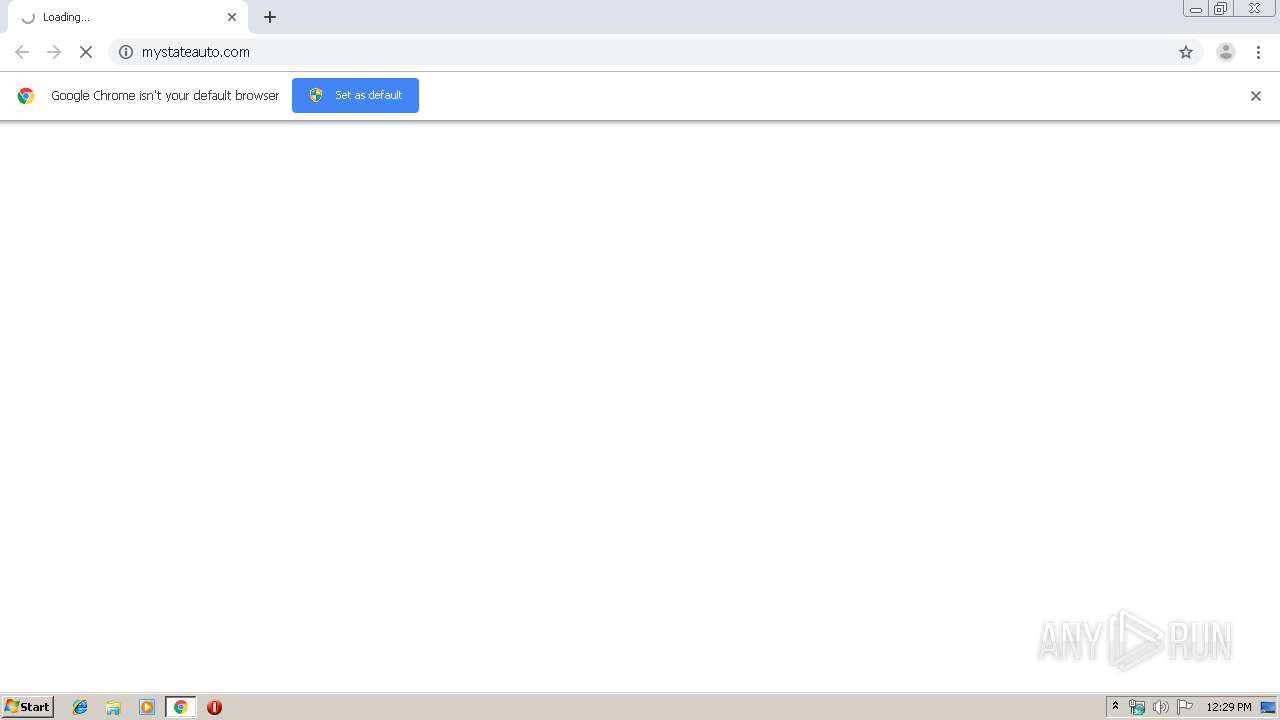
| URL: | http://mystateauto.com/ |
| Full analysis: | https://app.any.run/tasks/b7a4a70e-ed4b-469e-8ba9-cd88769b2887 |
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2019, 11:29:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1A19DED661AA12ADF5EF1E8D0AFC91AB |
| SHA1: | 2BE156E305CBEFFDDCF724DDACAECD19A741E868 |
| SHA256: | 534899099744314B03A8319EABAB4F9968B028CC2D92402530A6BC719C7881CF |
| SSDEEP: | 3:N1KTTEEKt:Cvi |
MALICIOUS
No malicious indicators.SUSPICIOUS
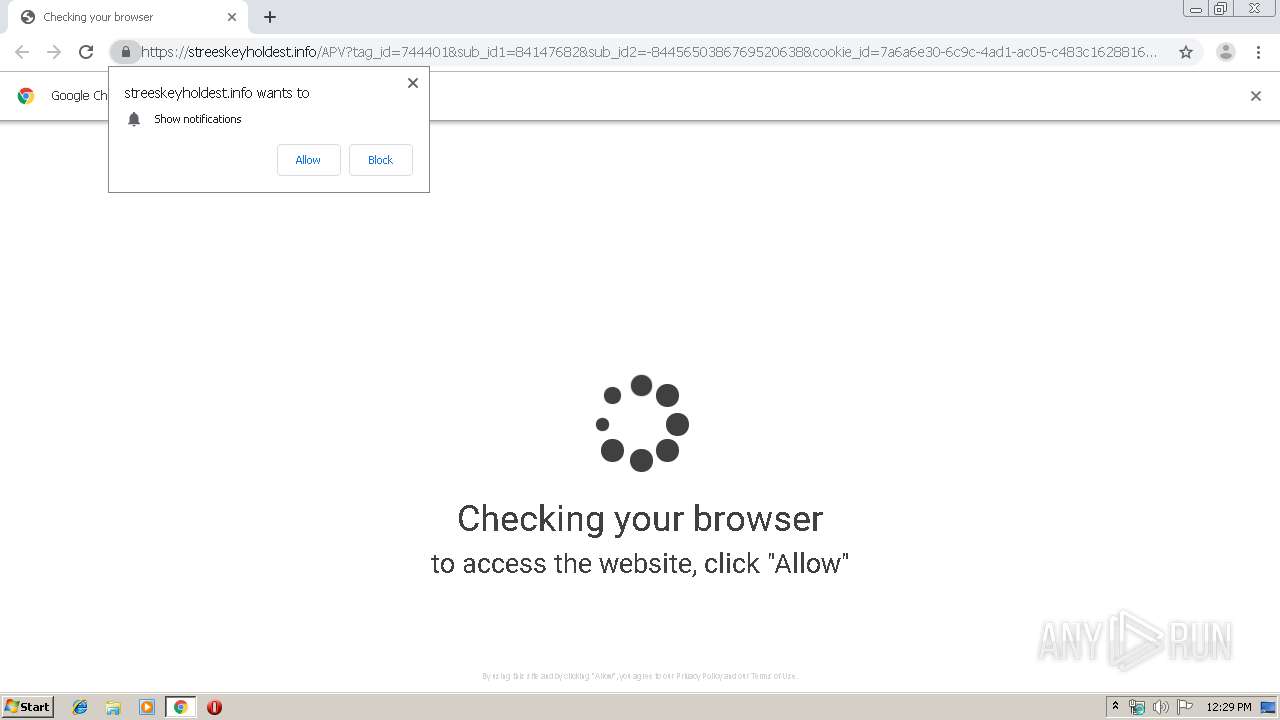
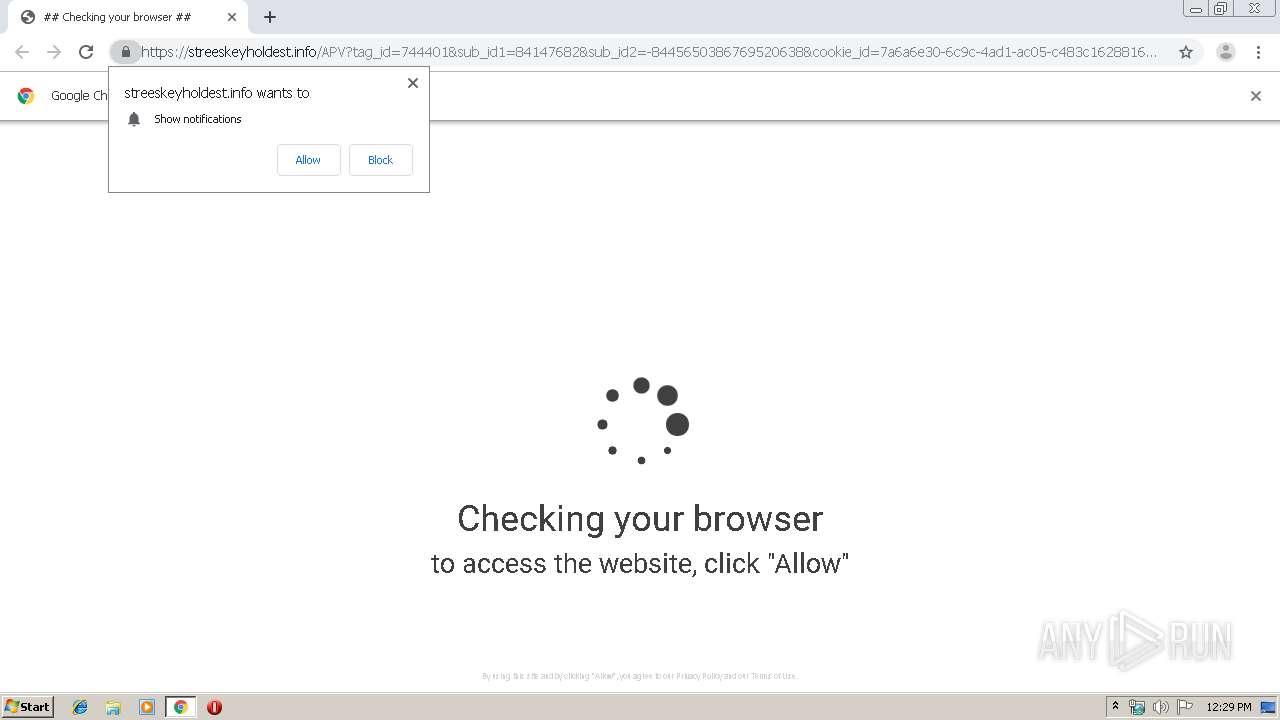
Modifies files in Chrome extension folder
- chrome.exe (PID: 3424)
INFO
Application launched itself
- chrome.exe (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10094527964094308808 --mojo-platform-channel-handle=1308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fdea9d0,0x6fdea9e0,0x6fdea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15997356089316375003 --mojo-platform-channel-handle=3880 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5922104337840118021 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14380078038768159060 --mojo-platform-channel-handle=3820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6712313633376066172 --mojo-platform-channel-handle=3656 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16666812321316604614 --mojo-platform-channel-handle=1060 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10365705416452752537 --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12766197159544397061 --mojo-platform-channel-handle=3024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3100629162699868429,15525636455395512705,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14174530214231397413 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
609
Read events
521
Write events
83
Delete events
5
Modification events
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3424-13210514985686250 |
Value: 259 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
24
Text files
193
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8f55b170-1f8d-49c4-bdc5-4891c65751a7.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1698ca.TMP | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
29
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2772 | chrome.exe | GET | 302 | 108.168.193.183:80 | http://mybestdc.com/aS/feedclick?s=j2q331W0qPwbR0ZlNj_oaK3dDnCBF-q5rMUtMFru4JrAM078pj-ORad73pnnDH6ohvzYfNFjJsIjeRAqbTvnp2bIMweJR9NLVFtq4HSO_D3fMVVyoveMVaYZ_8dAZcE4MLekFlfWsTpfBjRhq2gpKG5bIFyGV64-iegXUrvr2a0fZTd7tRZn2r7L4MaMTbTCr3lP1SdUWohdDRRXWhsIYY98a42odSNy7oX2dcE3g_Sa4VMG9-fEo5ExDvtLQ6TFwZAREc0JtJLrZD6b84KTdWaWAA0f2W__xtd_26SHJRi5n2jmrKDIYTJz5z3a5hAphrAwBMQZT4RhEkot035ncjqBJkVSS49XWA3y1uZiT0xfaQy3Bu-lCpe33k1oYToRHFmPThWOU2g__VqNfR7XzFOz08Hcm0QJW1qmo6MCdR5bWH-LkXmTk2JNLCtOxejiyrbXVlYzJpVJ_h8ZNI-ZqMwPsMCUEV7PmvveSwWT5_kFSqUsnYachA6raOLFP9238uM1IurVgtbZQWcrchUTJN5KPl9EmABmIT6YQDzFM4vQcYAOJwhMcT-8Vdipf1HjqKOC6MZSInGc1DTs1JvRfrCQKoBYeOPKhyjkQASiar8SsVluVRznJZr2C_bKDGrBnh2lPJuDQwwboEW8l7qhFxDxo-IAYq-yXt6Y3cpvEdiZyx-gy_7z-niZzSUrSHwBE9NkdmN9s4fxvO_9Gg5tEW0RpA2kxajL0pEllWiwUEOYDX9cnzDqJesNR-PQDpk9R55aoEMdYhKsFXnBOcqyOXqsazbGnVzAEhSwqwMsmzarEL6NW-RoyQKuCOmf6bJKlkXjq_l-lqeqGaUCLNl1kgD6lfpp3Wd5KcRP5awGksg45A6zy1POX9ddN8Q2t6CF6vxplFzs02wv6fyhMLQbsDh8LNGWArJQ8ZWt16X90e85R2LTbQ5b-kXxvf79bP1f2LiAEkUy6RizREpIqG80xl-V4RDvgdqBjsL4mEV2Iv26ZrnIUxl7fvQ64G5Ru-gkUf-aFDK6z6kmQHk1Y1zJvy15s7b6Ec-ecC0vqo8vIIgpnNXiU39HjqI6PnGrp6vuJQaKk2NYxi7oFq_IMplMgBm8BMuio9XsTU0DY4KLyjCPVzFX4InlR_-PmYRV2f34MeTCG-0_L9igbz8RYJpqYDr-BhBHgUSx9ZF3M8iSMvq7Vhjw3oaDsgygD-oMQXkVPk-R6K08ZVkZQ65_b_Vi6S13RtbJZF6RngwRWjLcJKWY6azbAV-H_maecdkoXZoIU9r1QVZhFVHA26Xn1pnCl7xQCjl5DrtM65IDACRHM8PyNxBGgXuQUQ-FV8MZnOtt-yaM-wgk2BCOYtYHxUcKOKc0OZIfpARwJCio2V0LSPQigeo668XmlI4fLnuawpSpjETGnGumM3NlUB6DshcmbgqGTX9j1jC7frgyHo5mTzbsbql-30brpTPGD1lUplNvhX89yigdeTAvxq8R9i-vhbt8k9-mum5-SrMsOVSOrFIeiwedU8j0yY4VM-NxvJ79a0Ol6tzyiboSOrbjEbq5e_vwAiKSDnfEd27PBbyxqdEykIfP_6vx2kdAmmzLFXubgxFd-pz25ktrh9EEVyRYA8ma27xqJzjTkrEYV0V1Ldpopyec5UJrWC1Wh3KHXo275meCTasL7X8TY03EDqJv4hUwjJBAo8FARU_6cwqzIu8nueE3ZFKNcOMC9YmaJwywCHvgZO3CoDLVK0wZbkaWbp5R1pl__-0ARhwT1_ntjXsTZaW8EaVDncv-s4nOZYs5pWfHqYflyc--sRlfUkfcvZK2xgigiui5_1LnqhiDHb12J13joqcbwX-xZmU-diWcGHZAmpdEFhSOGq3cP8hCZb3FLHAYfanxBVMeVkyWuTrT8Fb5rUs4SIfw4gTli-u-xbmaiQwuDCHwCi5Vgcqskb4YI7Vuy88PfNq7etY-RYphHrp2T8oEDvuUMF2MyXZ5nmUhER_L1uPVYDDM99q1X4-MWiZNLvQNgxeXHw_EhrbaR80cYJ8vcFBNZWh8gjCB53hb3w-RApj7JXtliIIyLL6YOg-drJ0U9Cj2y8T0f9XHbEccaekiVrq0qzLmE8d7v3au5fb_4RJpdcK6RU_FH8_U93VUp6Lz8BfNcl7lkNwPCsfAkVtTSG4H5W3ehxCC8bGfKp-EaPknDum8tXoLpsHb37MiMaY4OKsaRsbvZk_bpRfO6GPDMknjktdR5uiVSlonPvjngC1oqzIqTYwu6tYTKIhYOaBqWyaxuEa5cCBxns7rRyrIuWblt4W2jt5PU-e9NnsmTamiJnJbGGtViNHi0MXwDaN_Ifv8MMs5sBwlO7oBdjPsrkYcE9f57Y17E2WlvBGlQ53mh6y2RNxf5w | US | — | — | malicious |
2772 | chrome.exe | GET | 302 | 108.168.193.183:80 | http://p226681.mybestdc.com/adServe/domainClick?ai=Ez8q7JxwPJmHGoMIHSl0OY4ardw_yEJlvcUscBh9qfEFUx5WTJa5OtPwVvmtSzhIh_DiBOWL677FuZqJDC4MIfAKLlWByqyRvhgjtW7Lzw982rt61j5FimEeunZPygQO-5QwXYzJdnmeZSERH8vW49VgMMz32rVfj4xaJk0u9A2DF5cfD8SGttpHzRxgny9wUE1laHyCMIHneFvfD5ECmPsle2WIgjIsvpg6D52snRT0KPbLxPR_1cdsRxxp6SJWurSrMuYTx3u_dq7l9v_hEml1wrpFT8Ufz9T3dVSnovPwF81yXuWQ3A8Kx8CRW1NIbgflbd6HEILxsZ8qn4Ro-ScO6by1egumwdvfsyIxpjg4qxpGxu9mT9ulF87oY8MySeOS11Hm6JVKWic--OeALWirMipNjC7q1hMoiFg5oGpbJrG4RrlwIHGezutHKsi5ZuW3hbaO3k9T5702eyZNqaImclsYa1WI0eLQxfANo3-Tc-t90zEs3_trnU0jPpArU7wjWOl5RpDZQxGF12rkURNecs-9vJK1f_1vyTLYjVsoLuBAIS3oVWWp__riXRnqGnLL9g3RhC2ktJmalqtYdUYcE9f57Y17WJcqwJNsm7DtRr7O-Ik-Mglt7BALO2dZnKBFjok_pd8IJDyVRaU8O1CARLjWWIjaubNd0G9ZCKYdhr7d_8f_WjGpybQ90Go4ZZnqzIvm-Gm-wHSK4m9oDiX-MgTUZasXT5xISGsNs7ESRyc3Q7-jufs31EvJ1VNOm1kHg9SQxyiu38aEs3KNx7Cm2HeI0S938_gGwpSXr3tSAMcY_H2x0x44oOp7C1IxKiXhLmiyflhHQ2DhJtv57BYUyjjm9w6UwbN-HQI1TJo&ui=j2q331W0qPwbR0ZlNj_oaFY37AsT2AewB1KvTfzpBsjN836MAUpj3kSIFLvK_ap6s3qiZ0lGn3_jpXjwn_s6fm47ALWMpMcDVzftoICNQ0fZWY-zGFtE2g&si=1&oref=0b9f362ba490aa16a6b5e7376d0a6d5c&rb=wAOZ9K6KYGg&rr=0 | US | — | — | suspicious |
2772 | chrome.exe | GET | 302 | 35.153.26.224:80 | http://uthorner.info/redirect?tid=744401&subid=84147682&puid=000000000074933382106 | US | — | — | whitelisted |
2772 | chrome.exe | GET | 200 | 173.239.8.164:80 | http://mystateauto.com/ | US | html | 425 b | malicious |
2772 | chrome.exe | GET | 404 | 173.239.8.164:80 | http://mystateauto.com/favicon.ico | US | html | 188 b | malicious |
2772 | chrome.exe | POST | 200 | 173.239.8.164:80 | http://mystateauto.com/ | US | html | 1.92 Kb | malicious |
2772 | chrome.exe | GET | 200 | 173.194.150.139:80 | http://r5---sn-f5f7ln7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.217.54&mm=28&mn=sn-f5f7ln7s&ms=nvh&mt=1566040763&mv=u&mvi=4&pl=21&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2772 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.6 Kb | whitelisted |
2772 | chrome.exe | GET | 200 | 52.85.182.222:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2772 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2772 | chrome.exe | 173.239.8.164:80 | mystateauto.com | Webair Internet Development Company Inc. | US | malicious |
2772 | chrome.exe | 108.168.193.183:80 | mybestdc.com | SoftLayer Technologies Inc. | US | suspicious |
2772 | chrome.exe | 35.153.26.224:80 | uthorner.info | — | US | unknown |
— | — | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
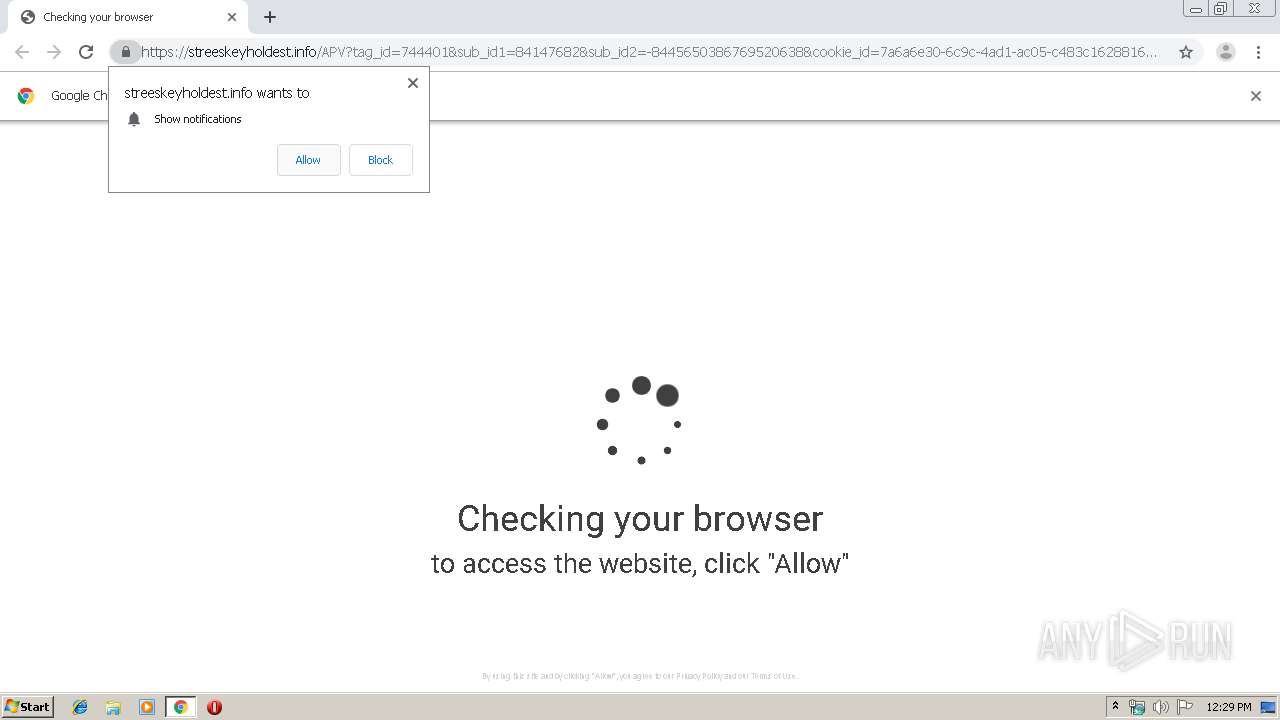
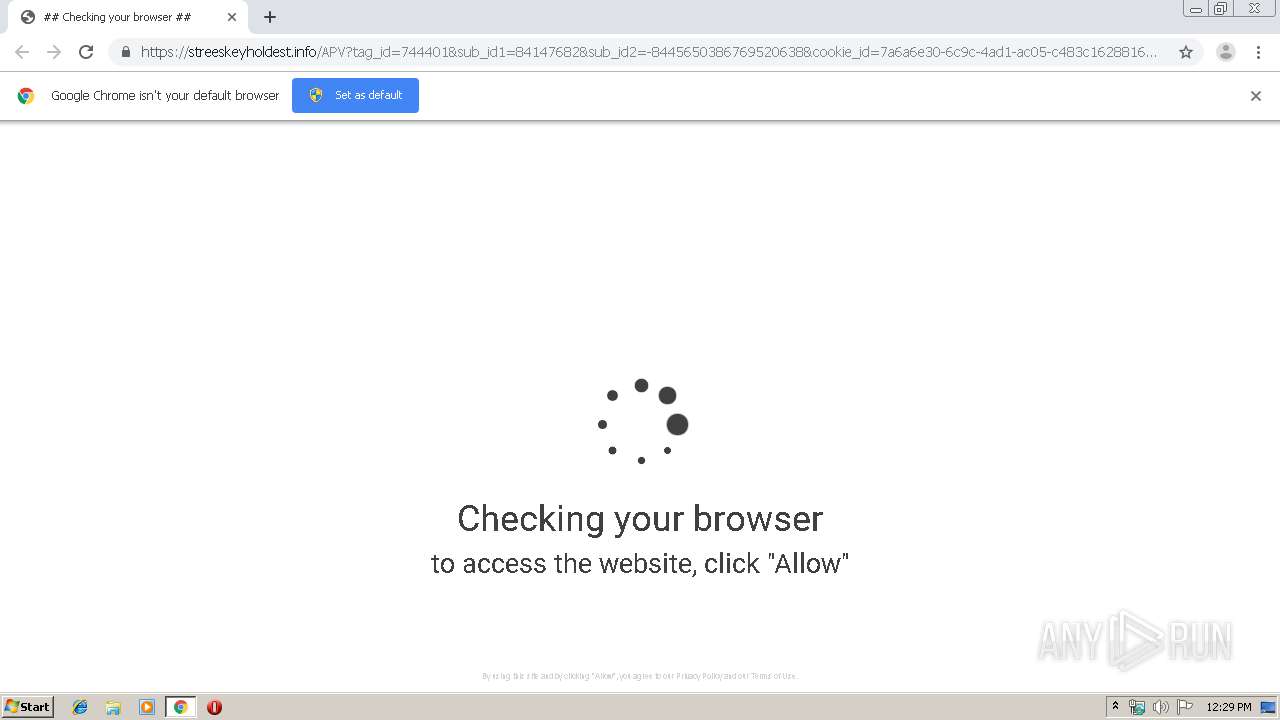
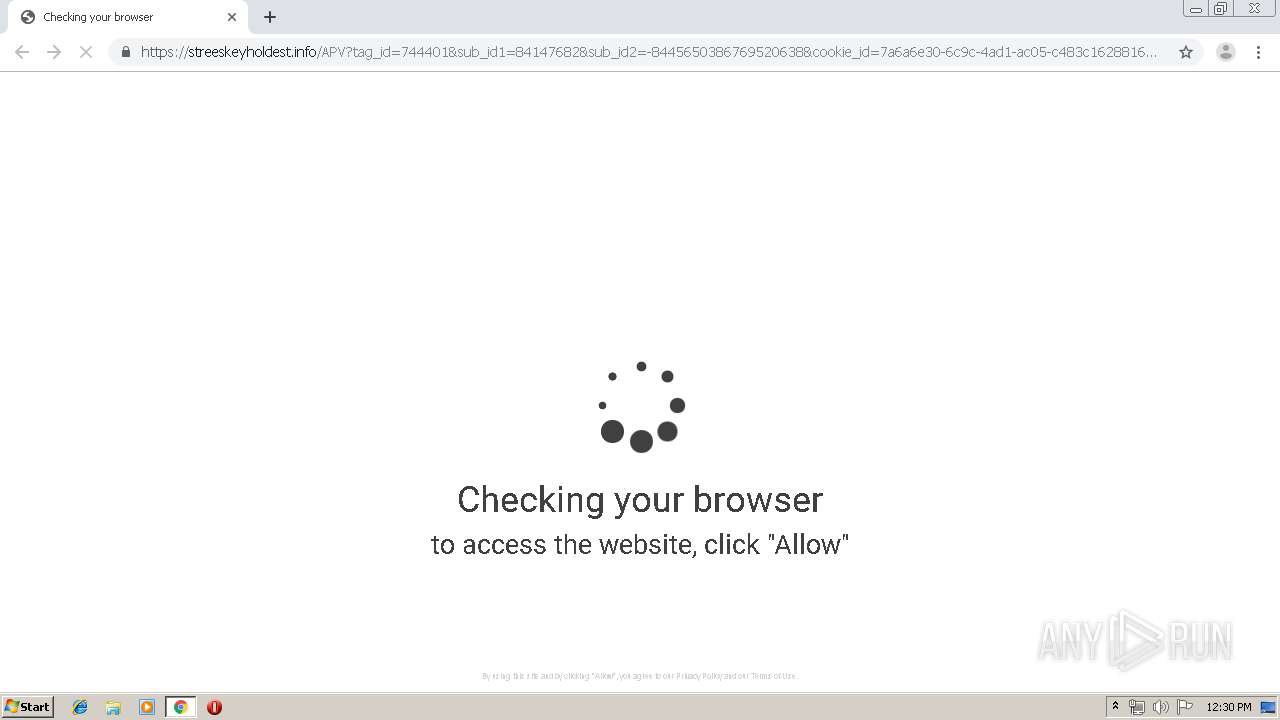
2772 | chrome.exe | 104.18.28.216:443 | streeskeyholdest.info | Cloudflare Inc | US | shared |
2772 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 173.194.150.139:80 | r5---sn-f5f7ln7s.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mystateauto.com |
| malicious |
accounts.google.com |
| shared |
mybestdc.com |
| malicious |
p226681.mybestdc.com |
| suspicious |
uthorner.info |
| whitelisted |
streeskeyholdest.info |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |