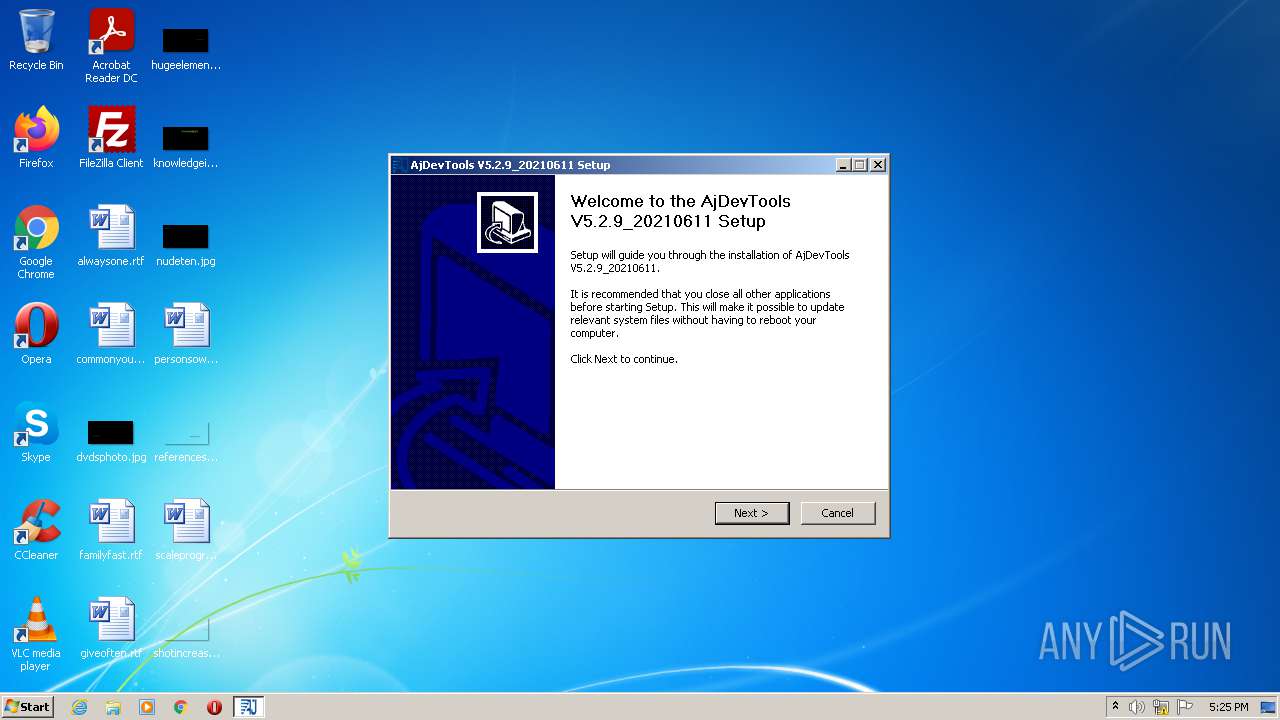
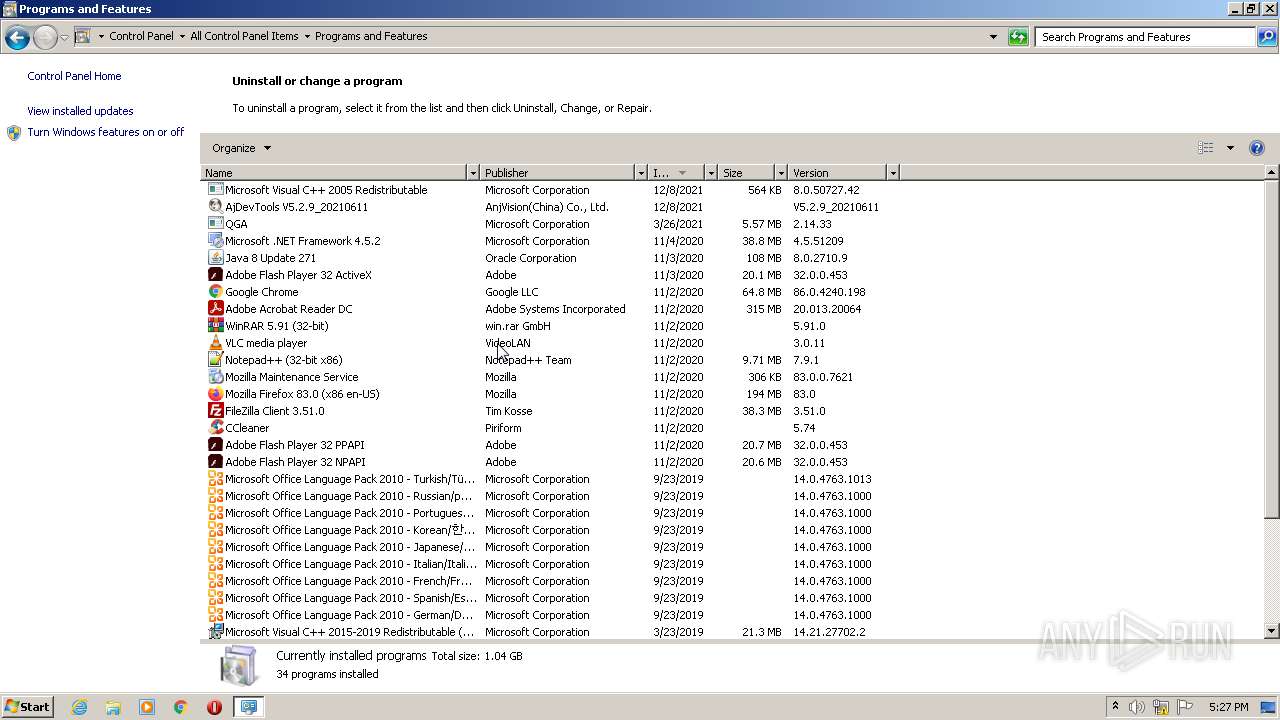
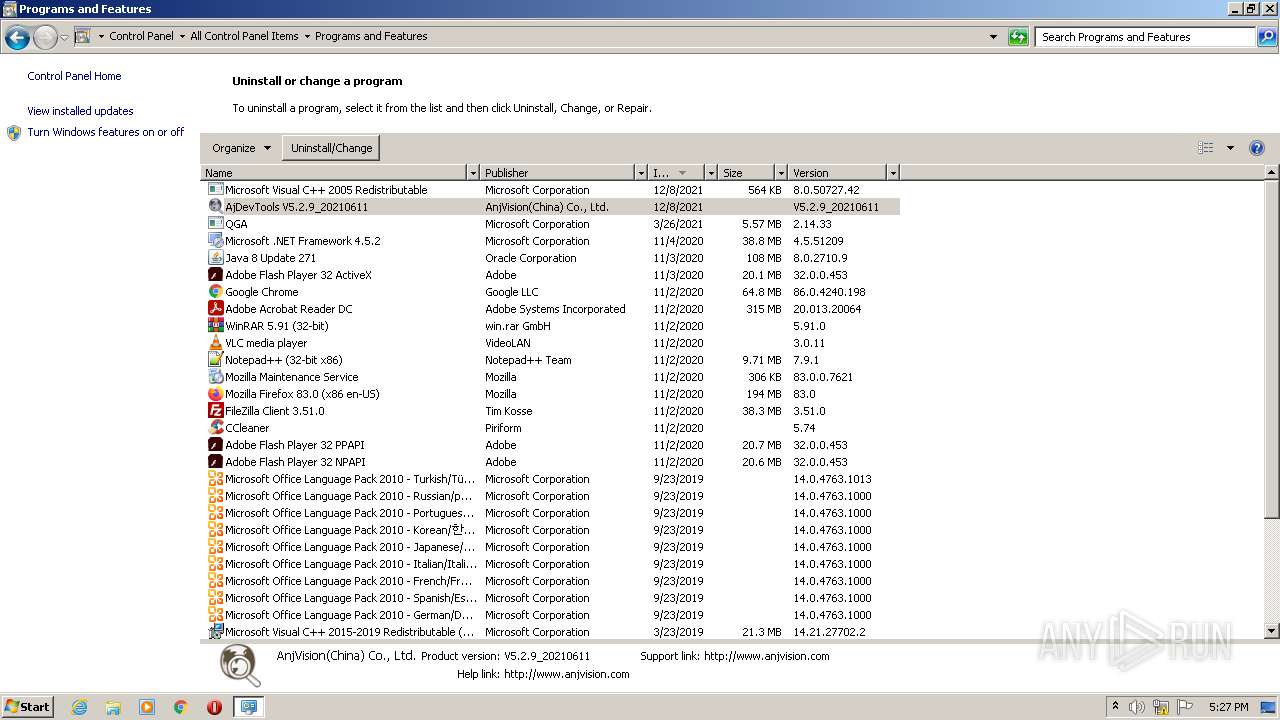
| File name: | AjDevTools_V5.2.9_20210611.exe |
| Full analysis: | https://app.any.run/tasks/e281b772-f5c0-4d9c-83de-7af37d9514d1 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2021, 17:25:23 |
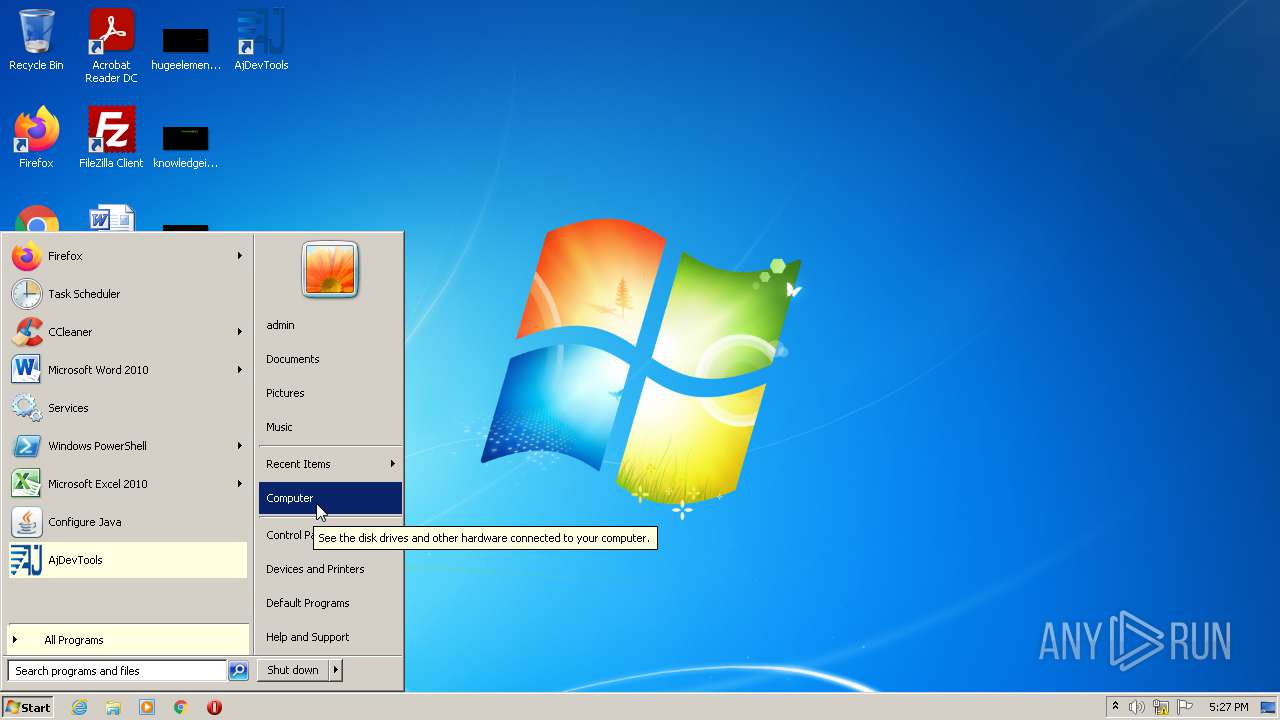
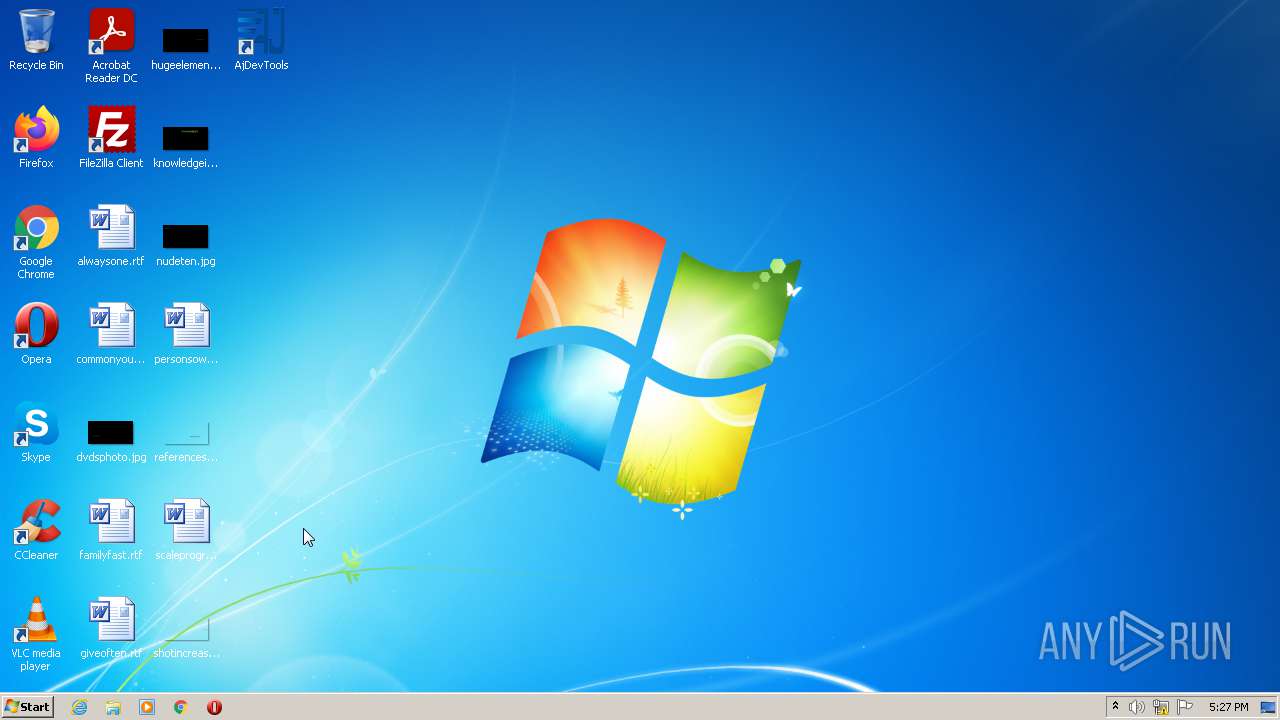
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
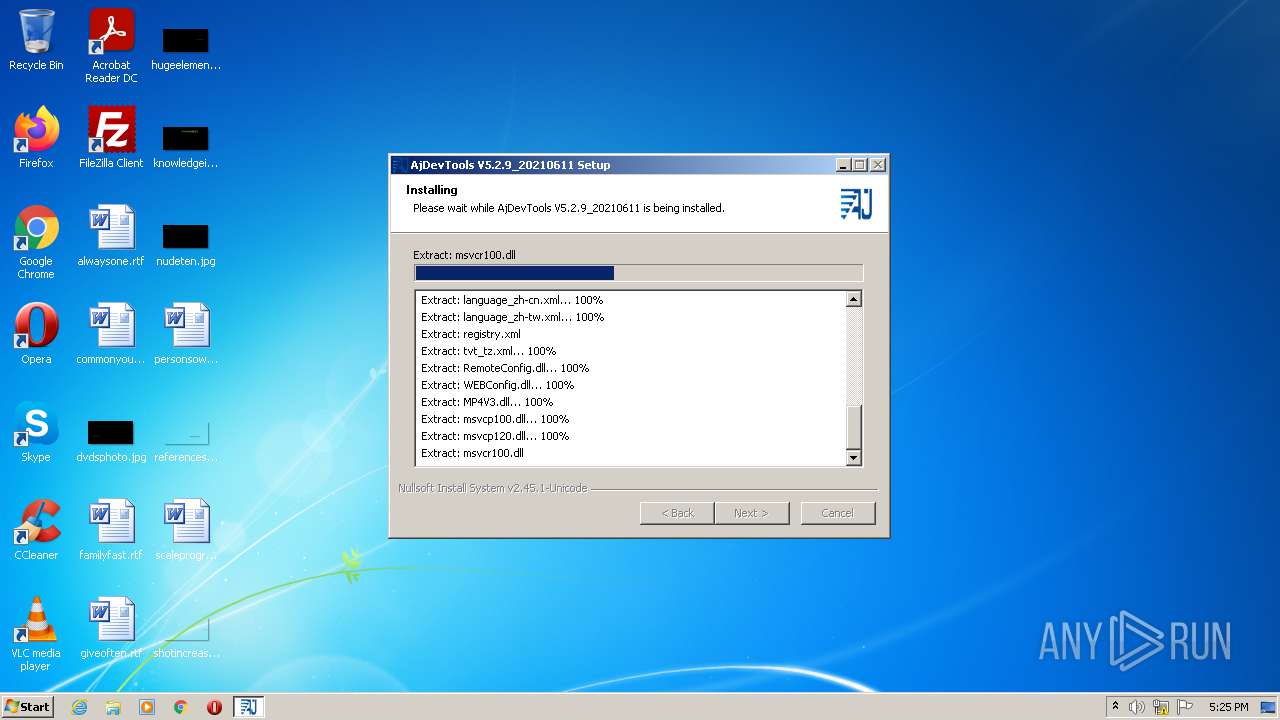
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 223A3C446558C62D76707B3014263389 |
| SHA1: | D8C64613842751B8BED01F1483A19A7DE85113B0 |
| SHA256: | 53284857B6DCF1BDC1B6E3737A4E4FCCD03B40409E634E700E53CC1FF154761B |
| SSDEEP: | 196608:GiPuhL9IibEeOqbMT5tPYjXPuxCup5vn9FeagO/A15pWWTMw4fA5g8hsG+Sm1lj5:GiiIi6TsXPs68/U5cM5HR+Z1Xn |
MALICIOUS
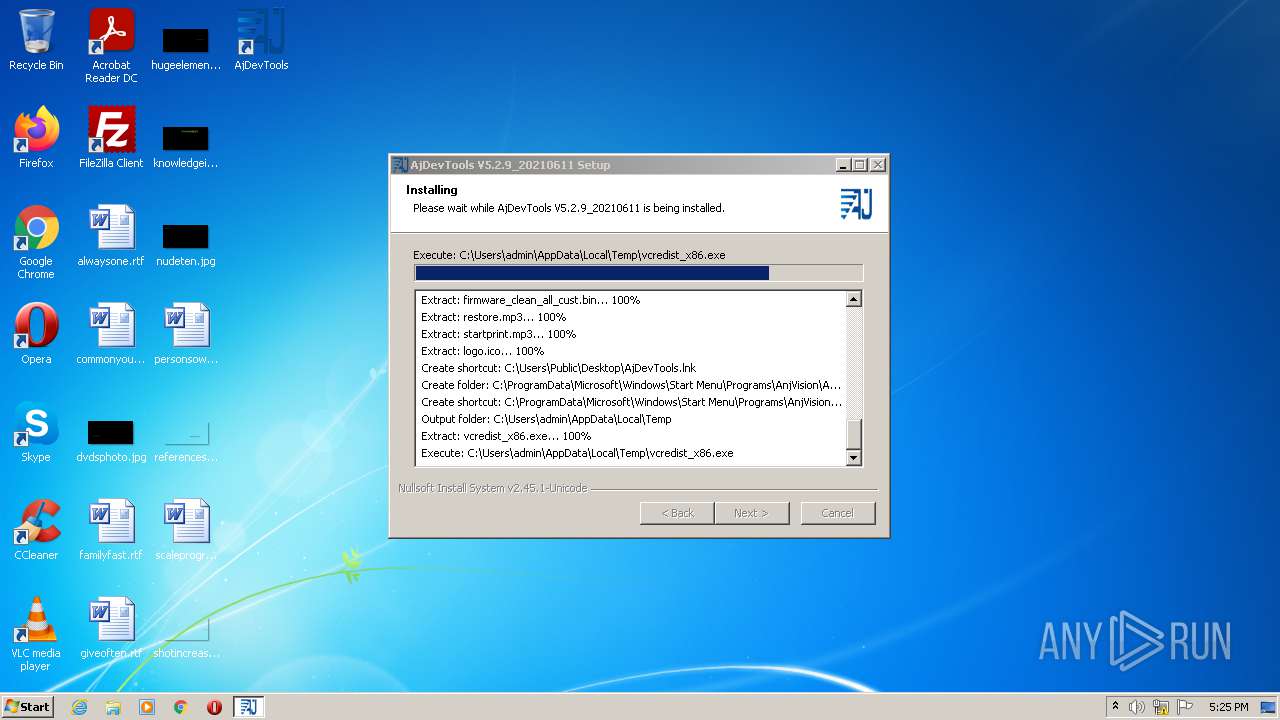
Loads dropped or rewritten executable
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- AjDevTools.exe (PID: 3732)
Drops executable file immediately after starts
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- uninst.exe (PID: 4080)
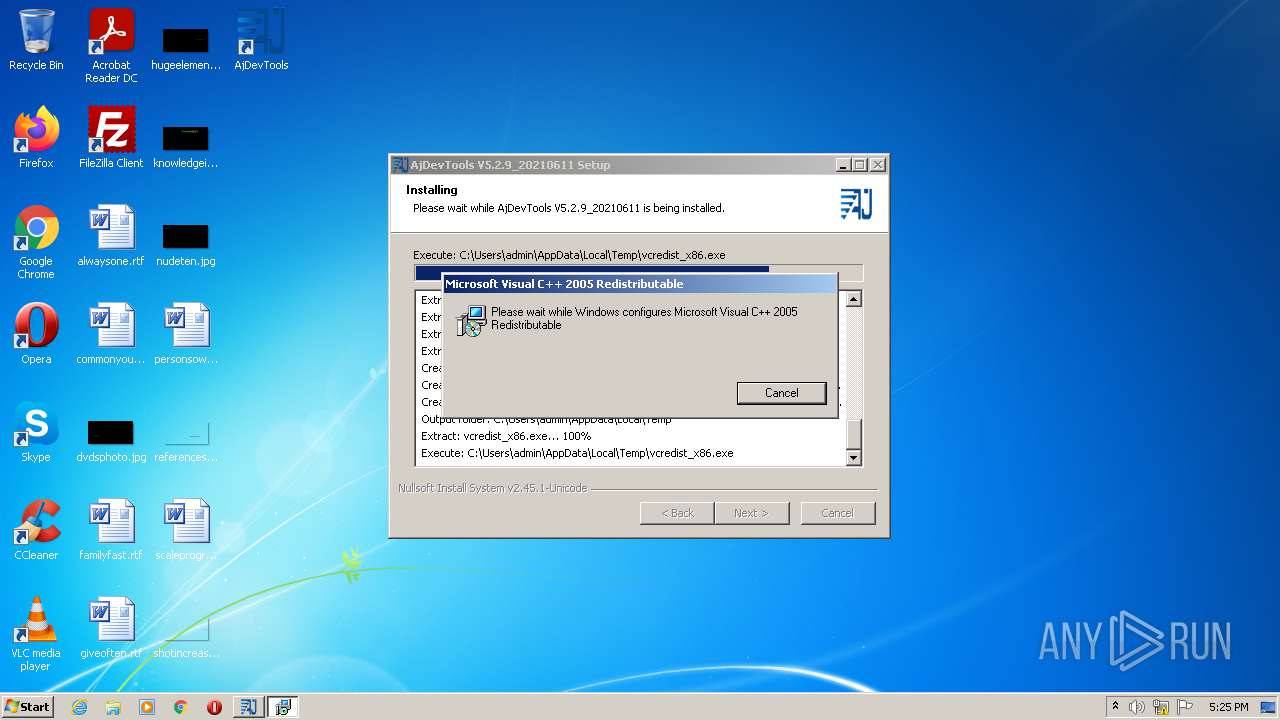
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 352)
Application was dropped or rewritten from another process
- vcredist_x86.exe (PID: 352)
- AjDevTools.exe (PID: 3732)
SUSPICIOUS
Reads the computer name
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- uninst.exe (PID: 4080)
- Au_.exe (PID: 3496)
Checks supported languages
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- vcredist_x86.exe (PID: 352)
- AjDevTools.exe (PID: 3732)
- uninst.exe (PID: 4080)
- Au_.exe (PID: 3496)
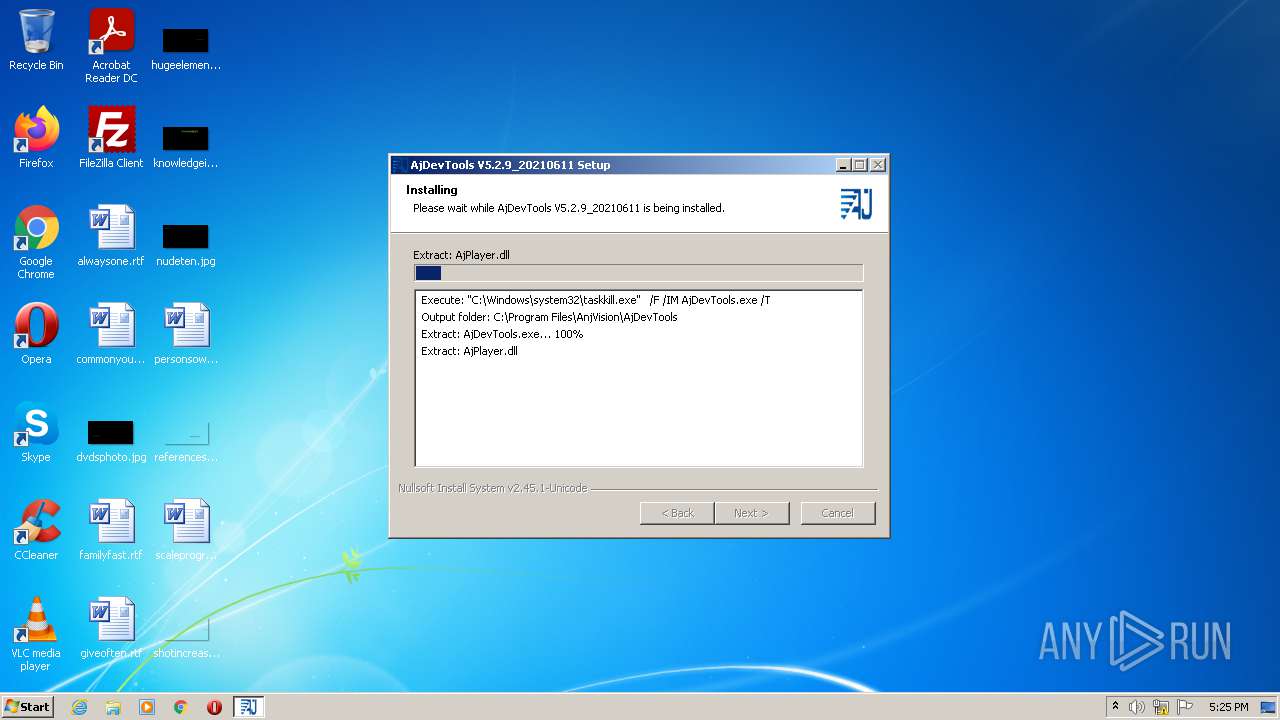
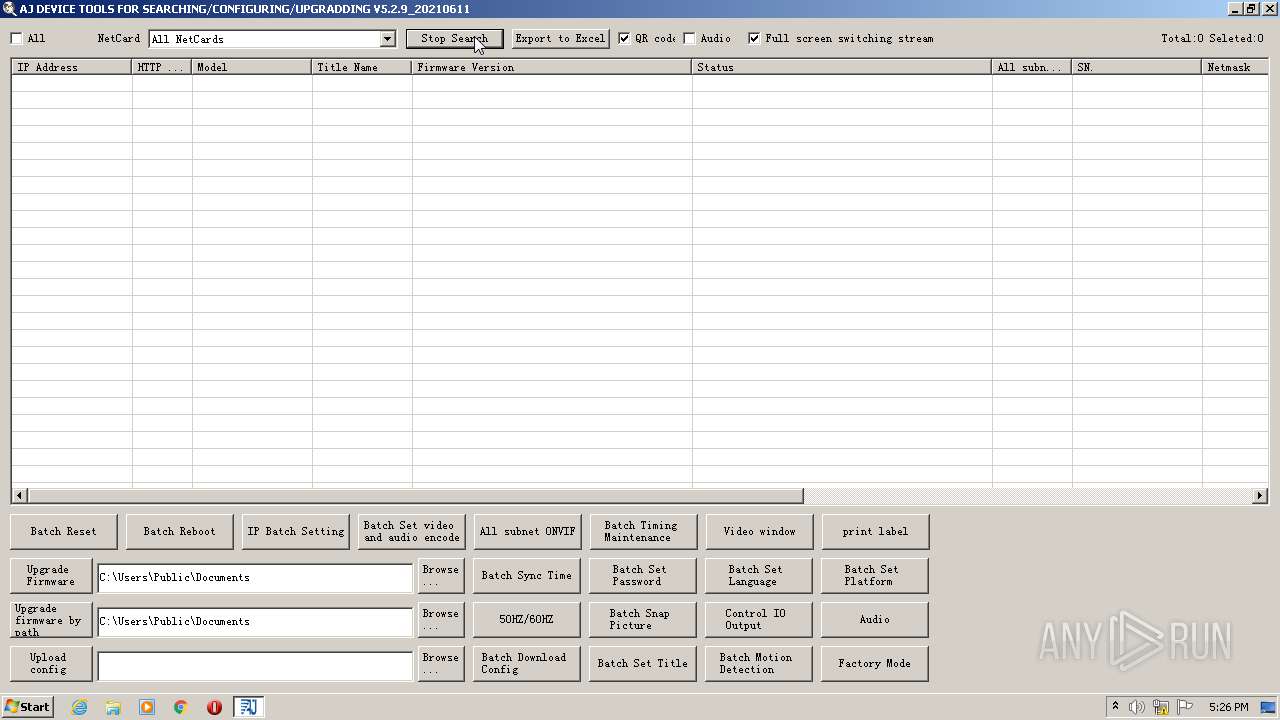
Uses TASKKILL.EXE to kill process
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
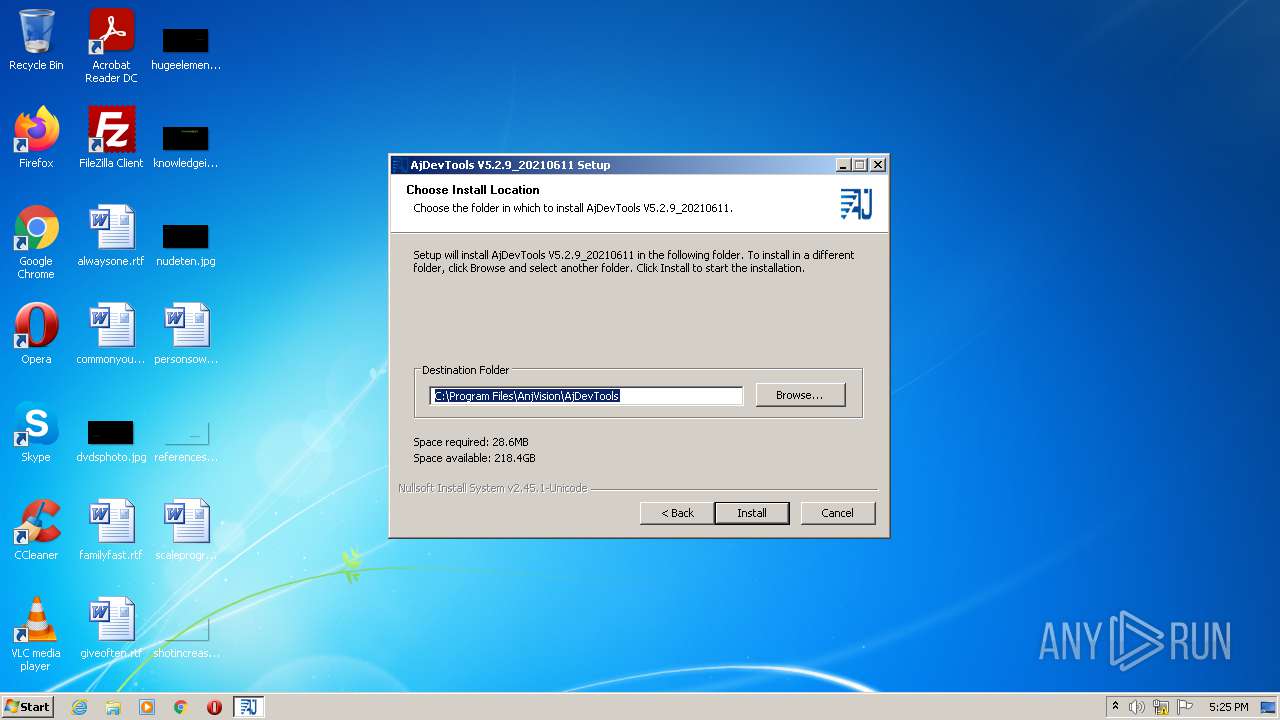
Creates a directory in Program Files
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- AjDevTools.exe (PID: 3732)
Drops a file that was compiled in debug mode
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- msiexec.exe (PID: 1328)
Drops a file with too old compile date
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- msiexec.exe (PID: 1328)
- uninst.exe (PID: 4080)
Executable content was dropped or overwritten
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- vcredist_x86.exe (PID: 352)
- msiexec.exe (PID: 1328)
- uninst.exe (PID: 4080)
Creates files in the program directory
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- msiexec.exe (PID: 1328)
Executed as Windows Service
- msiexec.exe (PID: 1328)
- vssvc.exe (PID: 2324)
Reads Windows owner or organization settings
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 1328)
Reads the Windows organization settings
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 1328)
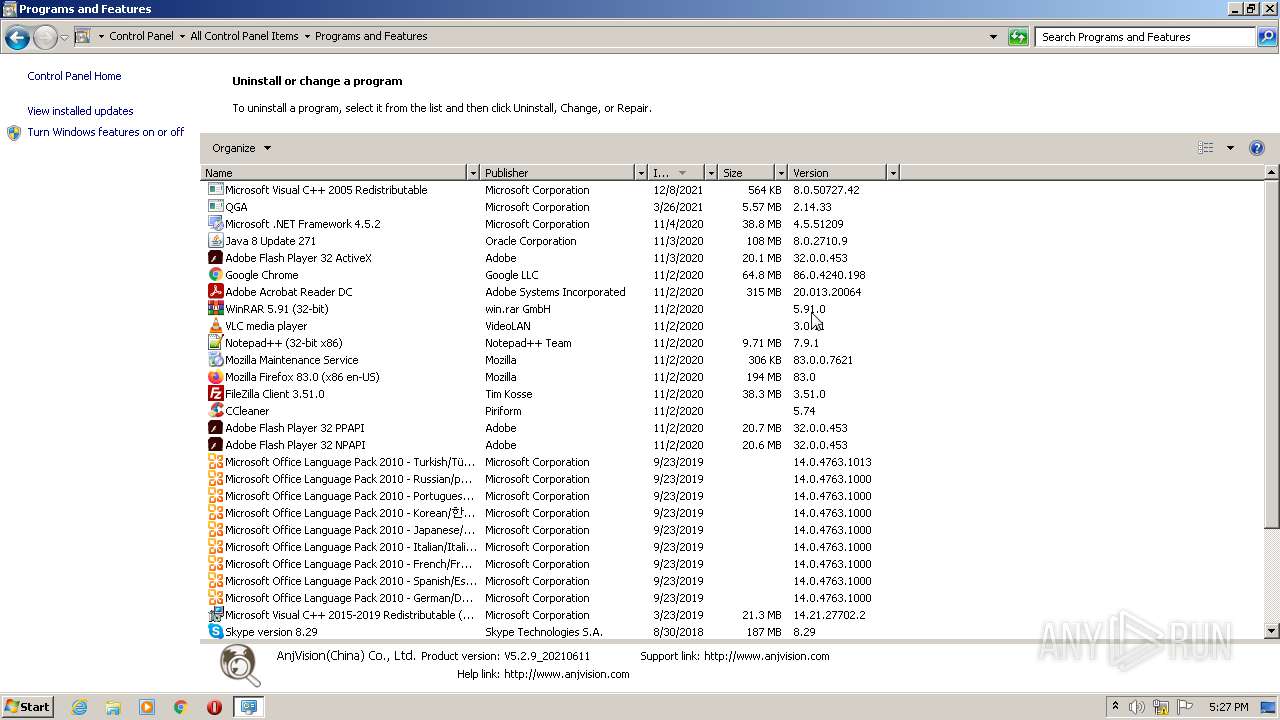
Searches for installed software
- msiexec.exe (PID: 1328)
- DllHost.exe (PID: 3604)
- AjDevTools.exe (PID: 3732)
- Au_.exe (PID: 3496)
Reads Environment values
- vssvc.exe (PID: 2324)
Application launched itself
- msiexec.exe (PID: 1328)
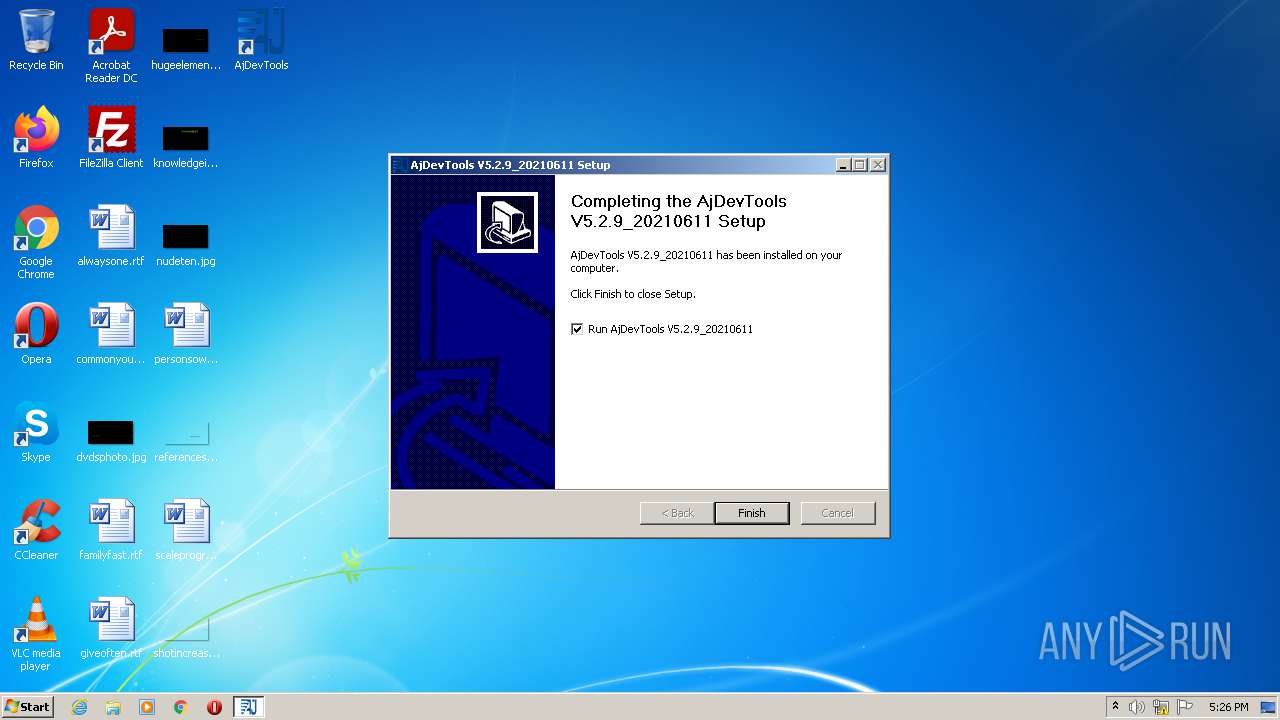
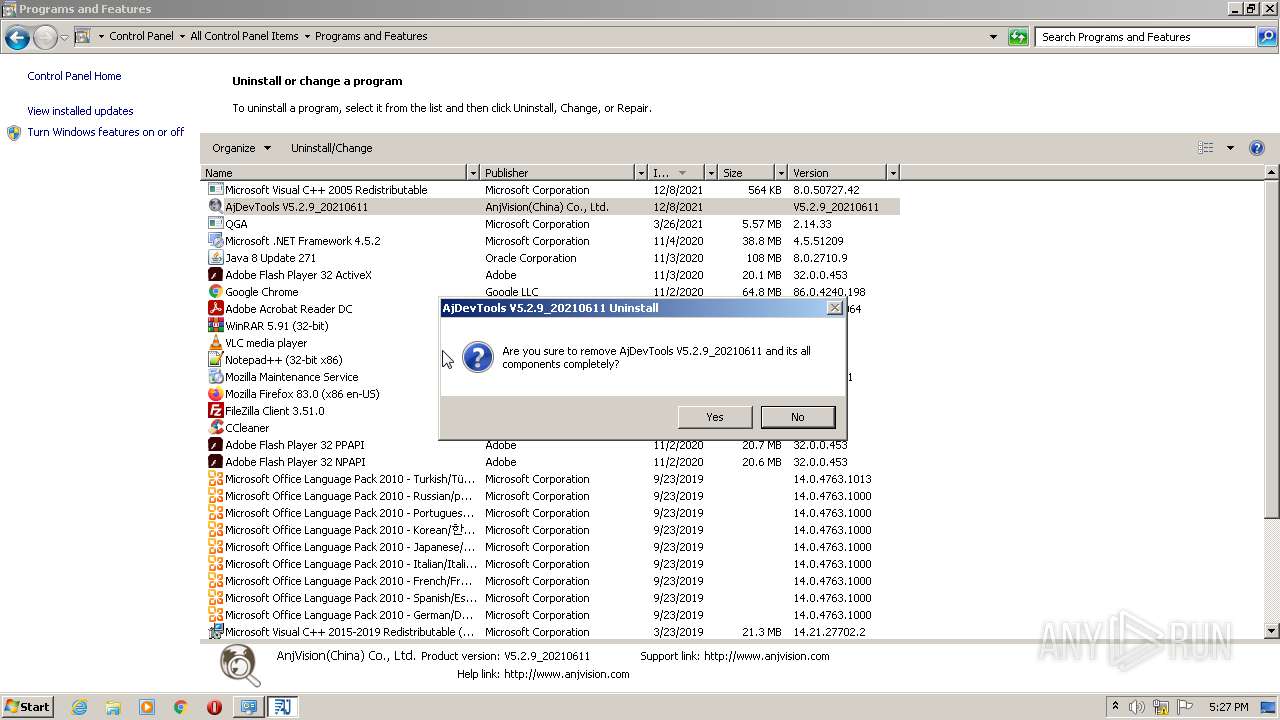
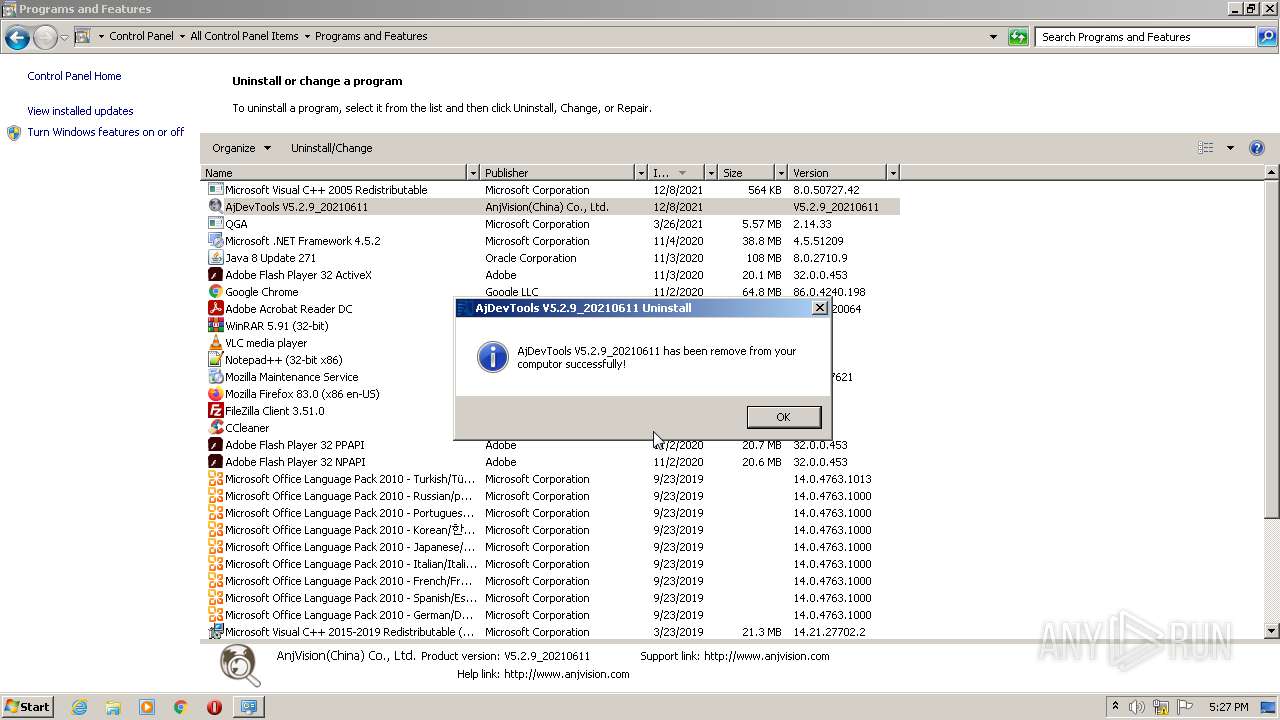
Creates a software uninstall entry
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
- msiexec.exe (PID: 1328)
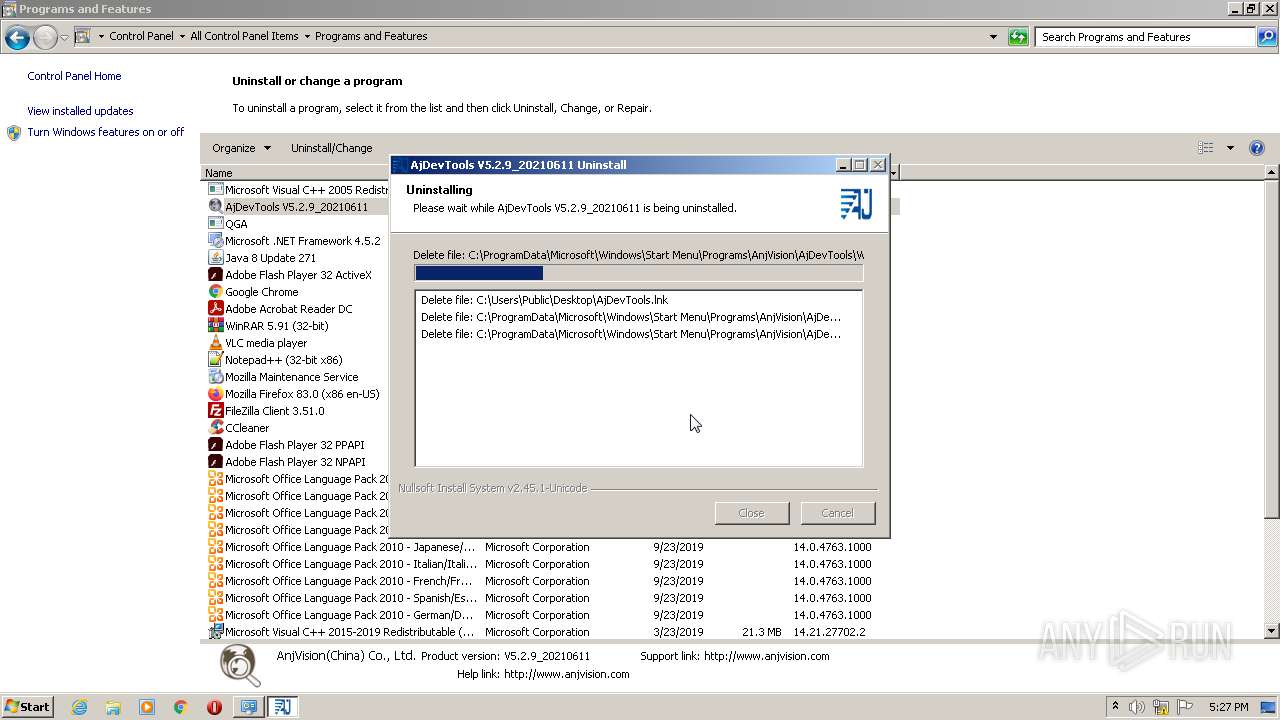
Removes files from Windows directory
- msiexec.exe (PID: 1328)
Executed via COM
- DllHost.exe (PID: 3604)
Starts itself from another location
- uninst.exe (PID: 4080)
Creates files in the Windows directory
- msiexec.exe (PID: 1328)
INFO
Checks supported languages
- taskkill.exe (PID: 3268)
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 1328)
- vssvc.exe (PID: 2324)
- MsiExec.exe (PID: 1120)
- DllHost.exe (PID: 3604)
Reads the computer name
- taskkill.exe (PID: 3268)
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 1328)
- vssvc.exe (PID: 2324)
- MsiExec.exe (PID: 1120)
- DllHost.exe (PID: 3604)
Dropped object may contain Bitcoin addresses
- AjDevTools_V5.2.9_20210611.exe (PID: 1172)
Checks Windows Trust Settings
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 1328)
Reads settings of System Certificates
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 1328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5 |
| ImageVersion: | 6.1 |
| OSVersion: | 5 |
| EntryPoint: | 0x33e9 |
| UninitializedDataSize: | 16896 |
| InitializedDataSize: | 431104 |
| CodeSize: | 25600 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2009:09:09 15:23:14+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Sep-2009 13:23:14 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Sep-2009 13:23:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006240 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42174 |
.rdata | 0x00008000 | 0x000018CA | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.87837 |
.data | 0x0000A000 | 0x0006667C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.35872 |
.ndata | 0x00071000 | 0x0008D000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000FE000 | 0x00023FF8 | 0x00024000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.65183 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21649 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.96461 | 38056 | UNKNOWN | English - United States | RT_ICON |
3 | 5.38193 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 5.78609 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 6.09952 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 6.21657 | 2440 | UNKNOWN | English - United States | RT_ICON |
7 | 6.16697 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 3.0112 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
57
Monitored processes
12
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Users\admin\AppData\Local\Temp\vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\vcredist_x86.exe | AjDevTools_V5.2.9_20210611.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IExpress Setup Exit code: 0 Version: 2.0.50727.42 Modules
| |||||||||||||||
| 1120 | C:\Windows\system32\MsiExec.exe -Embedding E1C9A4C1CED7DEC054BADD8EDC31A823 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
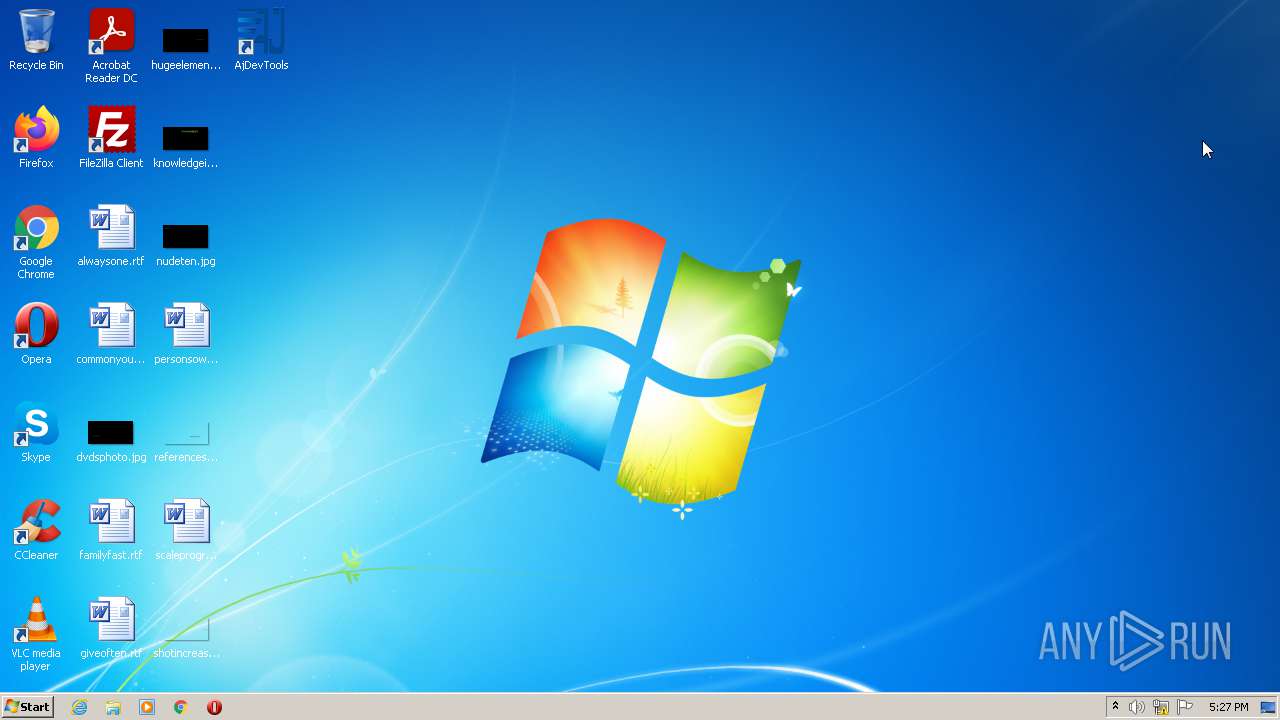
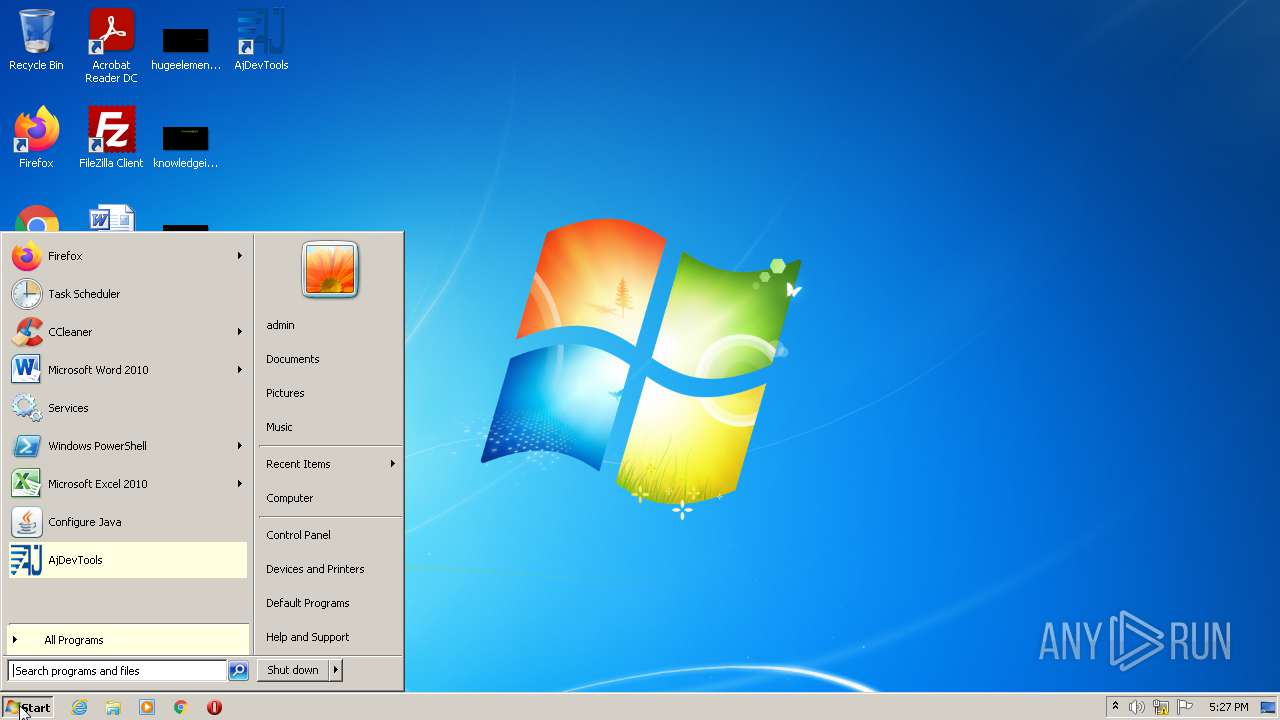
| 1172 | "C:\Users\admin\AppData\Local\Temp\AjDevTools_V5.2.9_20210611.exe" | C:\Users\admin\AppData\Local\Temp\AjDevTools_V5.2.9_20210611.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1328 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2324 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | msiexec /i vcredist.msi | C:\Windows\system32\msiexec.exe | — | vcredist_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3268 | "C:\Windows\system32\taskkill.exe" /F /IM AjDevTools.exe /T | C:\Windows\system32\taskkill.exe | — | AjDevTools_V5.2.9_20210611.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Au_.exe" _?=C:\Program Files\AnjVision\AjDevTools\ | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Au_.exe | — | uninst.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3604 | C:\Windows\system32\DllHost.exe /Processid:{FCC74B77-EC3E-4DD8-A80B-008A702075A9} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
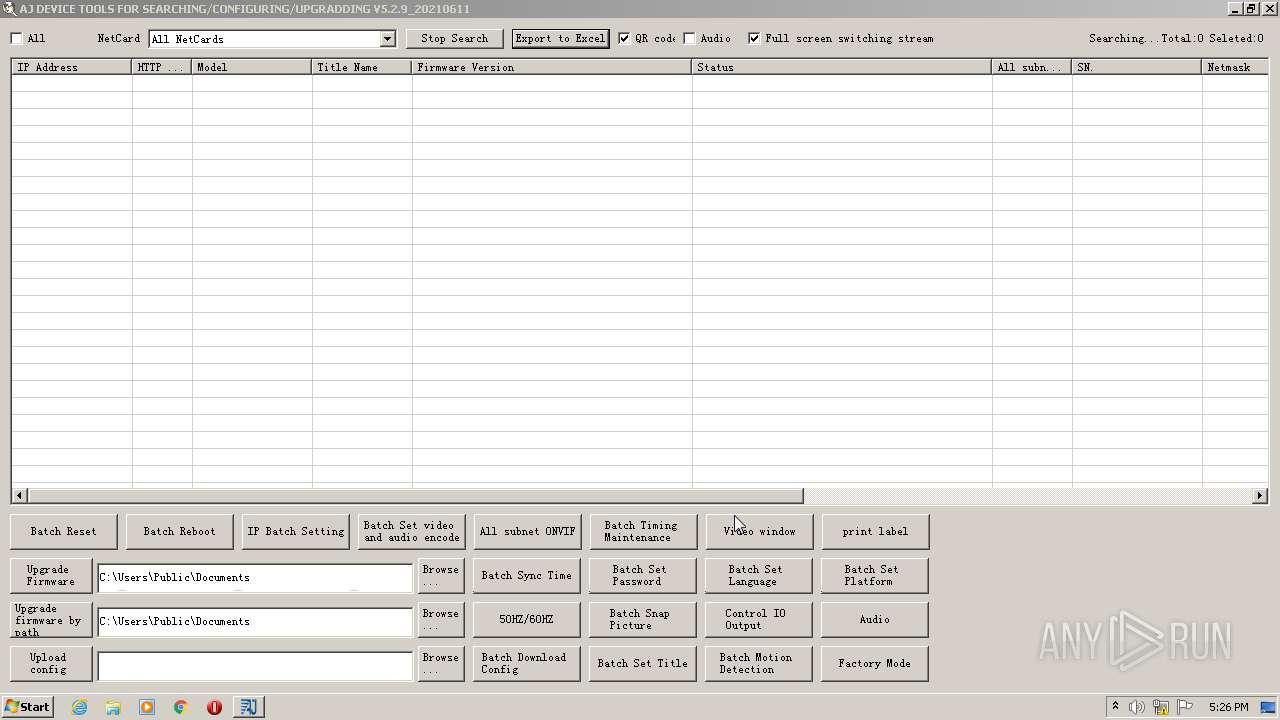
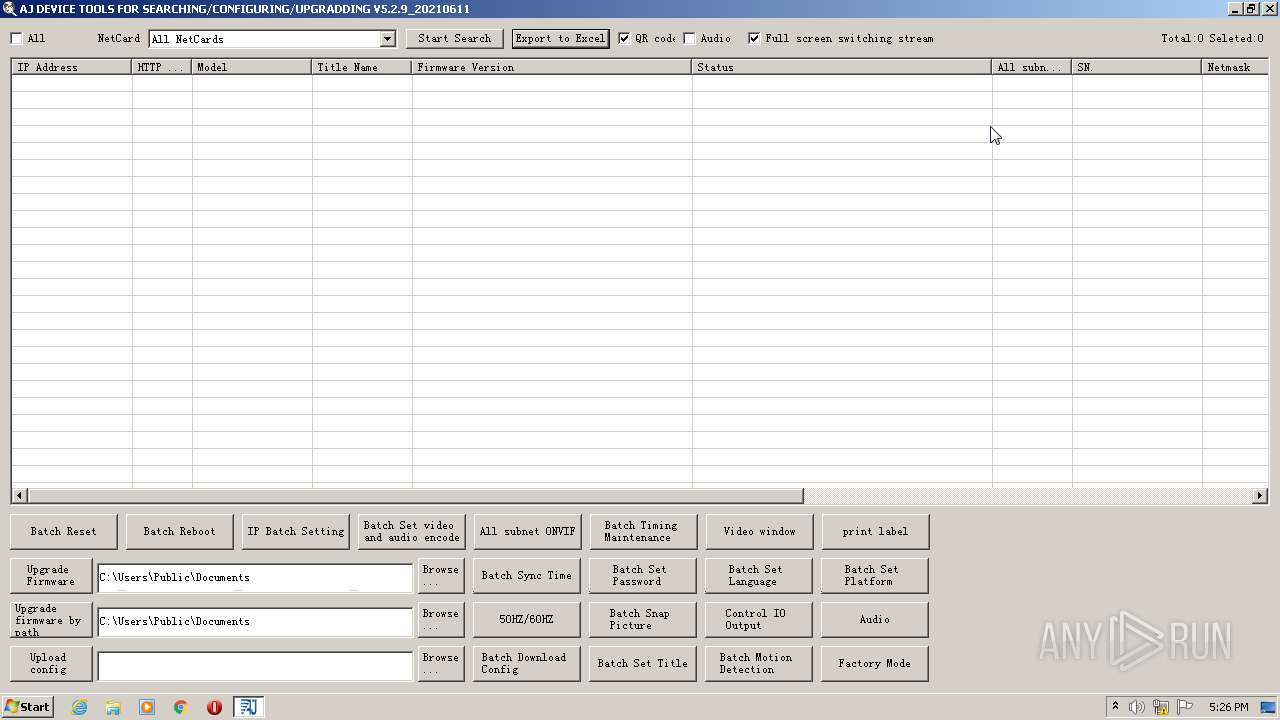
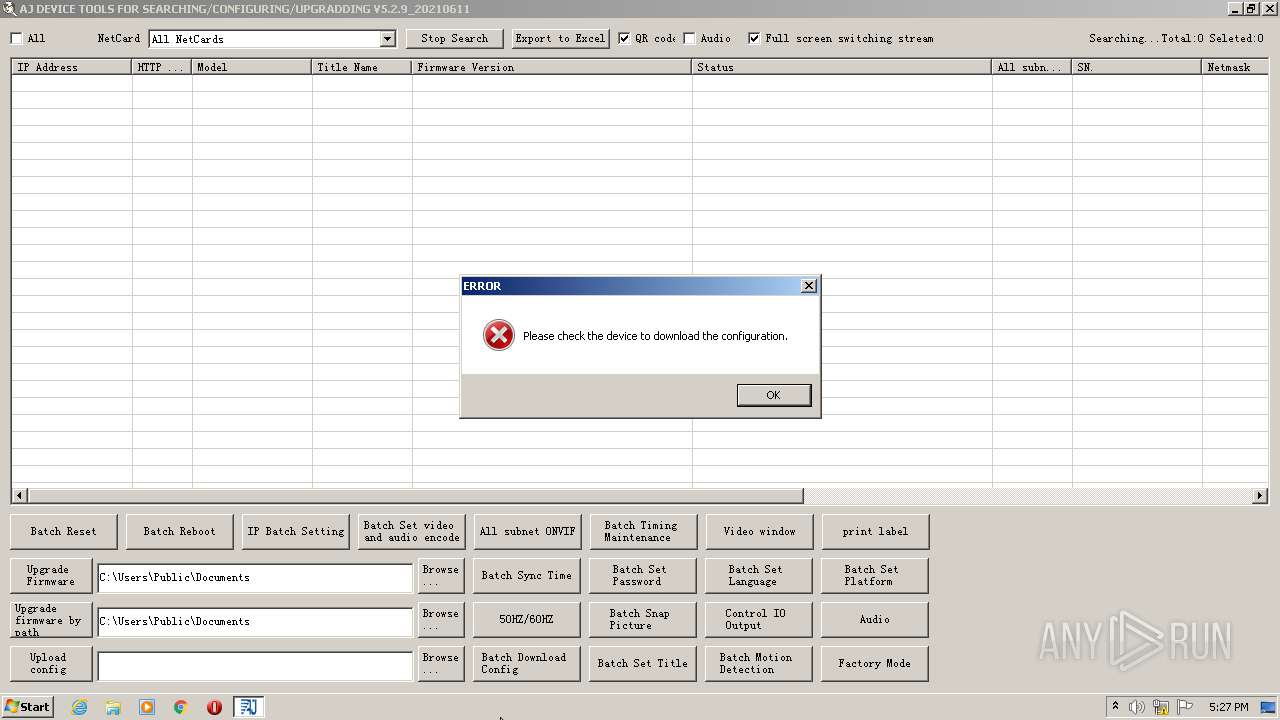
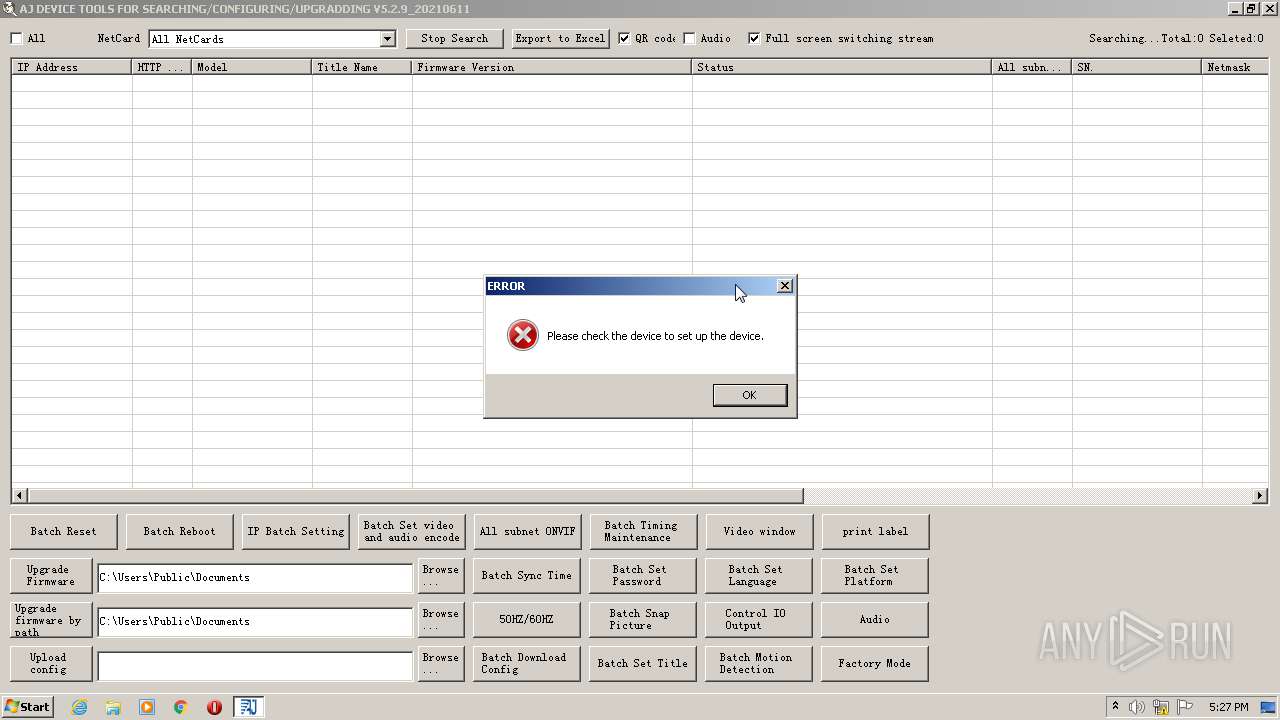
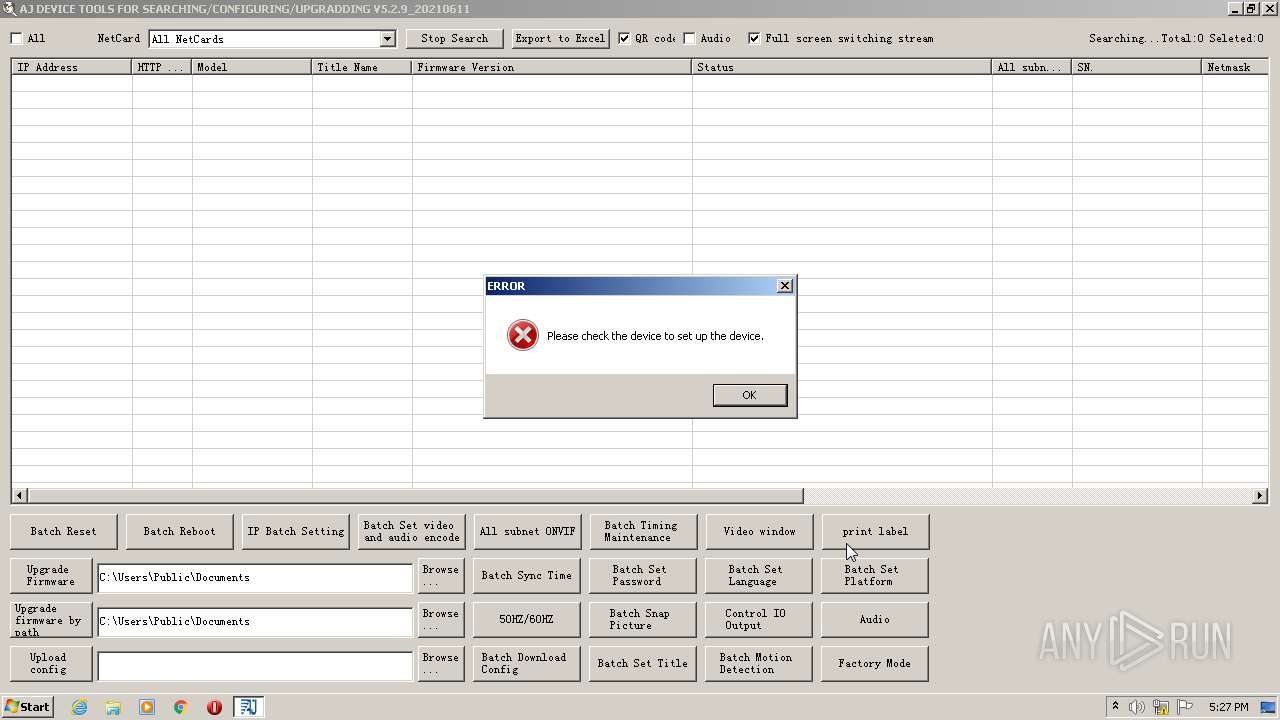
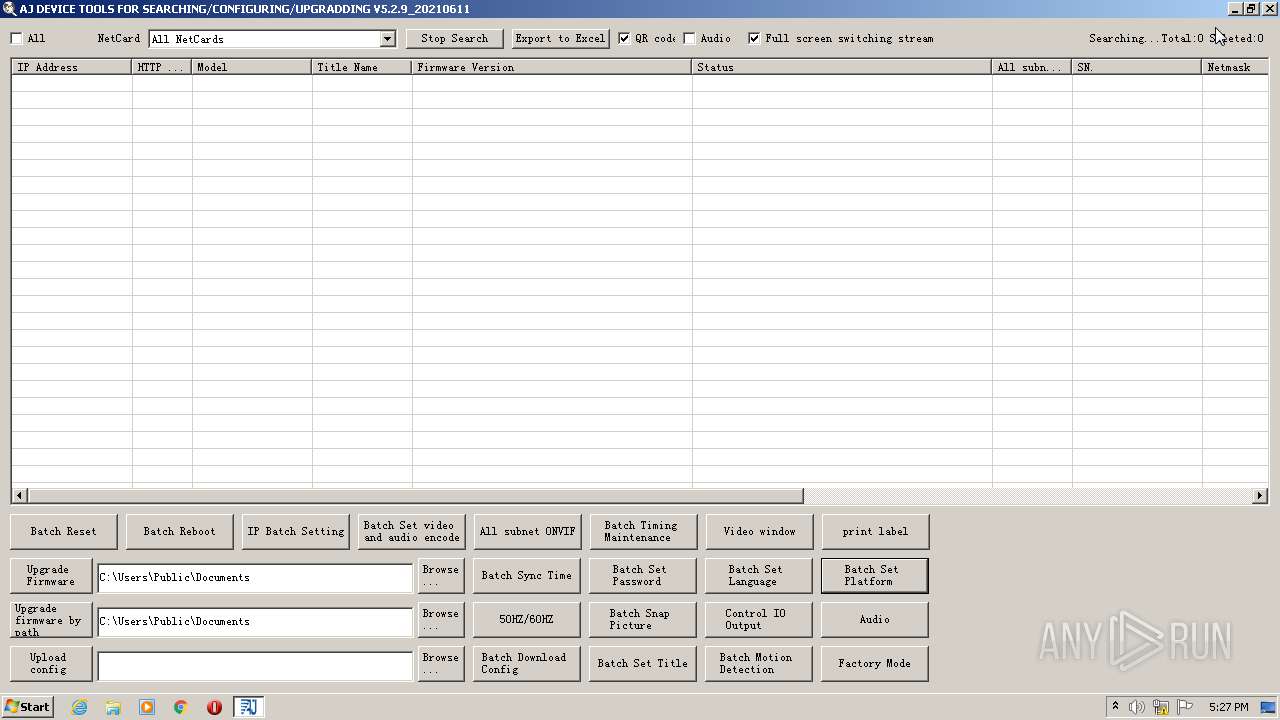
| 3732 | "C:\Program Files\AnjVision\AjDevTools\AjDevTools.exe" | C:\Program Files\AnjVision\AjDevTools\AjDevTools.exe | AjDevTools_V5.2.9_20210611.exe | ||||||||||||
User: admin Company: AnjVision Integrity Level: HIGH Description: IPC searching and upgrading tools Exit code: 3221225547 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
10 952
Read events
10 597
Write events
339
Delete events
16
Modification events
| (PID) Process: | (352) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (2420) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1328) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000F051ABA358ECD70130050000DC0B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1328) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000F051ABA358ECD70130050000DC0B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1328) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (1328) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000D0C21DA458ECD70130050000DC0B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1328) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D0C21DA458ECD7013005000048010000E80300000100000000000000000000006D6545E102CCC74B9D9CF10388F5EEA80000000000000000 | |||
| (PID) Process: | (2324) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000384C27A458ECD701140900002C0D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2324) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000384C27A458ECD70114090000F00E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2324) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000384C27A458ECD70114090000E00E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
47
Suspicious files
8
Text files
28
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
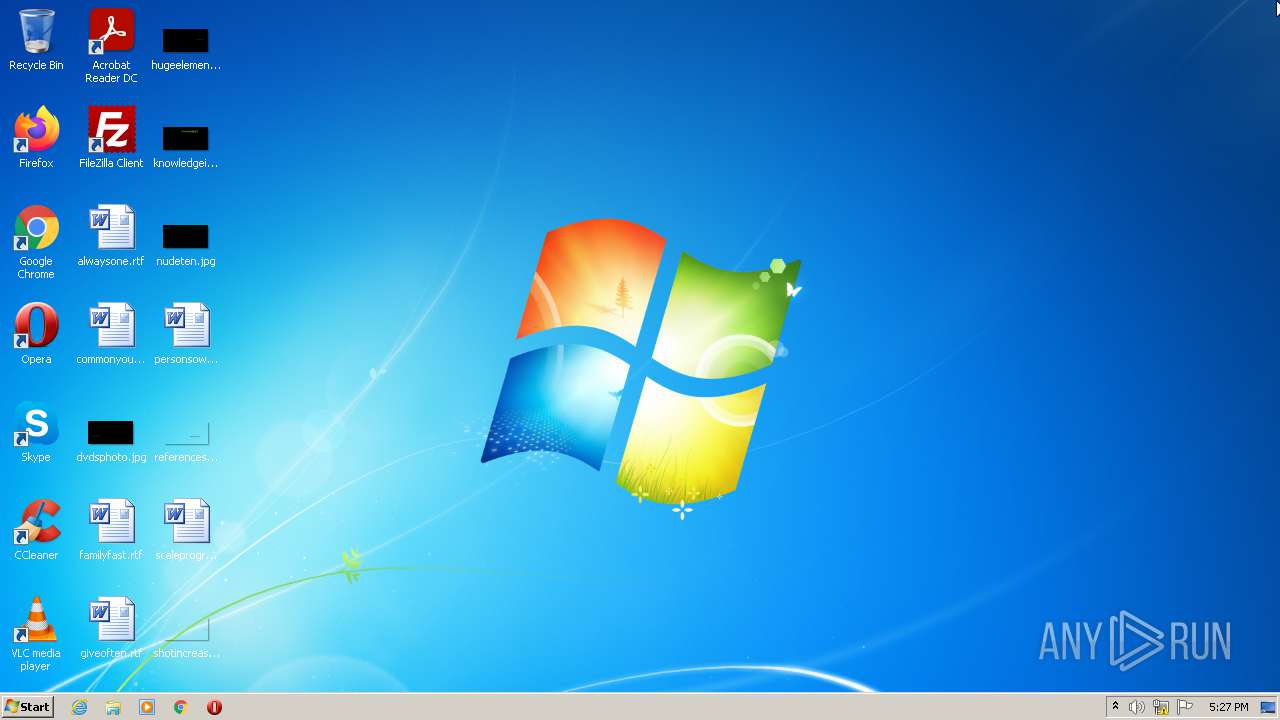
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Program Files\AnjVision\AjDevTools\AjDevTools.exe | executable | |
MD5:— | SHA256:— | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Users\admin\AppData\Local\Temp\nsv6A60.tmp\LangDLL.dll | executable | |
MD5:8E806EA2E205DC508A2FB5ADDA3419DB | SHA256:86A55734B8802051BBBD0E8C9C506D0CA985BC5C99113E99B309469046133937 | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Users\admin\AppData\Local\Temp\nsv6A60.tmp\ioSpecial.ini | text | |
MD5:6F98FCDA445825382121E480A64AE24C | SHA256:689A67B30946CBE12DCE92D17207EC0488E850A806BE608E6FB174F853F86B57 | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Program Files\AnjVision\AjDevTools\logo_t.ico | image | |
MD5:— | SHA256:— | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Program Files\AnjVision\AjDevTools\logo.ico | image | |
MD5:— | SHA256:— | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Program Files\AnjVision\AjDevTools\display.xml | html | |
MD5:— | SHA256:— | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Program Files\AnjVision\AjDevTools\language.xml | xml | |
MD5:— | SHA256:— | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Program Files\AnjVision\AjDevTools\language_en-us.xml | xml | |
MD5:— | SHA256:— | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Program Files\AnjVision\AjDevTools\AjRtspClientLib.dll | executable | |
MD5:— | SHA256:— | |||
| 1172 | AjDevTools_V5.2.9_20210611.exe | C:\Program Files\AnjVision\AjDevTools\AjDevTools.ico | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report