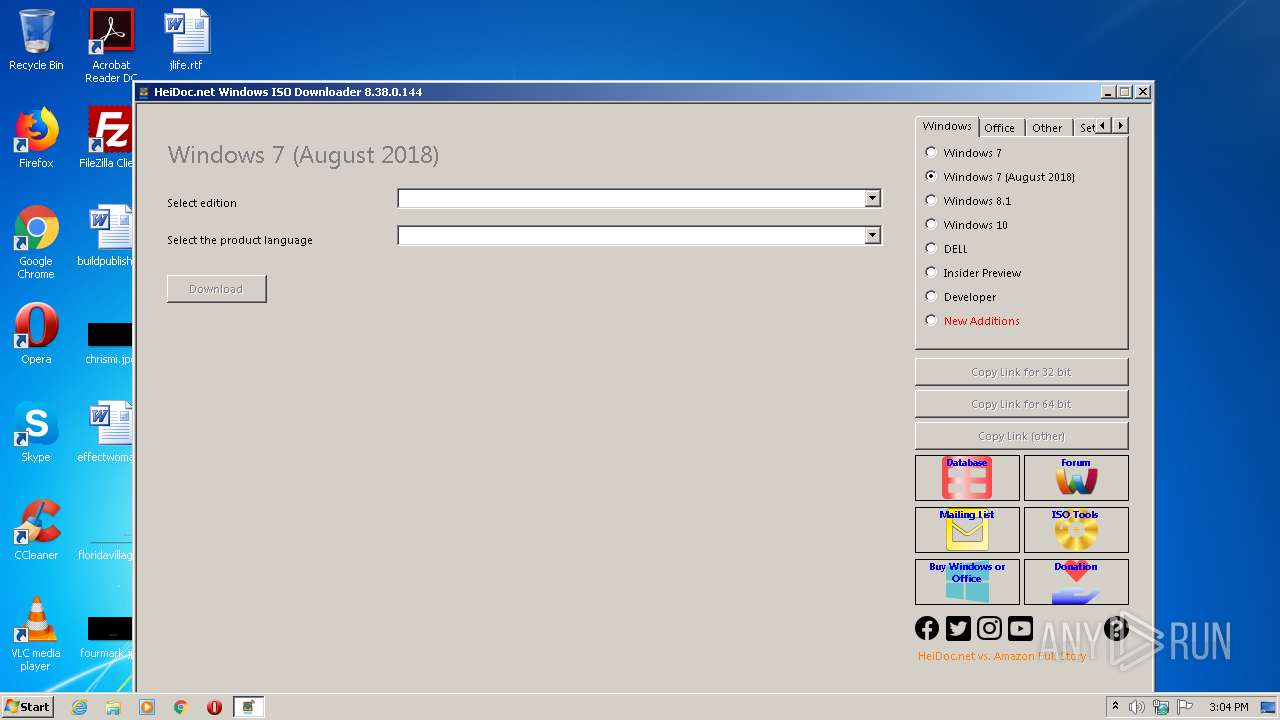
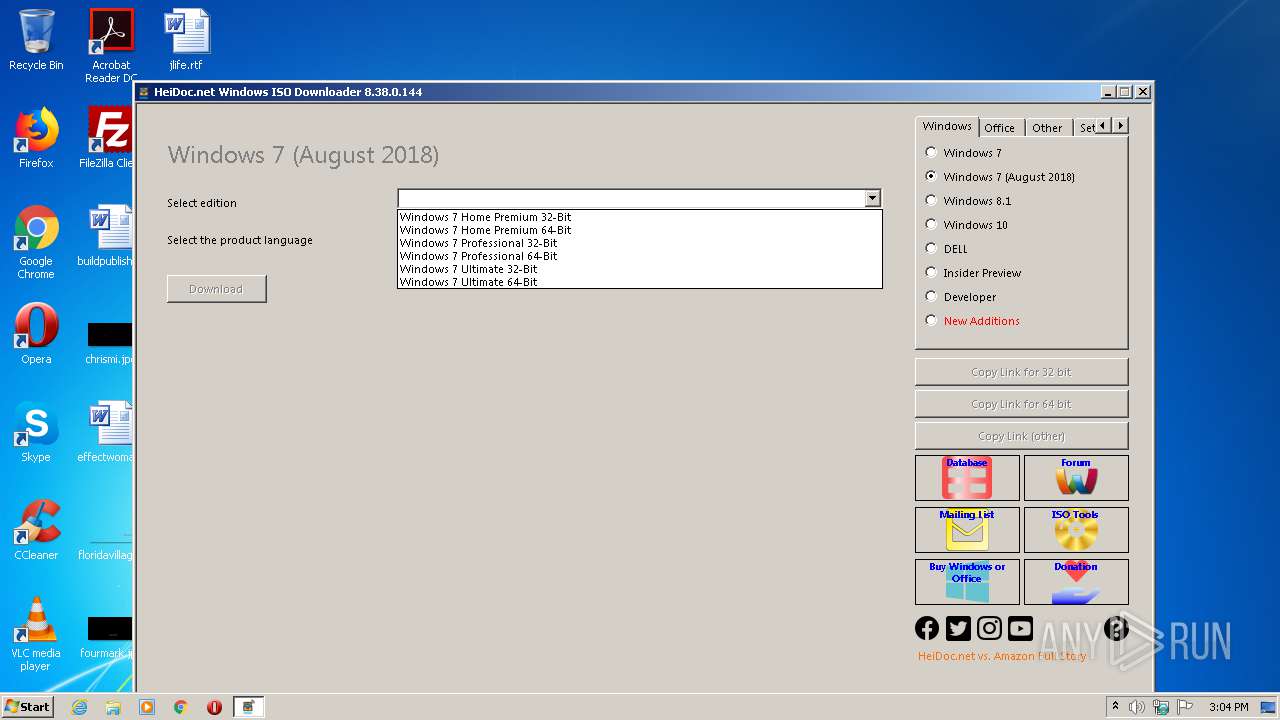
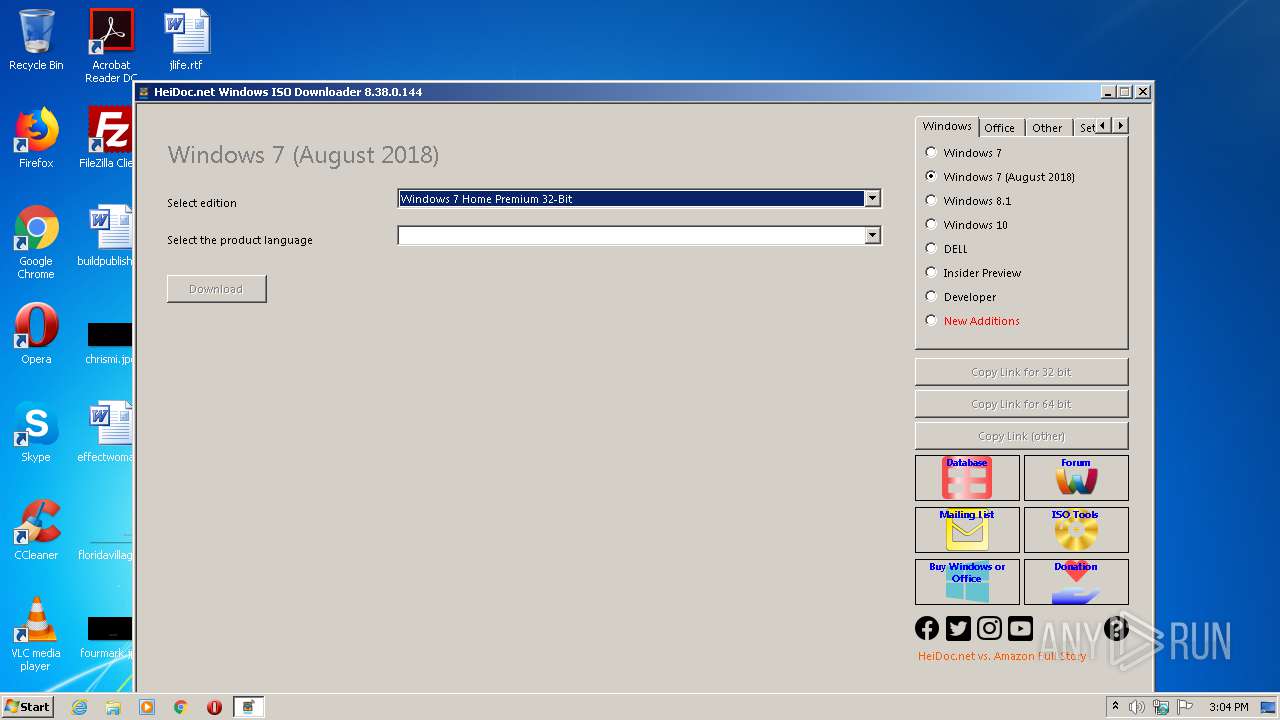
| File name: | Windows-ISO-Downloader.exe |
| Full analysis: | https://app.any.run/tasks/086a3934-6613-4ea3-8c91-d60652300cb3 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2020, 14:03:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 421AFBD29F46977BE567E7A2E6AE0A6C |
| SHA1: | B3A1A24BCC880CB93D029358FF4D02D3D0F3AF3F |
| SHA256: | 530346523D0860FAA2226709DE3815D8FAA3E4C33C4C8B39F8DC1C58A4CCF61B |
| SSDEEP: | 98304:uI68IzIRIRILgscFLWoDy9G32dm/RUFVHB/mQJkP4G:Y5syWoDy9GGOIlBewkP |
MALICIOUS
Changes settings of System certificates
- Windows-ISO-Downloader.exe (PID: 2624)
SUSPICIOUS
Adds / modifies Windows certificates
- Windows-ISO-Downloader.exe (PID: 2624)
Reads internet explorer settings
- Windows-ISO-Downloader.exe (PID: 2624)
Reads Internet Cache Settings
- Windows-ISO-Downloader.exe (PID: 2624)
Creates files in the user directory
- Windows-ISO-Downloader.exe (PID: 2624)
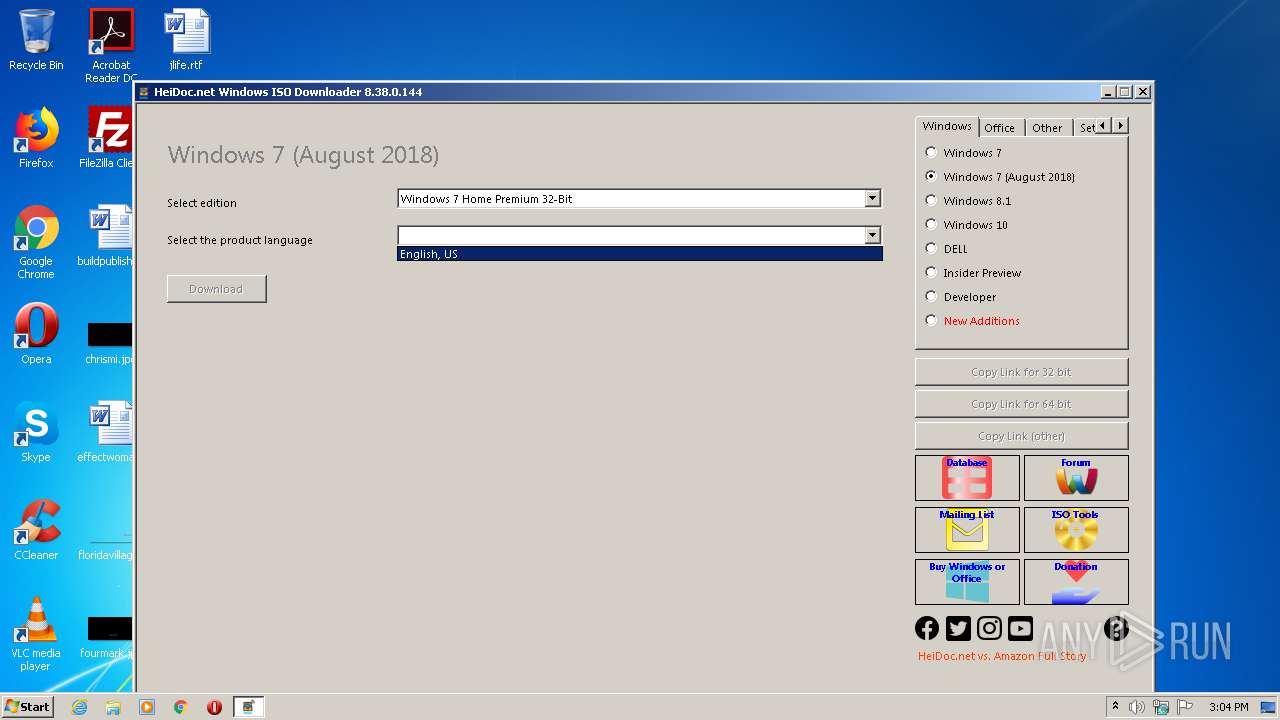
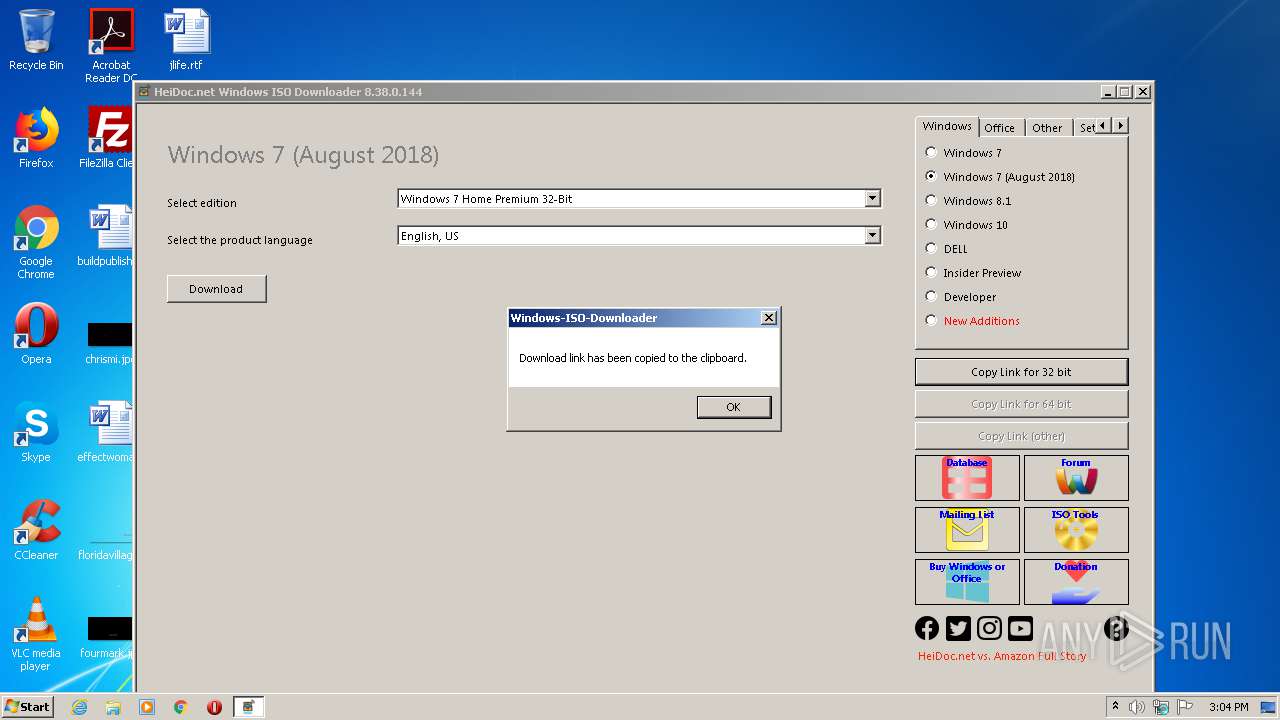
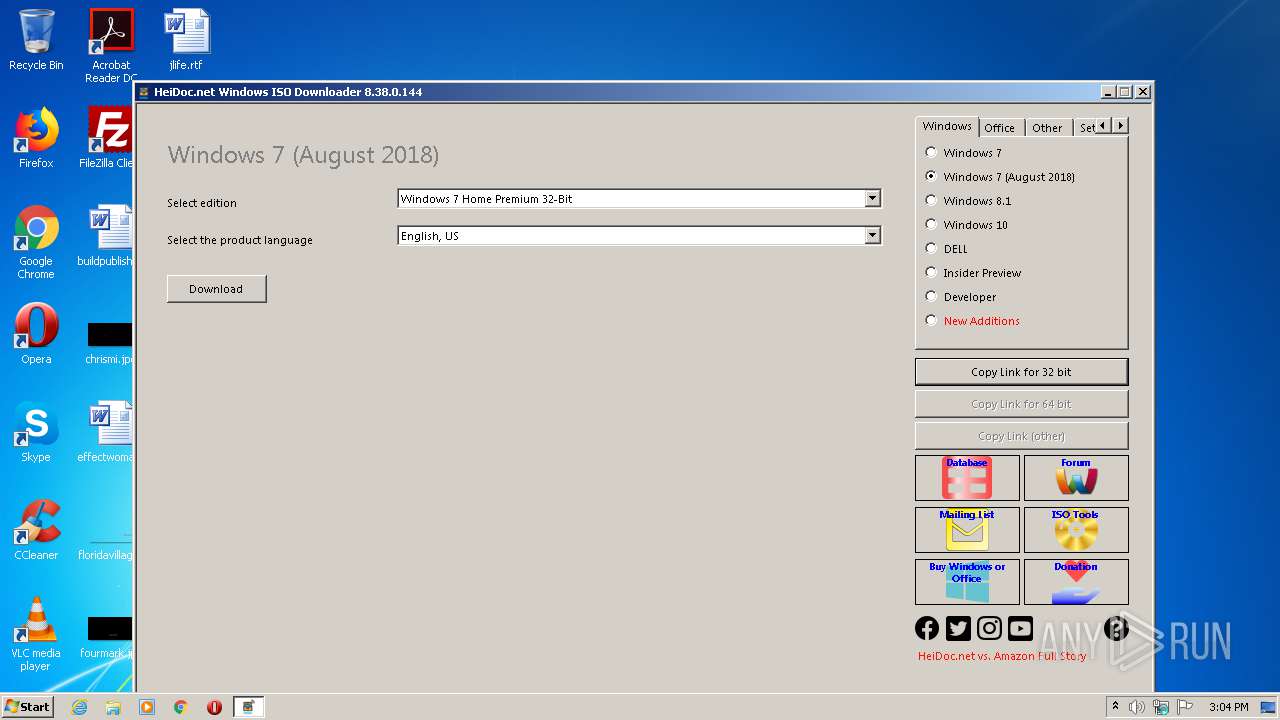
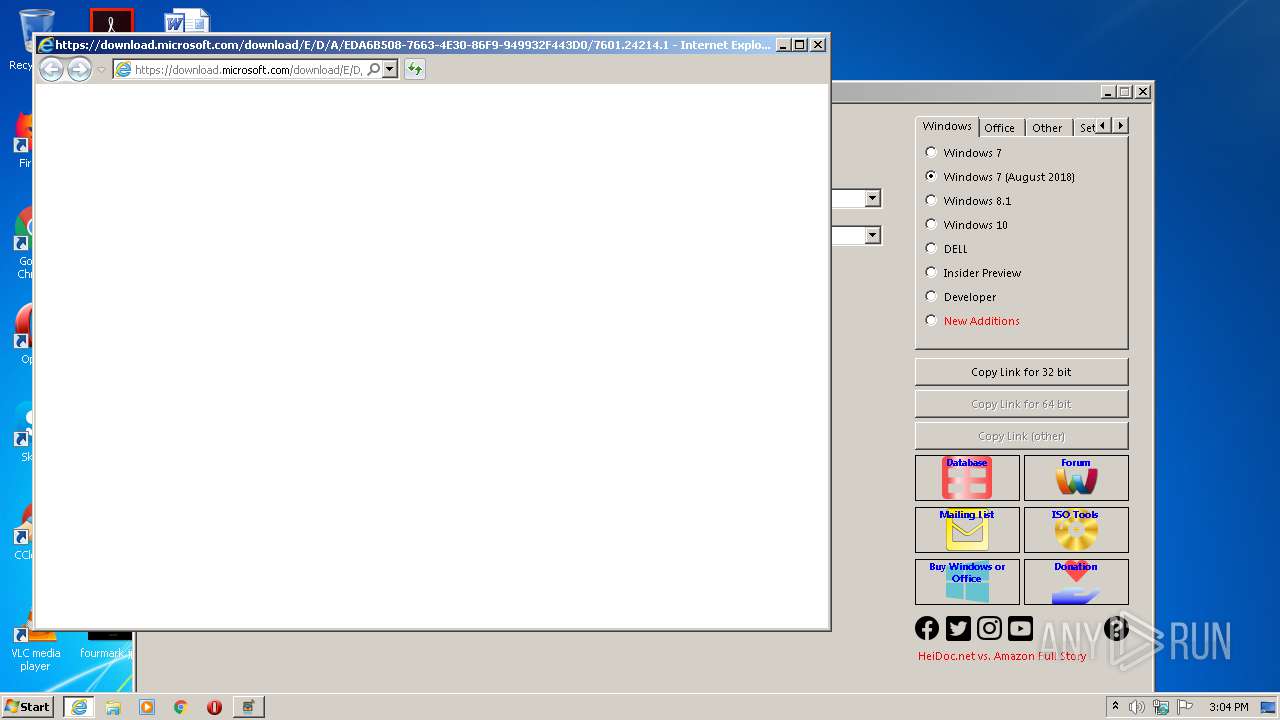
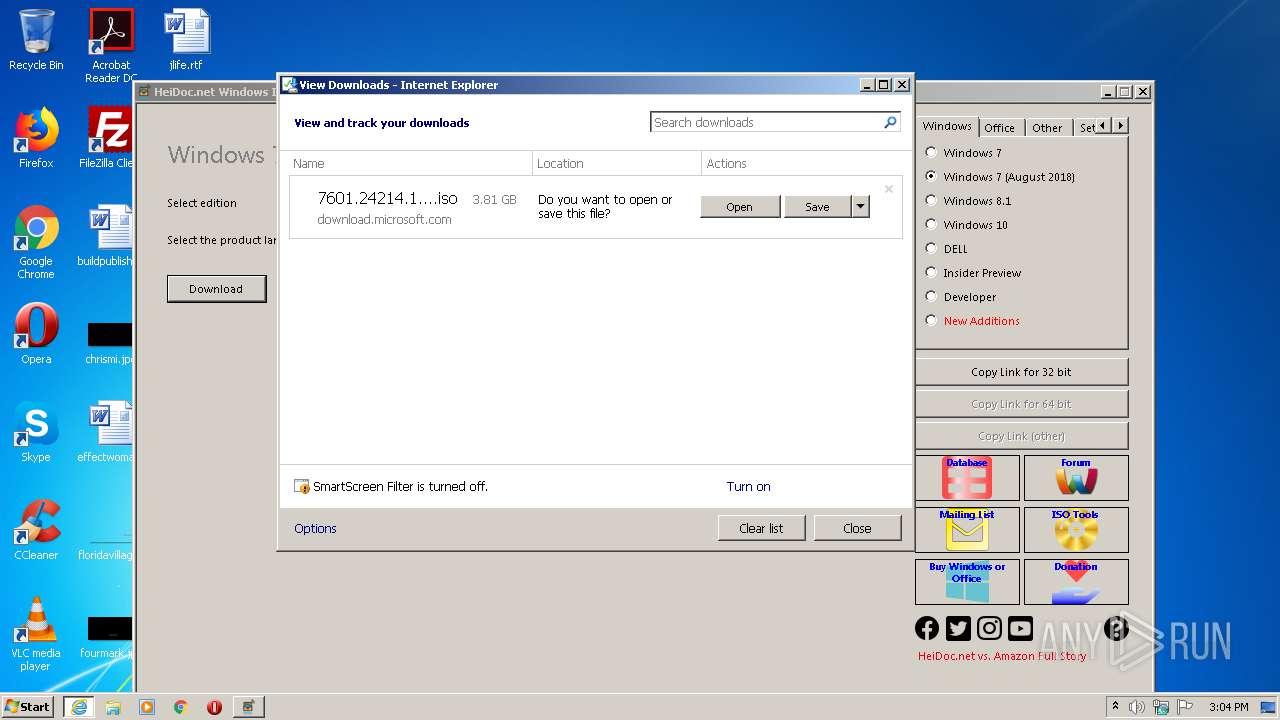
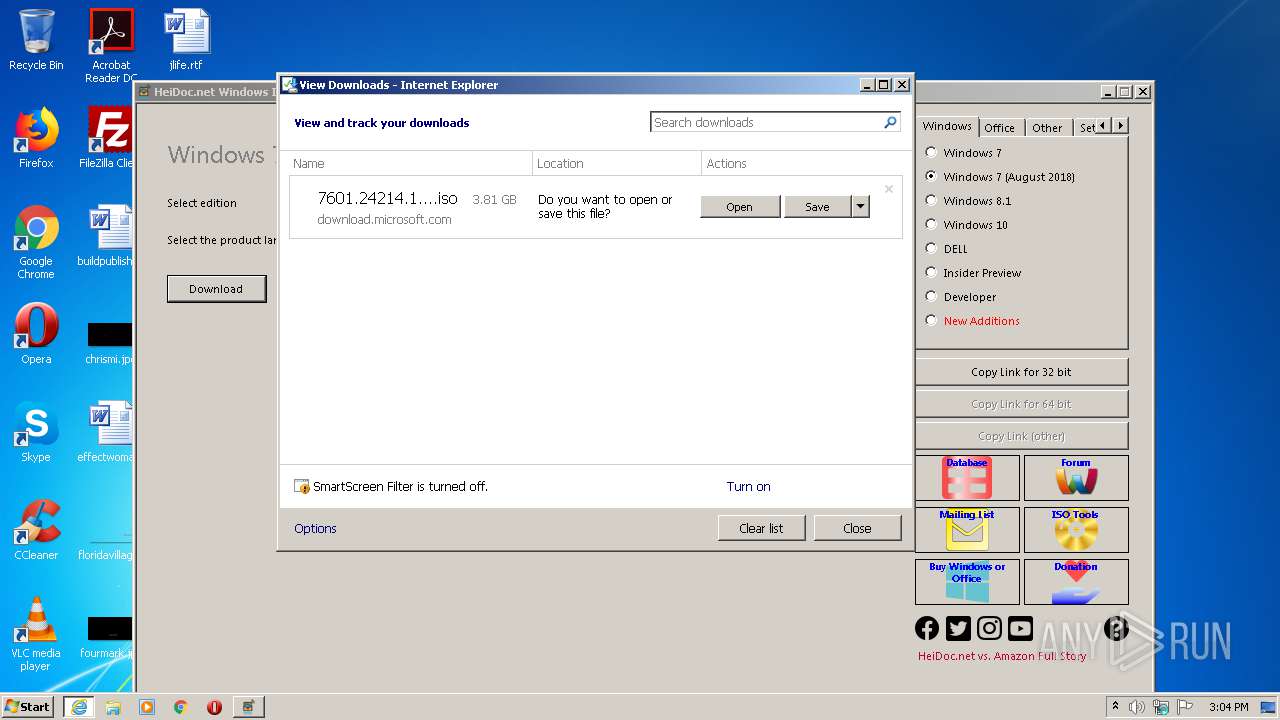
Starts Internet Explorer
- Windows-ISO-Downloader.exe (PID: 2624)
INFO
Application launched itself
- iexplore.exe (PID: 4008)
Reads Internet Cache Settings
- iexplore.exe (PID: 4008)
- iexplore.exe (PID: 1980)
Reads settings of System Certificates
- iexplore.exe (PID: 1980)
Changes internet zones settings
- iexplore.exe (PID: 4008)
Modifies the phishing filter of IE
- iexplore.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:07 23:58:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 6363648 |
| InitializedDataSize: | 308736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x61394a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.38.0.144 |
| ProductVersionNumber: | 8.38.0.144 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | HeiDoc V.O.F. |
| FileDescription: | Windows ISO Downloader |
| FileVersion: | 8.38.0.0144 |
| InternalName: | Windows-ISO-Downloader.exe |
| LegalCopyright: | Copyright © 2016-2020 |
| LegalTrademarks: | - |
| OriginalFileName: | Windows-ISO-Downloader.exe |
| ProductName: | Windows ISO Downloader |
| ProductVersion: | 8.38.0.0144 |
| AssemblyVersion: | 8.38.0.144 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jul-2020 21:58:09 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | HeiDoc V.O.F. |
| FileDescription: | Windows ISO Downloader |
| FileVersion: | 8.38.0.0144 |
| InternalName: | Windows-ISO-Downloader.exe |
| LegalCopyright: | Copyright © 2016-2020 |
| LegalTrademarks: | - |
| OriginalFilename: | Windows-ISO-Downloader.exe |
| ProductName: | Windows ISO Downloader |
| ProductVersion: | 8.38.0.0144 |
| Assembly Version: | 8.38.0.144 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Jul-2020 21:58:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00611950 | 0x00611A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.86771 |
.rsrc | 0x00614000 | 0x0004B3DC | 0x0004B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.42961 |
.reloc | 0x00660000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.43345 | 962 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 4.66927 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.31647 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.81771 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.50631 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.15714 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.02373 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 2.78483 | 152104 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 7.95518 | 14279 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 3.07075 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1980 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4008 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
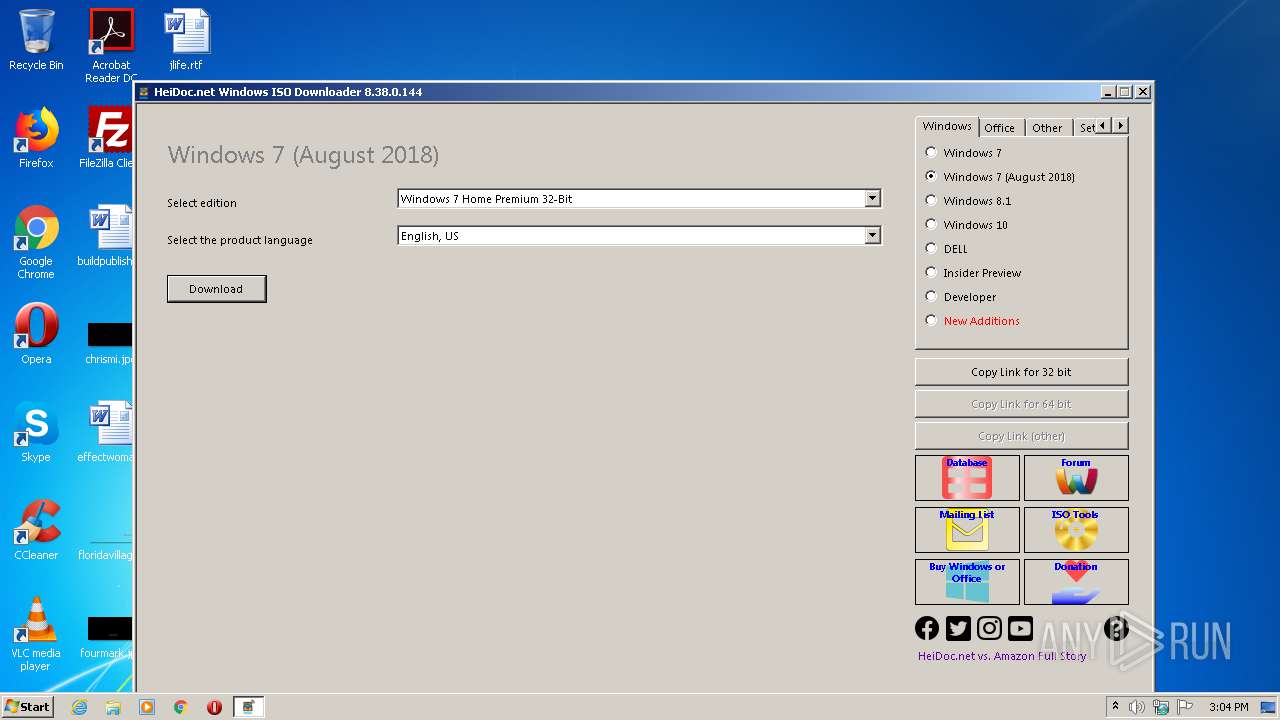
| 2624 | "C:\Users\admin\AppData\Local\Temp\Windows-ISO-Downloader.exe" | C:\Users\admin\AppData\Local\Temp\Windows-ISO-Downloader.exe | explorer.exe | ||||||||||||
User: admin Company: HeiDoc V.O.F. Integrity Level: MEDIUM Description: Windows ISO Downloader Exit code: 0 Version: 8.38.0.0144 Modules
| |||||||||||||||
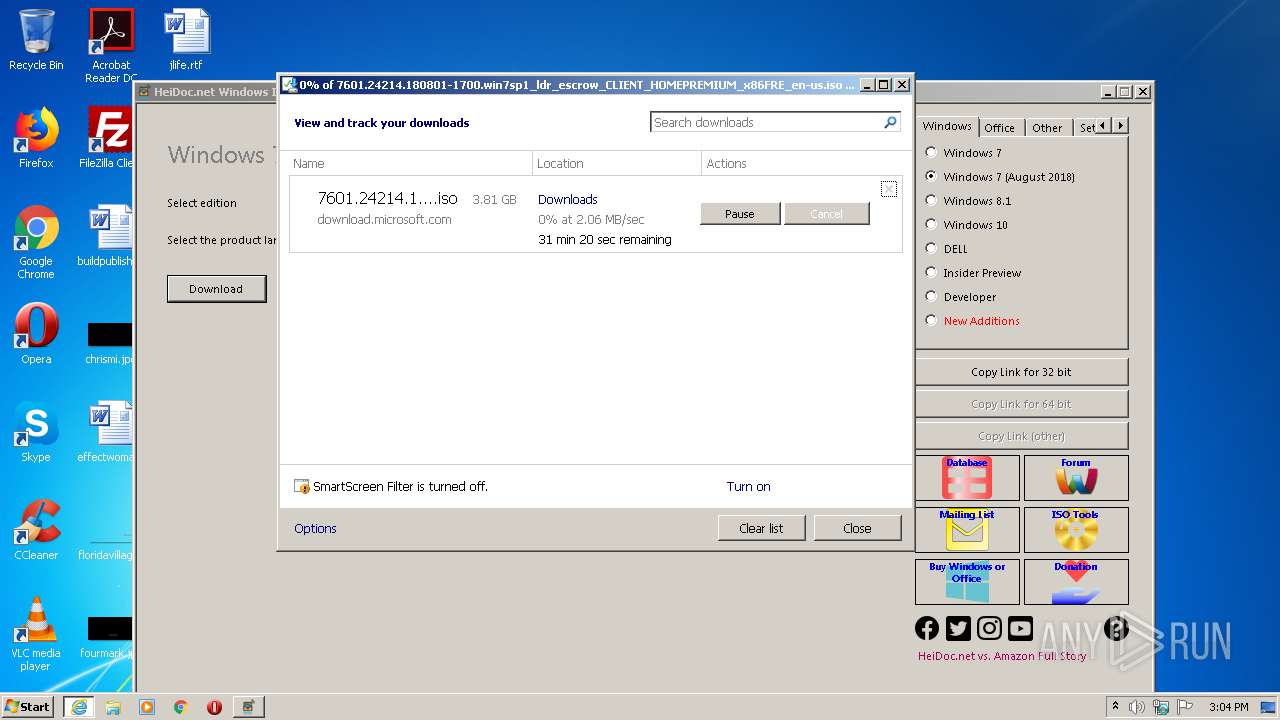
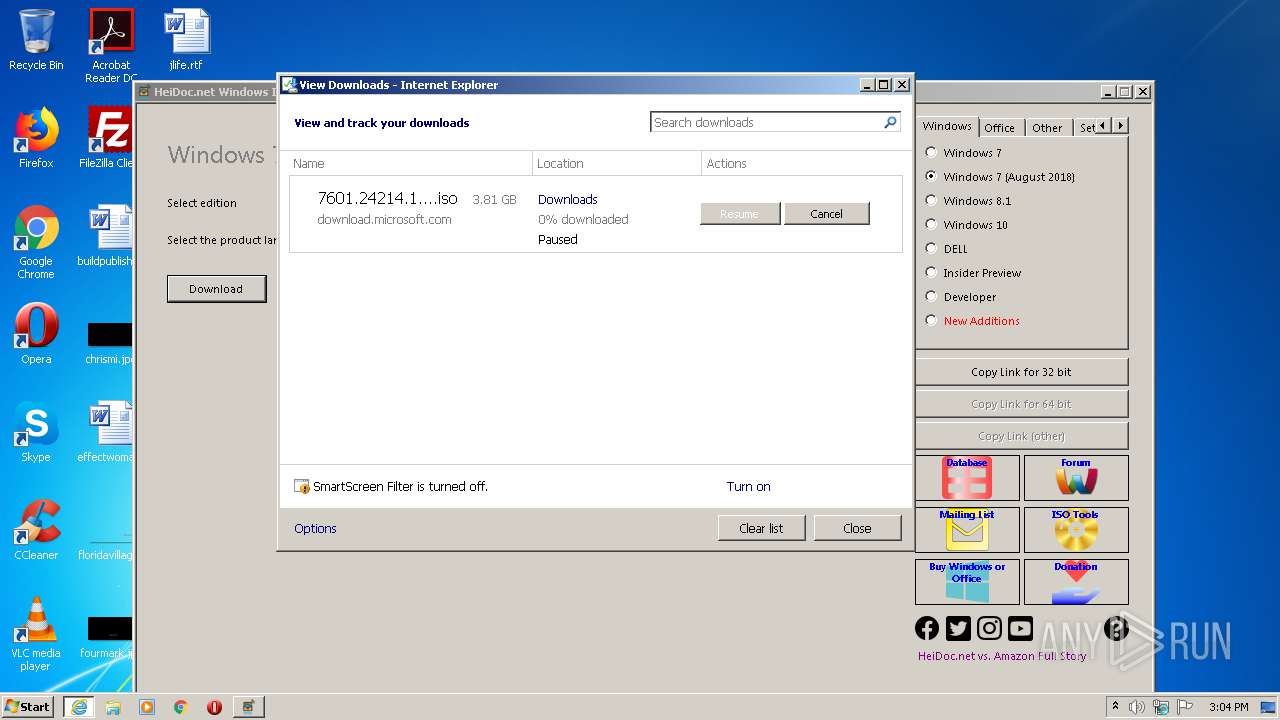
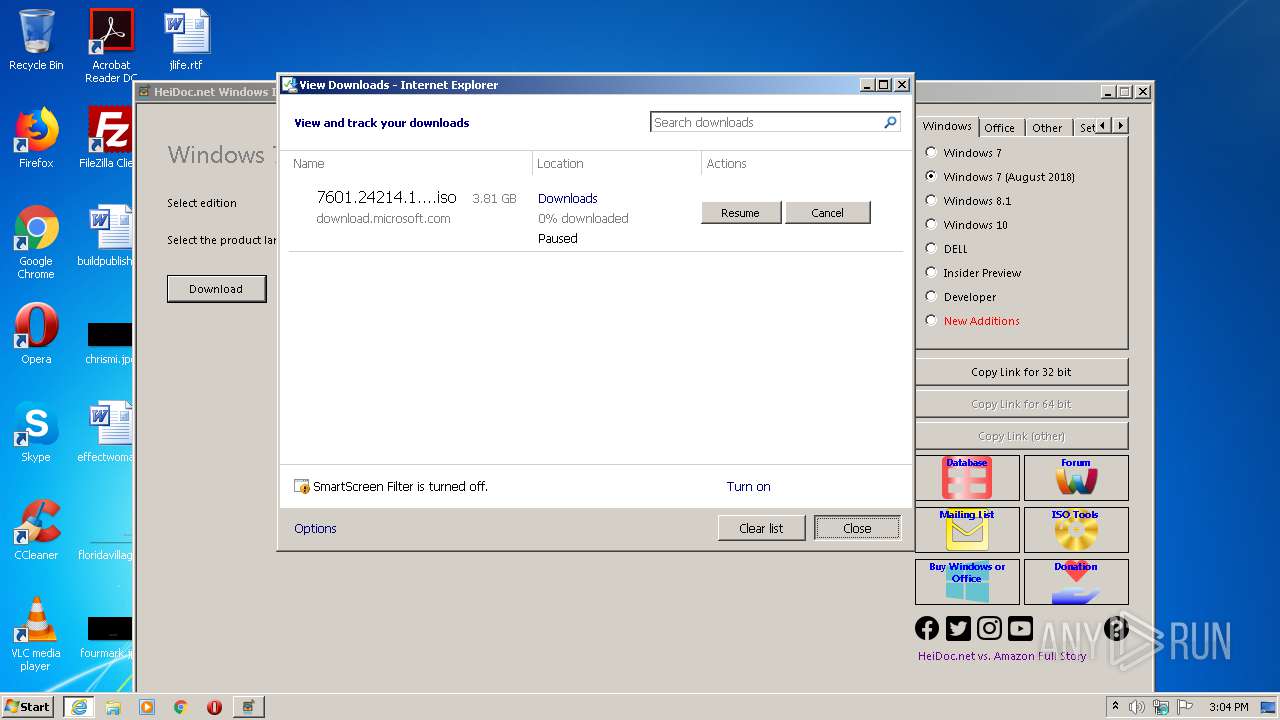
| 4008 | "C:\Program Files\Internet Explorer\iexplore.exe" https://download.microsoft.com/download/E/D/A/EDA6B508-7663-4E30-86F9-949932F443D0/7601.24214.180801-1700.win7sp1_ldr_escrow_CLIENT_HOMEPREMIUM_x86FRE_en-us.iso | C:\Program Files\Internet Explorer\iexplore.exe | — | Windows-ISO-Downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 028
Read events
885
Write events
130
Delete events
13
Modification events
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2624) Windows-ISO-Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
49
Text files
54
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\Local\Temp\Cab83E6.tmp | — | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\Local\Temp\Tar83E7.tmp | — | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\R9Y6OU4J.txt | — | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\www-player-vflKe1UkR[1].css | — | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\Local\Temp\7f237b41-a518-461b-9e7c-34ec4cac4017.css | text | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_92C27301B80B002C2BC1DBC4706E59AC | der | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_2207949320C9D045C2BF5129A5E62E71 | binary | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 2624 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_C0086AD90C61549B4157A48EB618916C | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
43
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | Windows-ISO-Downloader.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCp7BRe1FSElwgAAAAAS%2FYQ | US | der | 472 b | whitelisted |
2624 | Windows-ISO-Downloader.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1980 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAiIzVJfGSRETRSlgpHeuVI%3D | US | der | 1.47 Kb | whitelisted |
2624 | Windows-ISO-Downloader.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFEcbLX4Pkp7AgAAAABybME%3D | US | der | 471 b | whitelisted |
2624 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
2624 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2624 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
2624 | Windows-ISO-Downloader.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECBvWgOfaaqOAgAAAABybF4%3D | US | der | 471 b | whitelisted |
2624 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
2624 | Windows-ISO-Downloader.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDG%2BB3sanMzgAgAAAABybGI%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2624 | Windows-ISO-Downloader.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2624 | Windows-ISO-Downloader.exe | 172.217.22.78:443 | s.ytimg.com | Google Inc. | US | whitelisted |
2624 | Windows-ISO-Downloader.exe | 172.217.21.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
2624 | Windows-ISO-Downloader.exe | 172.217.16.194:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2624 | Windows-ISO-Downloader.exe | 216.58.206.6:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
2624 | Windows-ISO-Downloader.exe | 216.58.212.161:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
1980 | iexplore.exe | 92.122.255.148:443 | download.microsoft.com | GTT Communications Inc. | — | malicious |
1048 | svchost.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
2624 | Windows-ISO-Downloader.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2624 | Windows-ISO-Downloader.exe | 2.16.186.9:443 | statics-marketingsites-eus-ms-com.akamaized.net | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.heidoc.net |
| whitelisted |
aa.online-metrix.net |
| whitelisted |
c.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.youtube.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
static.doubleclick.net |
| whitelisted |