| File name: | explore.vbs |
| Full analysis: | https://app.any.run/tasks/bc3a333e-5a9d-4919-ac9c-49c0ec1f0d67 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2019, 08:51:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 747EC7879635F0B71D7E339067F209C8 |
| SHA1: | AA5336BC93D5A19F30D831A560D086996EE80892 |
| SHA256: | 53258E070A4ED1A219C6623766103064E95E7871912DF03677AAAFC5451F2018 |
| SSDEEP: | 768:x4tMa8aN1+rvy2pGeLYwvAWd3ygz/Y/lxnxslm8treFl:6lFNeHpTvrdCD/vnxslT4 |
MALICIOUS
Changes the autorun value in the registry
- WScript.exe (PID: 2924)
- svchost.exe (PID: 3044)
Application was dropped or rewritten from another process
- WScript.exe (PID: 2924)
- svchost.exe (PID: 3044)
Writes to a start menu file
- WScript.exe (PID: 2924)
- svchost.exe (PID: 3044)
SUSPICIOUS
Creates executable files which already exist in Windows
- WScript.exe (PID: 2924)
Starts itself from another location
- WScript.exe (PID: 2924)
Creates files in the user directory
- WScript.exe (PID: 2924)
Executable content was dropped or overwritten
- WScript.exe (PID: 2924)
INFO
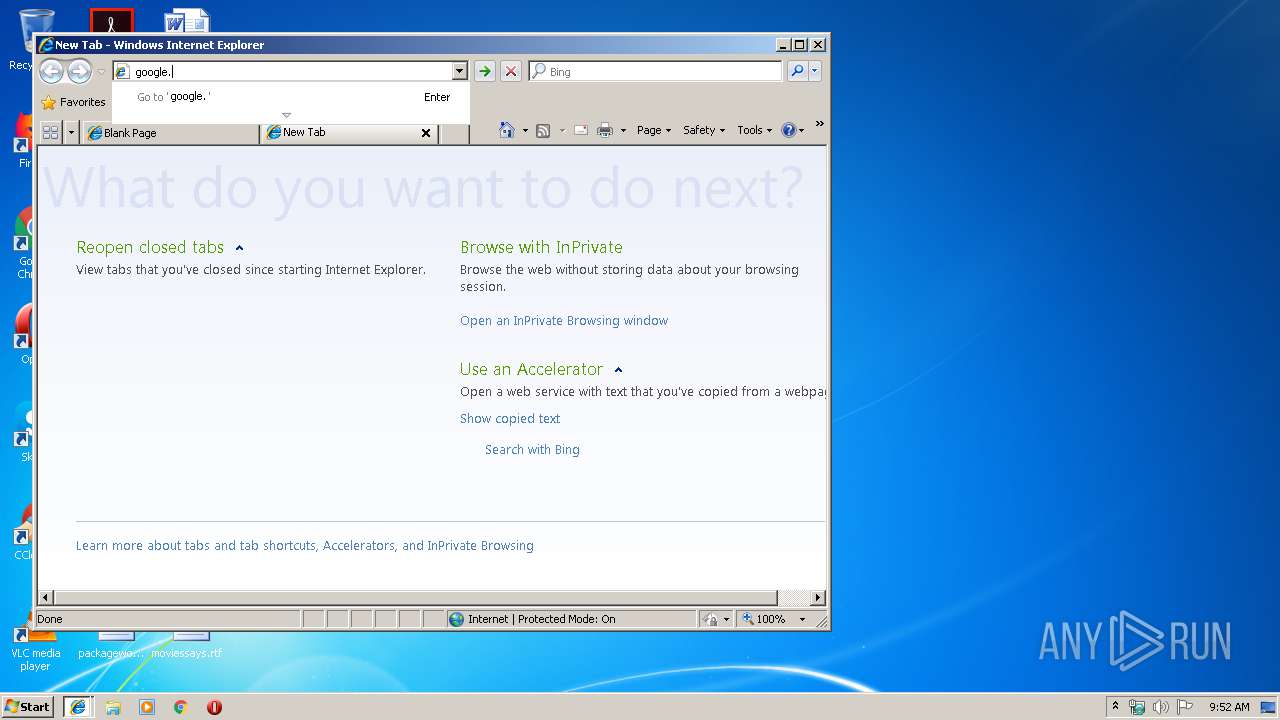
Reads internet explorer settings
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 2864)
Manual execution by user
- iexplore.exe (PID: 4052)
- explorer.exe (PID: 2164)
Application launched itself
- iexplore.exe (PID: 4052)
Changes internet zones settings
- iexplore.exe (PID: 4052)
Reads Internet Cache Settings
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 4052)
Reads settings of System Certificates
- iexplore.exe (PID: 4052)
Creates files in the user directory
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2164 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4052 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4052 CREDAT:6403 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2924 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\explore.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3044 | "C:\Users\admin\AppData\Local\Temp\eco\svchost.exe" //B "C:\Users\admin\AppData\Local\Temp\eco\explore.vbs" | C:\Users\admin\AppData\Local\Temp\eco\svchost.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 160
Read events
1 024
Write events
133
Delete events
3
Modification events
| (PID) Process: | (2924) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\explore |
| Operation: | write | Name: | |
Value: false - 9/3/2019 | |||
| (PID) Process: | (2924) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | explore |
Value: C:\Users\admin\AppData\Local\Temp\eco\svchost.exe //B "C:\Users\admin\AppData\Local\Temp\eco\explore.vbs" | |||
| (PID) Process: | (2924) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | explore |
Value: C:\Users\admin\AppData\Local\Temp\eco\svchost.exe //B "C:\Users\admin\AppData\Local\Temp\eco\explore.vbs" | |||
| (PID) Process: | (2924) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2924) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3044) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | explore |
Value: C:\Users\admin\AppData\Local\Temp\eco\svchost.exe //B "C:\Users\admin\AppData\Local\Temp\eco\explore.vbs" | |||
| (PID) Process: | (3044) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | explore |
Value: C:\Users\admin\AppData\Local\Temp\eco\svchost.exe //B "C:\Users\admin\AppData\Local\Temp\eco\explore.vbs" | |||
| (PID) Process: | (3044) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3044) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3044) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
9
Text files
27
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 2924 | WScript.exe | C:\Users\admin\AppData\Local\Temp\eco\explore.vbs | binary | |
MD5:— | SHA256:— | |||
| 3044 | svchost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\explore.vbs | binary | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\90M7YBYW\google_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2924 | WScript.exe | C:\Users\admin\AppData\Local\Temp\eco\svchost.exe | executable | |
MD5:D1AB72DB2BEDD2F255D35DA3DA0D4B16 | SHA256:047F3C5A7AB0EA05F35B2CA8037BF62DD4228786D07707064DBD0D46569305D0 | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
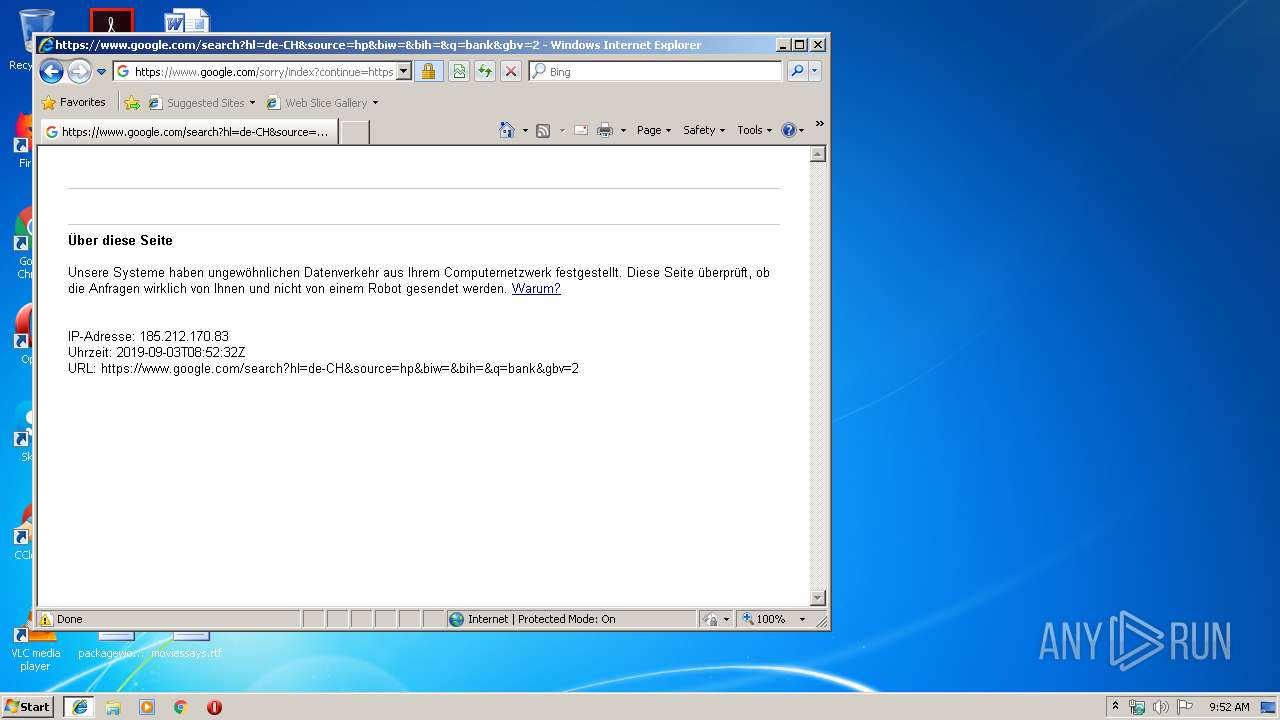
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
5
Threats
1
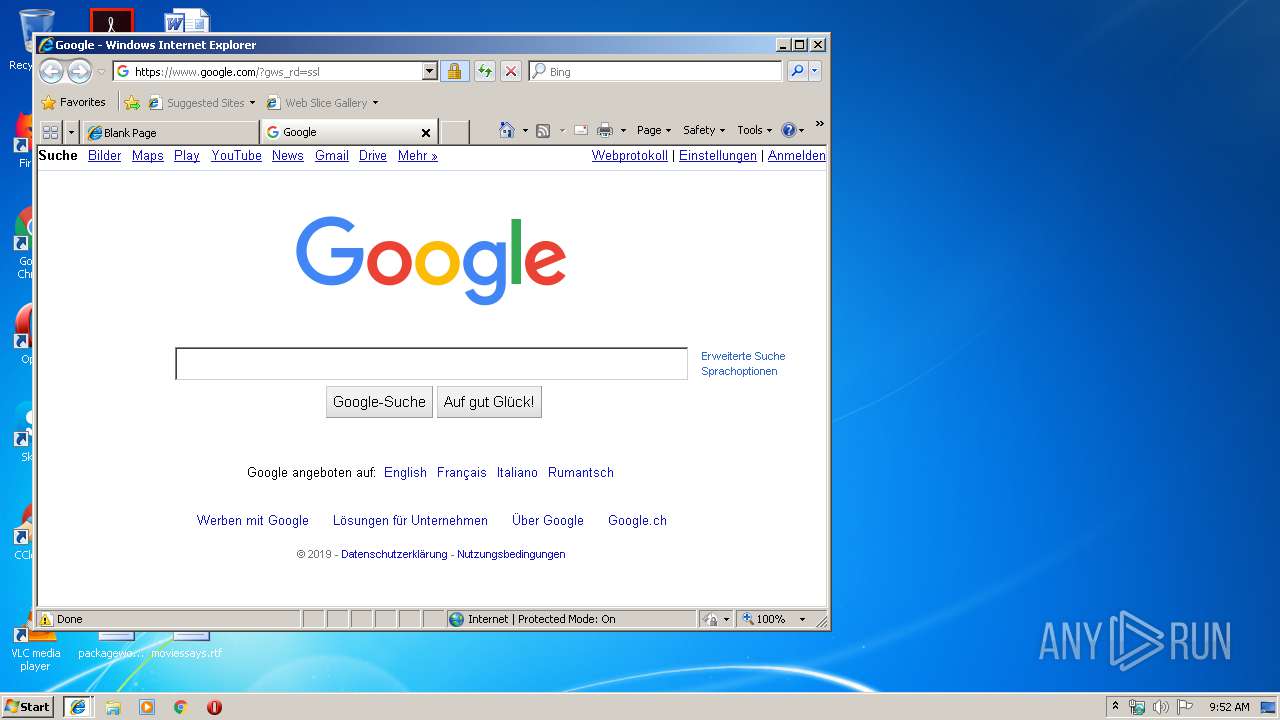
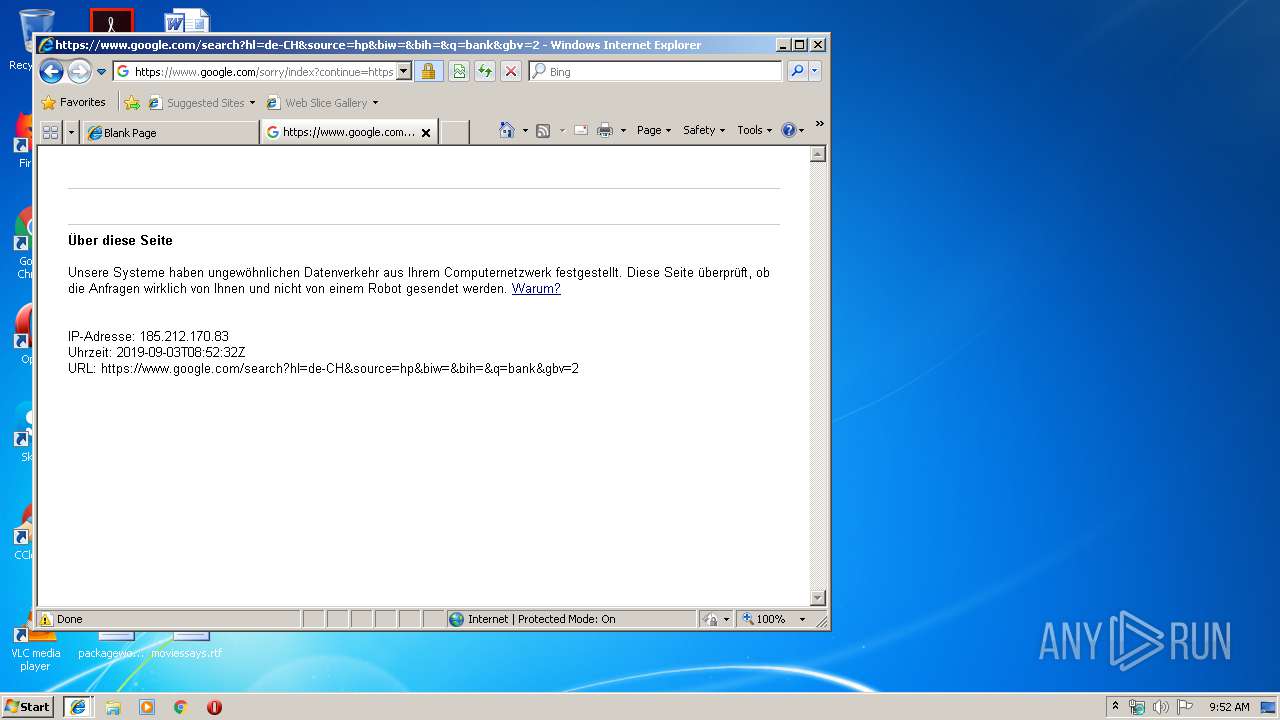
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2864 | iexplore.exe | GET | 302 | 172.217.18.164:80 | http://www.google.com/ | US | html | 231 b | malicious |
4052 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2864 | iexplore.exe | GET | 301 | 172.217.23.142:80 | http://google.com/ | US | html | 219 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3044 | svchost.exe | 141.255.146.151:1183 | sexycam.myq-see.com | Lost Oasis SARL | NL | unknown |
4052 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2864 | iexplore.exe | 172.217.23.142:80 | google.com | Google Inc. | US | whitelisted |
2864 | iexplore.exe | 172.217.18.164:80 | www.google.com | Google Inc. | US | whitelisted |
4052 | iexplore.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2864 | iexplore.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2864 | iexplore.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sexycam.myq-see.com |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| malicious |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potential Corporate Privacy Violation | ET INFO Observed DNS Query to .myq-see .com DDNS Domain |