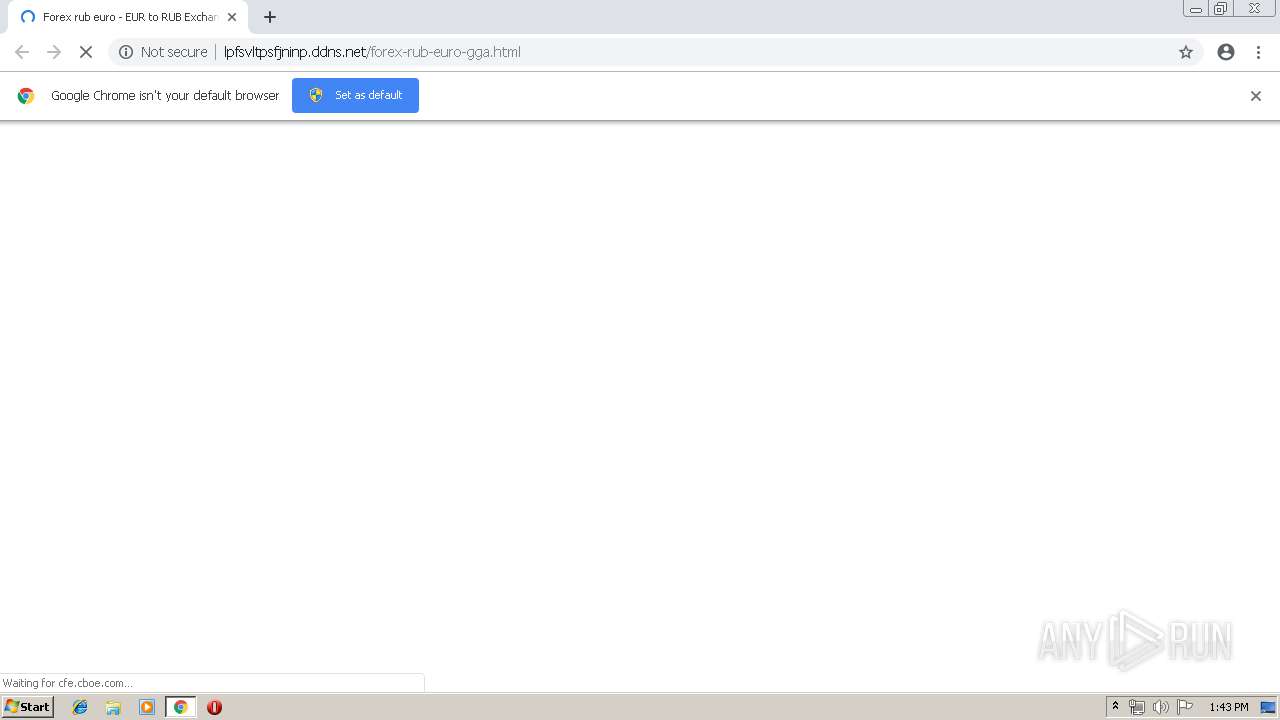
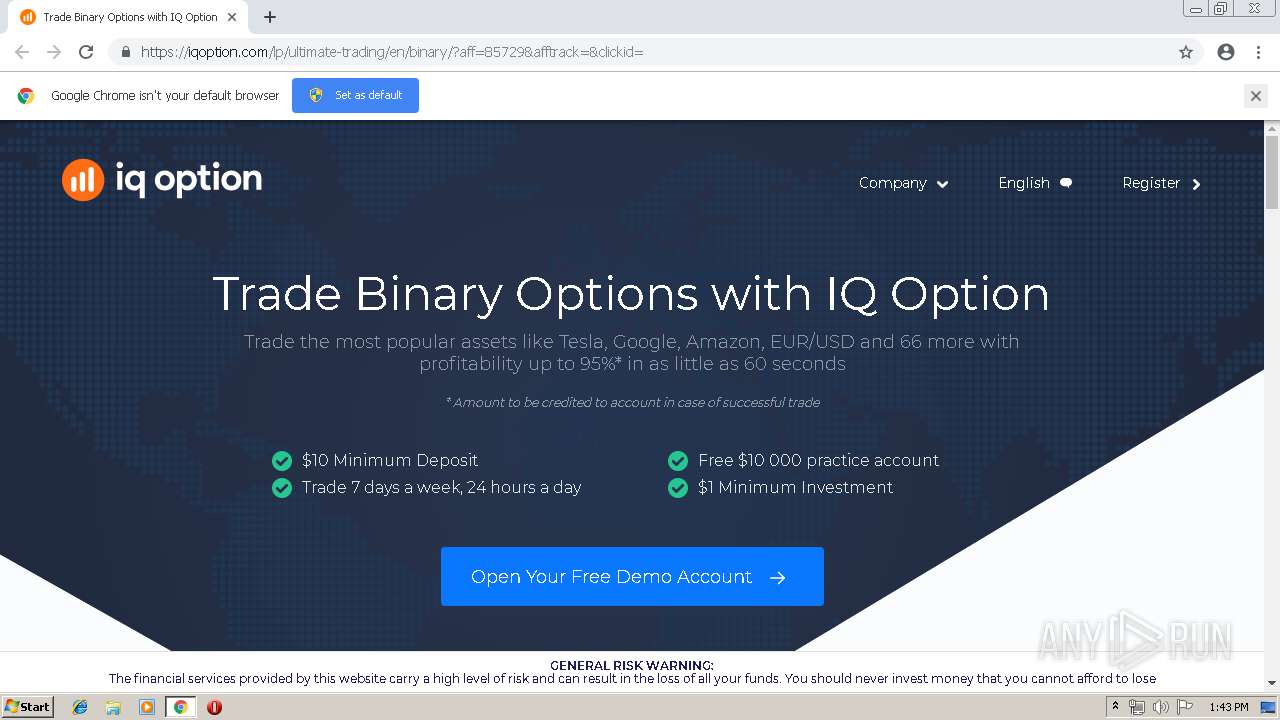
| URL: | http://lpfsvltpsfjninp.ddns.net/forex-rub-euro-gga.html |
| Full analysis: | https://app.any.run/tasks/72eca1a5-0739-413e-a118-18d9fdac3d72 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 12:43:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5B966EB400F6DCB6C440138E1BF8BF34 |
| SHA1: | 9C9C59F00520D3E439A99F973E5B99CC6B5EB166 |
| SHA256: | 5339B9ECCE6072B6092AF78EBEF142A207FF4C3706B270019C1E9CFE989DBB9E |
| SSDEEP: | 3:N1KSVDESOXBiL0CrksUJ:CSVDESoiLHrksQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2836)
INFO
Changes settings of System certificates
- chrome.exe (PID: 2836)
Application launched itself
- chrome.exe (PID: 2836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --service-pipe-token=11342234035670150271 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11342234035670150271 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16735344514188690593 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16735344514188690593 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8169600627146511039 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8169600627146511039 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8524420548475239854 --mojo-platform-channel-handle=4924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1939819875553031350 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1939819875553031350 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2672 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17900452069027208286 --mojo-platform-channel-handle=4768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9553660725732238060 --mojo-platform-channel-handle=2784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --service-pipe-token=1267025299571584538 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1267025299571584538 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5978971825631691989 --mojo-platform-channel-handle=4516 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13757712096839986545 --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
549
Read events
471
Write events
74
Delete events
4
Modification events
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2836-13202397822788875 |
Value: 259 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
41
Text files
164
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF120f3a.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dd45362e-e371-4632-8fdc-7d48a9877f42.tmp | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
74
DNS requests
51
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2836 | chrome.exe | GET | — | 79.137.24.220:80 | http://lpfsvltpsfjninp.ddns.net/forex-rub-euro-gga.html | DE | — | — | malicious |
2836 | chrome.exe | GET | 301 | 132.148.246.167:80 | http://www.financialhubindia.com/wp-content/uploads/2015/09/i-1024x557.png | US | — | — | unknown |
2836 | chrome.exe | GET | — | 132.148.246.167:80 | http://www.financialhubindia.com/ | US | — | — | unknown |
2836 | chrome.exe | GET | 200 | 104.17.227.57:80 | http://cfe.cboe.com/education/vixprimer/primerimages/b2.gif | US | image | 21.7 Kb | shared |
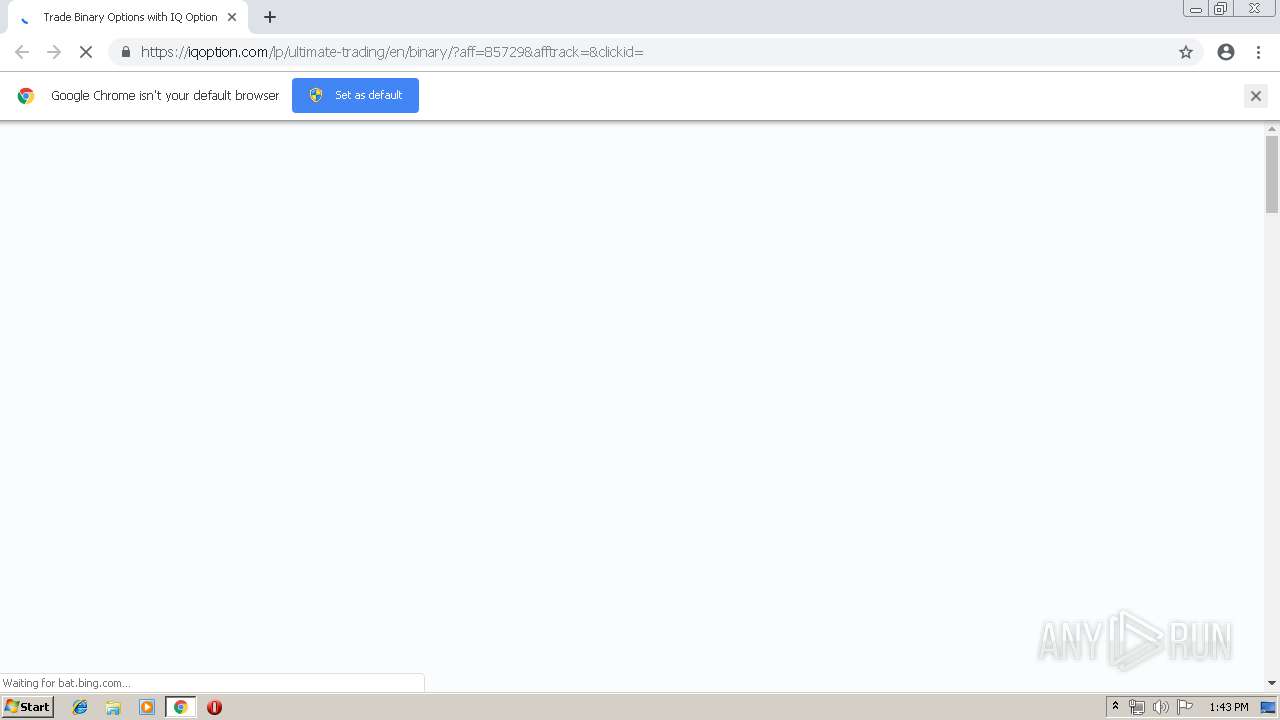
2836 | chrome.exe | GET | 200 | 5.9.48.245:80 | http://arbitko.ru/js/optavopowx.js?q=Forex%20rub%20euro | DE | text | 369 b | suspicious |
2836 | chrome.exe | GET | 200 | 87.248.114.12:80 | http://l2.yimg.com/bt/api/res/1.2/DRPVKf921nUivr3ag0o9zA--/YXBwaWQ9eW5ld3M7cT04NQ--/https://media.dailyfx.com/illustrations/2014/10/06/USD-RUB-Continues-Ascent-Despite-negation-of-Capital-Controls_body_Picture_1.png.full.png | GB | image | 46.4 Kb | shared |
2836 | chrome.exe | GET | 200 | 151.101.0.233:80 | http://media-s3-us-east-1.ceros.com/moneyweb/images/2016/02/03/640f92a0a0b7dd80d1f6dd2b7bf08f76/investments-0.jpg | US | image | 212 Kb | suspicious |
2836 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2836 | chrome.exe | GET | 200 | 195.208.1.106:80 | http://fx-news.pro/images/USDRUB-XBRUSD_87j90w9w.png | RU | image | 170 Kb | malicious |
2836 | chrome.exe | GET | 200 | 185.31.210.184:80 | http://fxbrok.com/upload/medialibrary/75e/75e39a61320cc4ab18c6375dc107be4d.jpg | DE | image | 39.3 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2836 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 79.137.24.220:80 | lpfsvltpsfjninp.ddns.net | OVH SAS | DE | malicious |
2836 | chrome.exe | 104.17.227.57:80 | cfe.cboe.com | Cloudflare Inc | US | shared |
2836 | chrome.exe | 5.9.48.245:80 | arbitko.ru | Hetzner Online GmbH | DE | unknown |
2836 | chrome.exe | 104.20.82.28:80 | www.roboforex.com | Cloudflare Inc | US | shared |
2836 | chrome.exe | 104.20.82.28:443 | www.roboforex.com | Cloudflare Inc | US | shared |
2836 | chrome.exe | 89.163.146.128:80 | www.fxteam.ru | myLoc managed IT AG | DE | unknown |
2836 | chrome.exe | 89.163.146.128:443 | www.fxteam.ru | myLoc managed IT AG | DE | unknown |
2836 | chrome.exe | 87.248.114.12:80 | l2.yimg.com | Yahoo! UK Services Limited | GB | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
lpfsvltpsfjninp.ddns.net |
| malicious |
clientservices.googleapis.com |
| whitelisted |
arbitko.ru |
| unknown |
www.roboforex.com |
| unknown |
cfe.cboe.com |
| unknown |
www.fxteam.ru |
| unknown |
l2.yimg.com |
| unknown |
crt.sectigo.com |
| whitelisted |
strategy4you.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2836 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Keitaro TDS Redirect |
2836 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |