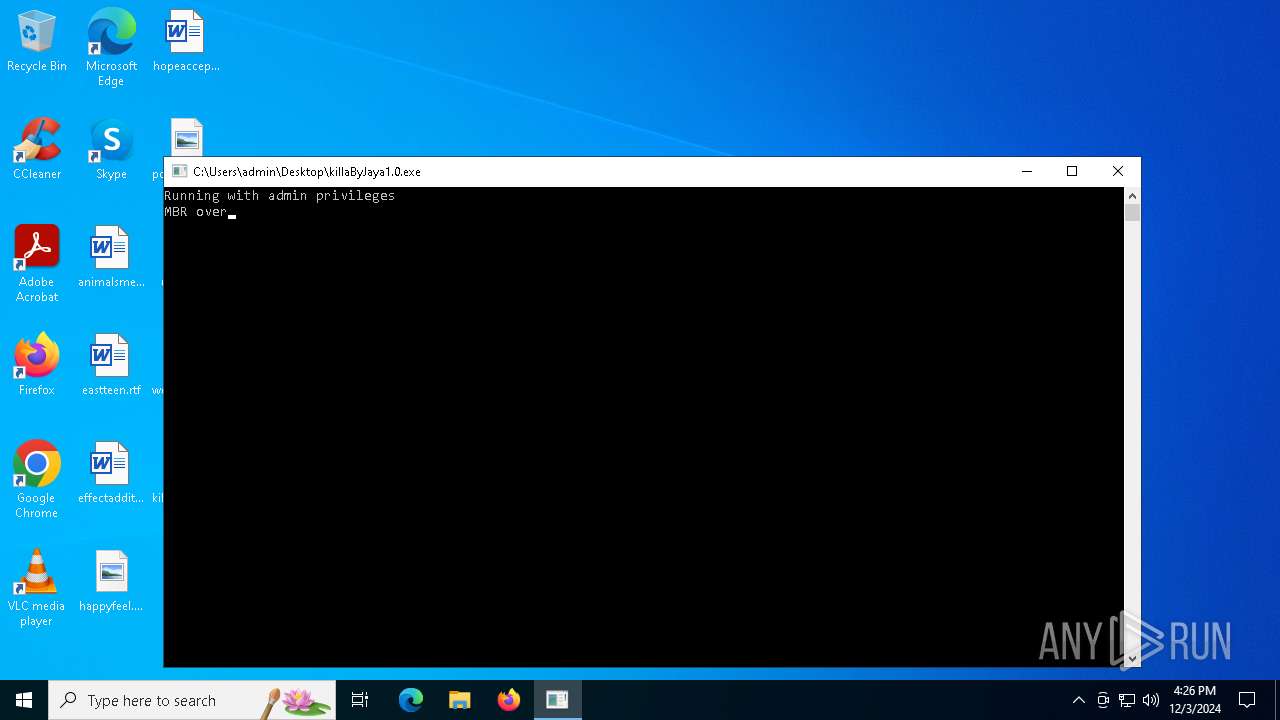
| File name: | killaByJaya1.0.exe |
| Full analysis: | https://app.any.run/tasks/79d2abf3-5e03-4b54-b9d7-764d9d4616bf |
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2024, 16:26:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 19 sections |
| MD5: | 1AA4E7F082AEA885328508C6DEE744FF |
| SHA1: | 42E824B9827CC6195414DF4FC32CB439B7D17AC9 |
| SHA256: | 53195A269FF58EF0036CB110CB96EA79309F8148B7F8D42FECACC5B23C4BD375 |
| SSDEEP: | 3072:n/m72twszoXdf3Dj5LsVEhvNPcadnz9PkSf8FxWLU0tW1CCb/LatQ8h29l:n/ngseVc6nz9ci8/MI9l |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- killaByJaya1.0.exe (PID: 6032)
Reads the date of Windows installation
- killaByJaya1.0.exe (PID: 6032)
Application launched itself
- killaByJaya1.0.exe (PID: 6032)
Starts CMD.EXE for commands execution
- killaByJaya1.0.exe (PID: 4684)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3848)
Starts SC.EXE for service management
- cmd.exe (PID: 1744)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 1668)
- cmd.exe (PID: 1480)
- cmd.exe (PID: 3732)
- cmd.exe (PID: 5496)
- cmd.exe (PID: 5564)
- cmd.exe (PID: 5640)
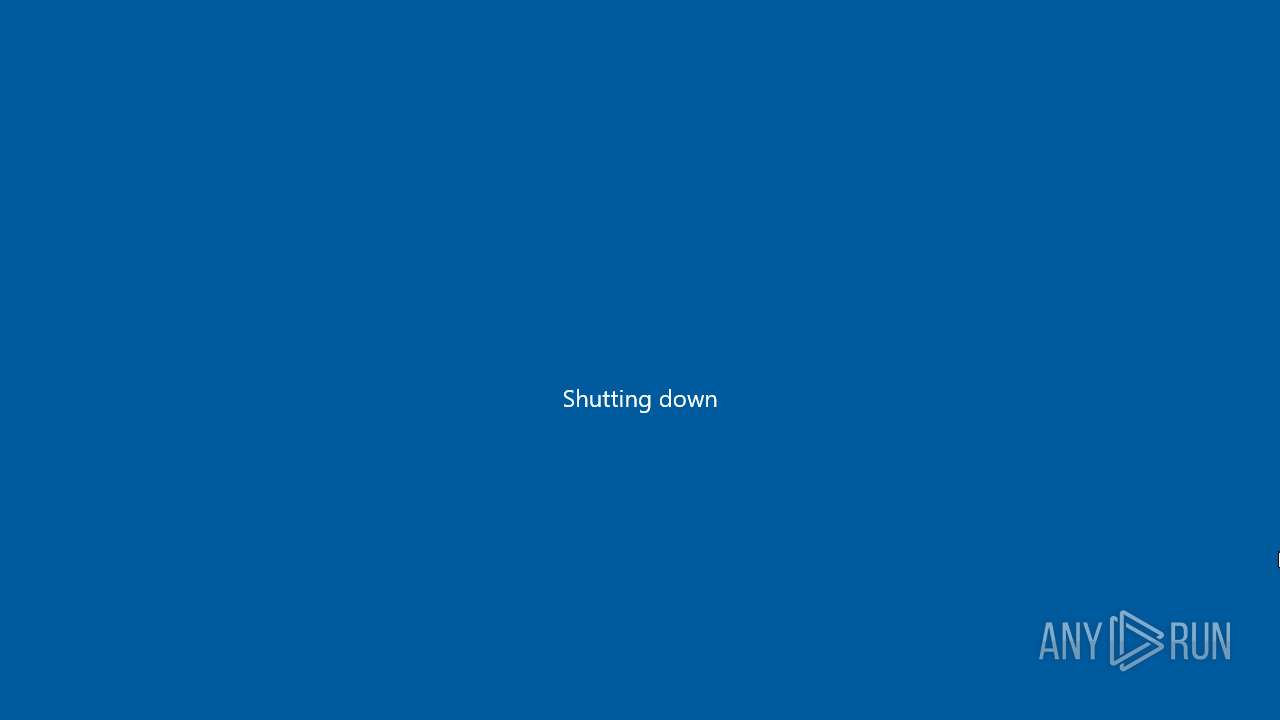
The system shut down or reboot
- cmd.exe (PID: 5968)
INFO
Reads the computer name
- killaByJaya1.0.exe (PID: 6032)
Process checks computer location settings
- killaByJaya1.0.exe (PID: 6032)
Checks supported languages
- killaByJaya1.0.exe (PID: 6032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:12:03 16:12:08+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.4 |
| CodeSize: | 30208 |
| InitializedDataSize: | 43008 |
| UninitializedDataSize: | 3072 |
| EntryPoint: | 0x14d0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
142
Monitored processes
24
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1480 | C:\WINDOWS\system32\cmd.exe /c sc delete iastorV | C:\Windows\System32\cmd.exe | — | killaByJaya1.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1540 | sc delete msahci | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | C:\WINDOWS\system32\cmd.exe /c sc delete kbdclass | C:\Windows\System32\cmd.exe | — | killaByJaya1.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1744 | C:\WINDOWS\system32\cmd.exe /c sc delete \Device\Harddisk0\DR0 | C:\Windows\System32\cmd.exe | — | killaByJaya1.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 123 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | shutdown /s /f /t 0 | C:\Windows\System32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2756 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | killaByJaya1.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2828 | sc delete LanmanServer | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3508 | sc delete NetBt | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3732 | C:\WINDOWS\system32\cmd.exe /c sc delete msahci | C:\Windows\System32\cmd.exe | — | killaByJaya1.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3812 | sc delete Tcpip | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
927
Read events
545
Write events
0
Delete events
382
Modification events
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Arial (TrueType) |
Value: arial.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Arial Black (TrueType) |
Value: ariblk.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Arial Bold (TrueType) |
Value: arialbd.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Arial Bold Italic (TrueType) |
Value: arialbi.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Arial Italic (TrueType) |
Value: ariali.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Bahnschrift (TrueType) |
Value: bahnschrift.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Calibri (TrueType) |
Value: calibri.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Calibri Bold (TrueType) |
Value: calibrib.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Calibri Bold Italic (TrueType) |
Value: calibriz.ttf | |||
| (PID) Process: | (5536) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | delete value | Name: | Calibri Italic (TrueType) |
Value: calibrii.ttf | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4684 | killaByJaya1.0.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4536 | svchost.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4536 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4536 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.99:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4536 | svchost.exe | 2.16.164.99:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4536 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |