| File name: | 123.exe |
| Full analysis: | https://app.any.run/tasks/78ac6664-163a-422e-9bf6-44dc89a729c0 |
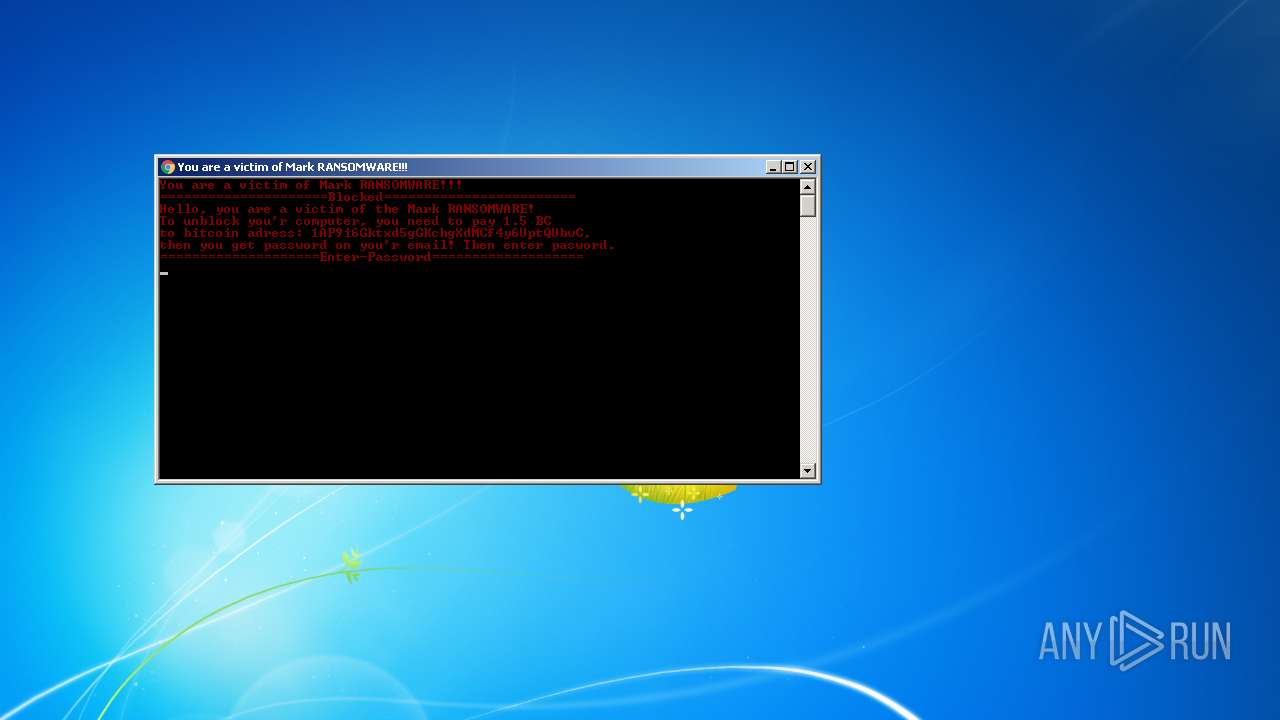
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 22:47:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 06D0294C27B8F1BEB6F5F559214E6057 |
| SHA1: | 8729CF2B7DB298D1D80071B6A552B93EBE223A43 |
| SHA256: | 5285628ABCA40CA53EFE6EAD8F69F3AA0A2CF453C4551E7E4A2C0B3485549112 |
| SSDEEP: | 3072:ffFfHgTWmCRkGbKGLeNTBfJx0wz5OdRSd:X5aWbksiNTBx+wNaSd |
MALICIOUS
Writes to a start menu file
- cmd.exe (PID: 3952)
Drops executable file immediately after starts
- cmd.exe (PID: 3952)
SUSPICIOUS
Checks supported languages
- 123.exe (PID: 2976)
- cmd.exe (PID: 3952)
Starts CMD.EXE for commands execution
- 123.exe (PID: 2976)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3952)
Creates files in the user directory
- cmd.exe (PID: 3952)
Executable content was dropped or overwritten
- cmd.exe (PID: 3952)
Drops a file with a compile date too recent
- cmd.exe (PID: 3952)
INFO
Checks supported languages
- taskkill.exe (PID: 1180)
Dropped object may contain Bitcoin addresses
- 123.exe (PID: 2976)
Reads the computer name
- taskkill.exe (PID: 1180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 73728 |
| CodeSize: | 70144 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2018:02:01 21:18:05+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Feb-2018 20:18:05 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2018 20:18:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0000387E | 0x00003A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.52797 |
.text | 0x00005000 | 0x0000D642 | 0x0000D800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54615 |
.rdata | 0x00013000 | 0x000033A8 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11033 |
.data | 0x00017000 | 0x0000178C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0994 |
.rsrc | 0x00019000 | 0x0000D8CF | 0x0000DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.22526 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.38732 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.85963 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.94888 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.12819 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.75663 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 7.97292 | 30269 | UNKNOWN | UNKNOWN | RT_ICON |
81FE93E3AC1C0E4C8539EE3461271A32 | 3.23593 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
8CFC8C3408 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D87F64201D8F3E95E213D0F055984216 | 7.83681 | 1097 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | taskkill /im explorer.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\AppData\Local\Temp\123.exe" | C:\Users\admin\AppData\Local\Temp\123.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 255 Modules
| |||||||||||||||
| 3952 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\D057.tmp\D058.tmp\D059.bat C:\Users\admin\AppData\Local\Temp\123.exe" | C:\Windows\system32\cmd.exe | 123.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
58
Read events
58
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | 123.exe | C:\Users\admin\AppData\Local\Temp\D057.tmp\D058.tmp\D059.bat | text | |
MD5:E08359D94934F092762331A3F47CFAE0 | SHA256:57CE6C2DDCCDB6FB313CD42E46E68766E5B22464AAC85EEEE4E24FE32232EA2C | |||
| 3952 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\123.exe | executable | |
MD5:06D0294C27B8F1BEB6F5F559214E6057 | SHA256:5285628ABCA40CA53EFE6EAD8F69F3AA0A2CF453C4551E7E4A2C0B3485549112 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report