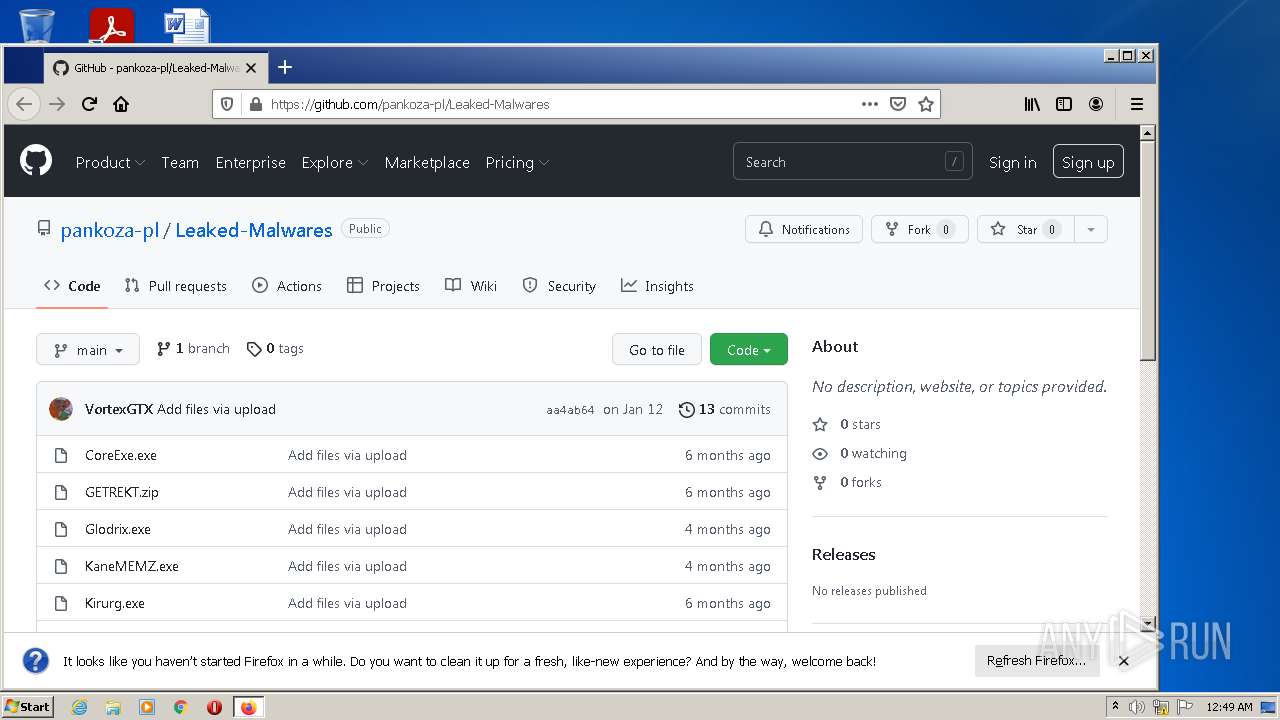
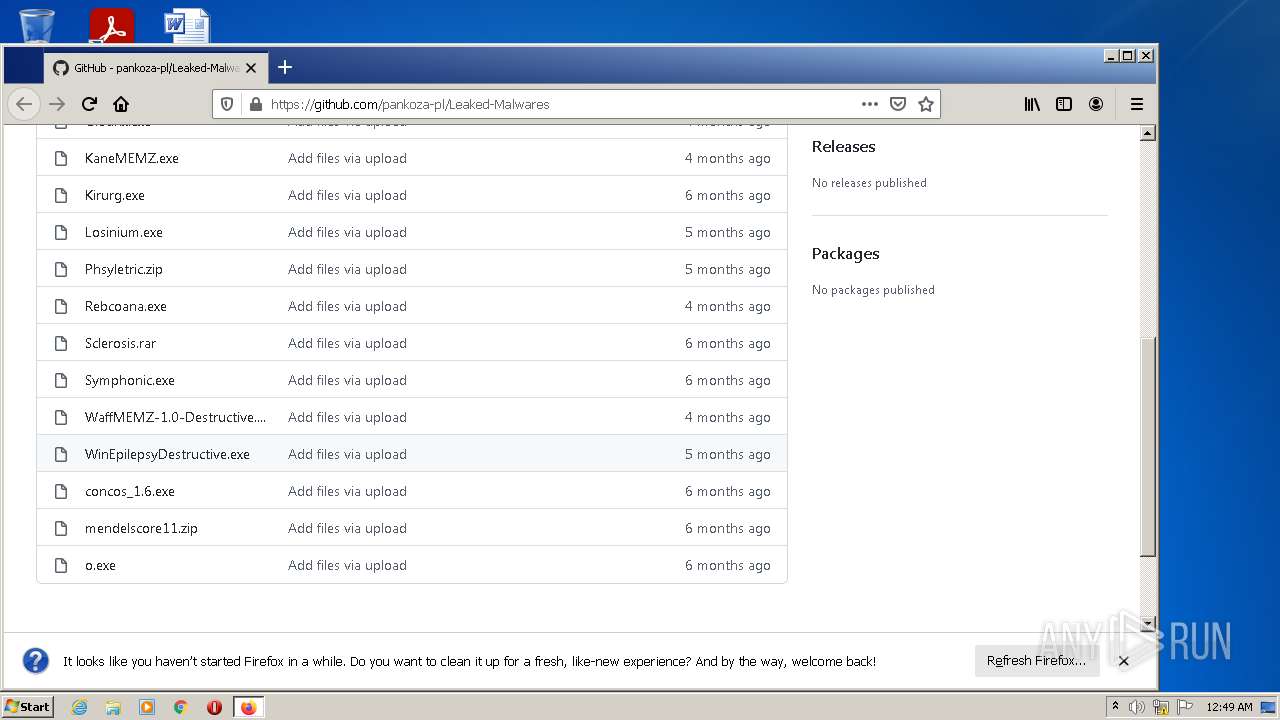
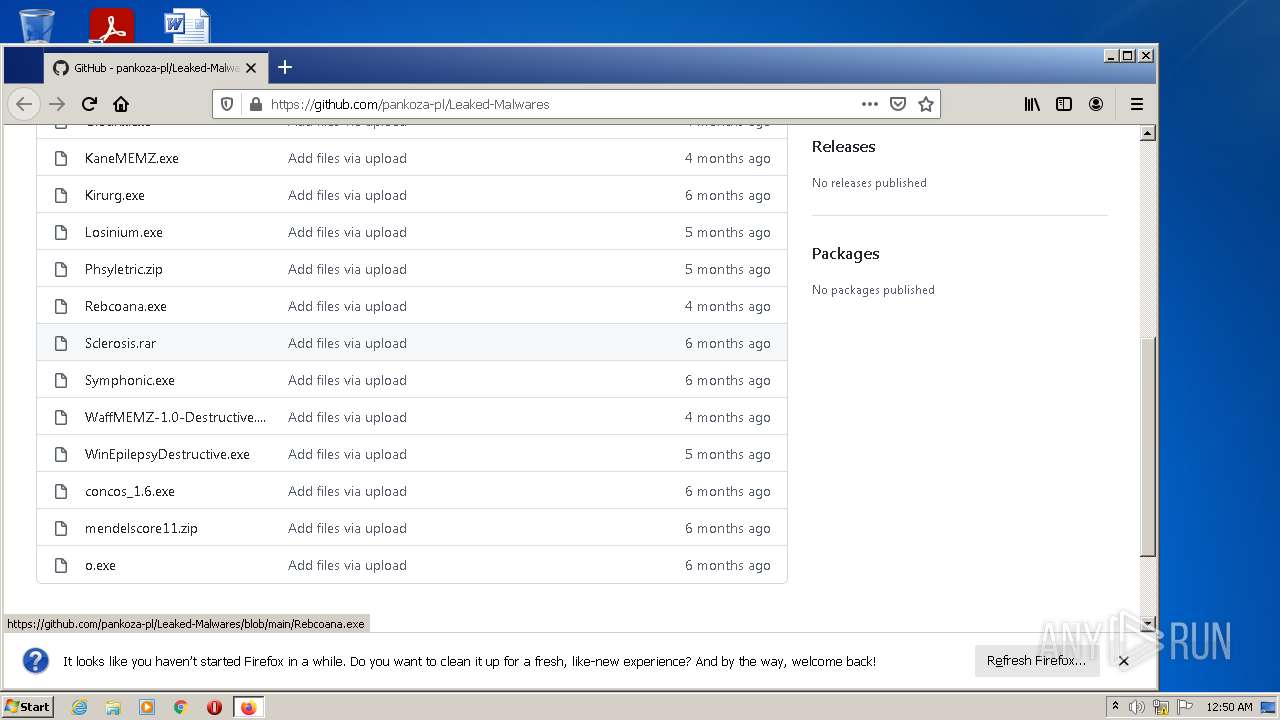
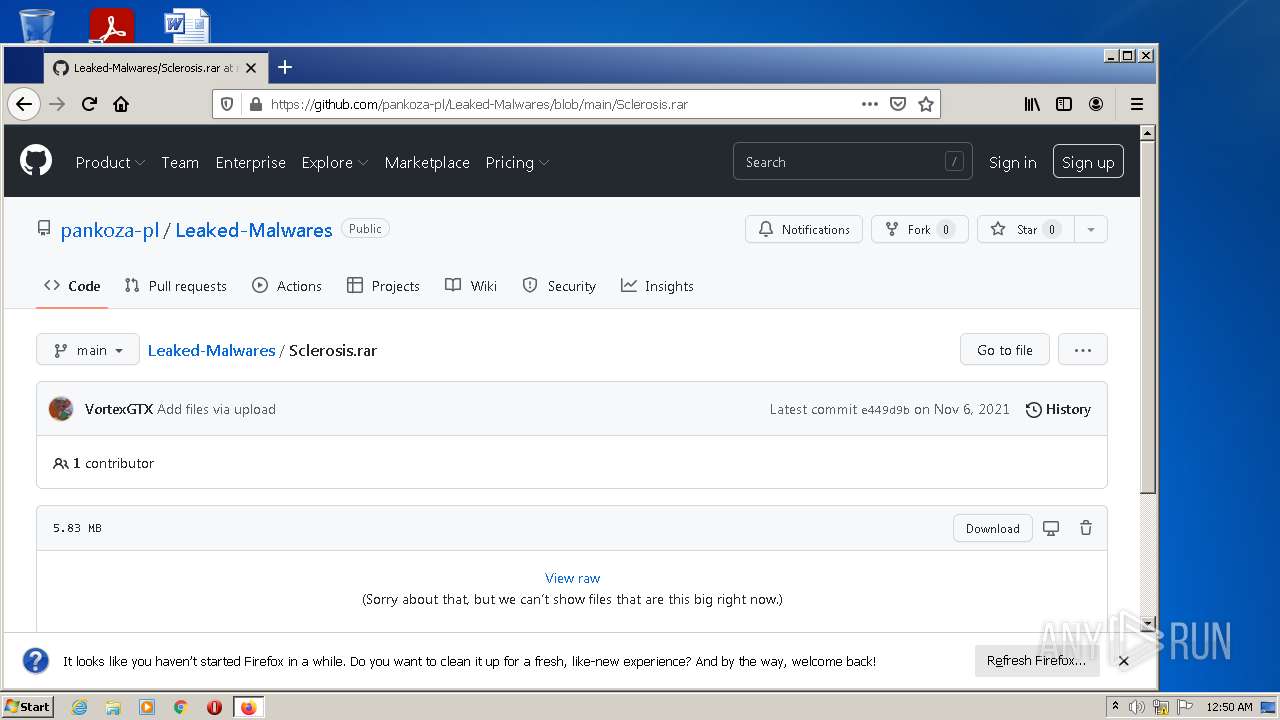
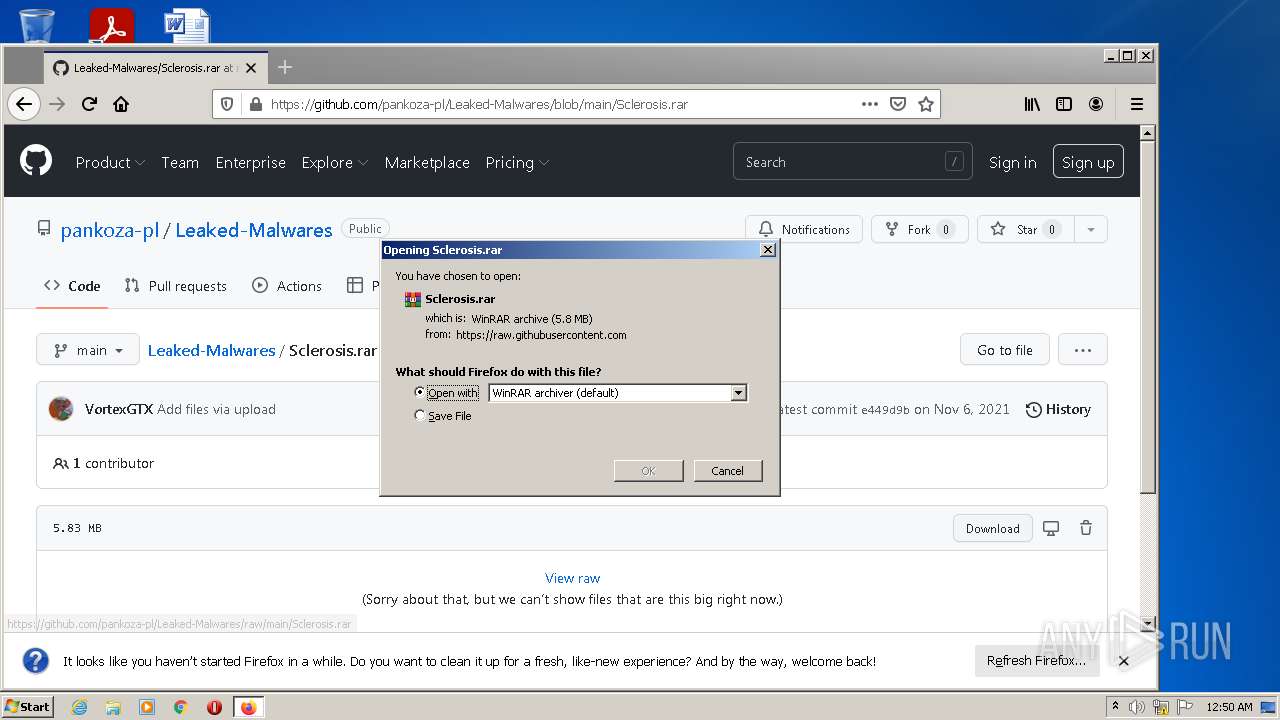
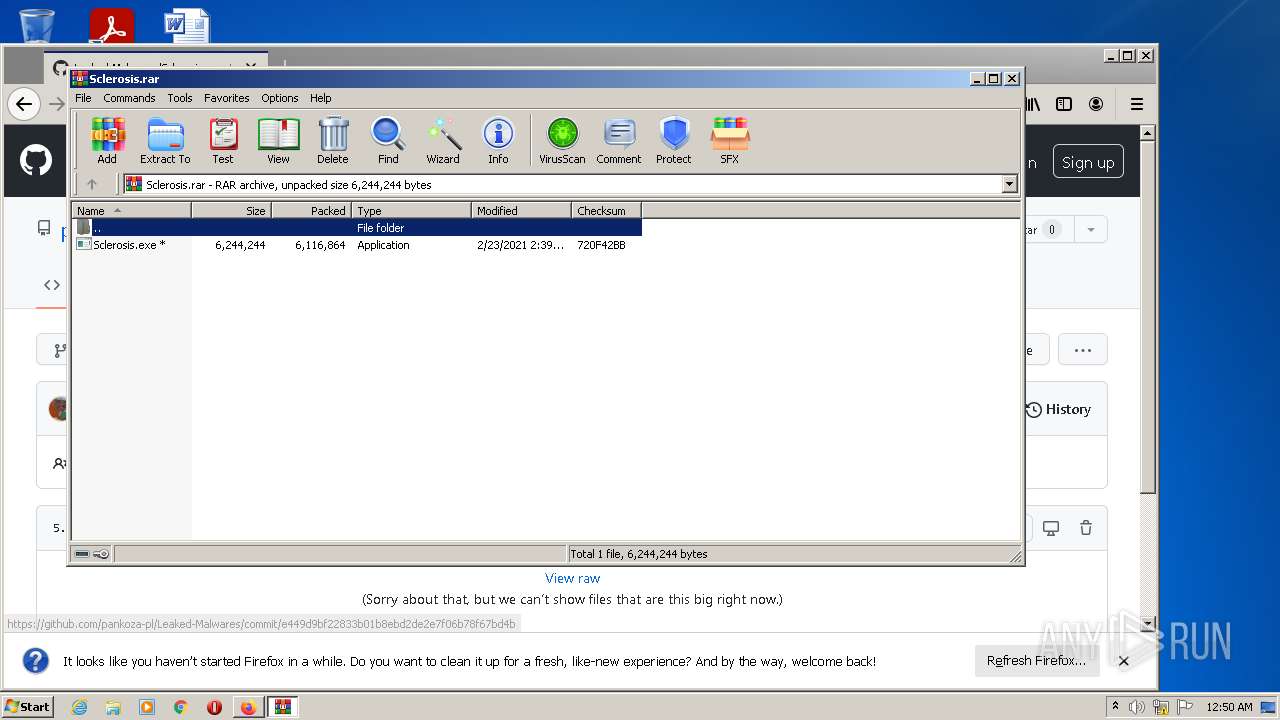
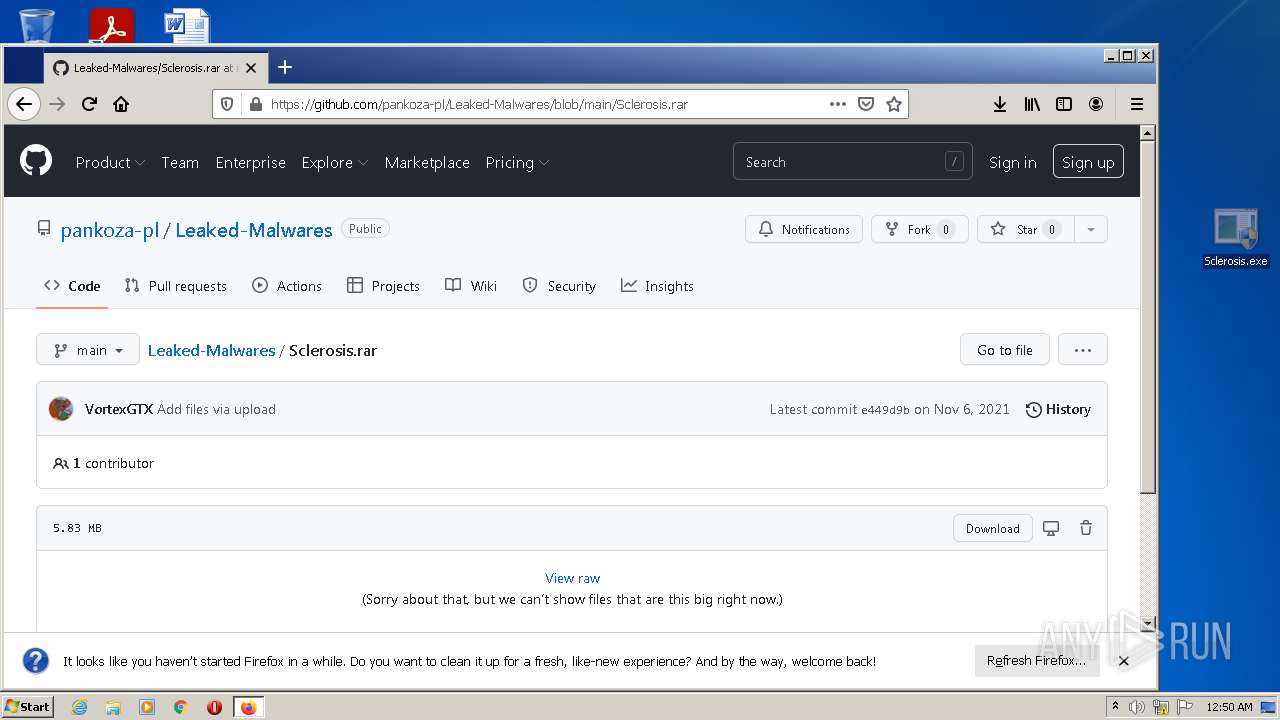
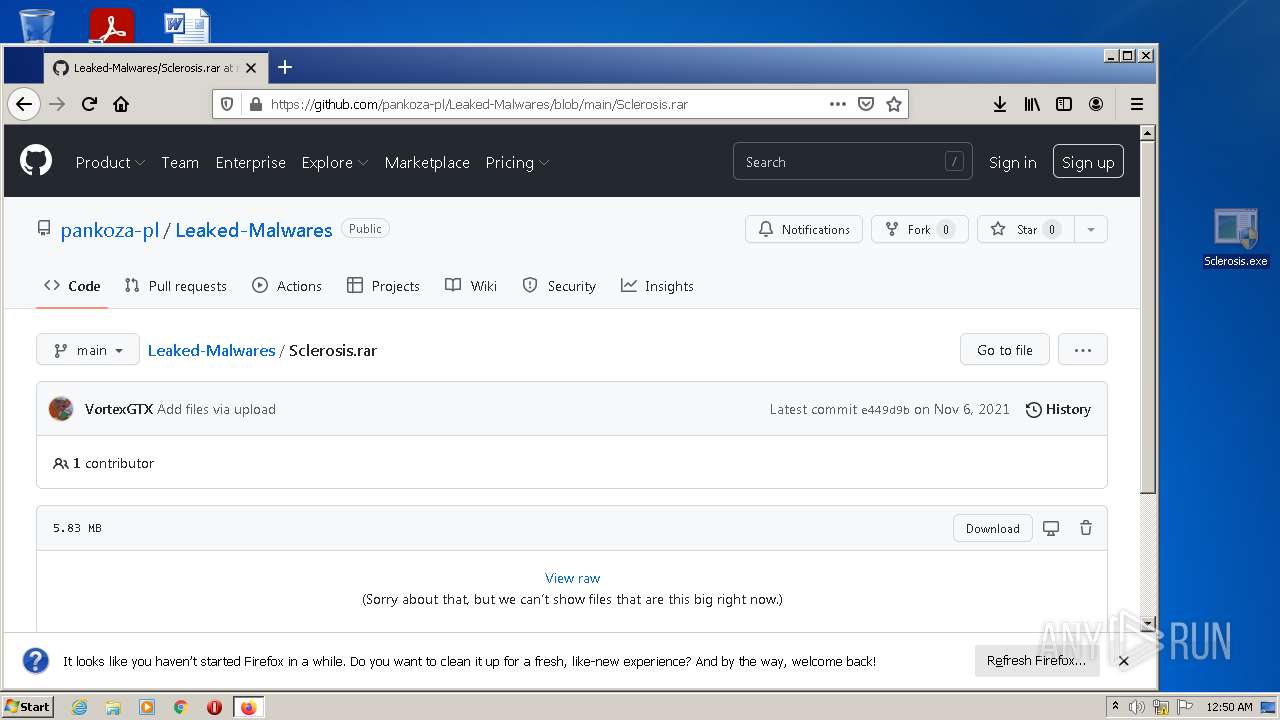
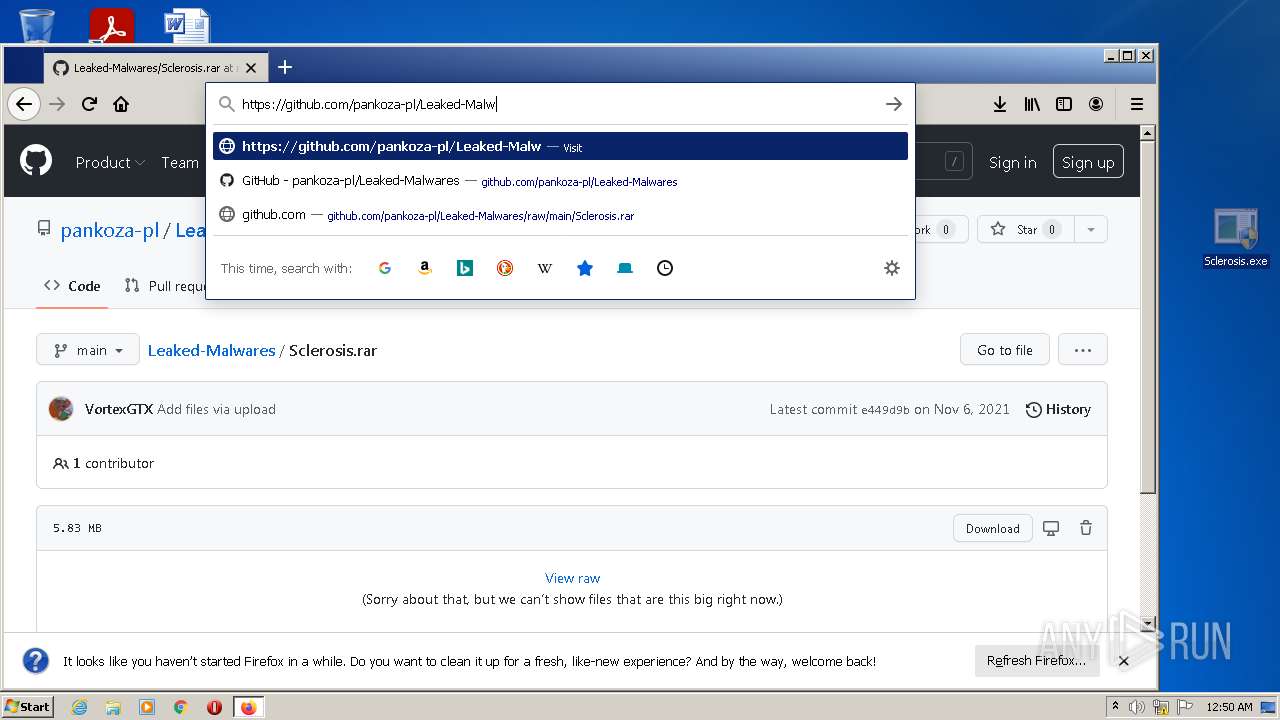
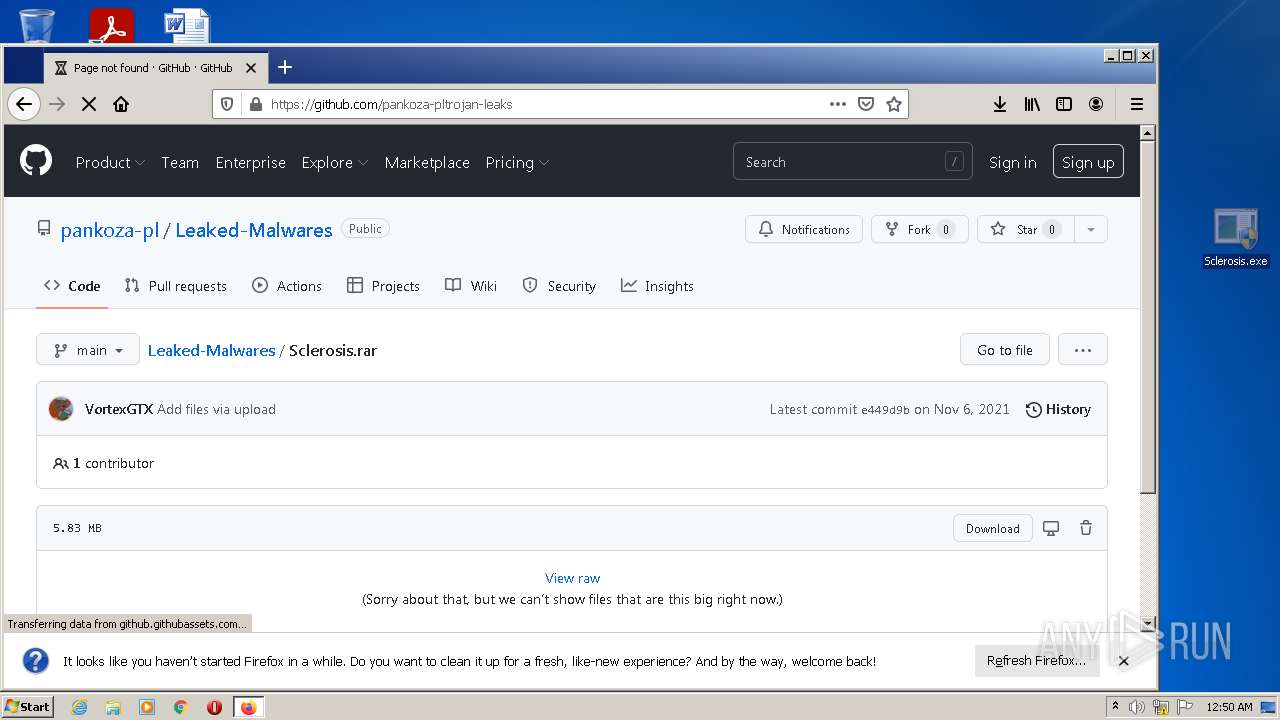
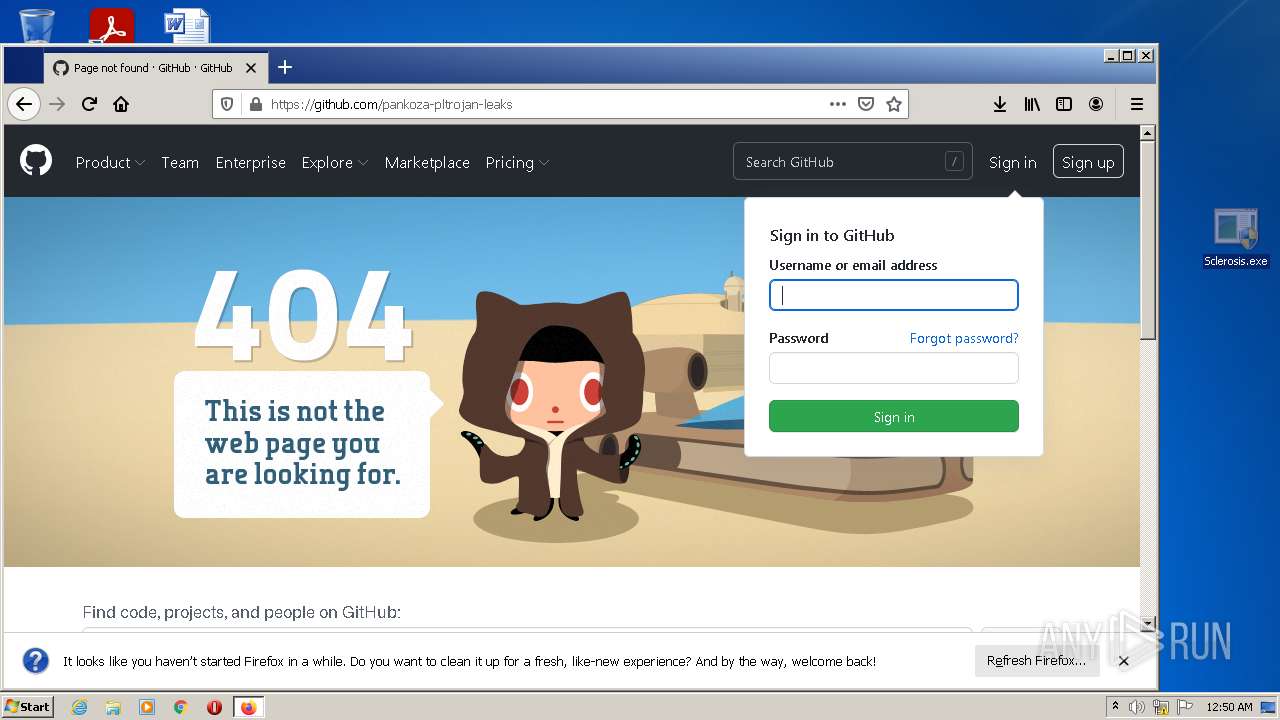
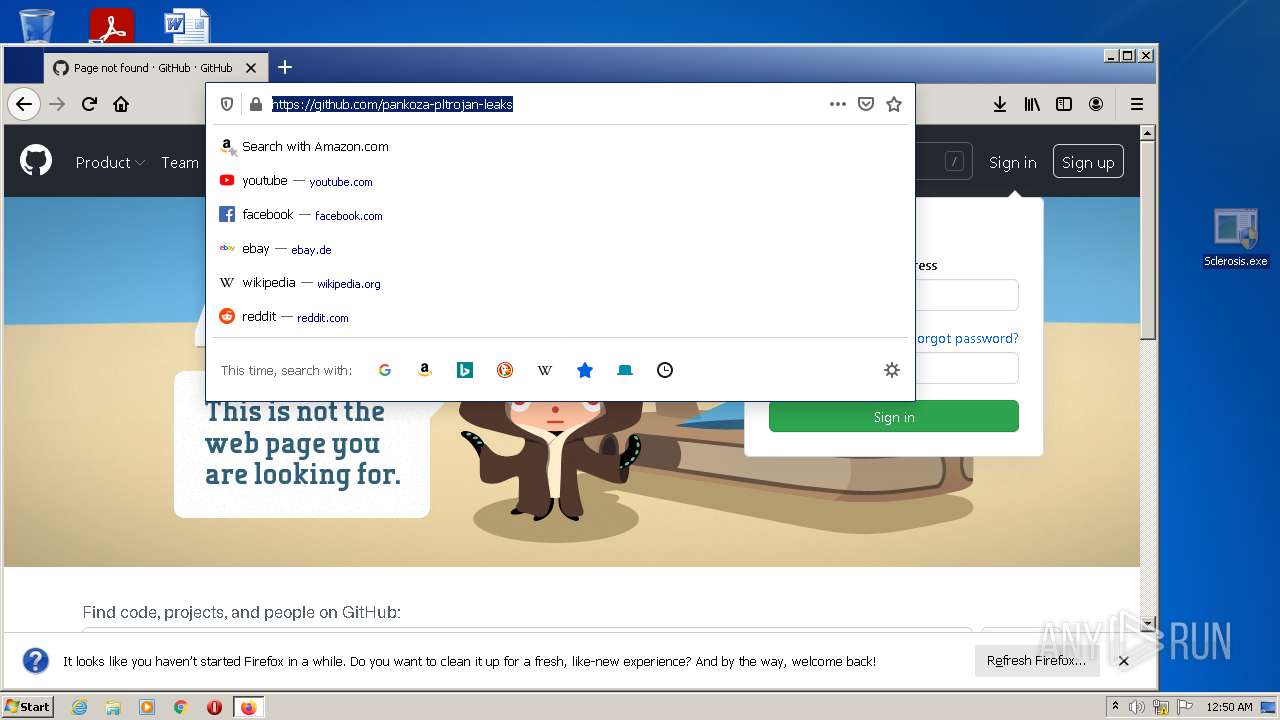
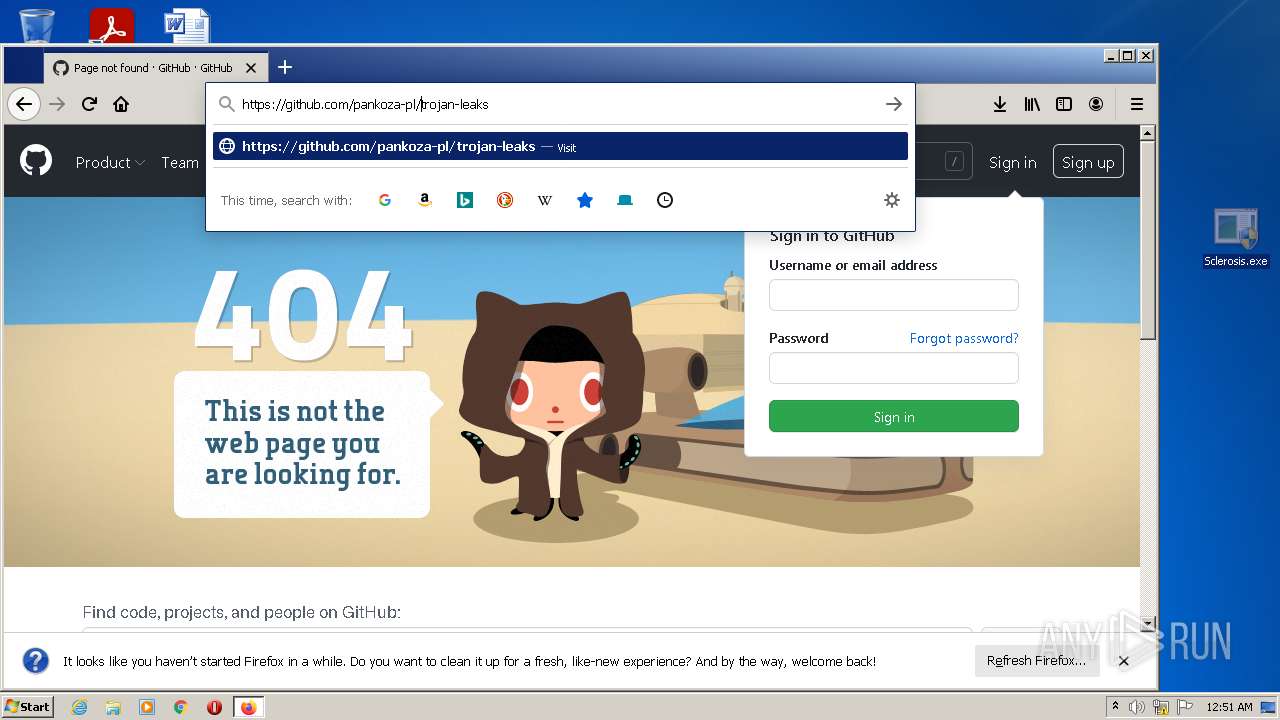
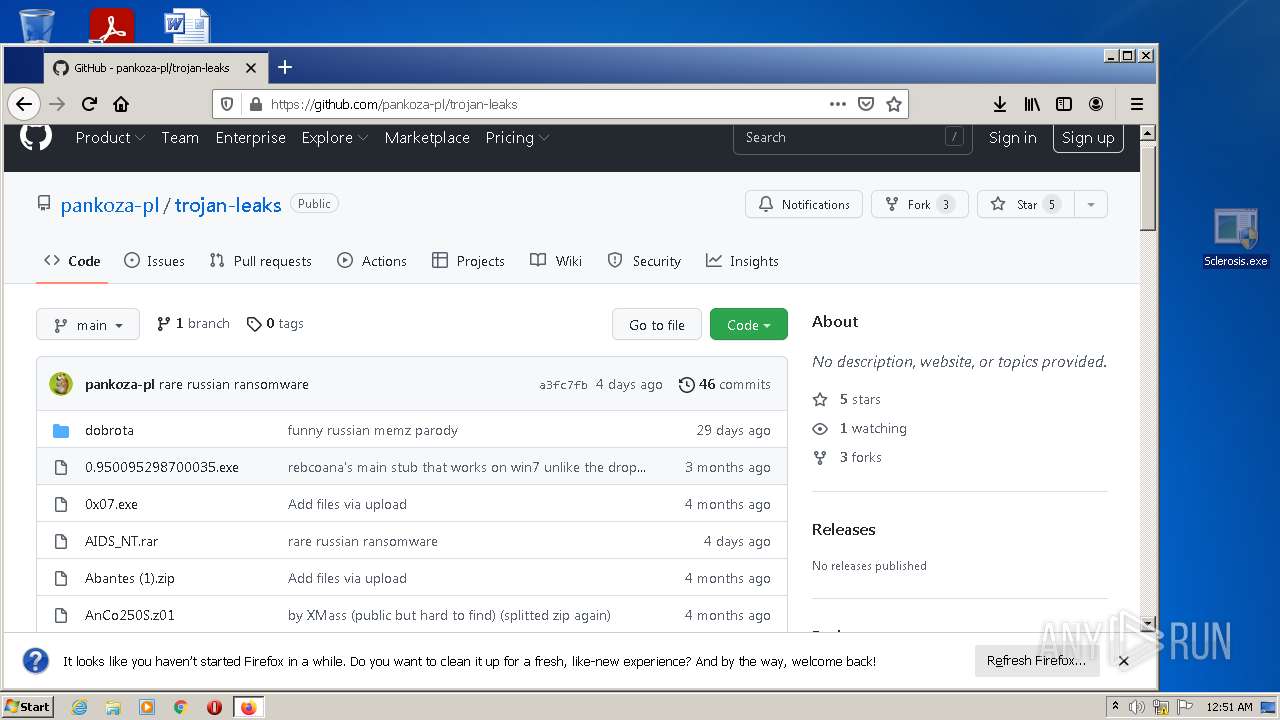
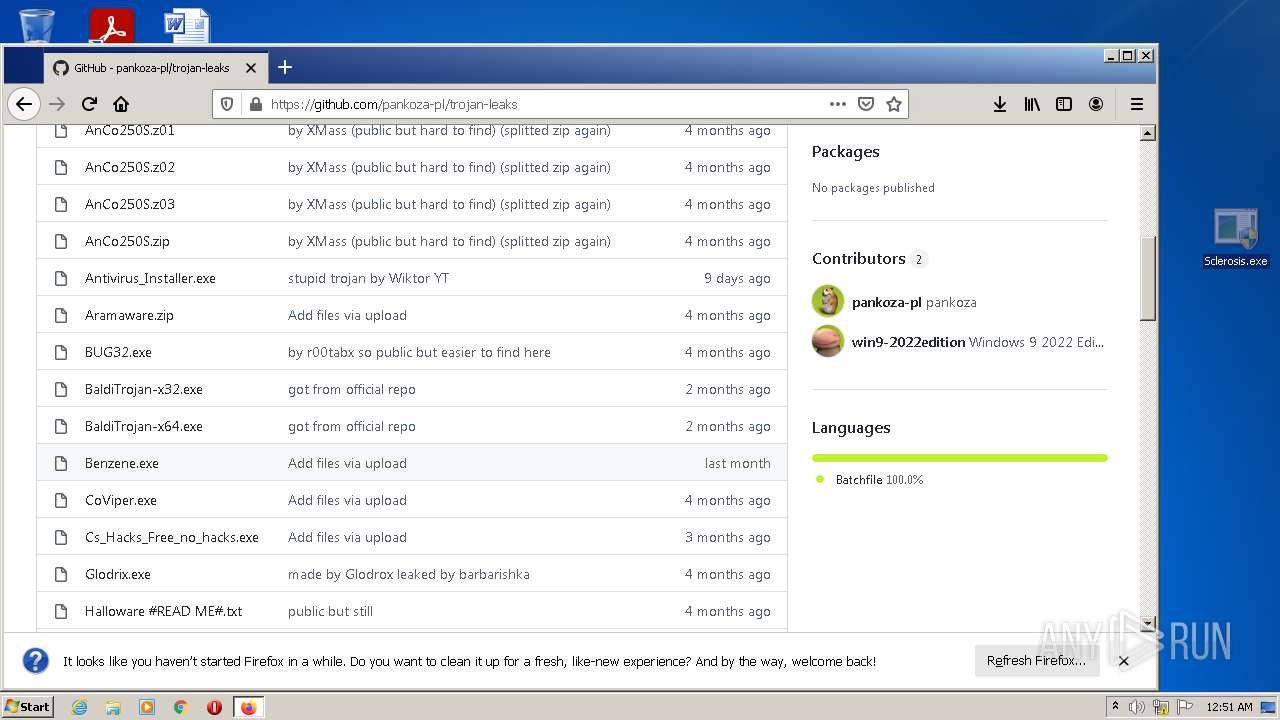
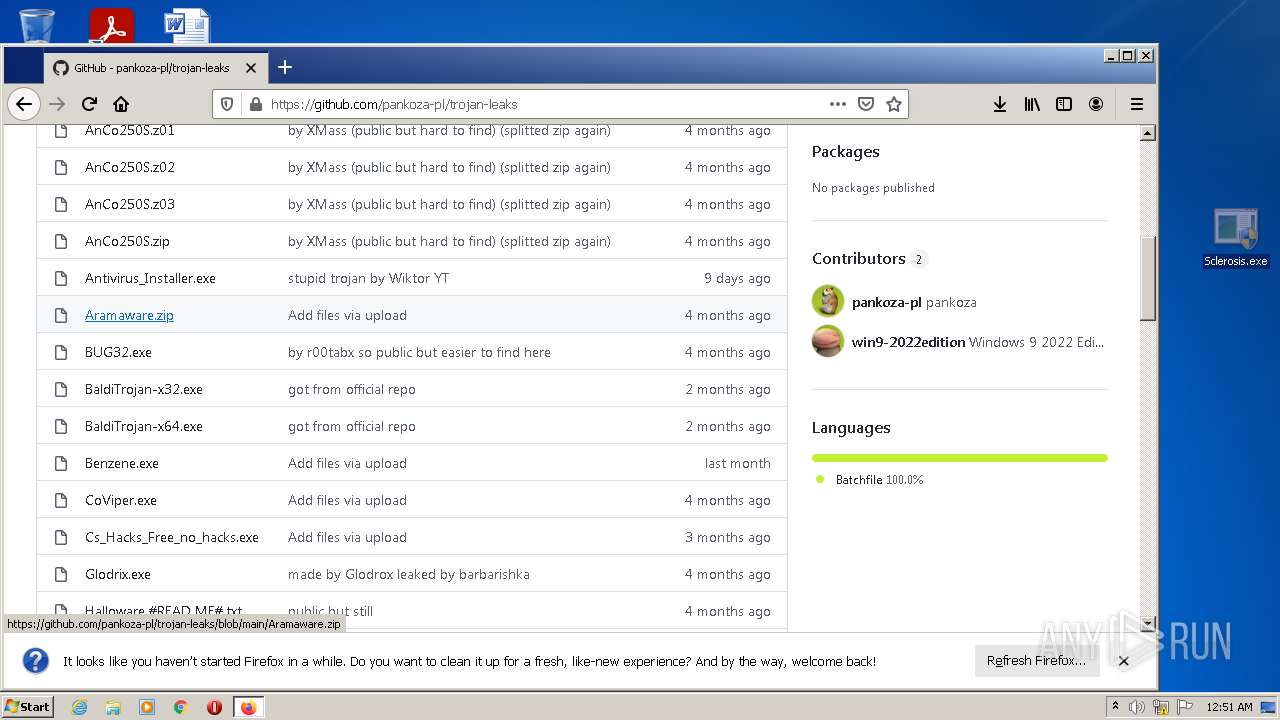
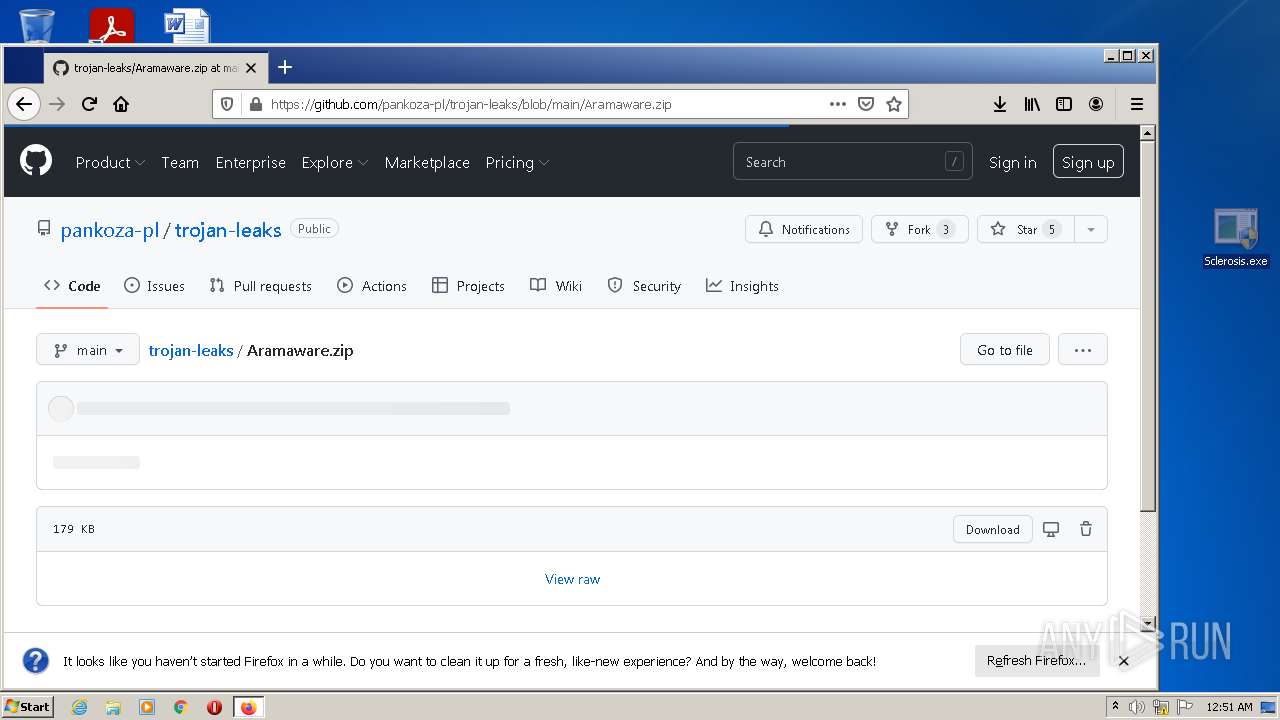
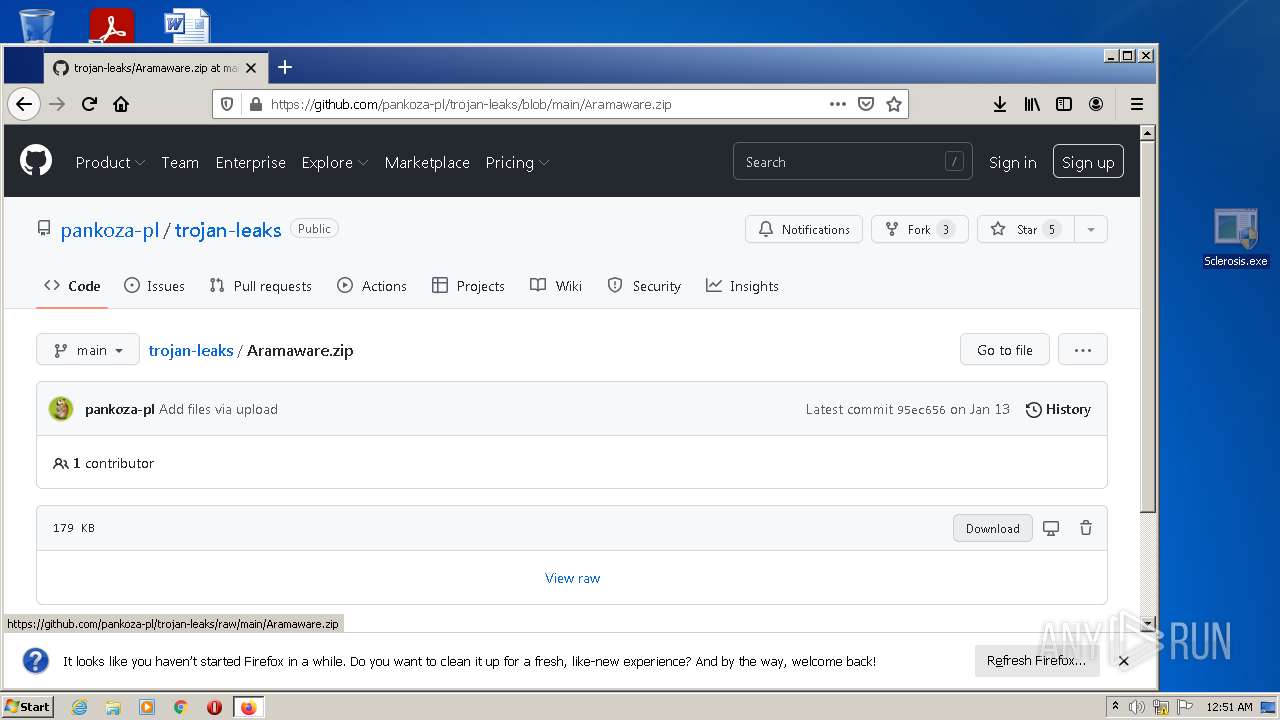
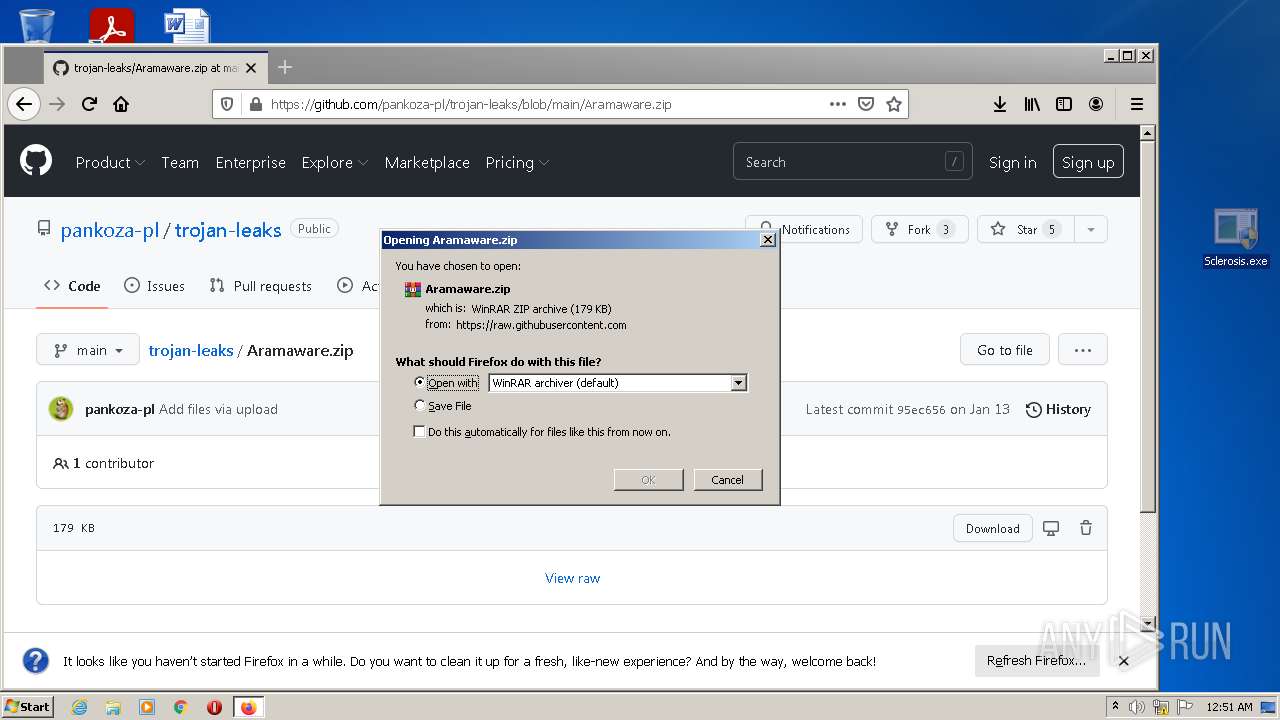
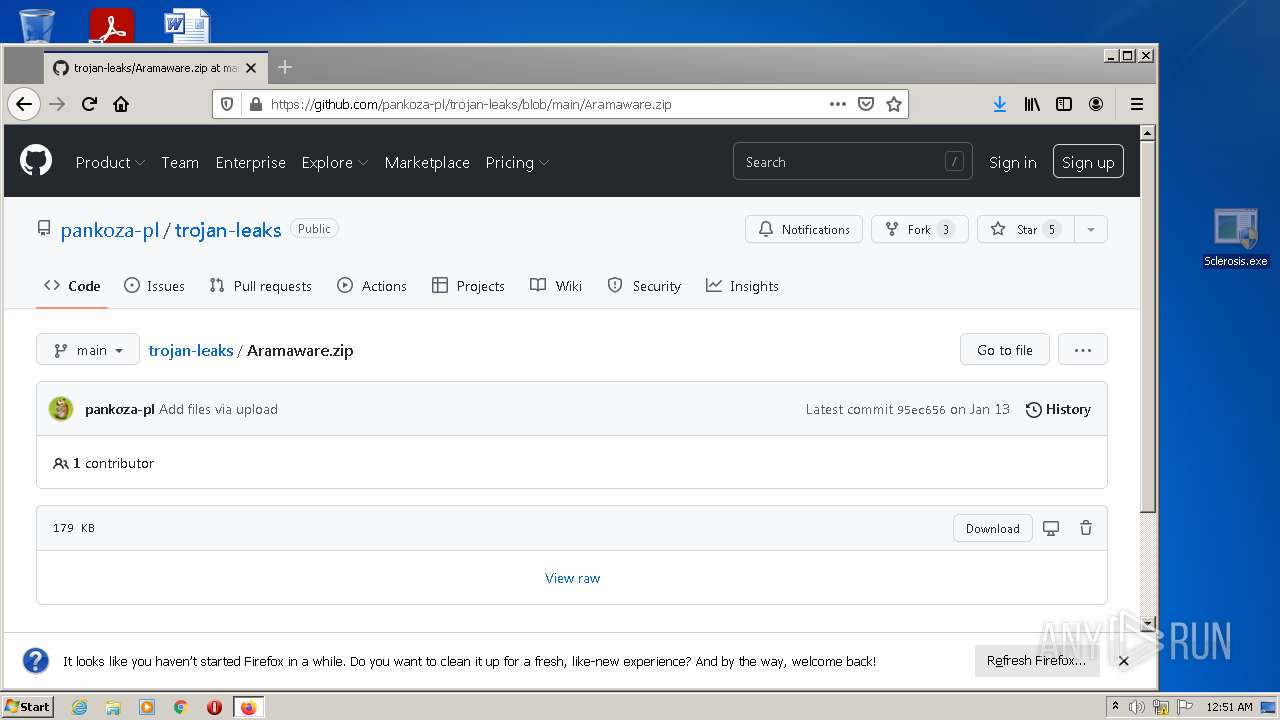
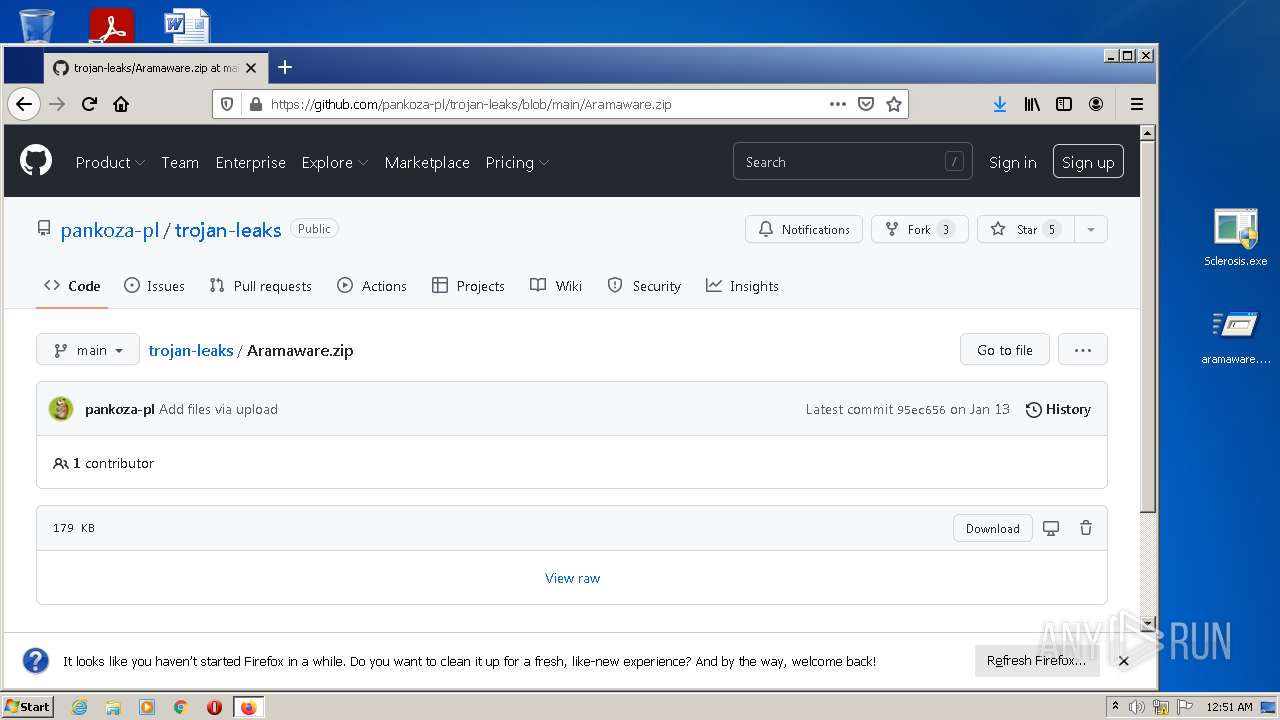
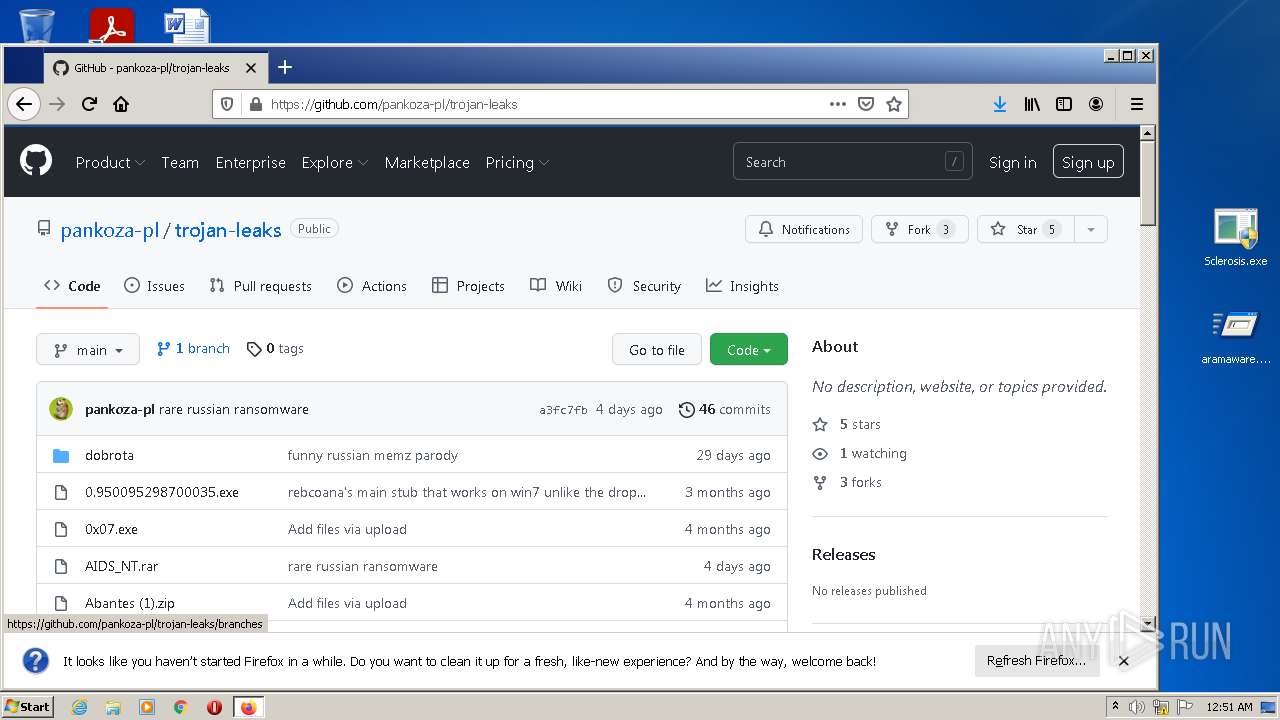
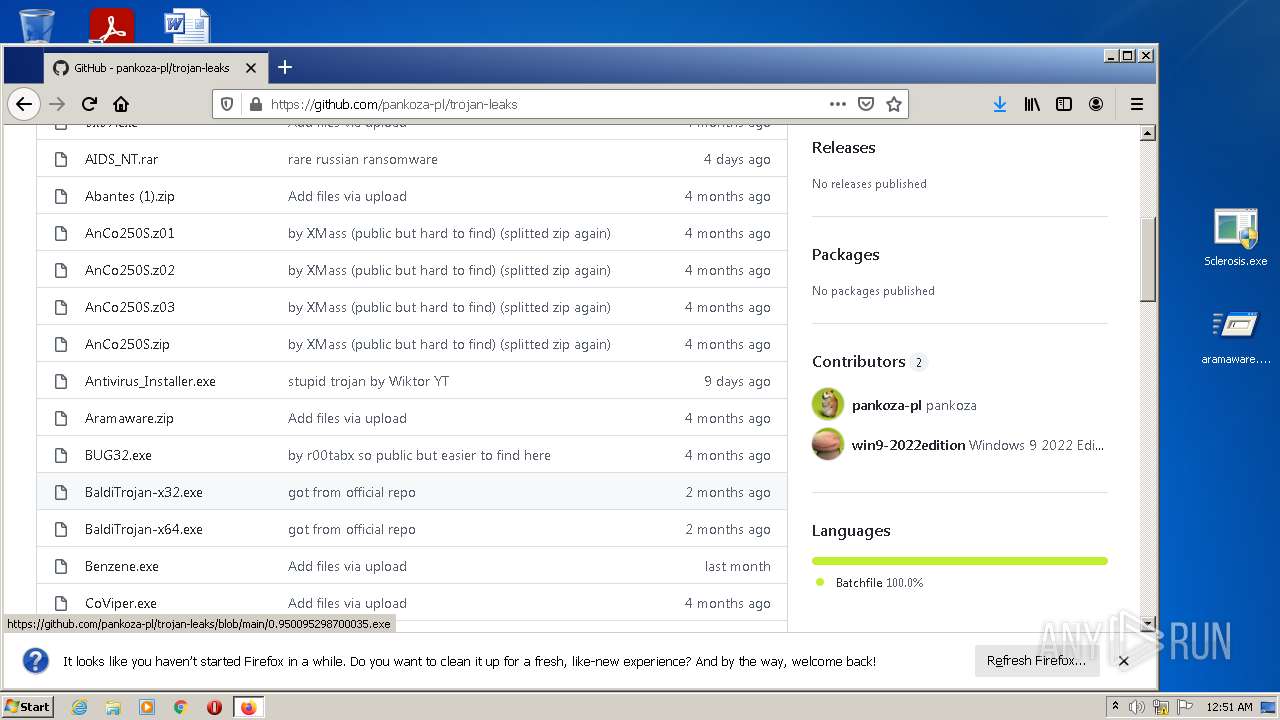
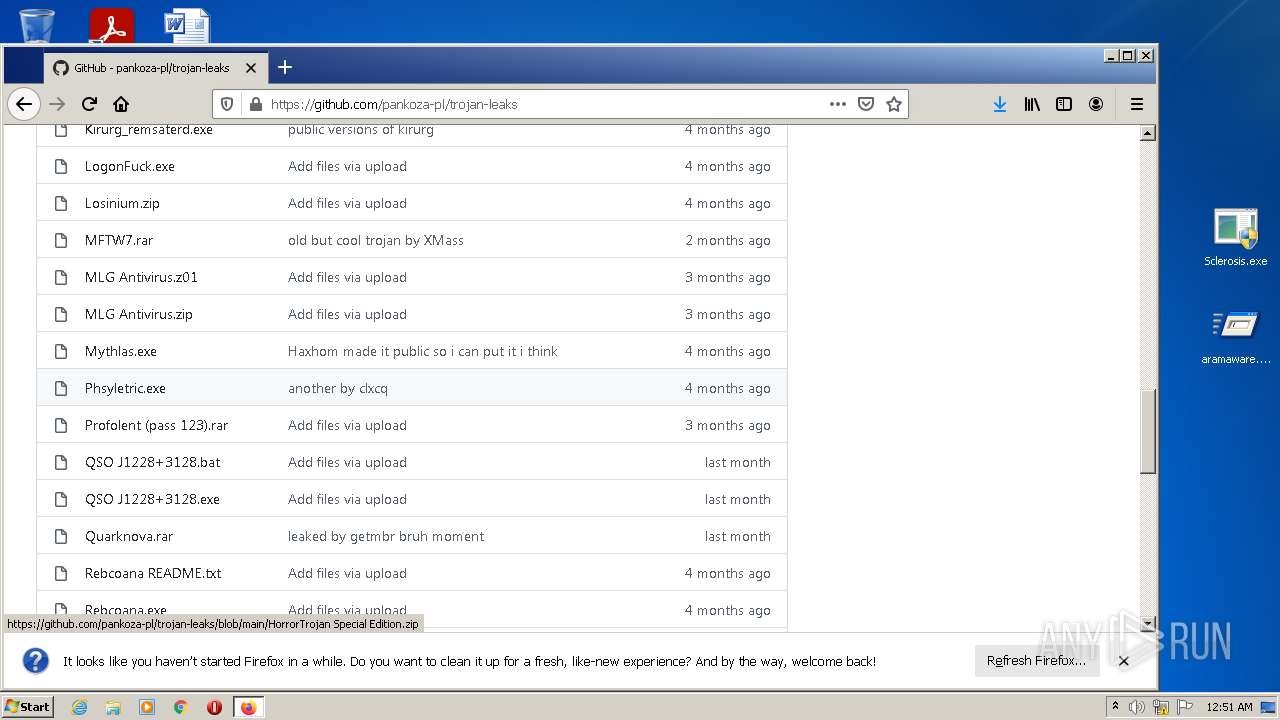
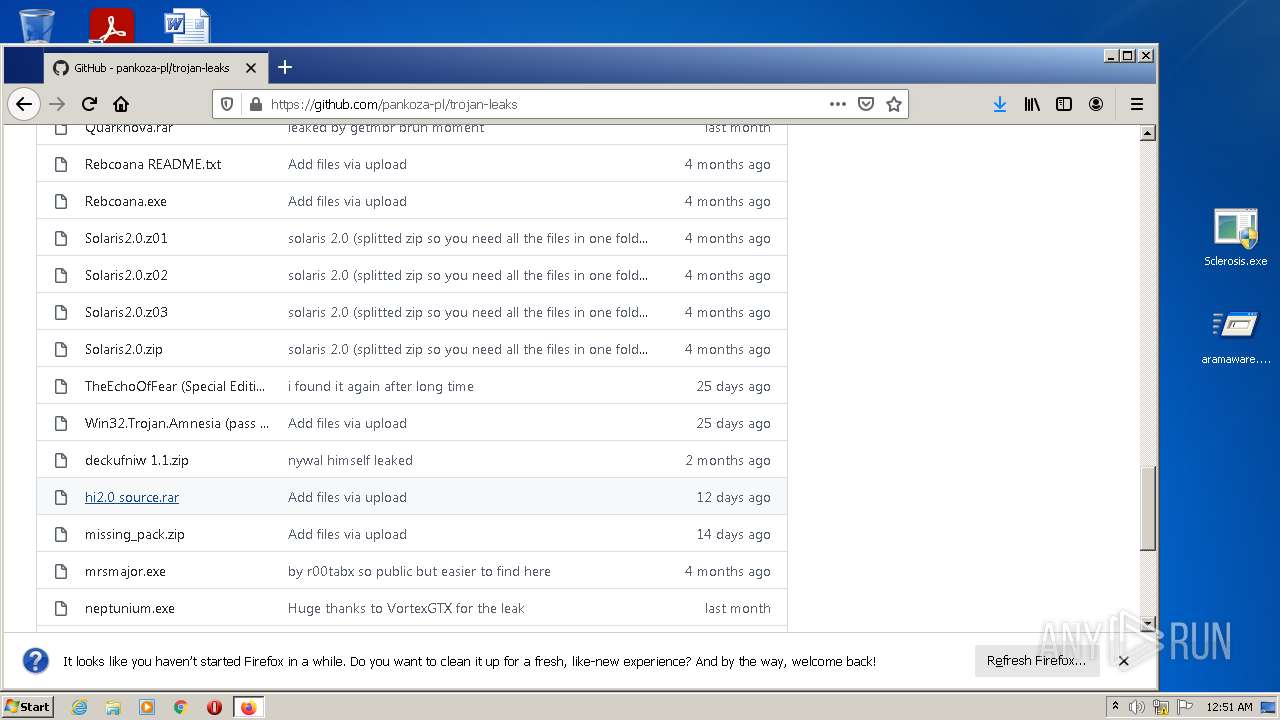
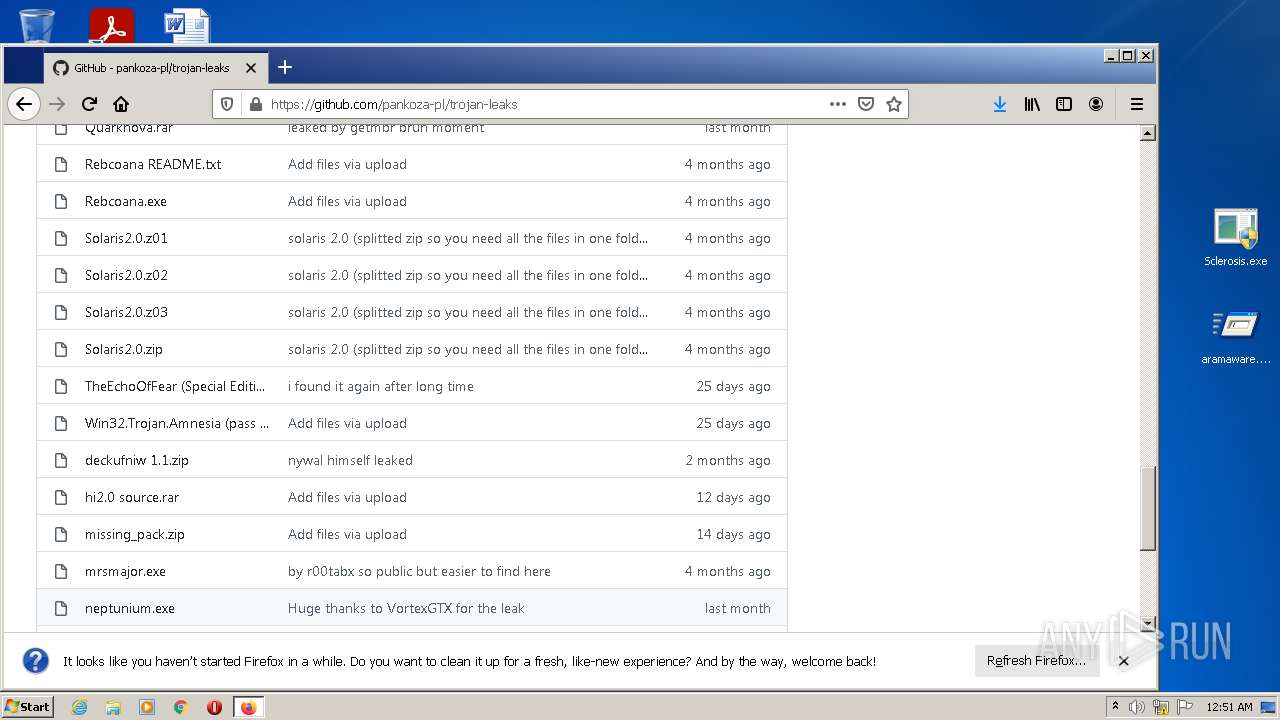
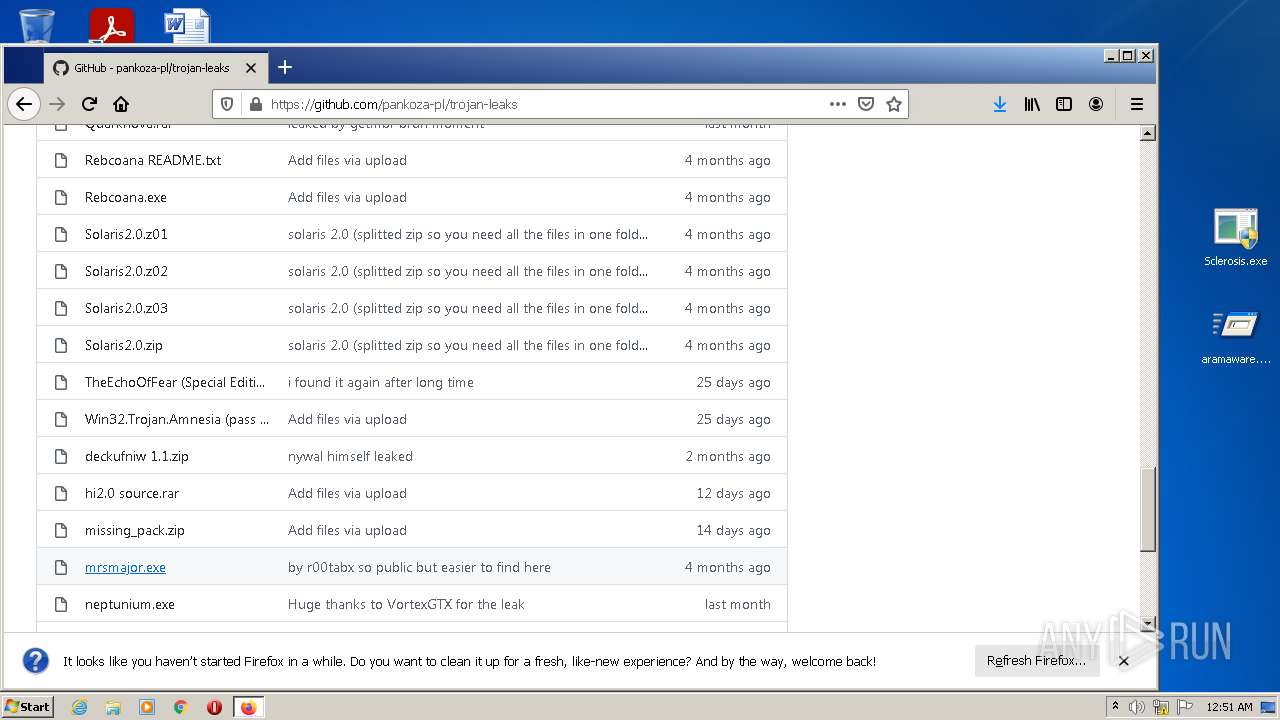
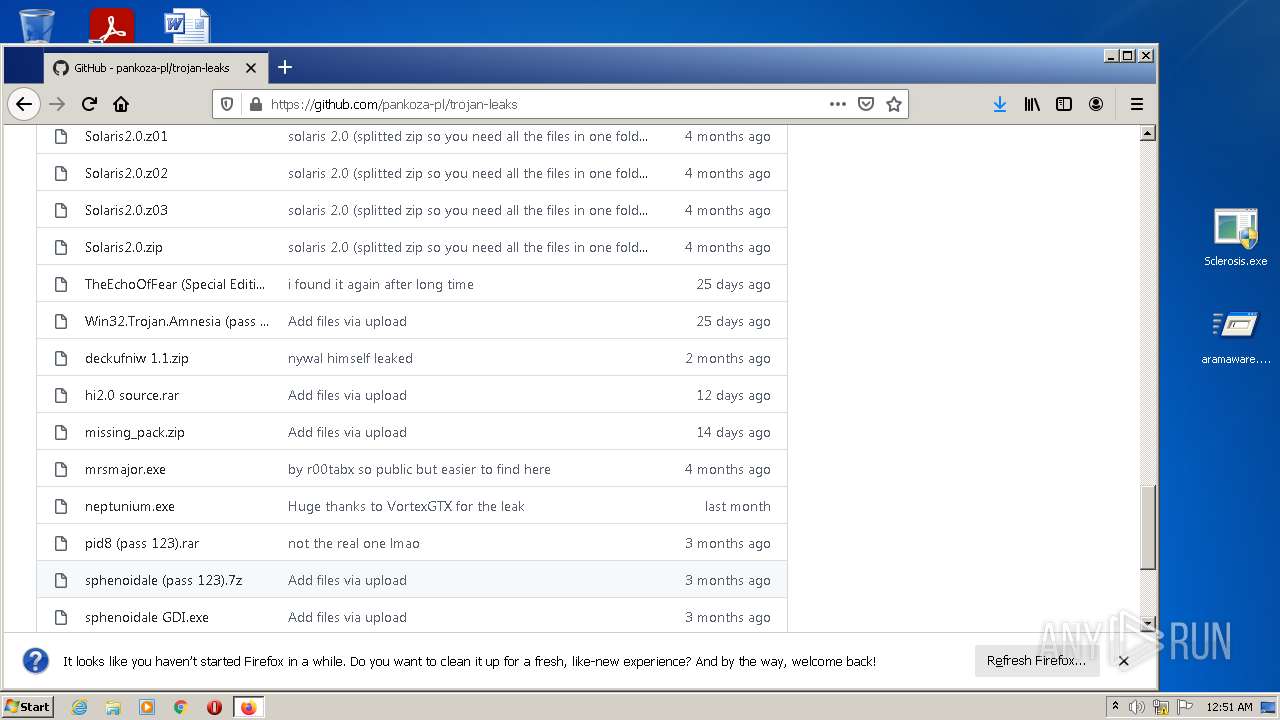
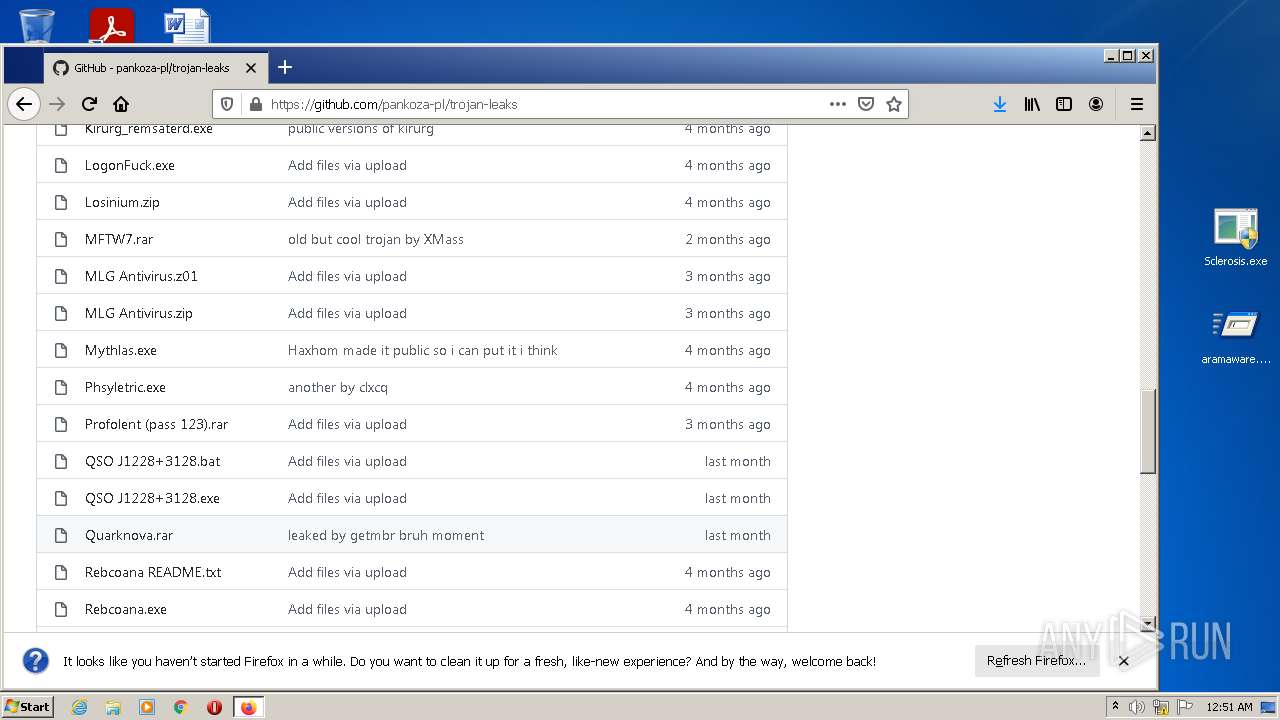
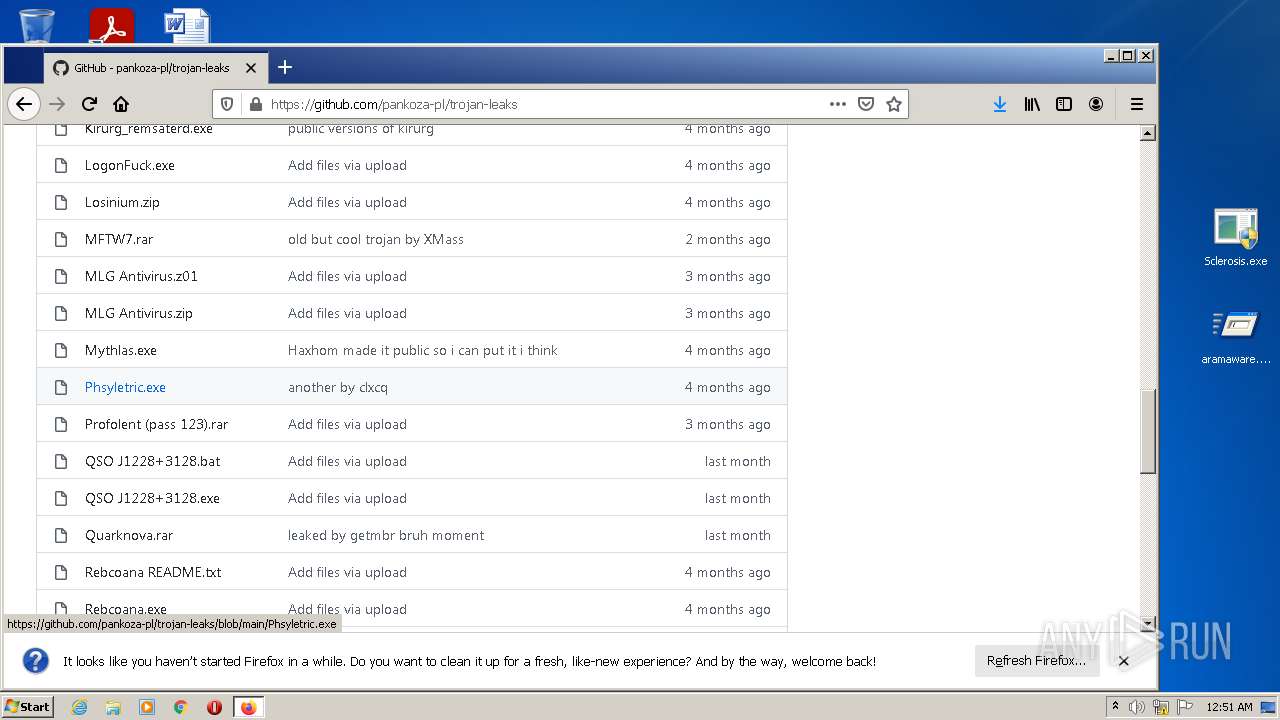
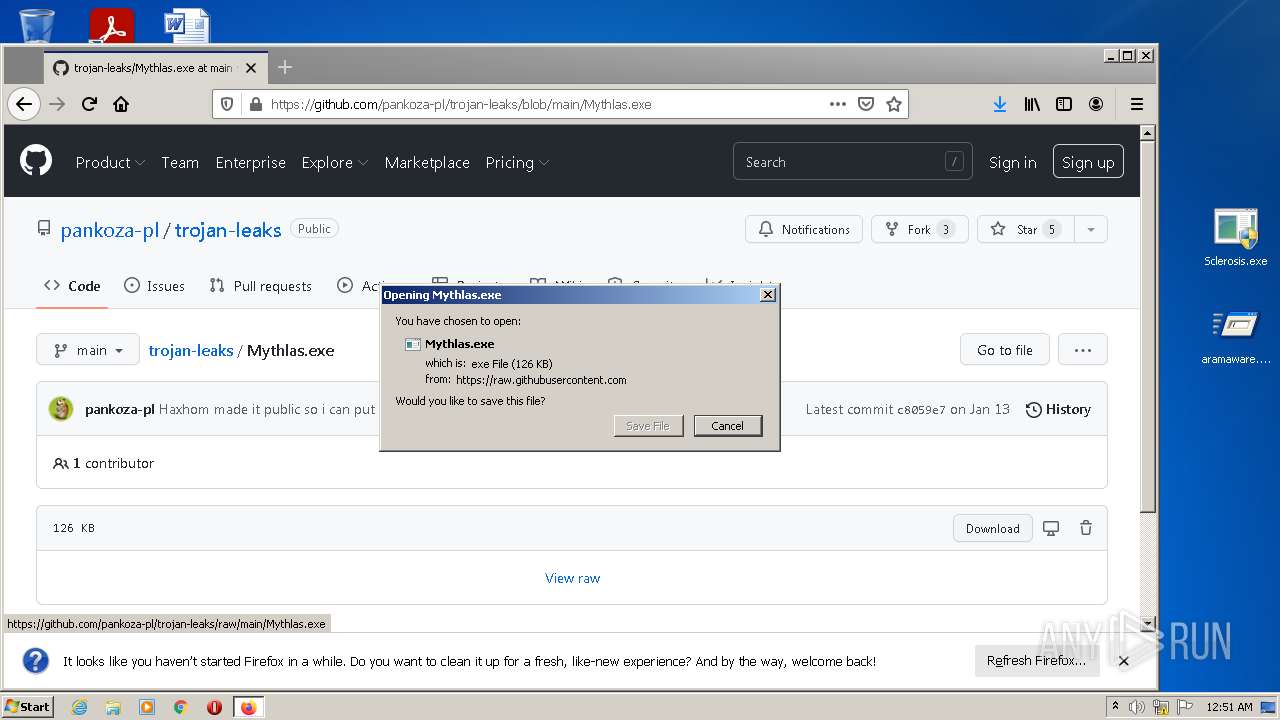
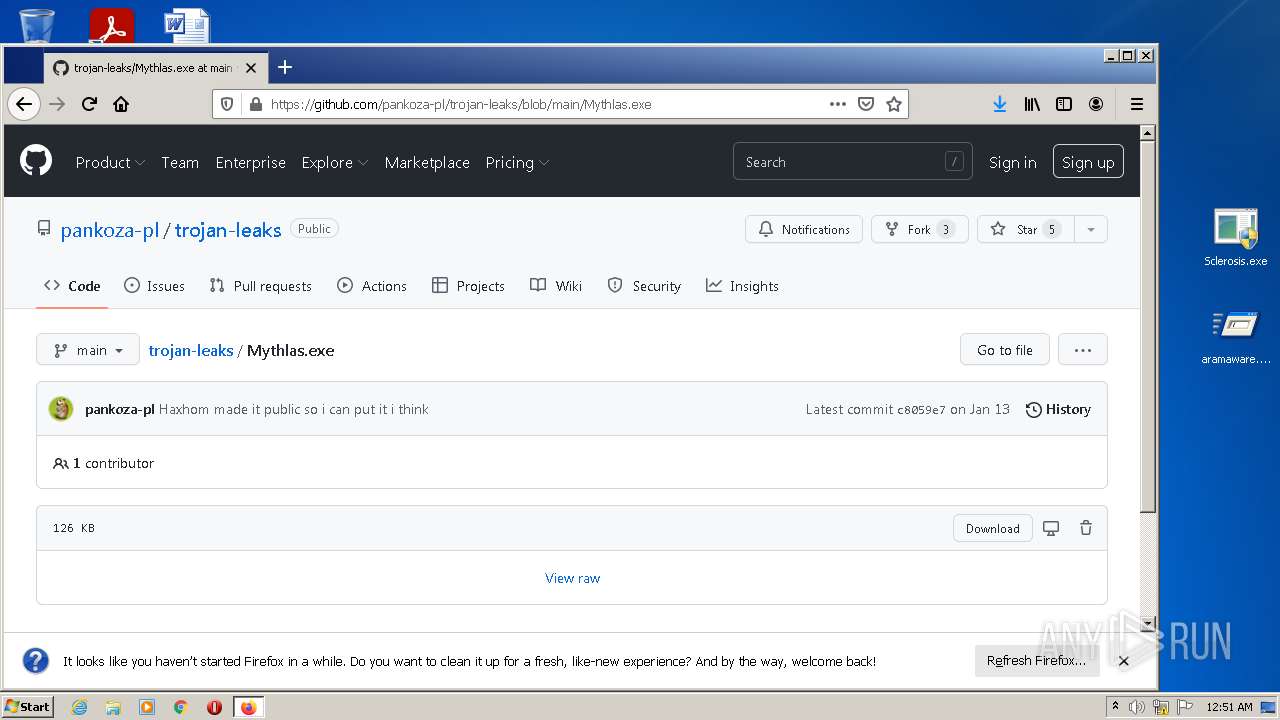
| URL: | https://github.com/pankoza-pl/Leaked-Malwares |
| Full analysis: | https://app.any.run/tasks/8fc831b7-afef-45c6-bdbb-2b3dee48d857 |
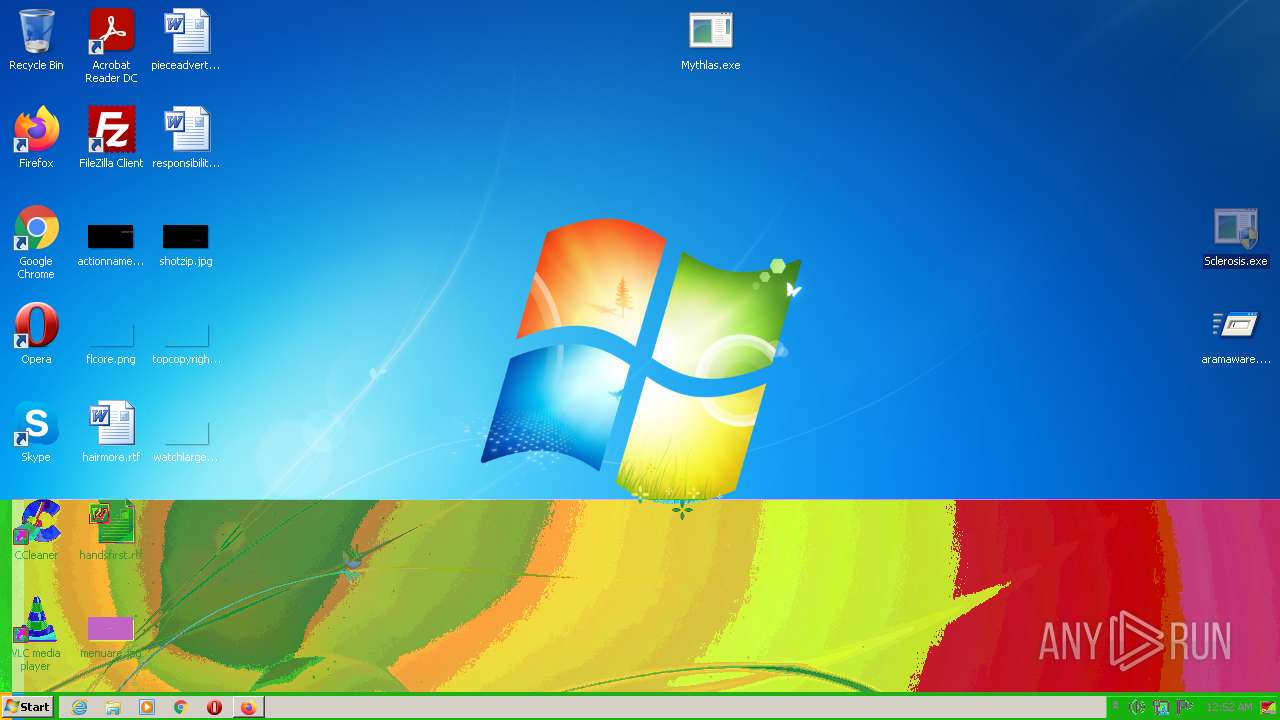
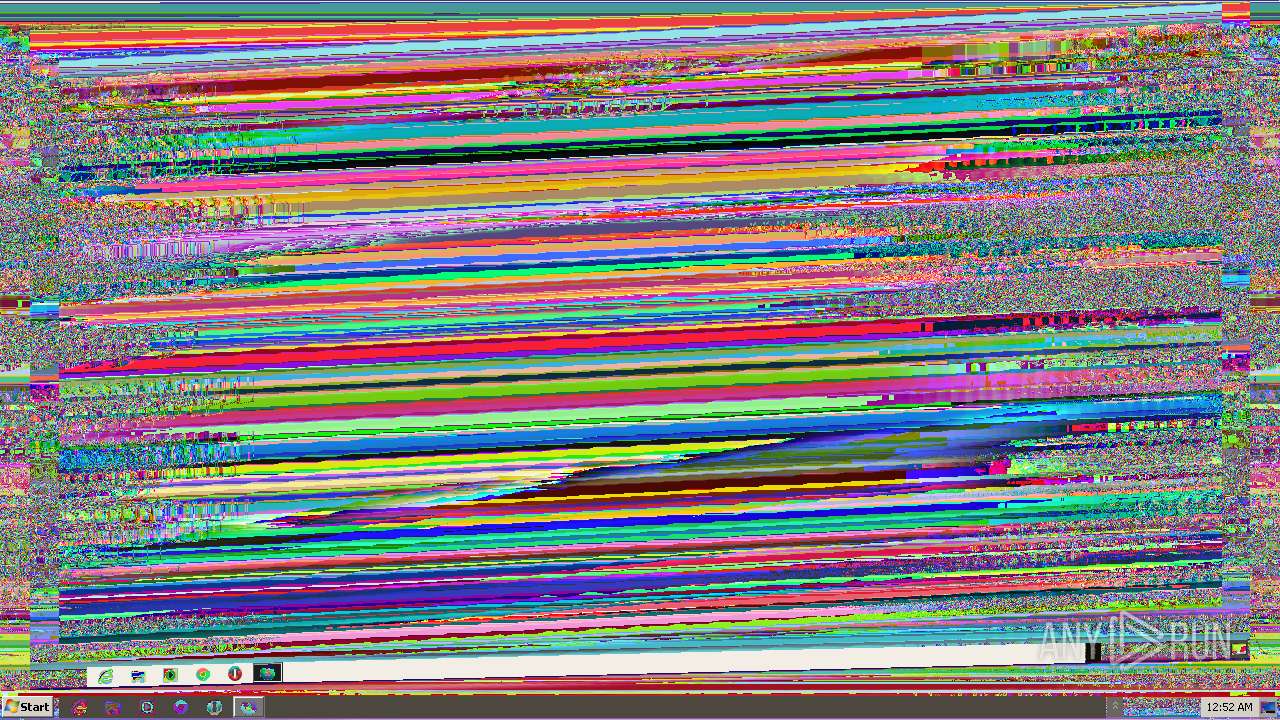
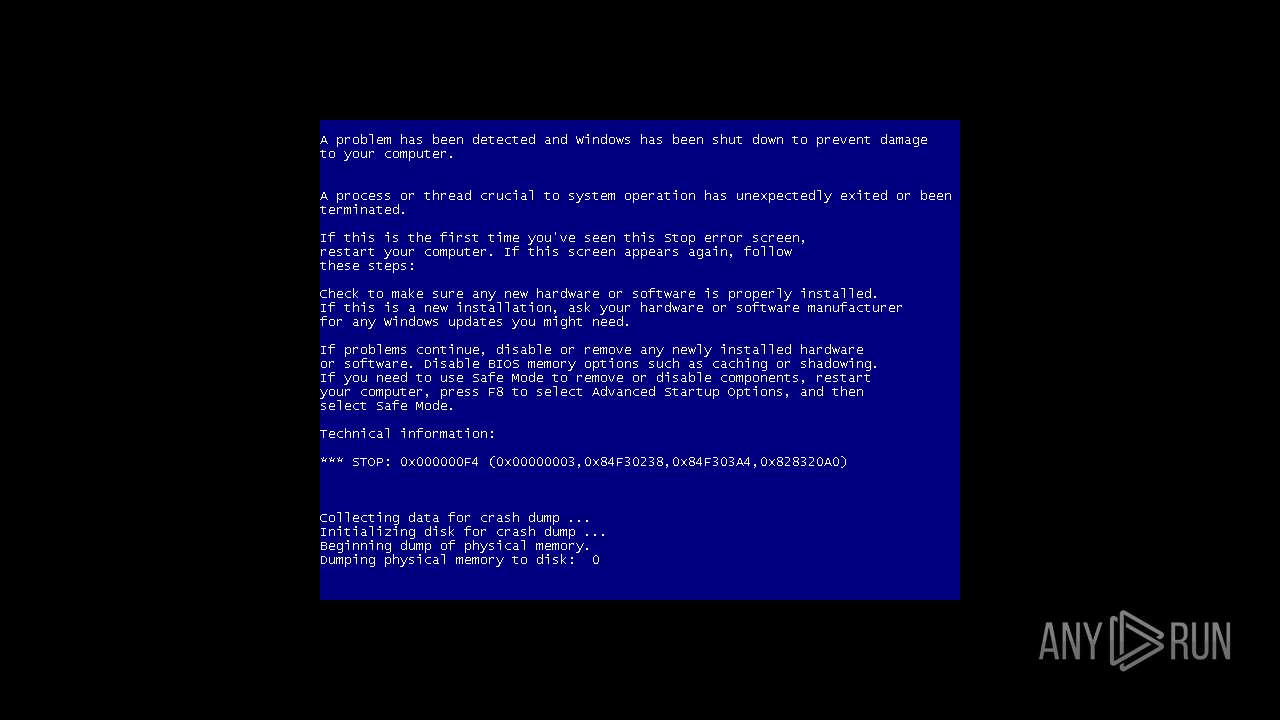
| Verdict: | Malicious activity |
| Analysis date: | May 05, 2022, 23:49:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DA7115123CE914F1BEF90E5D1EFF263C |
| SHA1: | 1764468B6E34451D512F13A0B35532DD02EE6F9E |
| SHA256: | 52D4874A6AD238A0CCC2BD312BC328609AEEE7029B4C14655F9909F3AD7A067A |
| SSDEEP: | 3:N8tEdlELlfVK6kGS+z:2uoLFjz |
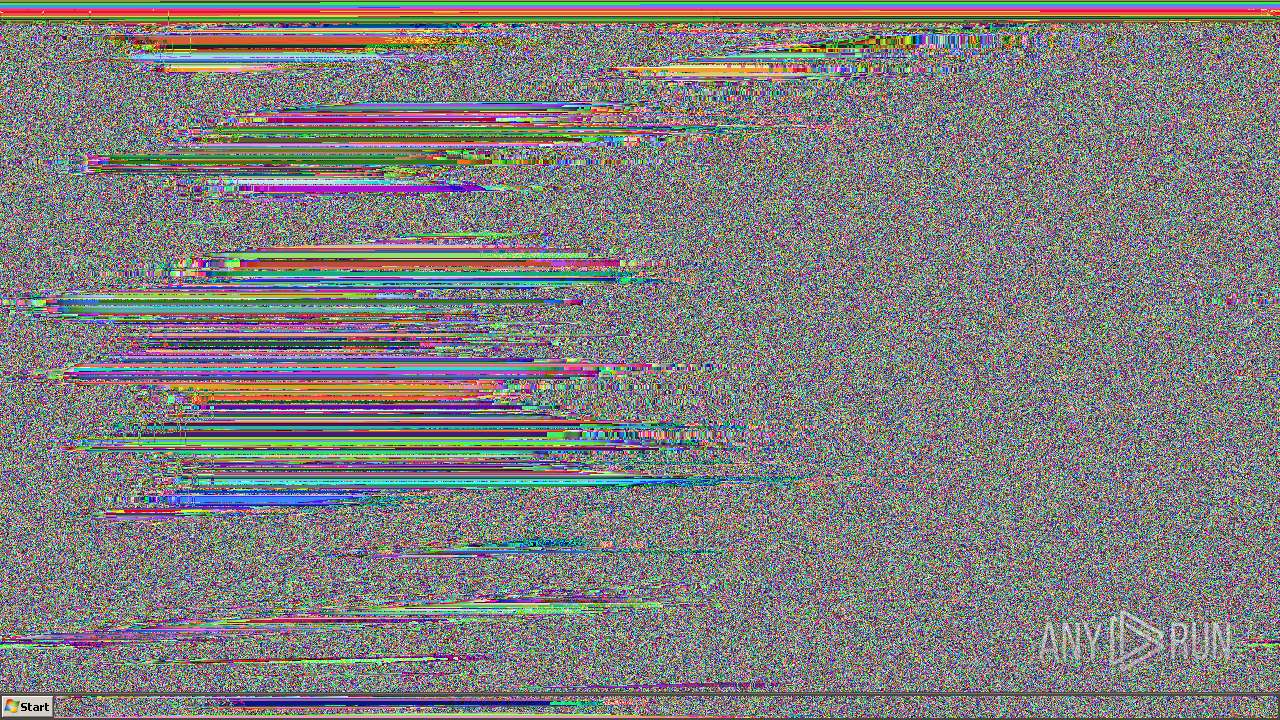
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 3760)
- firefox.exe (PID: 3316)
- WinRAR.exe (PID: 2712)
- Sclerosis.exe (PID: 3028)
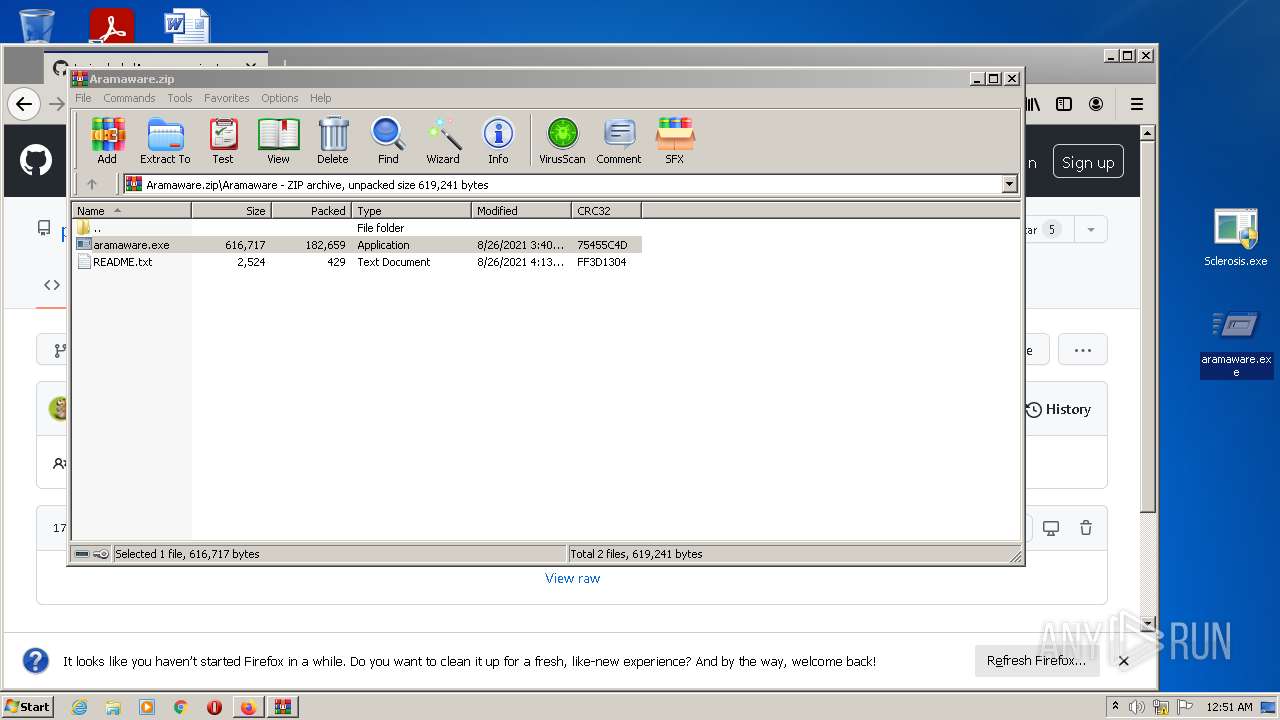
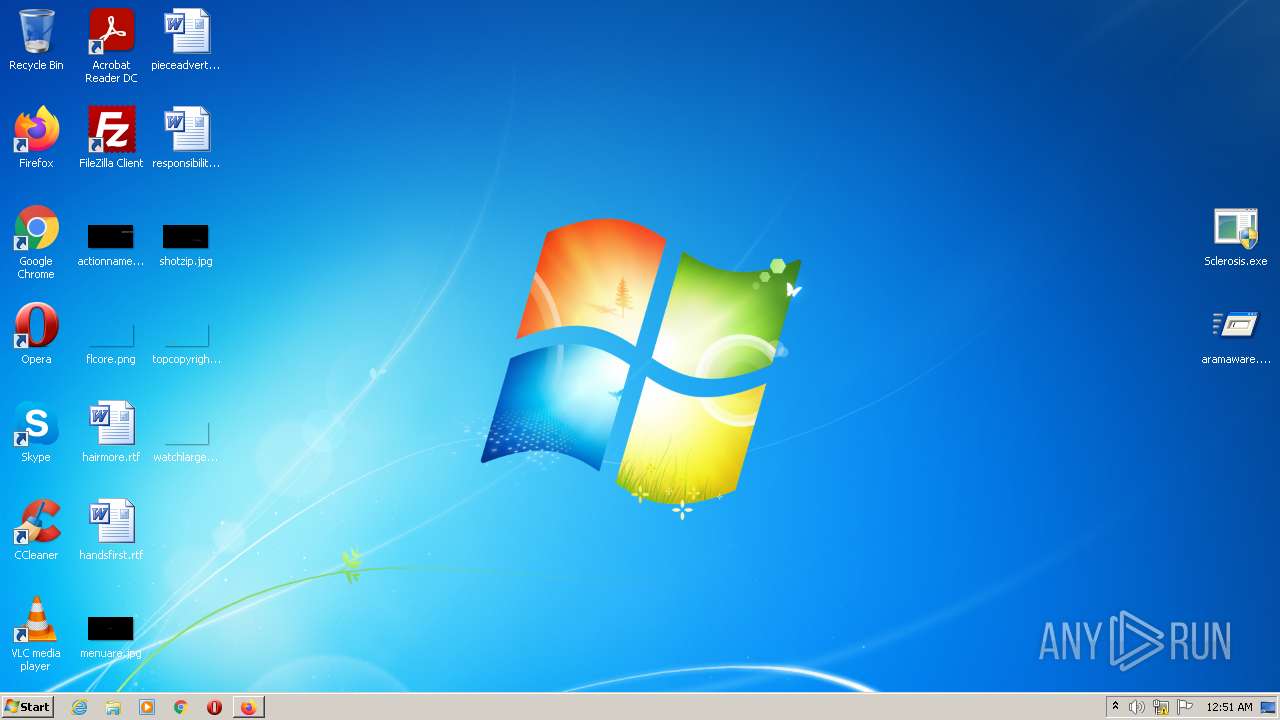
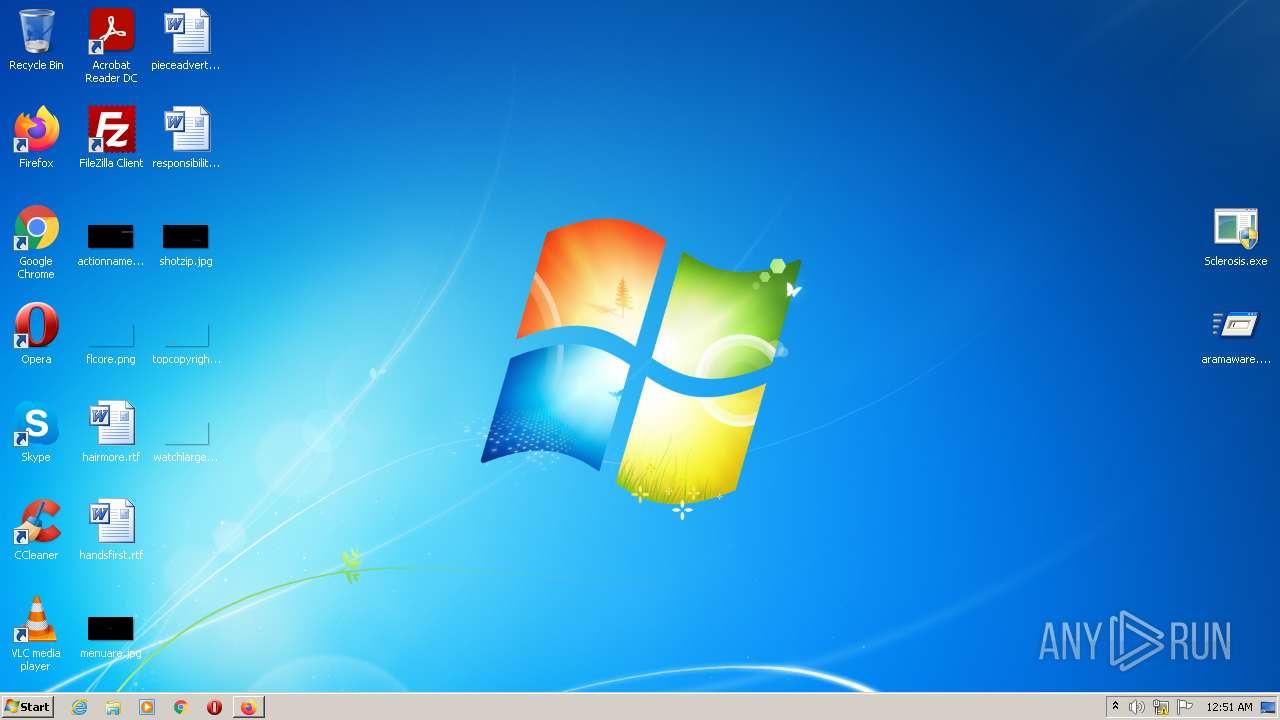
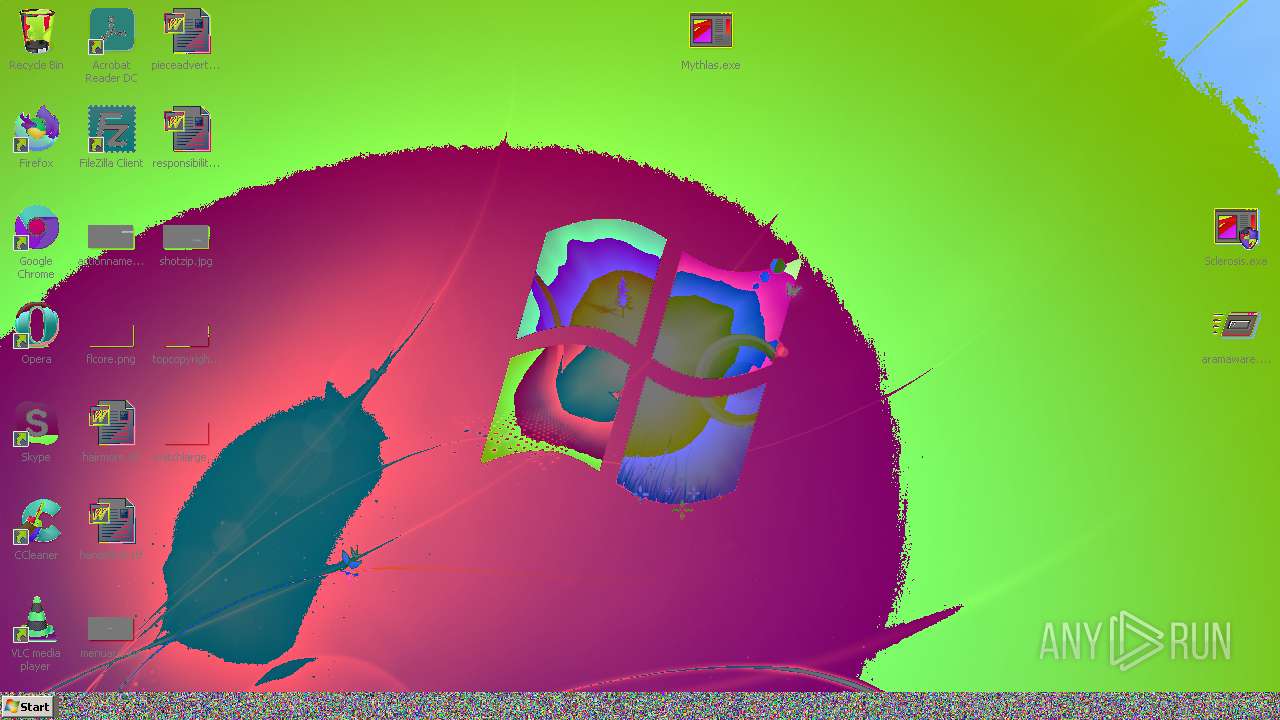
Application was dropped or rewritten from another process
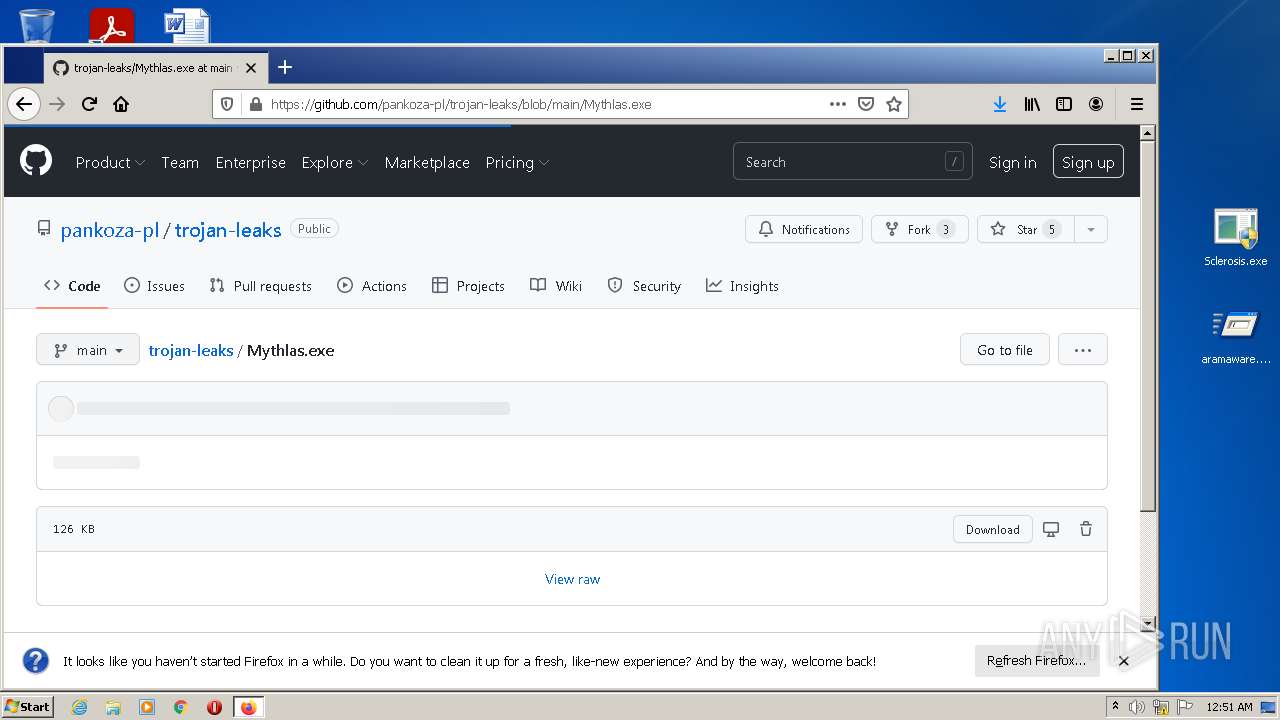
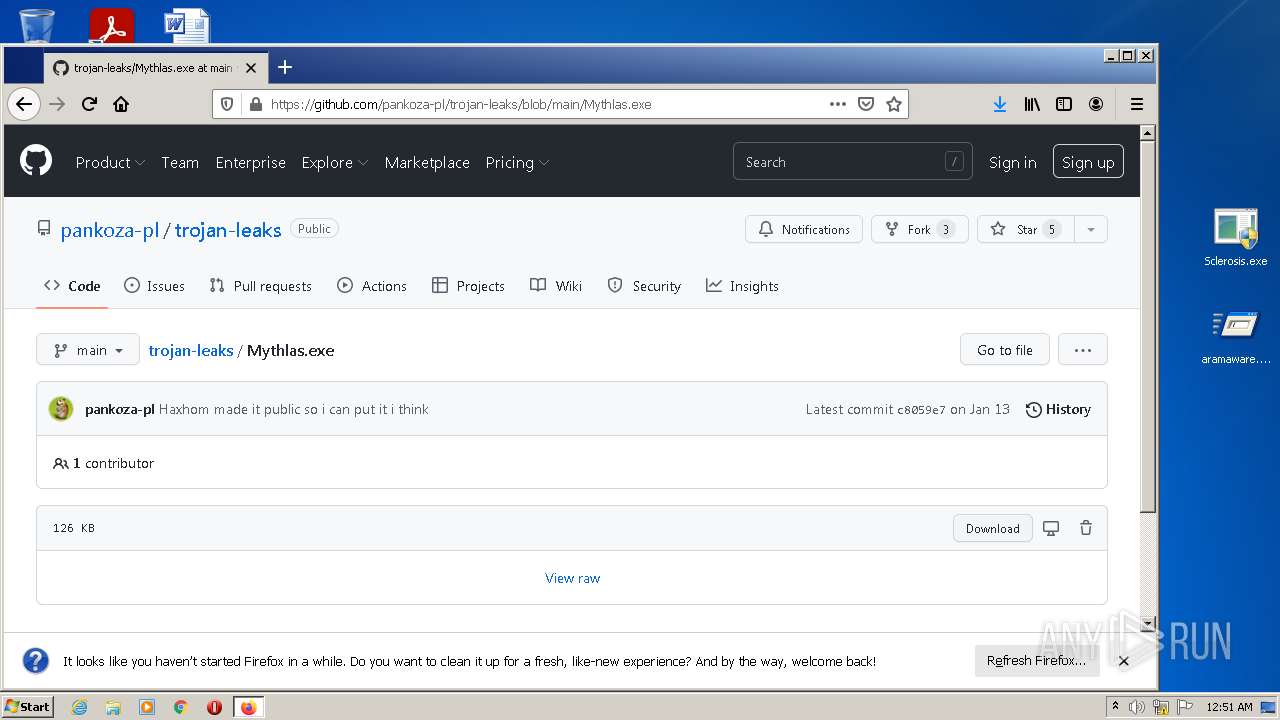
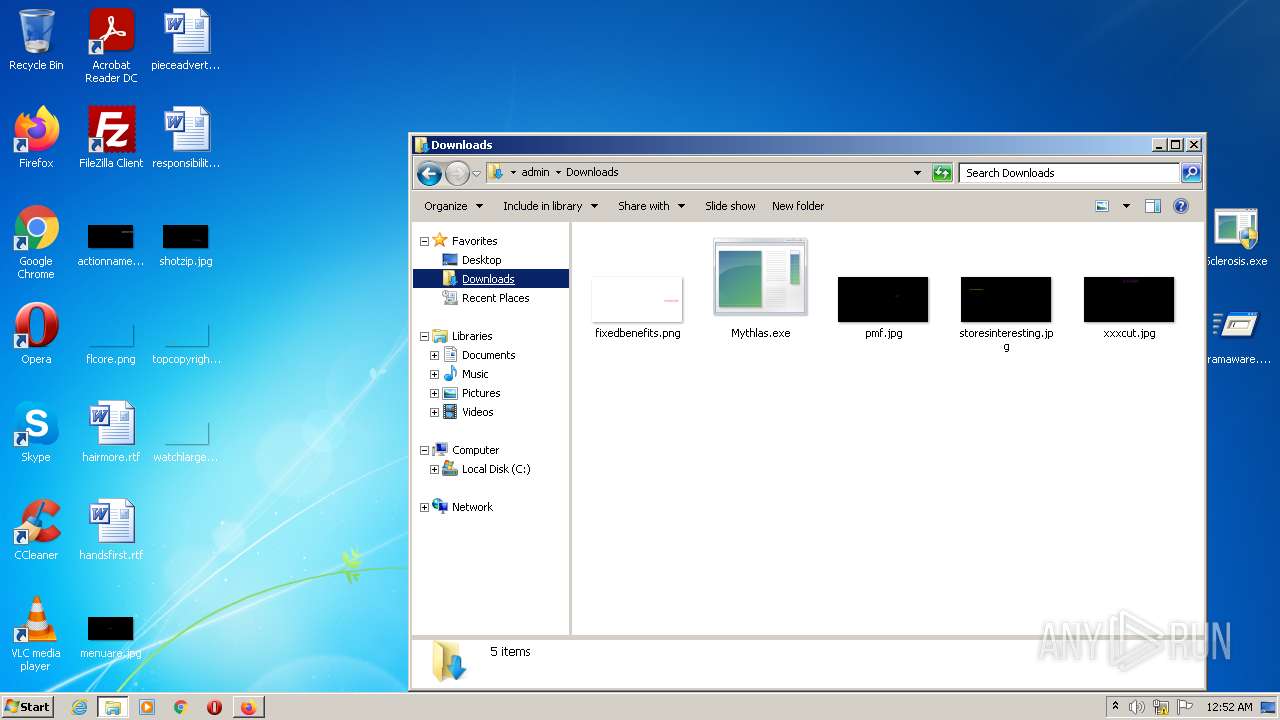
- Mythlas.exe (PID: 1564)
- aramaware.exe (PID: 2988)
- Sclerosis.exe (PID: 1856)
- Sclerosis.exe (PID: 3028)
- mbr.exe (PID: 1232)
- first.exe (PID: 2840)
- glit.exe (PID: 1156)
- invpaint.exe (PID: 3744)
- unic2.exe (PID: 2924)
- Sclerosis.exe (PID: 2896)
- Sclerosis.exe (PID: 3476)
- paint2.exe (PID: 3048)
- mbr.exe (PID: 116)
- glit.exe (PID: 3548)
- first.exe (PID: 3916)
- invpaint.exe (PID: 1396)
- m3.exe (PID: 3812)
- r3.exe (PID: 1868)
- unic2.exe (PID: 2940)
- paint2.exe (PID: 1800)
- scl.exe (PID: 2972)
- unic2.exe (PID: 2652)
- sqmove.exe (PID: 3740)
- paint2.exe (PID: 1640)
- m3.exe (PID: 3012)
- r3.exe (PID: 2288)
- m3.exe (PID: 2628)
- r3.exe (PID: 1280)
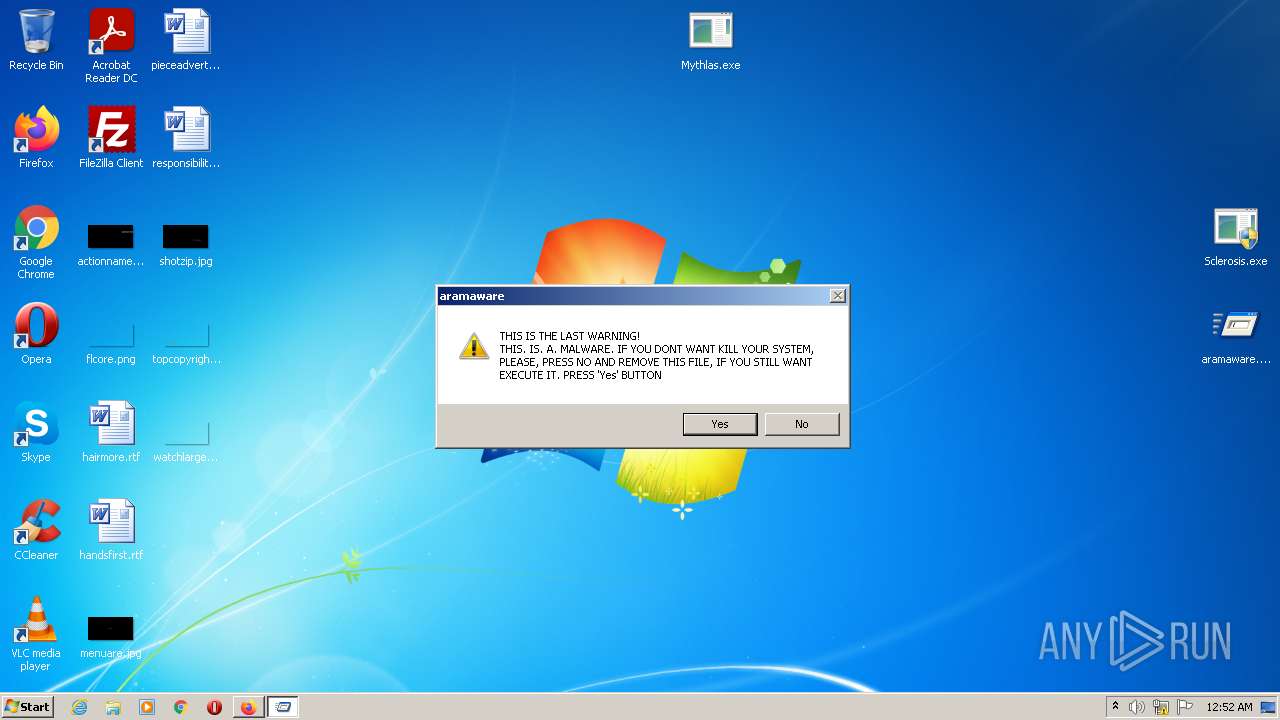
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 3076)
- reg.exe (PID: 928)
Loads dropped or rewritten executable
- glit.exe (PID: 1156)
- glit.exe (PID: 3548)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3760)
- WinRAR.exe (PID: 2712)
- Sclerosis.exe (PID: 3028)
- WScript.exe (PID: 1860)
- glit.exe (PID: 1156)
- Mythlas.exe (PID: 1564)
- Sclerosis.exe (PID: 2896)
- WScript.exe (PID: 452)
- glit.exe (PID: 3548)
Checks supported languages
- WinRAR.exe (PID: 3760)
- WinRAR.exe (PID: 2712)
- aramaware.exe (PID: 2988)
- Mythlas.exe (PID: 1564)
- cmd.exe (PID: 1024)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 3344)
- cmd.exe (PID: 3740)
- cmd.exe (PID: 268)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 1368)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 764)
- Sclerosis.exe (PID: 3028)
- WScript.exe (PID: 1860)
- cmd.exe (PID: 3980)
- mbr.exe (PID: 1232)
- glit.exe (PID: 1156)
- first.exe (PID: 2840)
- Sclerosis.exe (PID: 2896)
- invpaint.exe (PID: 3744)
- unic2.exe (PID: 2924)
- WScript.exe (PID: 452)
- paint2.exe (PID: 3048)
- cmd.exe (PID: 2636)
- mbr.exe (PID: 116)
- glit.exe (PID: 3548)
- invpaint.exe (PID: 1396)
- m3.exe (PID: 3812)
- r3.exe (PID: 1868)
- paint2.exe (PID: 1800)
- unic2.exe (PID: 2940)
- scl.exe (PID: 2972)
- sqmove.exe (PID: 3740)
- unic2.exe (PID: 2652)
- m3.exe (PID: 3012)
- r3.exe (PID: 2288)
- m3.exe (PID: 2628)
- r3.exe (PID: 1280)
- paint2.exe (PID: 1640)
- first.exe (PID: 3916)
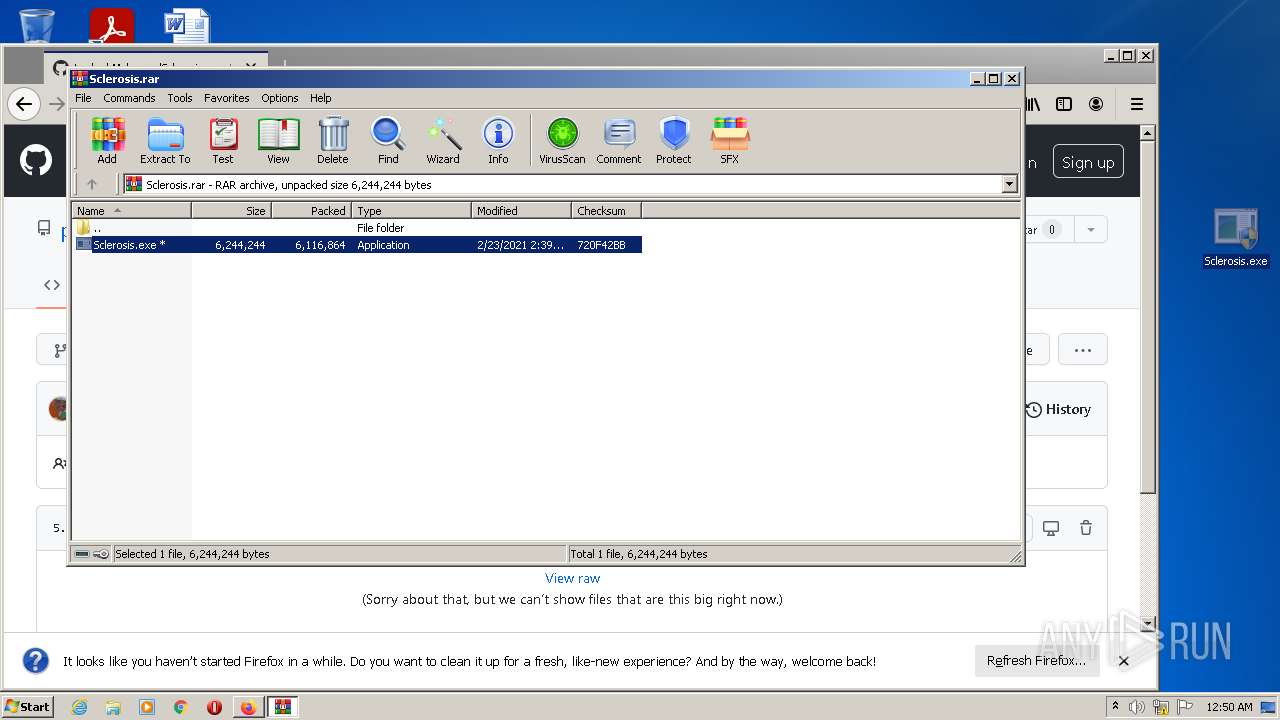
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2712)
- WinRAR.exe (PID: 3760)
- firefox.exe (PID: 3316)
- Sclerosis.exe (PID: 3028)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3760)
- WinRAR.exe (PID: 2712)
- firefox.exe (PID: 3316)
- Sclerosis.exe (PID: 3028)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3740)
- cmd.exe (PID: 3344)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 2636)
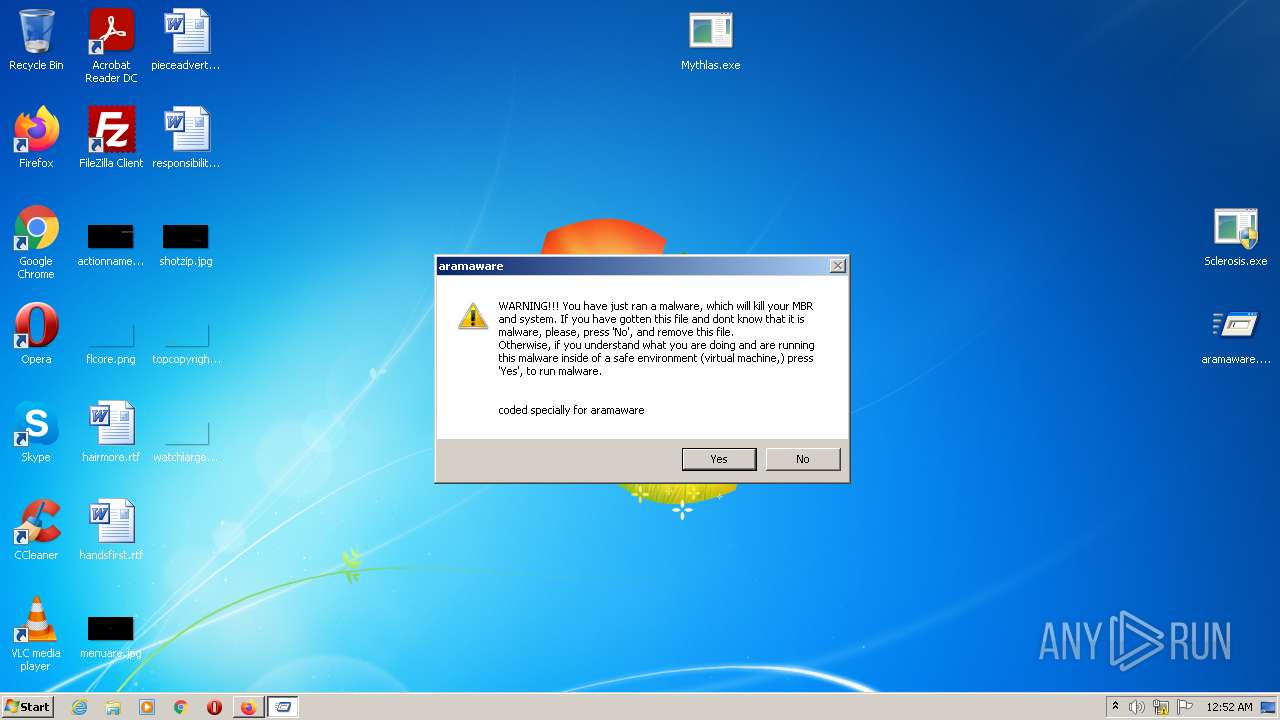
Starts CMD.EXE for commands execution
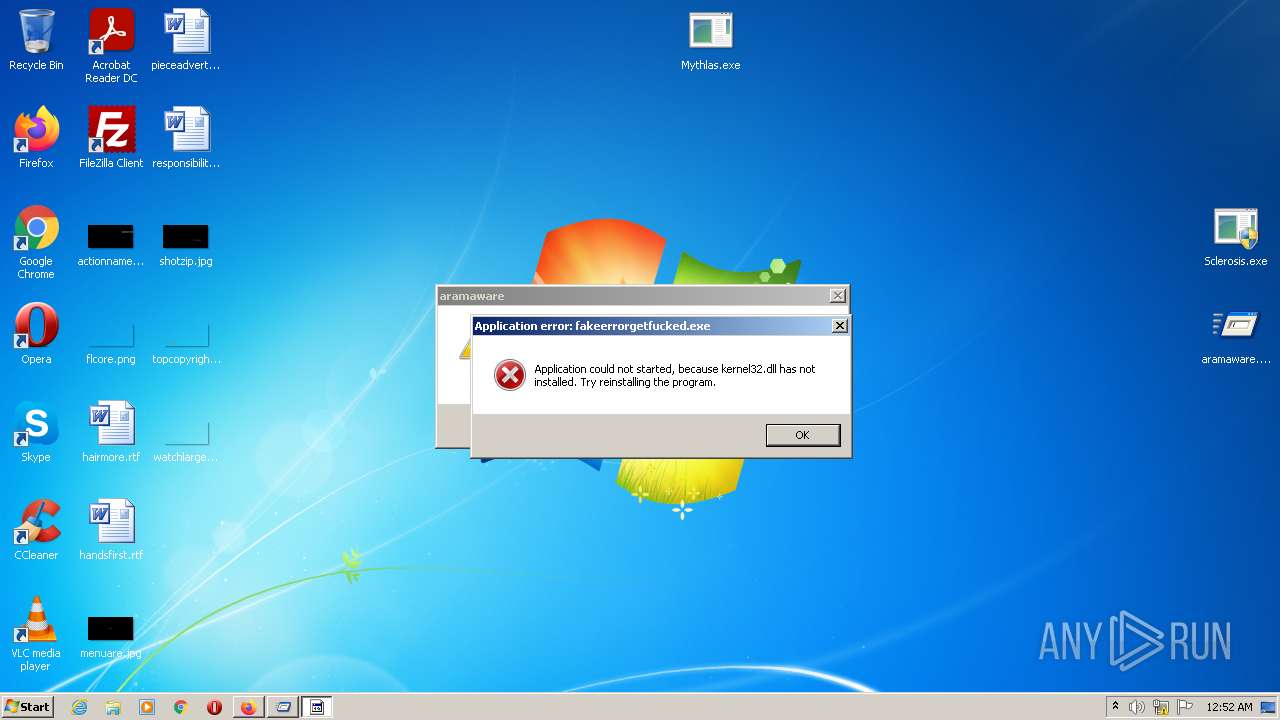
- aramaware.exe (PID: 2988)
- WScript.exe (PID: 1860)
- WScript.exe (PID: 452)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2116)
- cmd.exe (PID: 268)
Removes files from Windows directory
- Sclerosis.exe (PID: 3028)
- Sclerosis.exe (PID: 2896)
Creates files in the Windows directory
- Sclerosis.exe (PID: 3028)
- Sclerosis.exe (PID: 2896)
Executes scripts
- Sclerosis.exe (PID: 3028)
- Sclerosis.exe (PID: 2896)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3980)
- cmd.exe (PID: 2636)
INFO
Application launched itself
- firefox.exe (PID: 2908)
- firefox.exe (PID: 3316)
Reads the computer name
- firefox.exe (PID: 3316)
- firefox.exe (PID: 3560)
- firefox.exe (PID: 3504)
- firefox.exe (PID: 2280)
- firefox.exe (PID: 3436)
- firefox.exe (PID: 2720)
- firefox.exe (PID: 3352)
- firefox.exe (PID: 1620)
- takeown.exe (PID: 1032)
- takeown.exe (PID: 3460)
- taskkill.exe (PID: 1780)
- taskkill.exe (PID: 3012)
- taskkill.exe (PID: 4064)
- taskkill.exe (PID: 1536)
- taskkill.exe (PID: 3736)
- taskkill.exe (PID: 2504)
- taskkill.exe (PID: 3696)
- taskkill.exe (PID: 928)
- taskkill.exe (PID: 3900)
- taskkill.exe (PID: 128)
- taskkill.exe (PID: 1864)
Checks supported languages
- firefox.exe (PID: 3316)
- firefox.exe (PID: 3560)
- firefox.exe (PID: 2908)
- firefox.exe (PID: 3436)
- firefox.exe (PID: 3504)
- firefox.exe (PID: 2280)
- firefox.exe (PID: 3352)
- firefox.exe (PID: 2720)
- firefox.exe (PID: 1620)
- reg.exe (PID: 2692)
- takeown.exe (PID: 1032)
- reg.exe (PID: 1452)
- takeown.exe (PID: 3460)
- icacls.exe (PID: 616)
- icacls.exe (PID: 3756)
- timeout.exe (PID: 1504)
- reg.exe (PID: 3076)
- timeout.exe (PID: 3856)
- taskkill.exe (PID: 1780)
- taskkill.exe (PID: 3012)
- timeout.exe (PID: 2140)
- timeout.exe (PID: 3900)
- reg.exe (PID: 928)
- timeout.exe (PID: 760)
- timeout.exe (PID: 2628)
- taskkill.exe (PID: 1536)
- taskkill.exe (PID: 4064)
- timeout.exe (PID: 2268)
- taskkill.exe (PID: 3736)
- timeout.exe (PID: 2388)
- taskkill.exe (PID: 2504)
- taskkill.exe (PID: 928)
- timeout.exe (PID: 3988)
- timeout.exe (PID: 1980)
- timeout.exe (PID: 1876)
- taskkill.exe (PID: 3696)
- timeout.exe (PID: 2916)
- taskkill.exe (PID: 3900)
- taskkill.exe (PID: 128)
- timeout.exe (PID: 2396)
- taskkill.exe (PID: 1864)
Reads CPU info
- firefox.exe (PID: 3316)
Creates files in the program directory
- firefox.exe (PID: 3316)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3316)
Checks Windows Trust Settings
- firefox.exe (PID: 3316)
- WScript.exe (PID: 1860)
- WScript.exe (PID: 452)
Reads the date of Windows installation
- firefox.exe (PID: 3316)
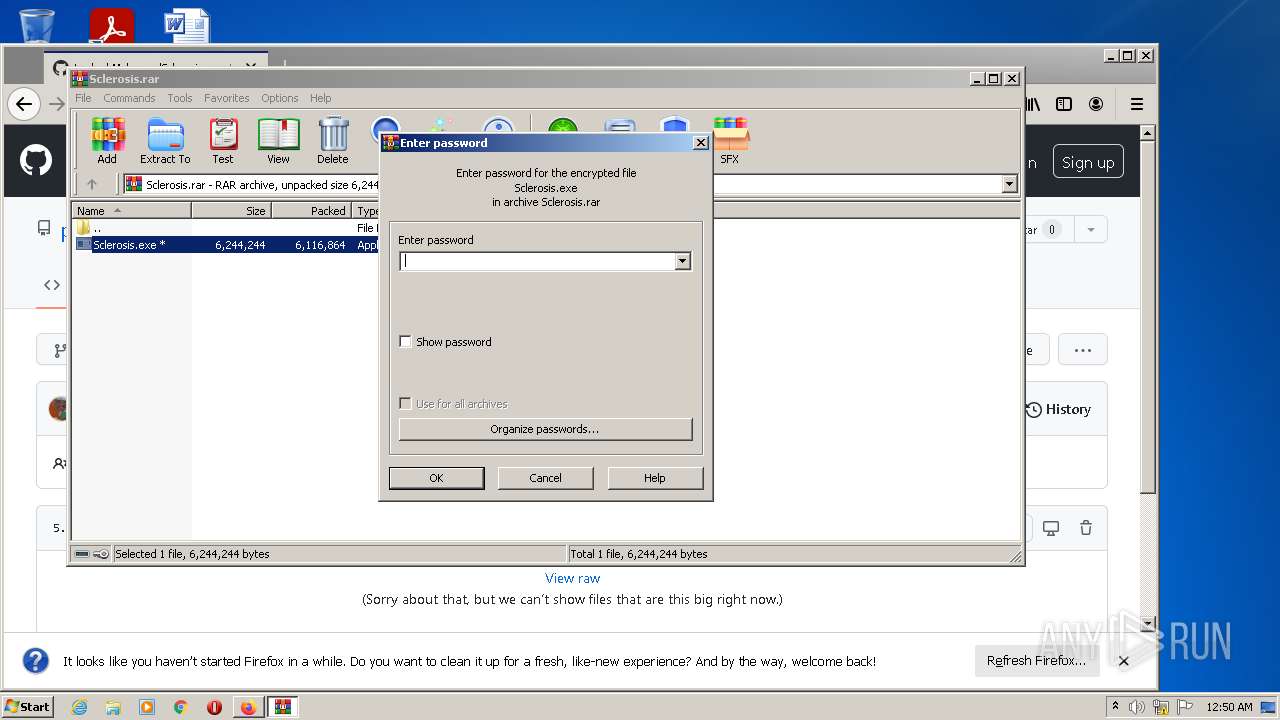
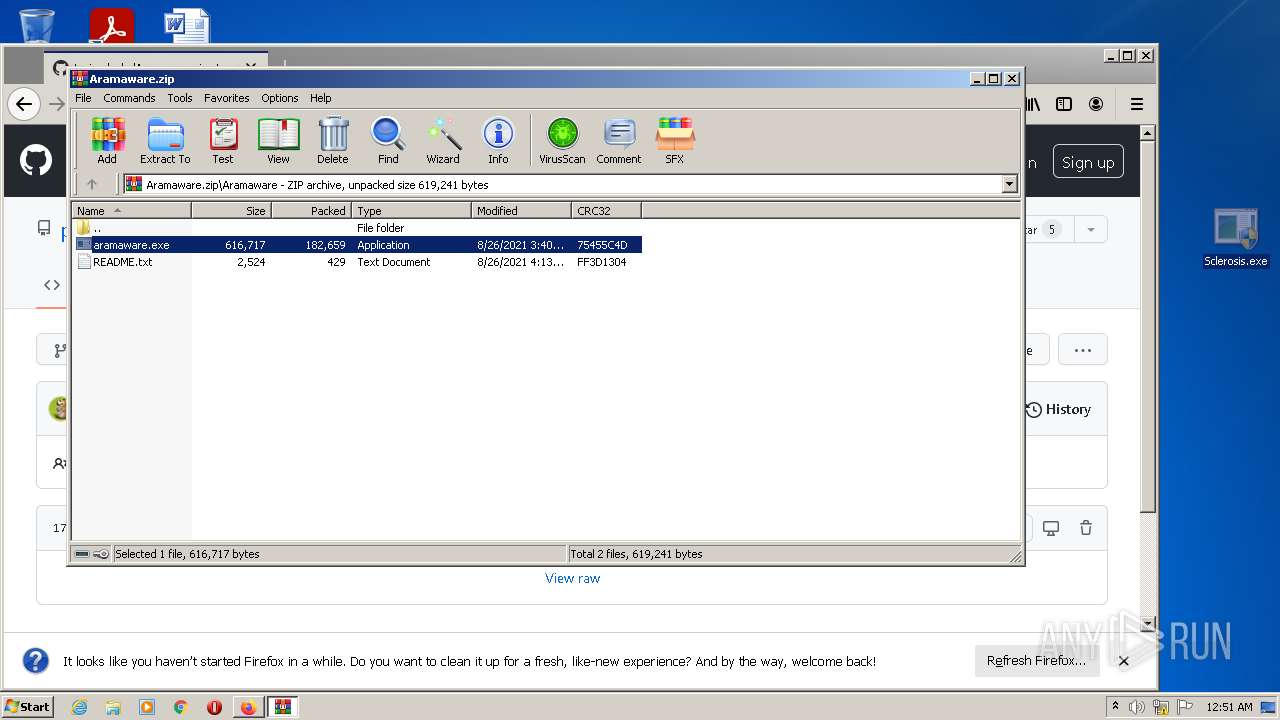
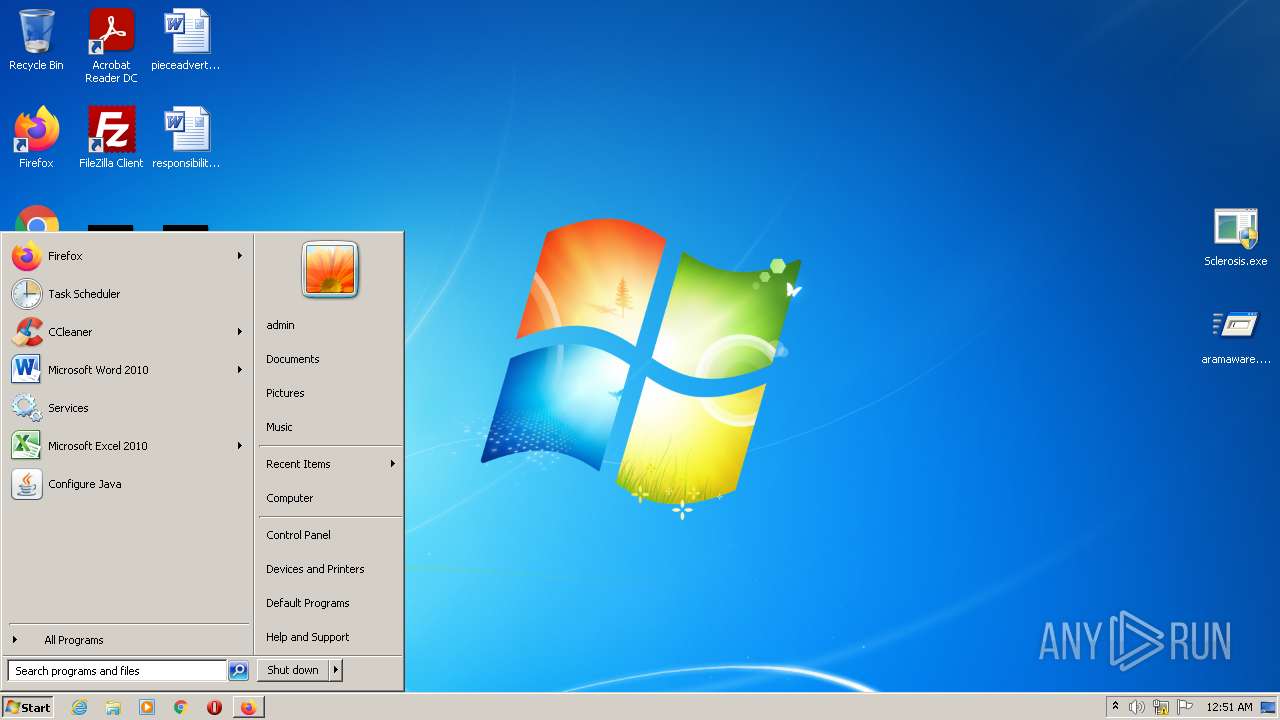
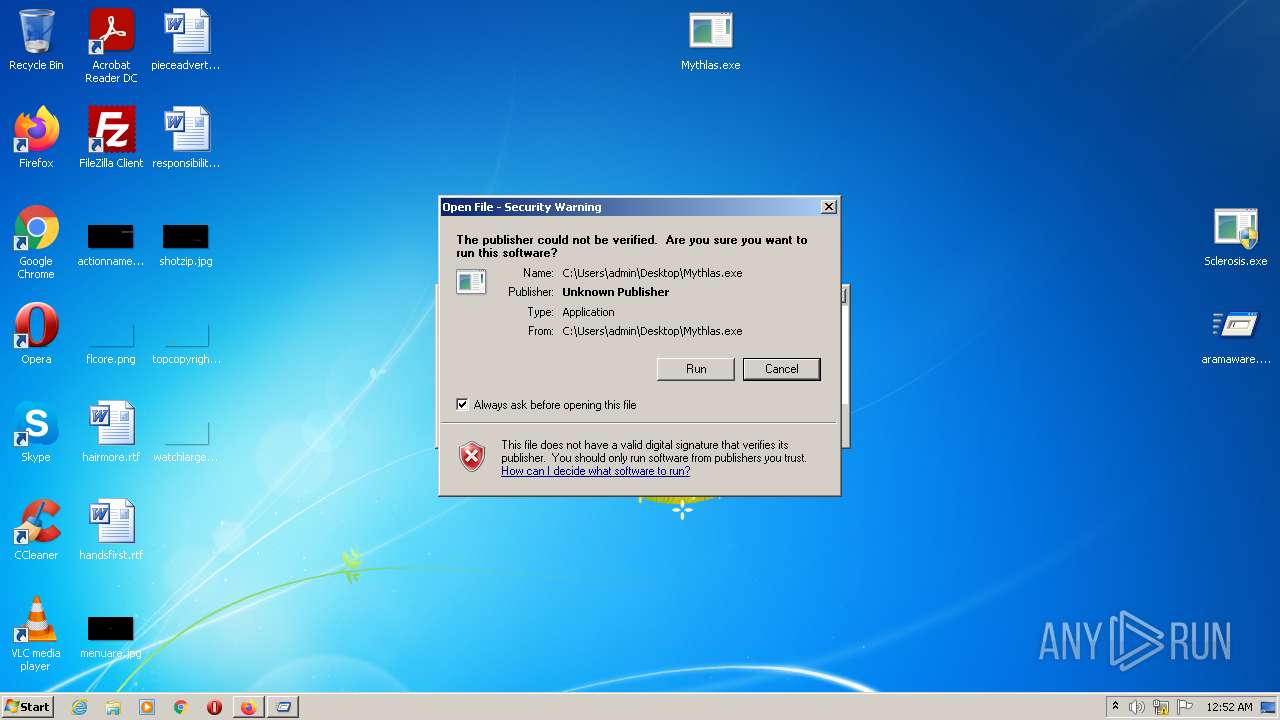
Manual execution by user
- WinRAR.exe (PID: 3760)
- WinRAR.exe (PID: 2712)
- aramaware.exe (PID: 2988)
- Mythlas.exe (PID: 1564)
- Sclerosis.exe (PID: 1856)
- Sclerosis.exe (PID: 3028)
- Sclerosis.exe (PID: 2896)
- Sclerosis.exe (PID: 3476)
Creates files in the user directory
- firefox.exe (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
146
Monitored processes
86
Malicious processes
10
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | mbr.exe | C:\Windows\Sclerosis\mbr.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 128 | taskkill /f /im unic2.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
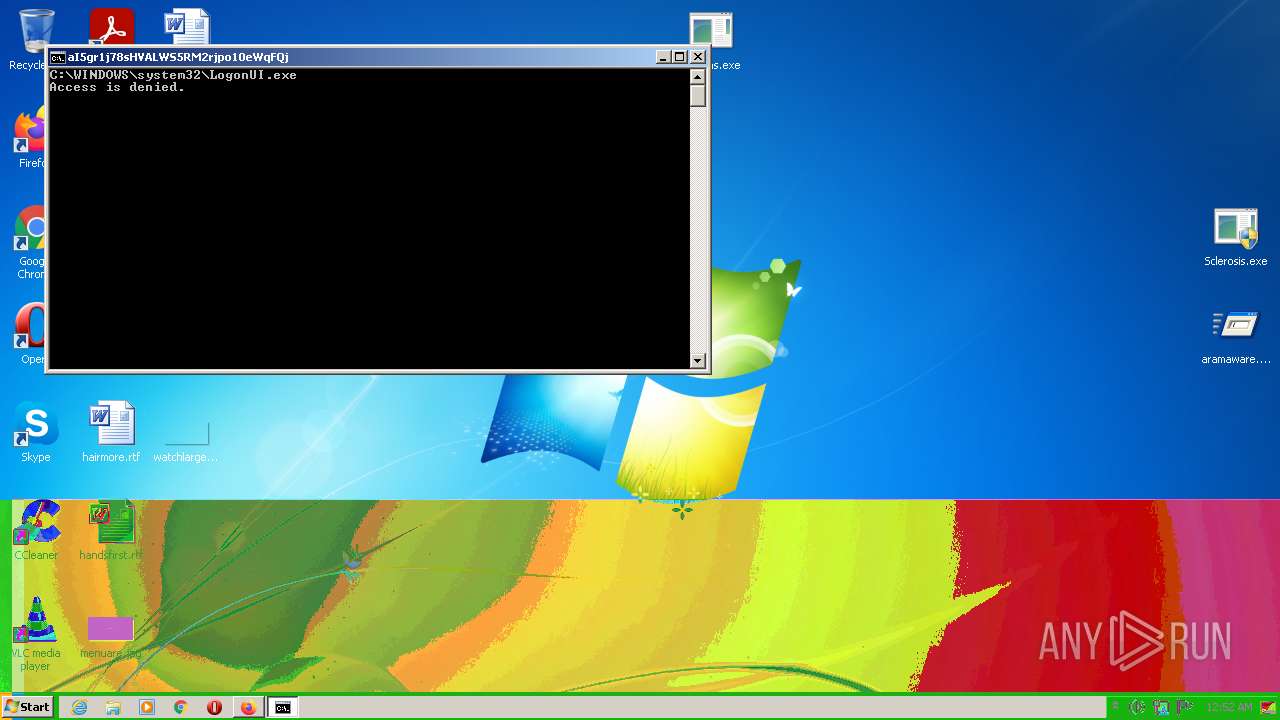
| 268 | C:\Windows\system32\cmd.exe /c icacls %WINDIR%\system32\logonui.exe /Grant:r %UserName% :F | C:\Windows\system32\cmd.exe | — | aramaware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 87 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 452 | "C:\Windows\System32\WScript.exe" "C:\Windows\Sclerosis\run.vbs" | C:\Windows\System32\WScript.exe | — | Sclerosis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 616 | icacls C:\Windows\system32\logonui.exe /Grant:r admin :F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 87 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 760 | timeout 2 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | C:\Windows\system32\cmd.exe /c assoc .vbs=.html | C:\Windows\system32\cmd.exe | — | aramaware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 928 | REG add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | taskkill /f /im r3.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | C:\Windows\system32\cmd.exe /c takeown /F %WINDIR%\system32\dllcache\logonui.exe | C:\Windows\system32\cmd.exe | — | aramaware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
18 361
Read events
18 230
Write events
131
Delete events
0
Modification events
| (PID) Process: | (2908) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 35A67E3342000000 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: EFAD7E3342000000 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
19
Suspicious files
134
Text files
47
Unknown types
36
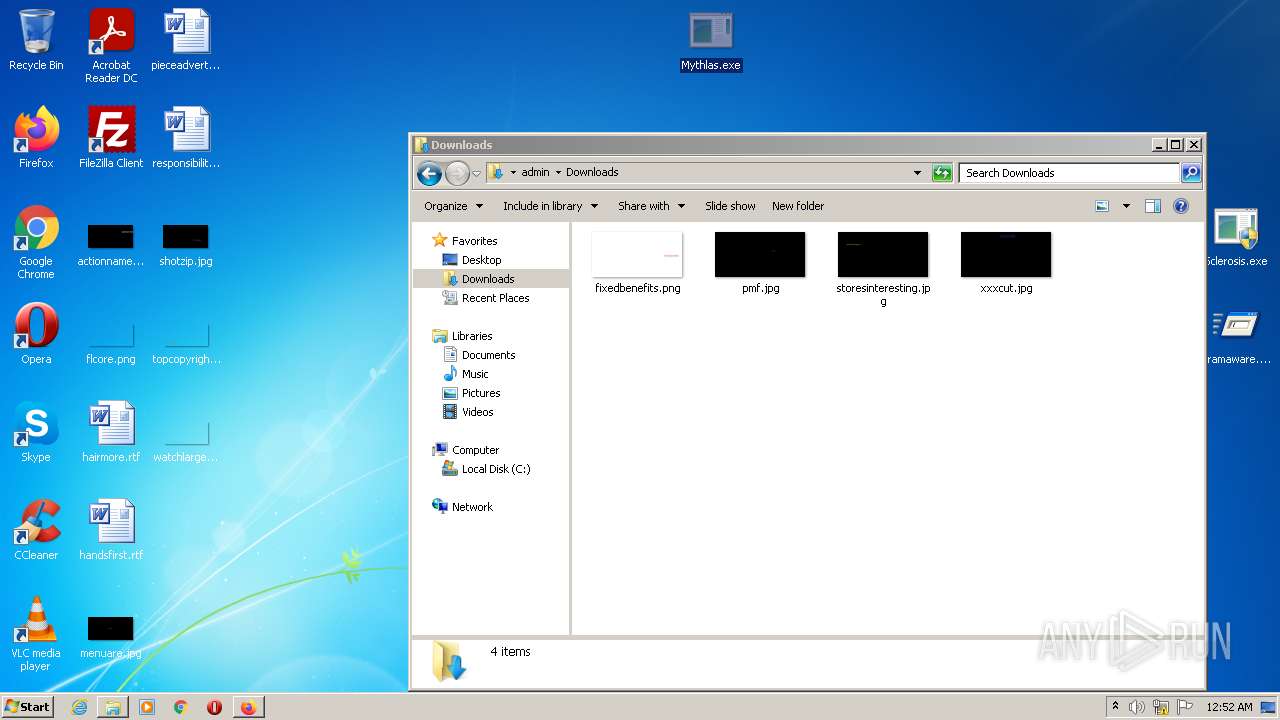
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\protections.sqlite-journal | binary | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
53
DNS requests
110
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 313 b | whitelisted |
3316 | firefox.exe | POST | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 313 b | whitelisted |
3316 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
3316 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
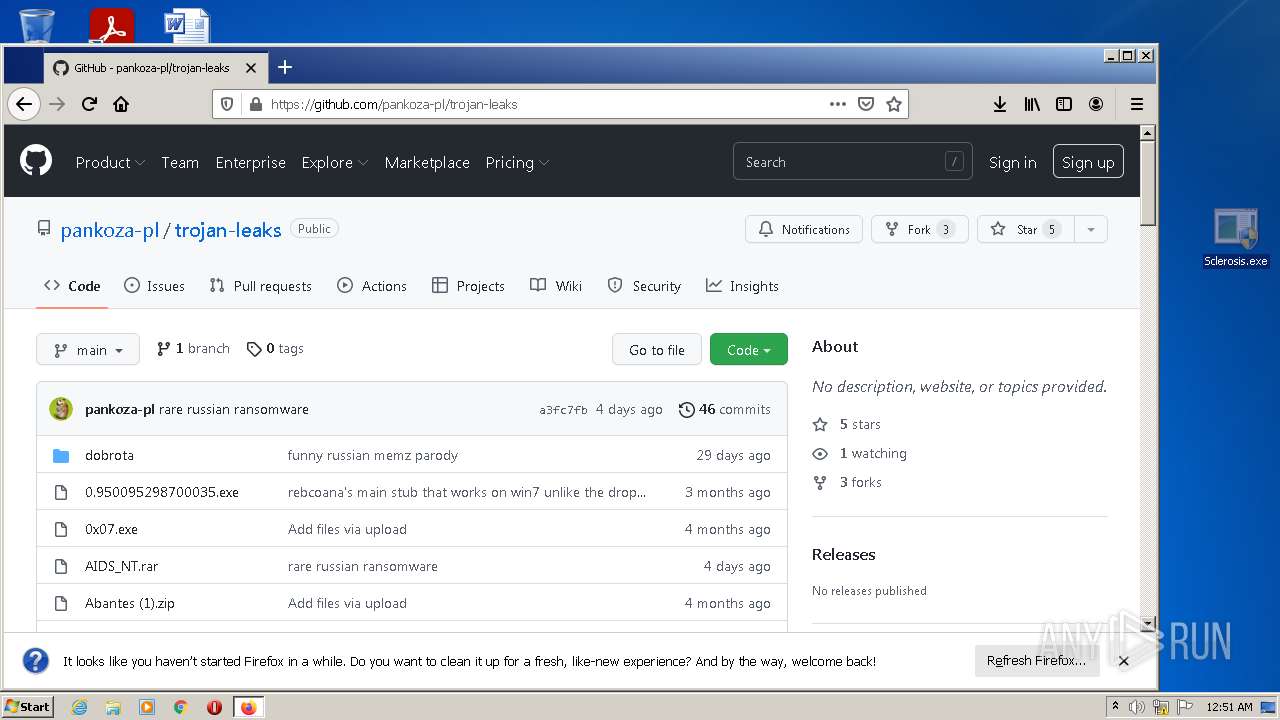
3316 | firefox.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3316 | firefox.exe | 18.66.248.29:443 | firefox.settings.services.mozilla.com | Massachusetts Institute of Technology | US | suspicious |
3316 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3316 | firefox.exe | 142.250.184.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3316 | firefox.exe | 35.161.134.161:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3316 | firefox.exe | 18.66.139.125:443 | content-signature-2.cdn.mozilla.net | Massachusetts Institute of Technology | US | malicious |
3316 | firefox.exe | 143.204.98.108:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | whitelisted |
3316 | firefox.exe | 142.250.185.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3316 | firefox.exe | 140.82.114.21:443 | collector.github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
github.com |
| malicious |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3316 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3316 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3316 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3316 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |