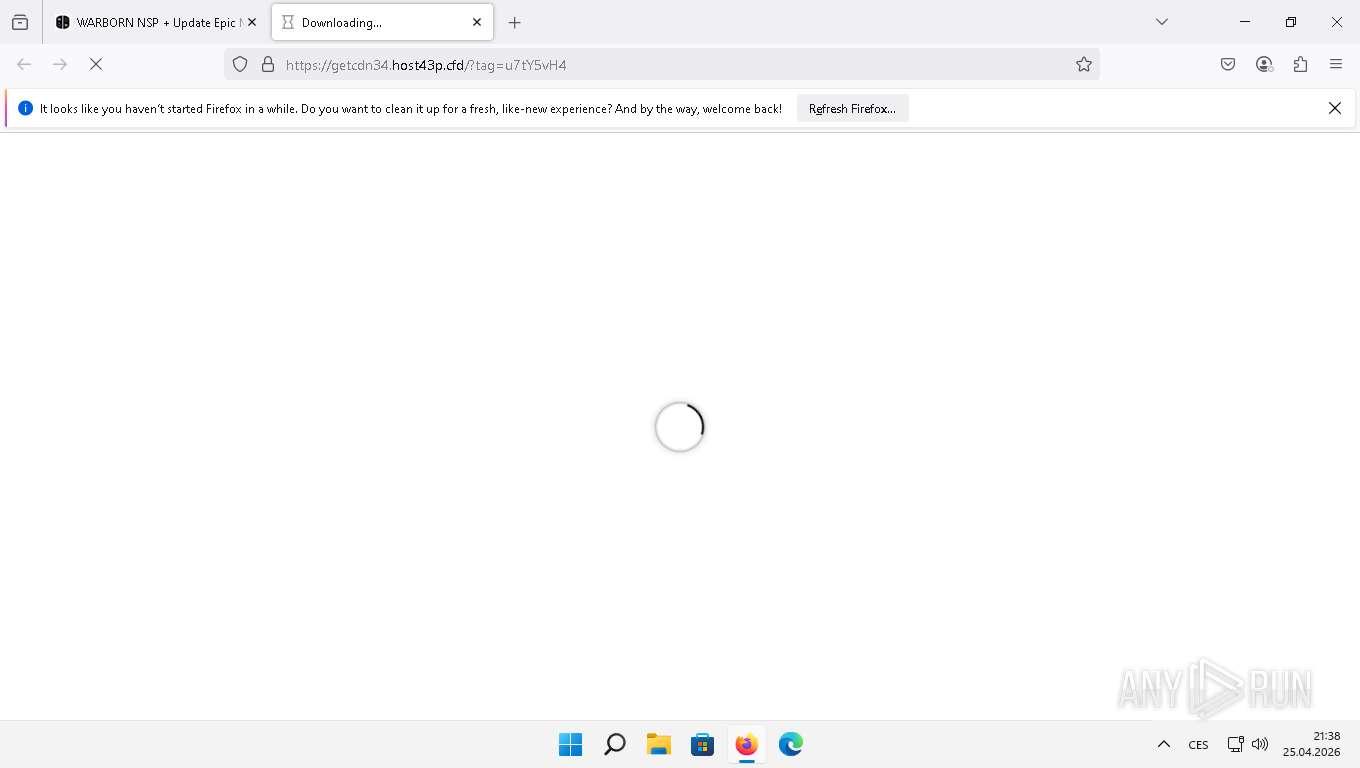
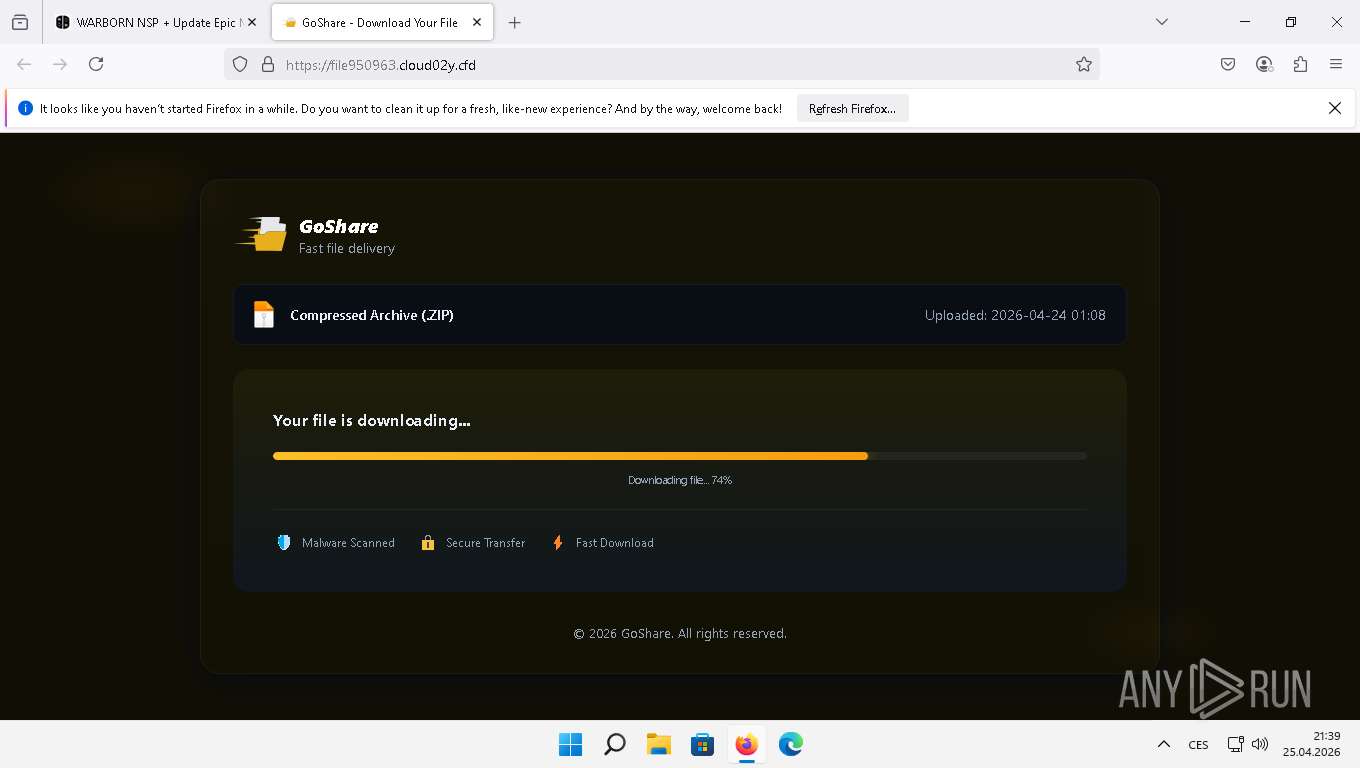
| URL: | https://nxbrew.me/ |
| Full analysis: | https://app.any.run/tasks/6d1ebc90-3f8e-4320-9471-15fa92f5fdb6 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 25, 2026, 19:38:14 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 565EF61F3E39E84E1FDB48C2684C69AD |
| SHA1: | 867A360A1F1723AF26F88ABB785D5B5C65337B55 |
| SHA256: | 524E8DF3C8C58A5CD23AB621276D1ABDA9233313AA39955B4820221FDA0B69F8 |
| SSDEEP: | 3:N8Q49K:2r9K |
MALICIOUS
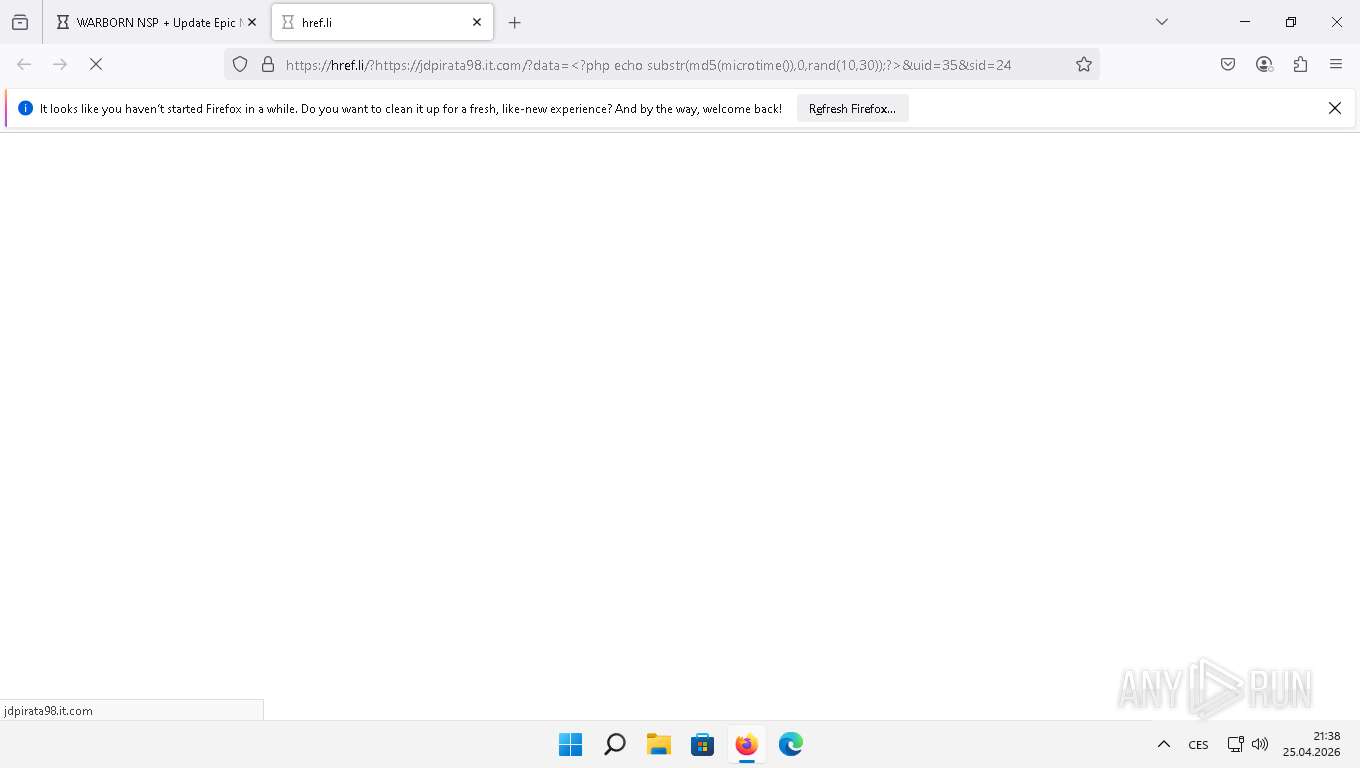
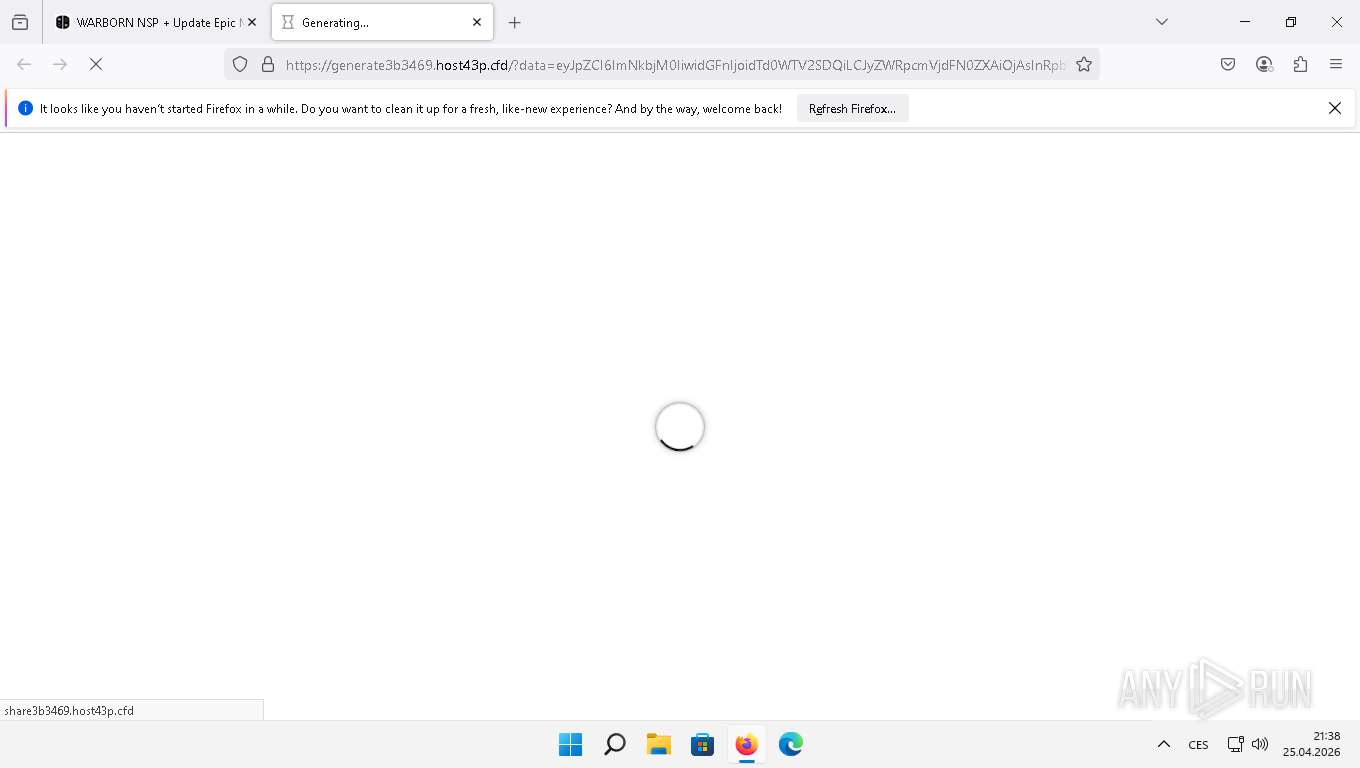
PHISHING has been detected (SURICATA)
- firefox.exe (PID: 6764)
GENERIC has been detected (SURICATA)
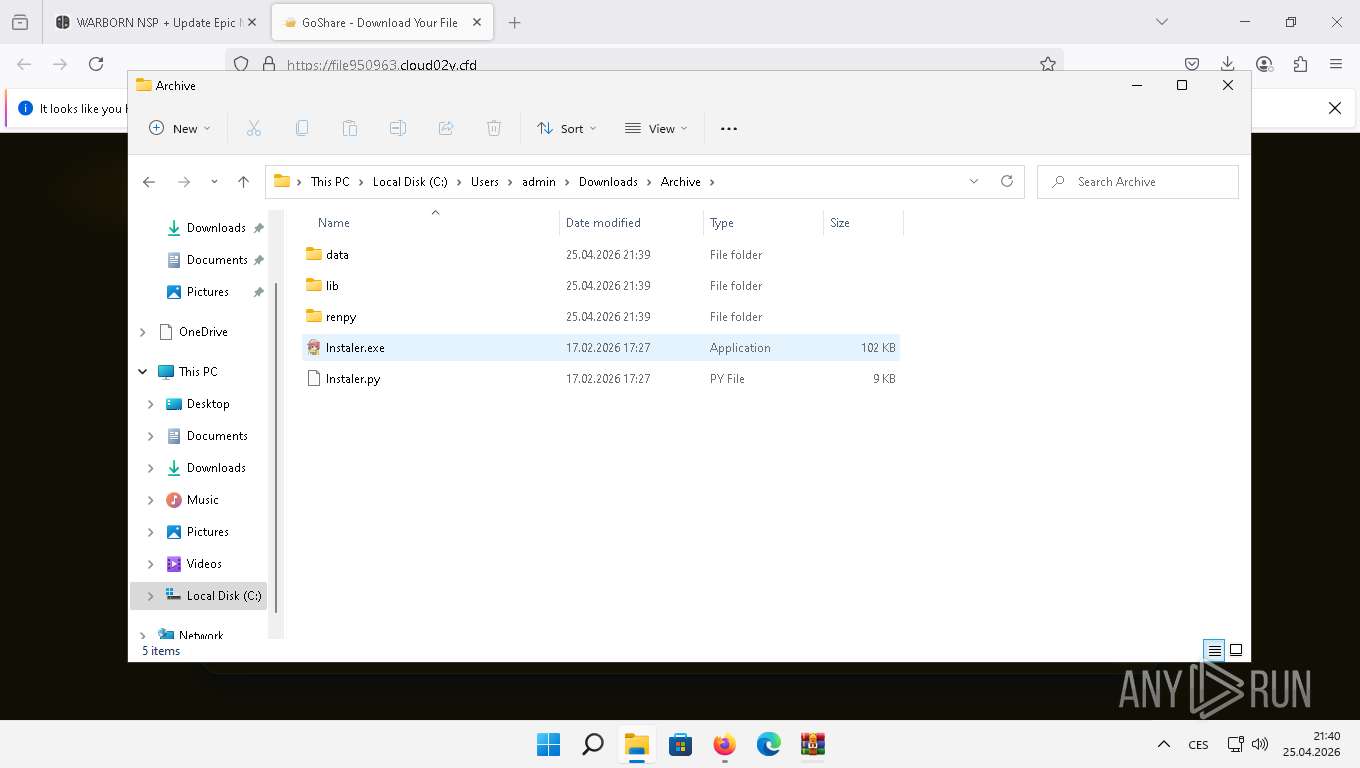
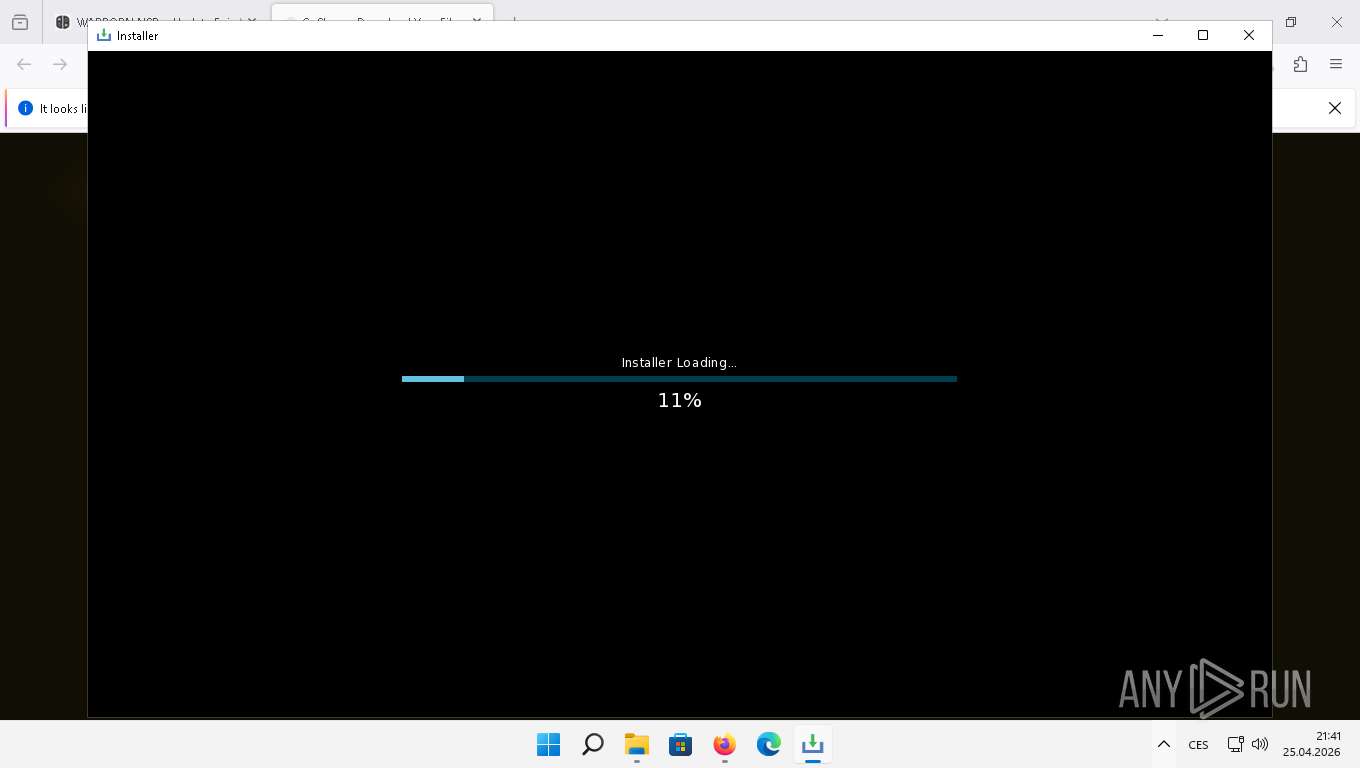
- lnstaler.exe (PID: 3376)
Executing a file with an untrusted certificate
- l6JZULP4N.exe (PID: 6924)
Generic malicious agent network activity observed
- lnstaler.exe (PID: 3376)
Actions looks like stealing of personal data
- l6JZULP4N.exe (PID: 6924)
Steals credentials from Web Browsers
- l6JZULP4N.exe (PID: 6924)
VIDAR has been detected (YARA)
- l6JZULP4N.exe (PID: 6924)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3648)
Creates scheduled task from XML file
- powershell.exe (PID: 3648)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 3648)
Run PowerShell with an invisible window
- powershell.exe (PID: 2408)
Execute application with conhost.exe as parent process
- powershell.exe (PID: 2408)
Changes powershell execution policy (Bypass)
- conhost.exe (PID: 1220)
ETHERHIDING has been detected (SURICATA)
- CheckNetIsolation.exe (PID: 1332)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8160)
- cmd.exe (PID: 2196)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 3264)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 5608)
- cmd.exe (PID: 3932)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2196)
- cmd.exe (PID: 3932)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 5608)
- l6JZULP4N.exe (PID: 6924)
- conhost.exe (PID: 1220)
- powershell.exe (PID: 2408)
Executes application which crashes
- lnstaler.exe (PID: 4732)
Reads the Internet Settings
- WerFault.exe (PID: 1672)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 6132)
- powershell.exe (PID: 6852)
- powershell.exe (PID: 4556)
- powershell.exe (PID: 8076)
- lnstaler.exe (PID: 3376)
- powershell.exe (PID: 3648)
- powershell.exe (PID: 2408)
- CheckNetIsolation.exe (PID: 1332)
Accesses local storage devices (Win32_LogicalDisk) (SCRIPT)
- powershell.exe (PID: 4556)
Checks for external IP
- lnstaler.exe (PID: 3376)
- svchost.exe (PID: 1736)
Possible stealing from browsers
- l6JZULP4N.exe (PID: 6924)
Searches for installed software
- l6JZULP4N.exe (PID: 6924)
Browser launch with unusual user-data-dir
- chrome.exe (PID: 4408)
- chrome.exe (PID: 5352)
- chrome.exe (PID: 6228)
- chrome.exe (PID: 1804)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 7624)
- chrome.exe (PID: 644)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 6844)
- chrome.exe (PID: 6508)
- chrome.exe (PID: 964)
- chrome.exe (PID: 7724)
- chrome.exe (PID: 4860)
- chrome.exe (PID: 7356)
- chrome.exe (PID: 1792)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 4184)
- chrome.exe (PID: 4044)
Possible stealing from crypto wallets
- l6JZULP4N.exe (PID: 6924)
Possible stealing of messenger data
- l6JZULP4N.exe (PID: 6924)
Possible stealing of FTP data
- l6JZULP4N.exe (PID: 6924)
Possible stealing of email data
- l6JZULP4N.exe (PID: 6924)
Possible stealing from 2fa
- l6JZULP4N.exe (PID: 6924)
Possible stealing of VPN data
- l6JZULP4N.exe (PID: 6924)
Possible stealing from password managers
- l6JZULP4N.exe (PID: 6924)
Multiple wallet extension IDs have been found
- l6JZULP4N.exe (PID: 6924)
The process bypasses the loading of PowerShell profile settings
- l6JZULP4N.exe (PID: 6924)
- conhost.exe (PID: 1220)
- powershell.exe (PID: 2408)
Executes script without checking the security policy
- powershell.exe (PID: 3648)
- powershell.exe (PID: 2408)
The process hides Powershell's copyright startup banner
- l6JZULP4N.exe (PID: 6924)
- powershell.exe (PID: 2408)
The process hide an interactive prompt from the user
- l6JZULP4N.exe (PID: 6924)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3648)
- powershell.exe (PID: 2408)
Enumerate domain computers
- powershell.exe (PID: 3648)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 3648)
- powershell.exe (PID: 2408)
Enumerate domain groups
- powershell.exe (PID: 3648)
Enumerate current domain
- powershell.exe (PID: 3648)
Enumerate domain controller
- powershell.exe (PID: 3648)
Enumerate organizational units
- powershell.exe (PID: 3648)
Bypass execution policy to execute commands
- powershell.exe (PID: 2408)
Get information on the list of running processes
- conhost.exe (PID: 1220)
The process executes via Task Scheduler
- conhost.exe (PID: 1220)
Executable content was dropped or overwritten
- csc.exe (PID: 3428)
Reads settings of System Certificates
- CheckNetIsolation.exe (PID: 1332)
Application launched itself
- powershell.exe (PID: 2408)
Potential Corporate Privacy Violation
- CheckNetIsolation.exe (PID: 1332)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 2408)
CSC.EXE is used to compile C# code
- csc.exe (PID: 3428)
INFO
Application launched itself
- firefox.exe (PID: 1888)
- firefox.exe (PID: 6764)
- chrome.exe (PID: 4408)
- chrome.exe (PID: 5352)
- chrome.exe (PID: 6228)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 1804)
- chrome.exe (PID: 7624)
- chrome.exe (PID: 644)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 6844)
- chrome.exe (PID: 6508)
- chrome.exe (PID: 964)
- chrome.exe (PID: 1792)
- chrome.exe (PID: 4860)
- chrome.exe (PID: 7356)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 4184)
- chrome.exe (PID: 7724)
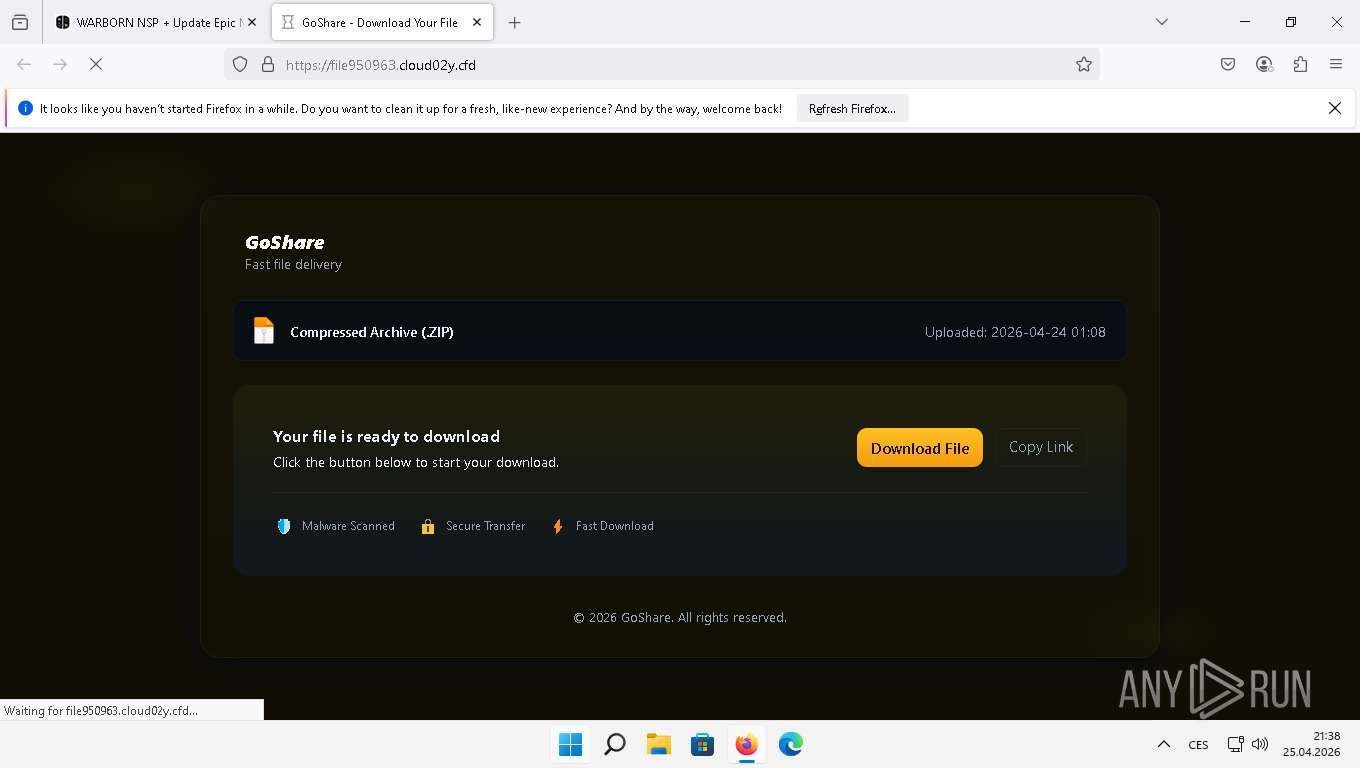
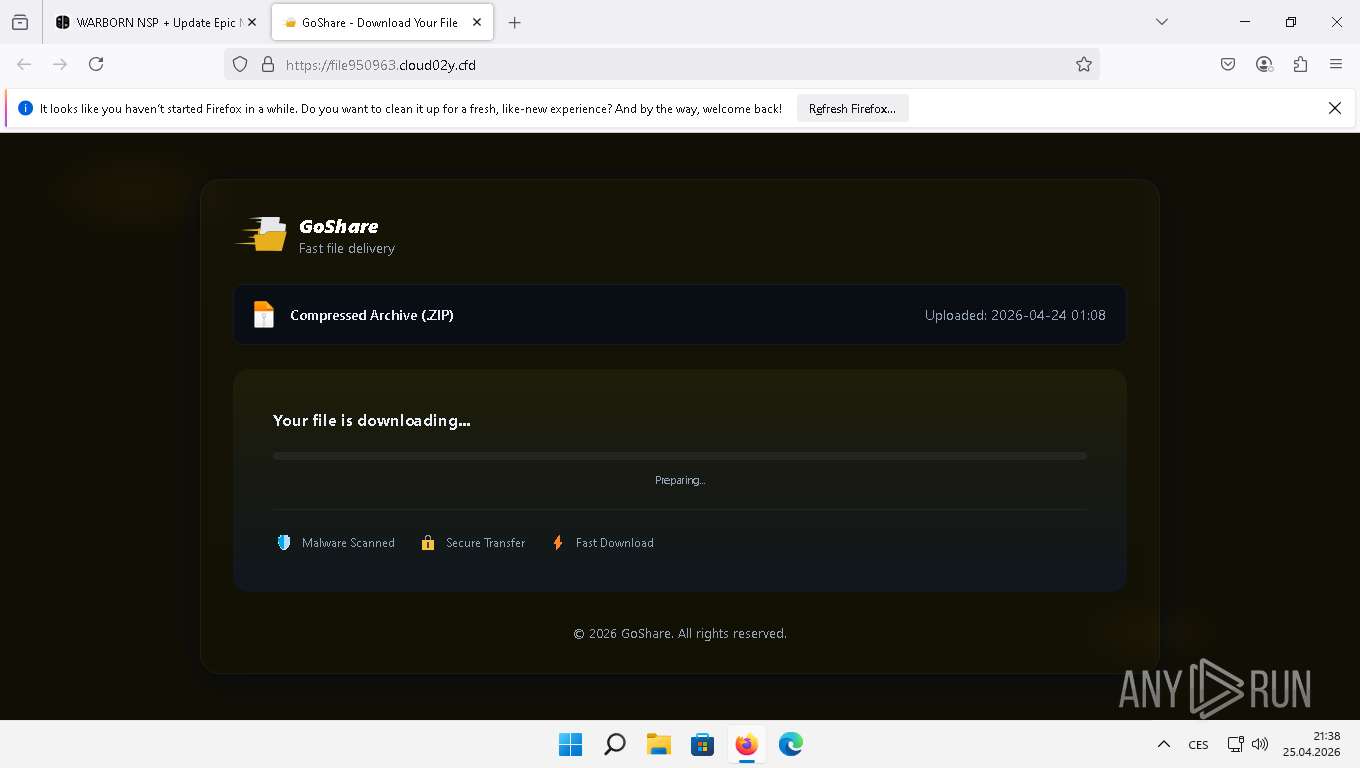
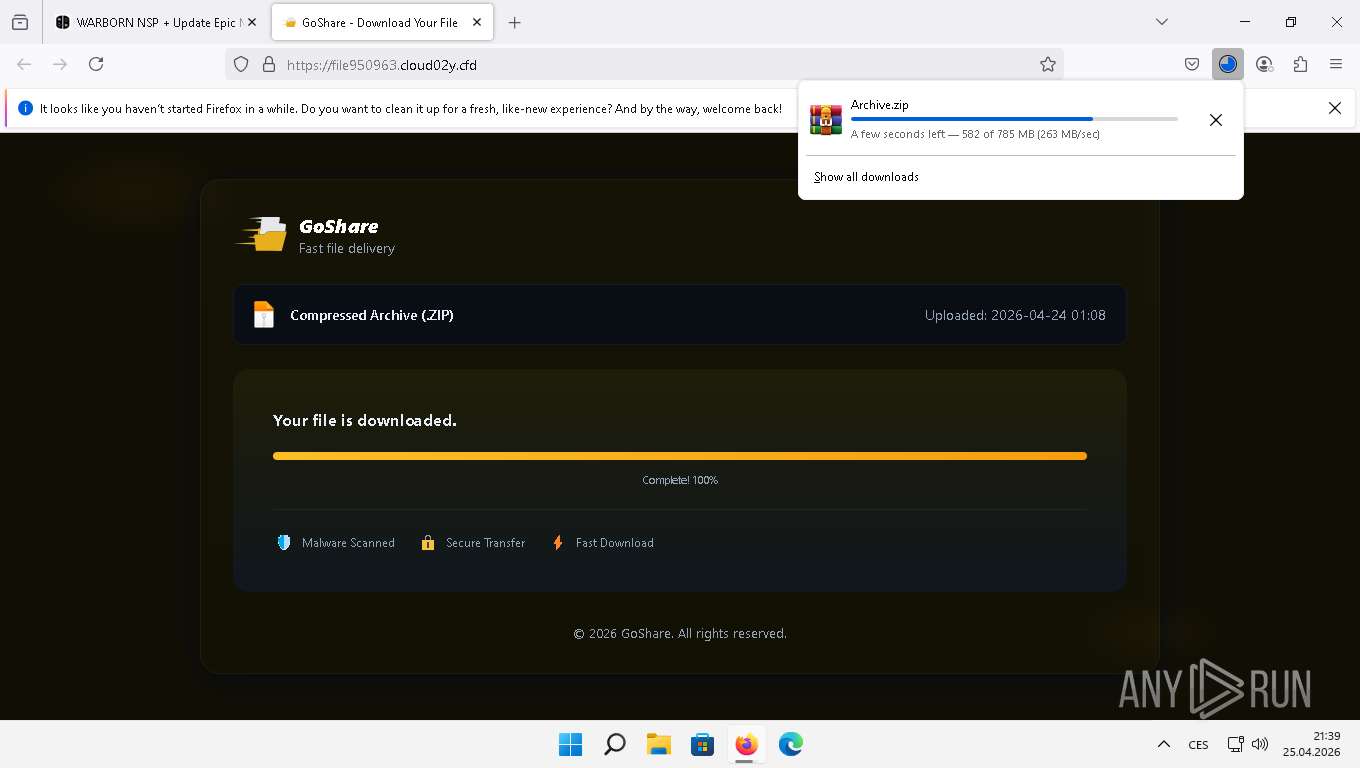
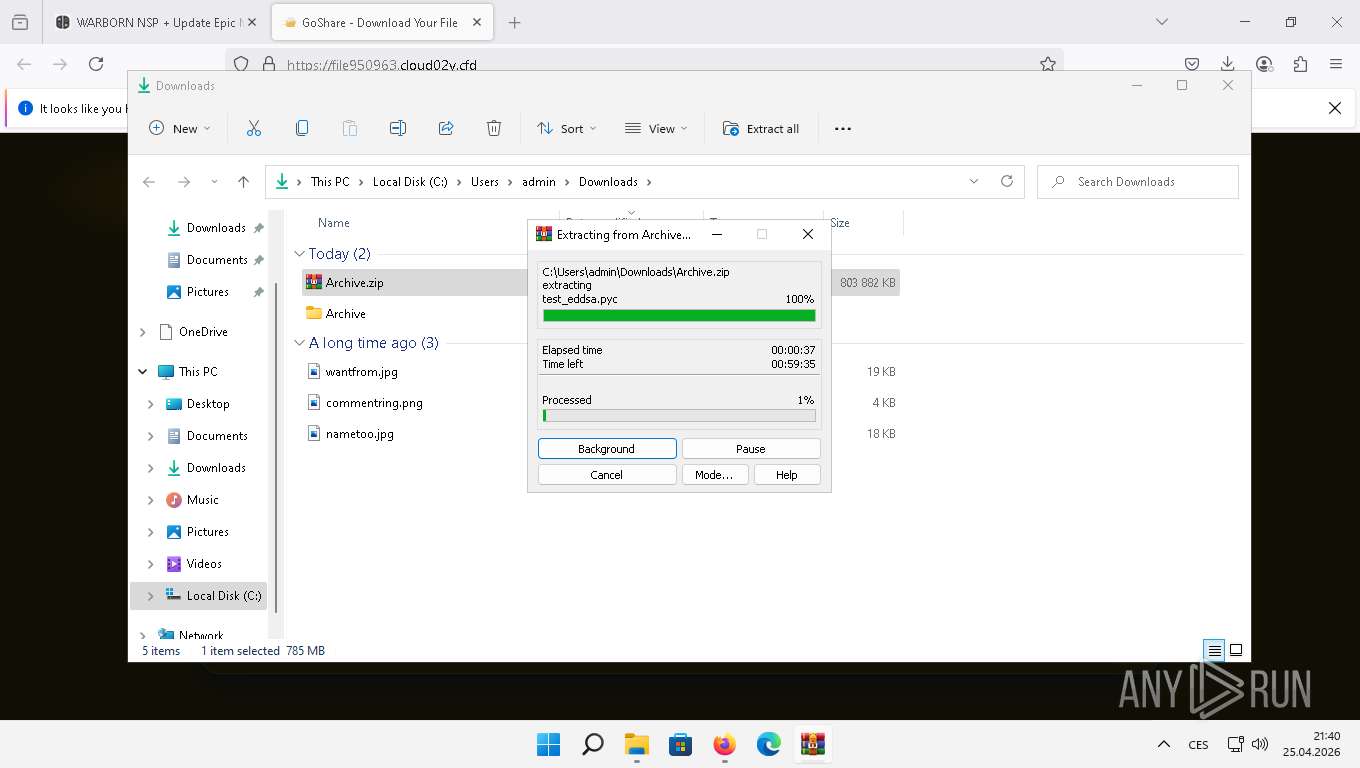
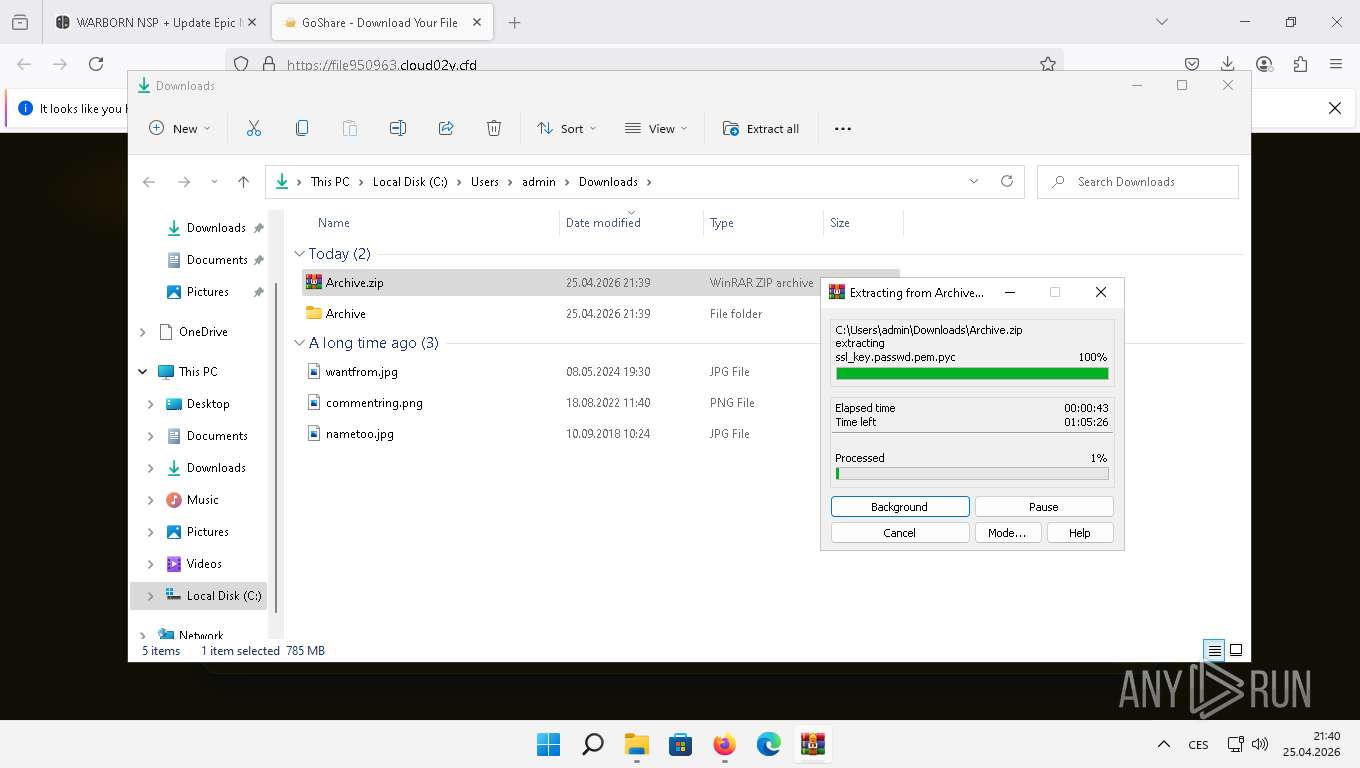
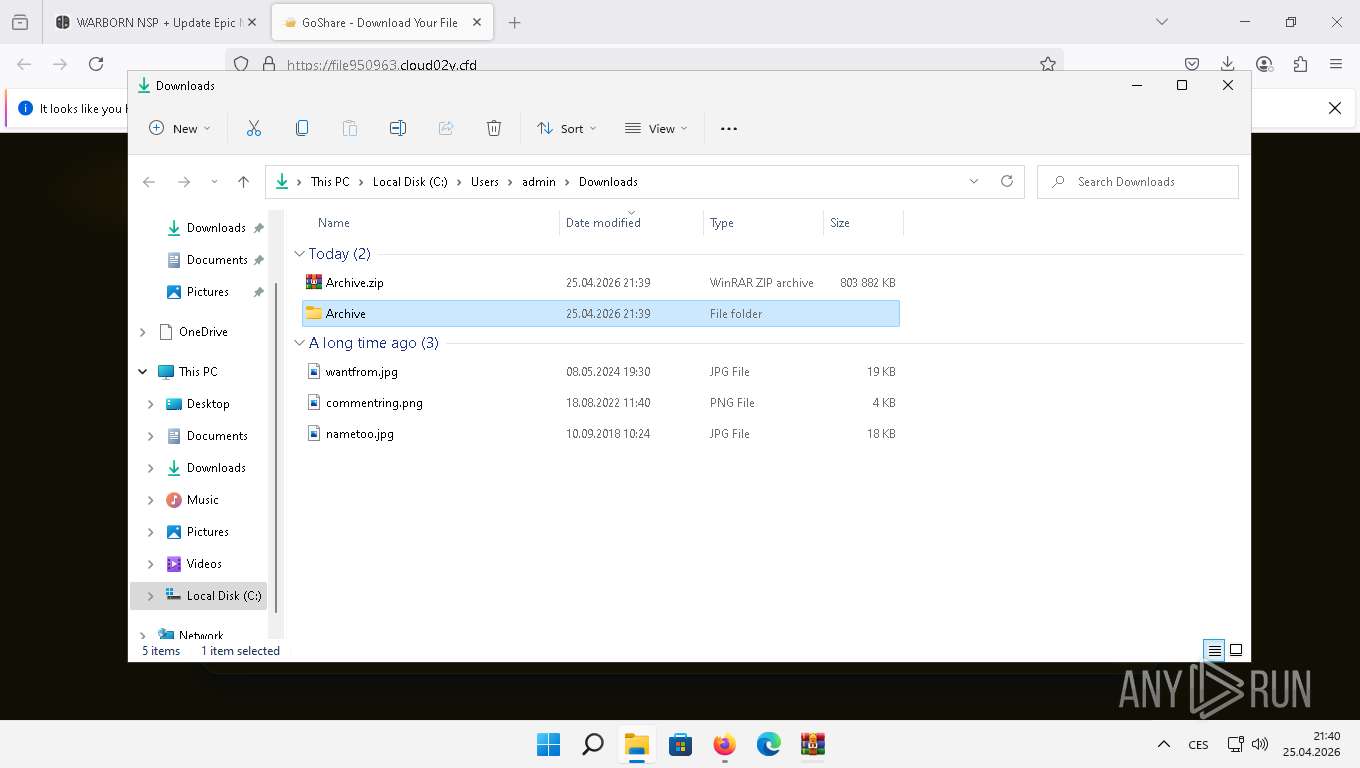
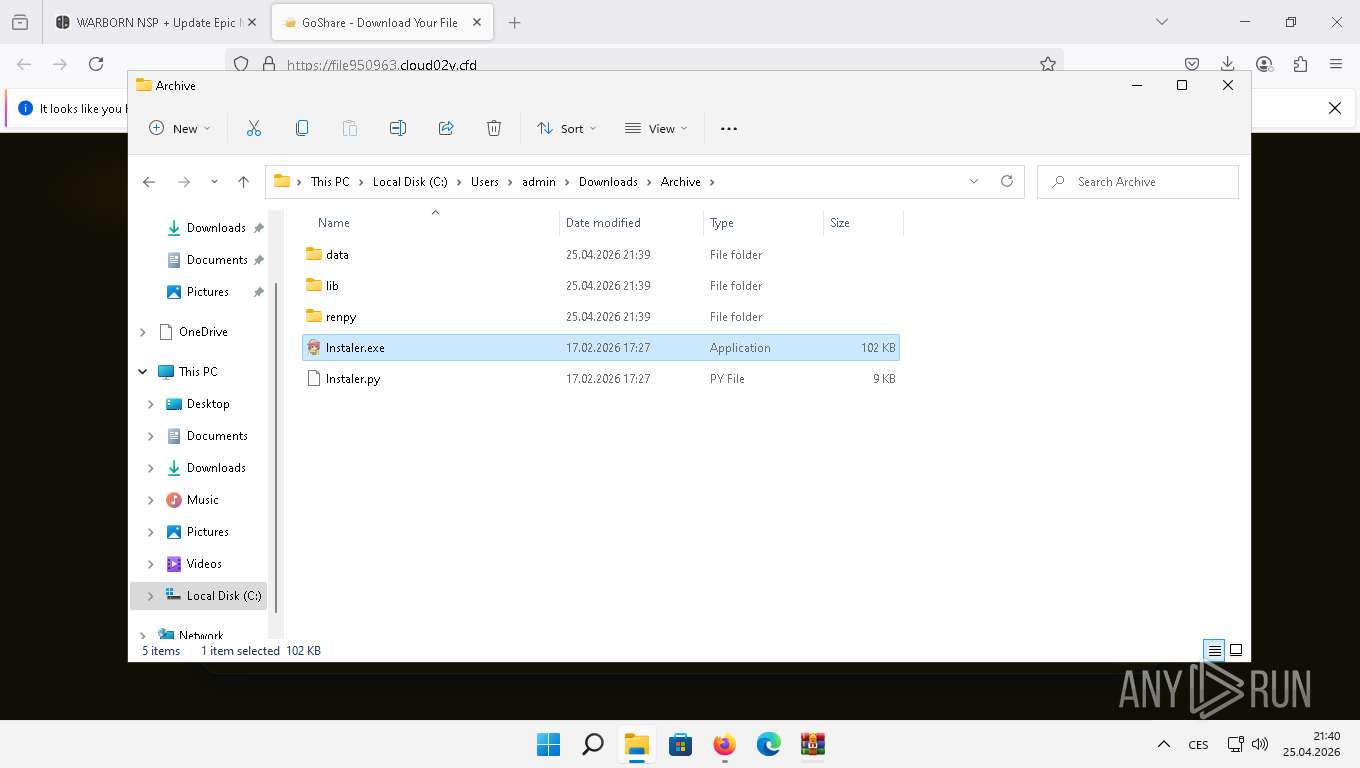
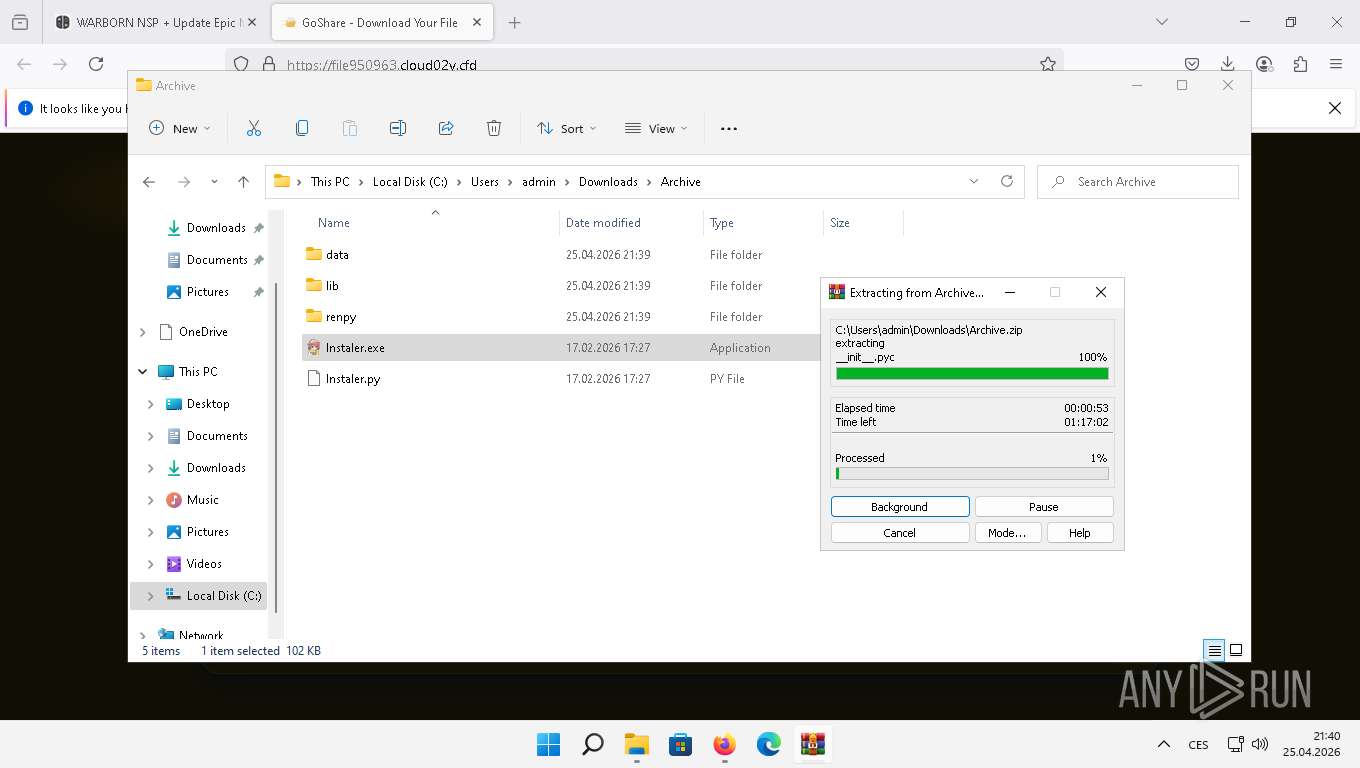
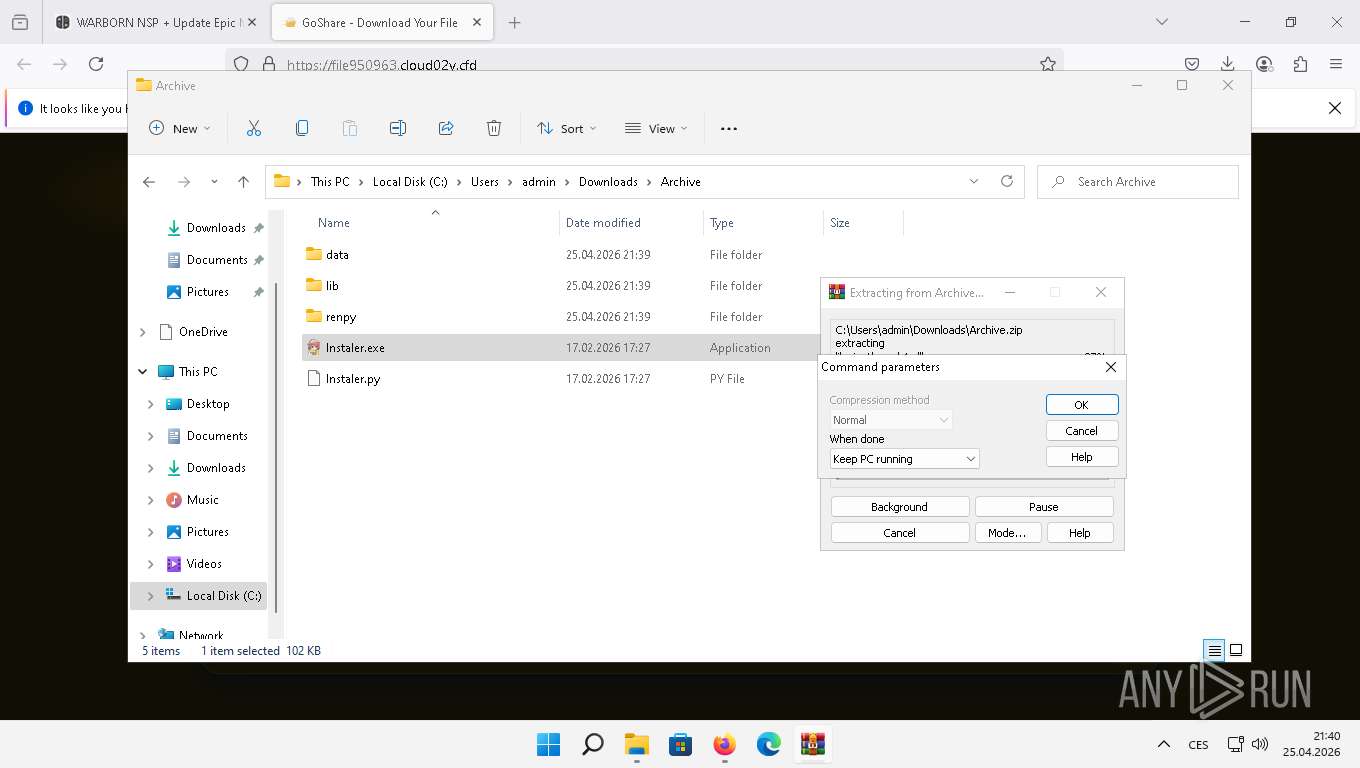
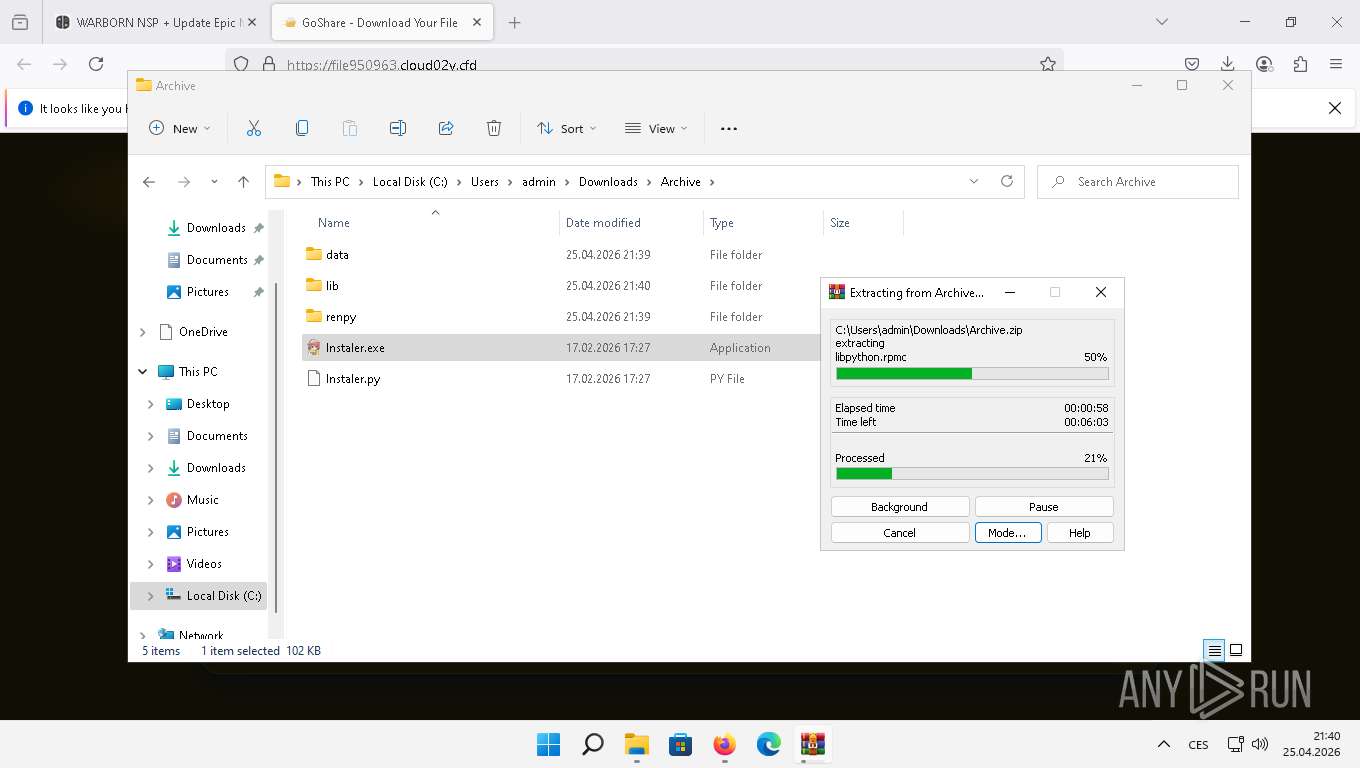
Executable content was dropped or overwritten
- firefox.exe (PID: 6764)
- WinRAR.exe (PID: 1076)
The sample compiled with english language support
- firefox.exe (PID: 6764)
- WinRAR.exe (PID: 1076)
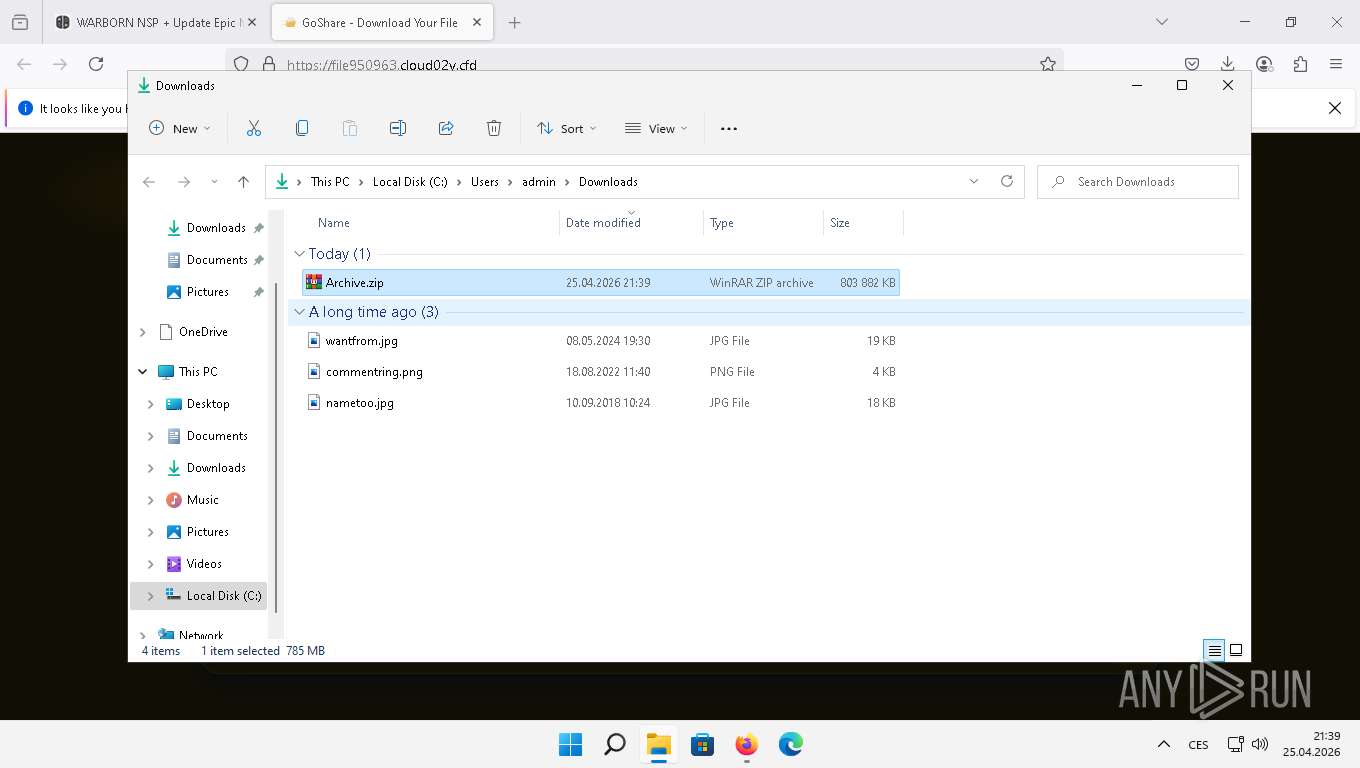
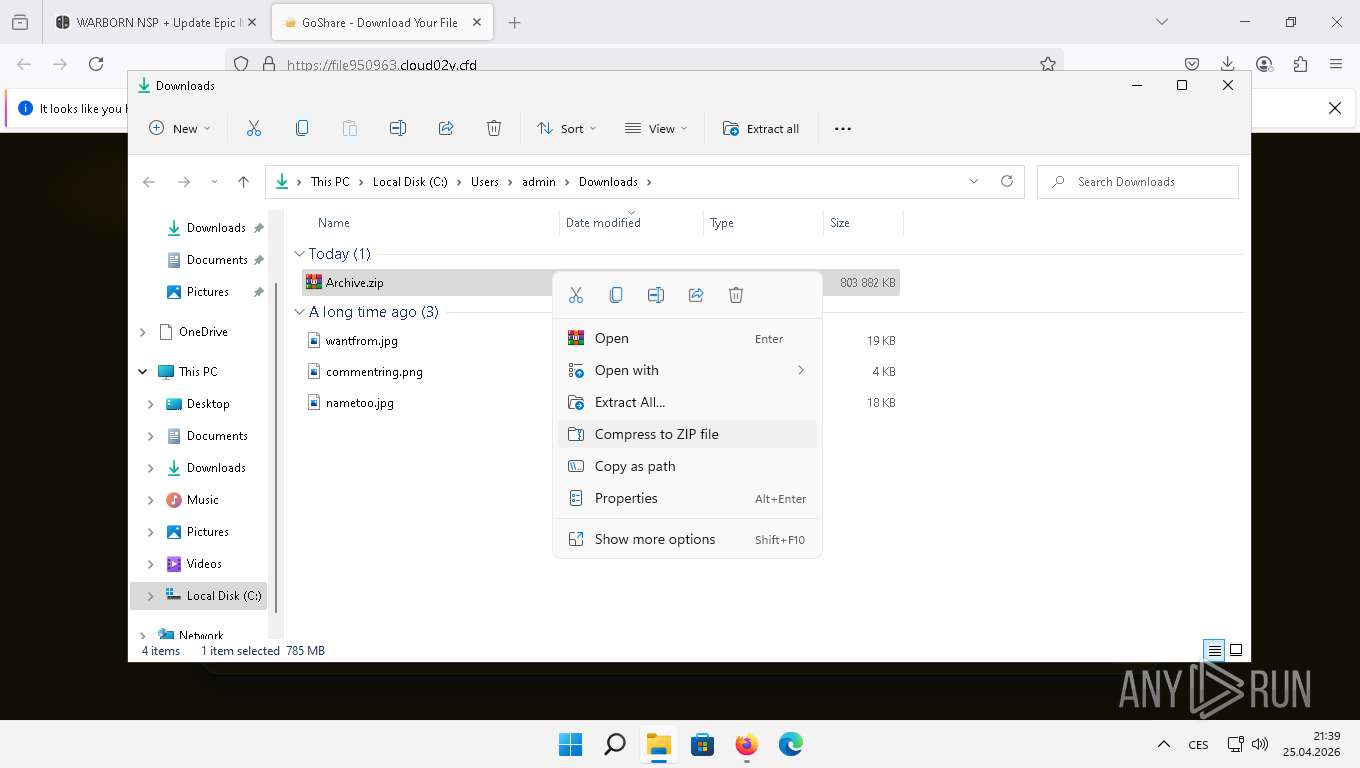
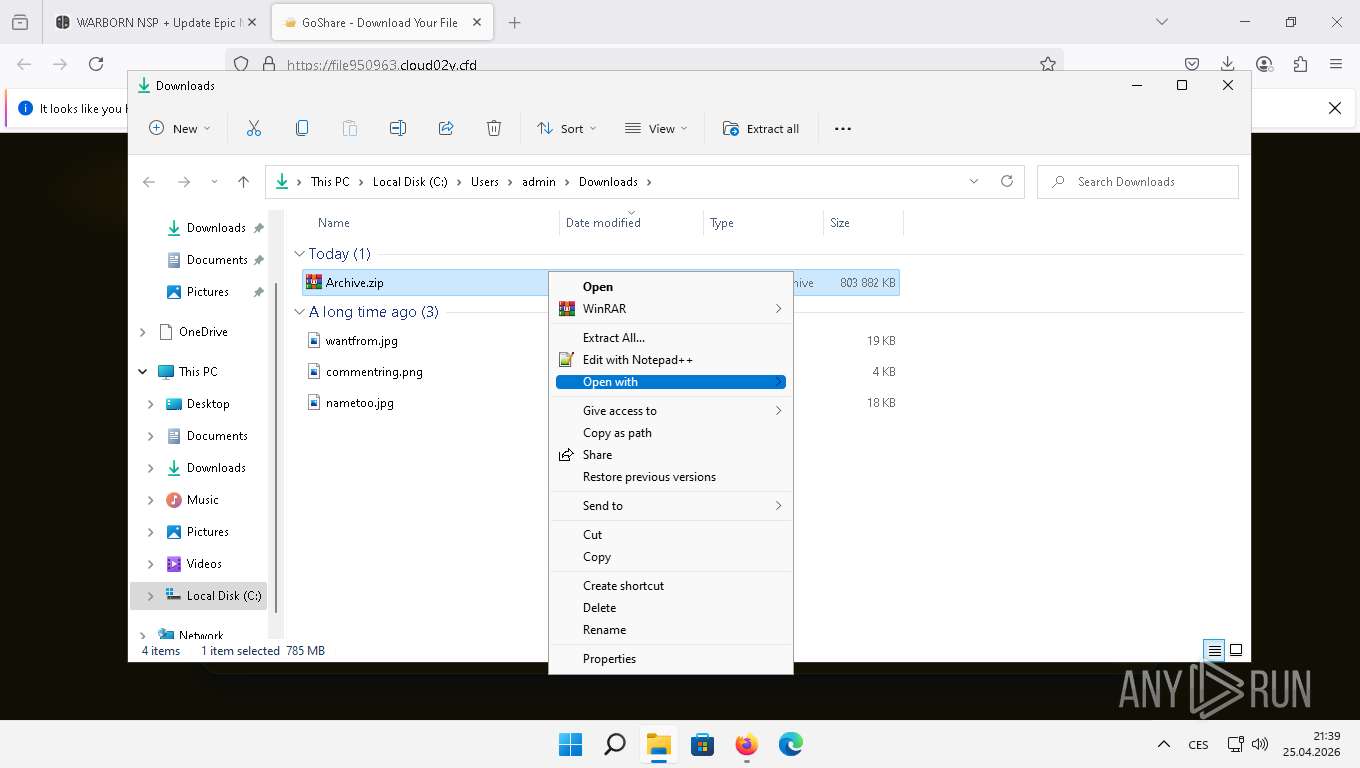
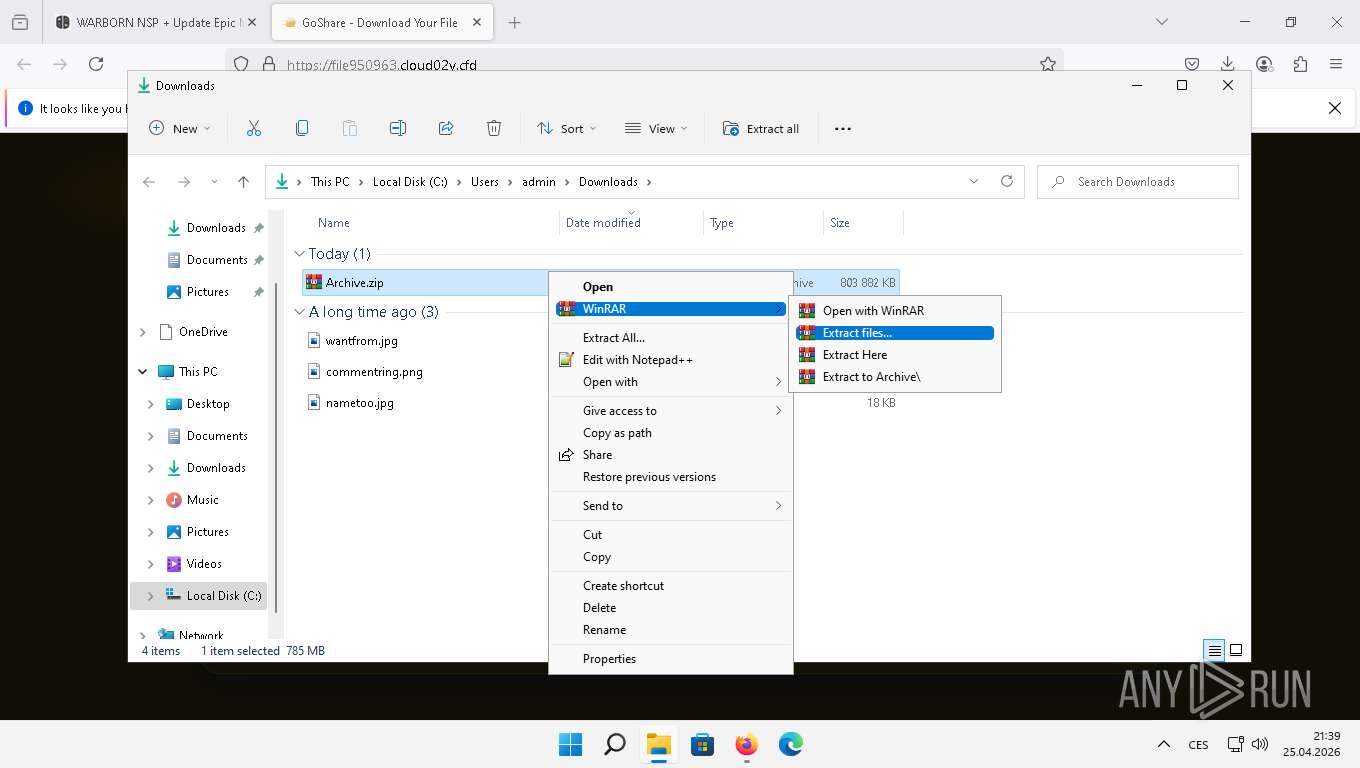
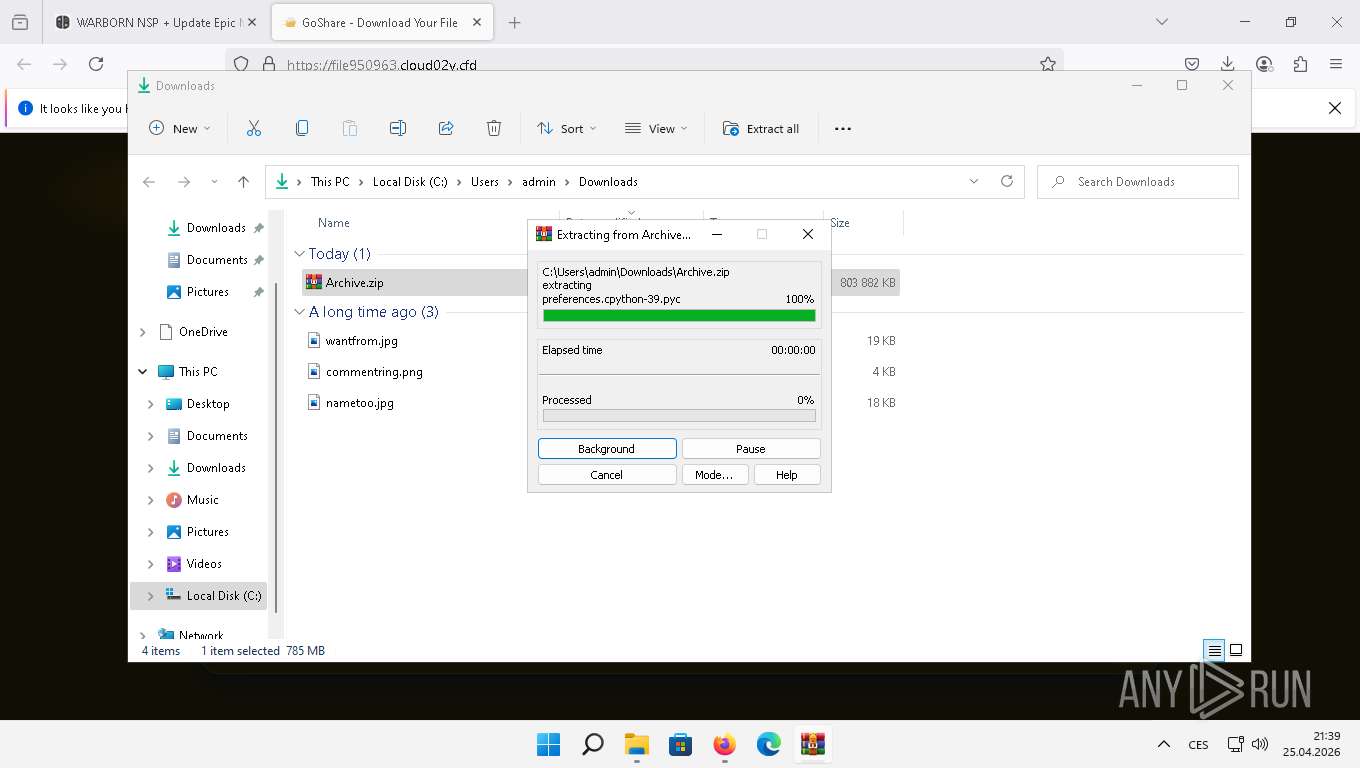
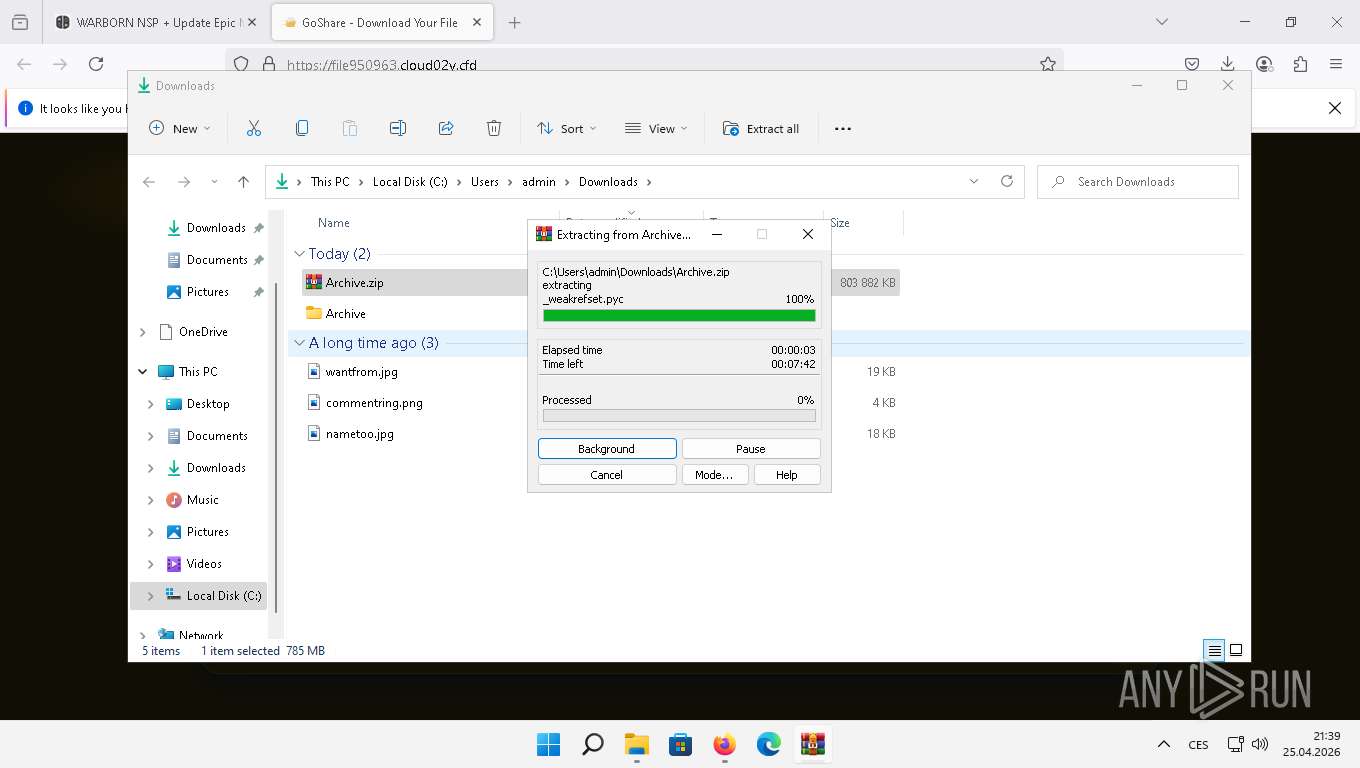
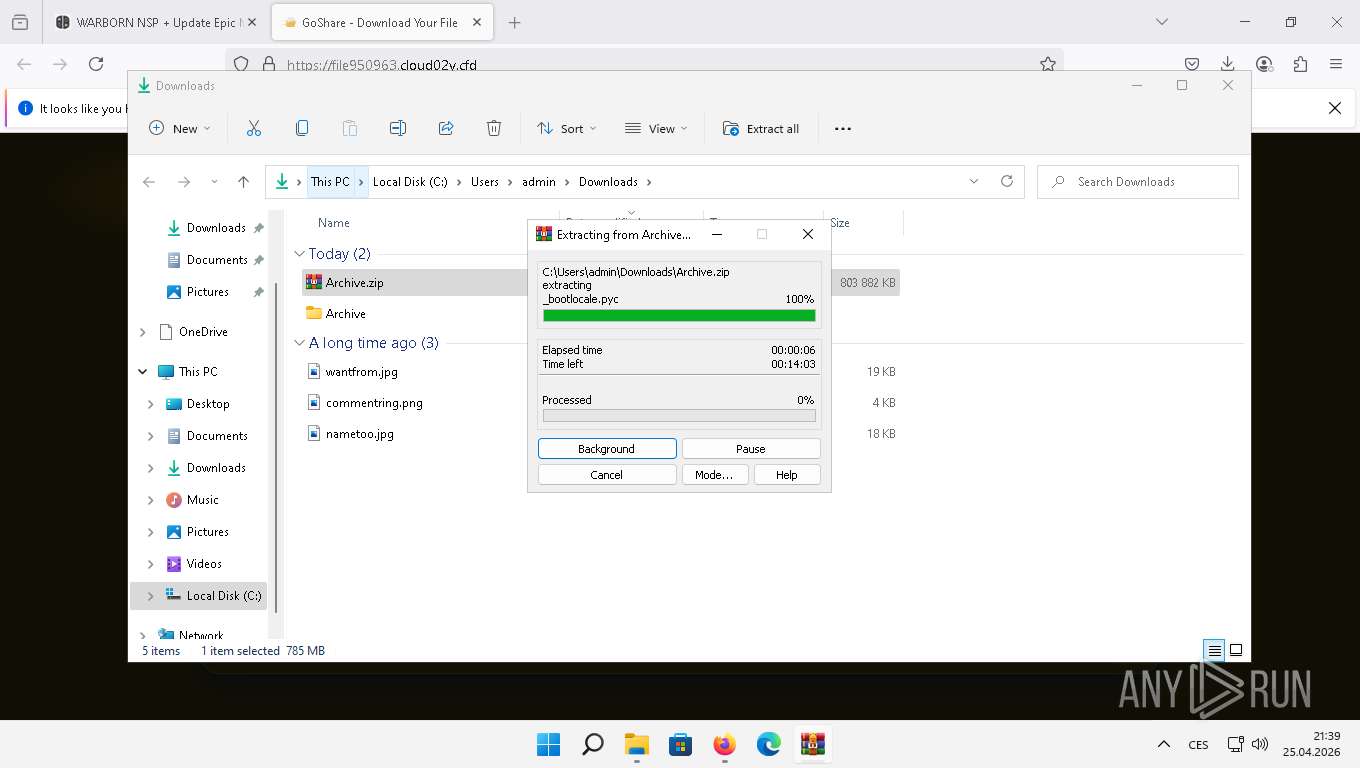
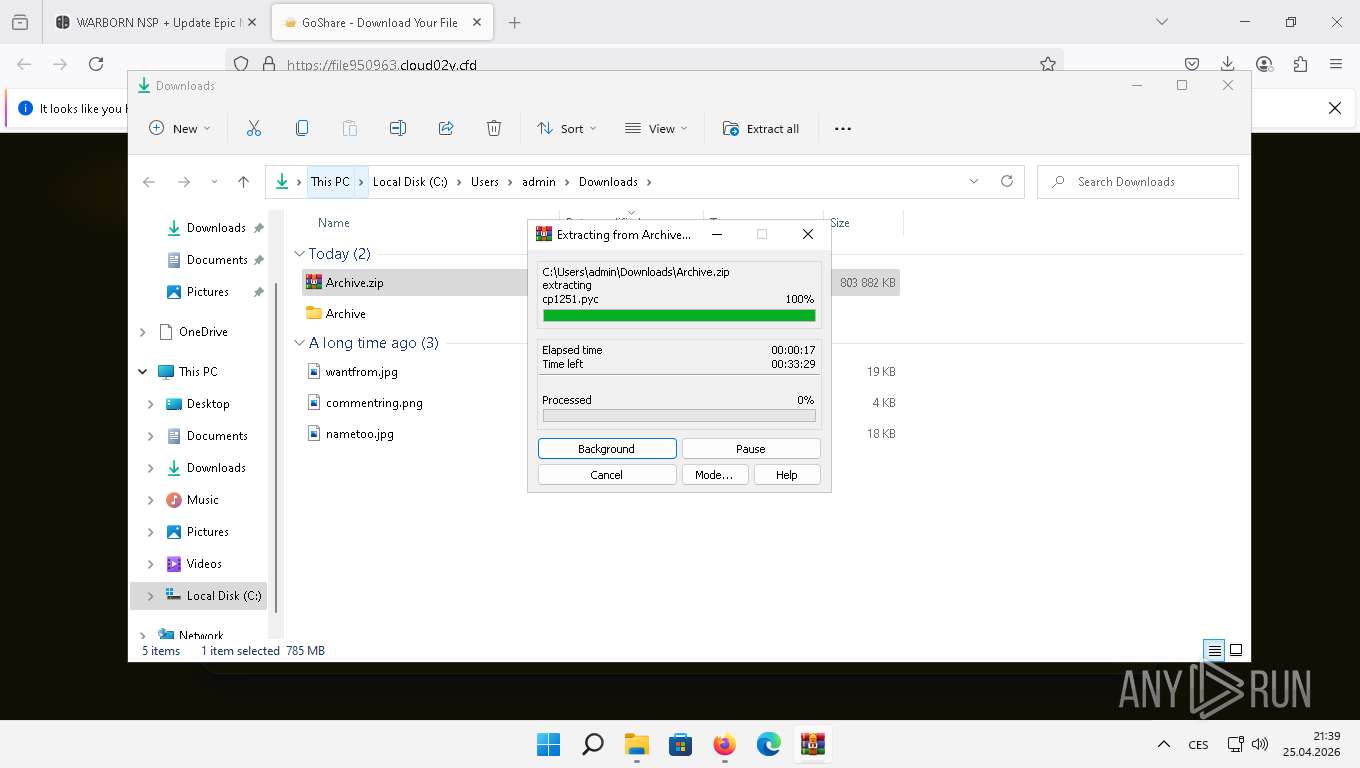
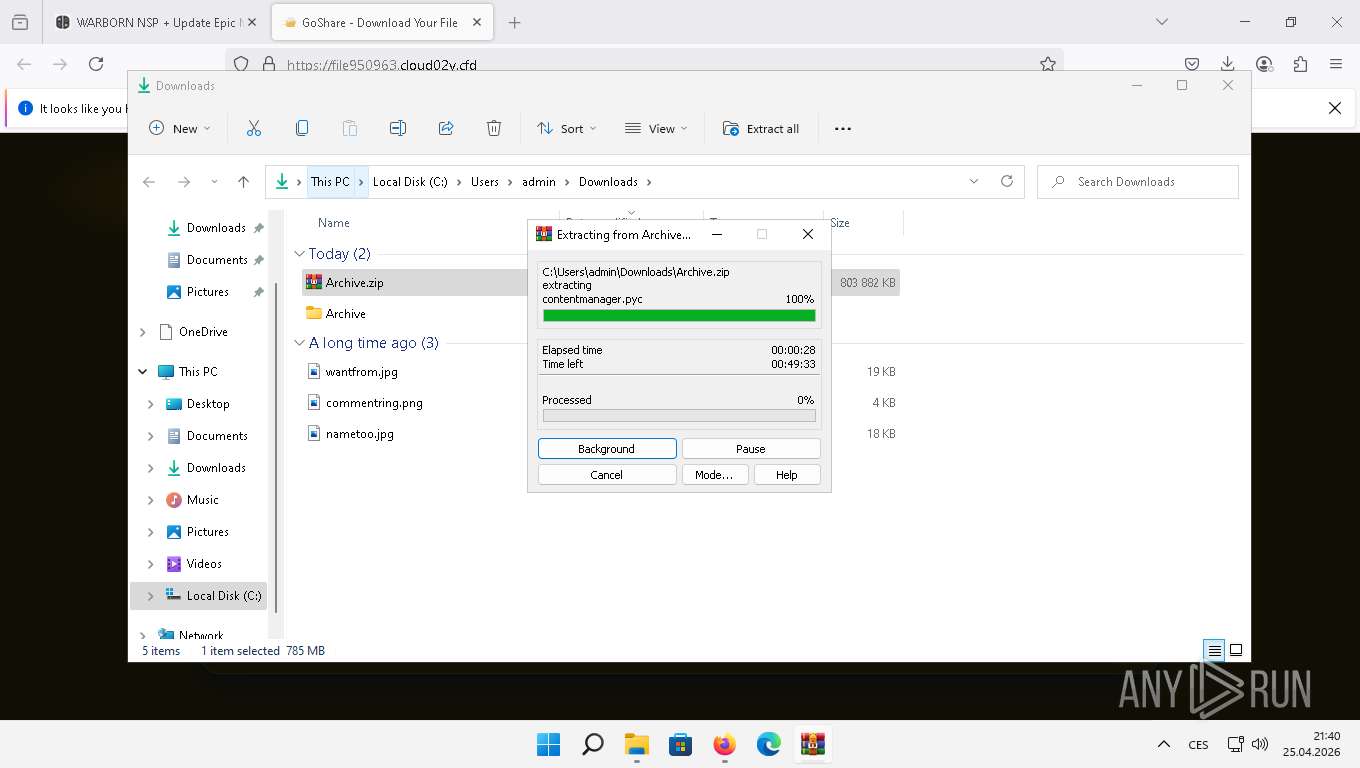
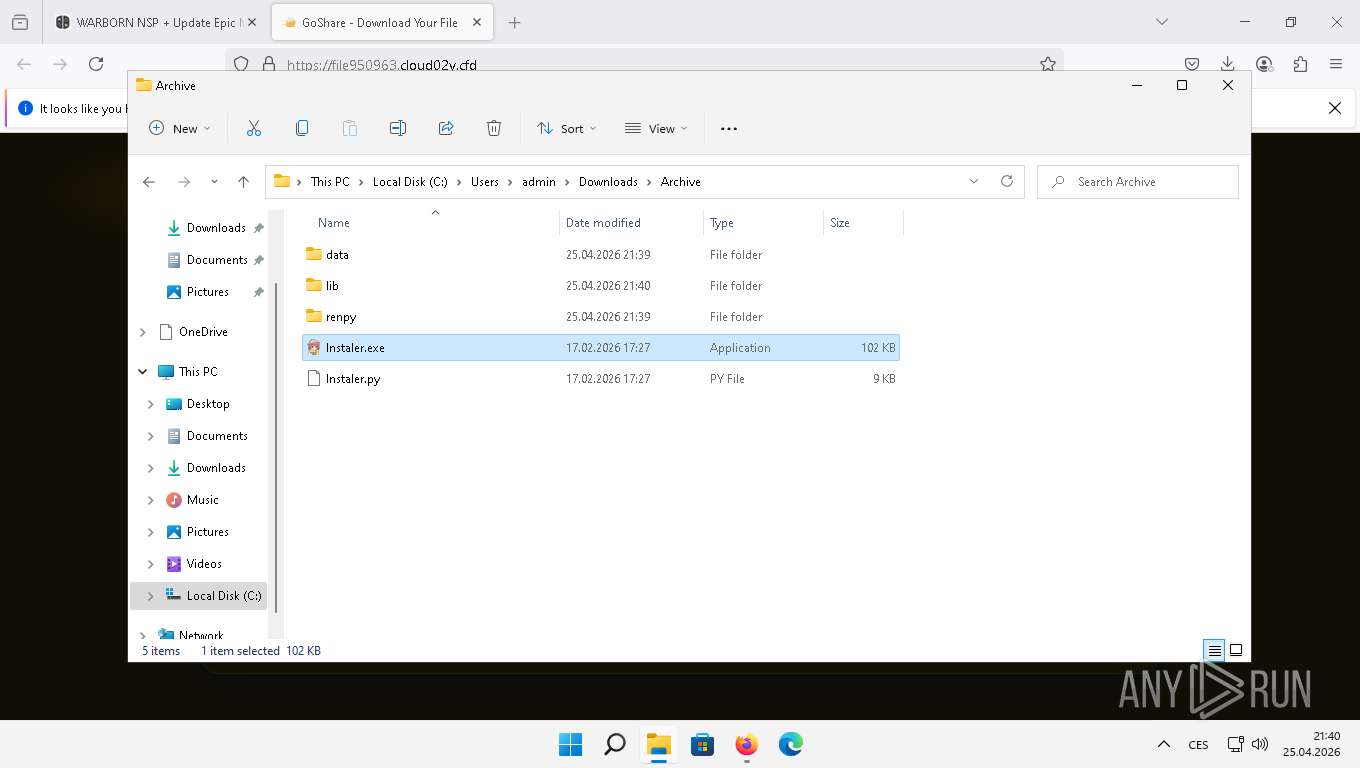
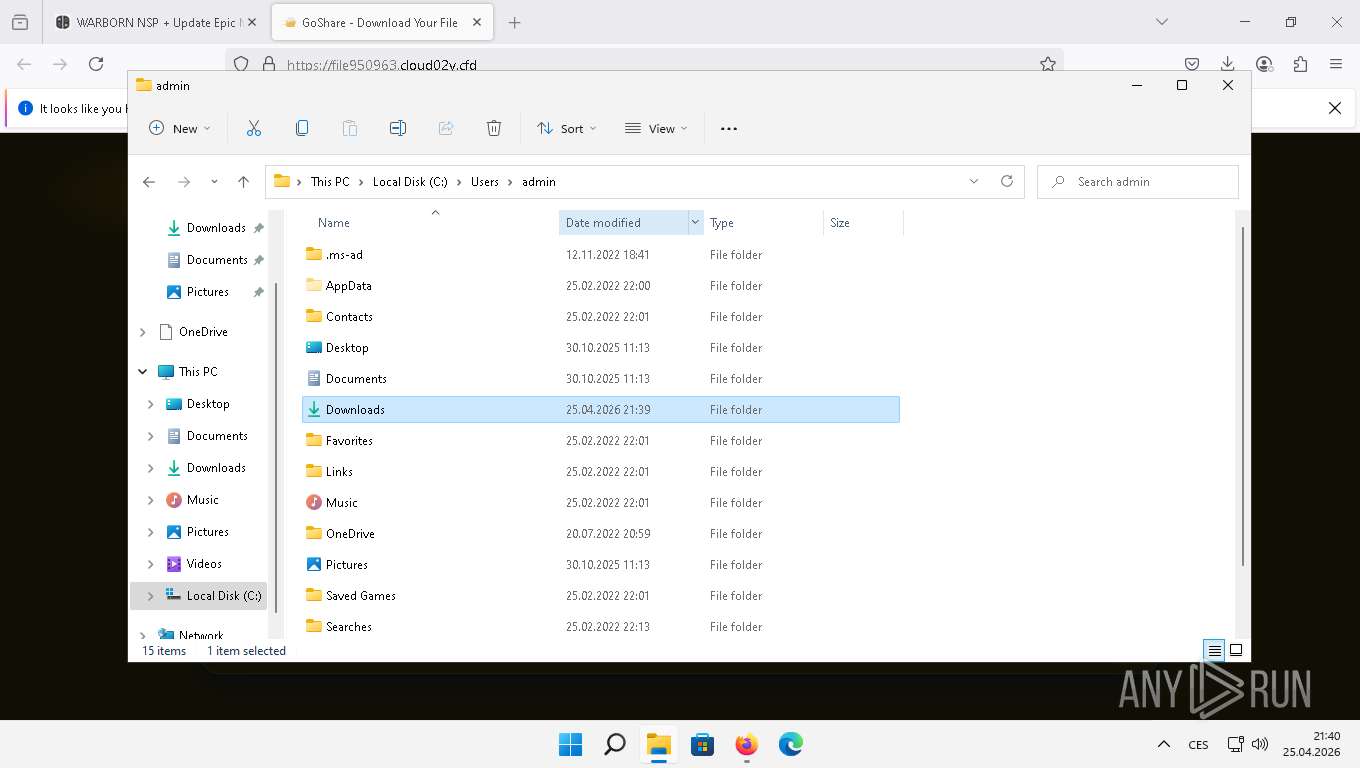
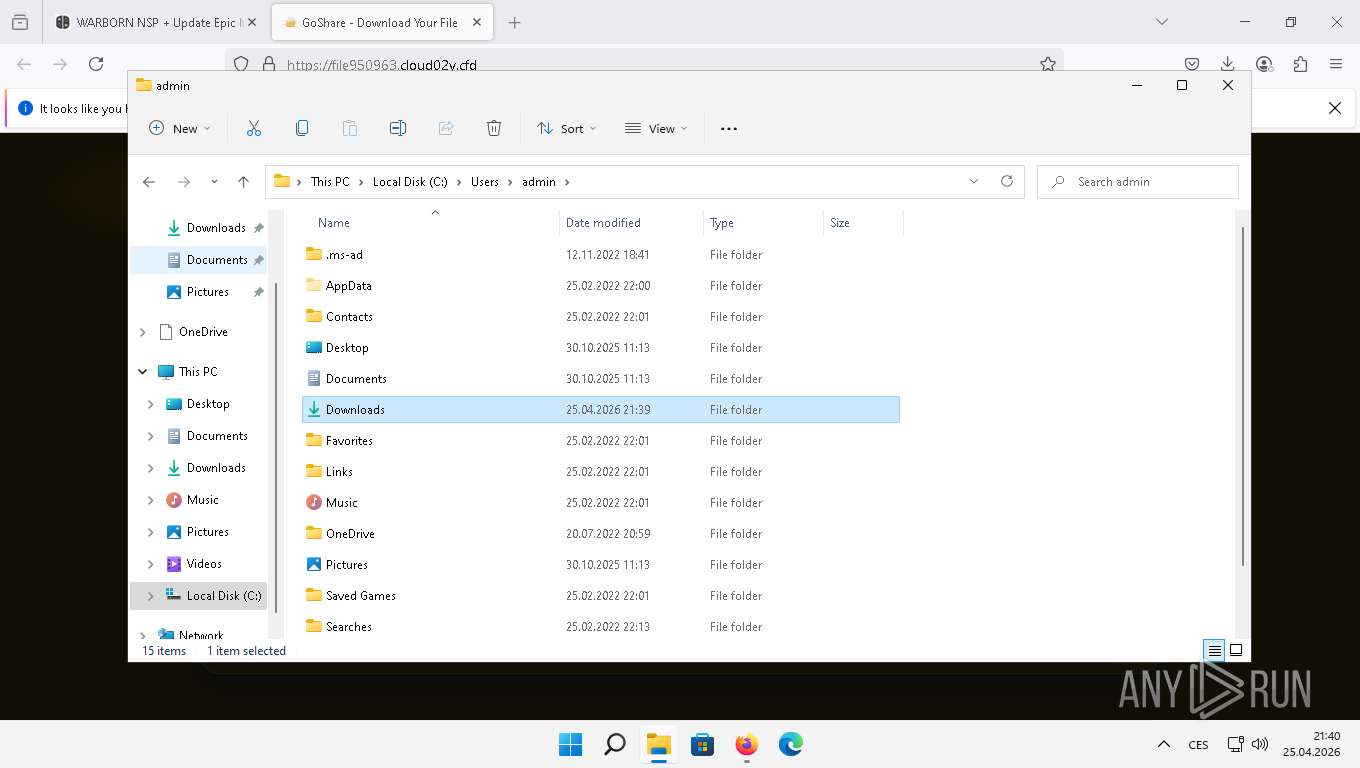
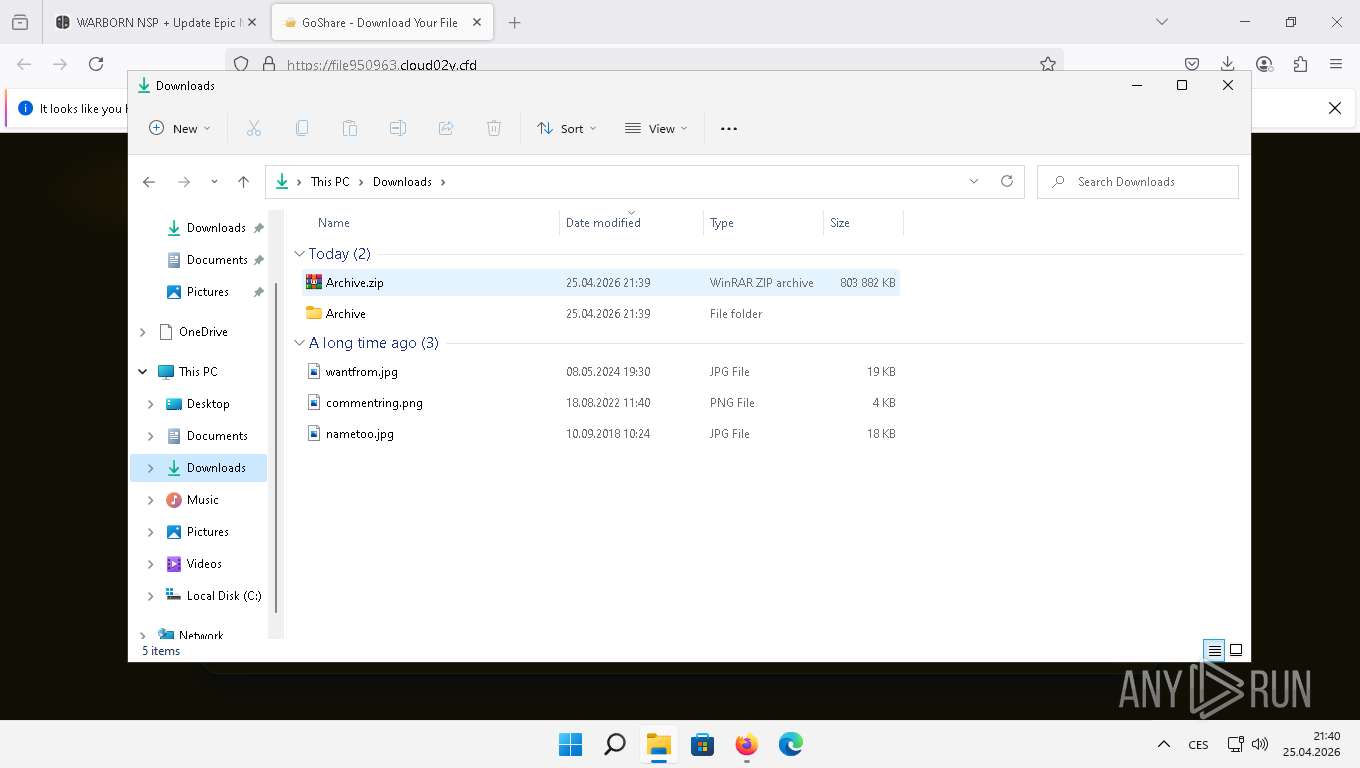
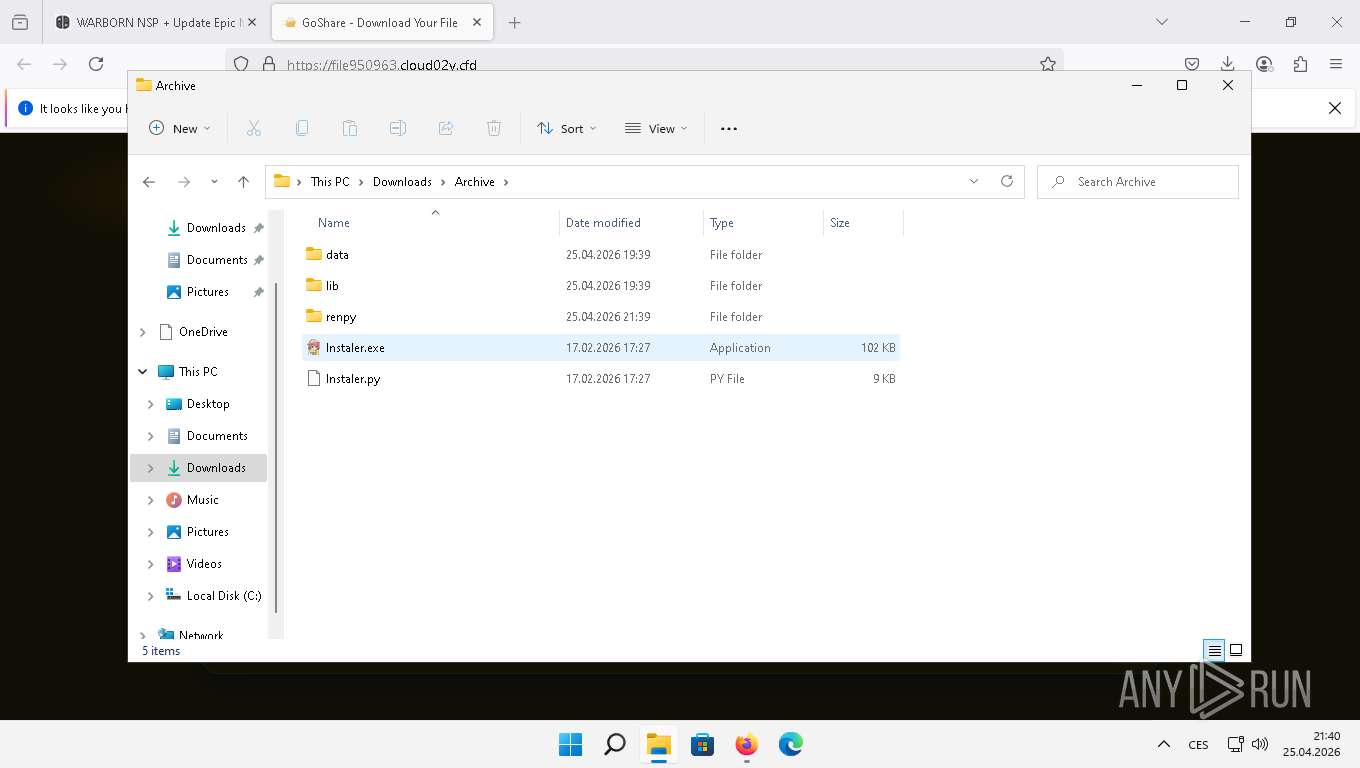
Manual execution by a user
- WinRAR.exe (PID: 1076)
- lnstaler.exe (PID: 4732)
- lnstaler.exe (PID: 3376)
There is functionality for taking screenshot (YARA)
- dllhost.exe (PID: 3336)
- lnstaler.exe (PID: 3376)
Checks supported languages
- lnstaler.exe (PID: 4732)
- lnstaler.exe (PID: 3376)
- l6JZULP4N.exe (PID: 6924)
- csc.exe (PID: 3428)
- cvtres.exe (PID: 6344)
Create files in a temporary directory
- lnstaler.exe (PID: 3376)
- powershell.exe (PID: 3648)
- csc.exe (PID: 3428)
- cvtres.exe (PID: 6344)
Creates files or folders in the user directory
- lnstaler.exe (PID: 3376)
- WerFault.exe (PID: 1672)
- CheckNetIsolation.exe (PID: 1332)
Reads the machine GUID from the registry
- lnstaler.exe (PID: 3376)
- l6JZULP4N.exe (PID: 6924)
- csc.exe (PID: 3428)
Checks operating system version
- lnstaler.exe (PID: 3376)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4556)
Reads the computer name
- l6JZULP4N.exe (PID: 6924)
- lnstaler.exe (PID: 3376)
Application based on Golang
- l6JZULP4N.exe (PID: 6924)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3648)
- l6JZULP4N.exe (PID: 6924)
- CheckNetIsolation.exe (PID: 1332)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 3648)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 3648)
Reads settings of System Certificates
- powershell.exe (PID: 3648)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2408)
- powershell.exe (PID: 3648)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
237
Monitored processes
113
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 2040 -prefsLen 34193 -prefMapHandle 2044 -prefMapSize 272325 -ipcHandle 2104 -initialChannelId {8cee1b90-77e5-4d2a-a7c4-650a8ced482f} -parentPid 6764 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6764" -appDir "C:\Program Files\Mozilla Firefox\browser" - 1 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 644 | "C:\Windows\system32\DllHost.exe" /Processid:{9F156763-7844-4DC4-B2B1-901F640F5155} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | l6JZULP4N.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 13 Version: 134.0.6998.36 Modules
| |||||||||||||||
| 648 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | l6JZULP4N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 13 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\HeadlessChrome6441529046 /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\HeadlessChrome6441529046\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=134.0.6998.36 --initial-client-data=0x210,0x214,0x218,0x1ec,0x21c,0x7ffeb71f4f38,0x7ffeb71f4f44,0x7ffeb71f4f50 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 134.0.6998.36 Modules
| |||||||||||||||
| 956 | "C:\Windows\system32\DllHost.exe" /Processid:{9F156763-7844-4DC4-B2B1-901F640F5155} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | l6JZULP4N.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 13 Version: 134.0.6998.36 Modules
| |||||||||||||||
| 988 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1000 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | l6JZULP4N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 13 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Archive.zip" C:\Users\admin\Downloads\Archive\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
52 438
Read events
52 368
Write events
70
Delete events
0
Modification events
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1672) WerFault.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IdentityCRL\Immersive\production\Property |
| Operation: | write | Name: | 0018801285BDAD14 |
Value: 0100000001000000D08C9DDF0115D1118C7A00C04FC297EB01000000035CE7C289251D45ADFDFC0C821355C9000000000200000000001066000000010000200000003C013B5027D2CBA9BA23838E9B6951E3CDAA856AD9AB18B195155267D1AB198C000000000E8000000002000020000000C587750E4039AE004344060CC70086233B8385F499C9DC86A0655F838057301C80000000B46B0E05A76D61D60584DEC7C4E5C66F61B3657F9CCA6BA865DA463EA663BC8A8D7462FED003C1FC47CF14721975F37241A40CD7FB40AC34F87F7FB248A3320BCA4820EC52992680F3E84CAD30BE91D7BA6FDBC90CADC8B3AEF628D2649AB2FE74A619A76ABAF29822F347ACD58E53C4CCE2DB08581CA6C94FC758061782086C40000000C46795828DD42347B4AEA3311C73251AC48F6A3F3C638663B8C59AEC6A340745491934541C845C3C40635308A5F46F33143F1120E056D36B0E7C837CB11A5CED | |||
| (PID) Process: | (1672) WerFault.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IdentityCRL\Immersive\production\Token\{67082621-8D18-4333-9C64-10DE93676363} |
| Operation: | write | Name: | DeviceTicket |
Value: 0100000001000000D08C9DDF0115D1118C7A00C04FC297EB01000000035CE7C289251D45ADFDFC0C821355C90000000002000000000010660000000100002000000003D2C0086EACF6F2DEF87A2EE4B14E7EA05A3FFD2E81450696917D6F76304104000000000E8000000002000020000000AA09BEE6B245C6B71AAFE062DD28DBF591B38261EB076893311E8D7374F65B1E200F0000CEEA92A0A4AEE8F8B42C01DD6E68CA0D3DD3AB4BA8BFDCFC1D30D051AC67EC5D79C532383F1B0B093C9F4F958B37A3C29C2534219866474CB47E3655D4F6EE1E4AFA0B36AF4D26DBB3D6ADEAD7FBCC5DB9EBEAA5AA0EEF772D4EFFE277CB1E3F111AE5EF1553AF789A6D9433212BF35C679E07056BC4709FBCBF00478AA9D6FD10C3DCBA81DB4DBECC98D0A933B954A7E8B4AB49B9CFD85F0BAEE18F07CE0BBFE8F0816E6400356E46B543D6A9962A00E924B0D1D9D60EE6A4948C7C6537221A5E40B90267C756CF660C97A5504D68D7D55461984DBE238418BDB502318429CF5E90820CCF2F0D4D3669955DB1BF29322EF17377C6EC771A40979546B34B583C3BA18CB05A94E526A73841C283ECCF137A037131996C680D2943FB8680A8D3A03E05EB1F4C75A961C00AFD0BF2D01EA023D7A7B98A074D5D956A993B9E1D22B7F519BE53FC7C0EAC98A946D19C294BA2DA3D179199C7488B33F0BE88DA5BC900AF0FAD9FE3BDAB25CAC7A0CFF5B93473533CEBF5585DB5DD2558C44DE461C5E51881812F98866BF8D2ECB661C44D438A12665DB8C5974FC690A76352F78202C55BC96A9FFD9E84A2F94259258C68A65CFD3C5032383A64BF18E67E1E1ACB439F29B28BC1F350D9CC322549564EDEA4022C16BC51B622D8AF44265B7043140F90188CFF9C1CBC95E2AFF0FFA5CD93B0451203544F5D47A31D2CD1405145061867BEF75BD6FDF1E716614495311F4D3CD4C1936B0221B9BBD04B0BBC728037B5C63F4B86BEF20EFCEC830A8E6B5271237D8C39965E43B5E9A2C742AE2E8CFBDC316CFE1A4E8DE294BF844C1420FEF10A6D7DAB90A4BA50F609DD2FB20D2E2E4CD74235CA484FEA73D9364250599FC7F9C1BEC355CC7B28A6BB6364CBC611D8040B2EEF70940CAB8A7F69A8BBC9FA2D233A2AF87CD8971F20F91E4C3F438A5300351F1941C536F05C9EA1AEFC39968ACCB27CF0DEE8F5E5A47C1C41533560DA8BD8211DE188860BCBBF3BFD152450D33A0F1CD0CA936A2E8464C38C177B4A1C92C31E6263A003D0BF9A2BAE1B6FC9F2A1DF1DB00B540819BA2EEC30EBCAACE2D78DB16A9090907D170D61B5F8890A4E58DD5C3E312556D856CBF70834EC40E1125C93EE280C298588C5A203BBE70D2A3EF506268E8C8D5CEBD5E39C24B0BD3326E50E537B7F957B877AF7D2E2BA69CC19ED2C684C107351AFA65BE7F82993E95F7E3148FF9867D0A05DF4E40207FEAA532E5A01AF7FD1A8066D6C955C9868FC4A00D3B8B3FFB4381A5236178E718C2915F2CD1E3E5DFE4CA863070A24A890C2A02CF5879D5A9174FE7C69E0FD3361E999EA4258F7133196D794D9D39133BCC8616F949504AA0E846867D5A031CBDC4107D3C5A1D4F6D68089CF8340B3F27CF4592F17A838735CC2BDFE041482B88E81D5A0165F7519E9B35A59EA8B8099A517075F575E540D3D4AF1E212F35EE0FDB17588F61A8281B76A01A762441B046A34AAB8B34D4A6D01B4F7AF146F7B85EB77ECF896F41F3D66B8A66BDBDD275C19C6E1BDB310628440DC3E2AABAED9B7602B6D05B3700DD838434C7BB986247BADD35641B0D733538C731420BB25518A58077C1D53BD02AA95D346AD217A13DB23A3E4B7DBA40D493E1AC9A4C273B831656FA95440B56043B7F379D2064F02C73DB448EE43D23B6F5C3FEB5E2C60E4645C96CEADC5D7AB7DF7594B18516929E2AD701F34FD5B1FC0195EE4CA15623D8A78385CF469F73CAF835BCDFEF5DDCDAD42B5571AAD8B9AFB941E40440B0BB2D11AEC56548A831B8E04D1763963258F7A93F53D6CCCEED6AE9251A386A86D7F05935D6A5EF966EE6D4A9BF0FA362DEA2CCE7D31C61195503384A7E1A14522098FF7B92F8E6574009190C4A0063C44623CE3A2AE1714BE6DF07E11122D5C13C0D2B7DDD7D0916AF6C5E578497E7915988BBEC99ACA90C5CE55239145B1E1DF9862279D0C95958124135B17222996A7449381689B7C598B397C8458EA4E2F6592BD3F3E7E550A8126E0AF7A7598AB1475113F25EA9B41E02315771F607A0FD27A669C93FEEEFB3B6C66FC0F810388D26F1B6510D6B8656AAF7EBC301FC8C56747818125A11D995BF48F253ABCBCDAF9D084944194EBA5163F87DAC50039B54AE4403E6AA4ABE80BA09F7F1F75065914FA93487164FFCA2715166E1B5770022BE9981CC2BAB36B85ADEB03F5FEABFBE14DBE43E2236E4BC47B35D8C6CBED9FE3996040FB4C80F0F8B32575F46E59178EE3ECAEDA8CAE73623A1EF6A76654B48214D4A3D0D6C0AE3C2086C28B2D6B0A8FB2E4615F762C5B6B648E6E62FC38E4A26EE4095BFF53236D586BE567F08C0795B48B7DA7C725A1BF0FAAF71E39CFDE4821B182CB77C558DF1E1EB109EBF7CD804DC2ABDAD8FF9F785803EB32EAE5B1083E2E8C8EDF357228B54F3101431C65E9A825CEA862A74B492A42D06FDE5948E11E2E431523B5519B0205A29F2915134722B34A89582E5CA3A34017FB7920537AF0077DCBC2771F5D1601073A9D5E2BD47BF8273913D97056FC0049973DB617D156A4B98A36E90CBC8BF15ED6929DA9949D46E4D8436C8AAAEB31815011616744C2E832FF85CDEA834C72C68FD3979631401C7C15A291D4BAE705A9374A5454EF1DE9D3A69AB374472F8D003A82D9F505C3237A23D61350A1851E41311C1A2F44FED689A7707DB4048D5108908AB8A9E82BADA97F26DE8212F9633D1FAC1B4DF6E3075857D86D195C1C11688B3695171BA92C81059405B3F6E77A7AE37BA1EB56950519BC97035EDFC0C524F953CE7DBF5B99B7F311D49048D62CCF50A19B2CF5F5C6E3875230FA6C66D3164877372204AE97C1246AFDF6402D9B338124236038F5C22071AD1AAB5D62A8FD33AE2DC18065AC60C6808052CB67973376F075751216FEF0E56483E58D4720B322B533092B2EAD13253301BE56C643EB1CD58C52345C234F47FC3B1511AED4BAD4D566DB1F7E503CE8D5FDFAE6B63528A3D6FDE0BAB670270DDF22875FD0544DFCB2C79C35808C6B3EA5CCAAD52D397D2837BD113995D5CB4667F26B8CF3BFA811AE079BA03F29DEEC485C5AFD4140F24186CA69604906E1E0258F346F6FF83BABBC89BB5E3A8832C1835FDE554F715B73B92E89F9E398DA7FCE55B3CBD17203A2677CA70FEA9136858B49CD2F5989AB973347308934B2FB850B82D9939E3827E4E2AFA753EB9B80B255979242CED5F71AF1BB6EE531A161B0B1C8CF1AF797819A07BE982589D3B994569D430BC2D91881BE15746CCD049CBF0E7CA503EB4F7885A79805725A53C8CD6EBF805970E185E21092A164603BF6E5719EE2177722D9469C1CEE18FAB7B71914F322ECEA16C924908CCBD67811409D6B872A71DE41ED4B3E6135CEC881785CEEB51C72B8E06BE914649D53A0A120BA20515641717EC17441989111ADEC2779C6387BE0C93A52FEC77ED751ACA000EB764026301CA9C5BECBF52982980BCD945B33A4D2F0B2FDFA801042108A1D3A2E6A9A137B50A6ED11ACB1BF37428C3E5E6020C0ABD457B223DDA86D2EC976BF17CB9FCBF48D59AA82F71EB6C535B03366DB25B4BA62F3C77D365DFB0B568B38D51E8DF2AA8B06EC1D5B60C274B11C69464AFC9D29314EF45379C44729E0C7F6323C1AE9E32813FD462C1A0D21C7D83B1F8ABBF3DA05BF93CE41EE6BA43D0108DBDB928C8E78A1D14EBDA90036DA7F36EE100A5C86793AB91261A31FE34B58A57861A71E263CCE49F8D788A9E0B548B38DBE4AD20D60B1676F8994BAAAA626B1FB5AC2B6FCFD72A82B410A221302AD1851DAFAA8A9BF5671DC7D21BC36F85CDD99DADBDADB3888BAFF20C8D1E4D2BE5520E5A731E693F042B365F808DAD57067A77C0F9F23CA9EA0FC968BA5DE16A3D996EED96EB43546642E3A5FDD68C7F30E99BCEA46BD1F98574E0F9435A6DB6B78351C3F67B1545F6033A02631BF0CAE5A0D6D484344DCF5EC4C801633150FCE8495111F21201024E09D38FBE7DE165DBDCF1A5312072CB58BD0E75B7861D9A6B19E42E38AD73584745D64C6DF62CF7A5304D7C0C067E7CB81BECD1699A65262338879FB008C1668EC5FAC262A3DB4E8D9D67035B9EE012528686A9A1793F20A61ADA9C051FC35B1D4C241A827A9DD5801269943A5463AE272E9B77015BF1A2DFEFD148EF9232C9B681067CF0953E1579B8168F79530D91D4009F2A734C7D19BFF8675D348F717B84D1BB1DC305E0AEDE4D418F7095FC75F3133F396DE66490B6B4A49A45D968A33D29B8D97FE5448845B7576021F37C390E83BD84CF984319A8965CEC43337F45831D50E047380765018521608843F9A59CF4F4F76BA892B660CF85F75299C10E1ED2A8C33A45CA40D6DD7D64B8E78862B678CDFECE7658555DF4E92ADD501E9B3DE7B52D01D072A6F8DB2606C9738A86E4B164773BDF860F3DD46580AAB024458118507C629DD5647865BB8DEB5F1C566AA86984F6EDCB53435A72CEA0D06298570603037ABD356B17665C25F1D06E8640B8914A8F6BE4A99D8CCD8DF5A8A7B1077D81E62C6AED3BD2CBF2590A966ED421B45C9B4DE8F740B3B8165BA08B0007B149A7CD1A09AD6BD8D51F3712690AB5BFEB00F4EC80068EE13C1A81B384473D6921897F2883CEC7FD7054092702F0B86D3EC1508571A06D00522BD79C233BE79CD818B94D61EC10476E6FC96F8EEBBB762D21226DE34CF5430A246BE91CE283C751D2752A76381DEED938A8AD9CC892879E2C82382BC1A25F106EDCDFDCEBCE2A20B2600DD8CFD56A10D48243FCA6853309DAA1A7E74FA25378798089FEF11E844CE2E4E670A010A0F75708C575C97C7BB9ADA2D738806CFA949B5599373D6A2CBA18BAA2EE11A58DD6234E05243A1CDD27AF596F6AE9DB4EA98C80851EDC4454310A2DB7E451F62CC714E9A64CA8285B737A6C2BDC2B72814E7D50323C417CC1827C4E8C8526C7B2429E4021144B9561B590D66B5C2DB861B93FEDF73859A7FC3E423CCFE290130C0EAD20A24B81B21B01F3B9F33AC5EC04EDC07F0853421DA9552E306C6CA432D4DFFFF64C64A00BB4EE51C0D2CF8DFAC555EDC428541ECAF8FF16683959990BB6A7D16928B2DEE8F0BB811F78AB5EB4DA7C349394A3DA973807BB575BF360CA52E3DFB5AF41850CA7A7E850A16DFE61BA3E56347460B5FF0E2B09642D48DD2DBD2590697AA673596C6BC5718160753D47B01C254DF8FCCC99D28D38A8C055C8A37AA2558BEDEC283A4F97D662971B6C73A51A6AF0520ECC7C55729CAA898DE44E1412EA16FA39D0A86342028E6005268DA30DD228283AB73603E468F06F4F58CB6B2DA0CA55EEC9327EC9306A684C57BBFD625EFF3BD9278CE906EE48F04B0A7B03096BB25842772DC4244556D564C04D872098E92996E32352B7ED25A2CCDFF6A4C8B81836A26E206C1B67C7DFAFF4D9D184CBAE360D57E3032708F0A8853B72403CF024E84ED66A355C829DDF208797A32A655400000007582F7B6028B94D82BD289B494BC00A6555E601274C30F4E6AFC03463039EFE8C579866C176C7A793D12A0FDCCFEA0436A5025DE4E1CA5142A28916644C1C48A | |||
| (PID) Process: | (1672) WerFault.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IdentityCRL\Immersive\production\Token\{67082621-8D18-4333-9C64-10DE93676363} |
| Operation: | write | Name: | DeviceId |
Value: 0018801285BDAD14 | |||
| (PID) Process: | (1672) WerFault.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\IdentityCRL\Immersive\production\Token\{67082621-8D18-4333-9C64-10DE93676363} |
| Operation: | write | Name: | ApplicationFlags |
Value: 1 | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
12
Suspicious files
1 752
Text files
2 279
Unknown types
281
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6764 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\8o2qovza.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\bounce-tracking-protection.sqlite-journal | binary | |
MD5:6313E13420C0EF94DB90A80E8B2CB2C3 | SHA256:47205A6524C4914AF3DFC18B9098549C658B953F6B252F154457AAE7100C52B5 | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\prefs-1.js | text | |
MD5:9574BA06A147D0B32FF1890757A0BBAD | SHA256:FE75683DE333F3ECED7D1D57103FE098D3E607216F127C282DA819E30765C637 | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\sessionCheckpoints.json.tmp | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\sessionCheckpoints.json | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\extensions\addon@example.com.xpi | compressed | |
MD5:EBF4E02DD4914A67295BC7B34AEC4A6A | SHA256:427AC8E99561F39FD5D20672793E0BE387E93EAC246472FED34B054119DEEAFD | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\prefs.js | text | |
MD5:9574BA06A147D0B32FF1890757A0BBAD | SHA256:FE75683DE333F3ECED7D1D57103FE098D3E607216F127C282DA819E30765C637 | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6764 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\8o2qovza.default-release\startupCache\urlCache-current.bin | binary | |
MD5:CCFF01F85E51B7C63B0E2D735B1F4415 | SHA256:981DC4889004805F91BB4E995E1359790EFA75A7FFD3094B1182D83C7E5D4DEF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
376
TCP/UDP connections
125
DNS requests
219
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1380 | svchost.exe | GET | 200 | 2.18.64.212:80 | http://www.msftconnecttest.com/connecttest.txt | NL | text | 22 b | whitelisted |
6764 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
6764 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
6764 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2025-10-19-08-10-44.chain | US | text | 5.18 Kb | whitelisted |
6764 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2025-10-19-08-10-44.chain | US | text | 5.18 Kb | whitelisted |
6764 | firefox.exe | GET | 200 | 92.113.23.99:443 | https://nxbrew.me/ | CY | html | 157 Kb | unknown |
6856 | svchost.exe | GET | 304 | 2.16.10.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?687dd679c9a8e4ad | NL | — | — | unknown |
6856 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
6764 | firefox.exe | GET | 200 | 92.113.23.99:443 | https://nxbrew.me/wp-includes/css/dist/block-library/style.min.css?ver=6.9.4 | CY | text | 116 Kb | unknown |
6764 | firefox.exe | GET | 200 | 92.113.23.99:443 | https://nxbrew.me/wp-content/themes/hitmag/css/fonts.css | CY | text | 3.50 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 52.110.17.45:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1380 | svchost.exe | 2.18.64.212:80 | — | AKAMAI-ASN1 | NL | whitelisted |
3876 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6764 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3984 | svchost.exe | 23.197.142.186:443 | fs.microsoft.com | AKAMAI-AS | US | whitelisted |
6856 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6764 | firefox.exe | 92.113.23.99:443 | nxbrew.me | AS-HOSTINGER | CY | unknown |
6764 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
6764 | firefox.exe | 151.101.193.91:443 | ads.mozilla.org | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
fs.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
nxbrew.me |
| unknown |
login.live.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
ads.mozilla.org |
| whitelisted |
mozilla.map.fastly.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1380 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
6764 | firefox.exe | Misc activity | INFO [ANY.RUN] Cloudflare DNS-over-HTTPS service requested (cloudflare-dns .com) |
1736 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6764 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1736 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1736 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
1736 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
1736 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
1736 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
1736 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome44081526718 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome53521526906 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome62281527265 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome23721527437 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome18041527828 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome76241527984 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome48601528437 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome73561528656 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome6441529046 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome38081529187 directory exists )
|