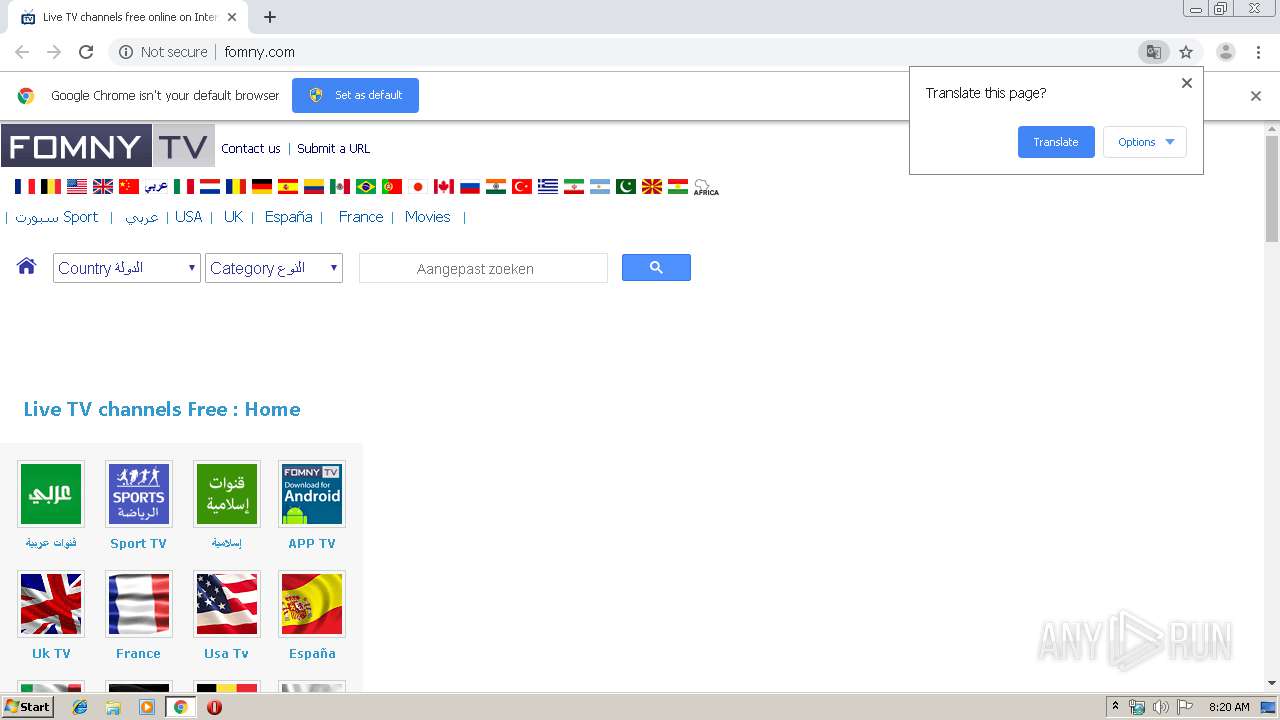
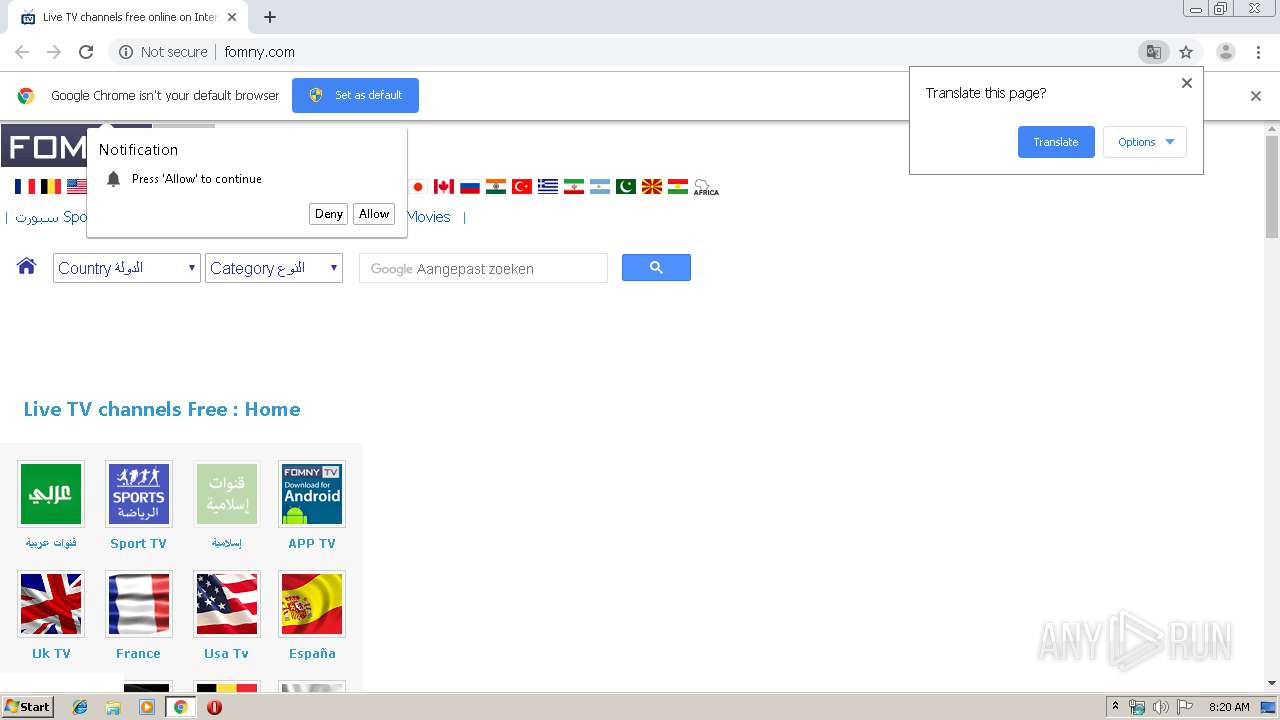
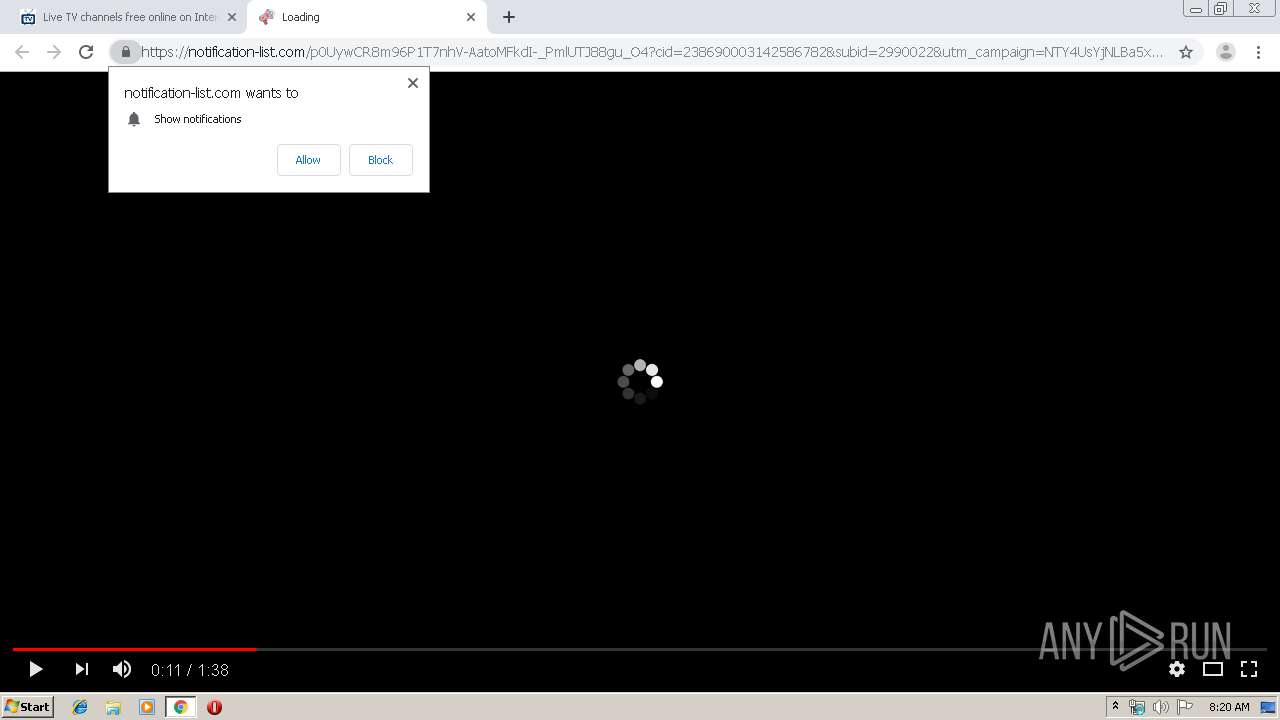
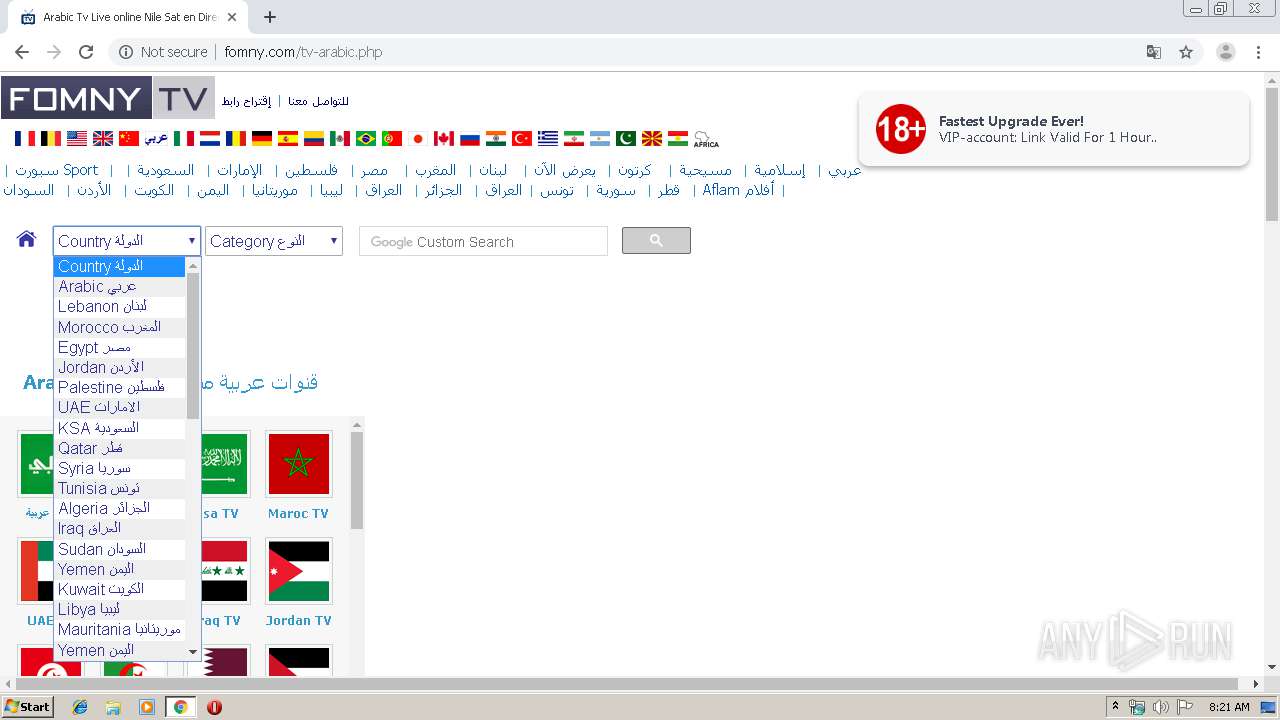
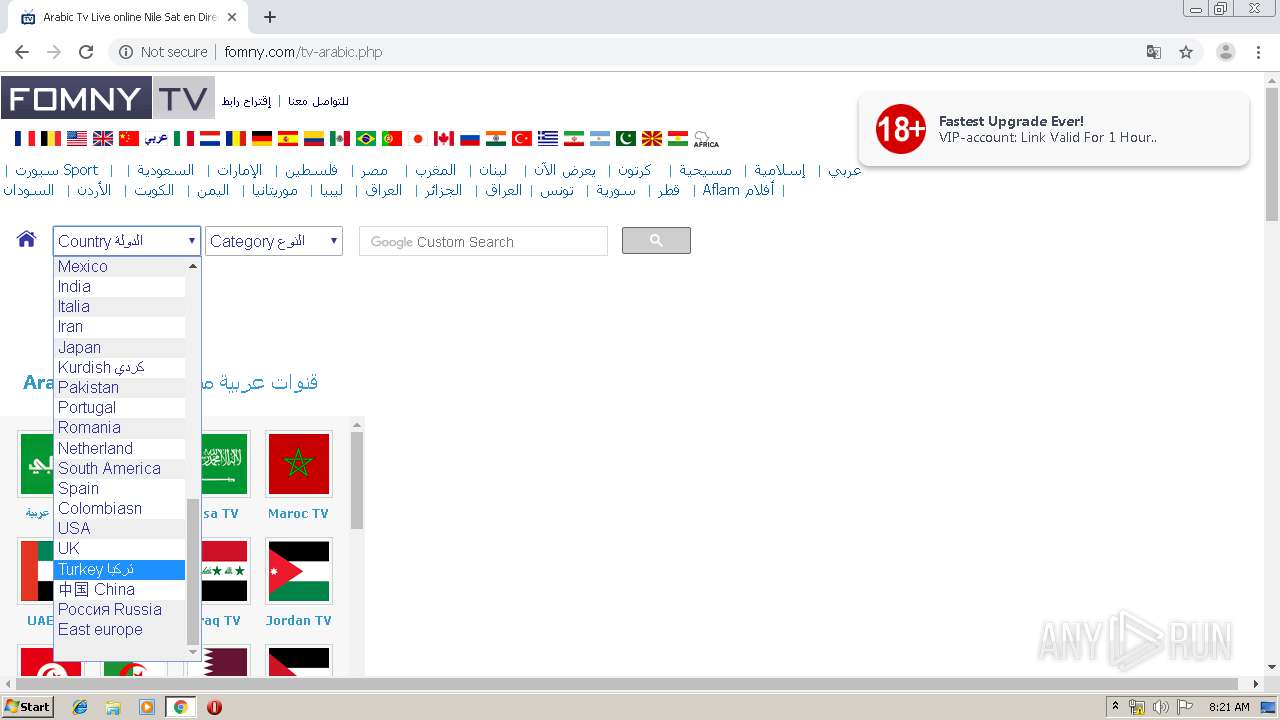
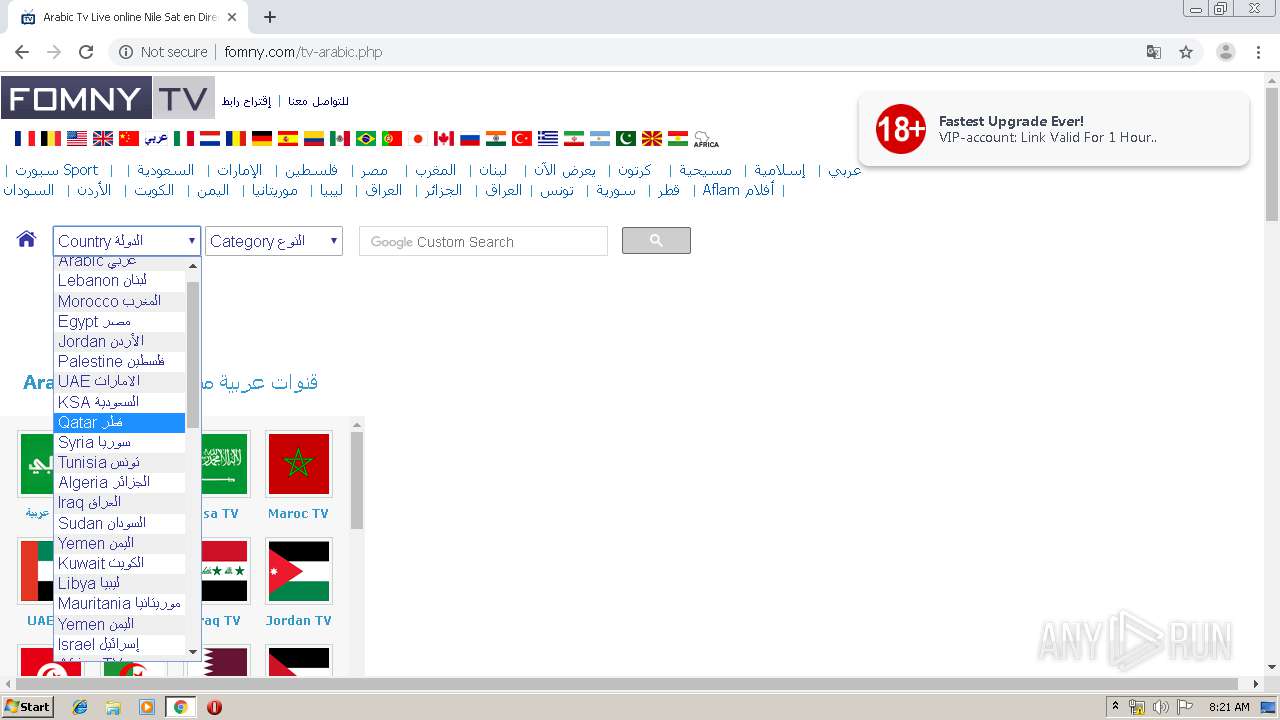
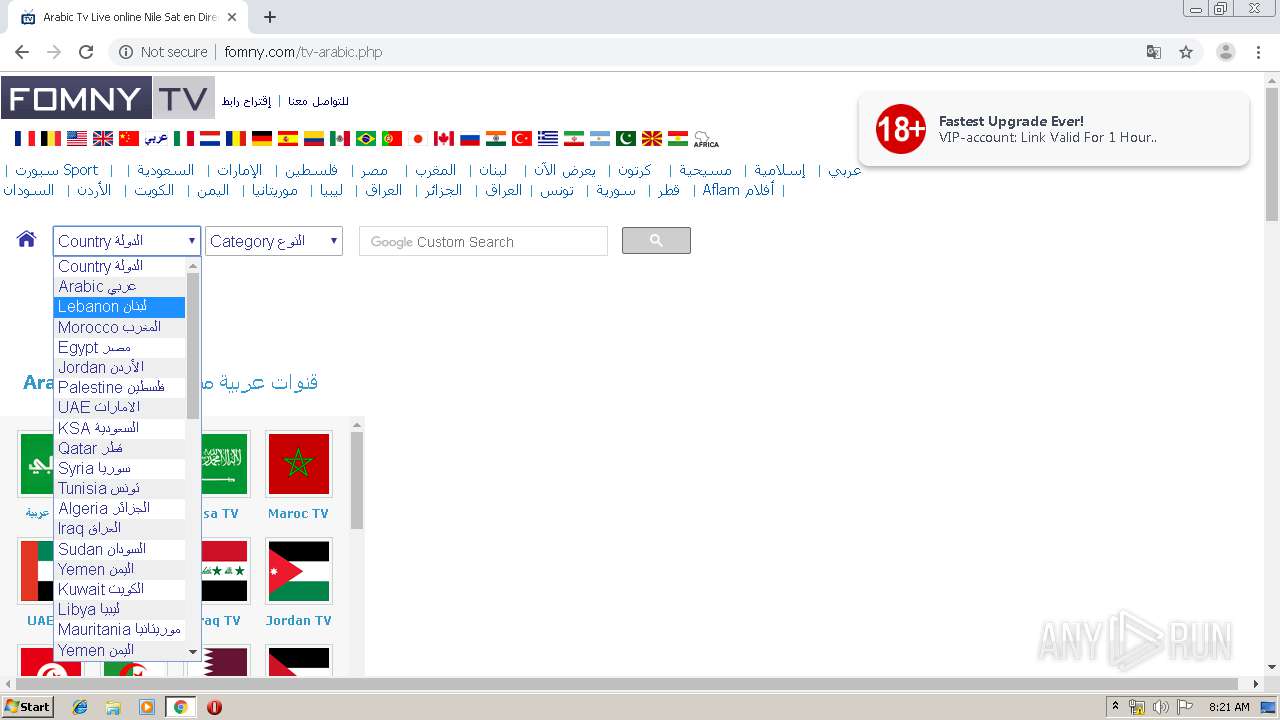
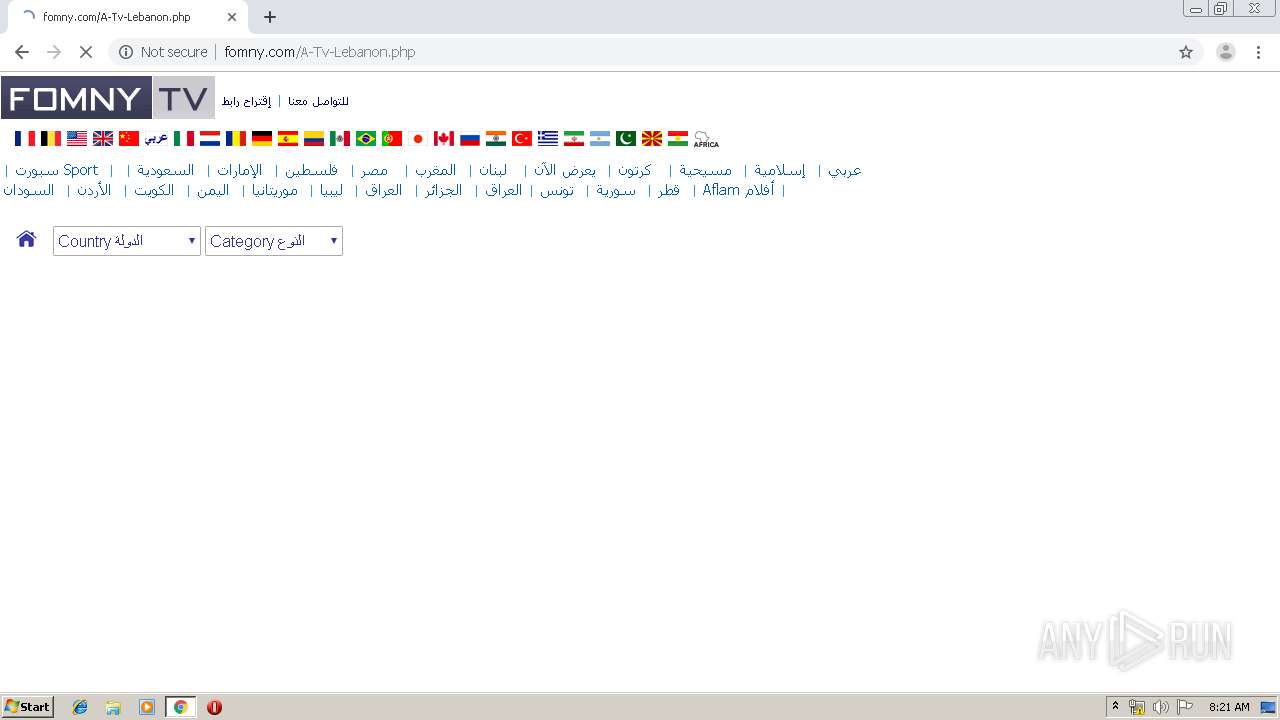
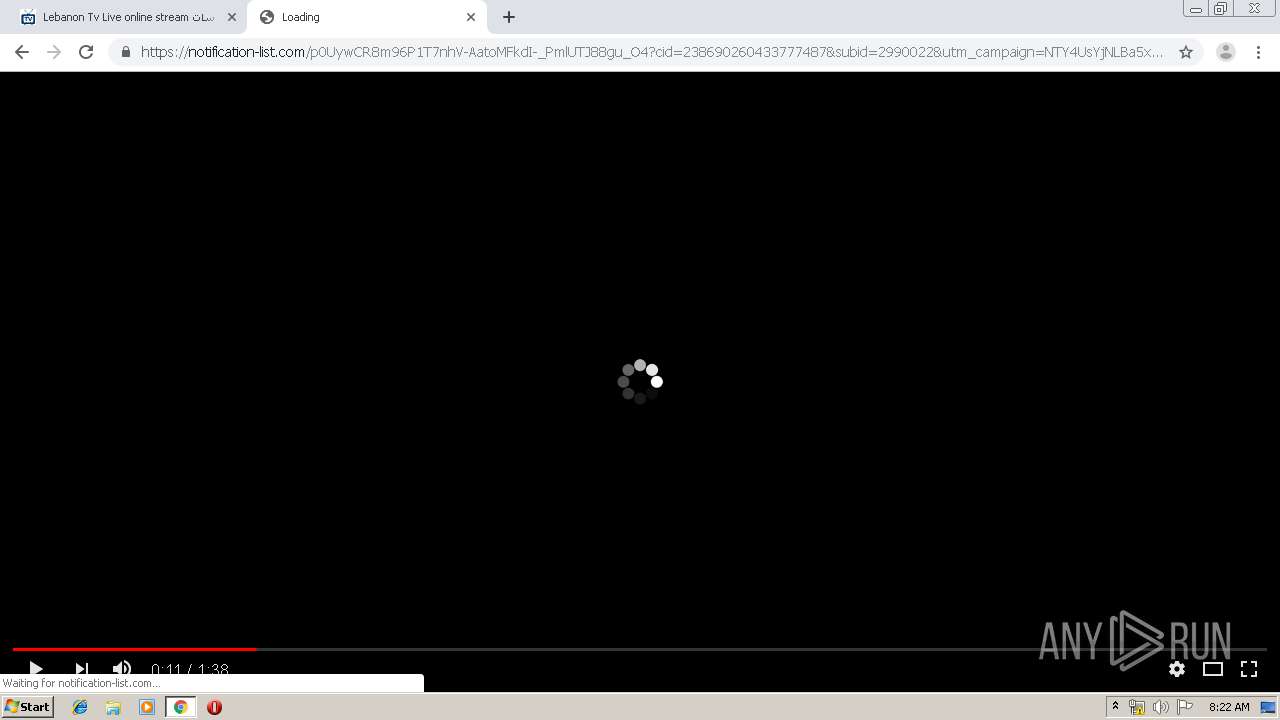
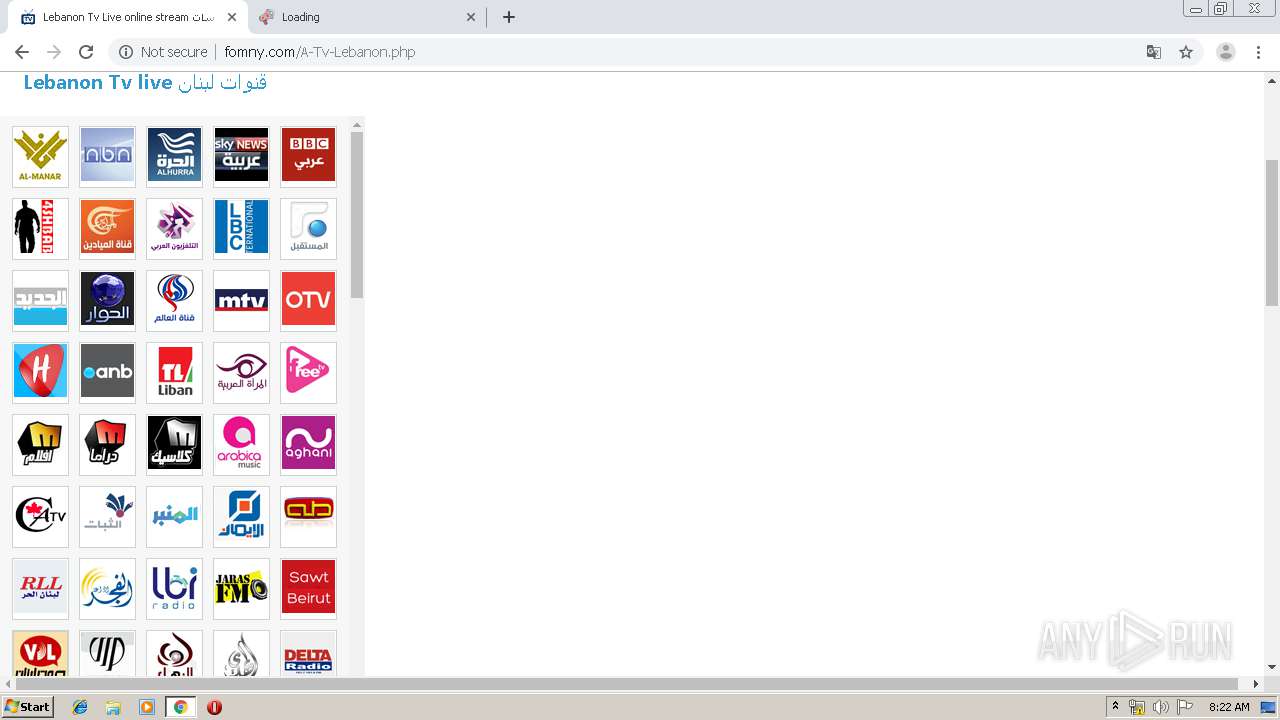
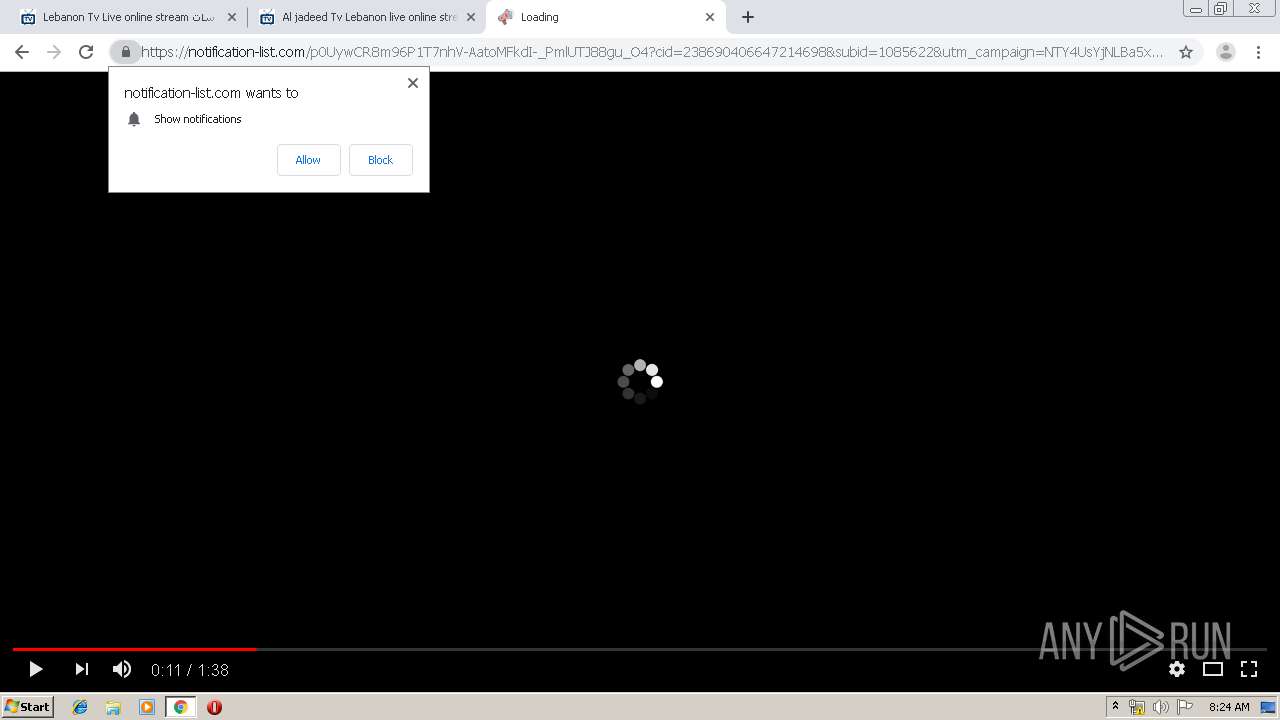
| URL: | https://www.fomny.com/ |
| Full analysis: | https://app.any.run/tasks/acb085bc-1c87-44f4-abe7-deb5c15c6038 |
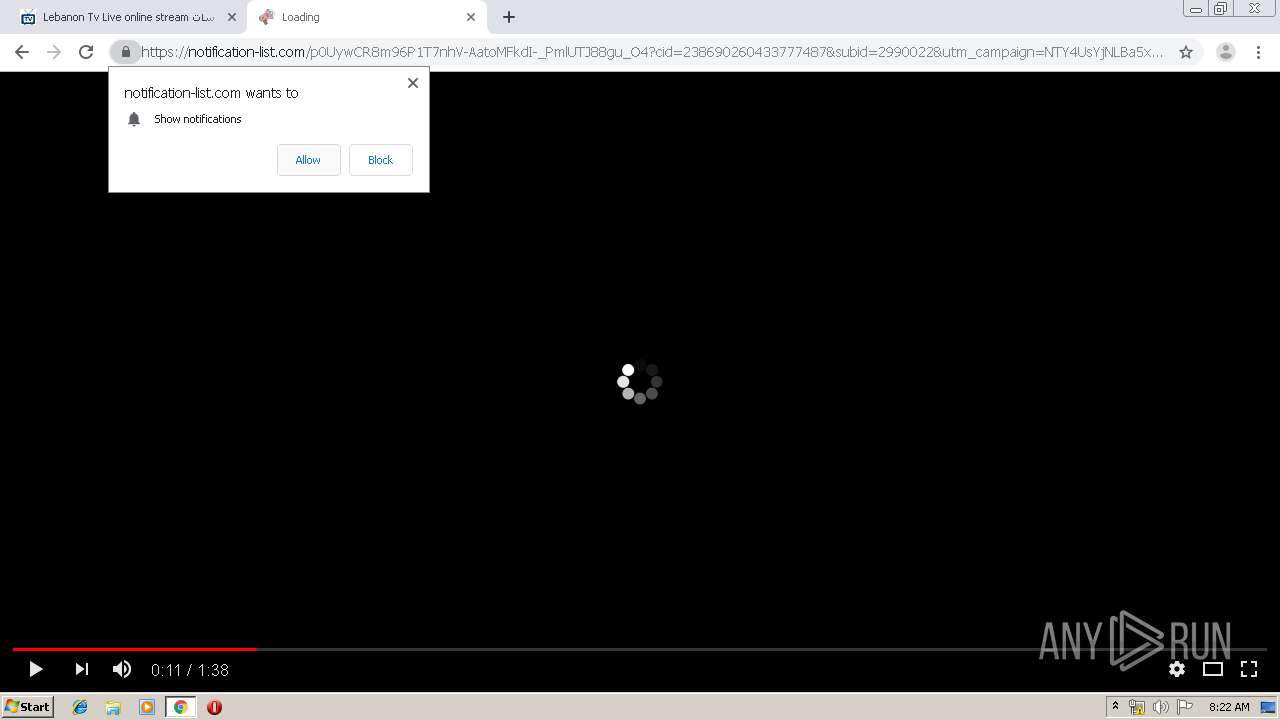
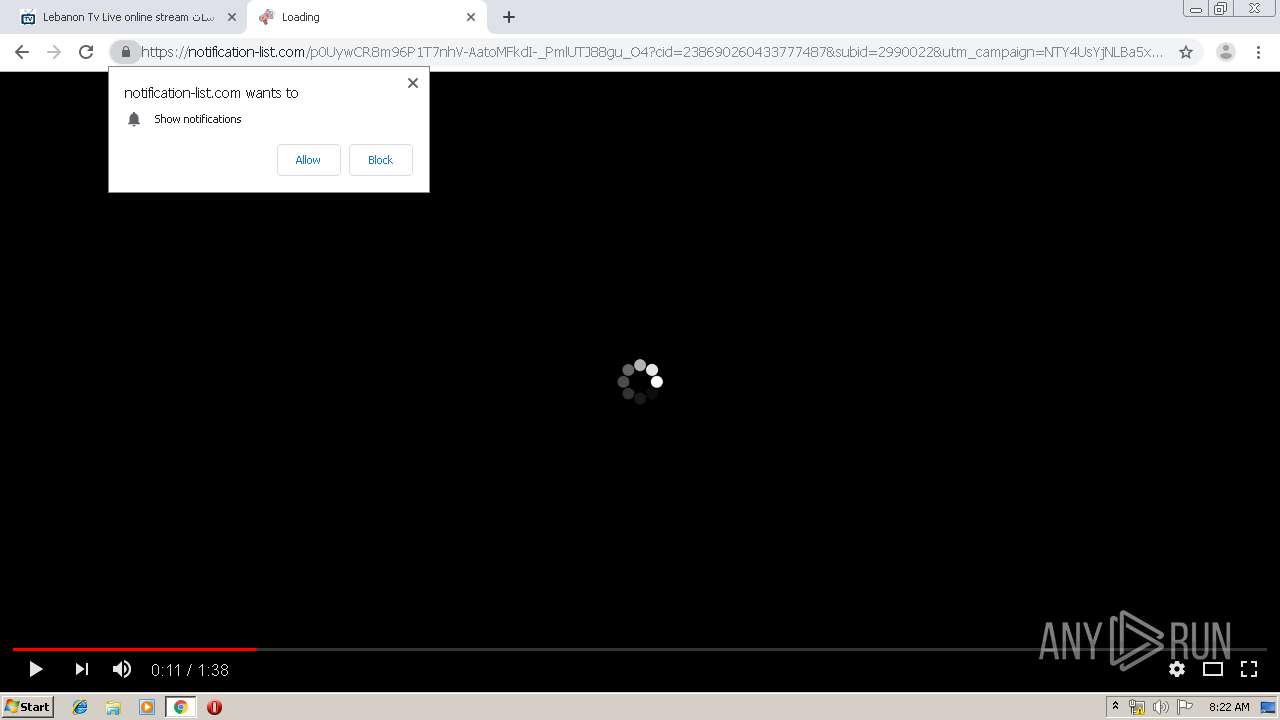
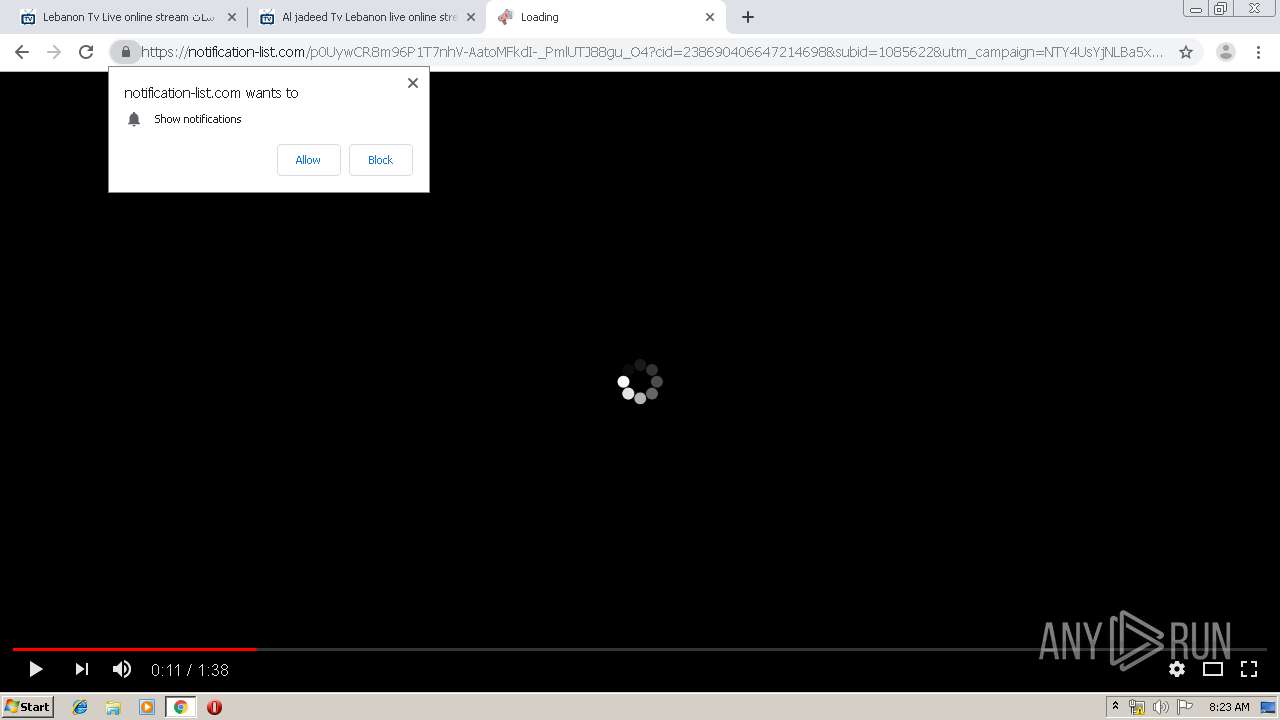
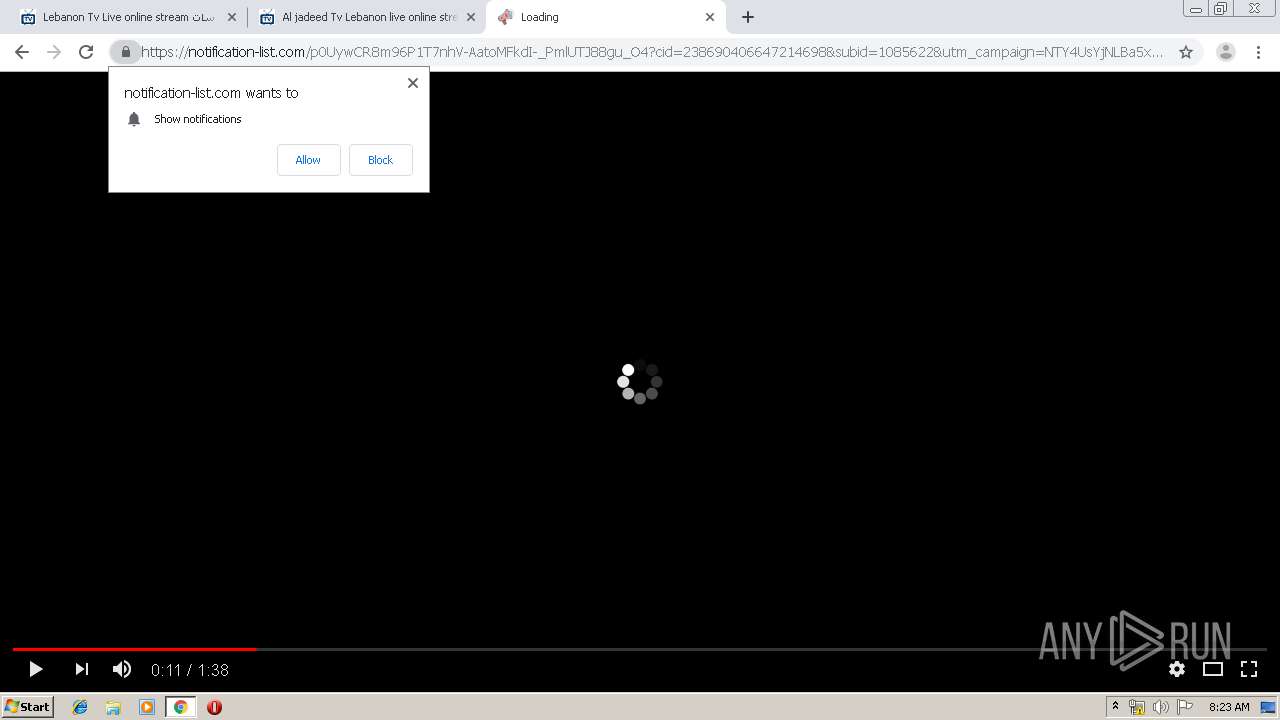
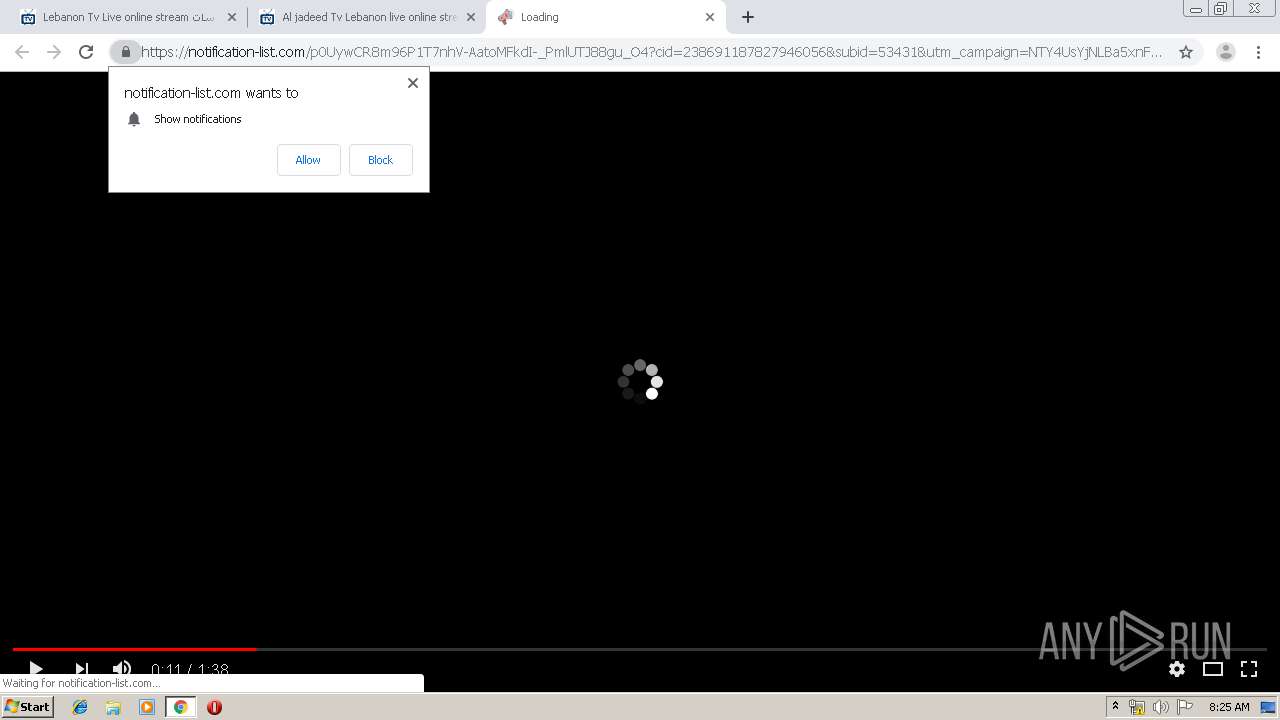
| Verdict: | Malicious activity |
| Analysis date: | January 08, 2020, 08:20:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E035B2575950D01F9038DB6D483A8AE1 |
| SHA1: | 7D9ACF03C64ECAFD6E8EC9E7E4472ACDEF4B8C8D |
| SHA256: | 52542E87C60E6FEBFB583CF29780DA46482EA70077B559560653AF7C22EFF8A2 |
| SSDEEP: | 3:N8DSLWILFK:2OLWI0 |
MALICIOUS
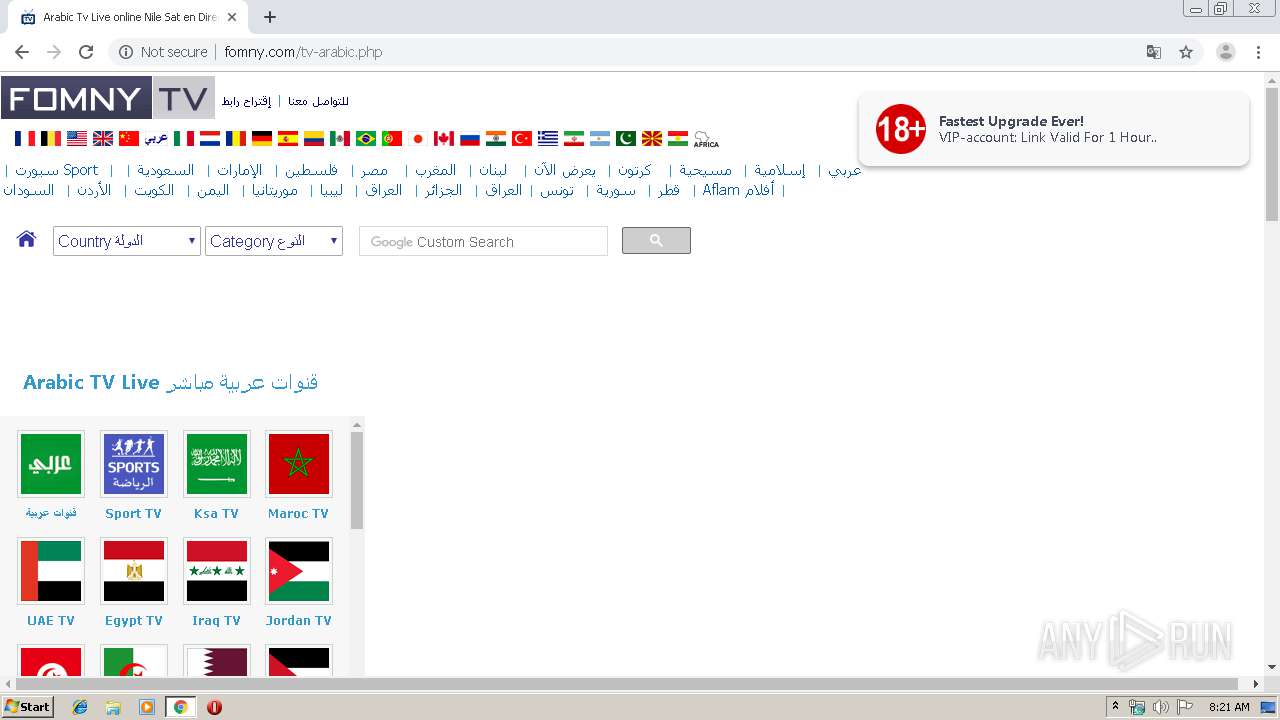
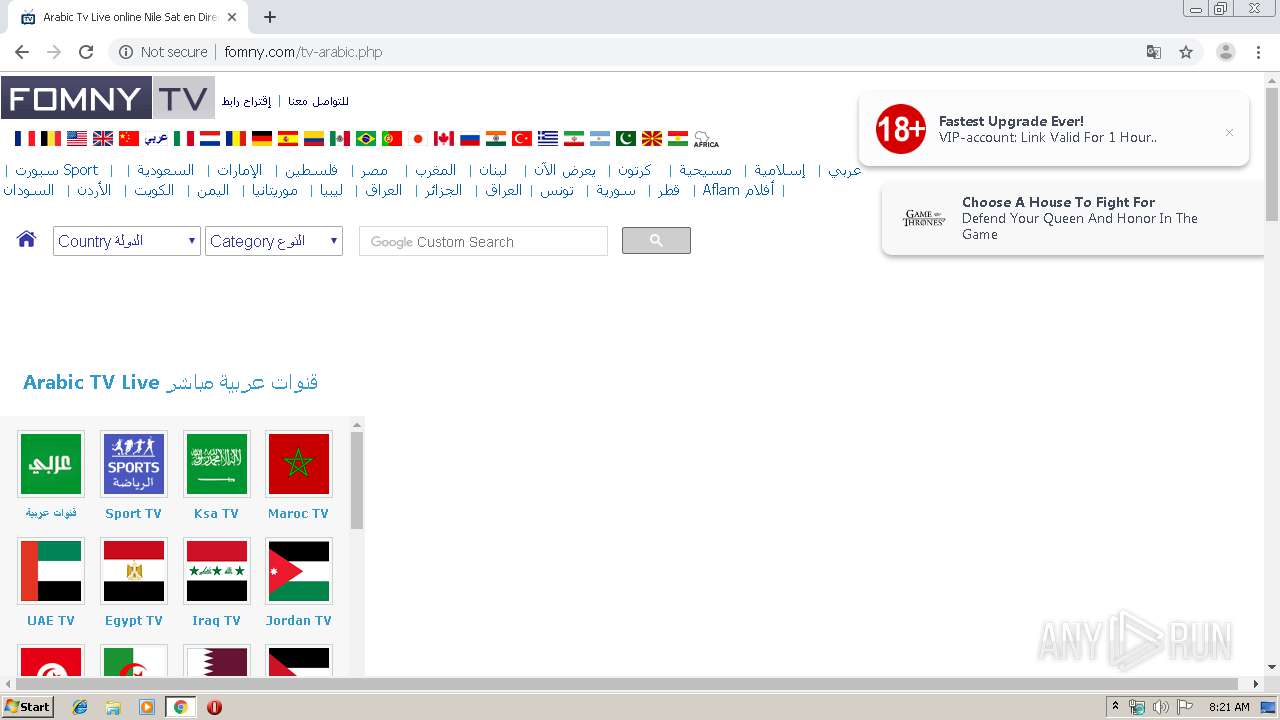
No malicious indicators.SUSPICIOUS
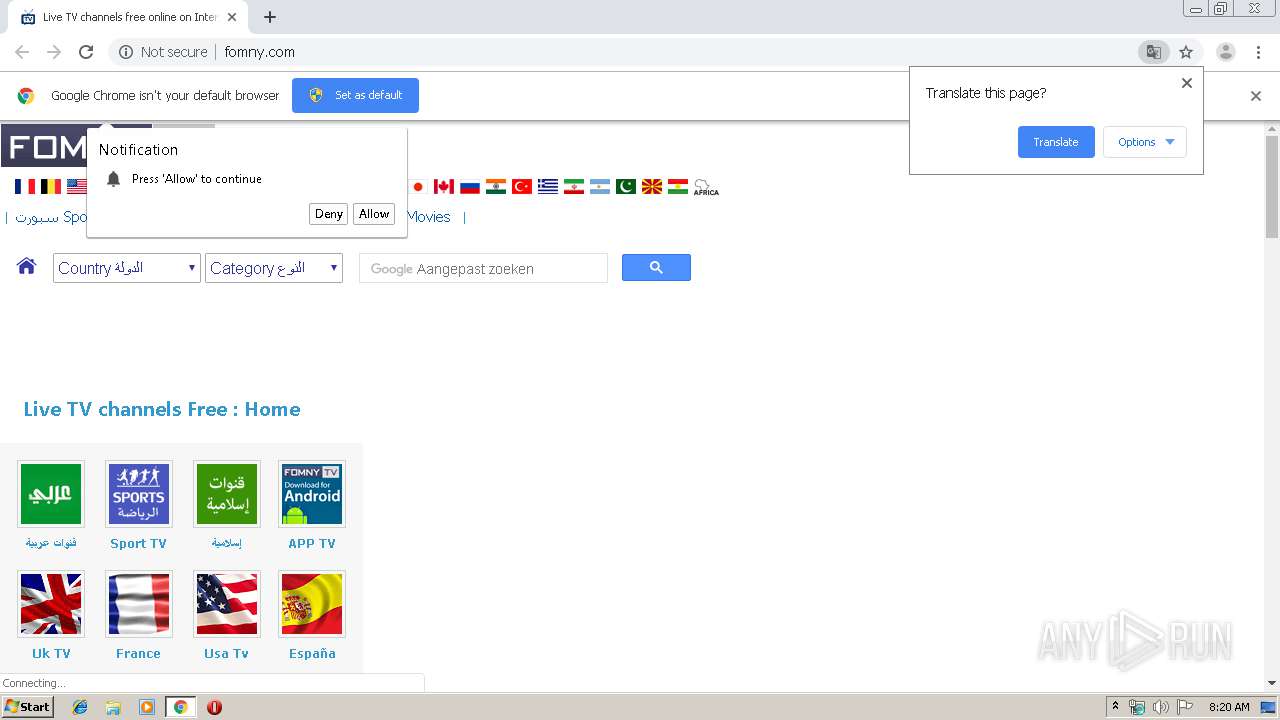
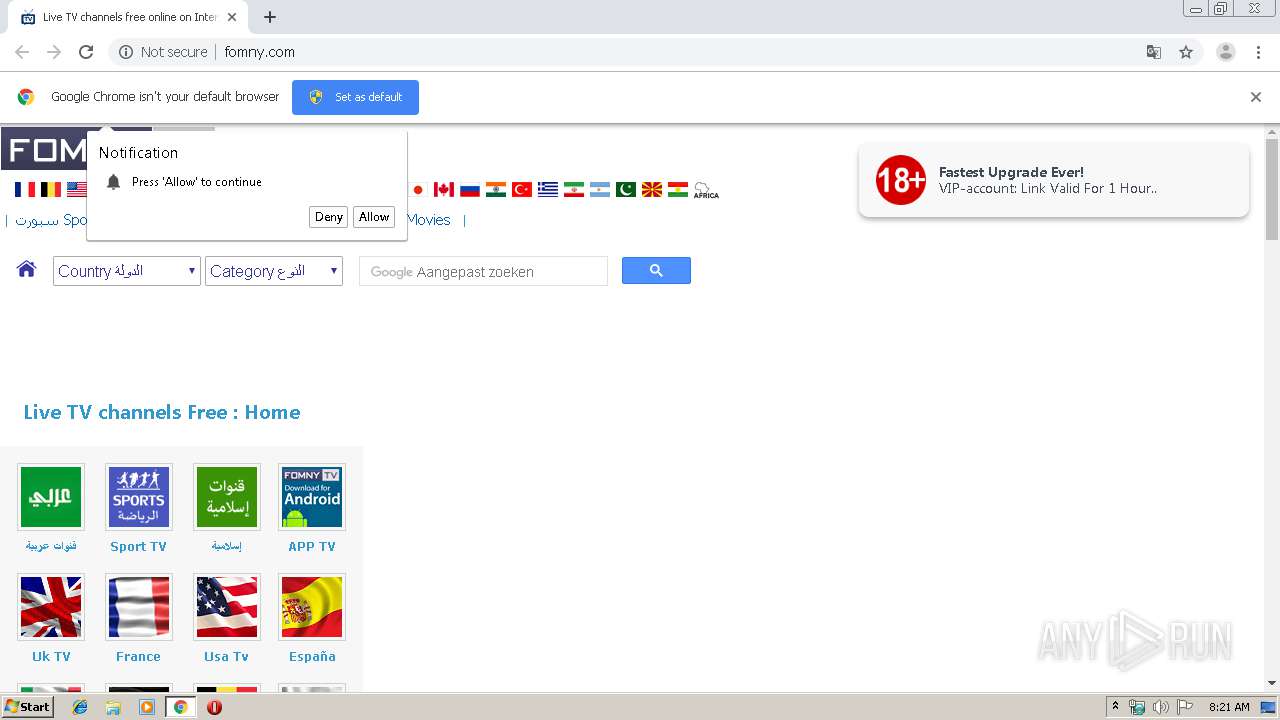
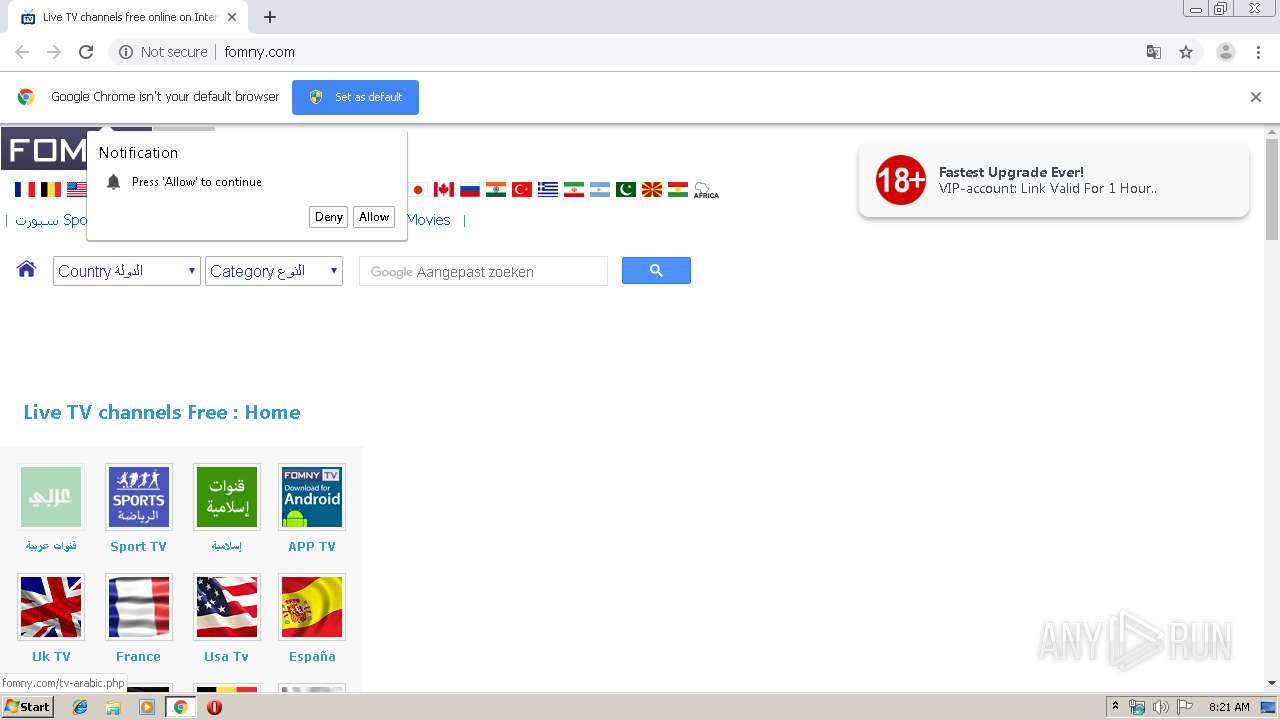
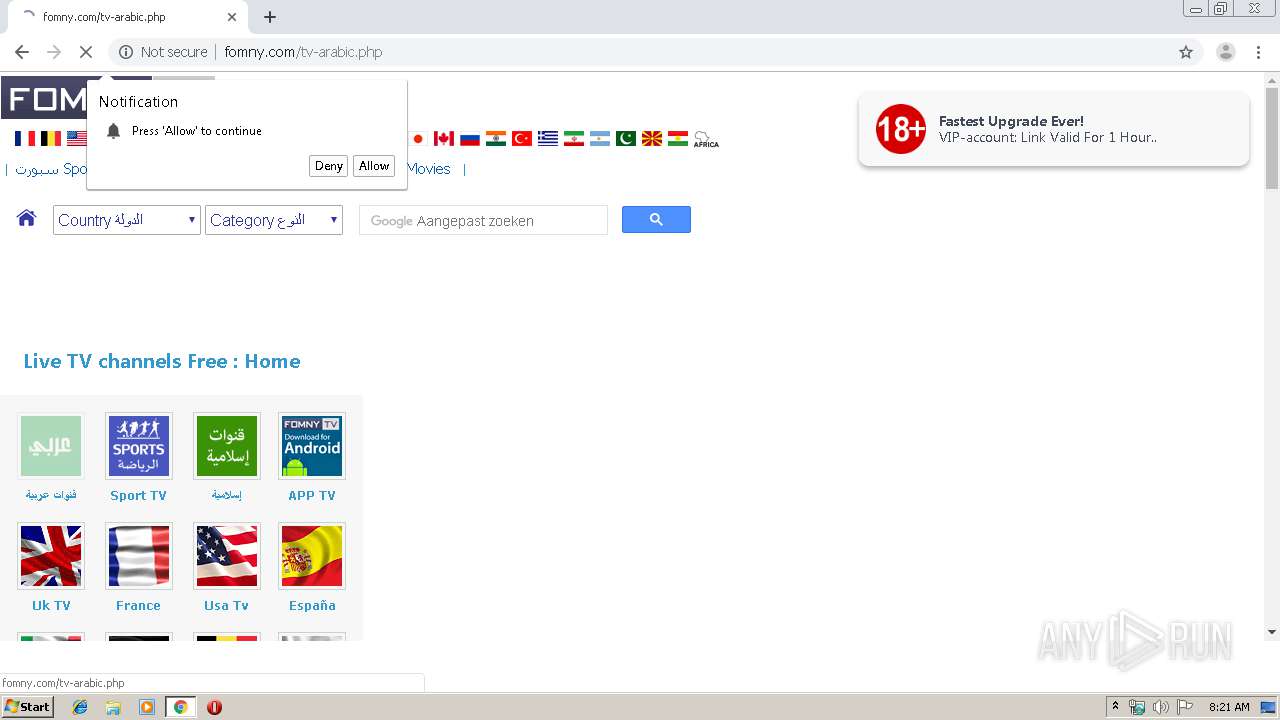
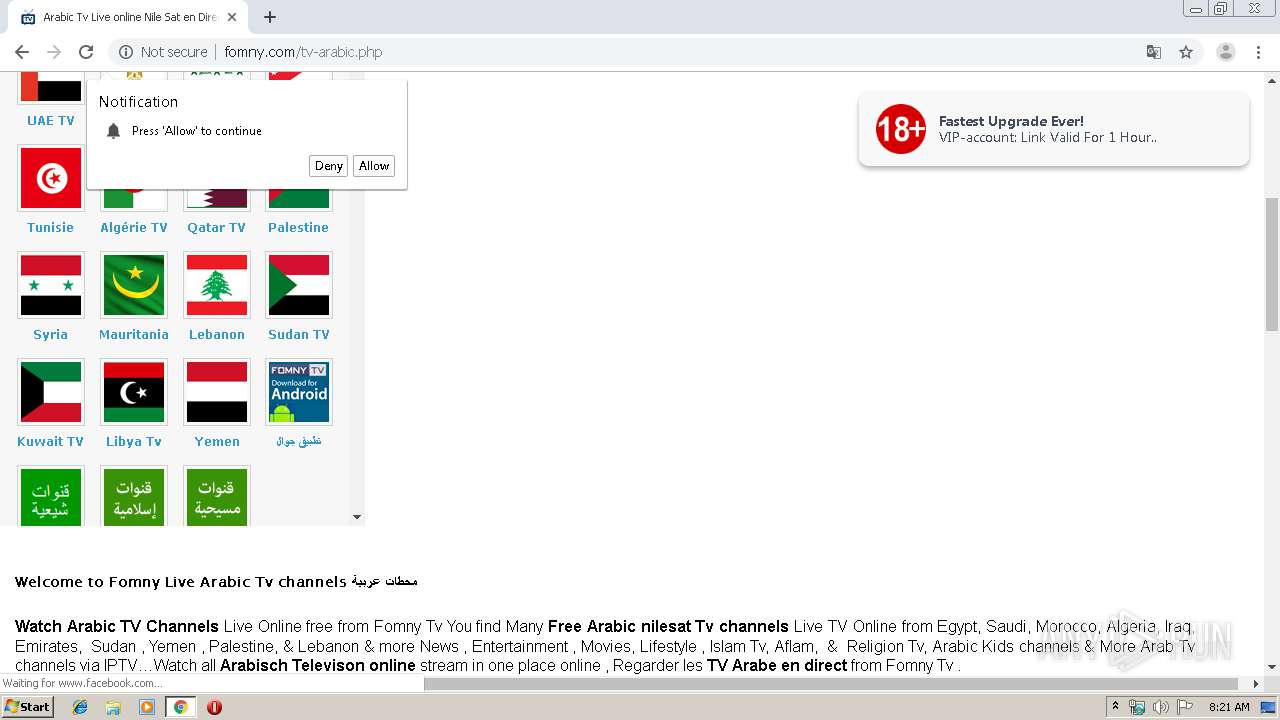
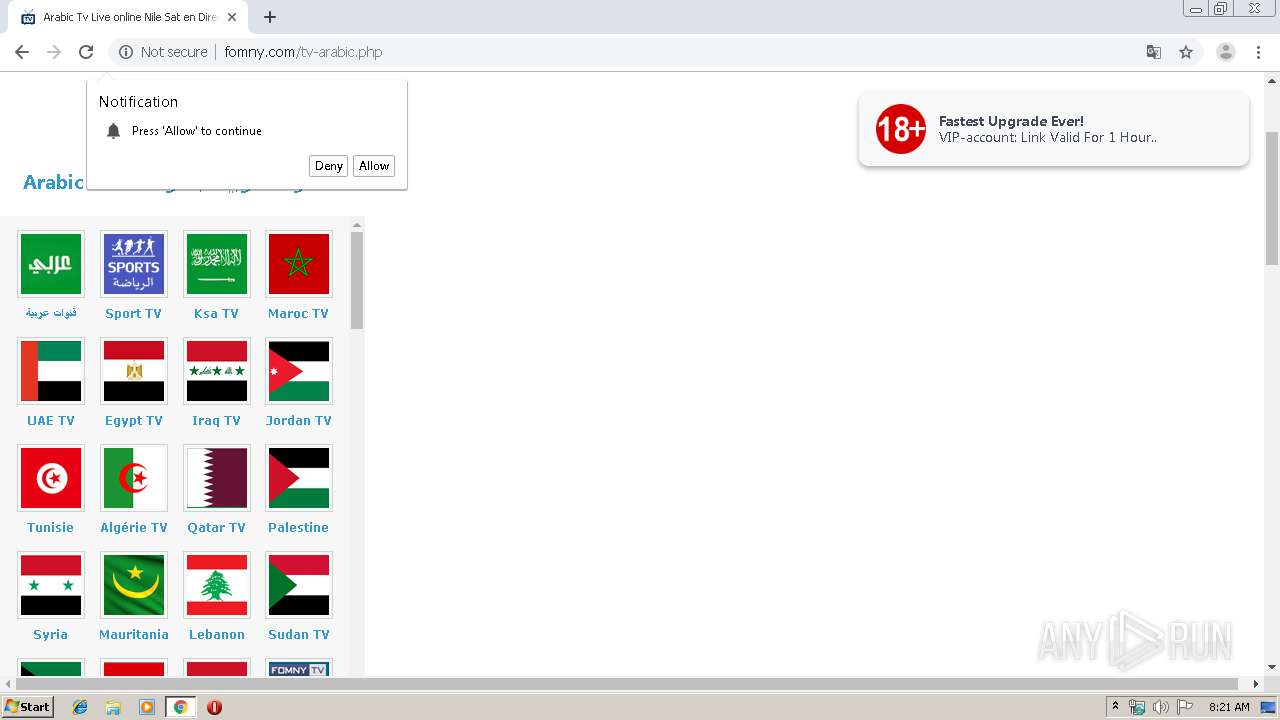
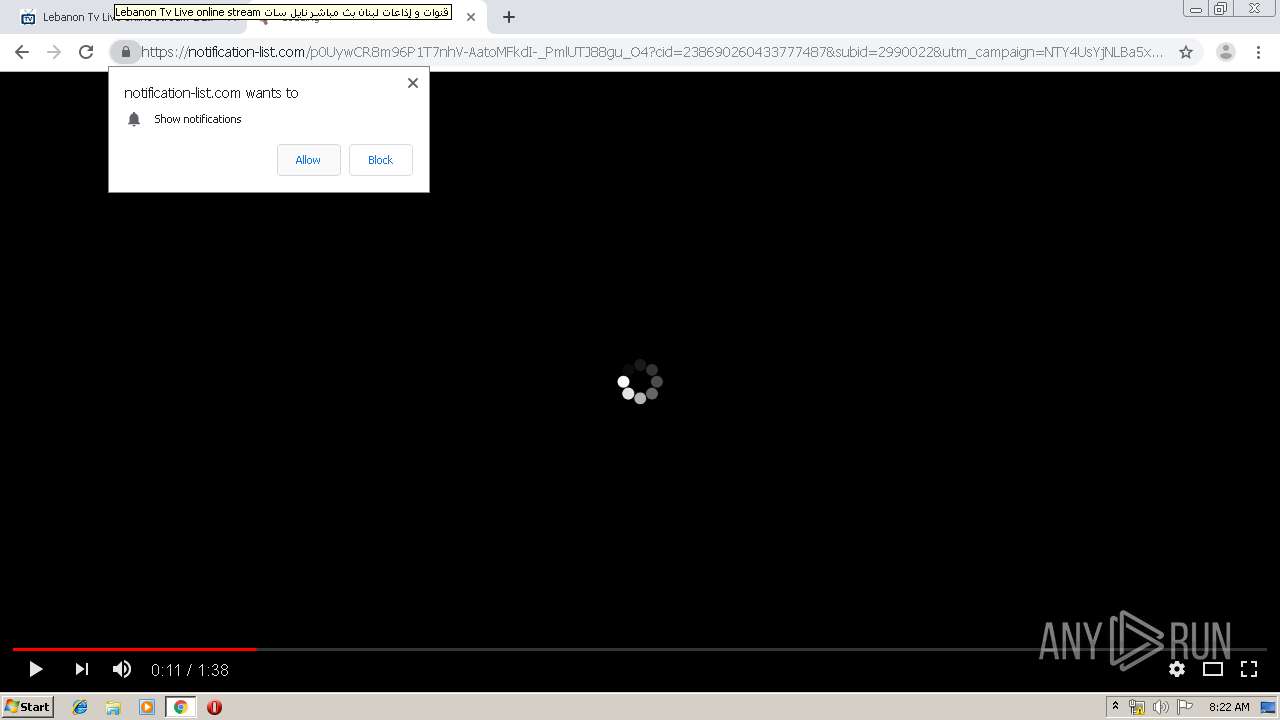
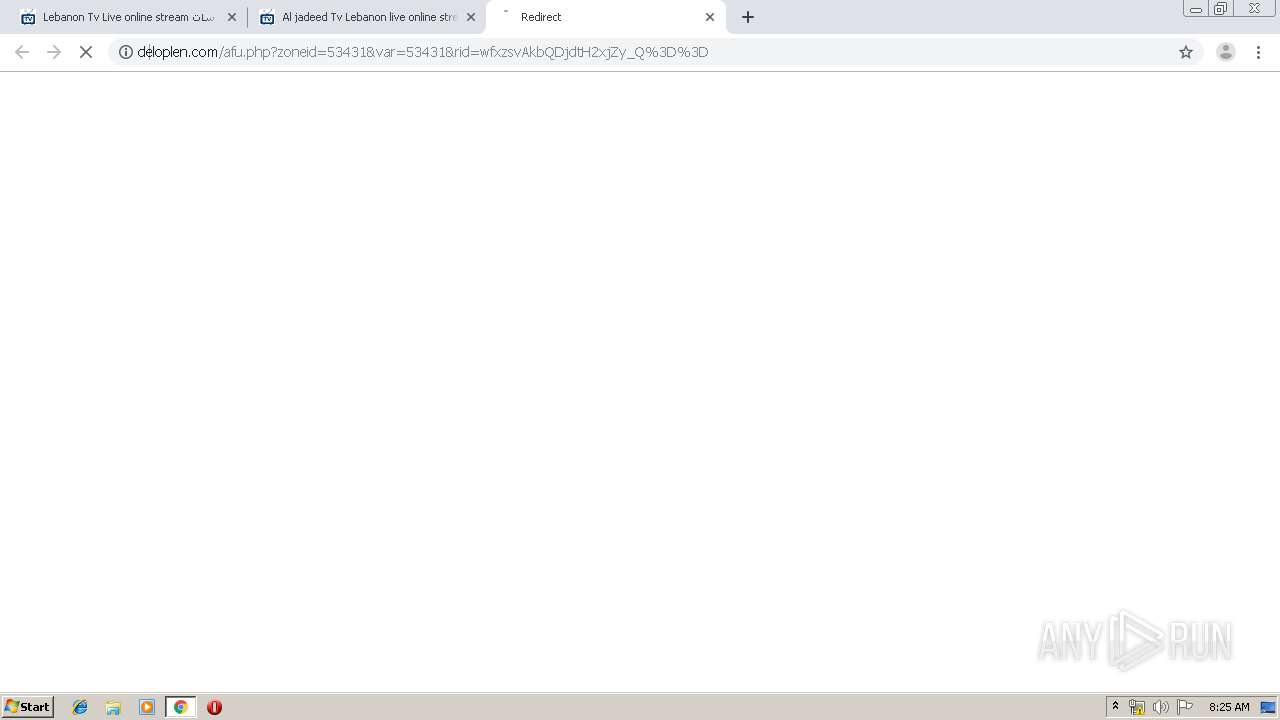
Modifies files in Chrome extension folder
- chrome.exe (PID: 2600)
INFO
Reads the hosts file
- chrome.exe (PID: 2600)
- chrome.exe (PID: 2788)
Dropped object may contain TOR URL's
- chrome.exe (PID: 2600)
Creates files in the user directory
- chrome.exe (PID: 2600)
Application launched itself
- chrome.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
82
Monitored processes
47
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11845574784945604377 --mojo-platform-channel-handle=4972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14281838680125796183 --mojo-platform-channel-handle=4204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11262829778806273355 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9271477627551142920 --mojo-platform-channel-handle=4776 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1515654459697637524 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1386603058058431497 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18014172802826855891 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3906681954743772167 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4684546560767730879 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5372 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14641631239787110779,9624876833645878372,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1469360881404663764 --mojo-platform-channel-handle=4976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
661
Read events
542
Write events
114
Delete events
5
Modification events
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2600-13222945244604125 |
Value: 259 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
157
Text files
273
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\77c19c35-e3f6-4c47-8b46-ba4b6ebdb726.tmp | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DC32343F45B01764B6267AD36548102A | SHA256:A250F5AD57D4BD58AAE92810D50278E3BE2DBF869F126A3A3519691BCDFC2075 | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:A519780ED0A2F4336DB4F5651D79C369 | SHA256:DA5B71BD0075B55757BF757BF5F4D4A1DCBCF0762CDA5B31B28680963E068C75 | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a86f.TMP | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a821.TMP | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a860.TMP | text | |
MD5:A519780ED0A2F4336DB4F5651D79C369 | SHA256:DA5B71BD0075B55757BF757BF5F4D4A1DCBCF0762CDA5B31B28680963E068C75 | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
570
TCP/UDP connections
147
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/images/Drapeaux/d-mexique.gif | US | image | 613 b | malicious |
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/images/styles-2.css | US | text | 189 b | malicious |
2788 | chrome.exe | GET | 301 | 104.19.133.78:80 | http://jsc.mgid.com/w/a/fomny.com.740355.js?t= | US | — | — | whitelisted |
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/ | US | html | 31.9 Kb | malicious |
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/images/logo-fomny002.gif | US | image | 2.90 Kb | malicious |
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/images/Drapeaux/d-china.gif | US | image | 591 b | malicious |
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/images/styles.css | US | text | 1.23 Kb | malicious |
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/images/Drapeaux/d-france.gif | US | image | 224 b | malicious |
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/images/Drapeaux/flag-belgique.jpg | US | image | 3.90 Kb | malicious |
2788 | chrome.exe | GET | 200 | 104.28.3.93:80 | http://fomny.com/images/Drapeaux/d-Netherland.gif | US | image | 144 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2788 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2788 | chrome.exe | 104.28.3.93:443 | www.fomny.com | Cloudflare Inc | US | unknown |
2788 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2788 | chrome.exe | 104.28.3.93:80 | www.fomny.com | Cloudflare Inc | US | unknown |
2788 | chrome.exe | 104.19.133.78:80 | jsc.mgid.com | Cloudflare Inc | US | unknown |
2788 | chrome.exe | 172.217.18.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
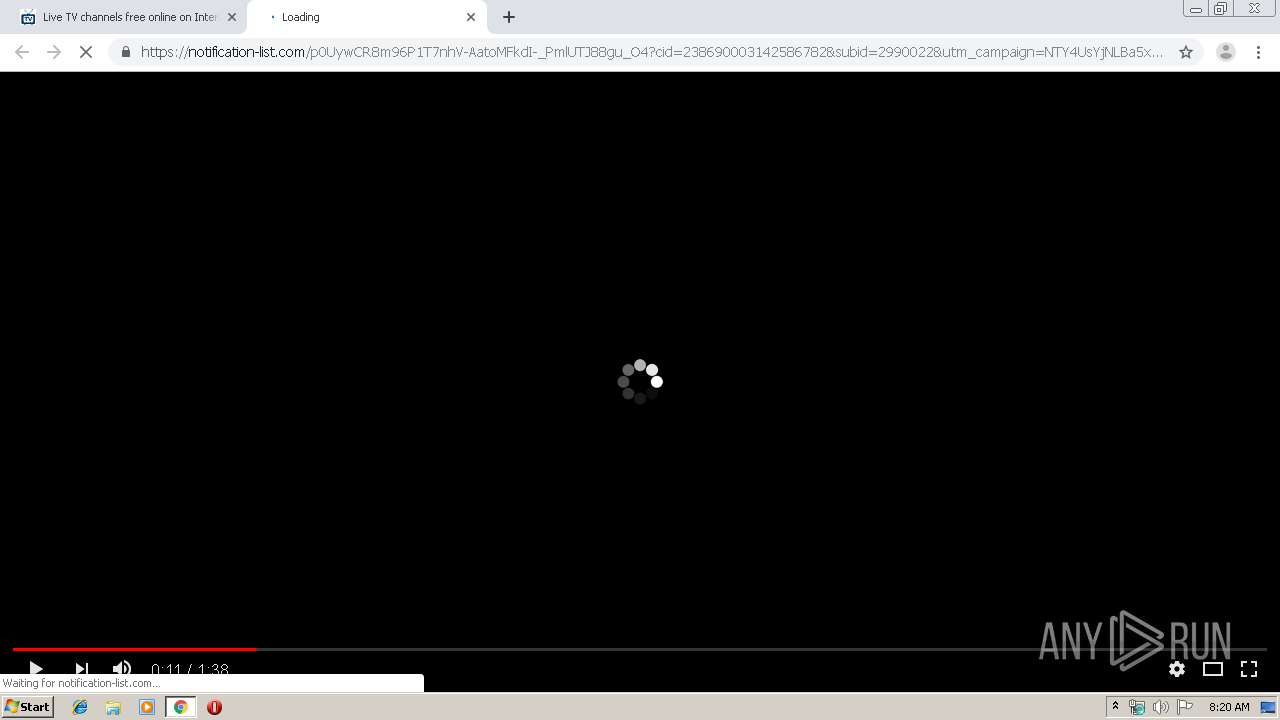
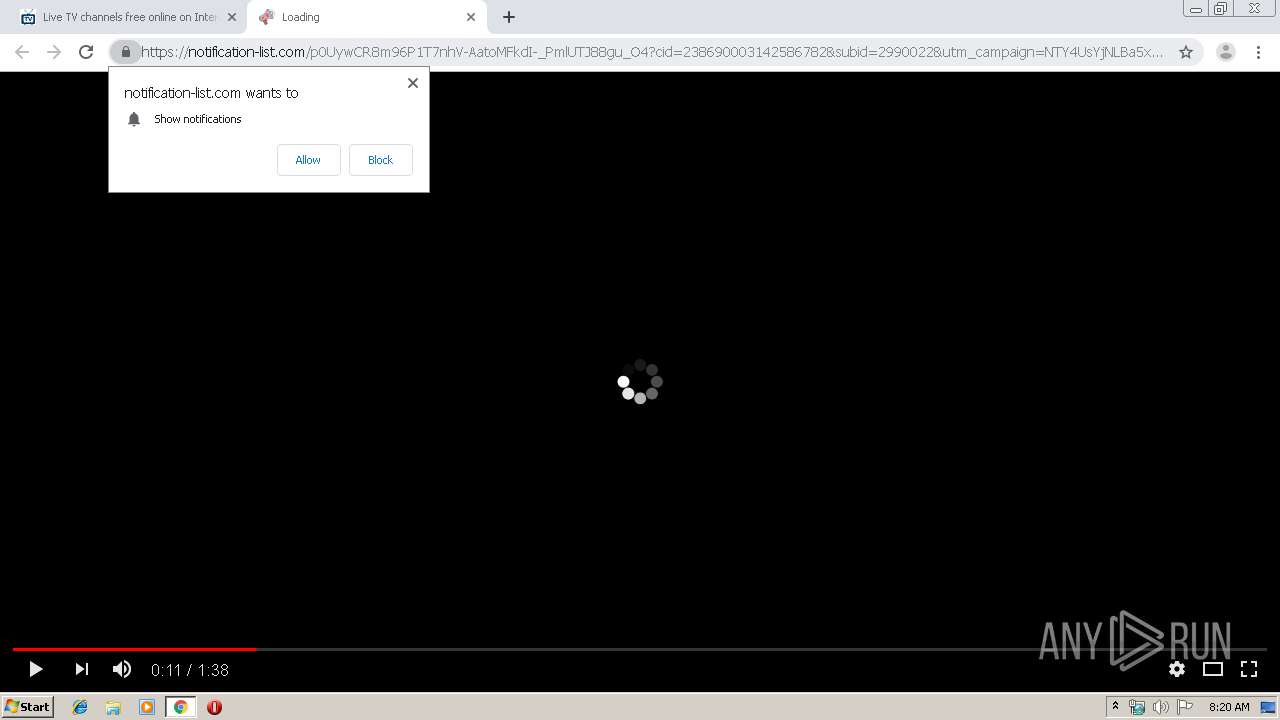
2788 | chrome.exe | 194.187.98.181:80 | sendmepush.com | Webzilla B.V. | NL | unknown |
2788 | chrome.exe | 104.19.133.78:443 | jsc.mgid.com | Cloudflare Inc | US | unknown |
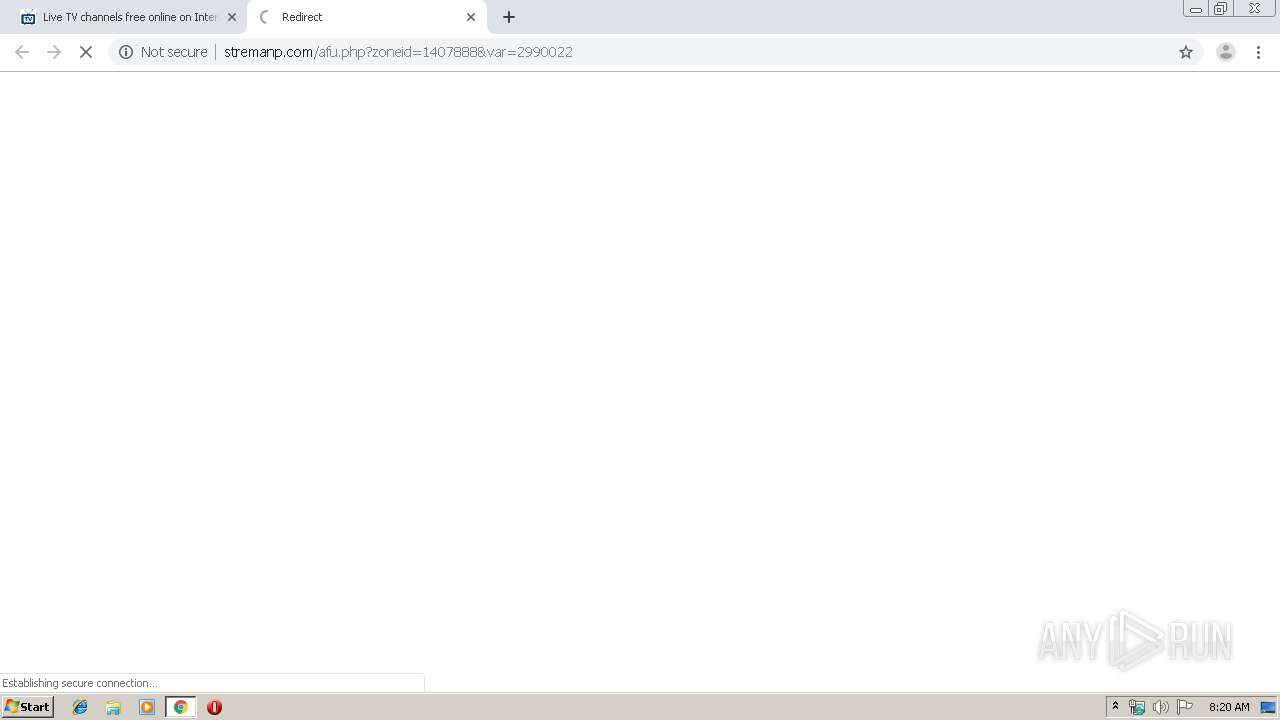
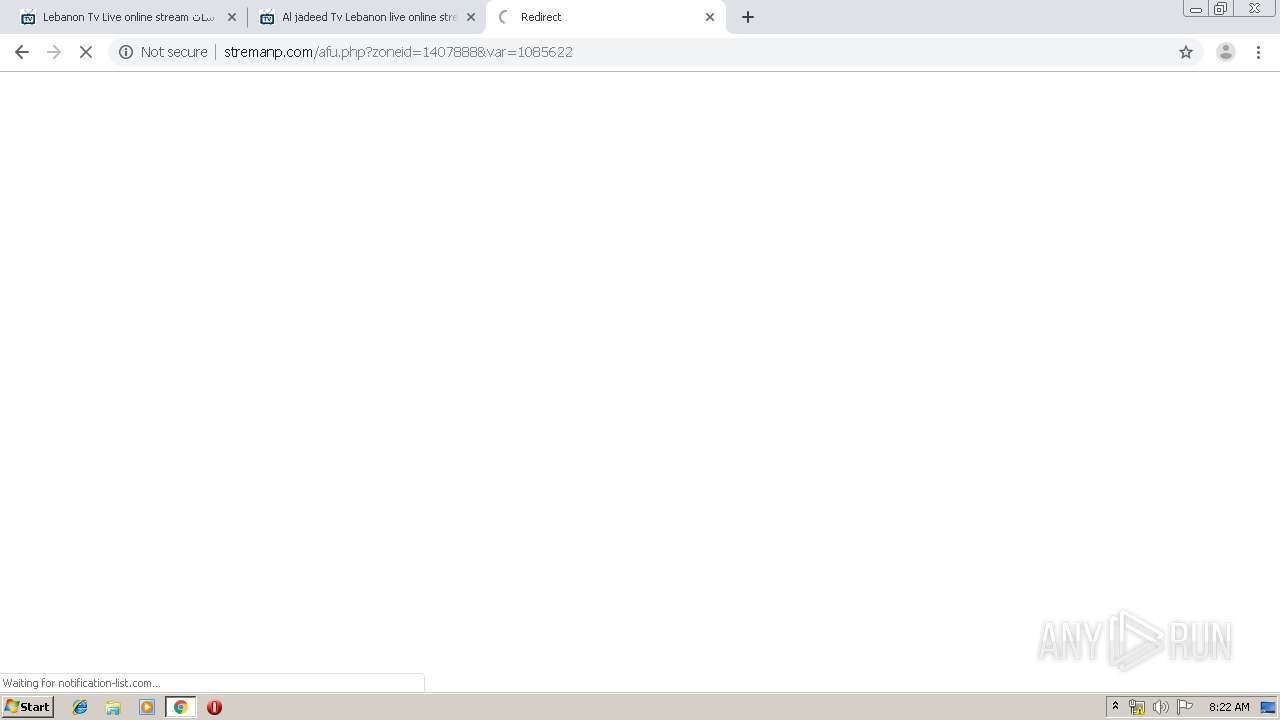
2788 | chrome.exe | 188.72.202.229:80 | stremanp.com | Webzilla B.V. | NL | unknown |
2788 | chrome.exe | 78.140.191.227:80 | inpagepush.com | Webzilla B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.fomny.com |
| unknown |
accounts.google.com |
| shared |
fomny.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
jsc.mgid.com |
| whitelisted |
sendmepush.com |
| whitelisted |
ajax.cloudflare.com |
| whitelisted |
arr-tv.com |
| unknown |
www.googletagmanager.com |
| whitelisted |