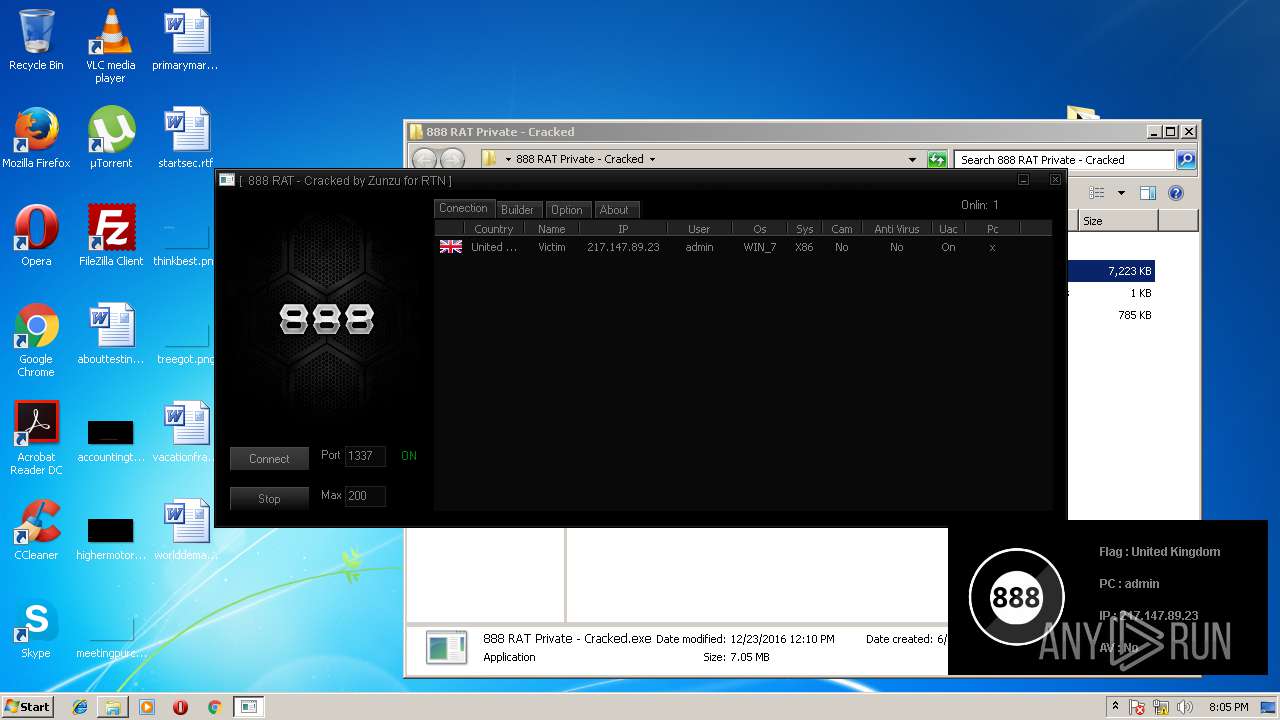
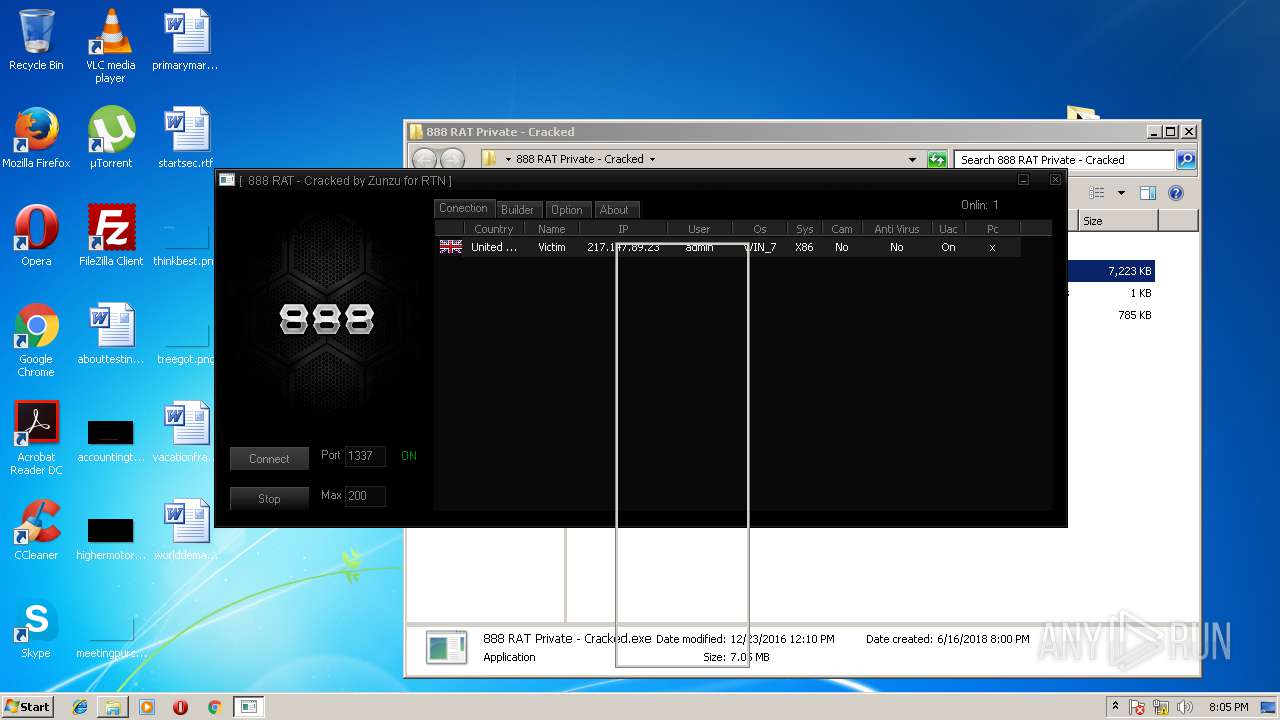
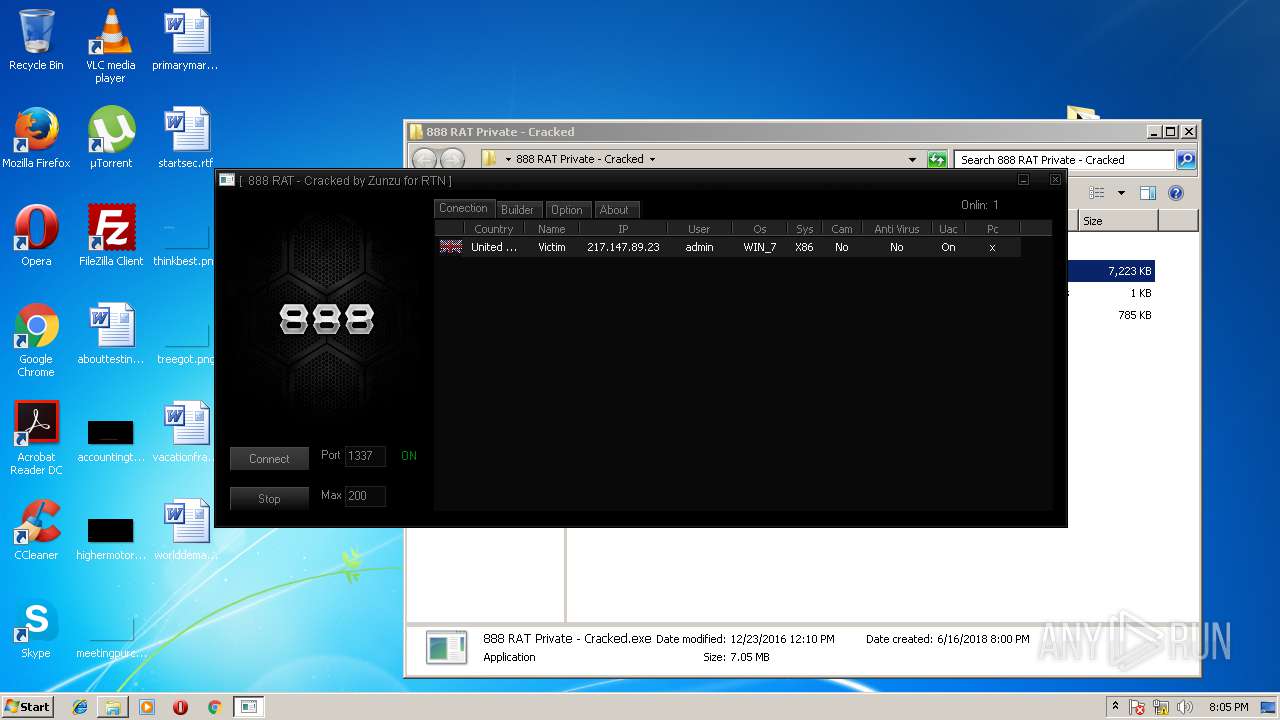
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2018, 18:59:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 59D25A280036C7D37A3AAF29F474B907 |
| SHA1: | 01F040AC6ECCDDE25EE0FC6610FA5C6806F98043 |
| SHA256: | 535CD5A8BB5E89E154736B9E0121871E06D6841BCD180DB451F0E6E2FD240E58 |
| SSDEEP: | 3:N8X/iGEhu/RxHRVc8SMgJLWJsEY:29wwHHYDM2Lwsz |
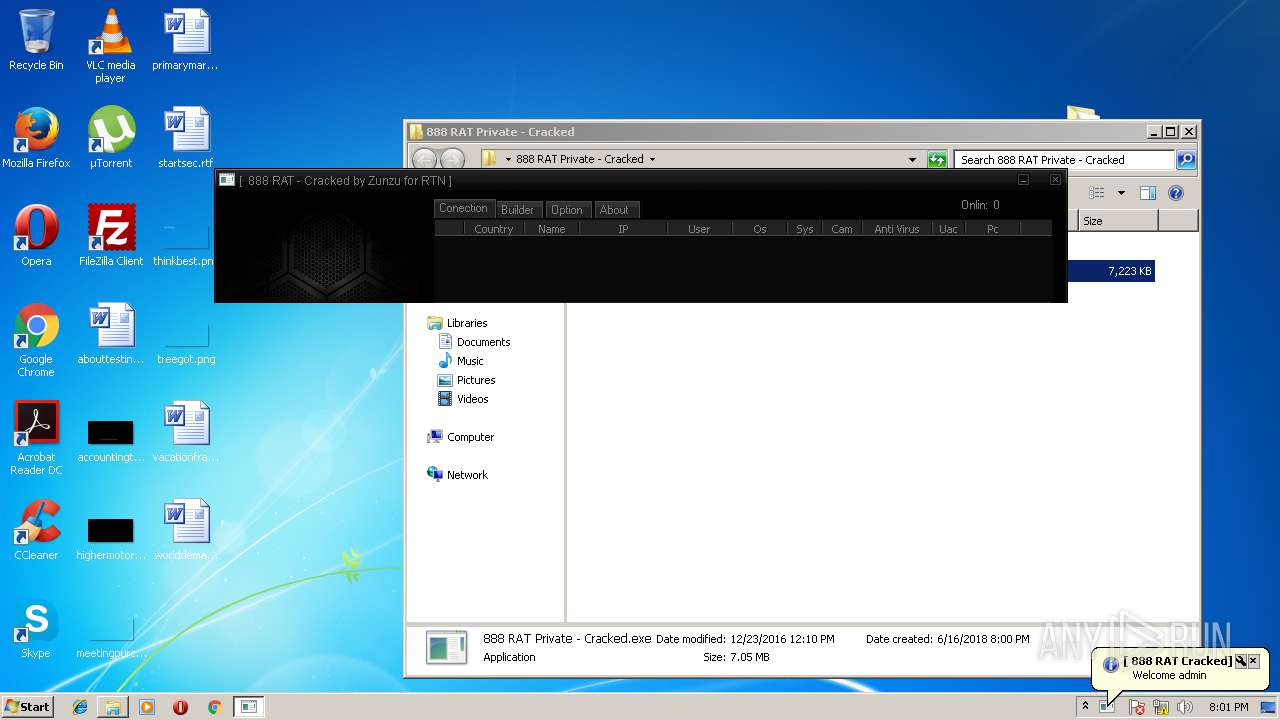
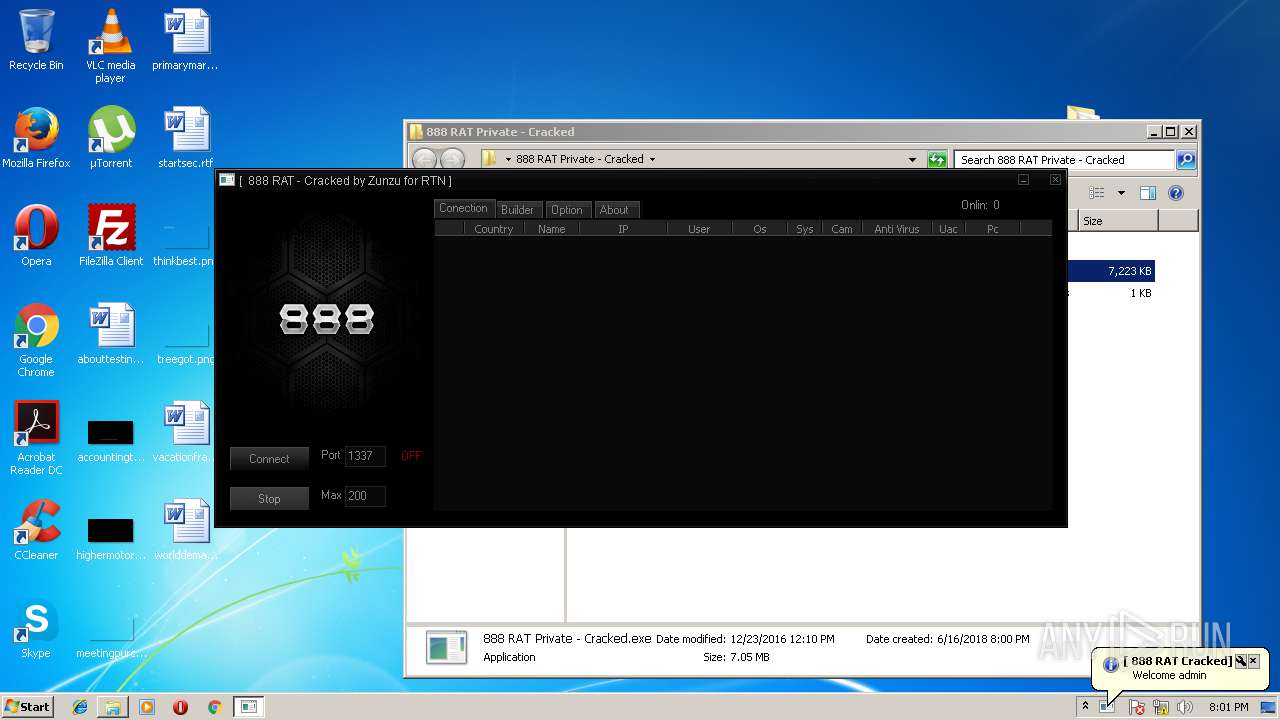
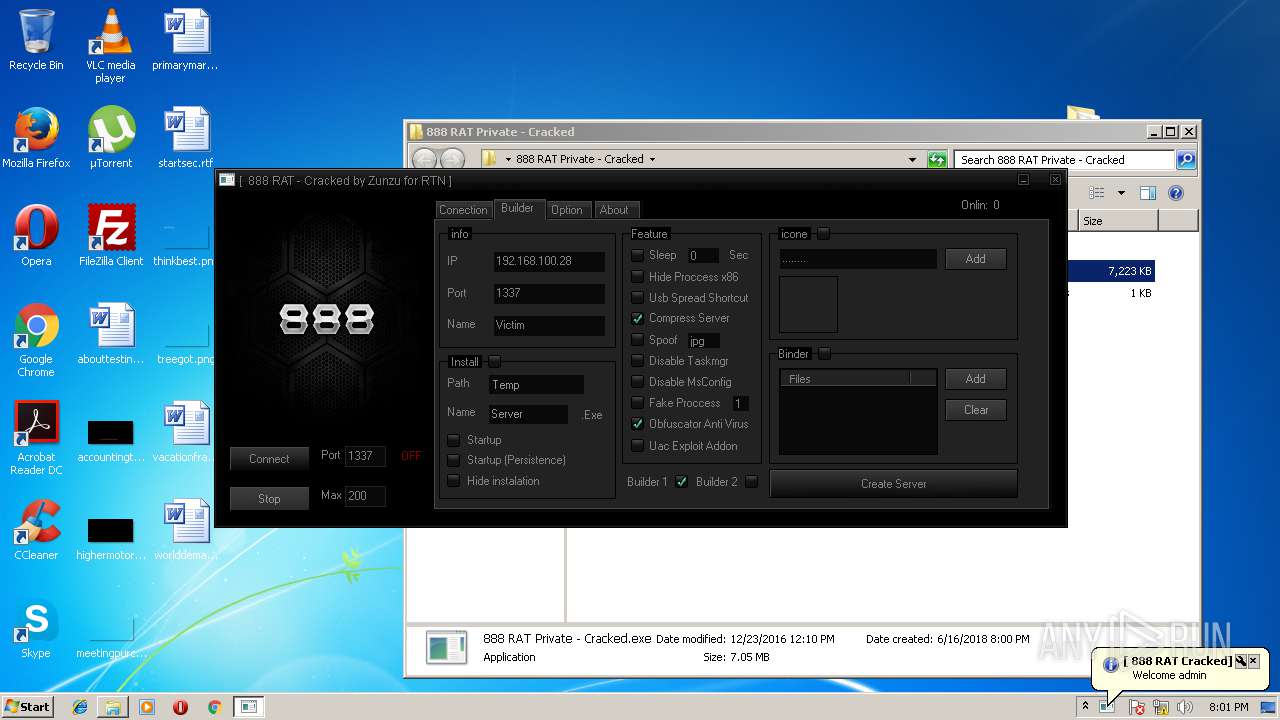
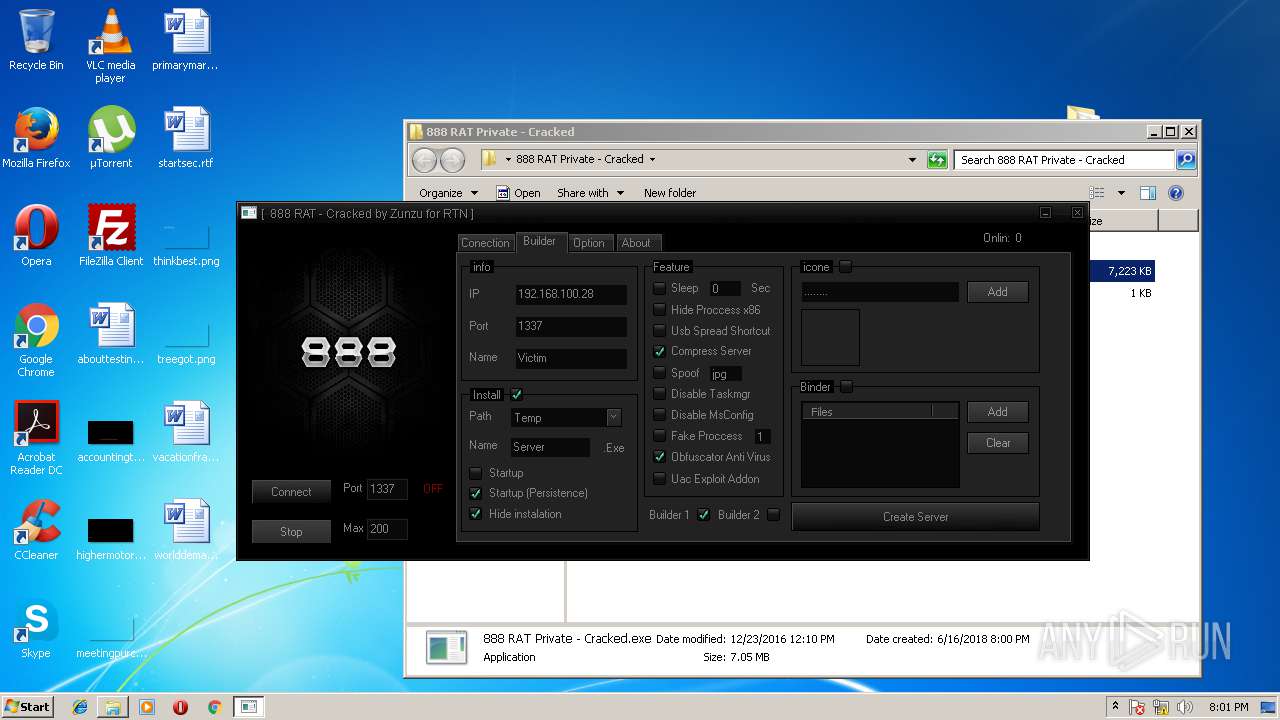
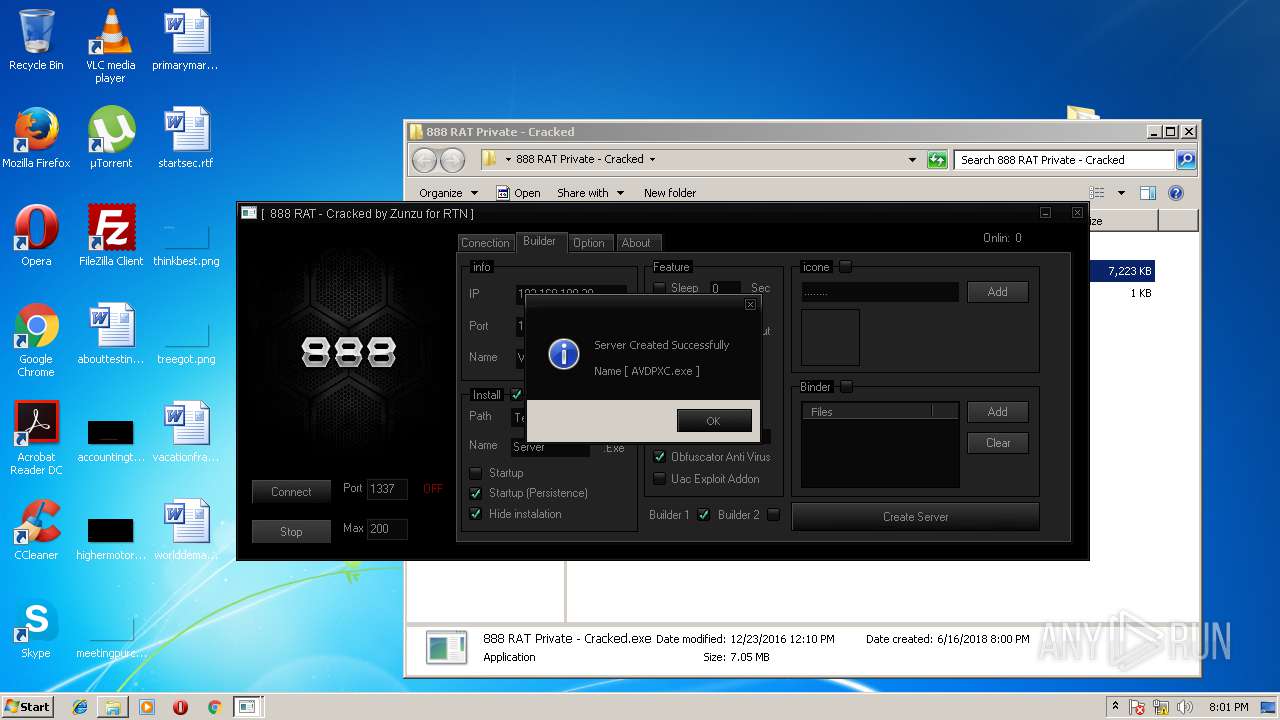
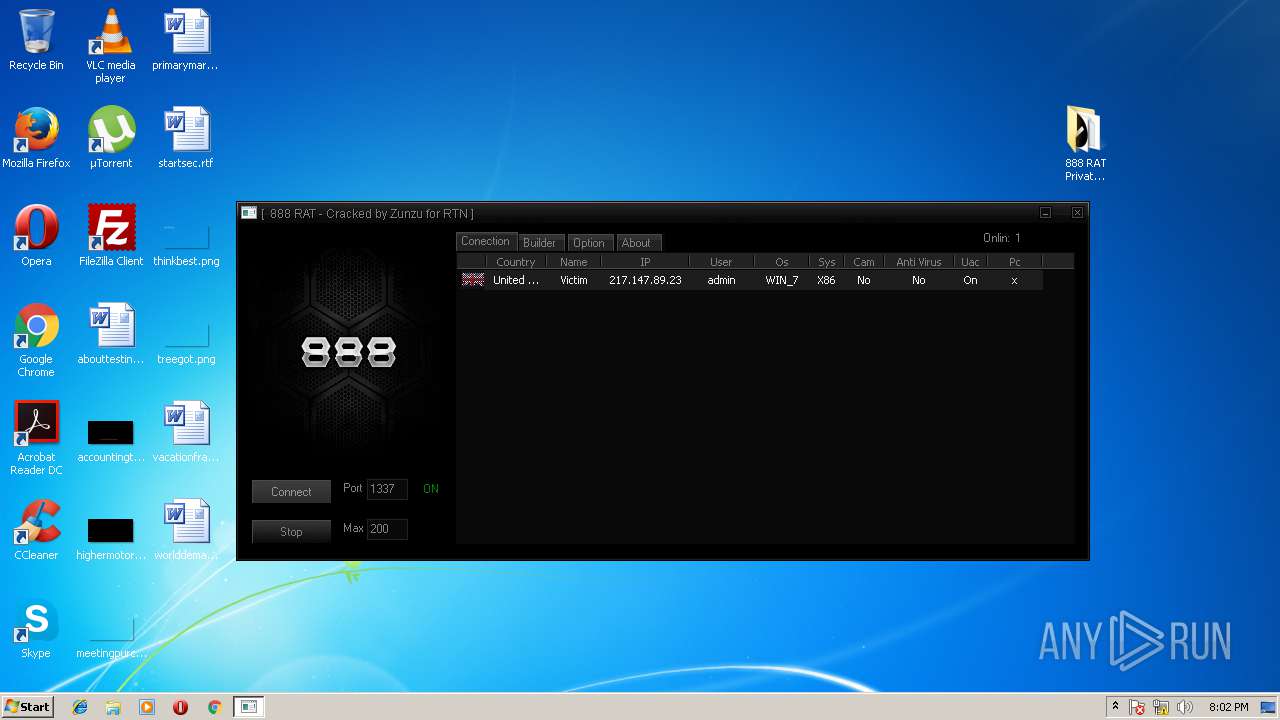
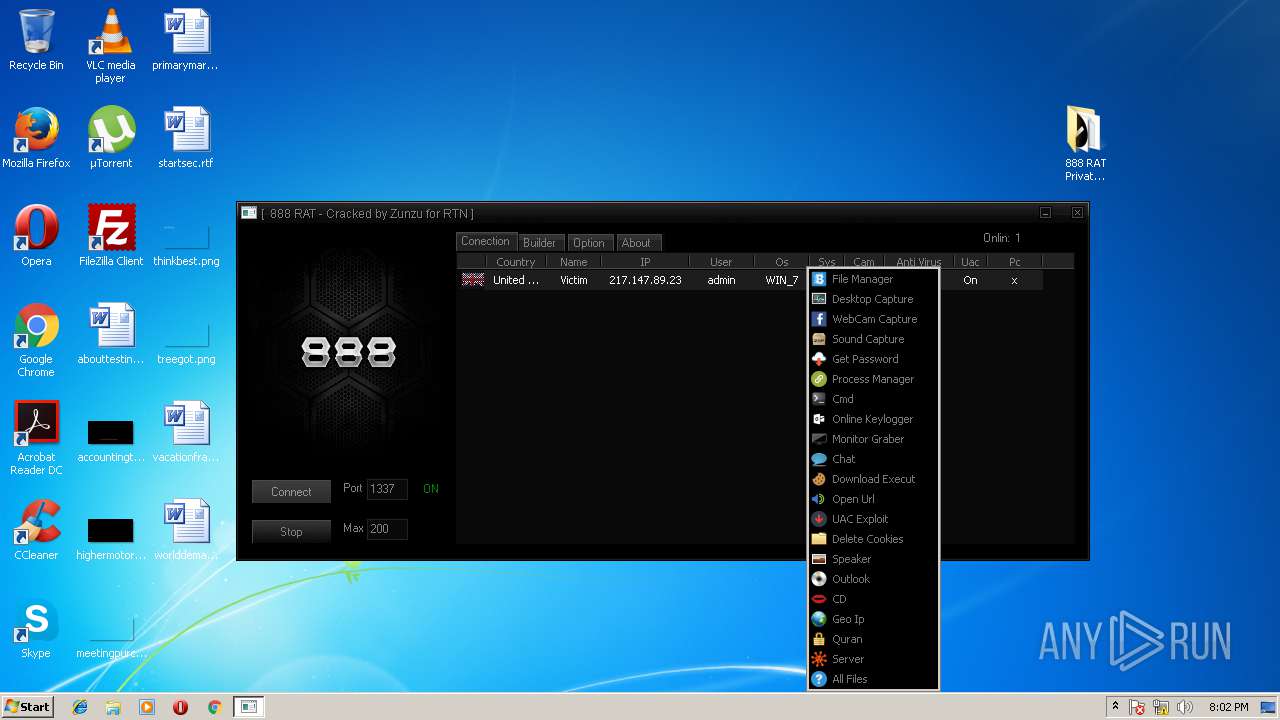
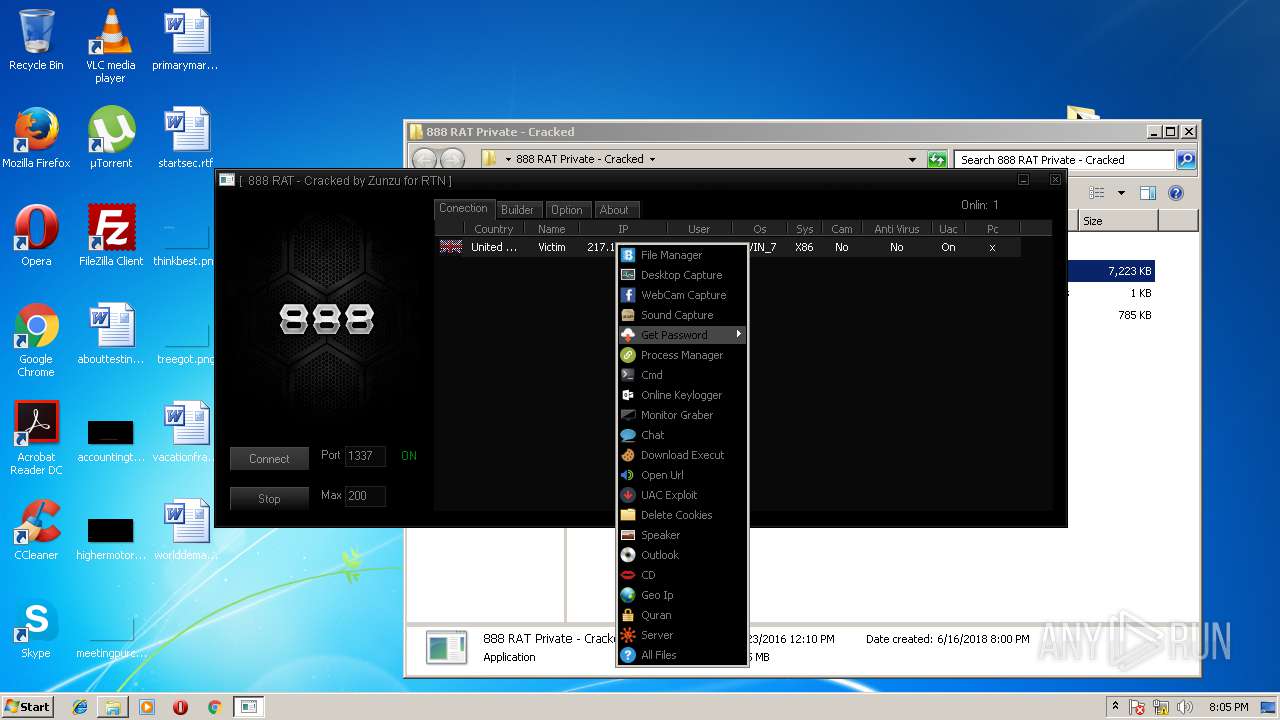
MALICIOUS
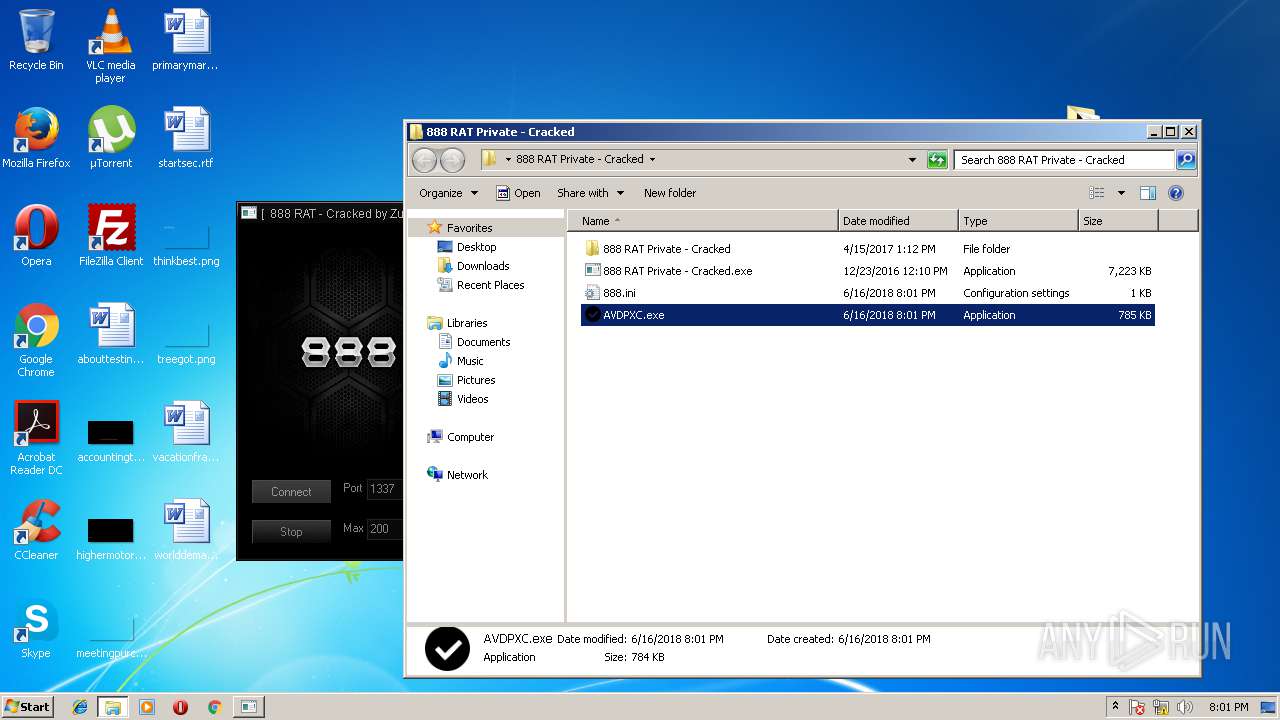
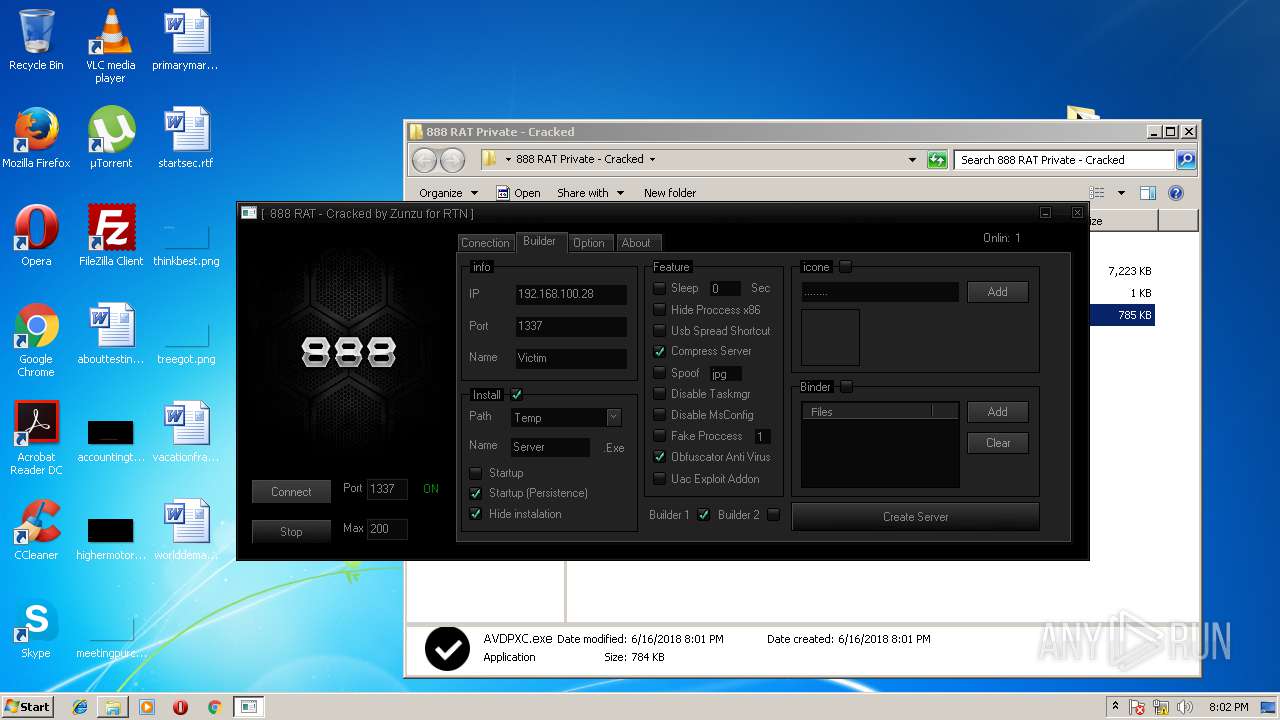
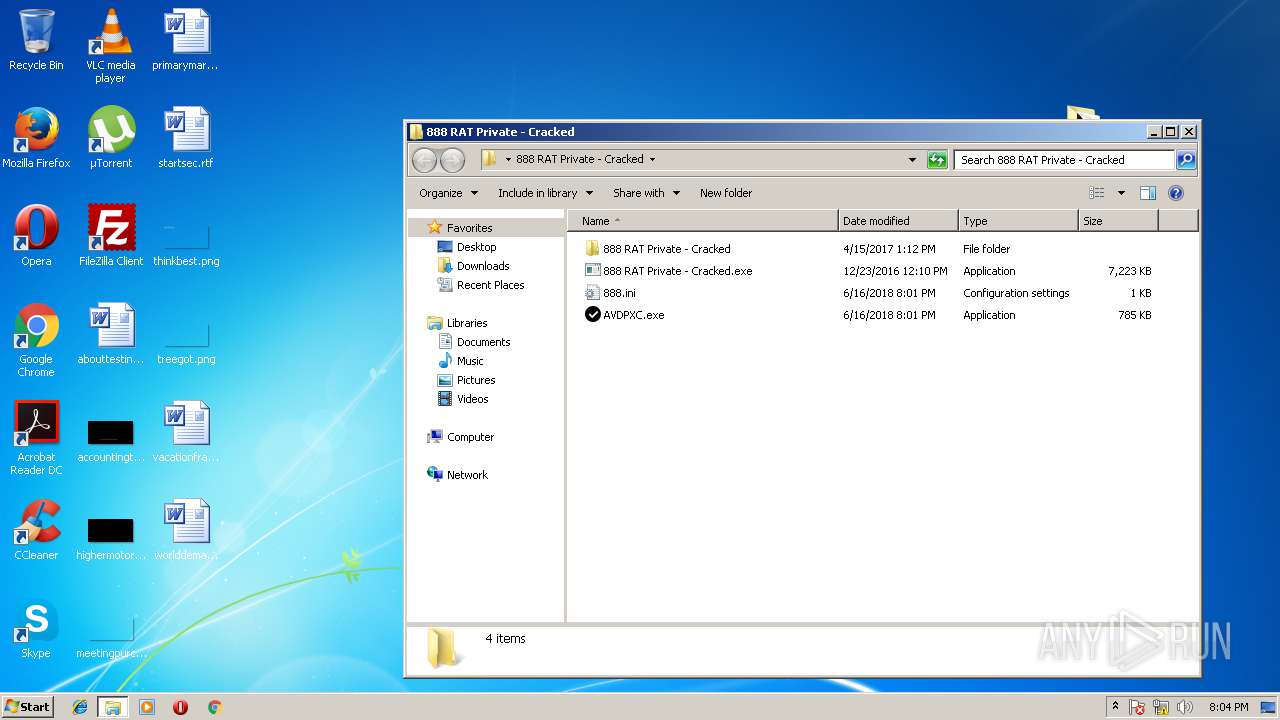
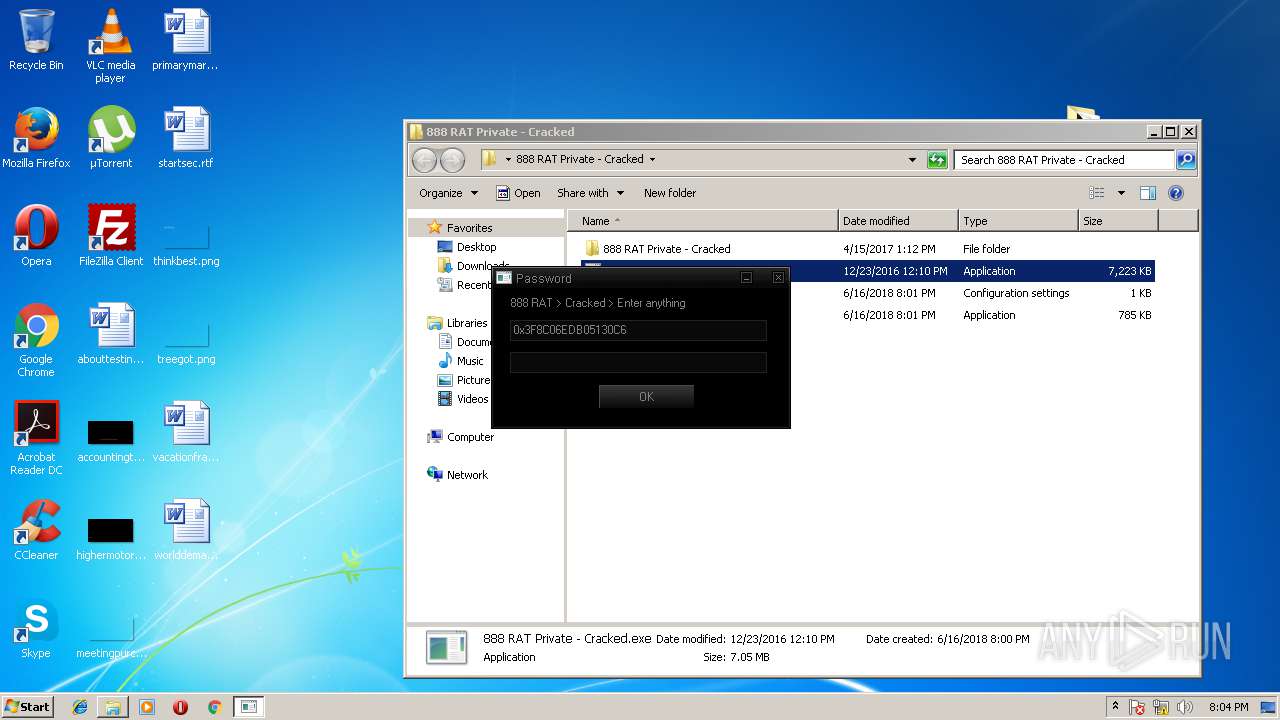
Application was dropped or rewritten from another process
- flagx.exe (PID: 2948)
- 888 RAT Private - Cracked.exe (PID: 900)
- Obfuscator.exe (PID: 2148)
- Aut2exe.exe (PID: 2164)
- upx.exe (PID: 3988)
- 888 RAT Private - Cracked.exe (PID: 2524)
- AVDPXC.exe (PID: 3128)
Loads dropped or rewritten executable
- 888 RAT Private - Cracked.exe (PID: 900)
- 888 RAT Private - Cracked.exe (PID: 2524)
Writes to a start menu file
- AVDPXC.exe (PID: 3128)
Runs app for hidden code execution
- AVDPXC.exe (PID: 3128)
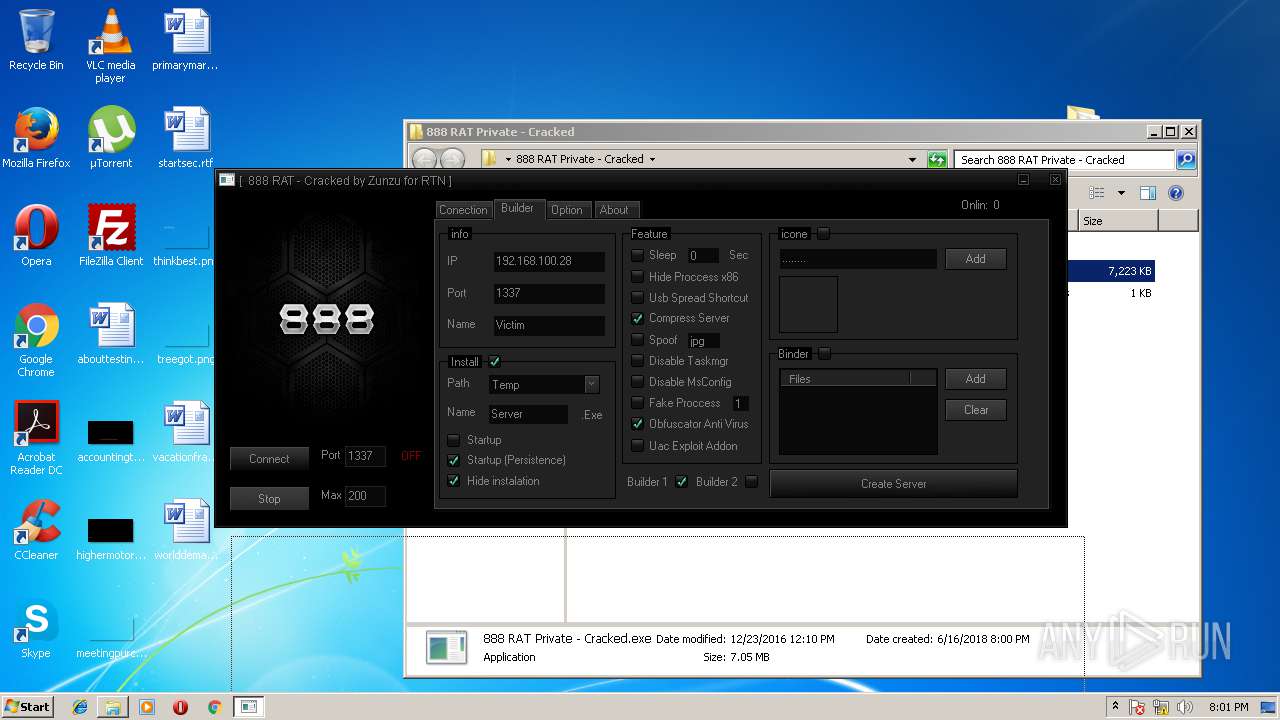
SUSPICIOUS
Application launched itself
- software_reporter_tool.exe (PID: 3652)
Executable content was dropped or overwritten
- 888 RAT Private - Cracked.exe (PID: 900)
- Aut2exe.exe (PID: 2164)
- upx.exe (PID: 3988)
- 888 RAT Private - Cracked.exe (PID: 2524)
- AVDPXC.exe (PID: 3128)
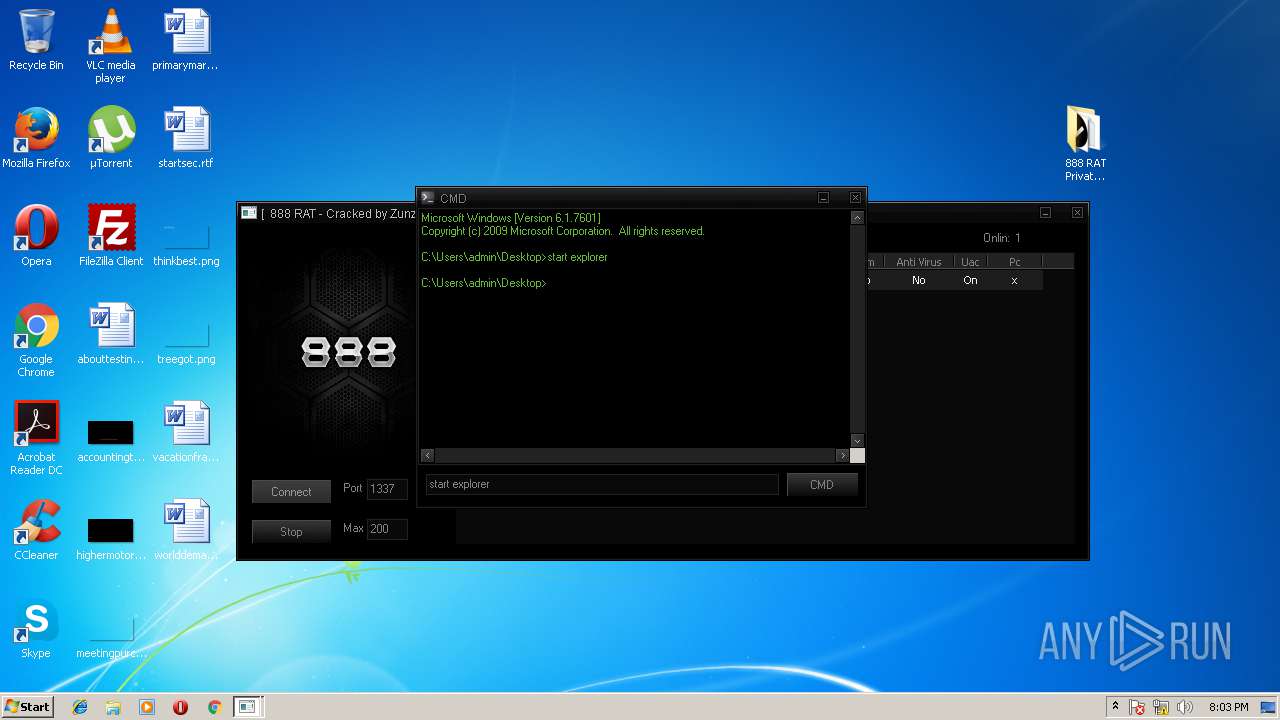
Starts CMD.EXE for commands execution
- 888 RAT Private - Cracked.exe (PID: 900)
- AVDPXC.exe (PID: 3128)
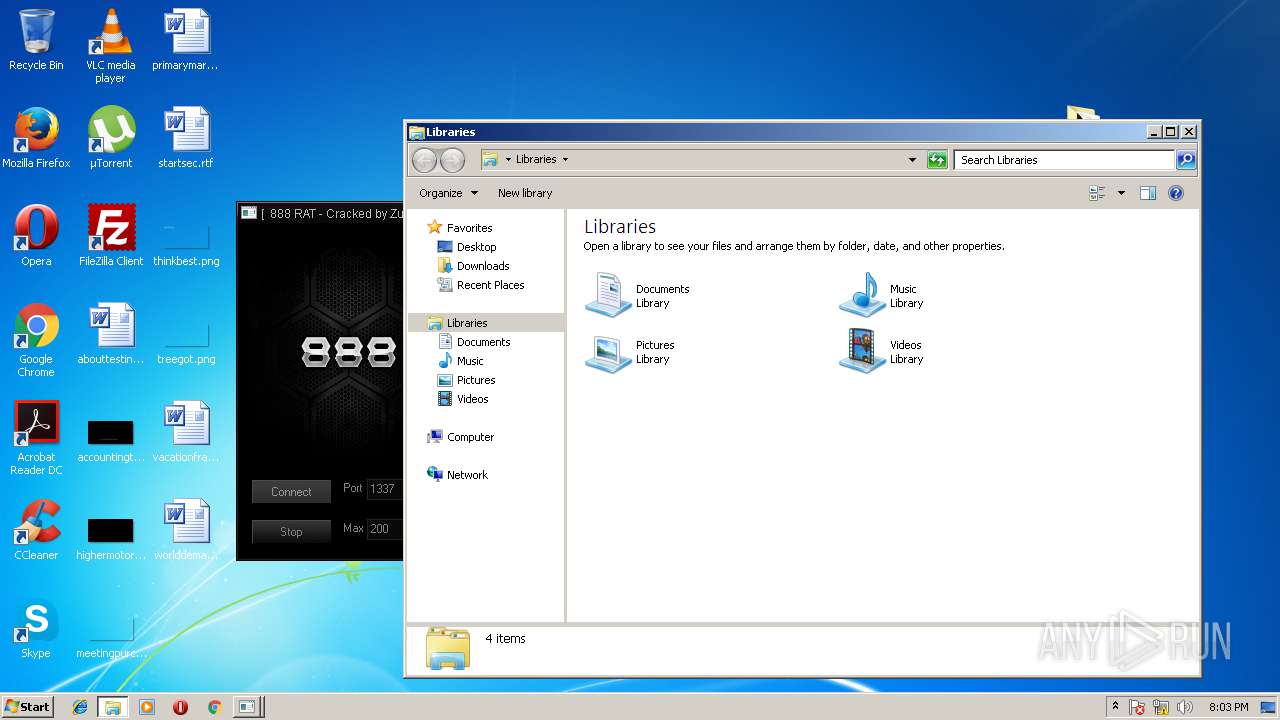
Creates files in the user directory
- AVDPXC.exe (PID: 3128)
Reads Internet Cache Settings
- rundll32.exe (PID: 620)
- rundll32.exe (PID: 3032)
- rundll32.exe (PID: 2940)
- rundll32.exe (PID: 4028)
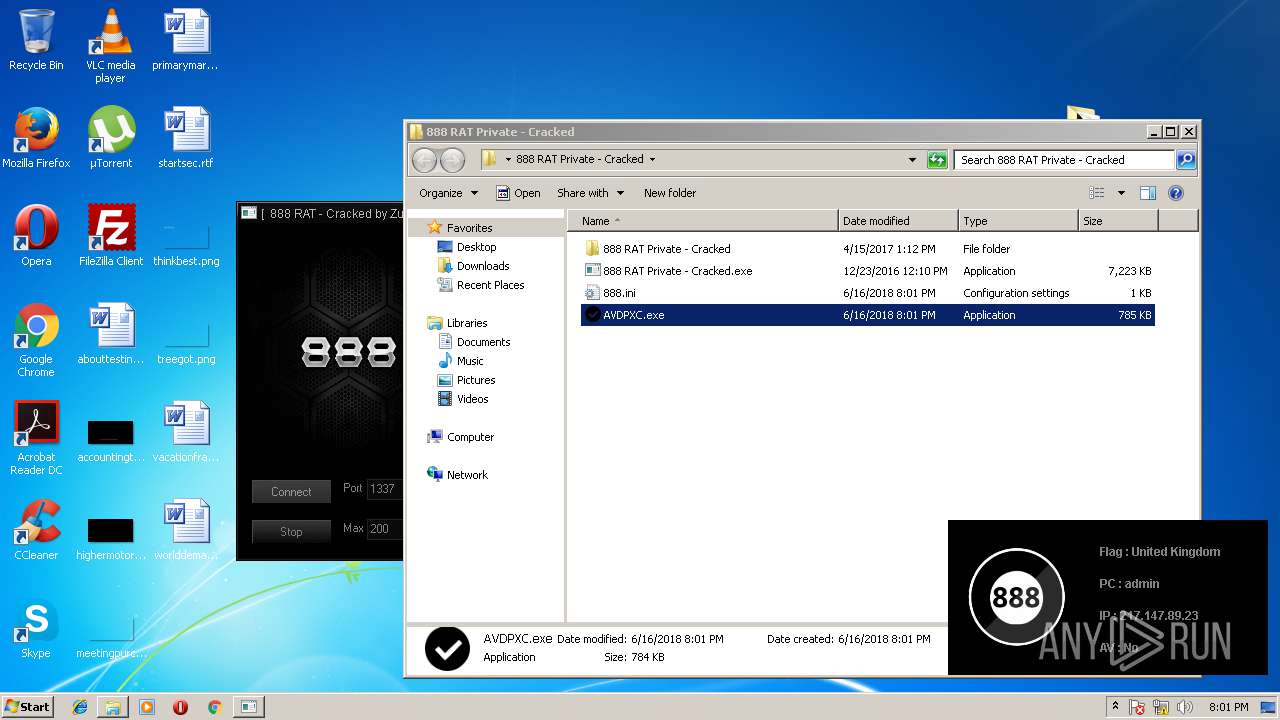
Checks for external IP
- AVDPXC.exe (PID: 3128)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 3236)
Changes internet zones settings
- iexplore.exe (PID: 3236)
Application launched itself
- iexplore.exe (PID: 3236)
- chrome.exe (PID: 3900)
Dropped object may contain URL's
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 3236)
- 888 RAT Private - Cracked.exe (PID: 900)
- chrome.exe (PID: 3900)
- Obfuscator.exe (PID: 2148)
- 888 RAT Private - Cracked.exe (PID: 2524)
- AVDPXC.exe (PID: 3128)
Reads internet explorer settings
- iexplore.exe (PID: 2876)
Reads Internet Cache Settings
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 3236)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 3652)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3236)
Changes settings of System certificates
- iexplore.exe (PID: 3236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
29
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
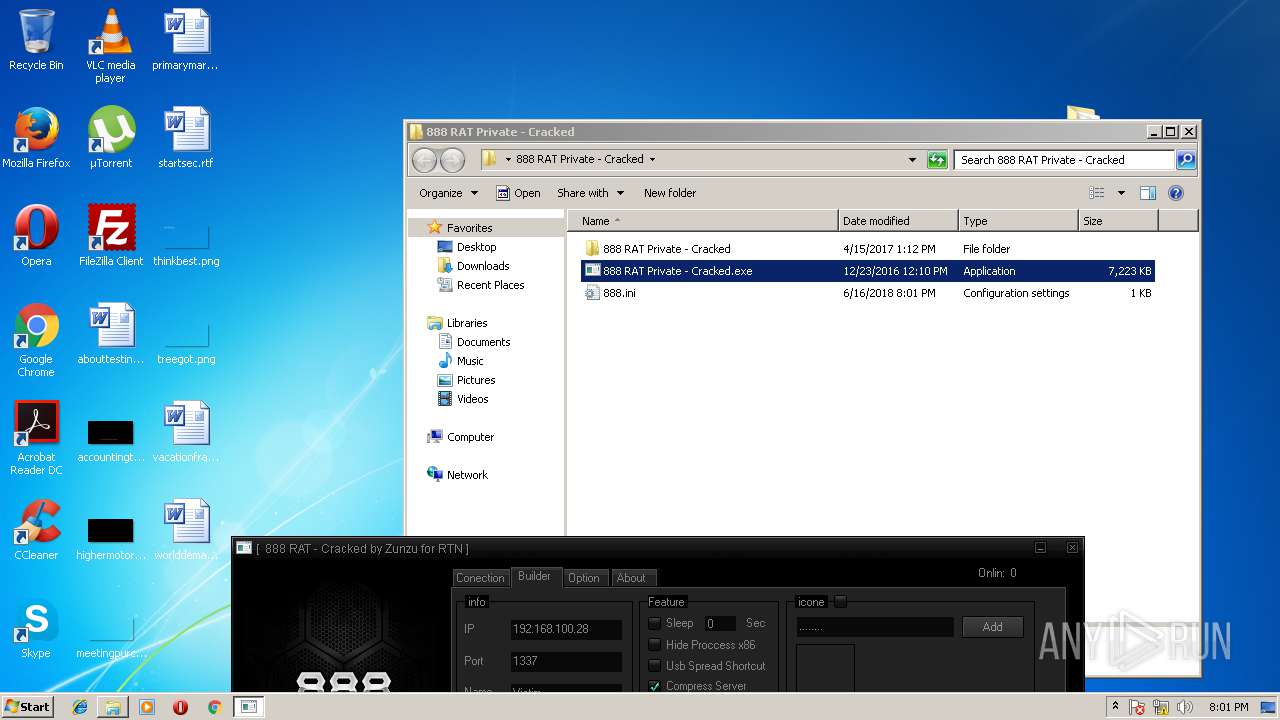
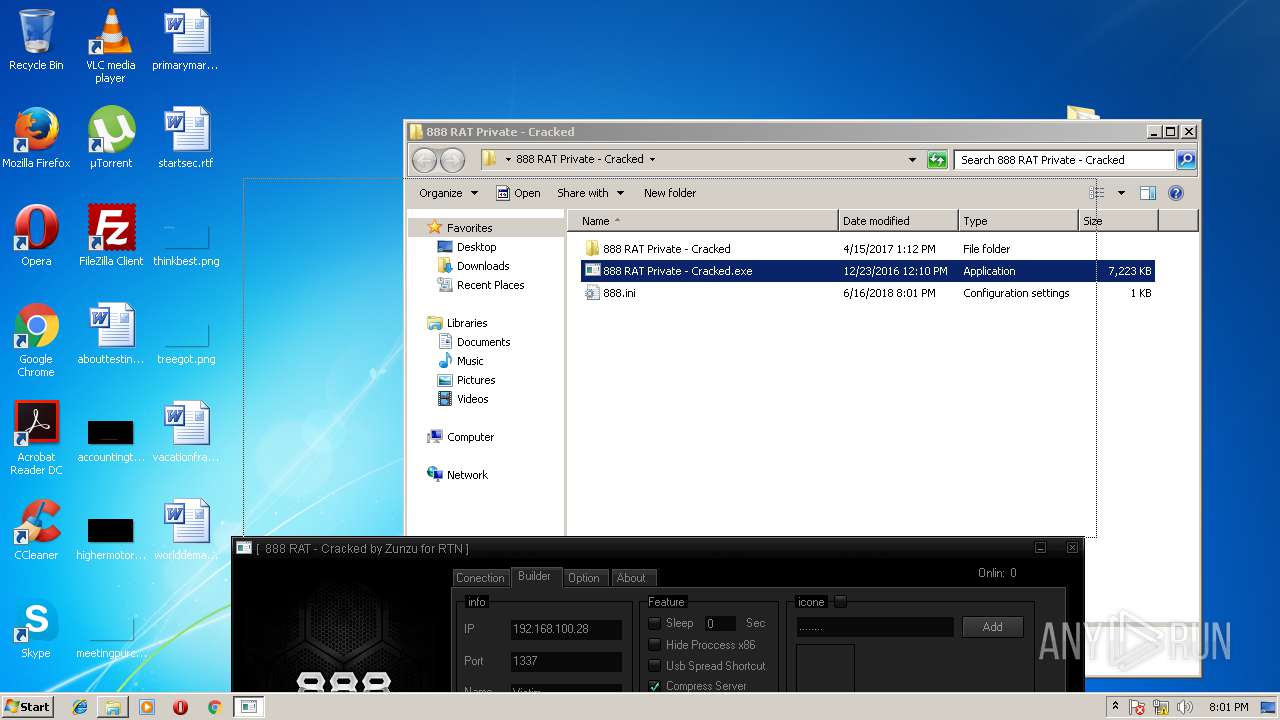
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | AVDPXC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
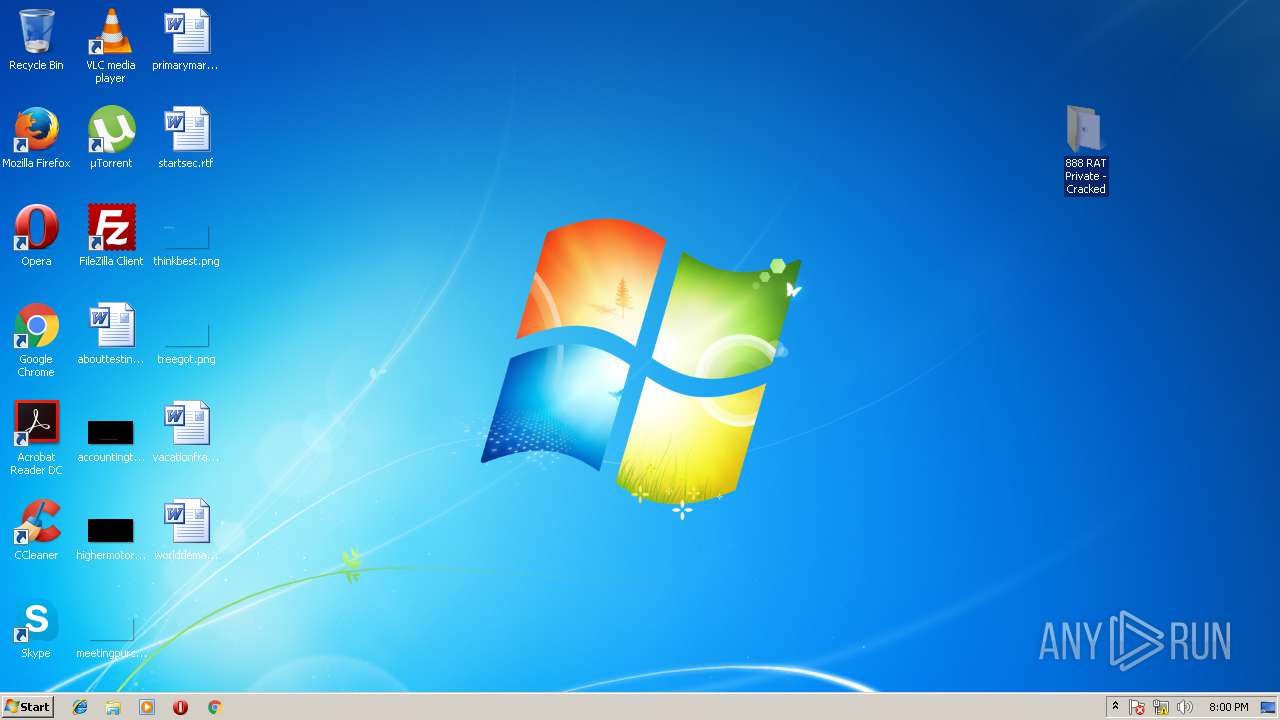
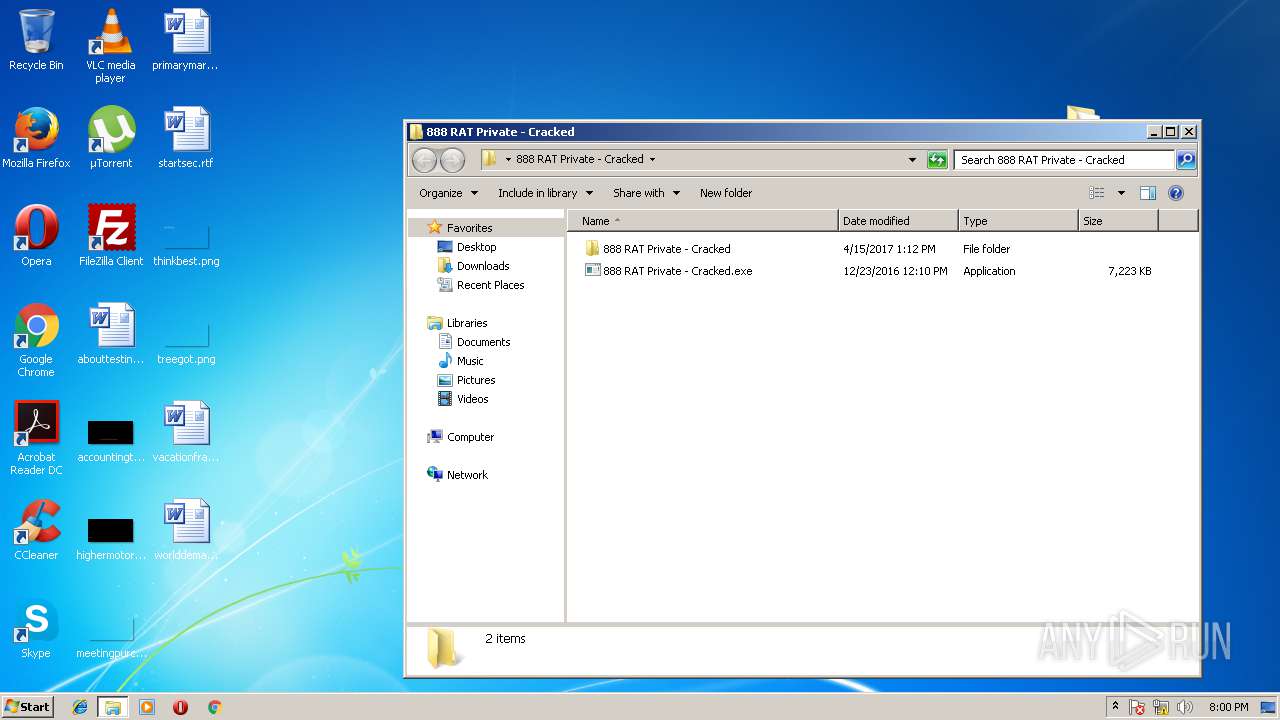
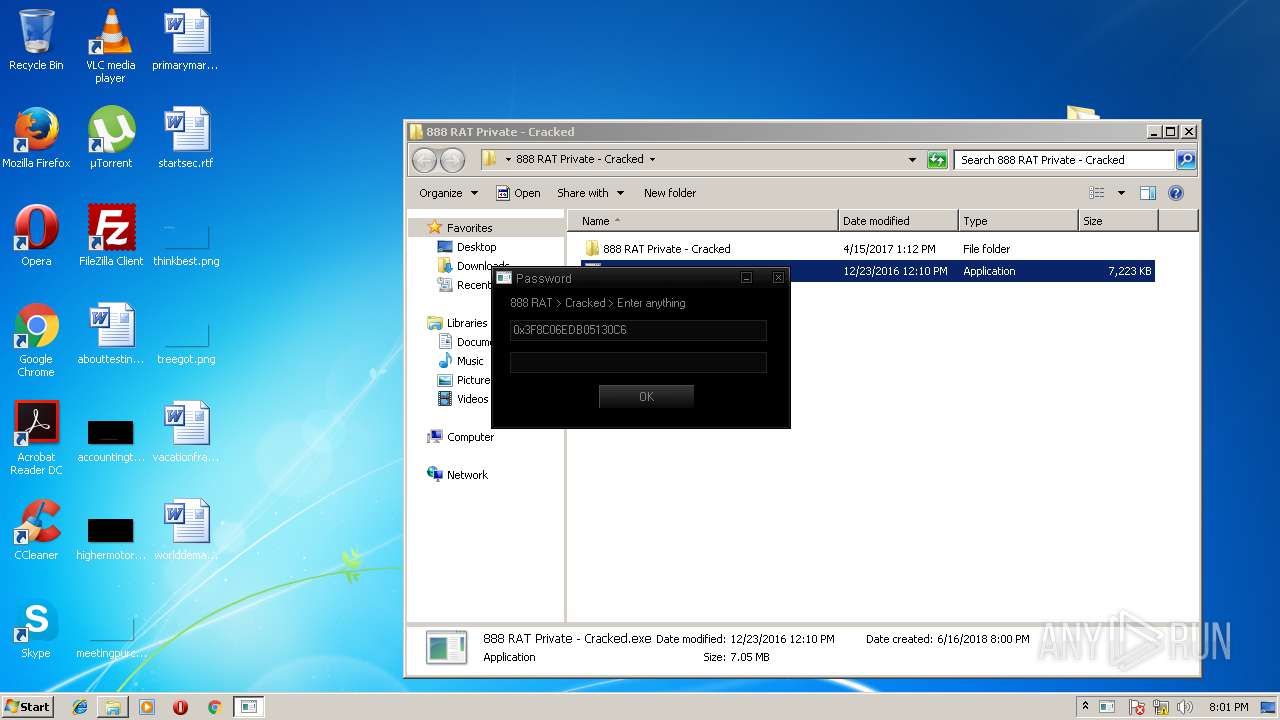
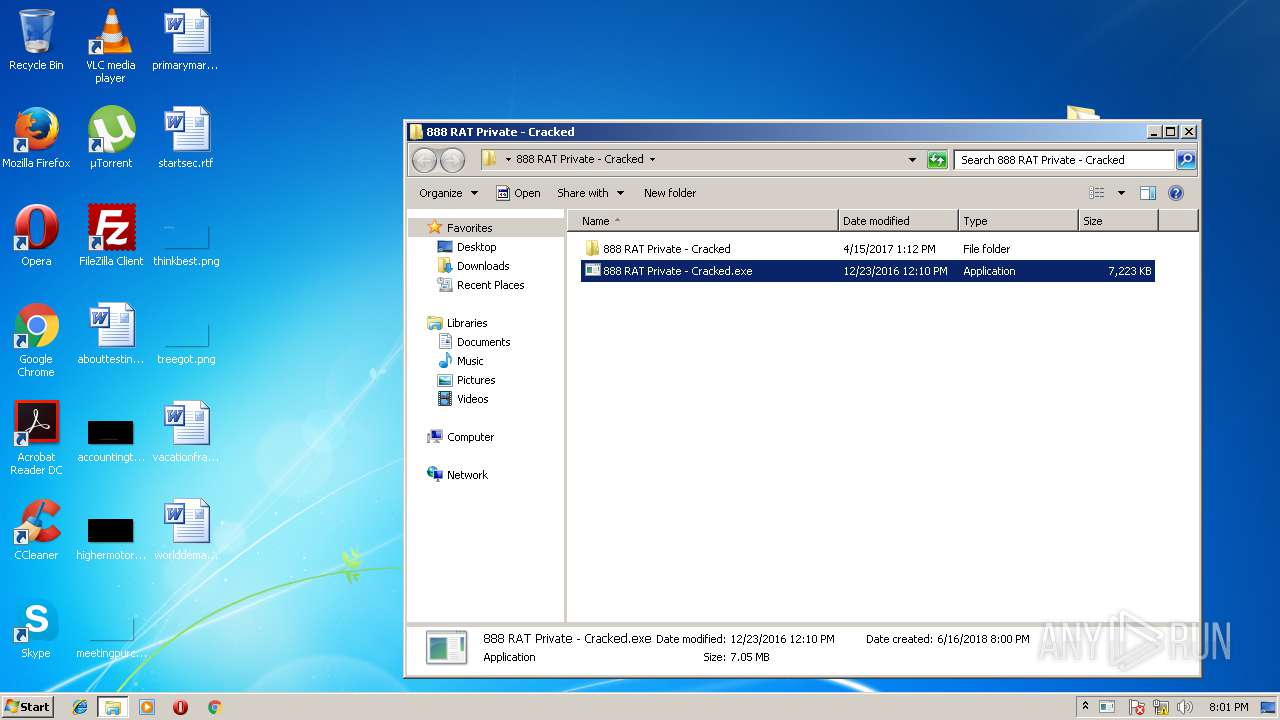
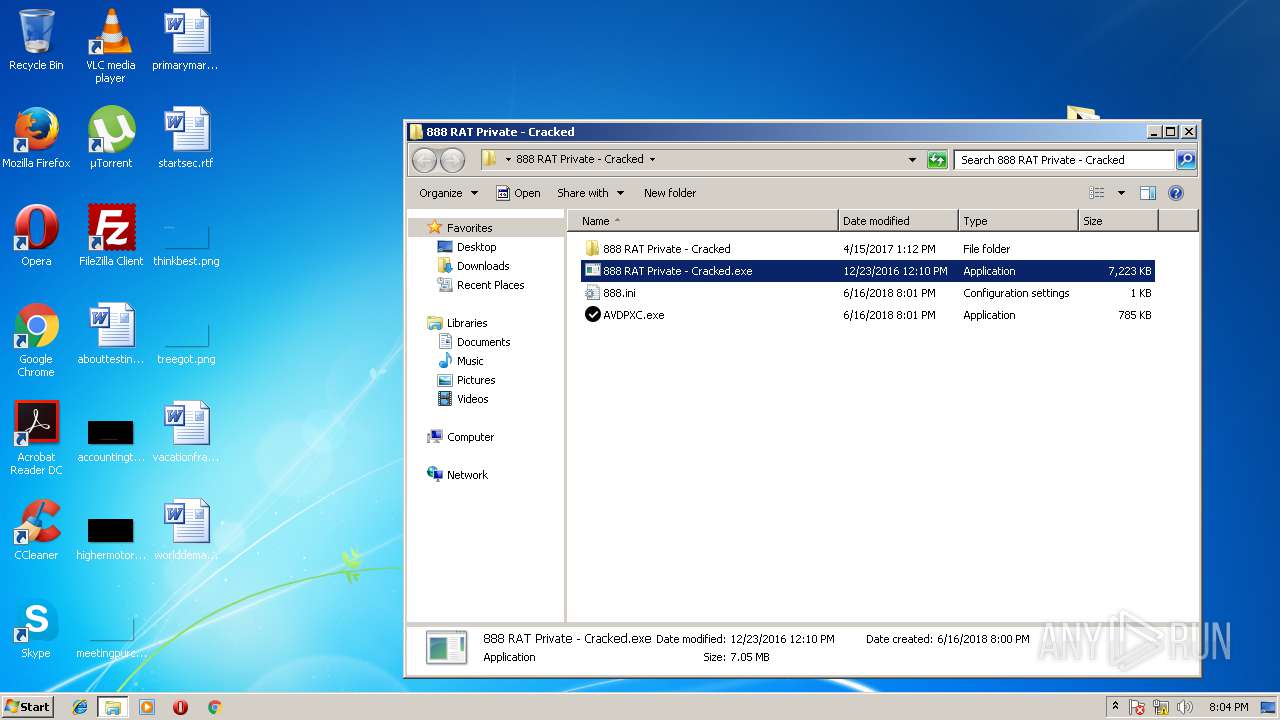
| 900 | "C:\Users\admin\Desktop\888 RAT Private - Cracked\888 RAT Private - Cracked.exe" | C:\Users\admin\Desktop\888 RAT Private - Cracked\888 RAT Private - Cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 1616 | explorer | C:\Windows\explorer.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1616 | ipconfig | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1600,10216688186975681857,13422416391357201734,131072 --service-pipe-token=ED974B1E66EAA91A1871181D3AB5DA66 --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=ED974B1E66EAA91A1871181D3AB5DA66 --renderer-client-id=4 --mojo-platform-channel-handle=1612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2148 | Obfuscator.exe Server.au3 | C:\Users\admin\AppData\Local\Temp\Obfuscator.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Strip and/or Obfuscate your AutoIt3 scripts. Exit code: 5 Version: 1.0.31.0 Modules
| |||||||||||||||
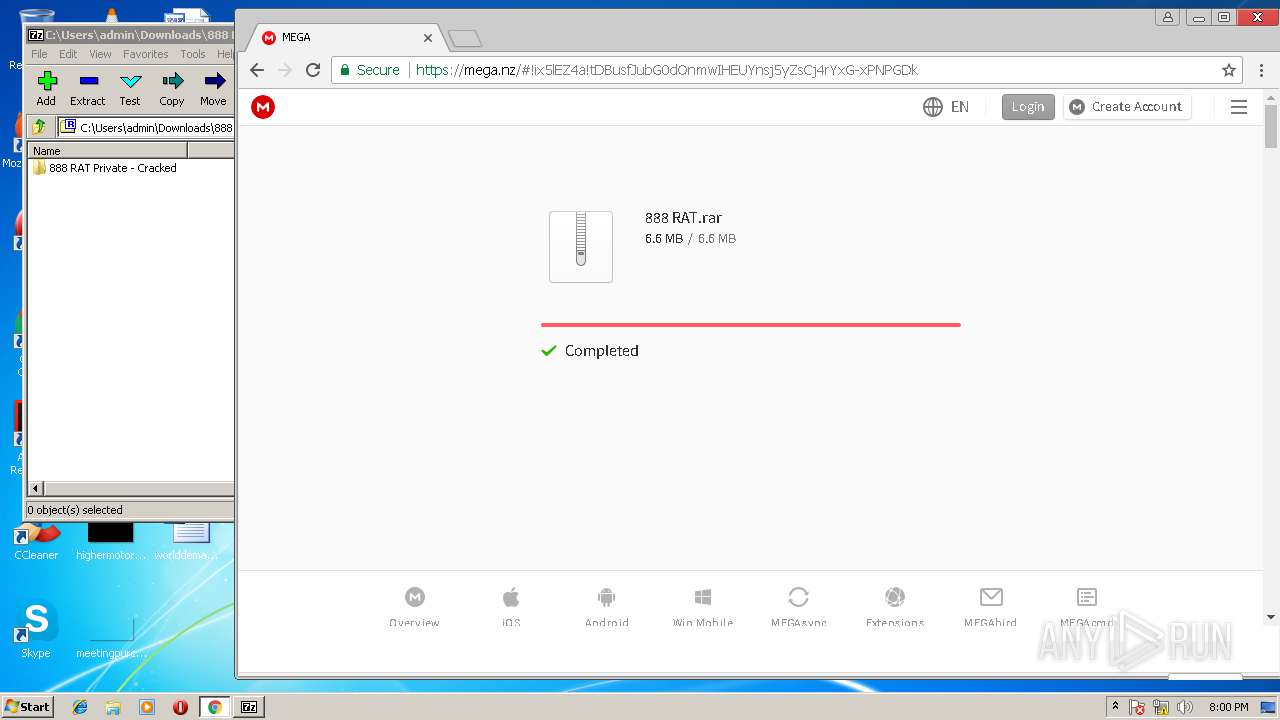
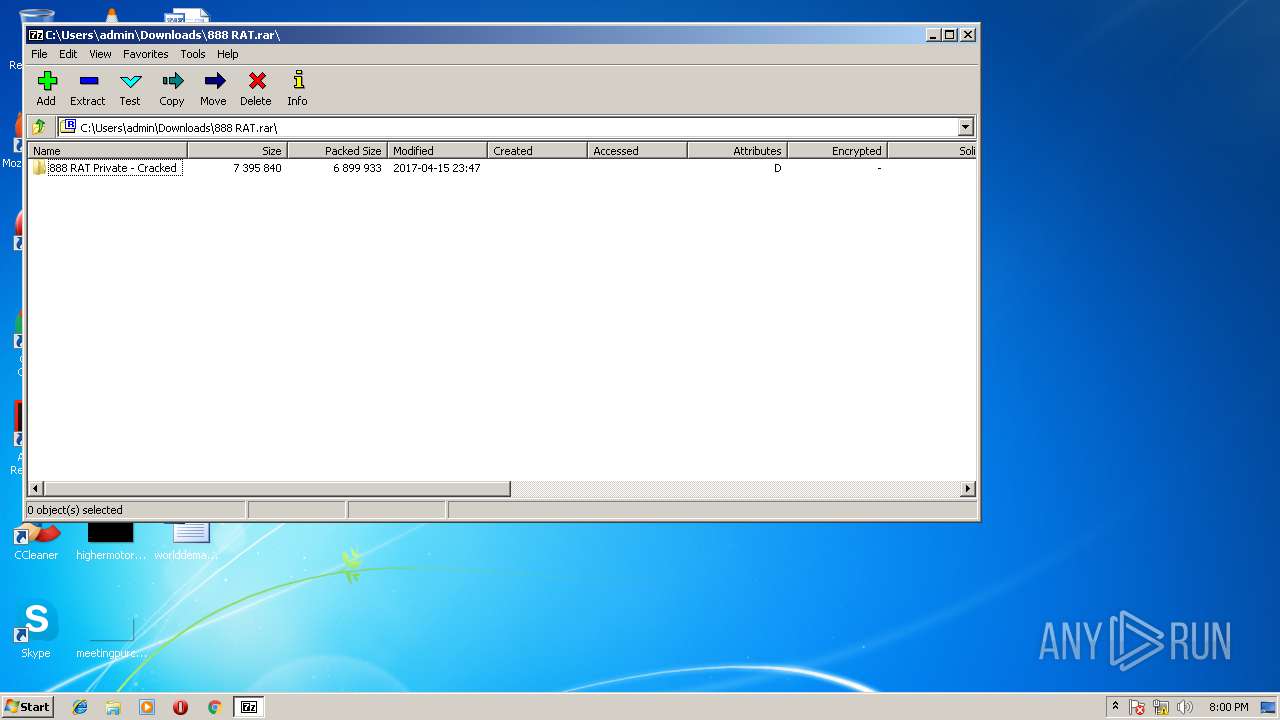
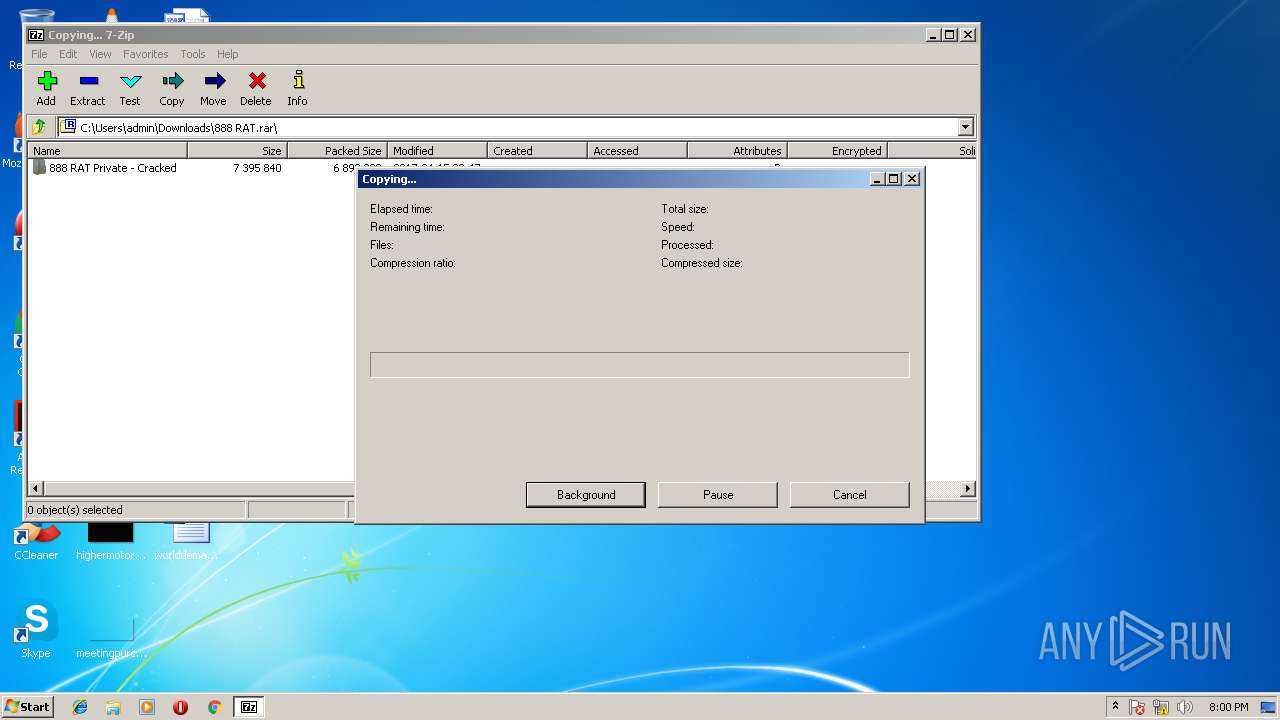
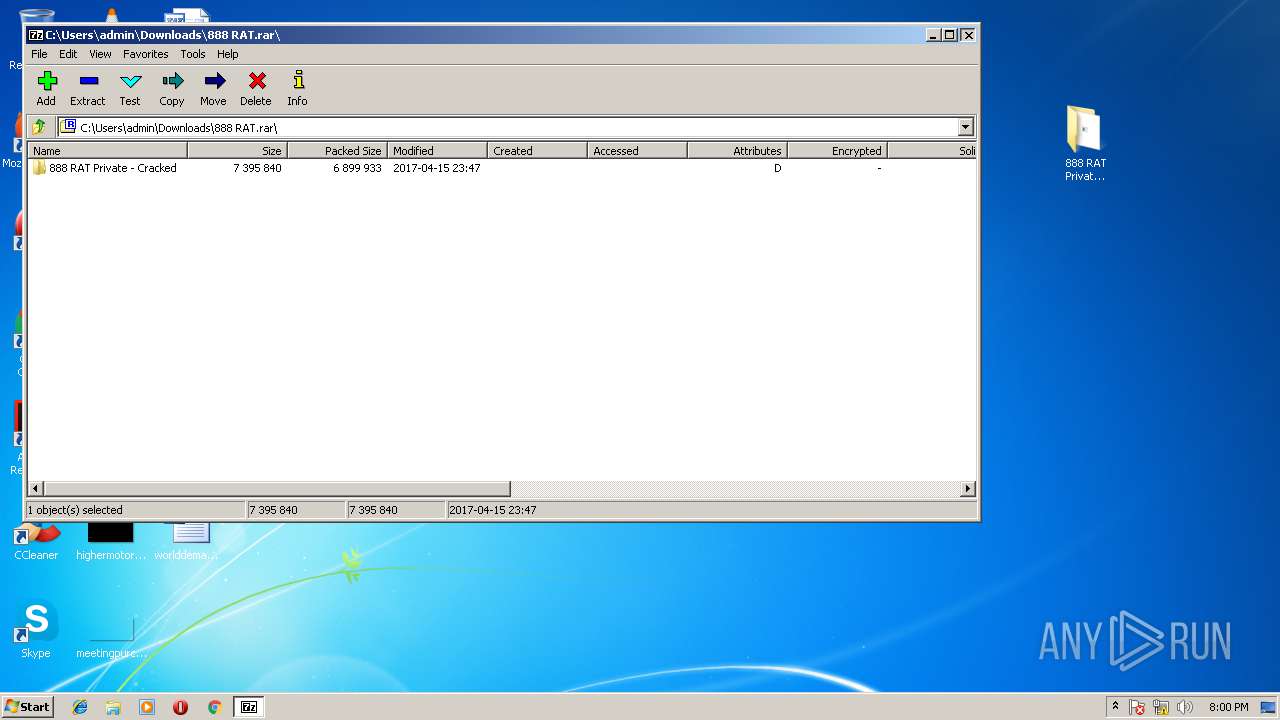
| 2160 | "C:\Program Files\7-Zip\7zFM.exe" "C:\Users\admin\Downloads\888 RAT.rar" | C:\Program Files\7-Zip\7zFM.exe | — | chrome.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
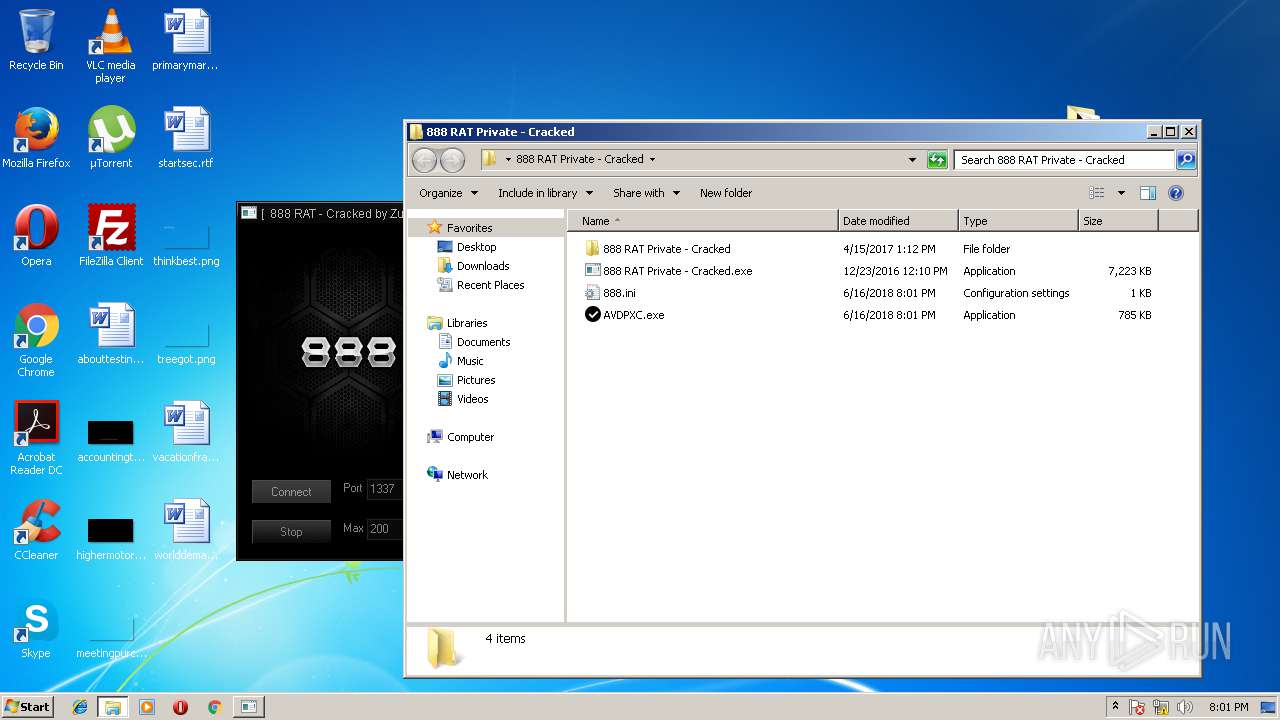
| 2164 | C:\Users\admin\AppData\Local\Temp\Aut2exe.exe /in C:\Users\admin\AppData\Local\Temp/Server.au3 /out C:\Users\admin\AppData\Local\Temp/AVDPXC.exe /icon C:\Users\admin\AppData\Local\Temp\ssc.ico /comp 2 /pack /Unicode | C:\Users\admin\AppData\Local\Temp\Aut2exe.exe | 888 RAT Private - Cracked.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: Aut2Exe Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.100 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f8a7d7c,0x6f8a7da4,0x6f8a7d8c | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
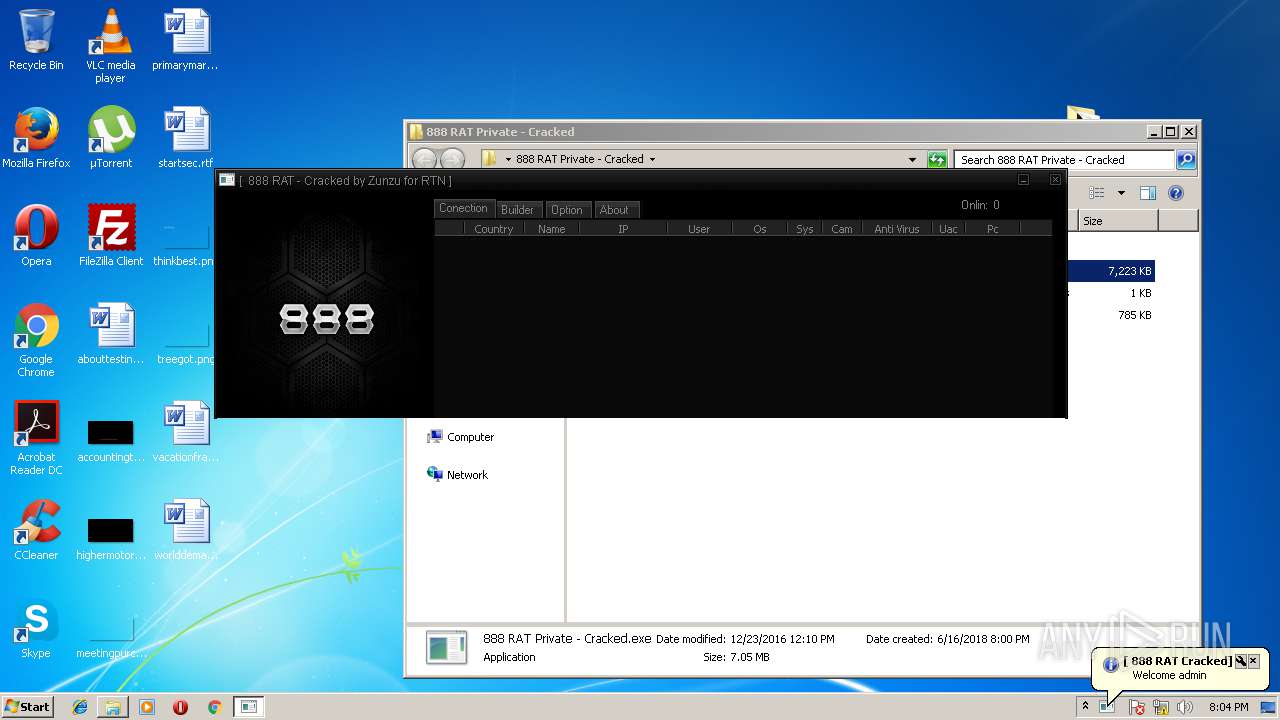
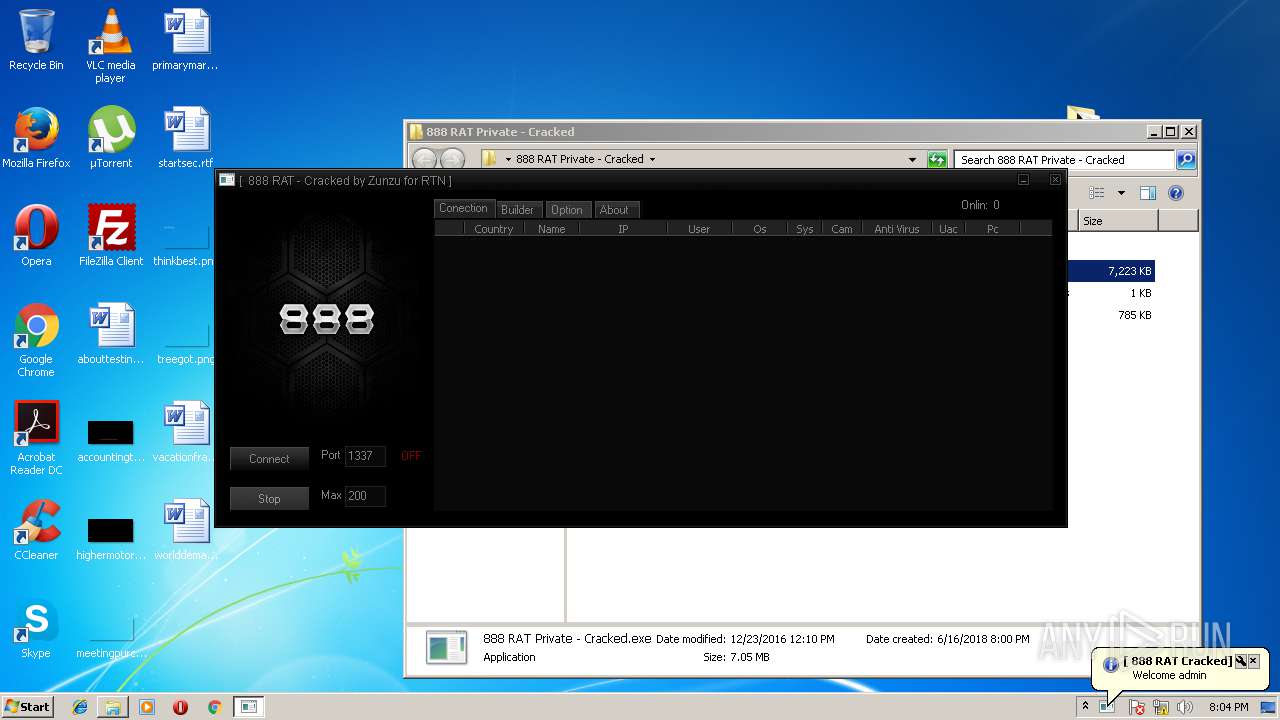
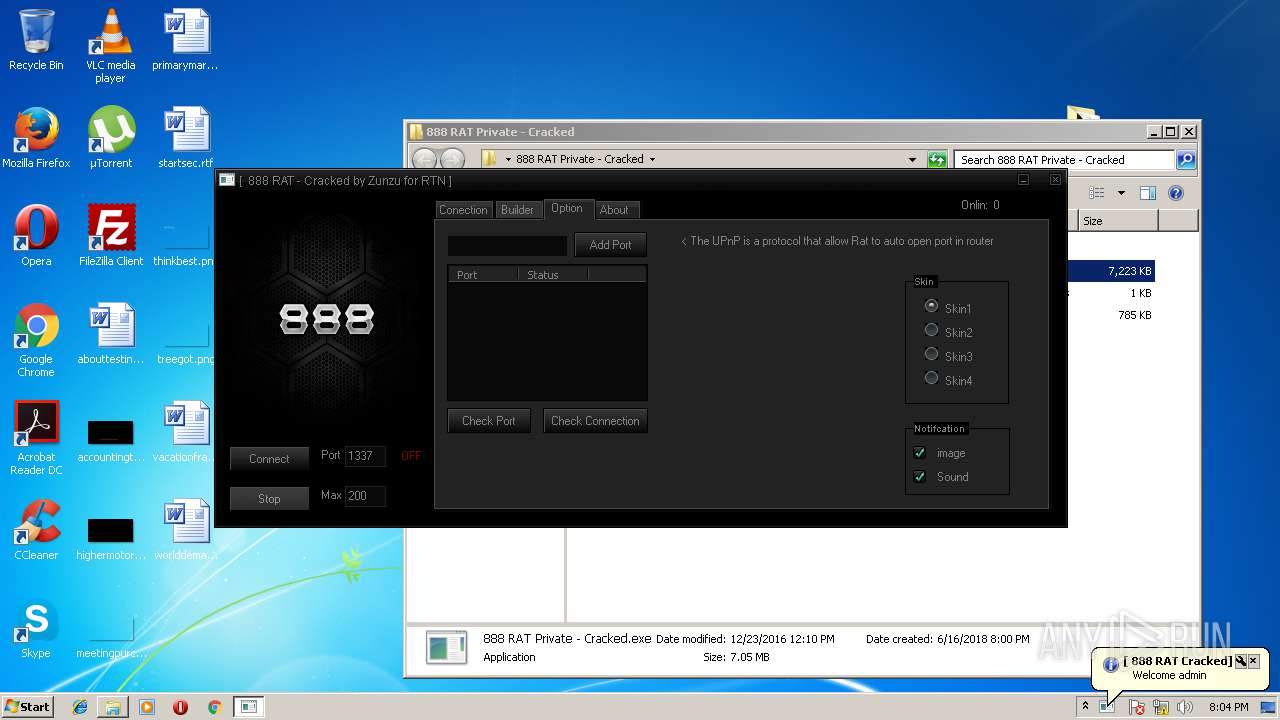
| 2524 | "C:\Users\admin\Desktop\888 RAT Private - Cracked\888 RAT Private - Cracked.exe" | C:\Users\admin\Desktop\888 RAT Private - Cracked\888 RAT Private - Cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 248
Read events
1 852
Write events
381
Delete events
15
Modification events
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006B000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {7DD003EB-7197-11E8-B27F-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207060006001000130000000B00C000 | |||
Executable files
32
Suspicious files
83
Text files
421
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF57130F5E4D437ACC.TMP | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5C7381F13B9FB742.TMP | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF425477786EE266B2.TMP | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7DD003EC-7197-11E8-B27F-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDDF3255FA7AF6ACC.TMP | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{7DD003EB-7197-11E8-B27F-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000040.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
28
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3900 | chrome.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEAanQ4DU6%2F7UNbWj9%2BFqvdg%3D | GB | der | 727 b | whitelisted |
3900 | chrome.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | GB | der | 471 b | whitelisted |
3128 | AVDPXC.exe | GET | 200 | 95.211.125.236:80 | http://ip-score.com/checkip/ | NL | html | 9.52 Kb | shared |
3900 | chrome.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT0MXB3rveIElndnl0j8v4md2bQRgQUOdr%2FyigUiqh0Ewi55A6p0vp%2BnWkCEHufHZnyvEFnS%2Bni68rHsIU%3D | GB | der | 471 b | whitelisted |
3236 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3236 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2876 | iexplore.exe | 31.216.148.10:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
3900 | chrome.exe | 172.217.21.195:443 | www.google.ru | Google Inc. | US | whitelisted |
3900 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 172.217.23.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 216.58.208.46:443 | apis.google.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 178.255.83.1:80 | ocsp.usertrust.com | CCANET Limited | GB | unknown |
3900 | chrome.exe | 31.216.147.133:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
mega.nz |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.ru |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3128 | AVDPXC.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
3128 | AVDPXC.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-score.com |