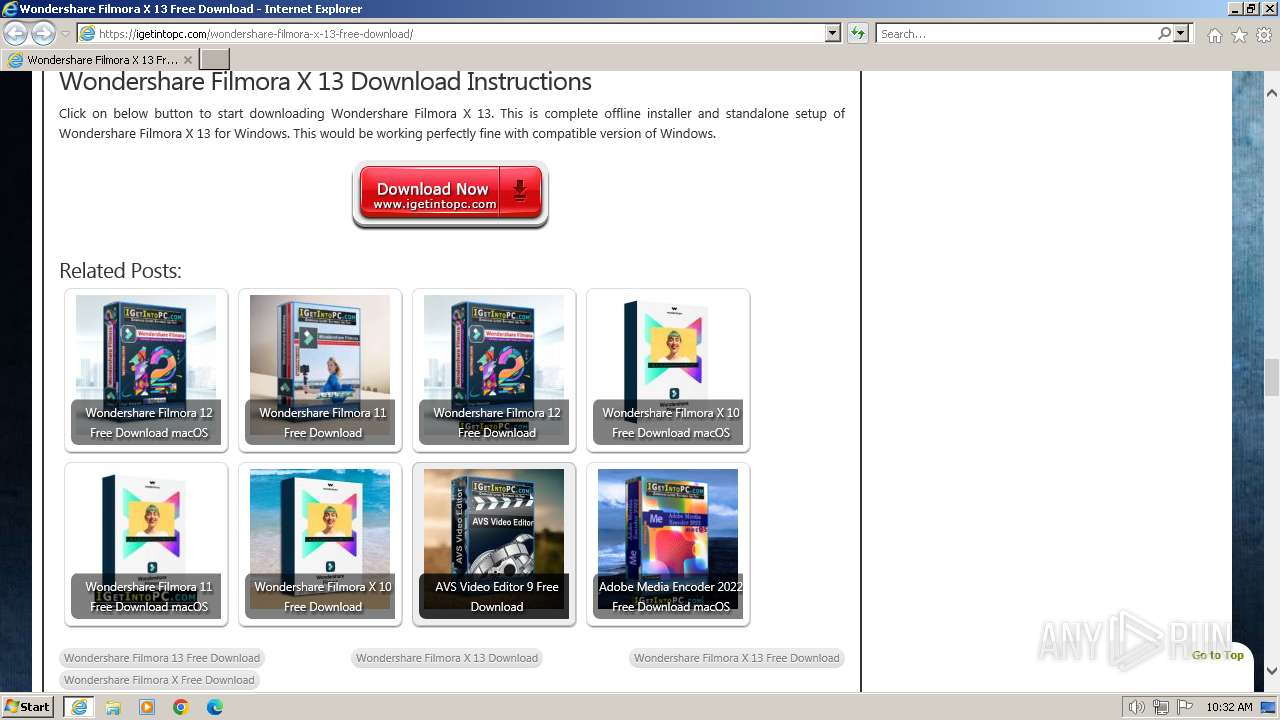
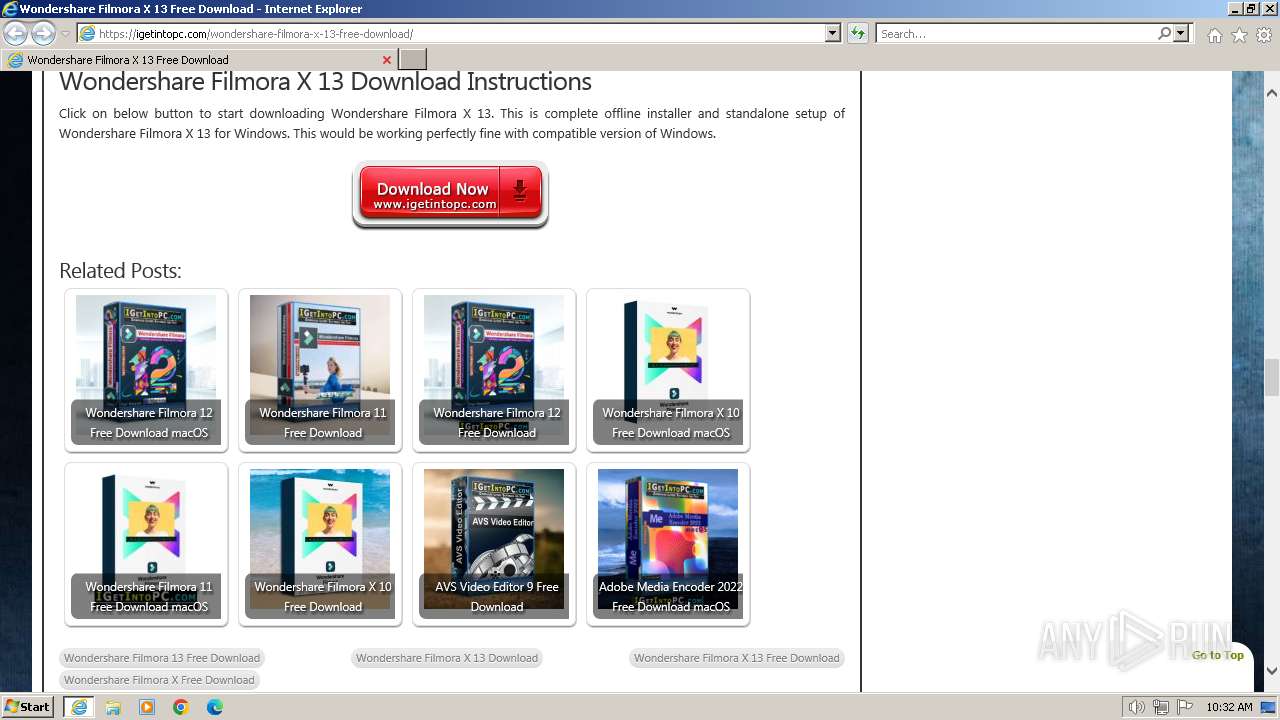
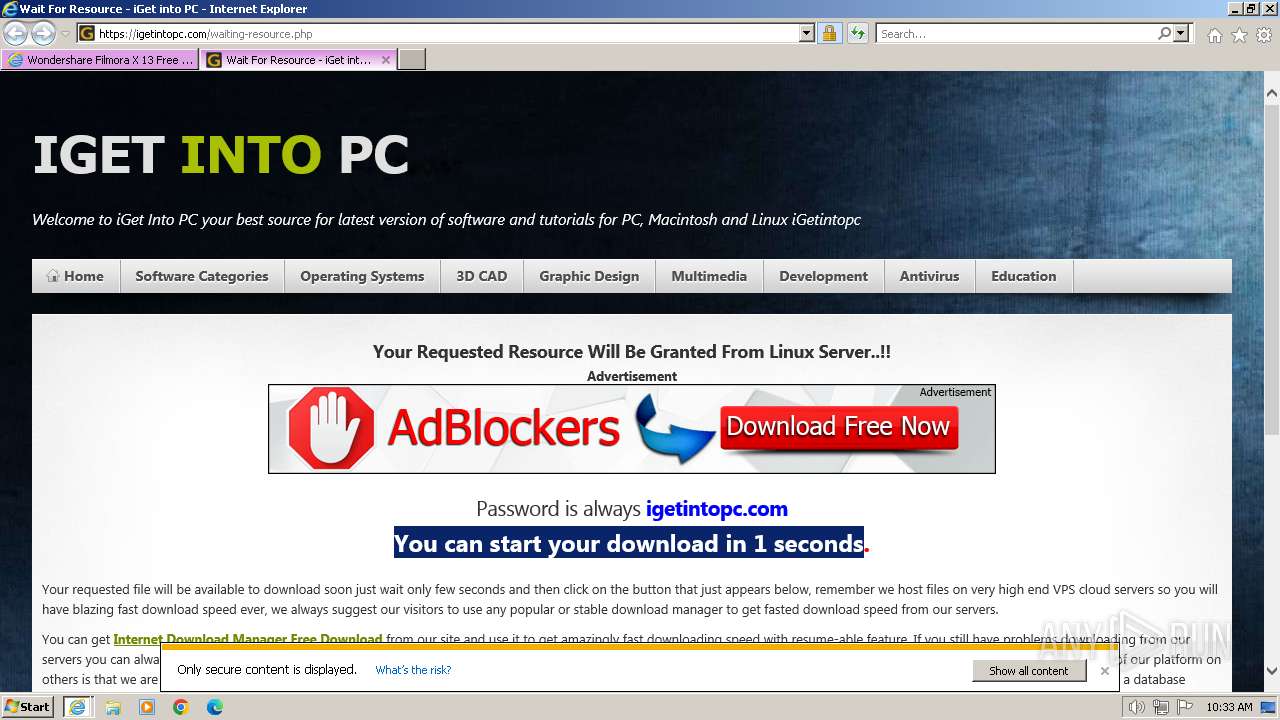
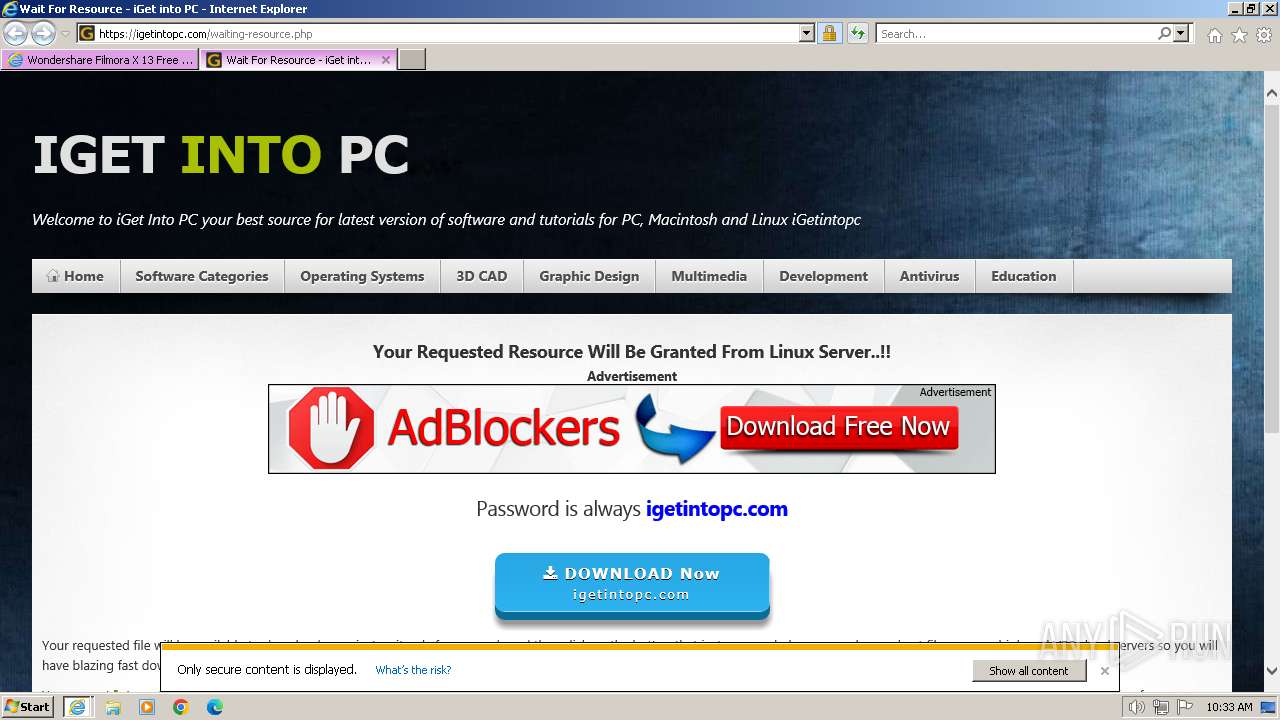
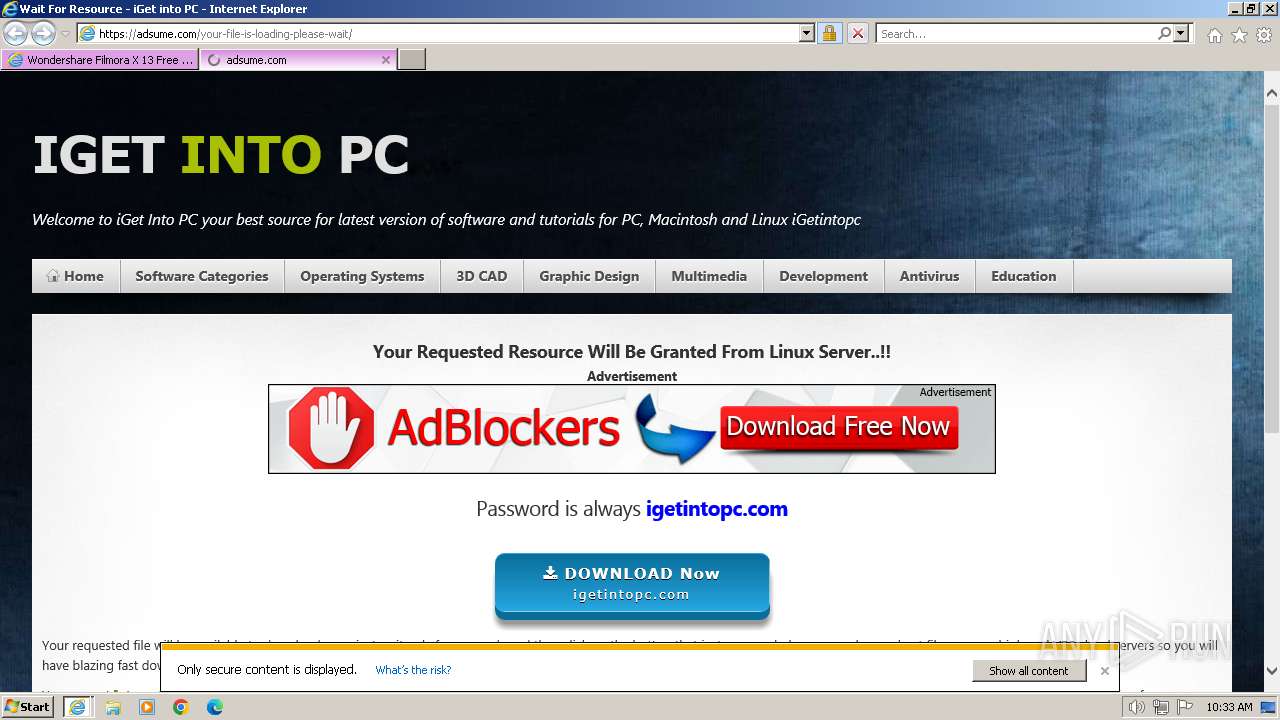
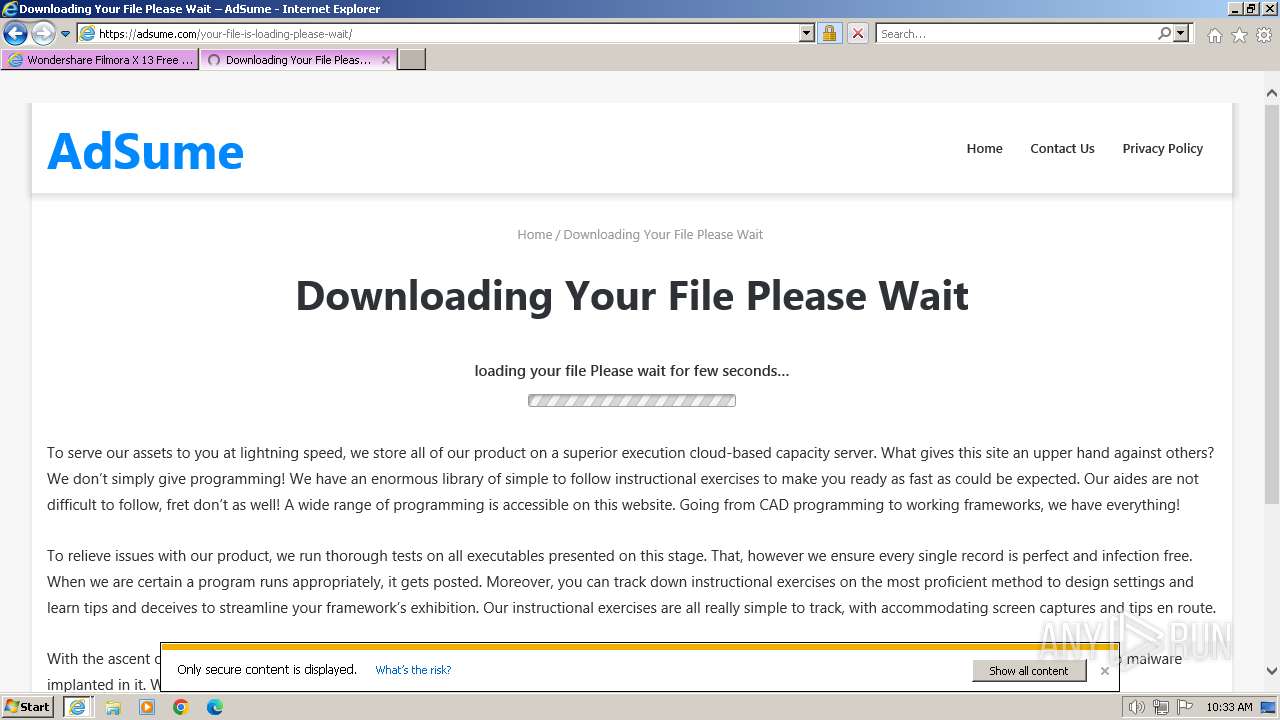
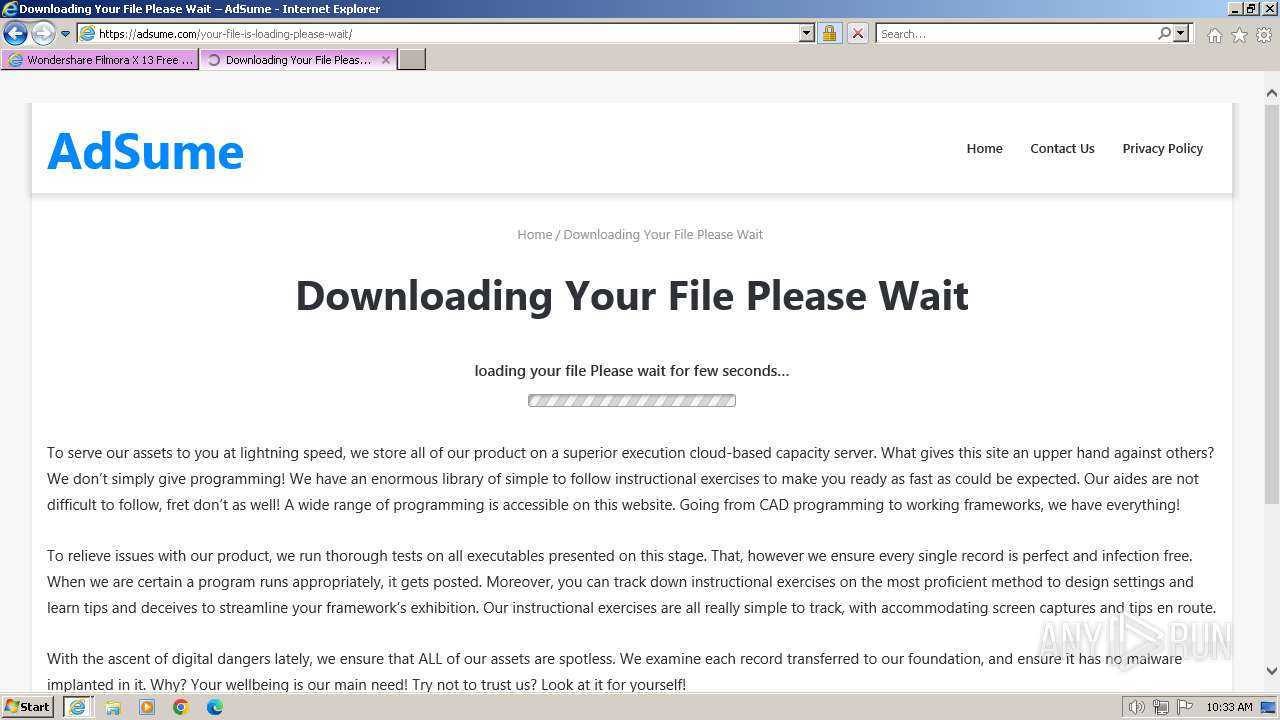
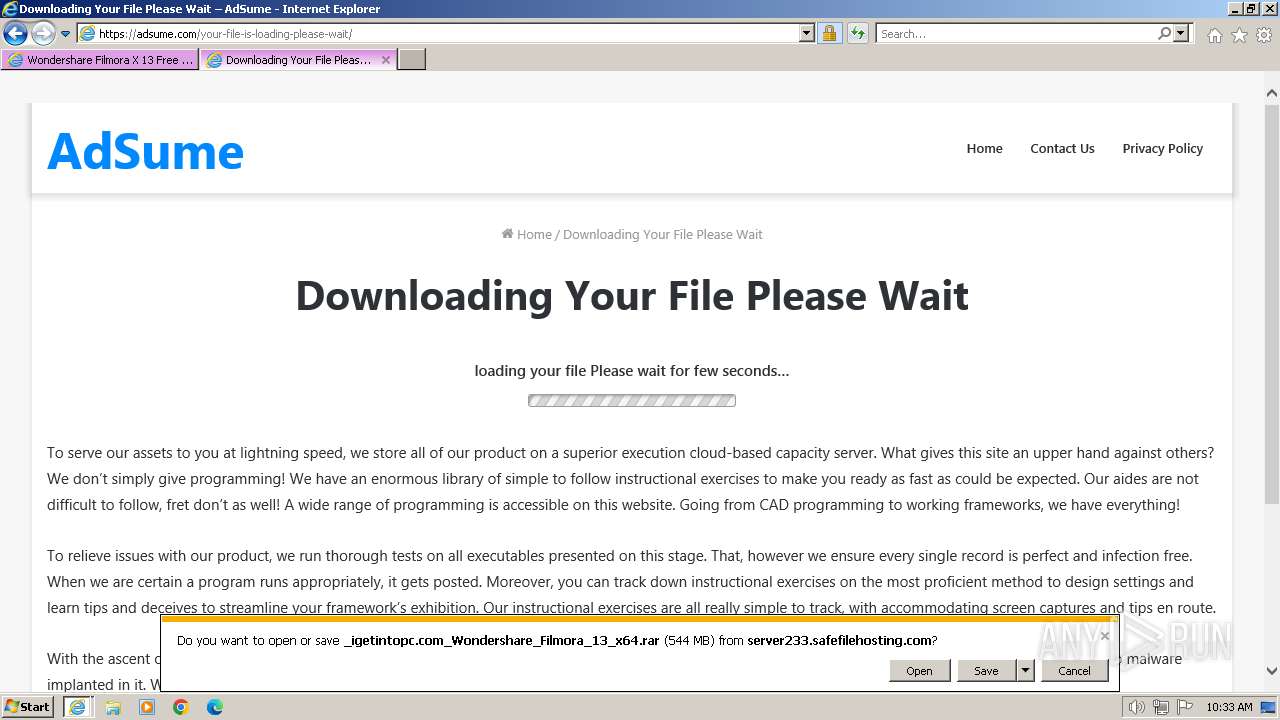
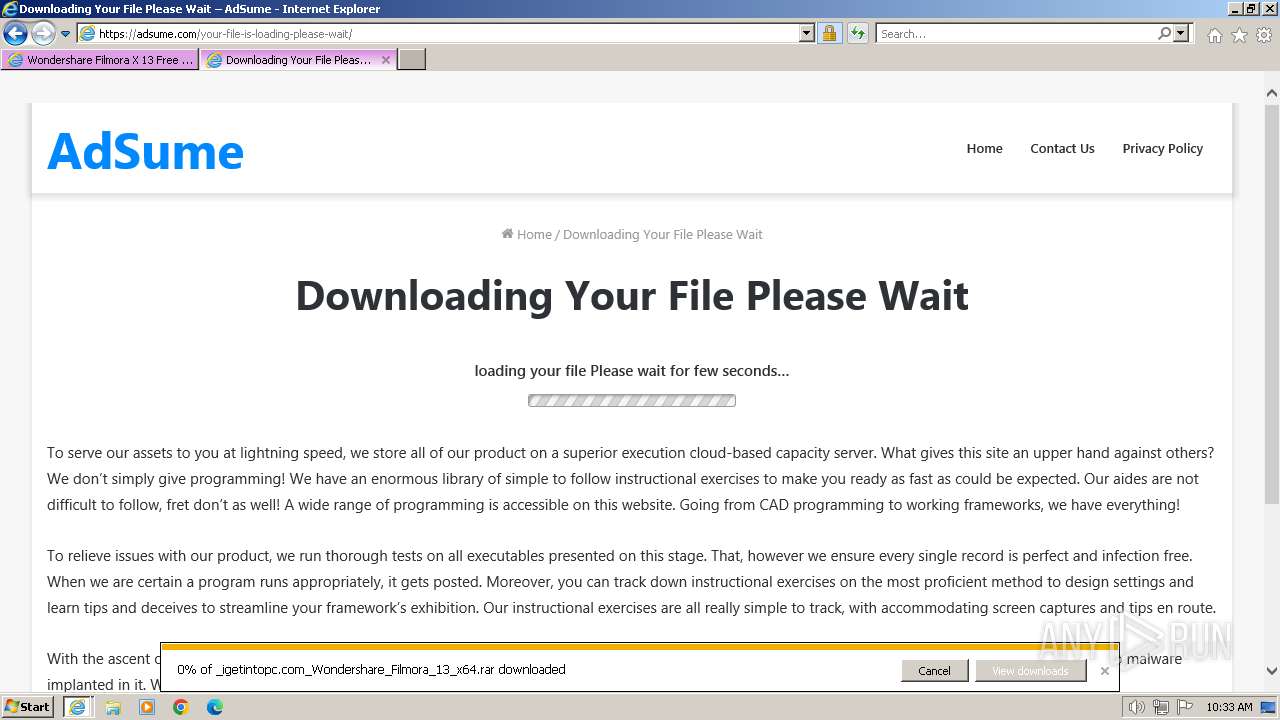
| URL: | https://igetintopc.com/wondershare-filmora-x-13-free-download/ |
| Full analysis: | https://app.any.run/tasks/aced499b-dff7-47c1-9c81-00e4c52028b7 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2024, 10:32:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CABE7D3BF0523E04000E09EF6F0AABCD |
| SHA1: | 7BD0CB008F983296009D1BAD2454C881549ADF8A |
| SHA256: | 527FDC5EF9BB4CC6C59FF682FA2A19C9EEFA07B2286FDF22696A6BF4C4C0A536 |
| SSDEEP: | 3:N8LjLdIE1yfQIUV+BFmn:2LSQb+2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
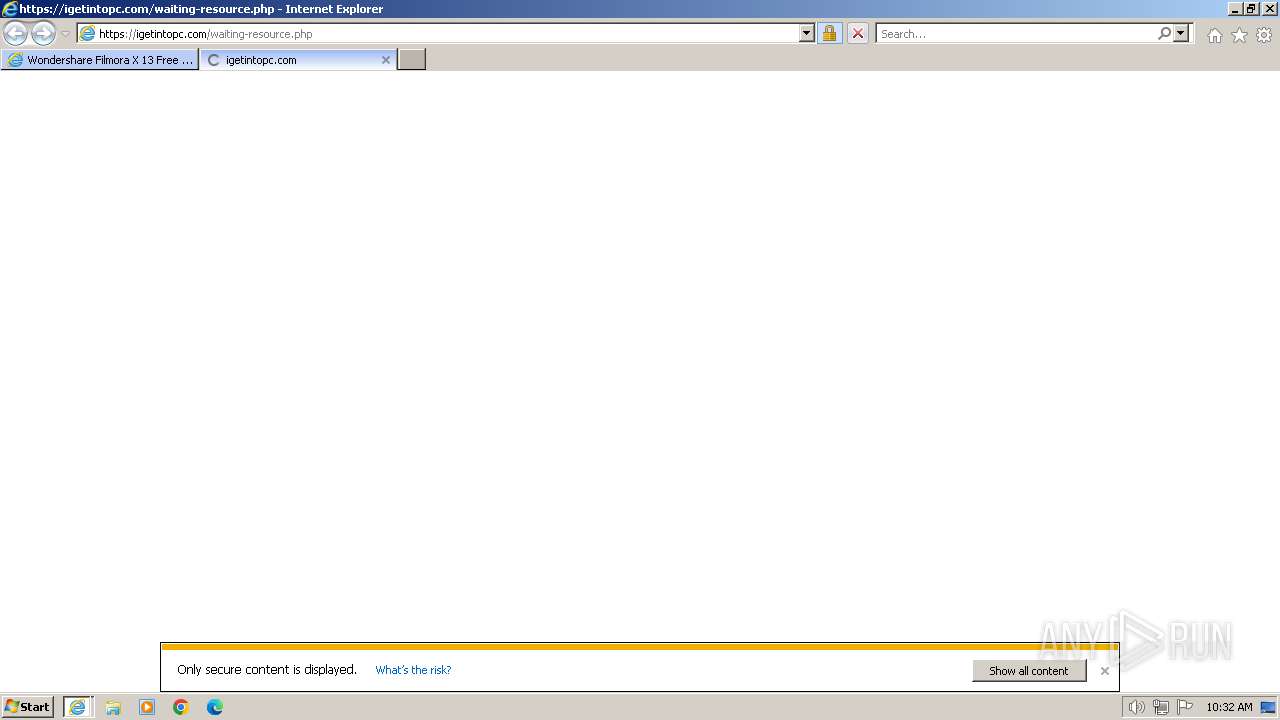
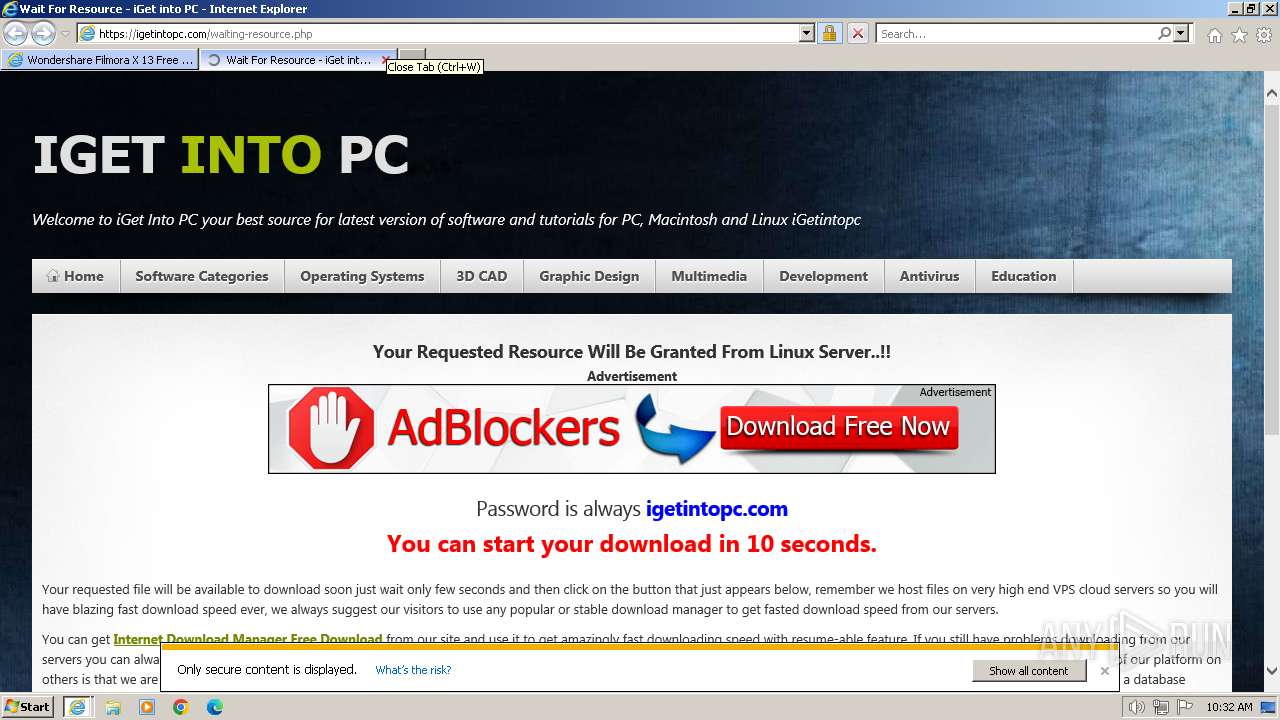
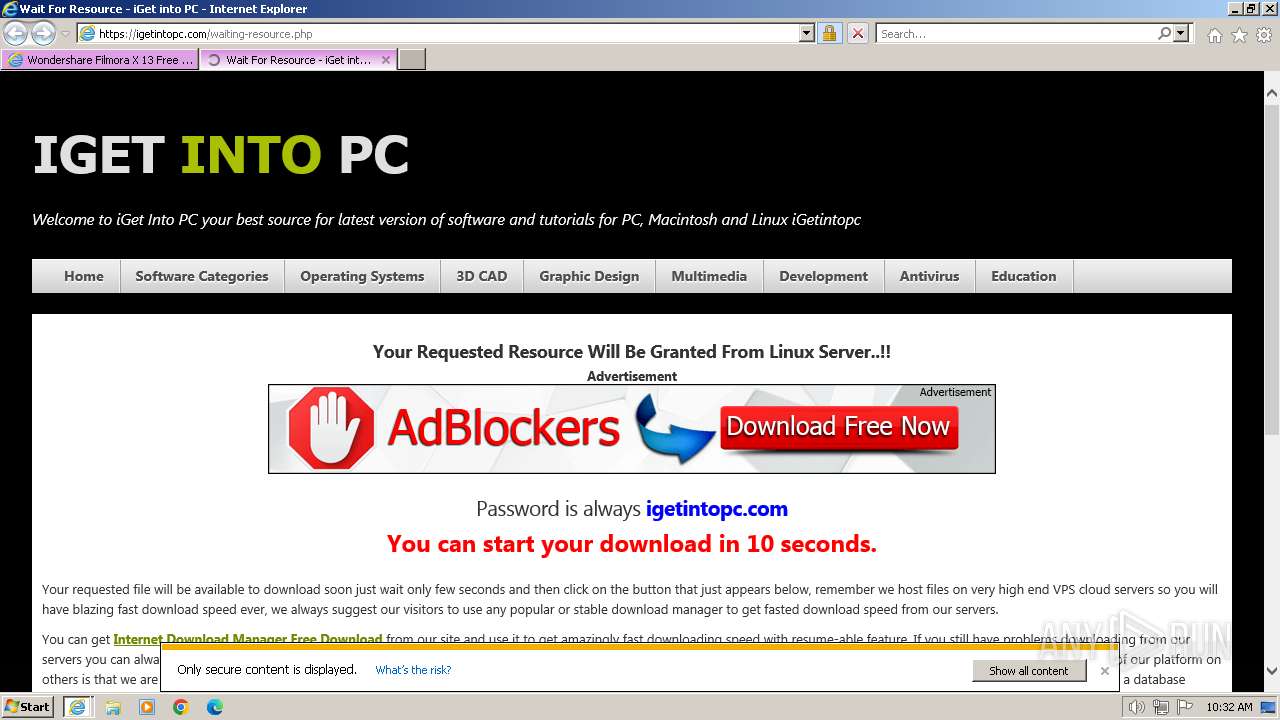
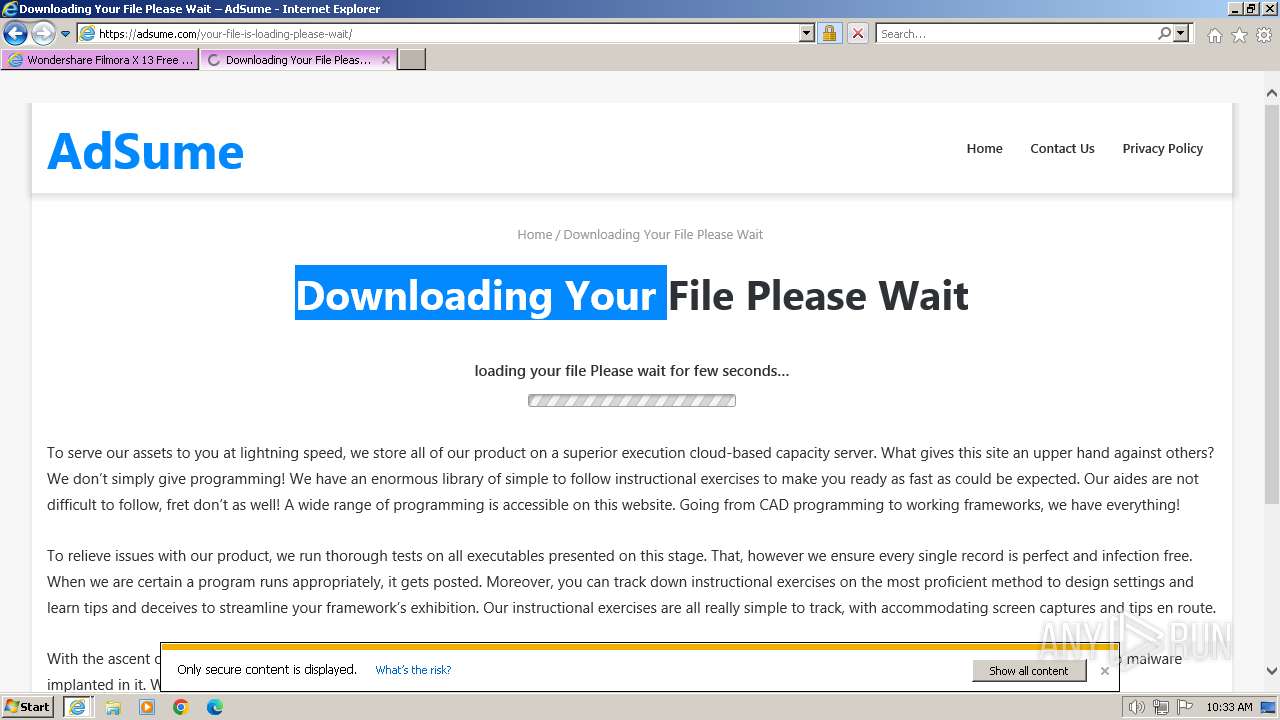
Modifies the phishing filter of IE
- iexplore.exe (PID: 3936)
Application launched itself
- iexplore.exe (PID: 3936)
Connects to unusual port
- iexplore.exe (PID: 492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3936 CREDAT:529692 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3936 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://igetintopc.com/wondershare-filmora-x-13-free-download/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3936 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
34 279
Read events
34 133
Write events
110
Delete events
36
Modification events
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 949158704 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31095876 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31095876 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
46
Text files
162
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:83F64246AAE64DD0B98398DB0D5ECC22 | SHA256:68F39C98FD317489B739A4B97DBFF51D465C857128A9EA248130E48DFBF41E21 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\Wondershare-Filmora-X-Free-Download-macOS-1-140x140[1].jpg | image | |
MD5:3E78A8EE0DDDC1DF34103D7A13D36E84 | SHA256:CF0DA904682A101A4A4A4C0547F0AEDCA48DA7E41FB25016373E1B86A59D41EC | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:654D44DADF325EB8D4A7A1B64B9D3688 | SHA256:FA68B7C2DD040B38EE531D237FFCF21A6008EBE241AD9719DEDBAABBA000FFB9 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\wondershare-filmora-x-13-free-download[1].htm | html | |
MD5:9BDF6E4E314488CBFDDDEFA2BA31B644 | SHA256:E63BF8D8C4D84AD6CE3A3F82CB490EA1A1CEB6E640D90CB53092CBD00809CCF6 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:105EFD49E3D9BA74950C93EBD14B1EA8 | SHA256:F948F6F6EF168F8EFFD367E023CB083DA81B5835FCC668222B1464EE181A71C8 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Wondershare-Filmora-11-Free-Download-1-140x140[1].jpg | image | |
MD5:500291A6470F56C7B751E211B0DC5B21 | SHA256:1B7481874795605D66E33C8D393190637E0F3807706CCF9EFE28D63A66100301 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\autoptimize_60f43fdabb6d51e2c7e1d88b60e7231b[1].css | text | |
MD5:E8A2048592882016831C64A4F511BDB7 | SHA256:2AF7D434294FCCF7FC22EE5125EB14E321BEF48FE61EB0D7F78D1042F5A497AF | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Wondershare-Filmora-X-13-Free-Download-1-1[1].jpg | image | |
MD5:746C958E1E81CA4ECC8D94DC2342E95D | SHA256:69F1BDB8D60B9DA4A488CF681748F240789421A7F7A39A4E18087E2F7C6856C6 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Wondershare-Filmora-X-13-Free-Download-1[1].jpg | image | |
MD5:9C3DCD5D59A9F1DEDDF27B11888093C1 | SHA256:42D0A6DA6546AB99AAD854E2526CB733DCBFE89180F6387CE93D4CED840CF0F6 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\jquery.min[1].js | text | |
MD5:826EB77E86B02AB7724FE3D0141FF87C | SHA256:CB6F2D32C49D1C2B25E9FFC9AAAFA3F83075346C01BCD4AE6EB187392A4292CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
132
DNS requests
54
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
3964 | iexplore.exe | GET | 304 | 178.79.238.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?92967c53a8c0ec29 | unknown | — | — | unknown |
3964 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.49 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | binary | 1.42 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
3964 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 108.138.2.107:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 184.24.77.81:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRGrTsrU7INT6W5t2T2Mc7ErA%3D%3D | unknown | binary | 503 b | unknown |
3964 | iexplore.exe | GET | 200 | 184.24.77.81:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRGrTsrU7INT6W5t2T2Mc7ErA%3D%3D | unknown | binary | 503 b | unknown |
3964 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHUeP1PjGFkz6V8I7O6tApc%3D | unknown | binary | 1.41 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3964 | iexplore.exe | 172.67.201.115:443 | igetintopc.com | CLOUDFLARENET | US | unknown |
3964 | iexplore.exe | 178.79.238.128:80 | ctldl.windowsupdate.com | LLNW | FR | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3964 | iexplore.exe | 172.217.16.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3964 | iexplore.exe | 172.217.18.8:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
3964 | iexplore.exe | 142.250.184.194:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
3964 | iexplore.exe | 5.255.255.70:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
igetintopc.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
d18t35yyry2k49.cloudfront.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
yandex.ru |
| whitelisted |
d3q33rbmdkxzj.cloudfront.net |
| whitelisted |
grunoaph.net |
| unknown |
images.dmca.com |
| whitelisted |