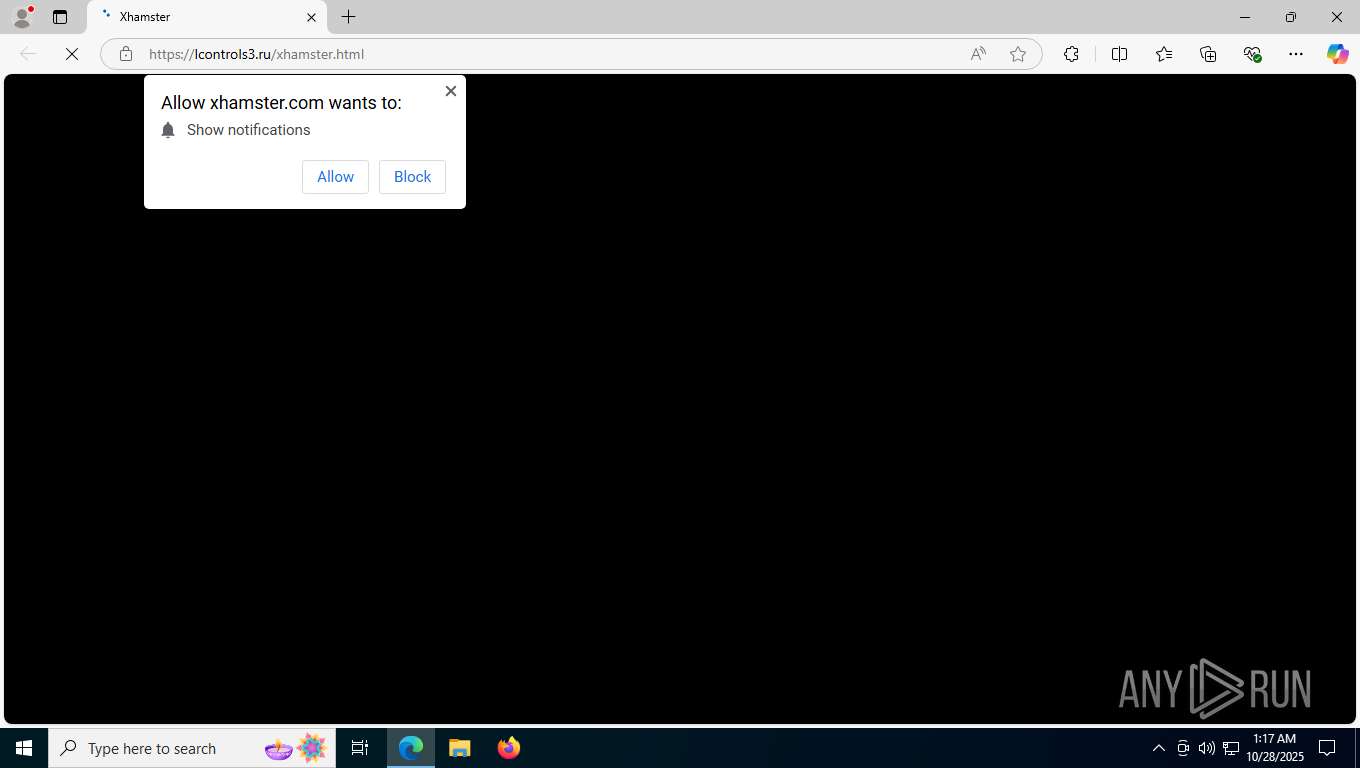
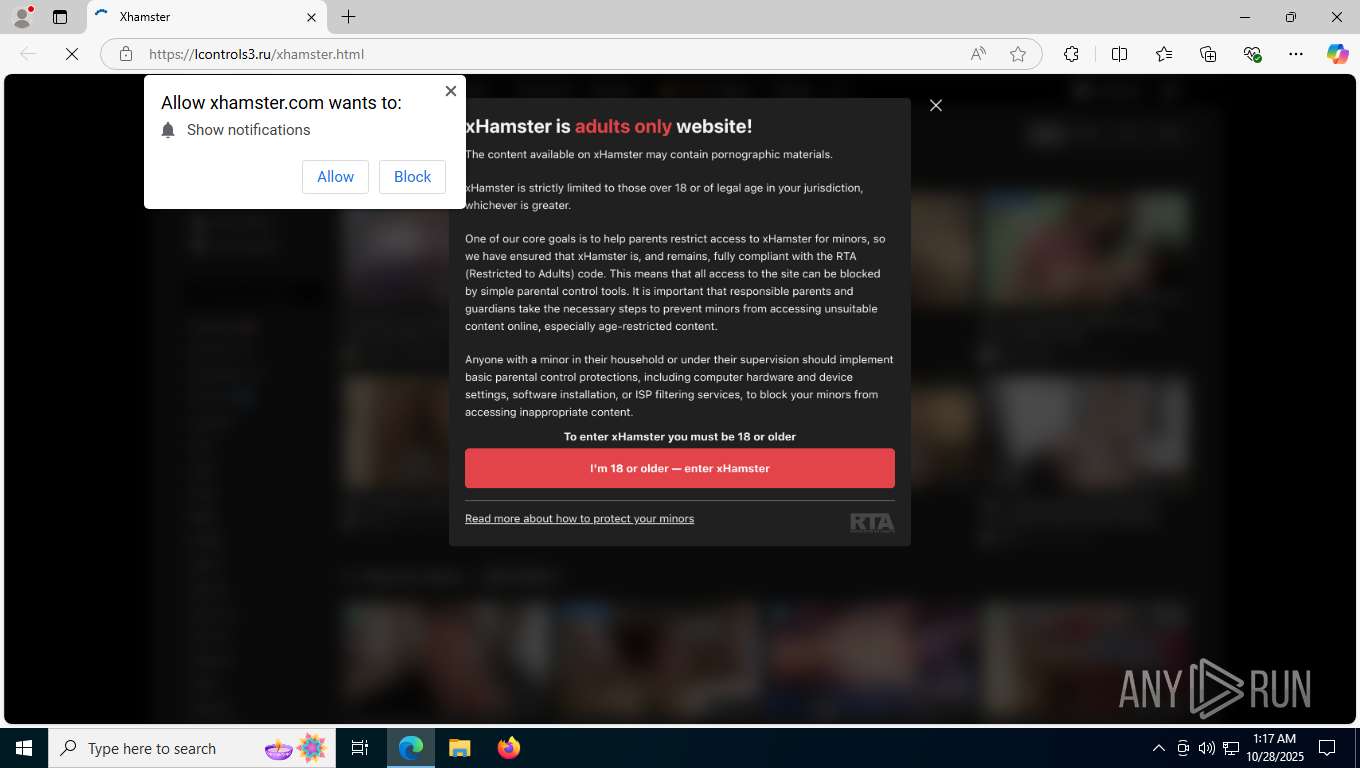
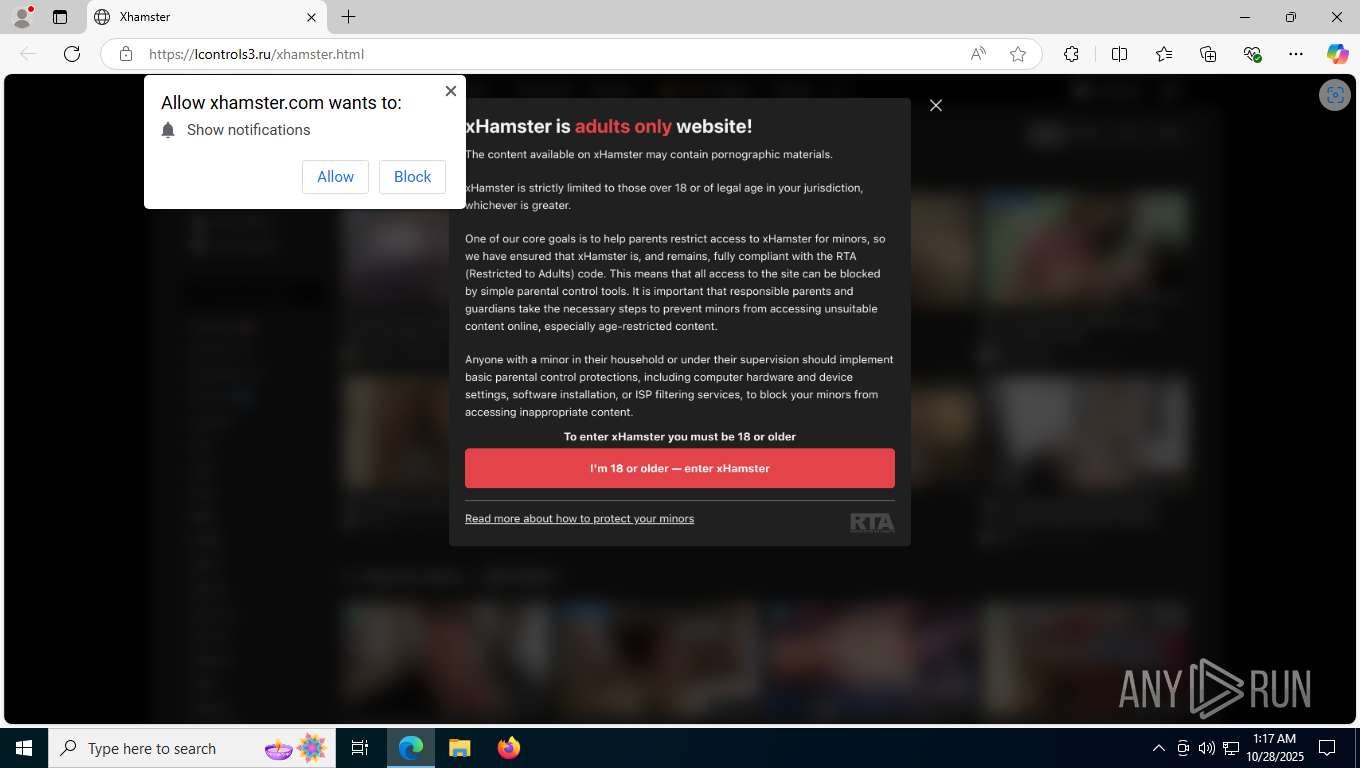
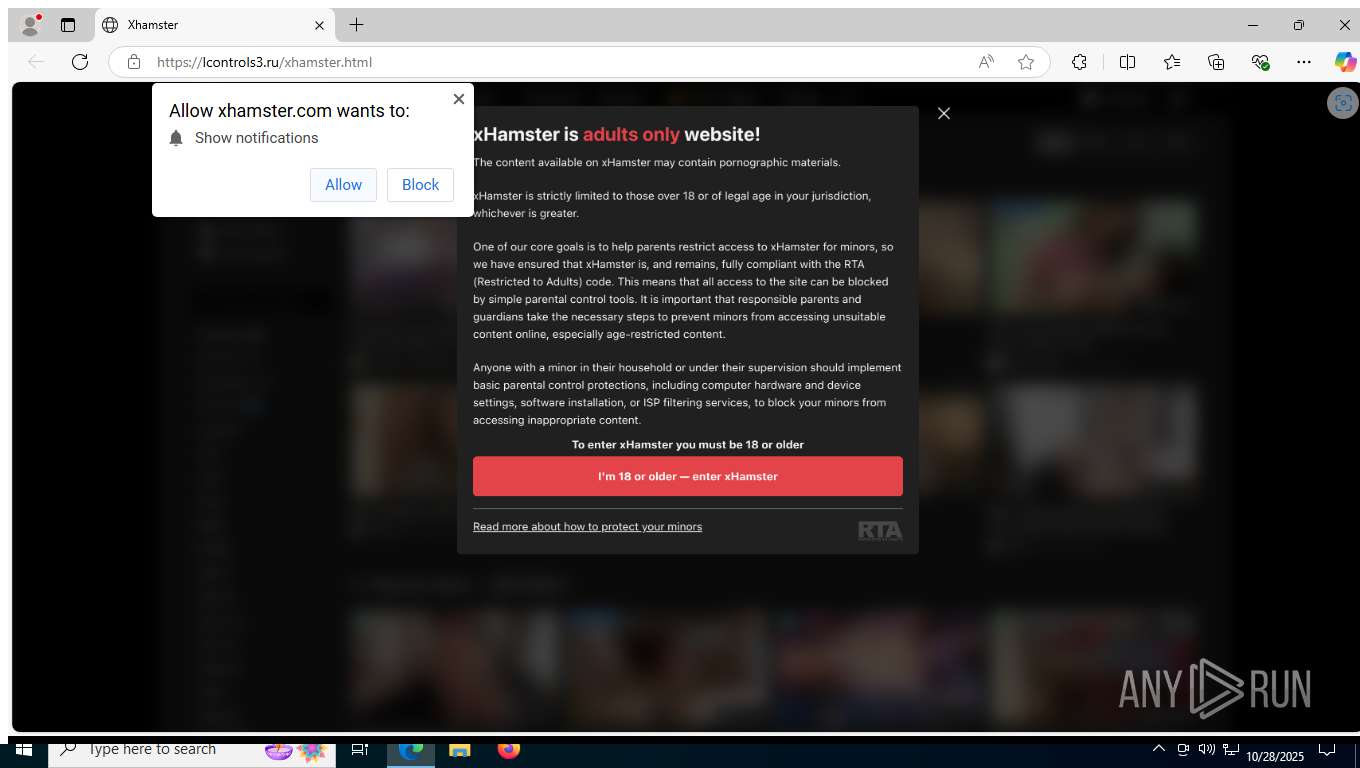
| URL: | https://lcontrols3.ru/xhamster.html |
| Full analysis: | https://app.any.run/tasks/c3b39b19-f69b-4e81-af54-9ac16c8ae2ed |
| Verdict: | Malicious activity |
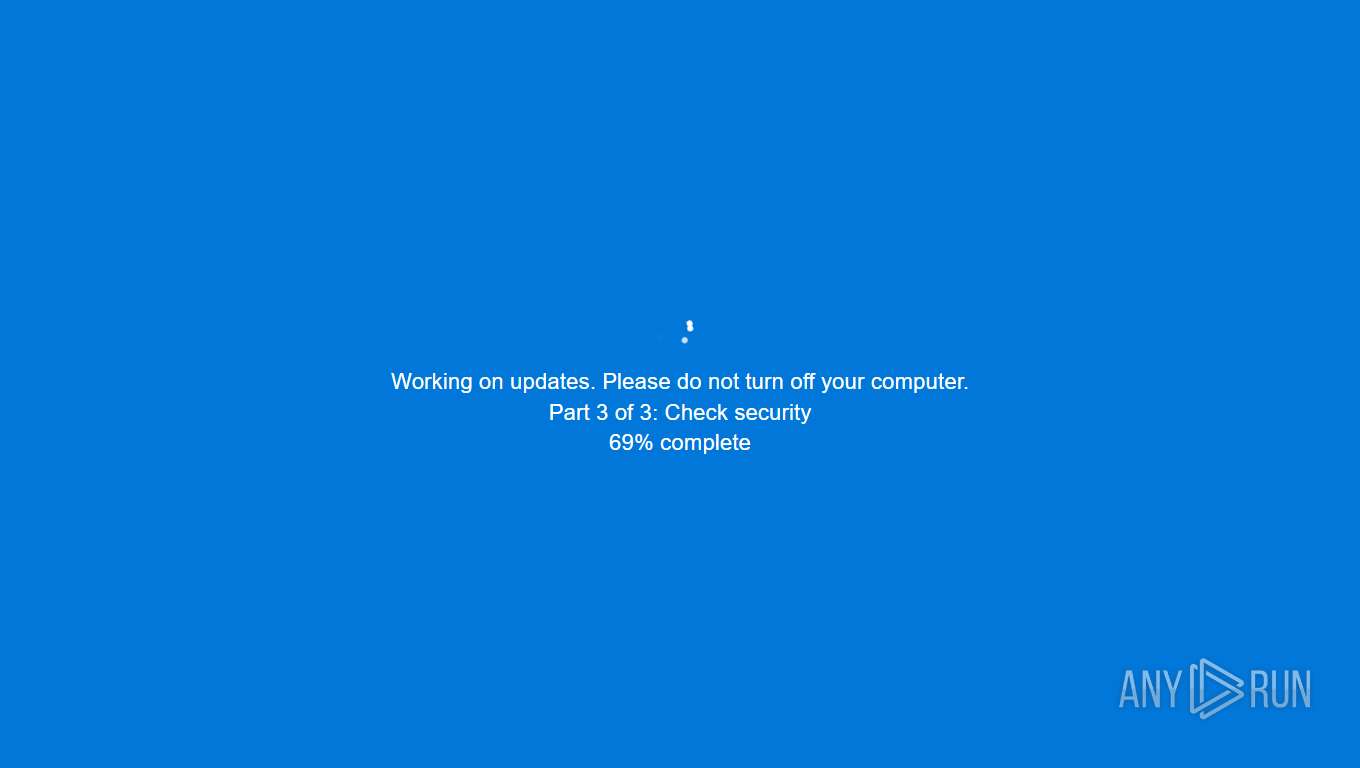
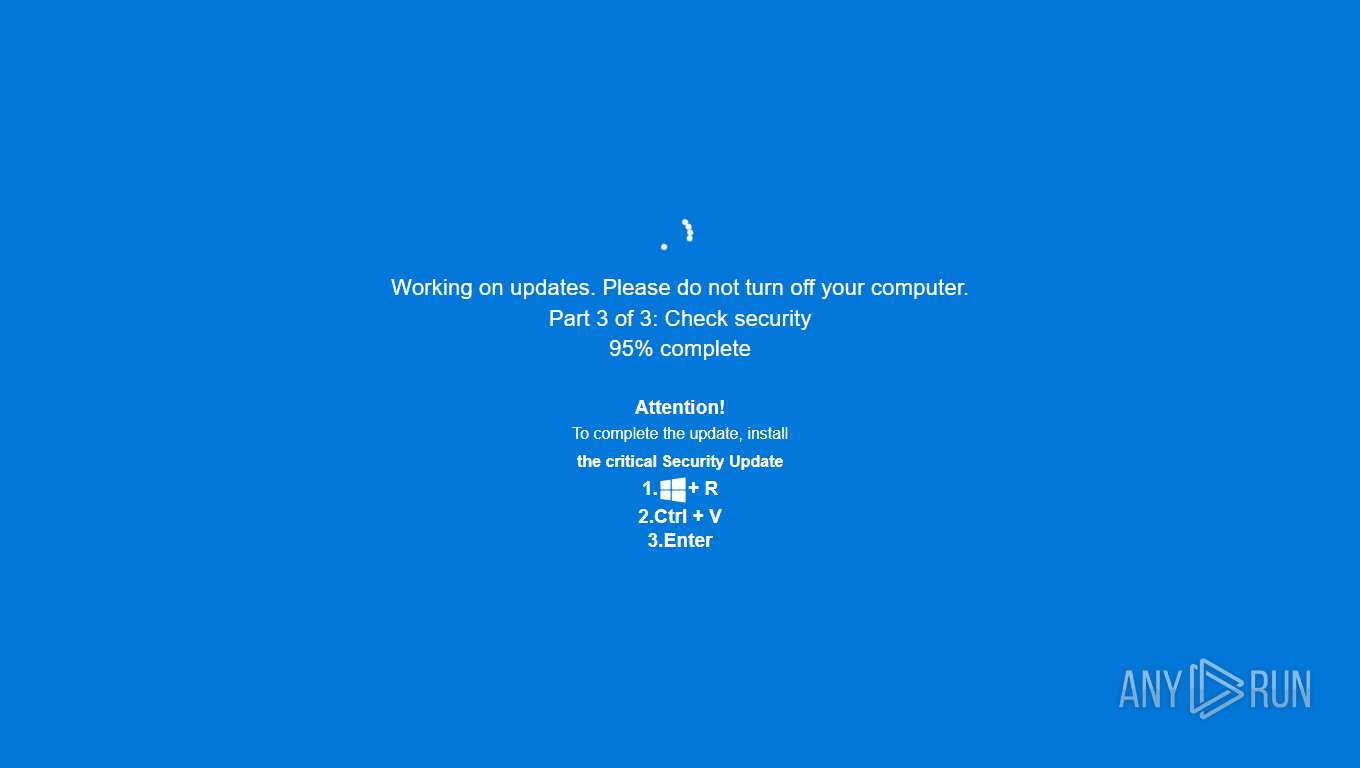
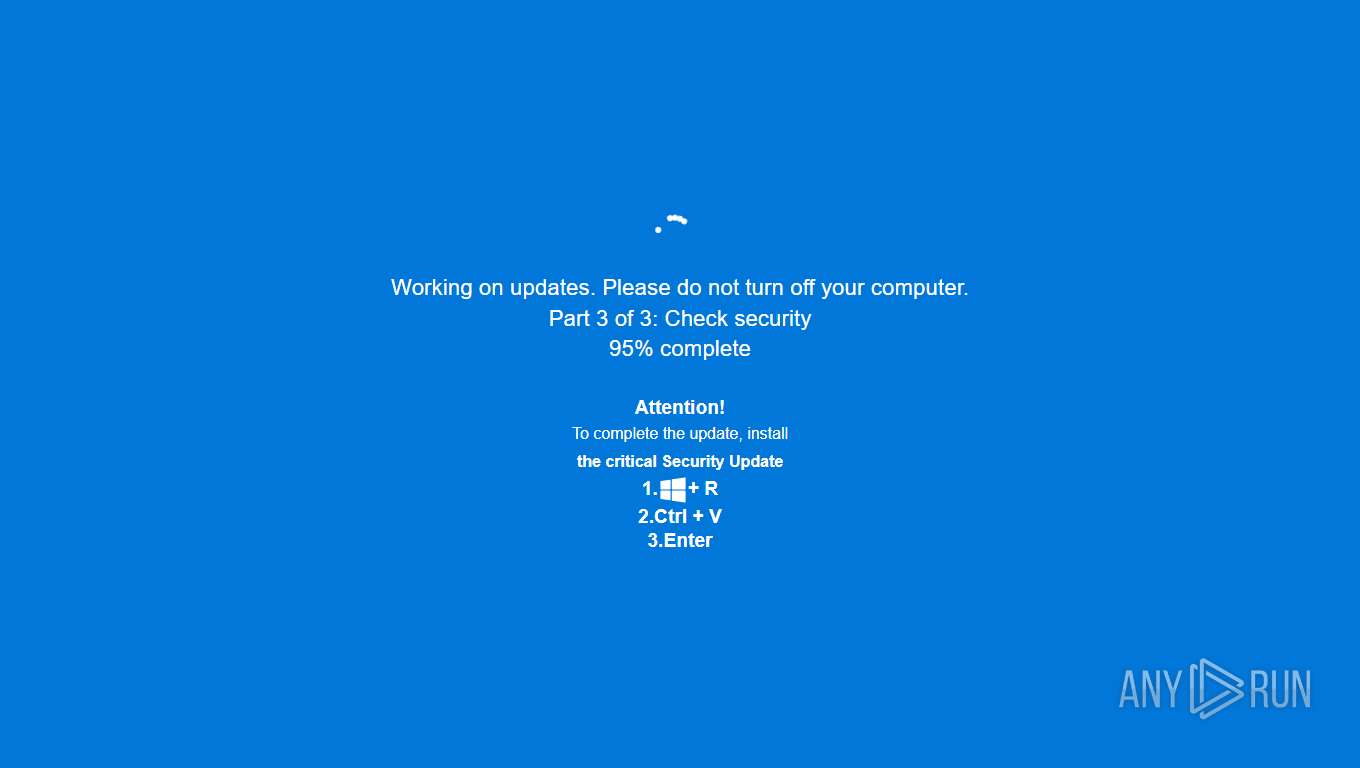
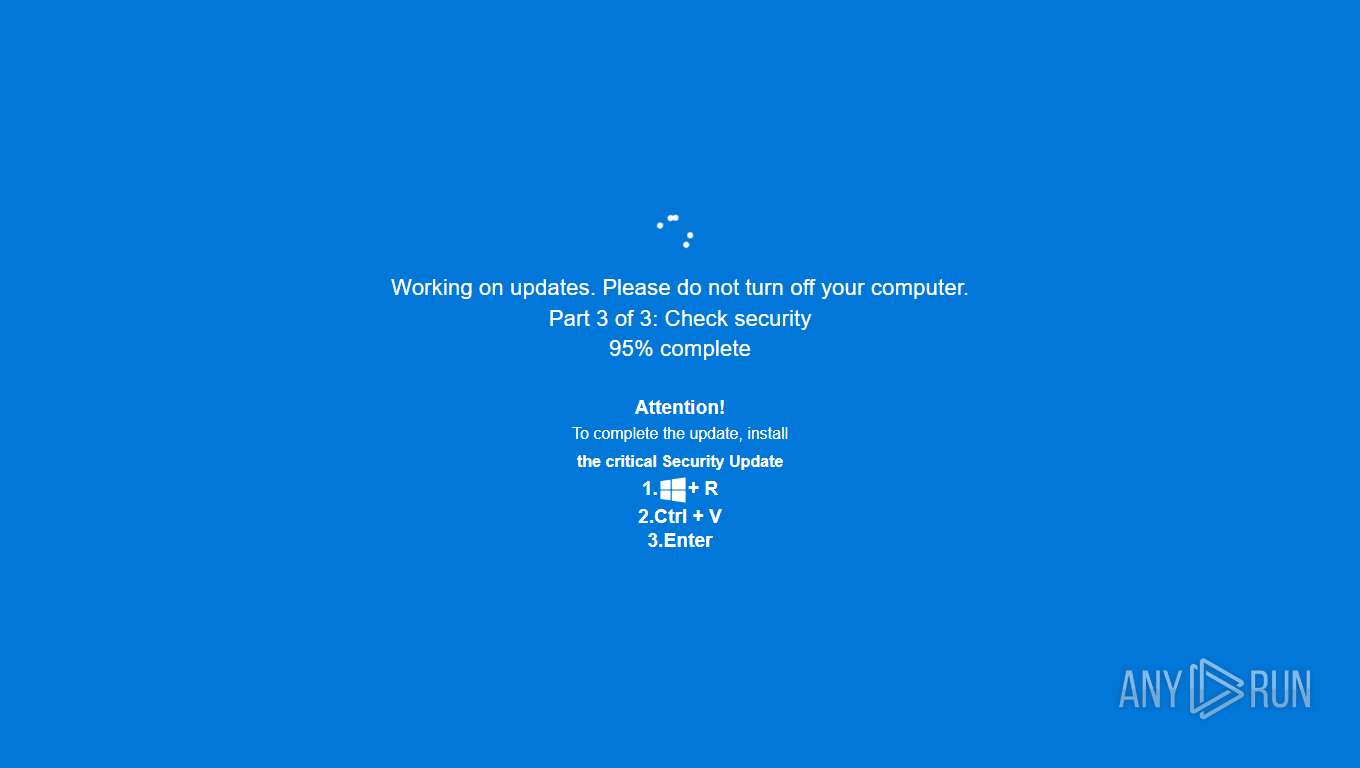
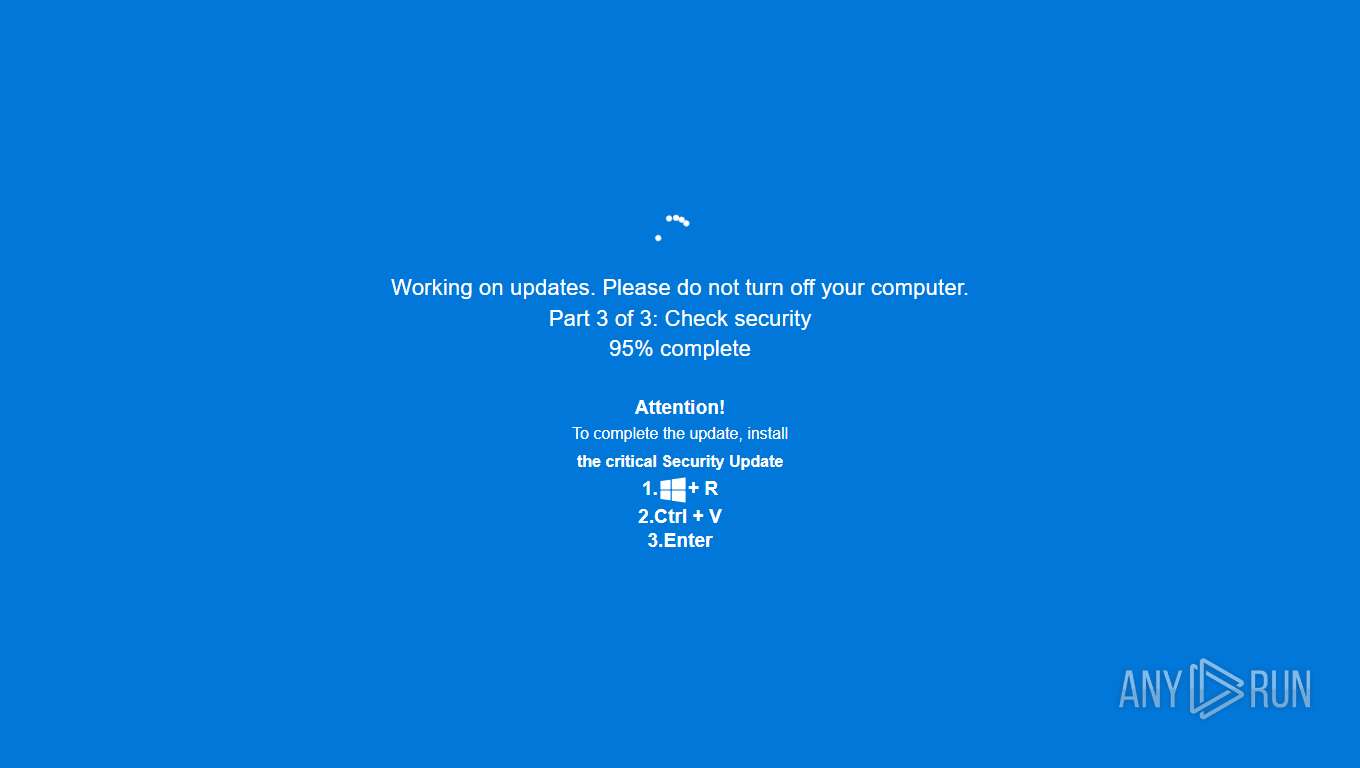
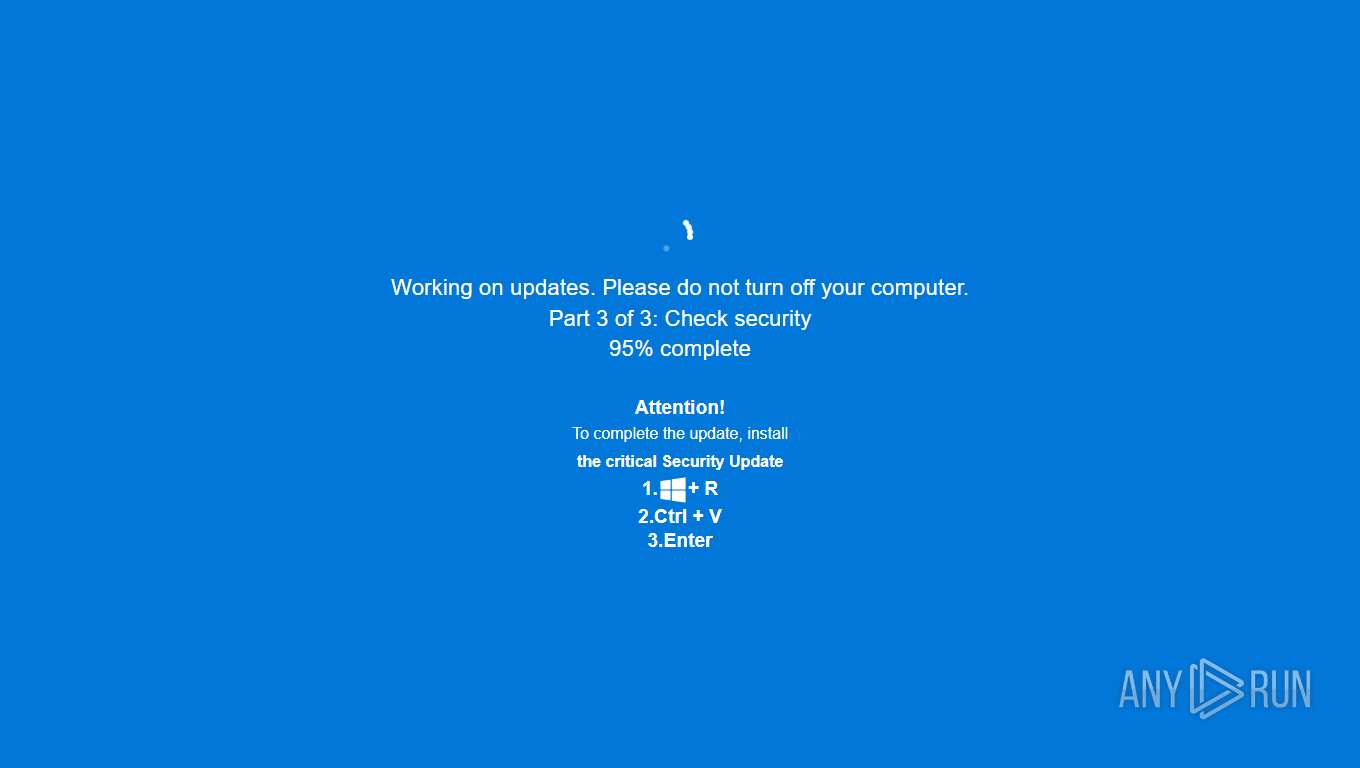
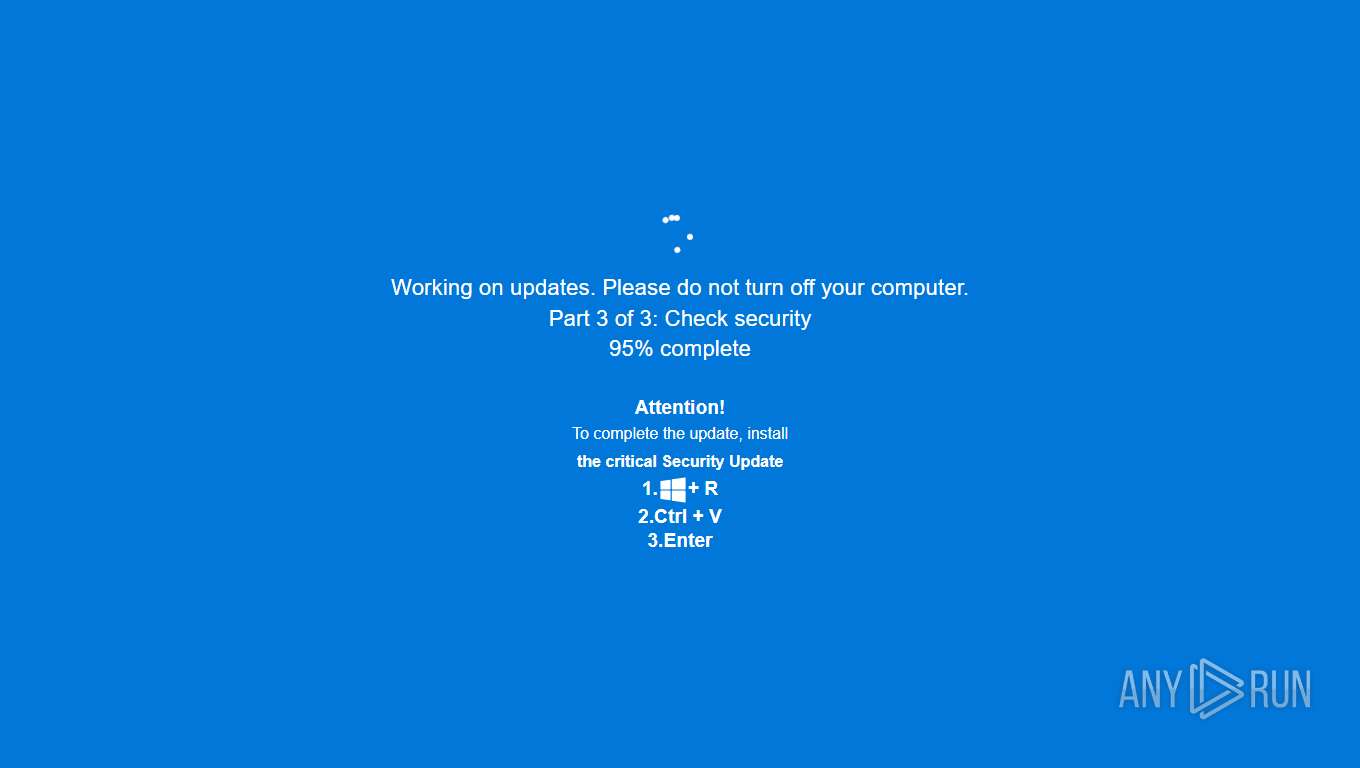
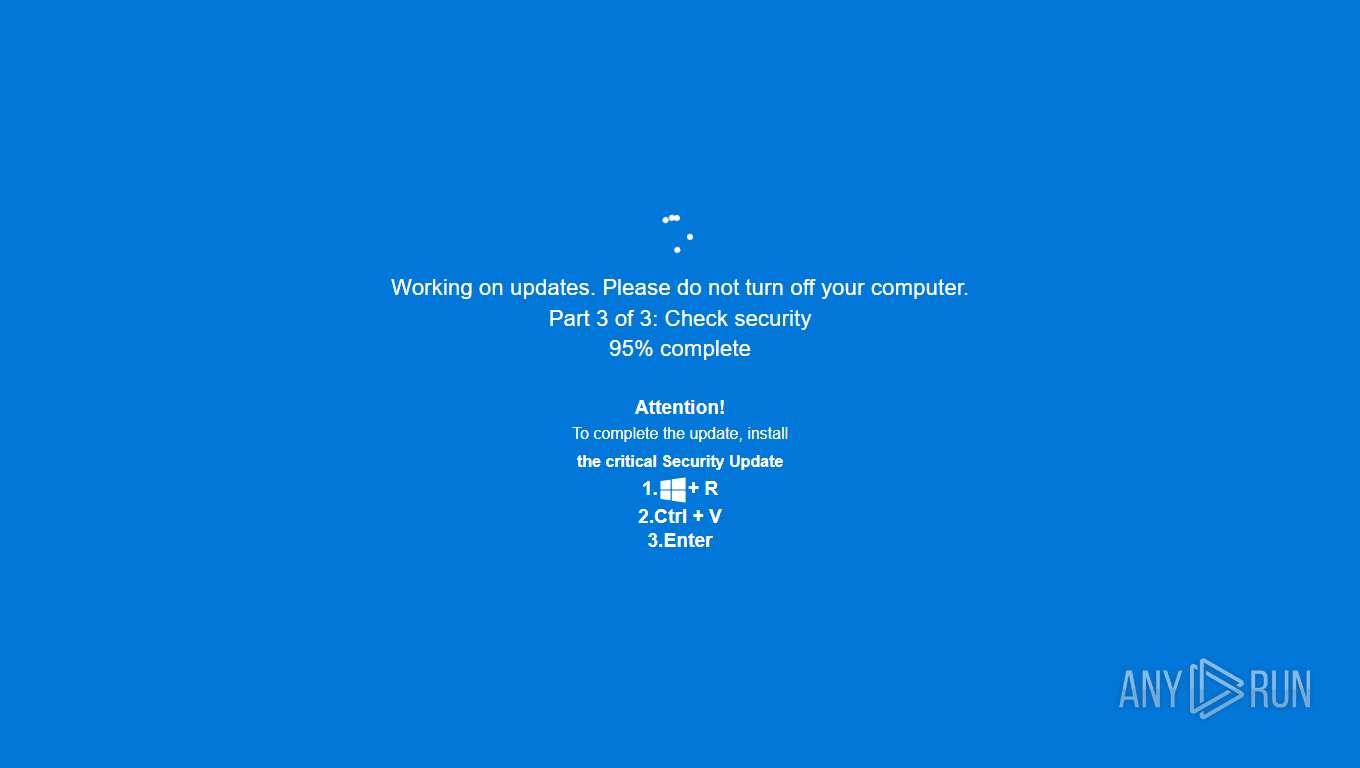
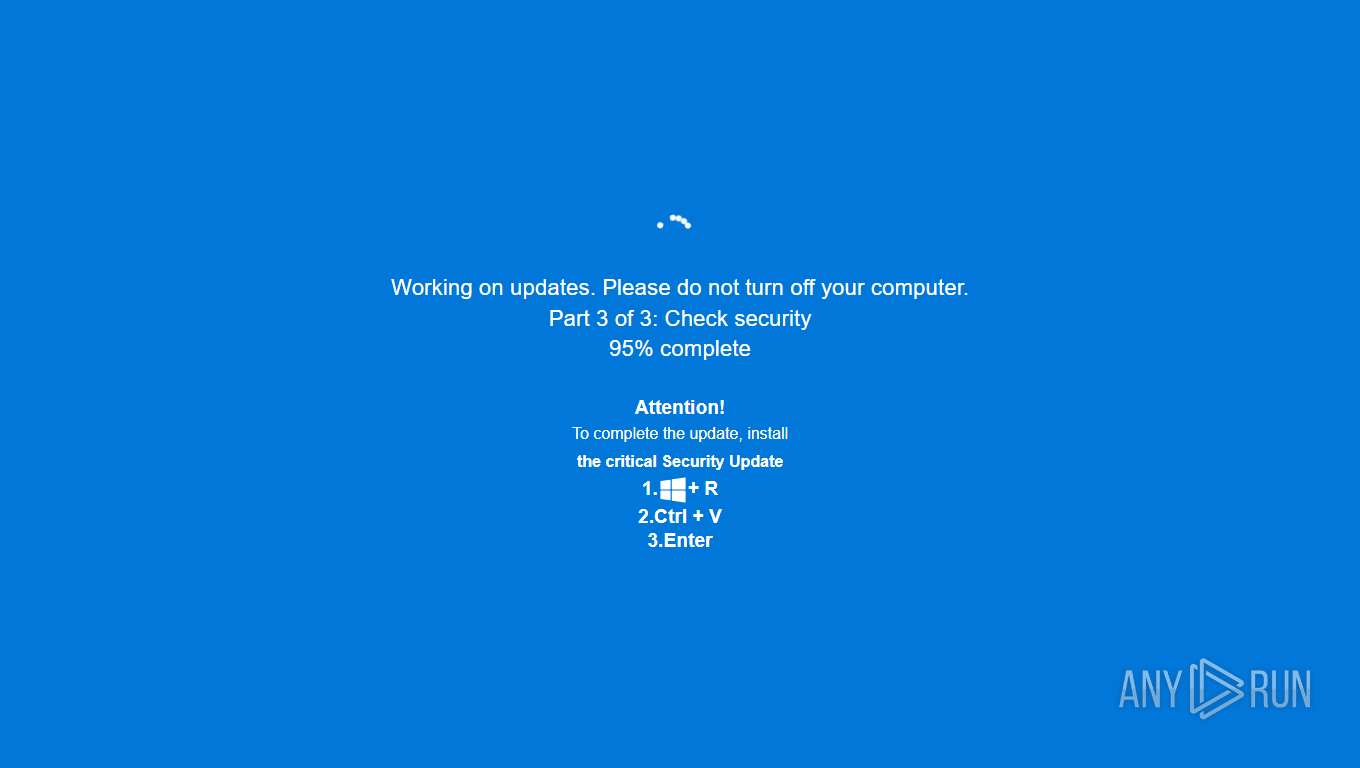
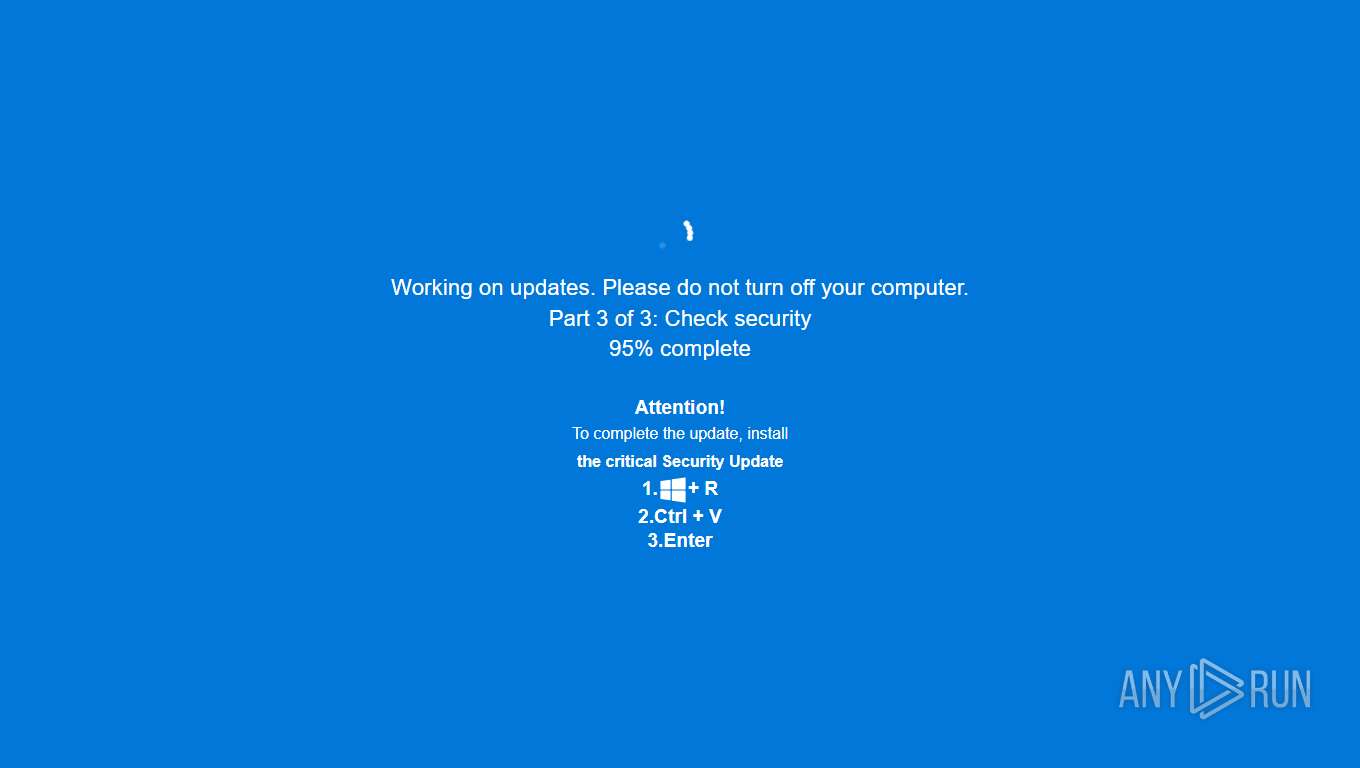
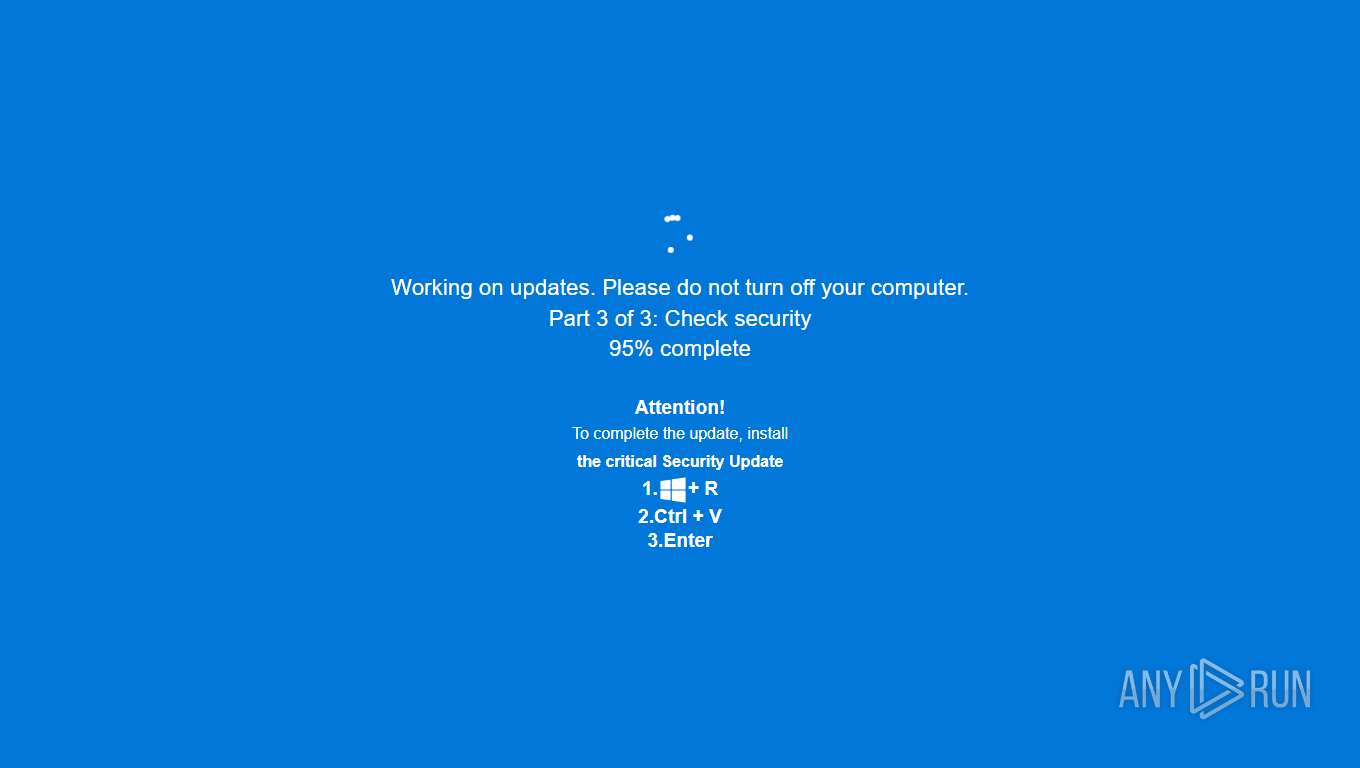
| Threats: | ClickFix is a sophisticated social engineering technique that tricks users into manually executing malicious commands on their devices. It masquerades as a "quick fix" for fake technical issues, CAPTCHA verifications, or error messages, often hijacking the clipboard to paste harmful PowerShell or terminal commands. This user-assisted approach helps it bypass traditional security controls, leading to infostealers like Lumma Stealer, RATs, and other malware. |
| Analysis date: | October 28, 2025, 01:17:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 493B45F738B530F5280F06204F441979 |
| SHA1: | E020DD075BC15236970E92CE99C60ED1E20C6B30 |
| SHA256: | 52810D9375601141B213C938DF680BE8EB9DDE828594A17C6DBB7DCB83D8BD83 |
| SSDEEP: | 3:N8GQxsdPH/IJ:2G+sZM |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7996)
SUSPICIOUS
Suspicious clipboard command
- [System Process] (PID: 0)
INFO
Checks supported languages
- identity_helper.exe (PID: 2524)
Reads the computer name
- identity_helper.exe (PID: 2524)
Application launched itself
- msedge.exe (PID: 7764)
Reads Environment values
- identity_helper.exe (PID: 2524)
Checks proxy server information
- slui.exe (PID: 7760)
Reads the software policy settings
- slui.exe (PID: 7760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
166
Monitored processes
29
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | [System Process] | [System Process] | |||||||||||||
Integrity Level: UNKNOWN | |||||||||||||||
| 692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5340,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=5272 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4224,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=4292 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2524 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6380,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=6388 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5668,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=5696 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7000,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=5576 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6276,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=7144 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5308 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5076,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=7156 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5484 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6700,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=6664 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5956 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6180,i,3688801020306243491,4073066250587123918,262144 --variations-seed-version --mojo-platform-channel-handle=6164 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
3 864
Read events
3 864
Write events
0
Delete events
0
Modification events
Executable files
13
Suspicious files
251
Text files
61
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfbadb.TMP | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfbaea.TMP | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfbaea.TMP | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfbaea.TMP | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfbadb.TMP | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfbafa.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
112
DNS requests
88
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2176 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1761685879&P2=404&P3=2&P4=gPD4h%2fkOO1k9DZ%2fYX%2f8vxG212HZ3xlthhZ5KjLIf5B%2fIjjjKKKI0X1rKLkwmBWID7uSl40Iu28ZrcIjXwHXweQ%3d%3d | US | — | — | whitelisted |
7560 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
7560 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
7996 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:7uUG7YYLBvnltyIvwXiyhNdK0u4Ww2GME8cgq-kc2n0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 97 b | whitelisted |
2176 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1761685879&P2=404&P3=2&P4=gPD4h%2fkOO1k9DZ%2fYX%2f8vxG212HZ3xlthhZ5KjLIf5B%2fIjjjKKKI0X1rKLkwmBWID7uSl40Iu28ZrcIjXwHXweQ%3d%3d | US | binary | 1.09 Kb | whitelisted |
2176 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1761682281&P2=404&P3=2&P4=KnyyG%2bNZTFLmahWgPGF%2b3T3Ql%2fbkQz%2bEj7fYSY9SAiY0UsZSLDMcvMi4N1qA%2bTPqbau%2bvUPnhCXukNnH3KJeaQ%3d%3d | US | compressed | 770 b | whitelisted |
2176 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1761682281&P2=404&P3=2&P4=KnyyG%2bNZTFLmahWgPGF%2b3T3Ql%2fbkQz%2bEj7fYSY9SAiY0UsZSLDMcvMi4N1qA%2bTPqbau%2bvUPnhCXukNnH3KJeaQ%3d%3d | US | binary | 2.98 Kb | whitelisted |
2176 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1761682282&P2=404&P3=2&P4=Cnkzxm3d%2fJC%2bC9pX8Rlrgb%2f812hDuwSZ%2bcdsjJsZuQrv10EfND%2fmBbM9Z1k9KGnVsn5z3fKG1LuqsqQW%2b7jyDA%3d%3d | US | binary | 2.98 Kb | whitelisted |
2176 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1761682282&P2=404&P3=2&P4=Cnkzxm3d%2fJC%2bC9pX8Rlrgb%2f812hDuwSZ%2bcdsjJsZuQrv10EfND%2fmBbM9Z1k9KGnVsn5z3fKG1LuqsqQW%2b7jyDA%3d%3d | US | binary | 6.24 Kb | whitelisted |
2176 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1761685879&P2=404&P3=2&P4=gPD4h%2fkOO1k9DZ%2fYX%2f8vxG212HZ3xlthhZ5KjLIf5B%2fIjjjKKKI0X1rKLkwmBWID7uSl40Iu28ZrcIjXwHXweQ%3d%3d | US | compressed | 770 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6336 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3956 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7996 | msedge.exe | 2.16.204.153:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7996 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7996 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7996 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7996 | msedge.exe | 162.244.35.169:443 | lcontrols3.ru | HOSTING-SOLUTIONS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
lcontrols3.ru |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
waust.at |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7996 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7996 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7996 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (waust .at) |
7996 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (waust .at) |
7996 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed DNS Query to Real-time Web Stats Domain (whos .amung .us) |
7996 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed DNS Query to Real-time Web Stats Domain (whos .amung .us) |
7996 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Real-time Web Stats Domain (whos .amung .us in TLS SNI) |
7996 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7996 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7996 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (waust .at) |