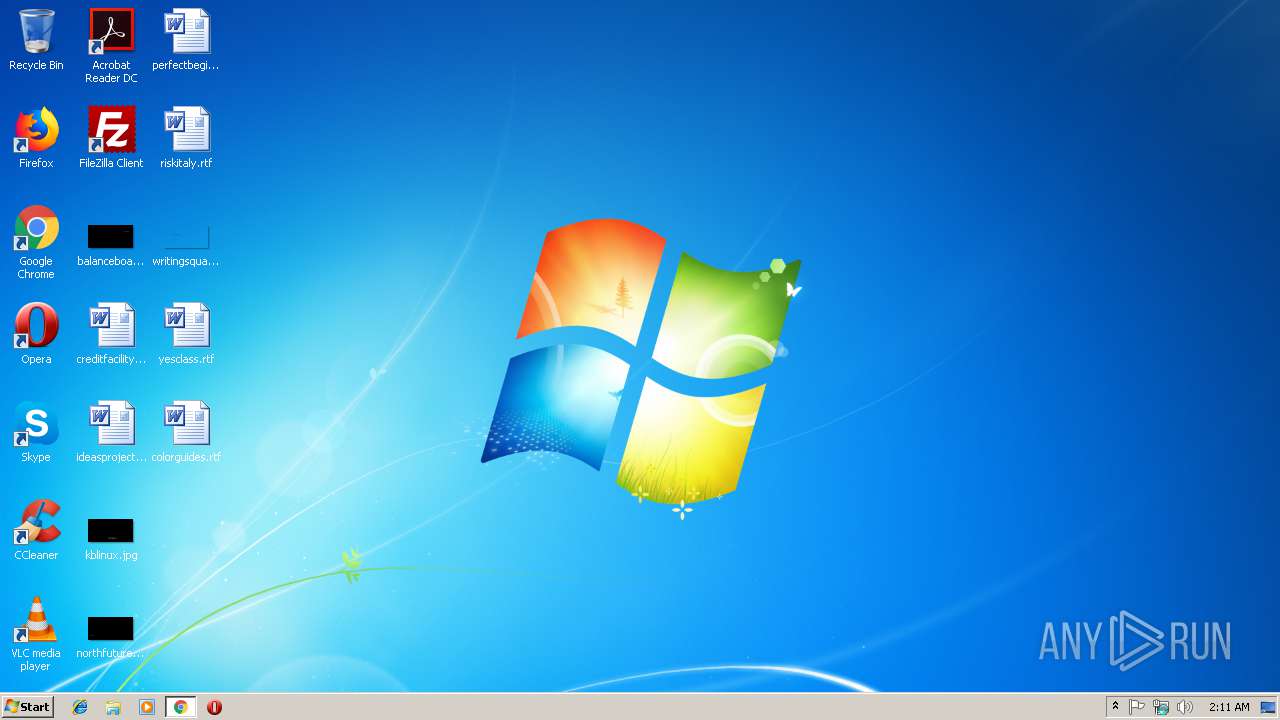
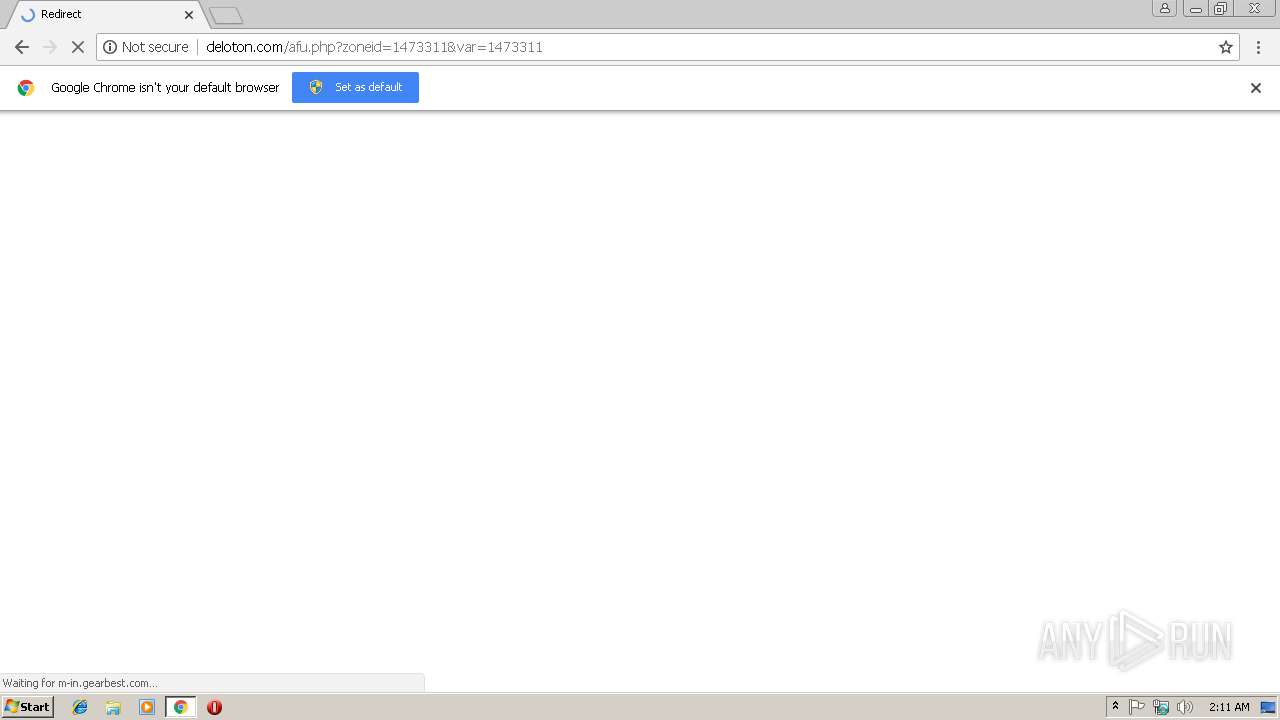
| URL: | http://deloton.com/afu.php?zoneid=1473311 |
| Full analysis: | https://app.any.run/tasks/f64c23f7-cbb1-4aa2-8a7d-8775974e043c |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2019, 02:11:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 300A3CBAE33B398F19B10AA309B7AF76 |
| SHA1: | 0D942854B634E180B423305513E9EBB85F716599 |
| SHA256: | 523D672F15315B45FDF84FEE51EA34E515729C8CB03706AC4DF6286A6BF4279B |
| SSDEEP: | 3:N1KaAJR/iMhz11MNn:CawaMhzQNn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3528)
Reads settings of System Certificates
- chrome.exe (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6feb00b0,0x6feb00c0,0x6feb00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,7851284230646779814,659526548120058616,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5005918307FF3BB85EA8A48B71761C53 --mojo-platform-channel-handle=2240 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,7851284230646779814,659526548120058616,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=69DE6D7726FDEBAAE27C9224DADDAC3D --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,7851284230646779814,659526548120058616,131072 --enable-features=PasswordImport --service-pipe-token=62BA4CE61BD9AE23AFDFD744C18670D9 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=62BA4CE61BD9AE23AFDFD744C18670D9 --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3532 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://deloton.com/afu.php?zoneid=1473311 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,7851284230646779814,659526548120058616,131072 --enable-features=PasswordImport --service-pipe-token=0276C375625CCE7F40512008710FF92C --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0276C375625CCE7F40512008710FF92C --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,7851284230646779814,659526548120058616,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=939DB486B9781261178486EAAB03CC8D --mojo-platform-channel-handle=3880 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
500
Read events
456
Write events
41
Delete events
3
Modification events
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3528-13195793501404125 |
Value: 259 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3528-13195793501404125 |
Value: 259 | |||
Executable files
0
Suspicious files
51
Text files
73
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\500126aa-2282-478a-9317-3e274eee06de.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7754afc6-a756-4865-b69e-9f3a53e7c6ca.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1ae502.TMP | text | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1ae521.TMP | text | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF1ae531.TMP | text | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model~RF1ae83e.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
51
DNS requests
56
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
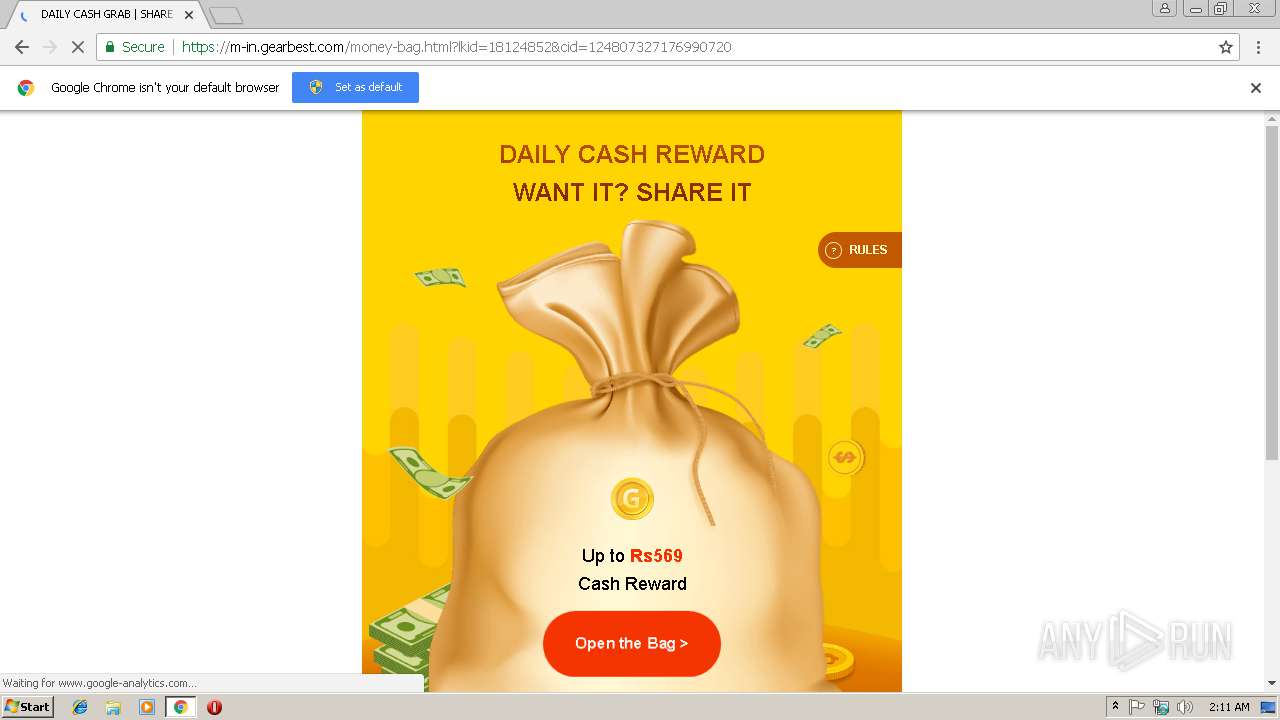
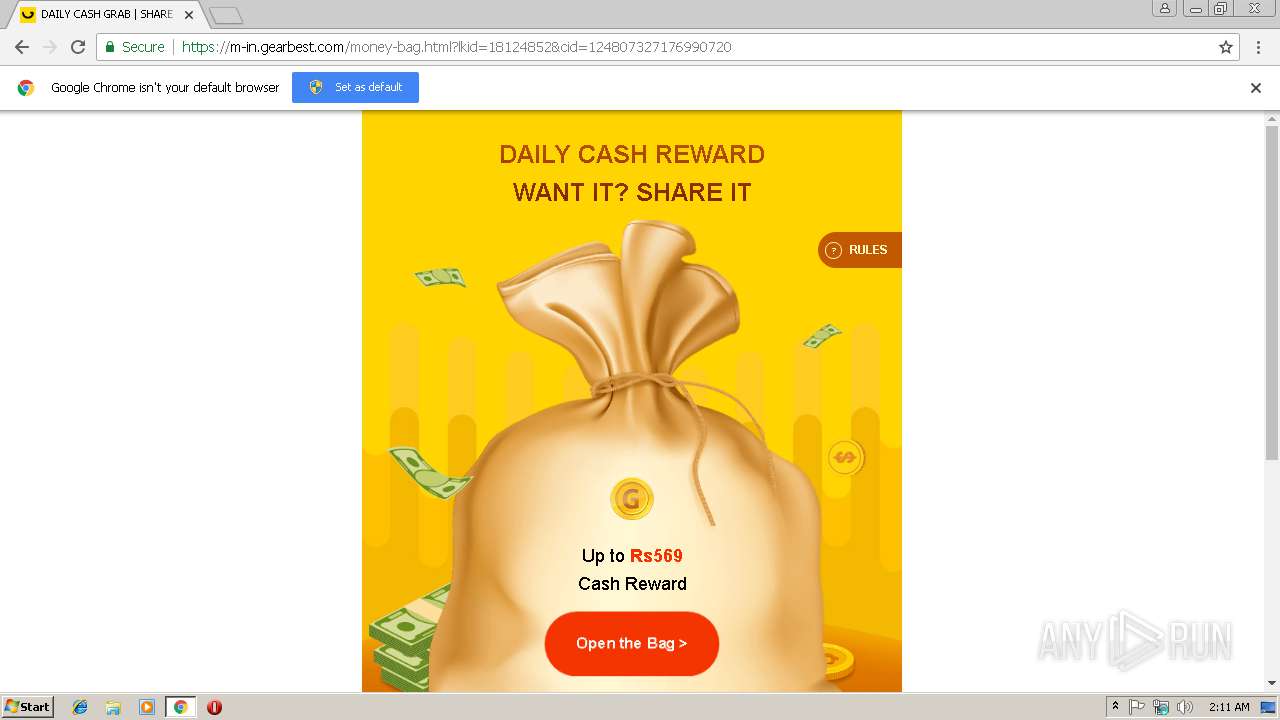
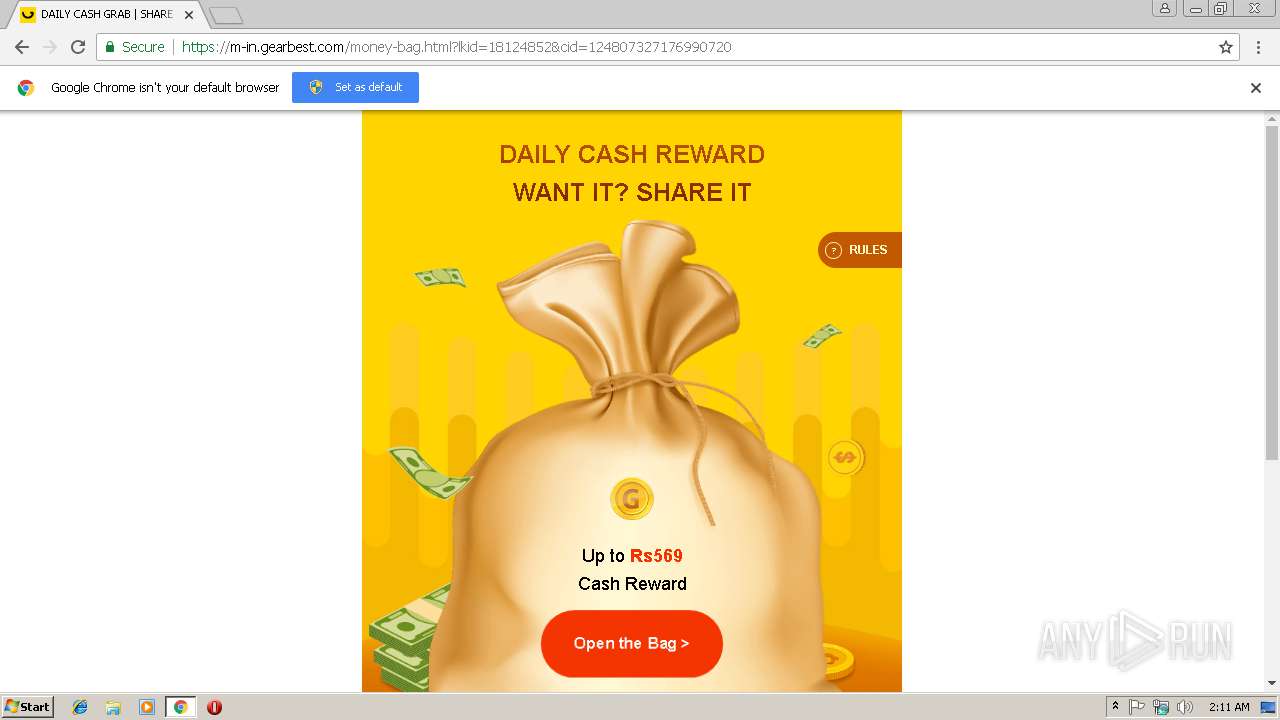
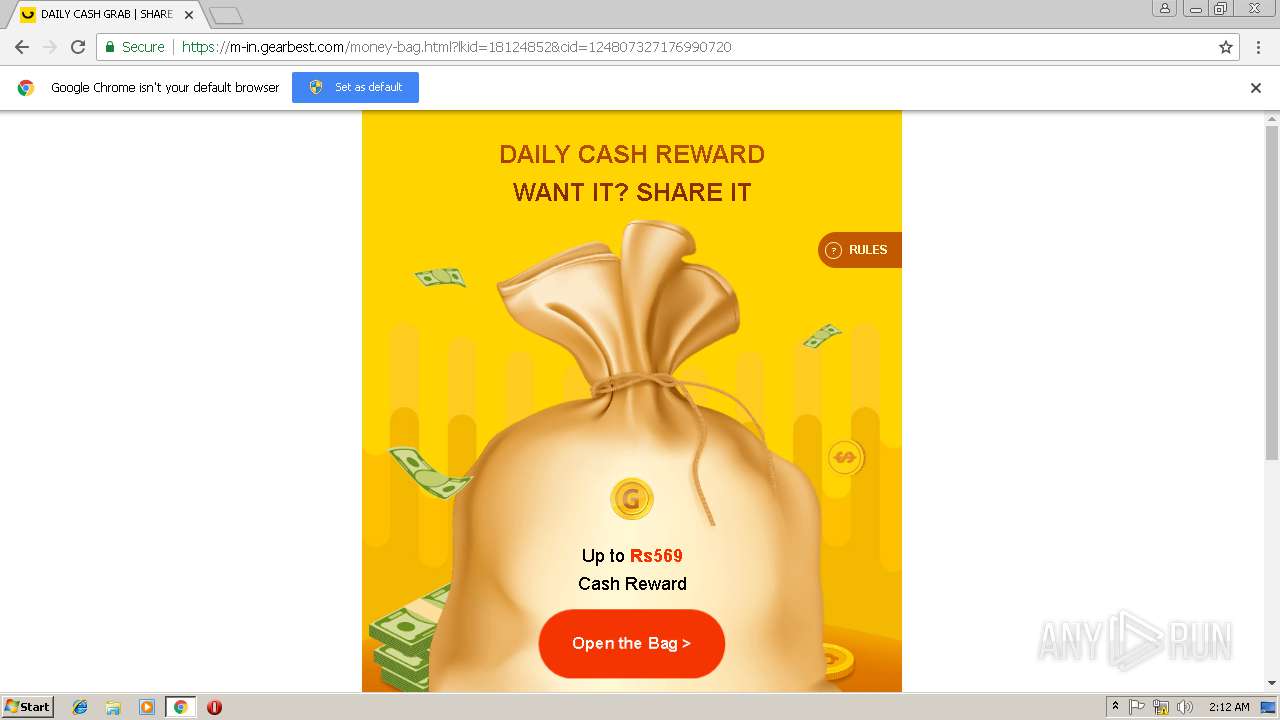
3528 | chrome.exe | GET | 301 | 104.108.33.99:80 | http://m-in.gearbest.com/money-bag.html?lkid=18124852&cid=124807327176990720 | NL | — | — | whitelisted |
3528 | chrome.exe | GET | 302 | 188.72.213.176:80 | http://cobalten.com/?r=%2Fmb%2Fhan&pbk3=89dd37fbd757e346b3c659dfea3e80a36662868246159417175&empty=0&uuid=0aa8c387-a5dd-43f3-9e5e-de349cc80c6a&ad_scheme=1&rotation_type=22&ppucounter=0&first_visit=0&on_test=0&offer_views=0&ab_test=2756&adparams=bm9qcz0w&ip=3f05ac1cbe514282b4b81b295ae22368&zoneid=1473311&x=1040&y=586&sw=1280&sh=720&sah=692&wx=0&wy=0&ww=1280&wh=692&cw=1040&wiw=1040&wih=586&wfc=0&pl=http%3A%2F%2Fdeloton.com%2Fafu.php%3Fzoneid%3D1473311%26var%3D1473311&drf=&np=1&pt=0&nb=1&ng=1&dm=undefined&cf=0&nw=0&hil=undefined&id=07b88578f2b44ab66735350bd3297e05&co=1&rf=0&hs=d01d492f13aec958676a3d4656a2a36c&ix=0&fs=0&sf_type=1&timeout=0 | NL | — | — | malicious |
3528 | chrome.exe | GET | 200 | 67.27.158.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3528 | chrome.exe | GET | 200 | 194.187.98.221:80 | http://deloton.com/afu.php?zoneid=1473311 | NL | html | 4.35 Kb | whitelisted |
3528 | chrome.exe | GET | 200 | 67.27.158.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3528 | chrome.exe | POST | 200 | 188.42.160.69:80 | http://my.rtmark.net/img.gif?f=merge&userId=f5d13a6f7cd915932aca9321fbc1c31f | NL | image | 43 b | whitelisted |
3528 | chrome.exe | GET | 200 | 104.18.11.39:80 | http://cacerts.rapidssl.com/RapidSSLRSACA2018.crt | US | der | 1.18 Kb | whitelisted |
3528 | chrome.exe | GET | 200 | 52.85.182.224:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3528 | chrome.exe | GET | 200 | 52.85.182.224:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3528 | chrome.exe | GET | 200 | 67.27.158.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3528 | chrome.exe | 194.187.98.221:80 | deloton.com | Webzilla B.V. | NL | unknown |
3528 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3528 | chrome.exe | 188.42.160.69:80 | my.rtmark.net | Webzilla B.V. | NL | unknown |
3528 | chrome.exe | 188.72.213.176:80 | cobalten.com | Webzilla B.V. | NL | unknown |
3528 | chrome.exe | 104.108.33.99:80 | m-in.gearbest.com | Akamai Technologies, Inc. | NL | whitelisted |
3528 | chrome.exe | 172.217.21.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3528 | chrome.exe | 23.210.249.155:443 | css.gbtcdn.com | Akamai International B.V. | NL | whitelisted |
3528 | chrome.exe | 185.60.216.19:443 | platform-lookaside.fbsbx.com | Facebook, Inc. | IE | whitelisted |
3528 | chrome.exe | 104.108.33.99:443 | m-in.gearbest.com | Akamai Technologies, Inc. | NL | whitelisted |
3528 | chrome.exe | 216.58.206.1:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
deloton.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
my.rtmark.net |
| whitelisted |
m-in.gearbest.com |
| unknown |
cobalten.com |
| malicious |
orderm.gearbest.com |
| unknown |
css.gbtcdn.com |
| shared |
cartm.gearbest.com |
| unknown |