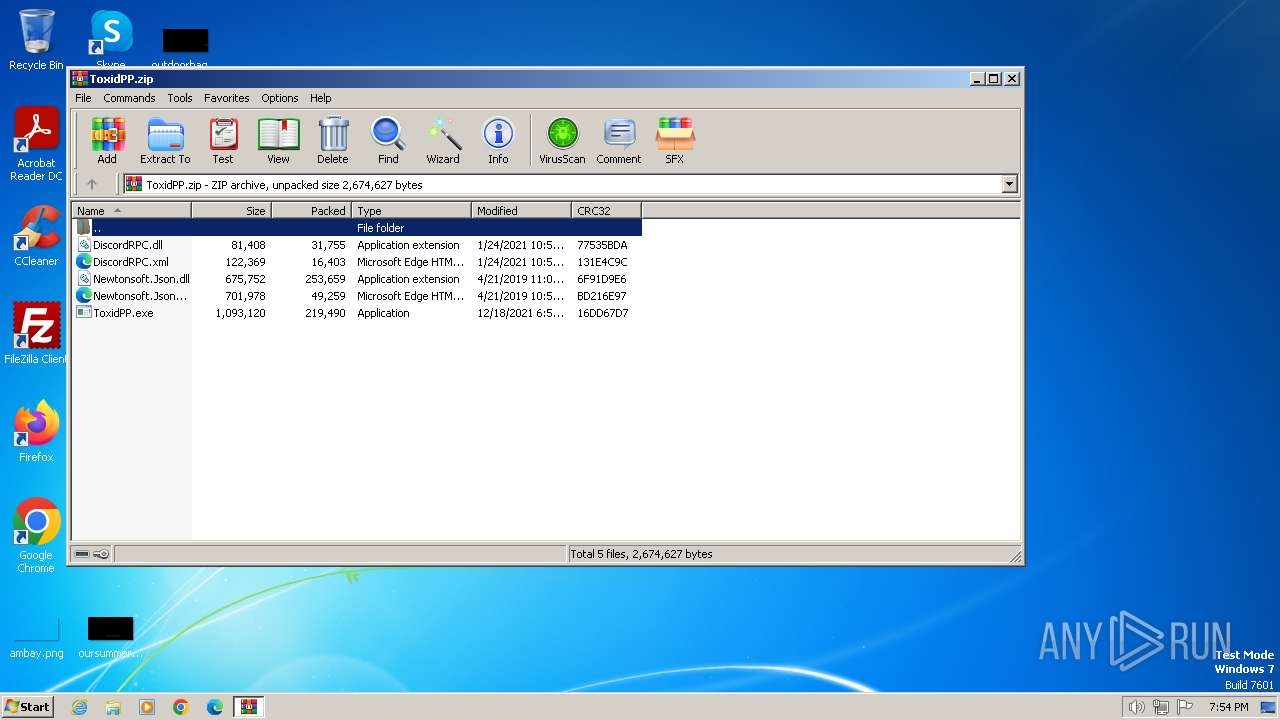
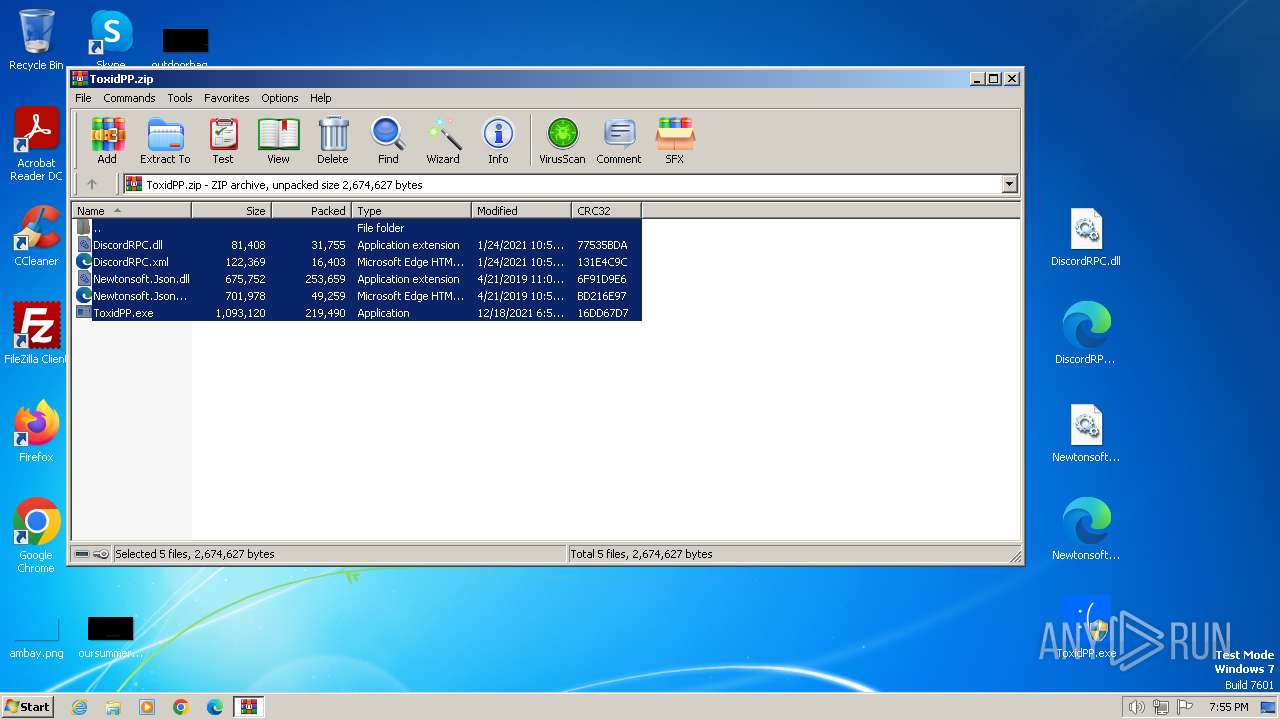
| File name: | ToxidPP.zip |
| Full analysis: | https://app.any.run/tasks/ab8780ea-19f8-4d76-b216-9e24e30308fb |
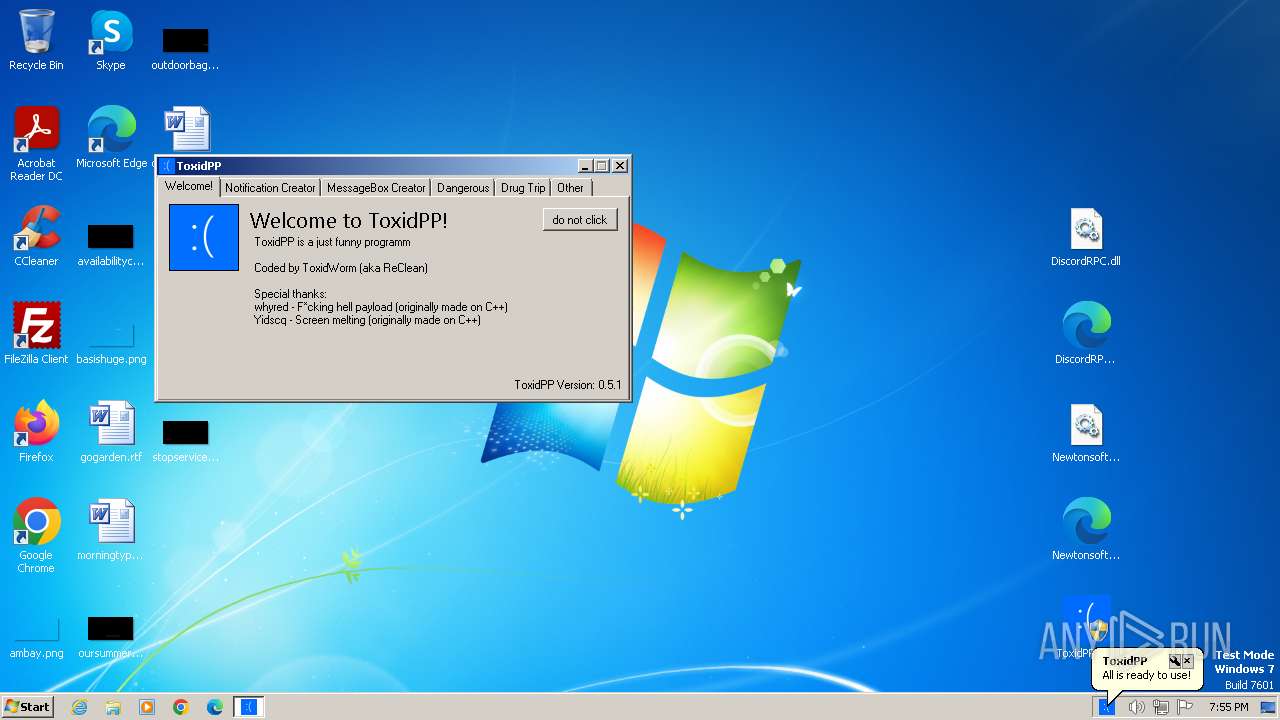
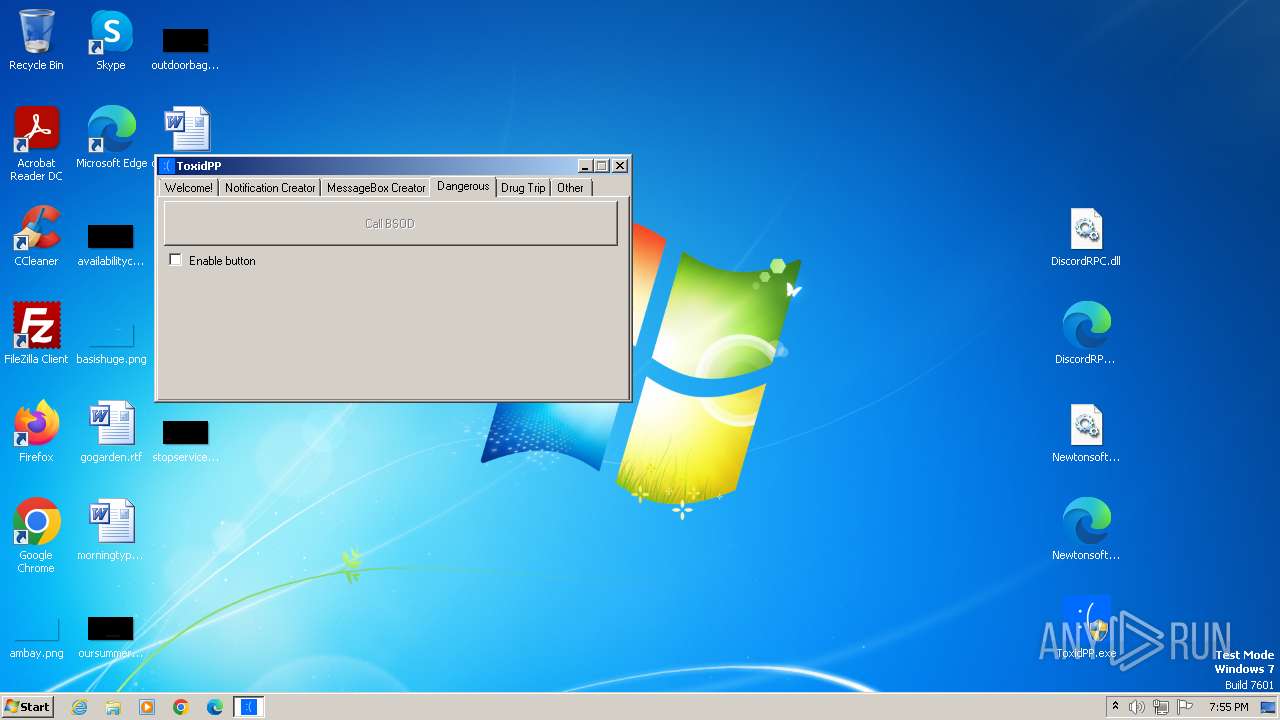
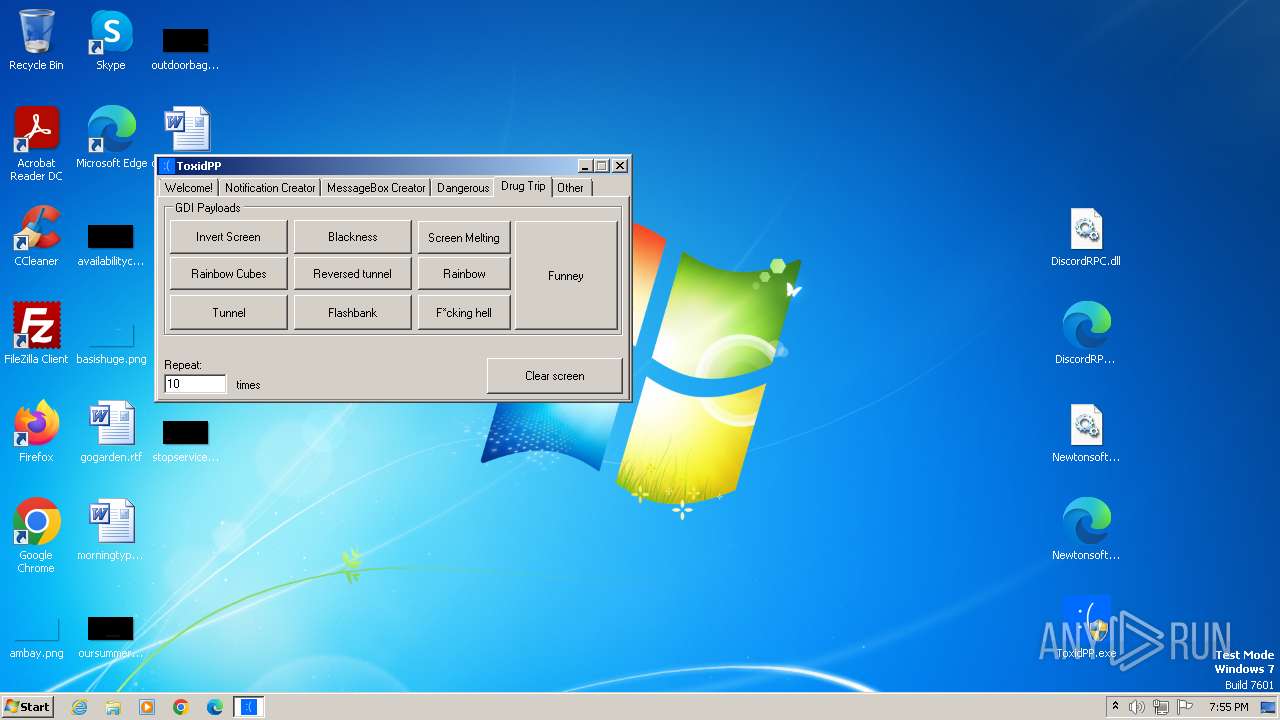
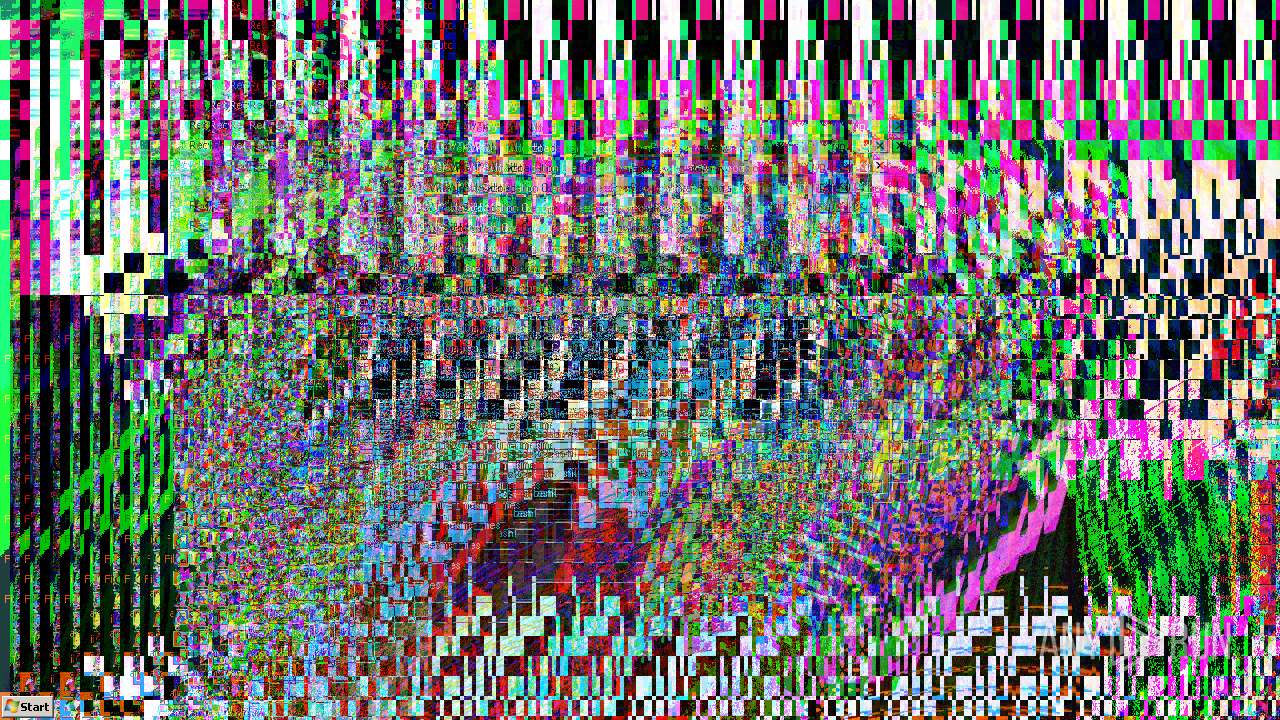
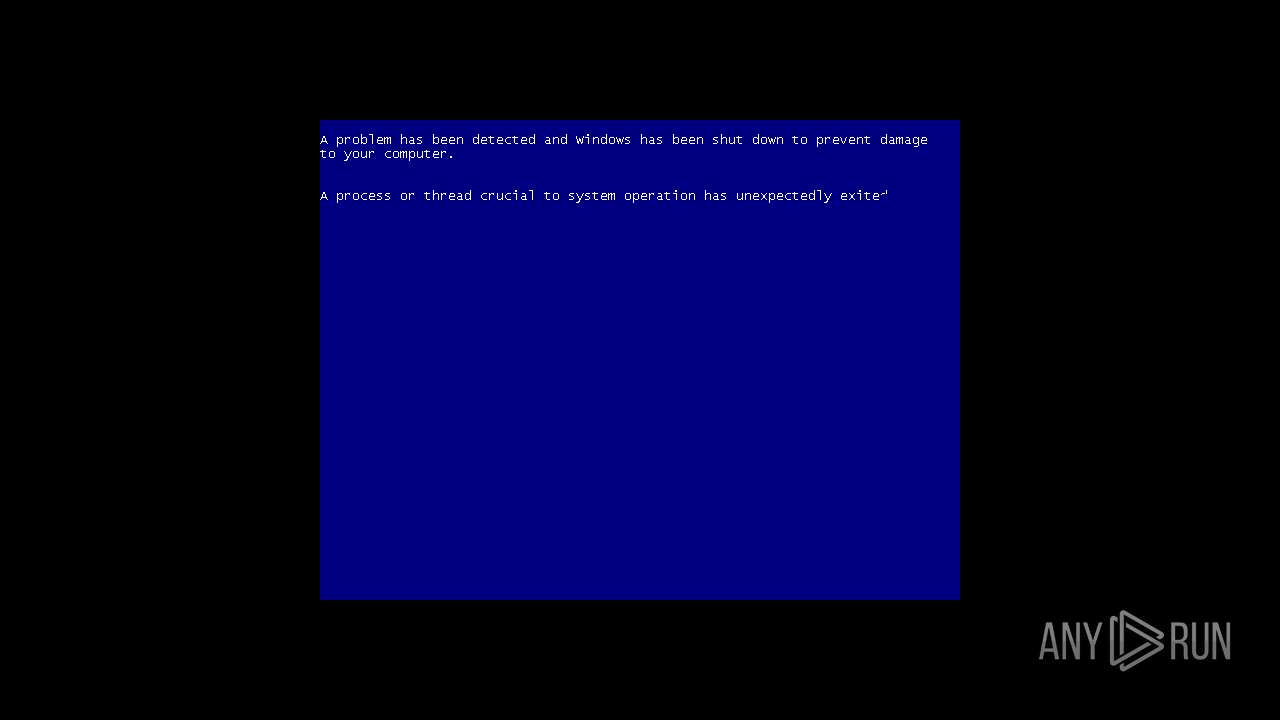
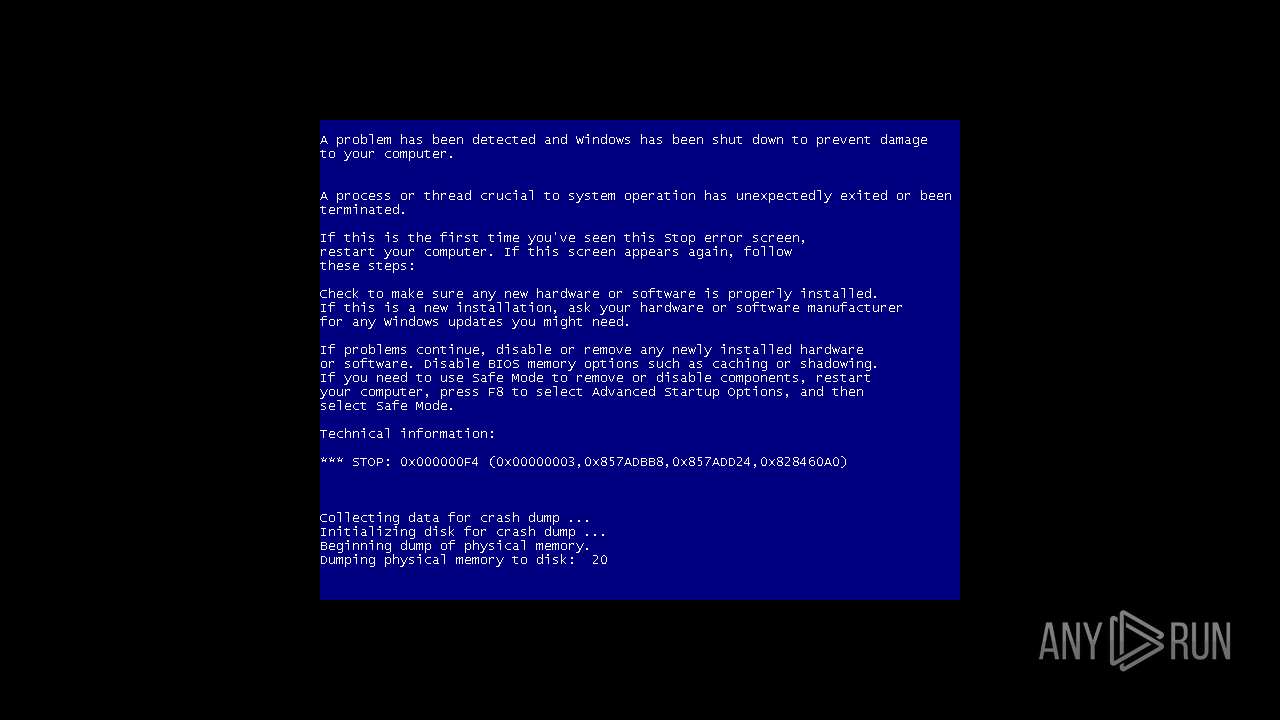
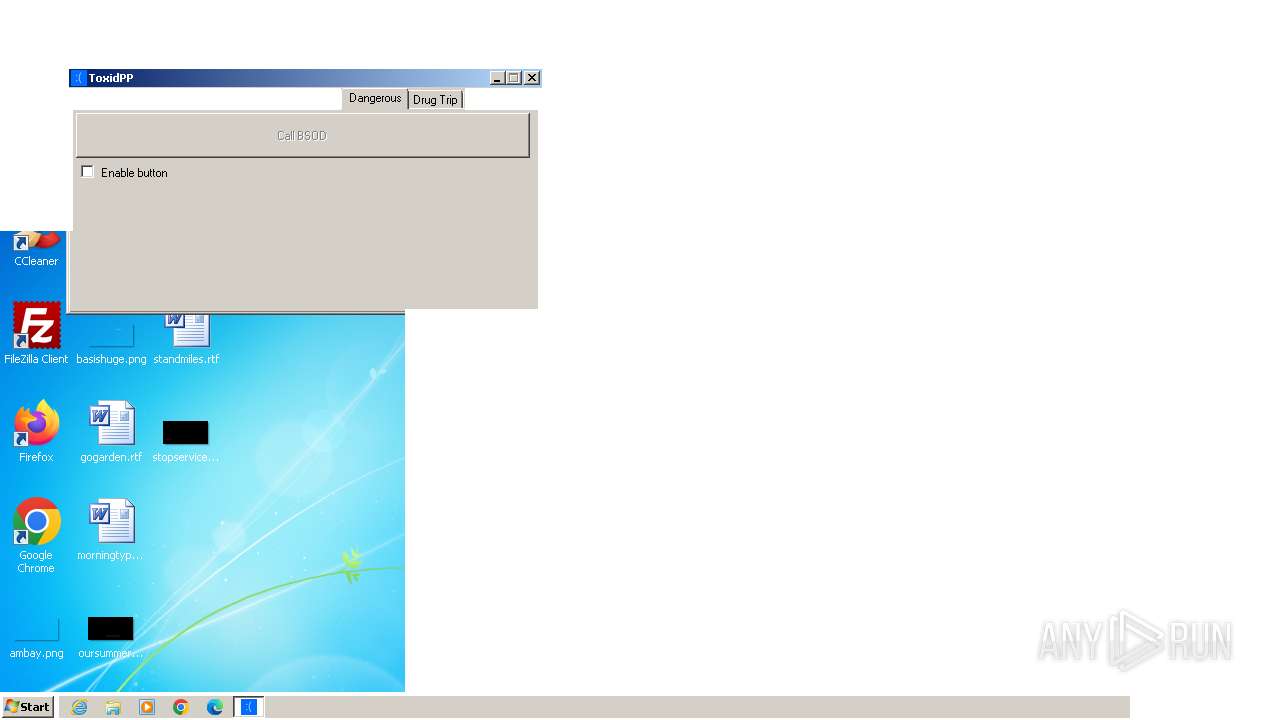
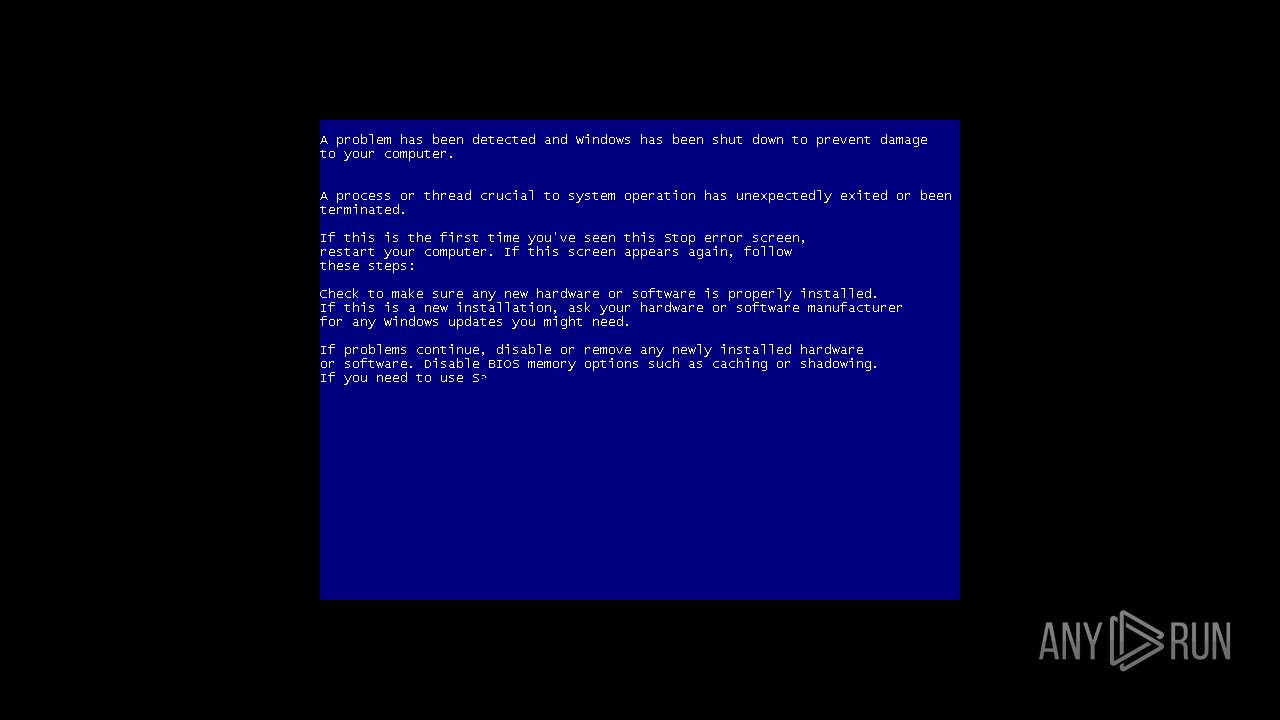
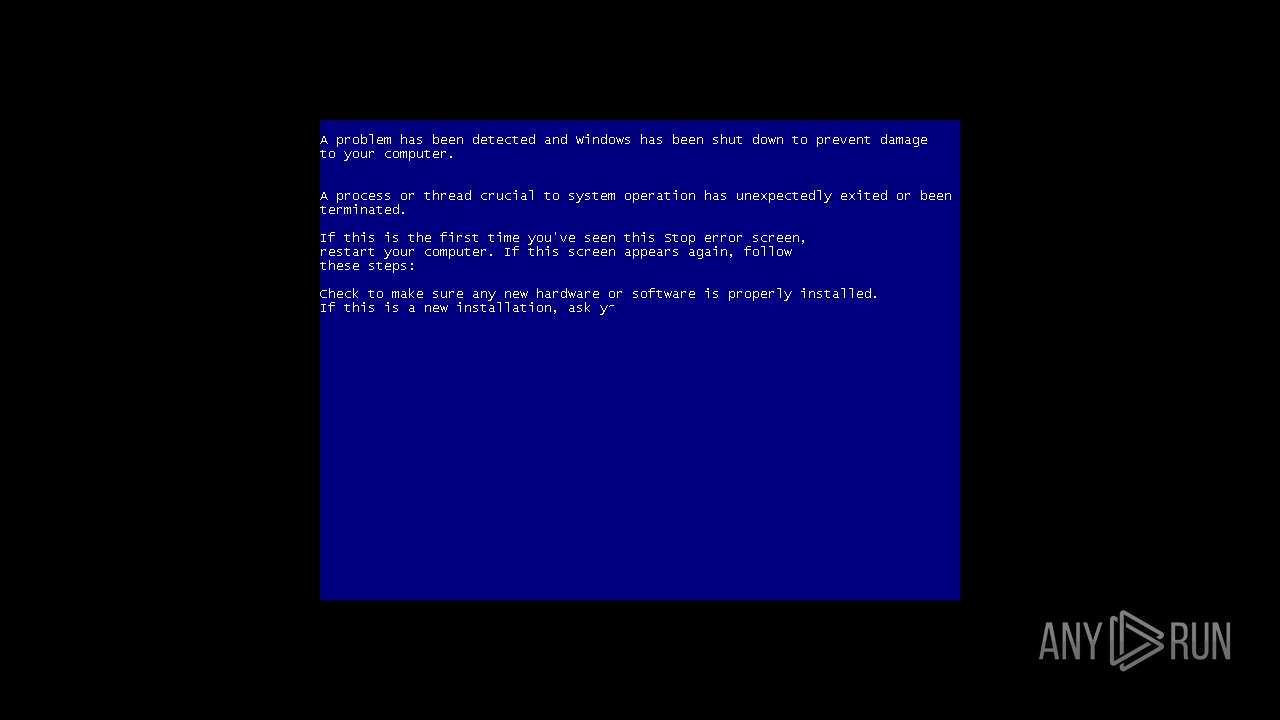
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2024, 19:54:43 |
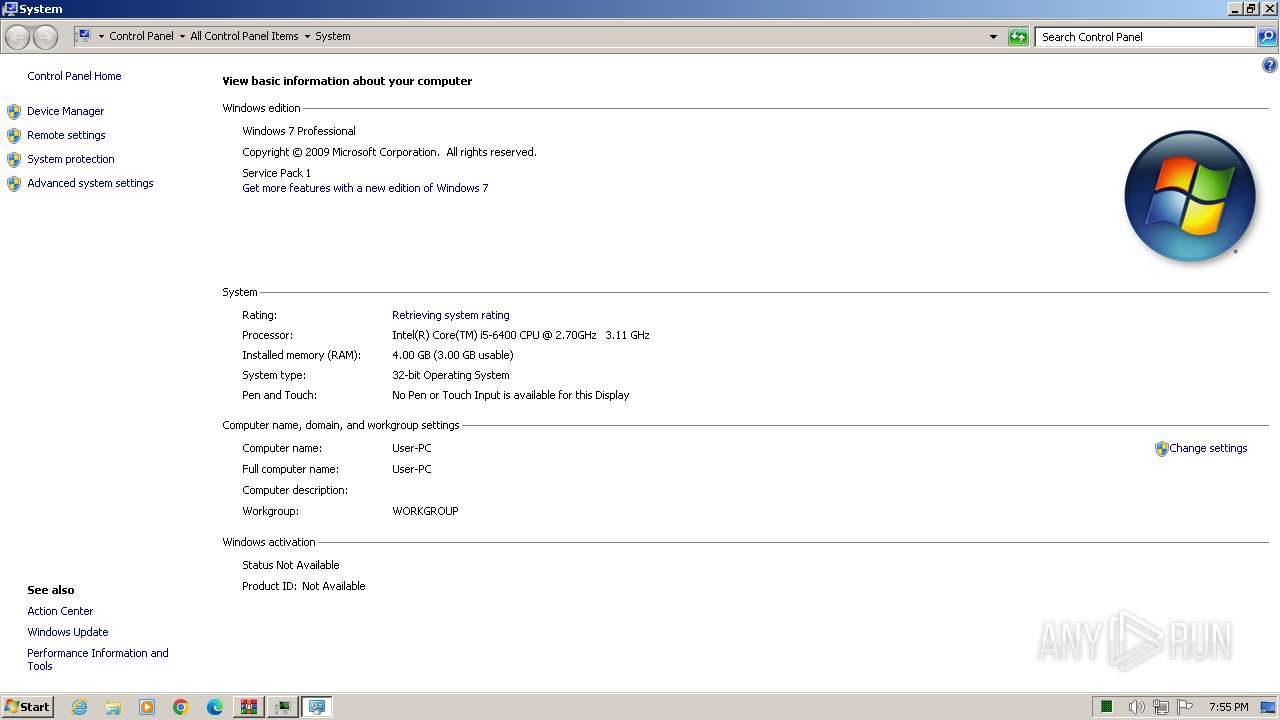
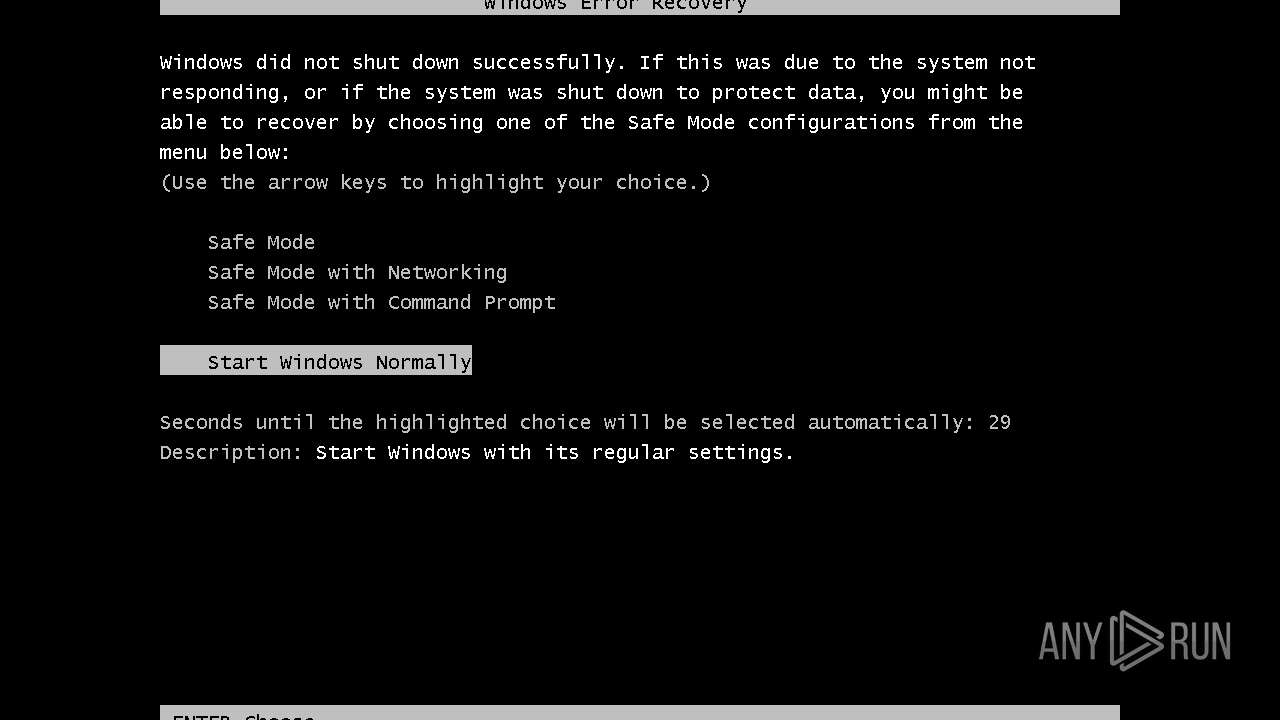
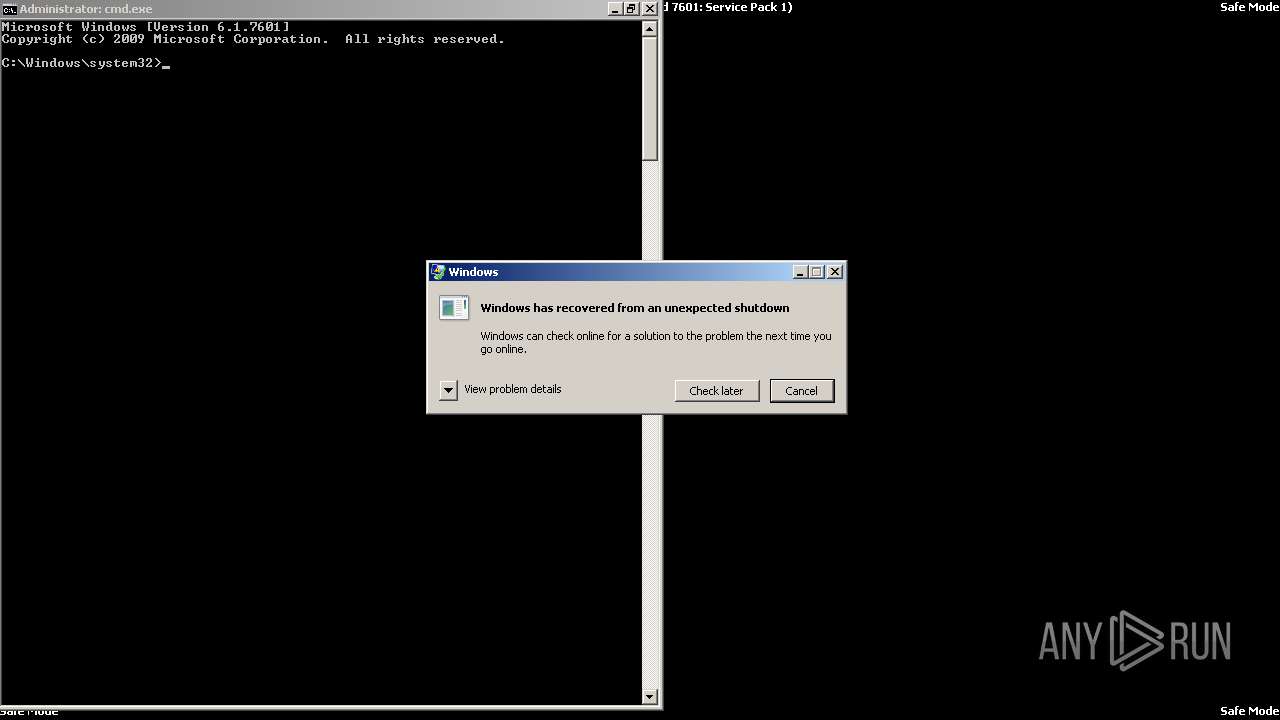
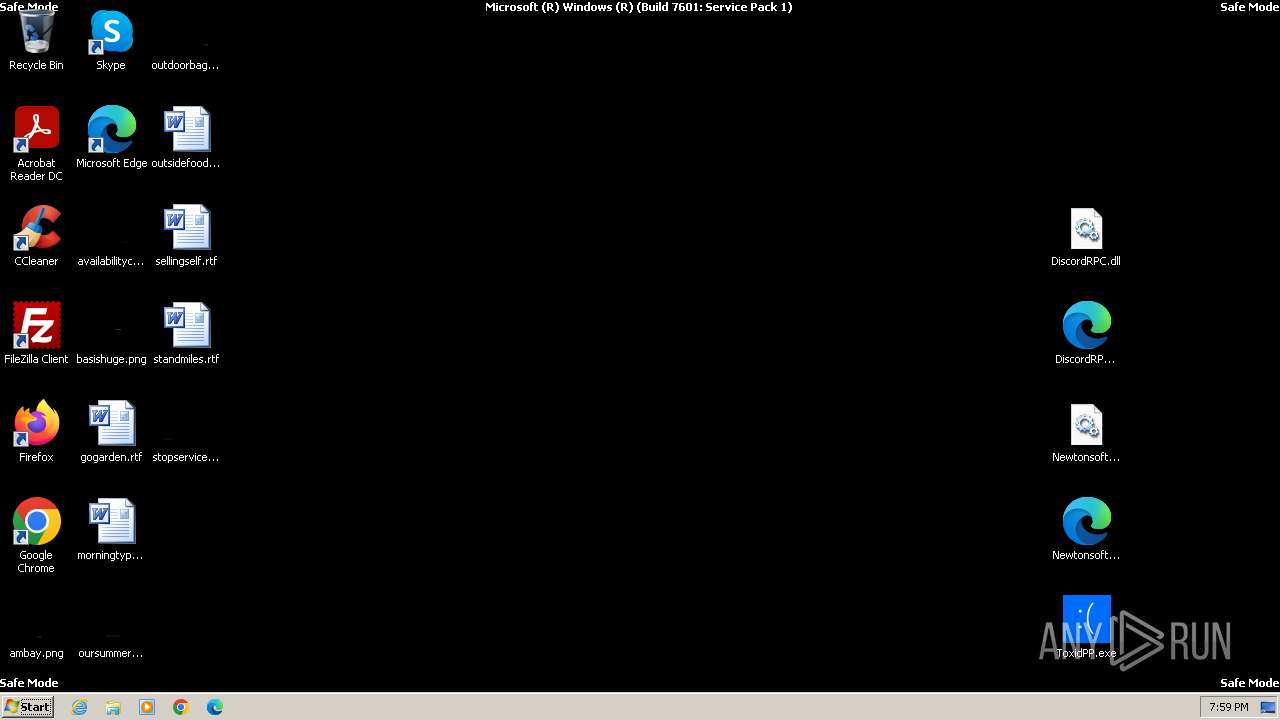
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E4C9B38ACD1F5495364020B0B29249EC |
| SHA1: | 0CEE5B2671795C71C54BE216635D8F62E16F517B |
| SHA256: | 523C187C70D392ECB8B0129EF0303C0C5B7C163FFC55D2E3543A99406C806229 |
| SSDEEP: | 24576:8ILwY16wAcOpa1S+A21x2kVDOkFHk8bC1H76LGirtKWqmeYmCUg:8ILwY16wAcOpa18272kVDRFHk8bC1H7Q |
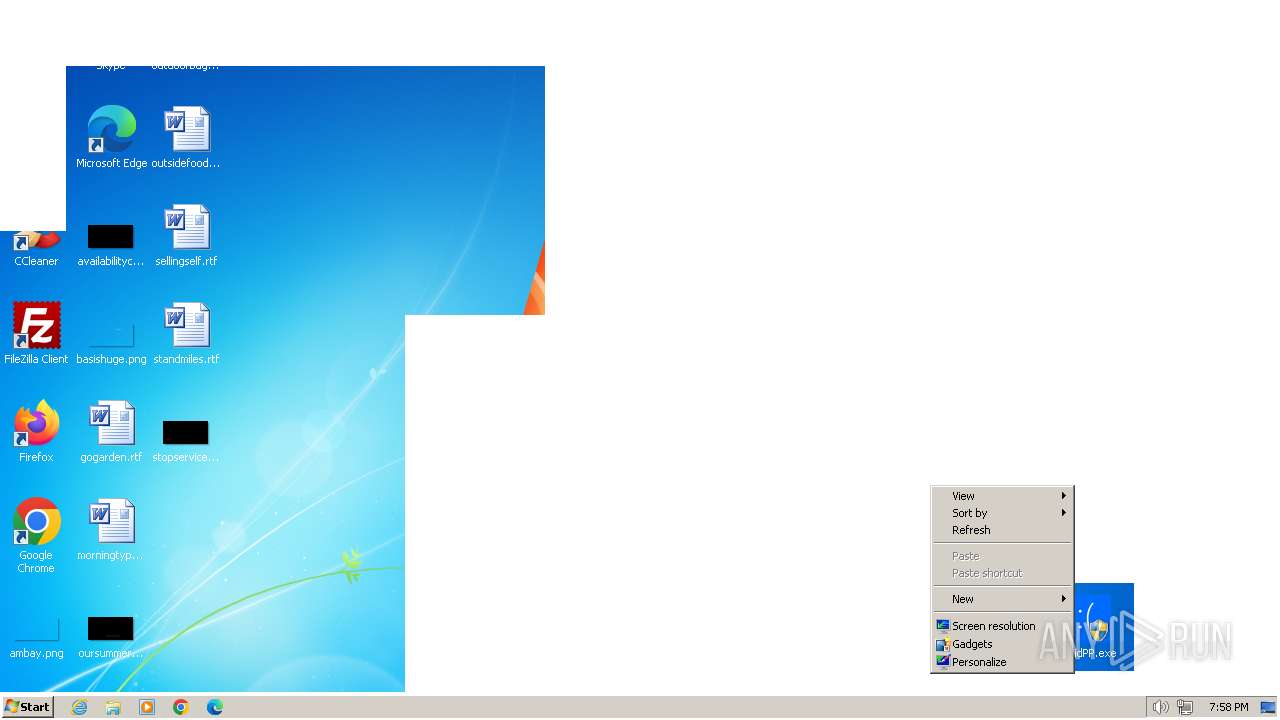
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3668)
SUSPICIOUS
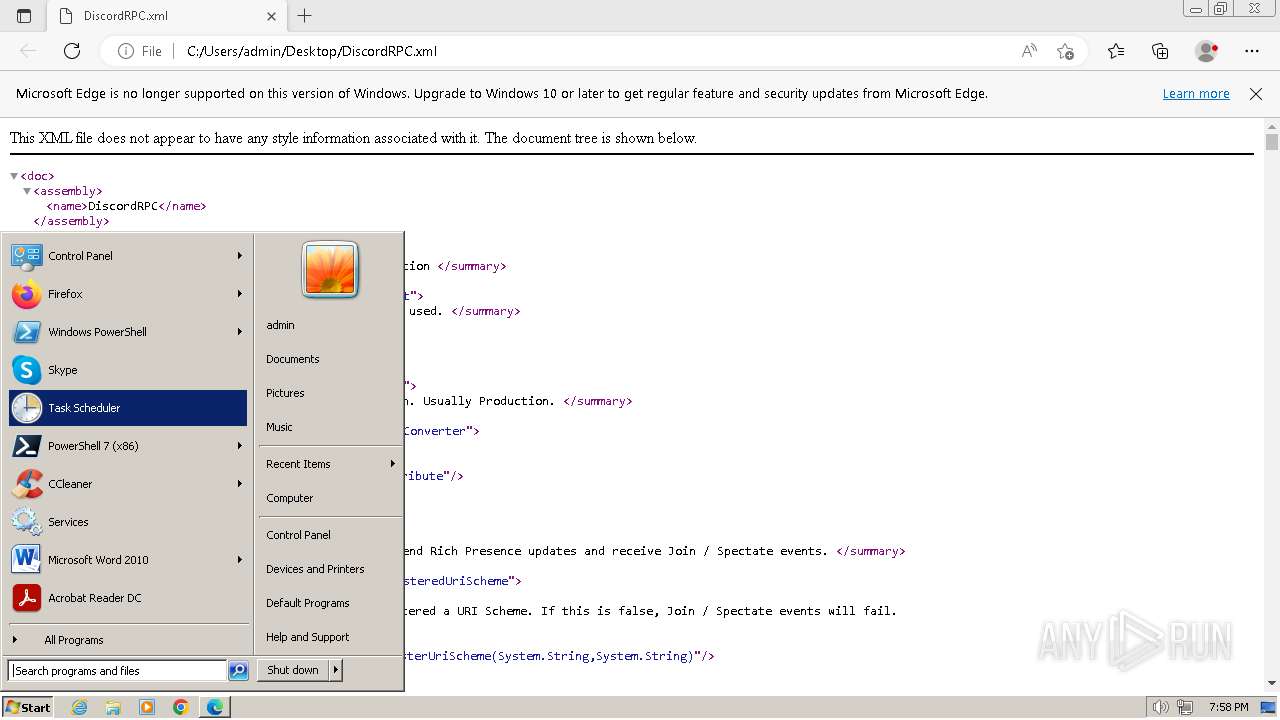
The process executes via Task Scheduler
- ctfmon.exe (PID: 1456)
- sipnotify.exe (PID: 1964)
Reads the Internet Settings
- sipnotify.exe (PID: 1964)
- runonce.exe (PID: 1332)
Application launched itself
- WerFault.exe (PID: 1484)
Reads settings of System Certificates
- sipnotify.exe (PID: 1964)
Reads the date of Windows installation
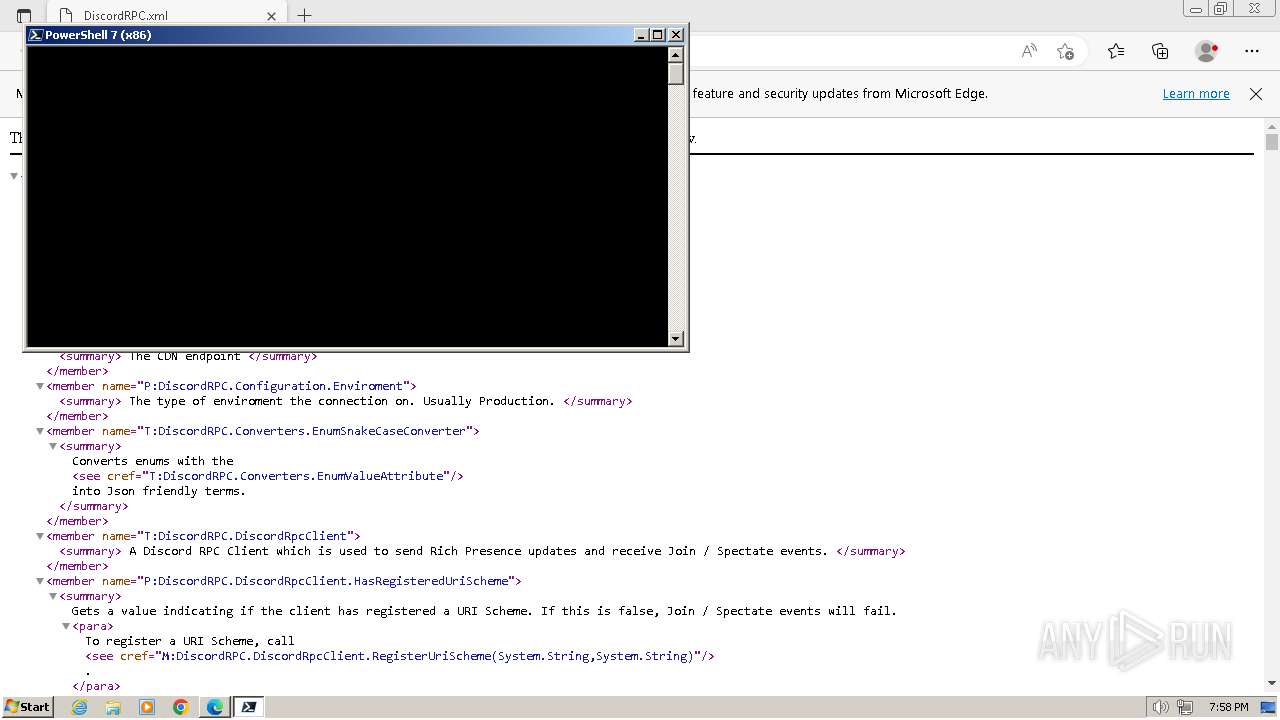
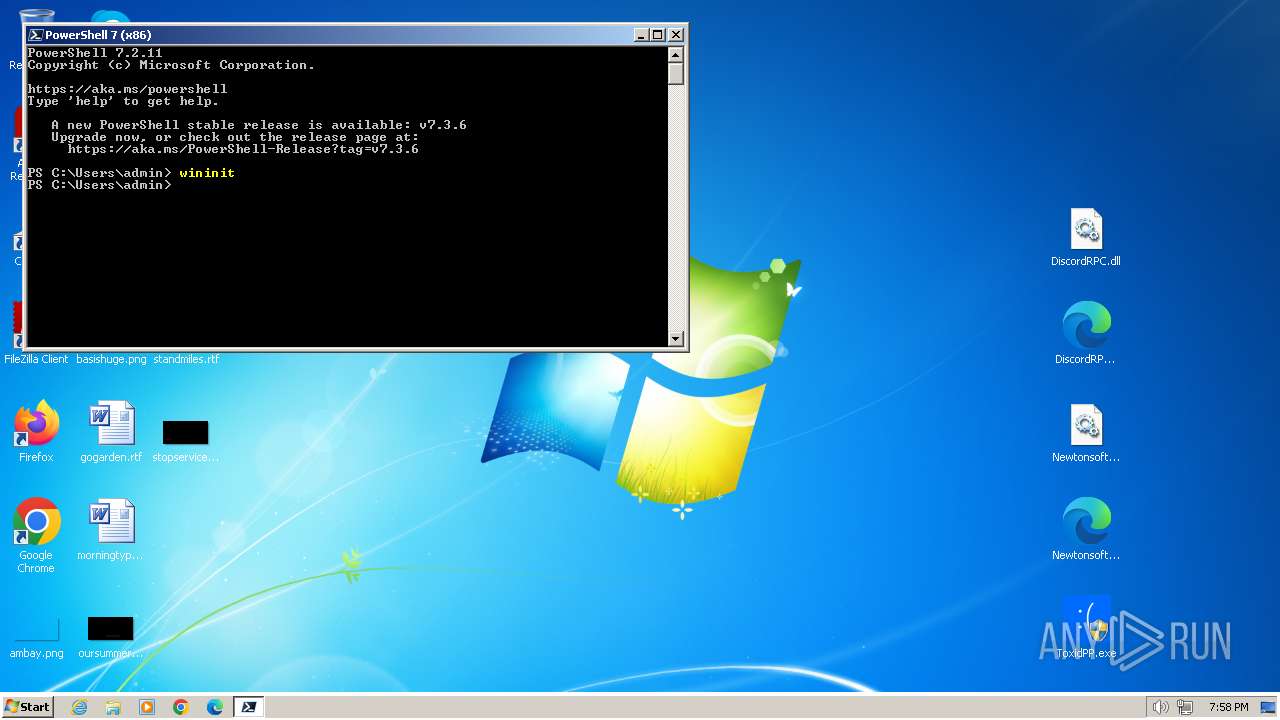
- pwsh.exe (PID: 3572)
INFO
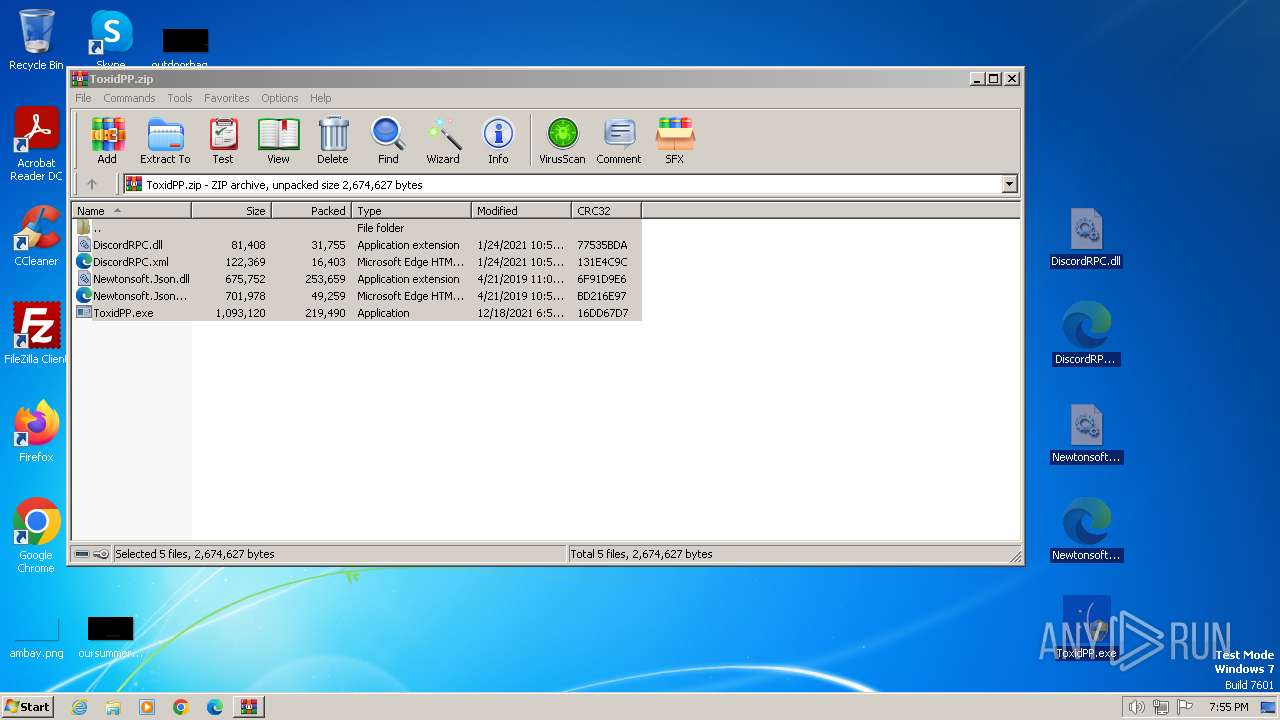
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3668)
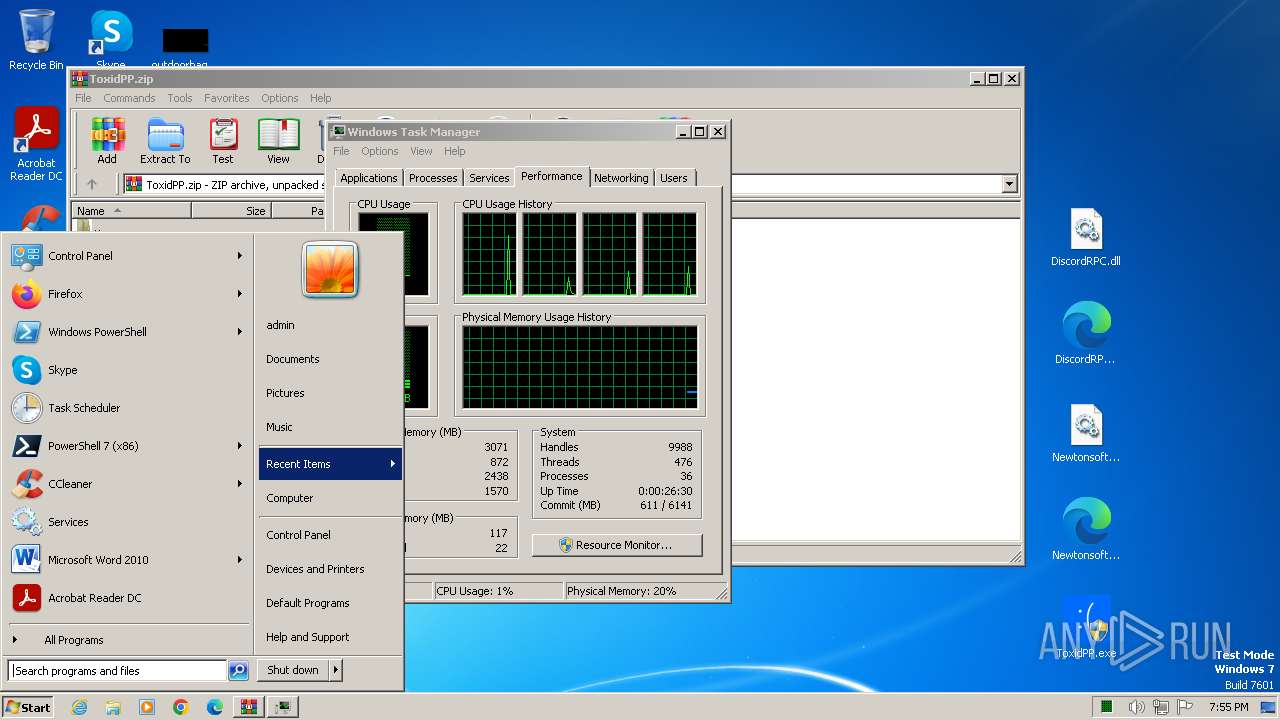
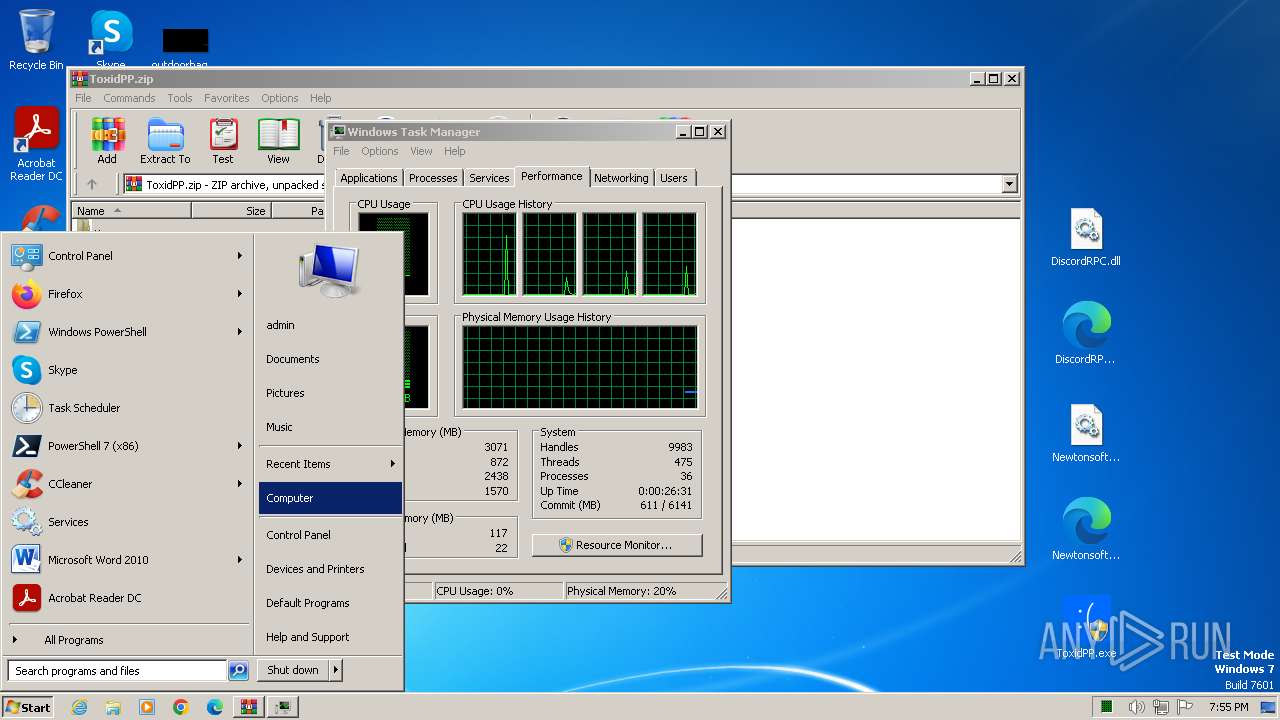
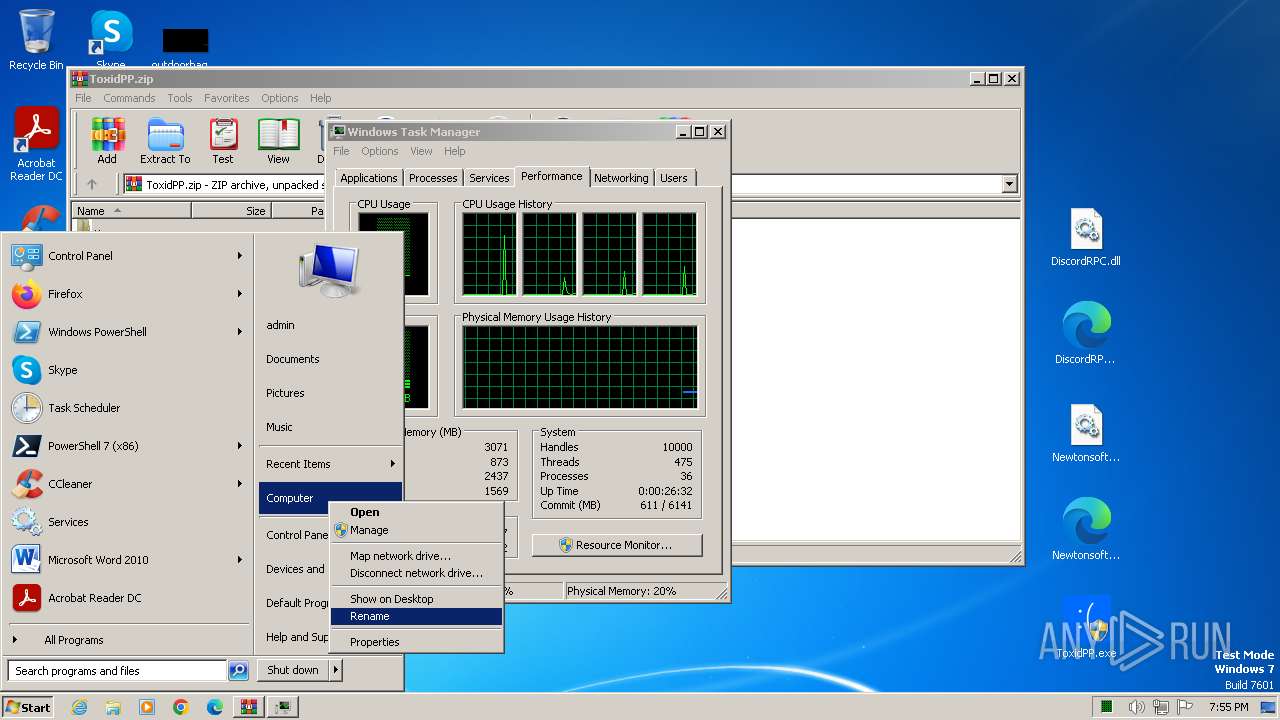
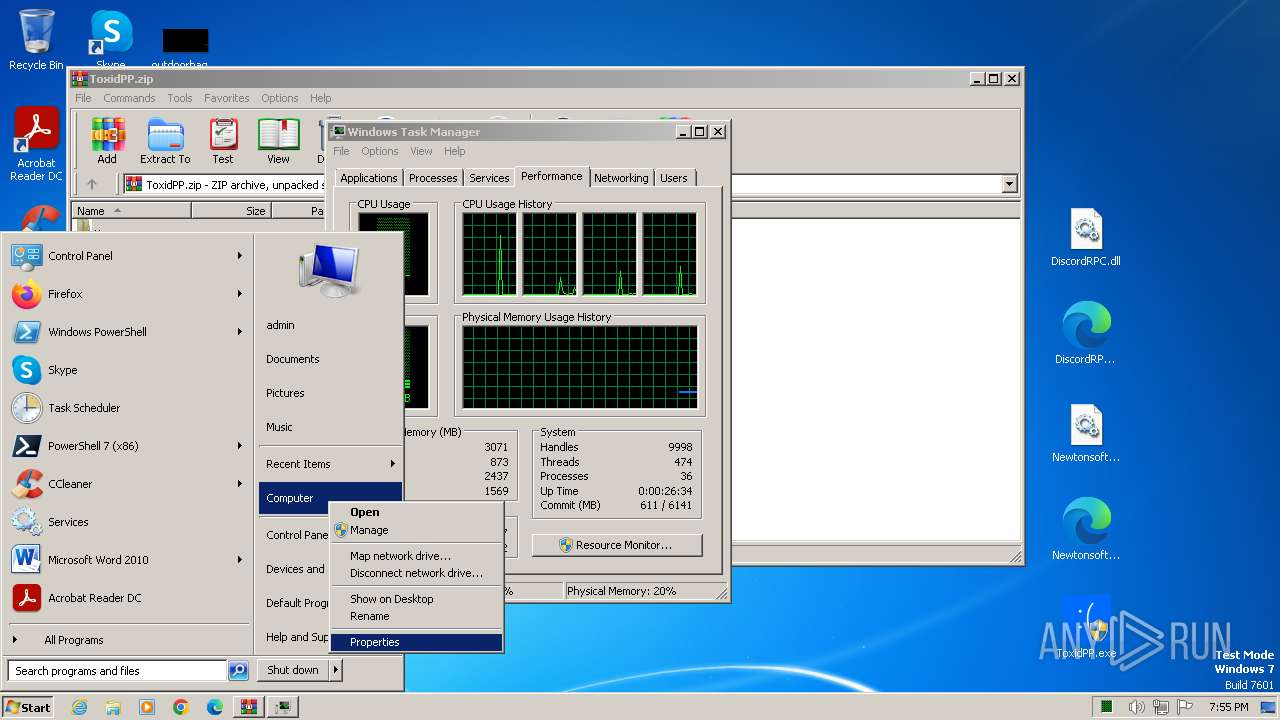
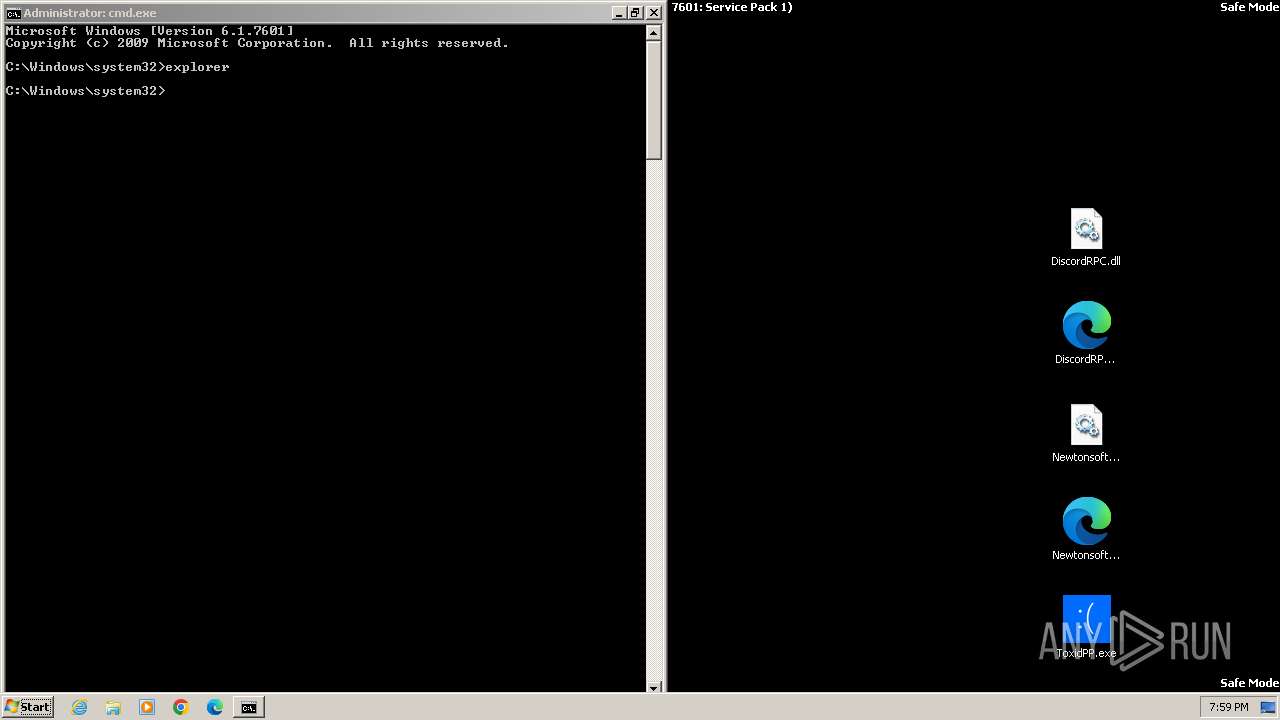
Manual execution by a user
- taskmgr.exe (PID: 3660)
- control.exe (PID: 1492)
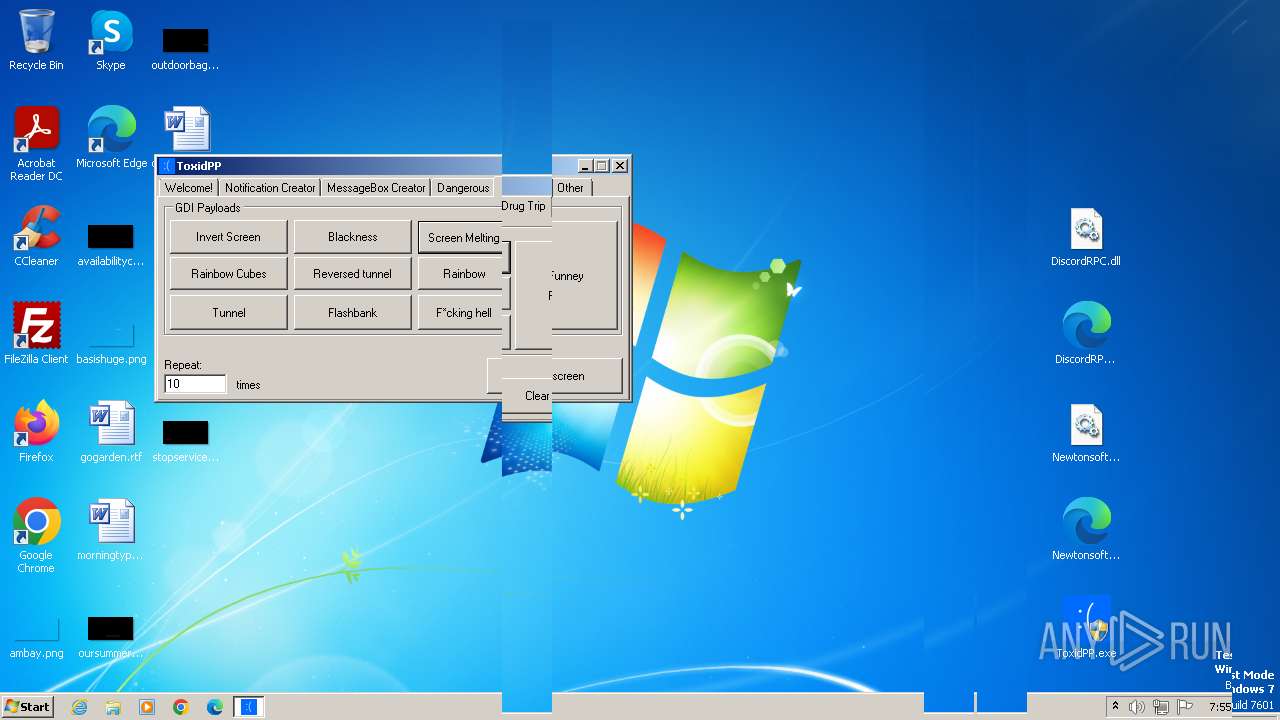
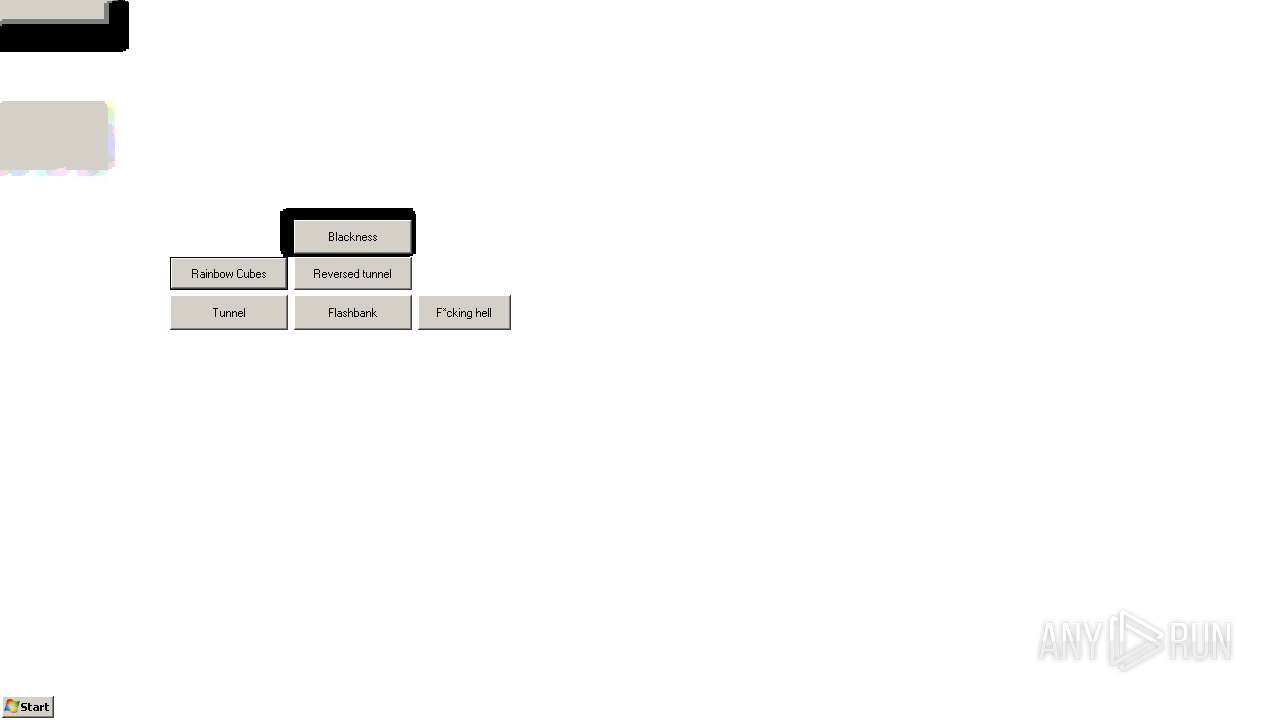
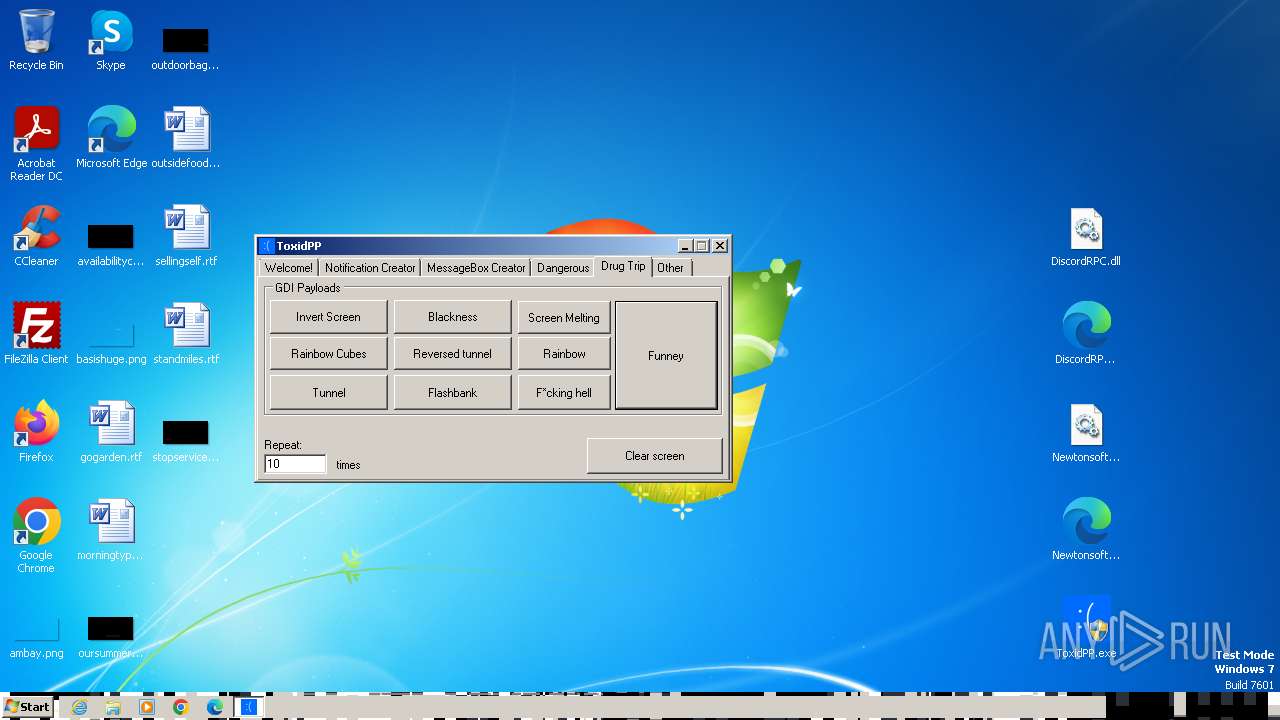
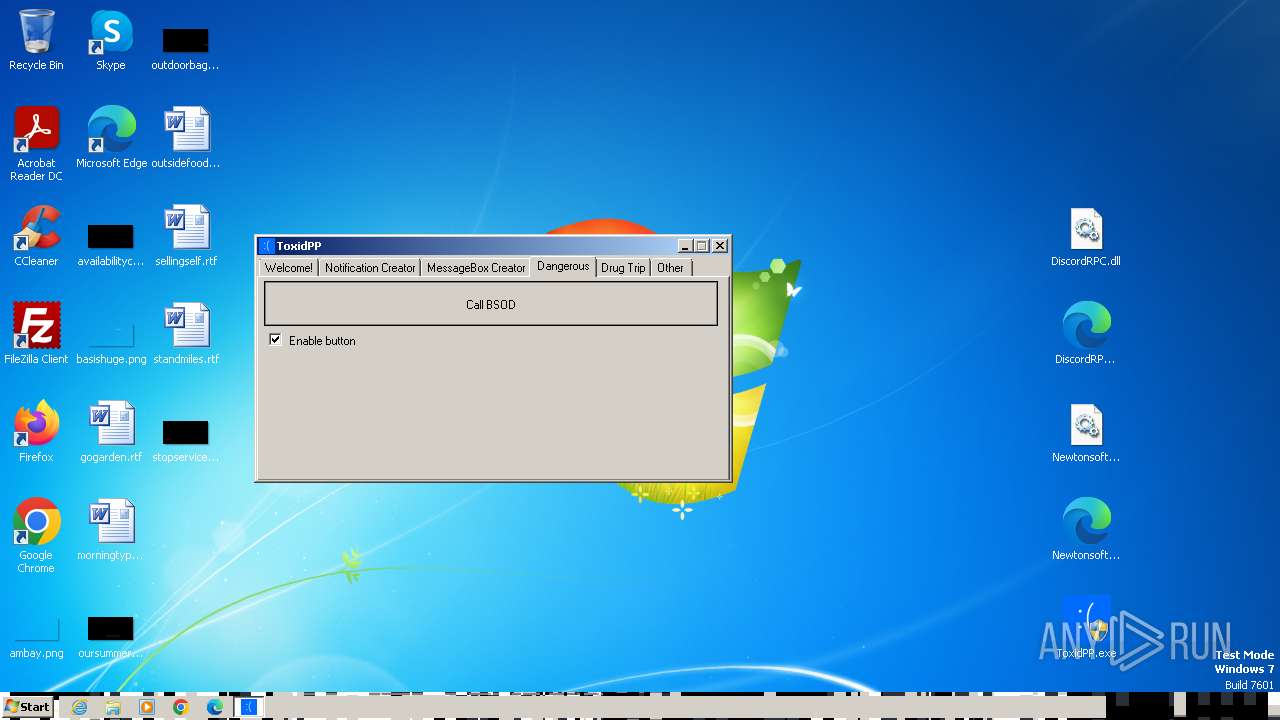
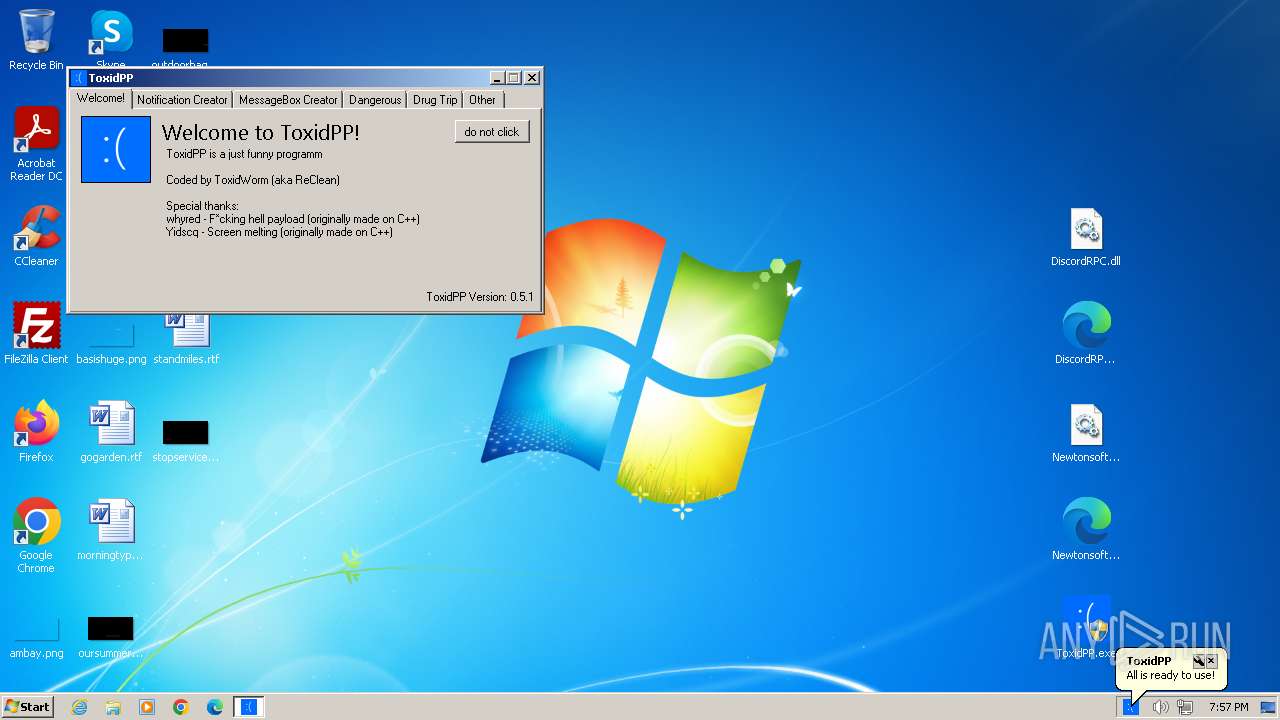
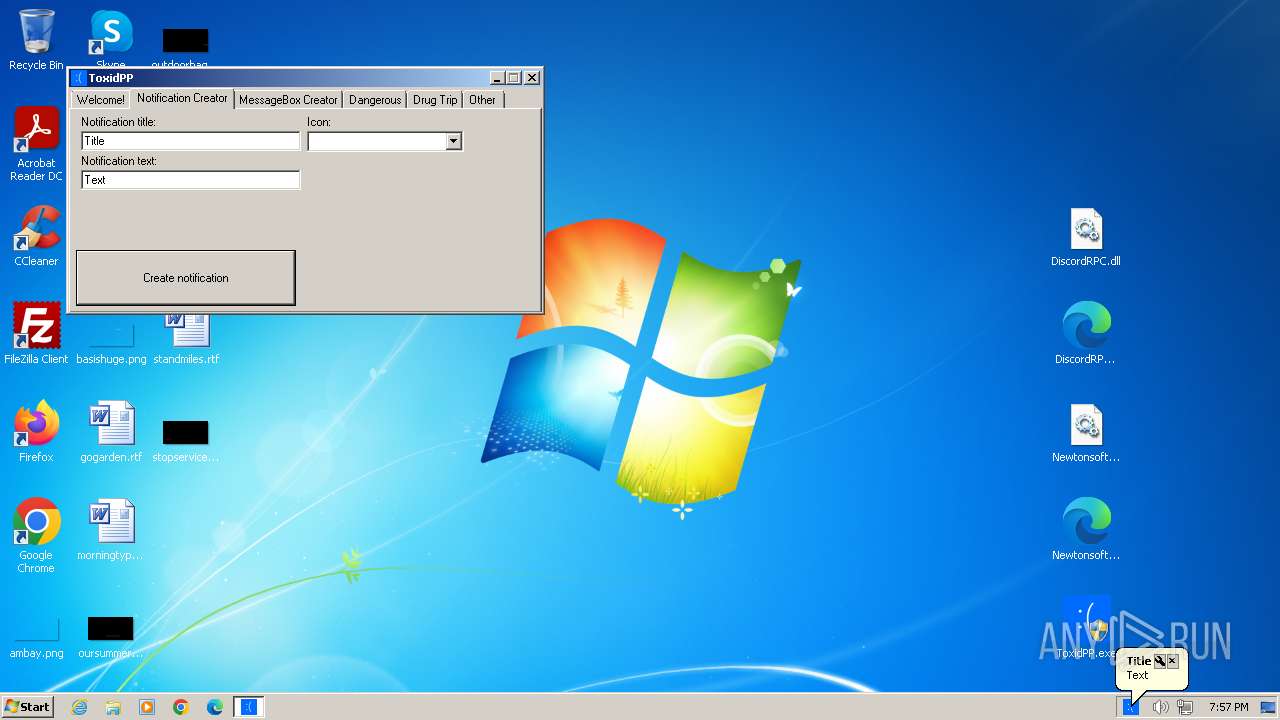
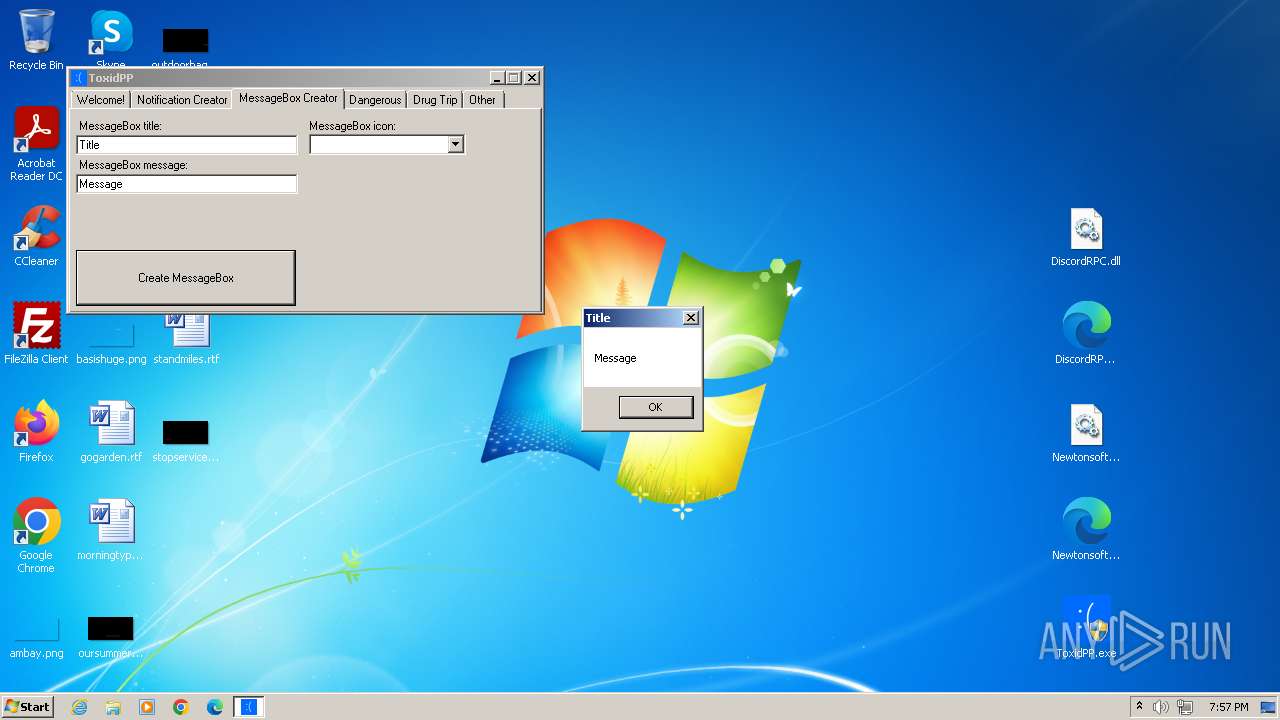
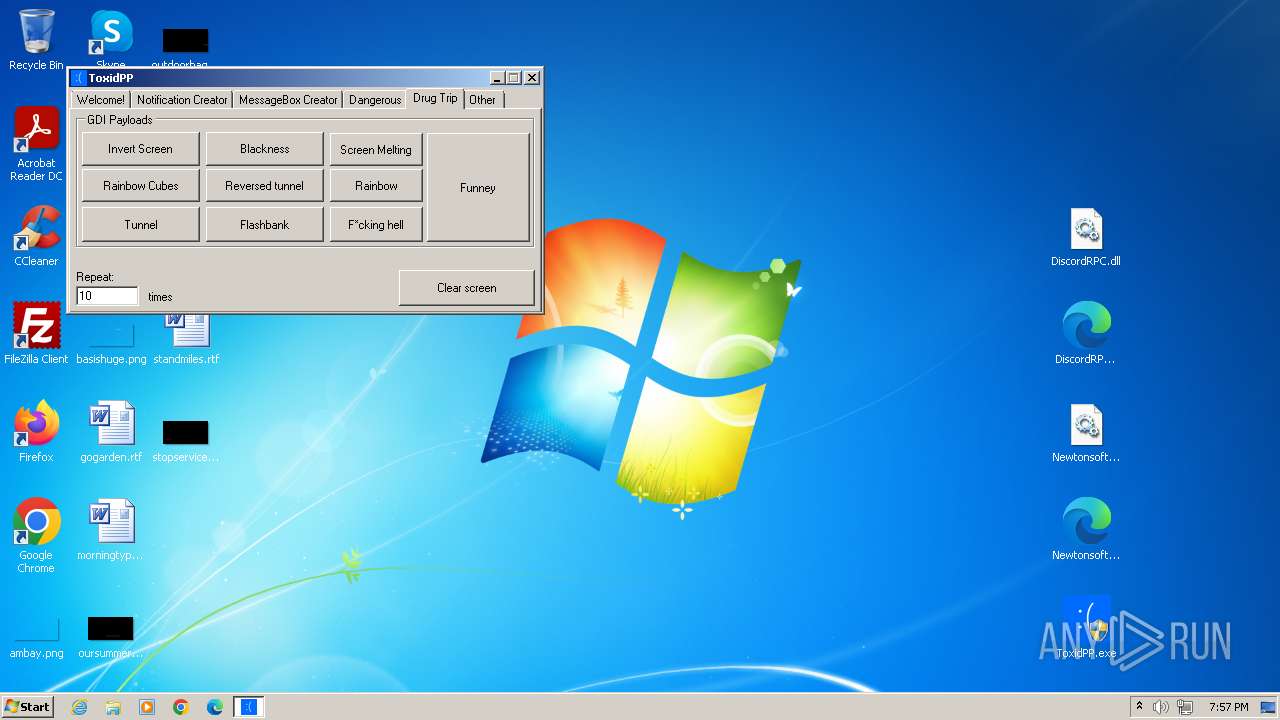
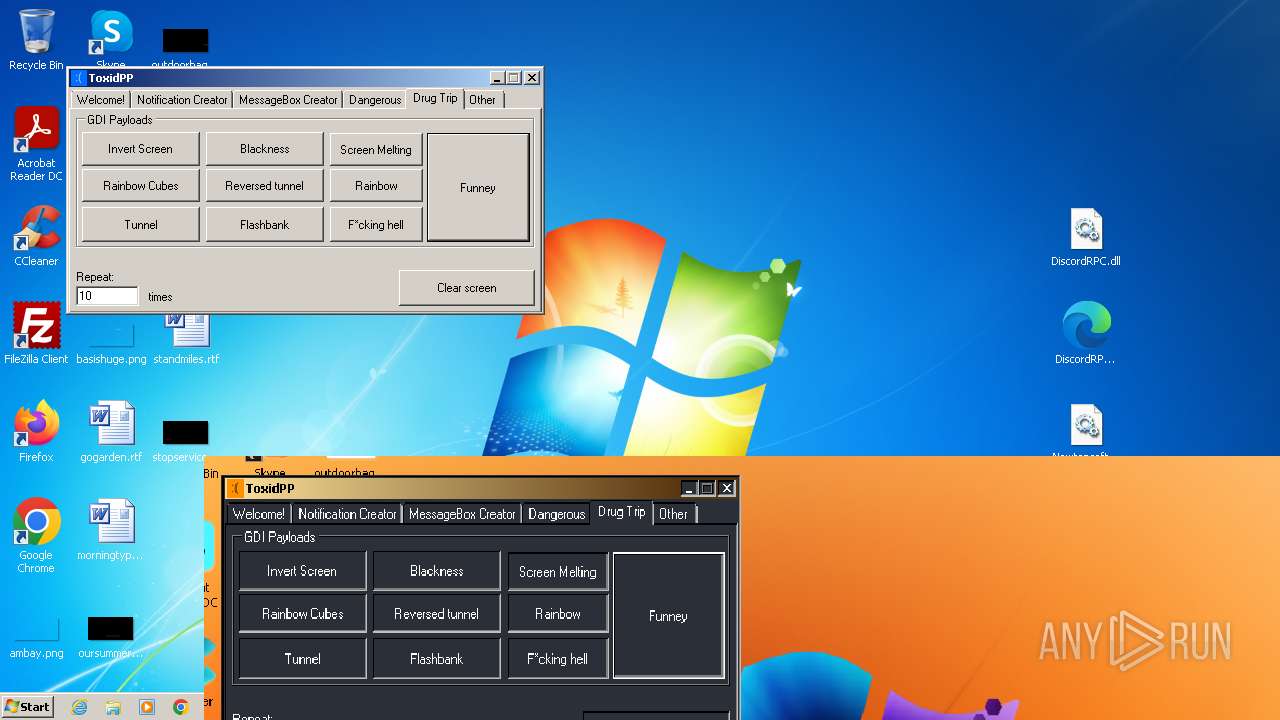
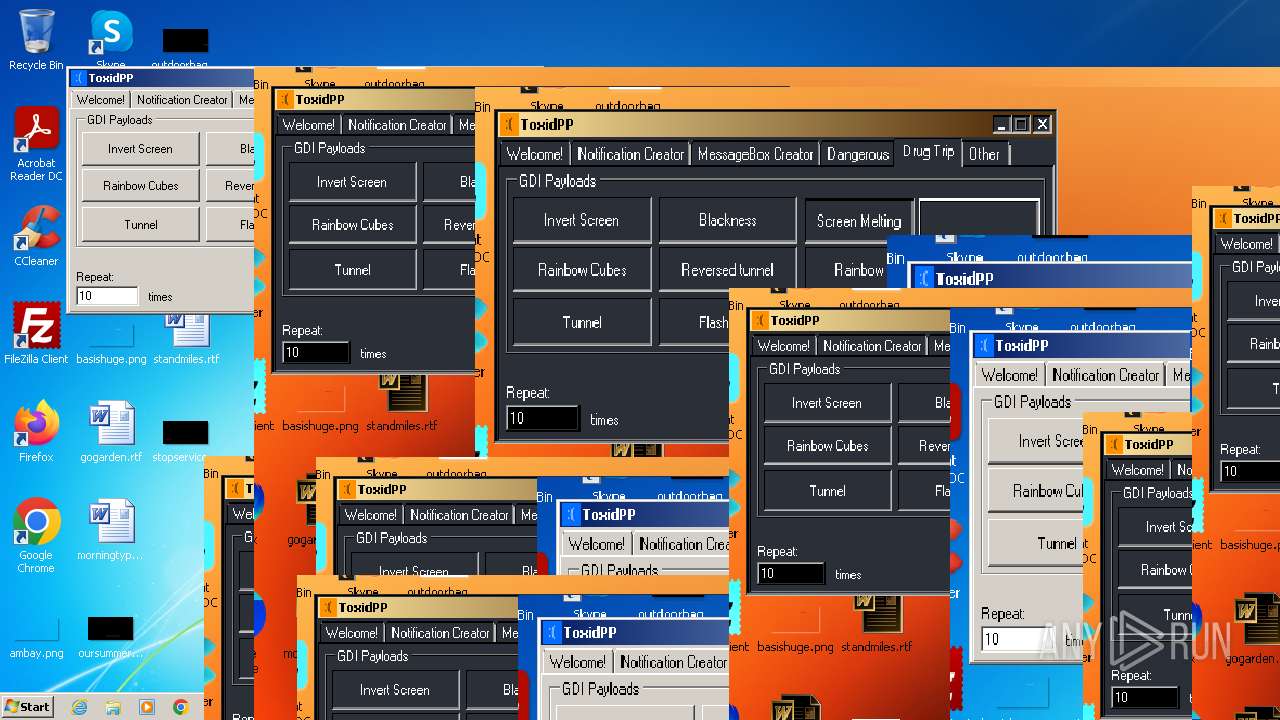
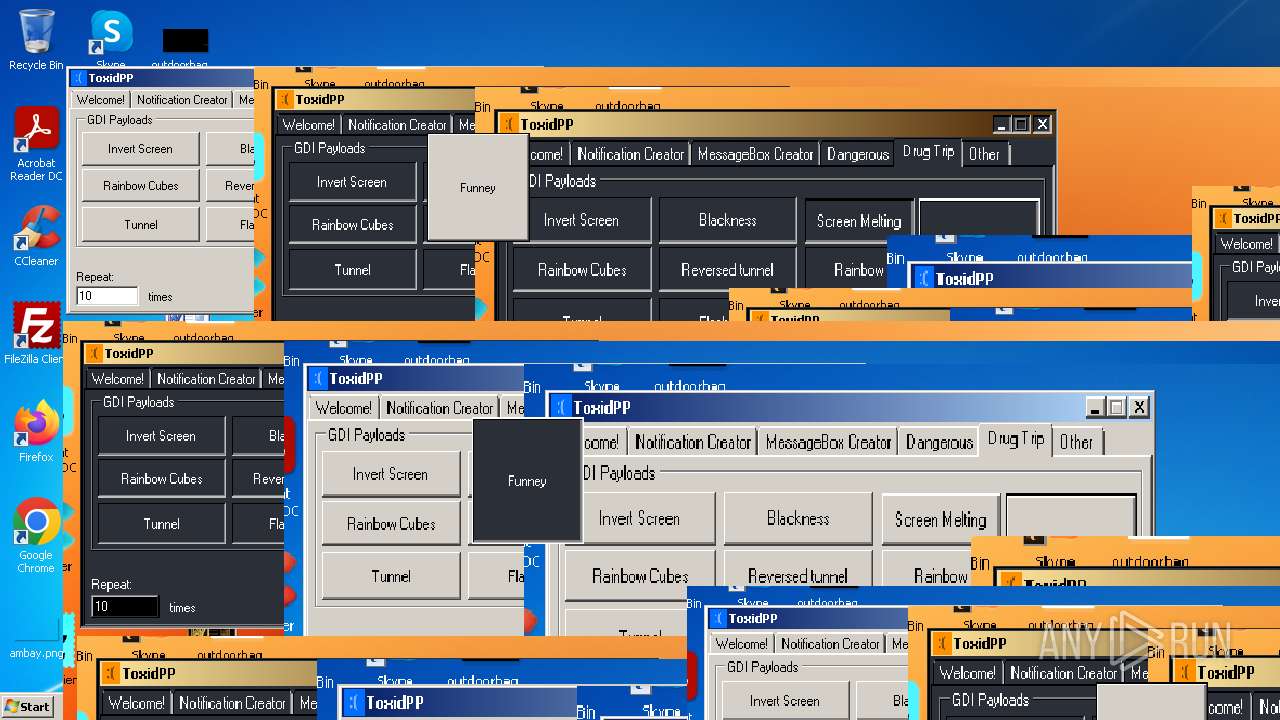
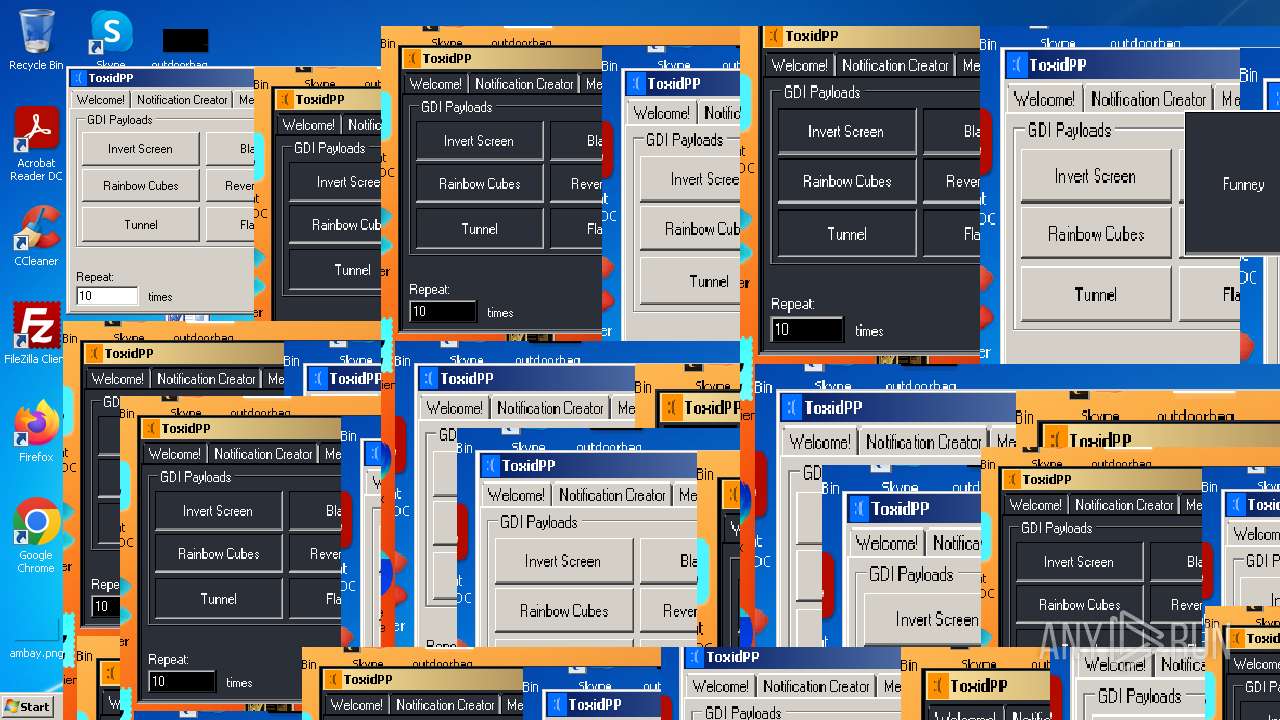
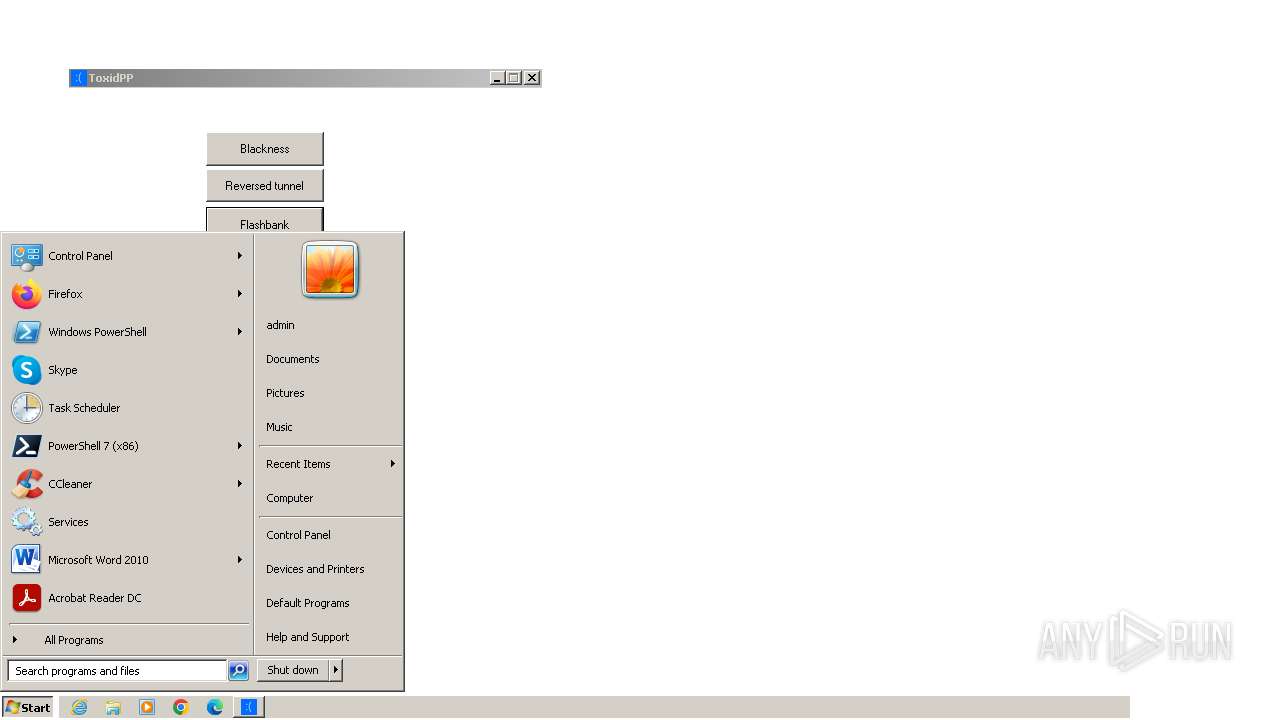
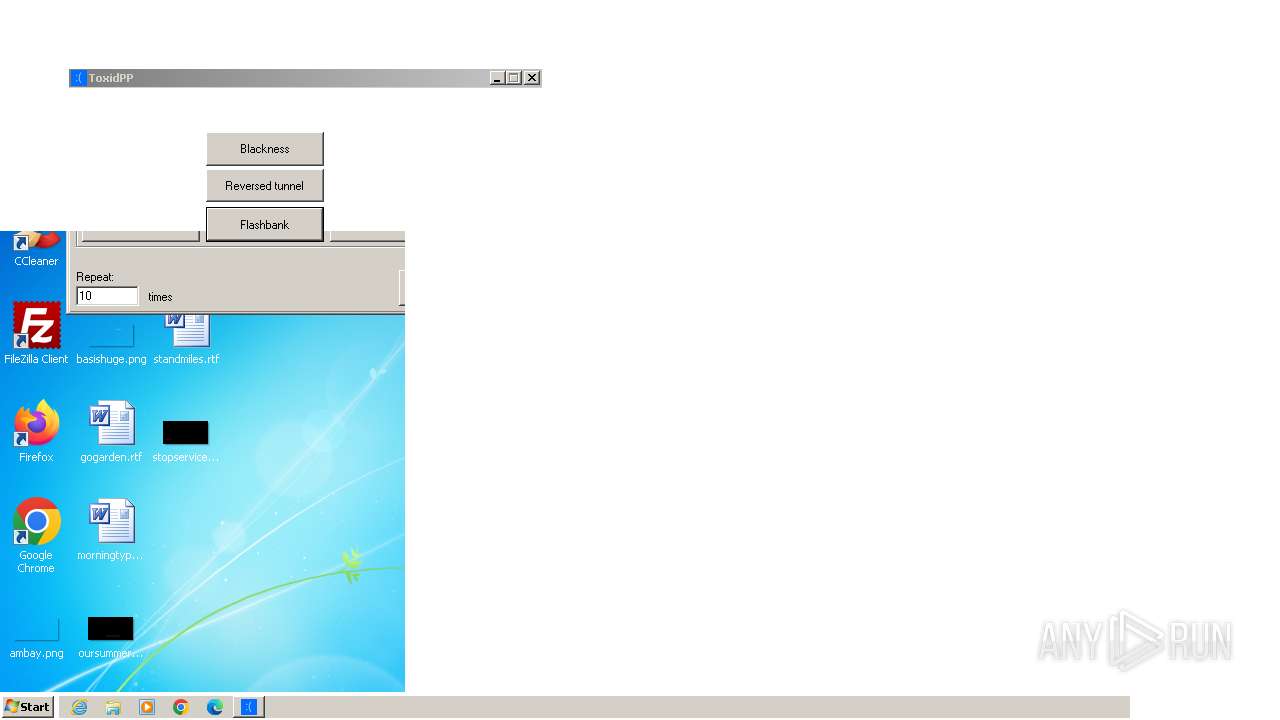
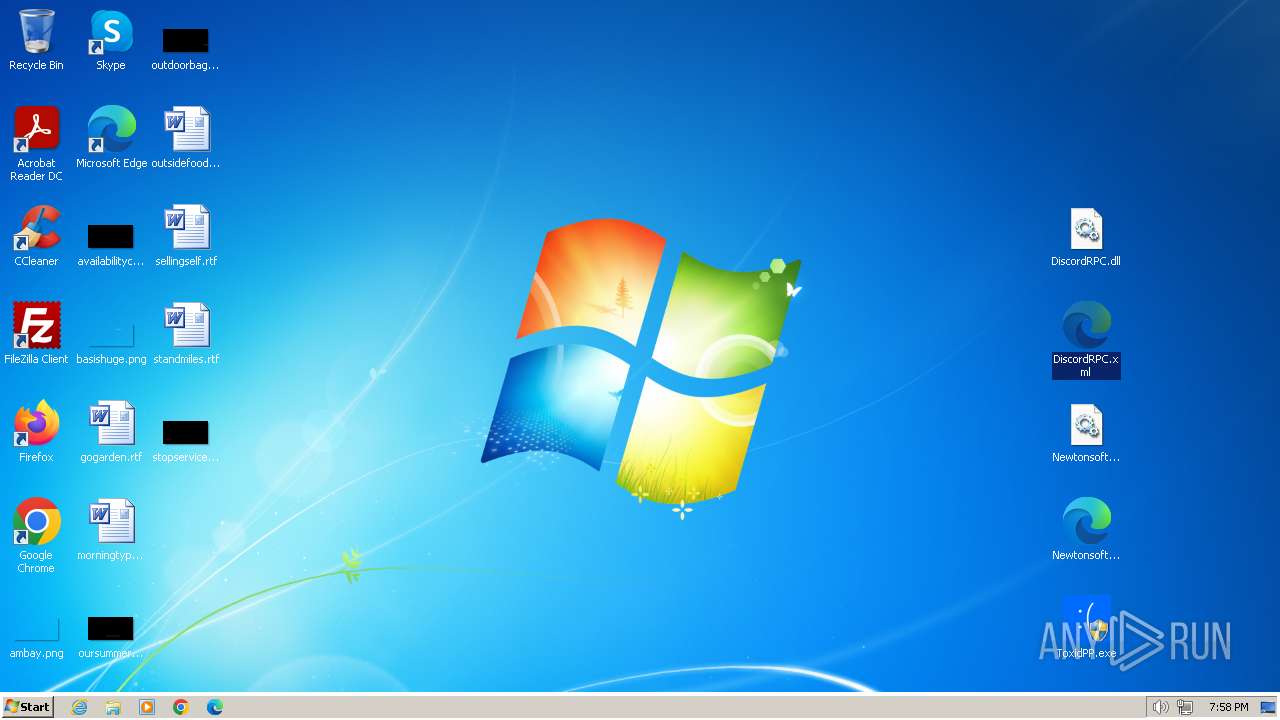
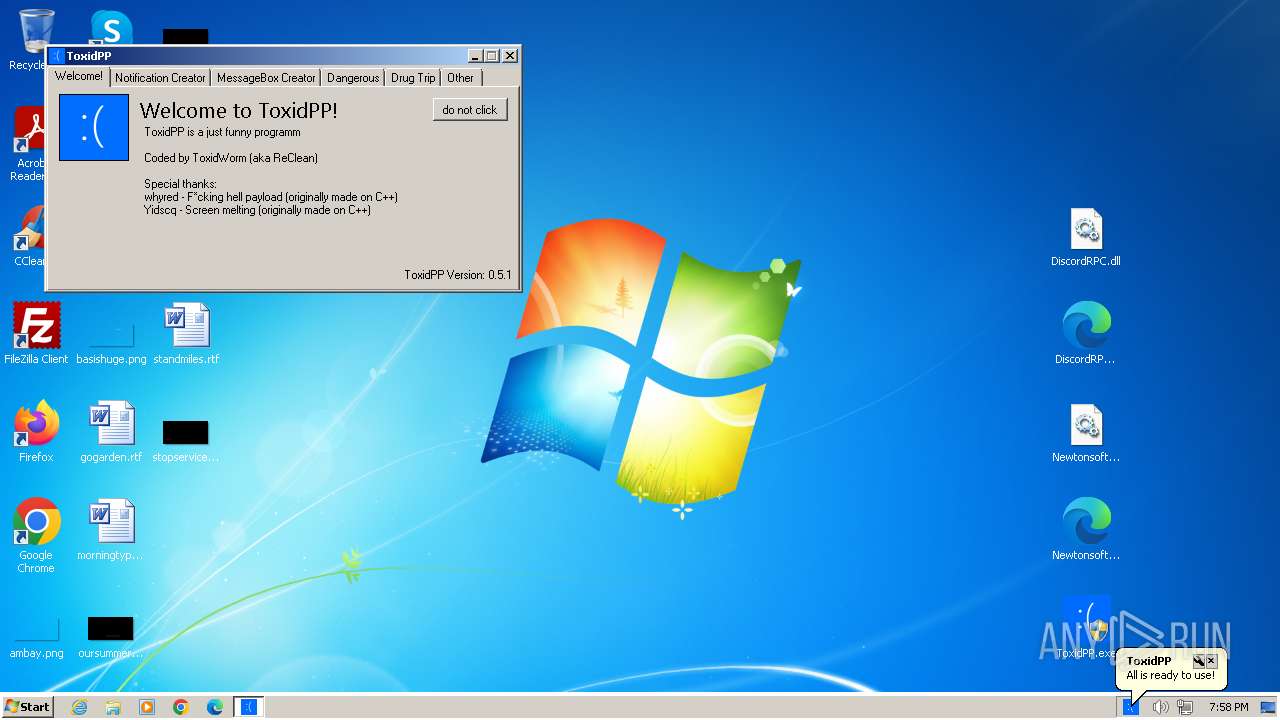
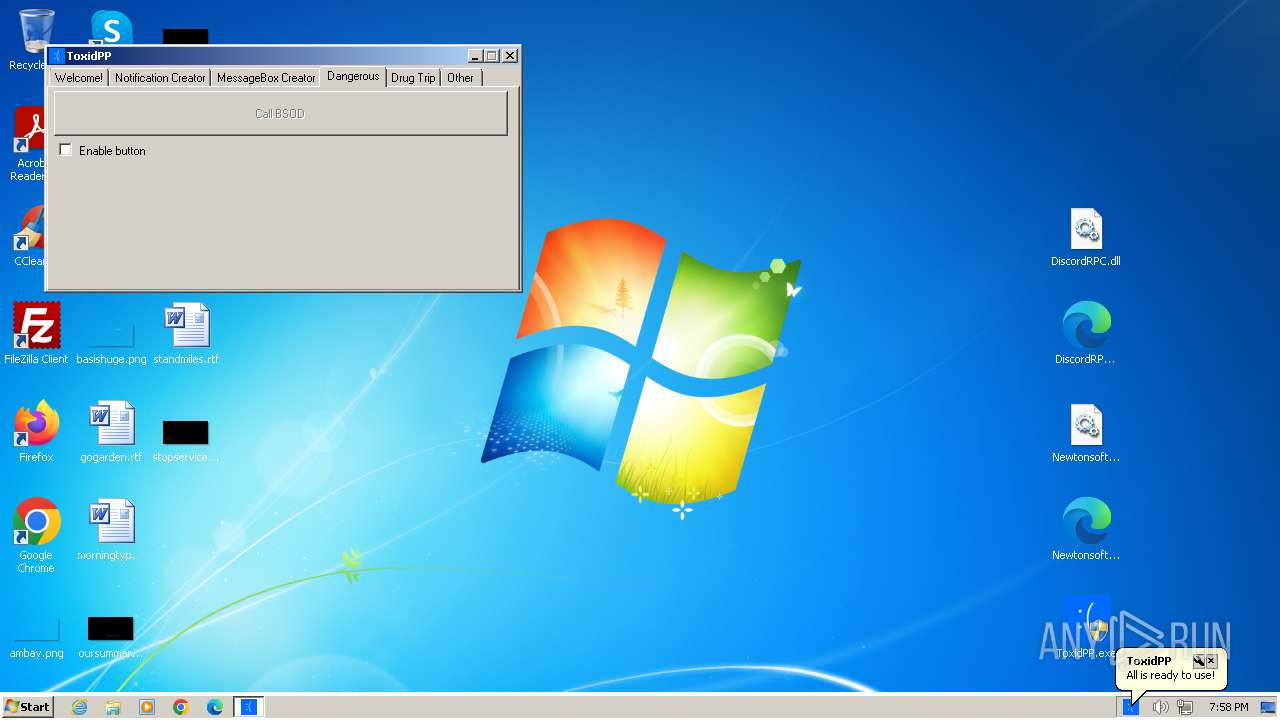
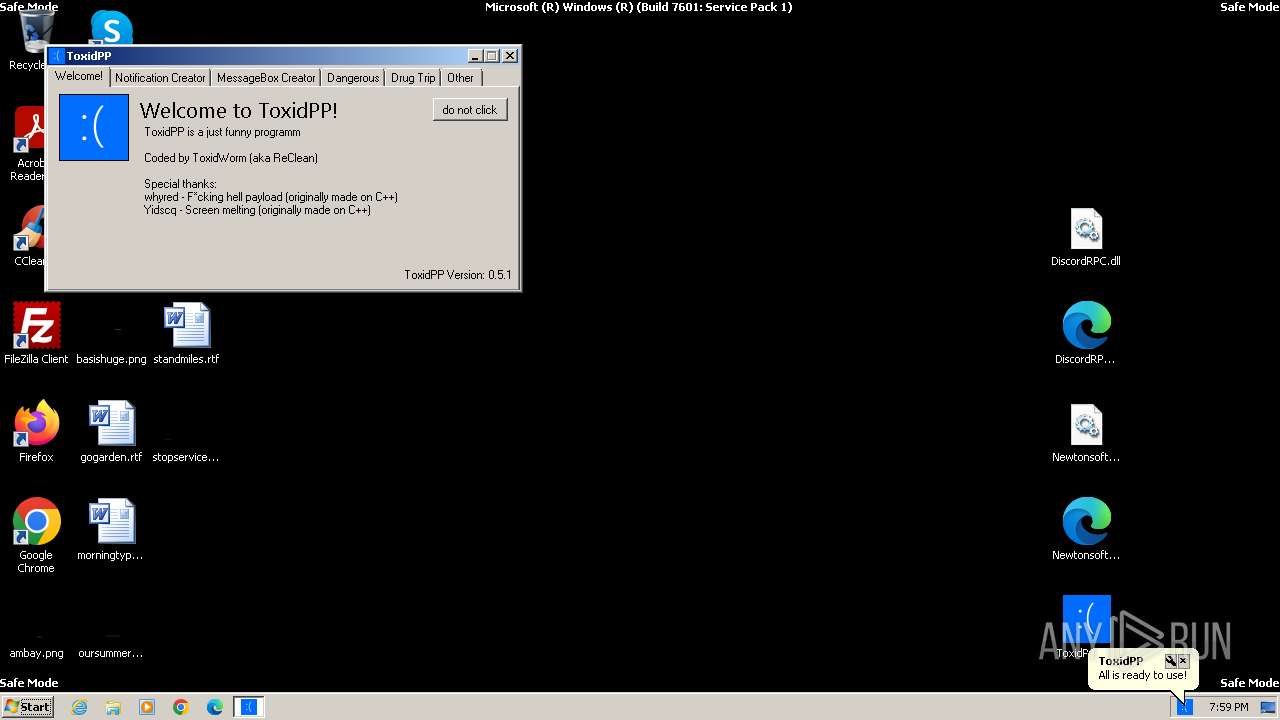
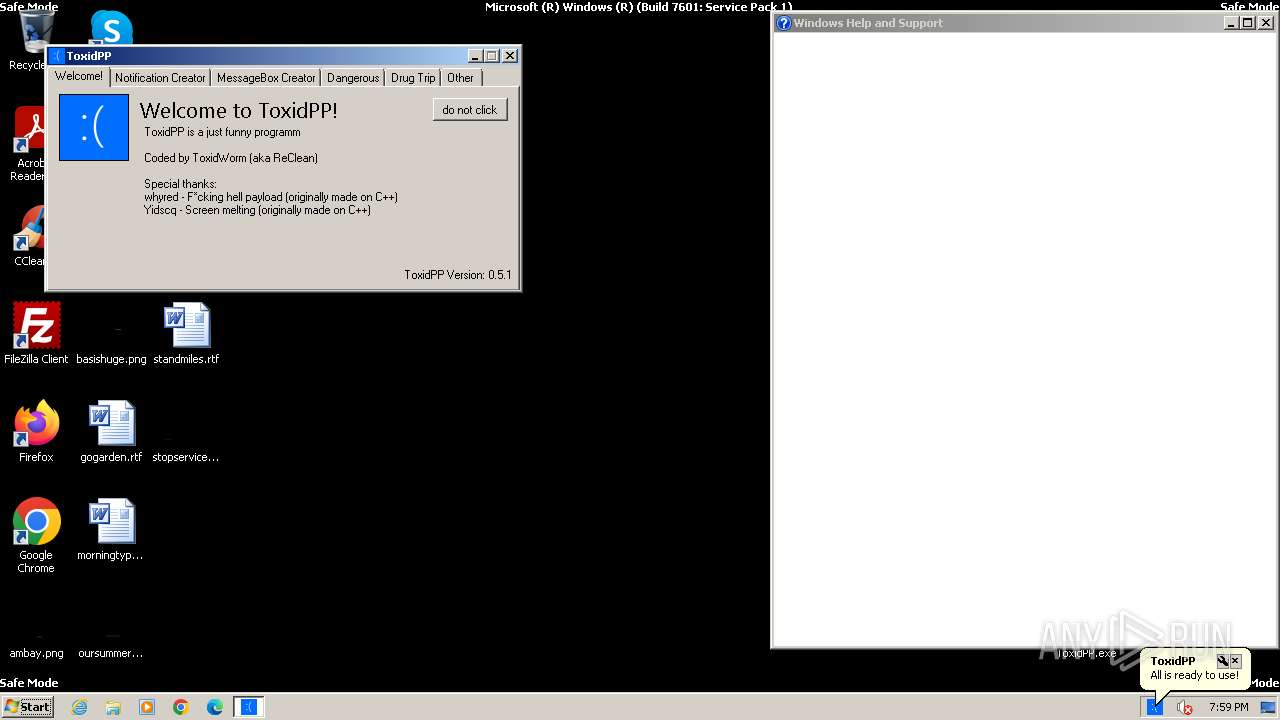
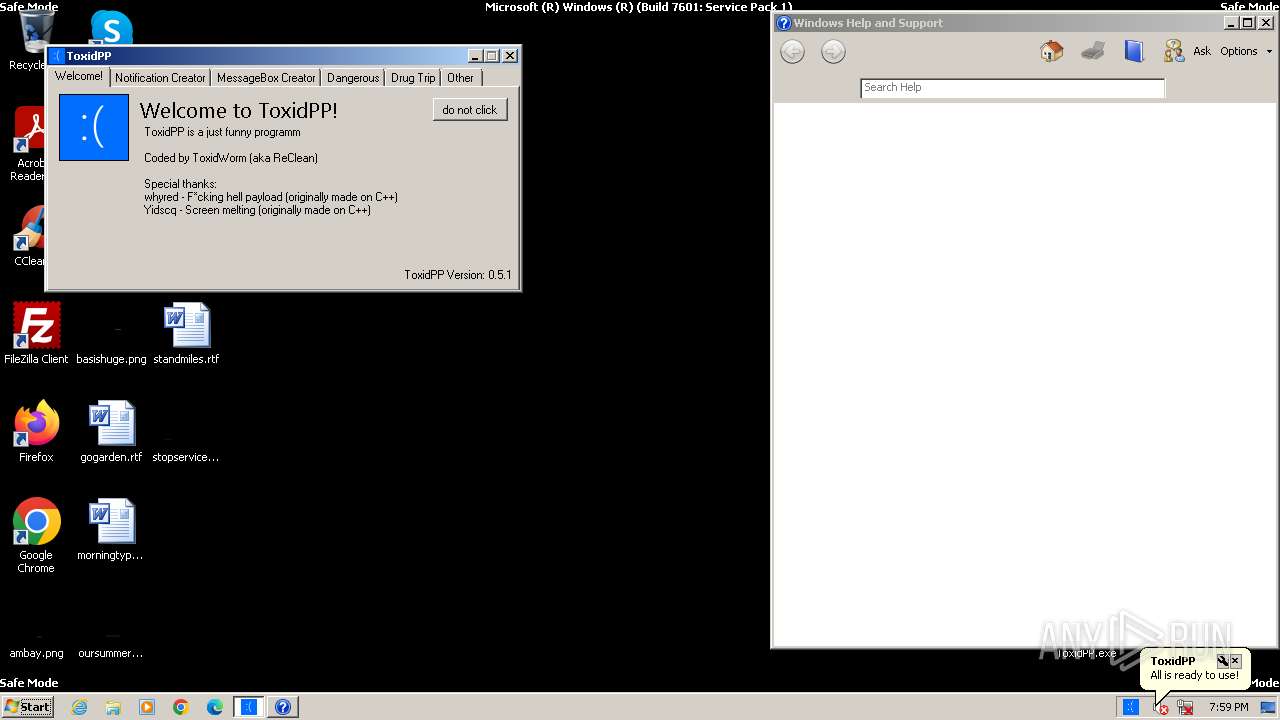
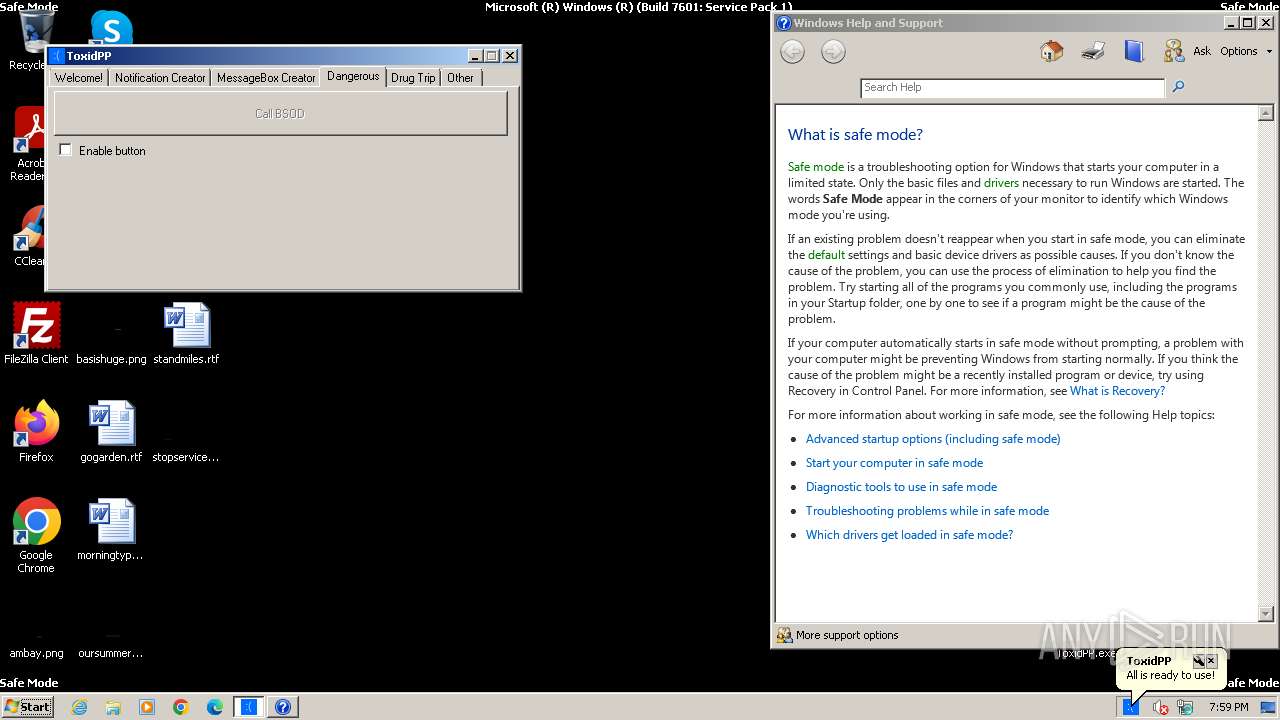
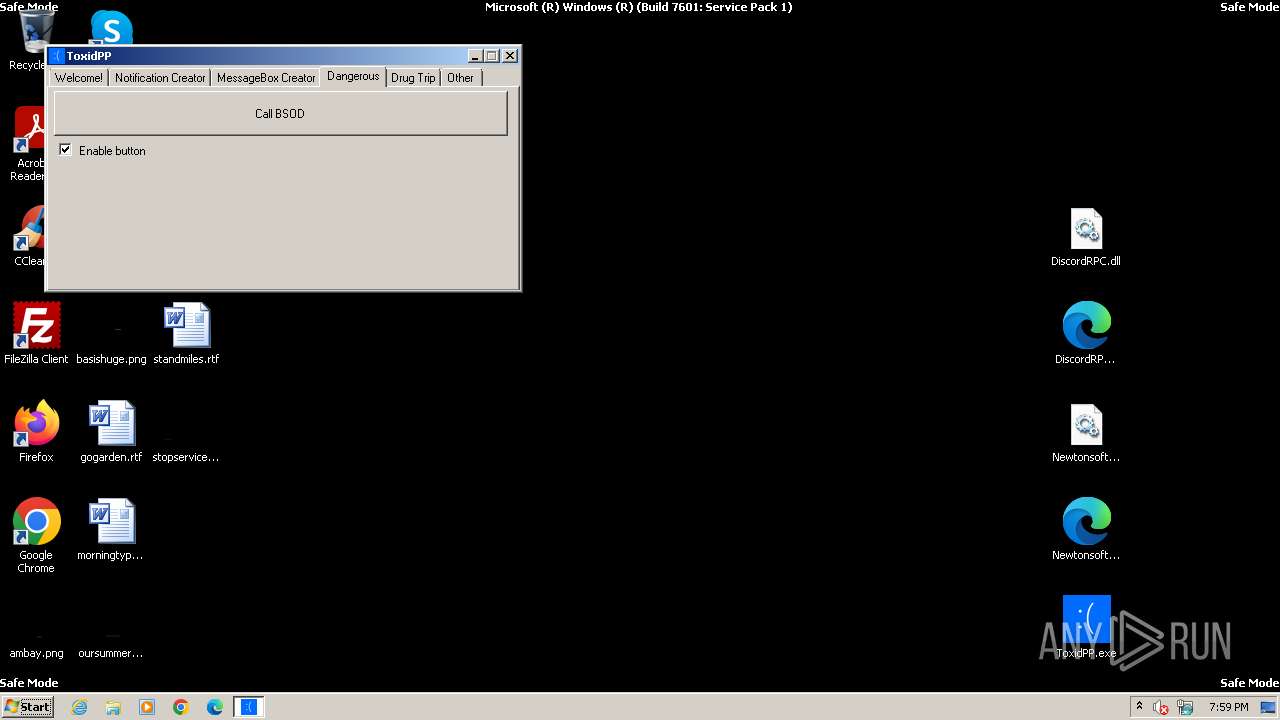
- ToxidPP.exe (PID: 3392)
- ToxidPP.exe (PID: 2364)
- runonce.exe (PID: 1332)
- IMEKLMG.EXE (PID: 2088)
- IMEKLMG.EXE (PID: 2100)
- ToxidPP.exe (PID: 2332)
- ToxidPP.exe (PID: 2448)
- wmpnscfg.exe (PID: 2560)
- wmpnscfg.exe (PID: 2764)
- msedge.exe (PID: 2884)
- pwsh.exe (PID: 3572)
- ToxidPP.exe (PID: 3936)
- ToxidPP.exe (PID: 4044)
- wmpnscfg.exe (PID: 2580)
Checks supported languages
- ToxidPP.exe (PID: 2364)
- IMEKLMG.EXE (PID: 2100)
- IMEKLMG.EXE (PID: 2088)
- ToxidPP.exe (PID: 2448)
- wmpnscfg.exe (PID: 2560)
- wmpnscfg.exe (PID: 2764)
- pwsh.exe (PID: 3572)
- ToxidPP.exe (PID: 4044)
- wmpnscfg.exe (PID: 2580)
Reads the machine GUID from the registry
- ToxidPP.exe (PID: 2364)
- ToxidPP.exe (PID: 2448)
- ToxidPP.exe (PID: 4044)
Reads the computer name
- ToxidPP.exe (PID: 2364)
- IMEKLMG.EXE (PID: 2100)
- IMEKLMG.EXE (PID: 2088)
- ToxidPP.exe (PID: 2448)
- wmpnscfg.exe (PID: 2764)
- pwsh.exe (PID: 3572)
- ToxidPP.exe (PID: 4044)
- wmpnscfg.exe (PID: 2560)
- wmpnscfg.exe (PID: 2580)
Reads the time zone
- runonce.exe (PID: 1332)
Reads security settings of Internet Explorer
- runonce.exe (PID: 1332)
- sipnotify.exe (PID: 1964)
Create files in a temporary directory
- WerFault.exe (PID: 128)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2100)
- IMEKLMG.EXE (PID: 2088)
Reads the software policy settings
- sipnotify.exe (PID: 1964)
Application launched itself
- msedge.exe (PID: 2884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:22 00:57:26 |
| ZipCRC: | 0xbd216e97 |
| ZipCompressedSize: | 49259 |
| ZipUncompressedSize: | 701978 |
| ZipFileName: | Newtonsoft.Json.xml |
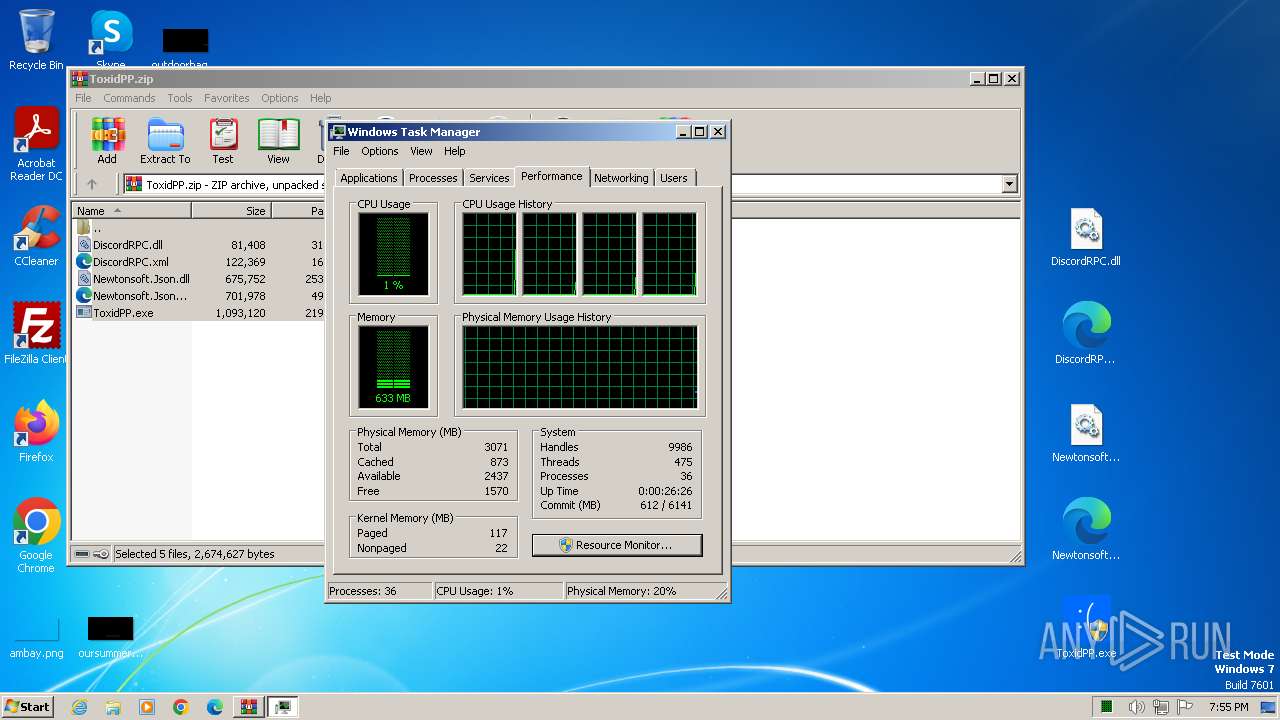
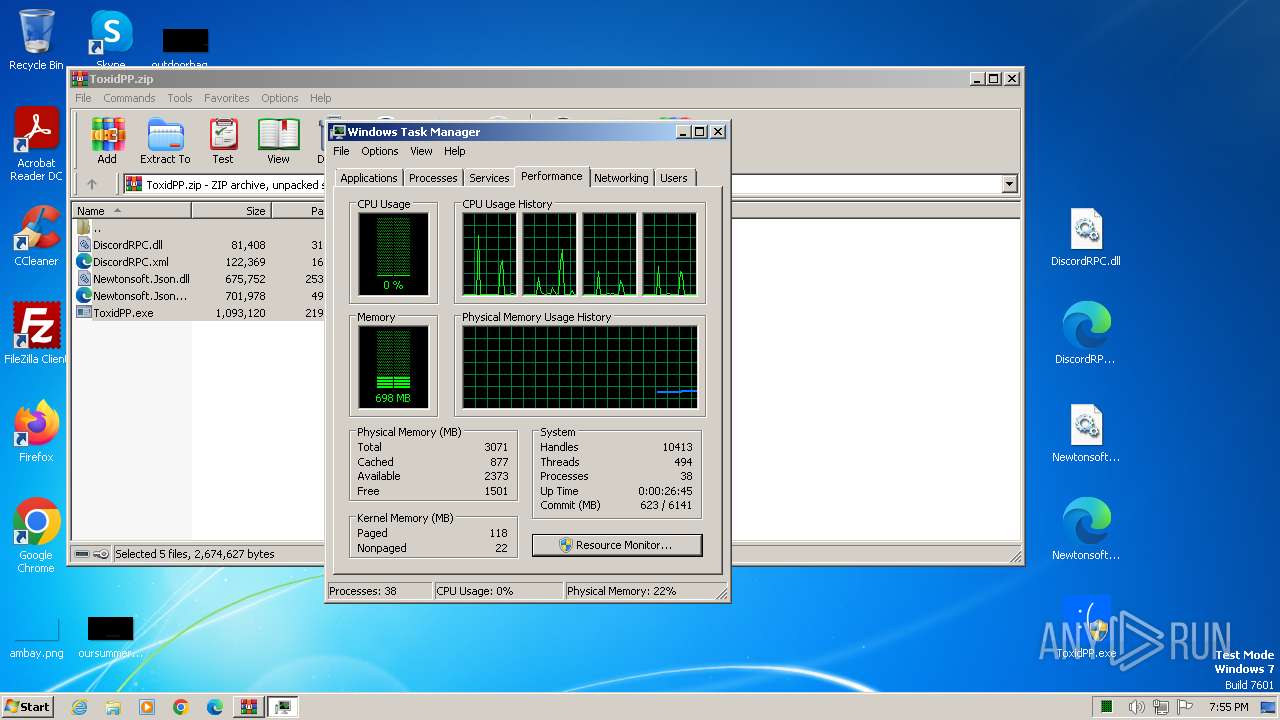
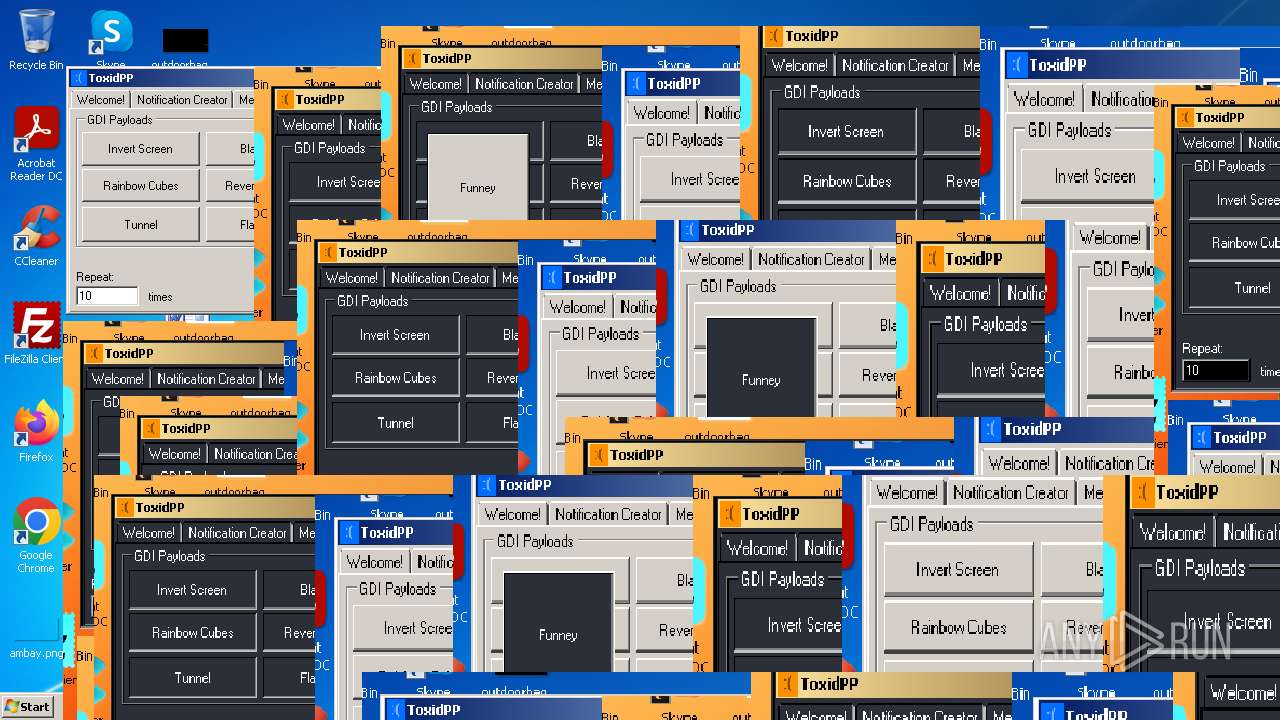
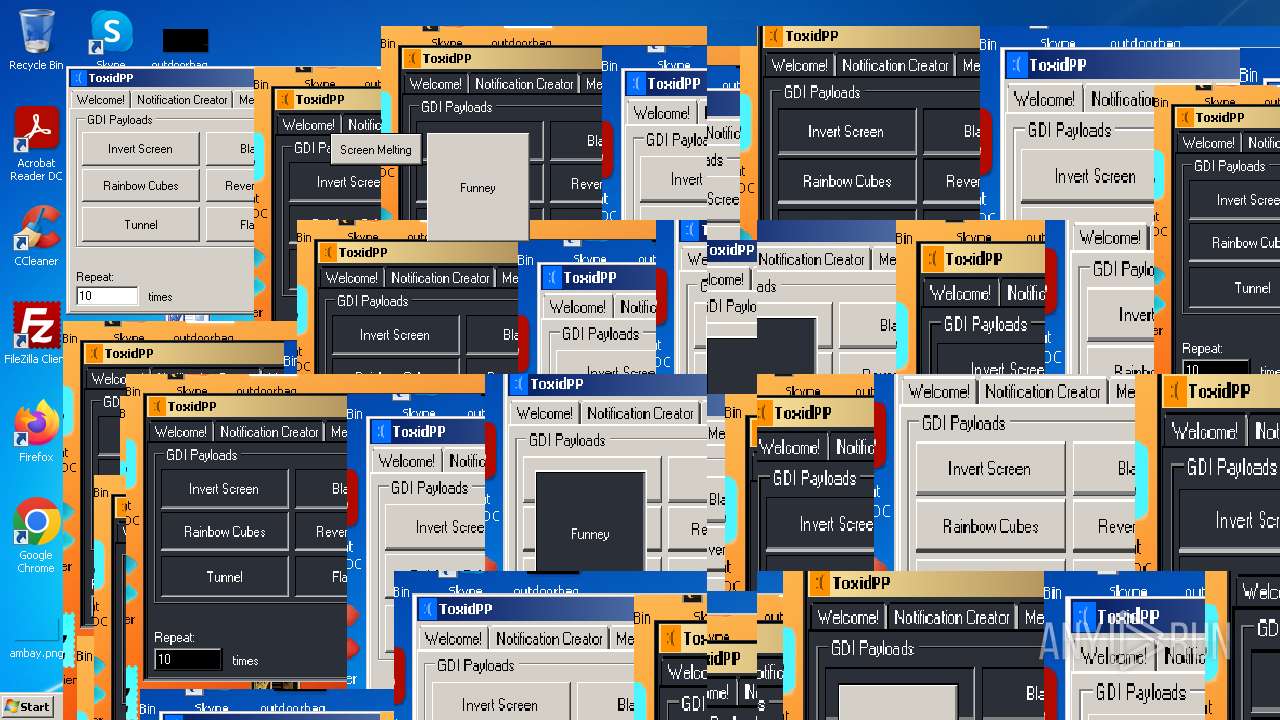
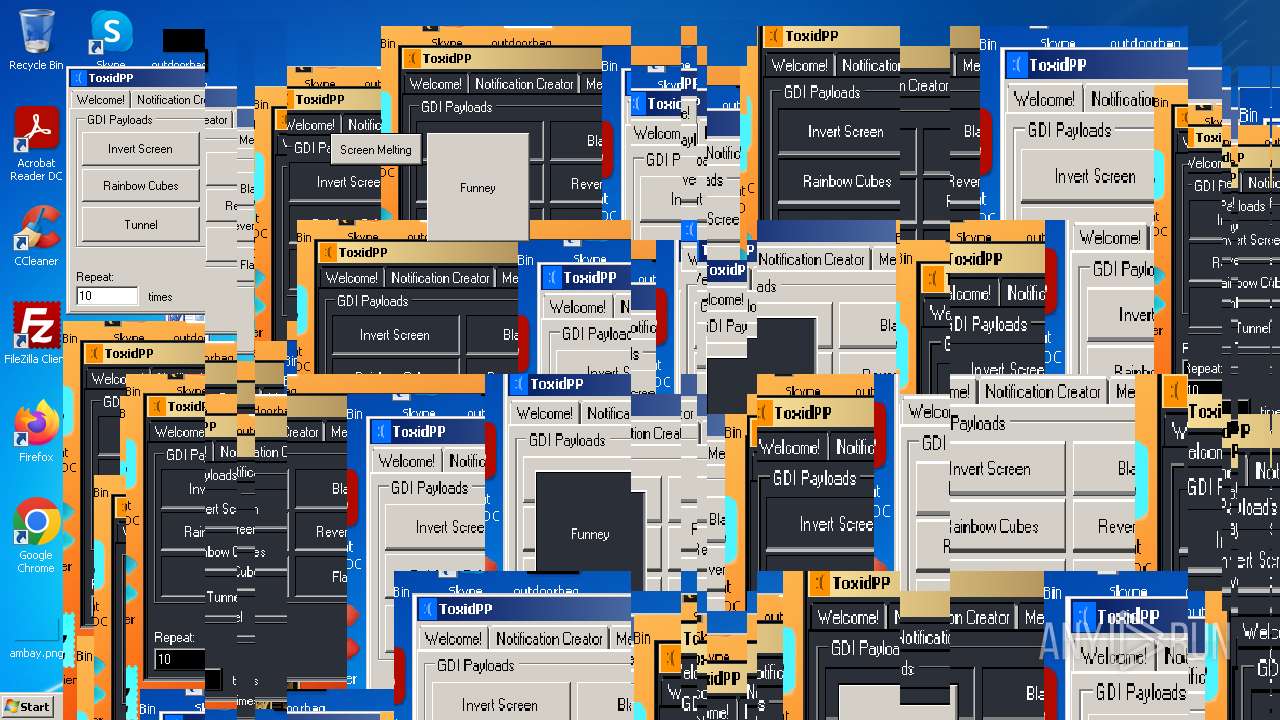
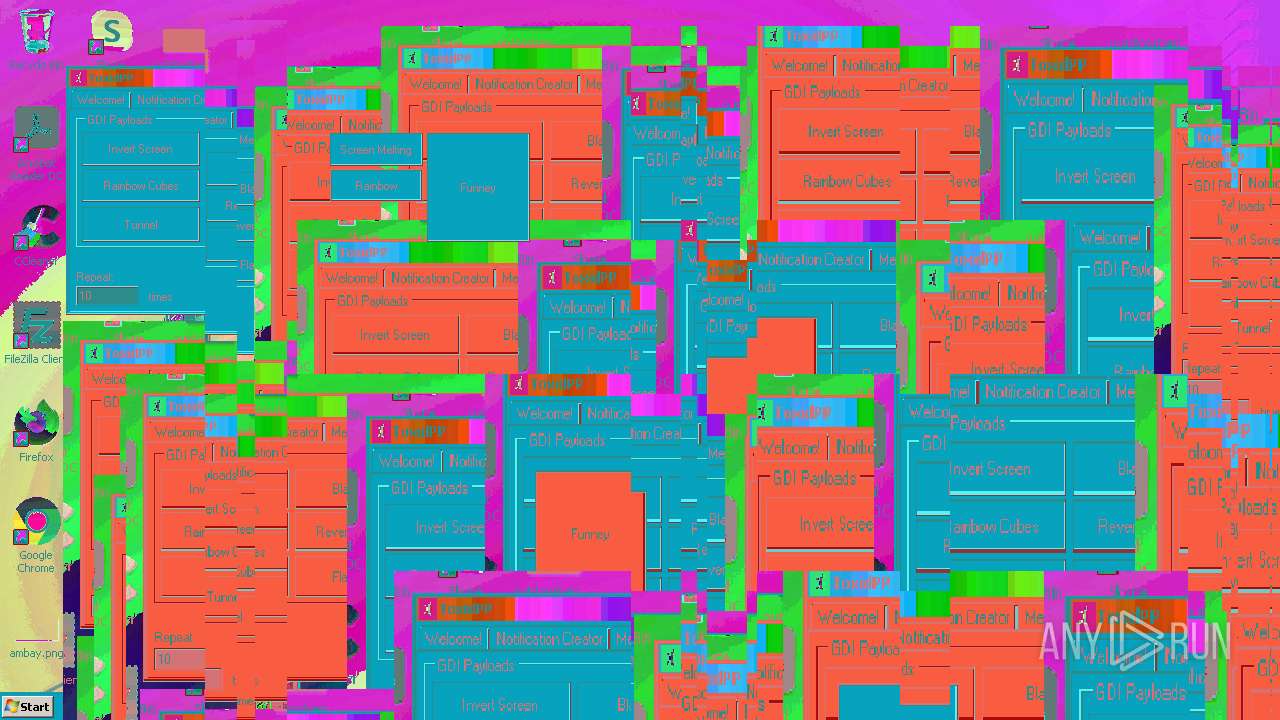
Total processes
125
Monitored processes
35
Malicious processes
1
Suspicious processes
0
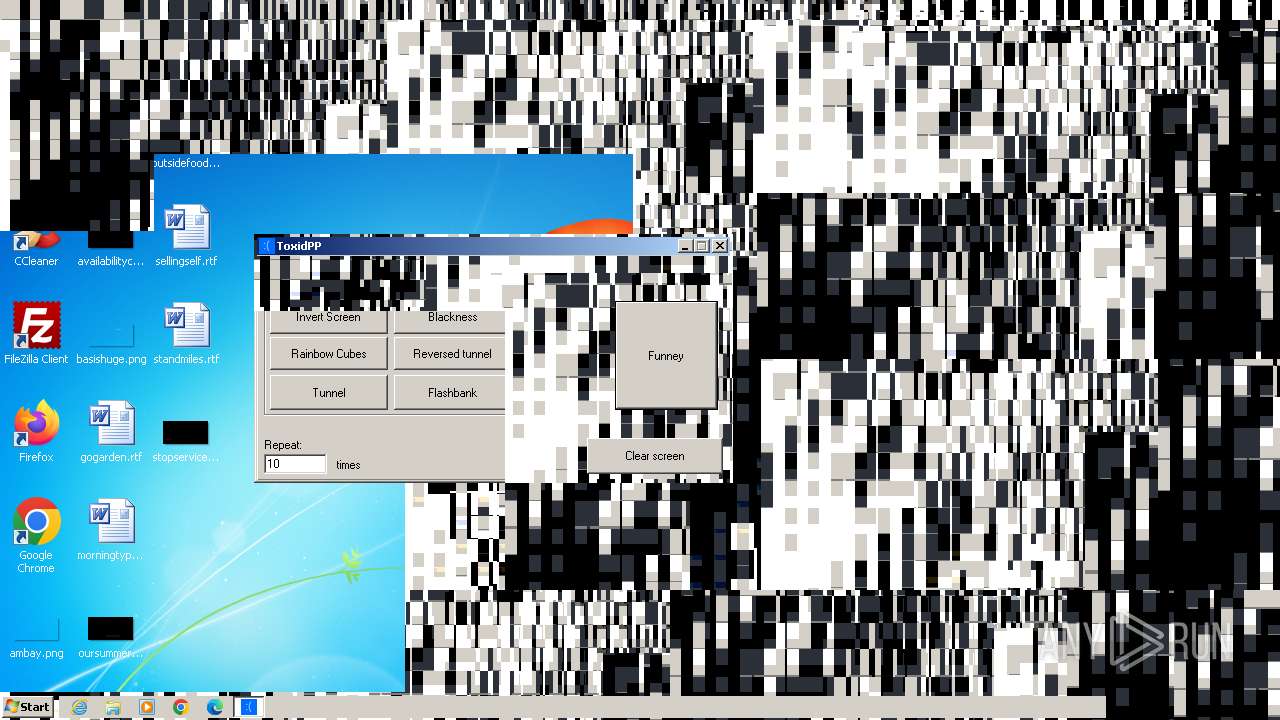
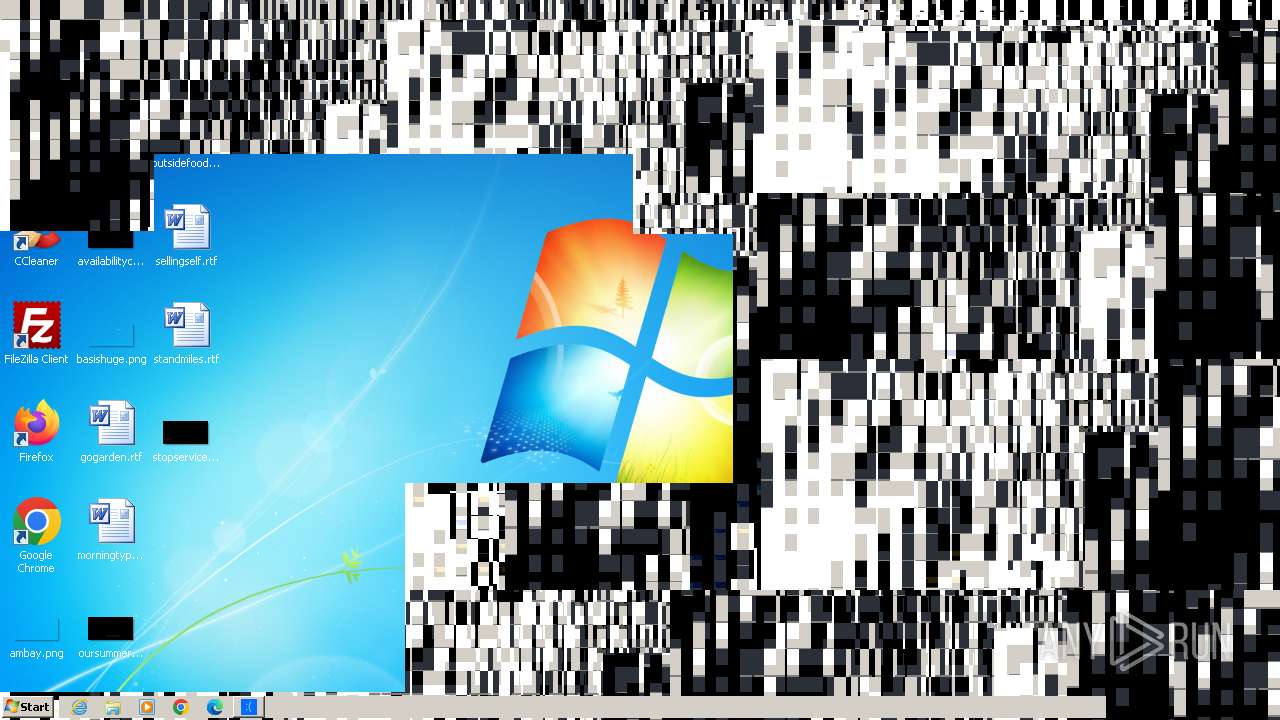
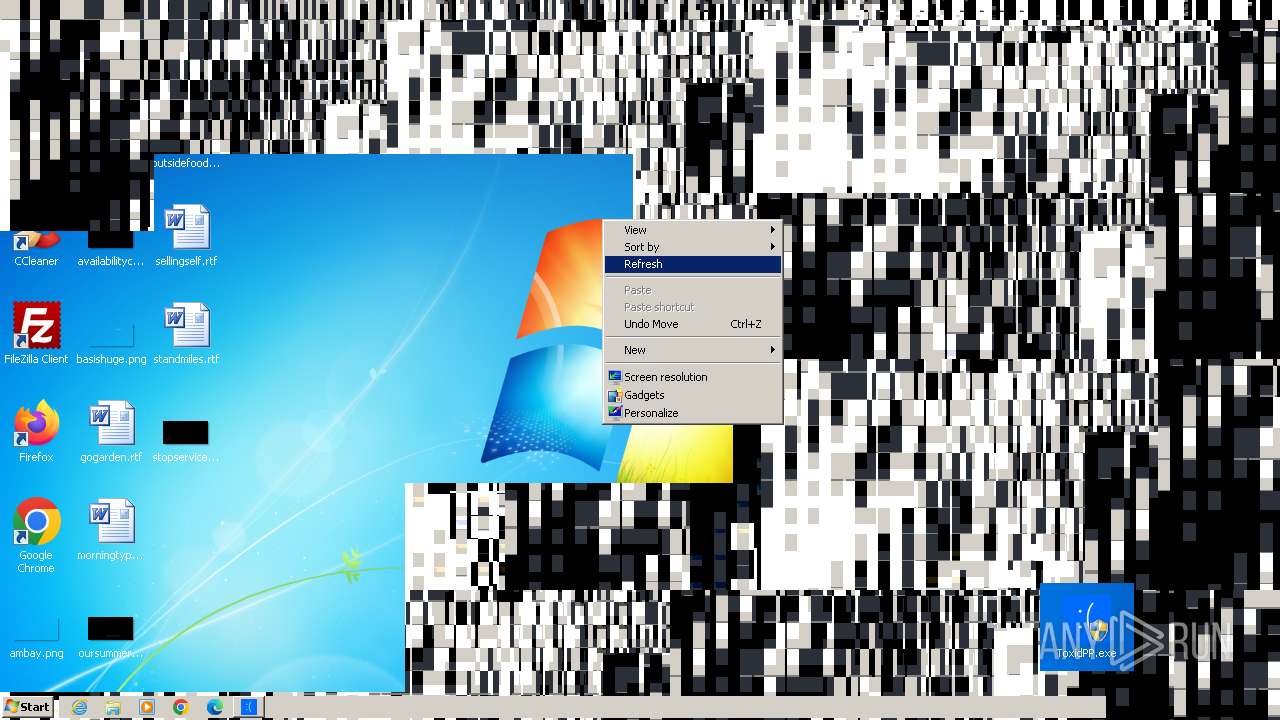
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | C:\Windows\System32\WerFault.exe -k -q | C:\Windows\System32\WerFault.exe | — | WerFault.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | runonce.exe /Explorer | C:\Windows\System32\runonce.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Windows\System32\WerFault.exe" -k -rq | C:\Windows\System32\WerFault.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1492 | "C:\Windows\System32\control.exe" SYSTEM | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1964 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\Desktop\ToxidPP.exe" | C:\Users\admin\Desktop\ToxidPP.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ToxidPP Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\Desktop\ToxidPP.exe" | C:\Users\admin\Desktop\ToxidPP.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ToxidPP Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
19 551
Read events
19 370
Write events
156
Delete events
25
Modification events
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\ToxidPP.zip | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
3
Suspicious files
56
Text files
54
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 128 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\Kernel_0_0_cab_0080689d\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3668.48558\ToxidPP.exe | executable | |
MD5:DFC559E2A5994DBCB4CCFE080FC28CAF | SHA256:9DBAB7AF2FC3FEB7CF356F055A67469212655ED65613FA854AF16BF4DAEDA244 | |||
| 3668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3668.48558\Newtonsoft.Json.dll | executable | |
MD5:4DF6C8781E70C3A4912B5BE796E6D337 | SHA256:3598CCCAD5B535FEA6F93662107A4183BFD6167BF1D0F80260436093EDC2E3AF | |||
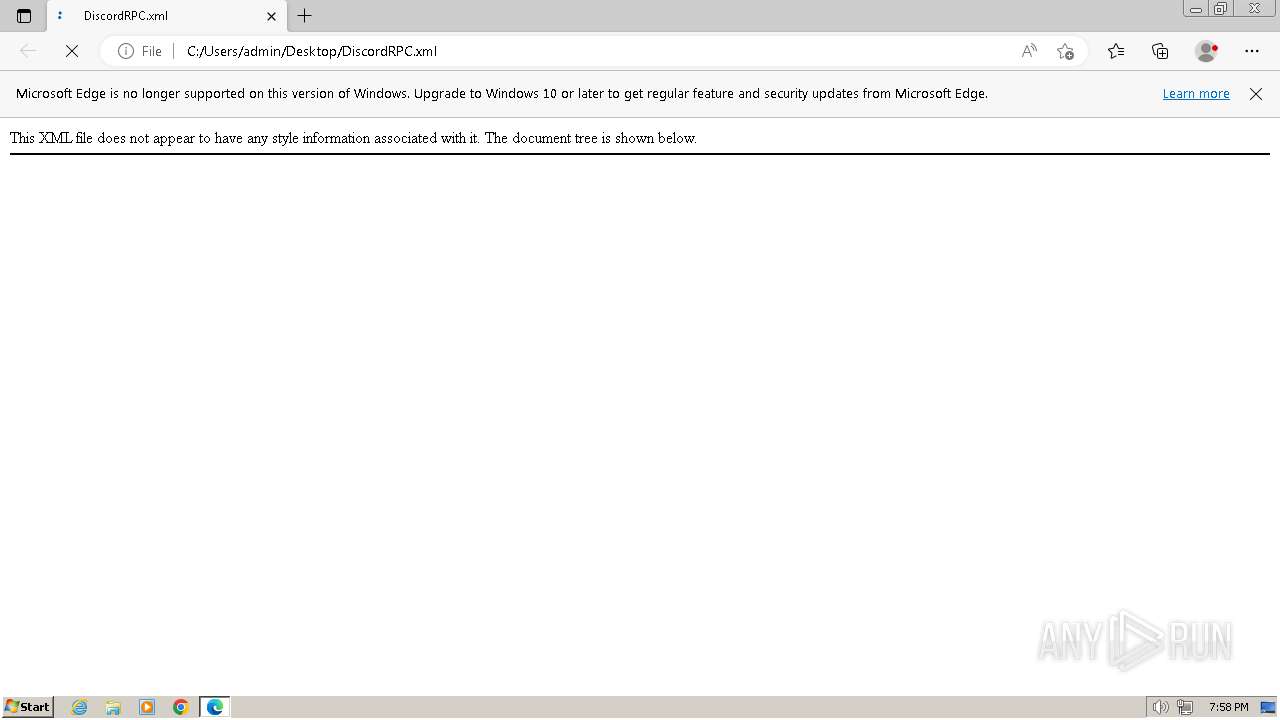
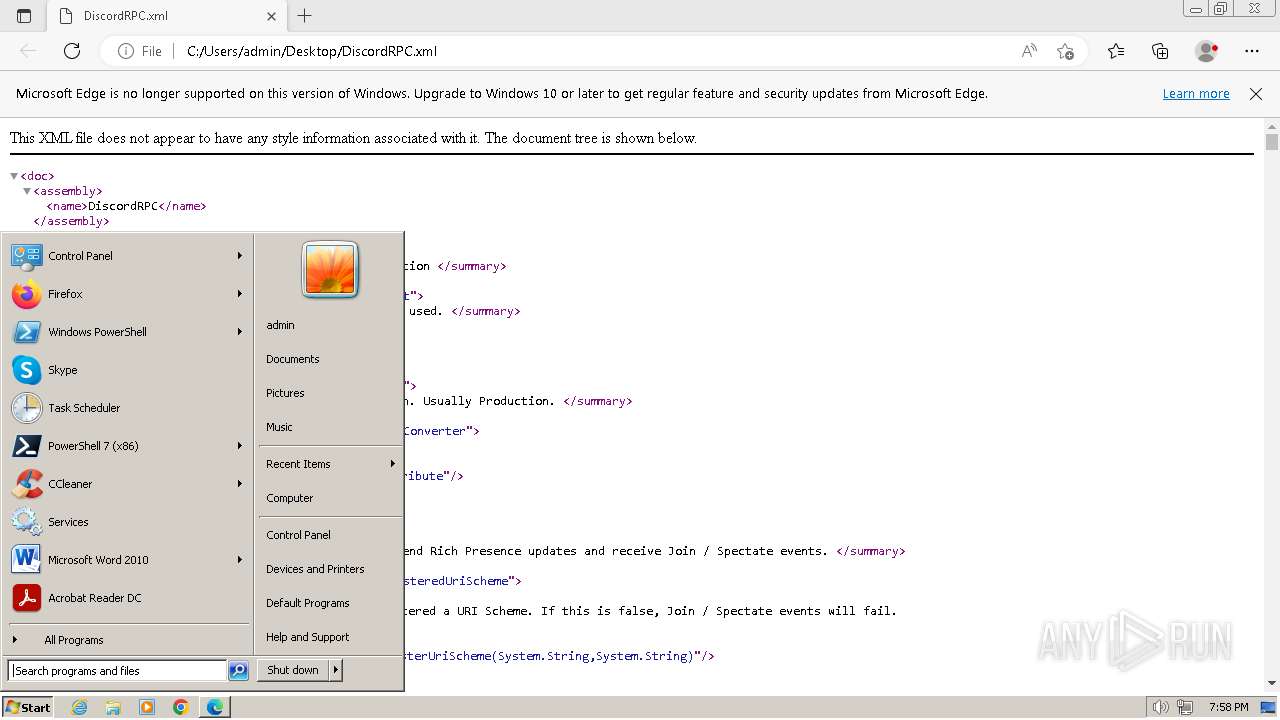
| 3668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3668.48558\DiscordRPC.dll | executable | |
MD5:AD463F573775C43A561ADE842C41B0E8 | SHA256:6A18DFC8BDC6030787B5814C76B8663DBE5B8CA469BEB65A2CA9F5731FA1906F | |||
| 1964 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\metadata.json | binary | |
MD5:E8A970BA6CE386EED9A5E724F26212A6 | SHA256:7E06107D585D8FC7870998F3856DCC3E35800AA97E4406AAB83BC8444B6CBDE3 | |||
| 3668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3668.48558\Newtonsoft.Json.xml | xml | |
MD5:ED67AC96769018255050AC0829CA459A | SHA256:F32ED922FE5B22DD693E160AEE4F0DCAB753EBD740BED40490AE4179274B4B49 | |||
| 1964 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\styles.css | text | |
MD5:3383EEF350240253D7C2C2564381B3CB | SHA256:85443493D86D6D7FB0E07BC9705DFC9C858086FBA1B0E508092AB328D5F145E8 | |||
| 128 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER67F2.tmp.cab.tmp | binary | |
MD5:CD3792869B1CC42322EF474AC58C3A6B | SHA256:1C49B640B7A90D8D553CB2BAB4DE4758970D59AFA9D7E42B01356635B82C9D5A | |||
| 128 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER6806.tmp.cab.tmp | binary | |
MD5:8BA028678E2B812B0A124ADC1BAB3ECE | SHA256:9C43C0DF390C39D64F1E5E8E9E032029A634F0B5CE12B24DE2D20A38BF8A0CEC | |||
| 1964 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\script.js | text | |
MD5:A2682382967C351F7ED21762F9E5DE9E | SHA256:36B1D26F1EC69685648C0528C2FCE95A3C2DBECF828CDFA4A8B4239A15B644A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1964 | sipnotify.exe | HEAD | 200 | 88.221.61.151:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133519822219530000 | unknown | — | — | unknown |
1416 | svchost.exe | GET | 304 | 2.18.79.74:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d0eff84f2cec524b | unknown | — | — | unknown |
1112 | svchost.exe | GET | 304 | 2.18.79.82:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b898204f02a9350b | unknown | — | — | unknown |
1416 | svchost.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | binary | 814 b | unknown |
1416 | svchost.exe | GET | 200 | 2.18.79.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | binary | 1.01 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1112 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1964 | sipnotify.exe | 88.221.61.151:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | DE | unknown |
1416 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1416 | svchost.exe | 2.18.79.74:80 | ctldl.windowsupdate.com | Akamai International B.V. | AT | unknown |
1416 | svchost.exe | 2.18.79.138:80 | crl.microsoft.com | Akamai International B.V. | AT | unknown |
1416 | svchost.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
3080 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
aka.ms |
| whitelisted |