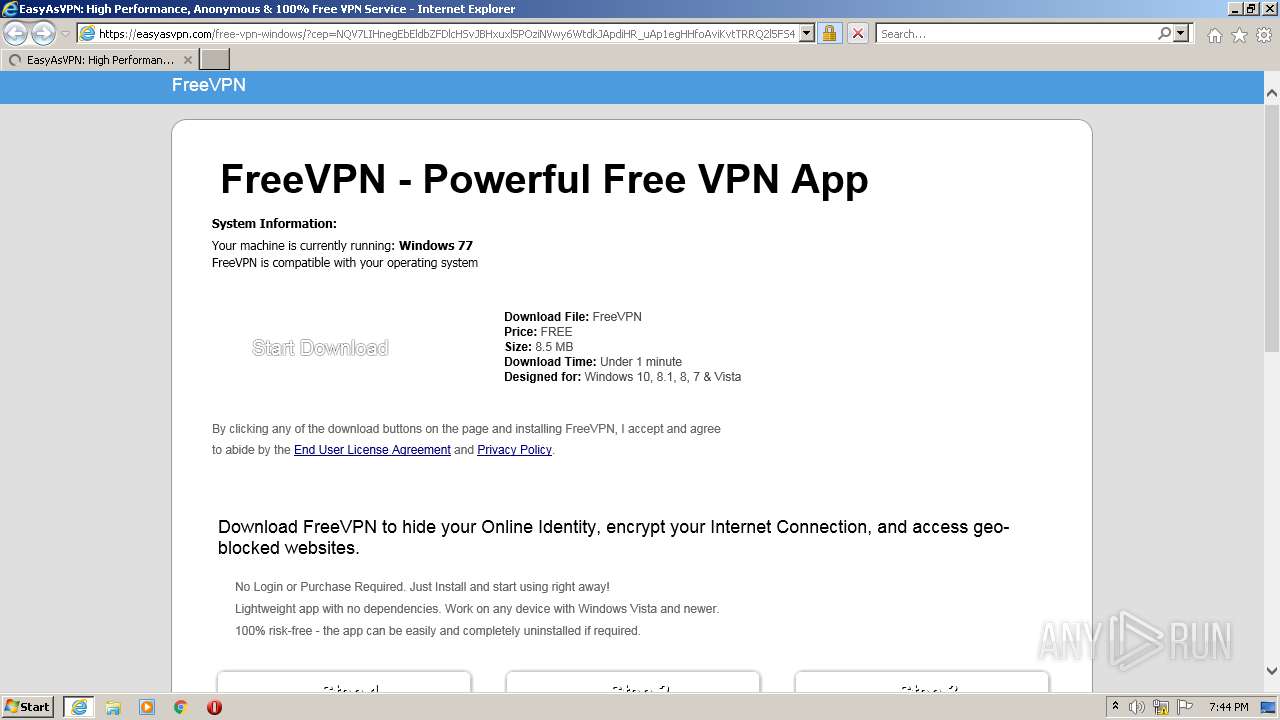
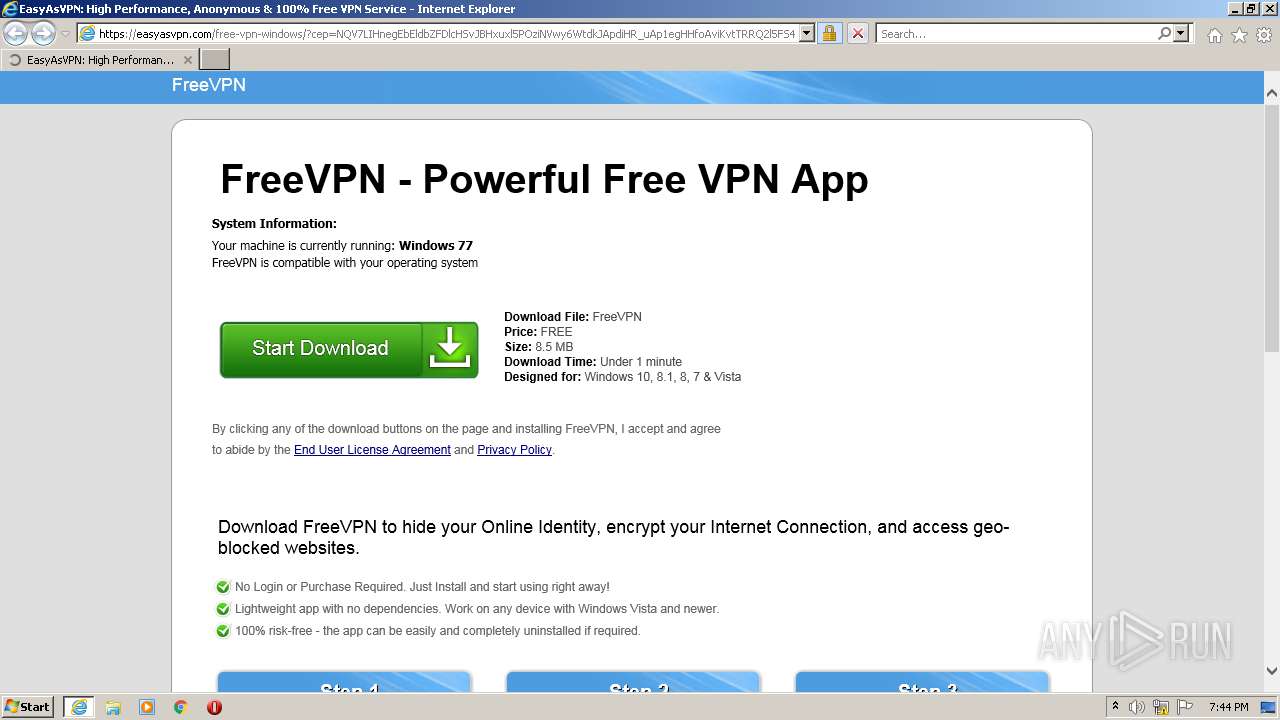
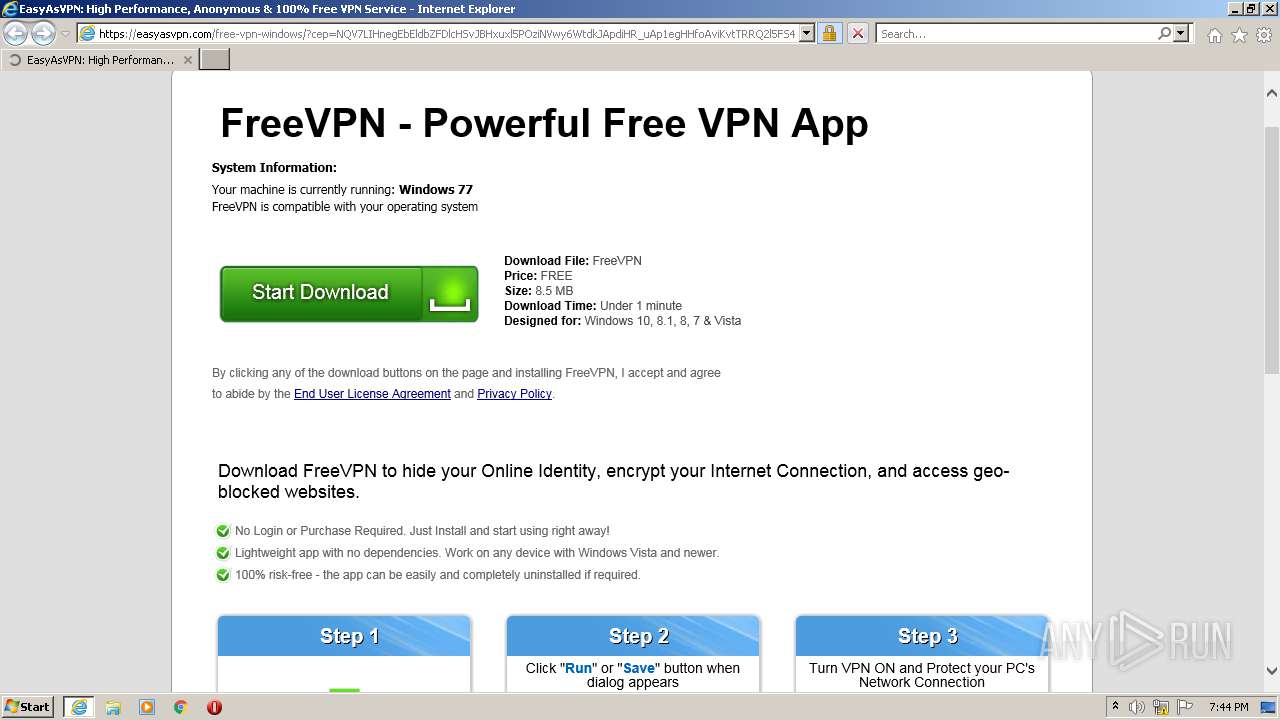
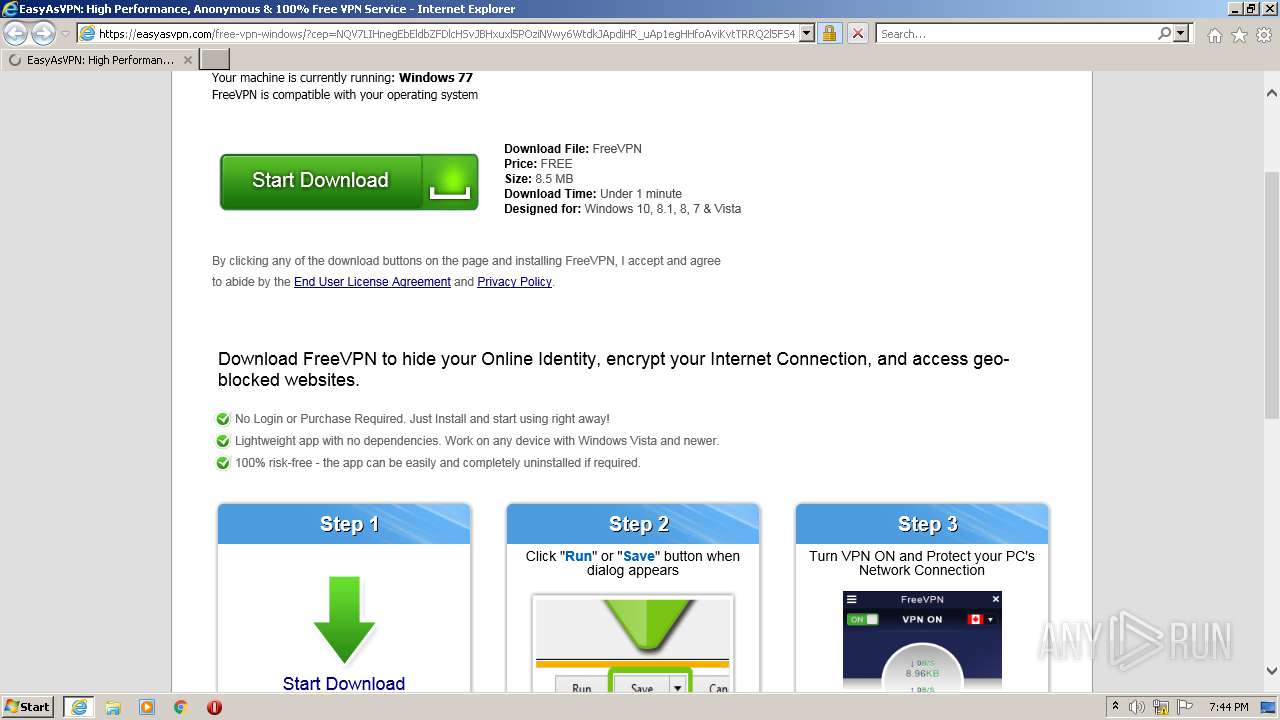
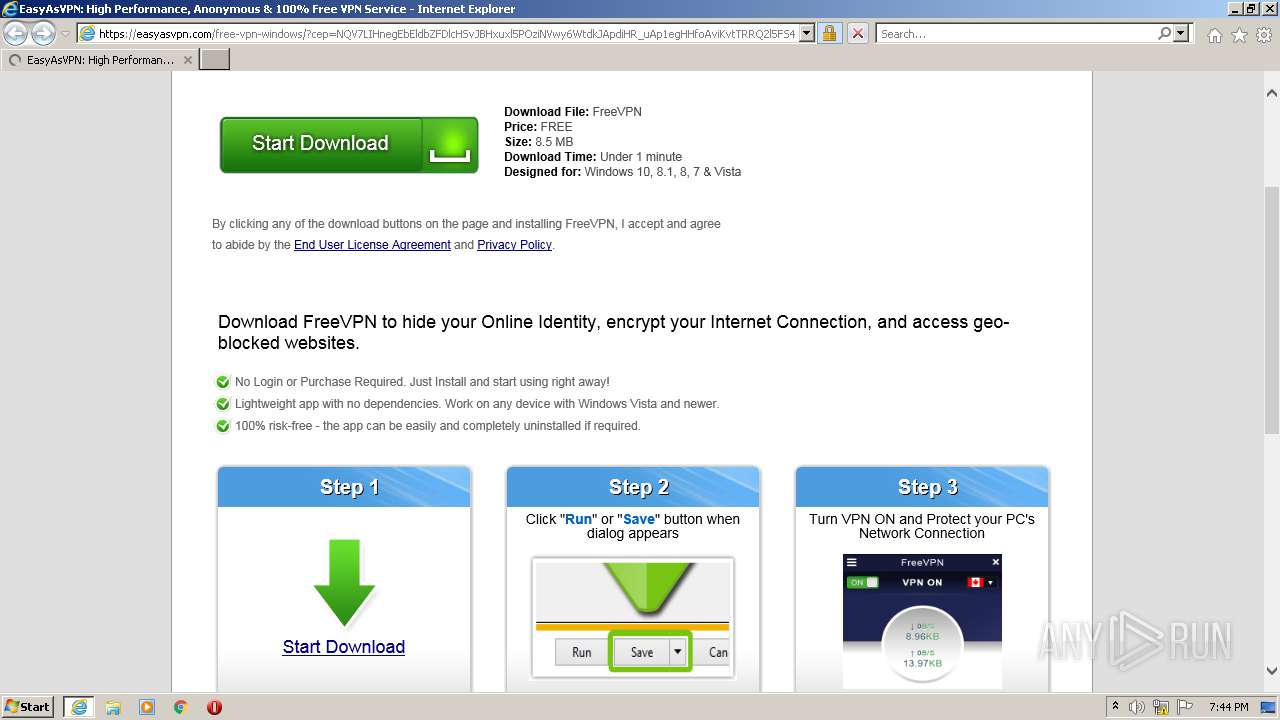
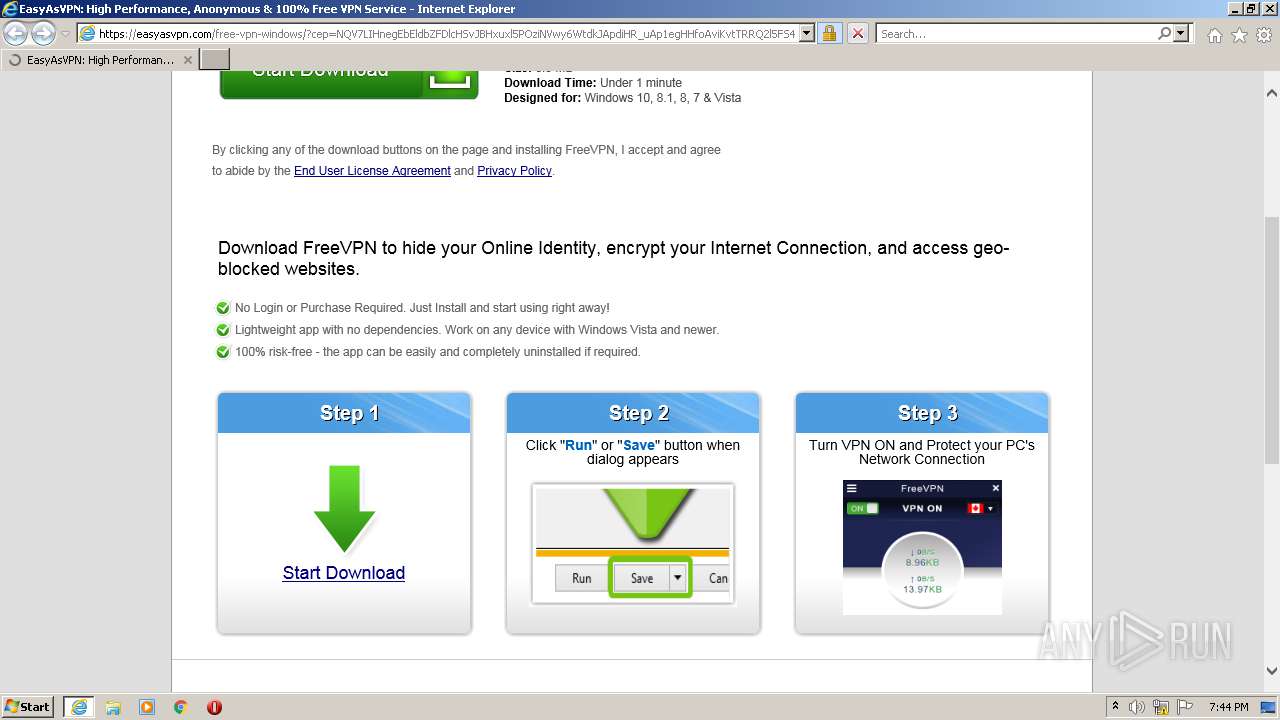
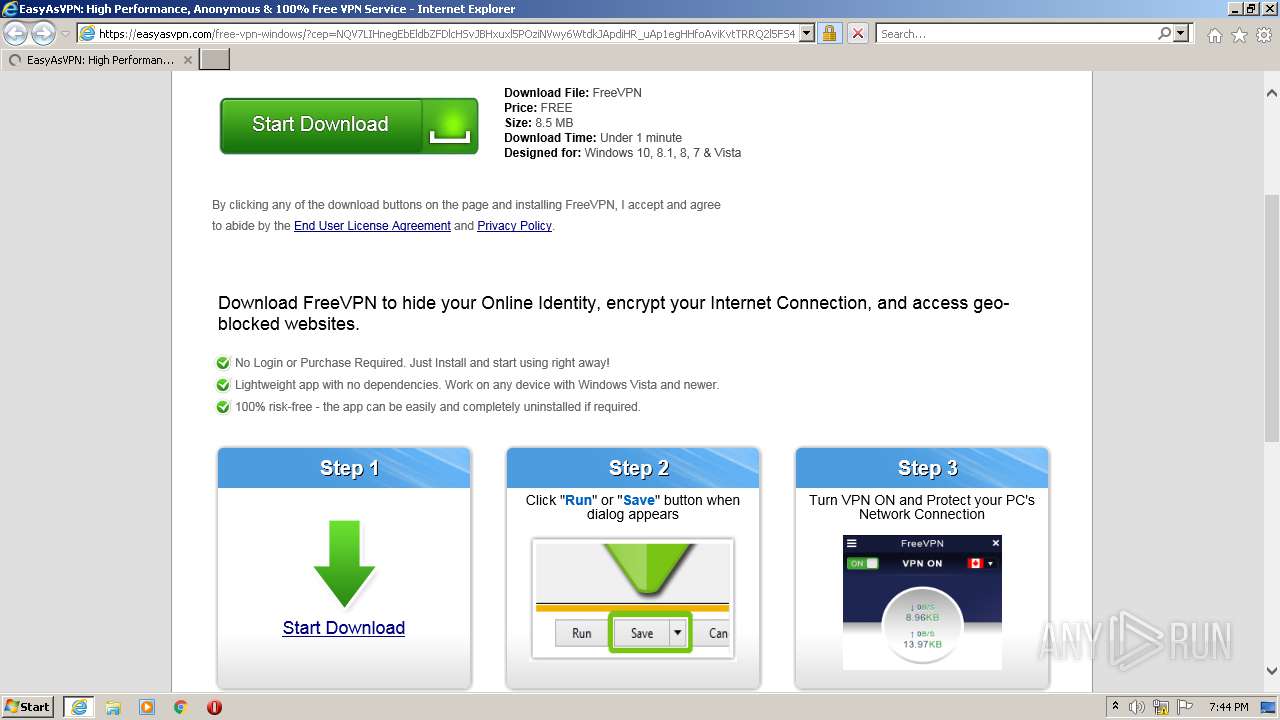
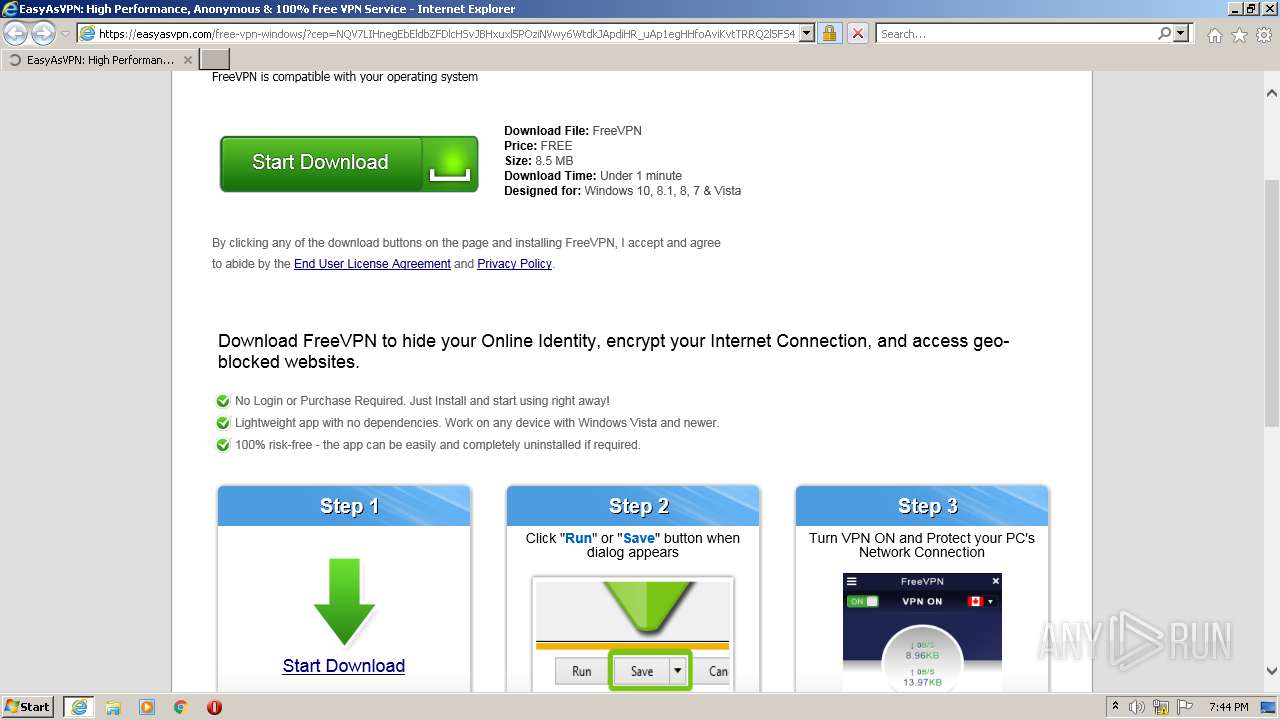
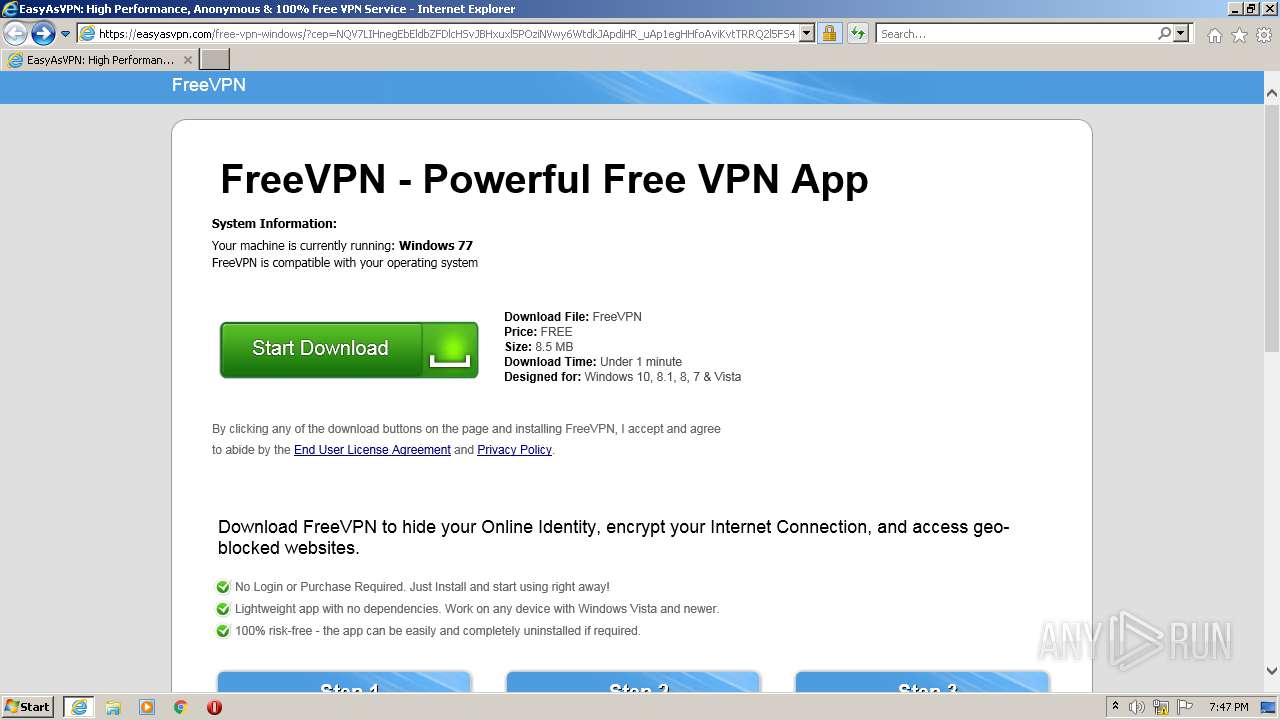
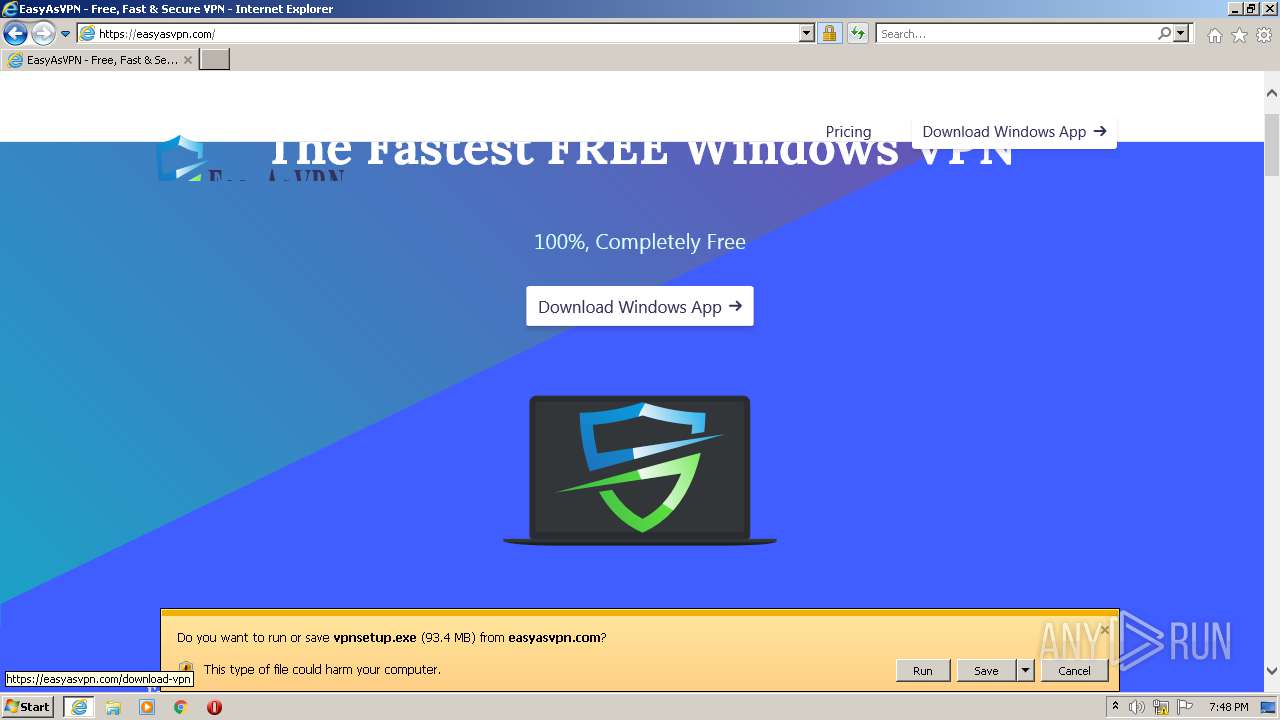
| URL: | https://easyasvpn.com/free-vpn-windows/?cep=NQV7LIHnegEbEldbZFDlcHSvJBHxuxl5POziNVwy6WtdkJApdiHR_uAp1egHHfoAviKvtTRRQ2l5FS4jT9Tj6qHQvjlqUgwb74bCcb14VwNAVWgzuf6HIQgAZY-ADzDDvA24Jdt4QT%20uG5L7BEQSdu7ACC4uaN2ERU0U6HDXL8IHYz9EFxQwNIqGIqt2ymk2lPc0eKyRPsEby6Uv7GAX7C80VUQcSuZ9iBqAZllF4rXmlzSjbB846TbZLL6WP7tAJh-oPm3zJVC3xGuo587JJltxROPg7YOc7oamYDAqmBgZ-3eeInq2zOICBDuEXg84r0Y1WVaM%203oz0mIBmBNFXk913bfOrWx_K23ZXAMsYQ1NpQb5MqCvm_5NgnpNksZ6D45ctMihd5HX6nVYDUji_htucvV1L0PIyNTehnkGln8_p_RI-9HowuPnpijaJGRoAnU_vJwgAr05GYjdngldZNS0EfNOEi2VwSQrghES8RyU0e3c35NzpIkn8wEj7KMibL5wDm%20yDbTaMd-iyvakfMn8sLul5bUm6v6aii23Jd6o9Zr_q_ks3qMbN0MDyHJ1w3-nviicRbR-IeJNGaF-u5kTPQzoWRL1ap1VKd4i-gigBx67Pr-PV6GZ7kMlOyqdZEBnJNvvJ9Yq391V1hFdAWoI79_-2TWhYIBw3gJGJtSuR-AyPuQHW19ntqEX0y47vJTL%20OzZ0eI2NL9fOPit2WVigQ&lptoken=165d1236930f57e68393&zoneid=2579647&bannerid=7674860&browser=chrome&os=windows&device=desktop®ion=jk&isp=mnc%20playmedia&useragent=Mozilla/5.0%20(Windows%20%20NT%2010.0;%20Win64;%20x64)%20AppleWebKit/537.36%20(KHTML,%20like%20Gecko)%20Chrome/88.0.4324.146%20Safari/537.36&language=en&connectiontype=cable&cost=0.000532&visitor_id=383235497436131595 |
| Full analysis: | https://app.any.run/tasks/ae4ffa21-c5d7-40bf-a22e-5bdd106578db |
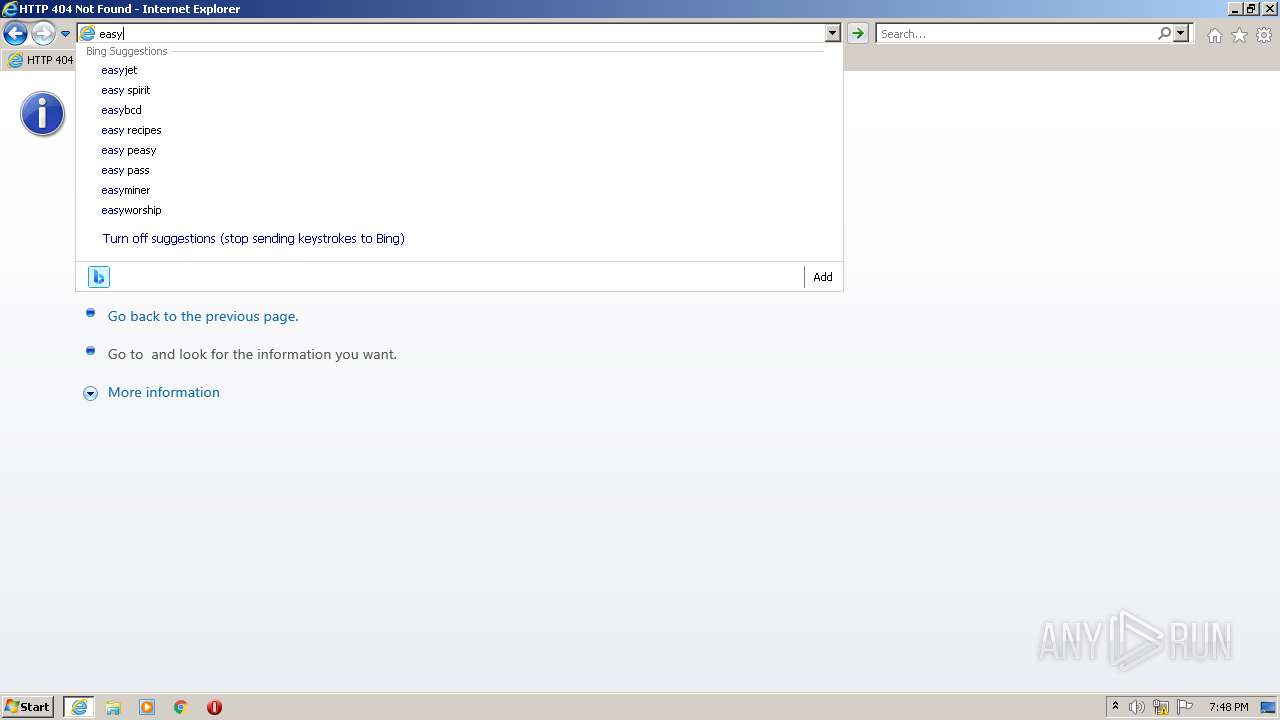
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2021, 18:44:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7AF4DD7B9C30C730917CC75A3ED2B75C |
| SHA1: | 280B4642E5B7B712A0C7DFBF2E01039F399D38C9 |
| SHA256: | 52D74419F6AD89F23F98B2F035CE03EFEC19EAF034F71CFB5CA1564C6B9AC442 |
| SSDEEP: | 24:2D6PMo0XAUQBfCYF/Eqp36t4CuecvUVibEagfwbcoe8cSQWYPzVKBzv:epGBfUqp36t4BYzaWRIPUzVKBr |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3280)
- iexplore.exe (PID: 2904)
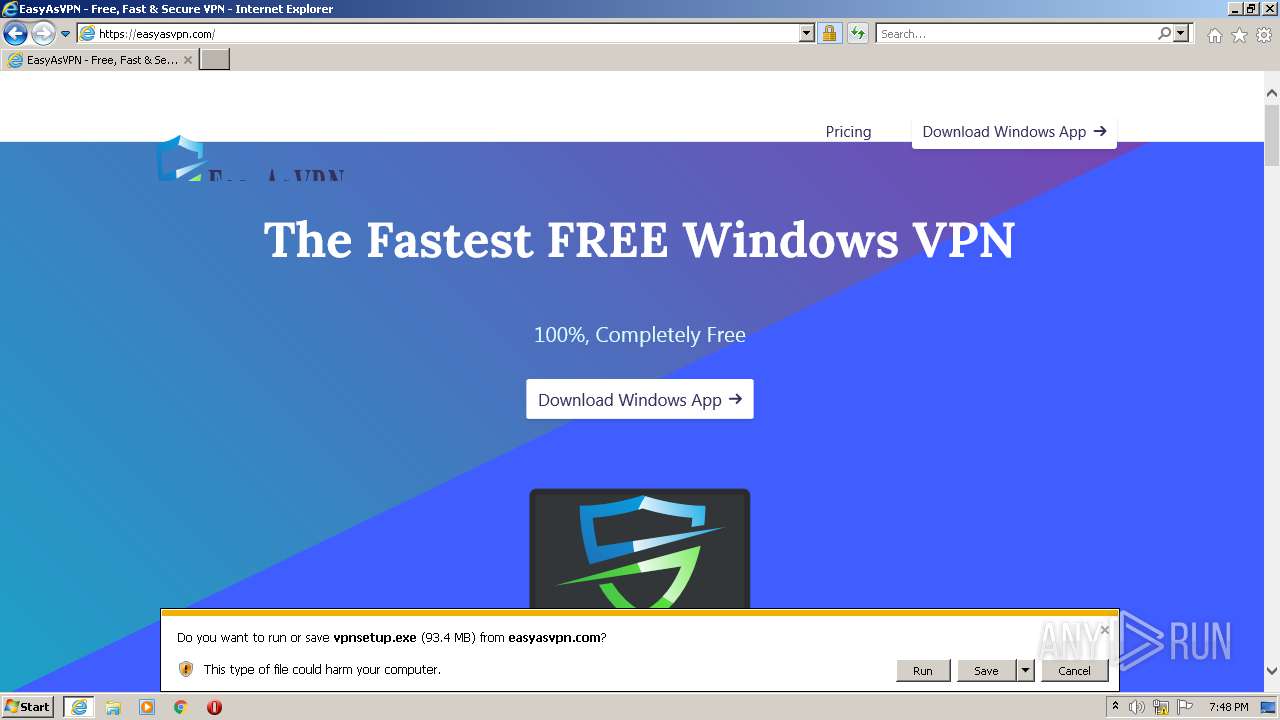
Executable content was dropped or overwritten
- iexplore.exe (PID: 3280)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2904)
Checks supported languages
- iexplore.exe (PID: 2904)
- iexplore.exe (PID: 3280)
Application launched itself
- iexplore.exe (PID: 2904)
Reads the computer name
- iexplore.exe (PID: 3280)
- iexplore.exe (PID: 2904)
Reads internet explorer settings
- iexplore.exe (PID: 3280)
Creates files in the user directory
- iexplore.exe (PID: 2904)
- iexplore.exe (PID: 3280)
Checks Windows Trust Settings
- iexplore.exe (PID: 2904)
- iexplore.exe (PID: 3280)
Reads settings of System Certificates
- iexplore.exe (PID: 3280)
- iexplore.exe (PID: 2904)
Changes settings of System certificates
- iexplore.exe (PID: 2904)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2904)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3280)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
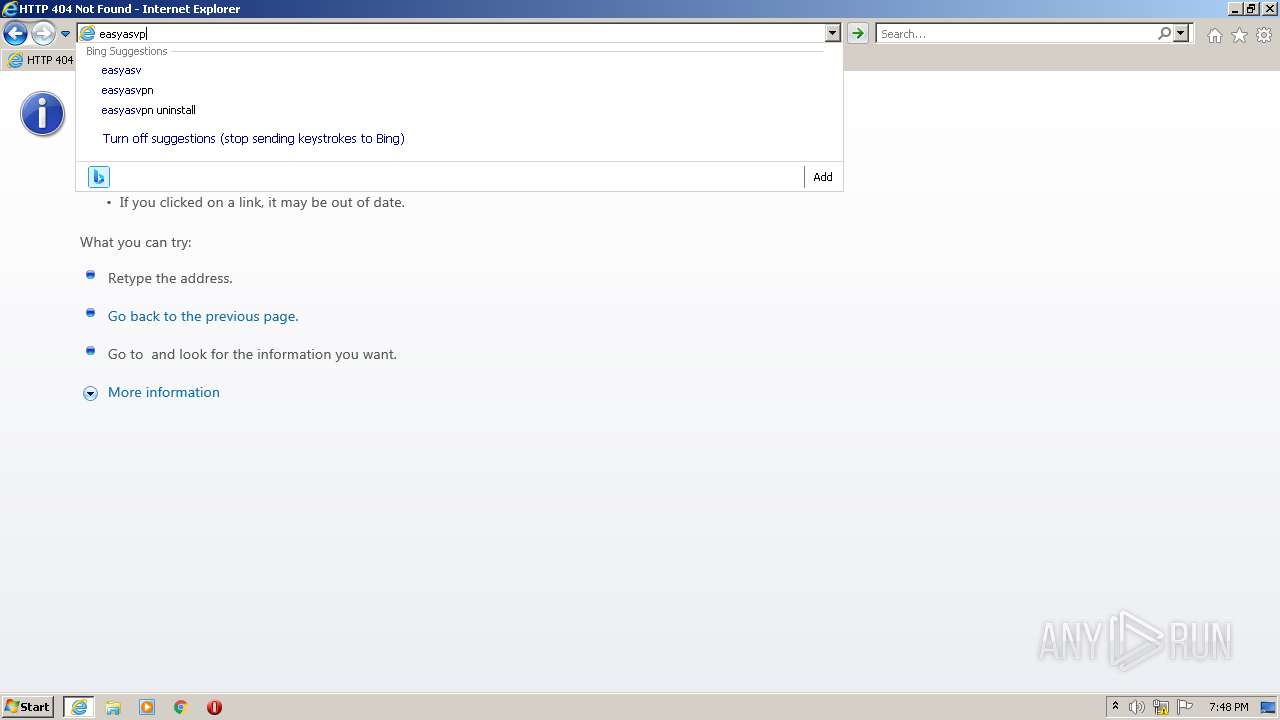
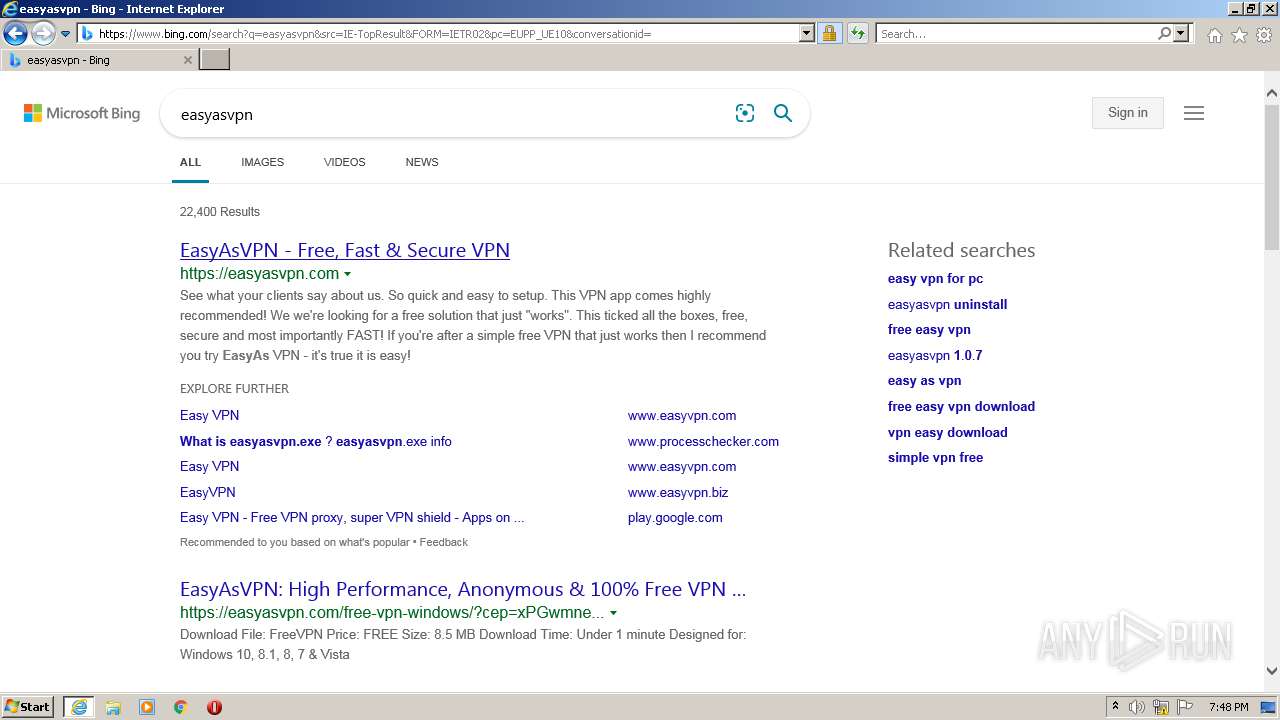
| 2904 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://easyasvpn.com/free-vpn-windows/?cep=NQV7LIHnegEbEldbZFDlcHSvJBHxuxl5POziNVwy6WtdkJApdiHR_uAp1egHHfoAviKvtTRRQ2l5FS4jT9Tj6qHQvjlqUgwb74bCcb14VwNAVWgzuf6HIQgAZY-ADzDDvA24Jdt4QT%20uG5L7BEQSdu7ACC4uaN2ERU0U6HDXL8IHYz9EFxQwNIqGIqt2ymk2lPc0eKyRPsEby6Uv7GAX7C80VUQcSuZ9iBqAZllF4rXmlzSjbB846TbZLL6WP7tAJh-oPm3zJVC3xGuo587JJltxROPg7YOc7oamYDAqmBgZ-3eeInq2zOICBDuEXg84r0Y1WVaM%203oz0mIBmBNFXk913bfOrWx_K23ZXAMsYQ1NpQb5MqCvm_5NgnpNksZ6D45ctMihd5HX6nVYDUji_htucvV1L0PIyNTehnkGln8_p_RI-9HowuPnpijaJGRoAnU_vJwgAr05GYjdngldZNS0EfNOEi2VwSQrghES8RyU0e3c35NzpIkn8wEj7KMibL5wDm%20yDbTaMd-iyvakfMn8sLul5bUm6v6aii23Jd6o9Zr_q_ks3qMbN0MDyHJ1w3-nviicRbR-IeJNGaF-u5kTPQzoWRL1ap1VKd4i-gigBx67Pr-PV6GZ7kMlOyqdZEBnJNvvJ9Yq391V1hFdAWoI79_-2TWhYIBw3gJGJtSuR-AyPuQHW19ntqEX0y47vJTL%20OzZ0eI2NL9fOPit2WVigQ&lptoken=165d1236930f57e68393&zoneid=2579647&bannerid=7674860&browser=chrome&os=windows&device=desktop®ion=jk&isp=mnc%20playmedia&useragent=Mozilla/5.0%20(Windows%20%20NT%2010.0;%20Win64;%20x64)%20AppleWebKit/537.36%20(KHTML,%20like%20Gecko)%20Chrome/88.0.4324.146%20Safari/537.36&language=en&connectiontype=cable&cost=0.000532&visitor_id=383235497436131595" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3280 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2904 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 459
Read events
19 276
Write events
181
Delete events
2
Modification events
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 480025008 | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30903027 | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 780031805 | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30903027 | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
23
Text files
158
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3280 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\index[1].css | text | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\free-vpn-windows[1].htm | html | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\dlcommon[1].js | text | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\assist[1].css | text | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\icon_monitor_driver_update_sdp[1].gif | image | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\step_3[1].png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
86
DNS requests
38
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3280 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | DE | der | 1.16 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2904 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2904 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3280 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2904 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 13.225.84.97:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2904 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
3280 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 13.225.84.49:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
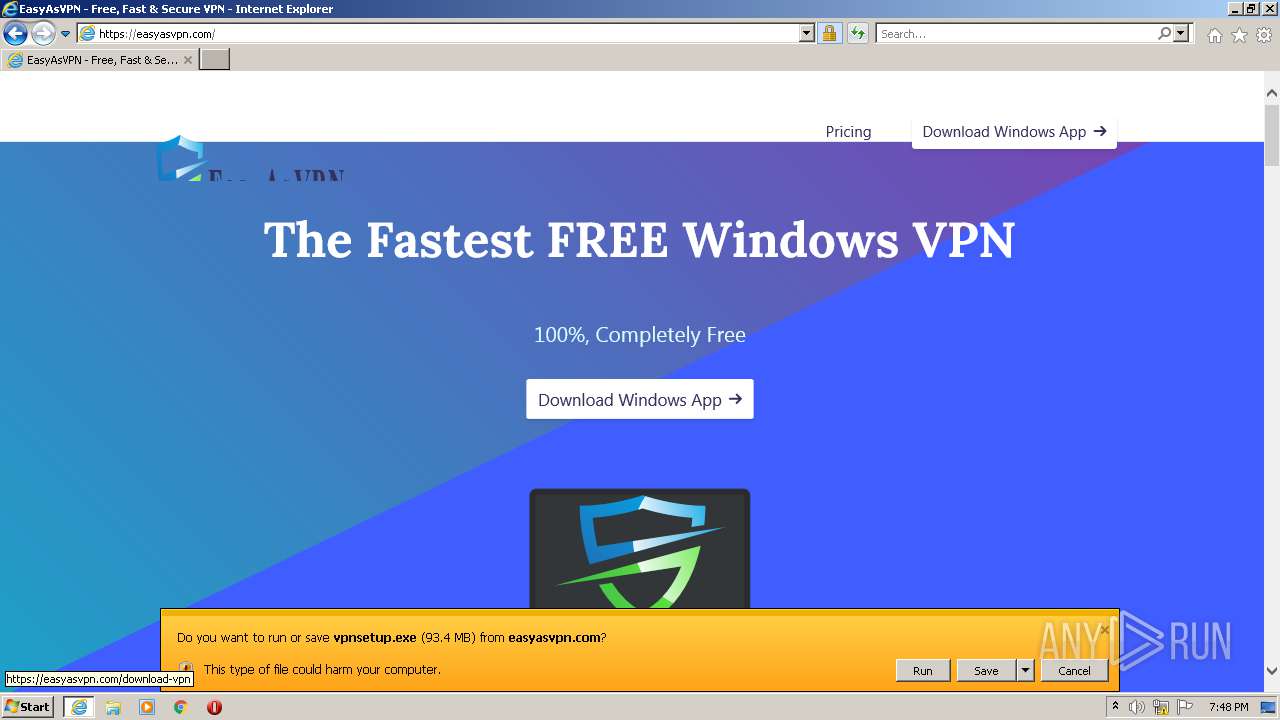
3280 | iexplore.exe | 172.67.210.204:443 | easyasvpn.com | — | US | suspicious |
3280 | iexplore.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | Microsoft Corporation | US | whitelisted |
3280 | iexplore.exe | 18.193.209.105:443 | turninted-suradios.icu | Massachusetts Institute of Technology | US | suspicious |
3280 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3280 | iexplore.exe | 195.138.255.11:80 | crl.identrust.com | AS33891 Netzbetrieb GmbH | DE | whitelisted |
2904 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2904 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2904 | iexplore.exe | 172.67.210.204:443 | easyasvpn.com | — | US | suspicious |
3280 | iexplore.exe | 104.21.16.110:443 | easyasvpn.com | Cloudflare Inc | US | suspicious |
2904 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
easyasvpn.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
turninted-suradios.icu |
| suspicious |
crl.identrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3280 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
3280 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |
3280 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |
3280 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
3280 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |