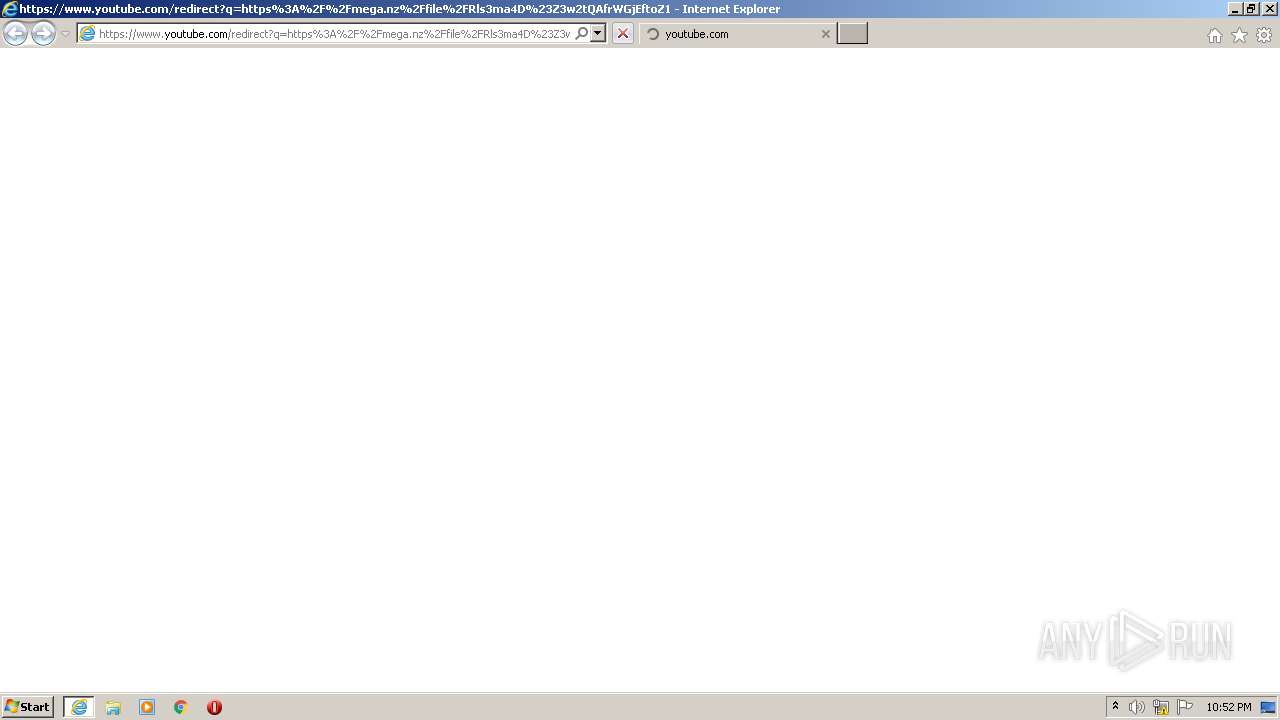
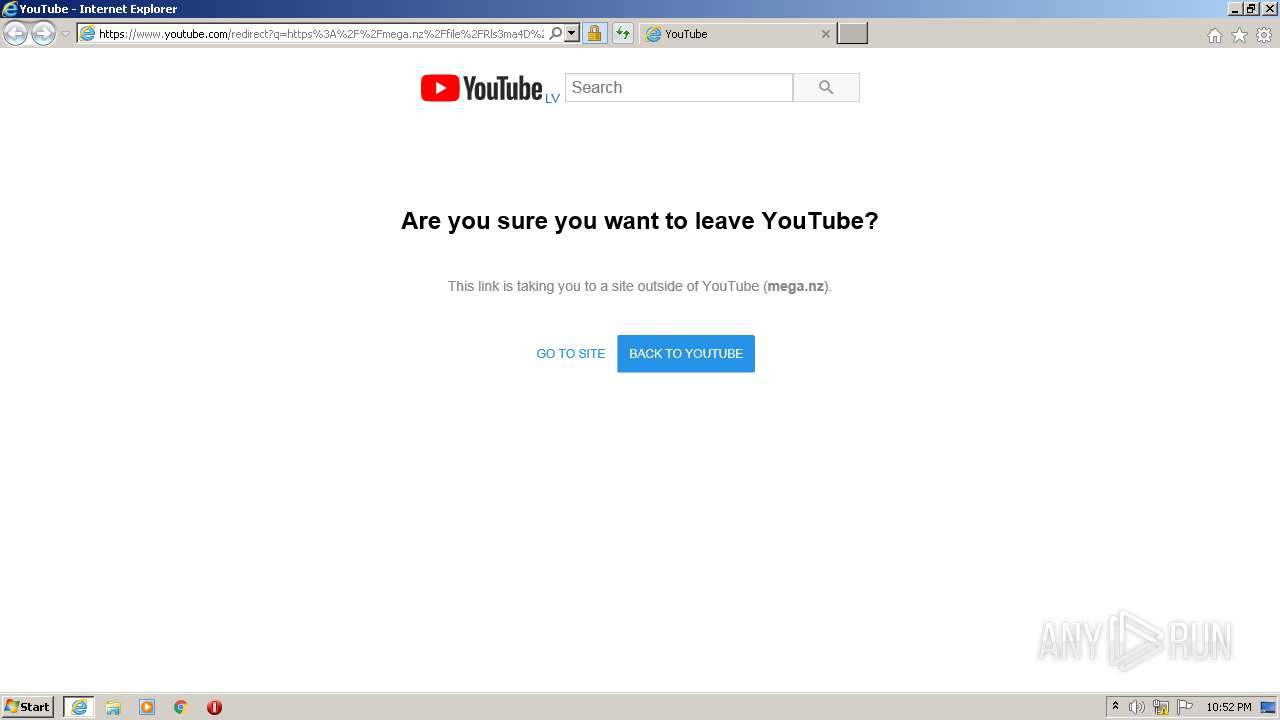
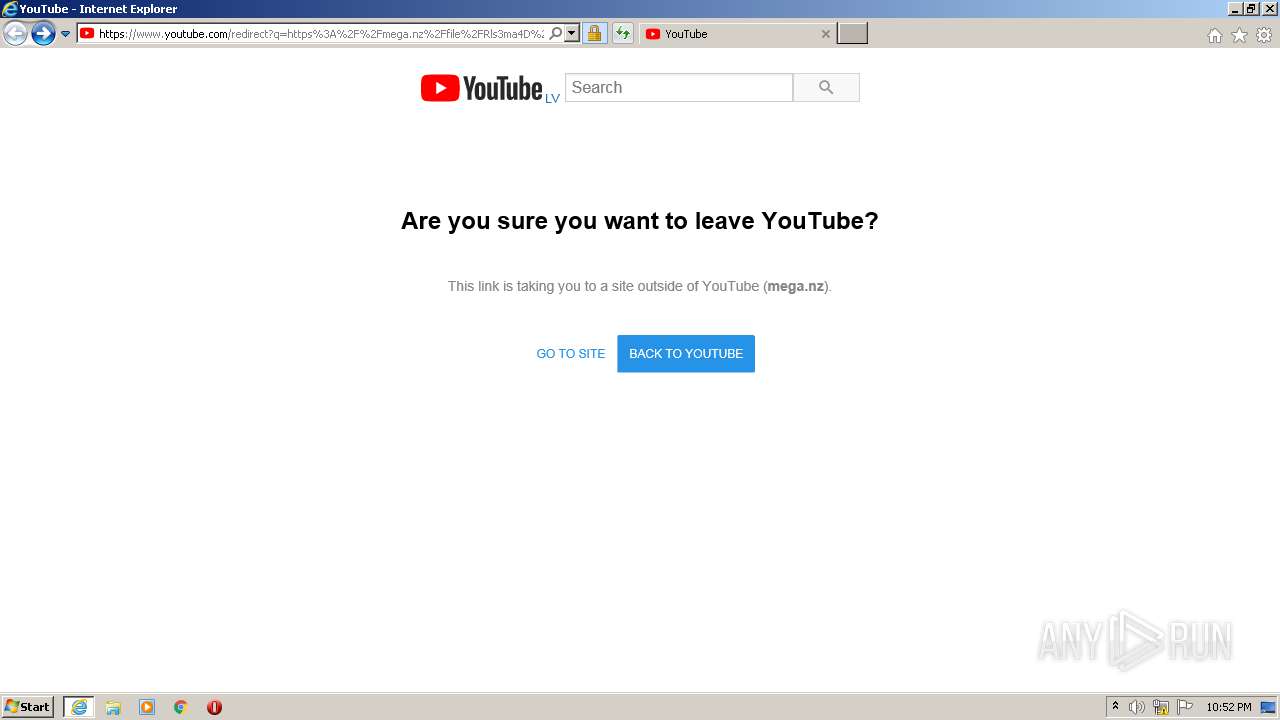
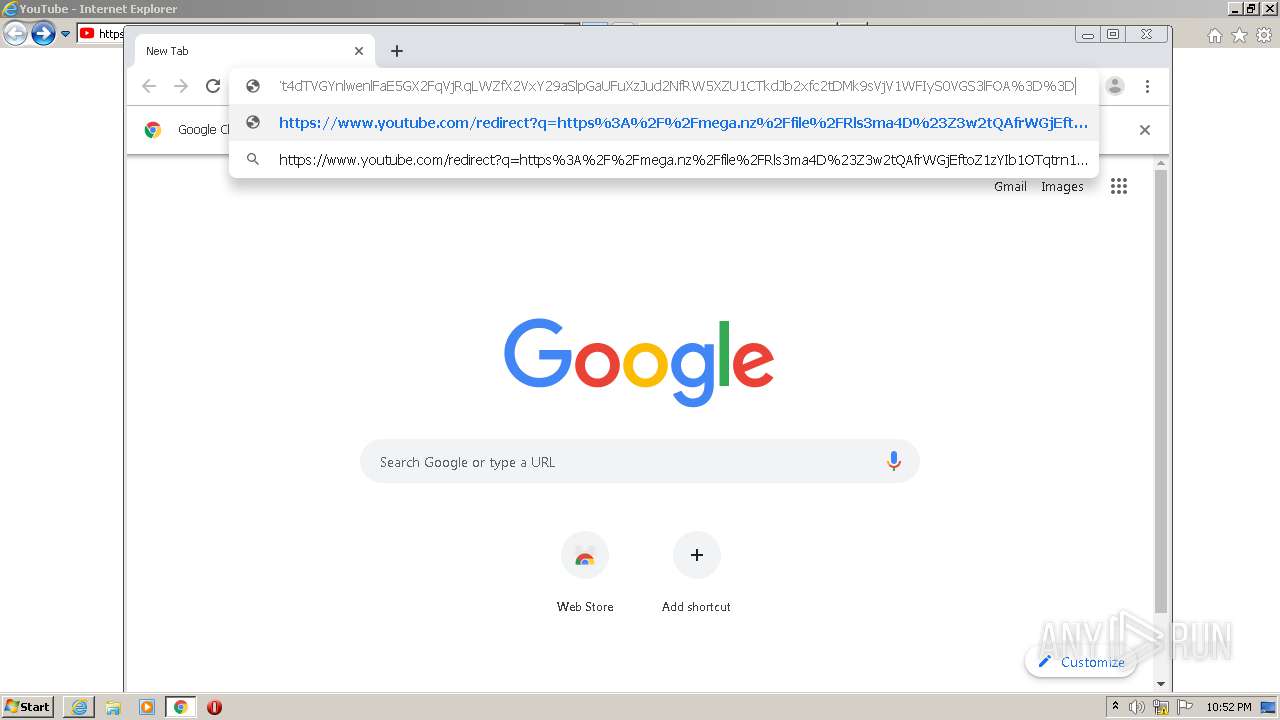
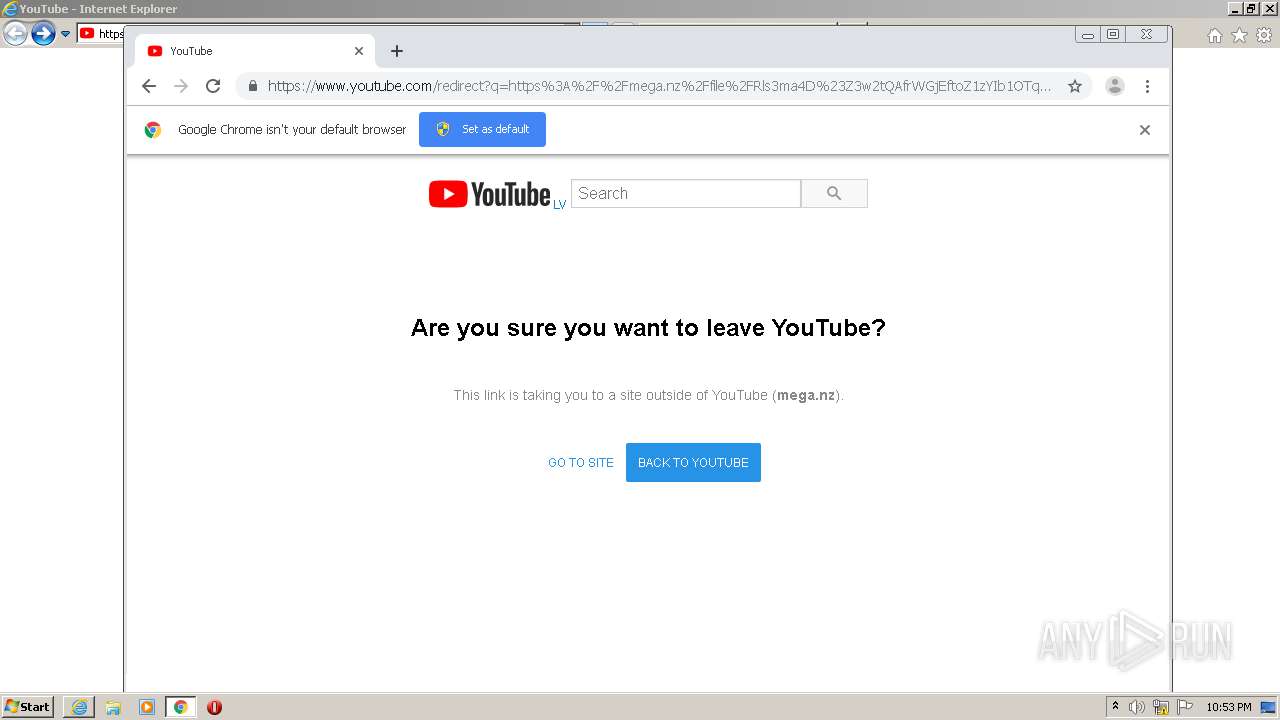
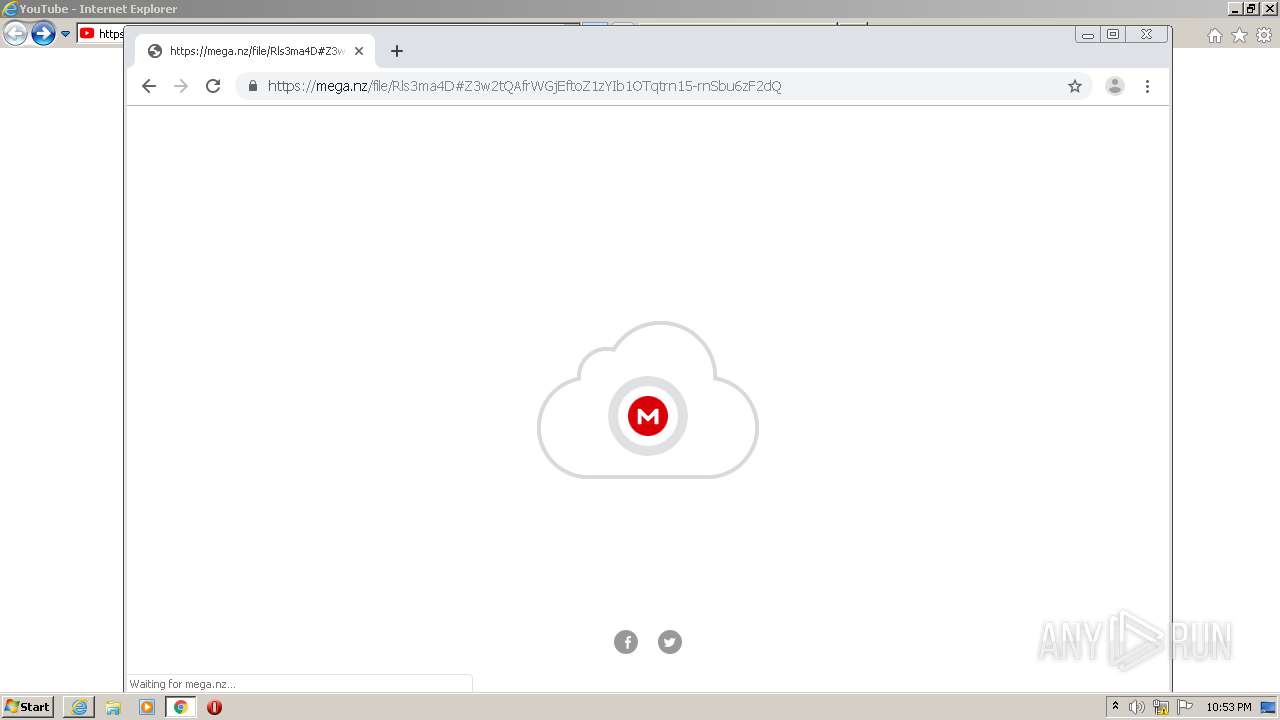
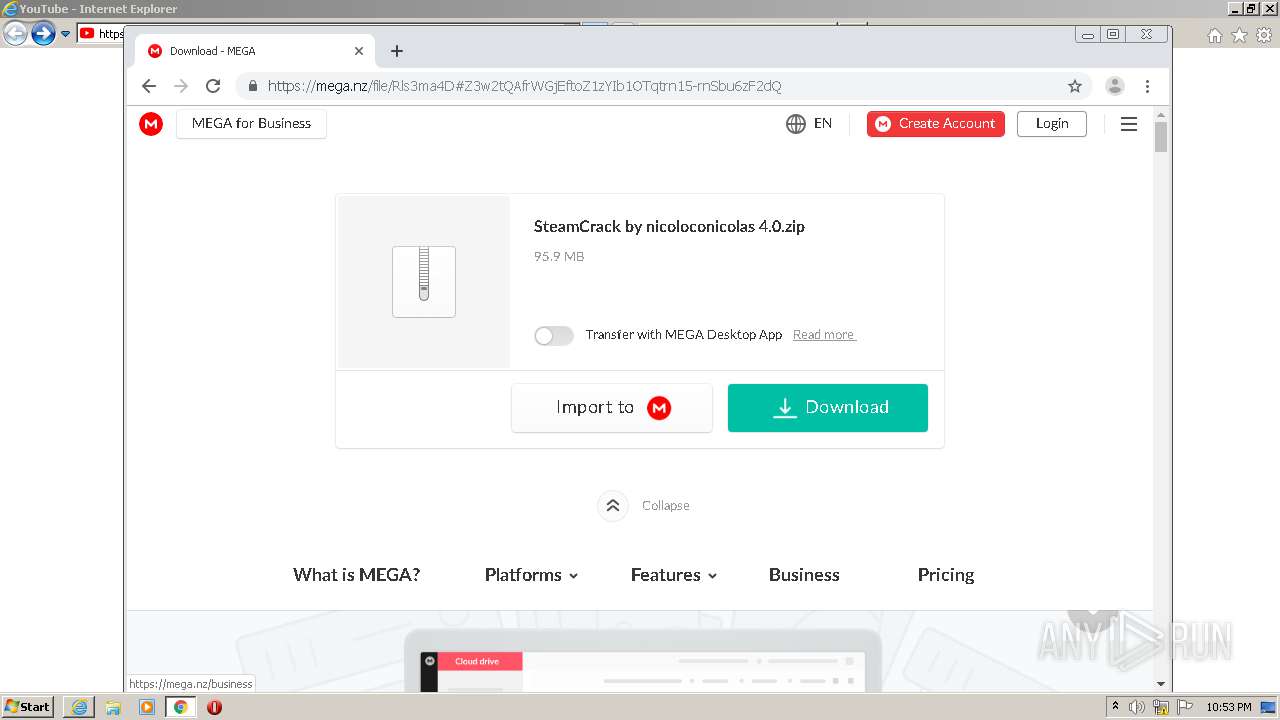
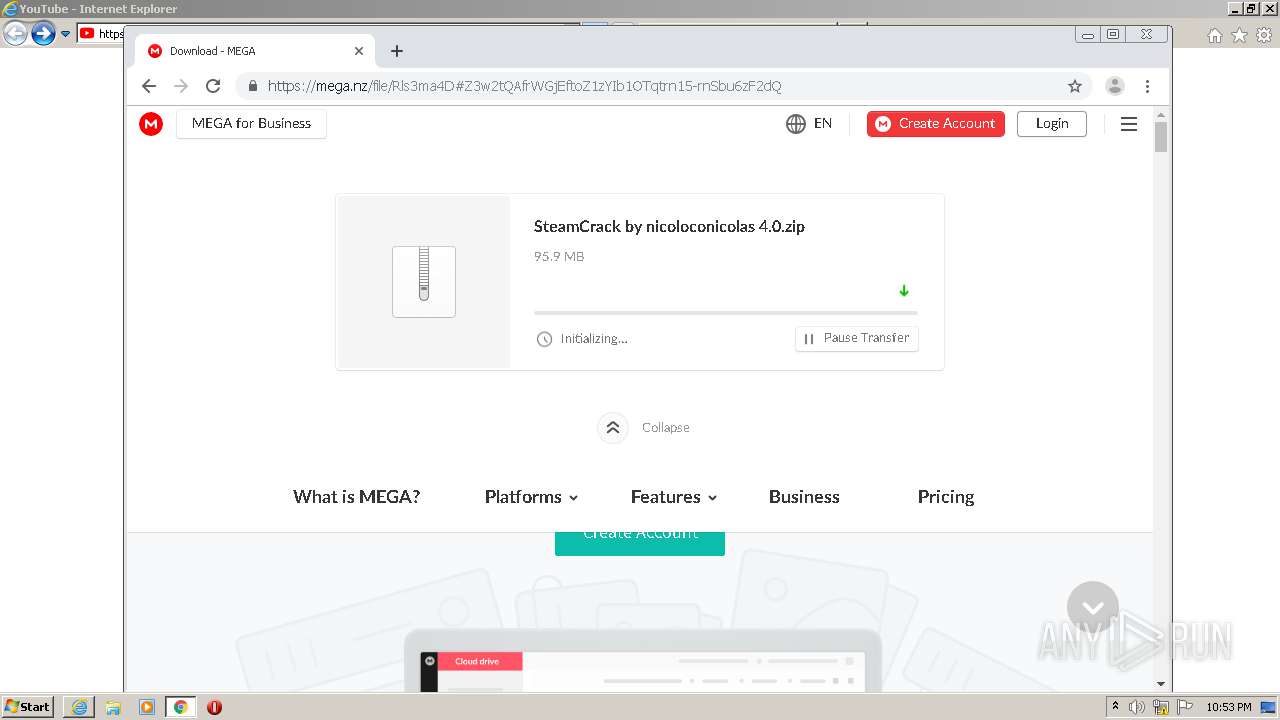
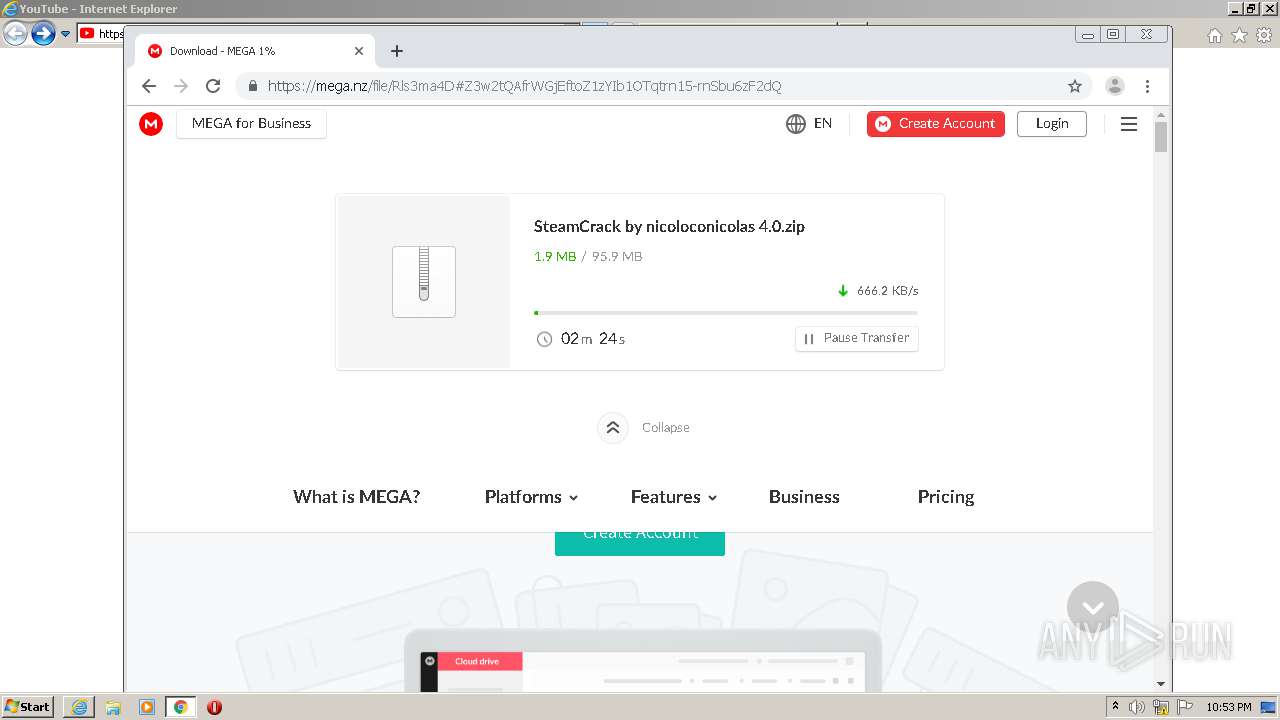
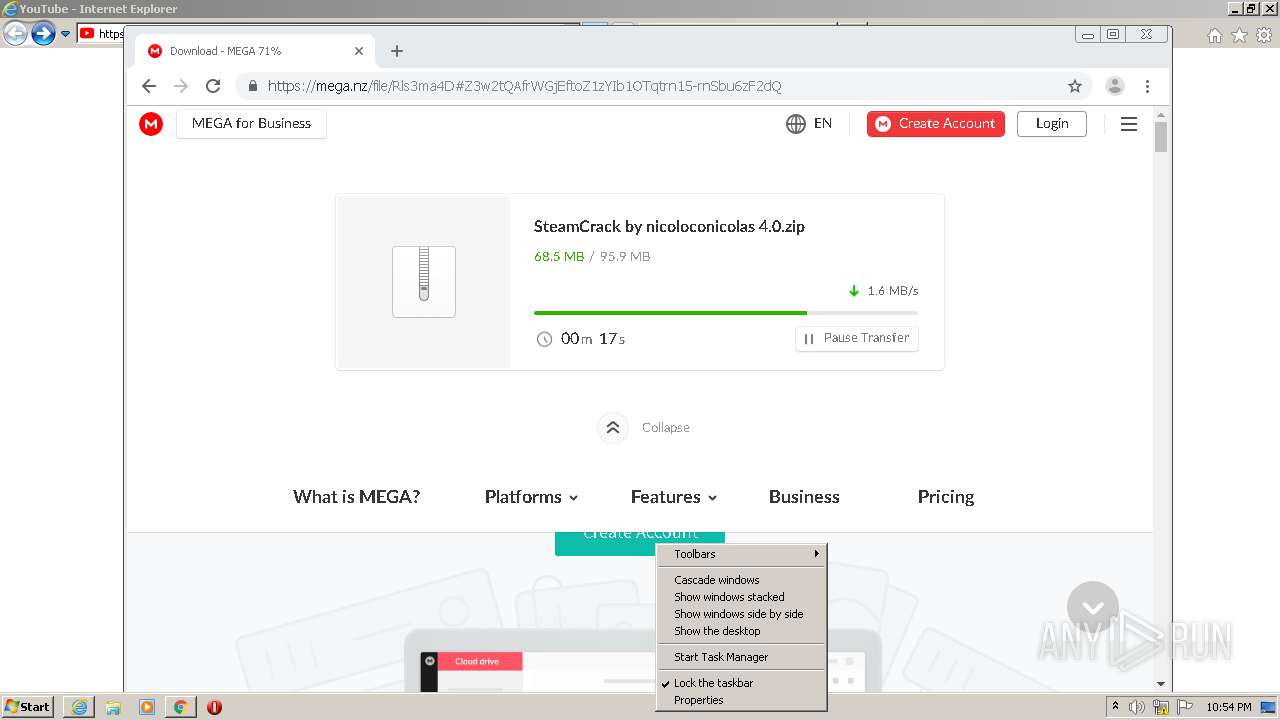
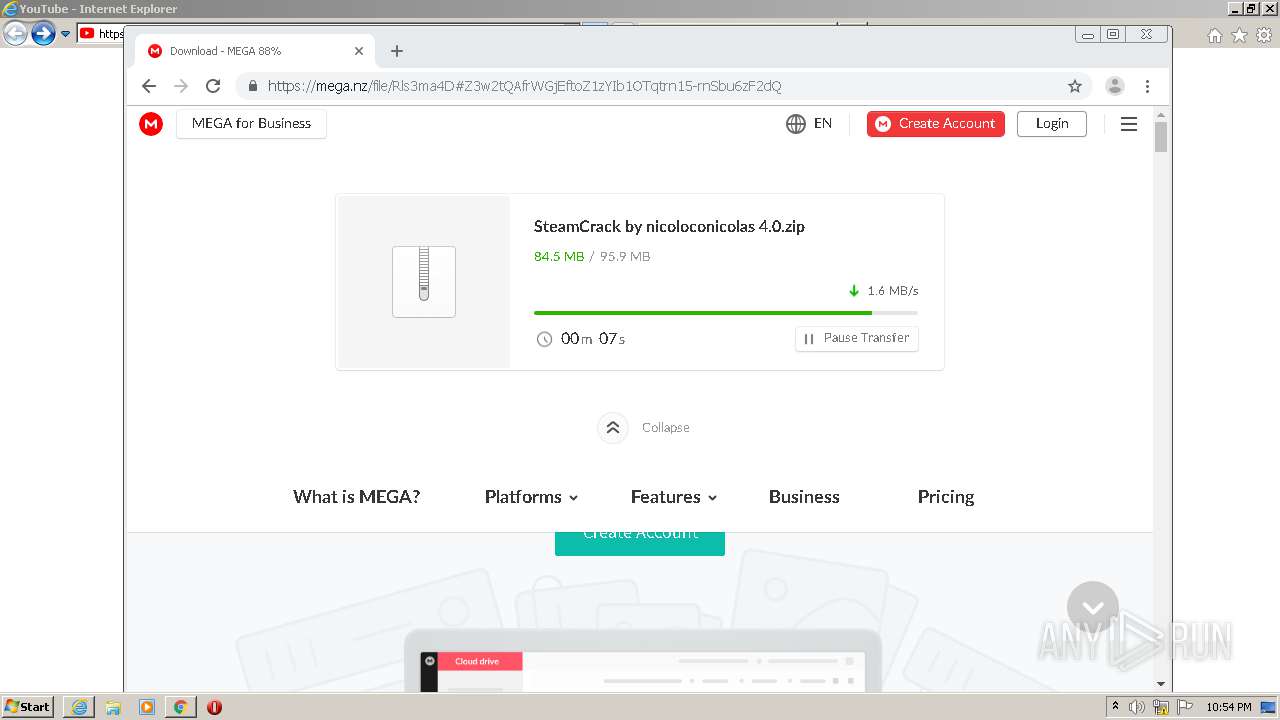
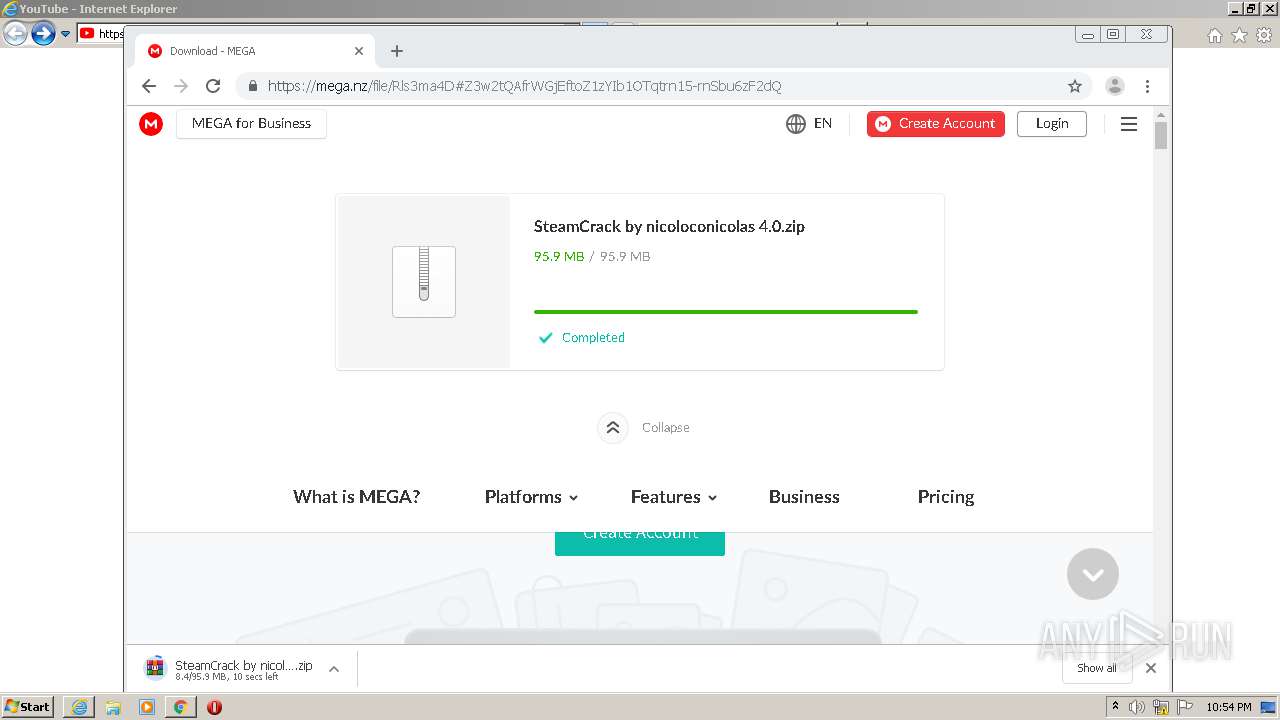
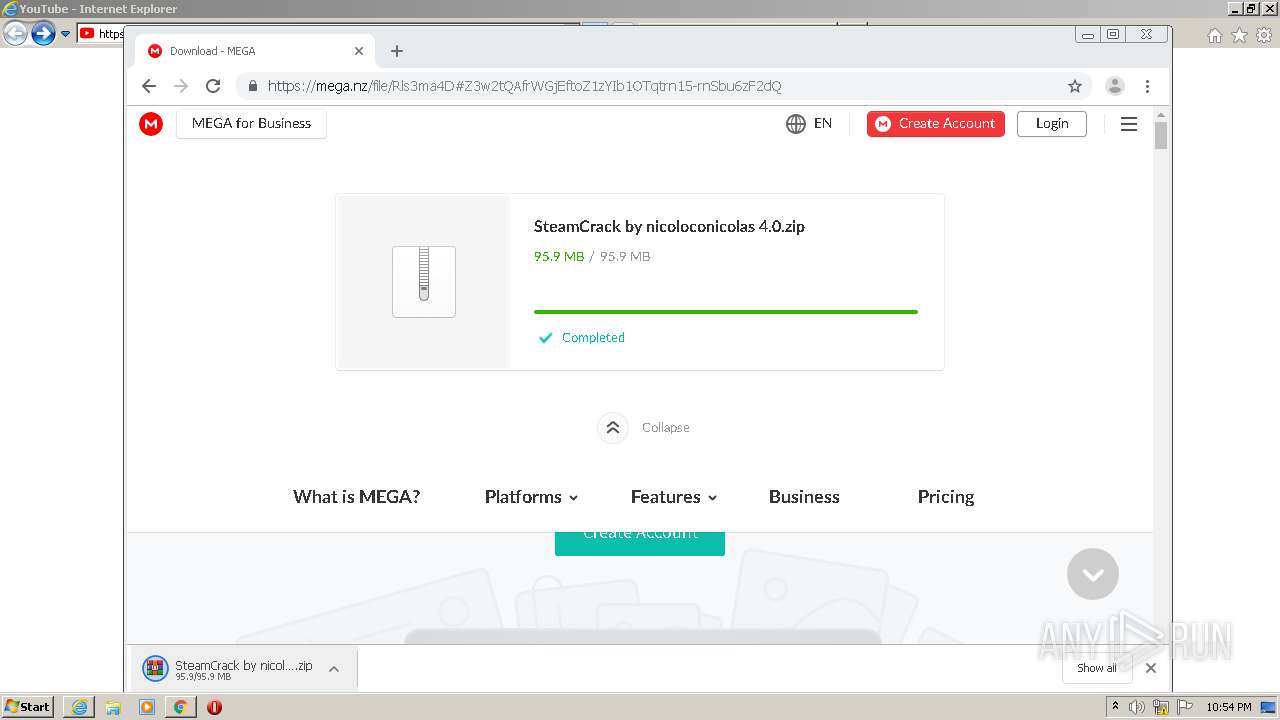
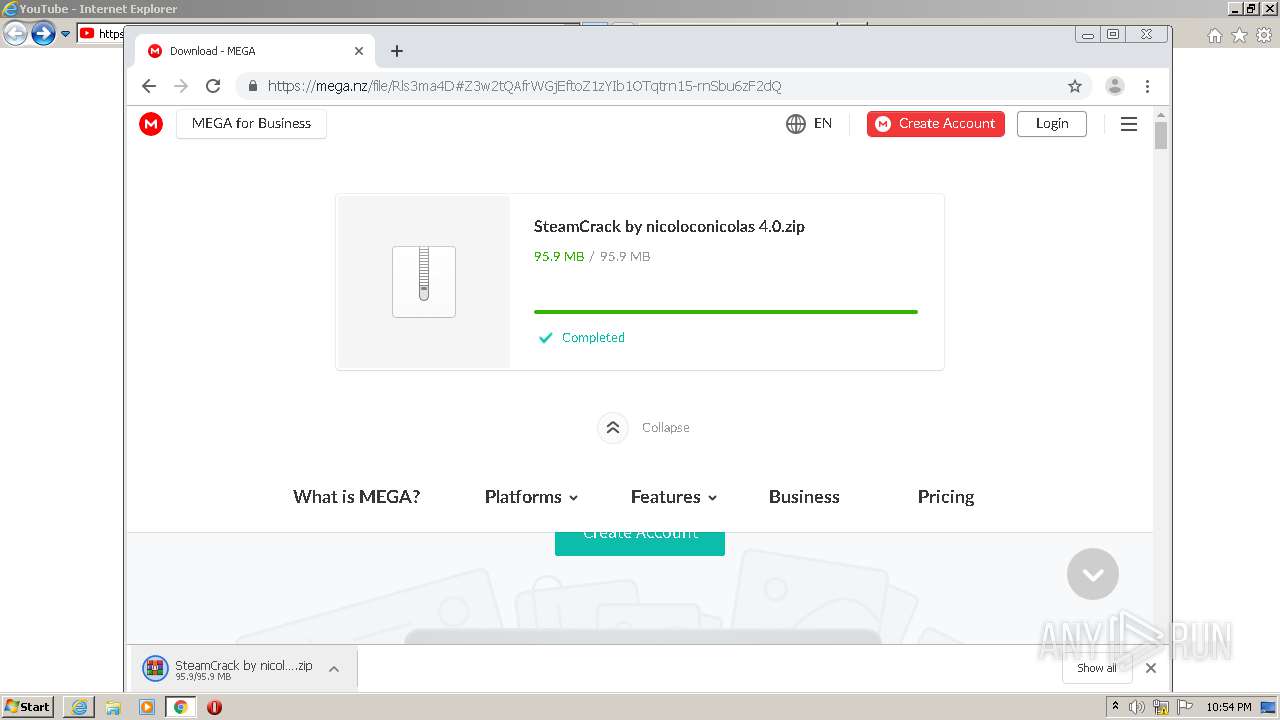
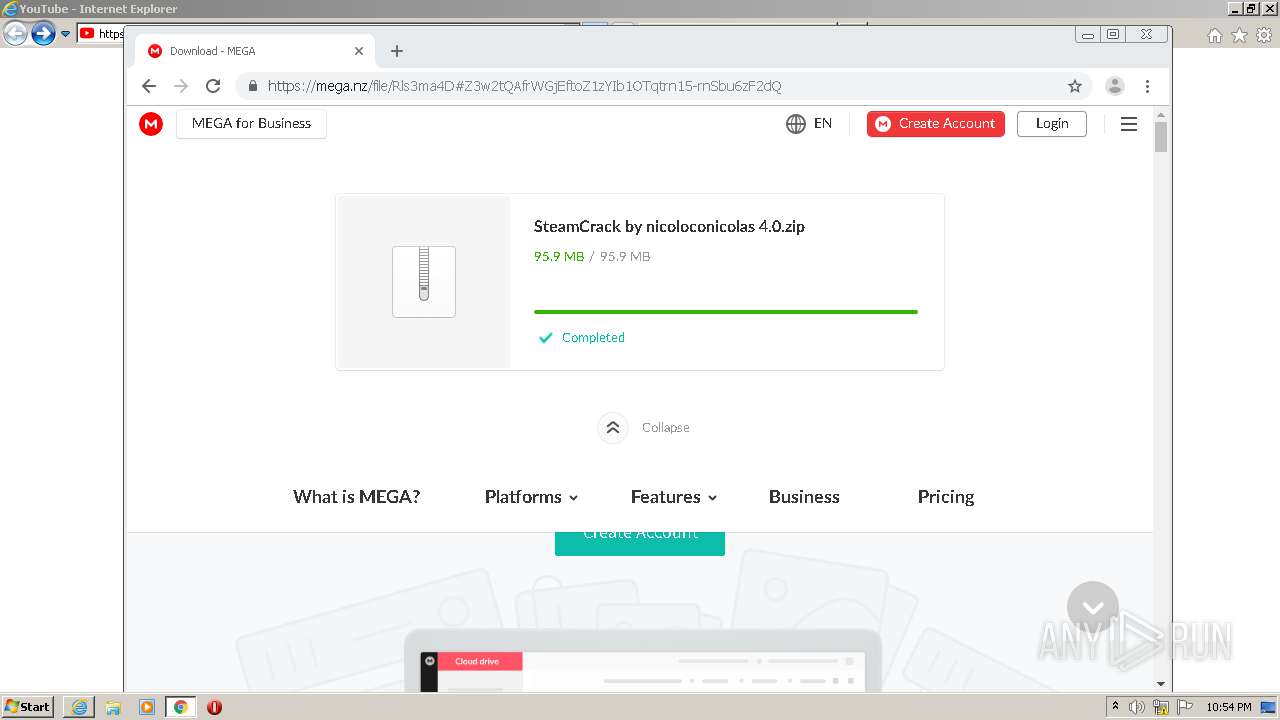
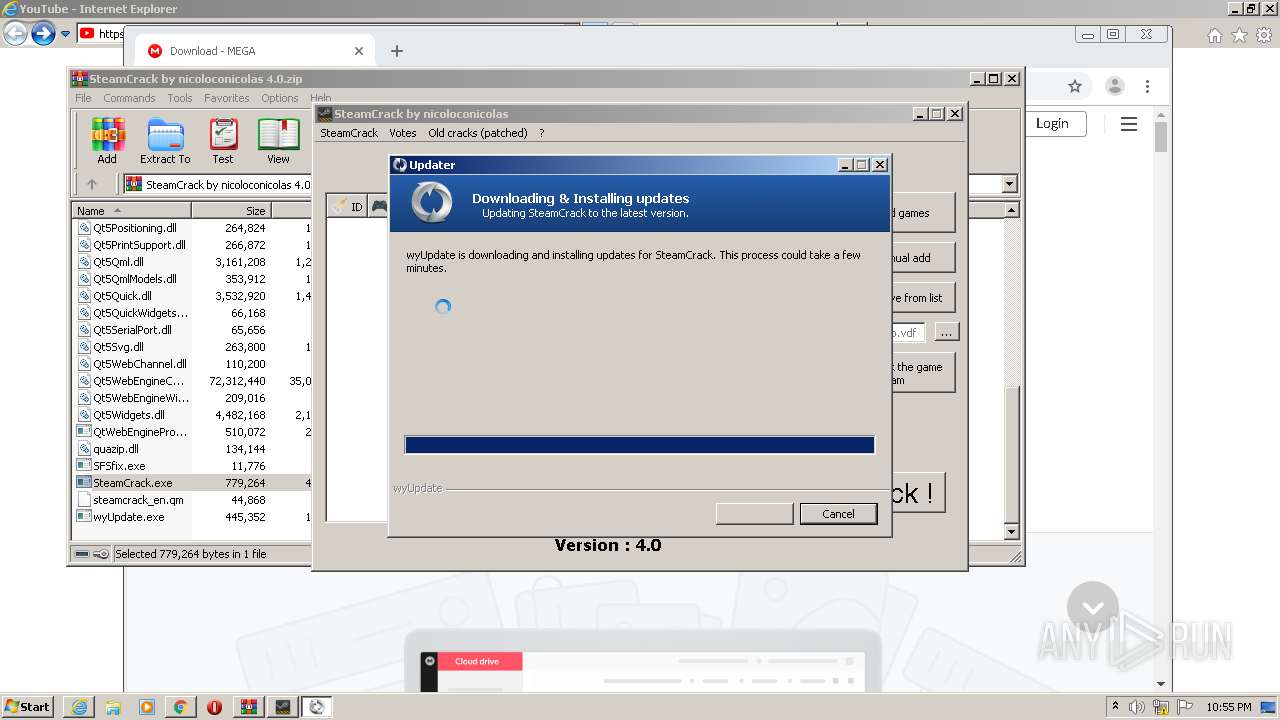
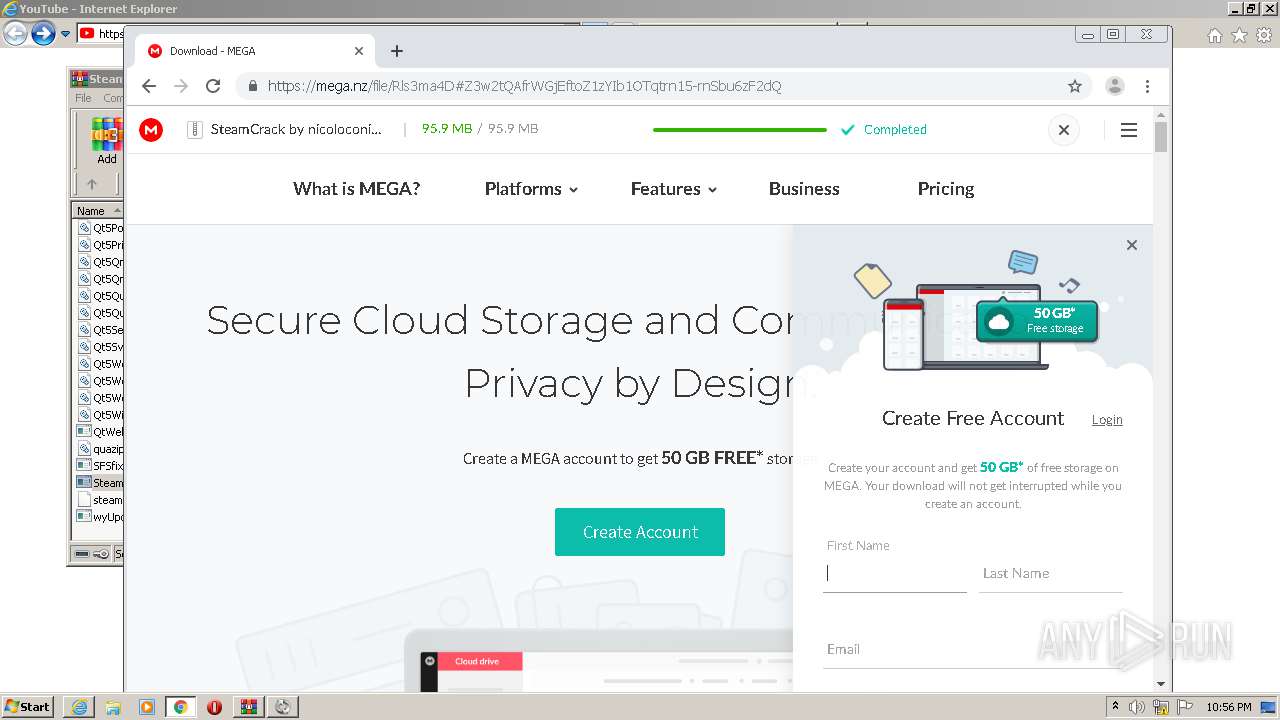
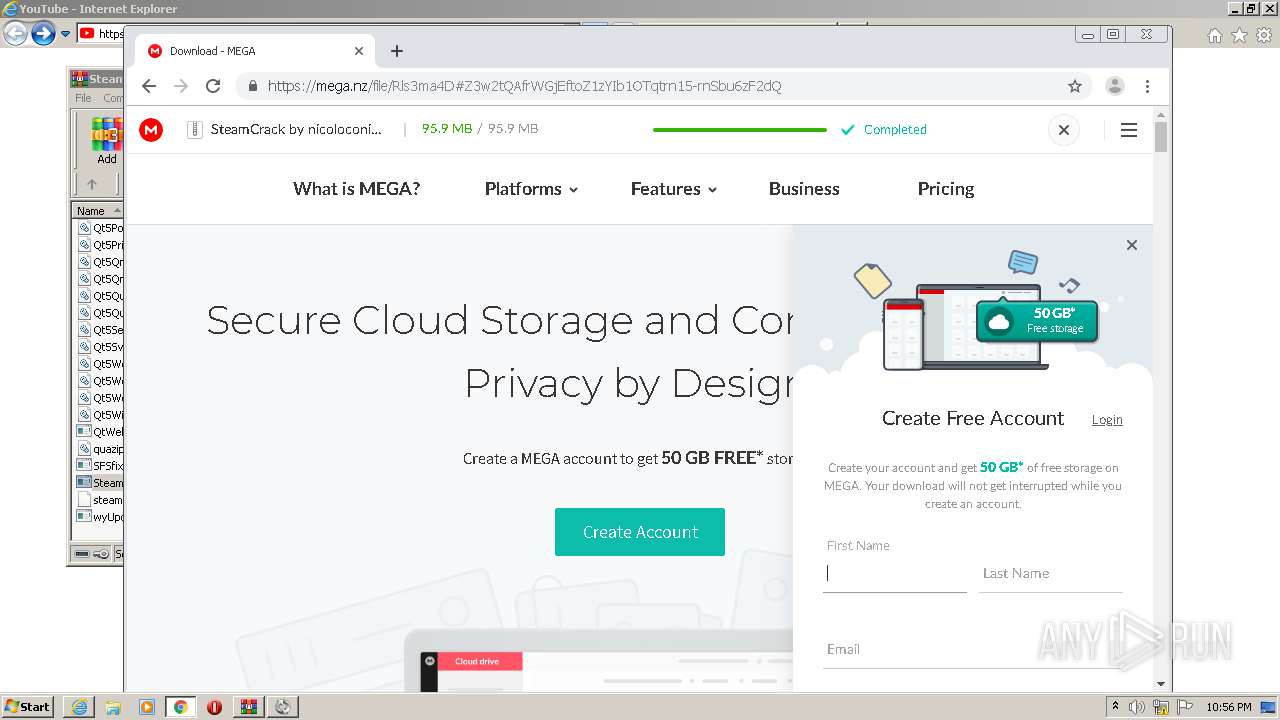
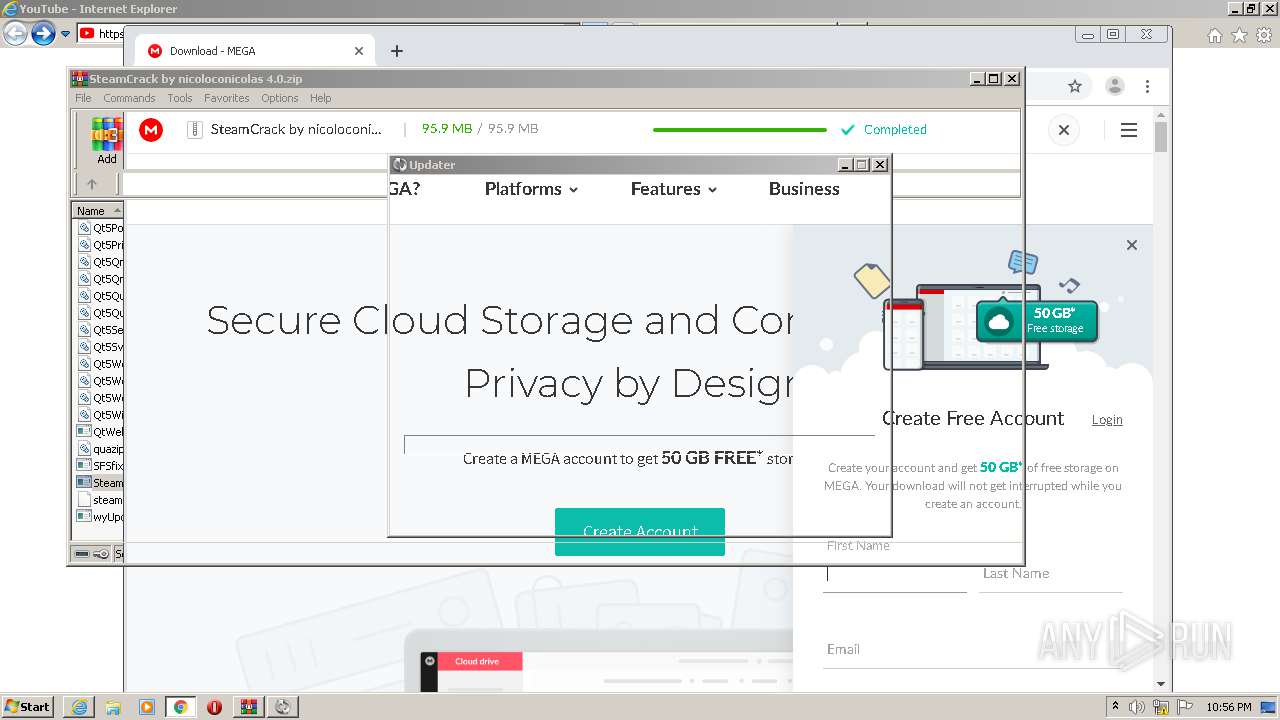
| URL: | https://www.youtube.com/redirect?q=https%3A%2F%2Fmega.nz%2Ffile%2FRls3ma4D%23Z3w2tQAfrWGjEftoZ1zYIb1OTqtrn15-rnSbu6zF2dQ&event=video_description&v=WHBnDFEwZmU&redir_token=QUFFLUhqbHB4U0lVaVV0ZlIyNDRaVmhpZ2VkaHlDRnlnUXxBQ3Jtc0ttMi1nek9jckM4eURmRTZJdFNzVjEwQUxxMjFqeHYtajBqNW9DRUxvVWt4dTVGYnlwenlFaE5GX2FqVjRqLWZfX2VxY29aSlpGaUFuXzJud2NfRW5XZU1CTkdJb2xfc2tDMk9sVjV1WFIyS0VGS3lFOA%3D%3D |
| Full analysis: | https://app.any.run/tasks/a018ff9e-75e5-4578-9a6f-afbc5090dcc8 |
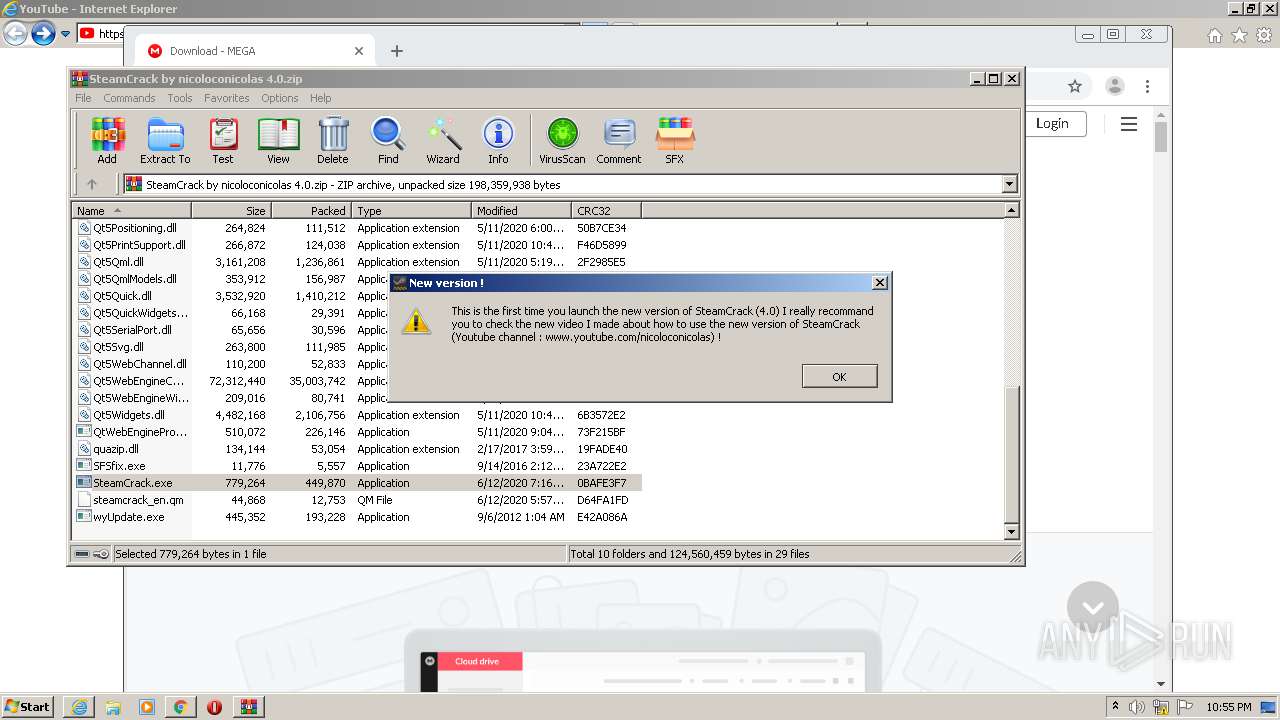
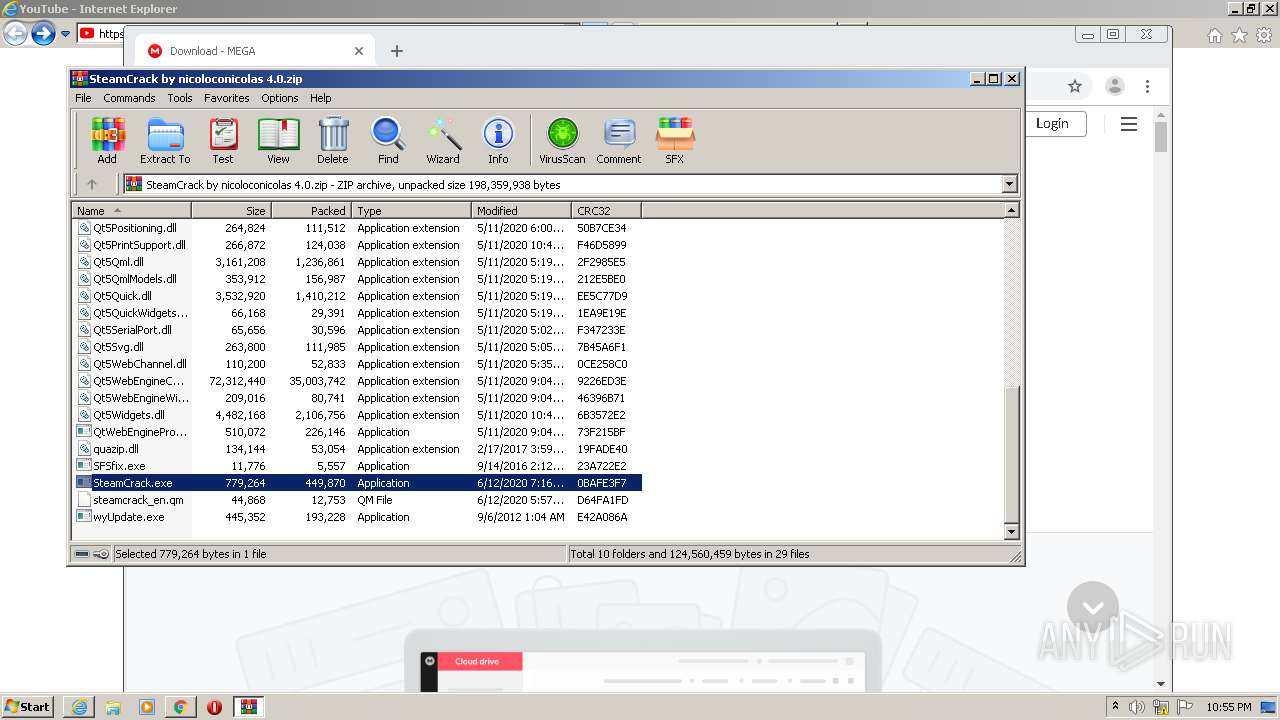
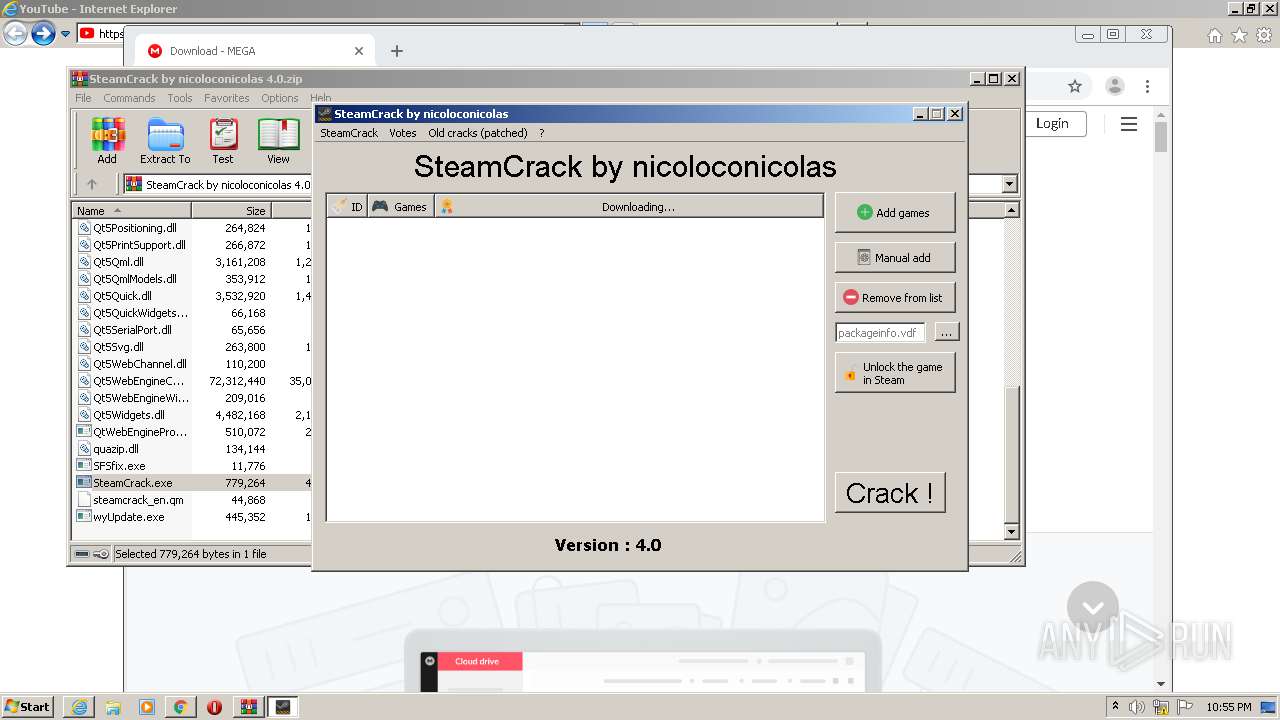
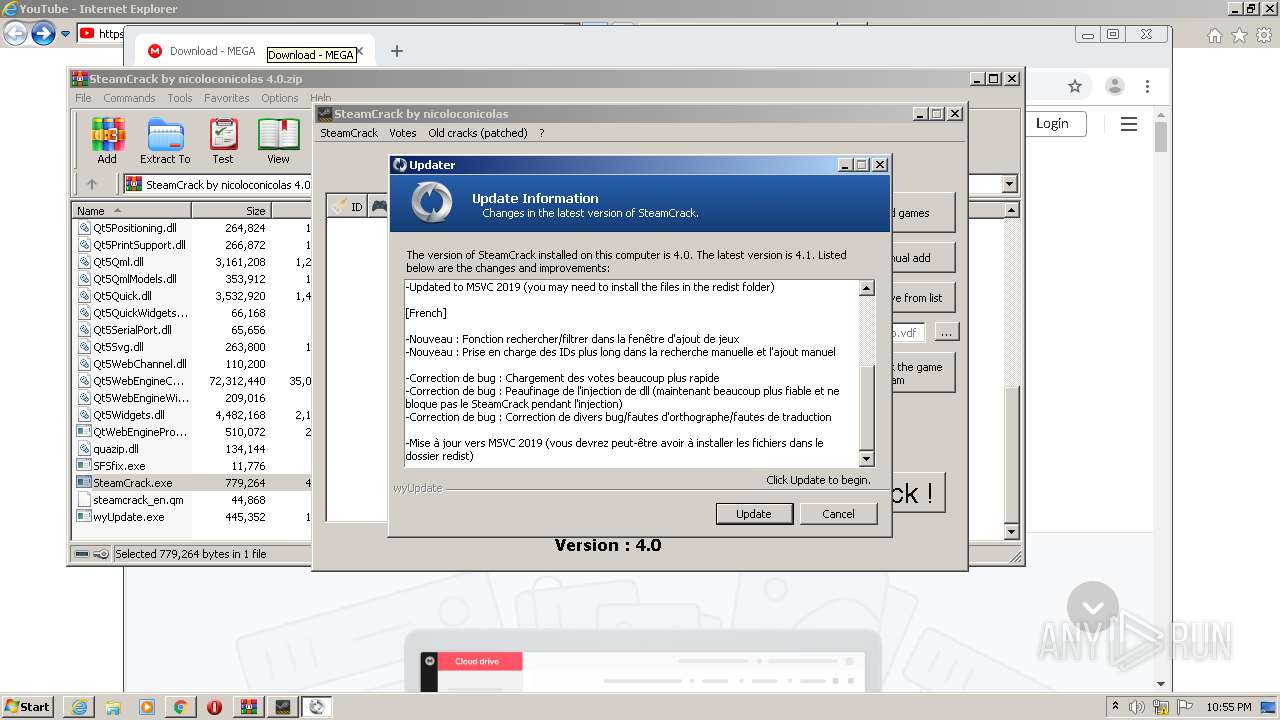
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2021, 22:52:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 92B118EC19C8BA3A464CB8AFCFFBE9AF |
| SHA1: | 88B29D175A02FE3D8926FDF0EF0AFD34FAC131CB |
| SHA256: | 5353E853D11FFD518470A1F1EF525F1AE021F7C57E43C217F6F12DEE1E045279 |
| SSDEEP: | 6:2OLUxGKW5zgTiBv/Q2c0DCRXhDGZM9E9aKiRnQrrlx1iYj9a+X4CmoZ2UVOvH:2jG14iBv405r9v7xDiYjMo4CWMOv |
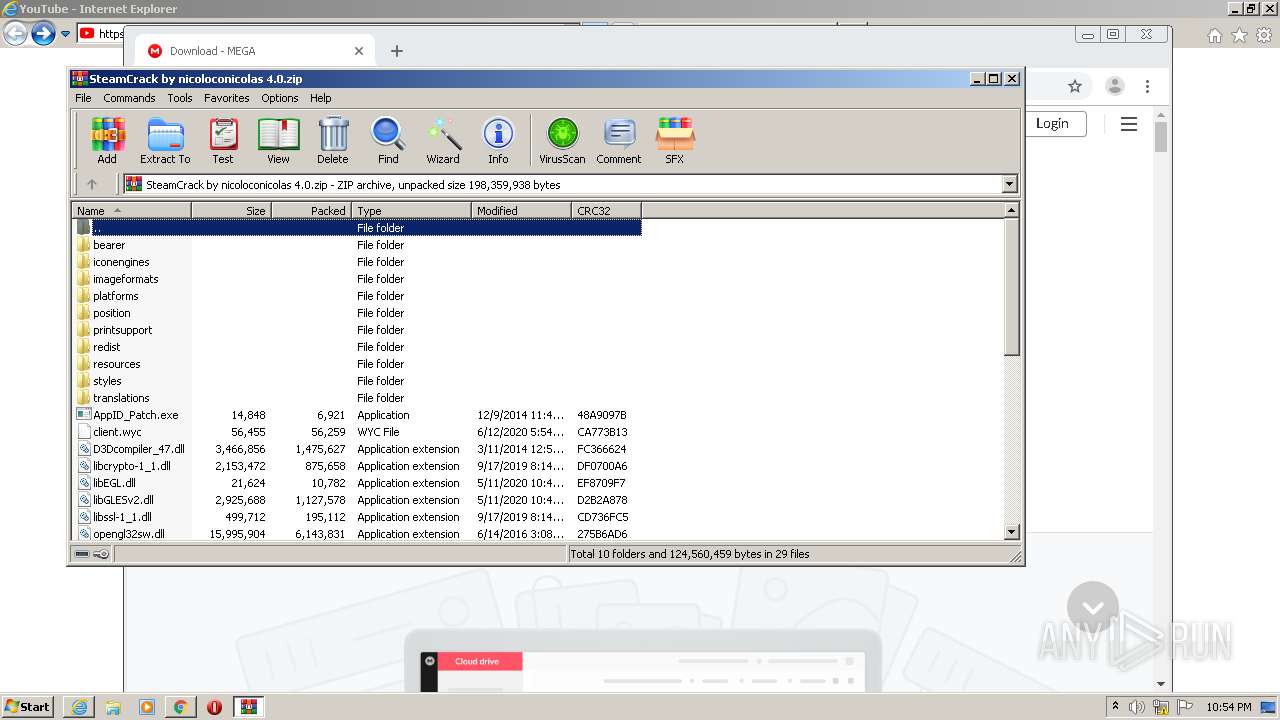
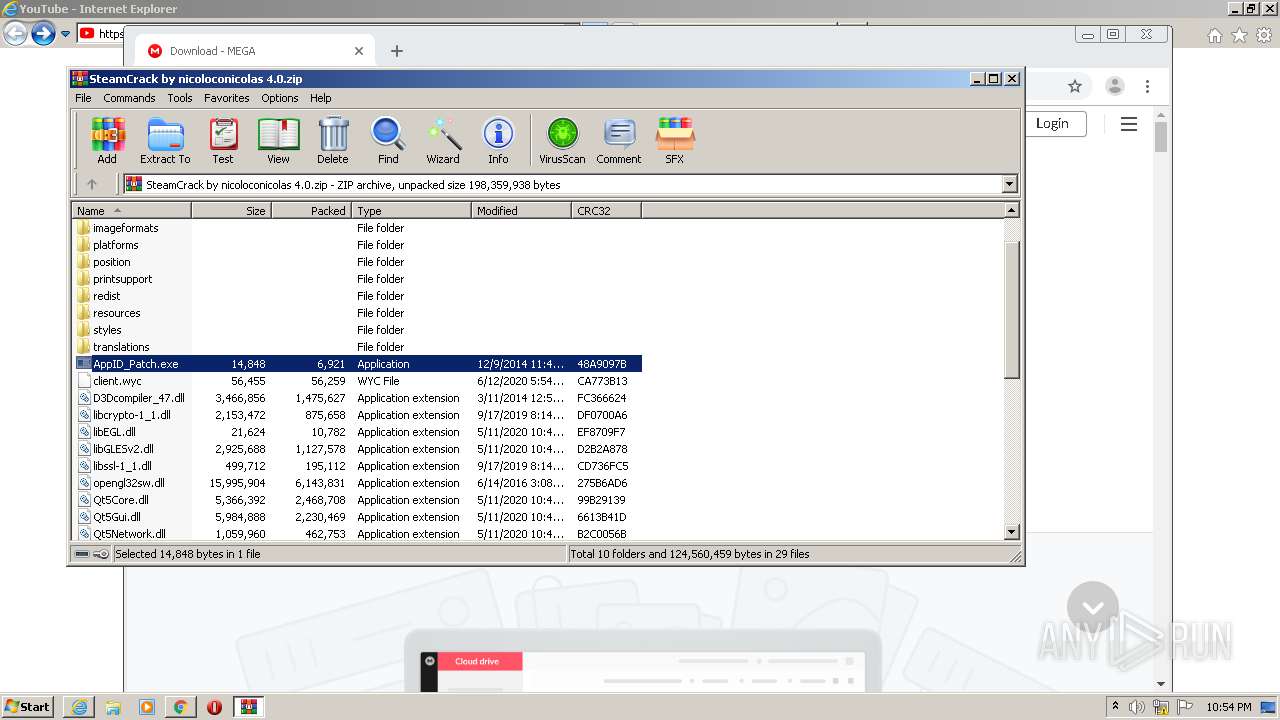
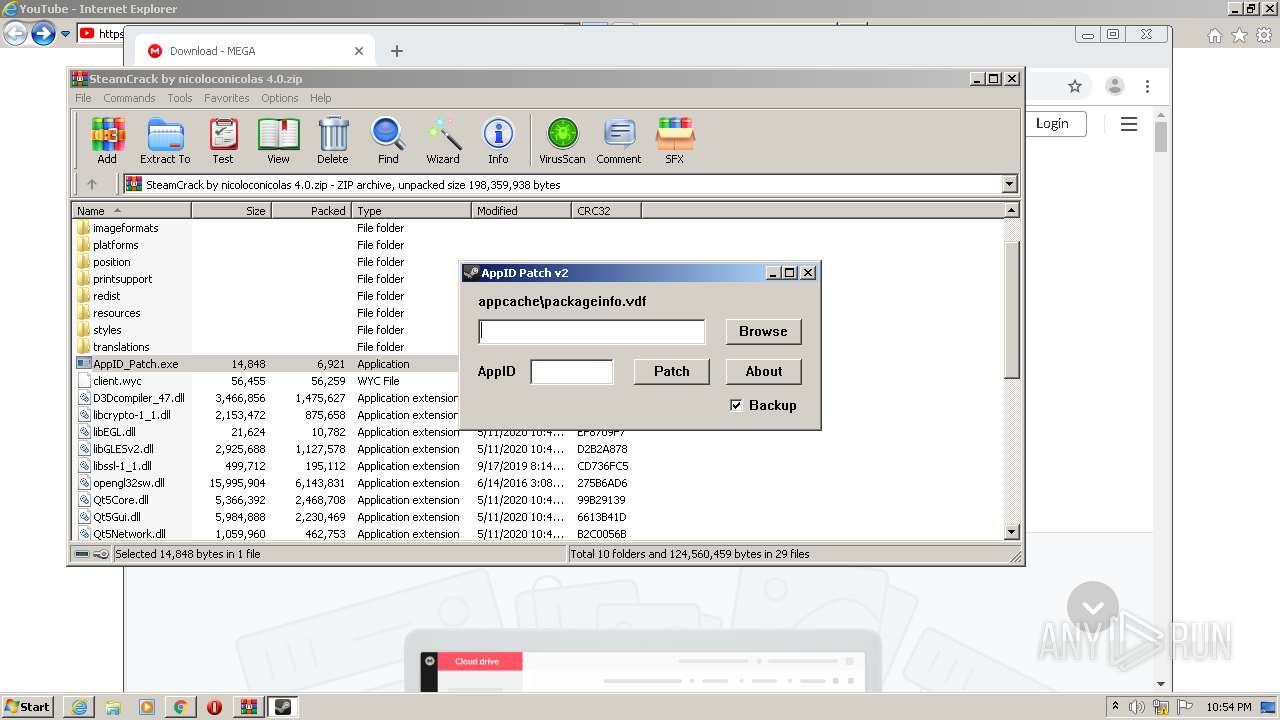
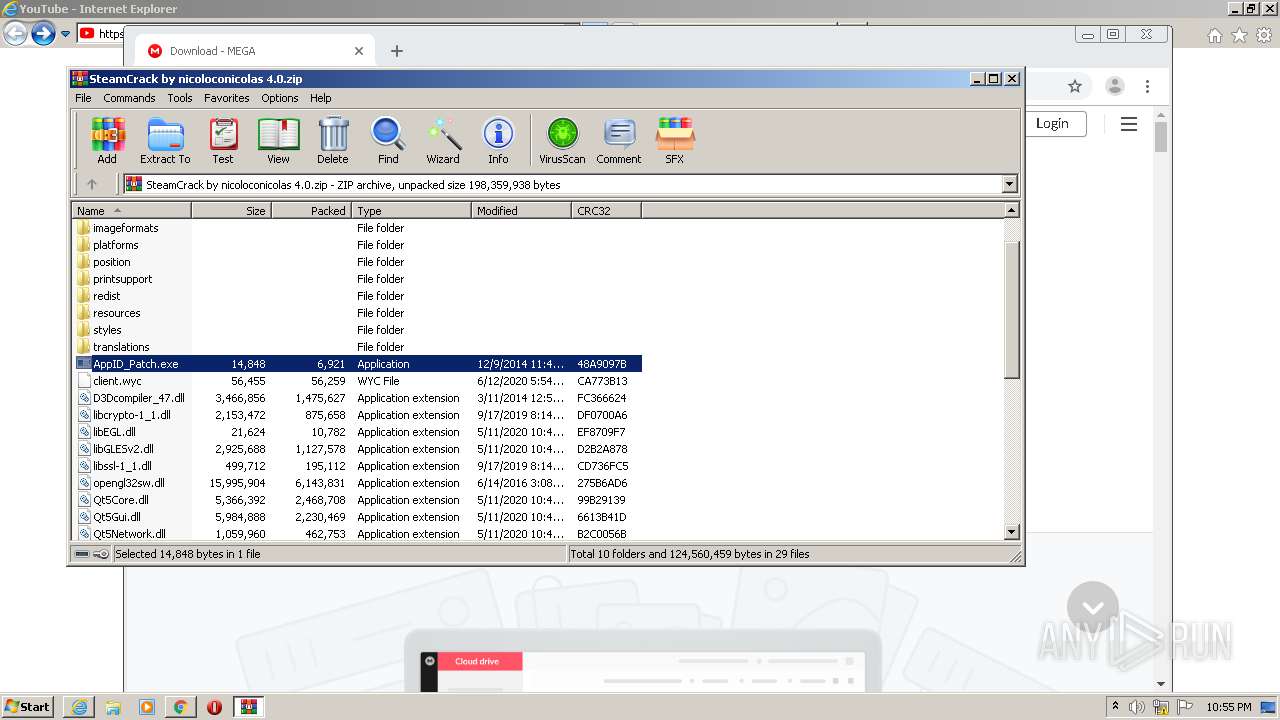
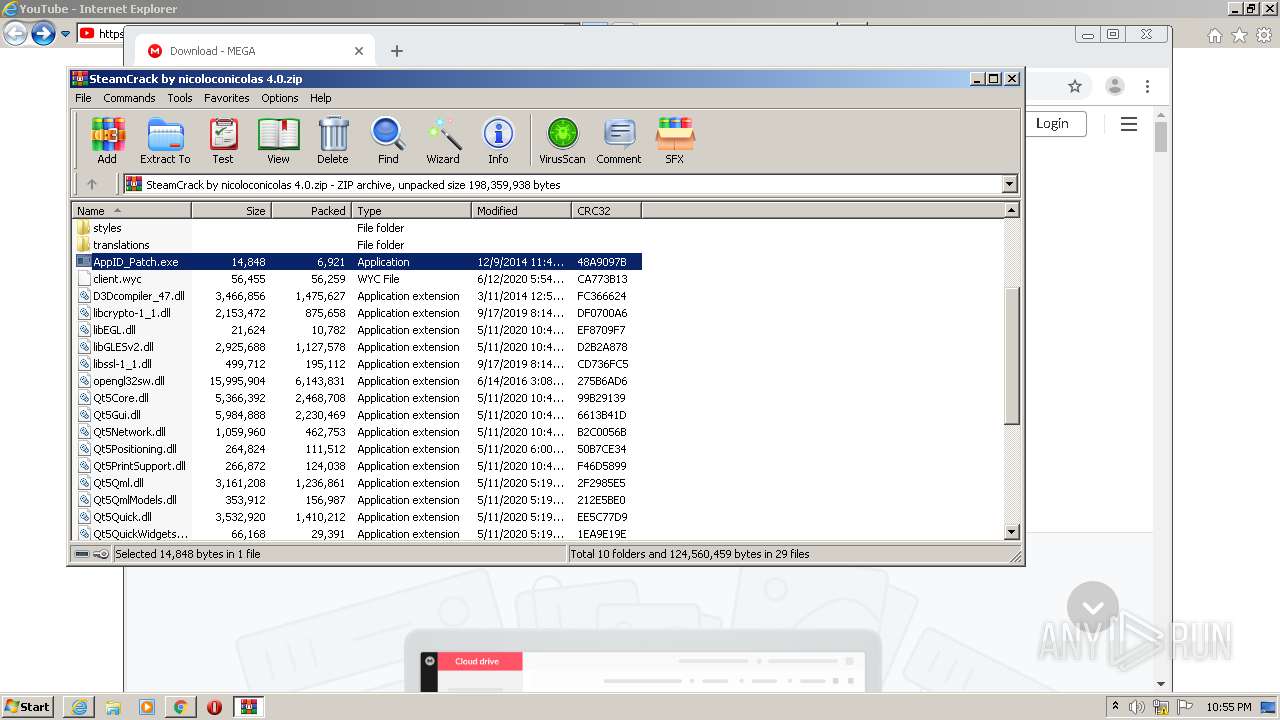
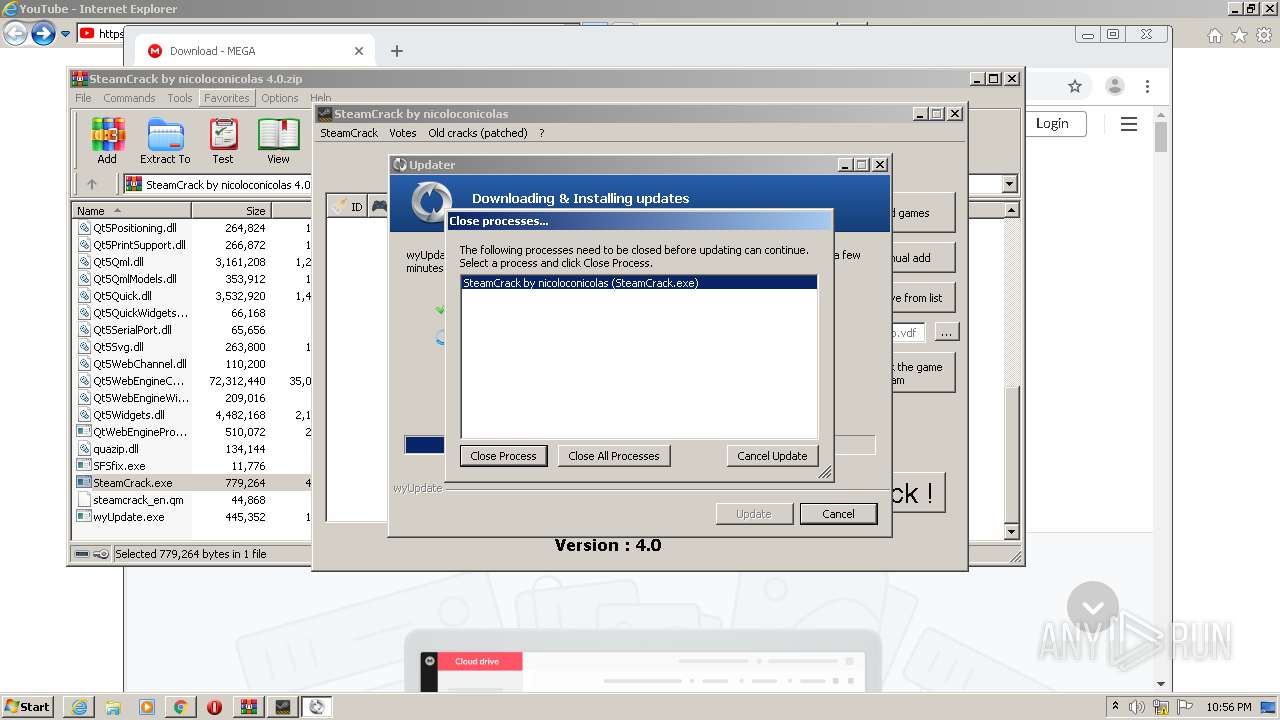
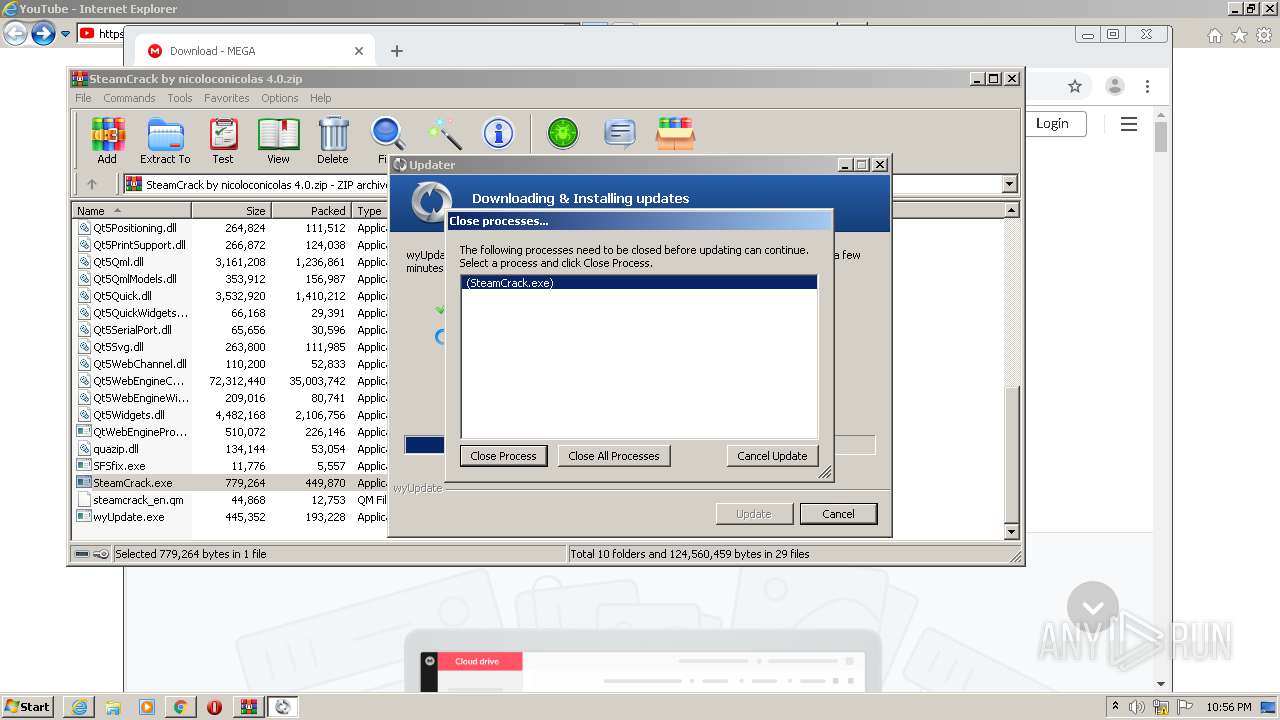
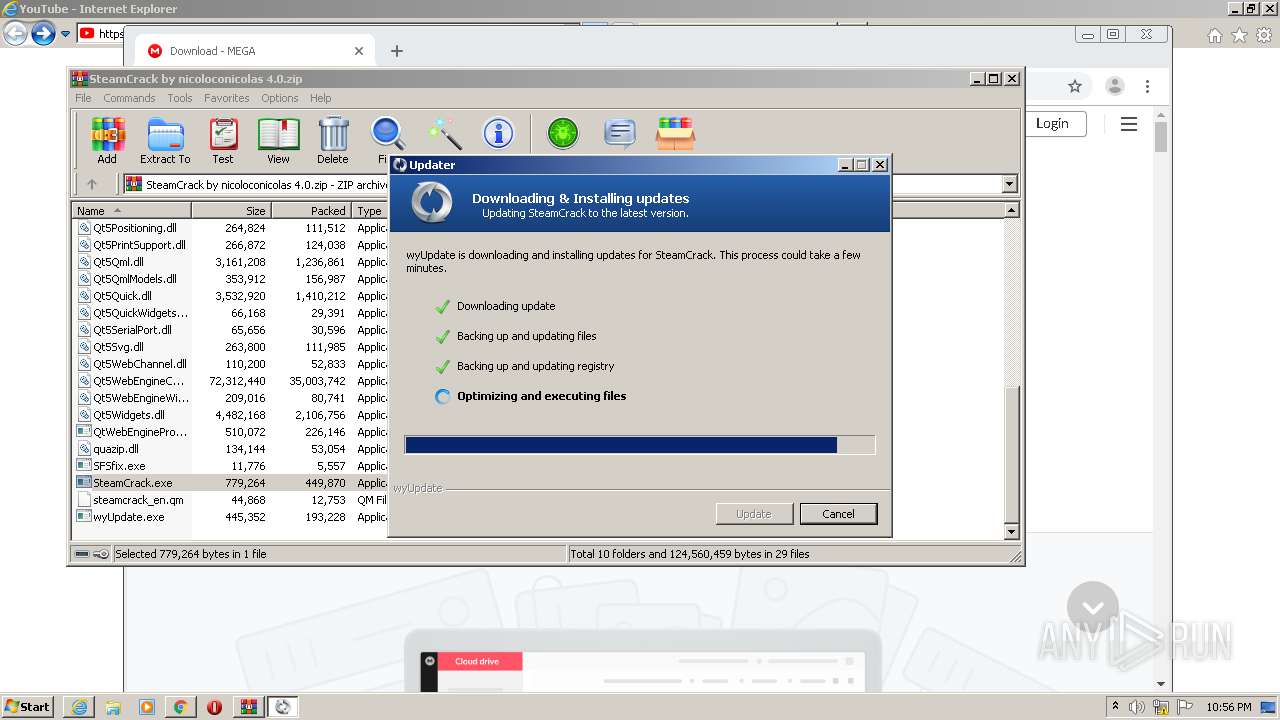
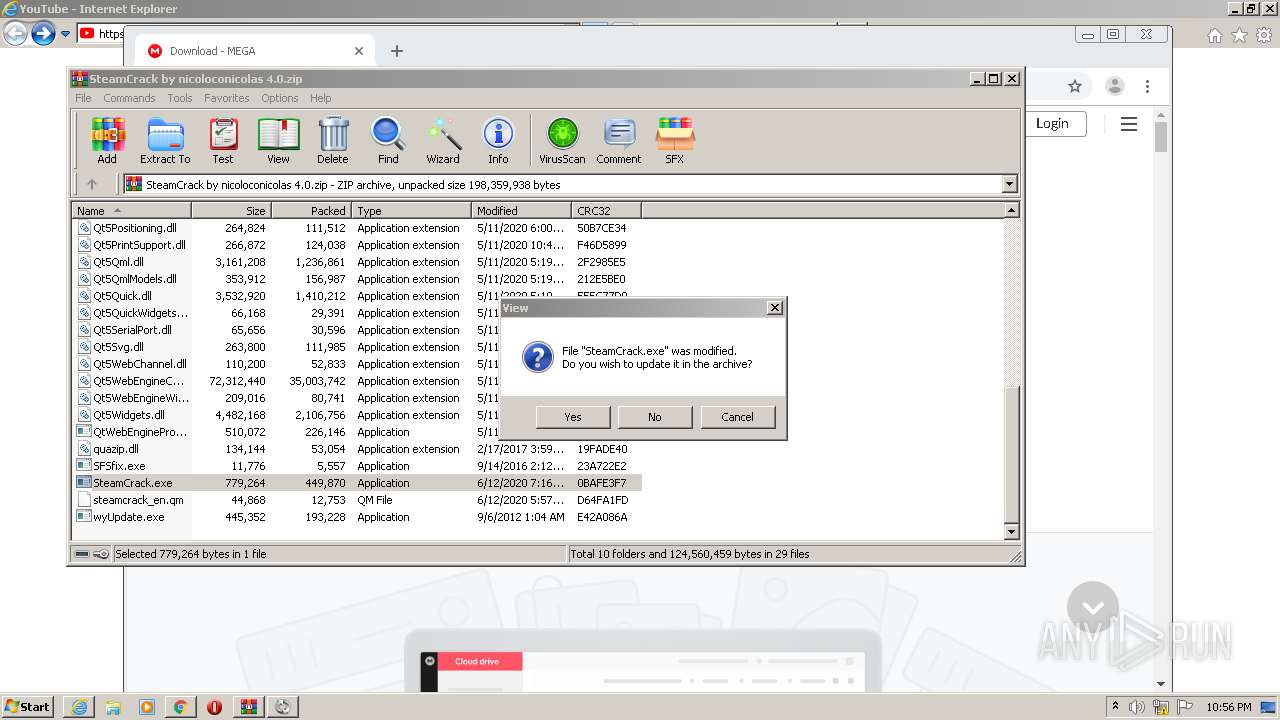
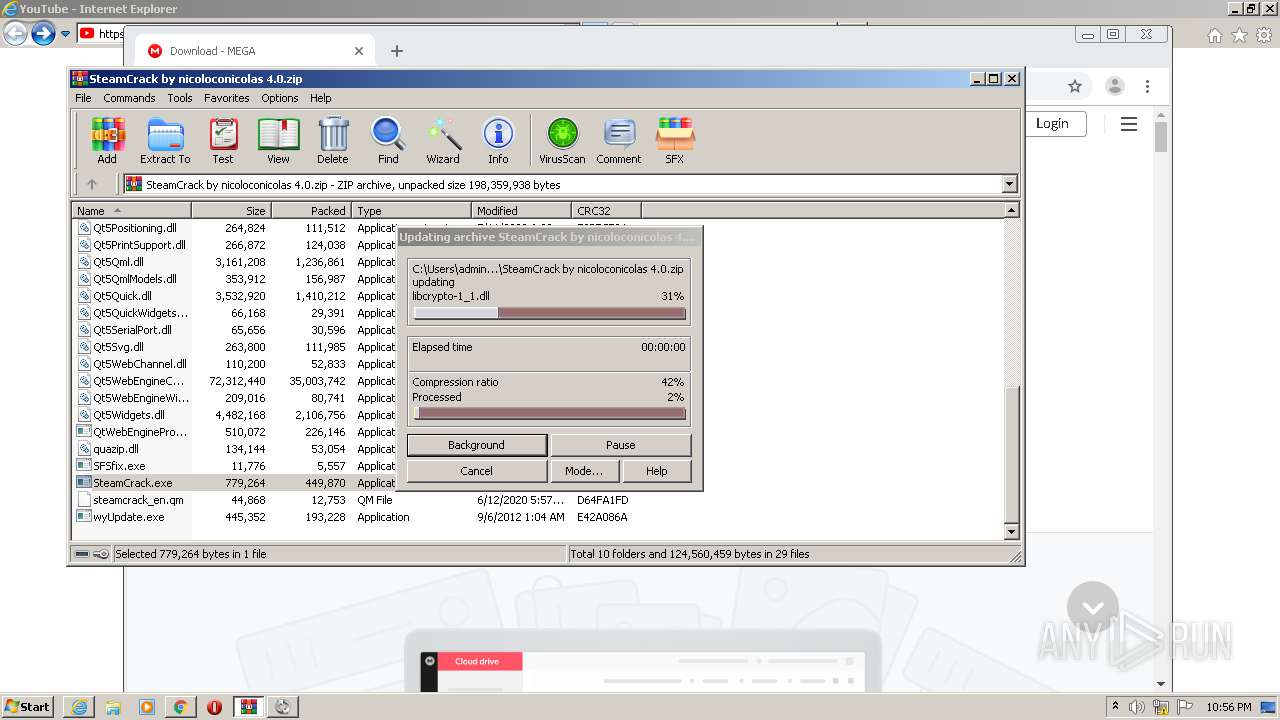
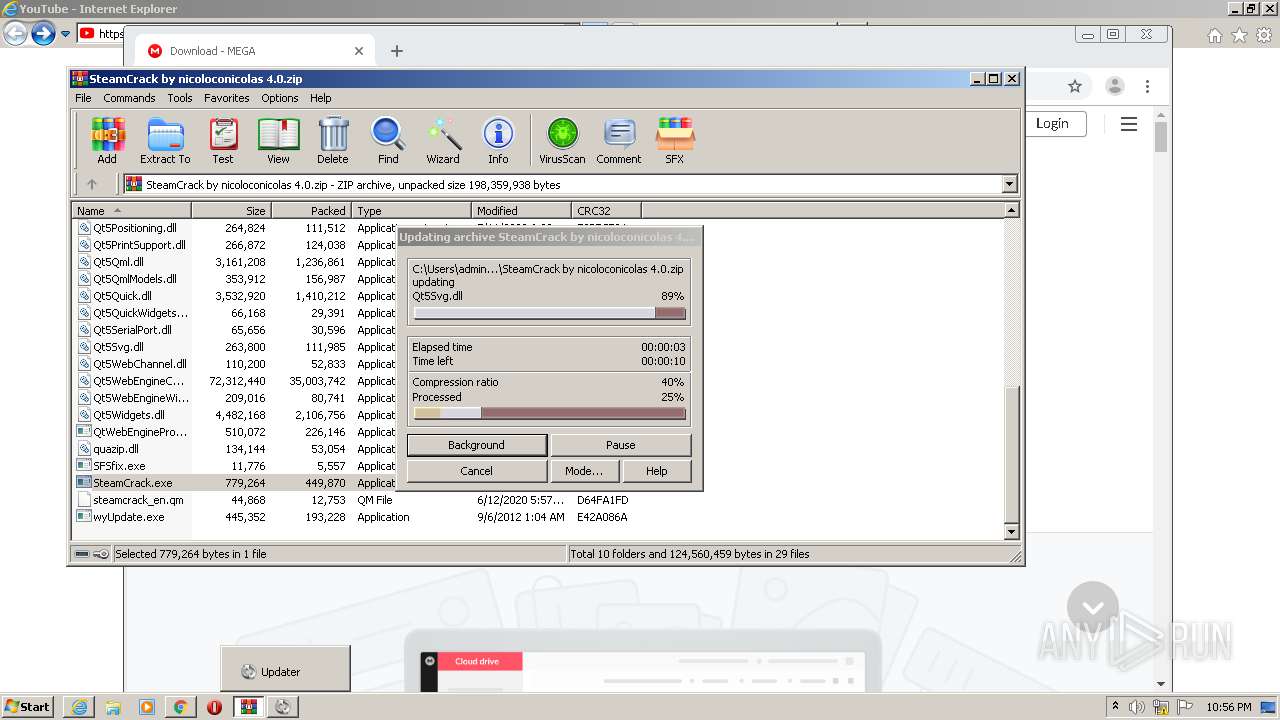
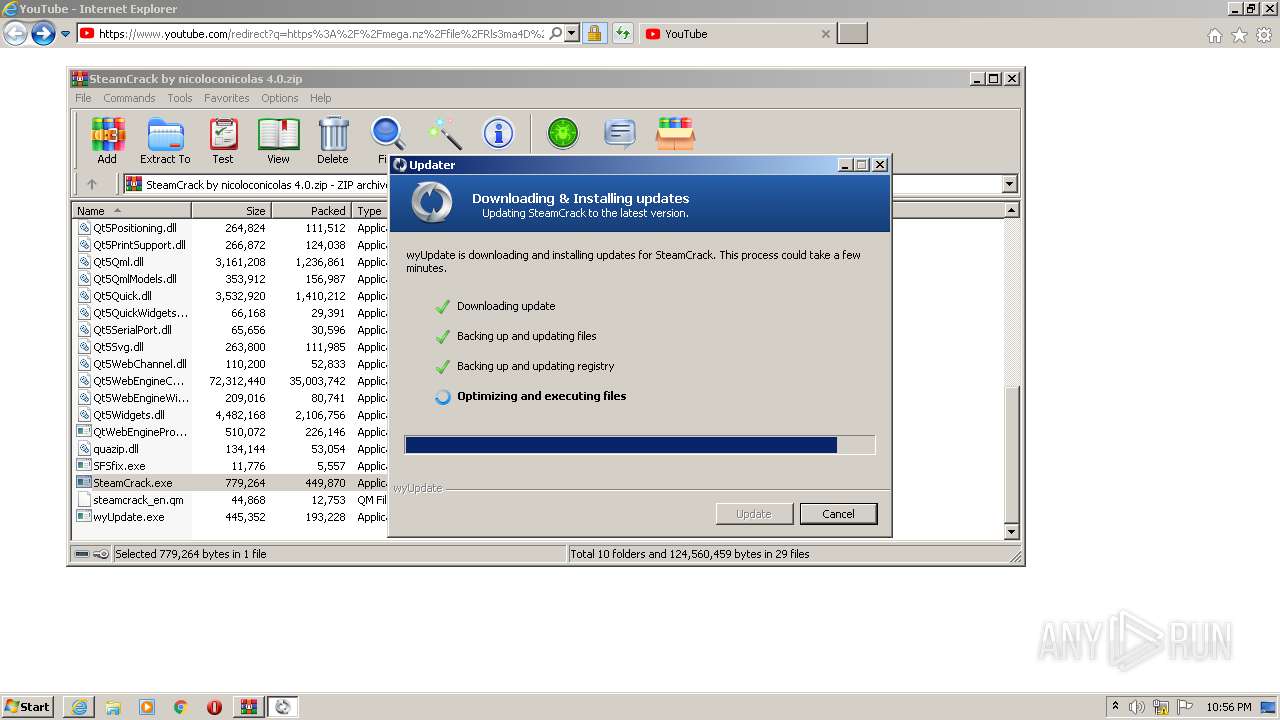
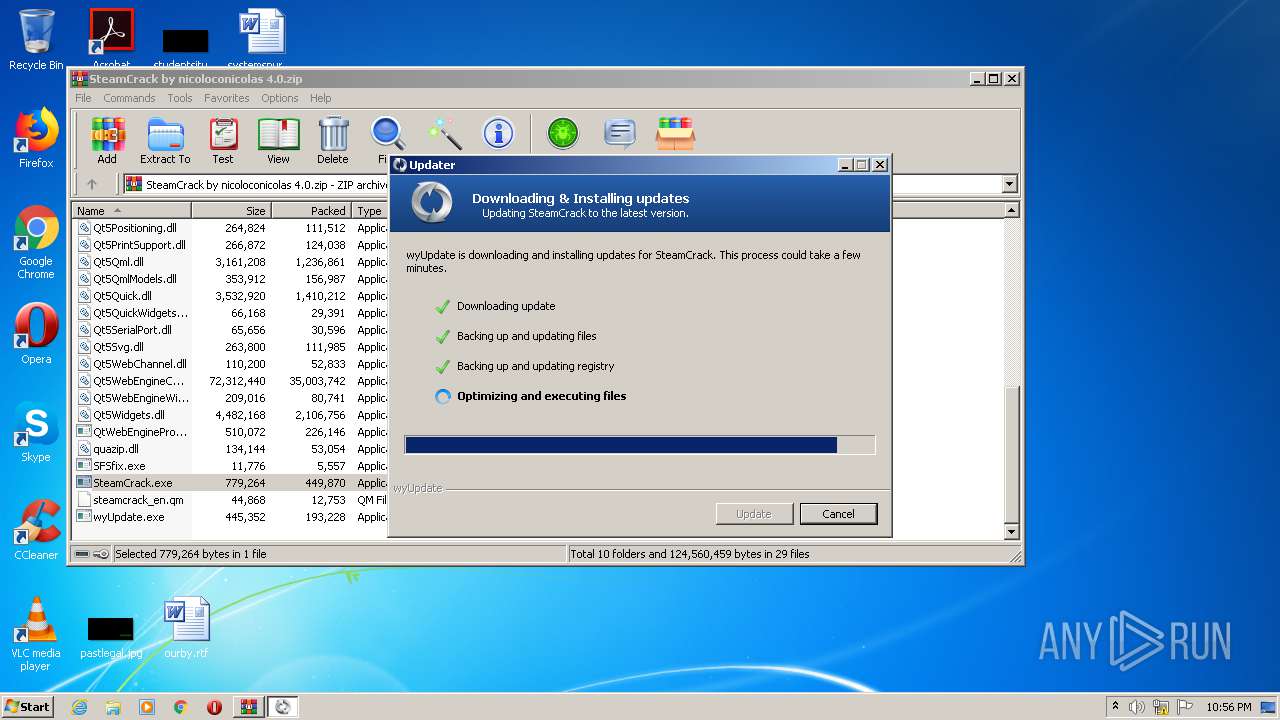
MALICIOUS
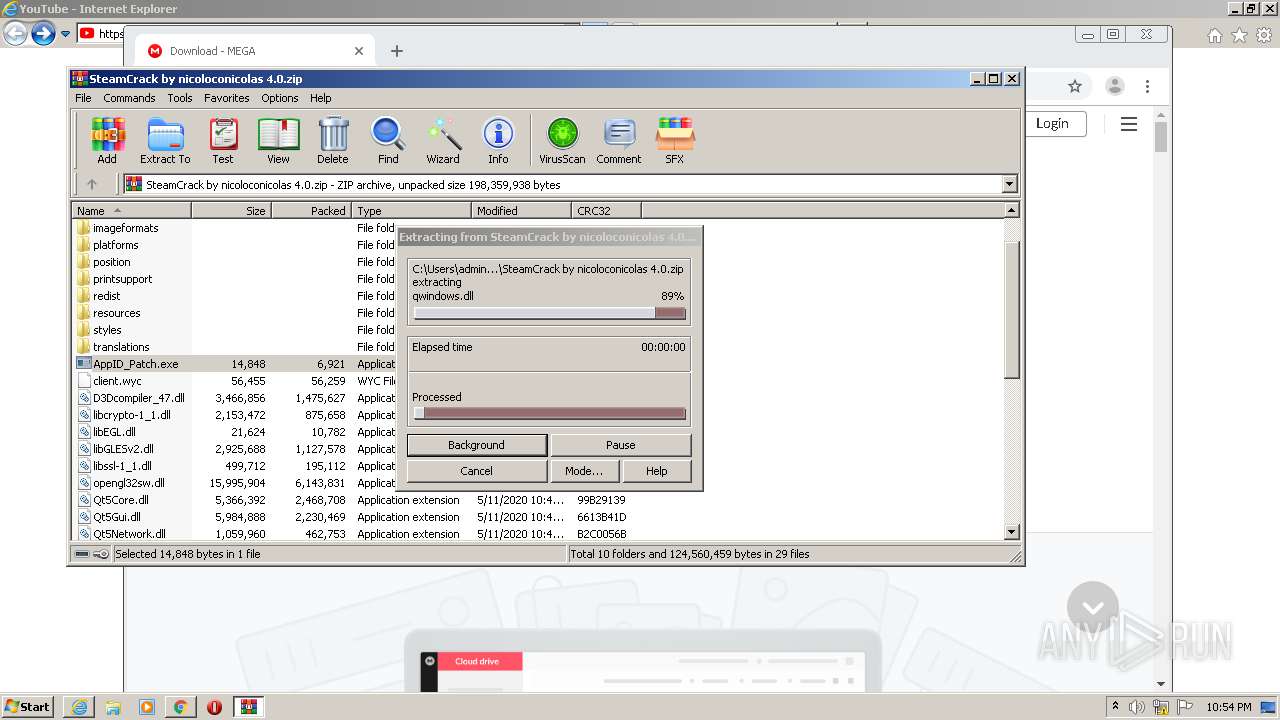
Application was dropped or rewritten from another process
- AppID_Patch.exe (PID: 3920)
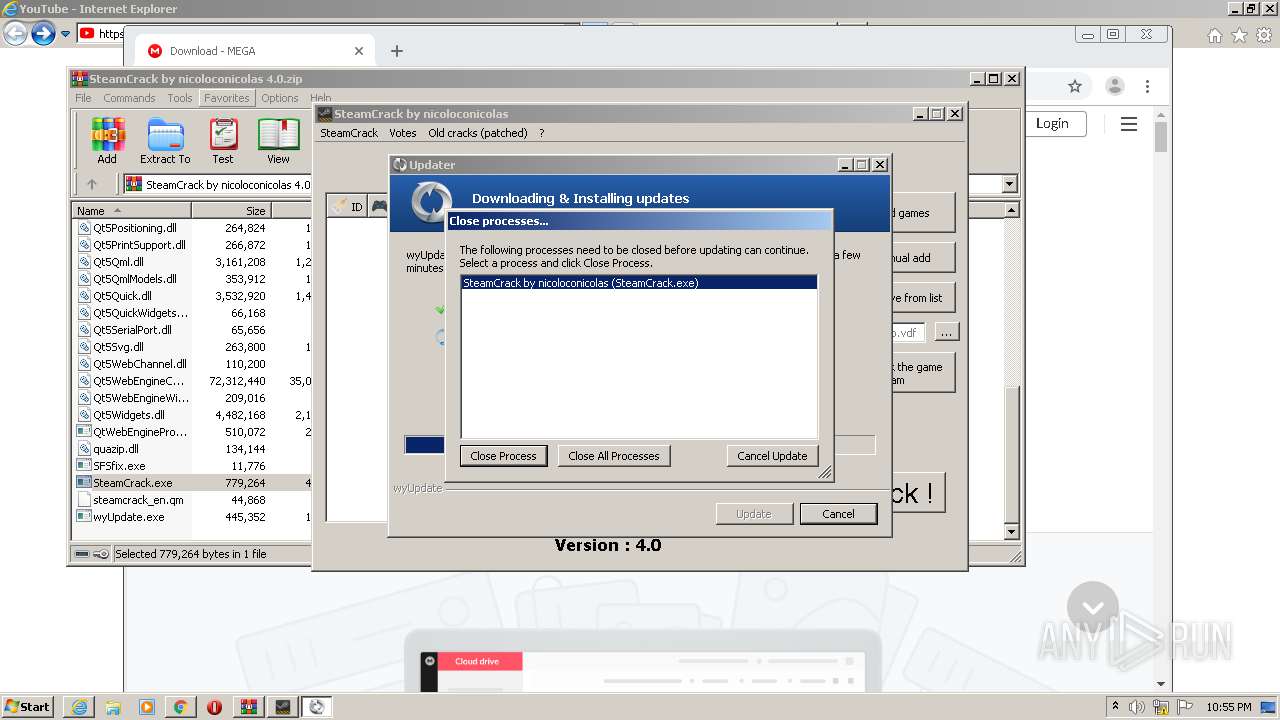
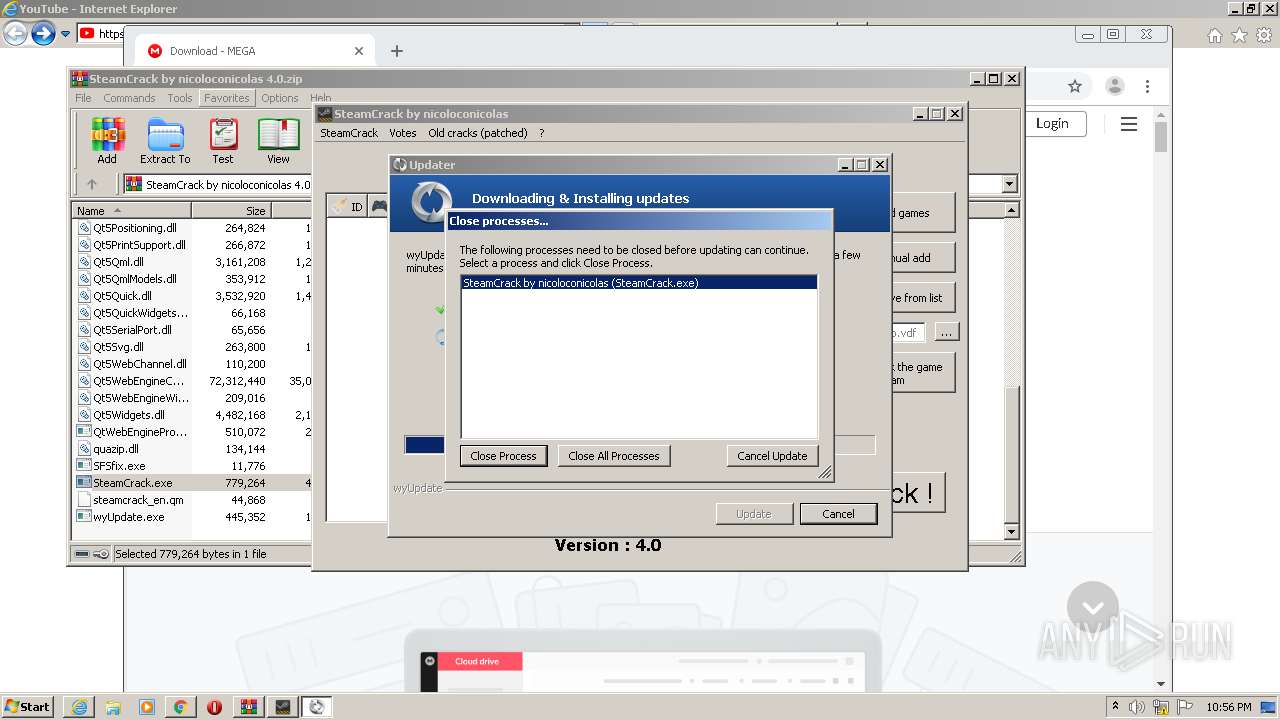
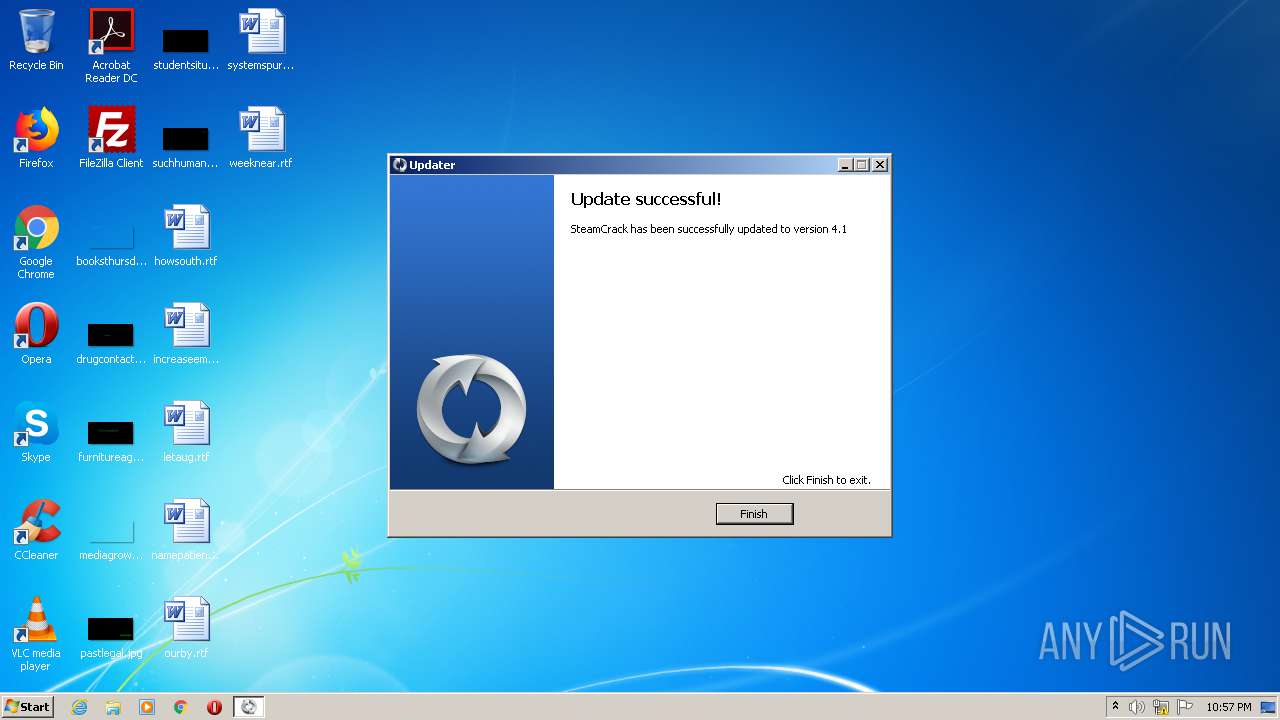
- SteamCrack.exe (PID: 2896)
- SteamCrack.exe (PID: 3732)
- vc_redist.x86.exe (PID: 2896)
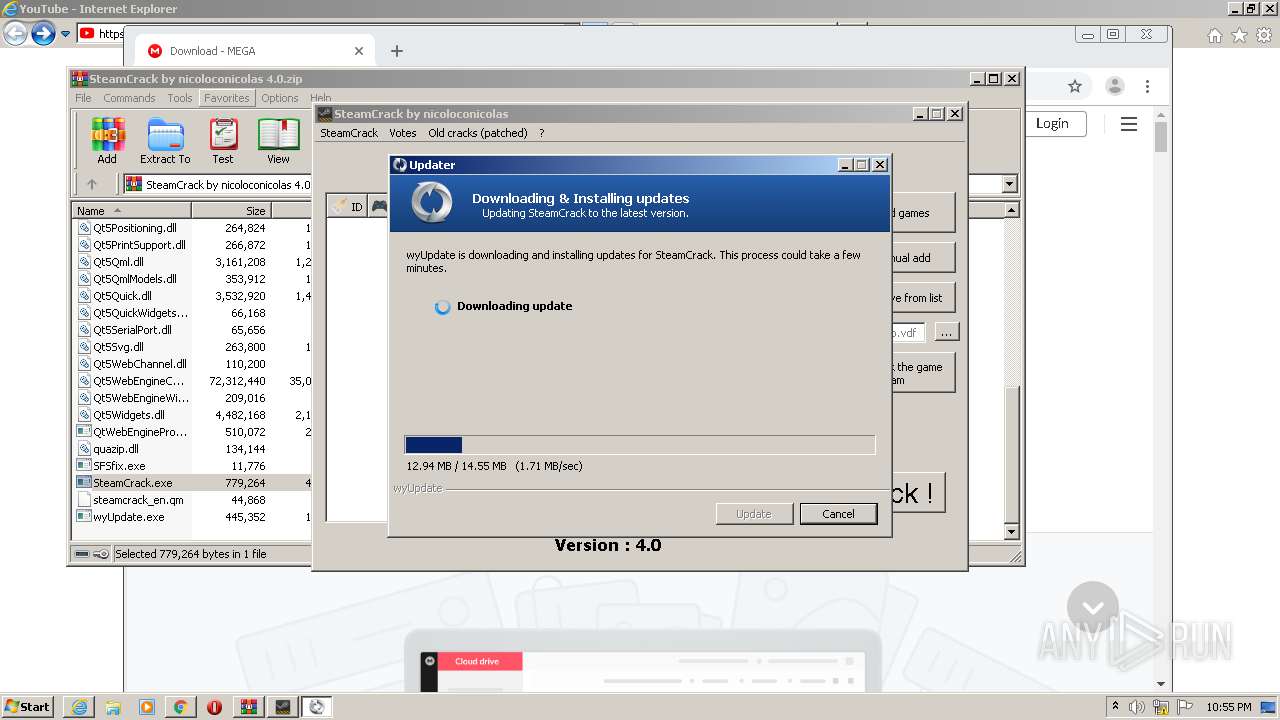
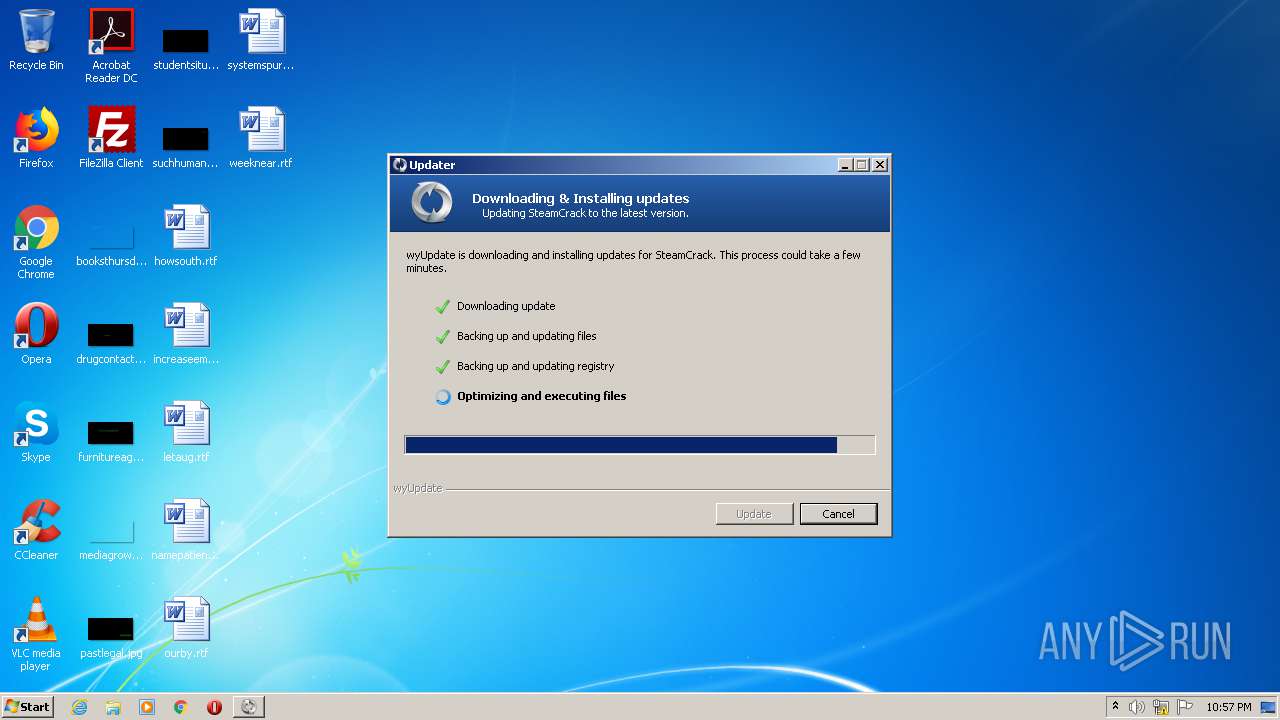
- wyUpdate.exe (PID: 2900)
- AppID_Patch.exe (PID: 2240)
- VC_redist.x86.exe (PID: 1808)
- vc_redist.x86.exe (PID: 3780)
- VC_redist.x86.exe (PID: 2812)
- VC_redist.x86.exe (PID: 3268)
- VC_redist.x86.exe (PID: 1624)
Loads dropped or rewritten executable
- SteamCrack.exe (PID: 3732)
- vc_redist.x86.exe (PID: 3780)
- VC_redist.x86.exe (PID: 1624)
Drops executable file immediately after starts
- vc_redist.x86.exe (PID: 2896)
- vc_redist.x86.exe (PID: 3780)
- VC_redist.x86.exe (PID: 1624)
- VC_redist.x86.exe (PID: 3268)
Changes settings of System certificates
- wyUpdate.exe (PID: 2900)
- msiexec.exe (PID: 584)
Changes the autorun value in the registry
- VC_redist.x86.exe (PID: 1808)
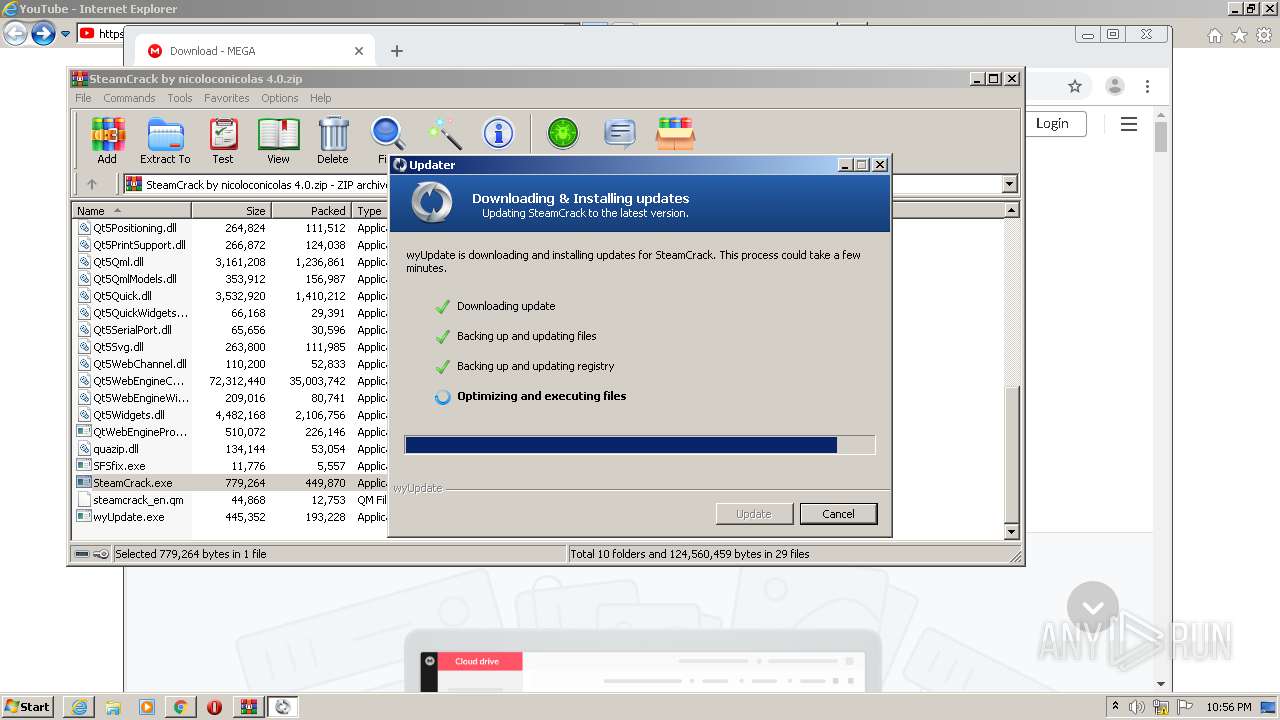
SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 3528)
- wyUpdate.exe (PID: 2900)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2188)
- wyUpdate.exe (PID: 2900)
- vc_redist.x86.exe (PID: 2896)
- vc_redist.x86.exe (PID: 3780)
- VC_redist.x86.exe (PID: 1808)
- msiexec.exe (PID: 584)
- VC_redist.x86.exe (PID: 3268)
- VC_redist.x86.exe (PID: 1624)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3040)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2188)
- wyUpdate.exe (PID: 2900)
- vc_redist.x86.exe (PID: 2896)
- vc_redist.x86.exe (PID: 3780)
- VC_redist.x86.exe (PID: 1808)
- msiexec.exe (PID: 584)
- VC_redist.x86.exe (PID: 1624)
- VC_redist.x86.exe (PID: 3268)
Adds / modifies Windows certificates
- wyUpdate.exe (PID: 2900)
- msiexec.exe (PID: 584)
Creates files in the Windows directory
- vc_redist.x86.exe (PID: 3780)
- vc_redist.x86.exe (PID: 2896)
- msiexec.exe (PID: 584)
- VC_redist.x86.exe (PID: 1624)
Starts itself from another location
- vc_redist.x86.exe (PID: 3780)
Executed as Windows Service
- vssvc.exe (PID: 3968)
Searches for installed software
- VC_redist.x86.exe (PID: 1808)
Creates files in the program directory
- VC_redist.x86.exe (PID: 1808)
Creates a software uninstall entry
- VC_redist.x86.exe (PID: 1808)
- VC_redist.x86.exe (PID: 3268)
Application launched itself
- VC_redist.x86.exe (PID: 2812)
- VC_redist.x86.exe (PID: 1624)
Removes files from Windows directory
- VC_redist.x86.exe (PID: 1624)
- vc_redist.x86.exe (PID: 3780)
- vc_redist.x86.exe (PID: 2896)
INFO
Application launched itself
- iexplore.exe (PID: 2408)
- chrome.exe (PID: 3040)
Creates files in the user directory
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 2408)
Reads settings of System Certificates
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 2408)
- wyUpdate.exe (PID: 2900)
Reads internet explorer settings
- iexplore.exe (PID: 3976)
Changes settings of System certificates
- iexplore.exe (PID: 2408)
Changes internet zones settings
- iexplore.exe (PID: 2408)
Reads the hosts file
- chrome.exe (PID: 3040)
- chrome.exe (PID: 3528)
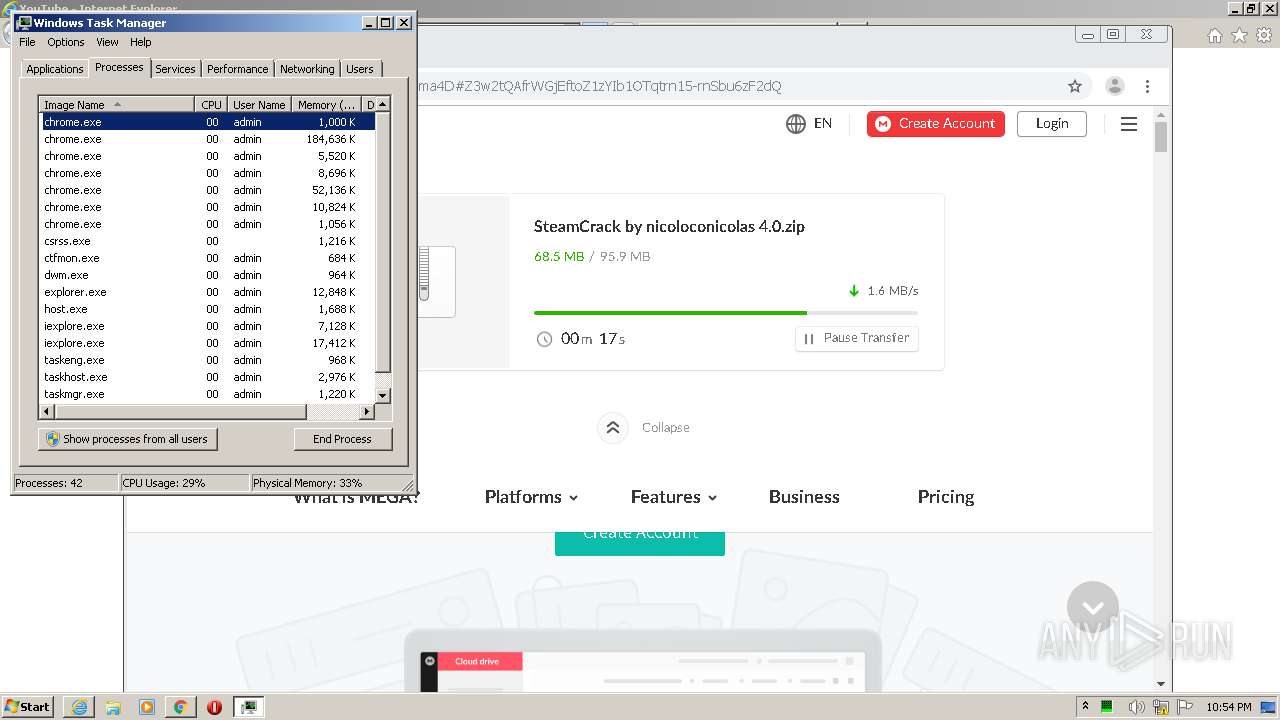
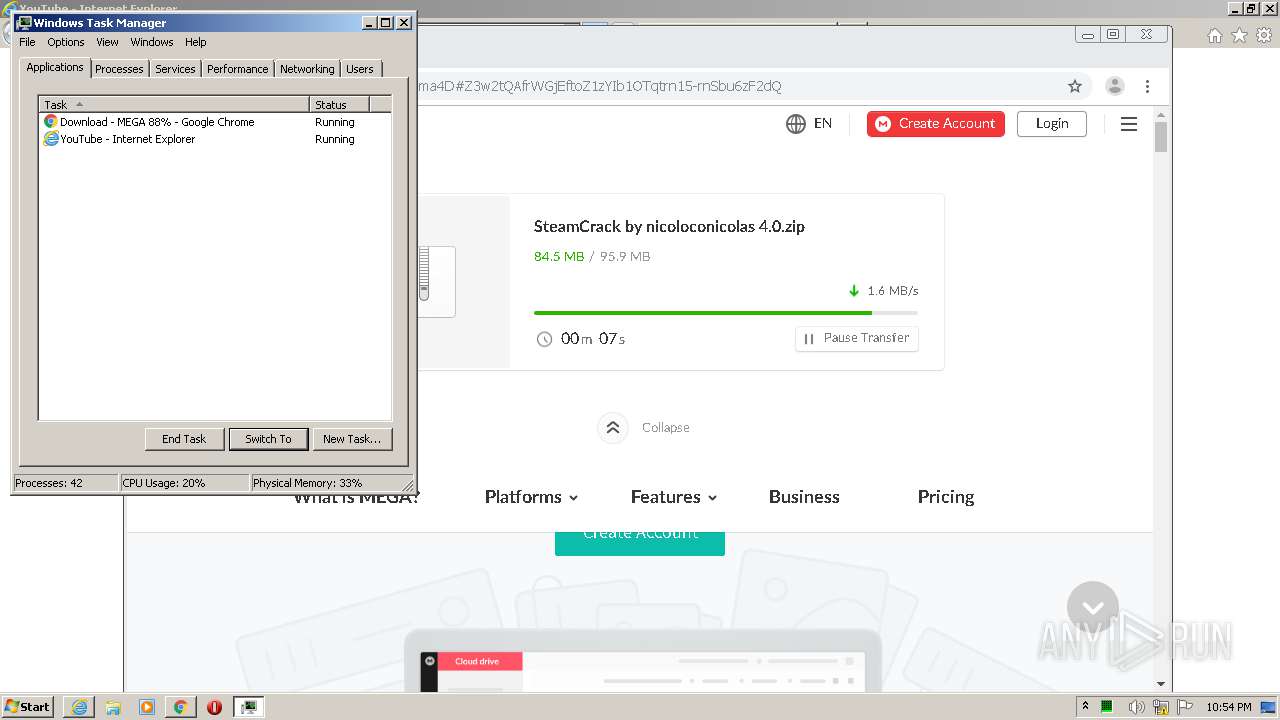
Manual execution by user
- taskmgr.exe (PID: 2904)
- chrome.exe (PID: 3040)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2408)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2188)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3968)
Creates a software uninstall entry
- msiexec.exe (PID: 584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
49
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,2629508473407498059,945531858574682328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1747770459661872807 --mojo-platform-channel-handle=1188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,2629508473407498059,945531858574682328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8155493936470665562 --mojo-platform-channel-handle=3904 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,2629508473407498059,945531858574682328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4446796711665500203 --mojo-platform-channel-handle=2480 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1624 | "C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" -burn.clean.room="C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 -uninstall -quiet -burn.related.upgrade -burn.ancestors={1aaa01ad-3069-4288-9c6f-37a140a8f6c7} -burn.filehandle.self=852 -burn.embedded BurnPipe.{9704B197-5987-4F84-84D7-316E8CF39111} {C0A47D0E-00FA-4876-883F-7C901A5AC8FA} 1808 | C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.21.27702 Exit code: 0 Version: 14.21.27702.2 Modules
| |||||||||||||||
| 1808 | "C:\Windows\Temp\{21A17197-18FB-462E-85C8-7A343B721040}\.be\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{DA9E39C9-4227-46B2-9824-AF9EEA9BA692} {00FD62BC-82B9-4060-9932-0C5017869D1D} 3780 | C:\Windows\Temp\{21A17197-18FB-462E-85C8-7A343B721040}\.be\VC_redist.x86.exe | vc_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.27.29016 Exit code: 0 Version: 14.27.29016.0 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,2629508473407498059,945531858574682328,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17290872830786166019 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6e0ca9d0,0x6e0ca9e0,0x6e0ca9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,2629508473407498059,945531858574682328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2667753628324636116 --mojo-platform-channel-handle=2516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,2629508473407498059,945531858574682328,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7122178596341991949 --mojo-platform-channel-handle=4256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 176
Read events
3 187
Write events
693
Delete events
296
Modification events
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3601592894 | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30864236 | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
168
Suspicious files
214
Text files
421
Unknown types
197
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab493C.tmp | — | |
MD5:— | SHA256:— | |||
| 3976 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar493D.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab50ED.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar50EE.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_3355B43C47989EF584B0CB7FC066CA09 | binary | |
MD5:— | SHA256:— | |||
| 3976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 3976 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\P3CC999I.txt | text | |
MD5:— | SHA256:— | |||
| 3976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_9FD7DD1CB26D88792DDAD6765AC87012 | der | |
MD5:— | SHA256:— | |||
| 3976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\62478D561920306F690C5B049535ED71 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
100
DNS requests
51
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3732 | SteamCrack.exe | GET | 301 | 104.23.99.190:80 | http://pastebin.com/raw/Q9jdwLhS | US | — | — | malicious |
3976 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDHLJeKVKvb%2BAwAAAADHzUc%3D | US | der | 471 b | whitelisted |
3976 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCJL7s1TELEmwMAAAAAx82q | US | der | 472 b | whitelisted |
3976 | iexplore.exe | GET | 200 | 23.55.163.57:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
3976 | iexplore.exe | GET | 200 | 23.55.163.57:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
3976 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCJL7s1TELEmwMAAAAAx82q | US | der | 472 b | whitelisted |
3976 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3976 | iexplore.exe | GET | 200 | 23.55.163.58:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgP8owLytP9BPbRZgKw%2FGHdqJg%3D%3D | US | der | 503 b | shared |
3976 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
3976 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | iexplore.exe | 172.217.212.190:443 | www.youtube.com | Google Inc. | US | unknown |
3976 | iexplore.exe | 216.58.210.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3976 | iexplore.exe | 142.250.185.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2408 | iexplore.exe | 172.217.212.190:443 | www.youtube.com | Google Inc. | US | unknown |
2408 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
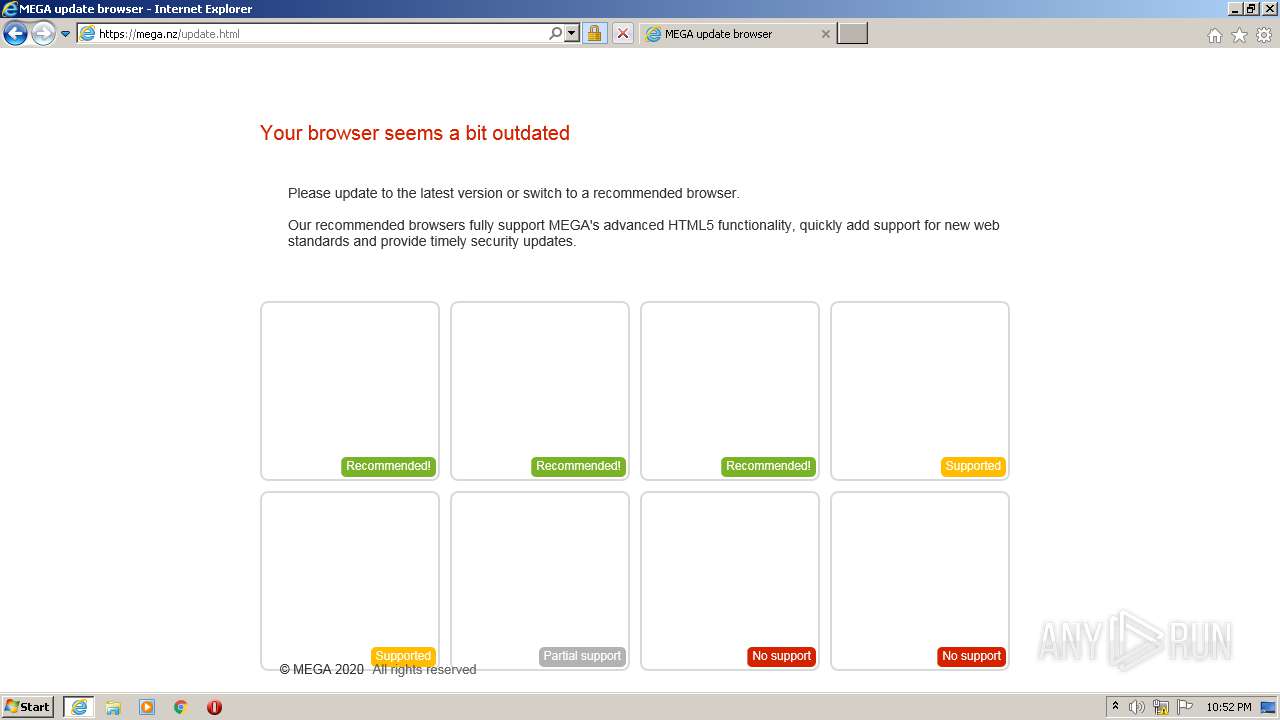
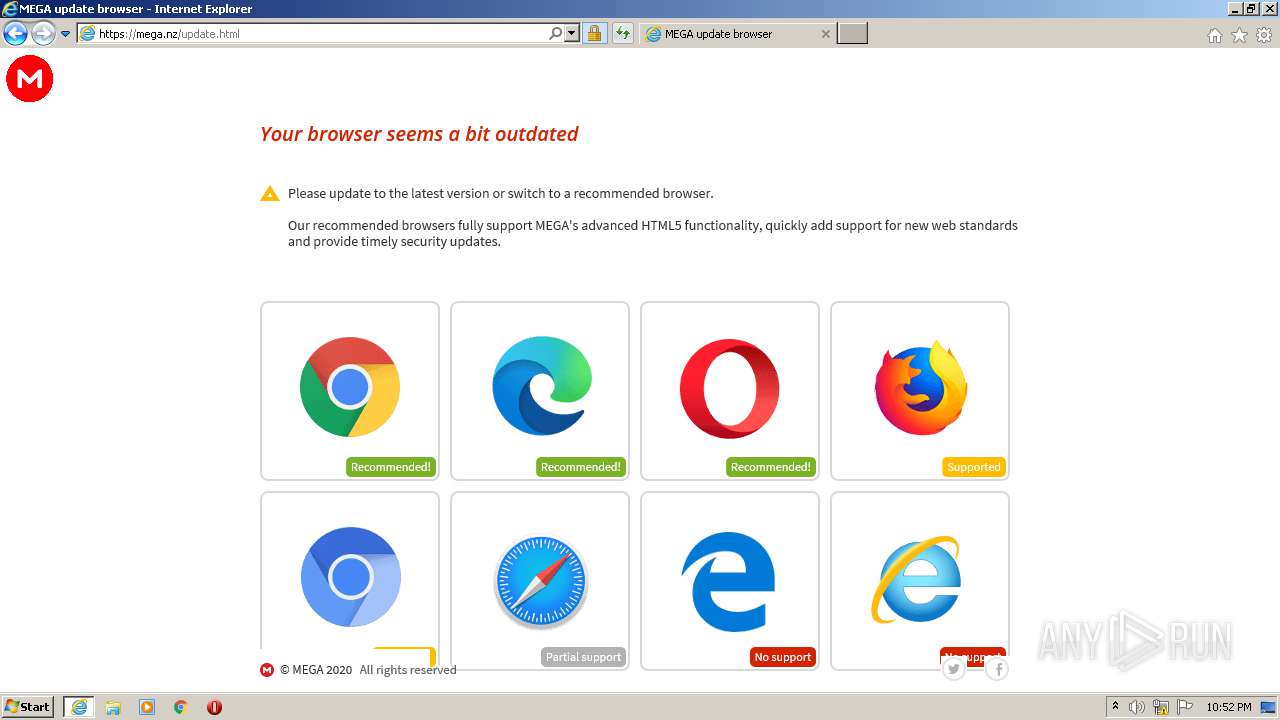
3976 | iexplore.exe | 89.44.169.135:443 | mega.nz | Datacenter Luxembourg S.A. | LU | suspicious |
3976 | iexplore.exe | 23.55.163.58:80 | r3.o.lencr.org | Akamai International B.V. | US | unknown |
3976 | iexplore.exe | 23.55.163.57:80 | crl.identrust.com | Akamai International B.V. | US | unknown |
3976 | iexplore.exe | 89.44.169.132:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
3976 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
mega.nz |
| whitelisted |
crl.identrust.com |
| whitelisted |
r3.o.lencr.org |
| shared |
eu.static.mega.co.nz |
| shared |
ocsp.usertrust.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
SteamCrack.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is |
SteamCrack.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
SteamCrack.exe | "generating new uuid : {943853d2-d0e9-4fba-80aa-3f729dfefa76}"
|