| File name: | SecuriteInfo.com.Trojan.TR.Downloader.Gen.4067.18966 |
| Full analysis: | https://app.any.run/tasks/2f5bfeee-a35b-4ec1-8a45-a8026f873cac |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2024, 11:50:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: FLAMES Launcher 1.5.2 Installer, Author: Ternion, Keywords: Installer, Comments: FLAMES is a registered trademark of Ternion Co., Template: Intel;1033, Revision Number: {0B71F0CA-EFFF-4EC4-A2DB-AE7C76CBC015}, Create Time/Date: Wed Aug 21 15:50:18 2024, Last Saved Time/Date: Wed Aug 21 15:50:18 2024, Number of Pages: 301, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 72224F44BEB53A071A238AB126E2DBFA |
| SHA1: | 15EBD98C0B91C6FF29F84D837A98DAF31563C791 |
| SHA256: | 524E2F37B162B8D8B6E1A0174FB8394D752500306997988E428CCFDCBD856E42 |
| SSDEEP: | 98304:/ATk2+fqxPZtx8RL5Q67hOqcyzHQWKtnYlCB12GwfUR1R+pmMbgtj0I1Cvtcb8ME:ncobmMlIMhSv27hJ6FlqCtP4raH109k |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 6668)
- msiexec.exe (PID: 512)
Executes as Windows Service
- VSSVC.exe (PID: 3604)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 512)
The process drops C-runtime libraries
- msiexec.exe (PID: 512)
Executing commands from a ".bat" file
- msiexec.exe (PID: 6668)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 6668)
INFO
Reads the computer name
- msiexec.exe (PID: 512)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6668)
Creates files or folders in the user directory
- msiexec.exe (PID: 6668)
Checks supported languages
- msiexec.exe (PID: 512)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6668)
- msiexec.exe (PID: 512)
Checks proxy server information
- msiexec.exe (PID: 6668)
Reads the software policy settings
- msiexec.exe (PID: 6668)
Manages system restore points
- SrTasks.exe (PID: 6344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
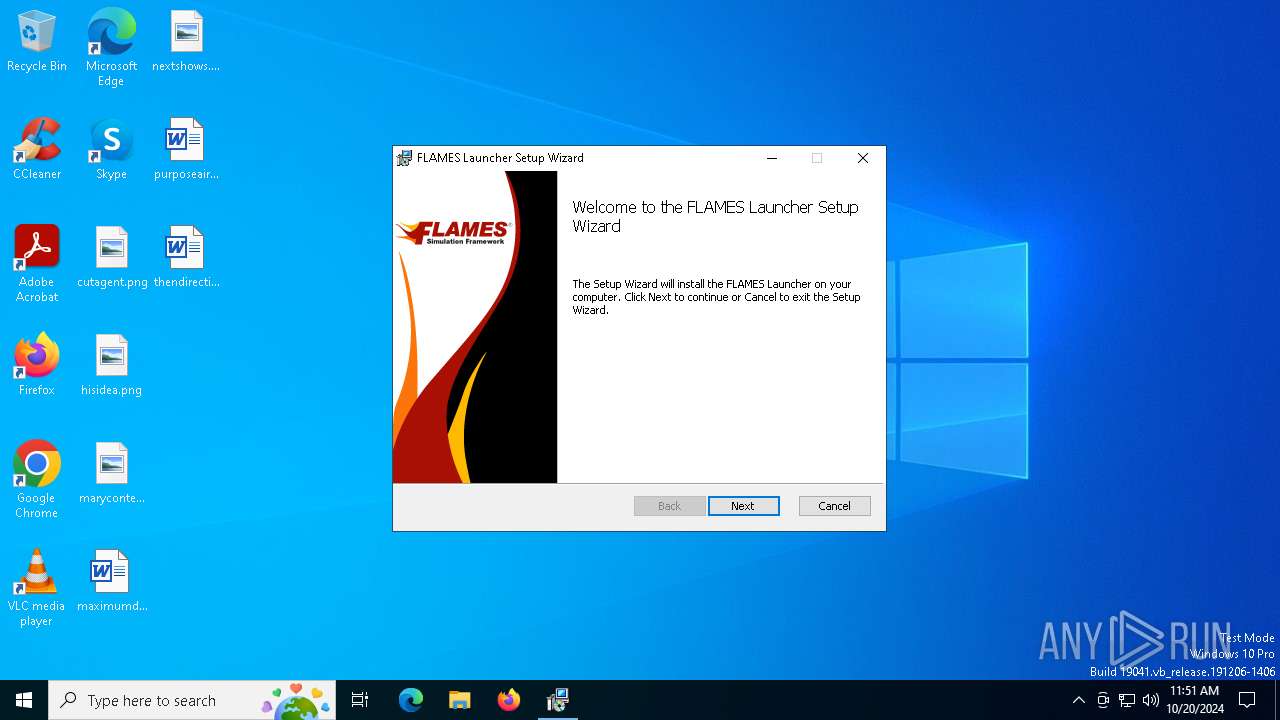
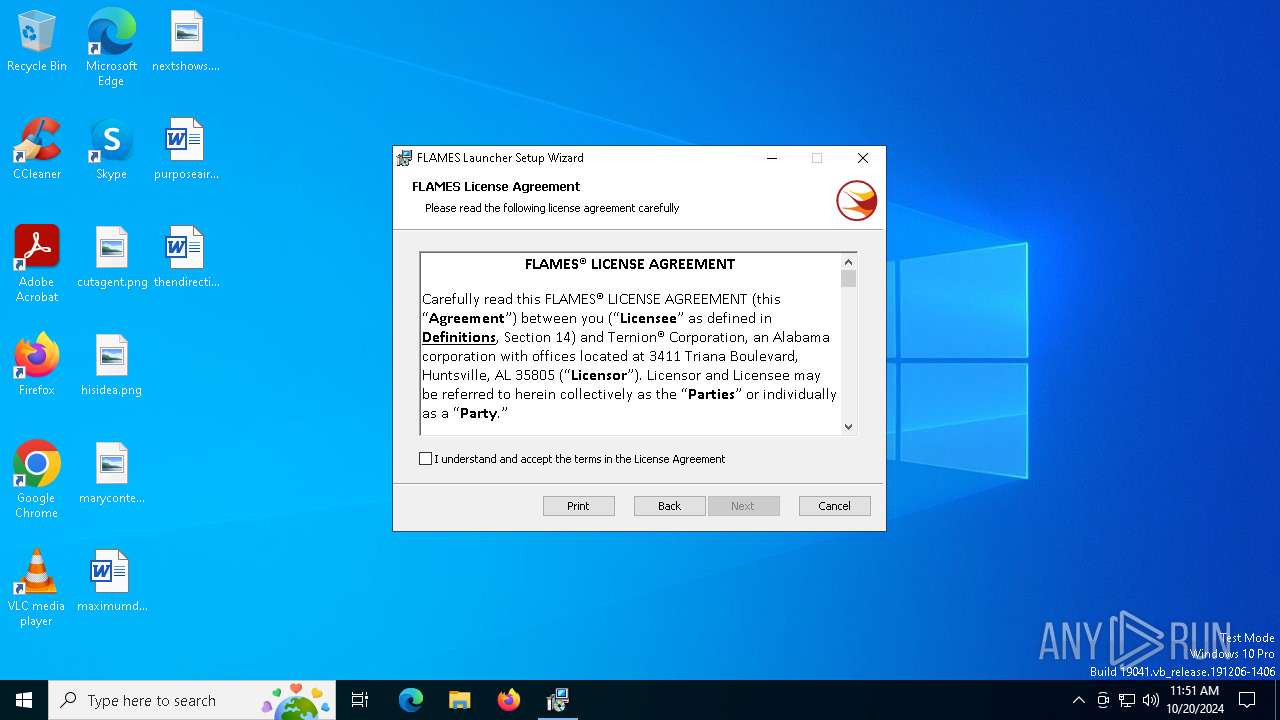
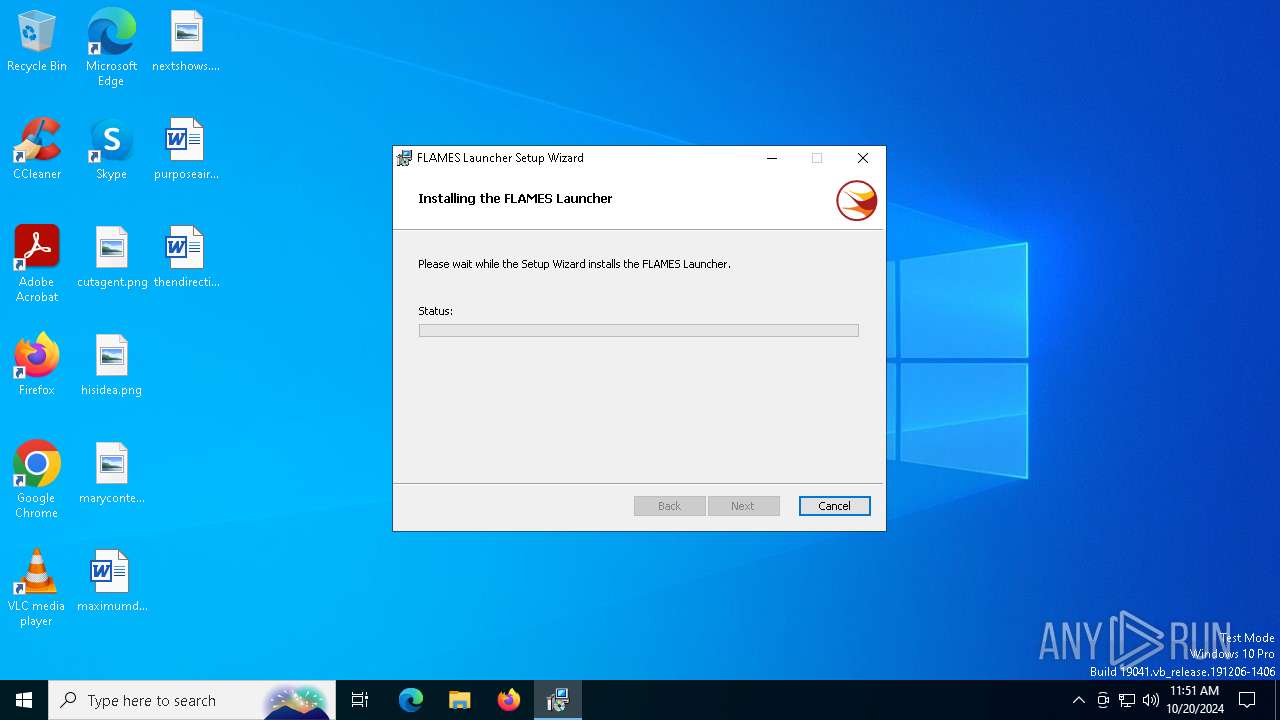
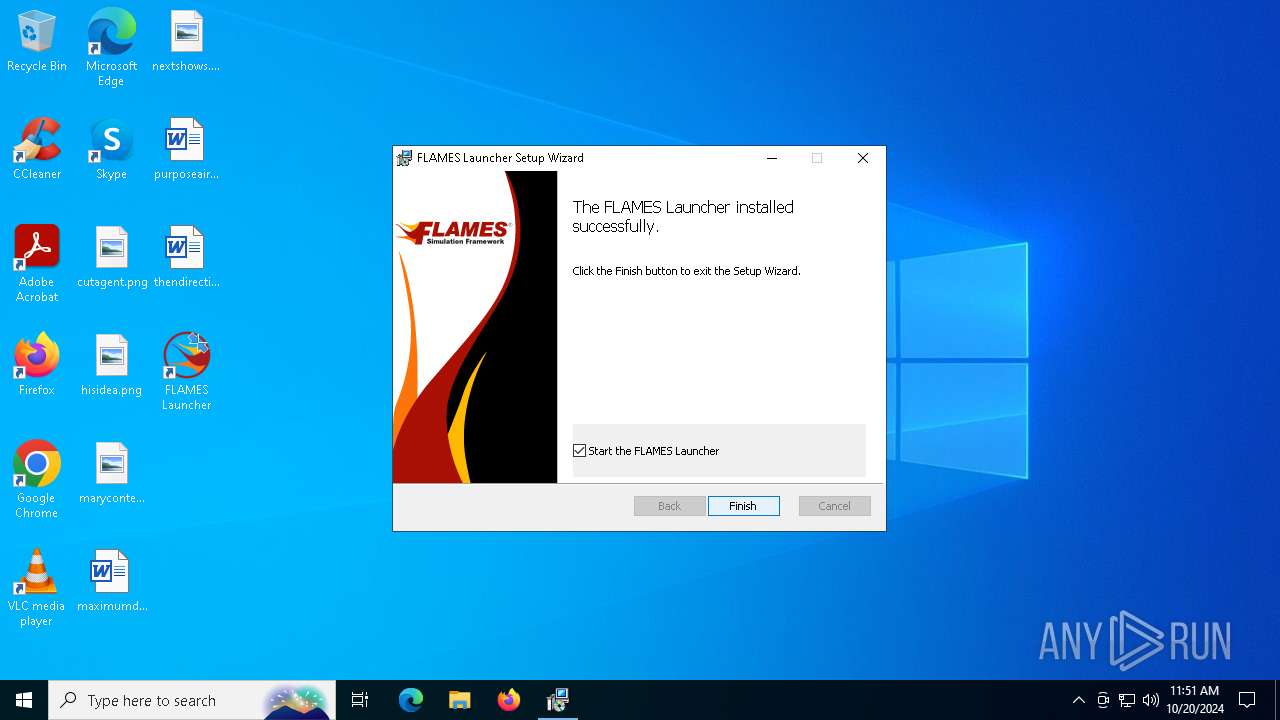
| Subject: | FLAMES Launcher 1.5.2 Installer |
| Author: | Ternion |
| Keywords: | Installer |
| Comments: | FLAMES is a registered trademark of Ternion Co. |
| Template: | Intel;1033 |
| RevisionNumber: | {0B71F0CA-EFFF-4EC4-A2DB-AE7C76CBC015} |
| CreateDate: | 2024:08:21 15:50:18 |
| ModifyDate: | 2024:08:21 15:50:18 |
| Pages: | 301 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
144
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3604 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4060 | C:\Windows\syswow64\MsiExec.exe -Embedding B38FB7893921CB16F717E050F0BA9CD1 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4088 | C:\Windows\syswow64\MsiExec.exe -Embedding 9473466F08D7236D51E2648B9461D00C E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 5516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5740 | C:\Windows\syswow64\MsiExec.exe -Embedding 053F5D6B42D623FC8F5FC0F1EA7D43D6 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 6344 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
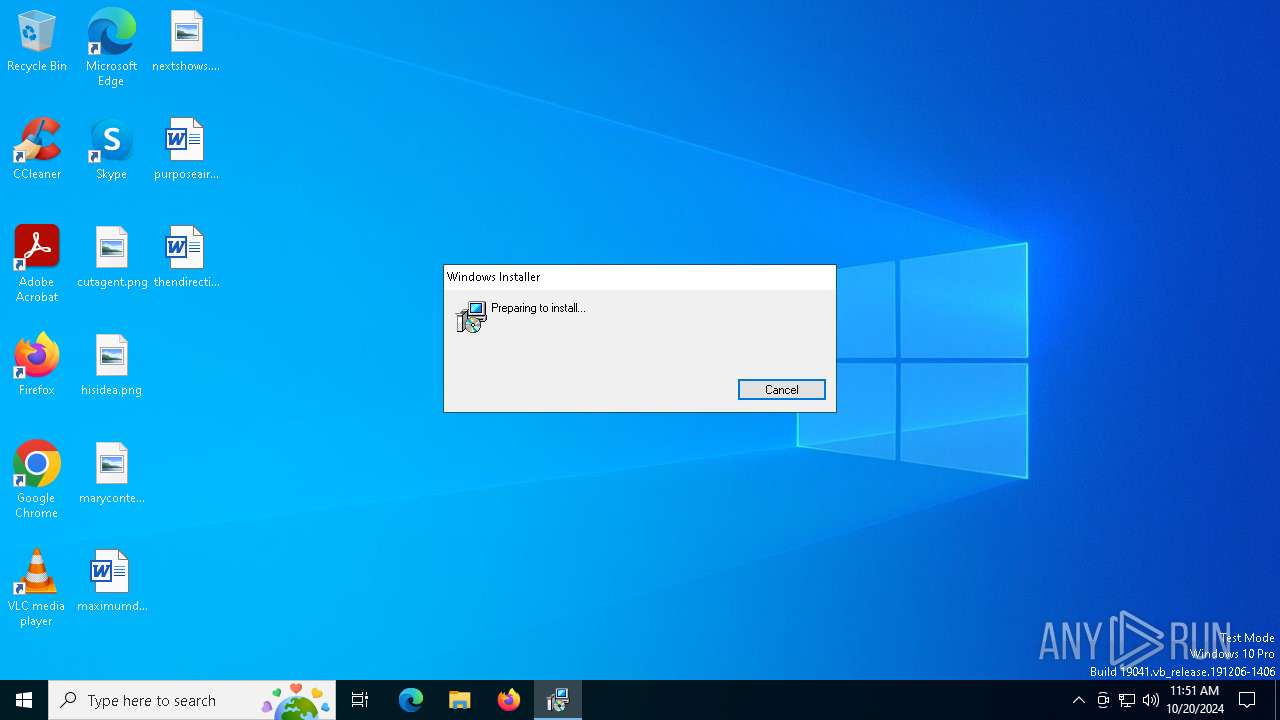
| 6668 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.TR.Downloader.Gen.4067.18966.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
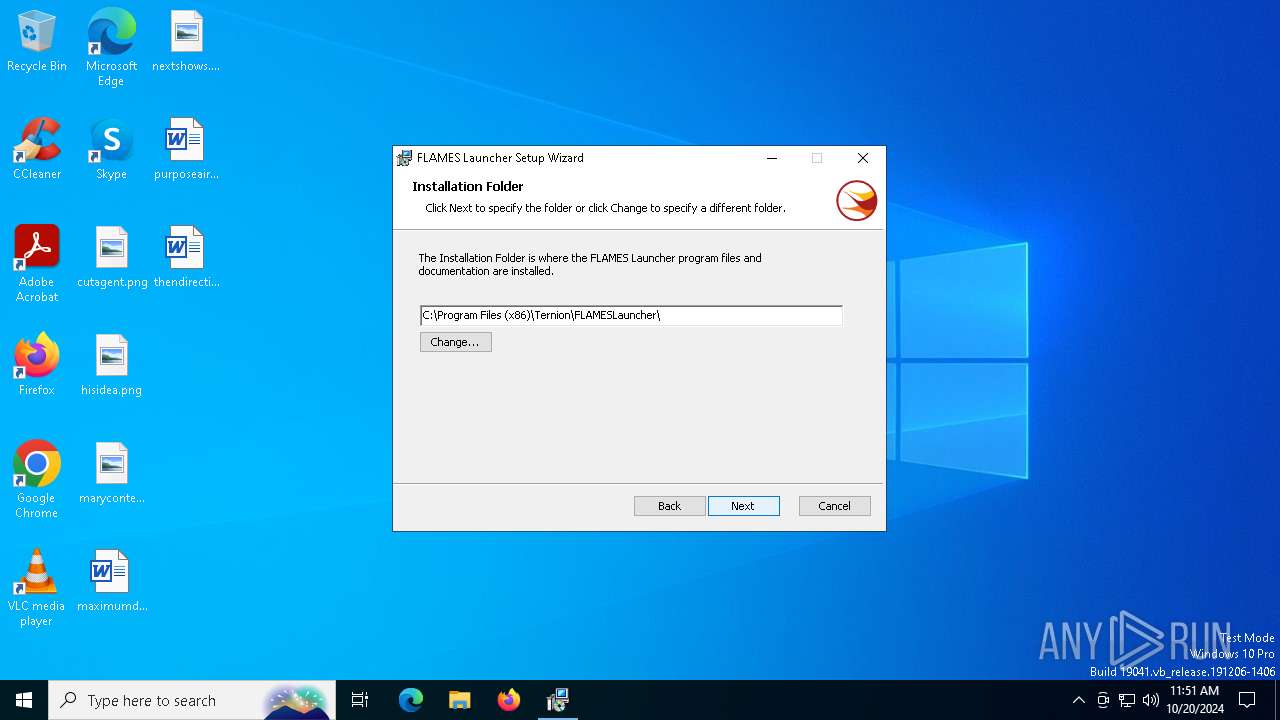
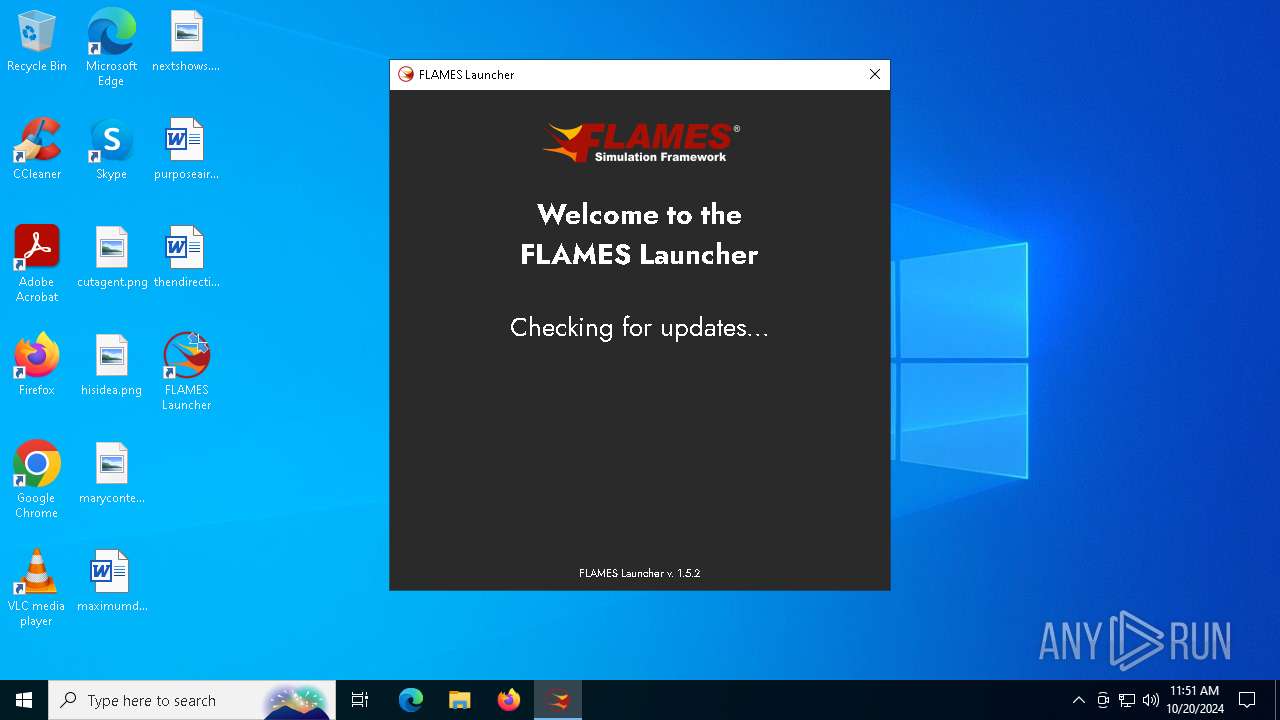
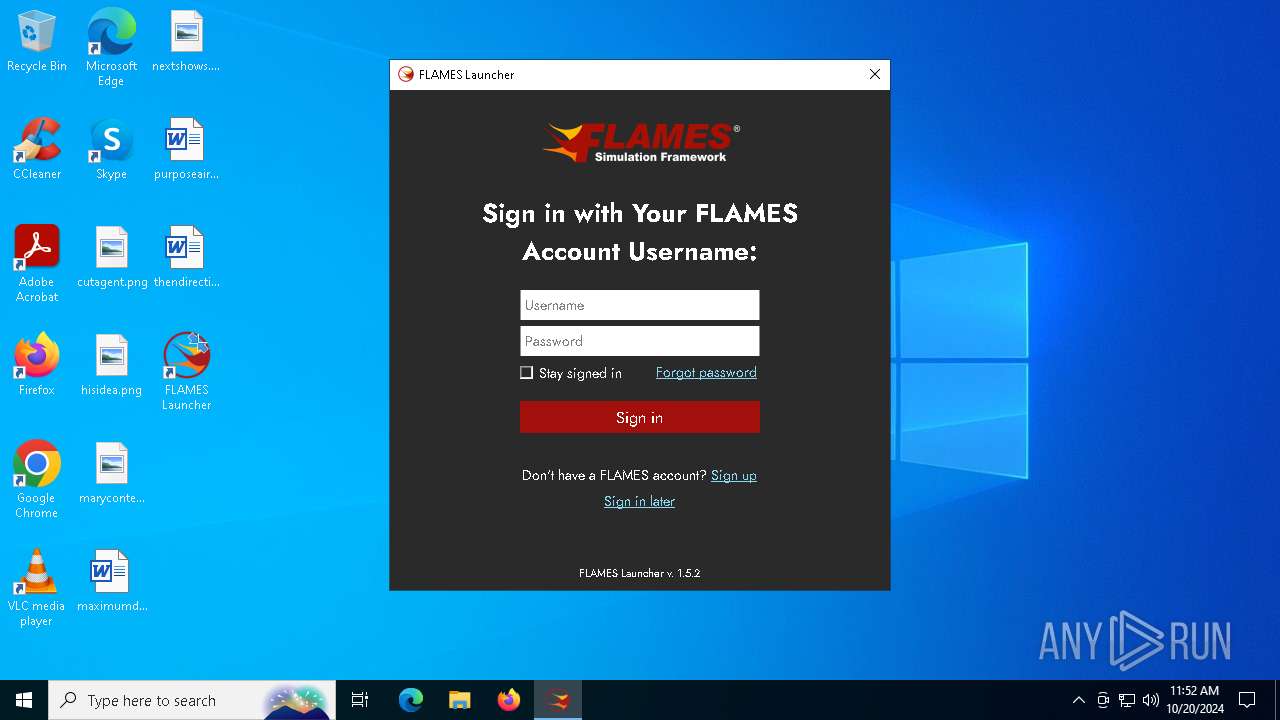
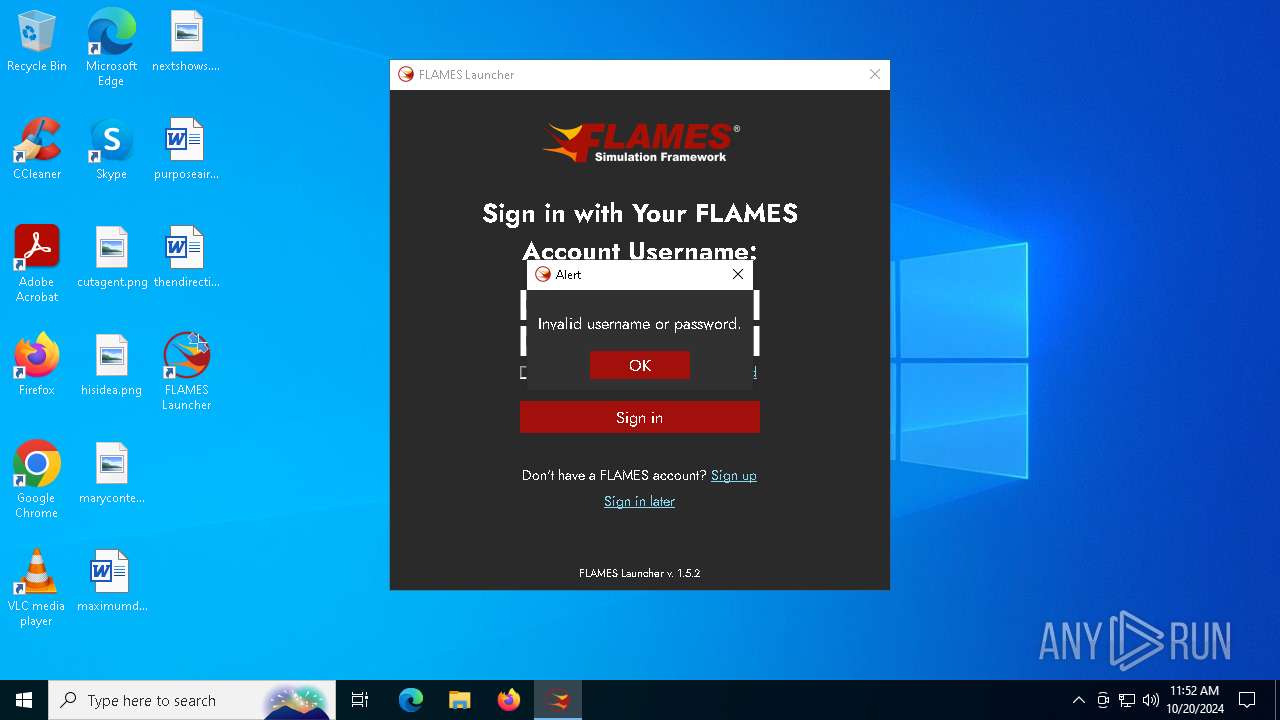
| 6856 | "C:\Program Files (x86)\Ternion\FLAMESLauncher\FLAMES Launcher.exe" | C:\Program Files (x86)\Ternion\FLAMESLauncher\FLAMES Launcher.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM | |||||||||||||||
| 6876 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files (x86)\Ternion\FLAMESLauncher\initstart.bat" "C:\ProgramData\Ternion\FLAMESLauncher\" "C:\Program Files (x86)\Ternion\FLAMESLauncher\FLAMES Launcher.exe" " | C:\Windows\System32\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
8 257
Read events
8 106
Write events
142
Delete events
9
Modification events
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000011800A64E622DB0100020000CC150000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000011800A64E622DB0100020000CC150000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000046B64364E622DB0100020000CC150000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000046B64364E622DB0100020000CC150000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000211A4664E622DB0100020000CC150000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000807D4864E622DB0100020000CC150000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000DC37AA64E622DB0100020000CC150000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000007F9CAC64E622DB0100020000680F0000E80300000100000000000000000000005EE98E476FF918409B85C3A4A036A56300000000000000000000000000000000 | |||
| (PID) Process: | (3604) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A4C7B364E622DB01140E000030100000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
23
Suspicious files
27
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 512 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 512 | msiexec.exe | C:\Windows\Installer\9421e.msi | — | |
MD5:— | SHA256:— | |||
| 6668 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_93702E680A5530C052C8D2BA33A2225F | binary | |
MD5:E46873EC79702EA2A866A3488A3A53AD | SHA256:1F9E2F9A114F95B23149D6A303D429791C35418A5D5DED1C92CCF889660944A2 | |||
| 512 | msiexec.exe | C:\Windows\Installer\MSI4646.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 6668 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3AA0DCD5A74331FBD6F344550EC48B87_AB2D9B69486D450272341417717C10BF | binary | |
MD5:2CF94FA542F9F58B26EB4926D25EB912 | SHA256:5E78C617EF418E36B898D47C6CEF170F1F6166A9FBC5E757CA8851E9BB336FB6 | |||
| 6668 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\18E6B4A57A6BC7EC9B861CDF2D6D0D02_EF52C1EC85F21F31CC0157A5C8803013 | der | |
MD5:3FA9229C04DBF8972FBA6C6B8D7054F6 | SHA256:EA5F1144380A22C2AAFD93C8EBE9F53F89DD45DC9361D09C488561DC25CE8DF4 | |||
| 6668 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIEA1A.tmp | executable | |
MD5:4FDD16752561CF585FED1506914D73E0 | SHA256:AECD2D2FE766F6D439ACC2BBF1346930ECC535012CF5AD7B3273D2875237B7E7 | |||
| 6668 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_93702E680A5530C052C8D2BA33A2225F | binary | |
MD5:C58609BF40685CB5C34DAB4979C2E0D0 | SHA256:FD8AC52BCC75885BA10ED1F25FD03B63A00C2BBCA34F606A62E01C35396D7DAE | |||
| 512 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:78621A05DC5EEB43AECAED1D69FA14D5 | SHA256:52094CC0173DD0ACFBCD17BEE6DD308AE6D921C9EEFCF7642CF345D6BB460435 | |||
| 512 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{478ee95e-f96f-4018-9b85-c3a4a036a563}_OnDiskSnapshotProp | binary | |
MD5:78621A05DC5EEB43AECAED1D69FA14D5 | SHA256:52094CC0173DD0ACFBCD17BEE6DD308AE6D921C9EEFCF7642CF345D6BB460435 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
64
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6668 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
6668 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
6668 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEQCdm6p45ZNVrE7ie5zWyTYX | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5232 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5948 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5948 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6680 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6908 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6668 | msiexec.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.177:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |