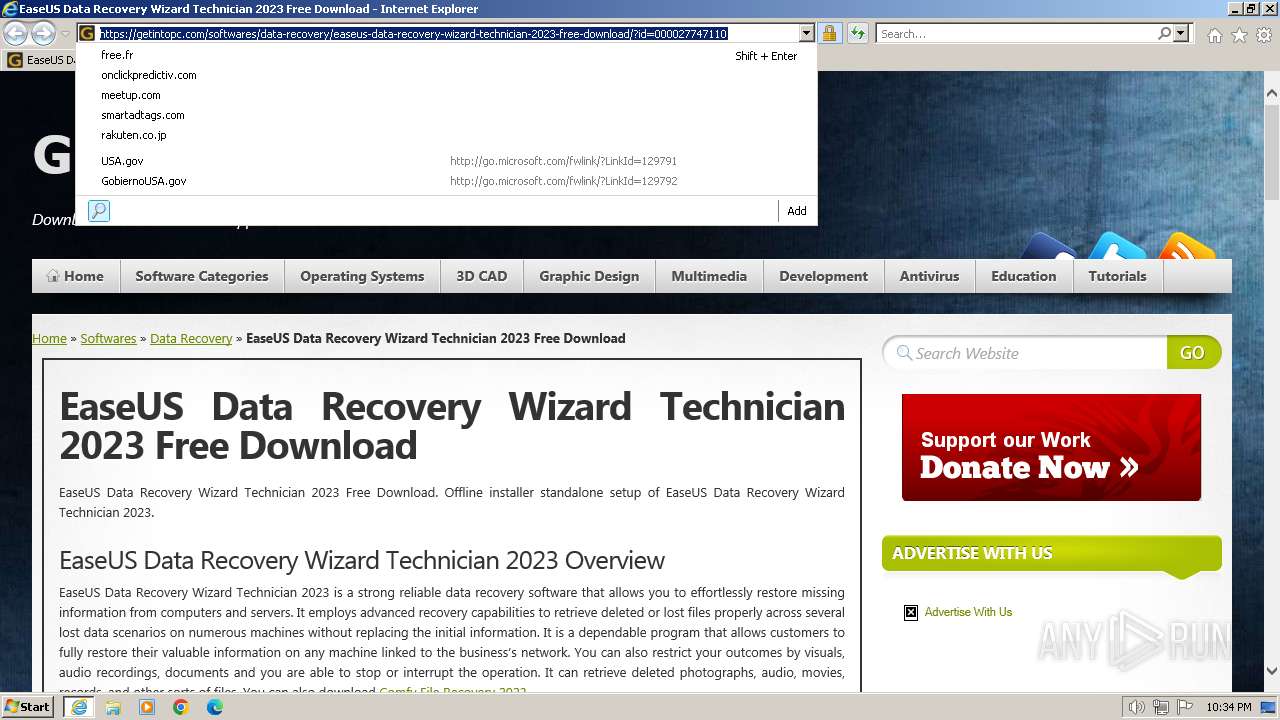
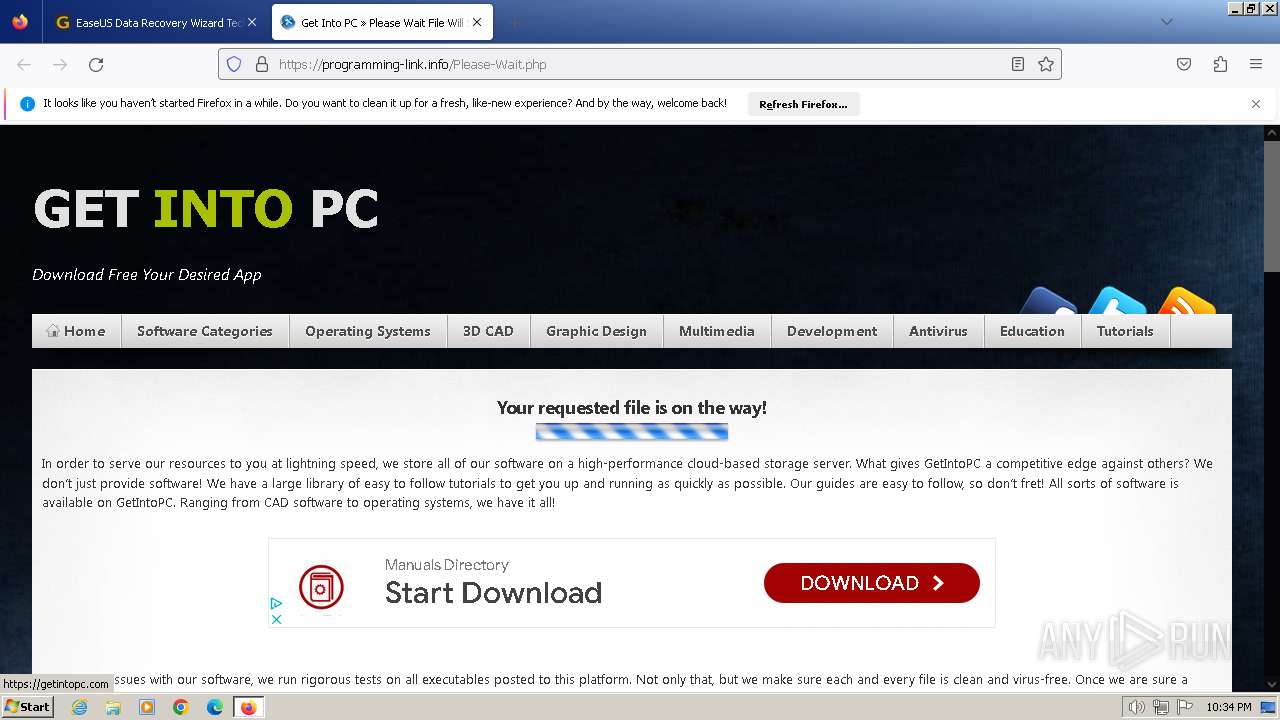
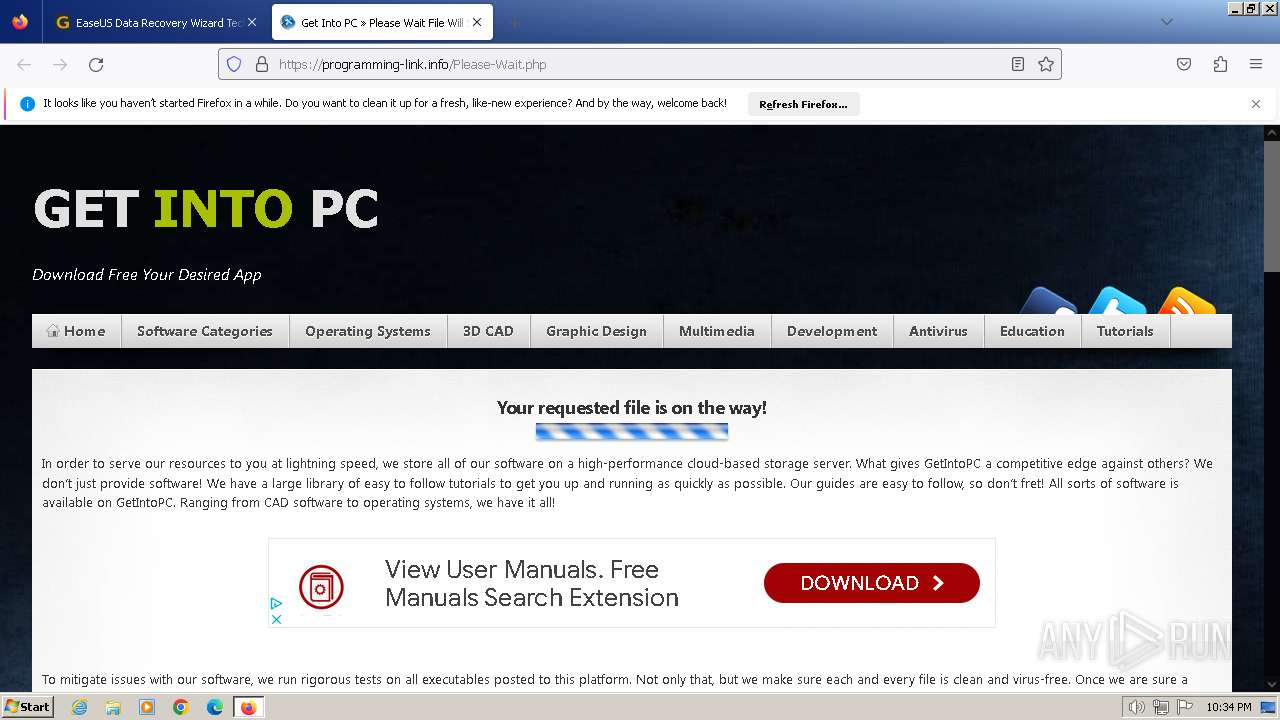
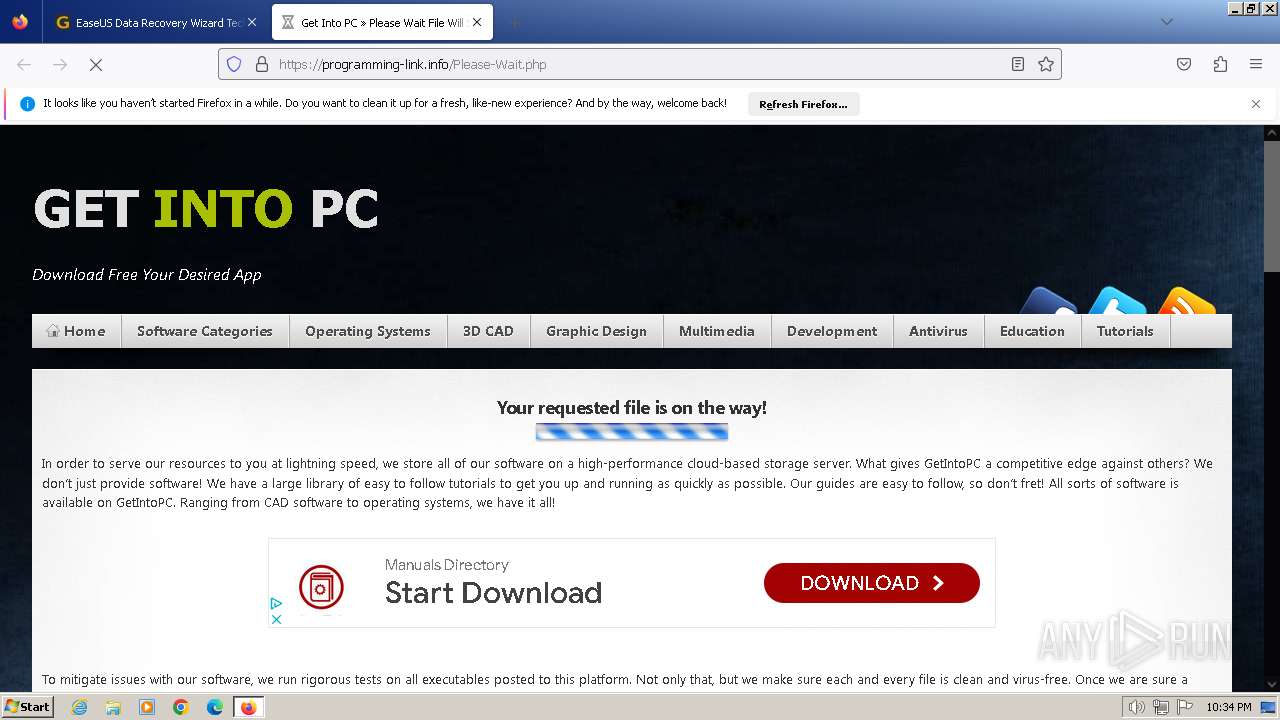
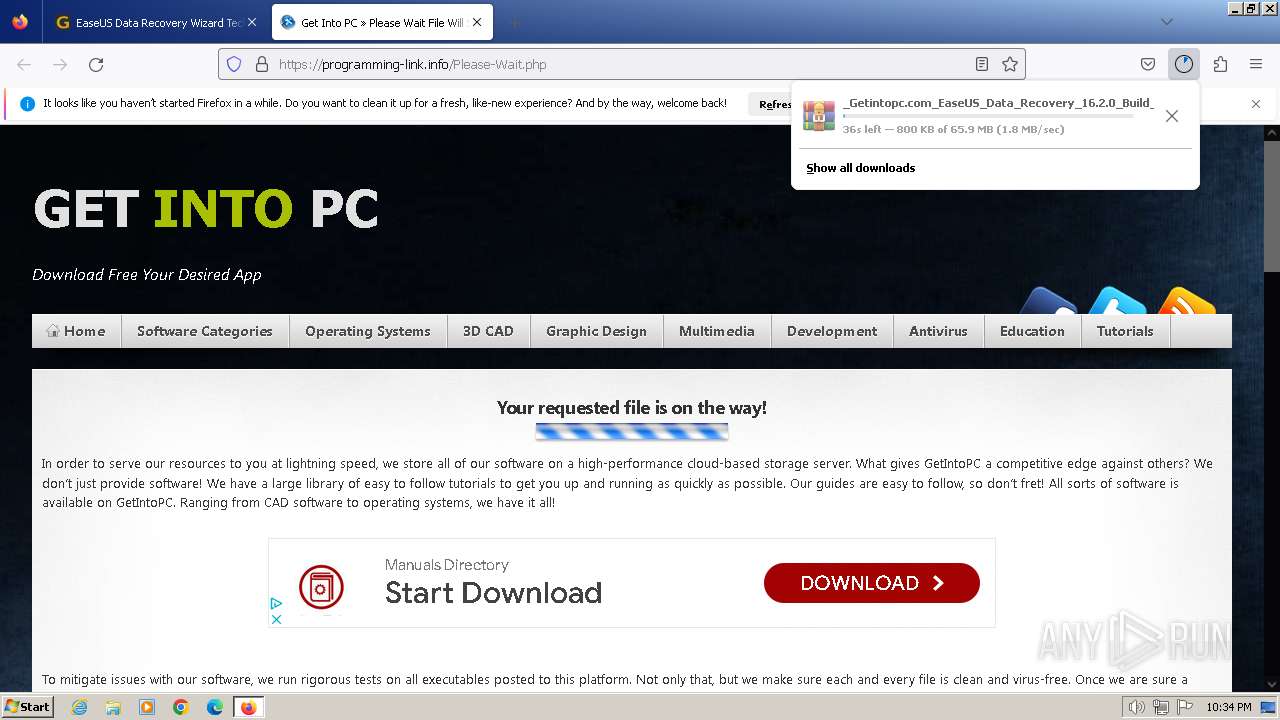
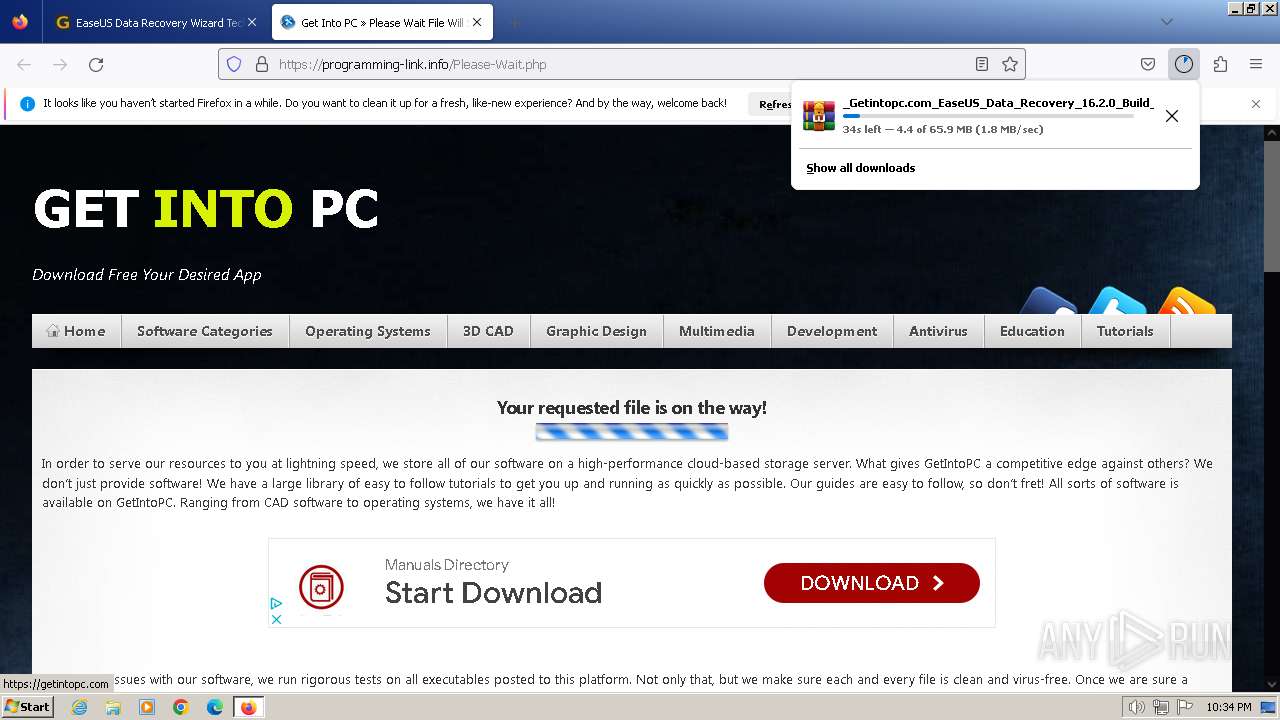
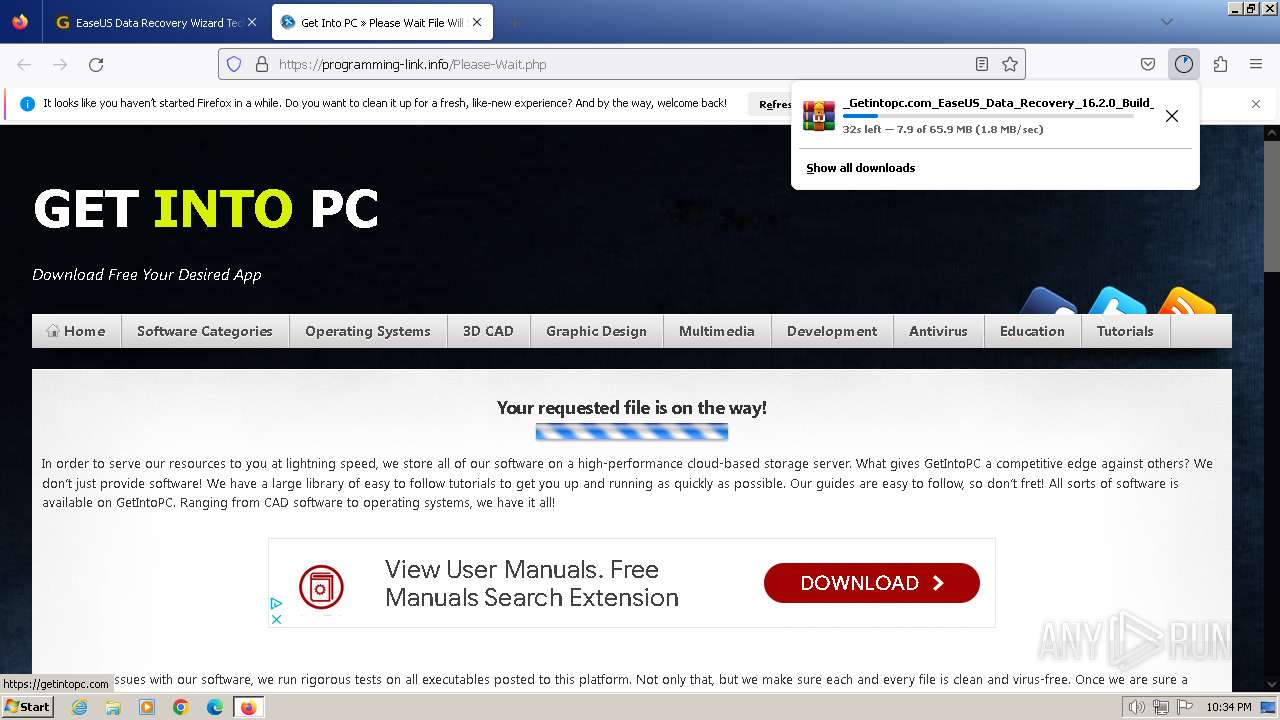
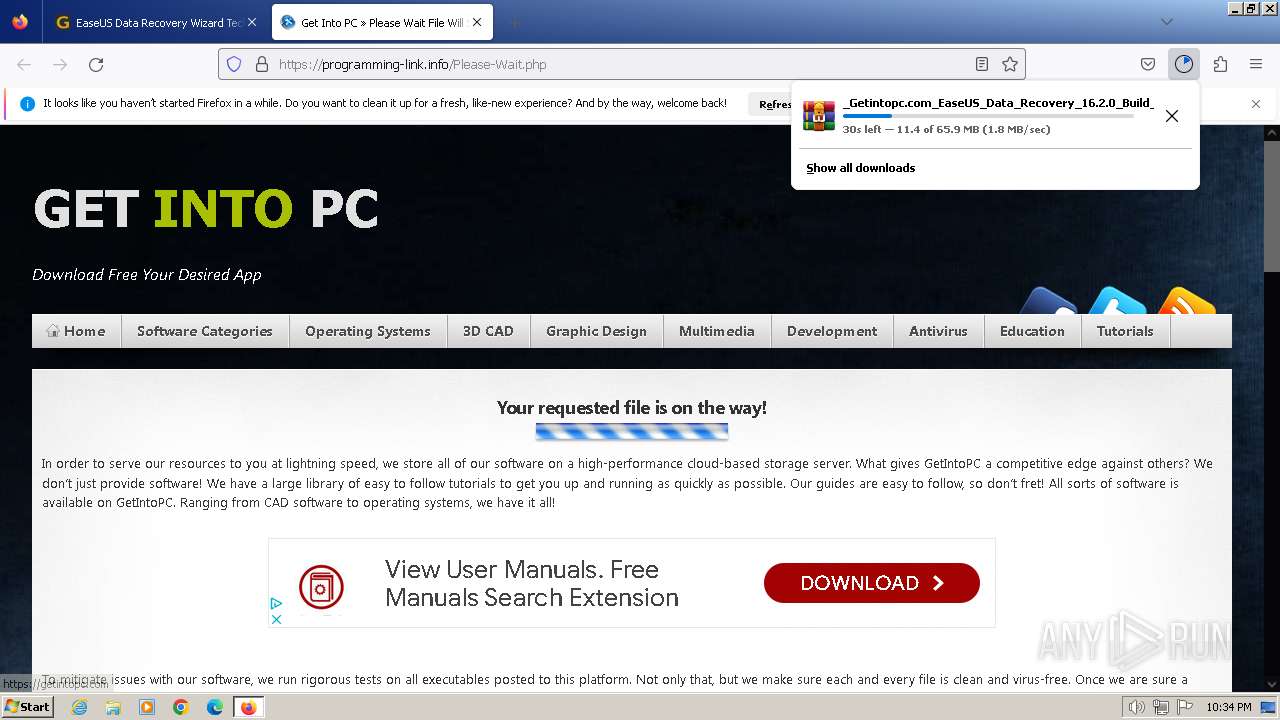
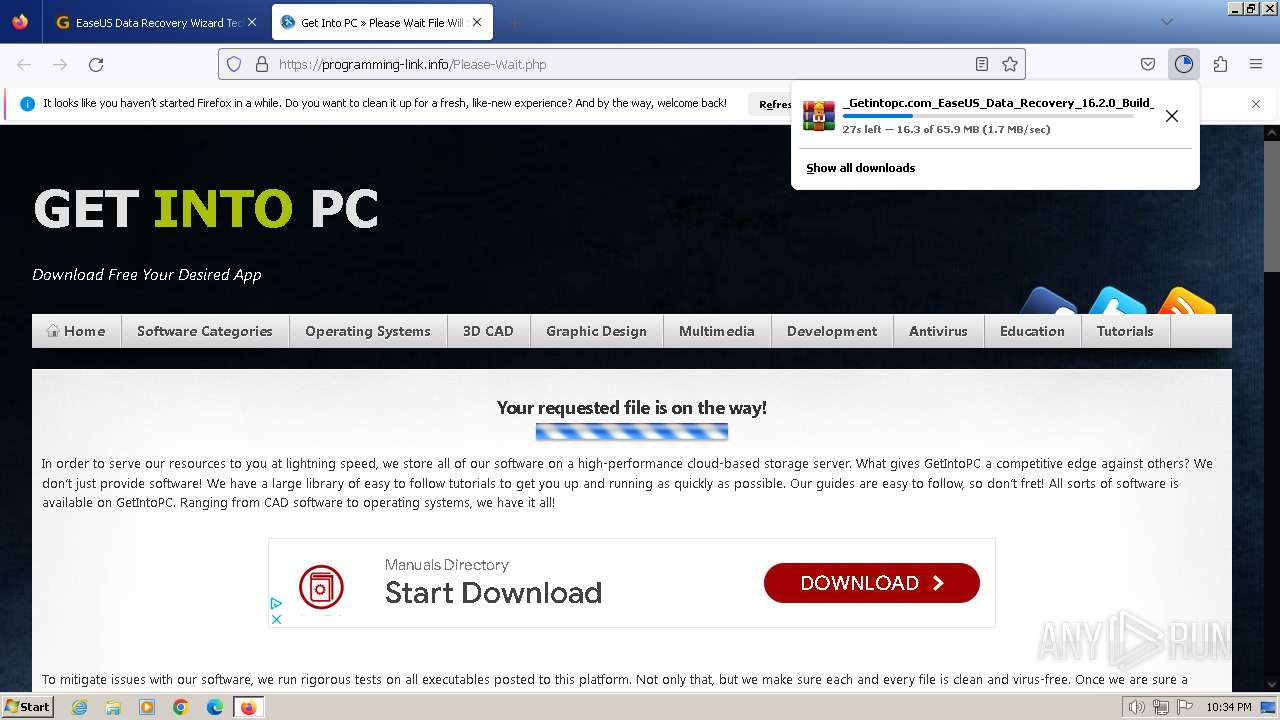
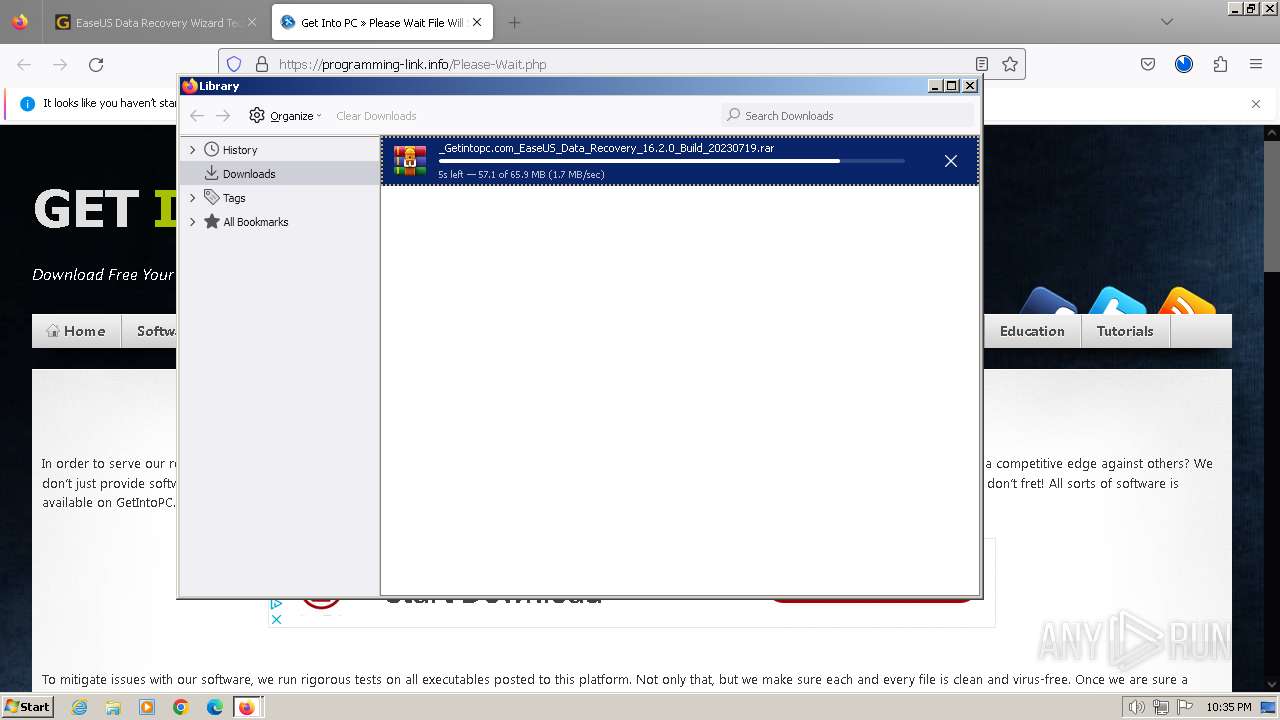
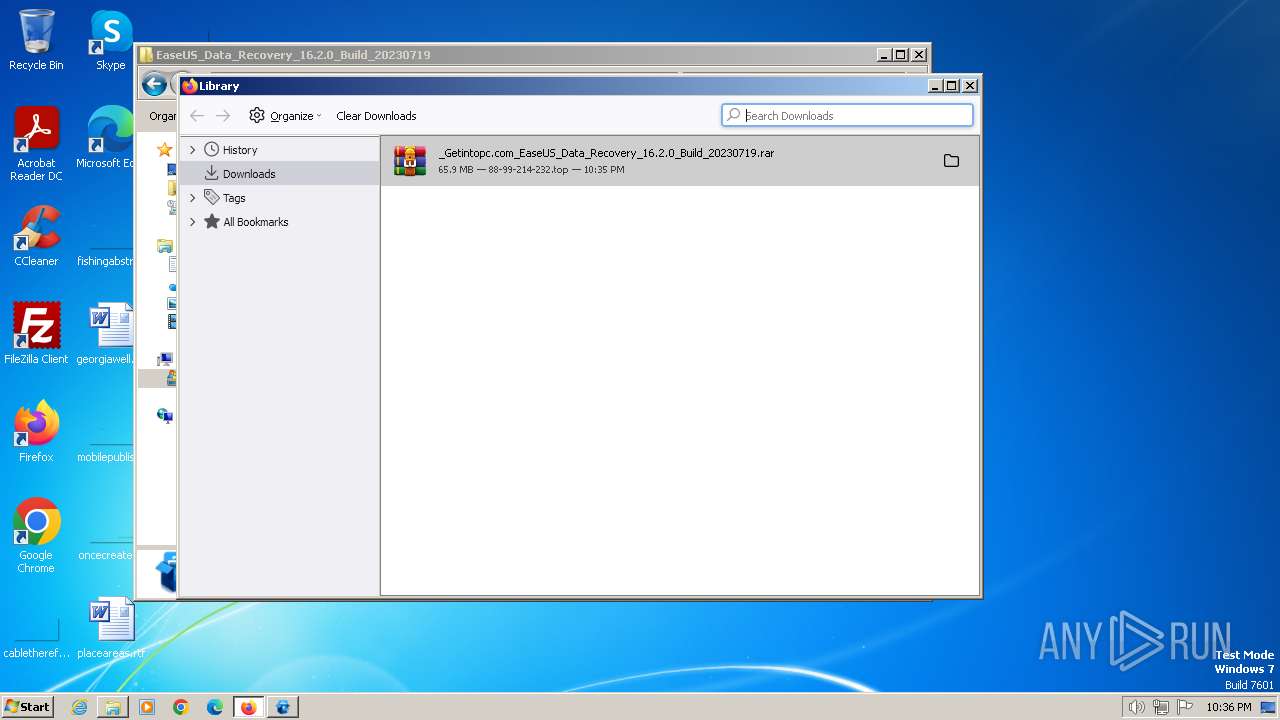
| URL: | https://getintopc.com/softwares/data-recovery/easeus-data-recovery-wizard-technician-2023-free-download/?id=000027747110 |
| Full analysis: | https://app.any.run/tasks/0a830348-c37c-4474-94e7-58c0f05d1a95 |
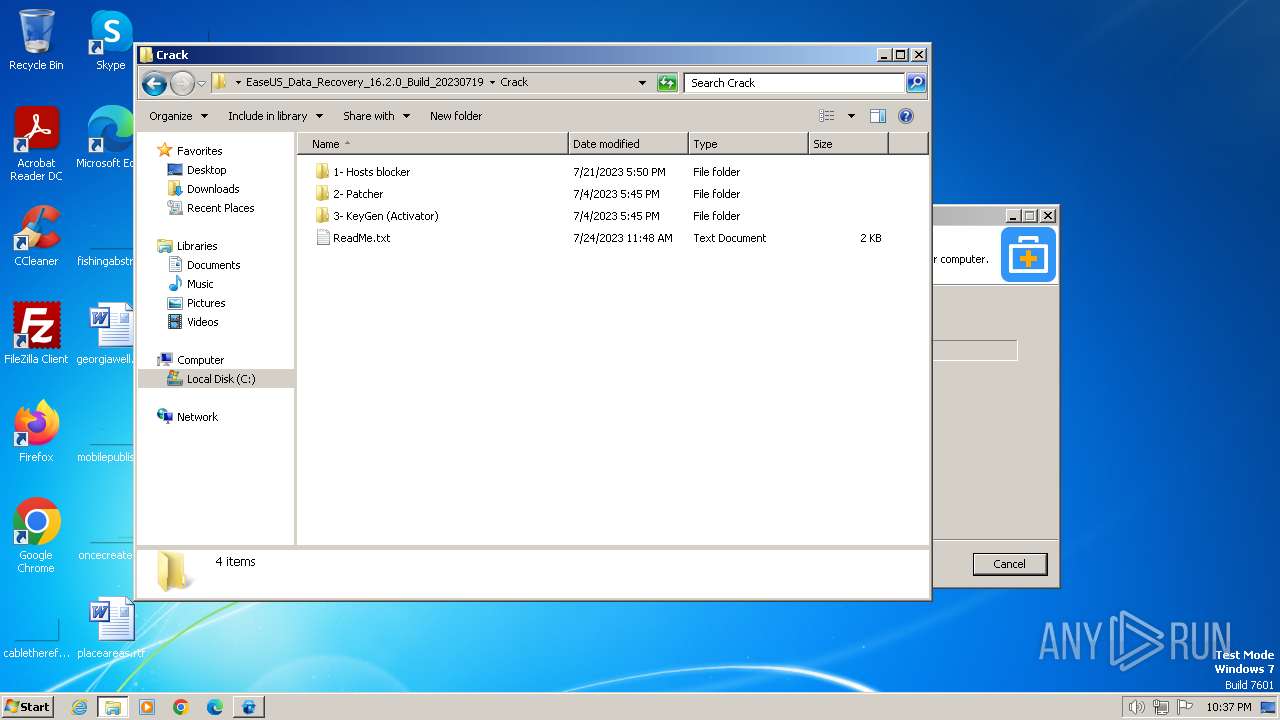
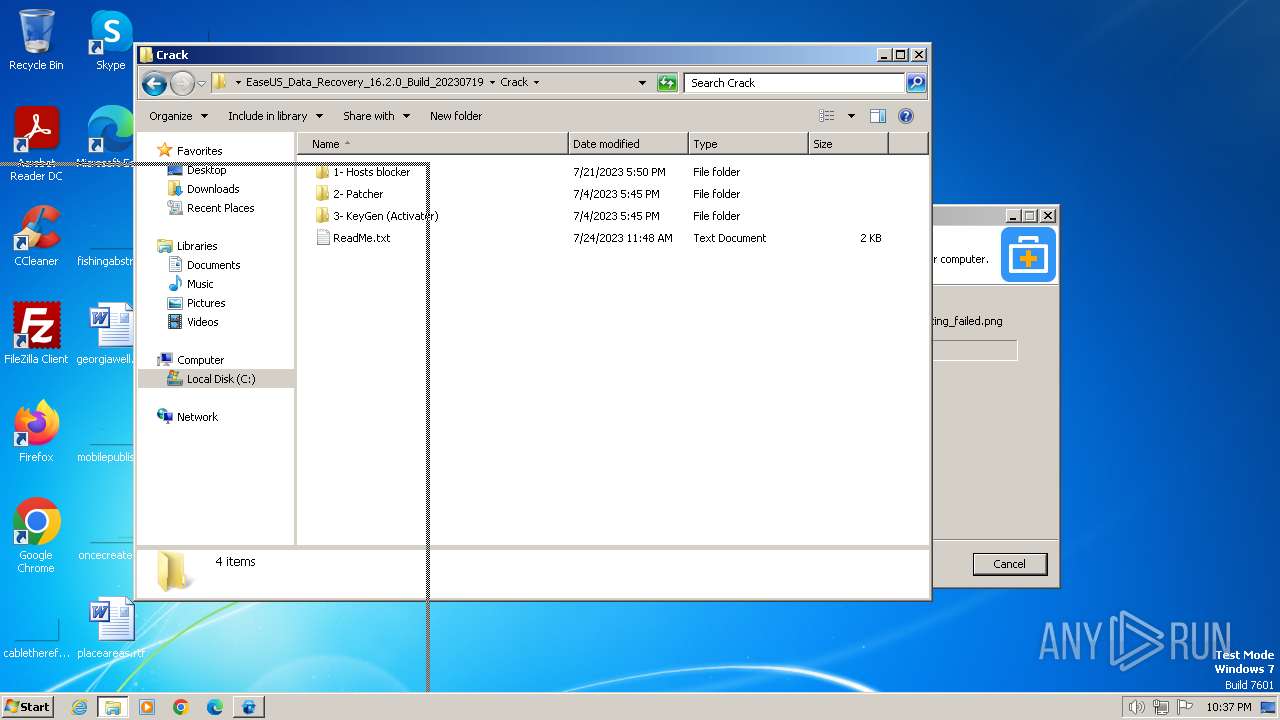
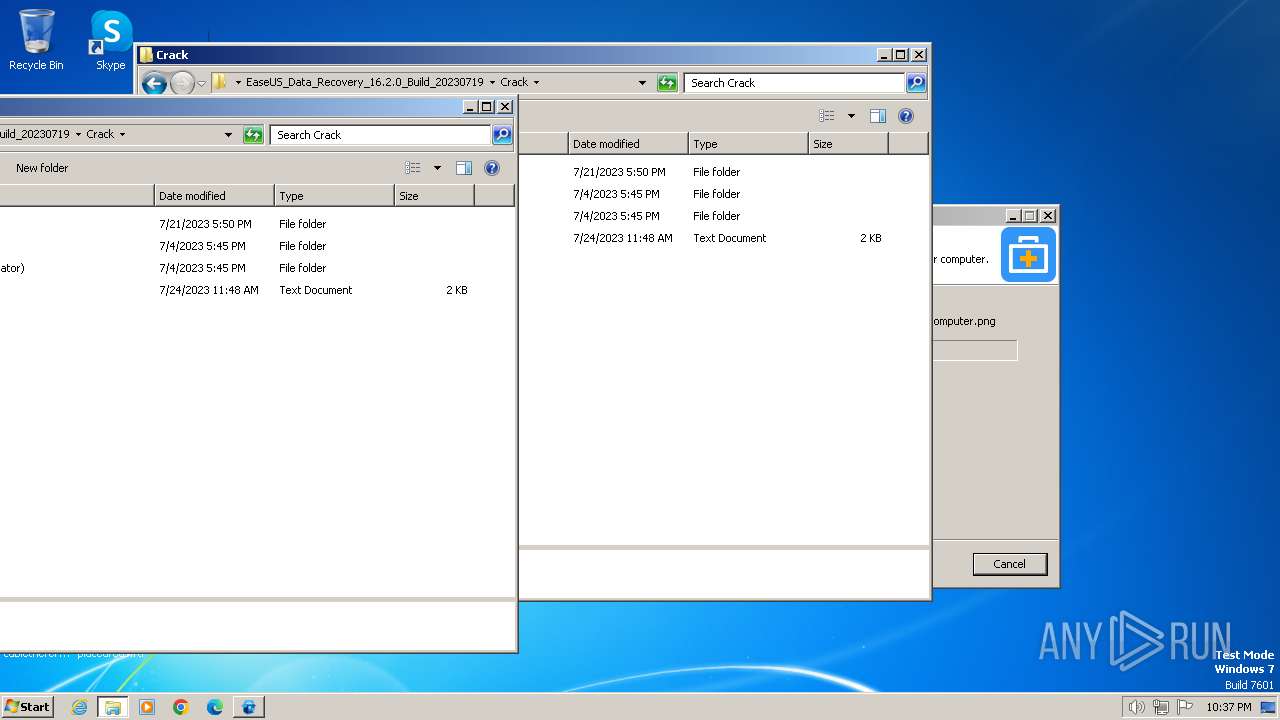
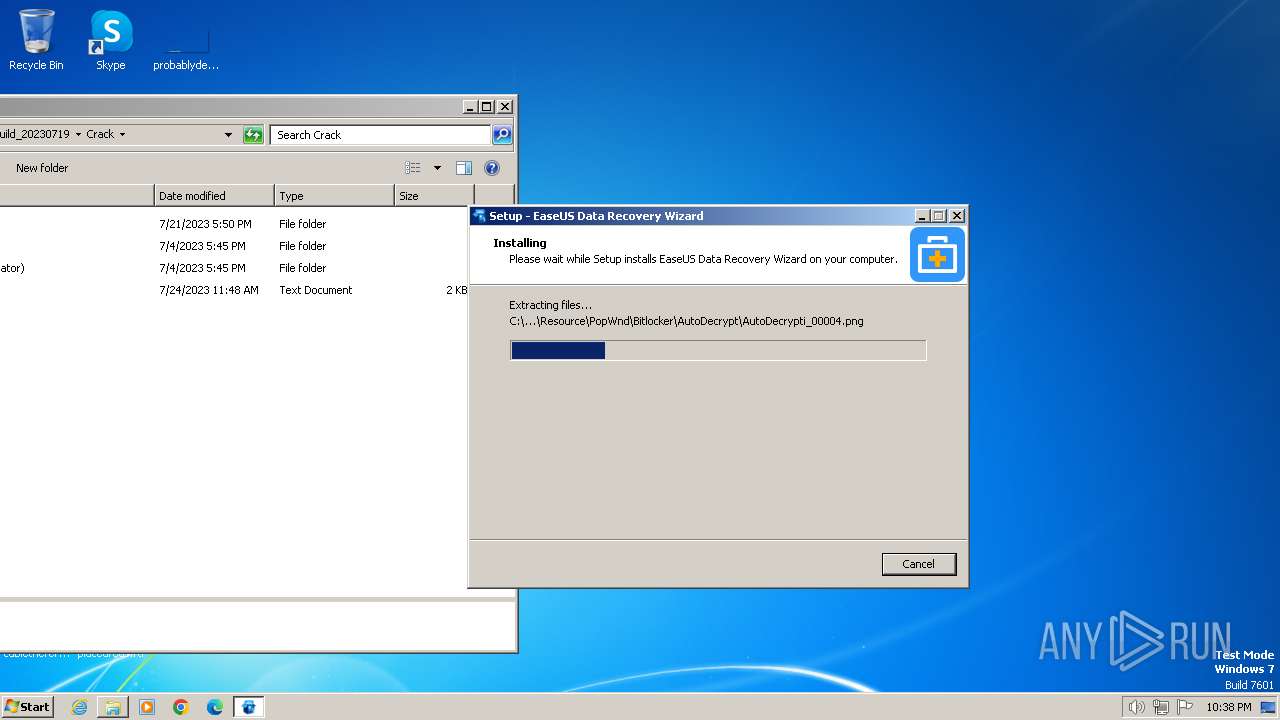
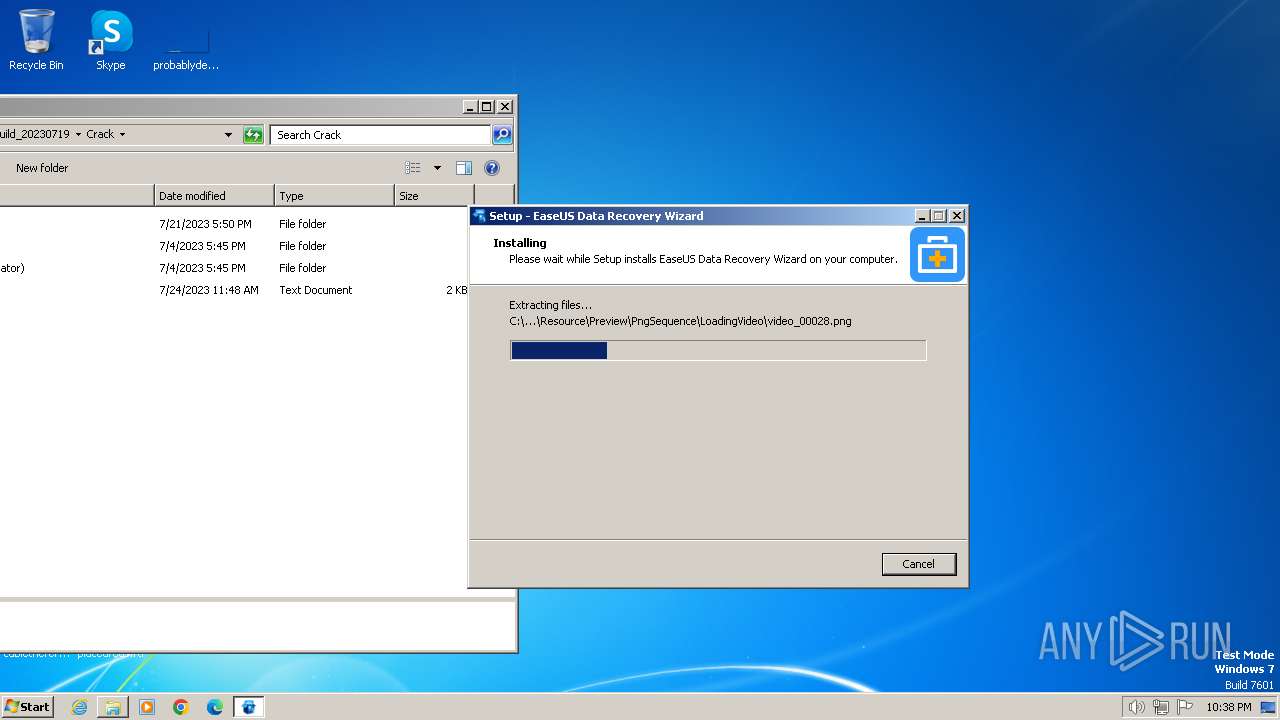
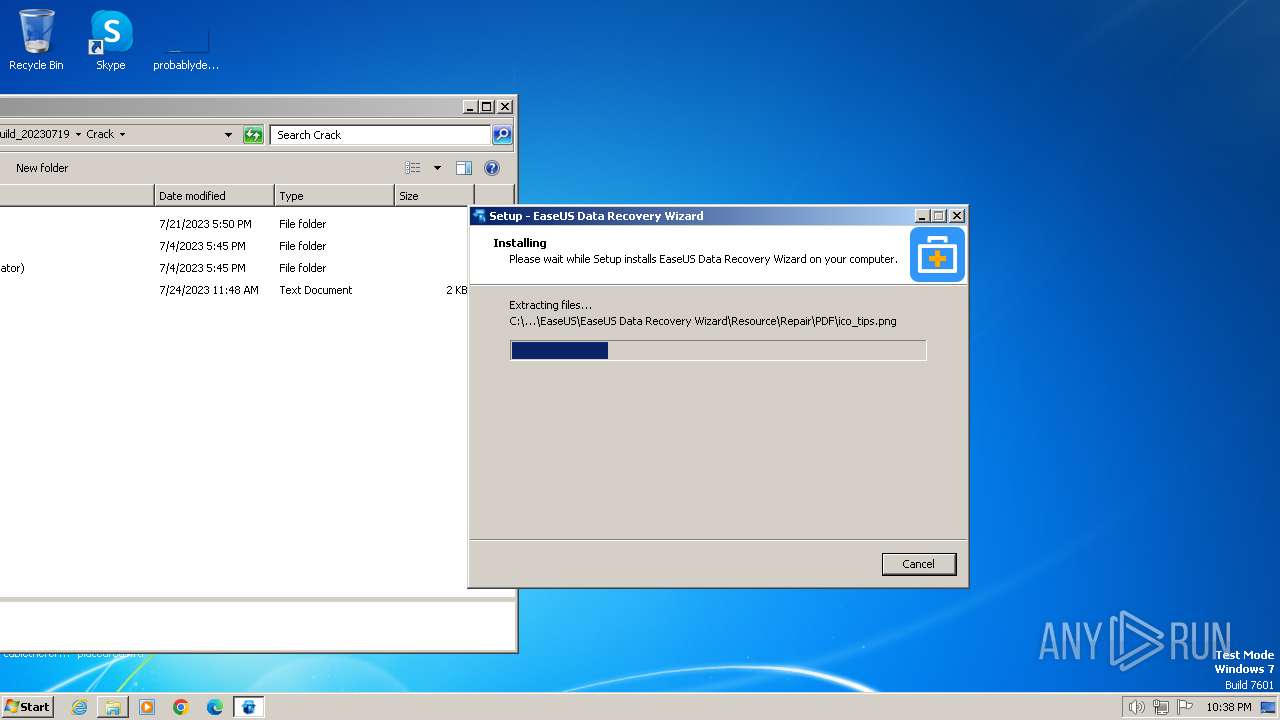
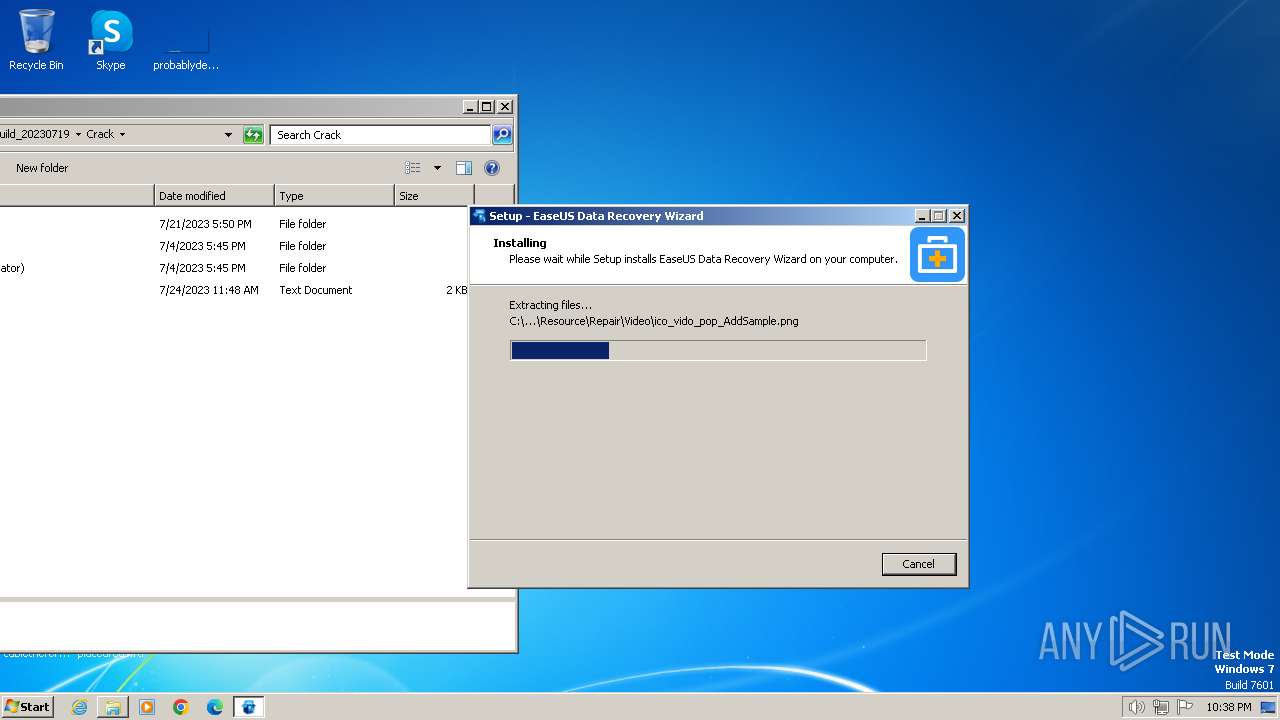
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2024, 22:33:50 |
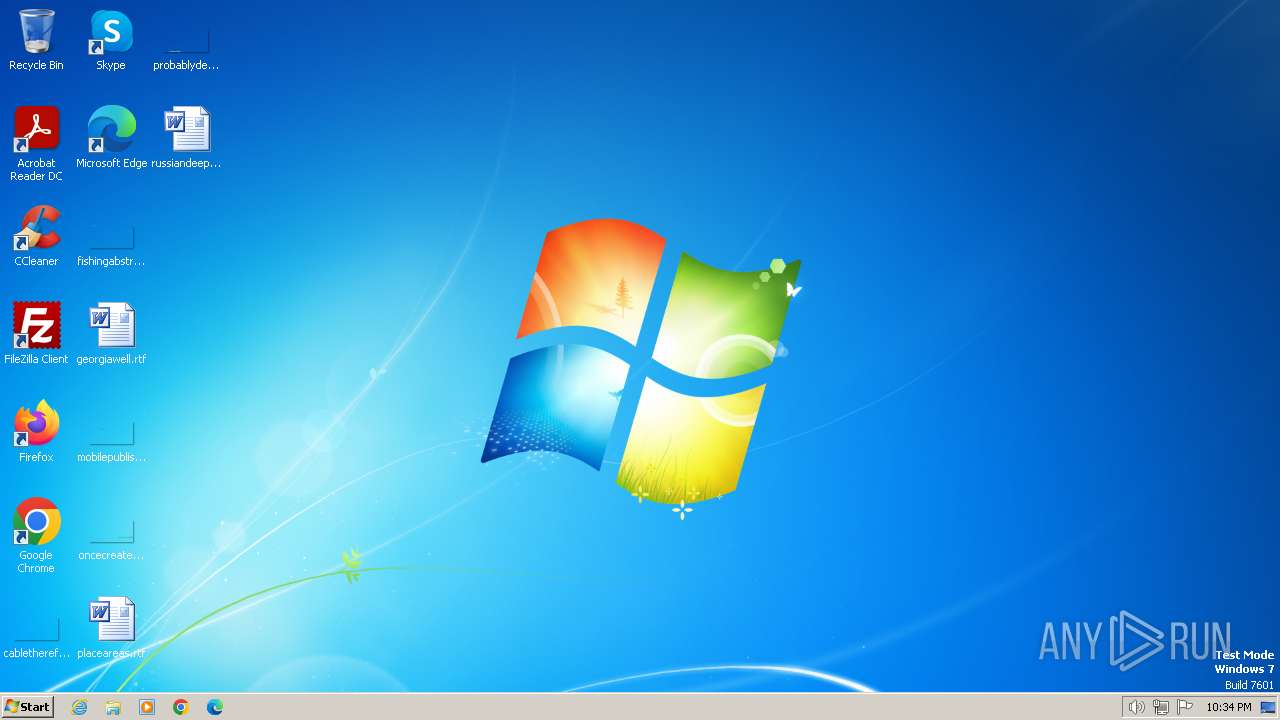
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CA2493DF69FAA3686D9655739993F753 |
| SHA1: | 8444781160E0C40FC00D4069720C0276BD3CA28D |
| SHA256: | 52B888F0D7CFA994A1B4363CEDF80562AC4F224E27EDC74EC7601580960E3818 |
| SSDEEP: | 3:N8hILdIYMHCS/fGTvRebE8FXW+XlIBFma6:2zimfcvRyE8FG+XlI96 |
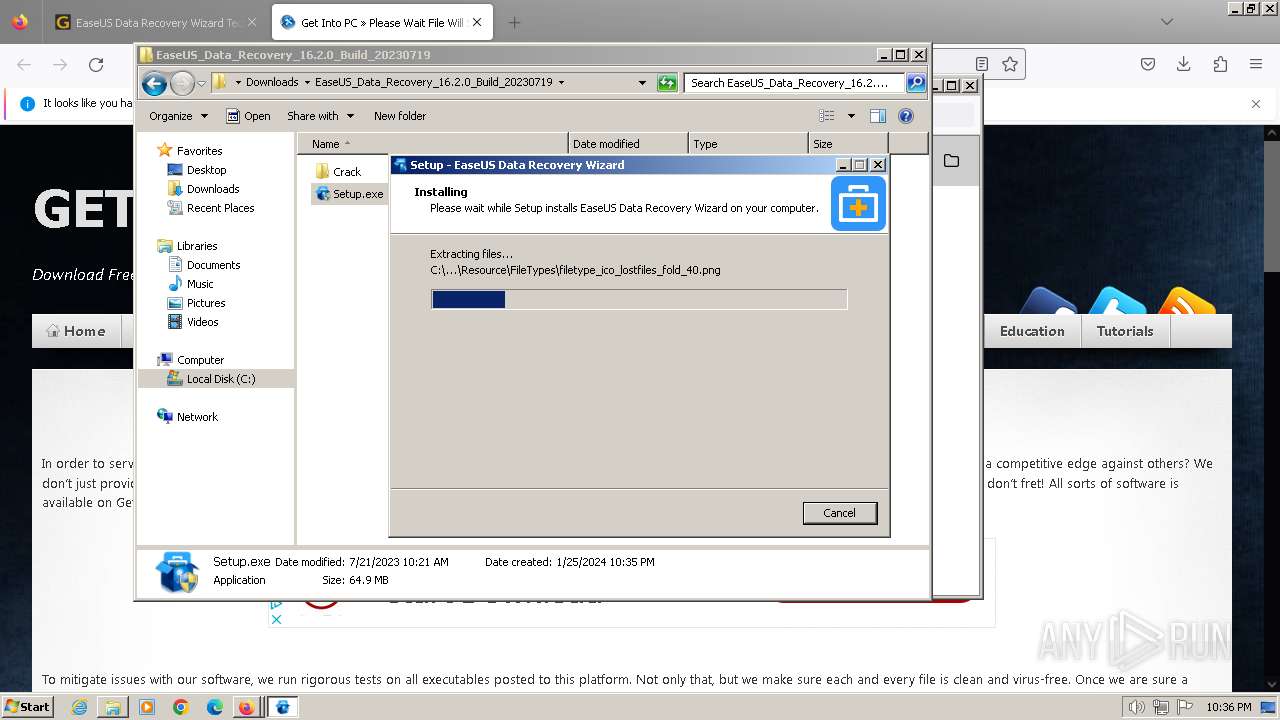
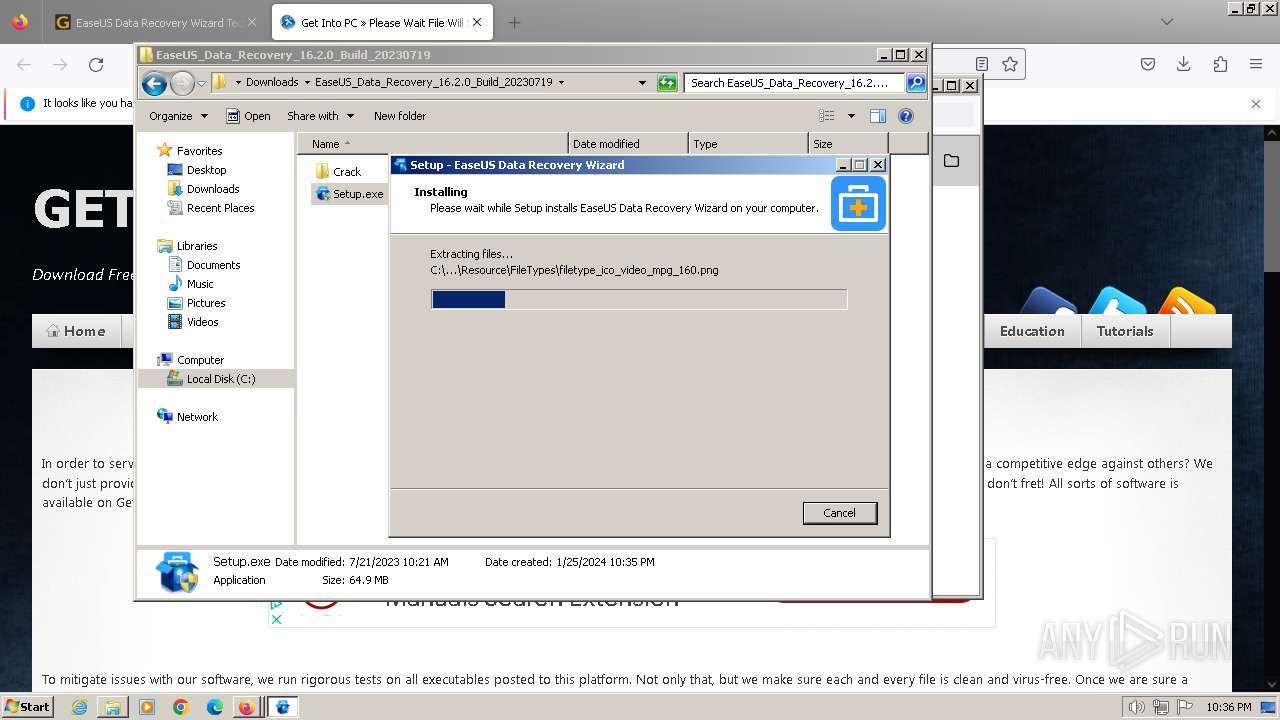
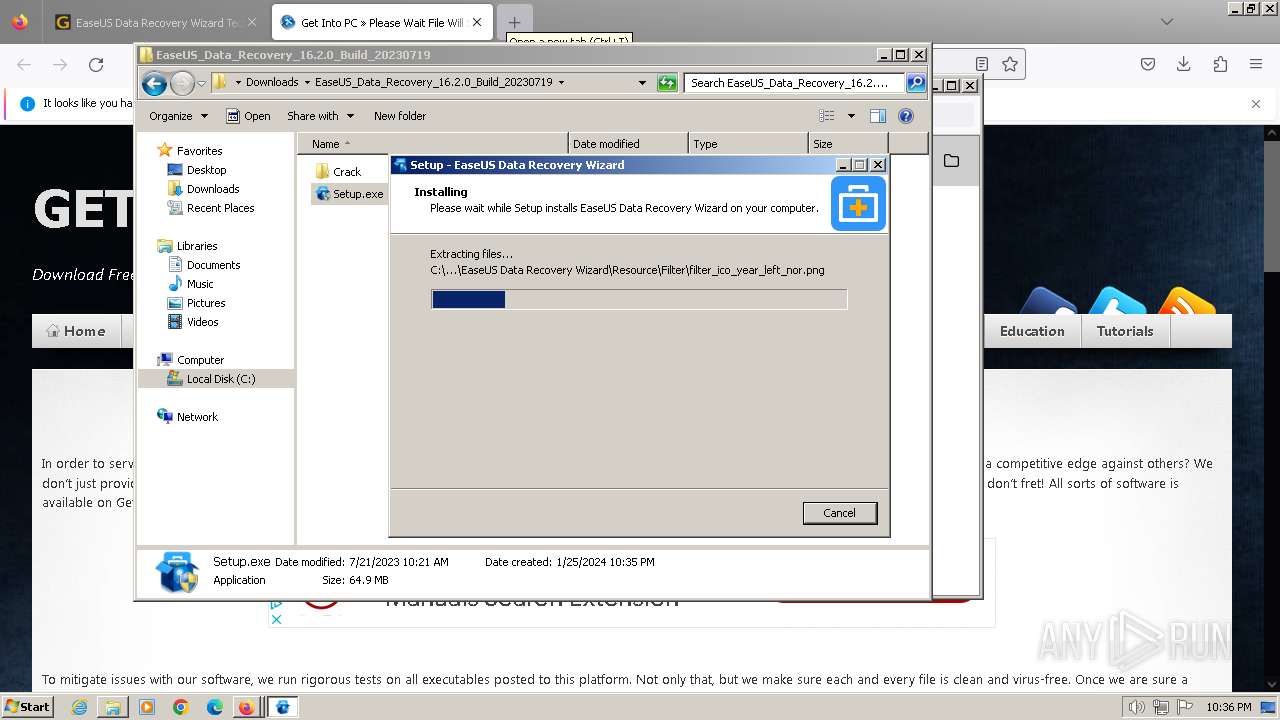
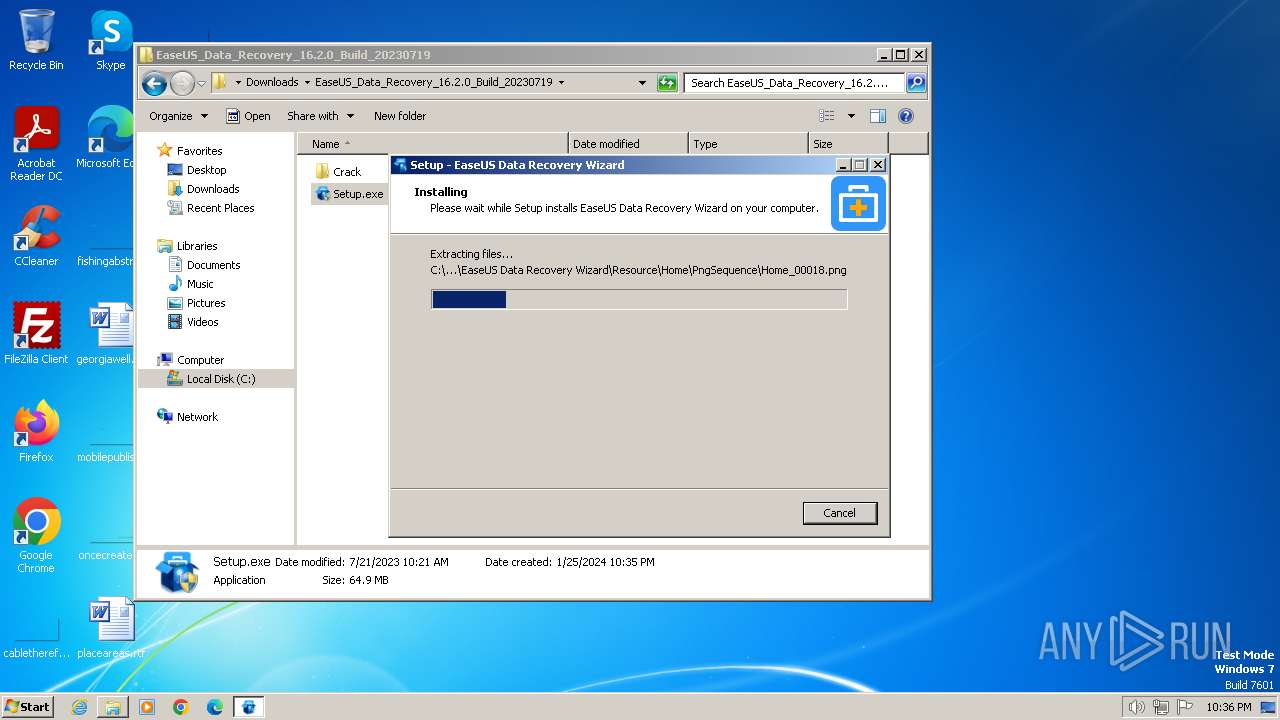
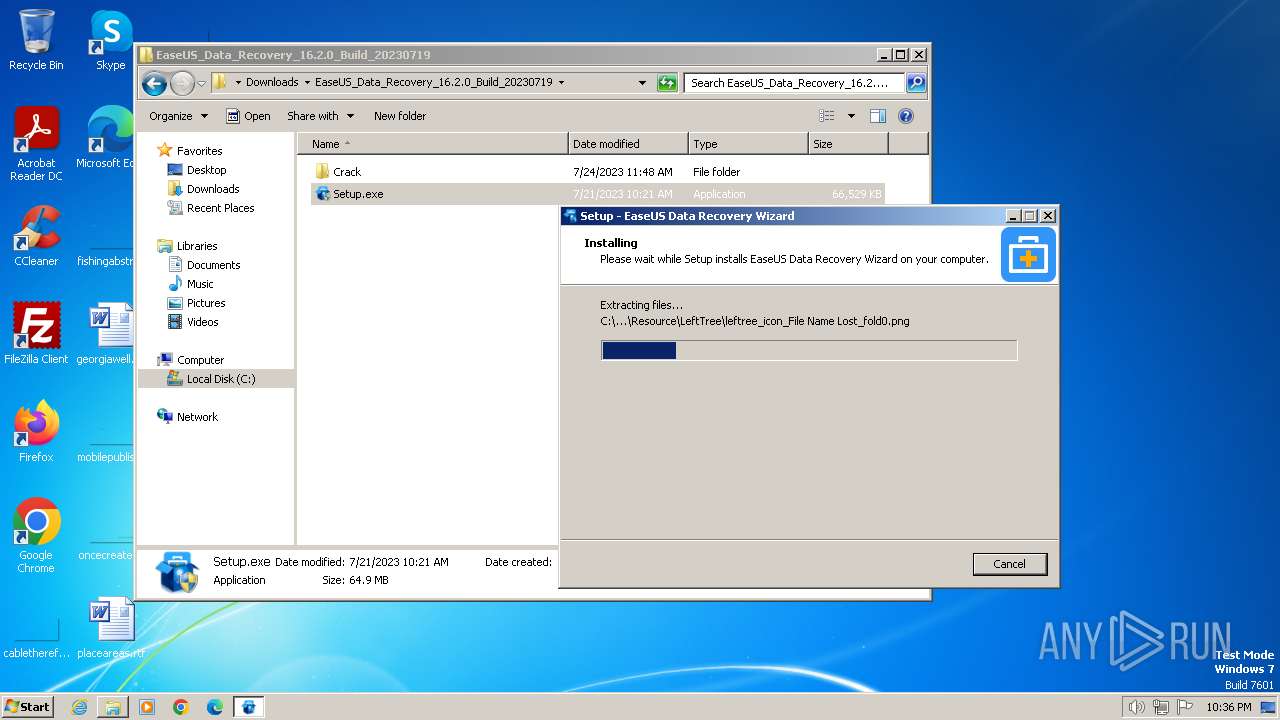
MALICIOUS
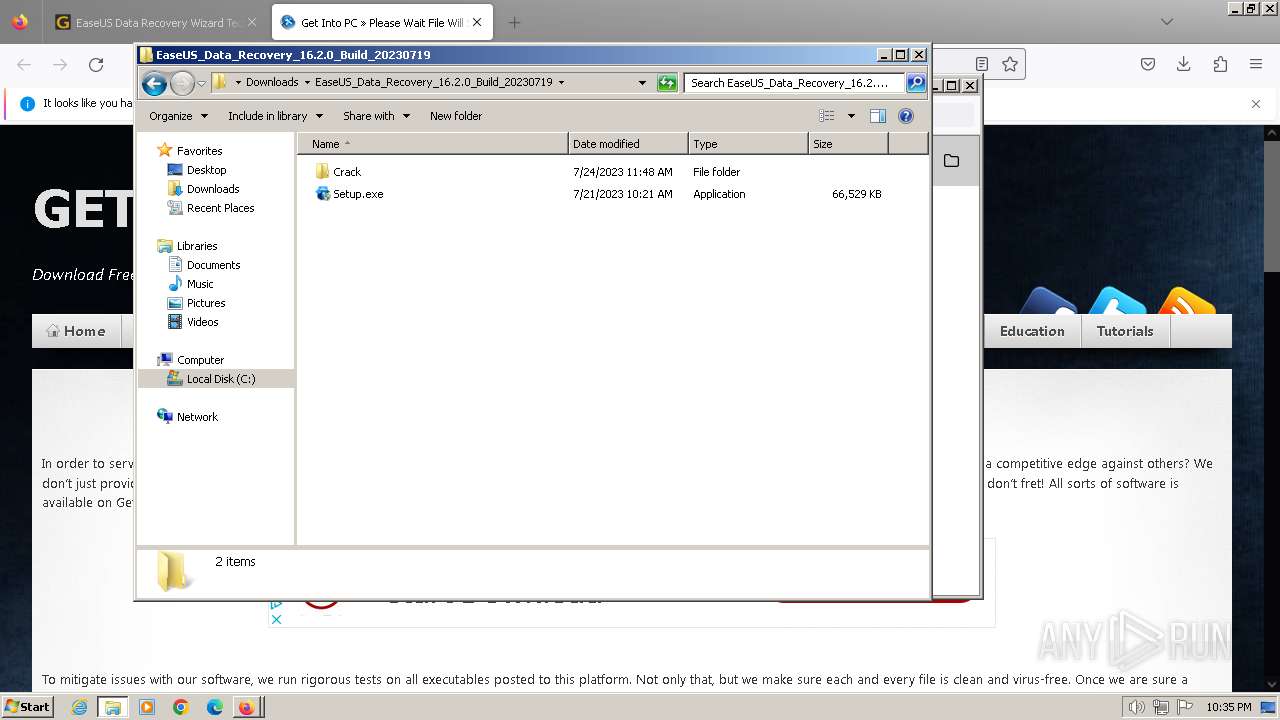
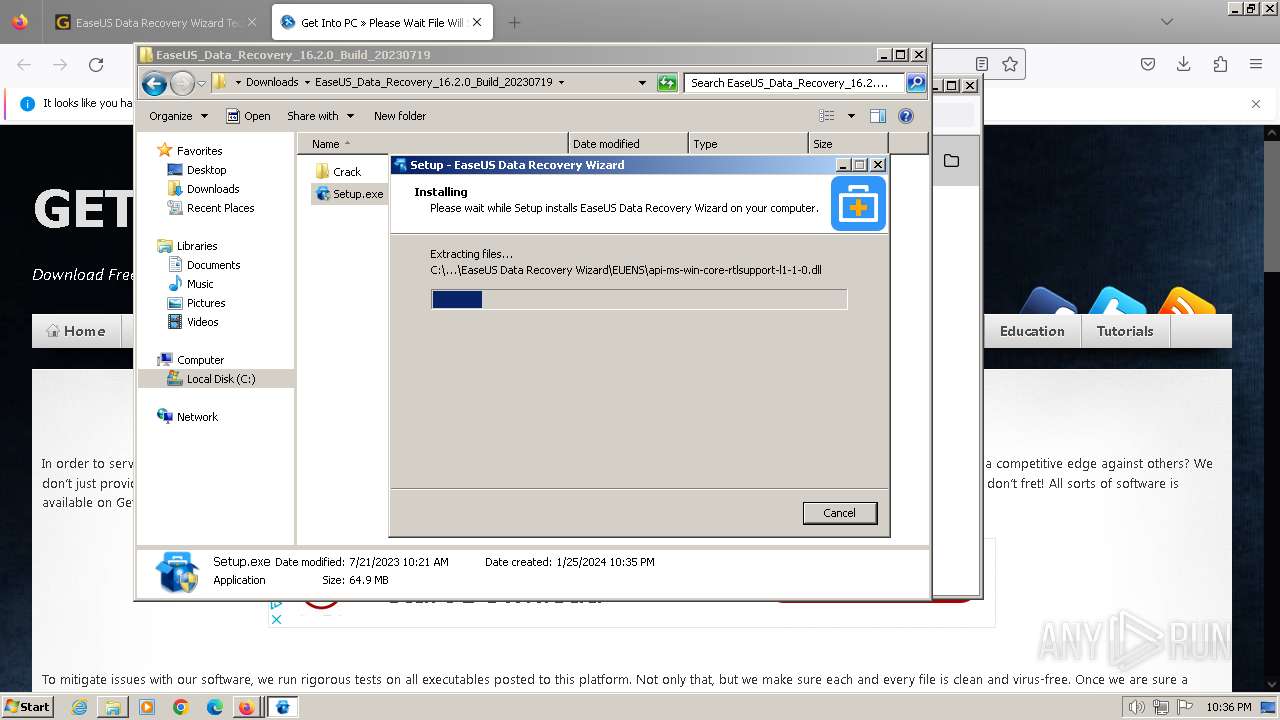
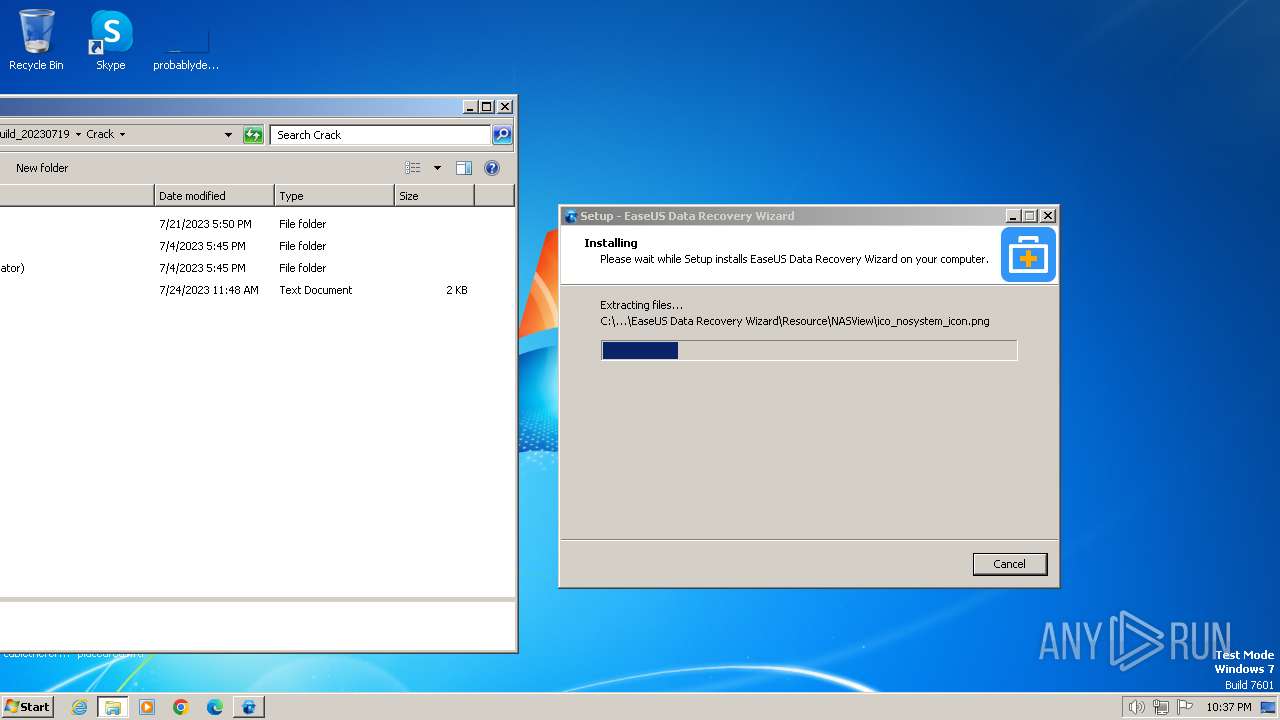
Drops the executable file immediately after the start
- Setup.exe (PID: 3096)
- Setup.tmp (PID: 2516)
SUSPICIOUS
Executable content was dropped or overwritten
- Setup.exe (PID: 3096)
- Setup.tmp (PID: 2516)
Reads the Windows owner or organization settings
- Setup.tmp (PID: 2516)
Reads the Internet Settings
- AliyunWrapExe.Exe (PID: 3476)
Process drops legitimate windows executable
- Setup.tmp (PID: 2516)
The process drops C-runtime libraries
- Setup.tmp (PID: 2516)
INFO
Application launched itself
- iexplore.exe (PID: 1036)
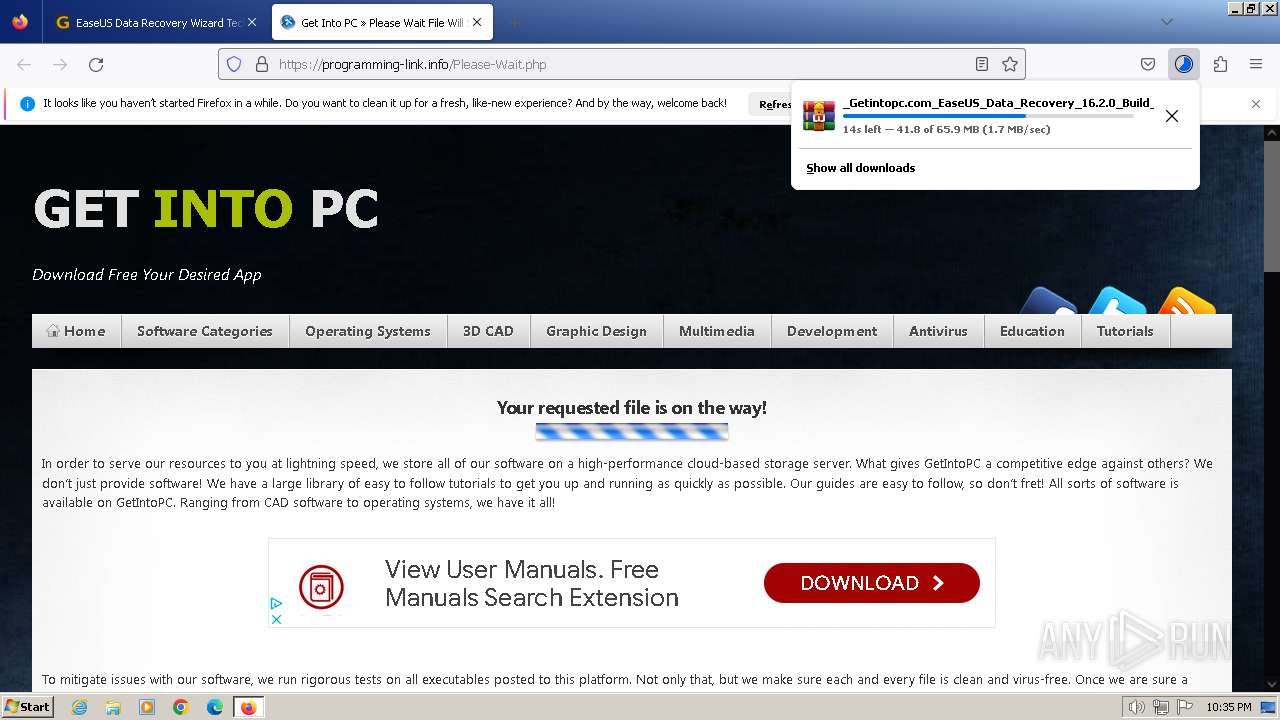
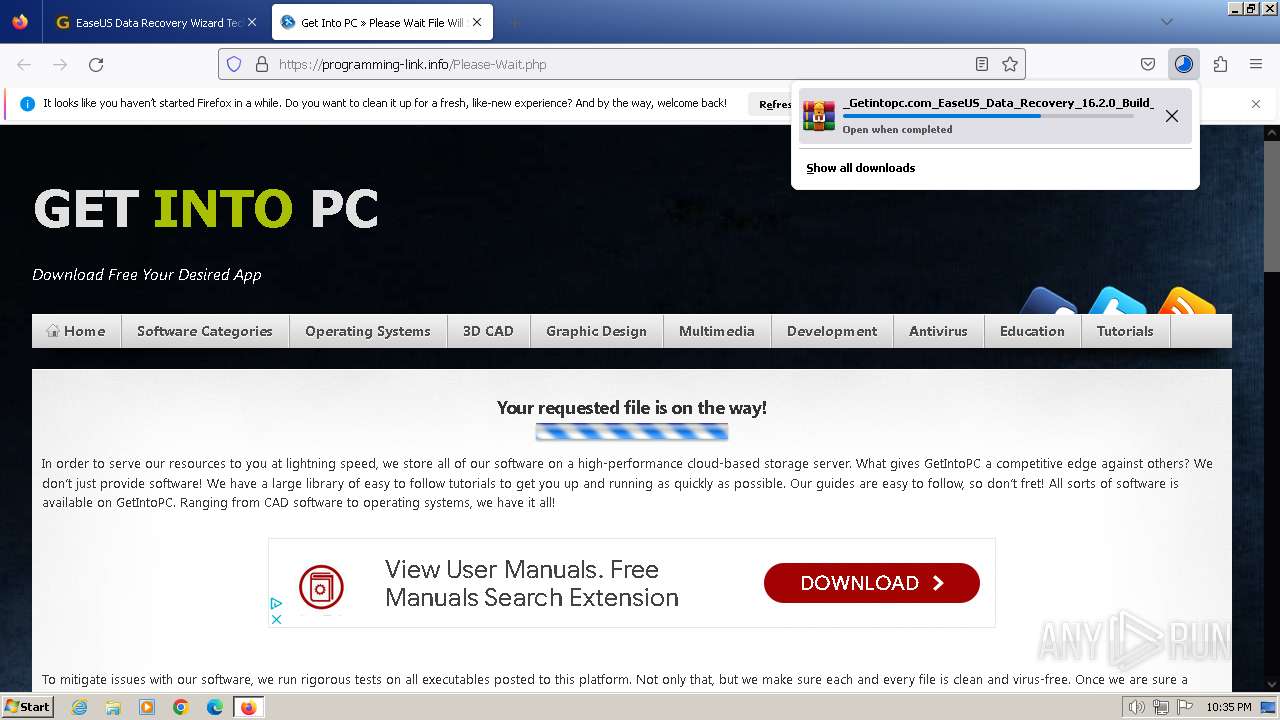
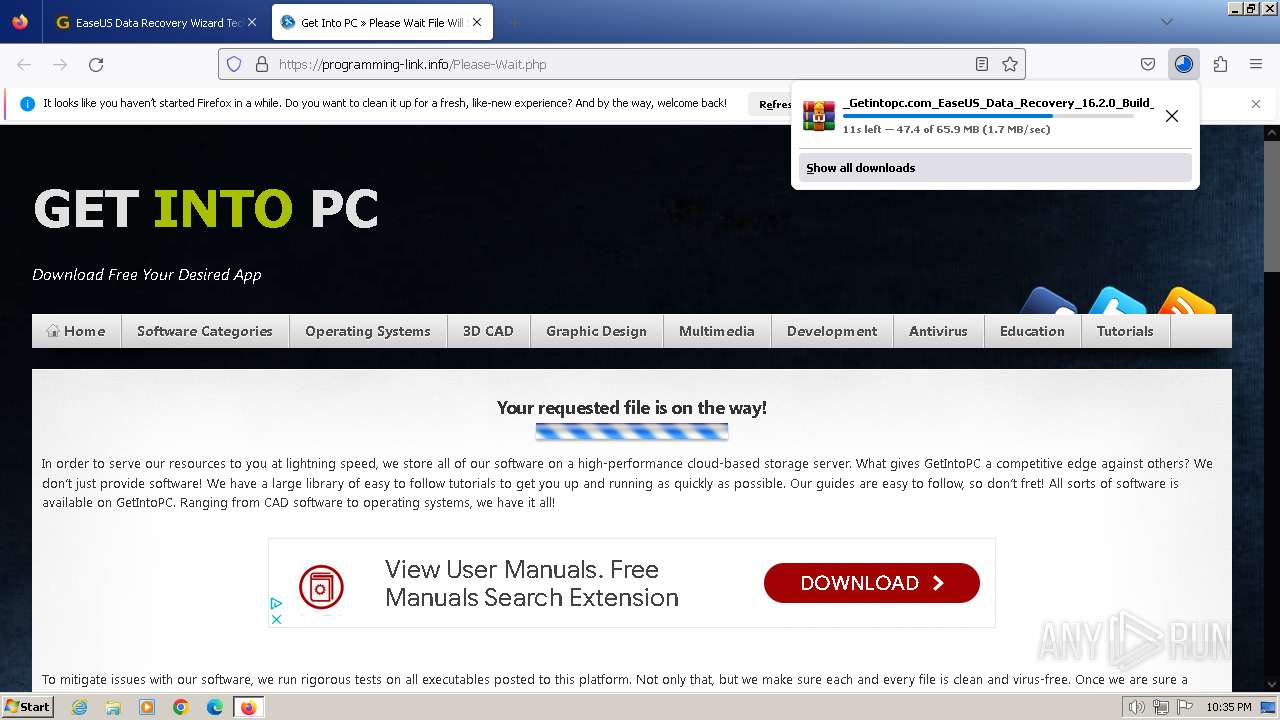
- firefox.exe (PID: 116)
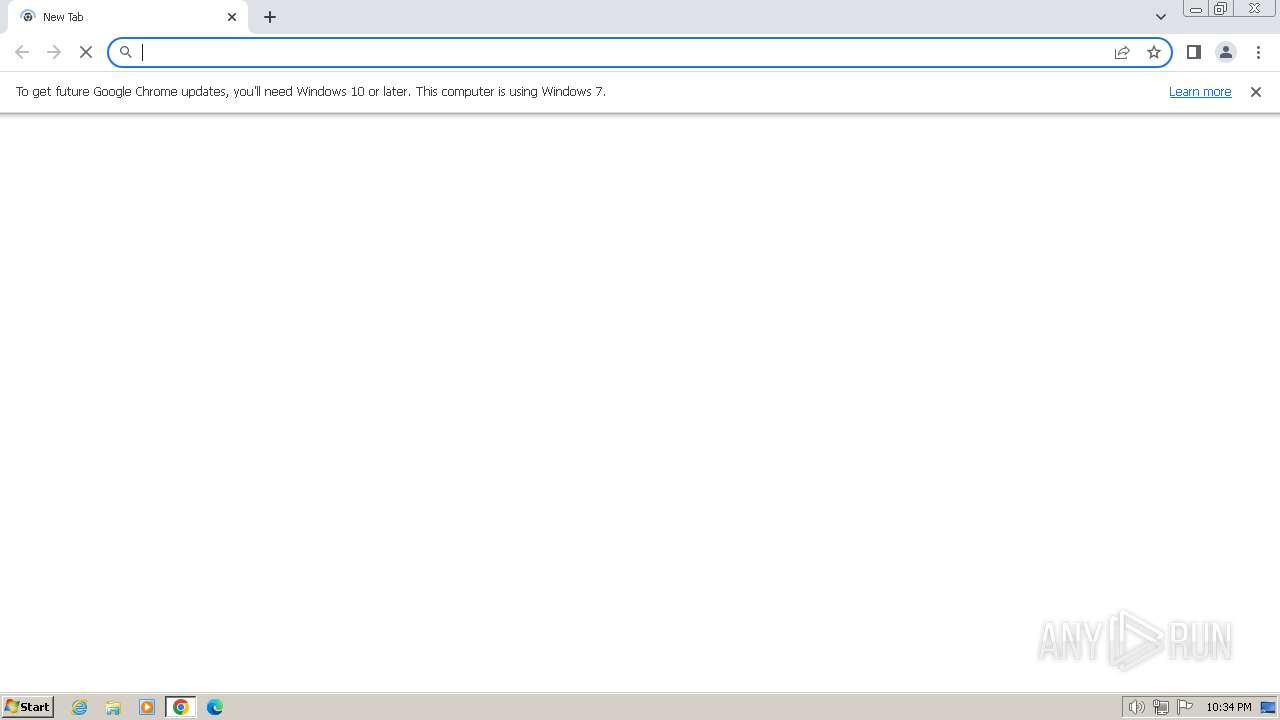
- chrome.exe (PID: 952)
- firefox.exe (PID: 3892)
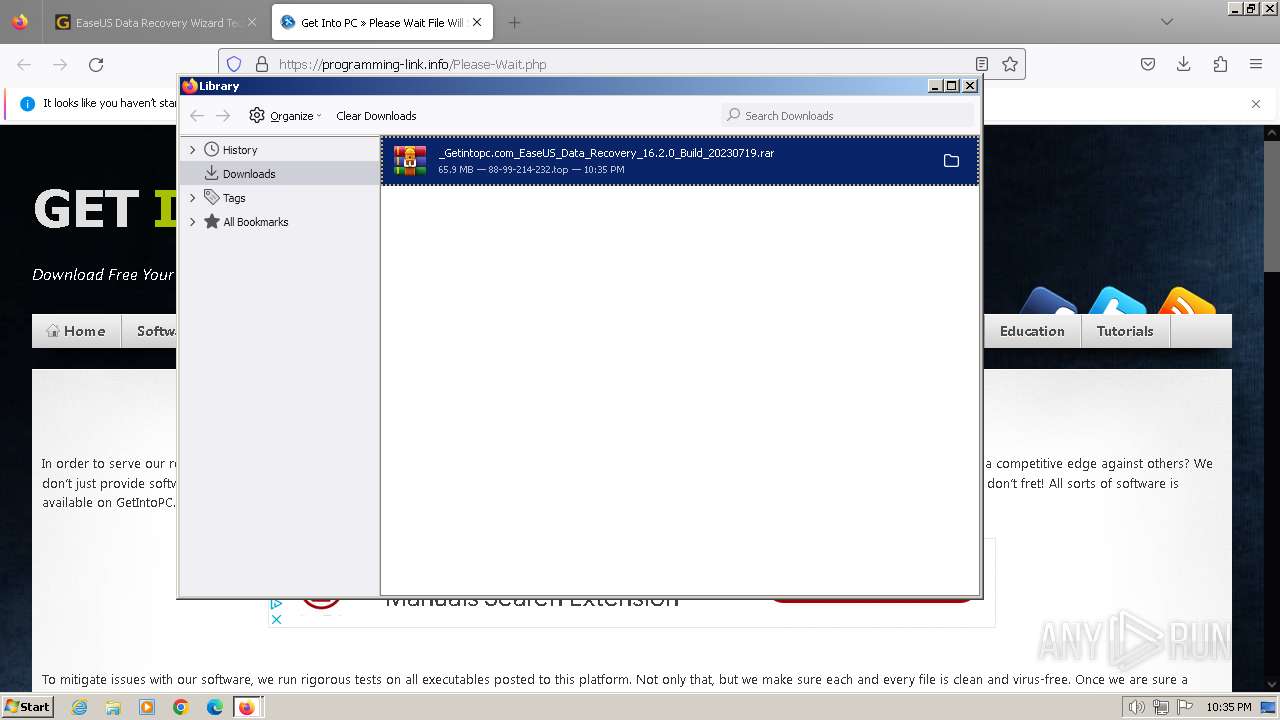
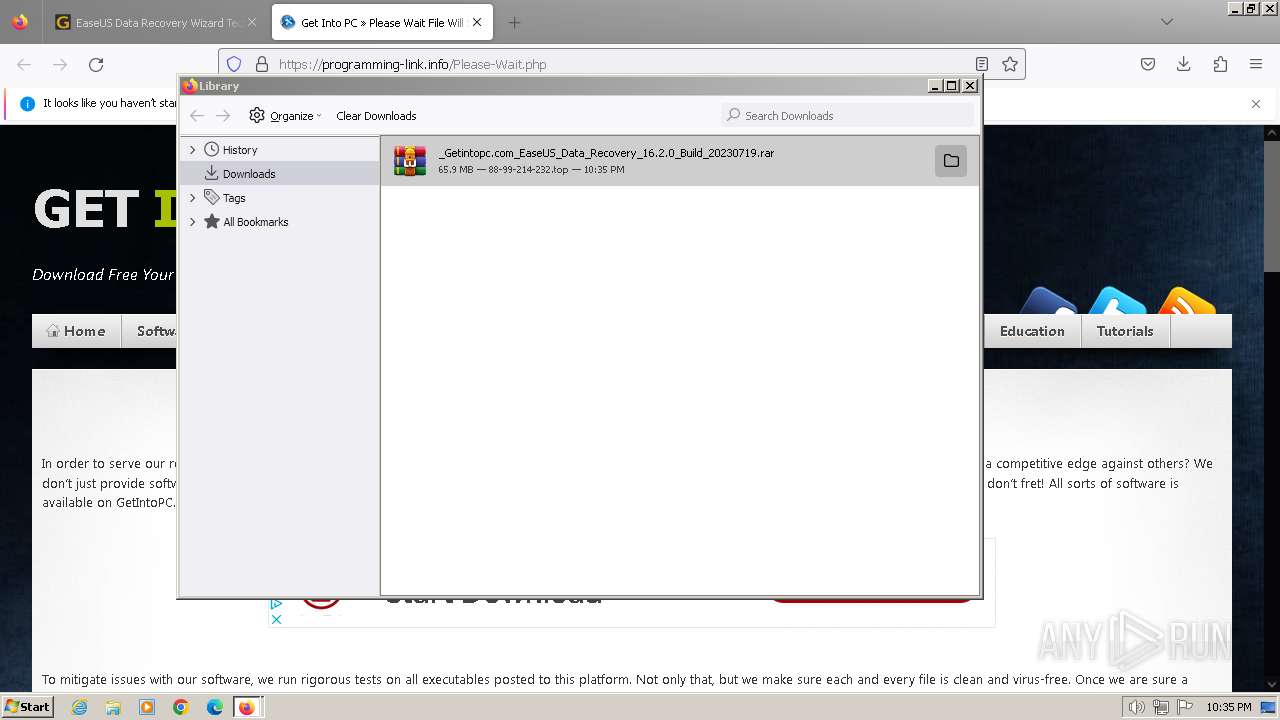
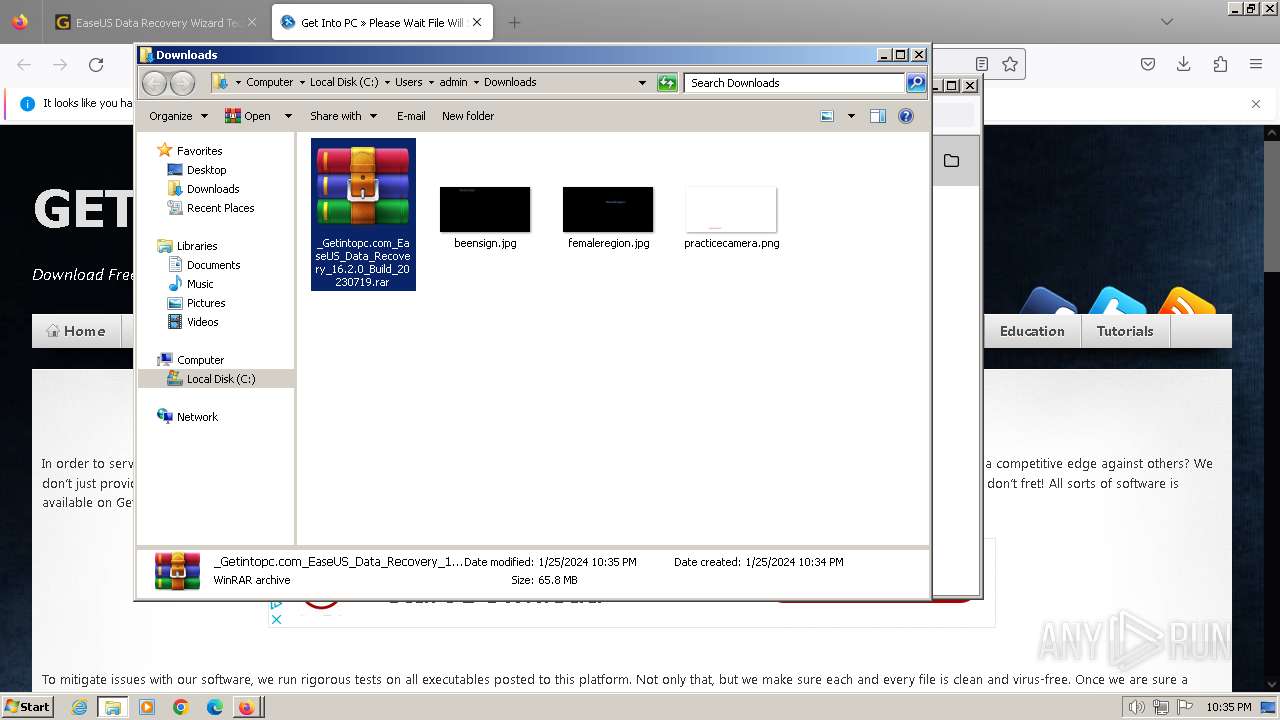
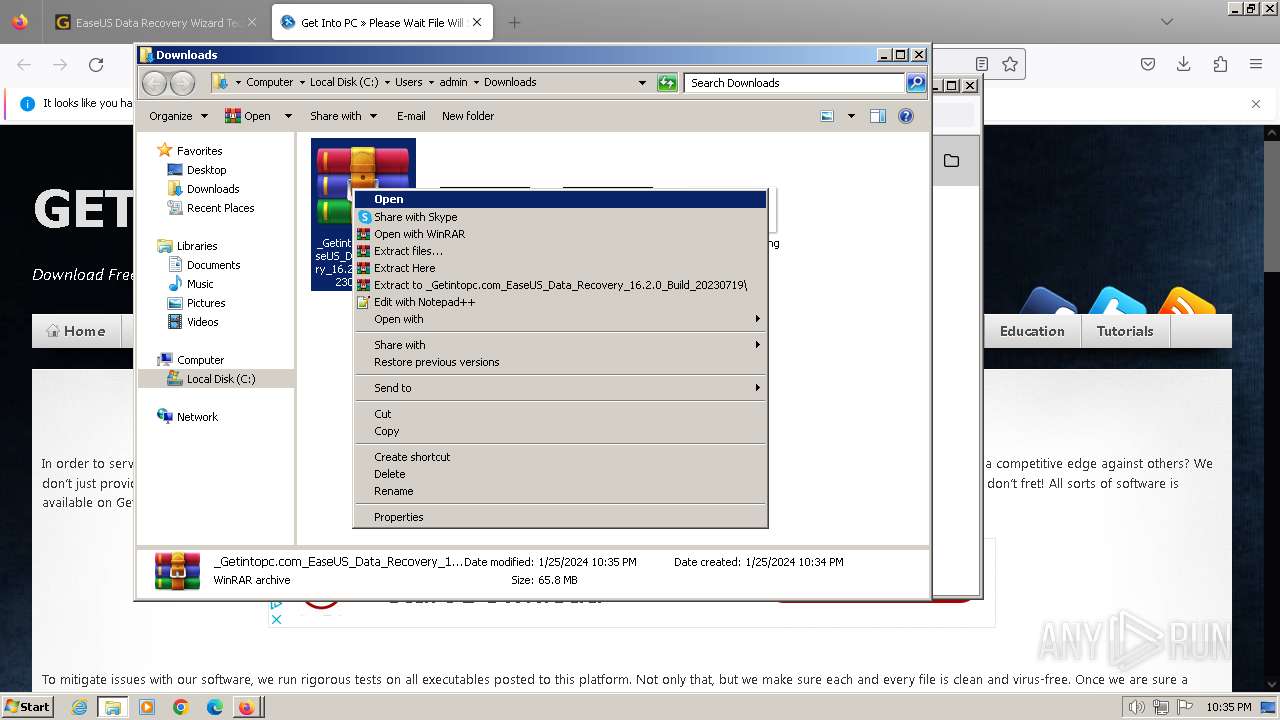
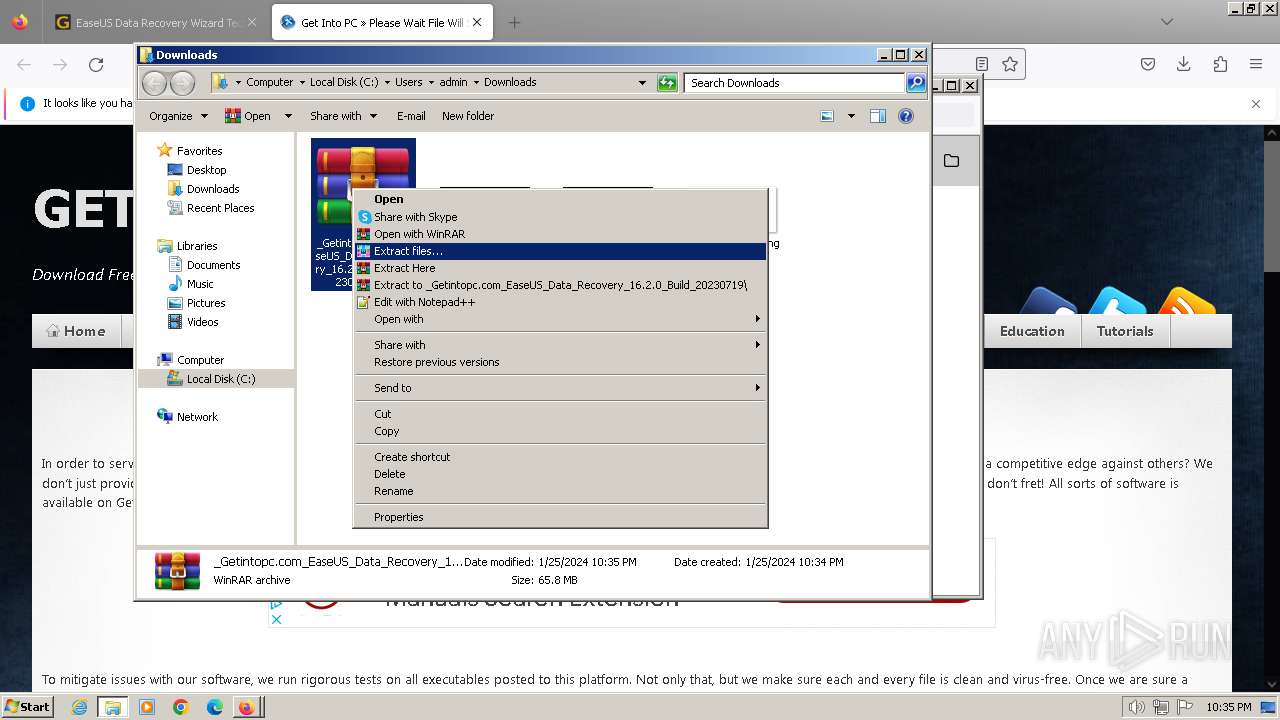
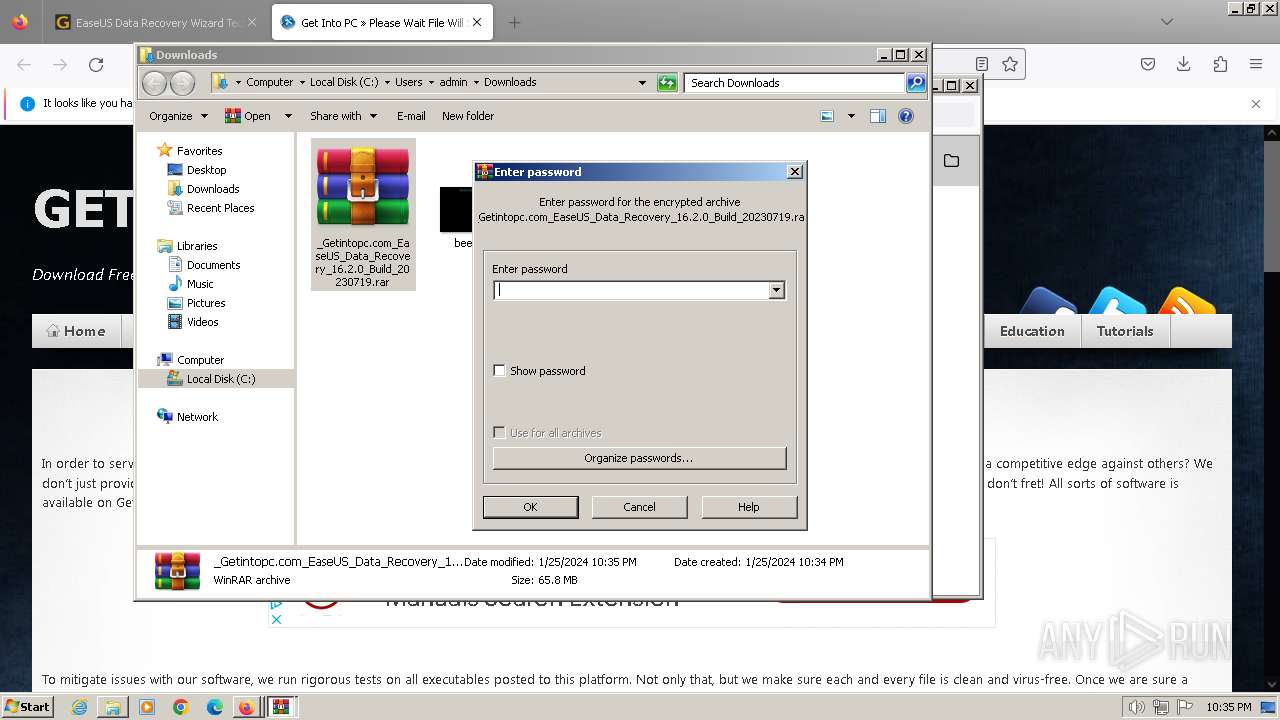
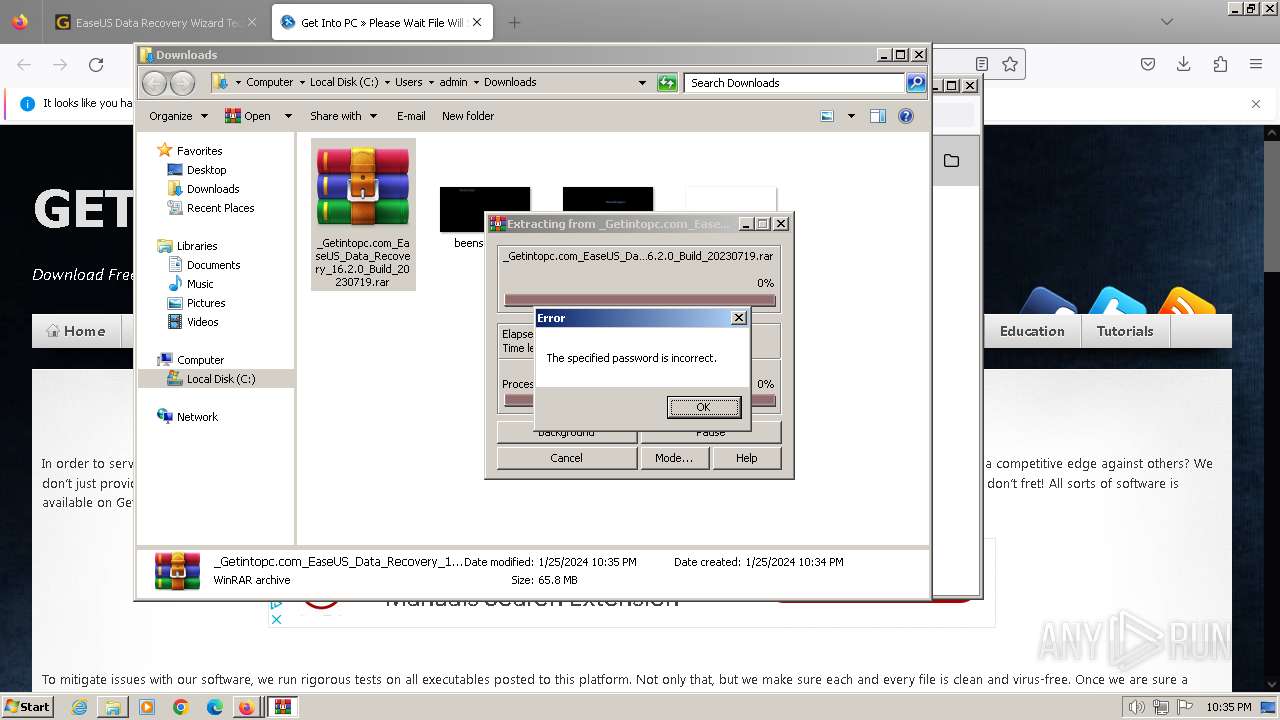
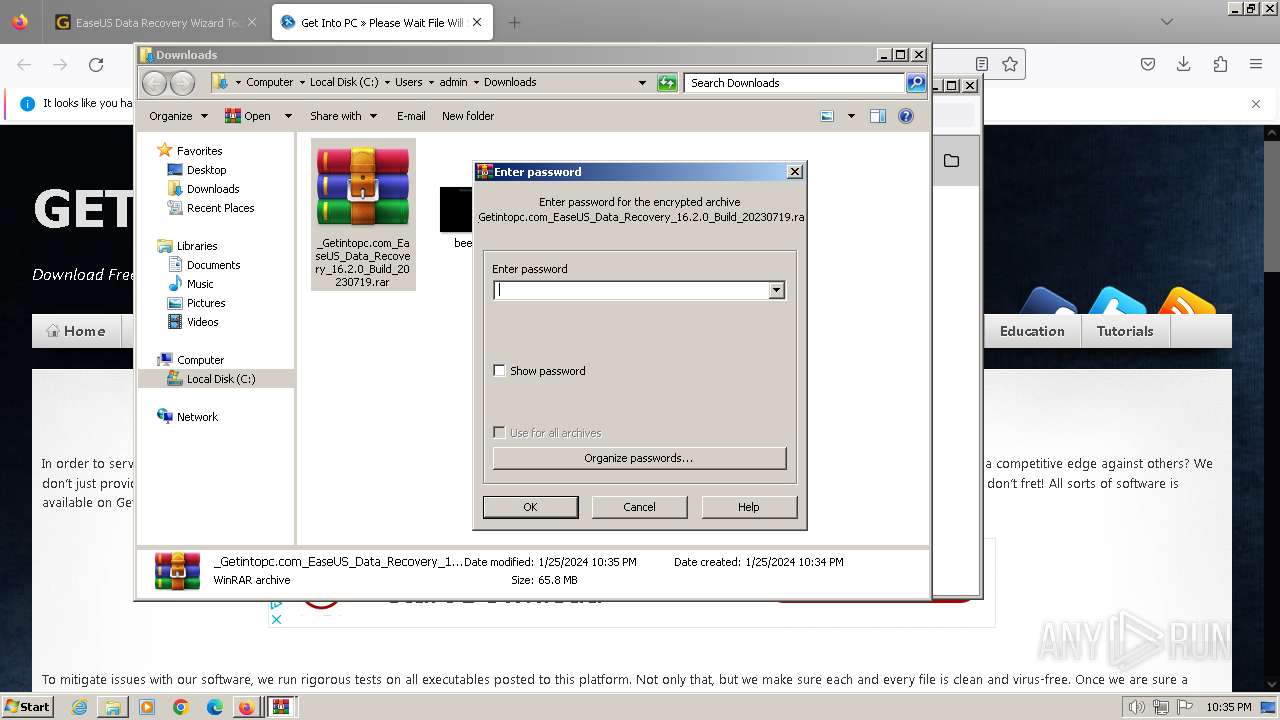
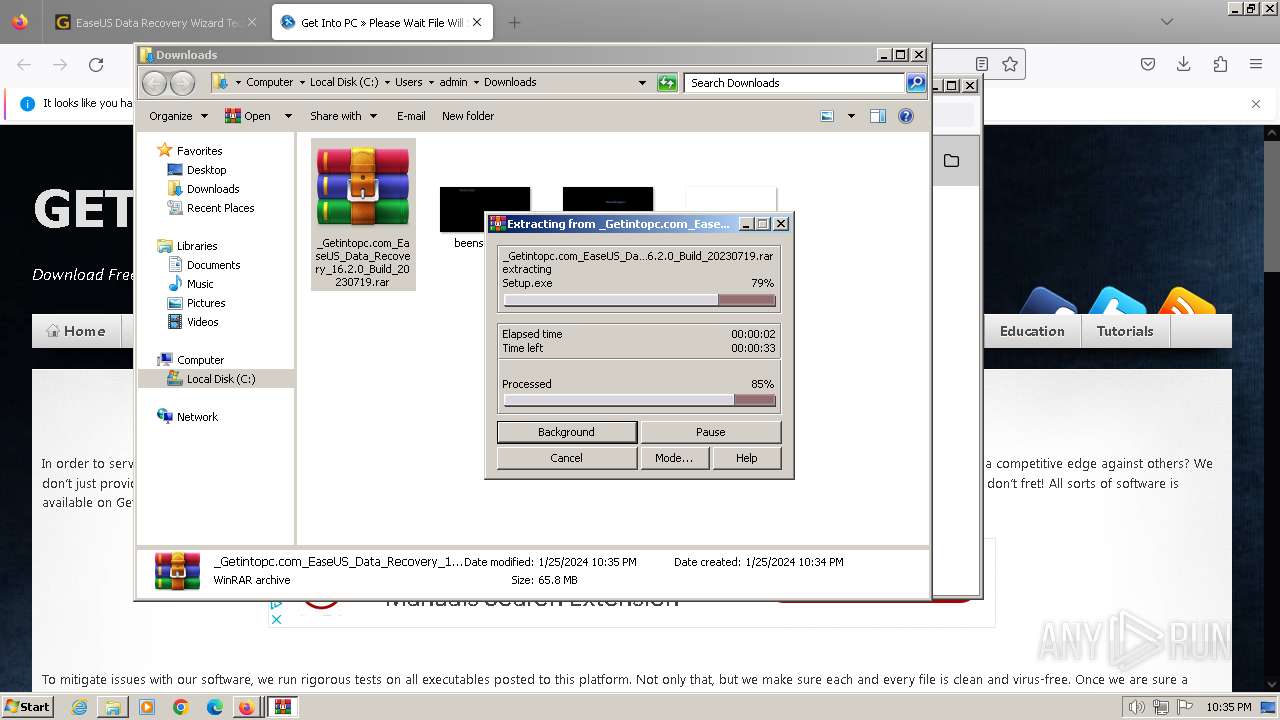
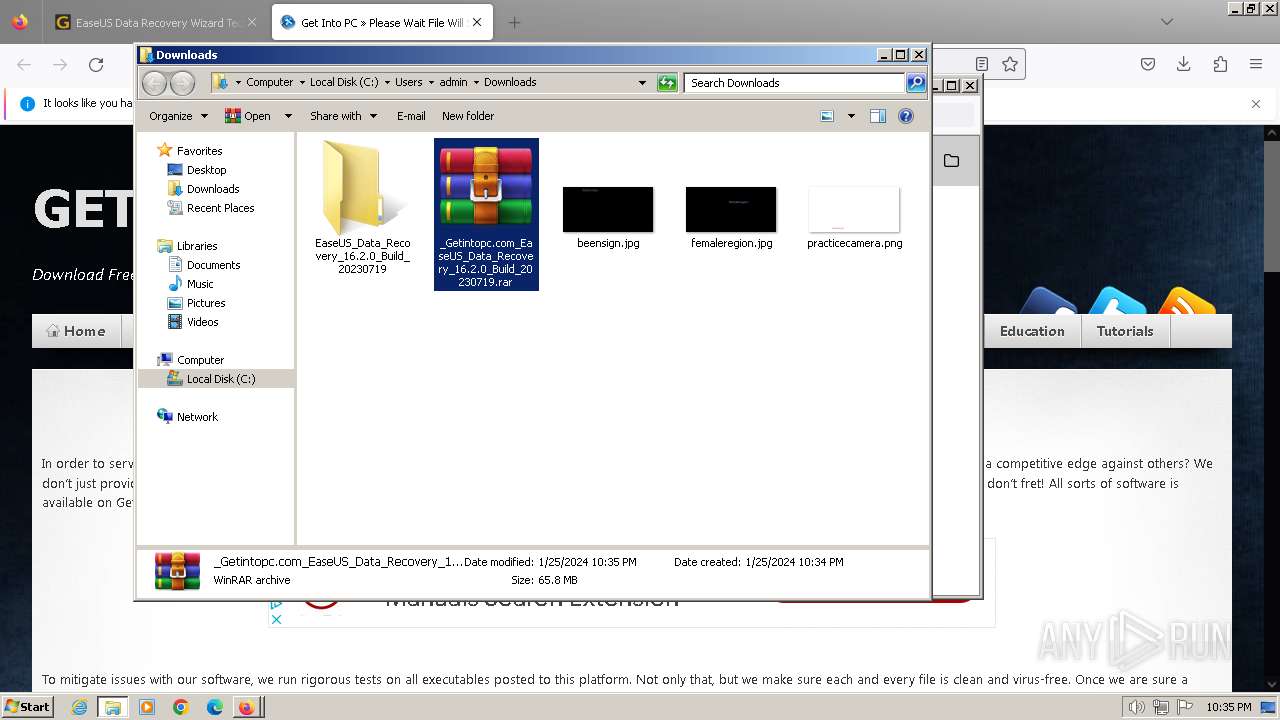
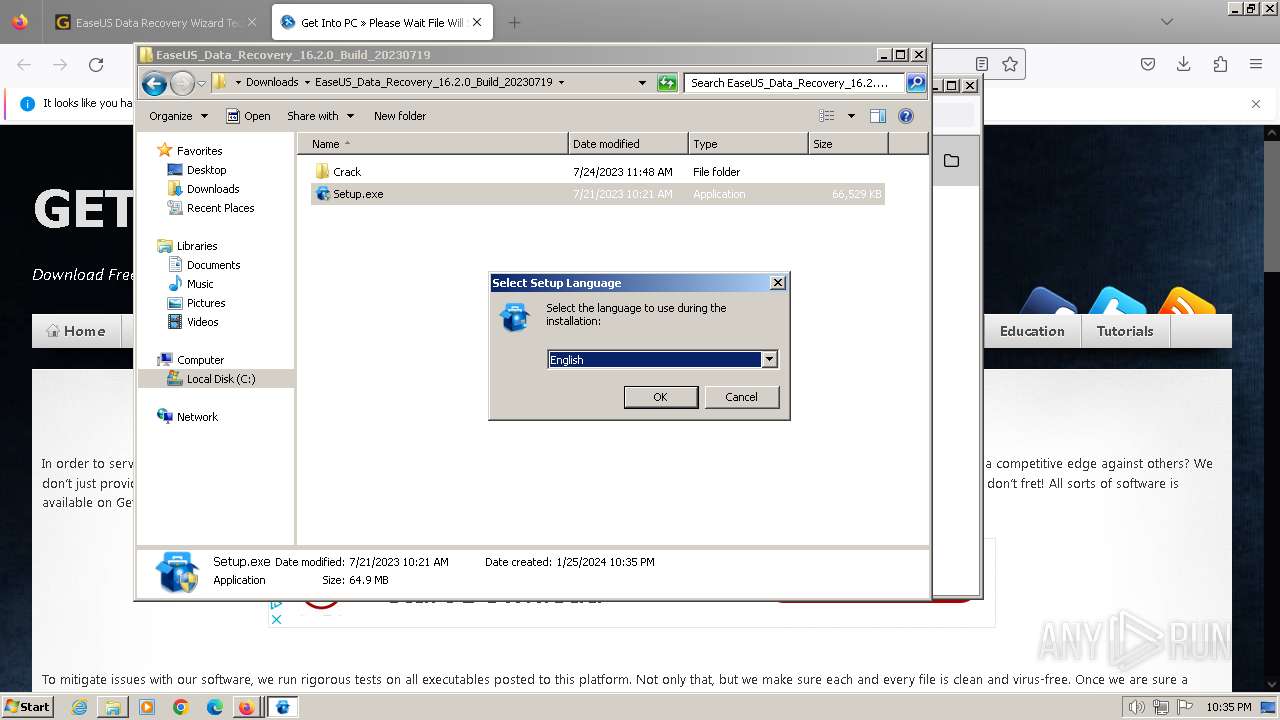
Manual execution by a user
- chrome.exe (PID: 952)
- WinRAR.exe (PID: 1748)
- firefox.exe (PID: 116)
- Setup.exe (PID: 3096)
- Setup.exe (PID: 3988)
The process uses the downloaded file
- firefox.exe (PID: 3892)
- WinRAR.exe (PID: 1748)
Checks supported languages
- Setup.exe (PID: 3096)
- Setup.tmp (PID: 2516)
- AliyunWrapExe.Exe (PID: 3476)
- InfoForSetup.exe (PID: 764)
- InfoForSetup.exe (PID: 1192)
- InfoForSetup.exe (PID: 1836)
- InfoForSetup.exe (PID: 3212)
- InfoForSetup.exe (PID: 1656)
Create files in a temporary directory
- Setup.exe (PID: 3096)
- Setup.tmp (PID: 2516)
- AliyunWrapExe.Exe (PID: 3476)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1748)
- firefox.exe (PID: 3892)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1748)
- firefox.exe (PID: 3892)
Reads the computer name
- Setup.tmp (PID: 2516)
- InfoForSetup.exe (PID: 1656)
- AliyunWrapExe.Exe (PID: 3476)
Reads the machine GUID from the registry
- AliyunWrapExe.Exe (PID: 3476)
Checks proxy server information
- AliyunWrapExe.Exe (PID: 3476)
Creates files or folders in the user directory
- AliyunWrapExe.Exe (PID: 3476)
Creates files in the program directory
- Setup.tmp (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
38
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
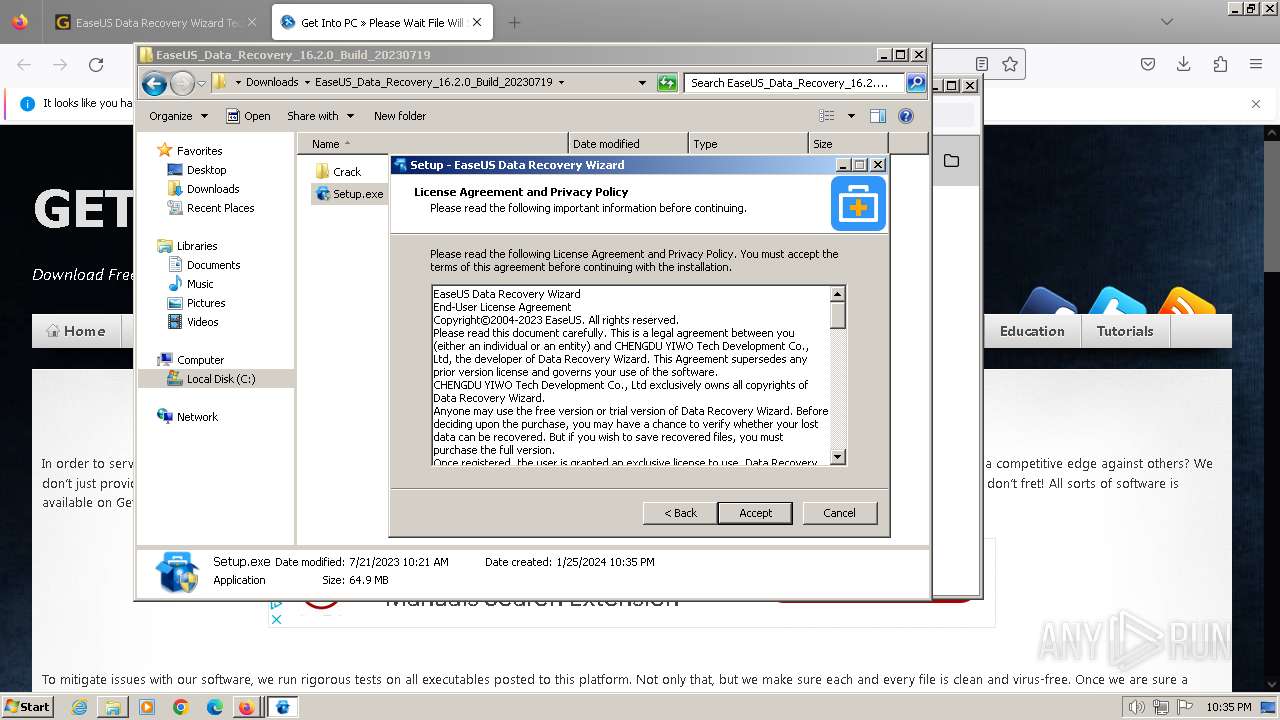
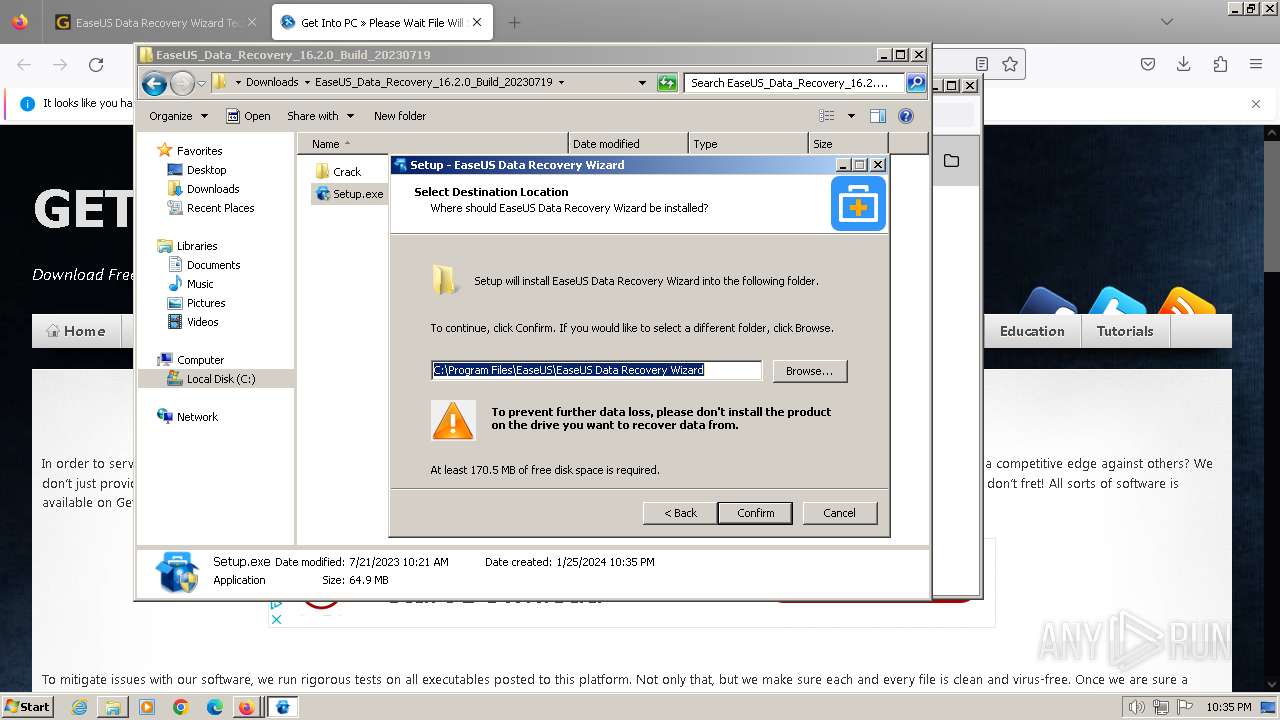
| 764 | "C:\Users\admin\AppData\Local\Temp\is-D465R.tmp\InfoForSetup.exe" /SendInfo "Window" "Selectdestinationlocation" "Activity" "Click_Confirm" "Attribute" "{\"Path\":\"C:/Program Files/EaseUS/EaseUS Data Recovery Wizard\"}" | C:\Users\admin\AppData\Local\Temp\is-D465R.tmp\InfoForSetup.exe | — | Setup.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://getintopc.com/softwares/data-recovery/easeus-data-recovery-wizard-technician-2023-free-download/?id=000027747110" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
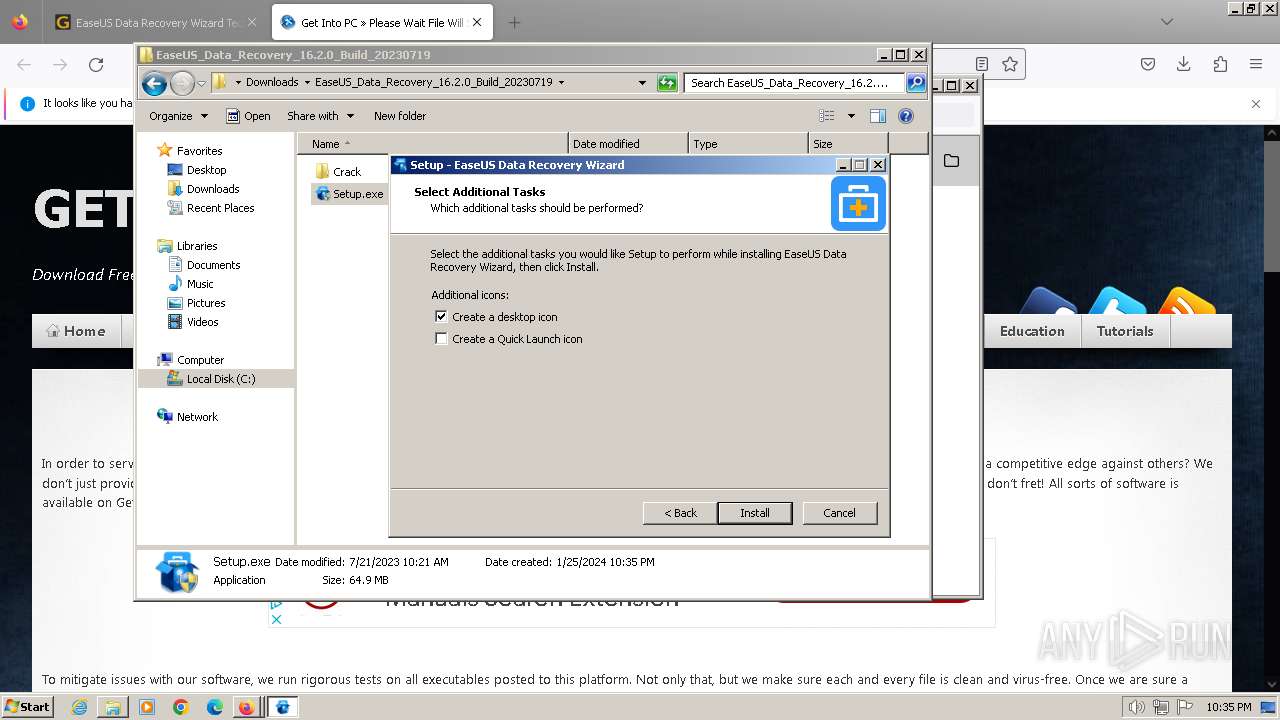
| 1192 | "C:\Users\admin\AppData\Local\Temp\is-D465R.tmp\InfoForSetup.exe" /SendInfo "Window" "Setup" "Activity" "Click_Next" | C:\Users\admin\AppData\Local\Temp\is-D465R.tmp\InfoForSetup.exe | — | Setup.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3892.3.2124712840\1568184366" -childID 2 -isForBrowser -prefsHandle 2936 -prefMapHandle 2932 -prefsLen 34225 -prefMapSize 244195 -jsInitHandle 904 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {9845d882-7bc7-485b-8db8-943e11abeb67} 3892 "\\.\pipe\gecko-crash-server-pipe.3892" 2948 169c6280 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3892.0.166630467\1617392062" -parentBuildID 20230710165010 -prefsHandle 1120 -prefMapHandle 1112 -prefsLen 28523 -prefMapSize 244195 -appDir "C:\Program Files\Mozilla Firefox\browser" - {75a4e6ad-2b8c-46ef-9650-619530d3af40} 3892 "\\.\pipe\gecko-crash-server-pipe.3892" 1208 d6a71a0 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 115.0.2 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1596 --field-trial-handle=1180,i,14585813738776597004,17423236447379104063,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1332 --field-trial-handle=1180,i,14585813738776597004,17423236447379104063,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3892.2.496987131\111381666" -childID 1 -isForBrowser -prefsHandle 1904 -prefMapHandle 1988 -prefsLen 28712 -prefMapSize 244195 -jsInitHandle 904 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {2c3a839d-6539-4790-a612-e34c3694b4ee} 3892 "\\.\pipe\gecko-crash-server-pipe.3892" 1940 1294e6d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
Total events
36 704
Read events
36 495
Write events
201
Delete events
8
Modification events
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
167
Suspicious files
389
Text files
3 359
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab93A5.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\vpnb[1].jpg | image | |
MD5:199ABDF70B59E843EA970BE05D7210B6 | SHA256:8C1940E92C3E9981680F4FF046D52FF4653C2C8EC43874618DCCAB9434AF2718 | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:DEC6BBE308EB44937F77160A25EE32DB | SHA256:68A71DE28F488586C2B169F4652347E0A1FD632D48A6D6725393607BFA18BC7E | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:2CD1F10011C9C972E3412DF1A52B2E56 | SHA256:C35600A62D79A32FA23A99AE0F0AD12448374C8156BB702228119912B470C8FC | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\how-to-install-this-software-video-guide-300x38[1].jpg | image | |
MD5:64C18496D1E14B02DB9E52400C621F40 | SHA256:606BAFE3466072A4890C74D0BC930639A6C4A748AE355364D2779471E3C24DEE | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9395.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9394.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\custom[1].js | text | |
MD5:8C2F0AA23AB723054AF33328B39FB889 | SHA256:F397A7D4B3C23E363C5713F26C513BE01067C6F25FE73EDD59F66B8F4F8CD5B1 | |||
| 2468 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar93A6.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
200
DNS requests
264
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2468 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f27fe043238c6b38 | unknown | — | — | unknown |
2468 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?96e261c22e45b24e | unknown | — | — | unknown |
2468 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3ecbecc82f68617c | unknown | compressed | 65.2 Kb | unknown |
2468 | iexplore.exe | GET | 200 | 104.76.201.34:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2468 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?09ca35c5e0844a72 | unknown | compressed | 65.2 Kb | unknown |
2468 | iexplore.exe | GET | 200 | 104.76.201.34:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
2468 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2468 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
2468 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDSGL5P0jvZghCoV3kPjCsM | unknown | binary | 472 b | unknown |
2468 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFejVwQAErPUClguUf1d52A%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2468 | iexplore.exe | 172.67.75.211:443 | getintopc.com | CLOUDFLARENET | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2468 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2468 | iexplore.exe | 104.76.201.34:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2468 | iexplore.exe | 142.250.186.170:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
2468 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2468 | iexplore.exe | 142.250.186.46:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
2468 | iexplore.exe | 199.232.192.134:443 | getintopcofficial.disqus.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getintopc.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google-analytics.com |
| whitelisted |
getintopcofficial.disqus.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |