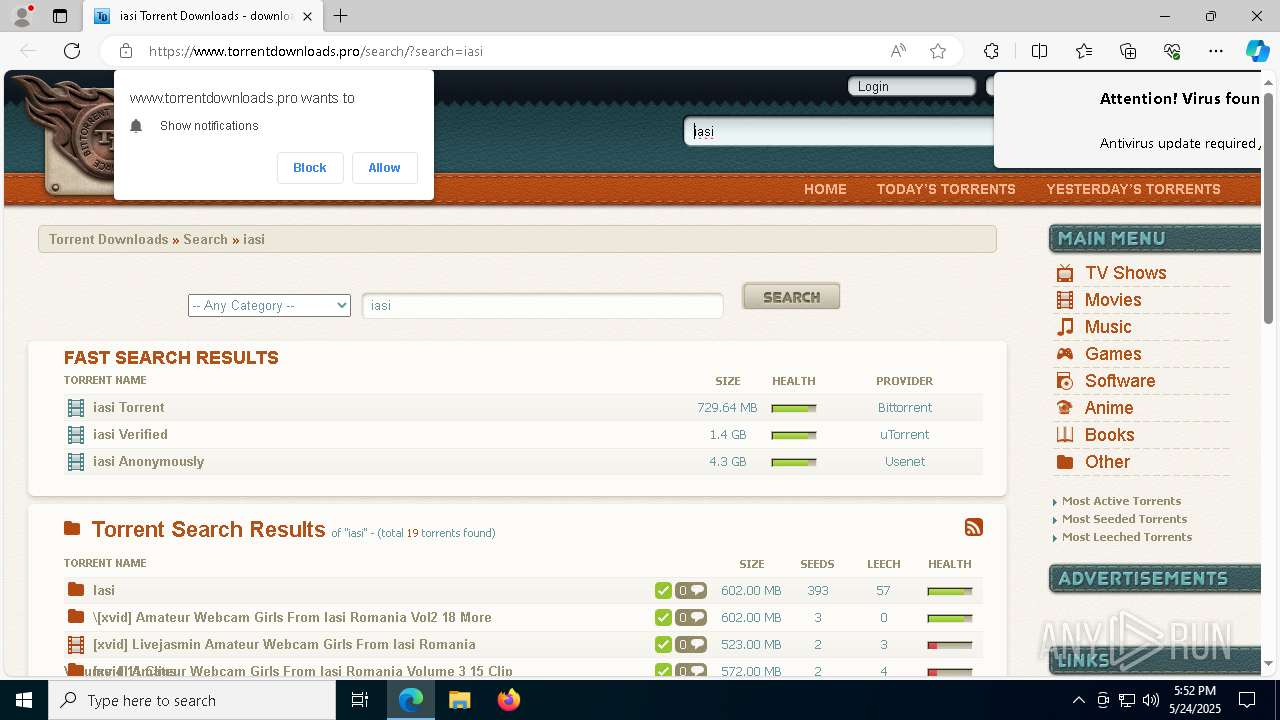
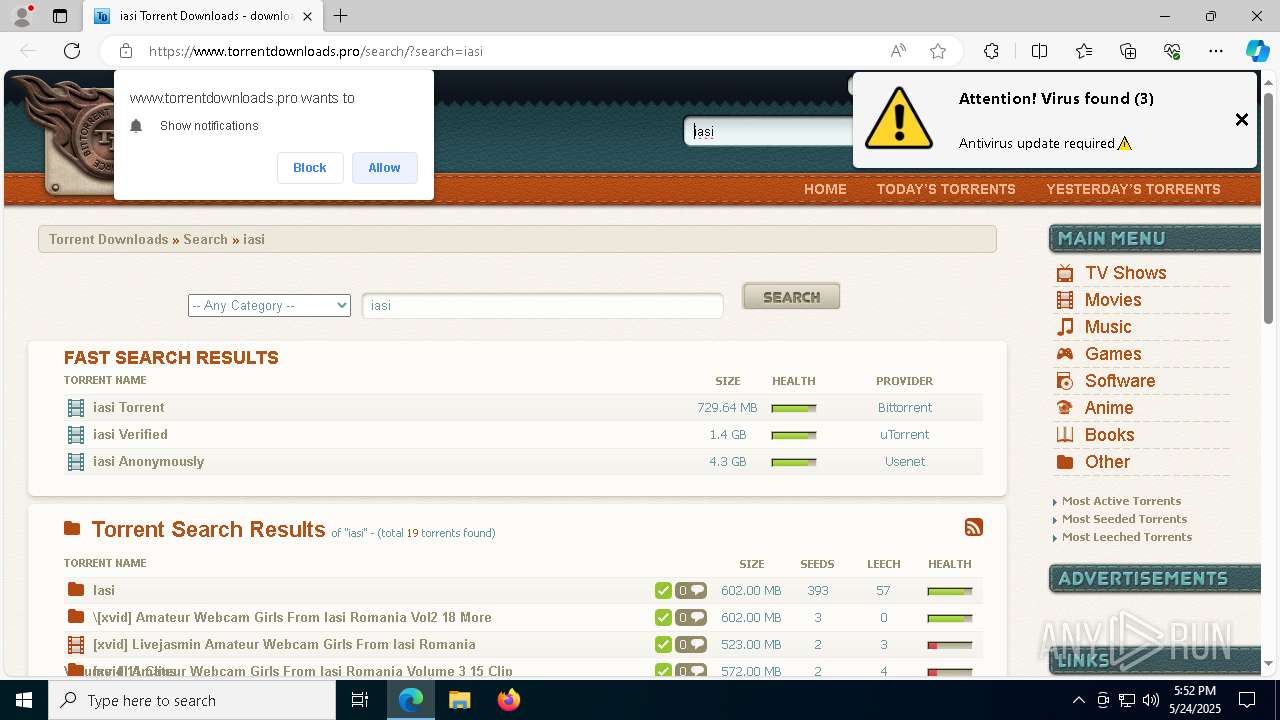
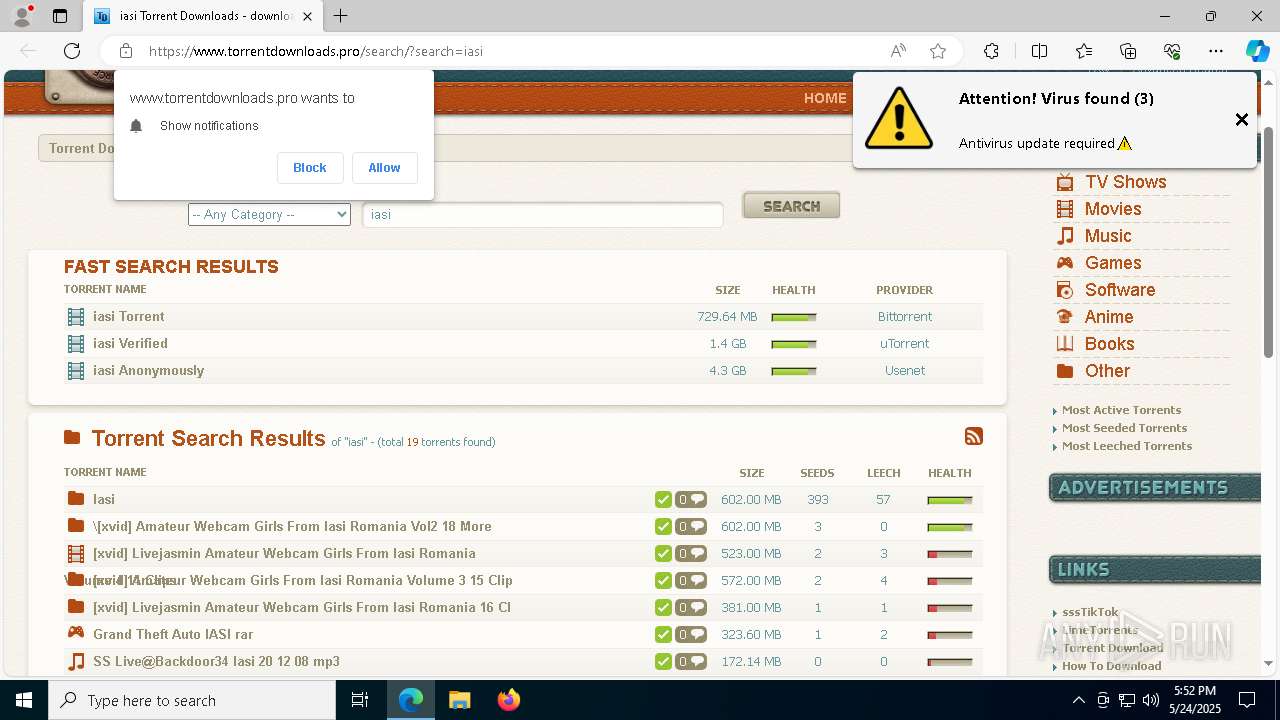
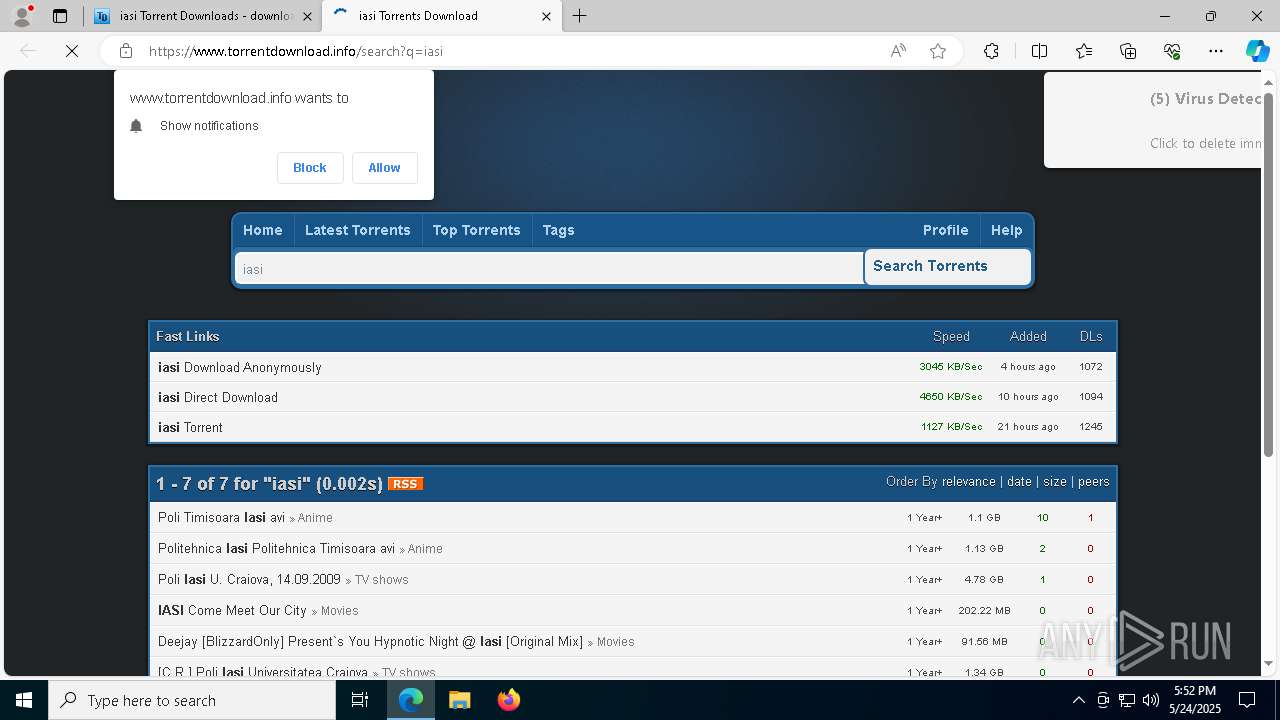
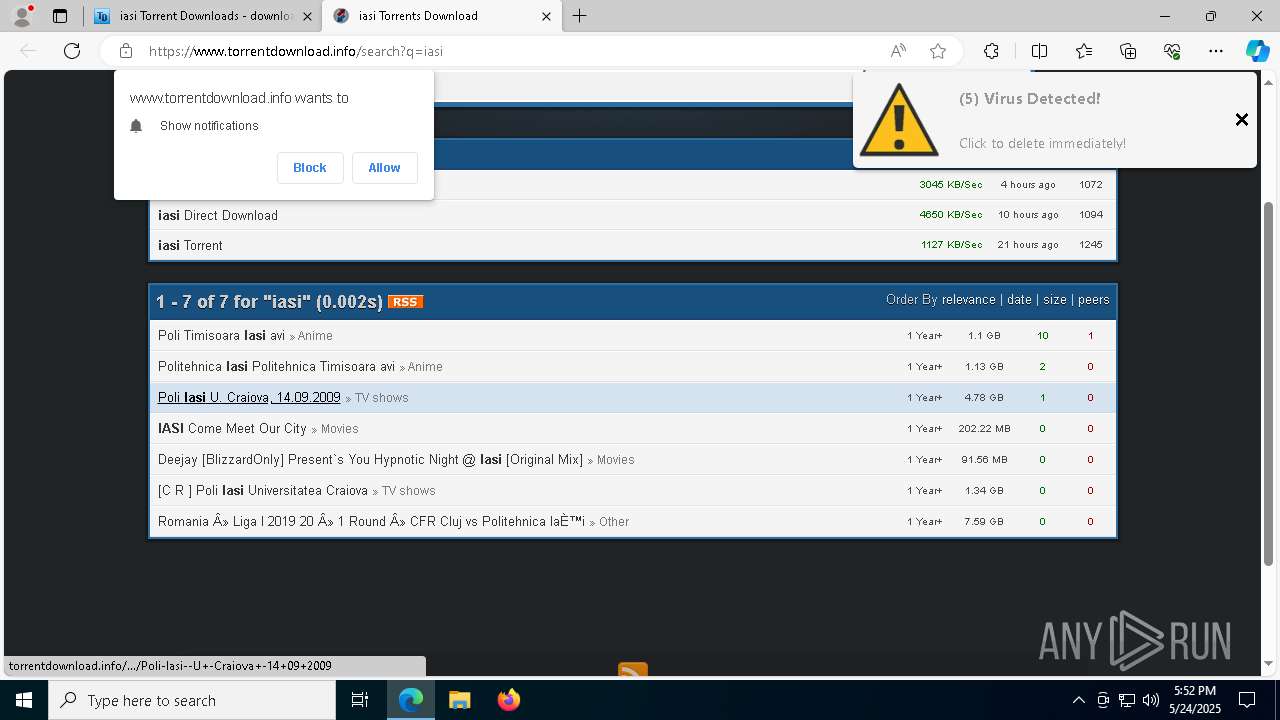
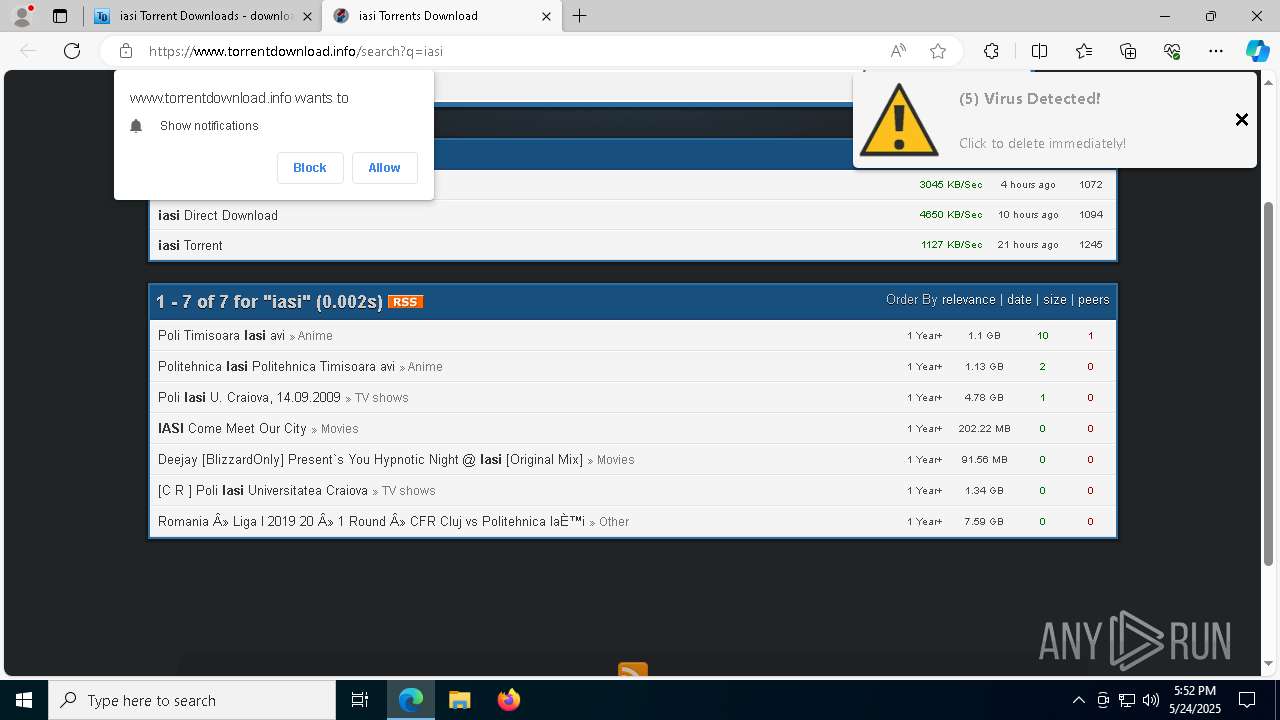
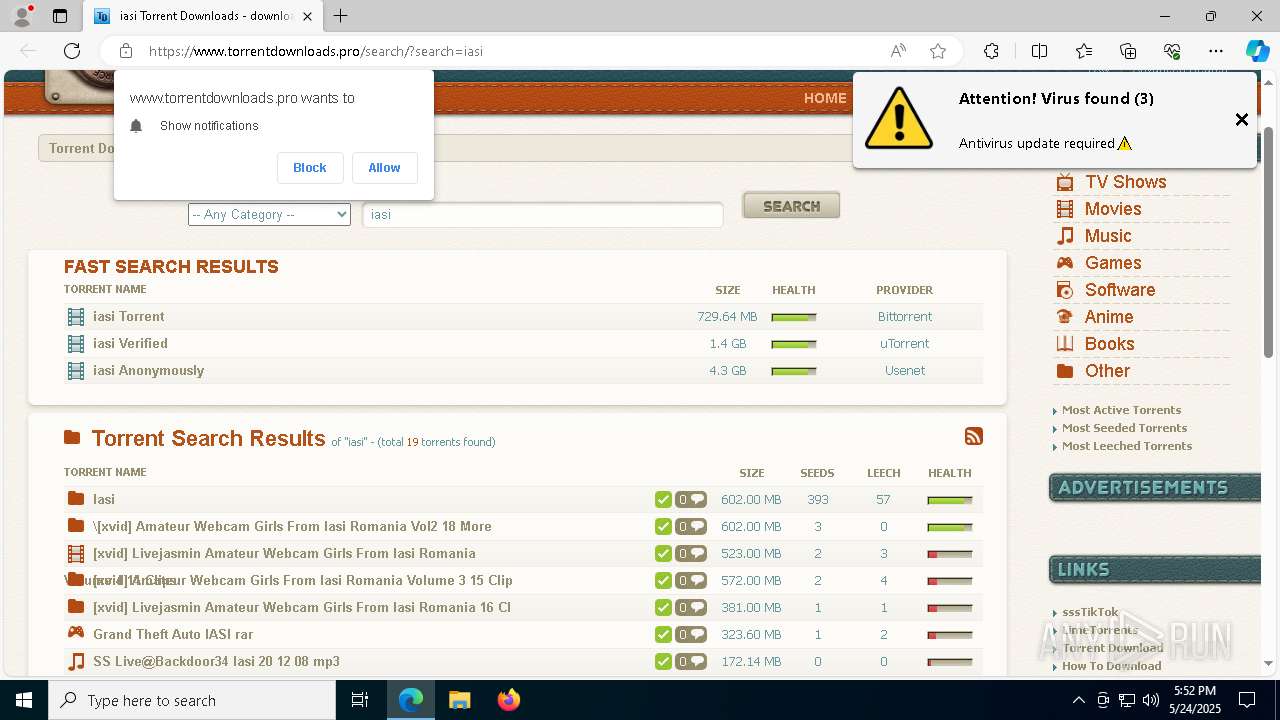
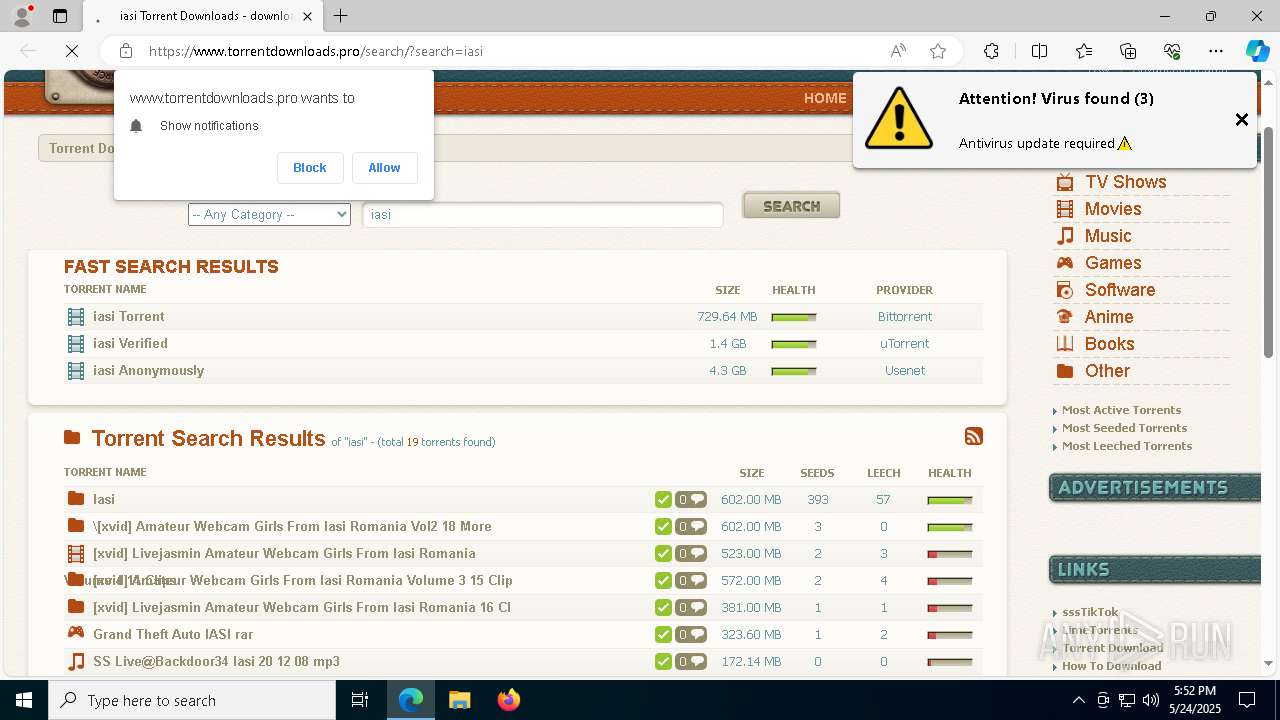
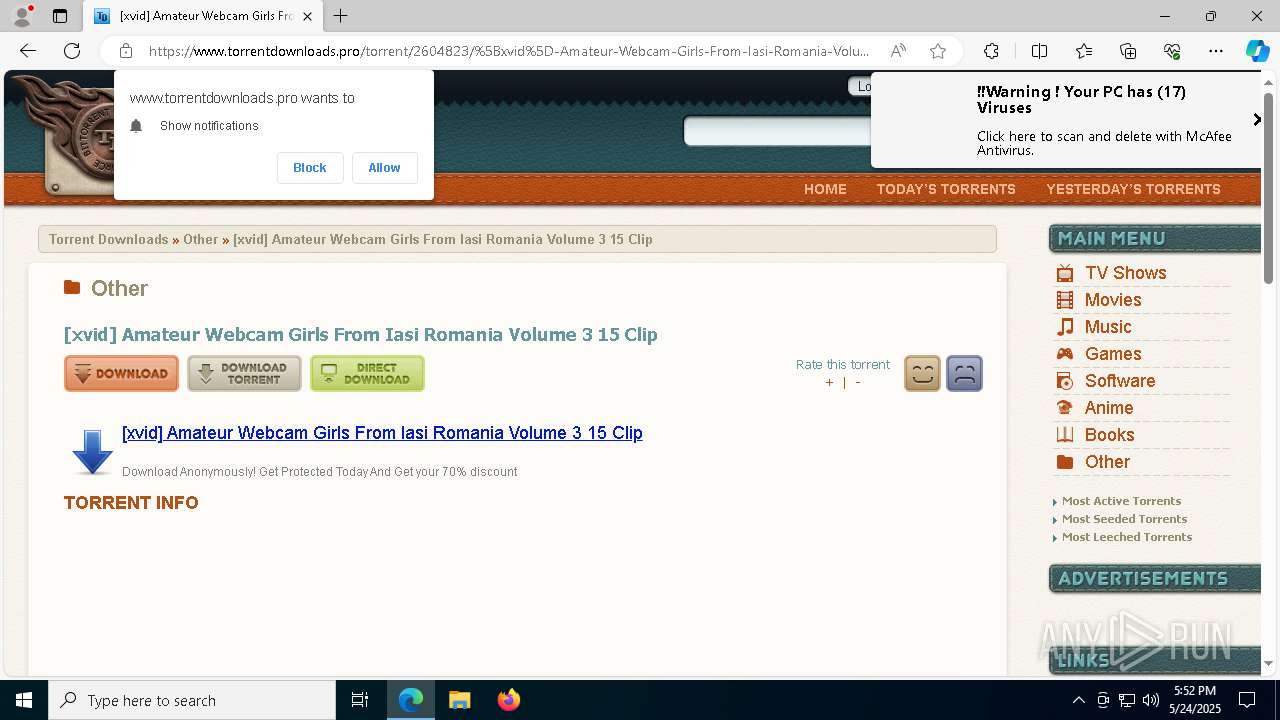
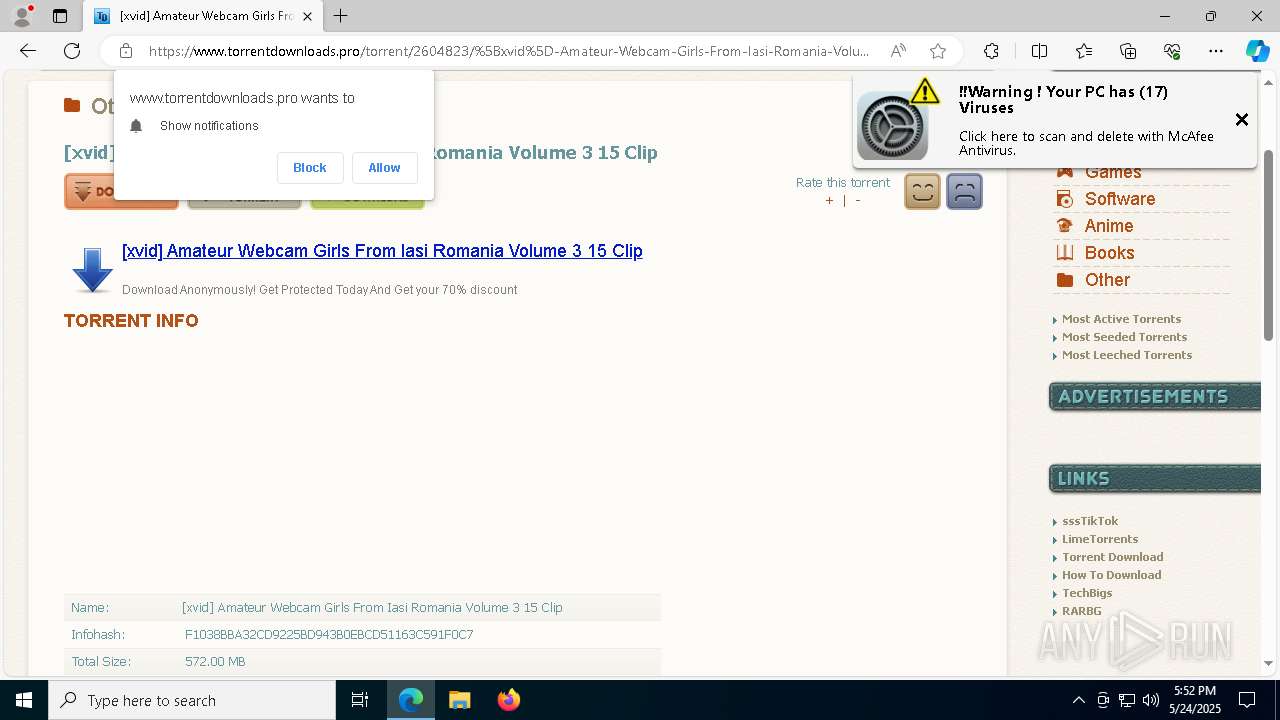
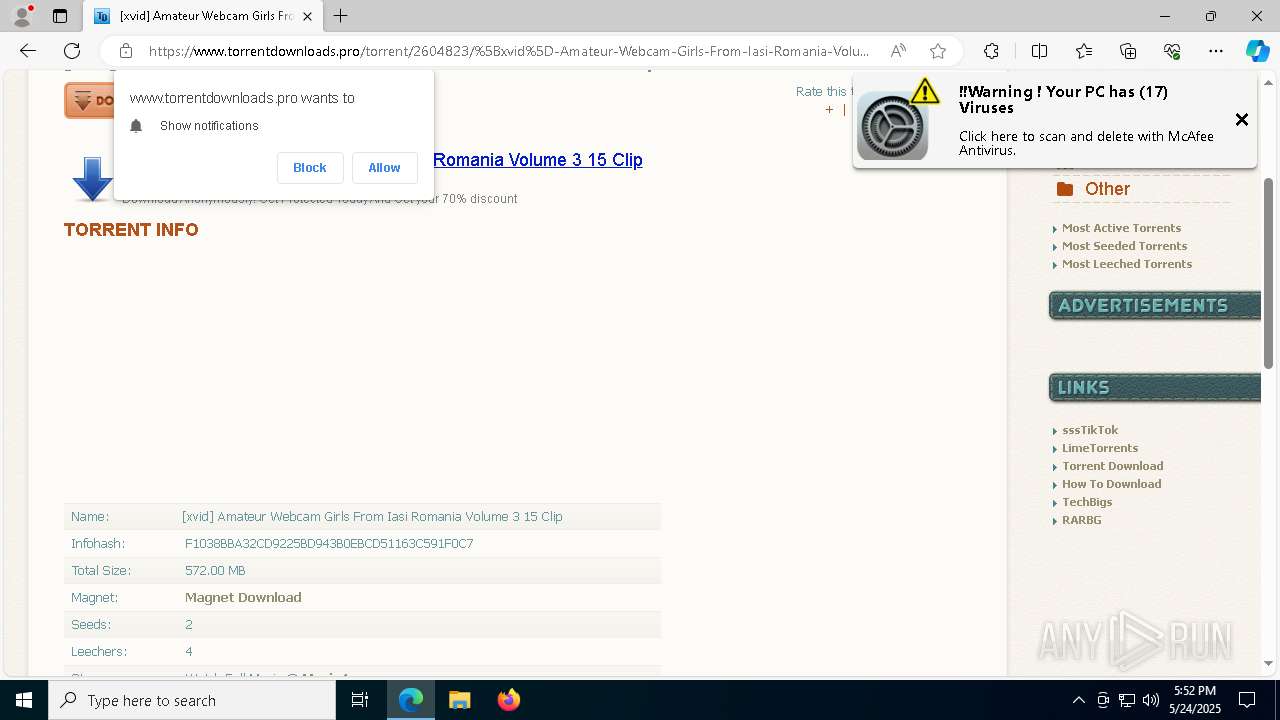
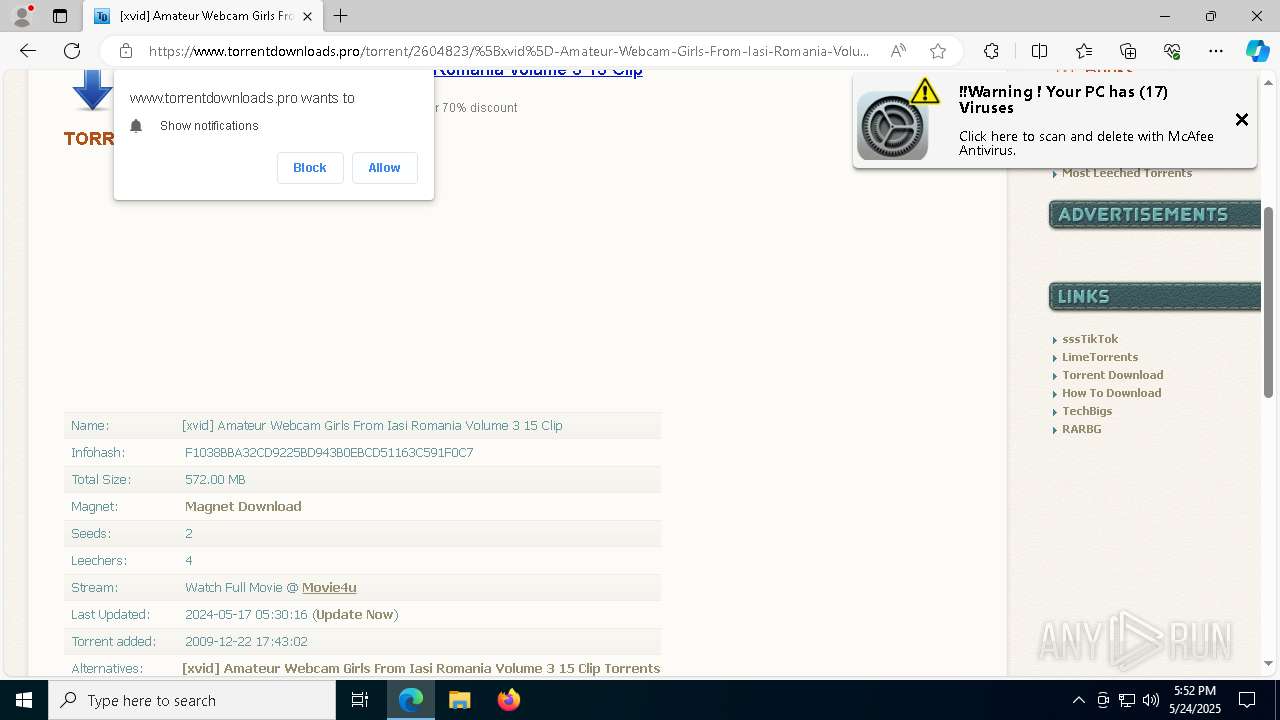
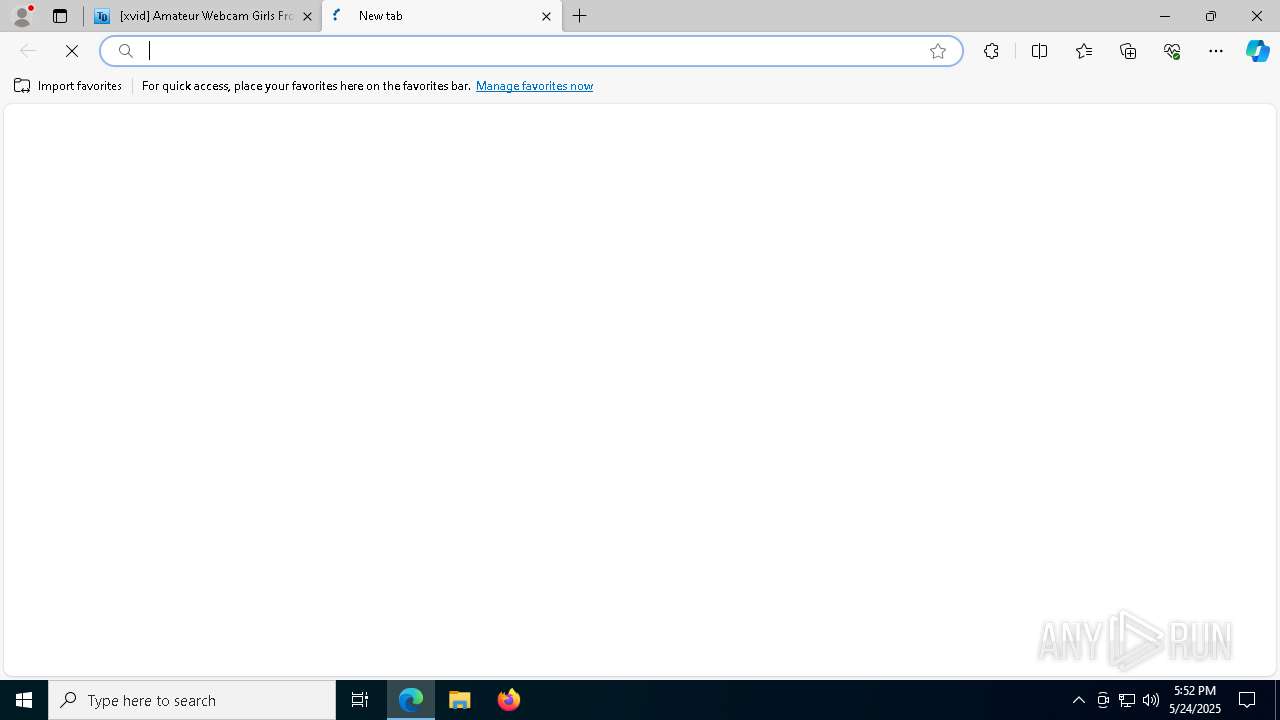
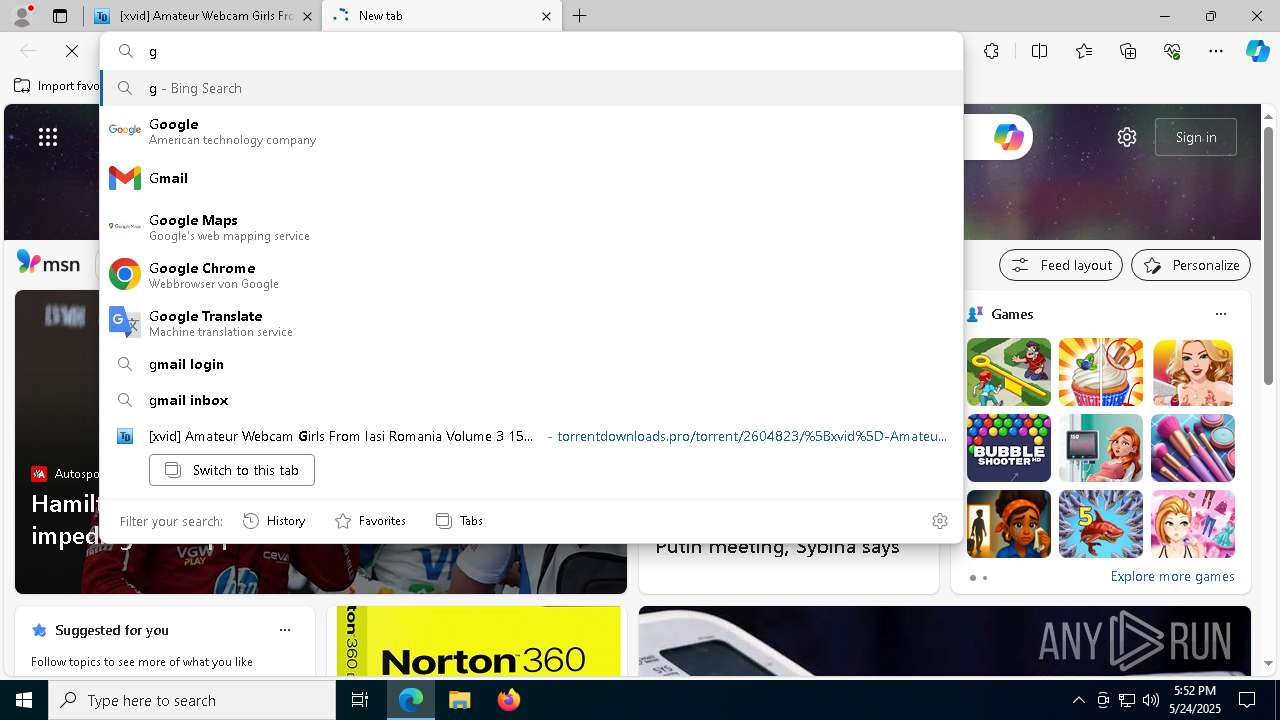
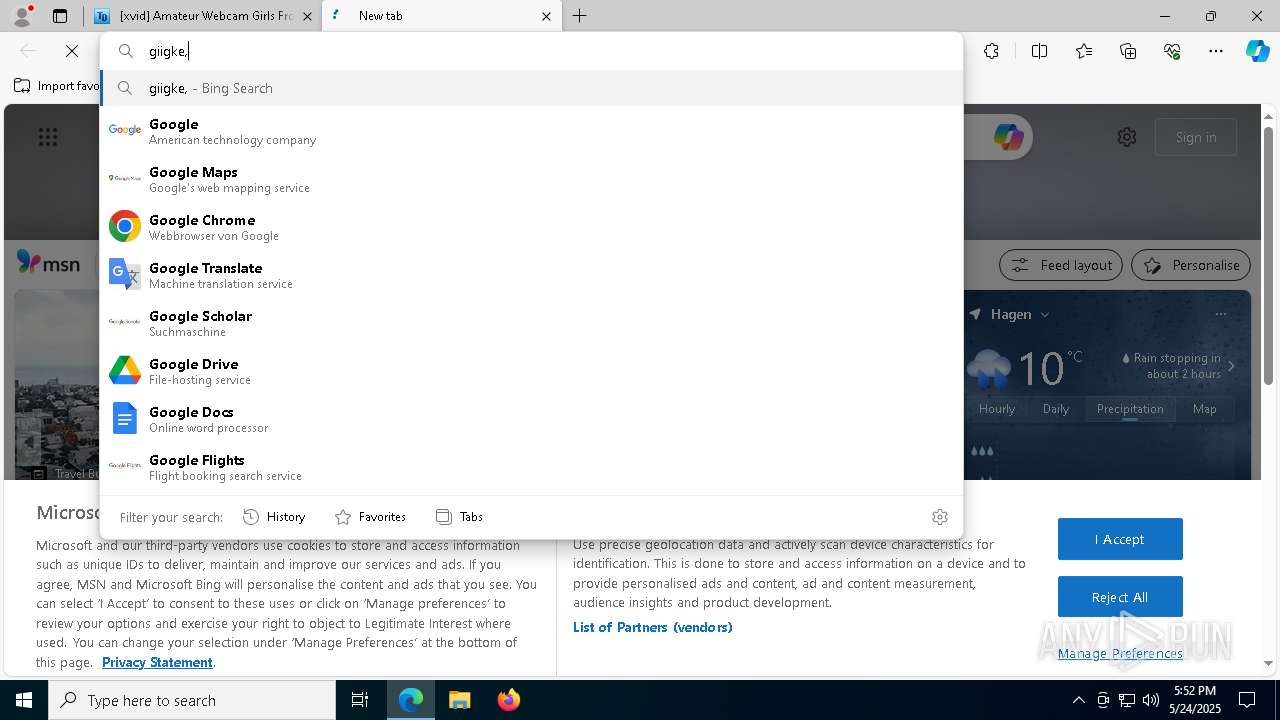
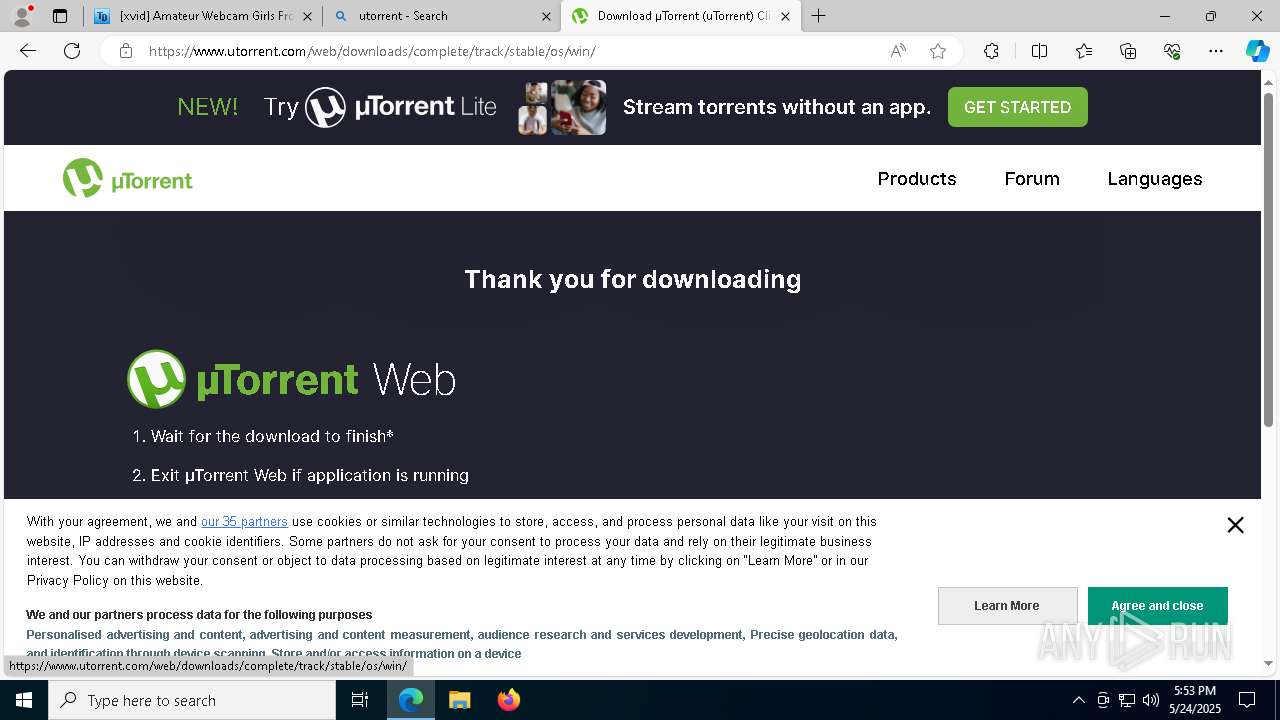
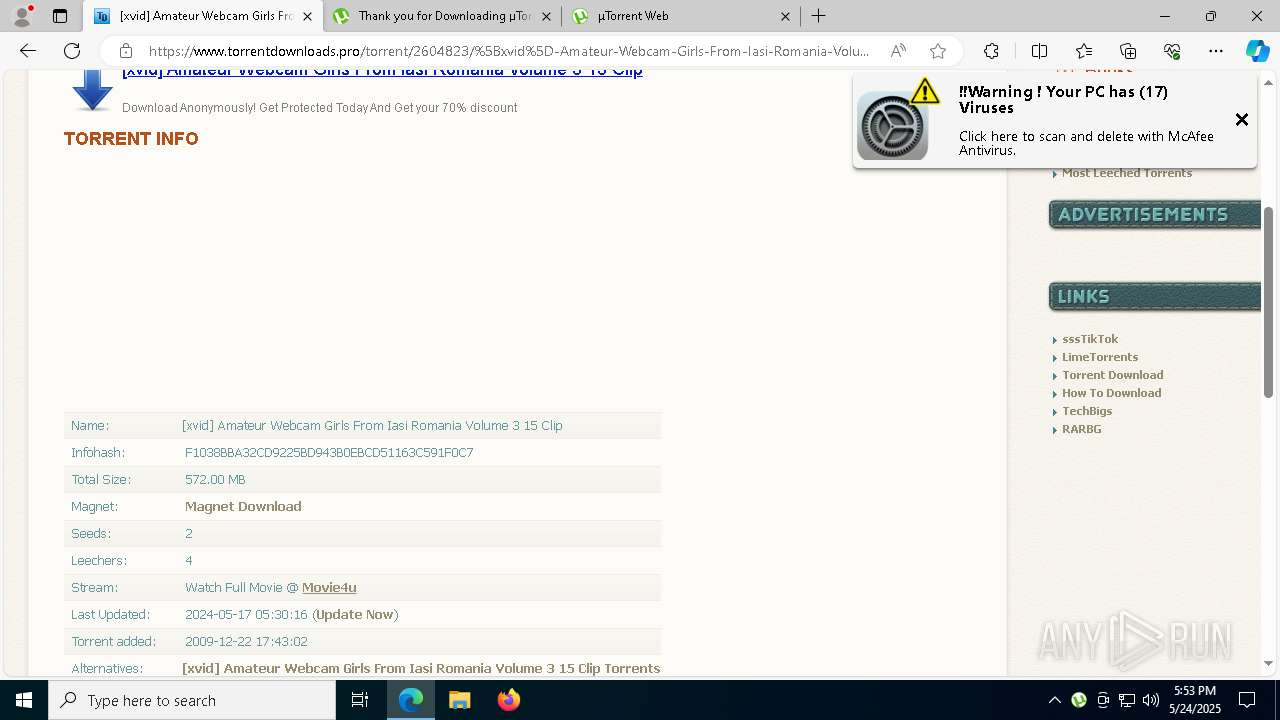
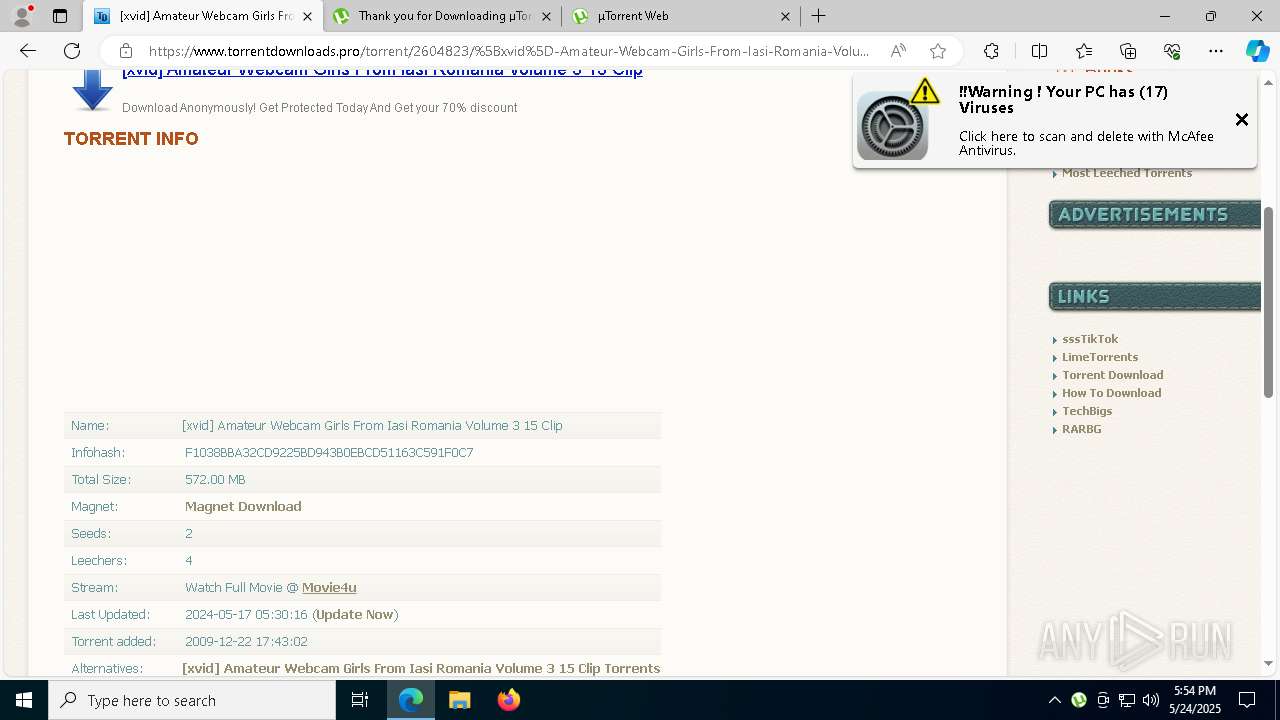
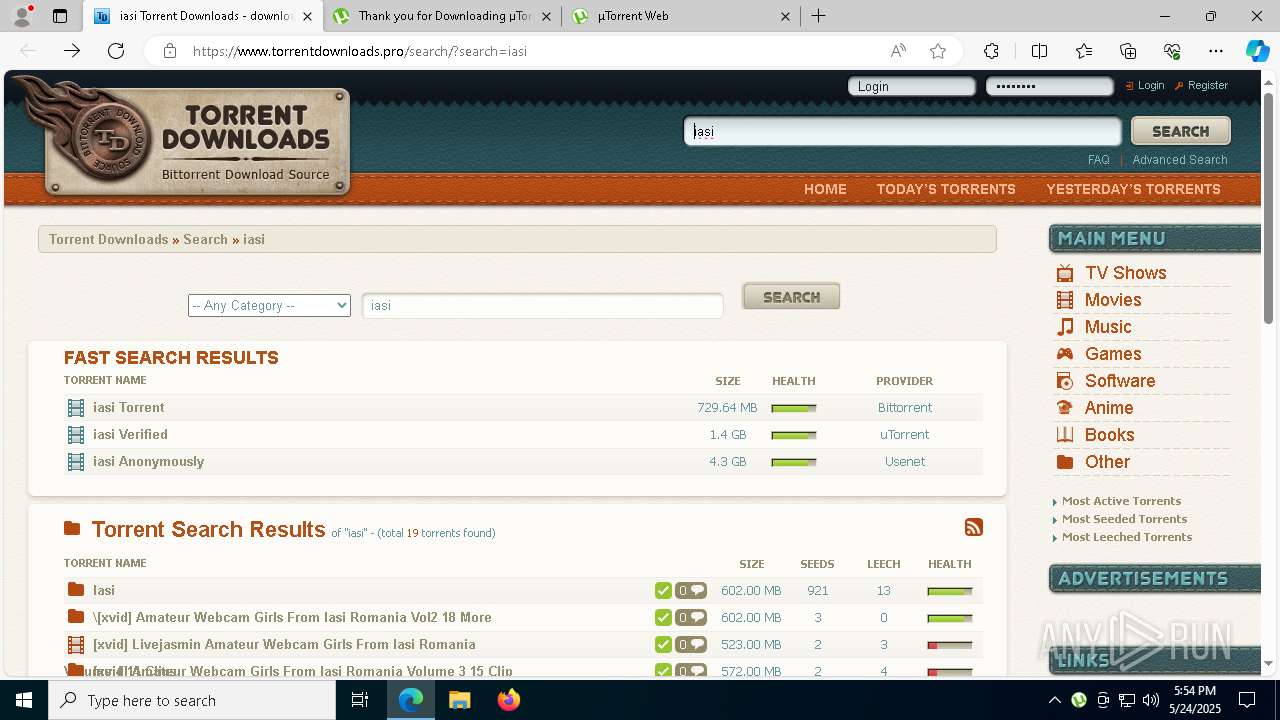
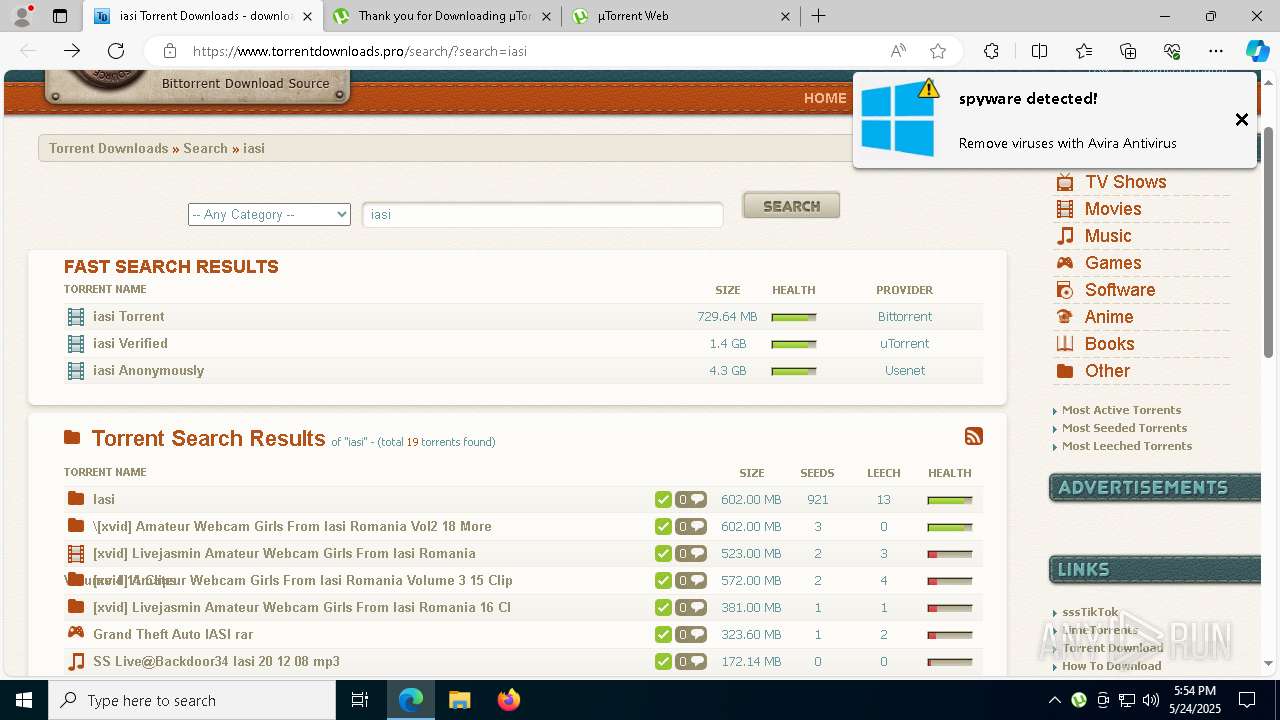
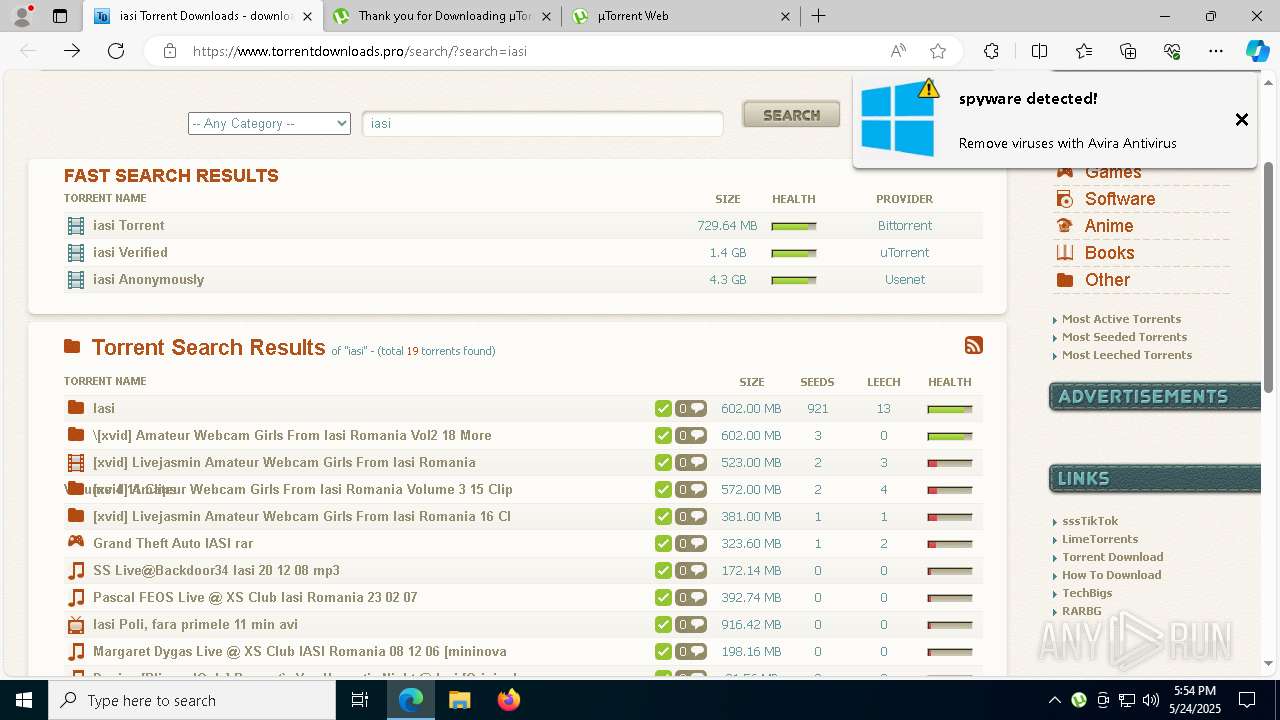
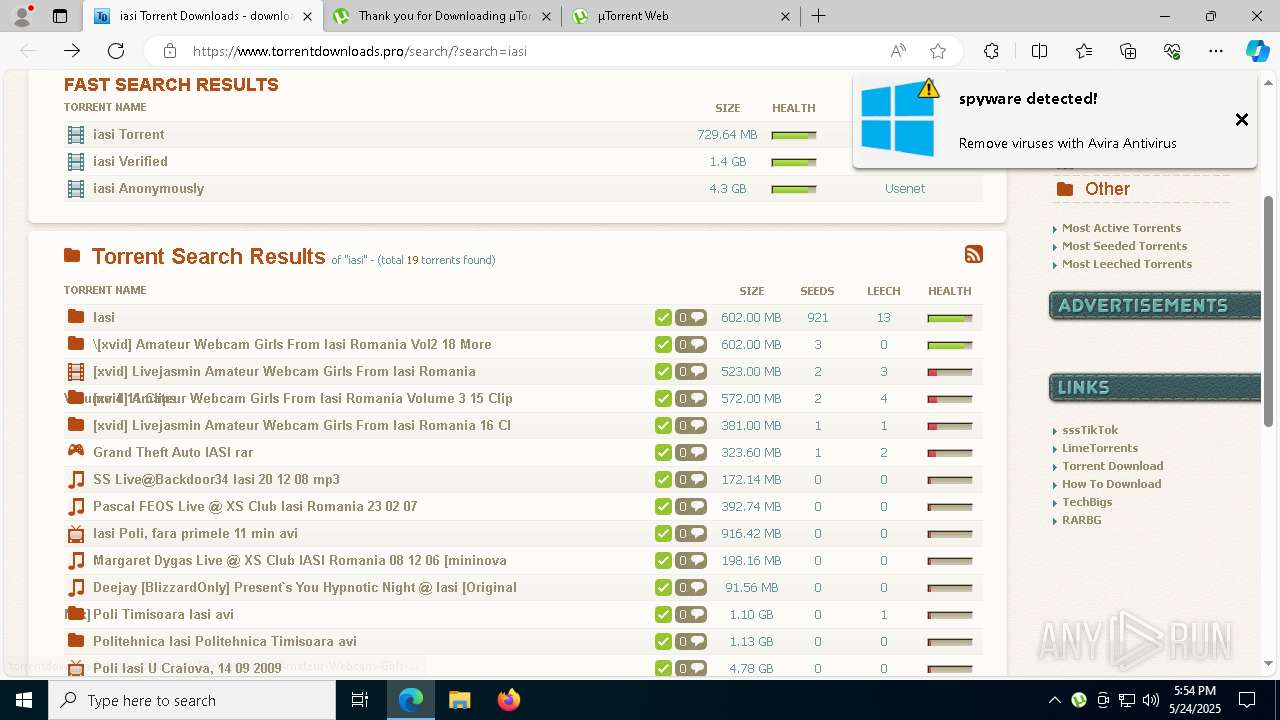
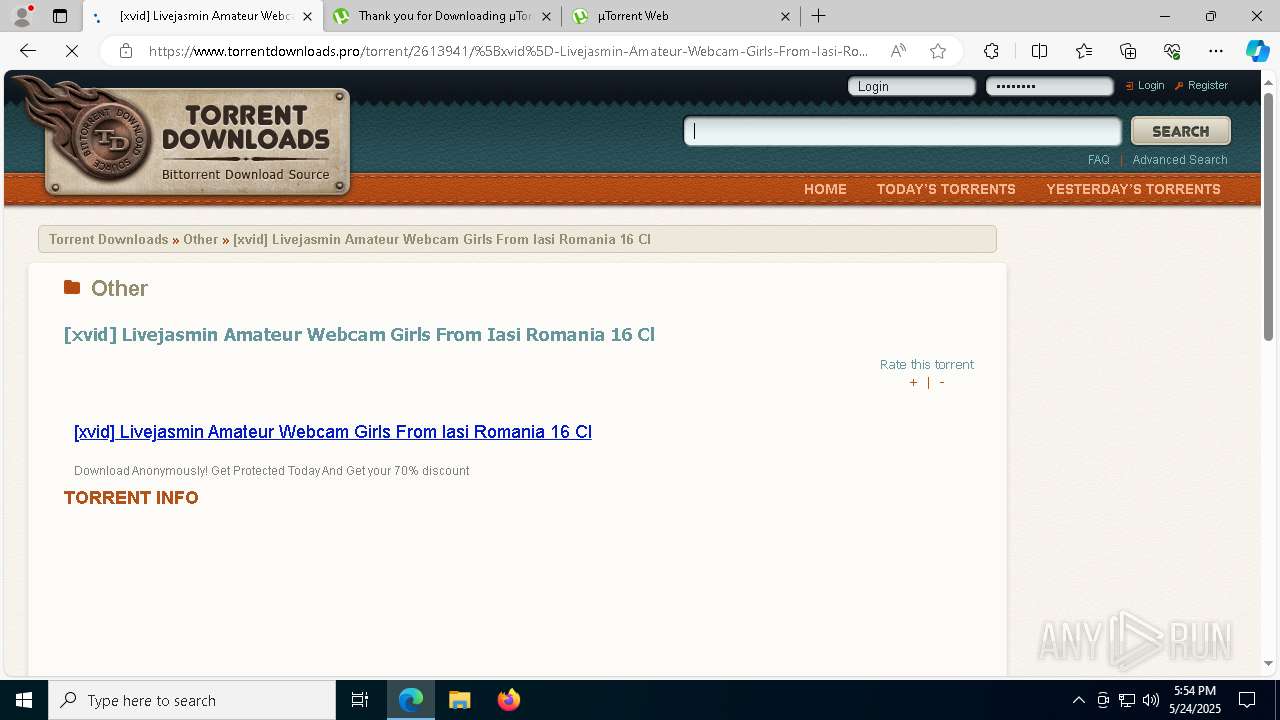
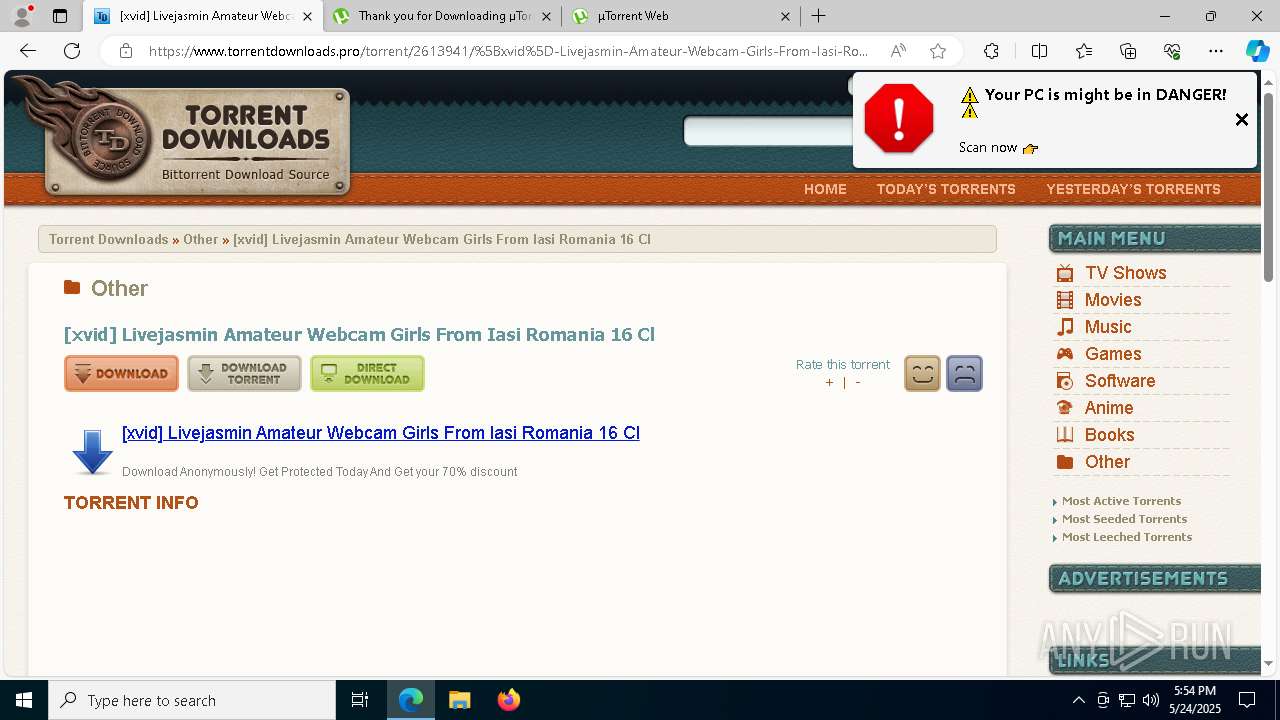
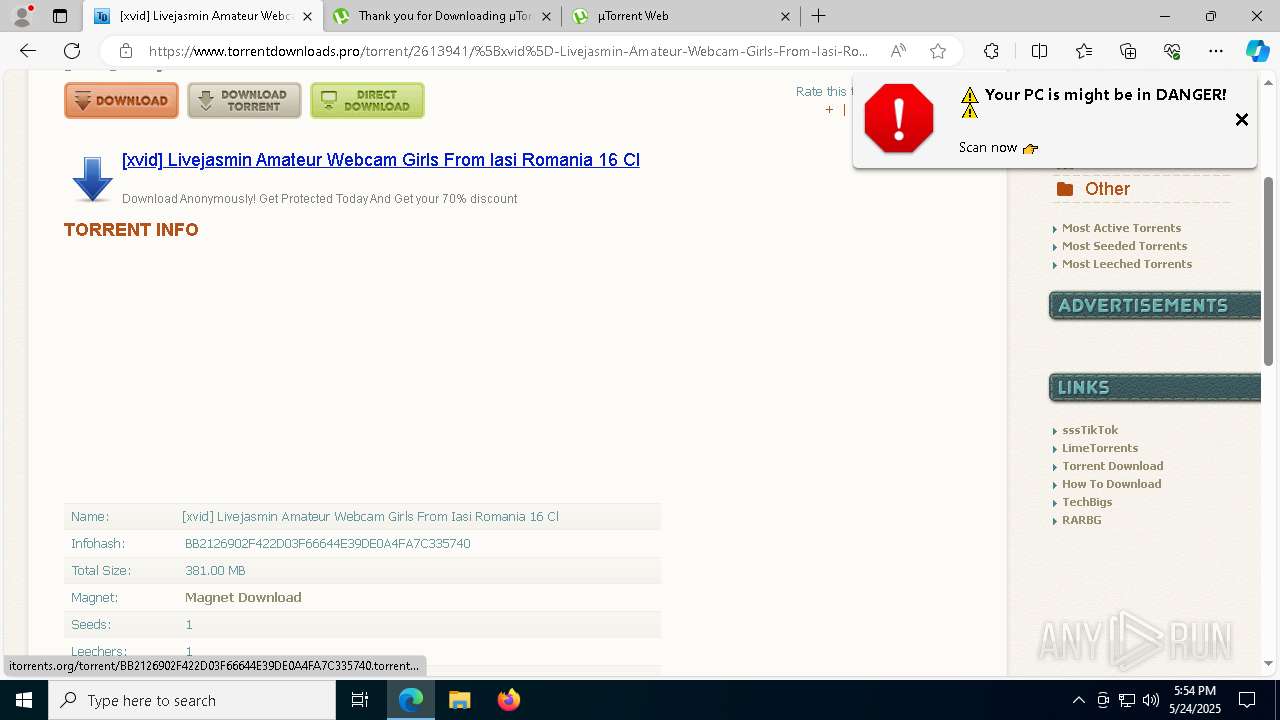
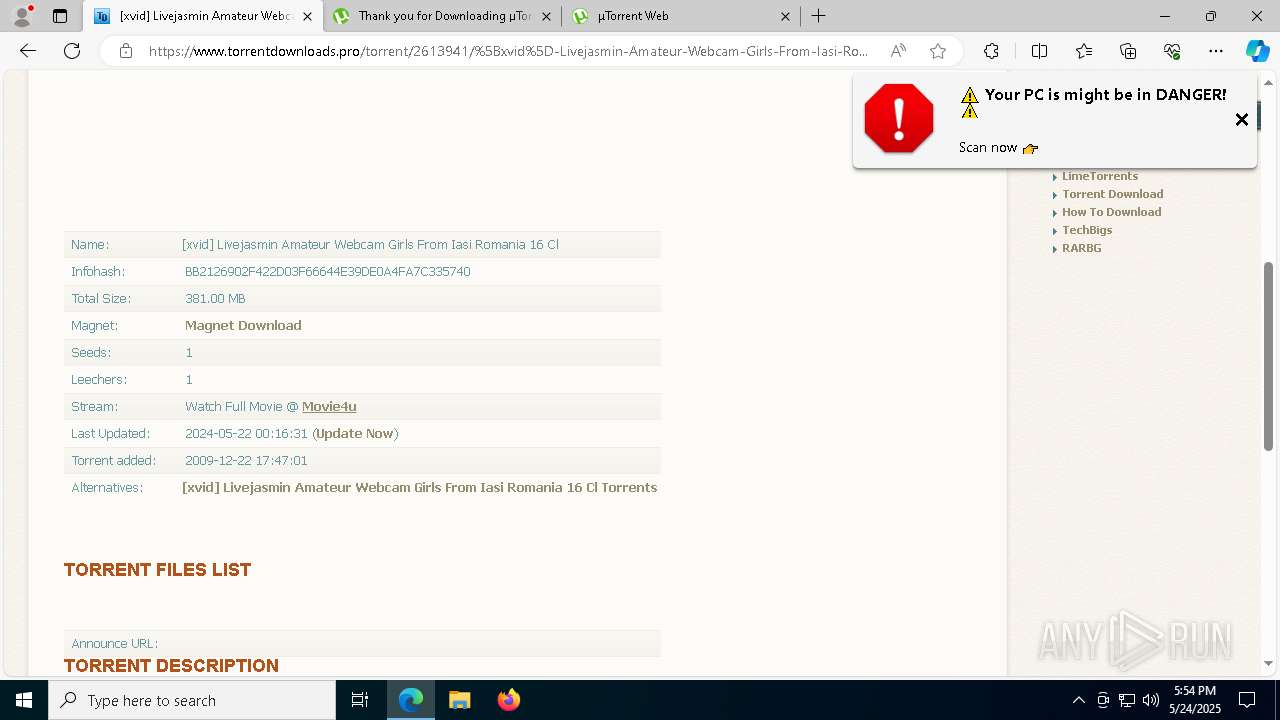
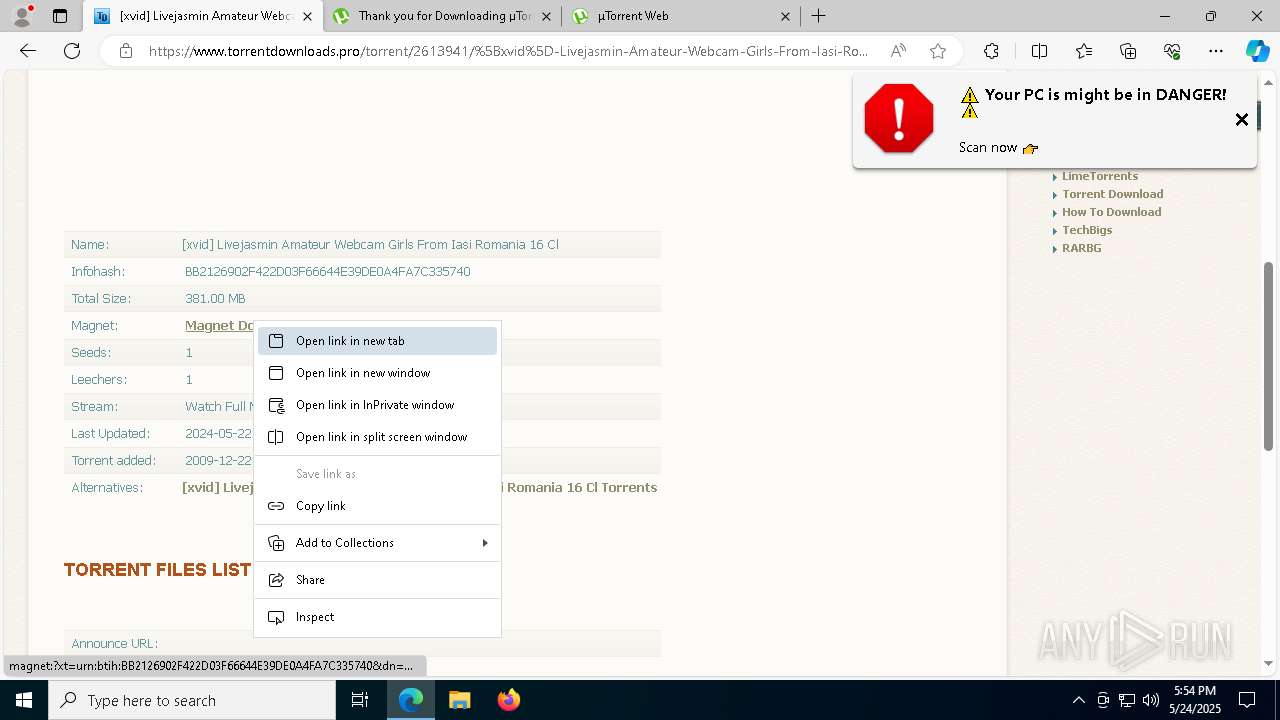
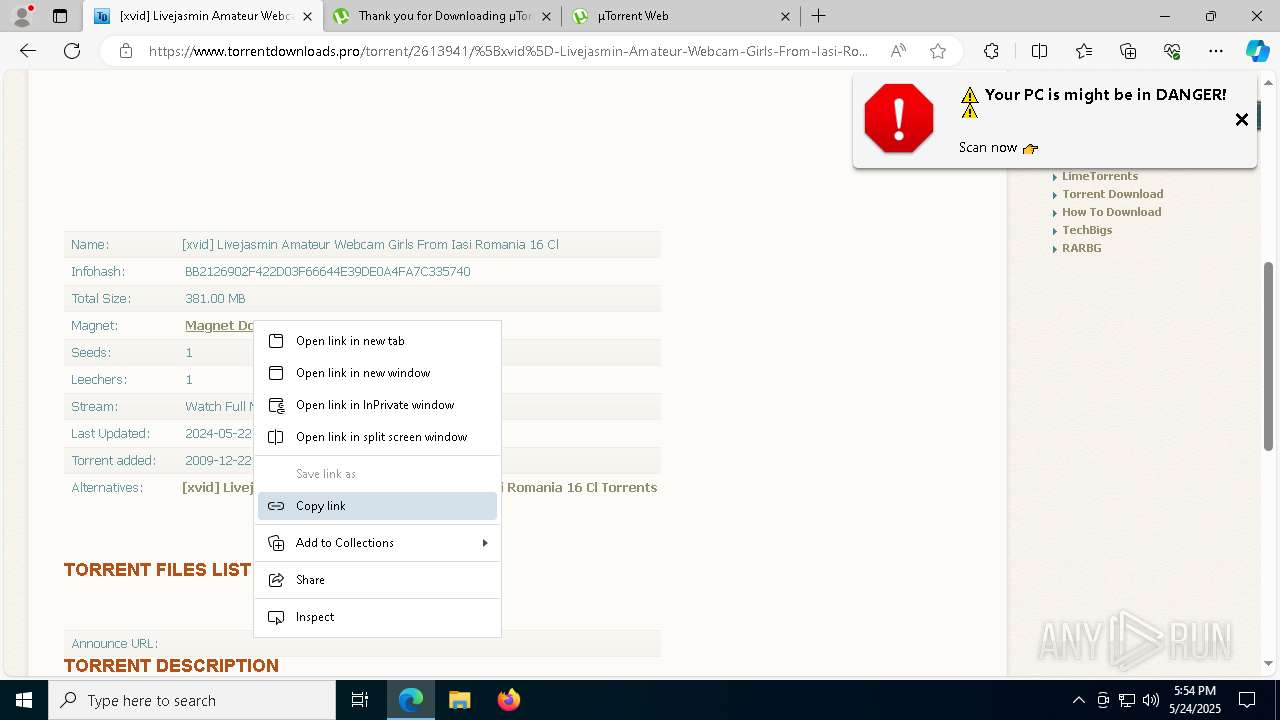
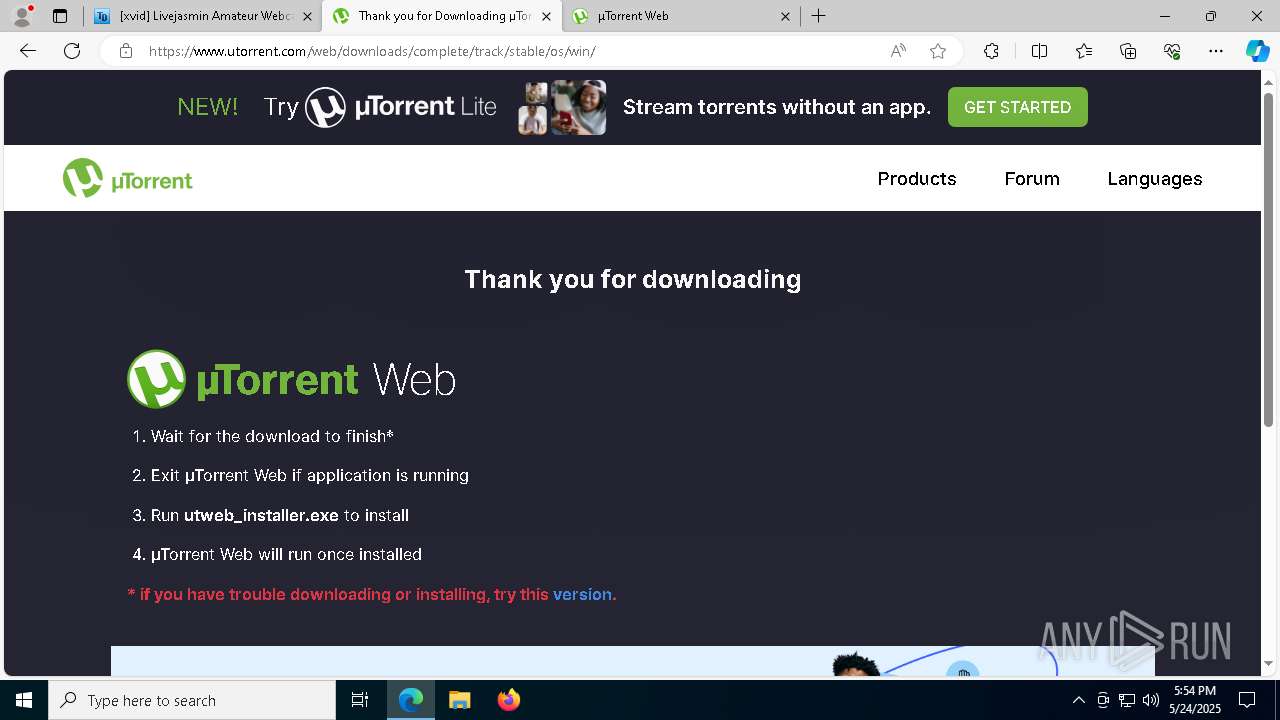
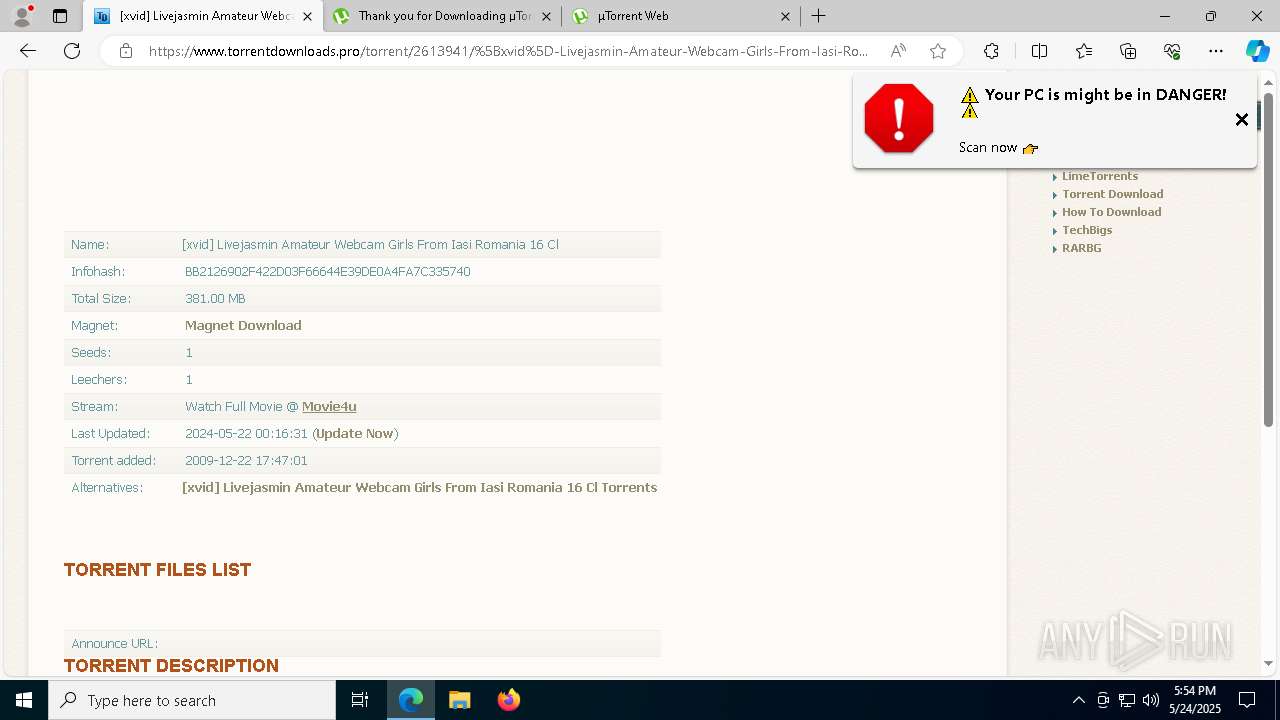
| URL: | https://www.torrentdownloads.pro/search/?search=iasi |
| Full analysis: | https://app.any.run/tasks/f653ce57-cbf6-4626-b98f-7348c19691ae |
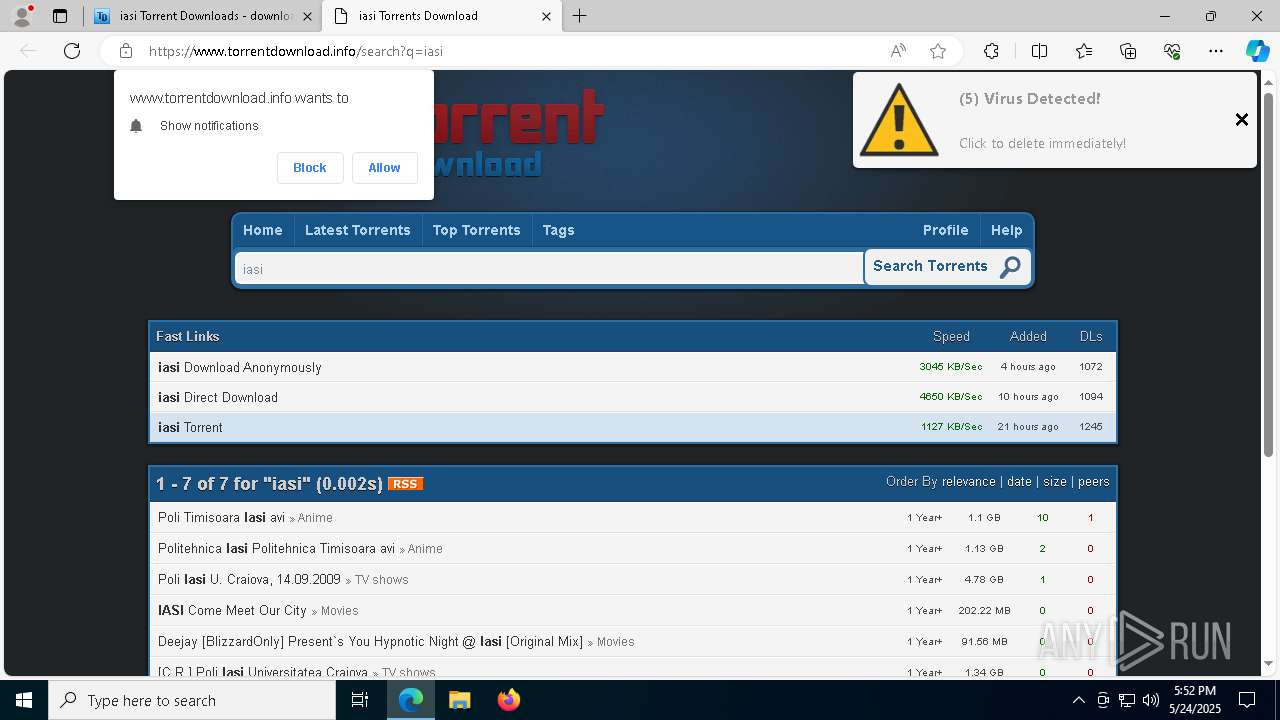
| Verdict: | Malicious activity |
| Threats: | IcedID is a banking trojan-type malware which allows attackers to utilize it to steal banking credentials of the victims. IcedID aka BokBot mainly targets businesses and steals payment information, it also acts as a loader and can deliver another viruses or download additional modules. |
| Analysis date: | May 24, 2025, 17:52:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AB2D9A2B5DC0A655BF8A4913871E12F1 |
| SHA1: | 870EE01CF5DD836D49676D4F81DAA42575420967 |
| SHA256: | 52E8B5133F86C8EFFEF418C6E1AC3738931319B0D7DBE998E93FB8A726852D57 |
| SSDEEP: | 3:N8DSL2XeBz4LX5JUWMn:2OLweBz25J0n |
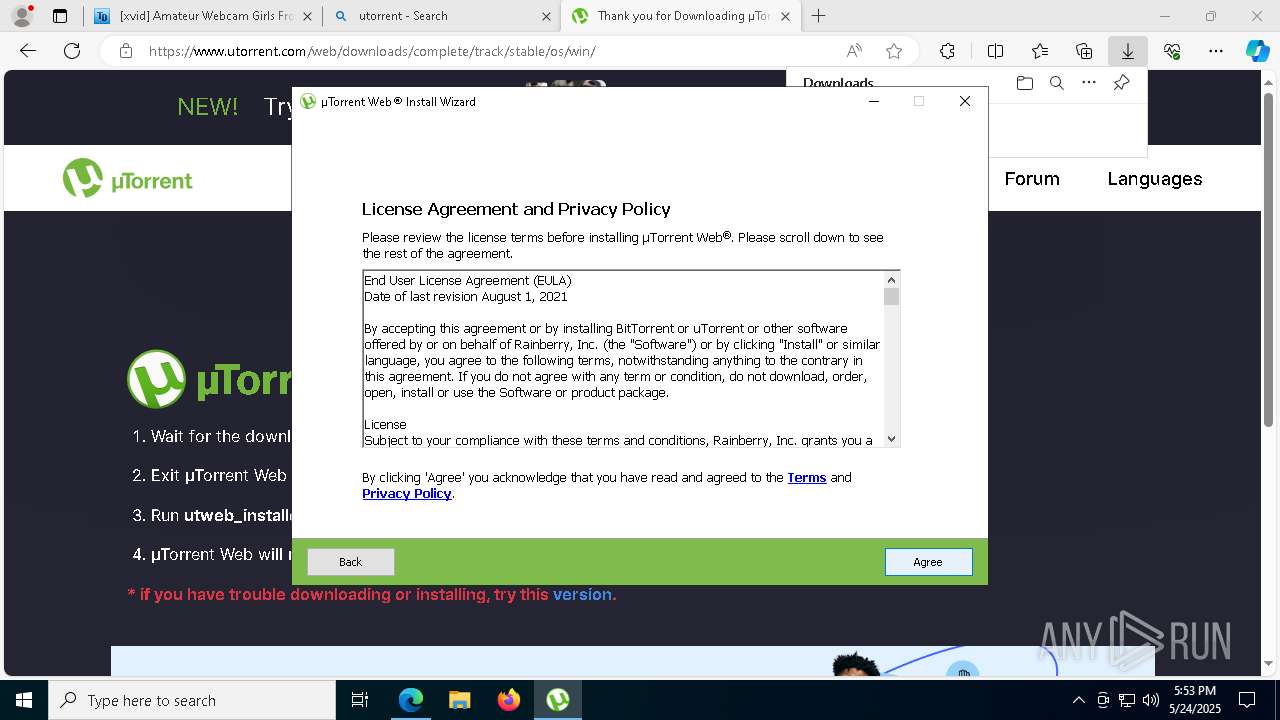
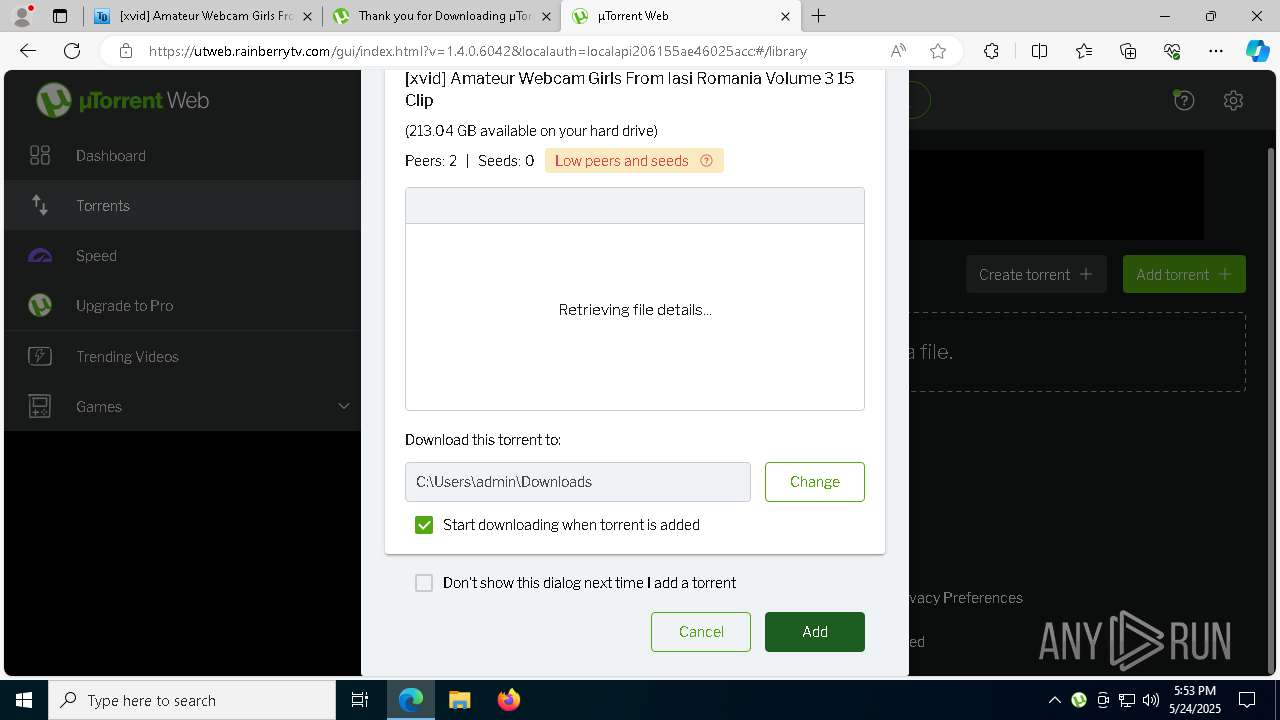
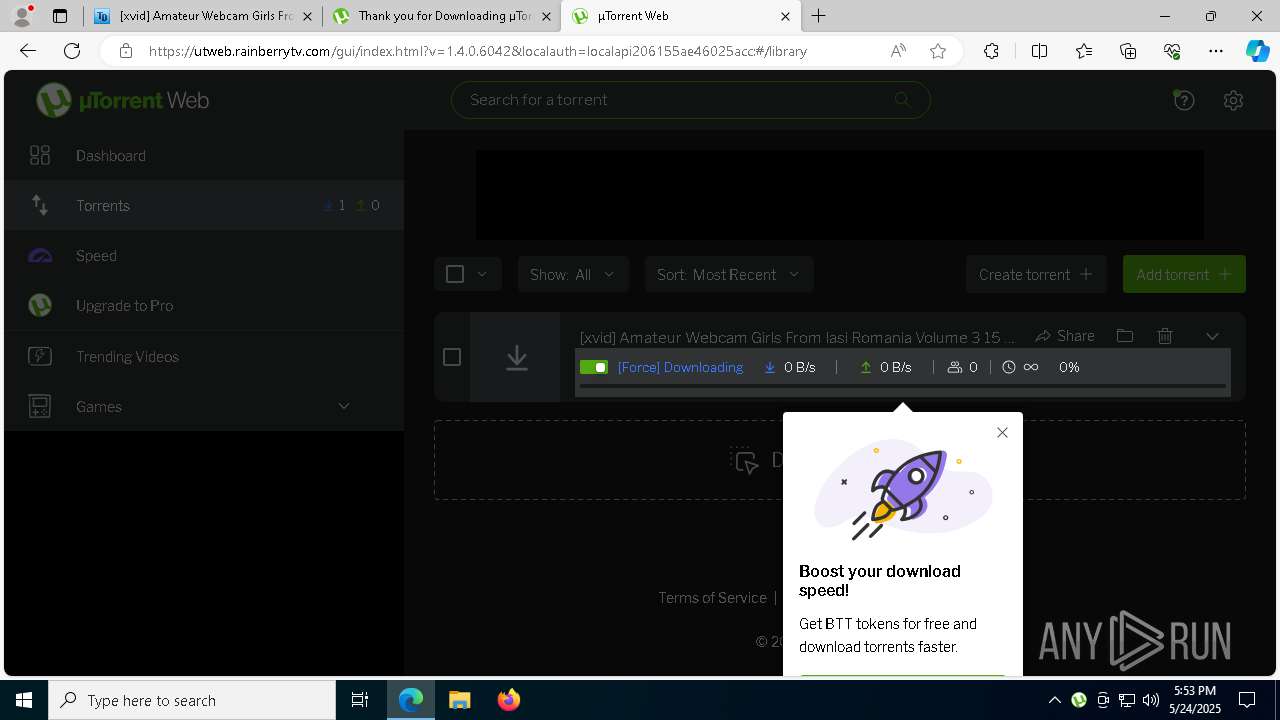
MALICIOUS
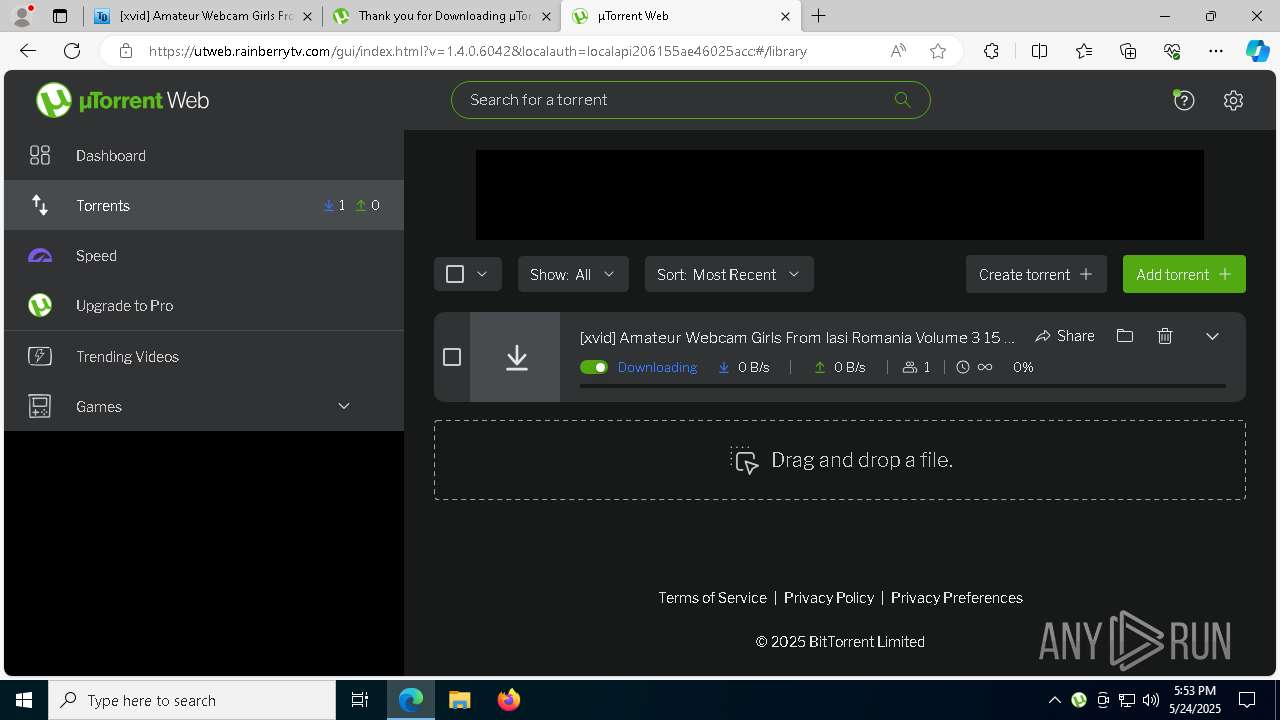
Changes the autorun value in the registry
- utweb.exe (PID: 3888)
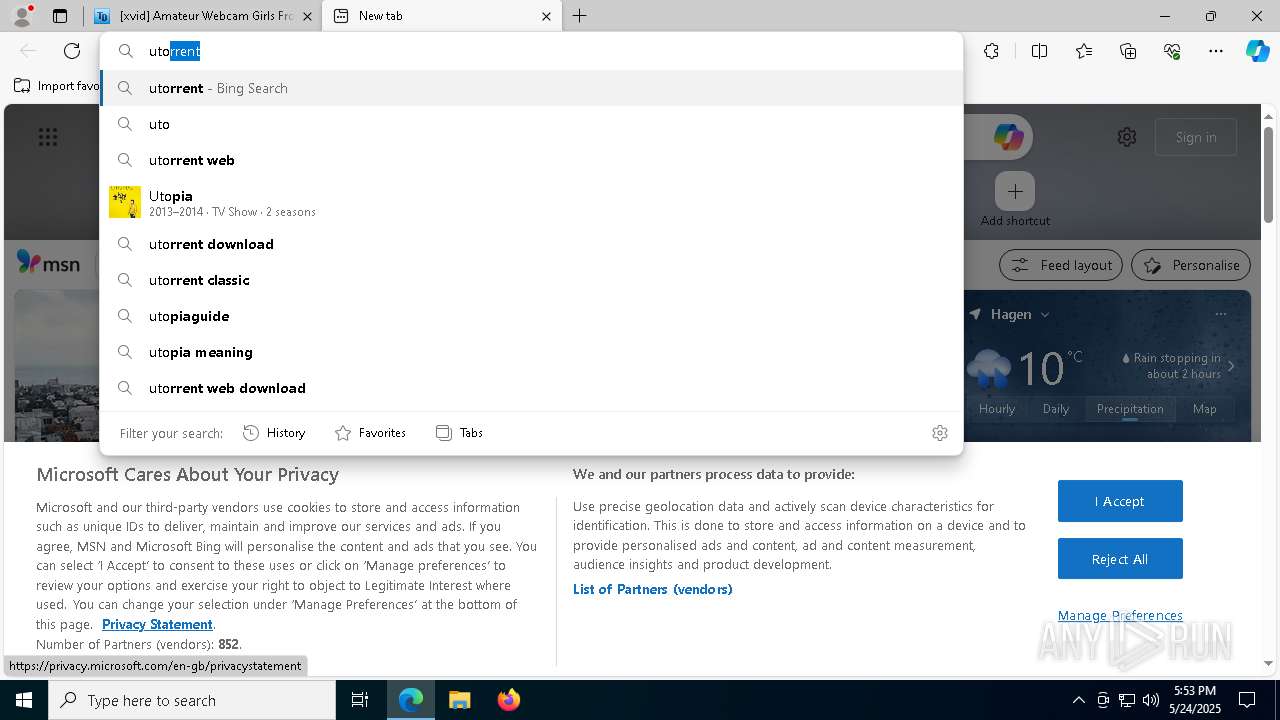
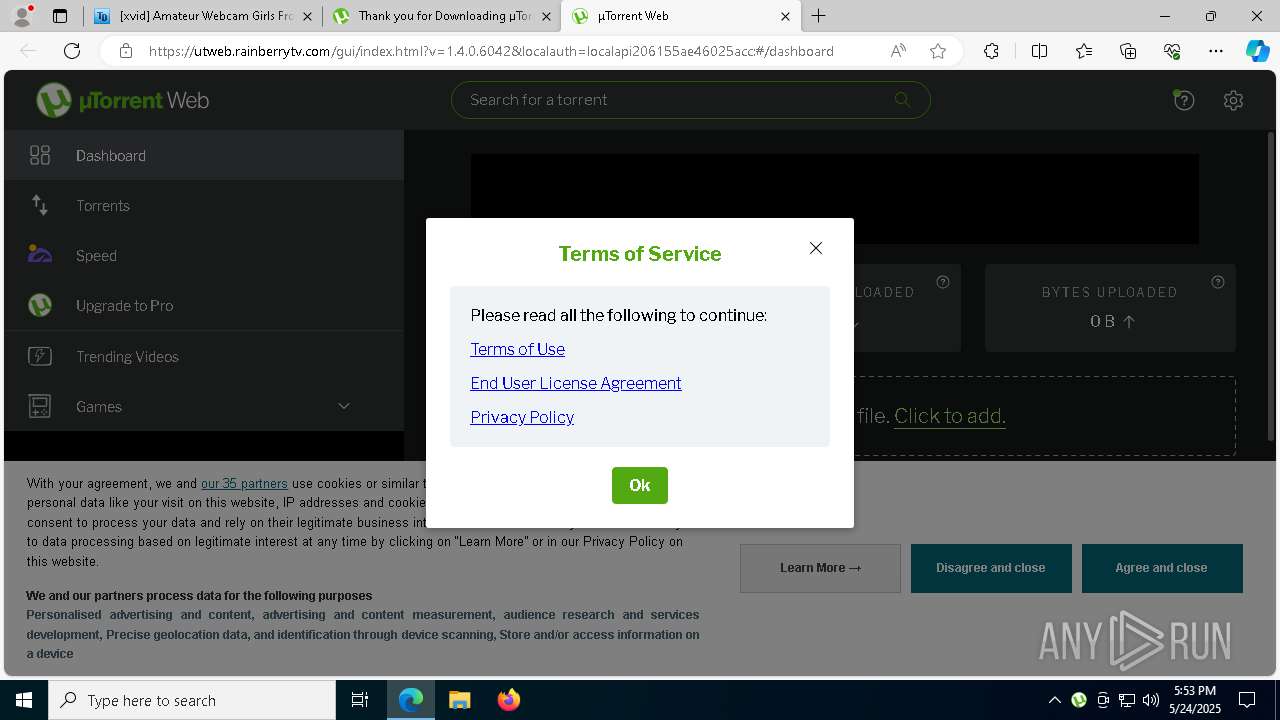
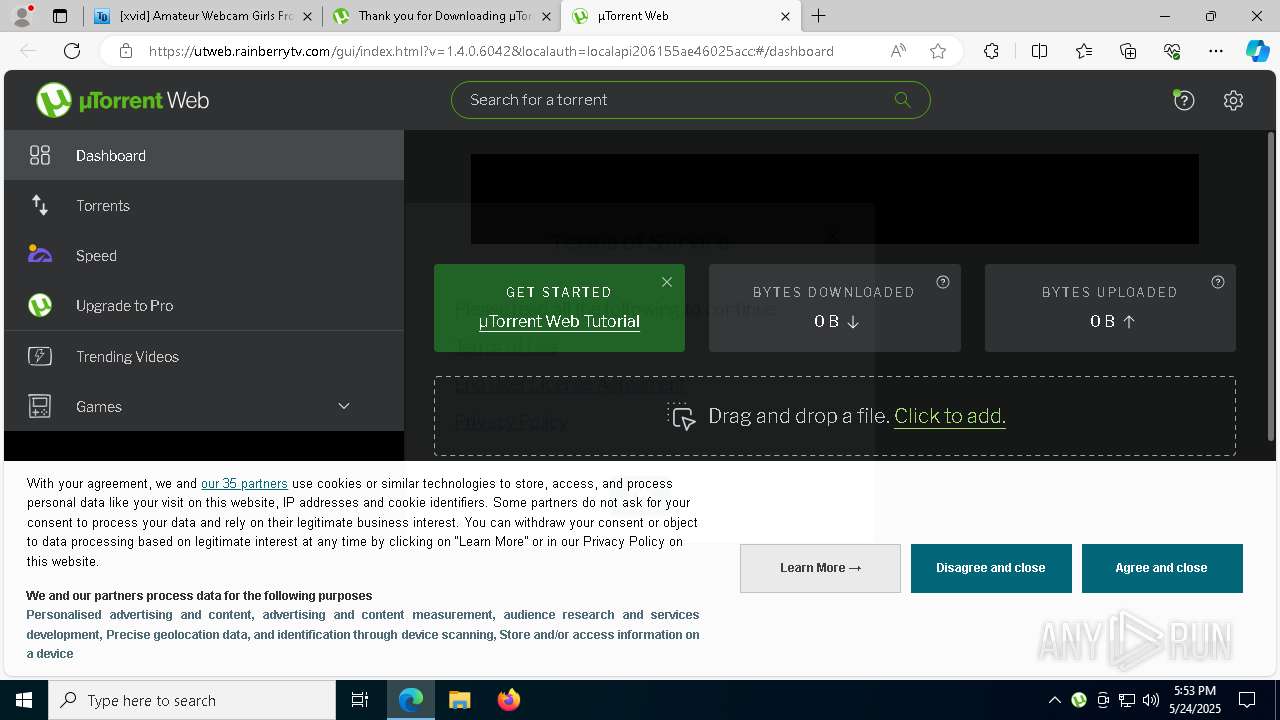
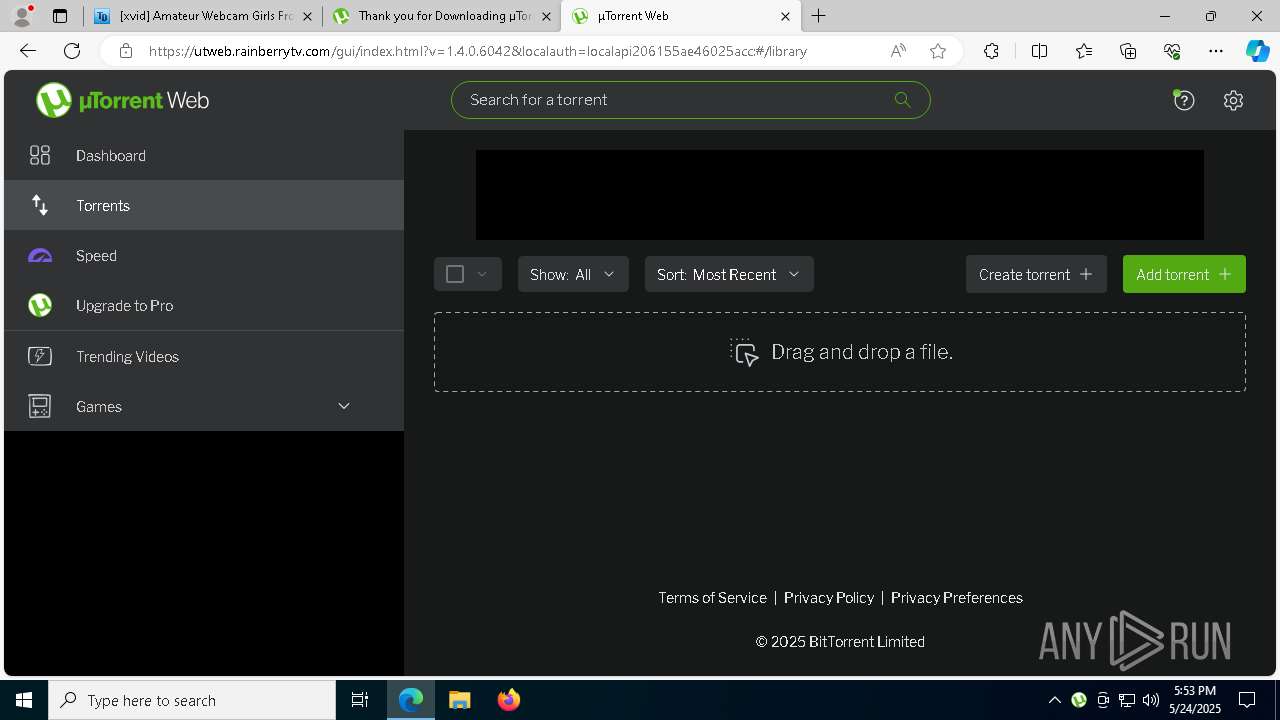
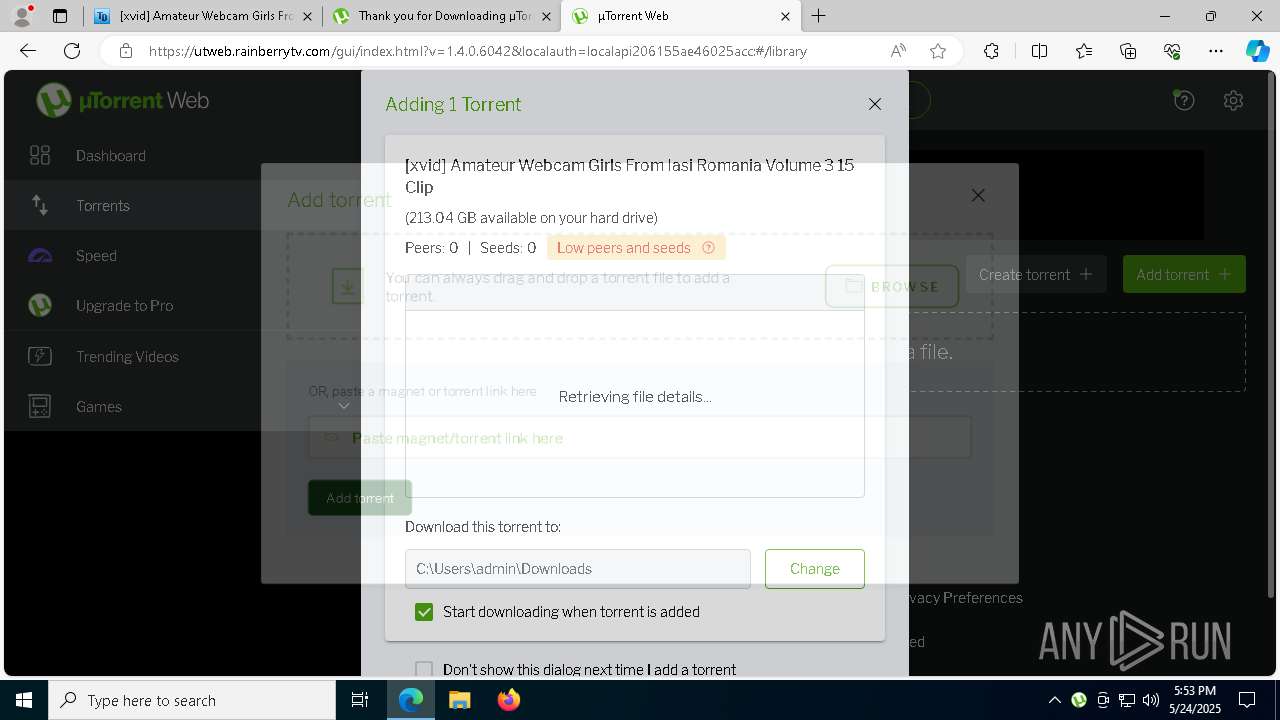
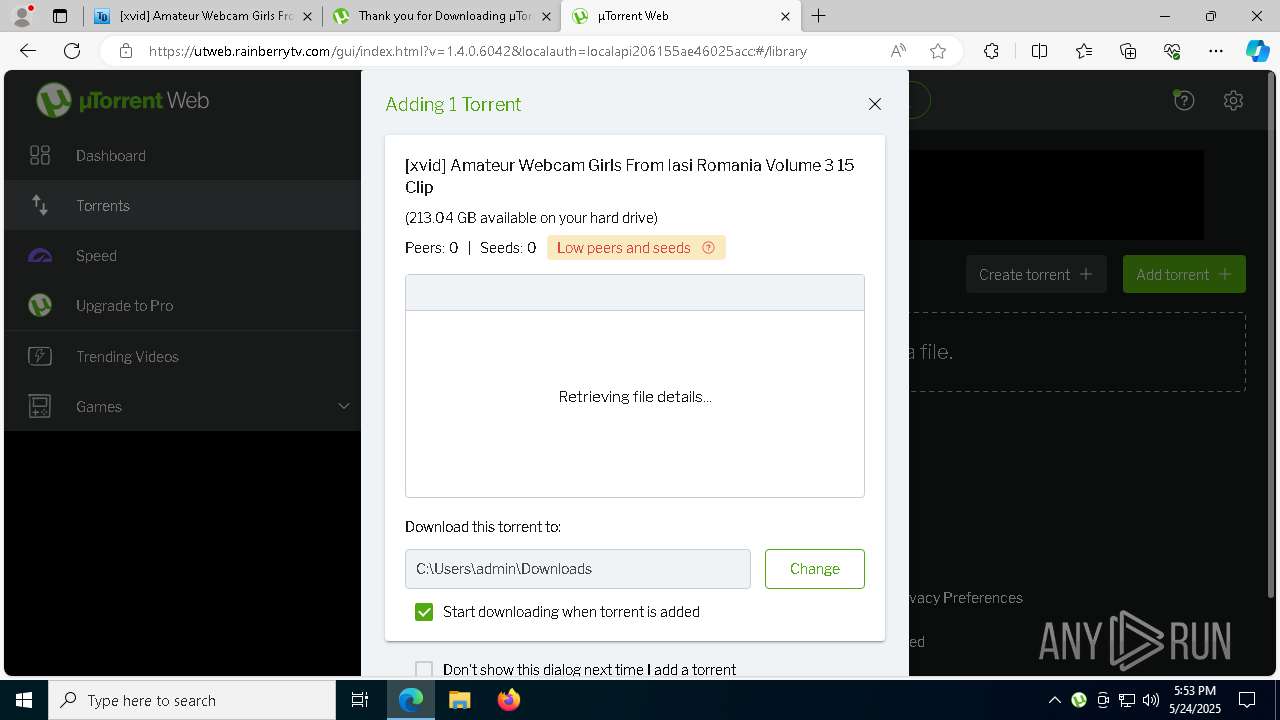
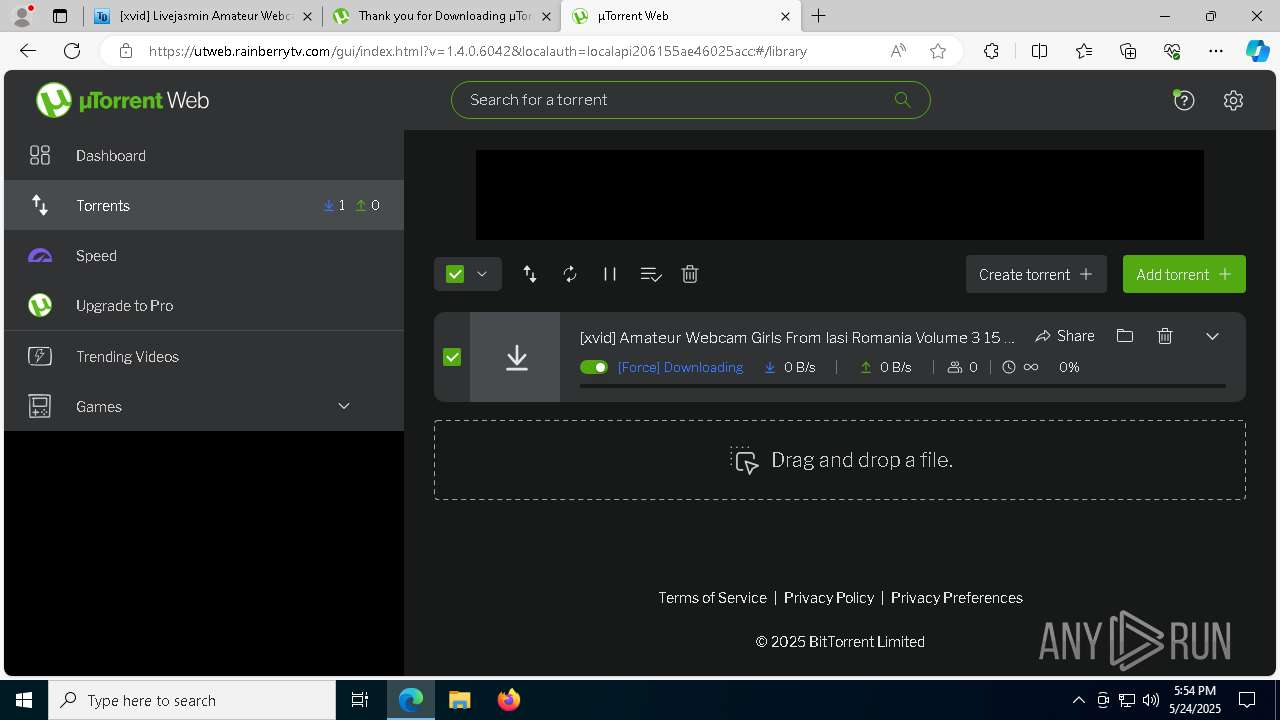
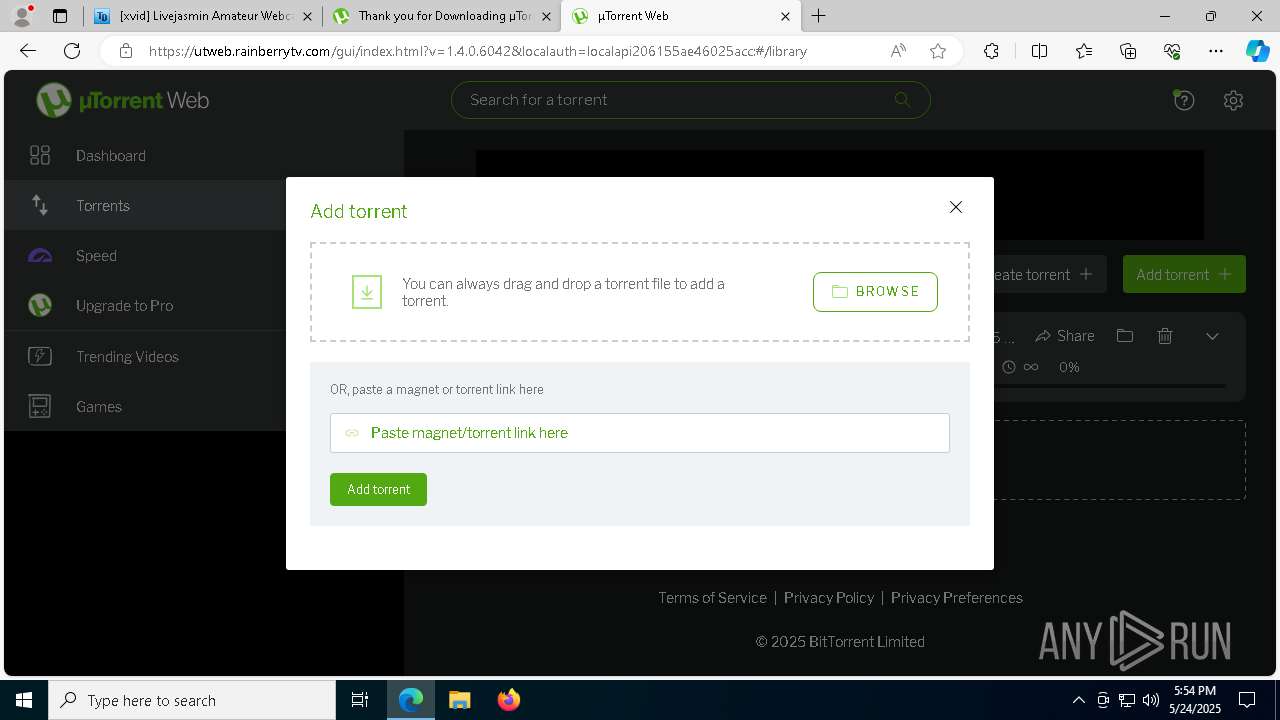
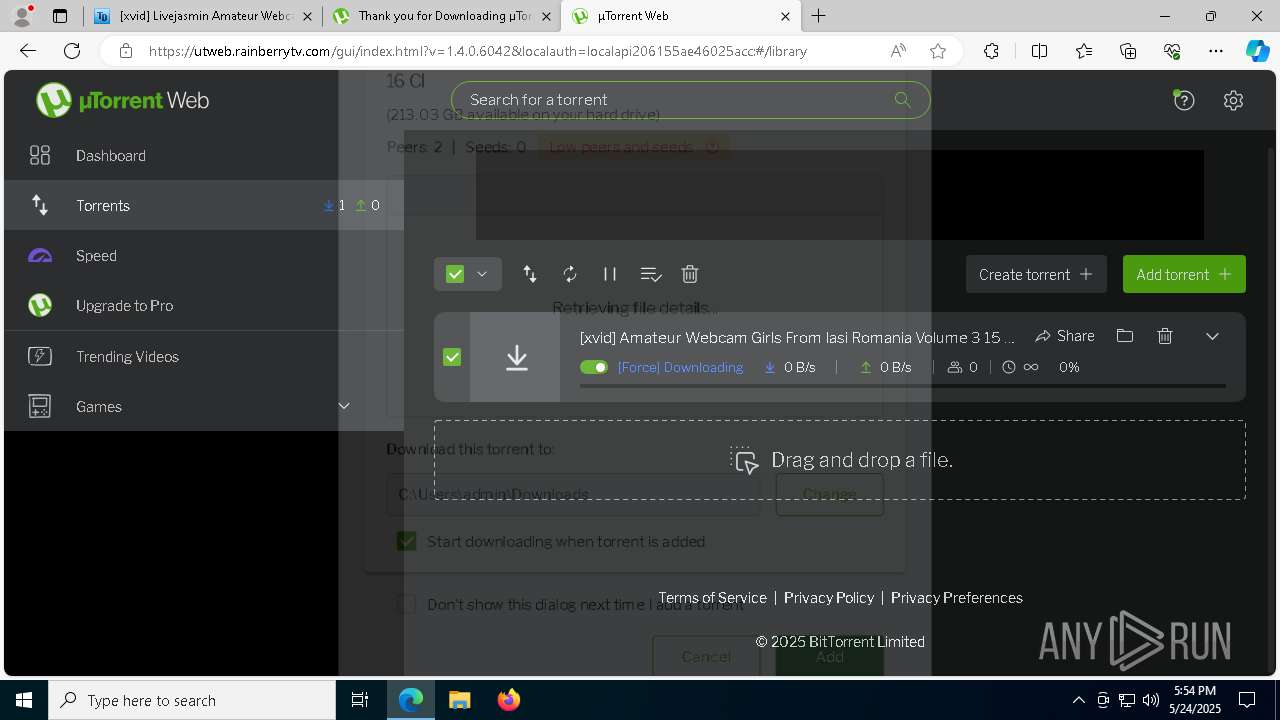
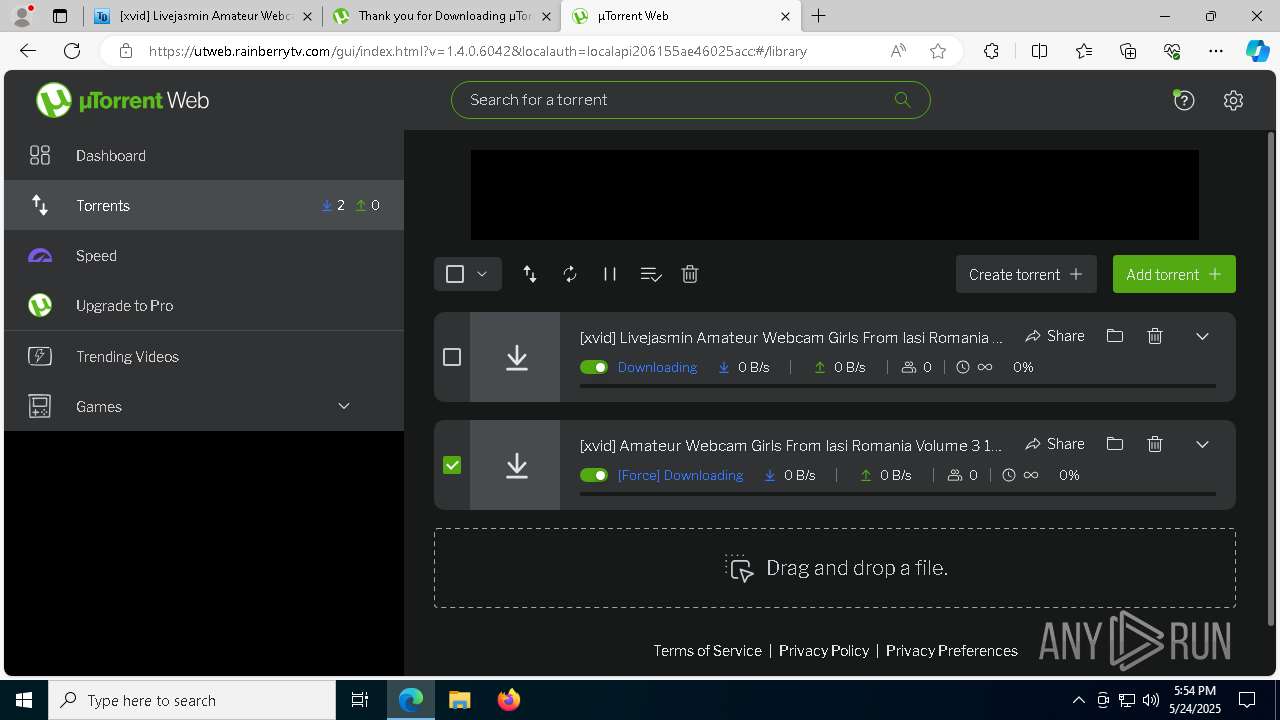
BITTORRENT has been detected (SURICATA)
- utweb.exe (PID: 3888)
ICEDID has been detected (YARA)
- servicehost.exe (PID: 6640)
- uihost.exe (PID: 4996)
SUSPICIOUS
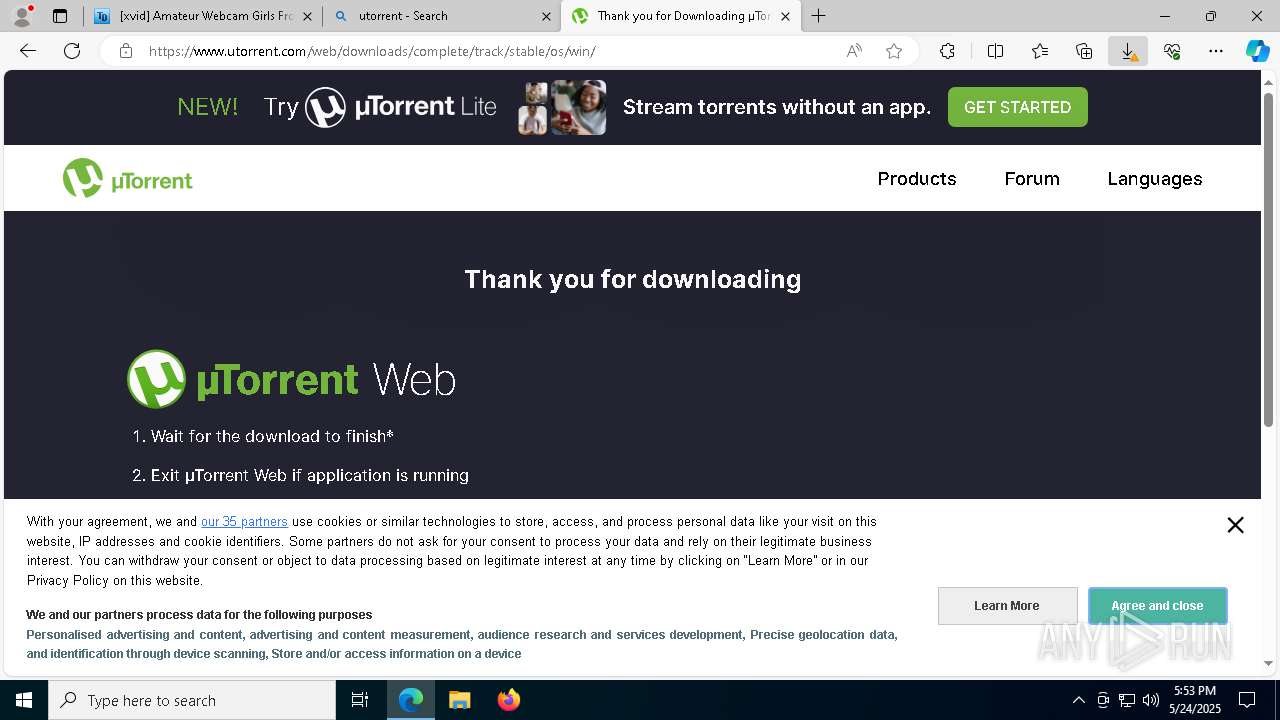
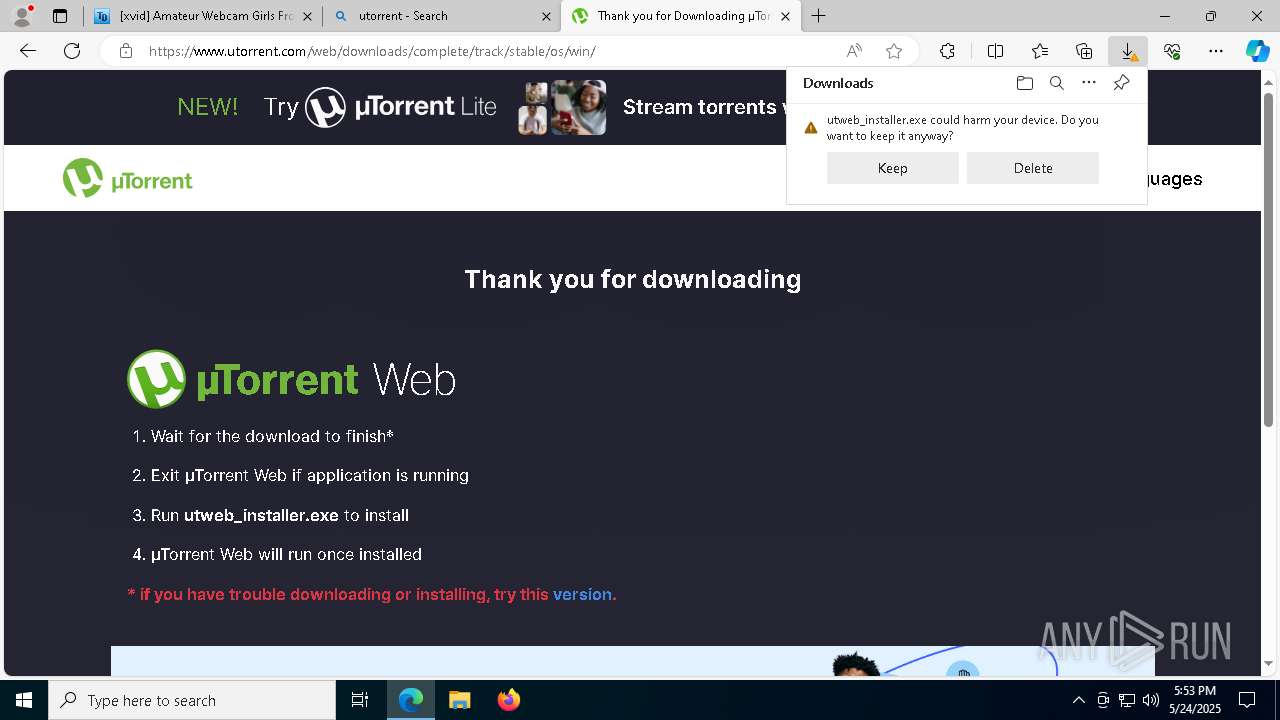
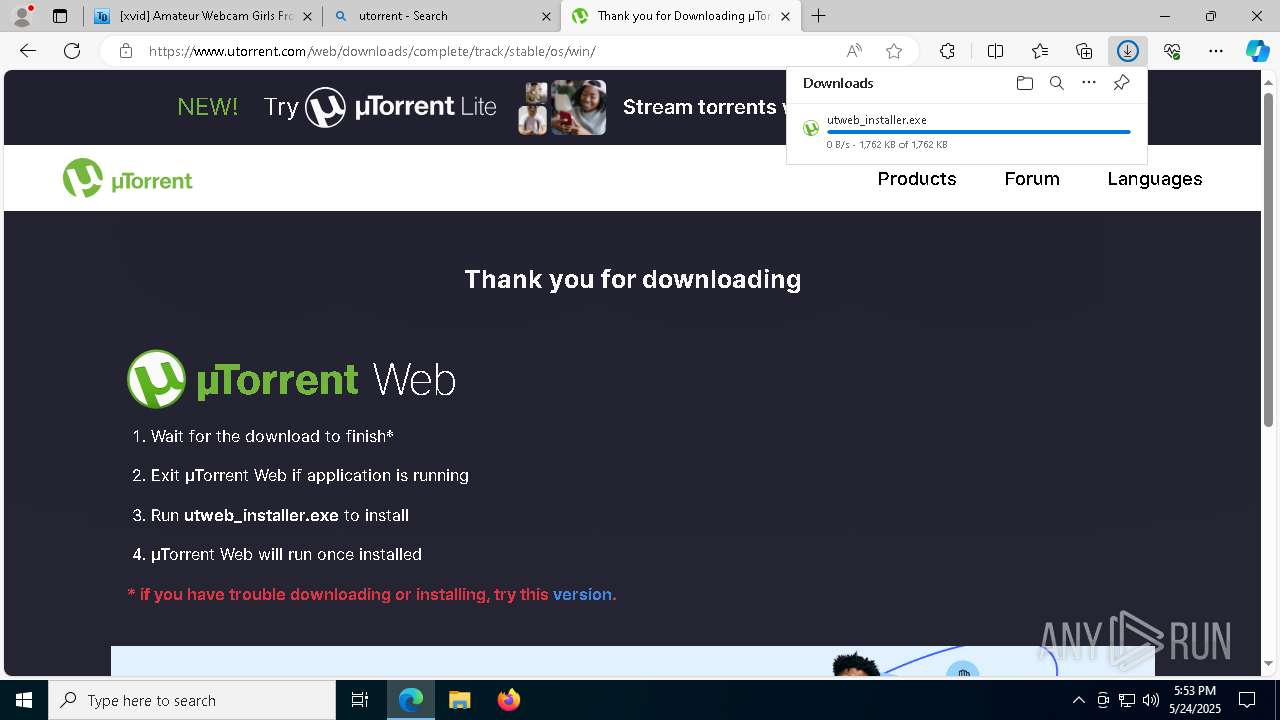
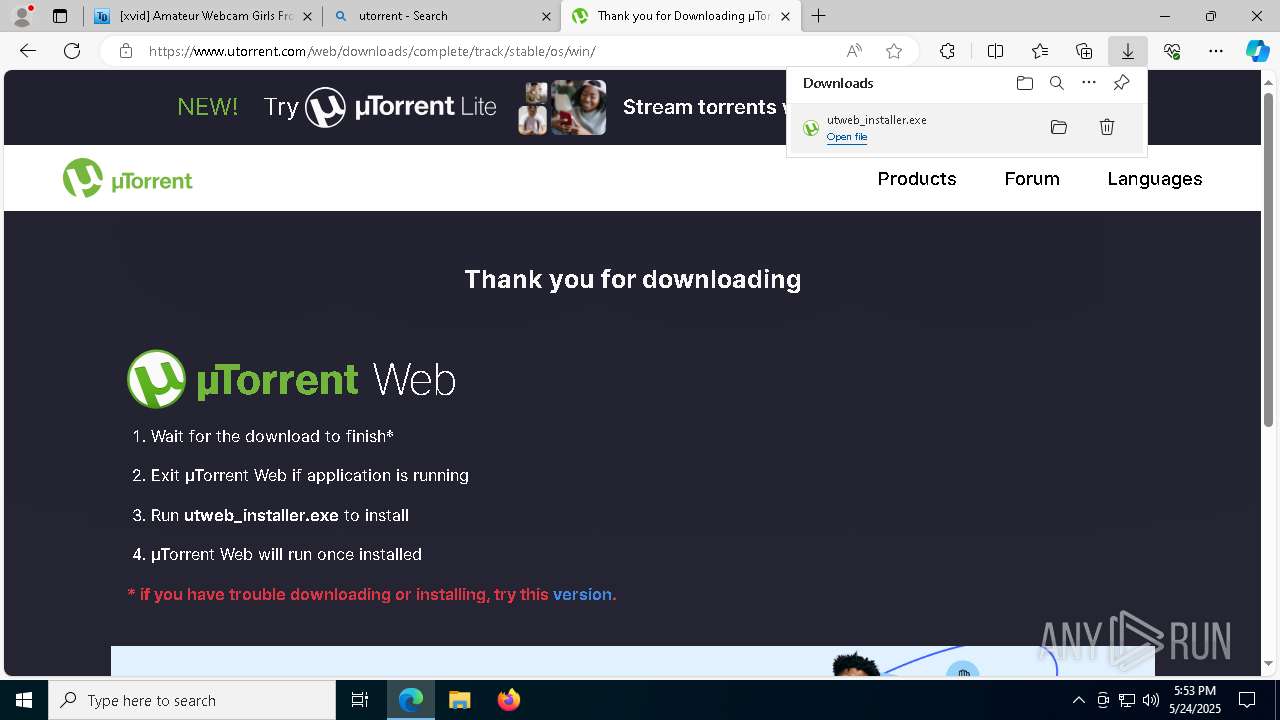
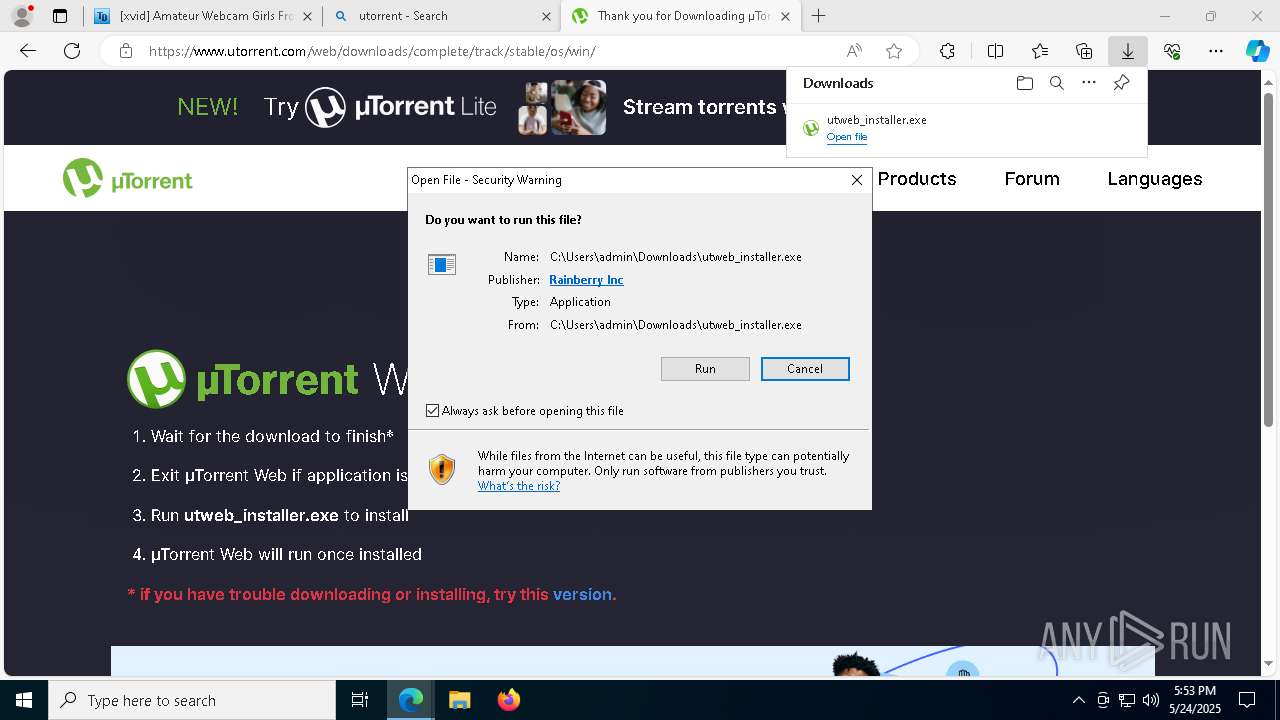
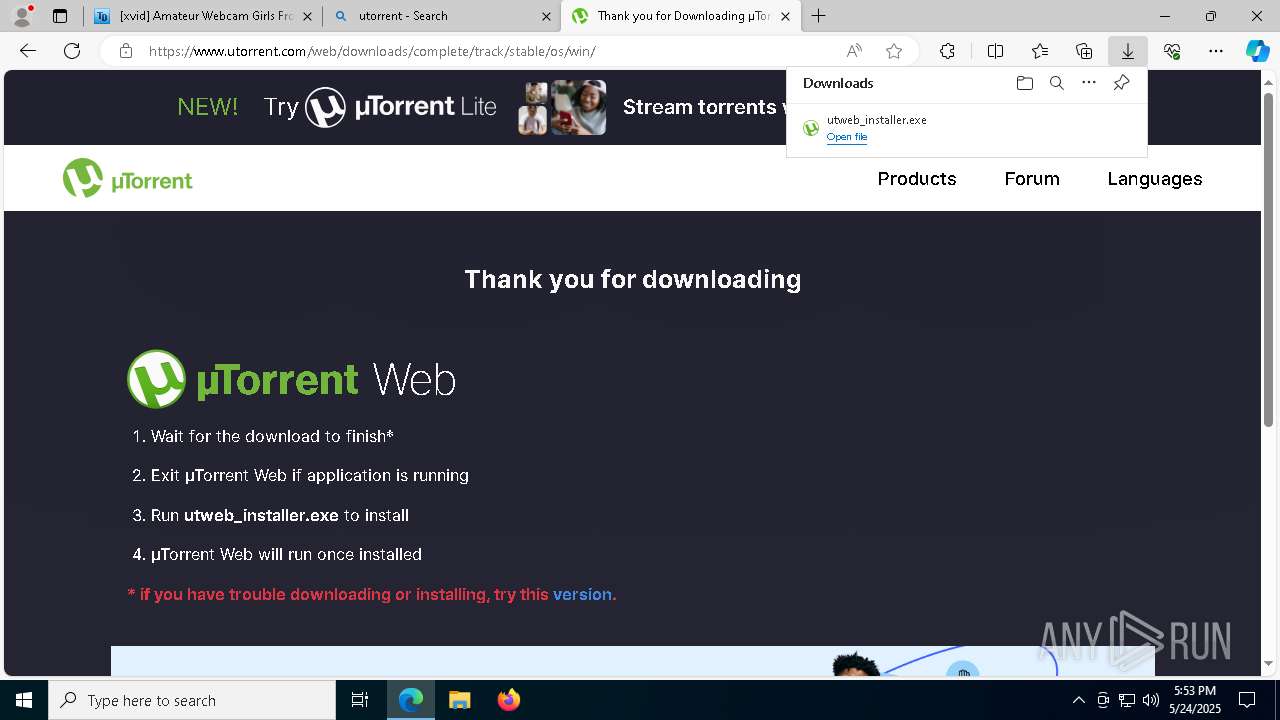
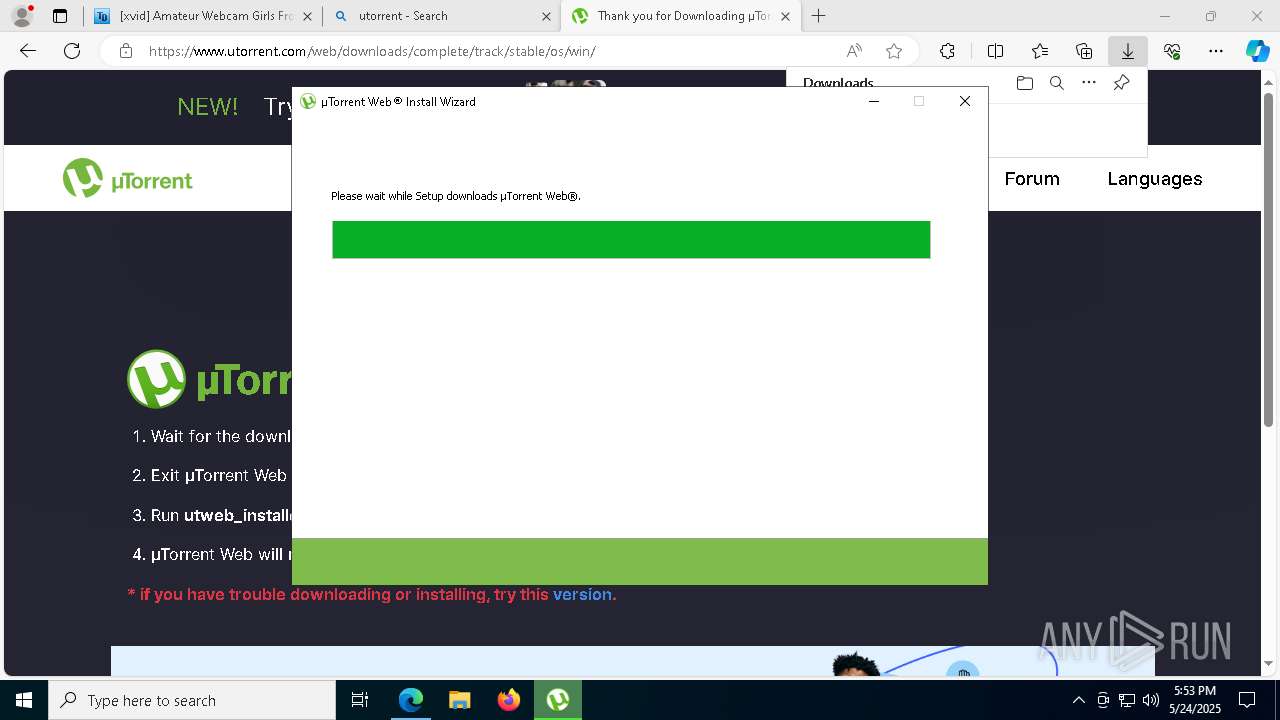
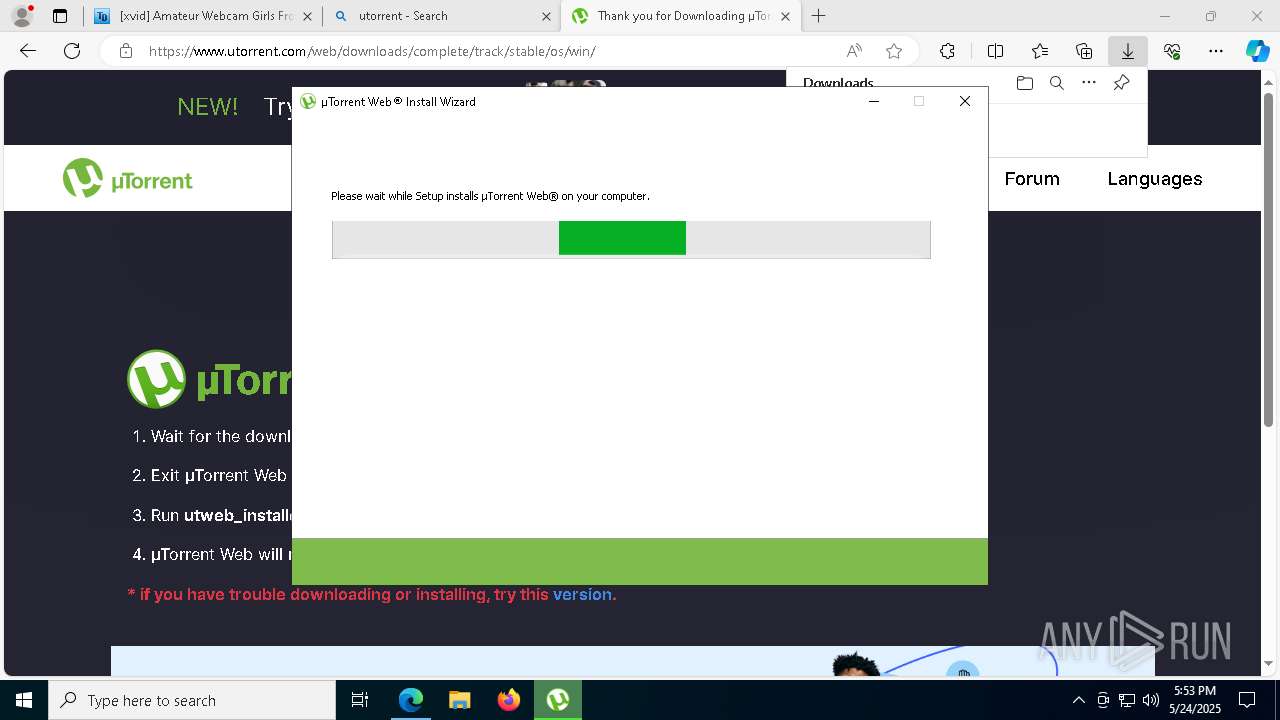
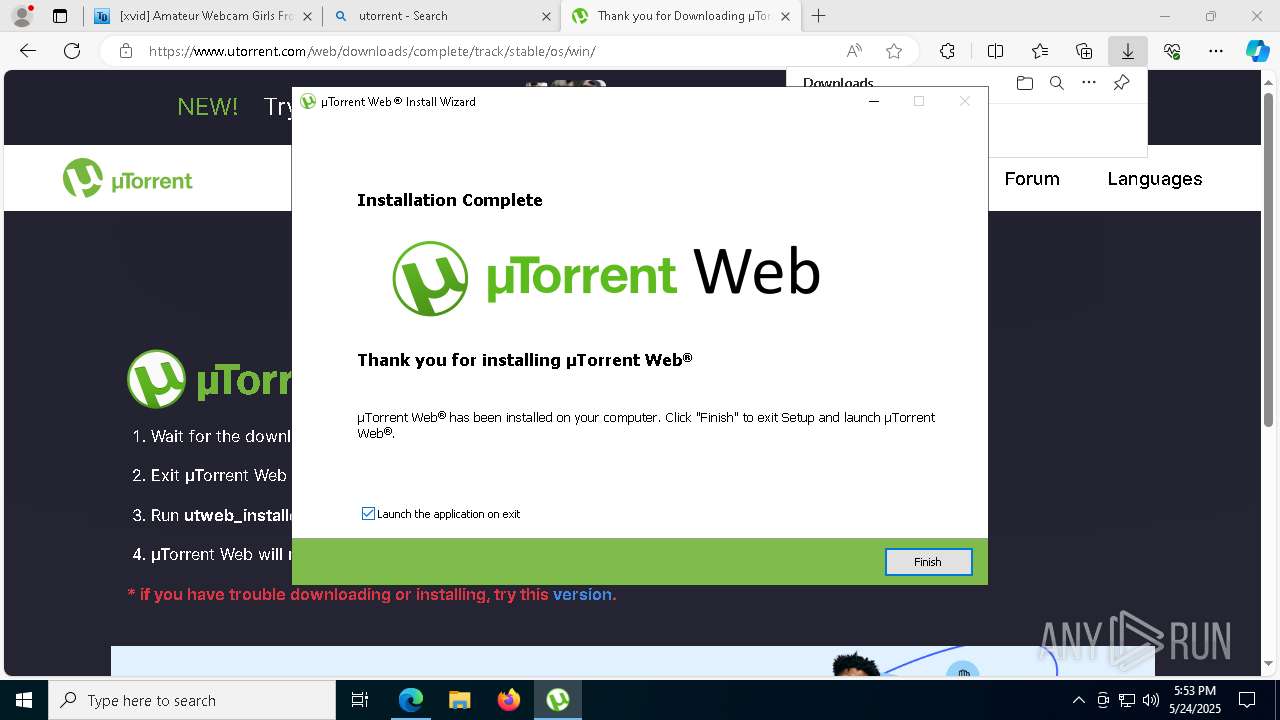
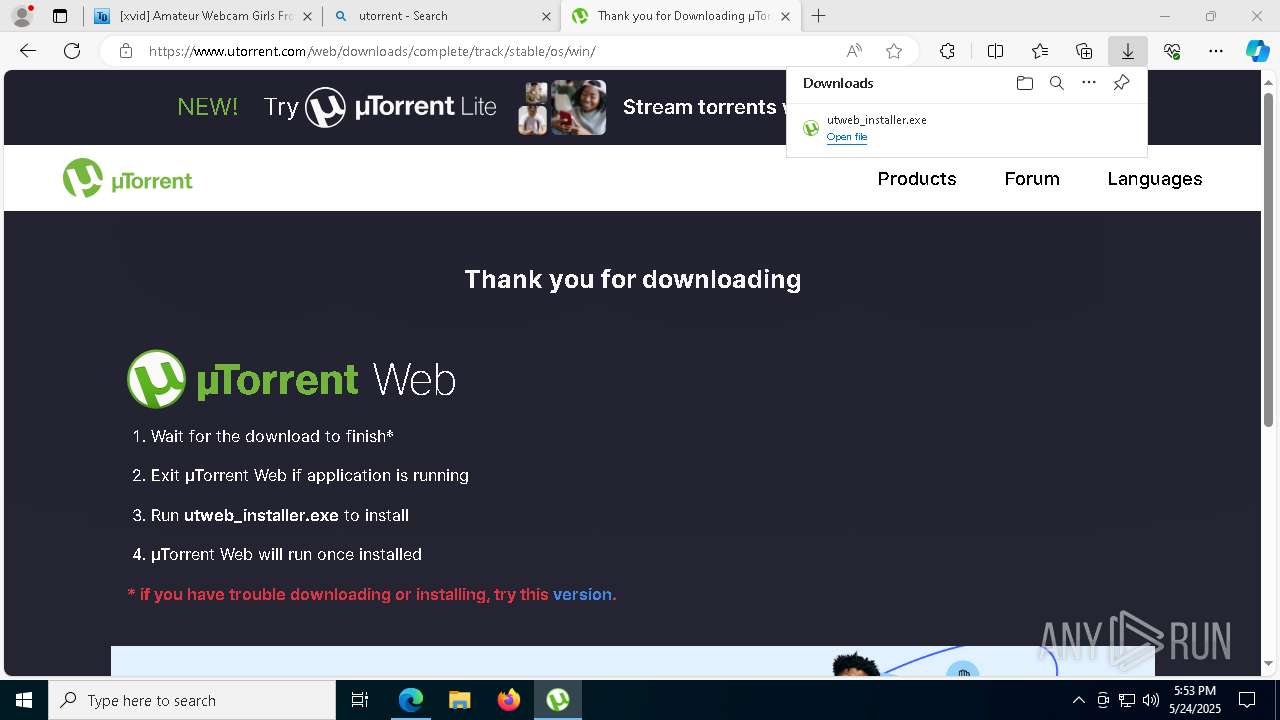
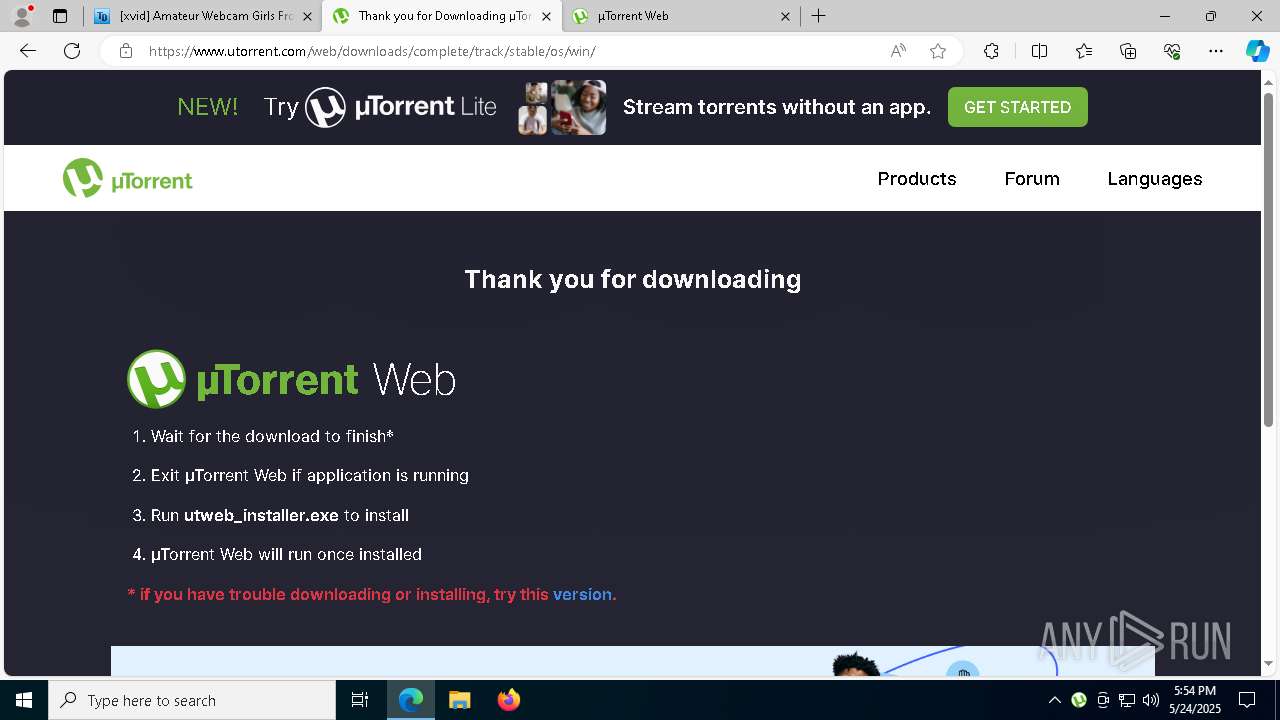
Executable content was dropped or overwritten
- utweb_installer.exe (PID: 7864)
- utweb_installer.exe (PID: 5744)
- utweb_installer.tmp (PID: 7544)
- saBSI.exe (PID: 2104)
- utweb_installer.exe (PID: 7832)
- saBSI.exe (PID: 5428)
- installer.exe (PID: 8828)
- utweb.exe (PID: 3888)
- installer.exe (PID: 8736)
Reads security settings of Internet Explorer
- utweb_installer.tmp (PID: 6136)
- utweb_installer.tmp (PID: 7544)
- saBSI.exe (PID: 2104)
- utweb_installer.exe (PID: 7832)
- utweb.exe (PID: 3888)
Mutex name with non-standard characters
- utweb_installer.tmp (PID: 7544)
The process creates files with name similar to system file names
- utweb_installer.exe (PID: 7832)
Malware-specific behavior (creating "System.dll" in Temp)
- utweb_installer.exe (PID: 7832)
Reads the Windows owner or organization settings
- utweb_installer.tmp (PID: 7544)
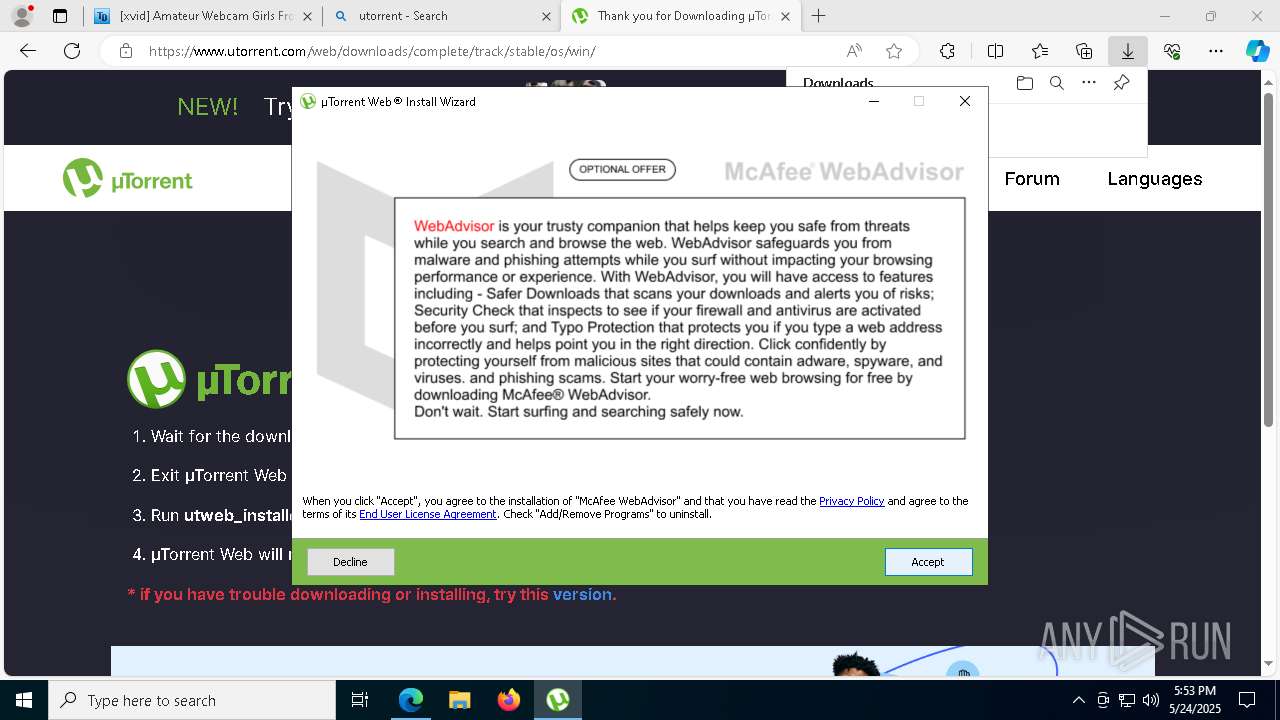
Adds/modifies Windows certificates
- saBSI.exe (PID: 2104)
Process drops legitimate windows executable
- installer.exe (PID: 8828)
Connects to unusual port
- utweb.exe (PID: 3888)
Executes as Windows Service
- servicehost.exe (PID: 6640)
Starts CMD.EXE for commands execution
- updater.exe (PID: 9108)
Potential Corporate Privacy Violation
- utweb.exe (PID: 3888)
There is functionality for taking screenshot (YARA)
- uihost.exe (PID: 4996)
INFO
Application launched itself
- msedge.exe (PID: 4400)
Reads the computer name
- identity_helper.exe (PID: 7780)
- utweb_installer.tmp (PID: 6136)
- utweb_installer.tmp (PID: 7544)
- saBSI.exe (PID: 2104)
- utweb_installer.exe (PID: 7832)
- saBSI.exe (PID: 5428)
- utweb.exe (PID: 3888)
Reads Environment values
- identity_helper.exe (PID: 7780)
Checks supported languages
- identity_helper.exe (PID: 7780)
- utweb_installer.exe (PID: 7864)
- utweb_installer.tmp (PID: 6136)
- utweb_installer.exe (PID: 5744)
- utweb_installer.exe (PID: 7832)
- utweb_installer.tmp (PID: 7544)
- saBSI.exe (PID: 2104)
- utweb.exe (PID: 3888)
- saBSI.exe (PID: 5428)
Executable content was dropped or overwritten
- msedge.exe (PID: 7176)
- msedge.exe (PID: 4400)
- msedge.exe (PID: 5392)
Create files in a temporary directory
- utweb_installer.exe (PID: 7864)
- utweb_installer.exe (PID: 5744)
- utweb_installer.tmp (PID: 7544)
- utweb_installer.exe (PID: 7832)
Process checks computer location settings
- utweb_installer.tmp (PID: 6136)
- utweb_installer.tmp (PID: 7544)
The sample compiled with russian language support
- utweb_installer.tmp (PID: 7544)
Reads the machine GUID from the registry
- utweb_installer.tmp (PID: 7544)
- saBSI.exe (PID: 2104)
- saBSI.exe (PID: 5428)
- utweb.exe (PID: 3888)
Reads the software policy settings
- utweb_installer.tmp (PID: 7544)
- saBSI.exe (PID: 2104)
- saBSI.exe (PID: 5428)
Checks proxy server information
- utweb_installer.tmp (PID: 7544)
- saBSI.exe (PID: 2104)
- utweb_installer.exe (PID: 7832)
Creates files or folders in the user directory
- utweb_installer.exe (PID: 7832)
- utweb.exe (PID: 3888)
The sample compiled with english language support
- utweb_installer.exe (PID: 7832)
- utweb_installer.tmp (PID: 7544)
- saBSI.exe (PID: 2104)
- installer.exe (PID: 8828)
- msedge.exe (PID: 5392)
- utweb.exe (PID: 3888)
- installer.exe (PID: 8736)
Creates files in the program directory
- saBSI.exe (PID: 2104)
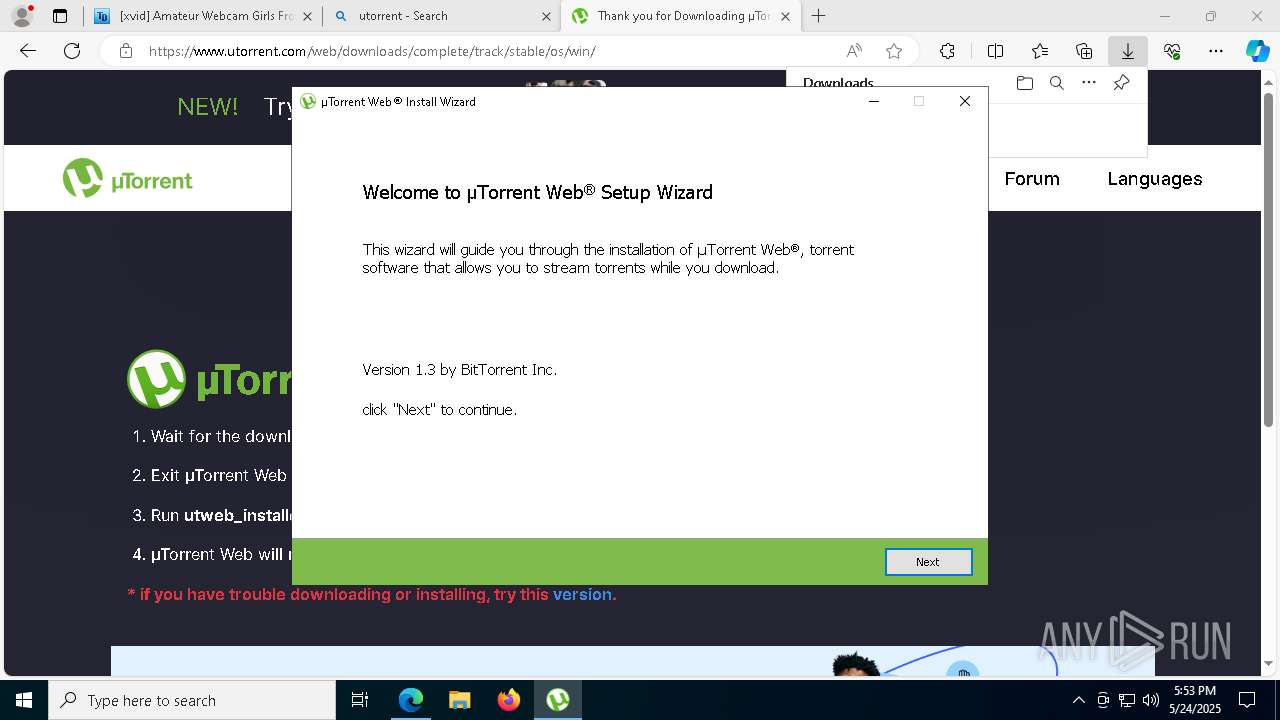
Detects InnoSetup installer (YARA)
- utweb_installer.exe (PID: 7864)
- utweb_installer.tmp (PID: 6136)
Compiled with Borland Delphi (YARA)
- utweb_installer.exe (PID: 7864)
- utweb_installer.tmp (PID: 6136)
Creates a software uninstall entry
- utweb_installer.exe (PID: 7832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
231
Monitored processes
87
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --mojo-platform-channel-handle=7340 --field-trial-handle=2264,i,9338499332168038278,14885238469909386034,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | ||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7568 --field-trial-handle=2264,i,9338499332168038278,14885238469909386034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6672 --field-trial-handle=2264,i,9338499332168038278,14885238469909386034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 2104 | "C:\Users\admin\AppData\Local\Temp\is-A4MO5.tmp\component0_extract\saBSI.exe" /affid 91082 PaidDistribution=true CountryCode=DE | C:\Users\admin\AppData\Local\Temp\is-A4MO5.tmp\component0_extract\saBSI.exe | utweb_installer.tmp | |
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee WebAdvisor(bootstrap installer) Exit code: 0 Version: 4,1,1,865 | ||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 2244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2260 --field-trial-handle=2264,i,9338499332168038278,14885238469909386034,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | ||||
| 2432 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | ||||
| 2560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6608 --field-trial-handle=2264,i,9338499332168038278,14885238469909386034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 2652 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6032 --field-trial-handle=2264,i,9338499332168038278,14885238469909386034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 3192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6764 --field-trial-handle=2264,i,9338499332168038278,14885238469909386034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
108
Suspicious files
1 407
Text files
1 014
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a673.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a6a2.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a6b2.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF10a70f.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:6971E42ED64D2BE125547F021EB852B1 | SHA256:B46CFDC4106DF566F71AA34D6F10B53767C561DFD17DD07A5930A18E67BB344B | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a71f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
661
DNS requests
364
Threats
52
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5596 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4400 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5596 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4400 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA74MnP04YNx7ulsojvPs3Y%3D | unknown | — | — | whitelisted |
4400 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7832 | utweb_installer.exe | POST | 200 | 54.172.53.136:80 | http://i-4101.b-6042.utweb.bench.utorrent.com/e?i=4101 | unknown | — | — | whitelisted |
7832 | utweb_installer.exe | POST | 200 | 54.172.53.136:80 | http://i-4101.b-6042.utweb.bench.utorrent.com/e?i=4101 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5796 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1472 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4400 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7176 | msedge.exe | 172.67.70.47:443 | www.torrentdownloads.pro | CLOUDFLARENET | US | unknown |
7176 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7176 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.torrentdownloads.pro |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7176 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
7176 | msedge.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL Certificate for Suspicious TLD (.top) |
7176 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
7176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7176 | msedge.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL Certificate for Suspicious TLD (.top) |
7176 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
7176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |