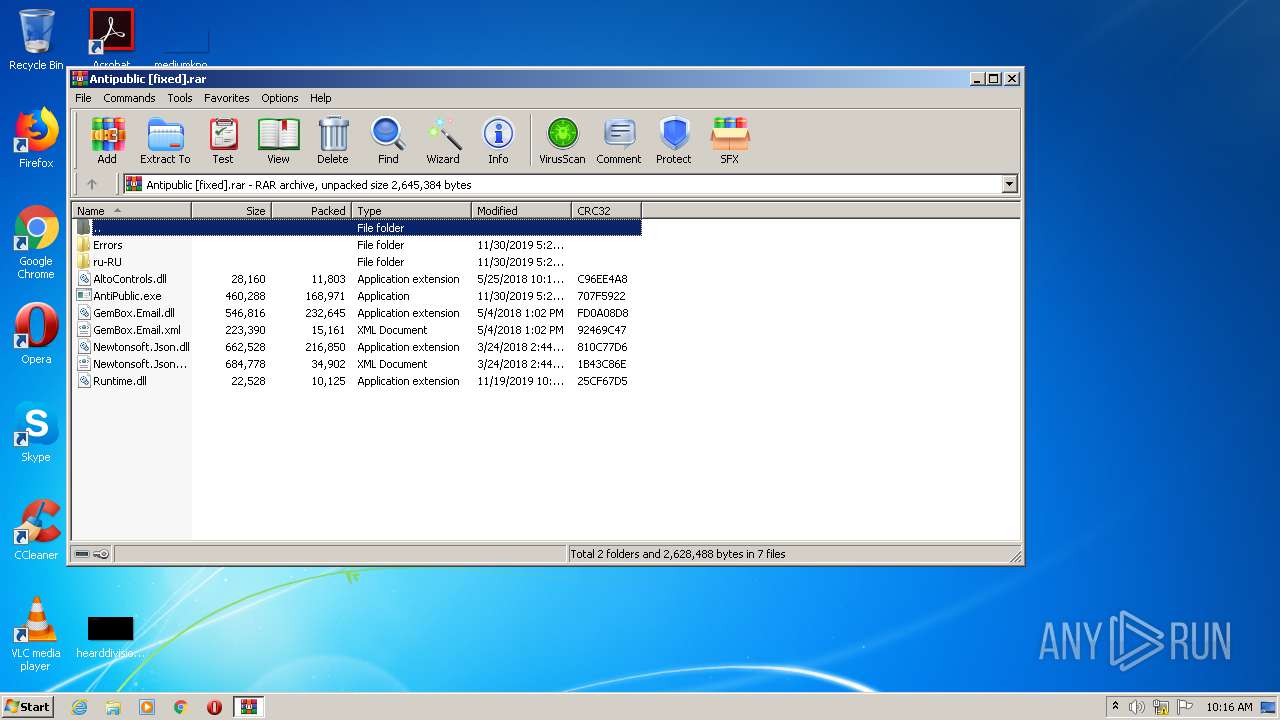
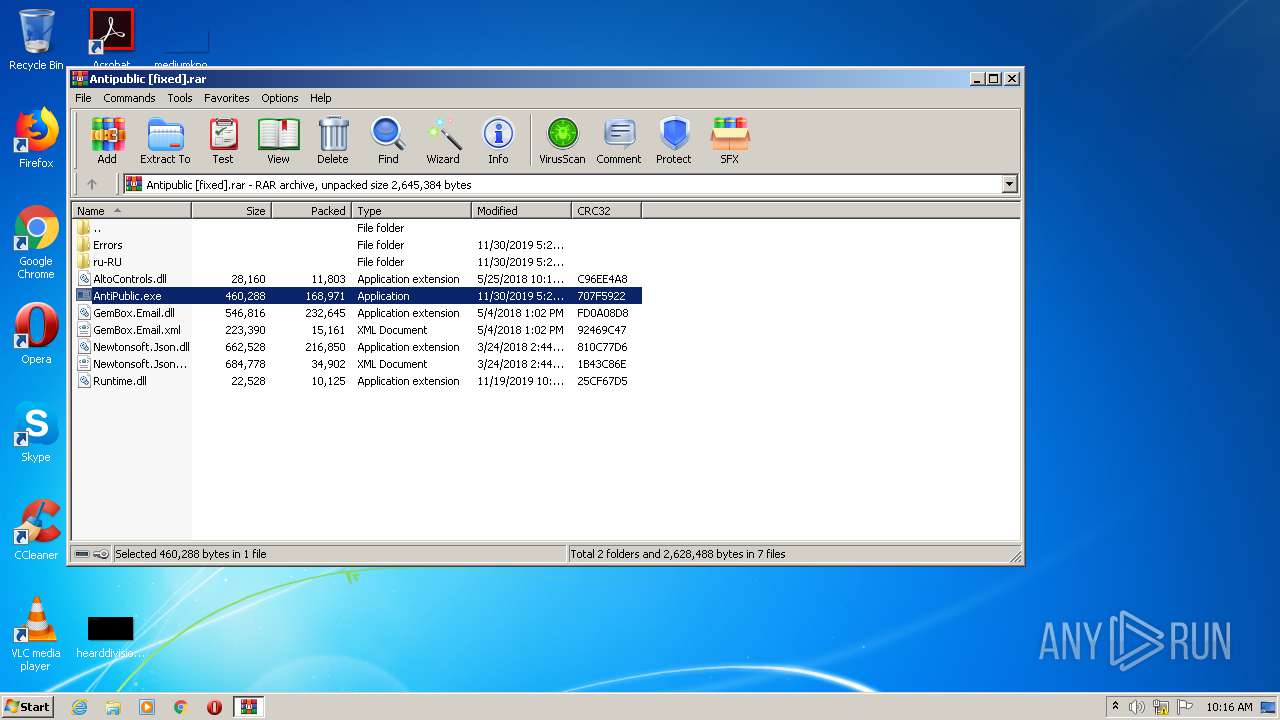
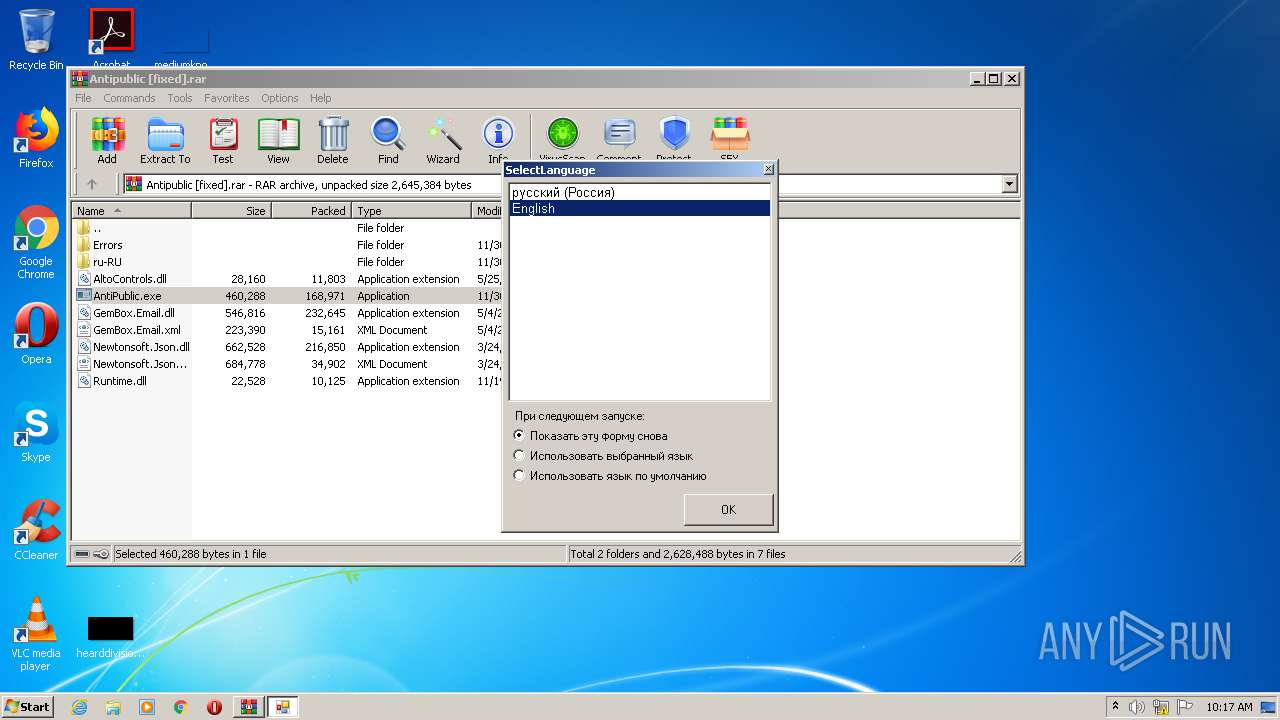
| File name: | Antipublic [fixed].rar |
| Full analysis: | https://app.any.run/tasks/8d9f9164-214f-4069-a9b7-b897b06e7e60 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 09:16:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 681DAAD66025BFF398B5ADAE46D3F22E |
| SHA1: | 0AD3EFC174C84BCEAACA88921FA8DC716F31A7C9 |
| SHA256: | 5261C1E632FA3F5E9F2A6331F5258B950741238BD9DCB77D1C2F56BA6A7C810B |
| SSDEEP: | 12288:rLnjBAL3K8lW6lC33mK7Ko1YpVzmoGUdKLalb5G7b6JcQoKO3nQei3O8m:rLnlArK8s6lC339KowMoGTLs7m36m |
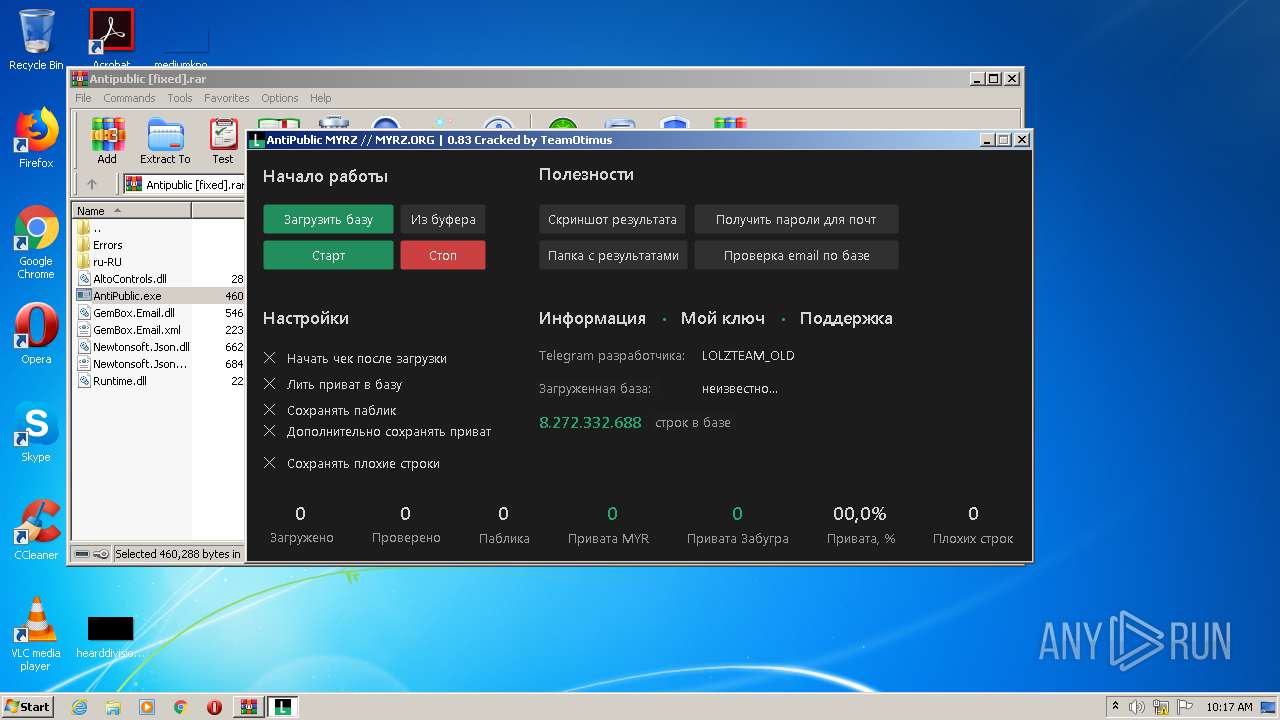
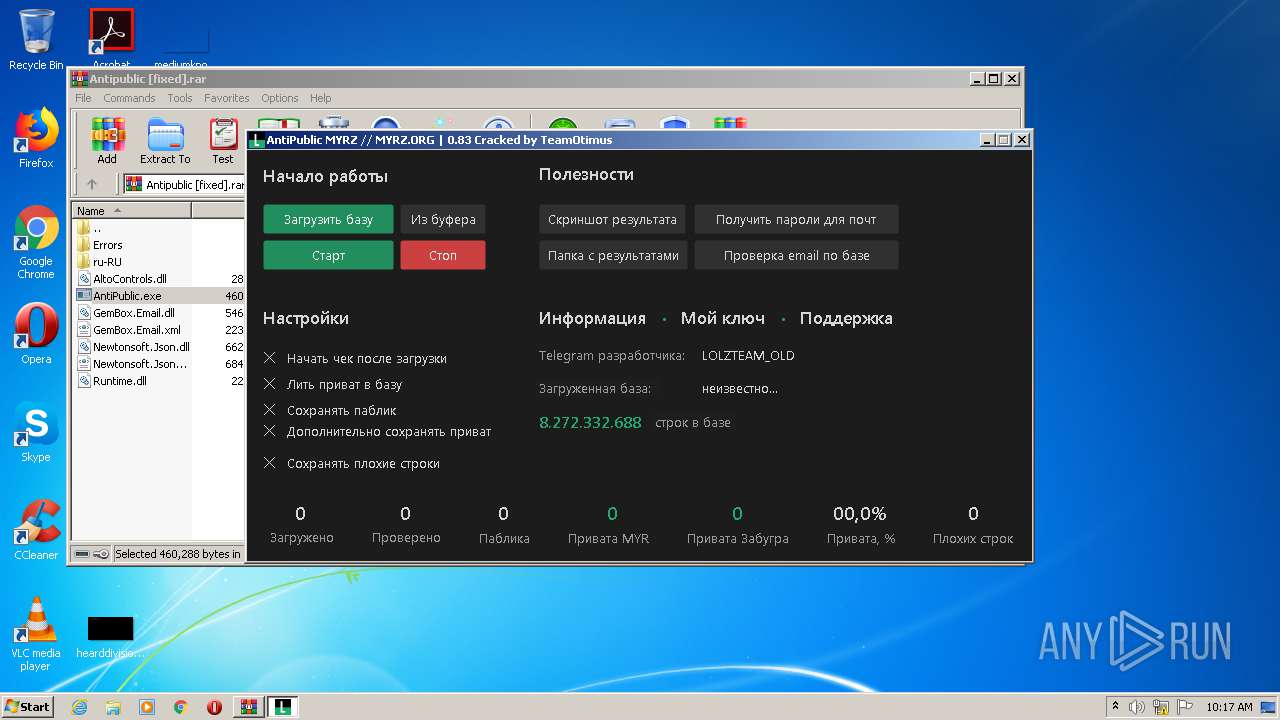
MALICIOUS
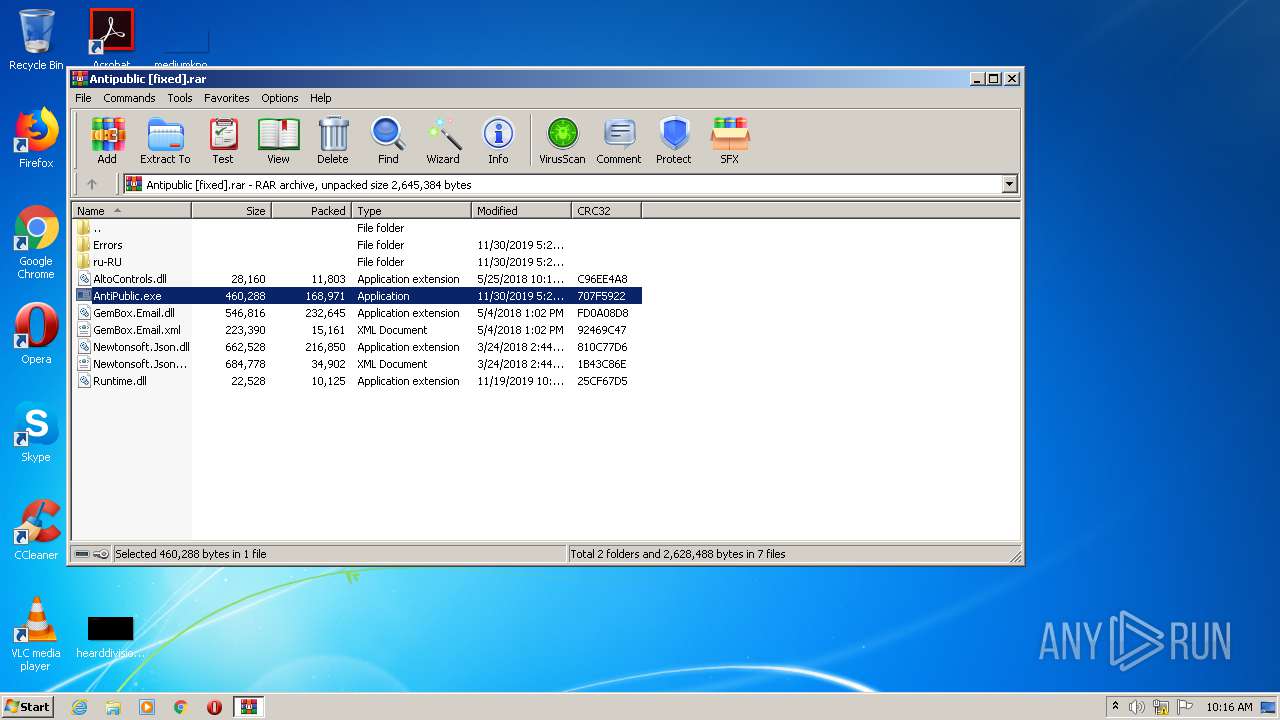
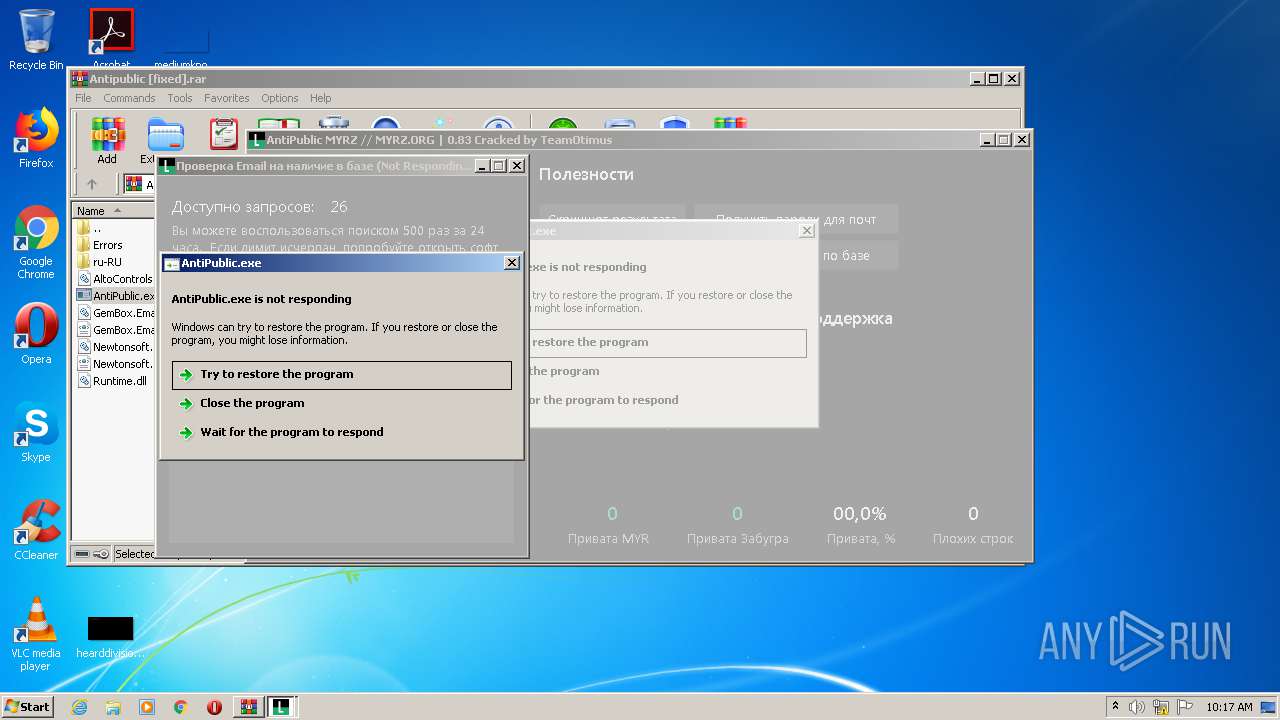
Application was dropped or rewritten from another process
- AntiPublic.exe (PID: 2676)
- AntiPublic.exe (PID: 2792)
Loads dropped or rewritten executable
- AntiPublic.exe (PID: 2676)
- AntiPublic.exe (PID: 2792)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2136)
- AntiPublic.exe (PID: 2676)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
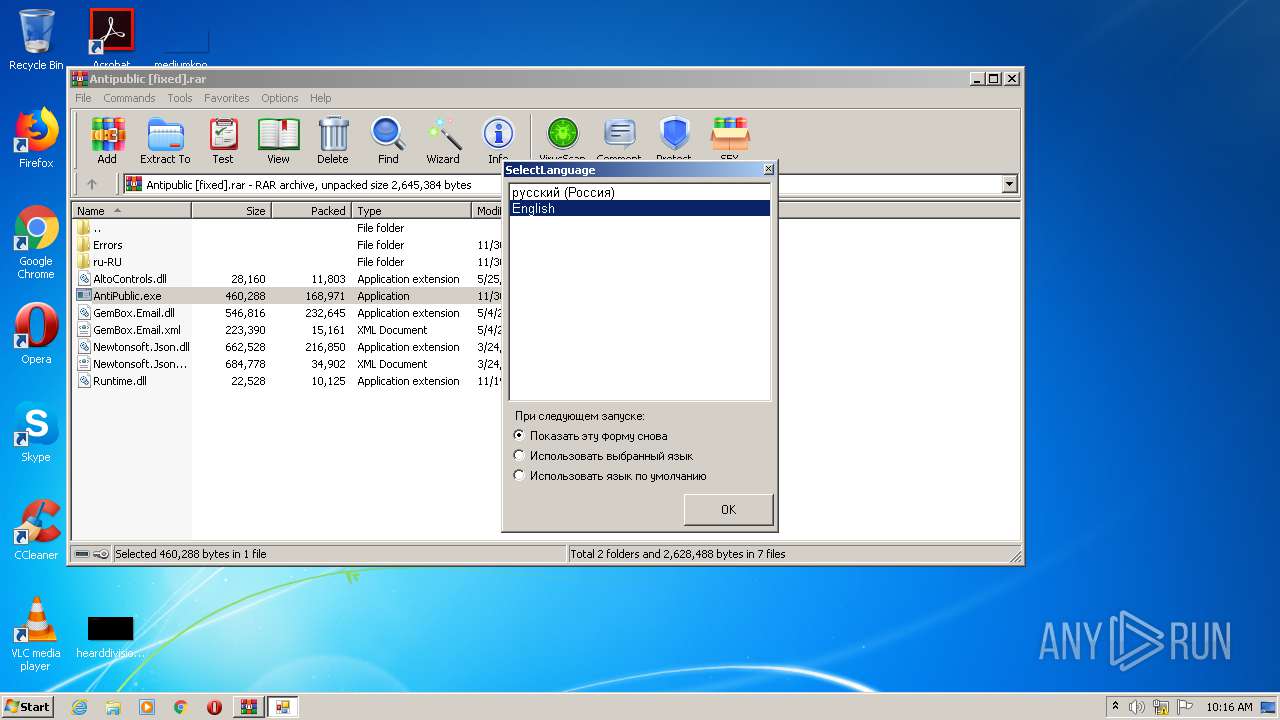
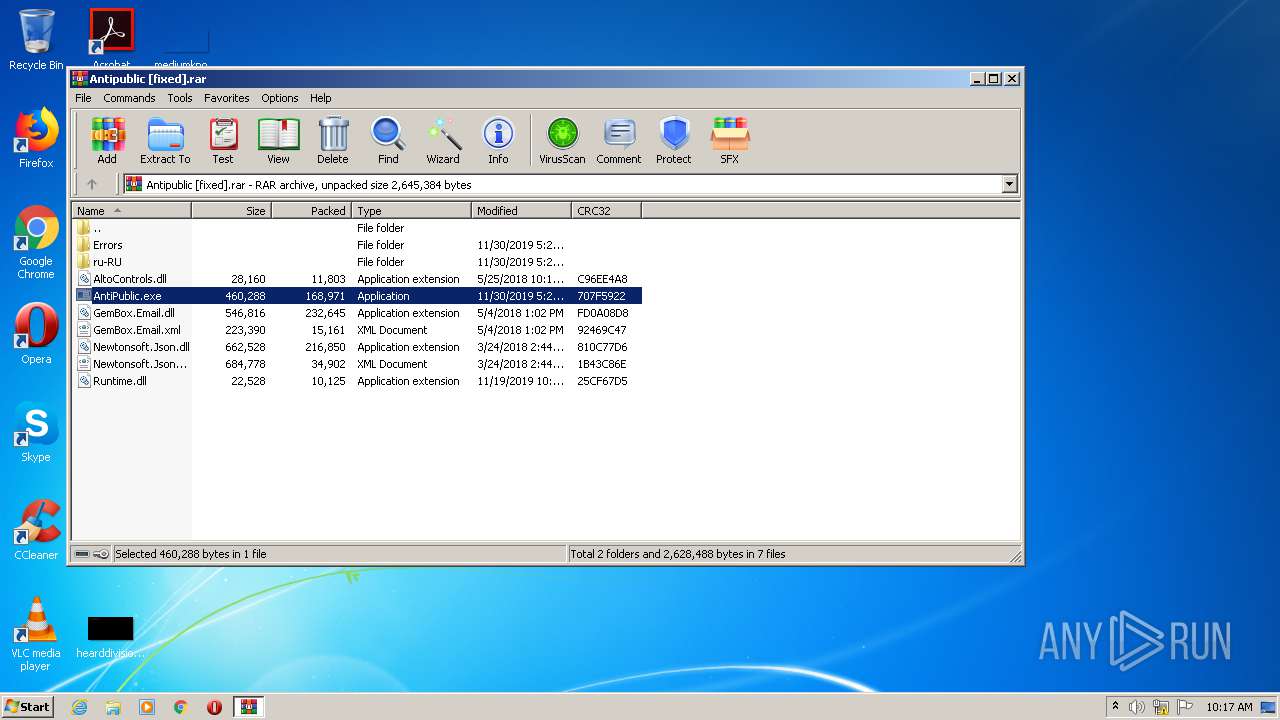
| 2136 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Antipublic [fixed].rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2676 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.24164\AntiPublic.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.24164\AntiPublic.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3489660927 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2792 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.27716\AntiPublic.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.27716\AntiPublic.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
524
Read events
490
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Antipublic [fixed].rar | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
| (PID) Process: | (2676) AntiPublic.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AntiPublic_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
13
Suspicious files
0
Text files
6
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.24164\Newtonsoft.Json.dll | executable | |
MD5:5AFDA7C7D4F7085E744C2E7599279DB3 | SHA256:F58C374FFCAAE4E36D740D90FBF7FE70D0ABB7328CD9AF3A0A7B70803E994BA4 | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.24164\GemBox.Email.dll | executable | |
MD5:3657F2F4783FC9D9505B8C137AABA060 | SHA256:A5899F6D6C6F3944DEC97CA32B4A915606EE7154ABCEC29020AF3C21AE9B3274 | |||
| 2676 | AntiPublic.exe | C:\Users\admin\AppData\Local\IsolatedStorage\hckdfqlk.jad\e33romm5.gqv\Url.gx4sxsygk0h40swph03hr3hqym5cb4tj\Url.gx4sxsygk0h40swph03hr3hqym5cb4tj\identity.dat | pi2 | |
MD5:— | SHA256:— | |||
| 2676 | AntiPublic.exe | C:\Users\admin\AppData\Local\IsolatedStorage\hckdfqlk.jad\e33romm5.gqv\Url.gx4sxsygk0h40swph03hr3hqym5cb4tj\identity.dat | pi2 | |
MD5:— | SHA256:— | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.24164\GemBox.Email.xml | xml | |
MD5:8655FDE8790C59D030ADEB2785272E11 | SHA256:50E6A3EFB27C484E370F35BDD1441520AE9C5642277E0B62CB3B42AE7D6A1146 | |||
| 2676 | AntiPublic.exe | C:\Users\admin\AppData\Local\IsolatedStorage\hckdfqlk.jad\e33romm5.gqv\Url.gx4sxsygk0h40swph03hr3hqym5cb4tj\Url.gx4sxsygk0h40swph03hr3hqym5cb4tj\Files\CultureSettings.xml | xml | |
MD5:388E09773F560969256C631FAAE2D2A2 | SHA256:EC795E4E751F3BB0C56880078C3C25B5F730D8325BF6B5A9C5EFB8E5B0526EFF | |||
| 2676 | AntiPublic.exe | C:\Users\admin\AppData\Local\IsolatedStorage\hckdfqlk.jad\e33romm5.gqv\Url.gx4sxsygk0h40swph03hr3hqym5cb4tj\info.dat | abr | |
MD5:22589A024E2B52B44365C84BF9053EAB | SHA256:335D953107E146619C0BF52F8D650C2CDBB5DAF1E1278F51437D96215AC74DB9 | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.27716\GemBox.Email.dll | executable | |
MD5:3657F2F4783FC9D9505B8C137AABA060 | SHA256:A5899F6D6C6F3944DEC97CA32B4A915606EE7154ABCEC29020AF3C21AE9B3274 | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.24164\Runtime.dll | executable | |
MD5:C5A8489BA2BFE112007D2356C54E25B6 | SHA256:0AF8E3865CA005A005A69C55F4F691B2D9504C796755A0BCEE73159F719996FD | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2136.27716\Newtonsoft.Json.dll | executable | |
MD5:5AFDA7C7D4F7085E744C2E7599279DB3 | SHA256:F58C374FFCAAE4E36D740D90FBF7FE70D0ABB7328CD9AF3A0A7B70803E994BA4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
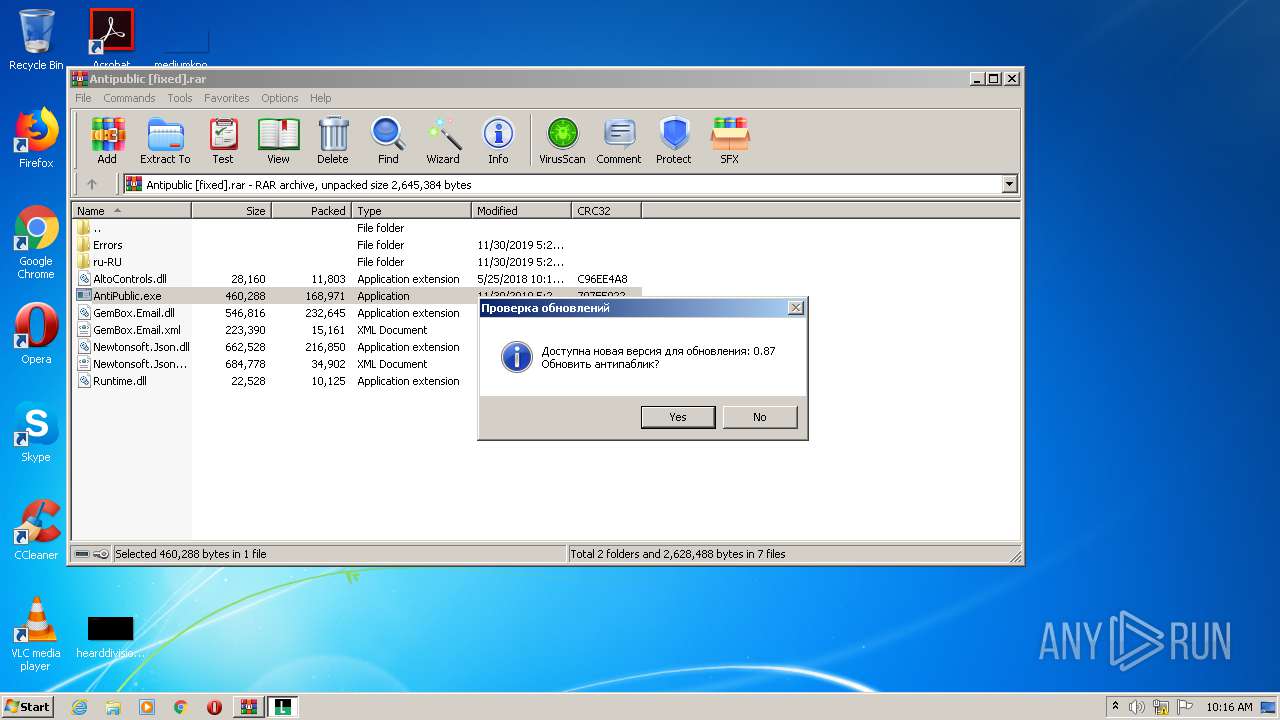
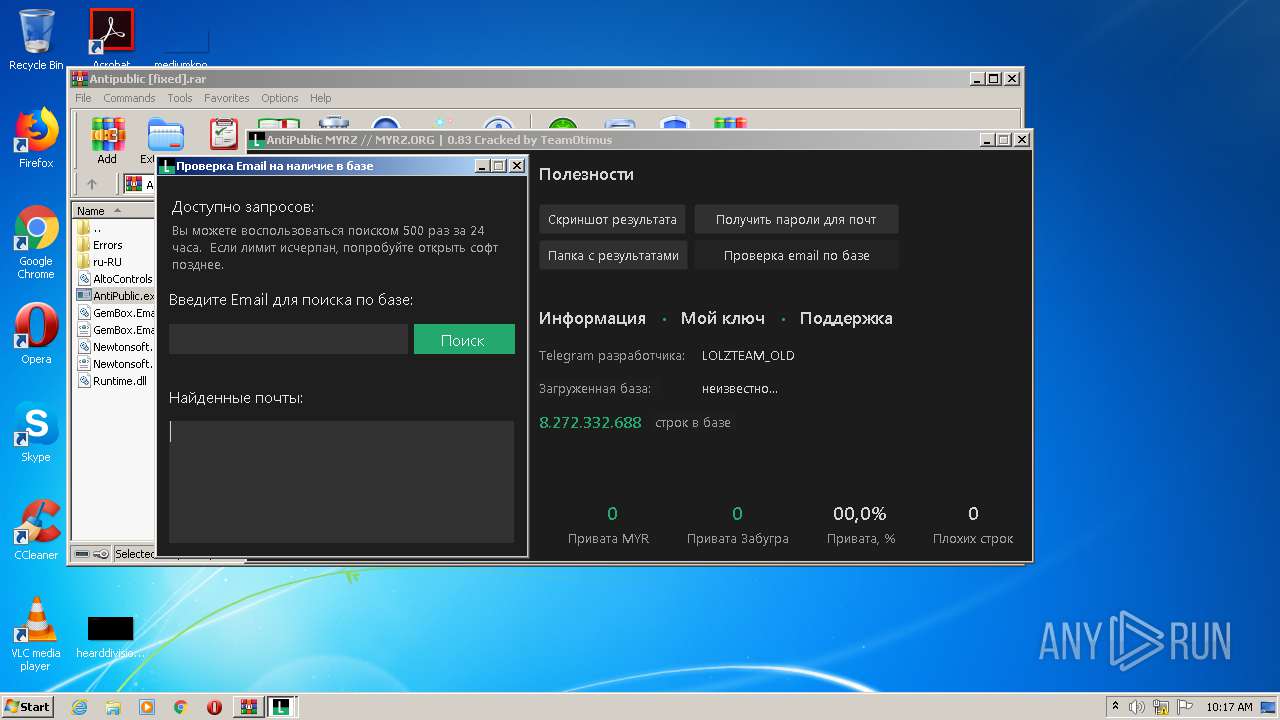
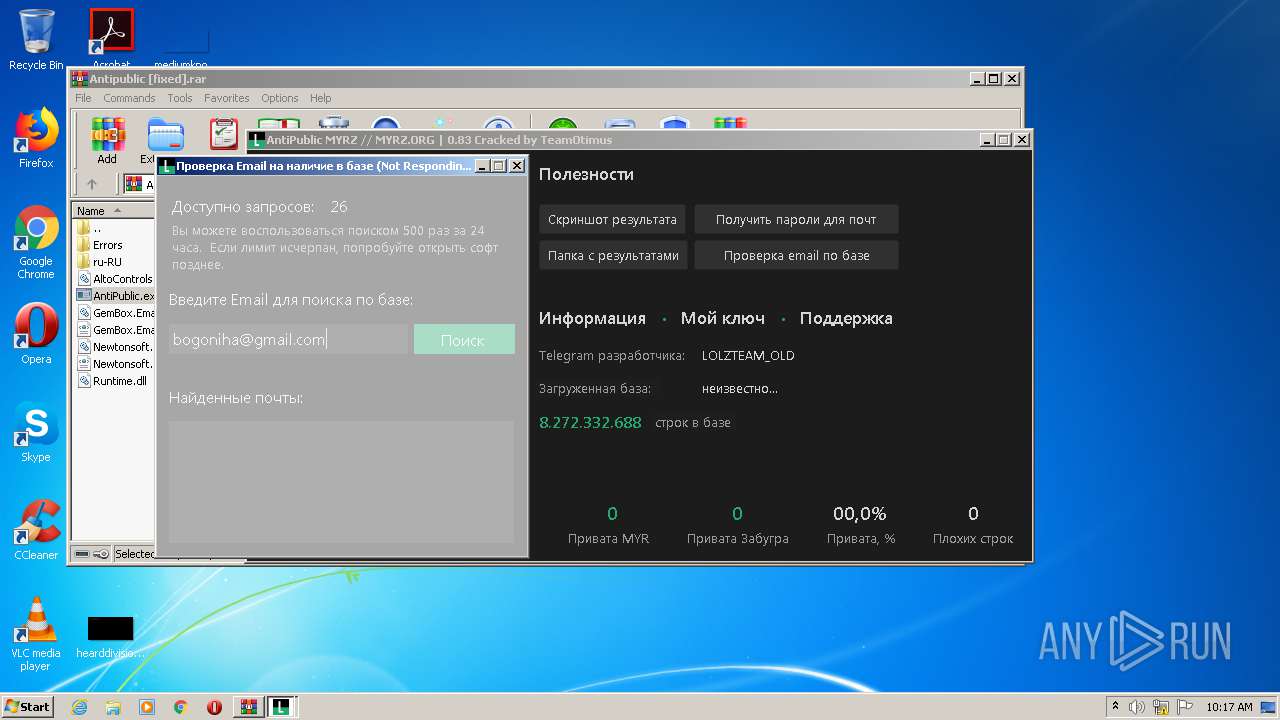
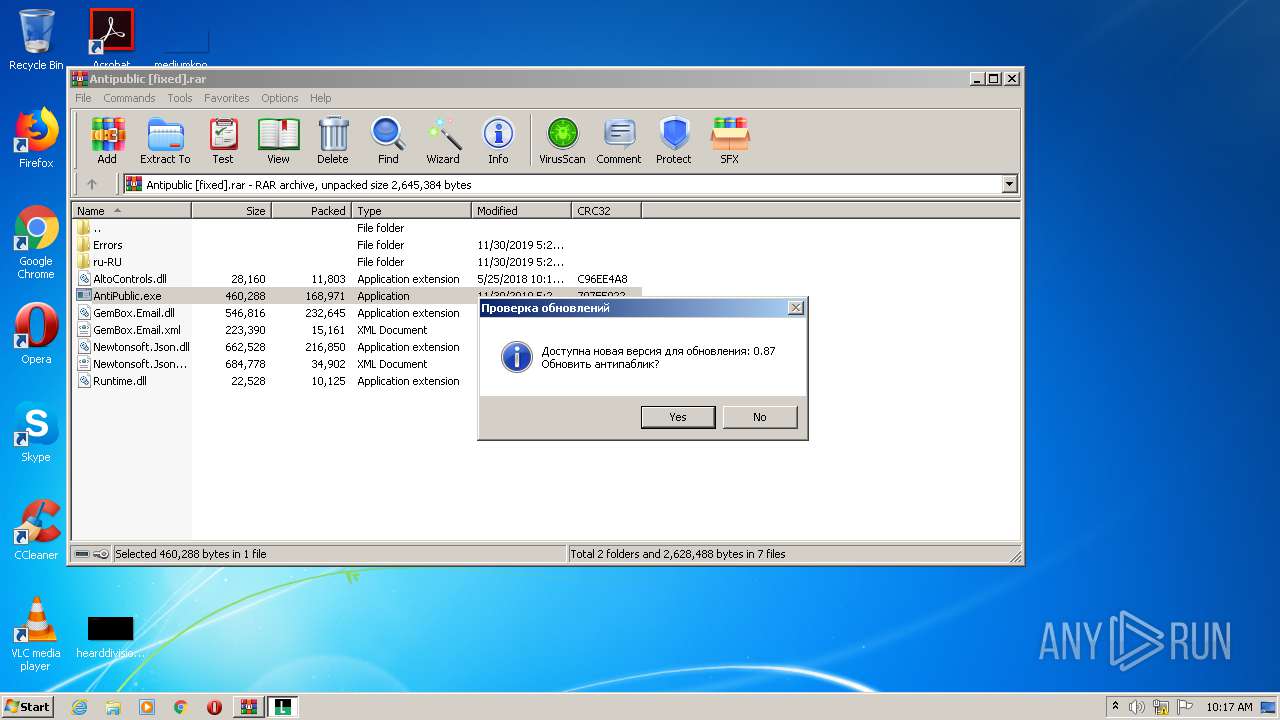
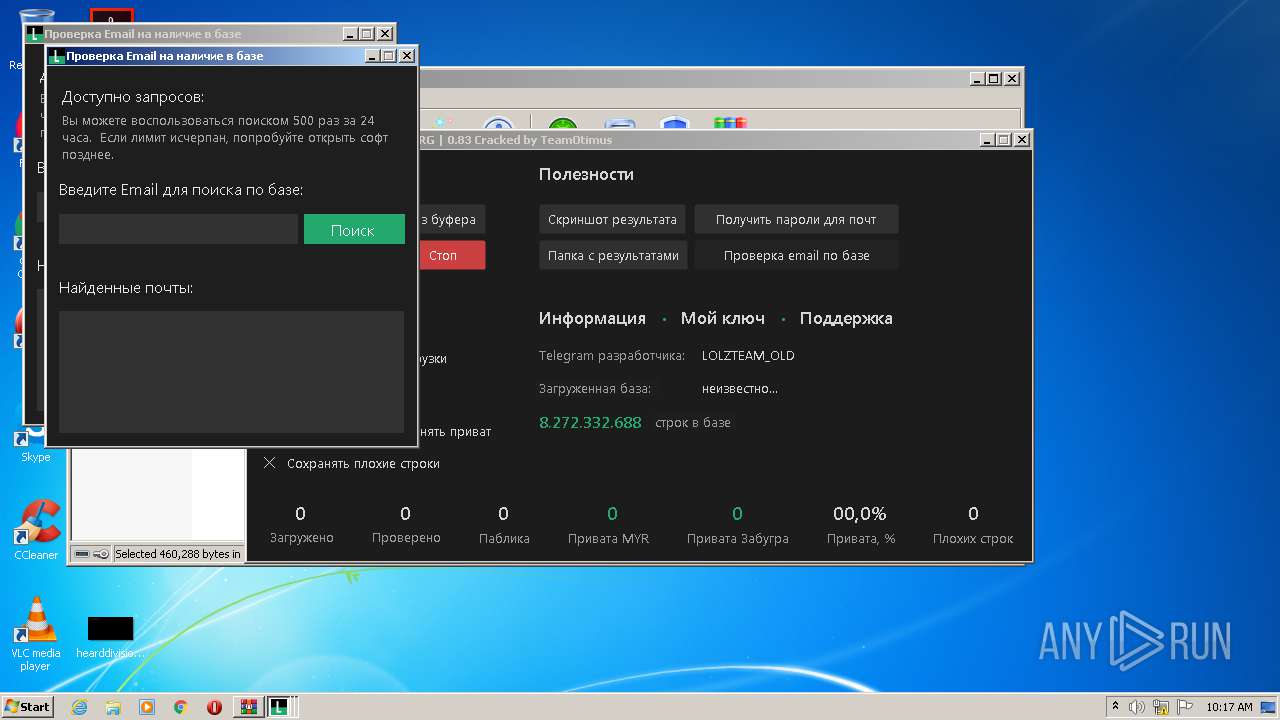
2792 | AntiPublic.exe | GET | 200 | 188.165.176.128:80 | http://myrz.org/api/check_updates.php?do=version | FR | text | 18 b | whitelisted |
2792 | AntiPublic.exe | GET | 200 | 188.165.176.128:80 | http://myrz.org/api/count_lines.php | FR | text | 10 b | whitelisted |
2792 | AntiPublic.exe | GET | 200 | 188.165.176.128:80 | http://myrz.org/api/check.php?key=5a55de396be770d56804a34d6c586360&plus=1 | FR | text | 97 b | whitelisted |
2792 | AntiPublic.exe | POST | 200 | 188.165.176.128:80 | http://myrz.org/api/email_search.php | FR | text | 23 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2676 | AntiPublic.exe | 188.165.176.128:80 | myrz.org | OVH SAS | FR | suspicious |
2792 | AntiPublic.exe | 188.165.176.128:80 | myrz.org | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
myrz.org |
| whitelisted |