| File name: | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin |
| Full analysis: | https://app.any.run/tasks/d79f4839-d229-4dd6-b058-1d71790095cb |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 07:53:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FE841FFE47614CA18259F11B7E899537 |
| SHA1: | DCAA2B828E338A155EFE886C38B87AC95D6D0936 |
| SHA256: | 52AA9AC835AC7561C80DA59C1EF0BA9EBBA4ED5CF7FC167541B268DE333CFF7B |
| SSDEEP: | 49152:EDXgoKH31fF1yYuRL0AbHnyCVLmzeDHlntfYdDyllKvFkAAeNTESftT:EraPRkL0aHyKRDHlVYdD5kuNr |
MALICIOUS
Actions looks like stealing of personal data
- 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe (PID: 3364)
Modifies files in Chrome extension folder
- 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe (PID: 3364)
SUSPICIOUS
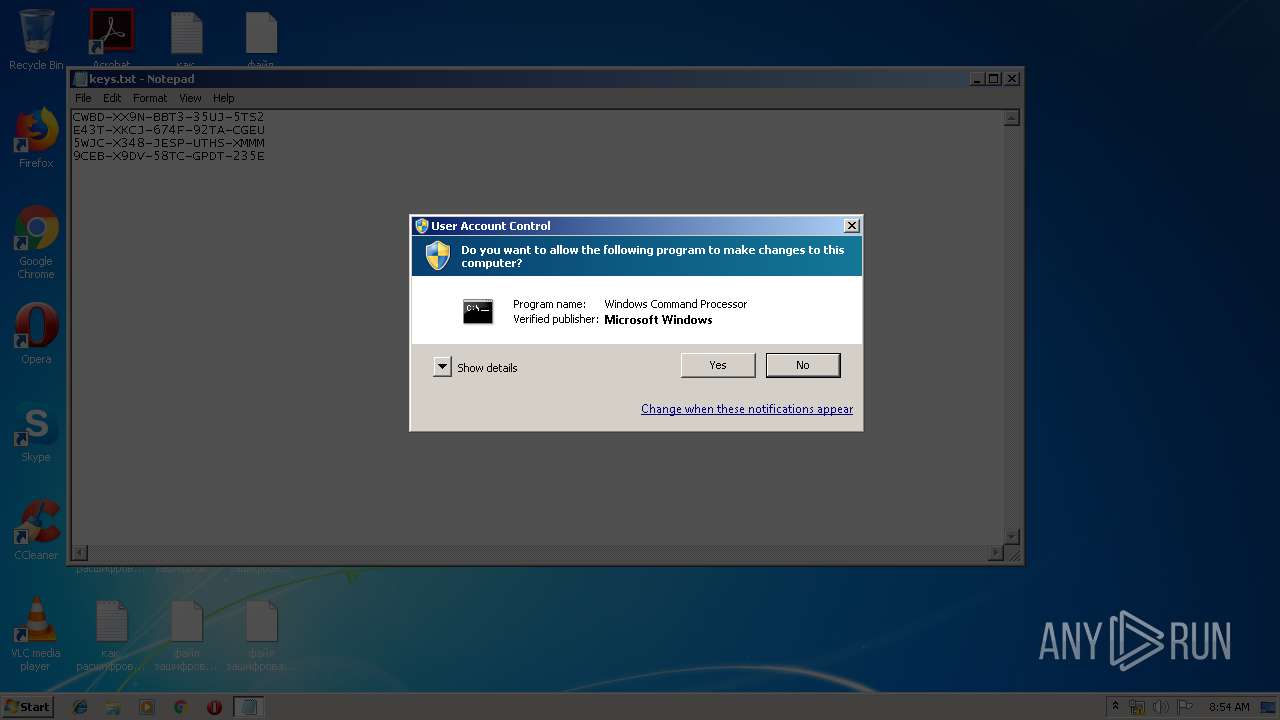
Starts application with an unusual extension
- cmd.exe (PID: 2084)
Starts CMD.EXE for commands execution
- 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe (PID: 3364)
Creates files in the user directory
- 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe (PID: 3364)
Changes the desktop background image
- 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe (PID: 3364)
Changes tracing settings of the file or console
- 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe (PID: 3364)
Checks for external IP
- 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe (PID: 3364)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:10 08:51:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1267712 |
| InitializedDataSize: | 267264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x673000 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2019 06:51:31 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 10-Jun-2019 06:51:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x00168000 | 0x00069000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9836 | |
.rsrc | 0x00169000 | 0x0001B400 | 0x00016600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97742 |
.idata | 0x00185000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.30872 |
0x00186000 | 0x00335000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.260771 | |
zwhicbjz | 0x004BB000 | 0x001B8000 | 0x001B7C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95429 |
xcobnbcj | 0x00673000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9054 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0447 | 3752 | UNKNOWN | English - United States | RT_ICON |
4078 | 7.56161 | 568 | UNKNOWN | UNKNOWN | RT_STRING |
4079 | 7.82379 | 1164 | UNKNOWN | UNKNOWN | RT_STRING |
4080 | 7.75812 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4081 | 7.73227 | 912 | UNKNOWN | UNKNOWN | RT_STRING |
4082 | 7.55699 | 788 | UNKNOWN | UNKNOWN | RT_STRING |
4083 | 7.65085 | 1152 | UNKNOWN | UNKNOWN | RT_STRING |
4084 | 7.64341 | 816 | UNKNOWN | UNKNOWN | RT_STRING |
4085 | 7.71514 | 1324 | UNKNOWN | UNKNOWN | RT_STRING |
4086 | 7.71366 | 1484 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
comctl32.dll |
kernel32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x0014263C |
__dbk_fcall_wrapper | 2 | 0x00011520 |
TMethodImplementationIntercept | 3 | 0x00062880 |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2084 | cmd /c ""C:\Users\admin\AppData\Local\Temp\run.bat" " | C:\Windows\system32\cmd.exe | — | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3068 | chcp 1251 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\AppData\Local\Temp\52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe" | C:\Users\admin\AppData\Local\Temp\52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
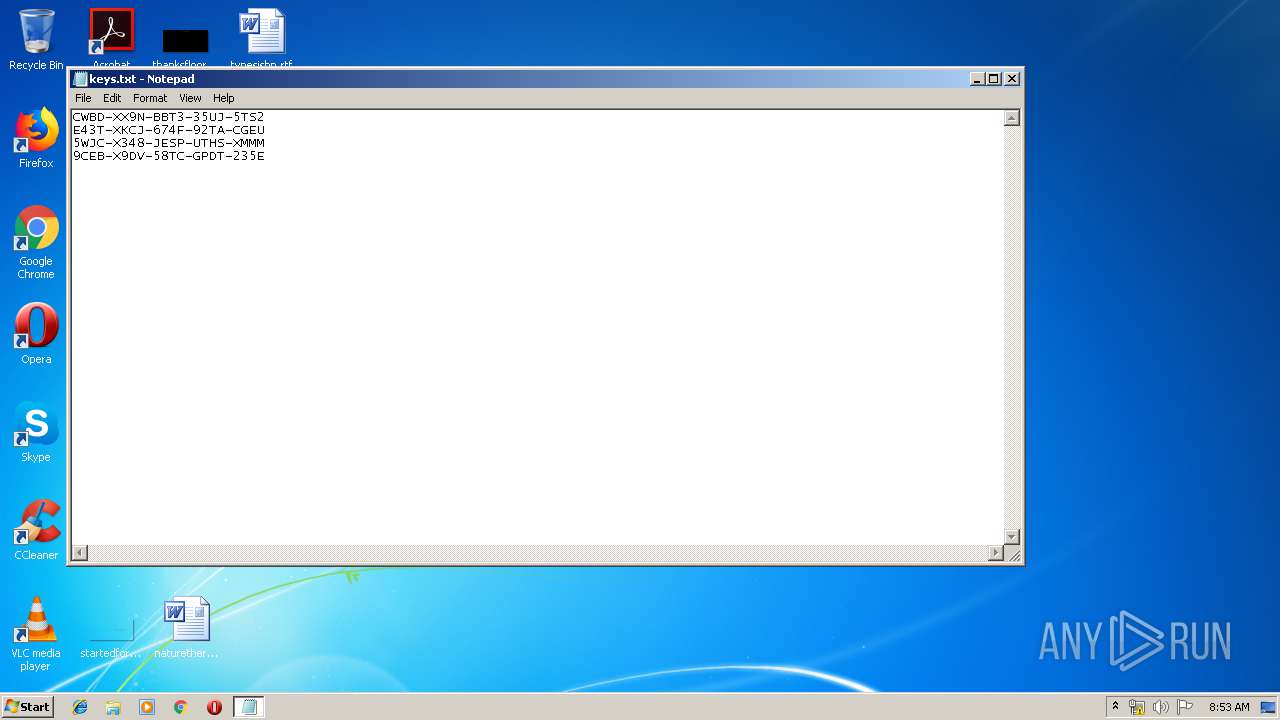
| 3756 | notepad.exe "C:\Users\admin\AppData\Local\Temp\keys.txt" | C:\Windows\system32\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
421
Read events
400
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | check |
Value: again | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3364) 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
431
Text files
14
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr.dat | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr65536.dat | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\CEF\User Data\Crashpad\settings.dat | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\FileZilla\default_auto16x16.png | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\FileZilla\default_cancel20x20.png | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\FileZilla\default_cancel24x24.png | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\FileZilla\default_close12x12.png | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\FileZilla\default_compare20x20.png | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\FileZilla\default_disconnect20x20.png | — | |
MD5:— | SHA256:— | |||
| 3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | C:\Users\admin\AppData\Local\FileZilla\default_dropdown12x12.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | CONNECT | — | 139.99.79.246:8080 | http://api.telegram.org:443 | SG | — | — | unknown |
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | GET | 200 | 216.239.32.21:80 | http://ipinfo.io/json | US | text | 154 b | shared |
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | GET | 200 | 216.239.32.21:80 | http://ipinfo.io/json | US | text | 154 b | shared |
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | GET | 200 | 216.239.32.21:80 | http://ipinfo.io/json | US | text | 154 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | 139.99.79.246:8080 | — | OVH SAS | SG | unknown |
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | 216.239.32.21:80 | ipinfo.io | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipinfo.io |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup ipinfo.io |
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup ipinfo.io |
3364 | 52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup ipinfo.io |
Process | Message |
|---|---|
52aa9ac835ac7561c80da59c1ef0ba9ebba4ed5cf7fc167541b268de333cff7b.bin.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|