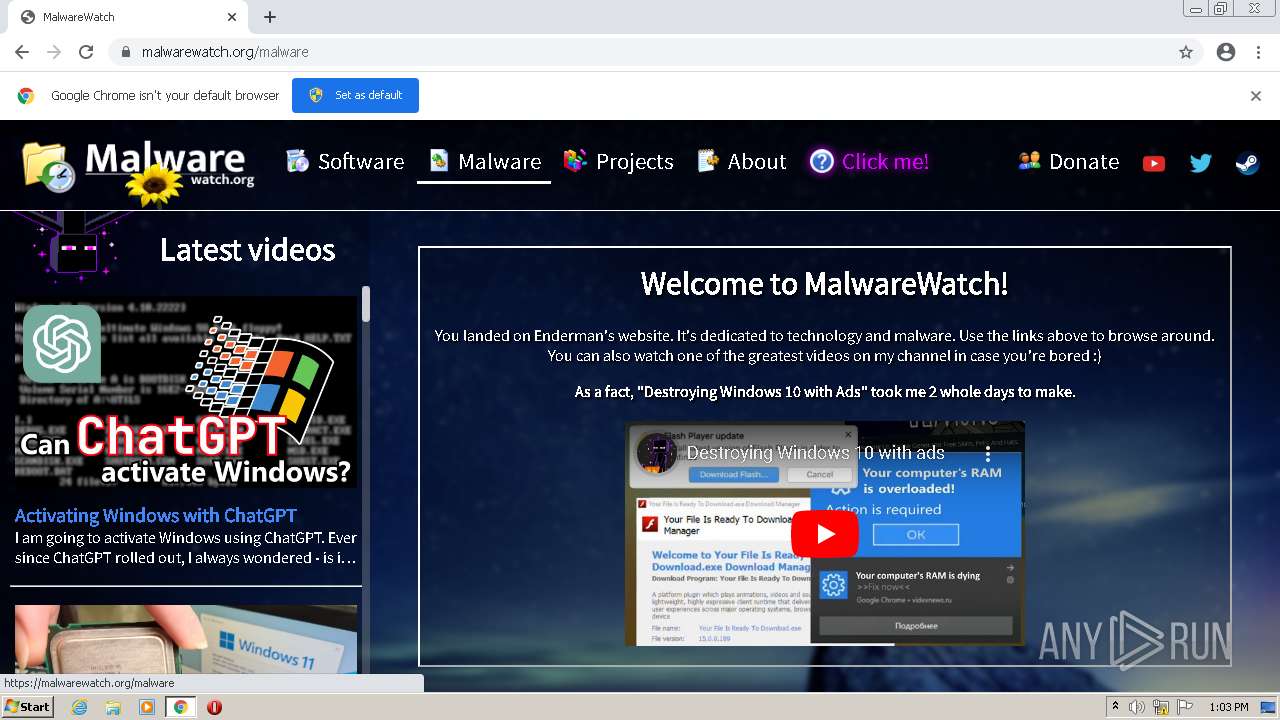
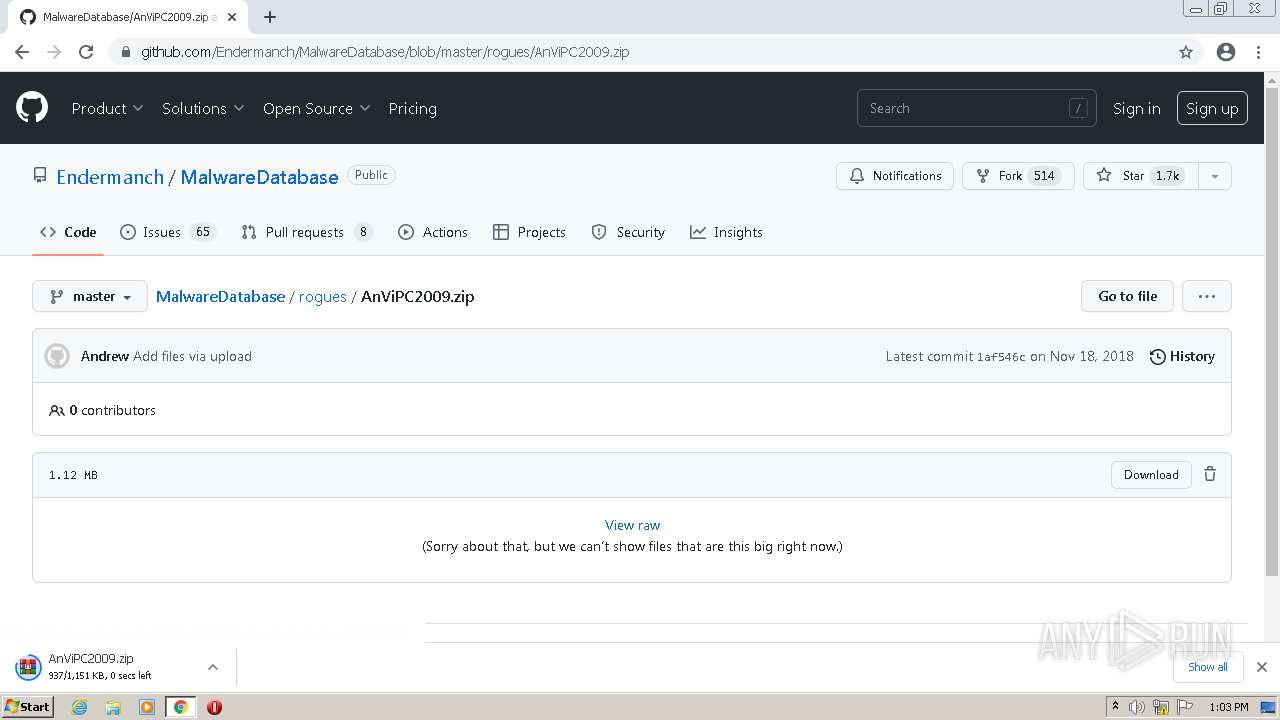
| URL: | https://malwarewatch.org |
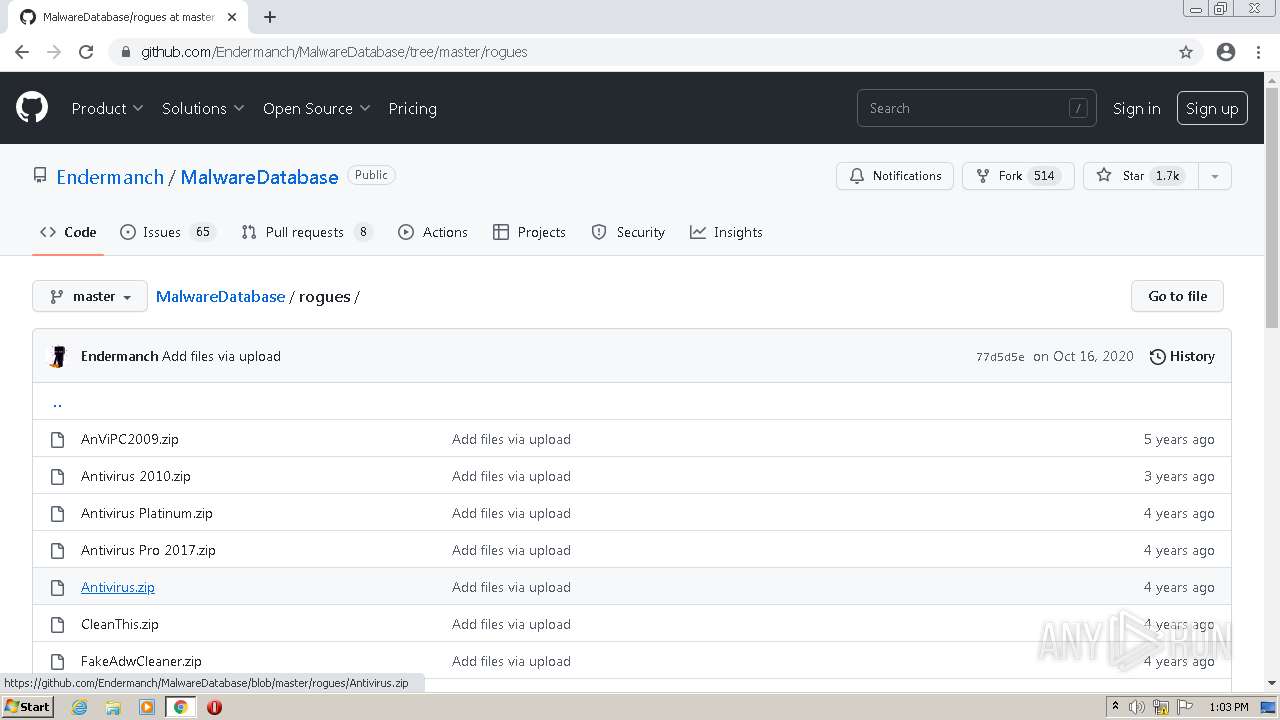
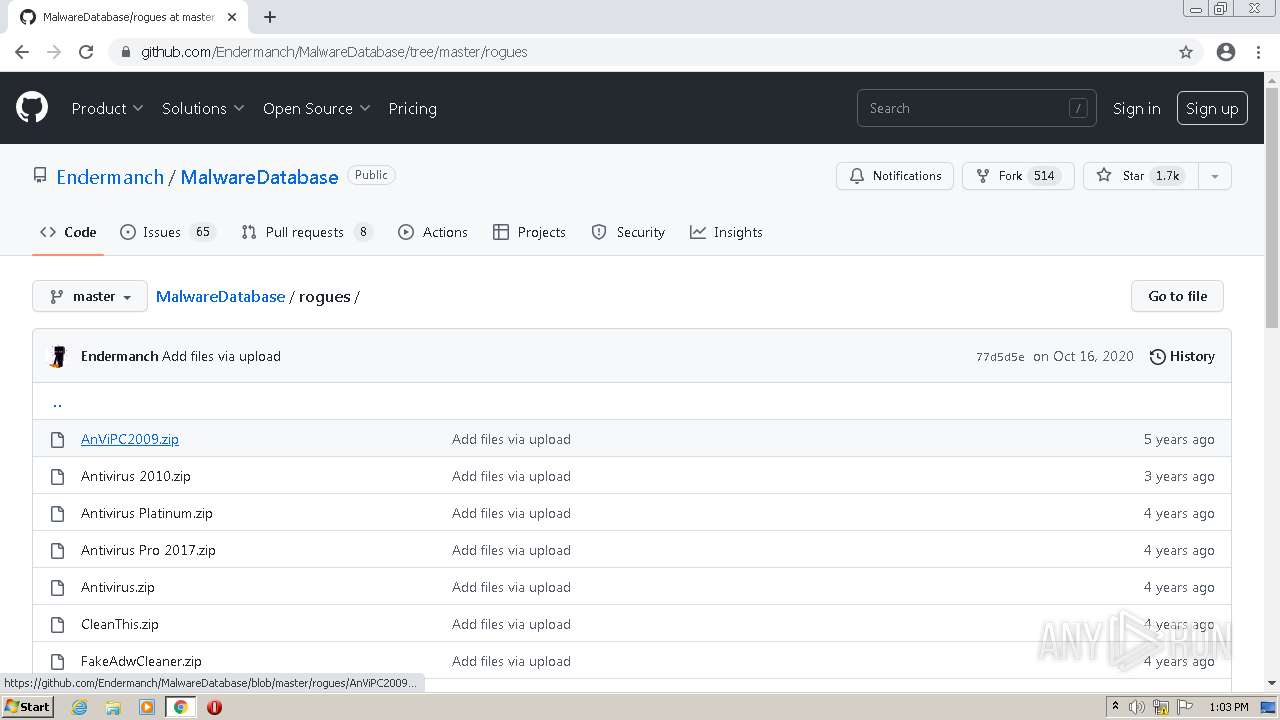
| Full analysis: | https://app.any.run/tasks/6a310cb7-46a6-4e8d-bf4d-261e4a5891f1 |
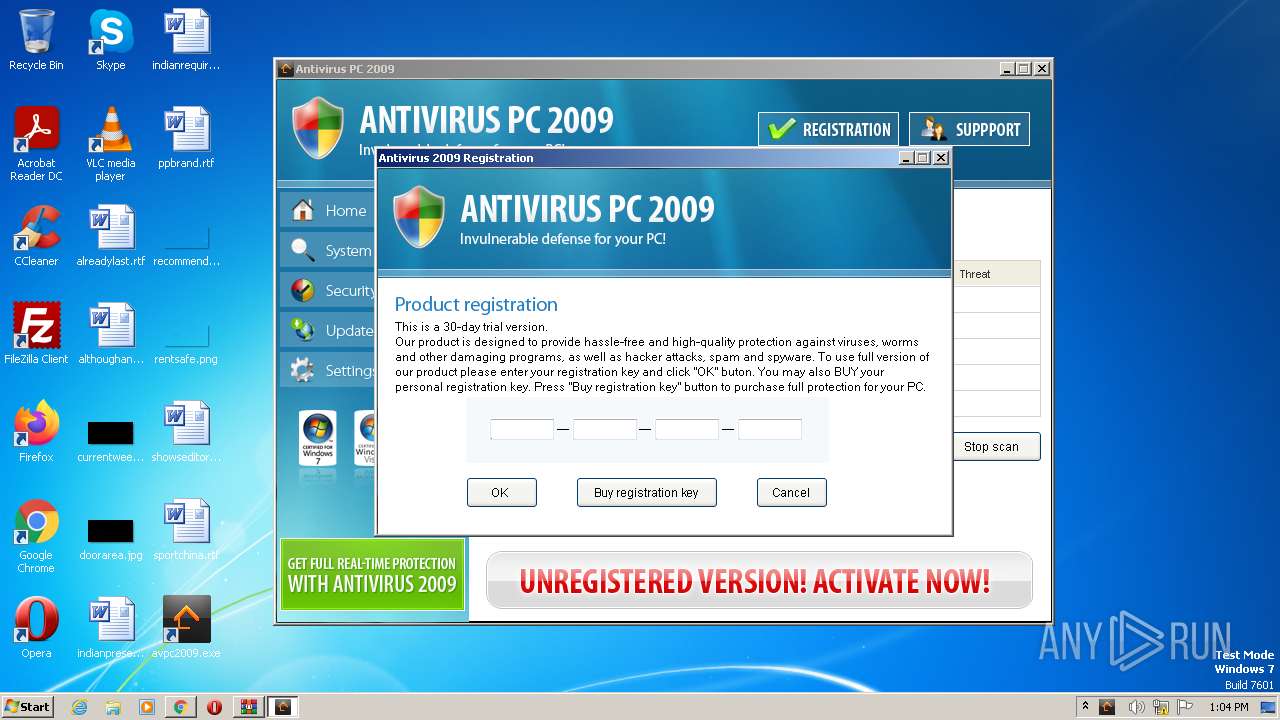
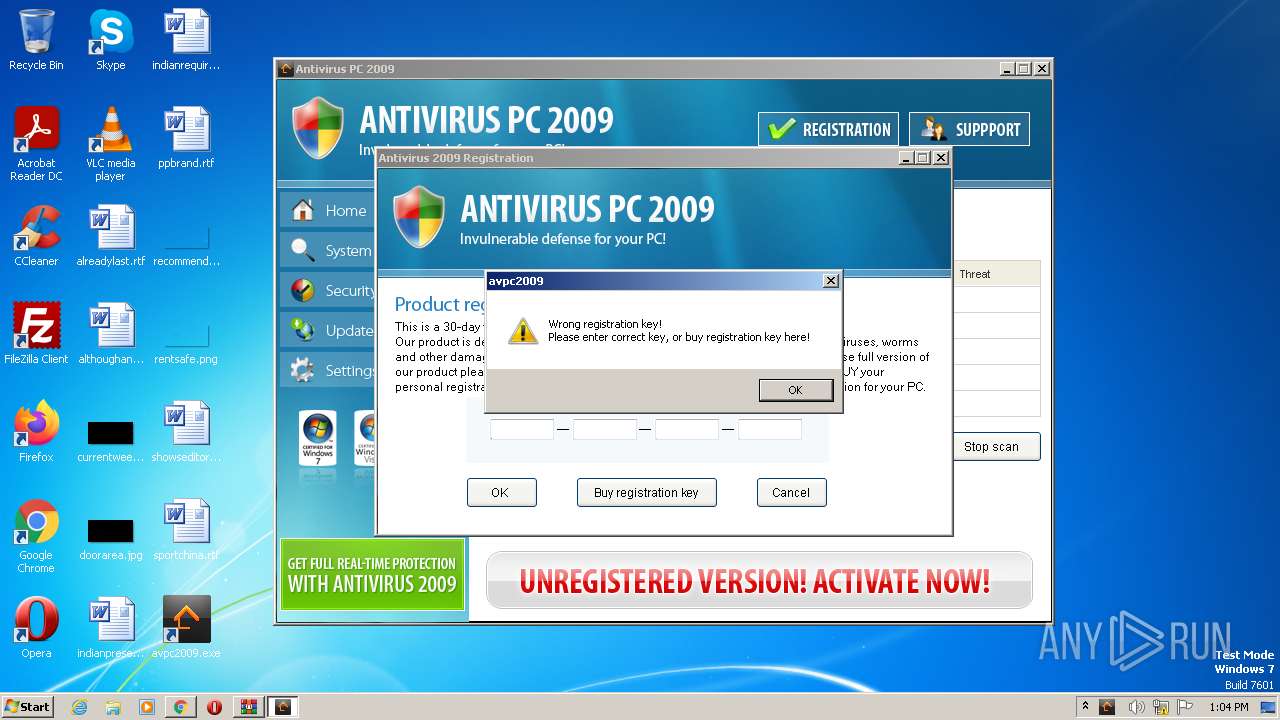
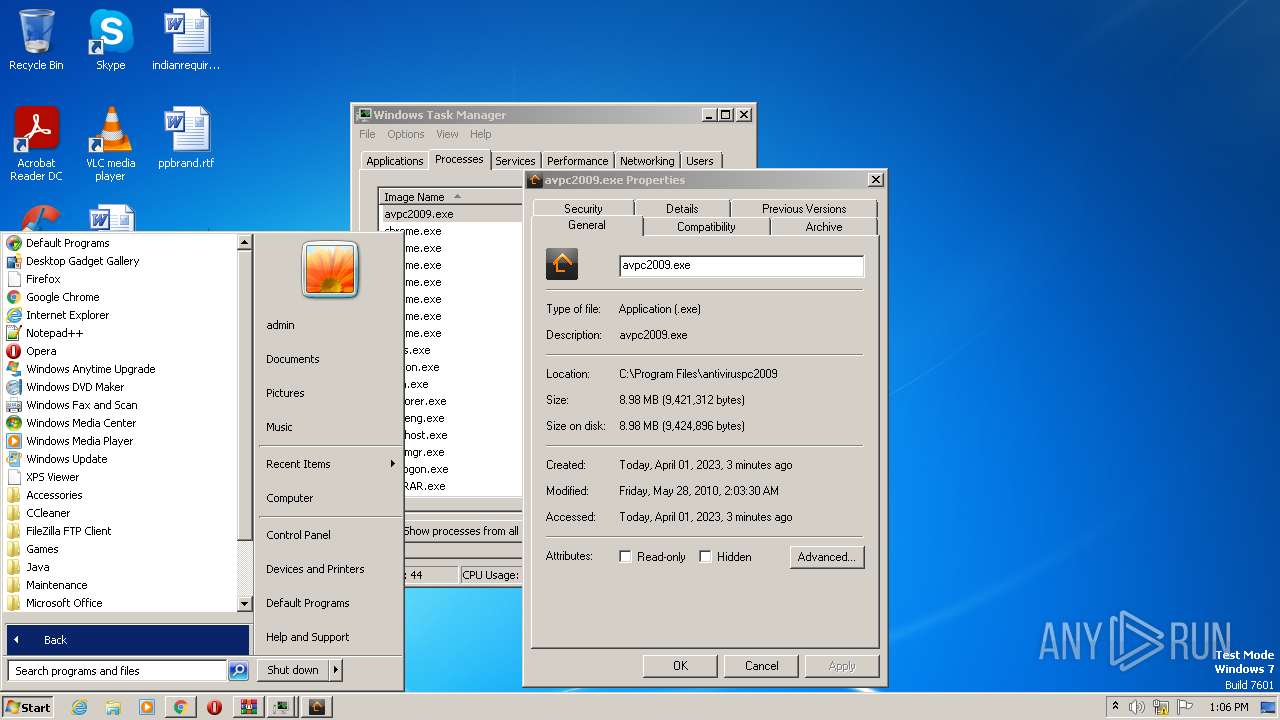
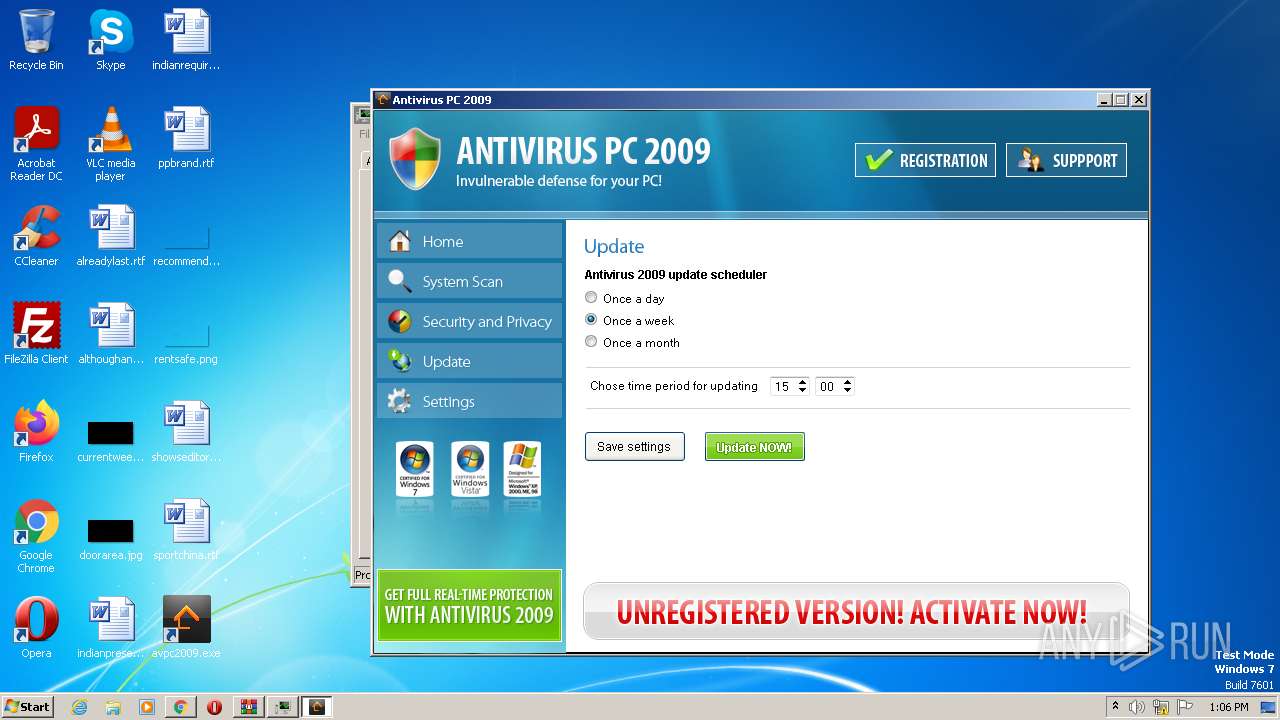
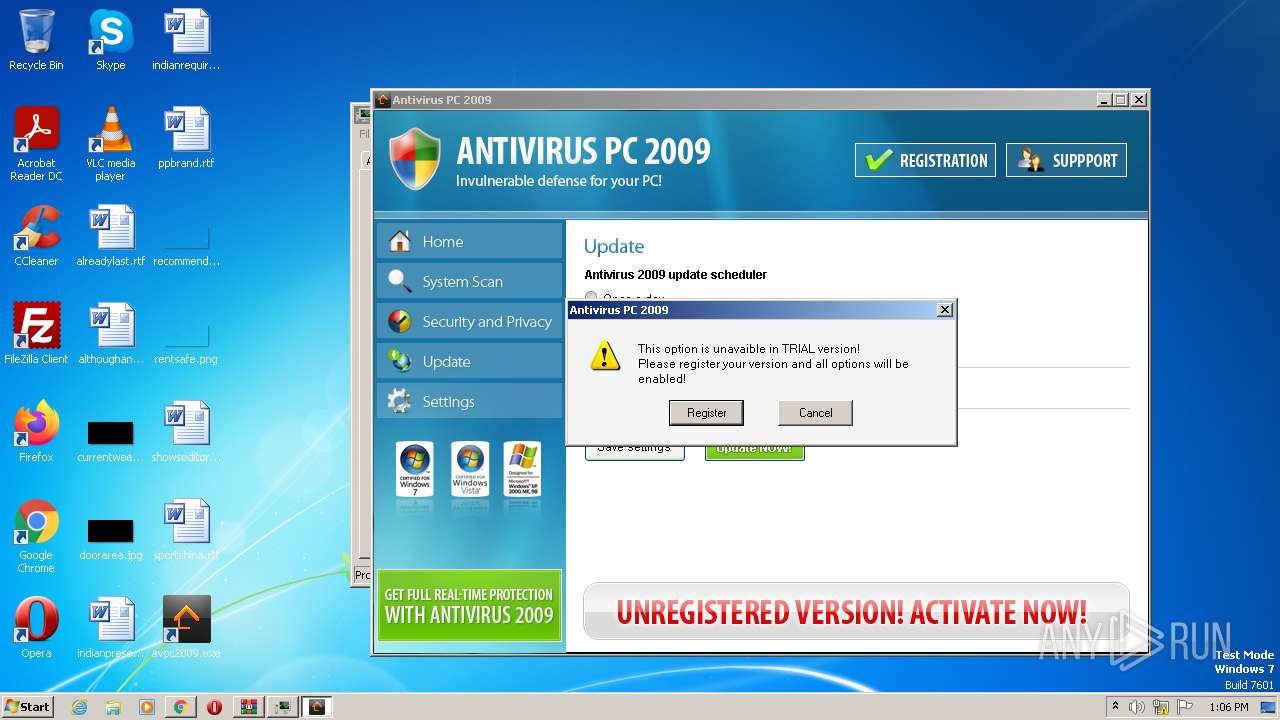
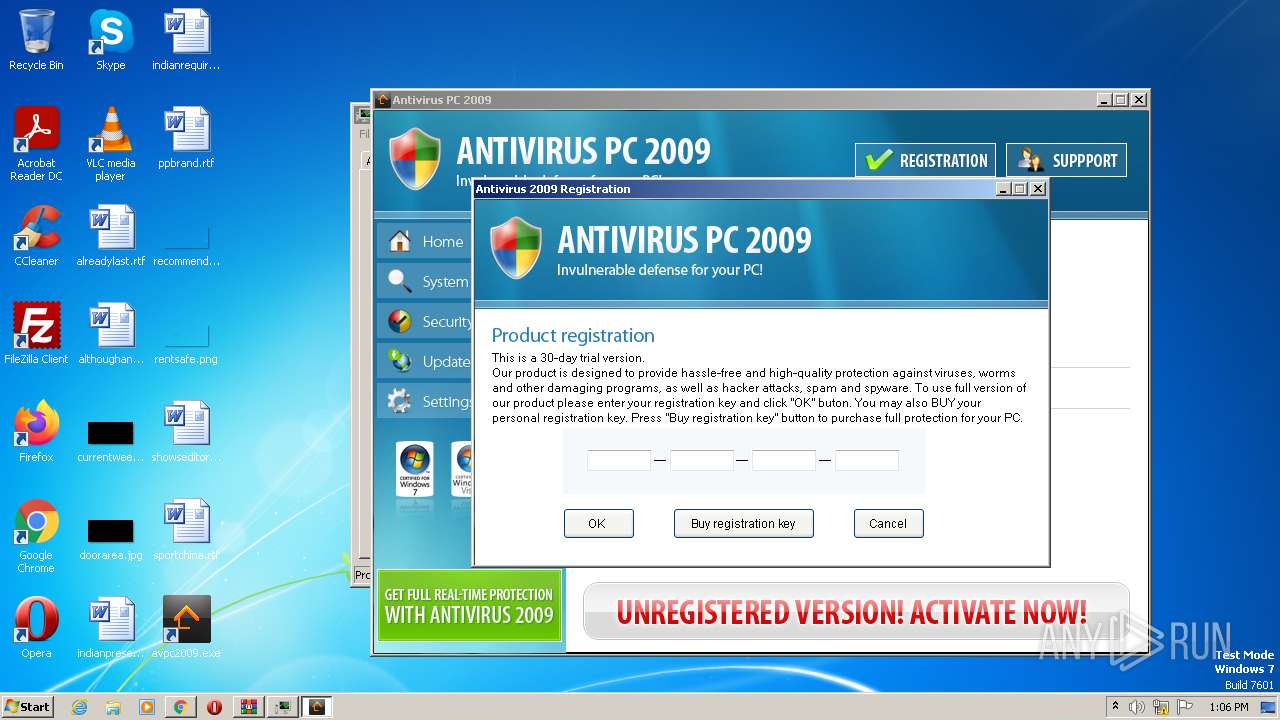
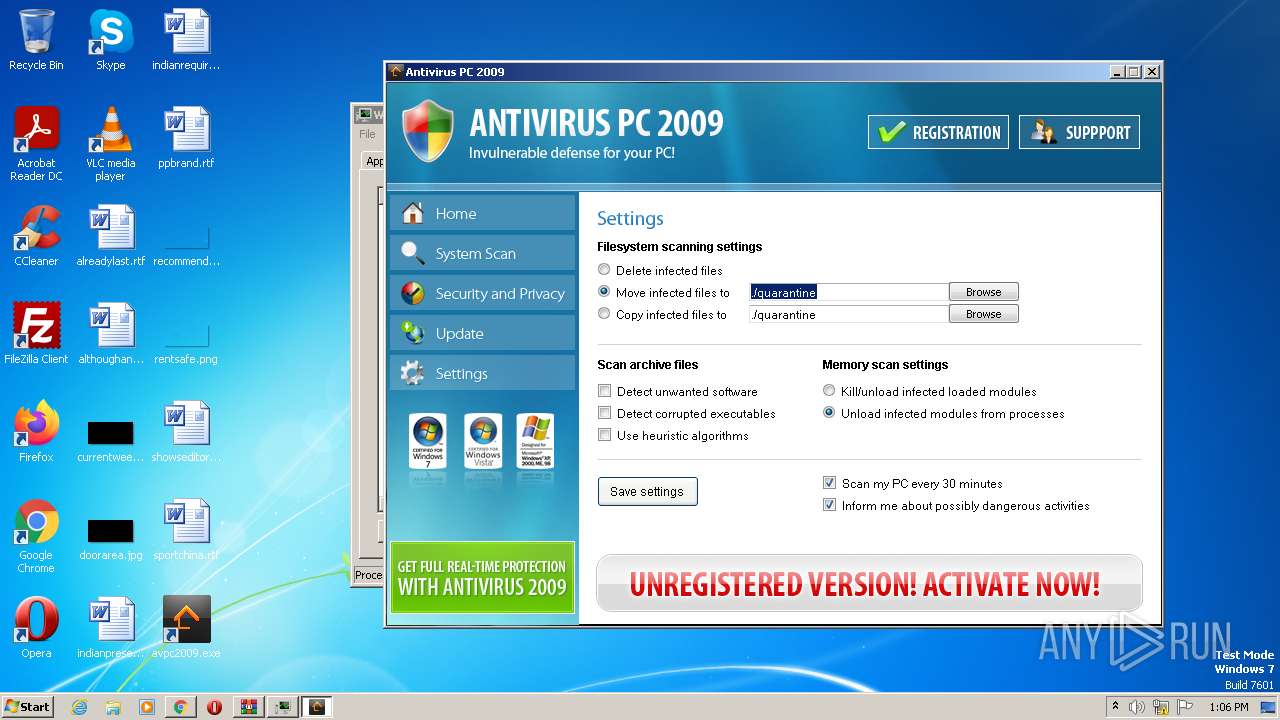
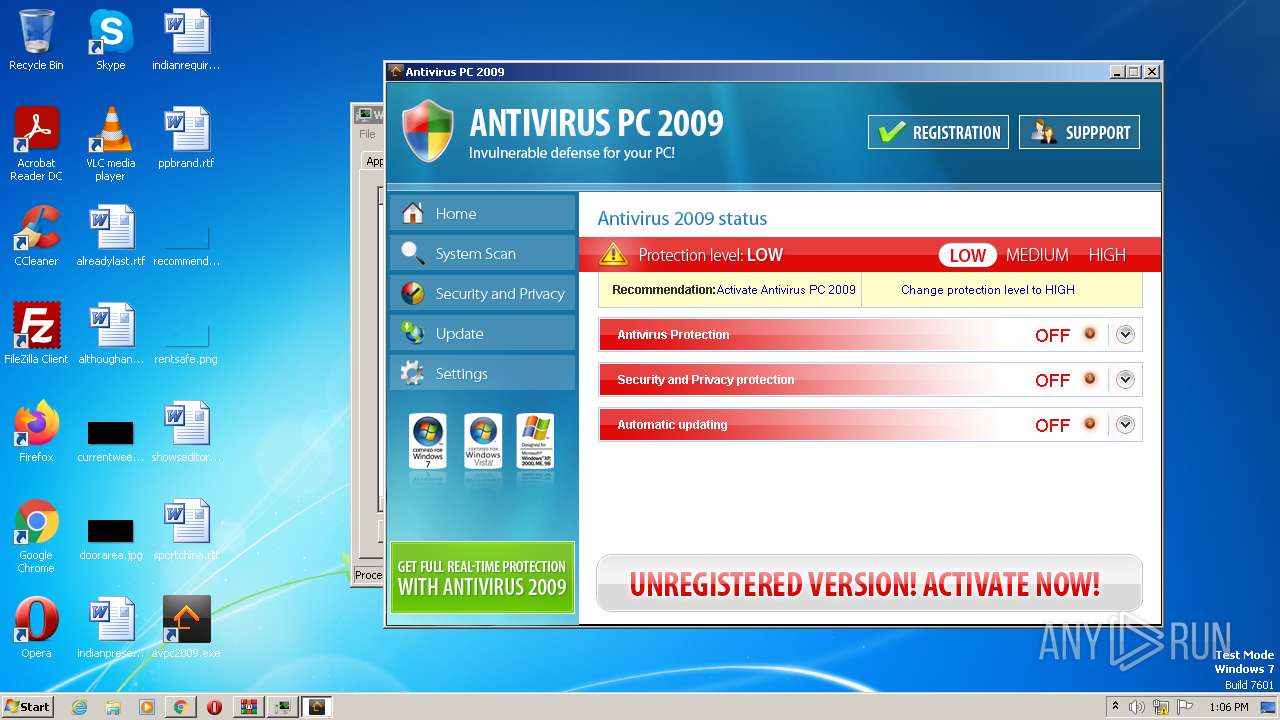
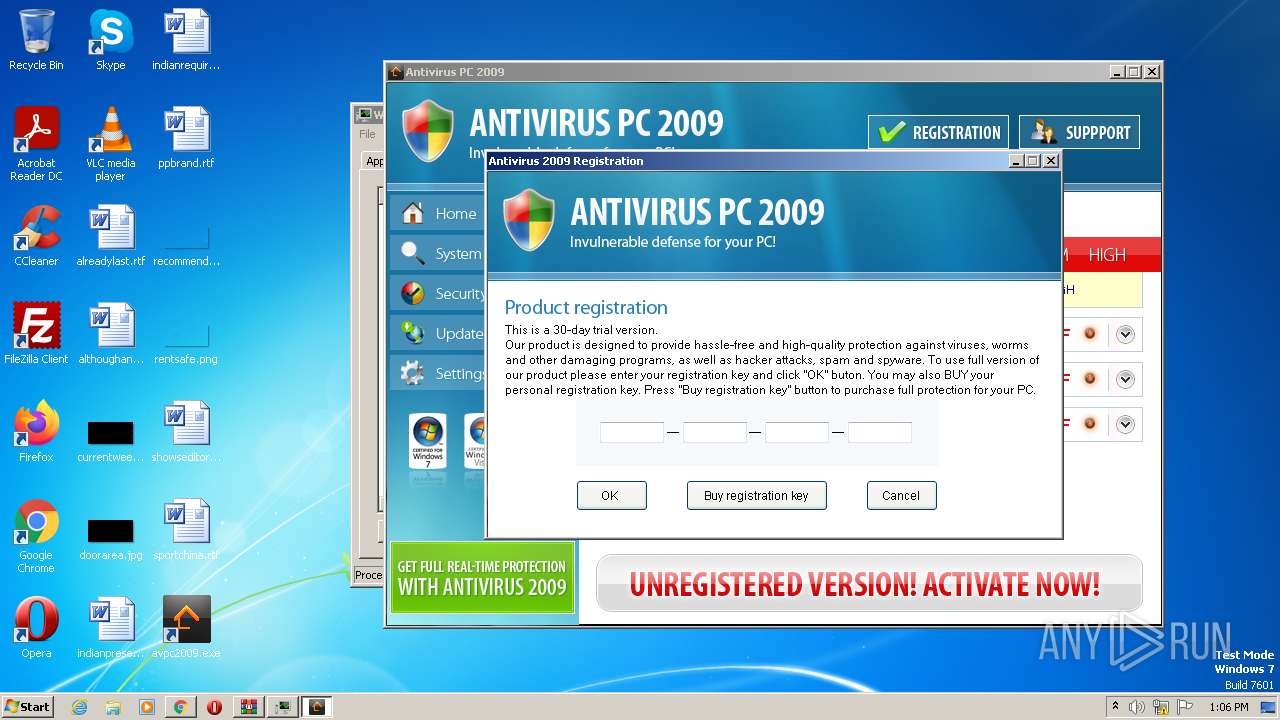
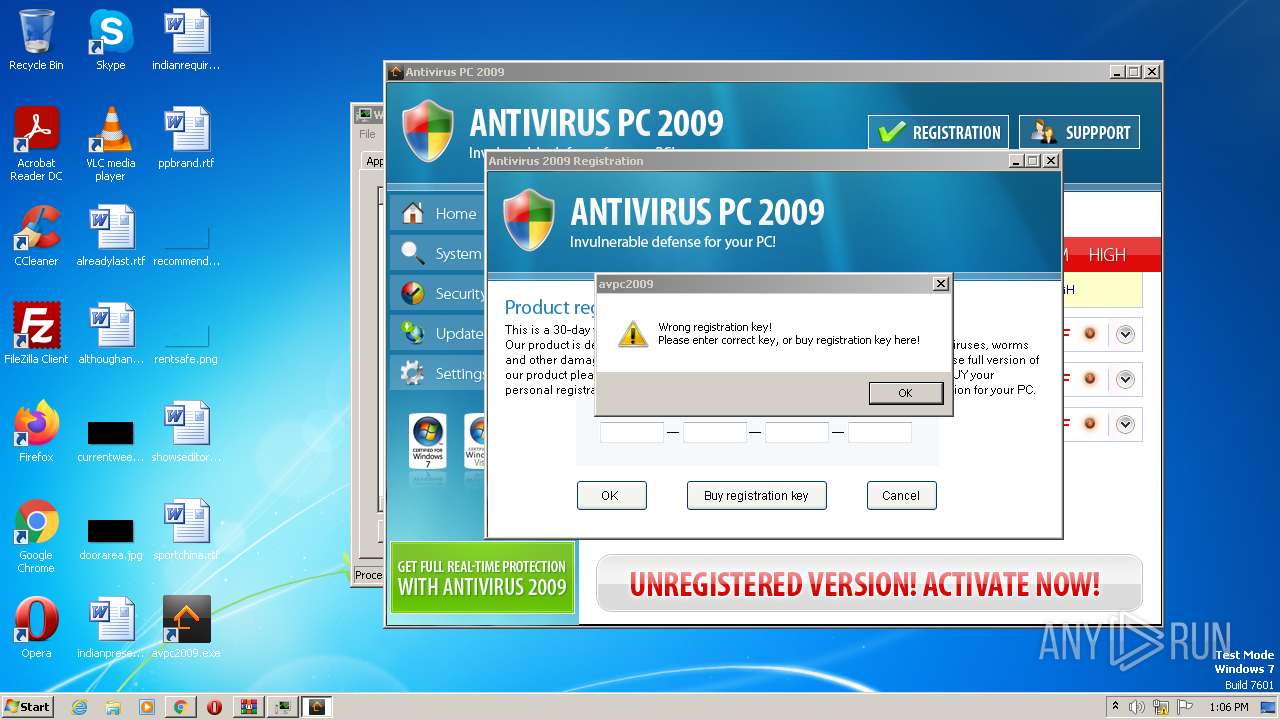
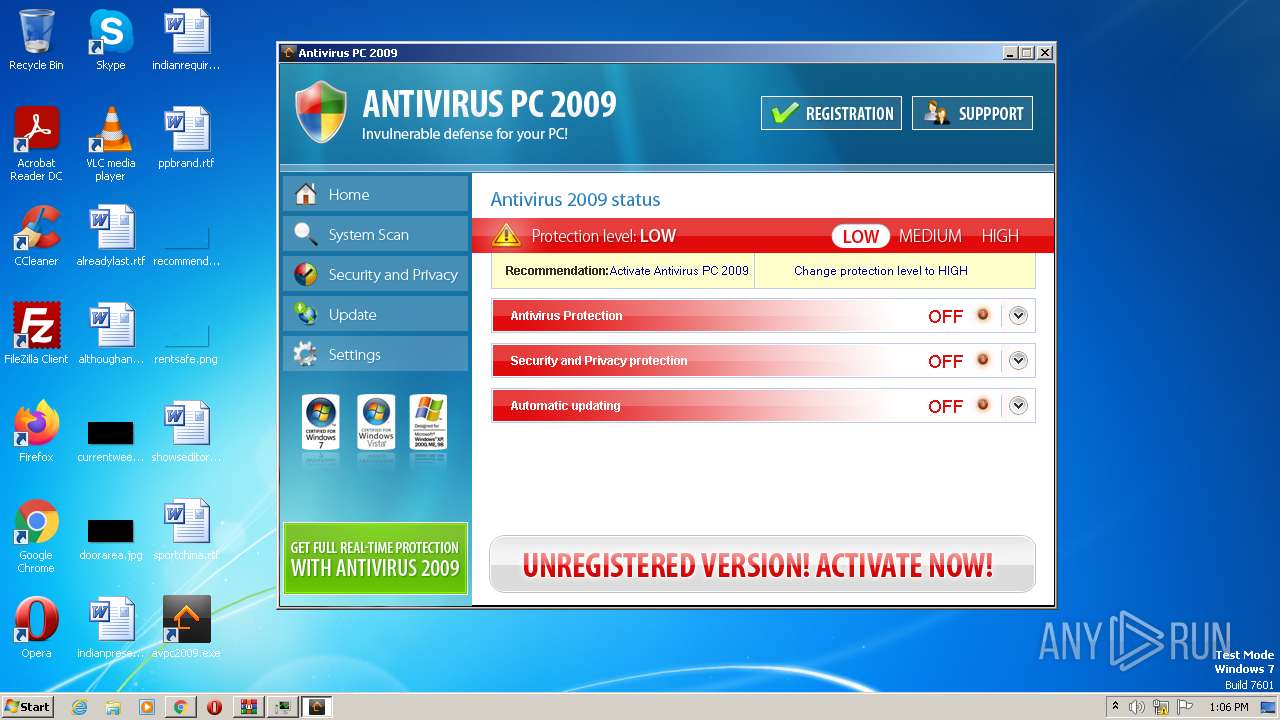
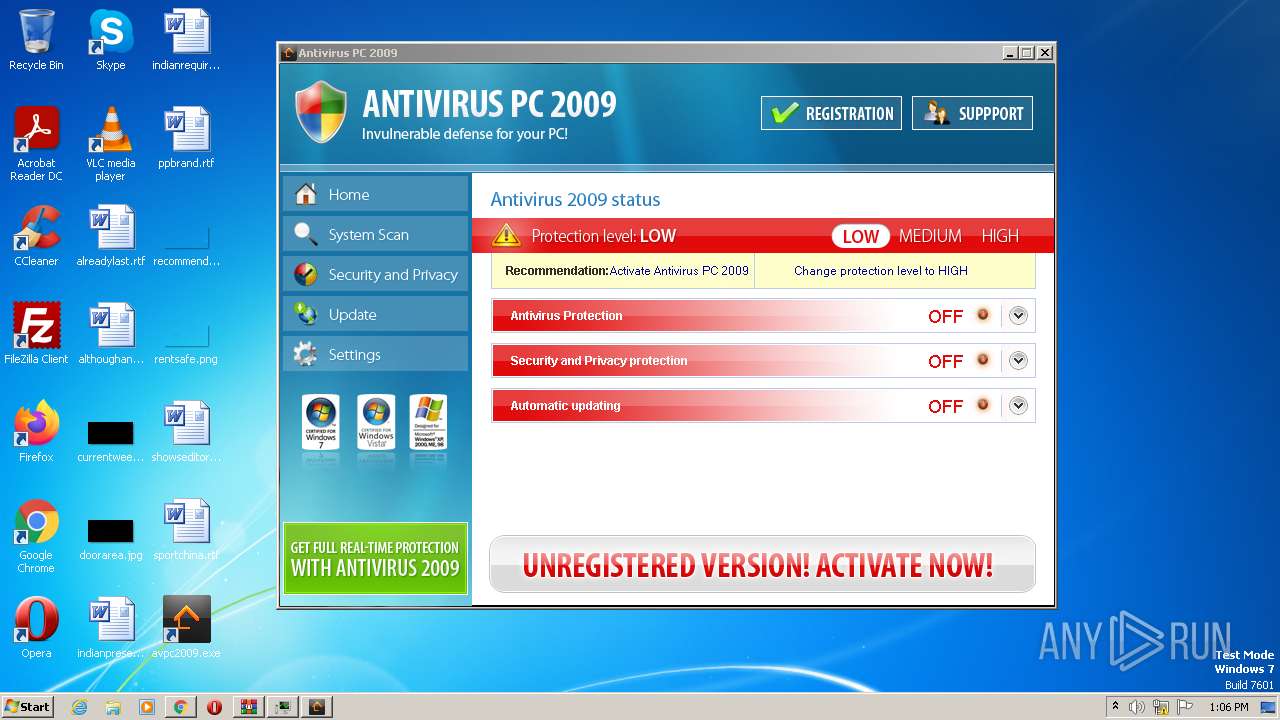
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 12:03:02 |
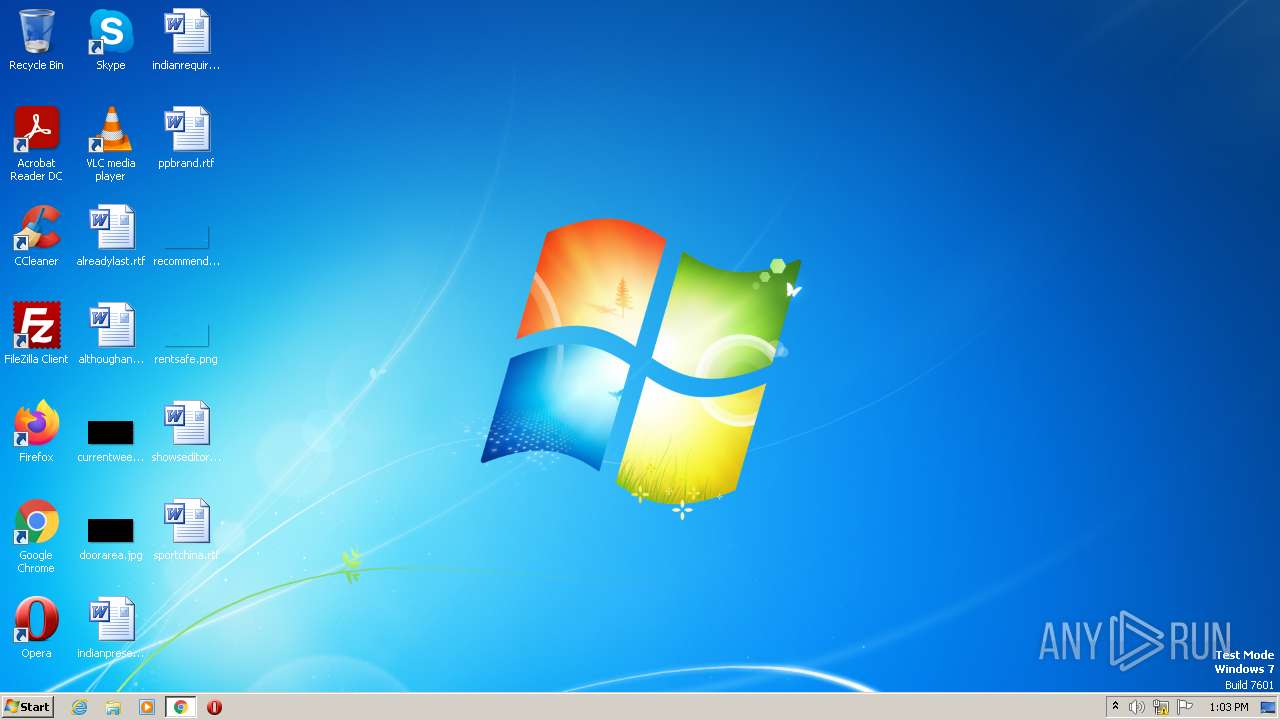
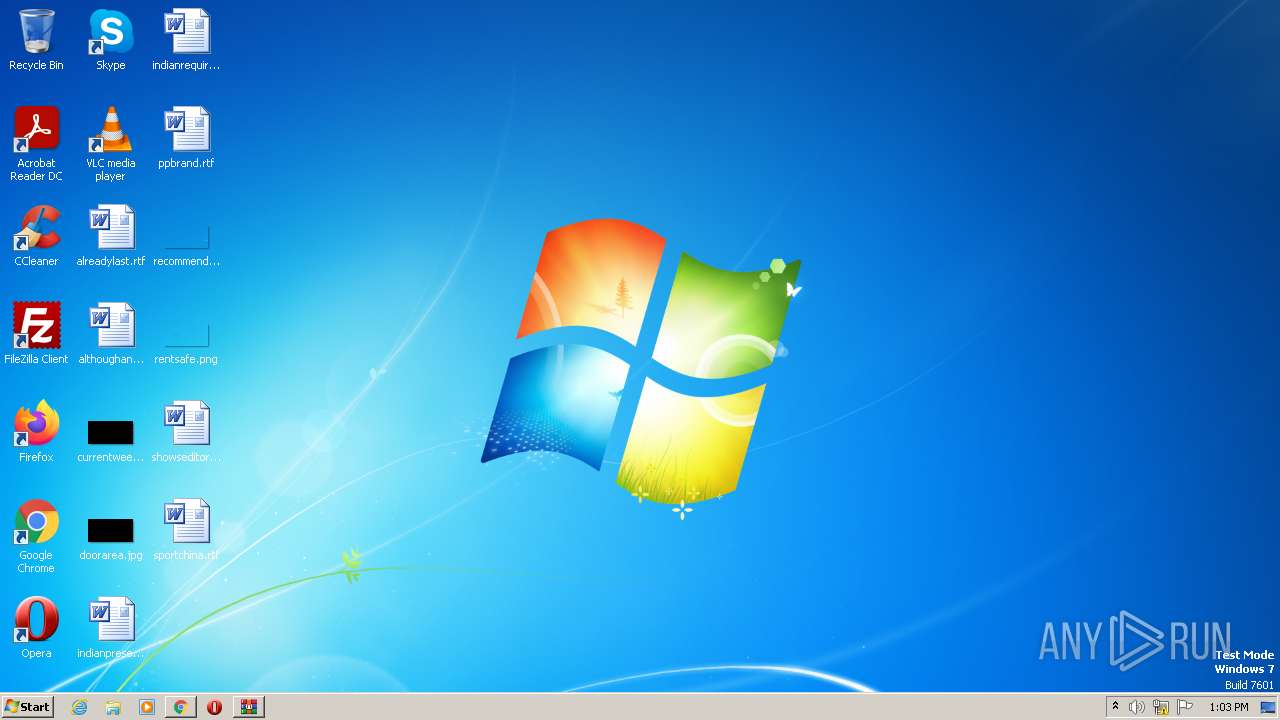
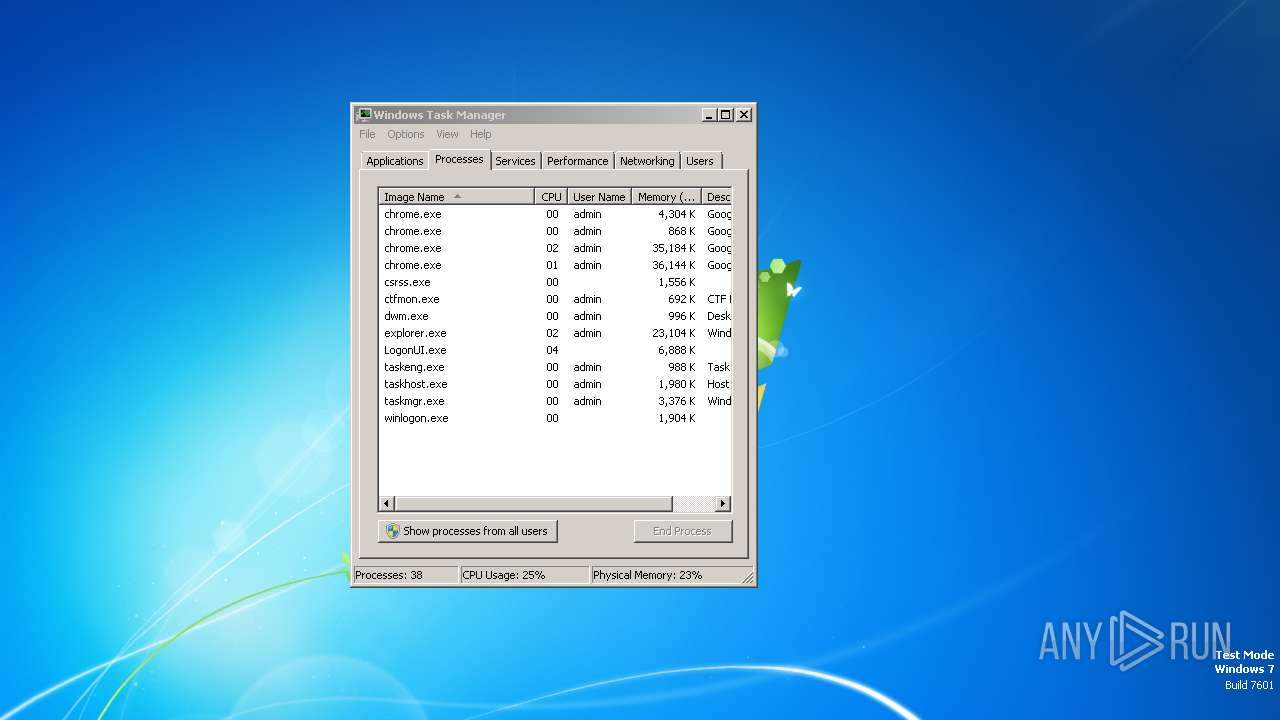
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 38471DF050AB7E5C142EE8F547E663D7 |
| SHA1: | EA7D6278ABCE991311717011007C5504C58CD903 |
| SHA256: | 523C8F5DD1F6505A968D9830D84C96E99FD2163DBDDFBDE921C46159F782DDAF |
| SSDEEP: | 3:N8mgNn:2mY |
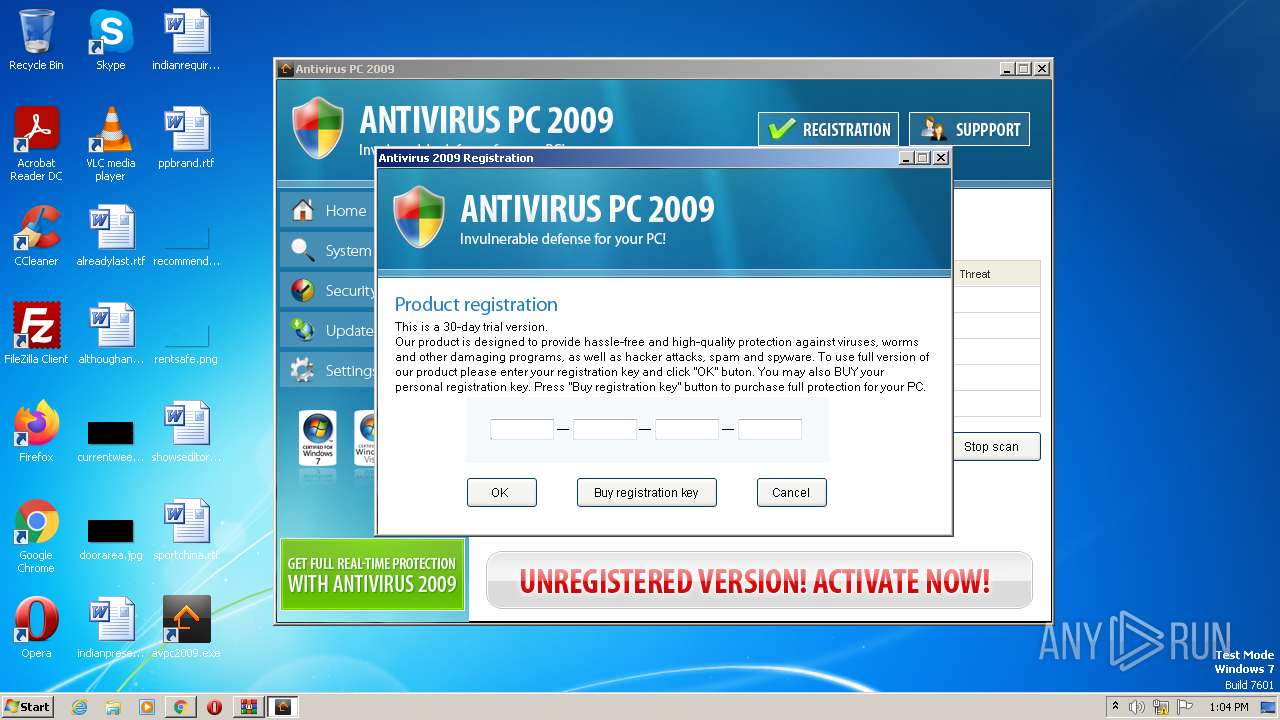
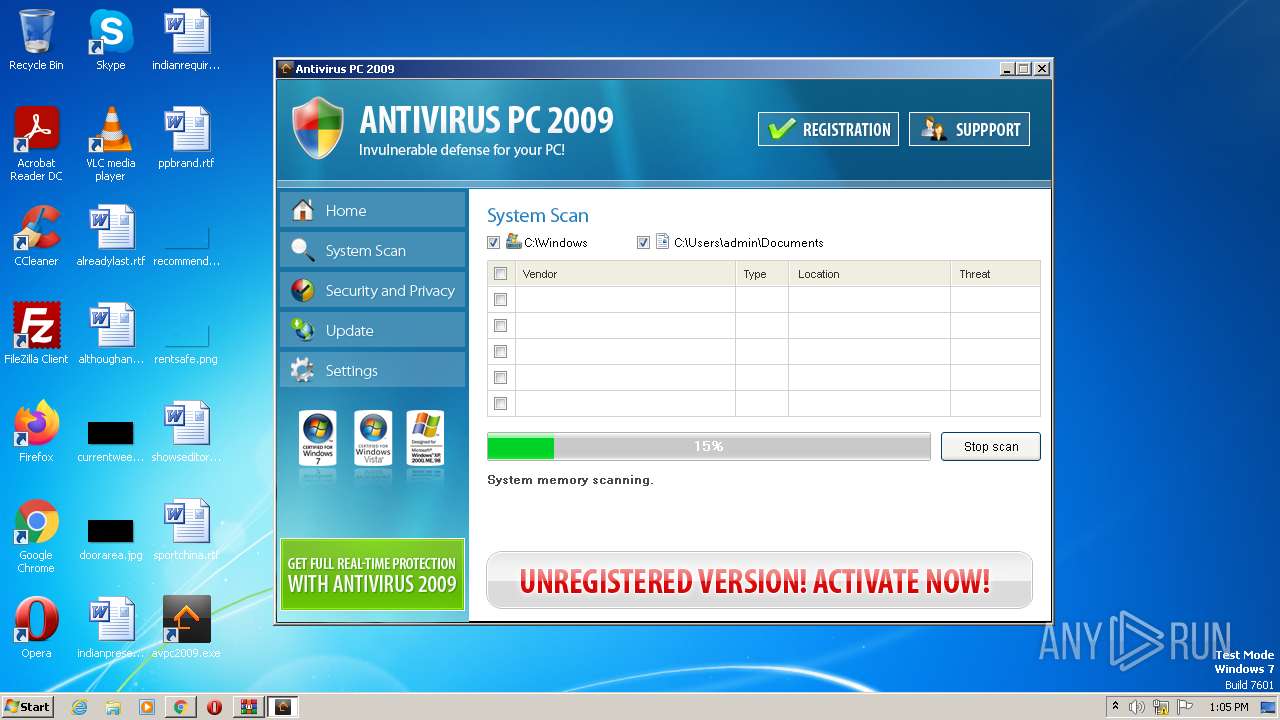
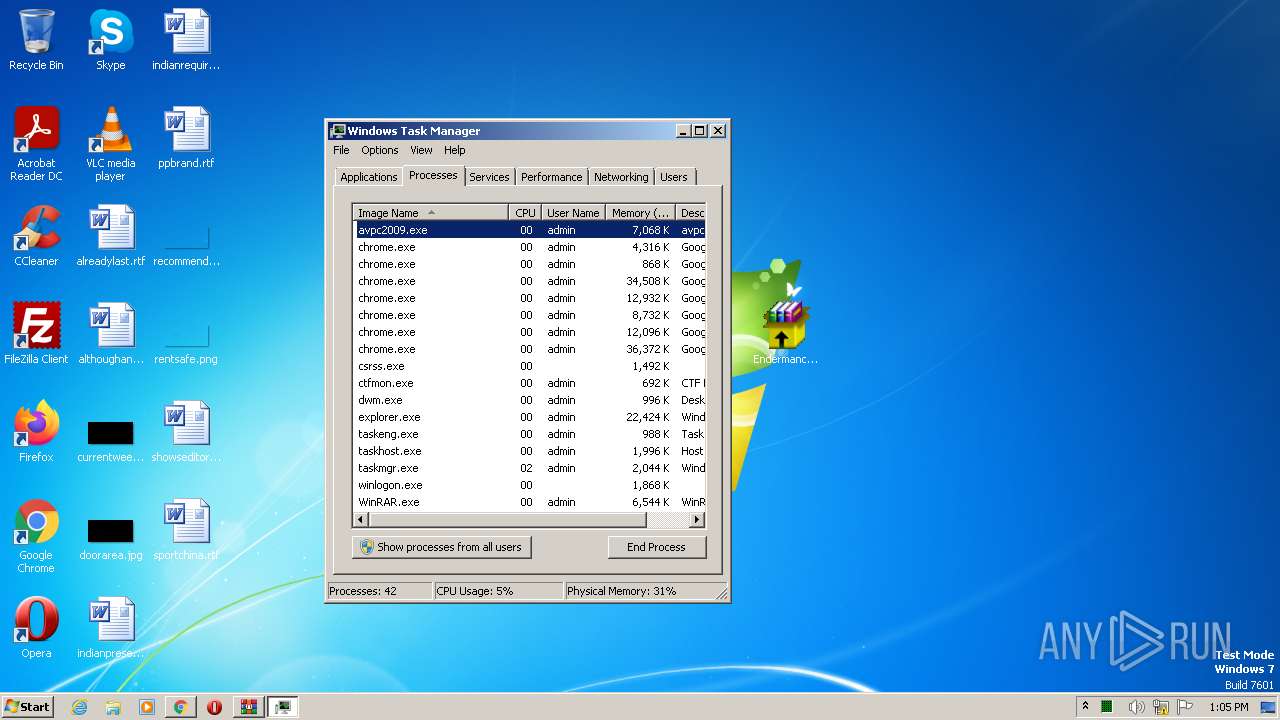
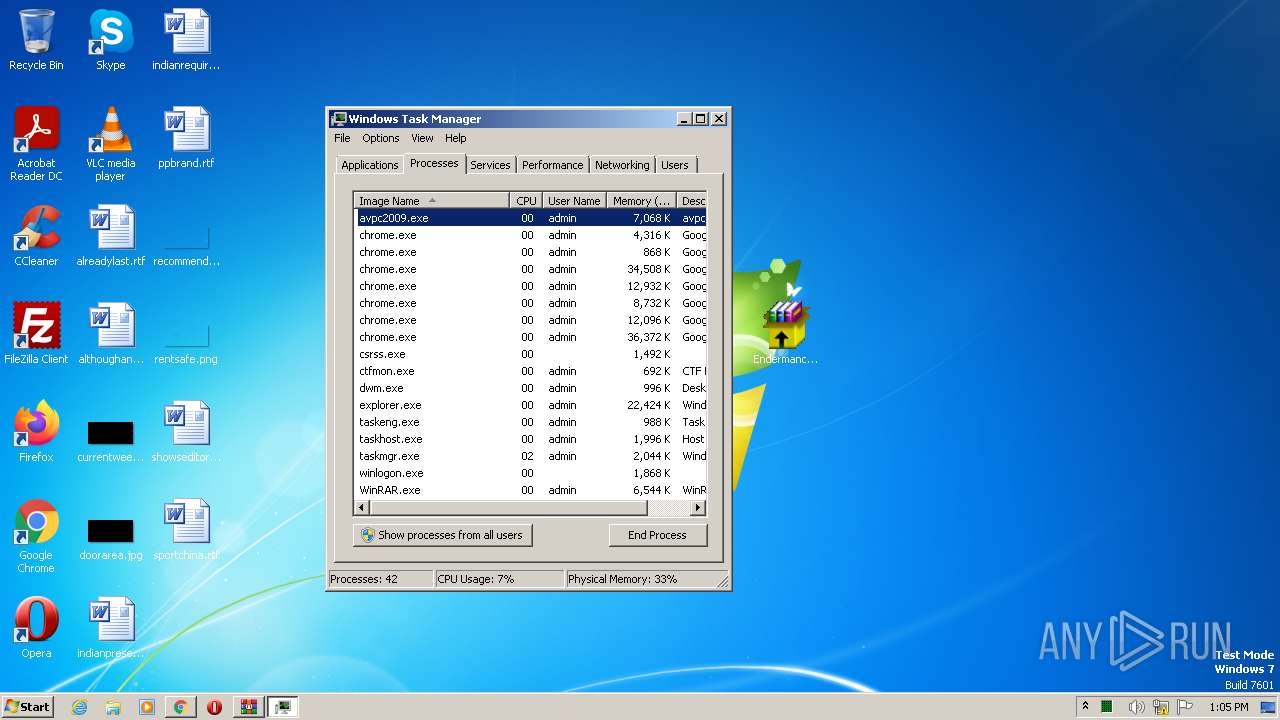
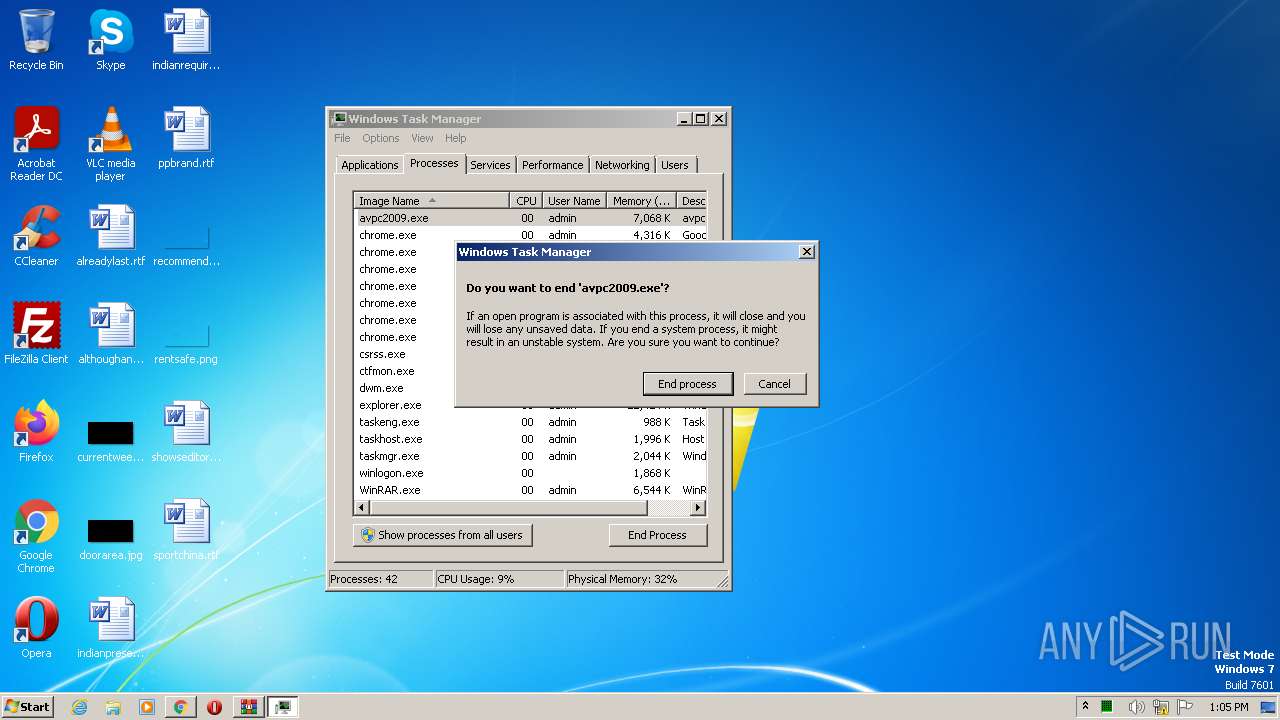
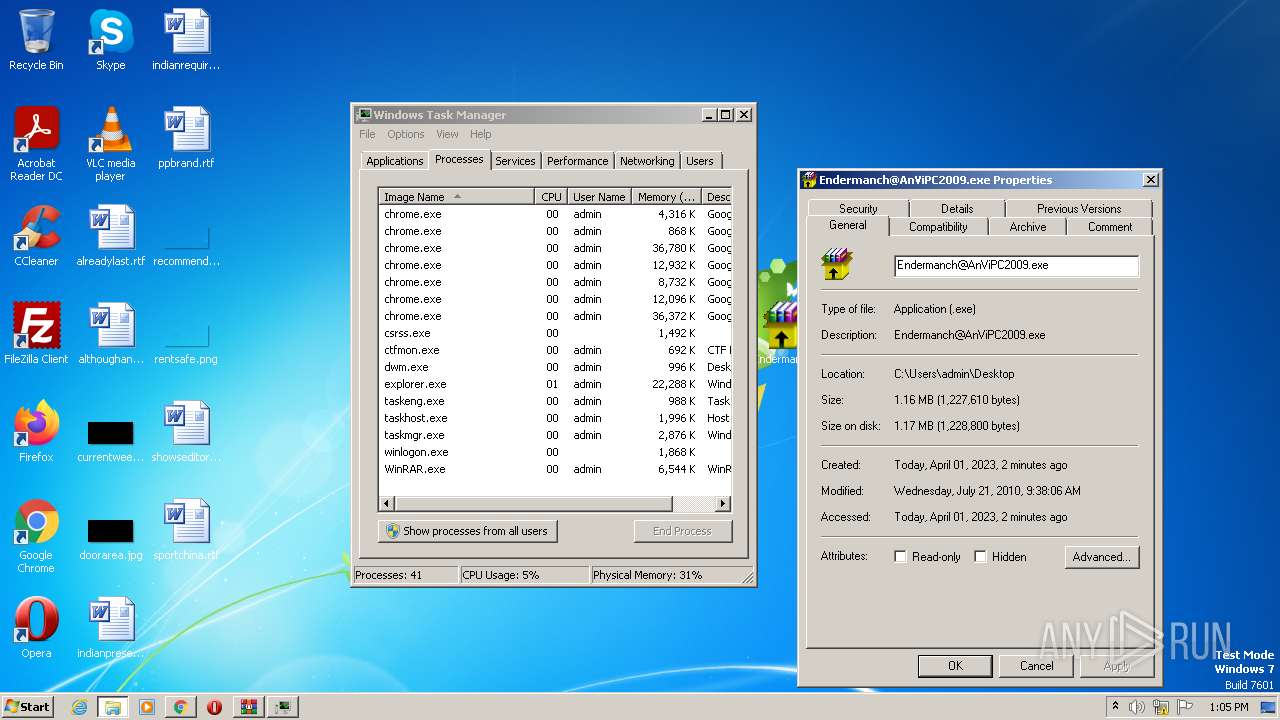
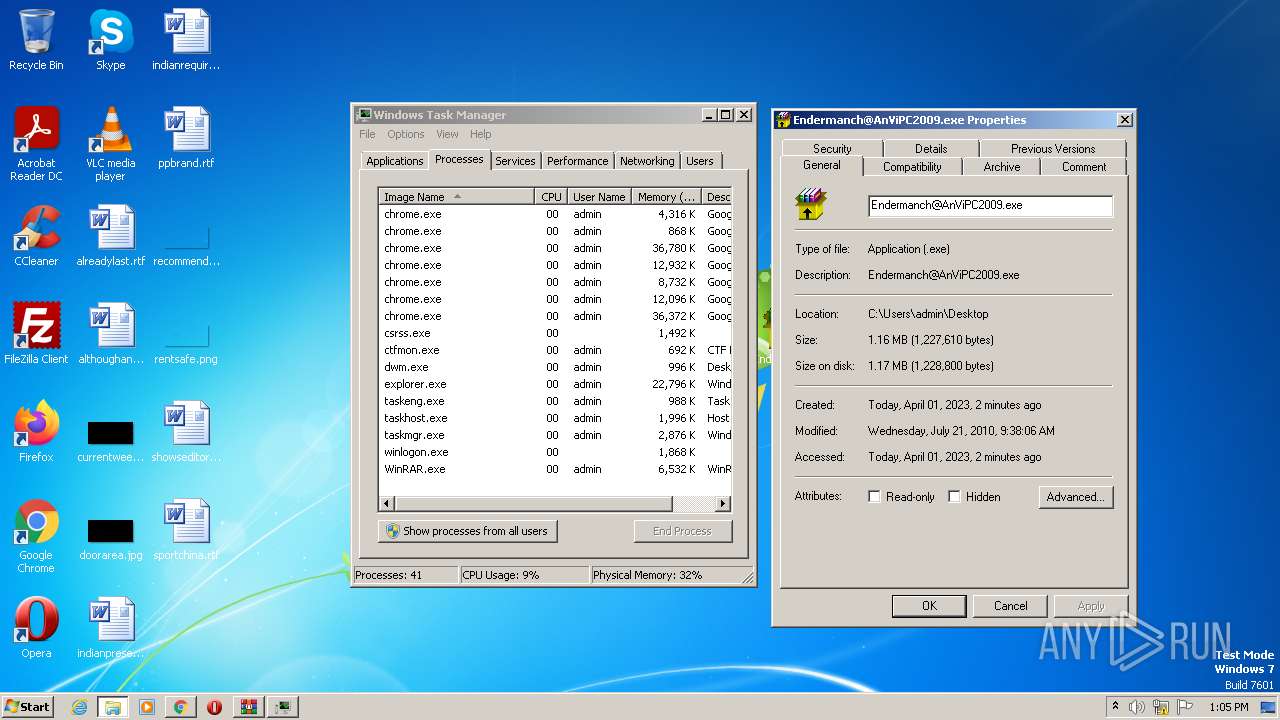
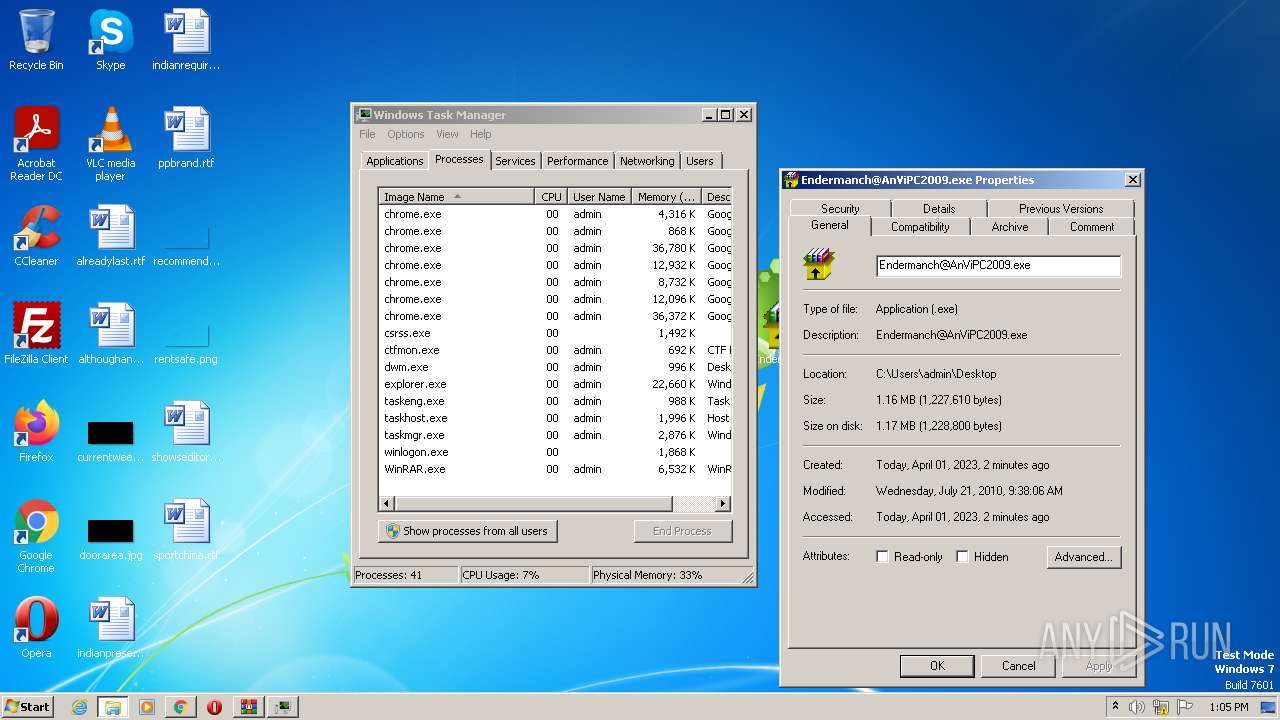
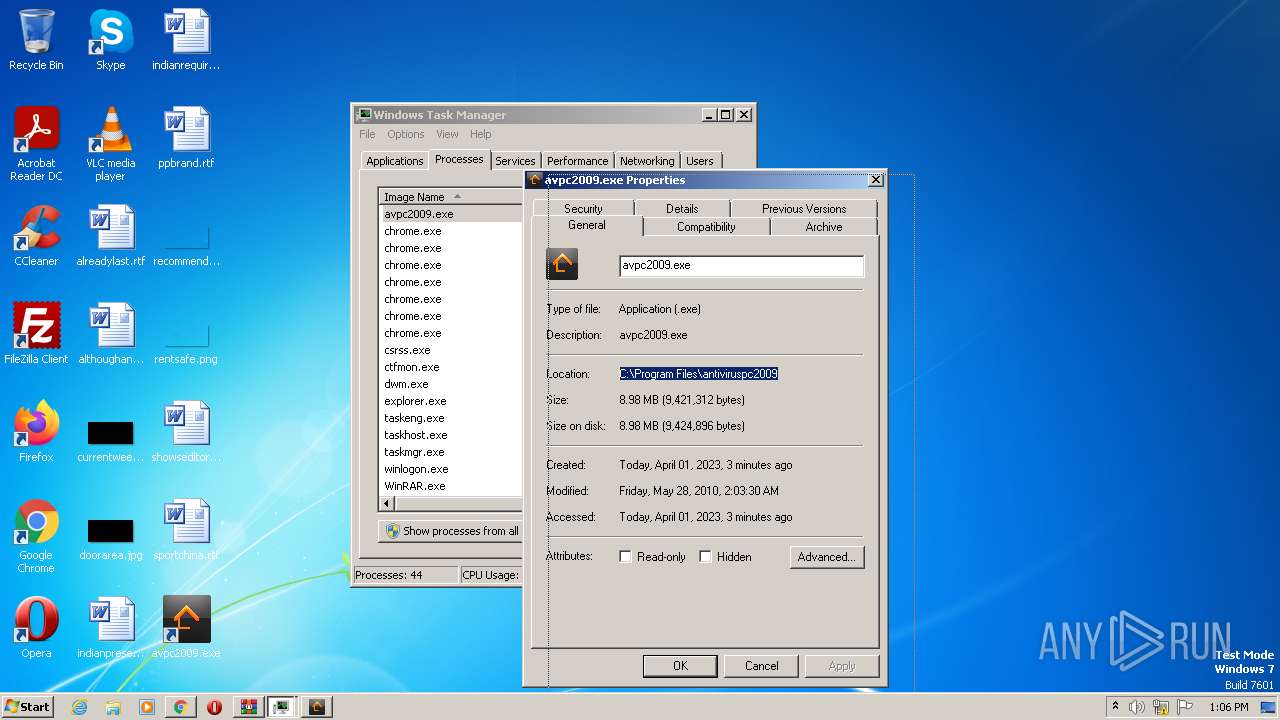
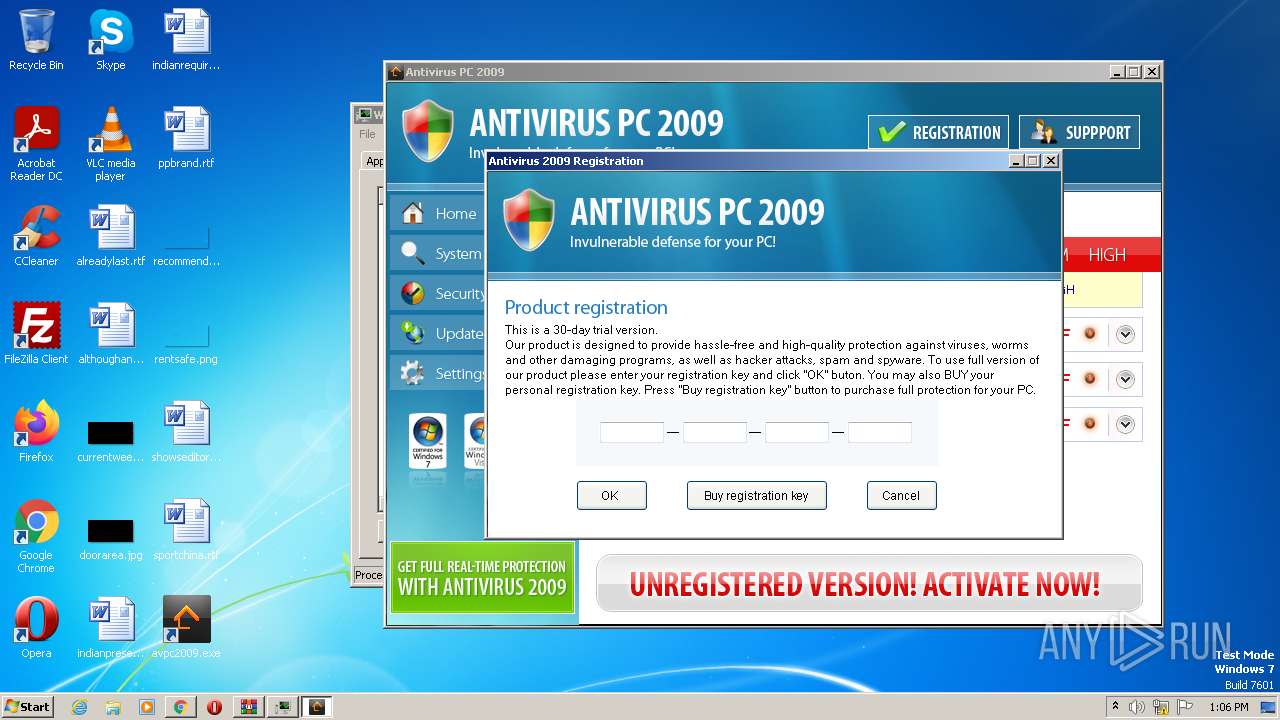
MALICIOUS
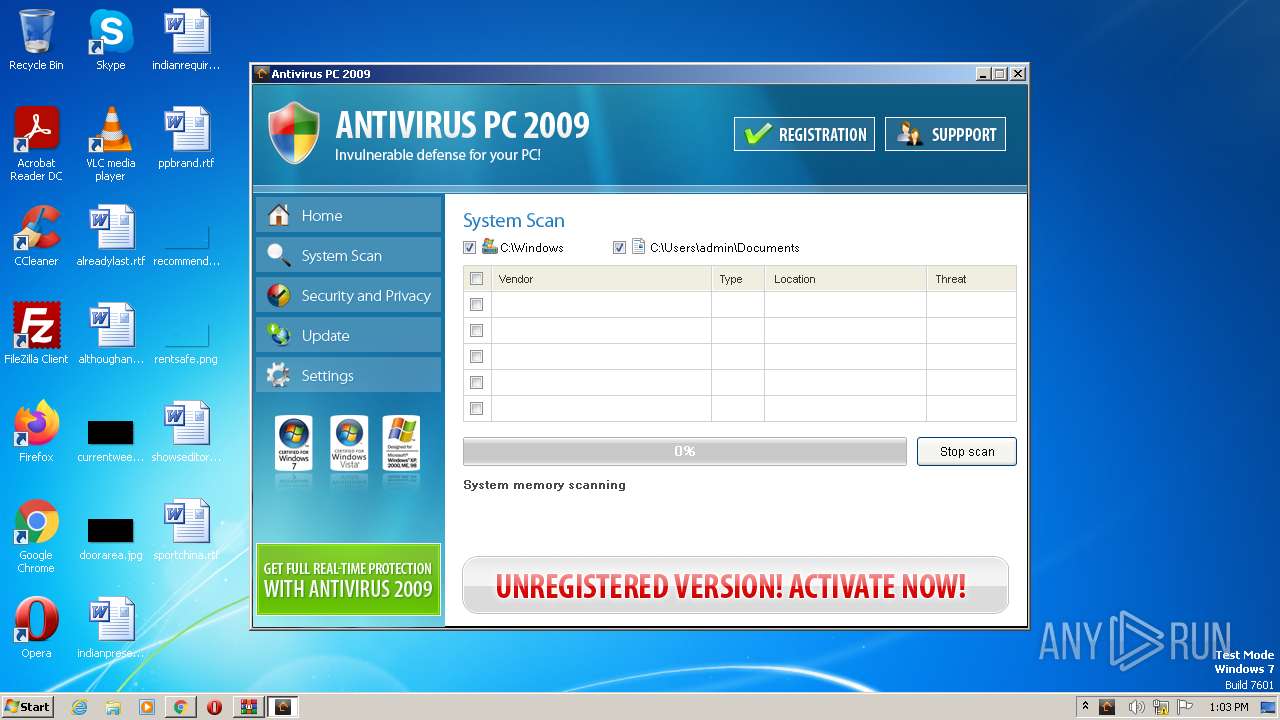
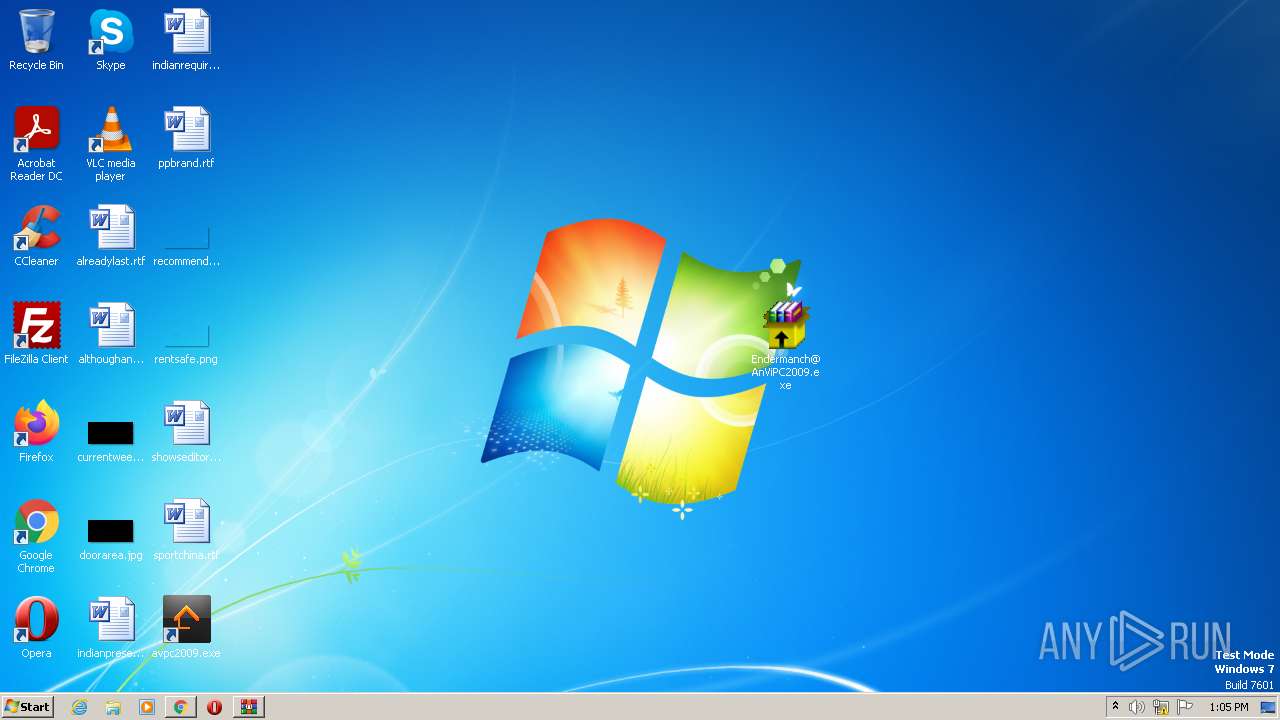
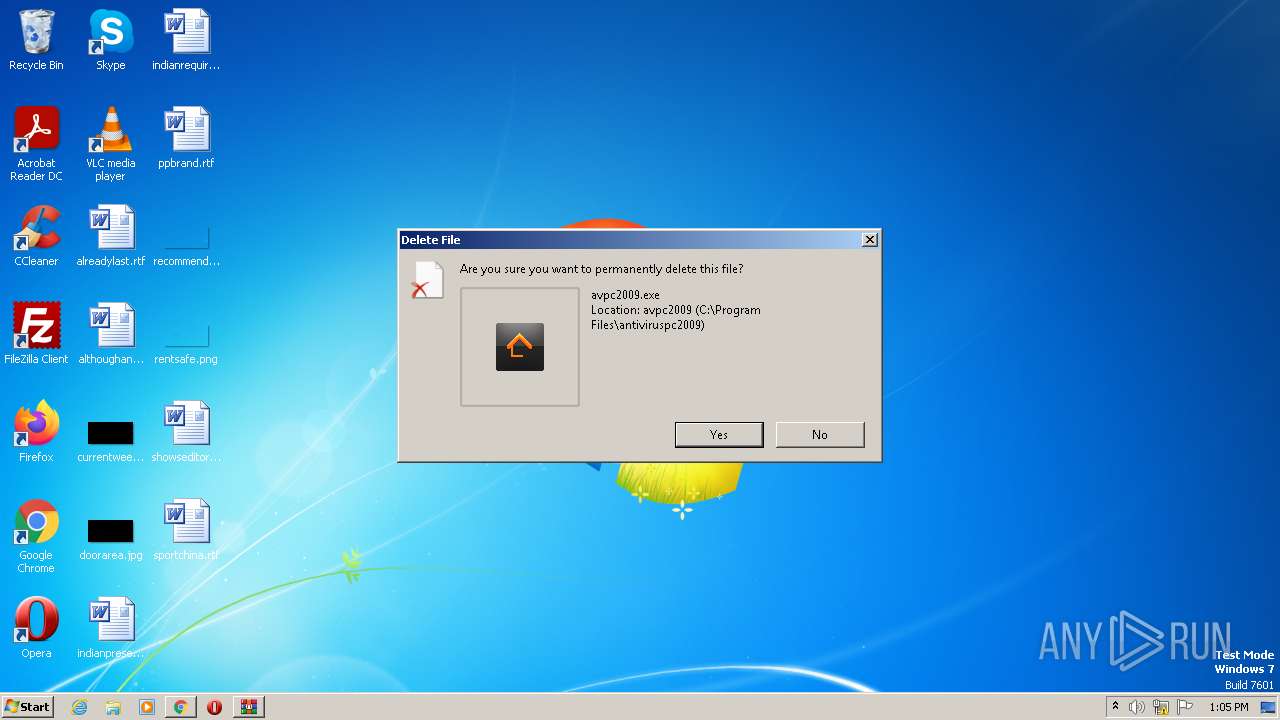
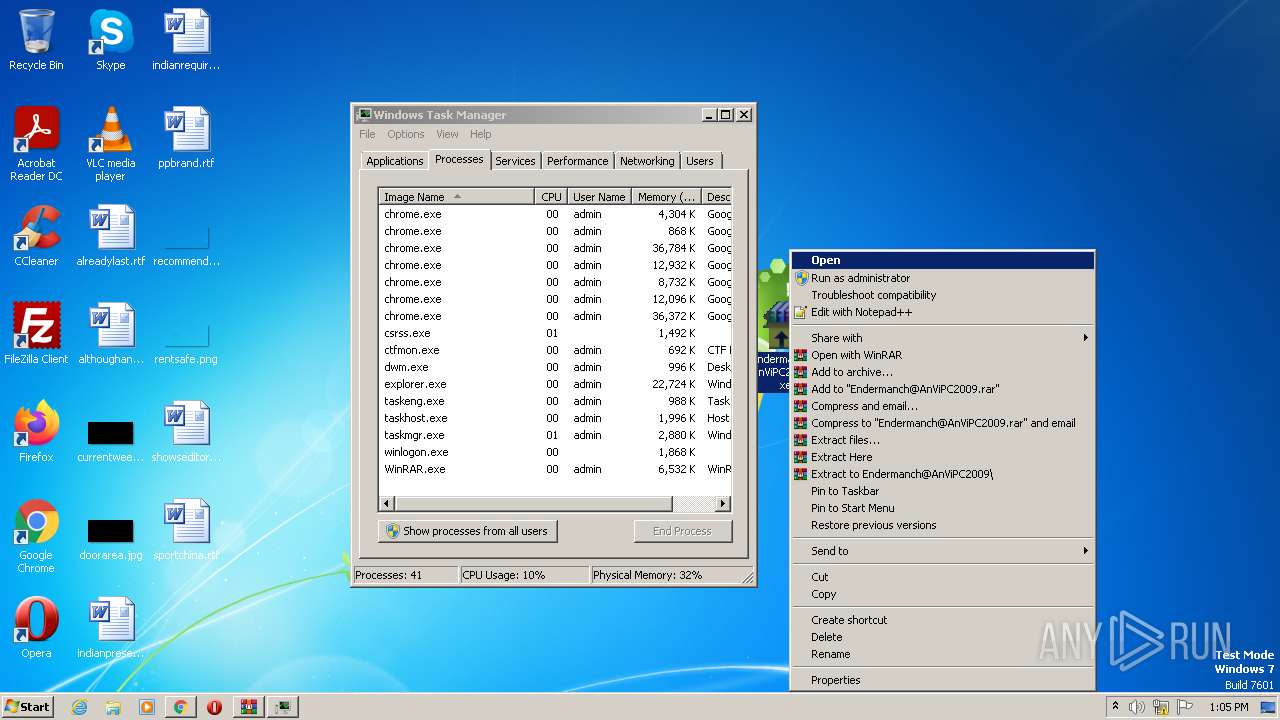
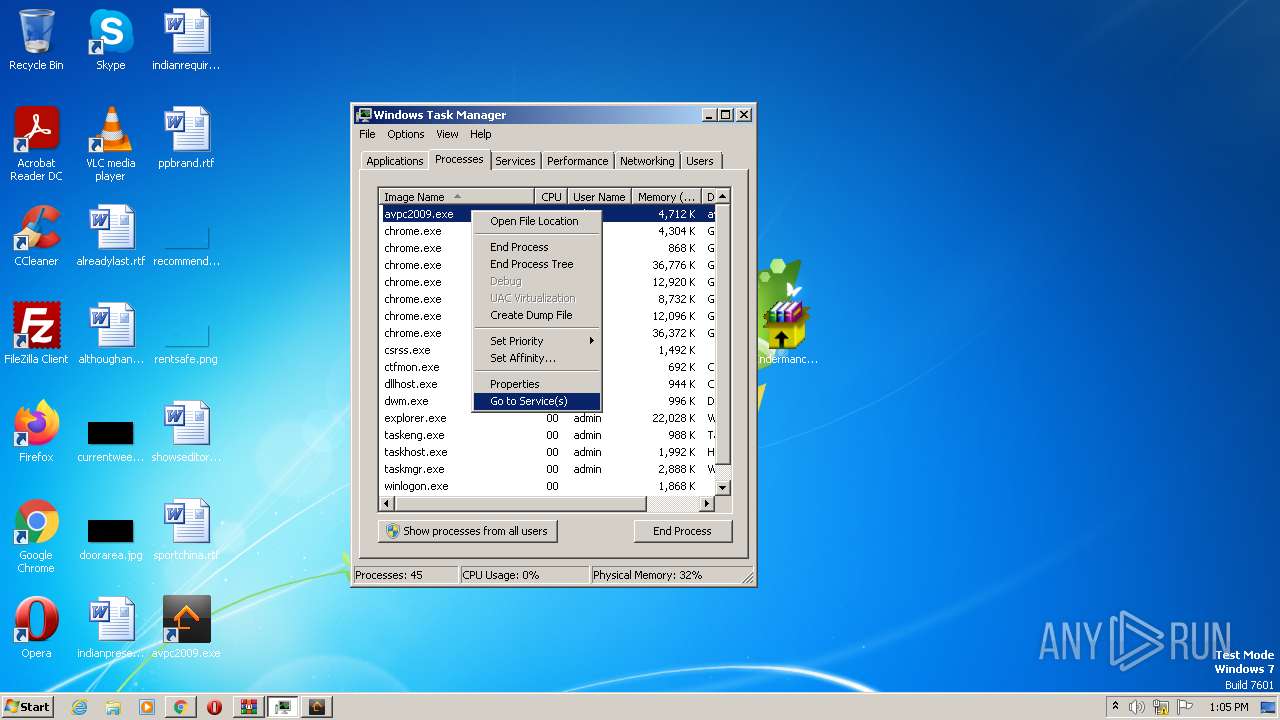
Application was dropped or rewritten from another process
- Endermanch@AnViPC2009.exe (PID: 120)
- Endermanch@AnViPC2009.exe (PID: 1632)
- Endermanch@AnViPC2009.exe (PID: 3728)
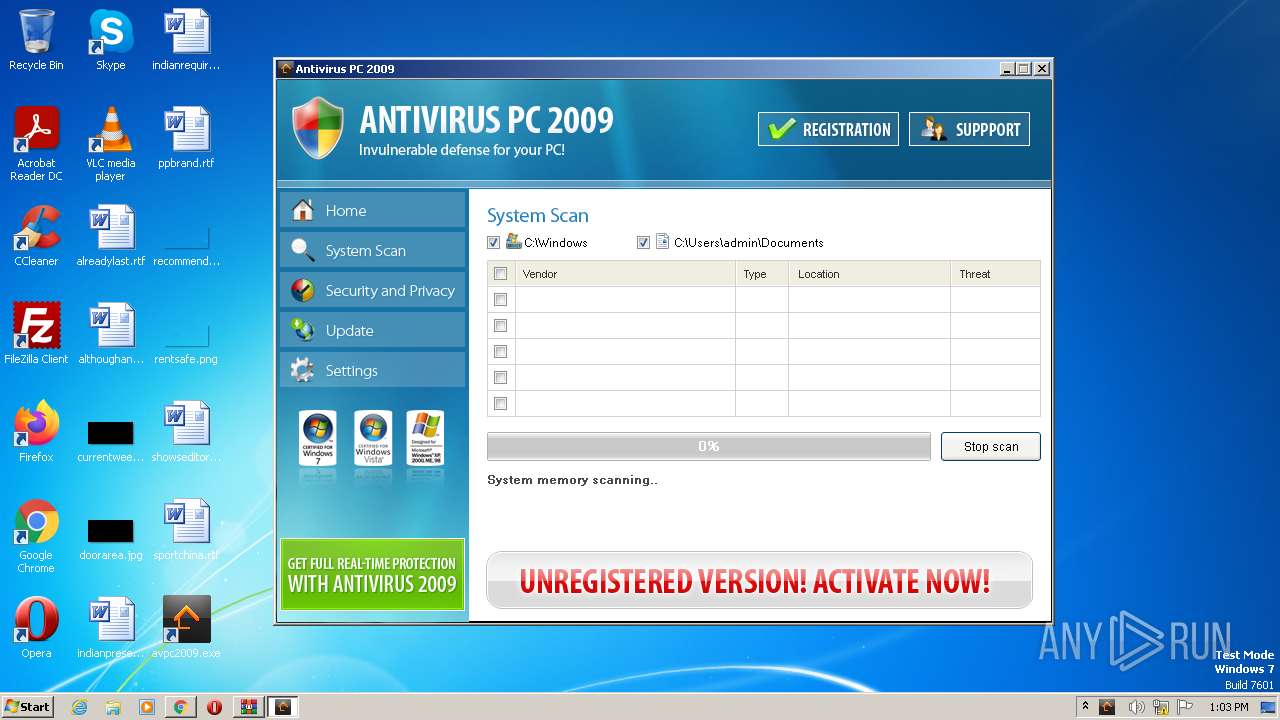
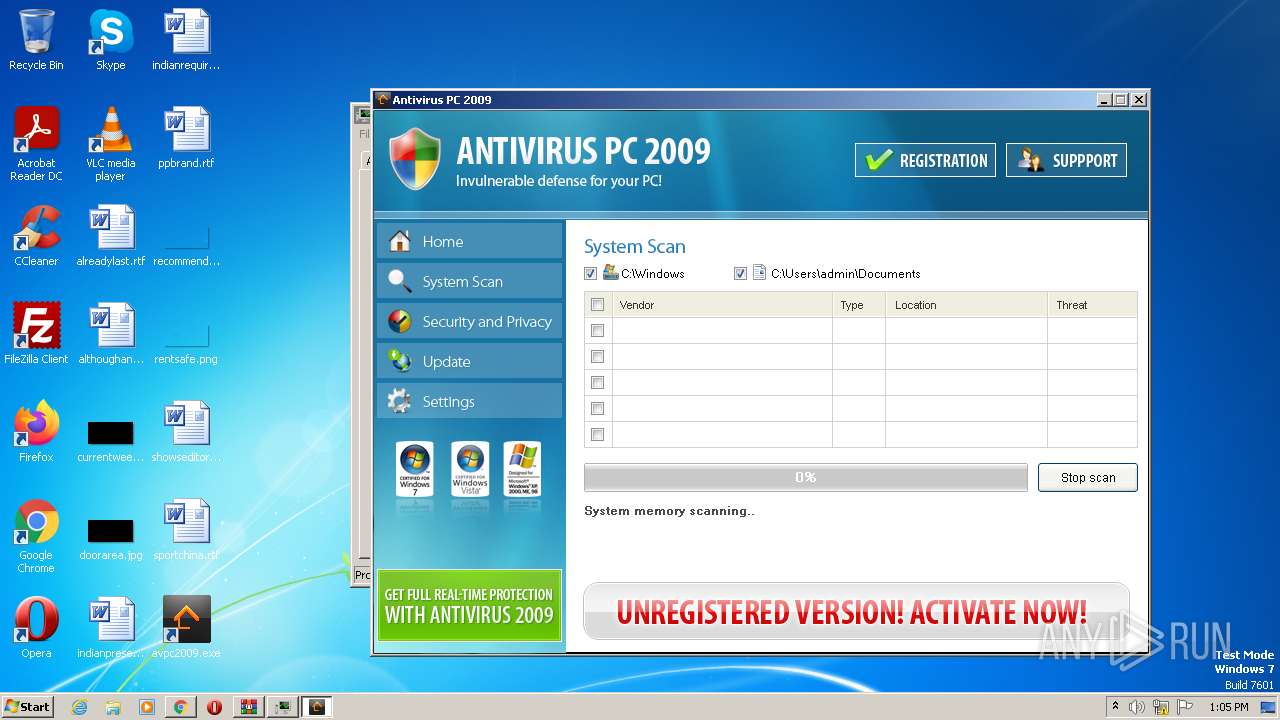
- avpc2009.exe (PID: 1896)
- Endermanch@AnViPC2009.exe (PID: 3720)
- avpc2009.exe (PID: 3616)
SUSPICIOUS
Application launched itself
- Endermanch@AnViPC2009.exe (PID: 120)
- Endermanch@AnViPC2009.exe (PID: 3728)
Reads the Internet Settings
- Endermanch@AnViPC2009.exe (PID: 120)
- Endermanch@AnViPC2009.exe (PID: 1632)
- Endermanch@AnViPC2009.exe (PID: 3728)
- Endermanch@AnViPC2009.exe (PID: 3720)
Executable content was dropped or overwritten
- Endermanch@AnViPC2009.exe (PID: 1632)
Adds/modifies Windows certificates
- Endermanch@AnViPC2009.exe (PID: 1632)
Reads settings of System Certificates
- avpc2009.exe (PID: 1896)
INFO
Application launched itself
- chrome.exe (PID: 2512)
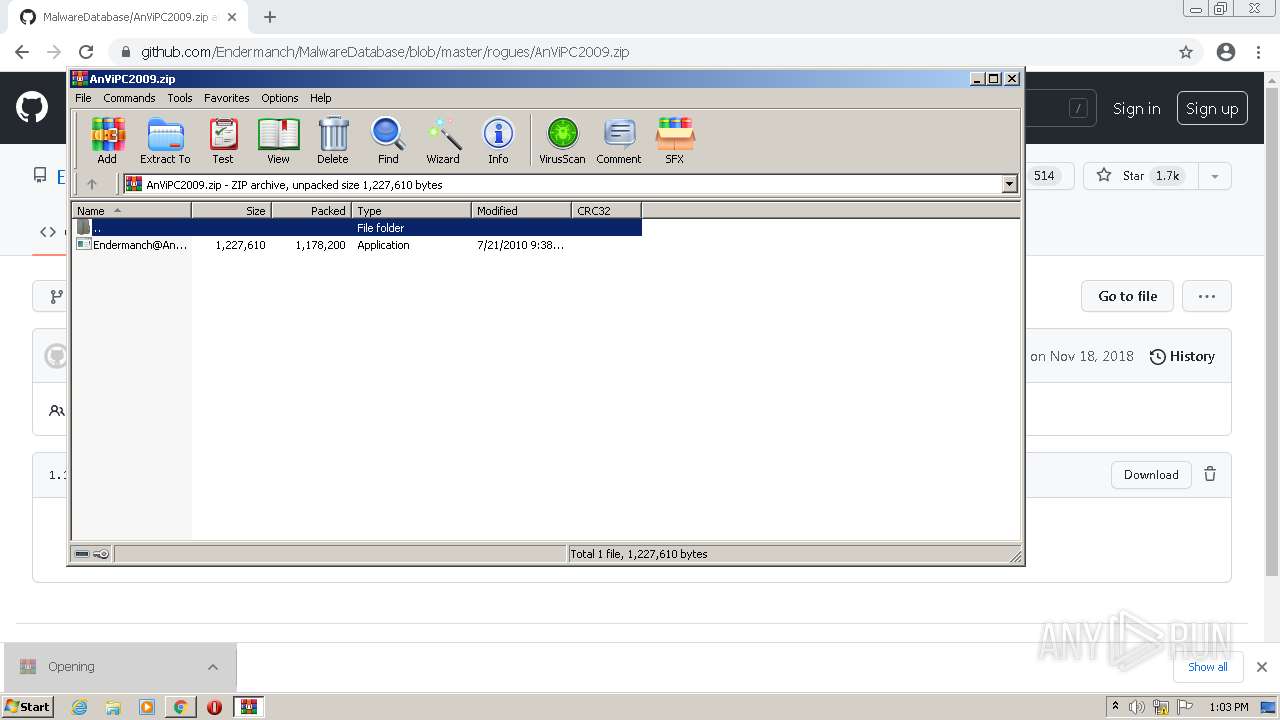
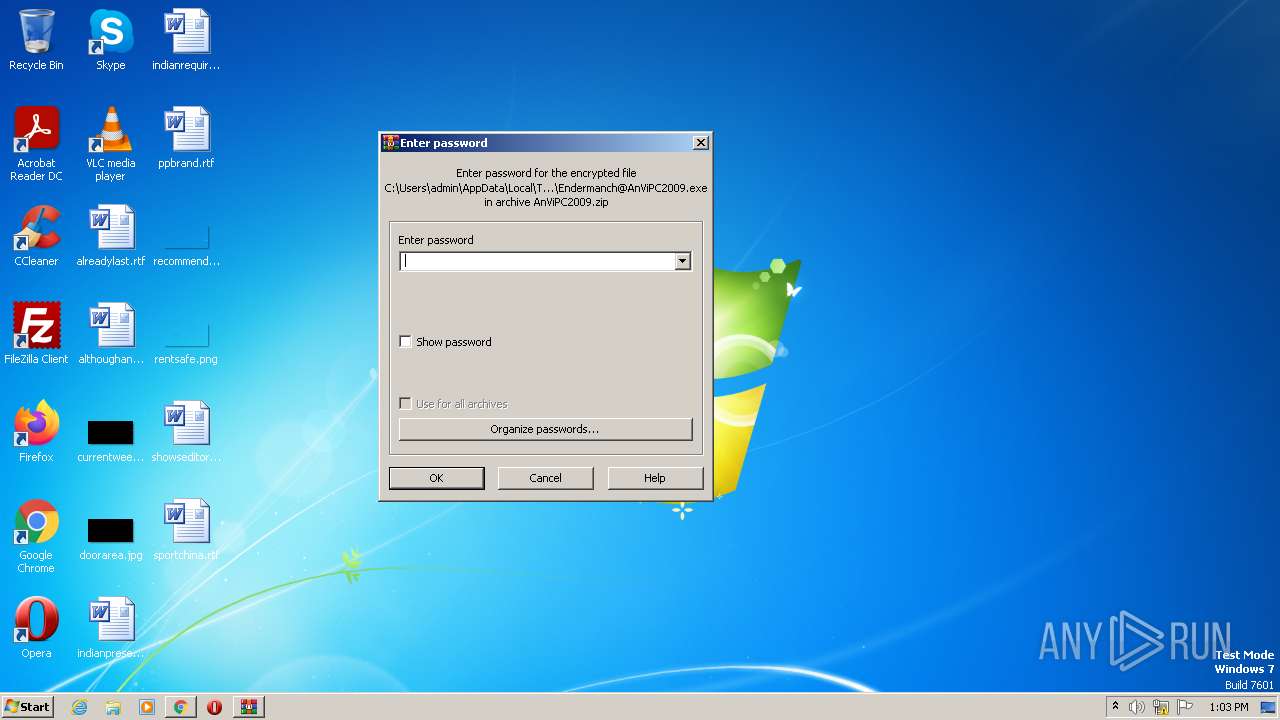
The process uses the downloaded file
- WinRAR.exe (PID: 1900)
- chrome.exe (PID: 3032)
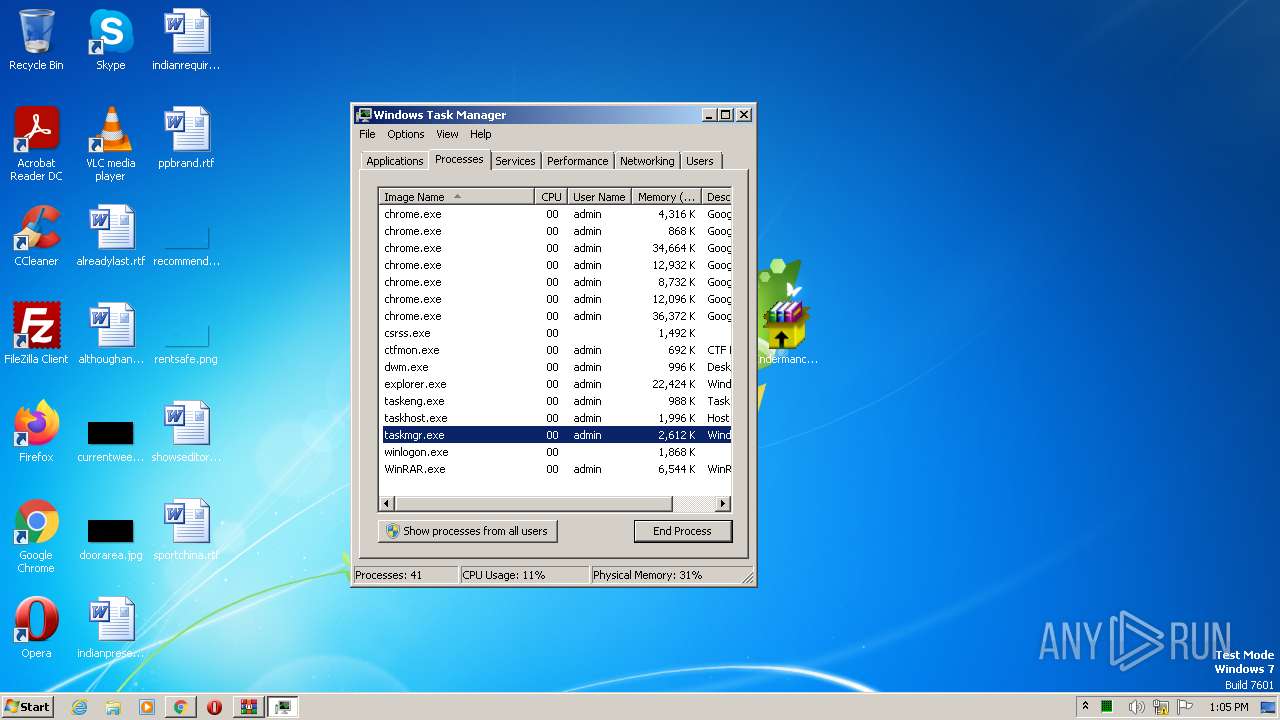
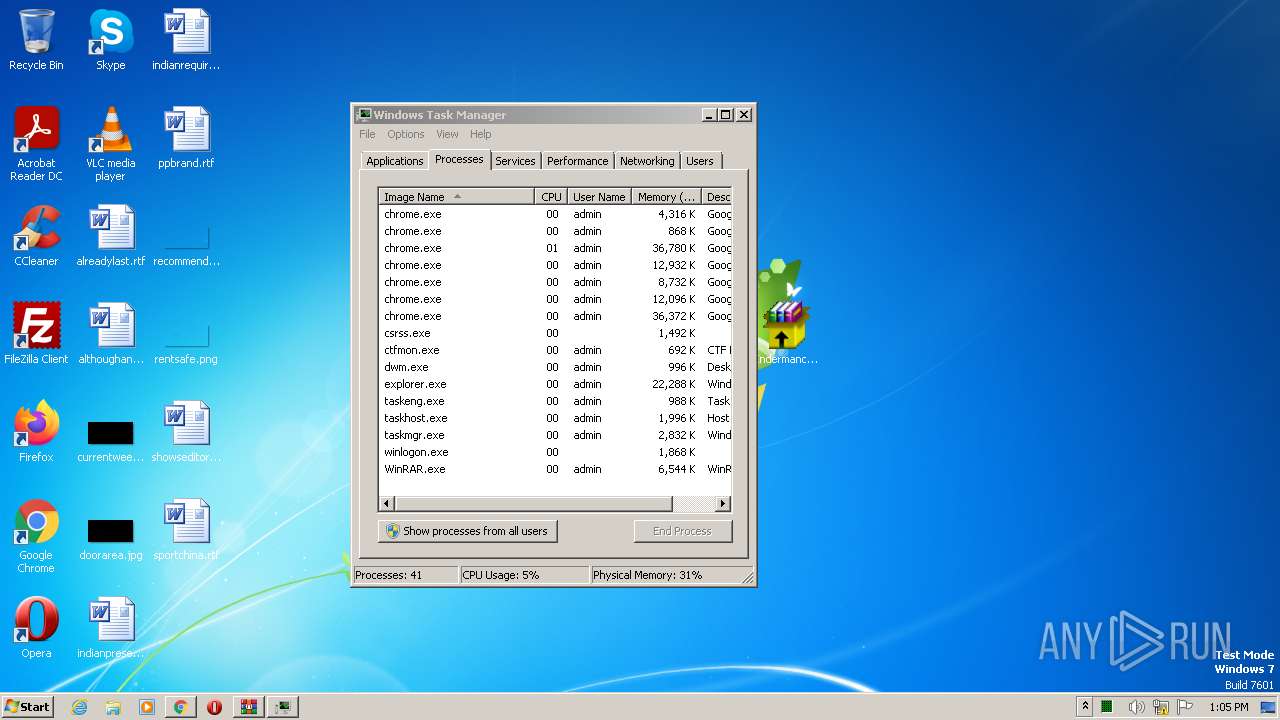
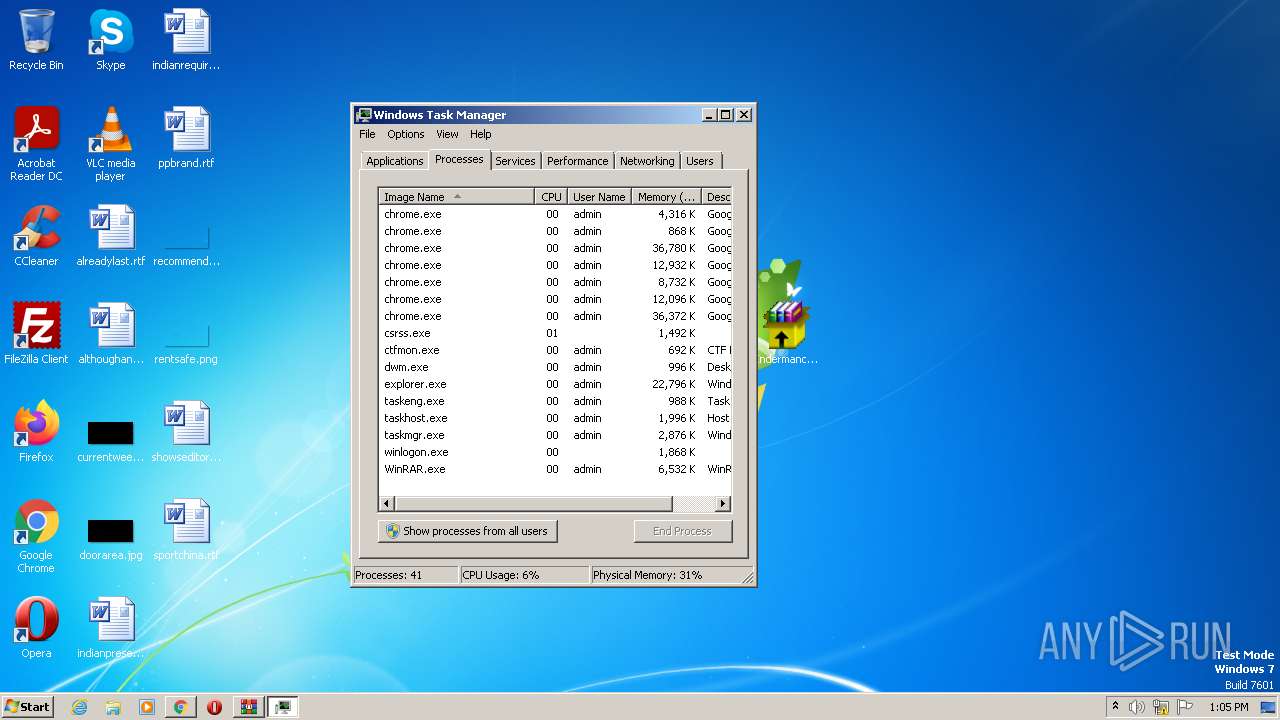
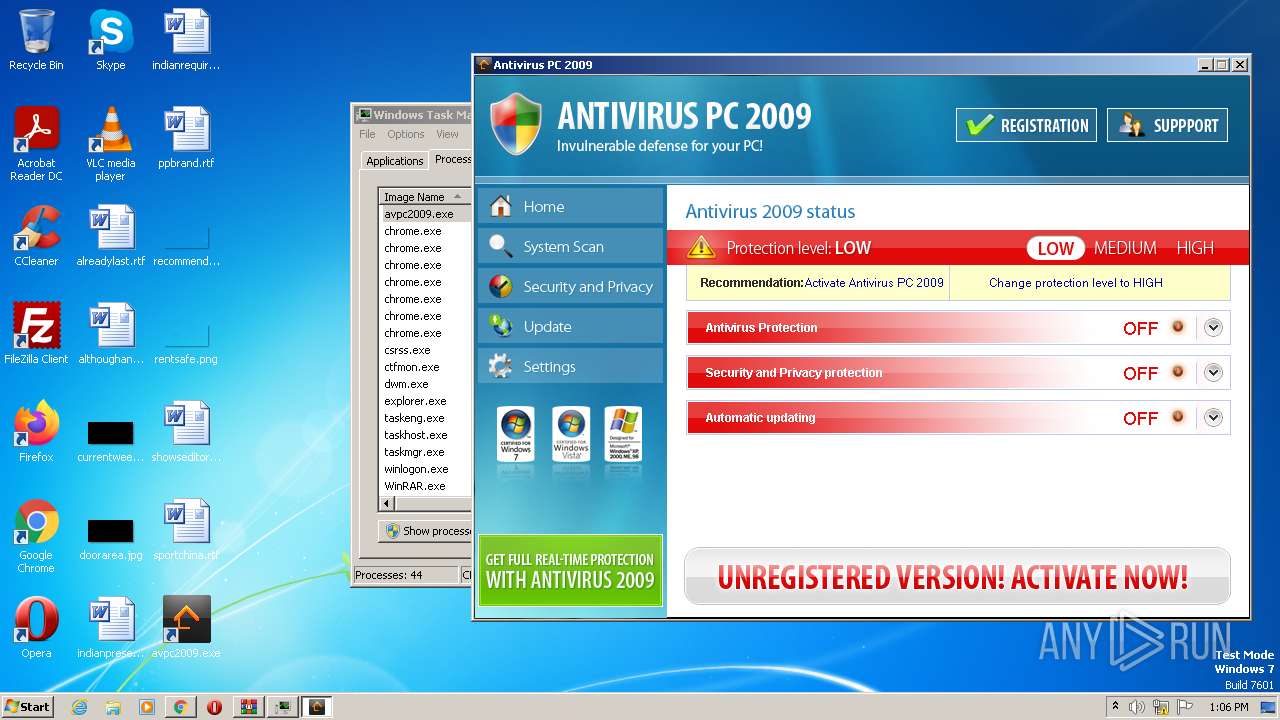
Manual execution by a user
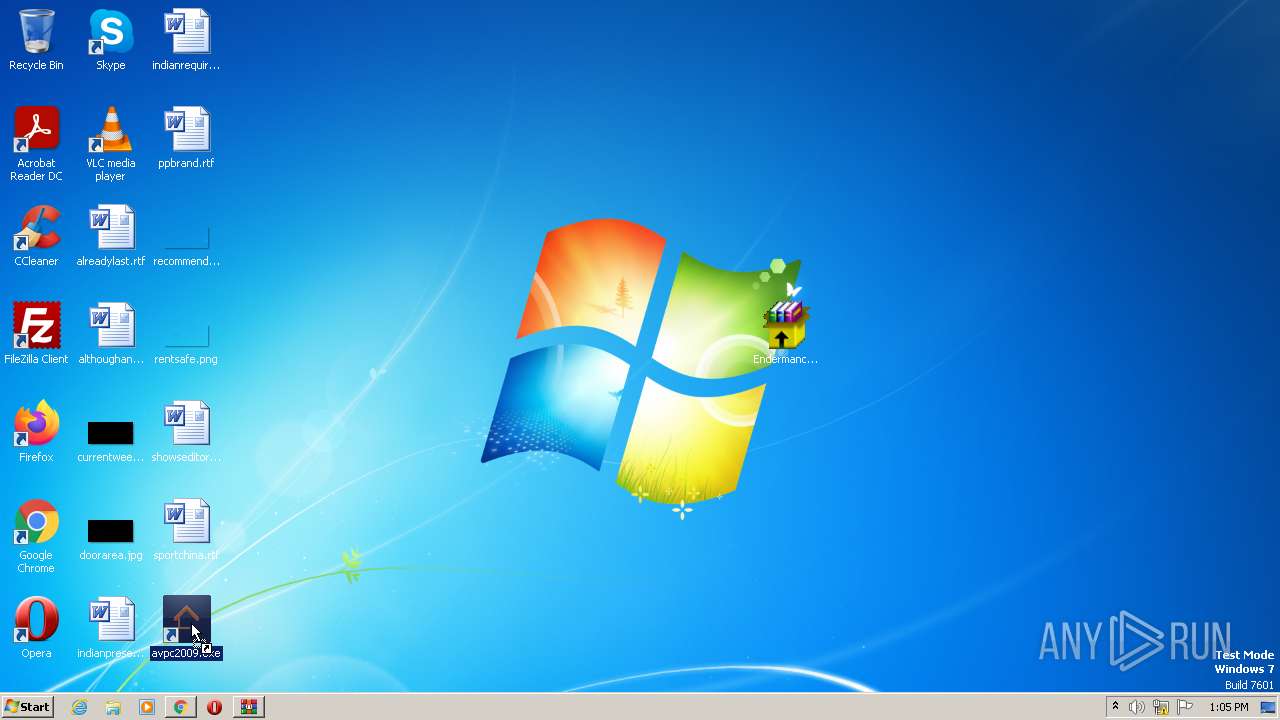
- Endermanch@AnViPC2009.exe (PID: 120)
- taskmgr.exe (PID: 3444)
- Endermanch@AnViPC2009.exe (PID: 3728)
Create files in a temporary directory
- chrome.exe (PID: 3348)
- chrome.exe (PID: 2512)
The process checks LSA protection
- Endermanch@AnViPC2009.exe (PID: 120)
- Endermanch@AnViPC2009.exe (PID: 1632)
- avpc2009.exe (PID: 1896)
- Endermanch@AnViPC2009.exe (PID: 3728)
- taskmgr.exe (PID: 3444)
- avpc2009.exe (PID: 3616)
- Endermanch@AnViPC2009.exe (PID: 3720)
Checks supported languages
- Endermanch@AnViPC2009.exe (PID: 120)
- Endermanch@AnViPC2009.exe (PID: 1632)
- avpc2009.exe (PID: 1896)
- Endermanch@AnViPC2009.exe (PID: 3728)
- Endermanch@AnViPC2009.exe (PID: 3720)
- avpc2009.exe (PID: 3616)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1900)
Reads the computer name
- Endermanch@AnViPC2009.exe (PID: 1632)
- Endermanch@AnViPC2009.exe (PID: 120)
- avpc2009.exe (PID: 1896)
- Endermanch@AnViPC2009.exe (PID: 3728)
- Endermanch@AnViPC2009.exe (PID: 3720)
- avpc2009.exe (PID: 3616)
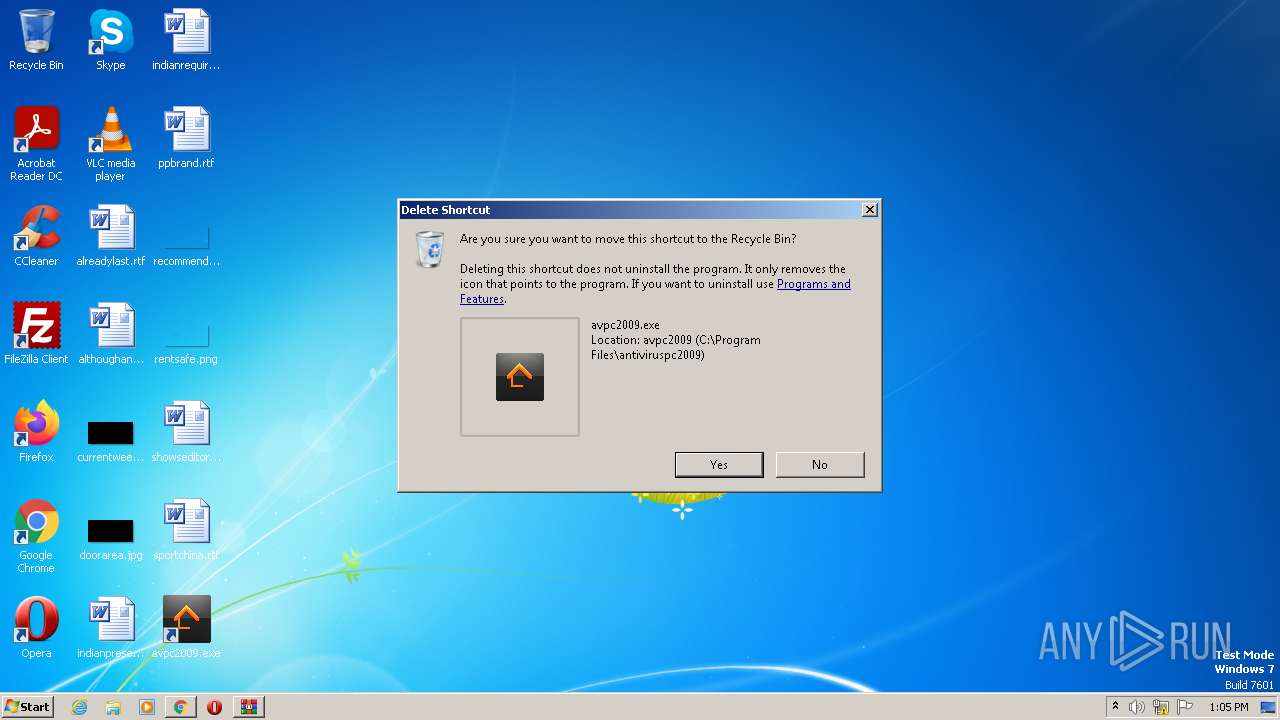
Creates files in the program directory
- Endermanch@AnViPC2009.exe (PID: 1632)
Reads the machine GUID from the registry
- avpc2009.exe (PID: 1896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
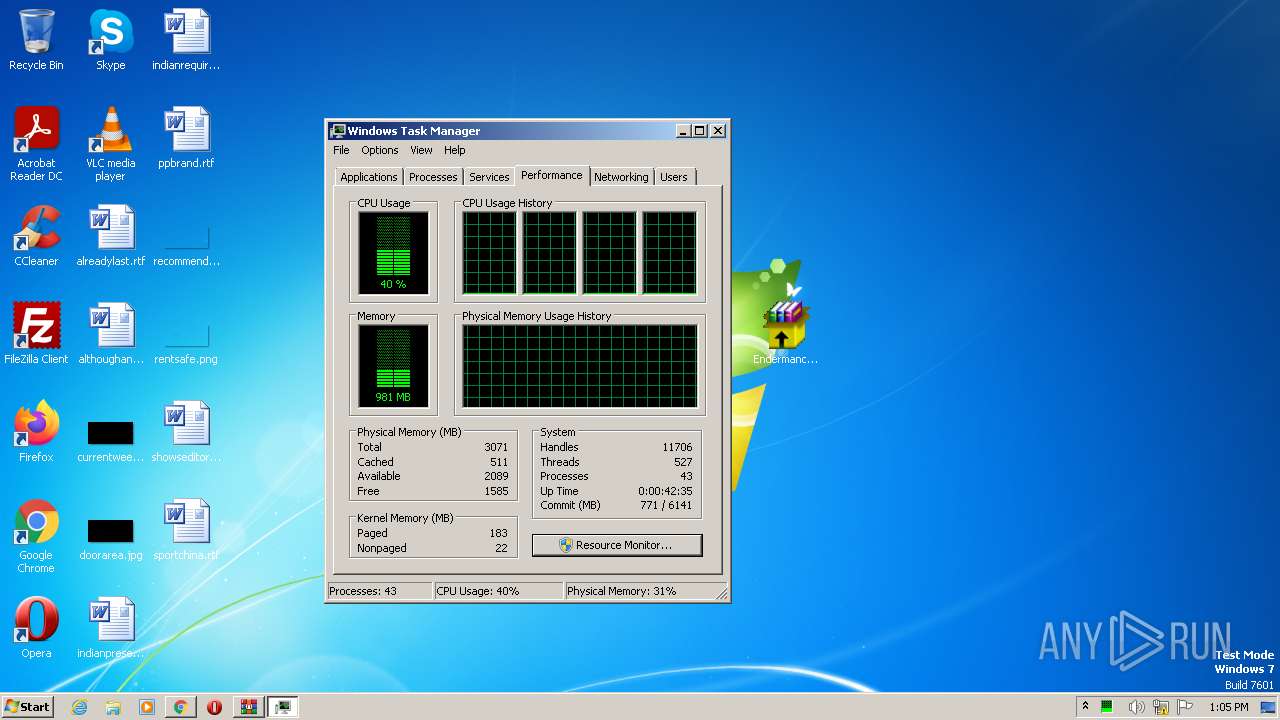
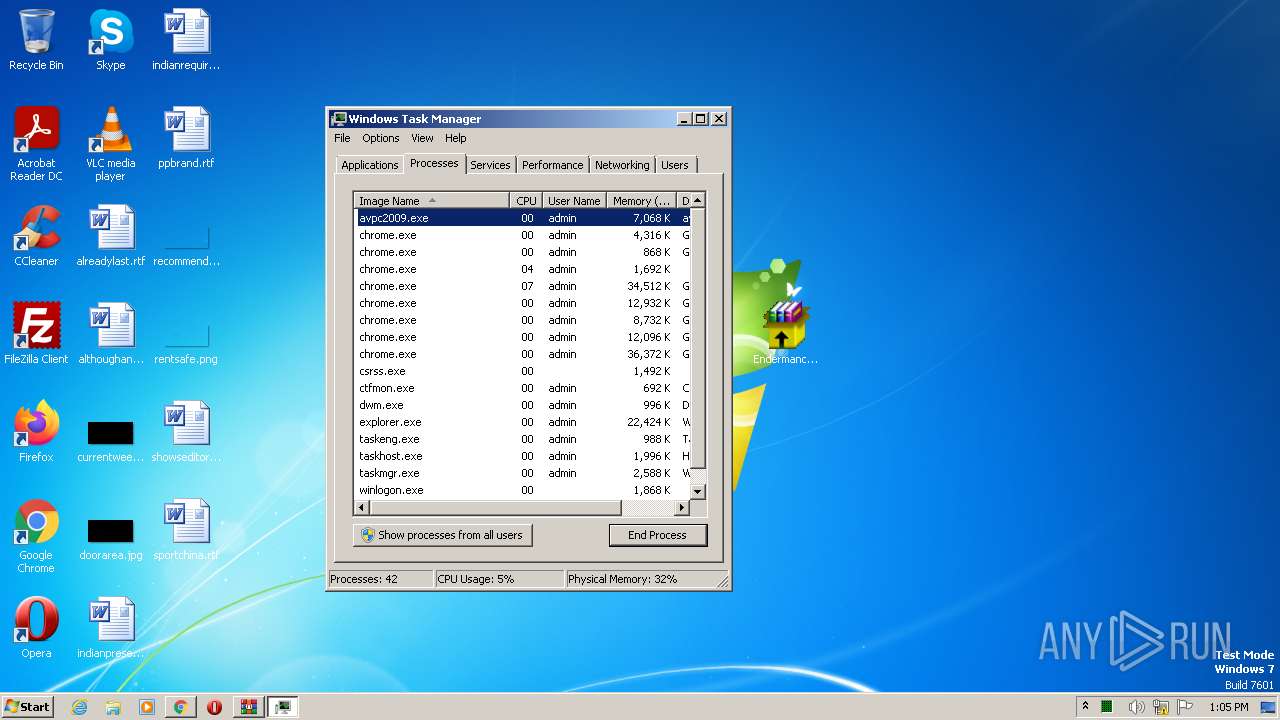
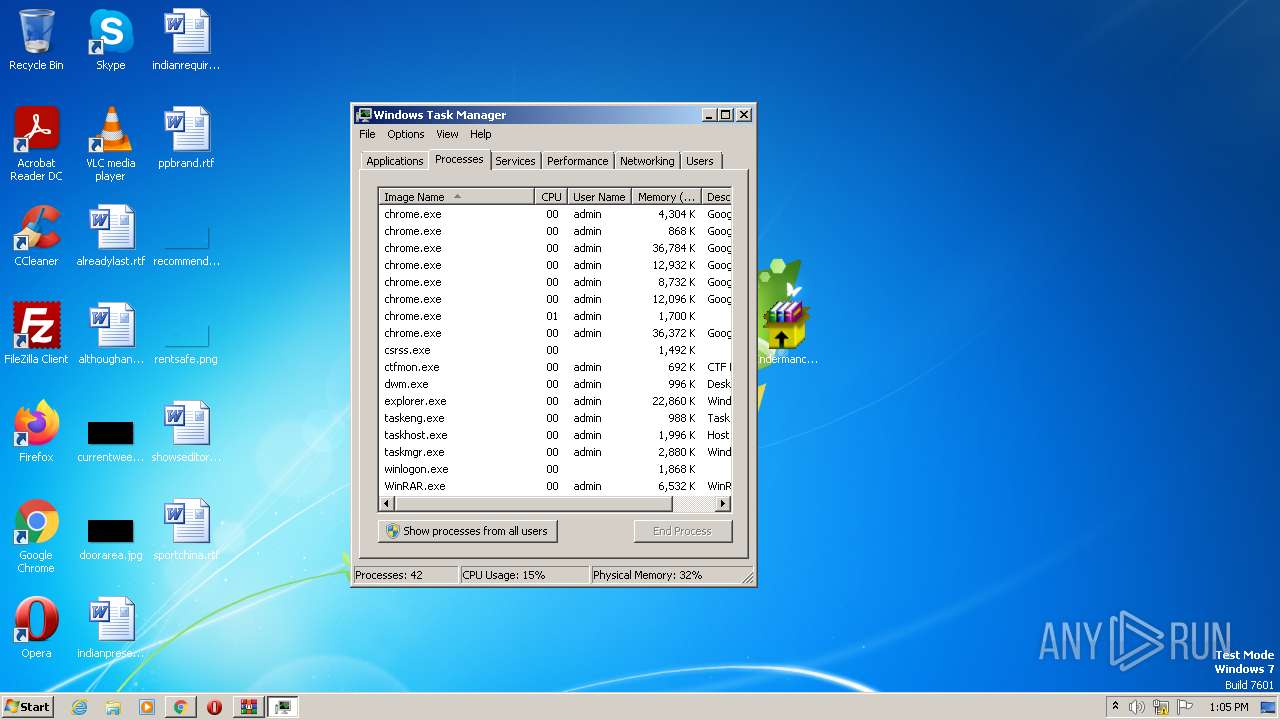
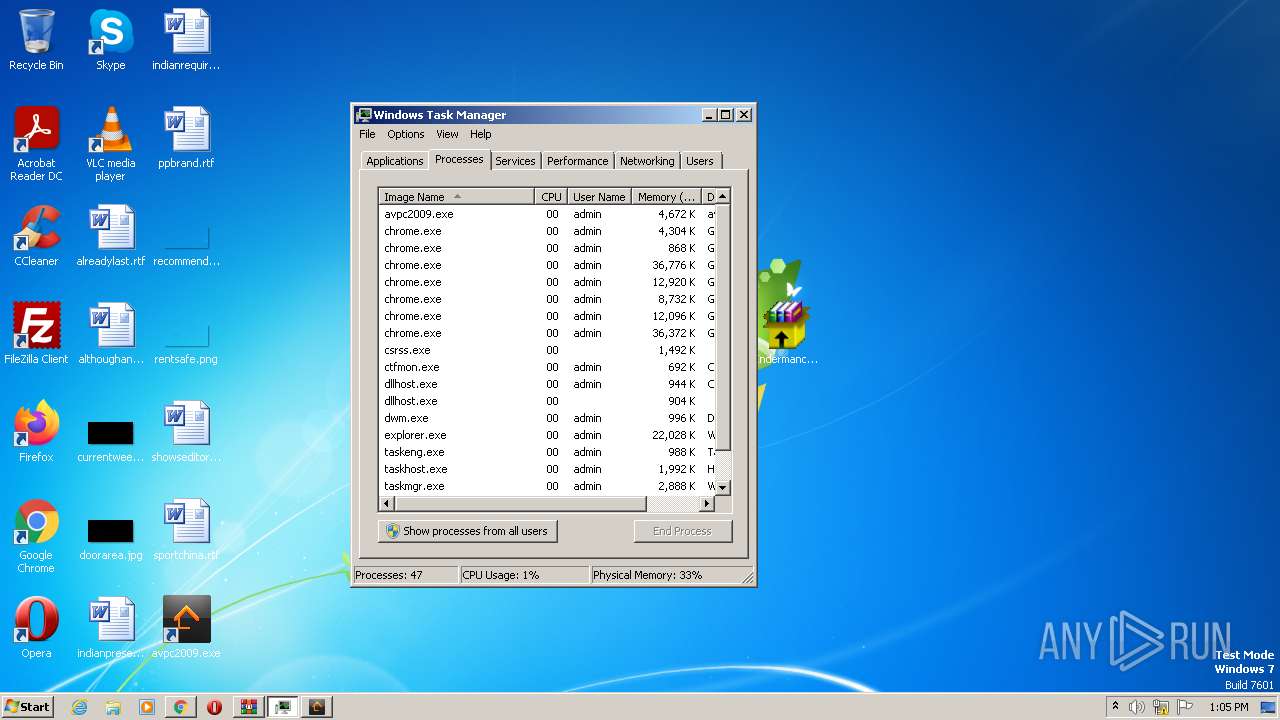
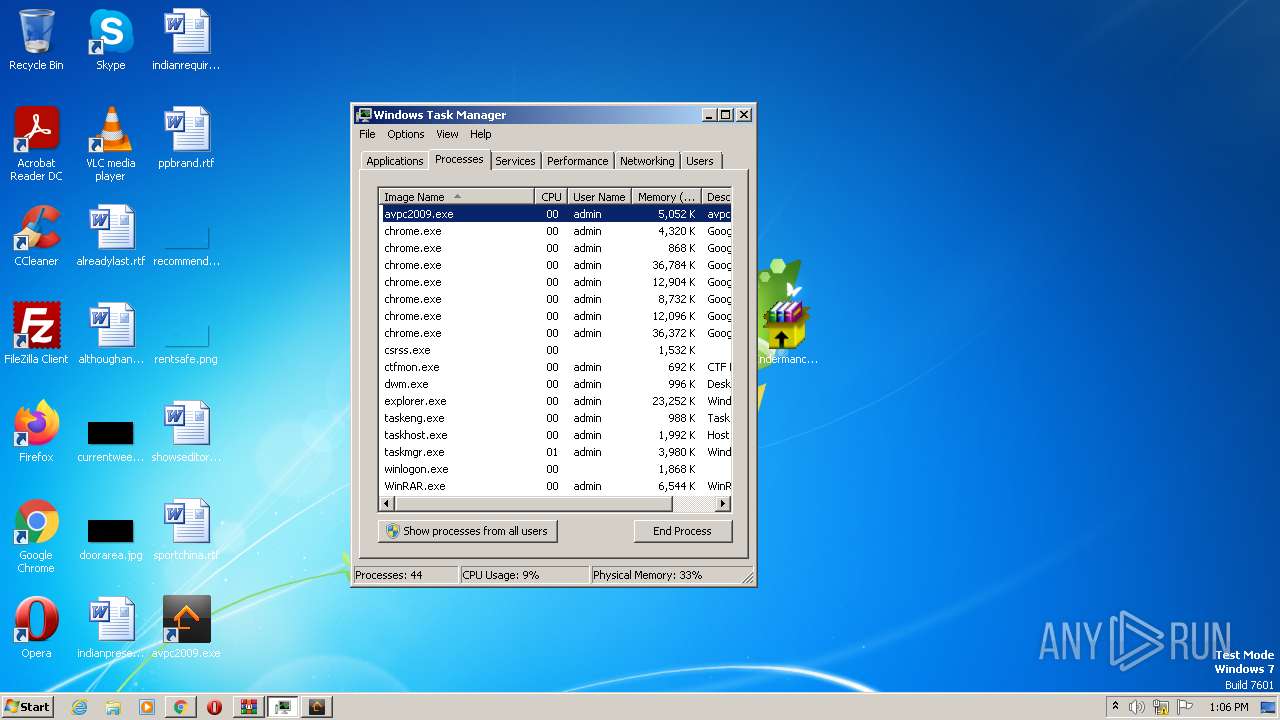
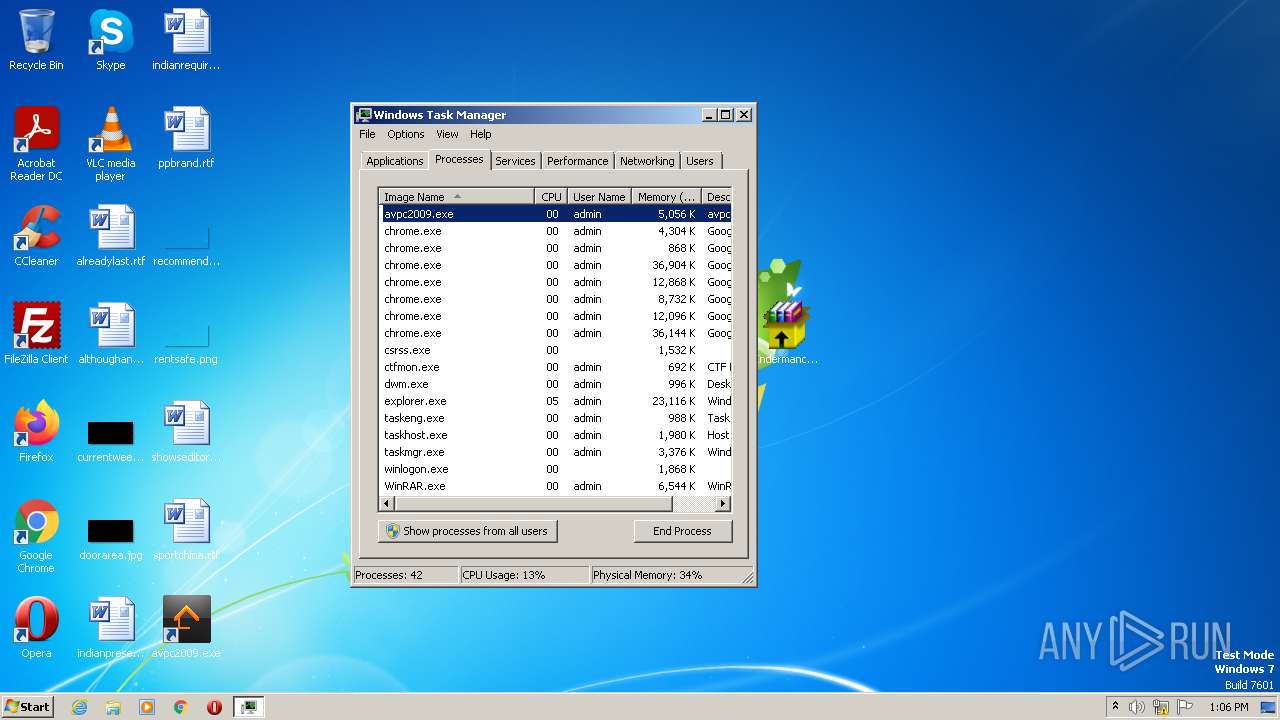
Total processes
84
Monitored processes
36
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\Desktop\Endermanch@AnViPC2009.exe" | C:\Users\admin\Desktop\Endermanch@AnViPC2009.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1052,2721312467202938198,16138510272847829393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=3416 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,2721312467202938198,16138510272847829393,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1632 | "C:\Users\admin\Desktop\Endermanch@AnViPC2009.exe" -el -s2 "-dC:\Program Files\antiviruspc2009" "-p" "-sp" | C:\Users\admin\Desktop\Endermanch@AnViPC2009.exe | Endermanch@AnViPC2009.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,2721312467202938198,16138510272847829393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,2721312467202938198,16138510272847829393,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
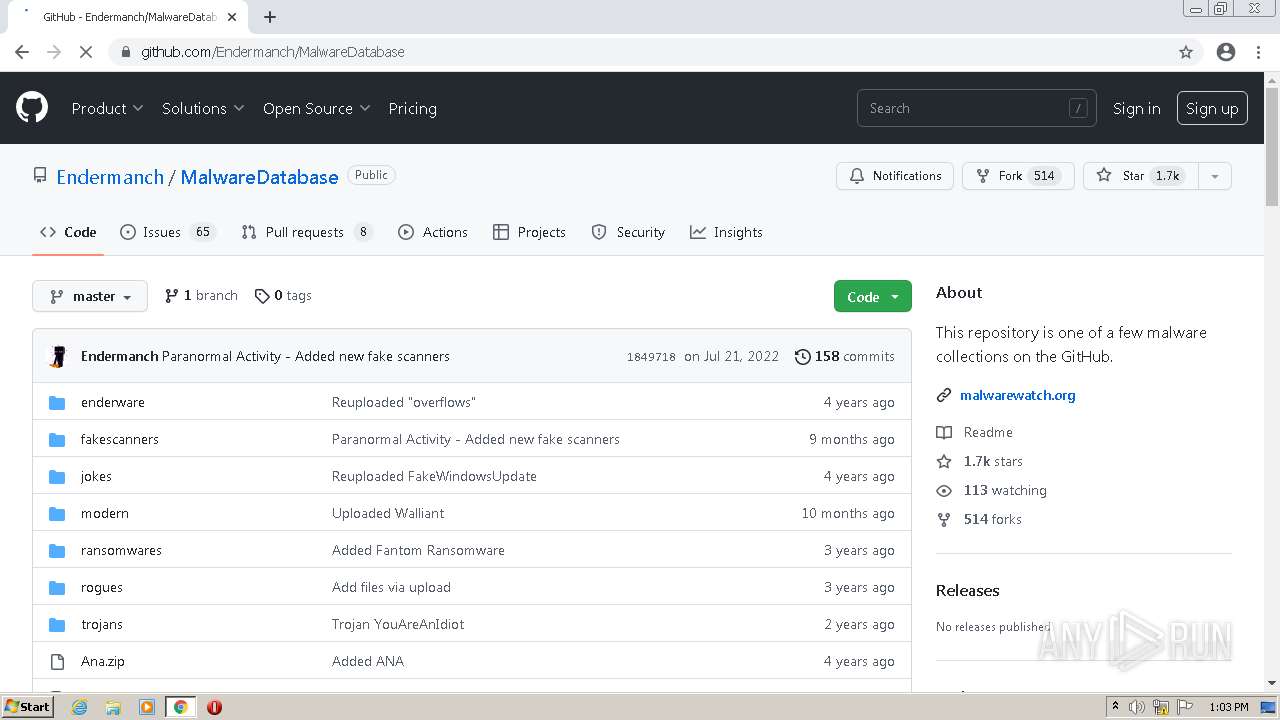
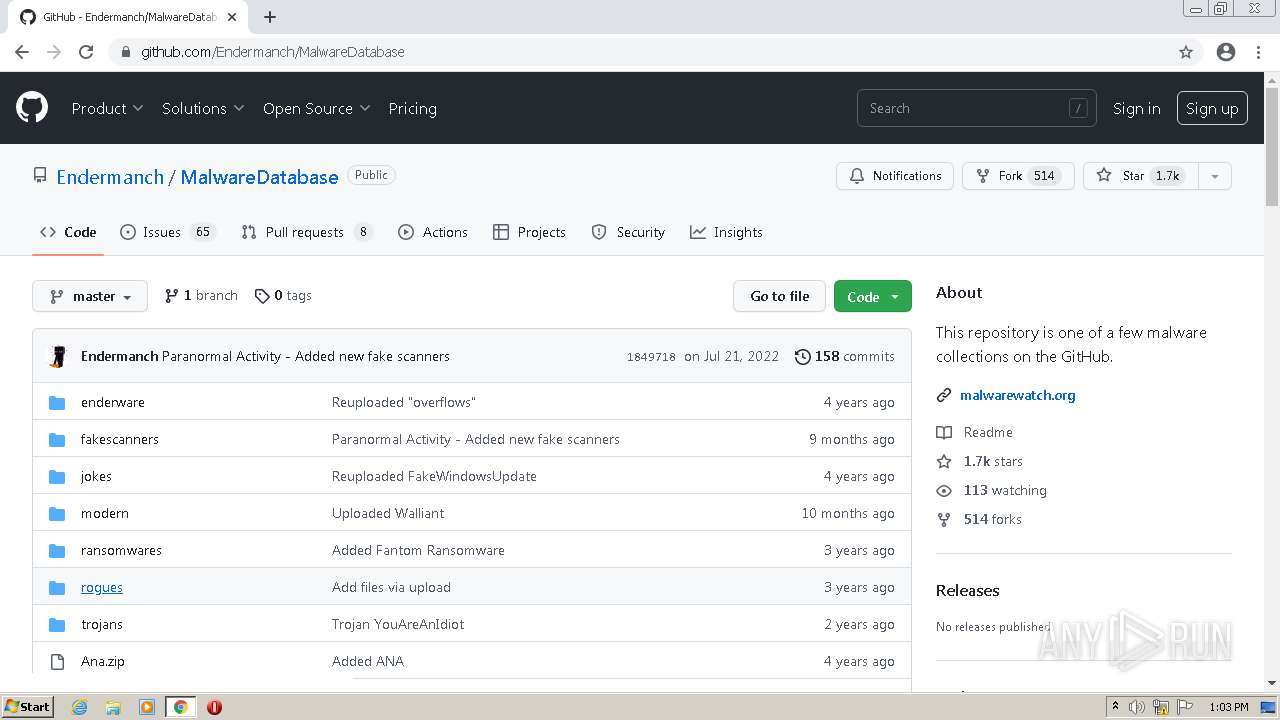
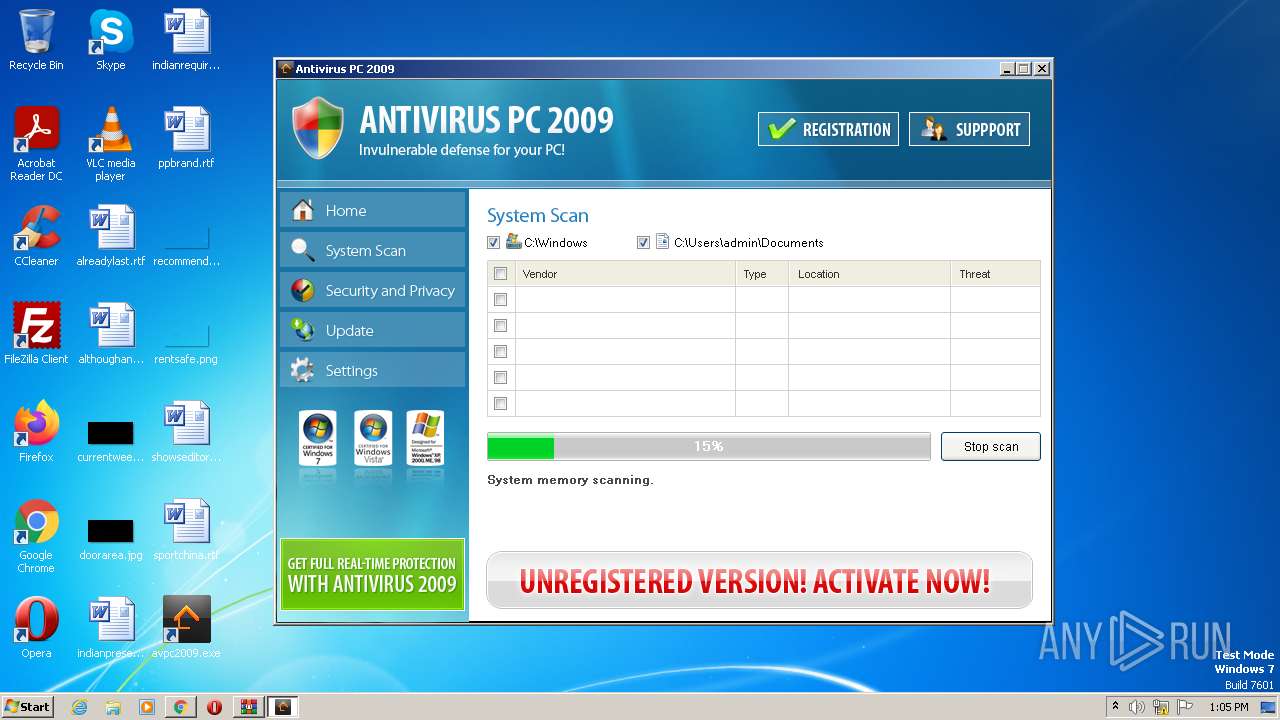
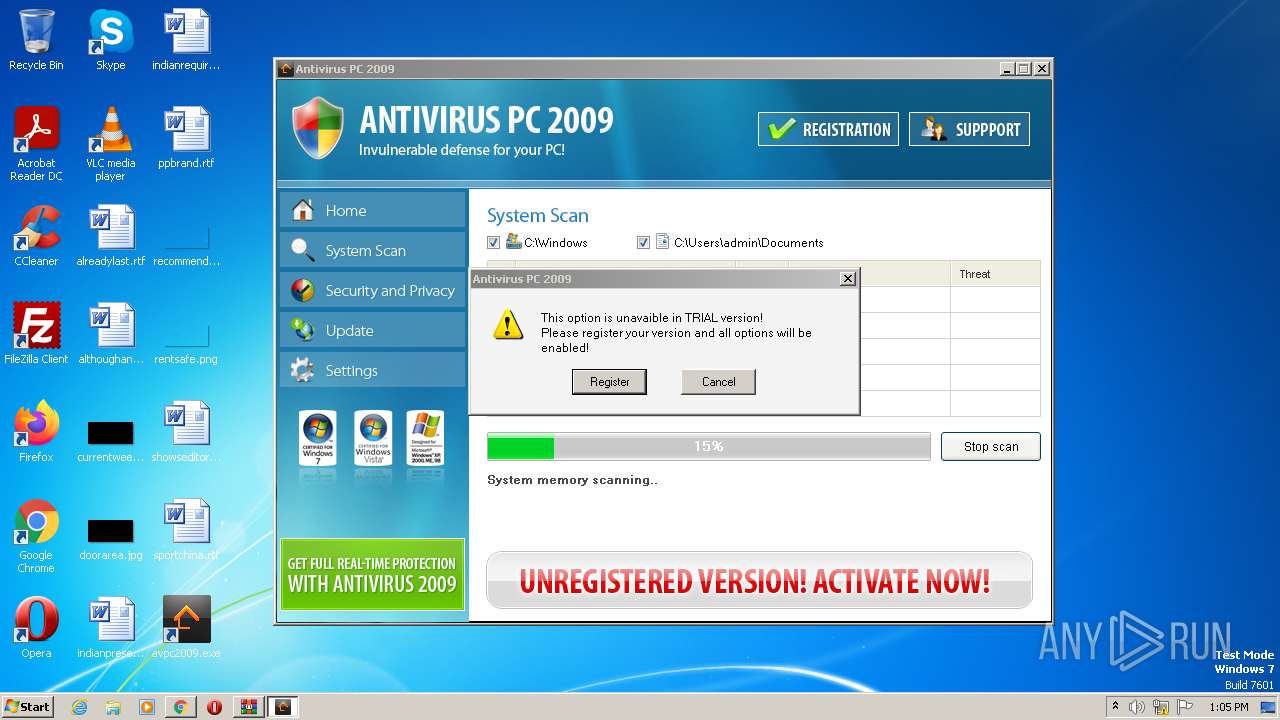
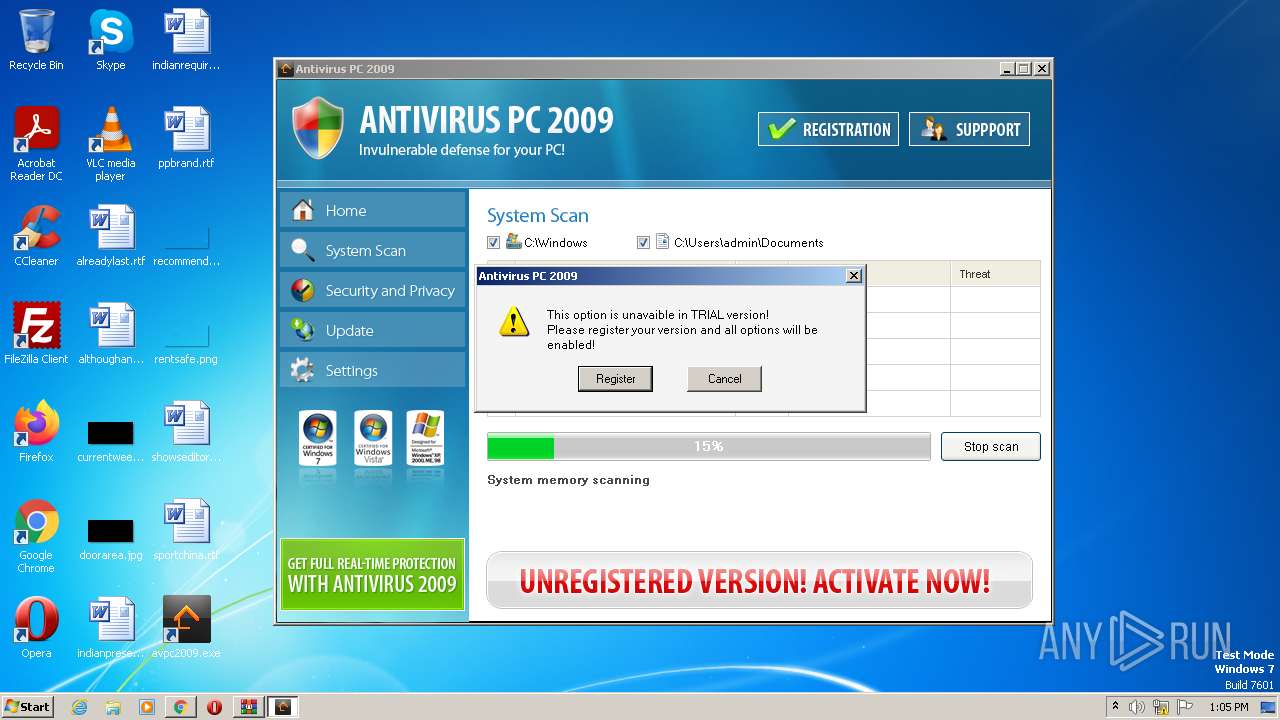
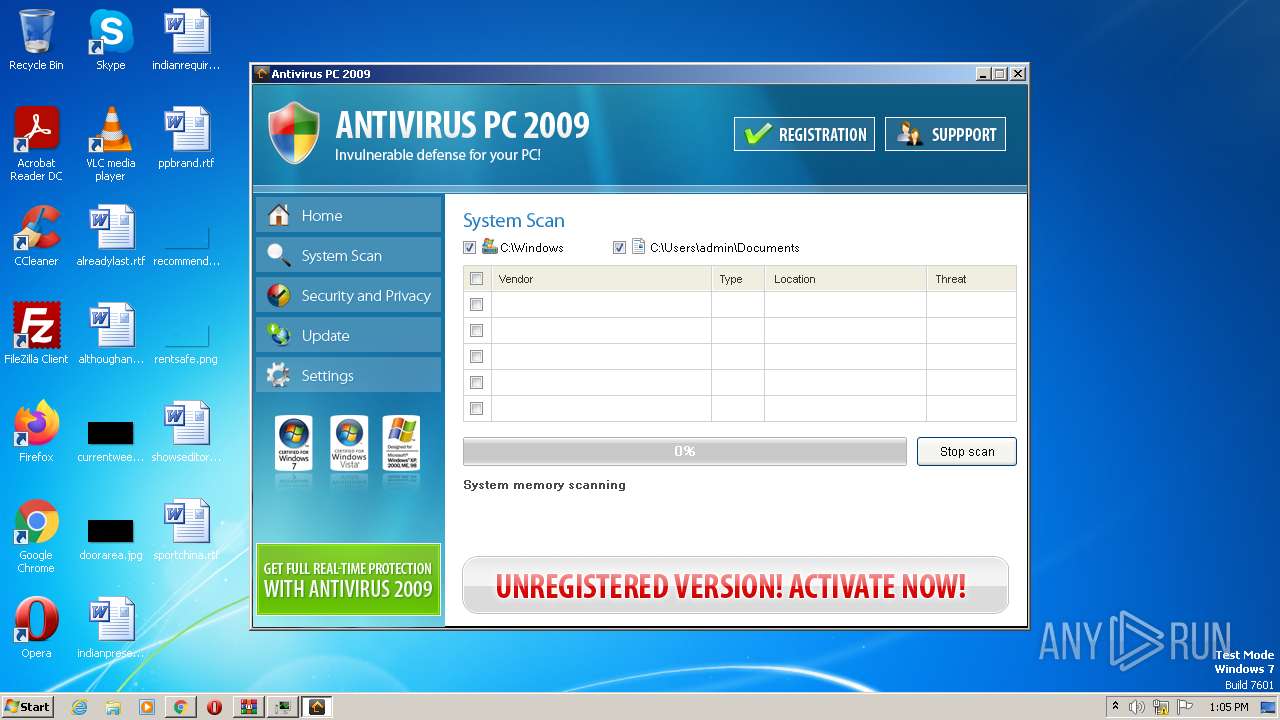
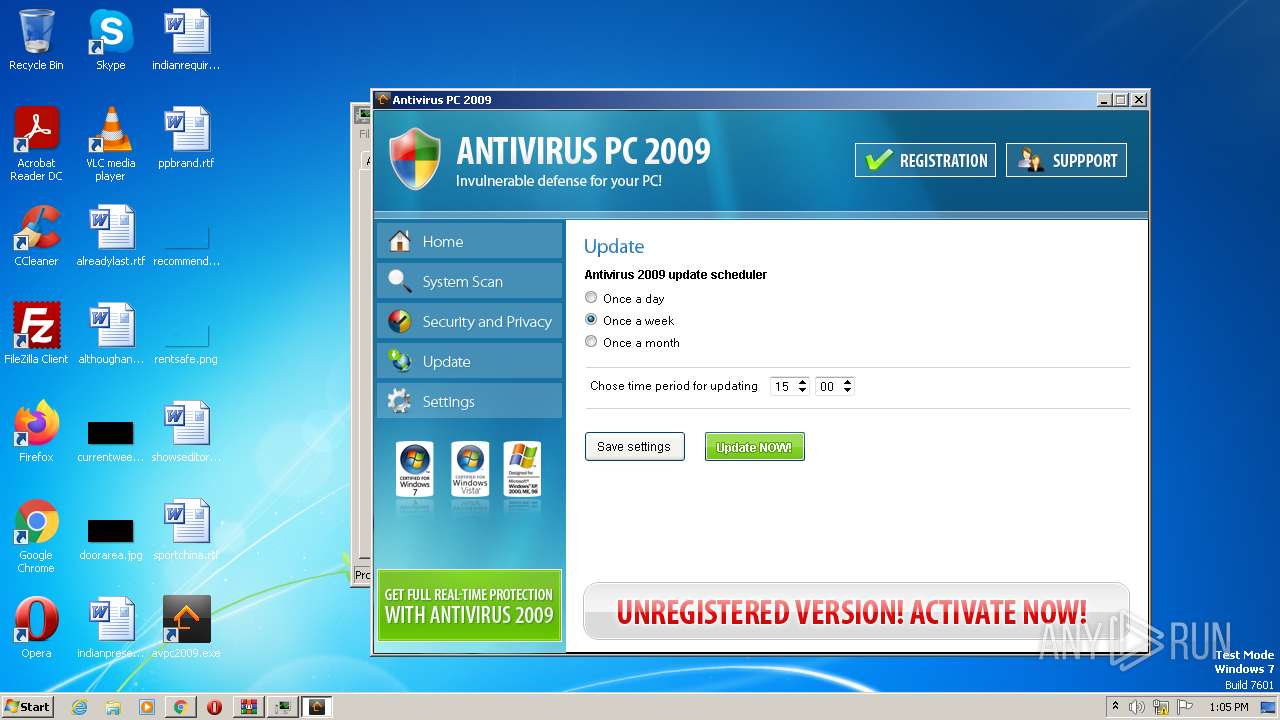
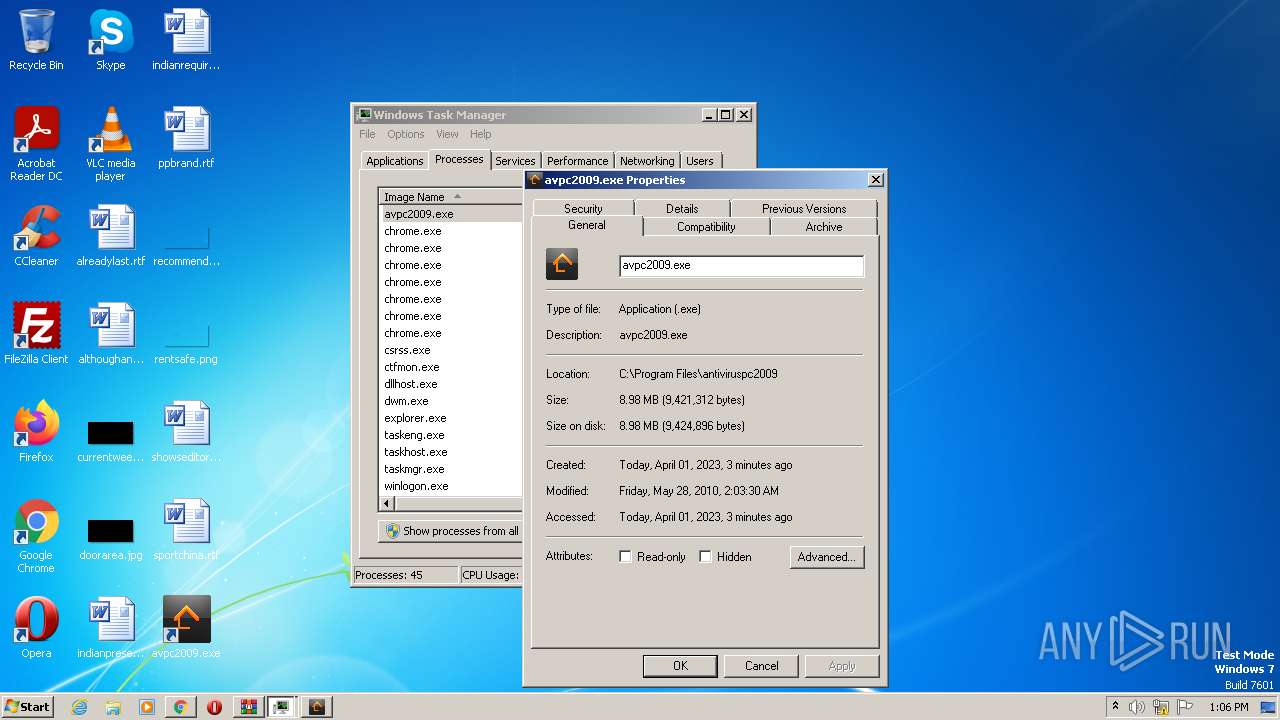
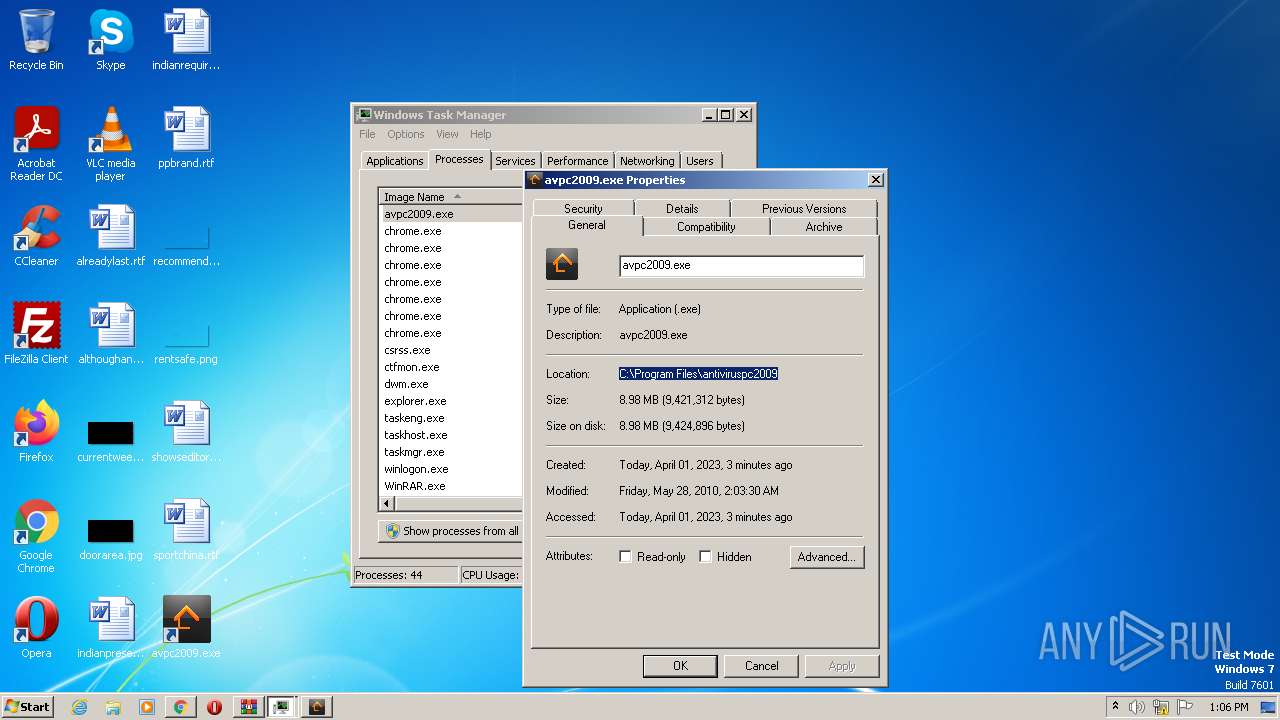
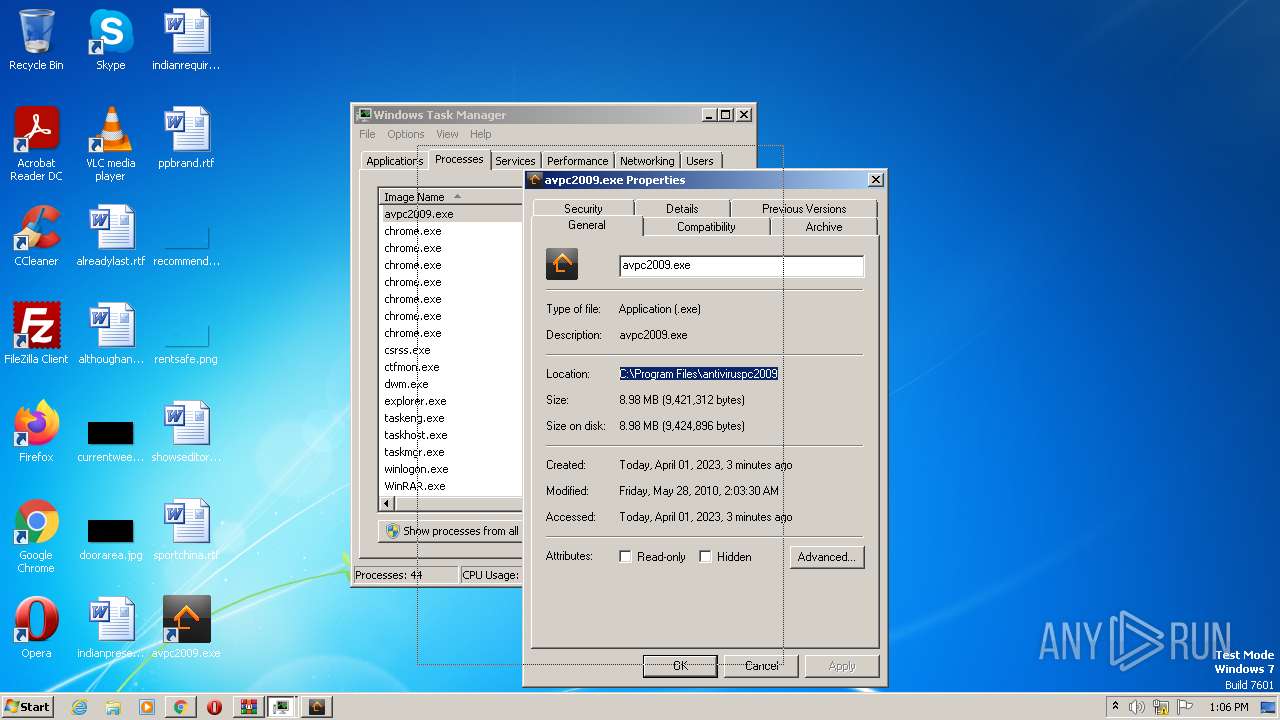
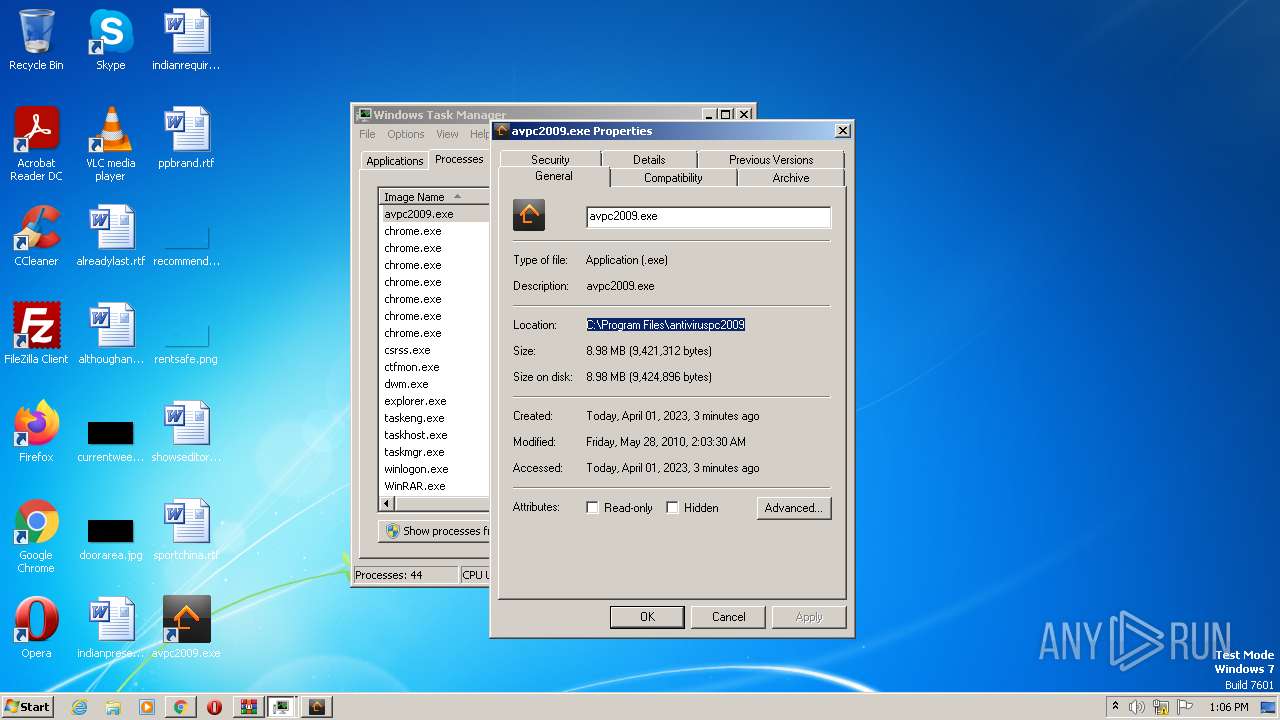
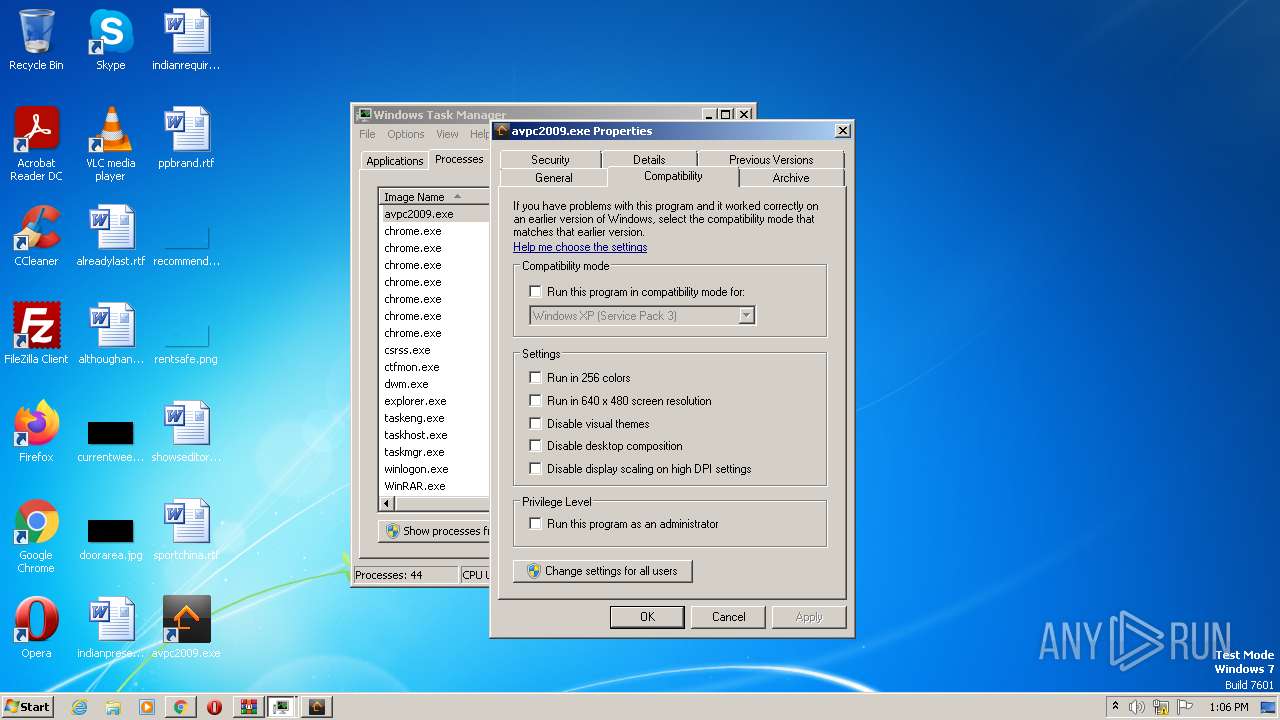
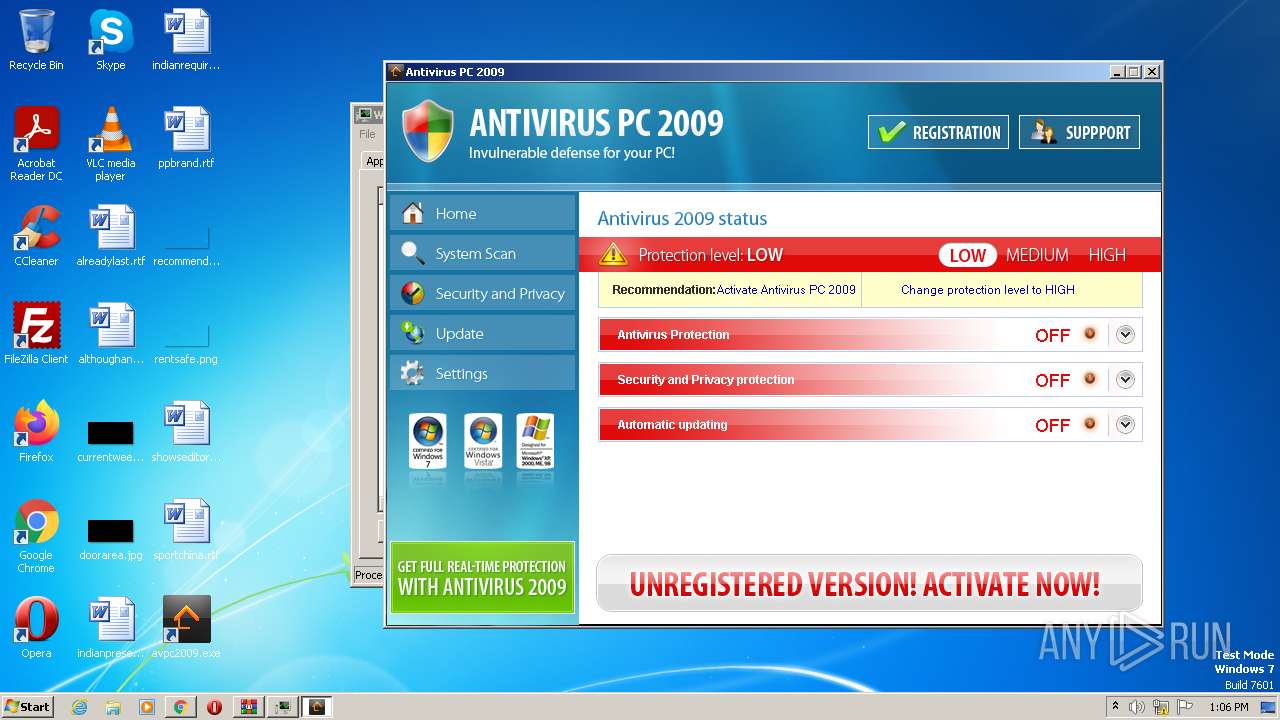
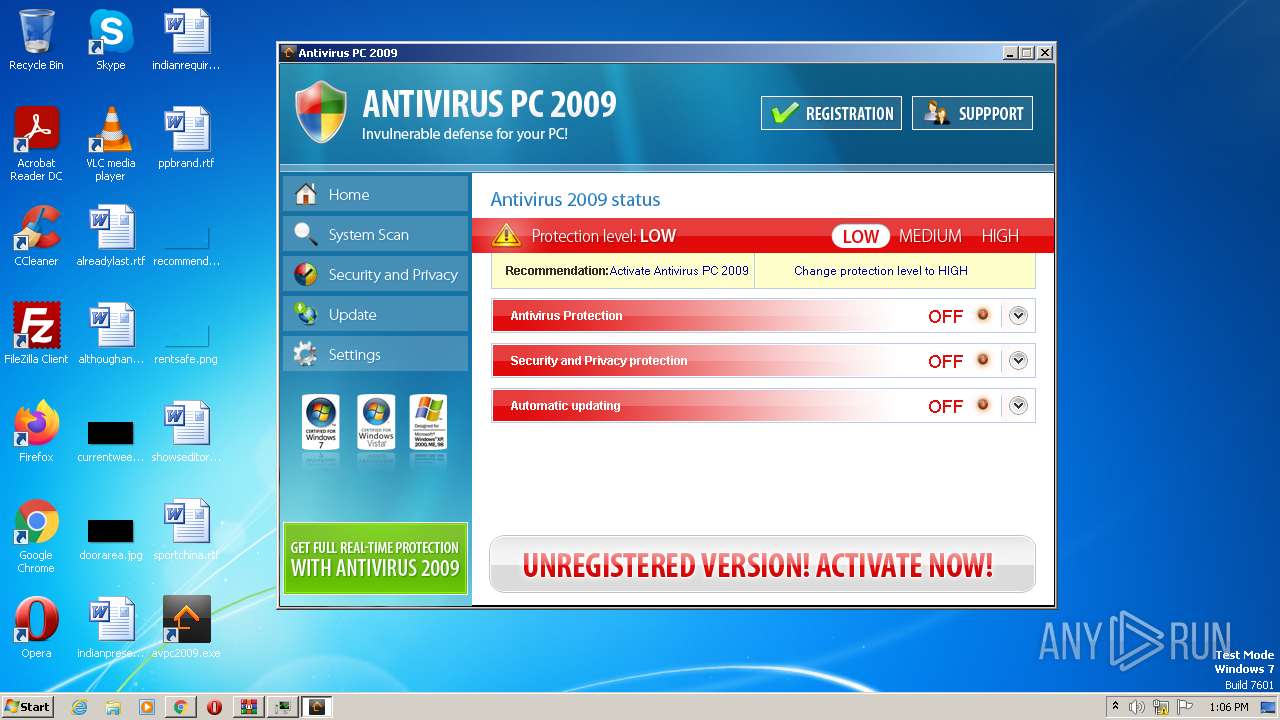
| 1896 | "C:\Program Files\antiviruspc2009\avpc2009.exe" | C:\Program Files\antiviruspc2009\avpc2009.exe | Endermanch@AnViPC2009.exe | ||||||||||||
User: admin Company: Antivirus PC 2009 Integrity Level: HIGH Exit code: 1 Version: 2.0.45.1 Modules
| |||||||||||||||
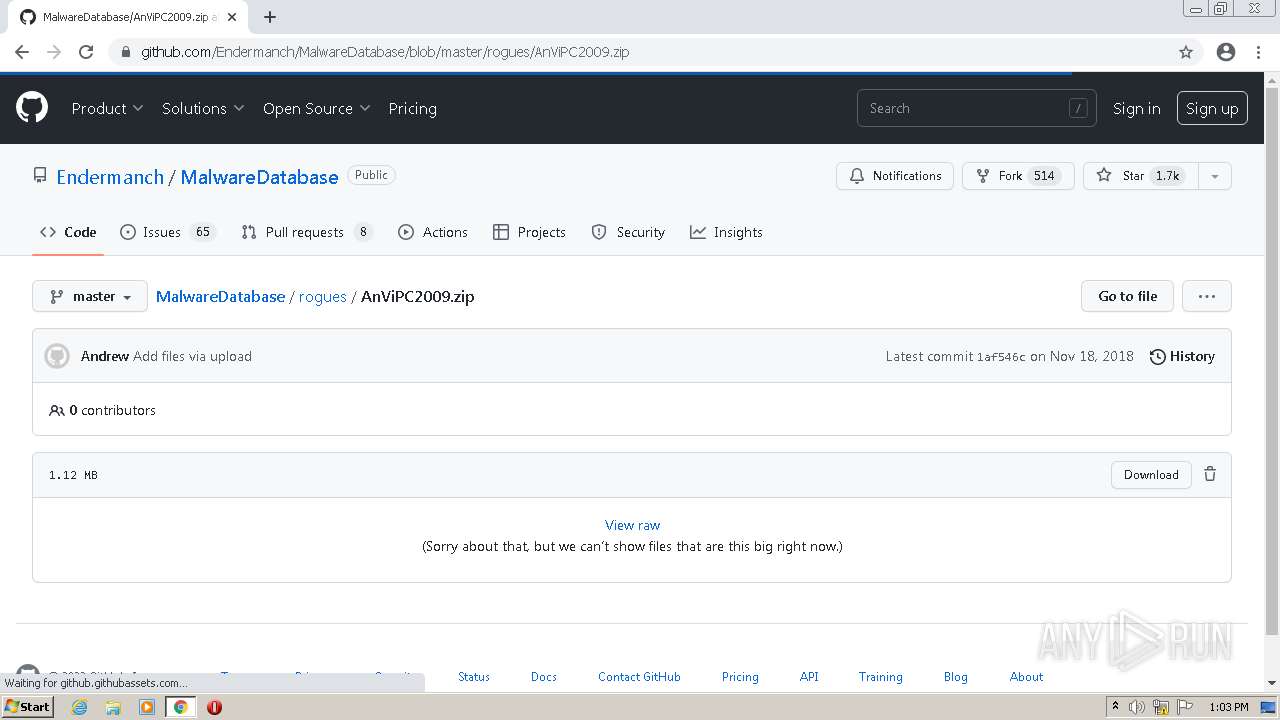
| 1900 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\AnViPC2009.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.91.0 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,2721312467202938198,16138510272847829393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f3dd988,0x6f3dd998,0x6f3dd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
44 866
Read events
44 482
Write events
374
Delete events
10
Modification events
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
10
Suspicious files
144
Text files
334
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-64281D7C-9D0.pma | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9abbe31f-a1a3-4139-8cb0-4b68d7226971.tmp | text | |
MD5:— | SHA256:— | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF24f4ff.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9c0891f7-e1b8-48bf-bb34-2f822868d138.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF24f53e.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
59
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
1896 | avpc2009.exe | GET | 302 | 77.88.55.60:80 | http://yandex.ru/1001 | RU | — | — | whitelisted |
1896 | avpc2009.exe | GET | 404 | 142.250.185.227:80 | http://google.ru/769029f7-8f3-495c-b450-2eacf65fb7a0 | US | html | 1.56 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac3n3d6wycjs4wavg2t6kq4eghoq_7945/hfnkpimlhhgieaddgfemjhofmfblmnib_7945_all_ac62jxv5dg4l2uvidem4cyh4xyqa.crx3 | US | binary | 14.9 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 126 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac3n3d6wycjs4wavg2t6kq4eghoq_7945/hfnkpimlhhgieaddgfemjhofmfblmnib_7945_all_ac62jxv5dg4l2uvidem4cyh4xyqa.crx3 | US | binary | 9.90 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | obj | 9.88 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/YGkwa4MXjfWSuERyWQYP_A_4/aapLKTSZ439A-0g3nqJr3Q | US | binary | 441 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dl6iudcrkm7tlleep5b7sio2si_2937/jflookgnkcckhobaglndicnbbgbonegd_2937_all_n6dma56ie7wmbezc4aw6zyp2jq.crx3 | US | obj | 9.88 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 289 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3348 | chrome.exe | 142.250.185.202:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3348 | chrome.exe | 142.250.186.99:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3348 | chrome.exe | 142.250.185.78:443 | www.youtube.com | GOOGLE | US | whitelisted |
3348 | chrome.exe | 142.250.186.182:443 | i.ytimg.com | GOOGLE | US | suspicious |
— | — | 142.250.74.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
3348 | chrome.exe | 142.250.186.66:443 | googleads.g.doubleclick.net | GOOGLE | US | whitelisted |
3348 | chrome.exe | 142.250.185.106:443 | jnn-pa.googleapis.com | GOOGLE | US | whitelisted |
3348 | chrome.exe | 142.250.184.196:443 | www.google.com | GOOGLE | US | whitelisted |
3348 | chrome.exe | 142.250.185.225:443 | yt3.ggpht.com | GOOGLE | US | whitelisted |
3348 | chrome.exe | 142.250.186.67:443 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
malwarewatch.org |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
unpkg.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.youtube.com |
| whitelisted |
i.ytimg.com |
| whitelisted |