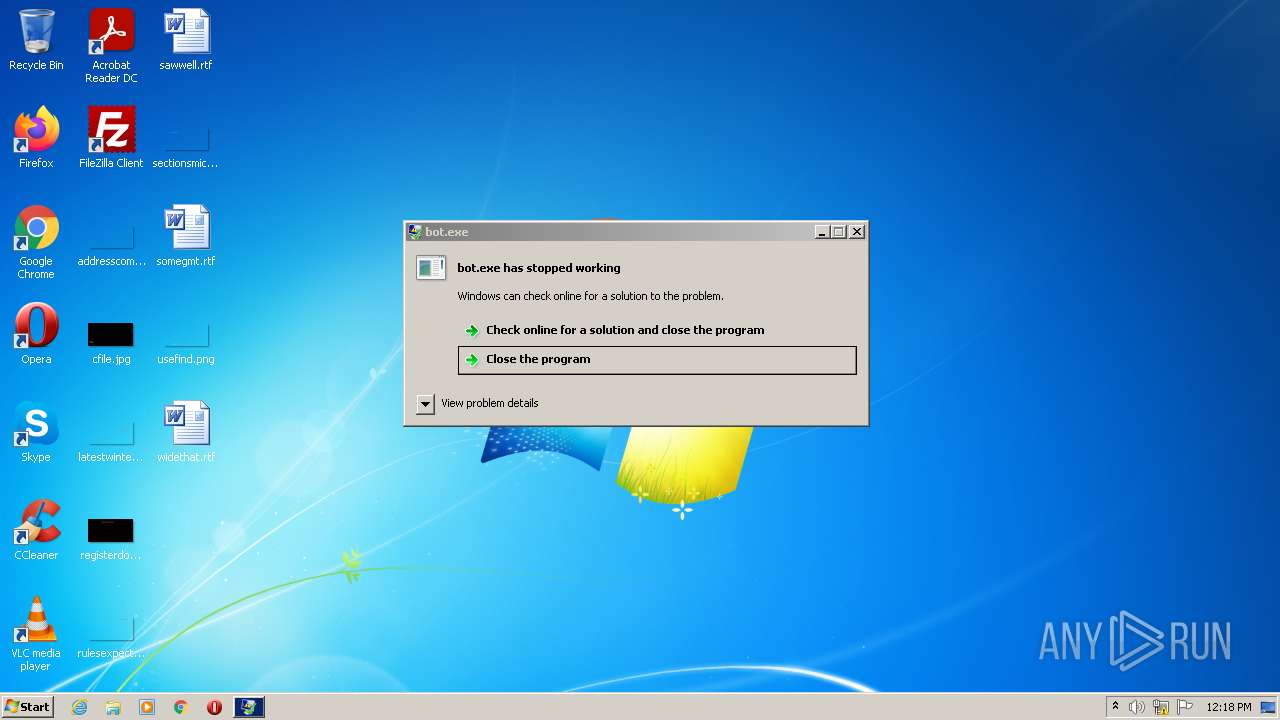
| File name: | bot.exe |
| Full analysis: | https://app.any.run/tasks/0674a4f0-cec4-4402-8c3b-4b219f22e807 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 27, 2022, 11:17:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3AC80DEE855E85C52C0170373AF79A04 |
| SHA1: | 79B6A5708B05B88847B605DFE5271073826BA5F4 |
| SHA256: | 52338ADD561F1E396B0F8377E77BAE2A05BCB8D7CC19548DBF9FF8CF0B57CC1F |
| SSDEEP: | 3072:WfUomEuYm98dlSq7gt5q7Dx+XgS6aCEwhOfUbCalNT2pbB3fIC1Xi6FLPo3c:WfUauY68uSWCx+XA7mg2pNr1Ljo3c |
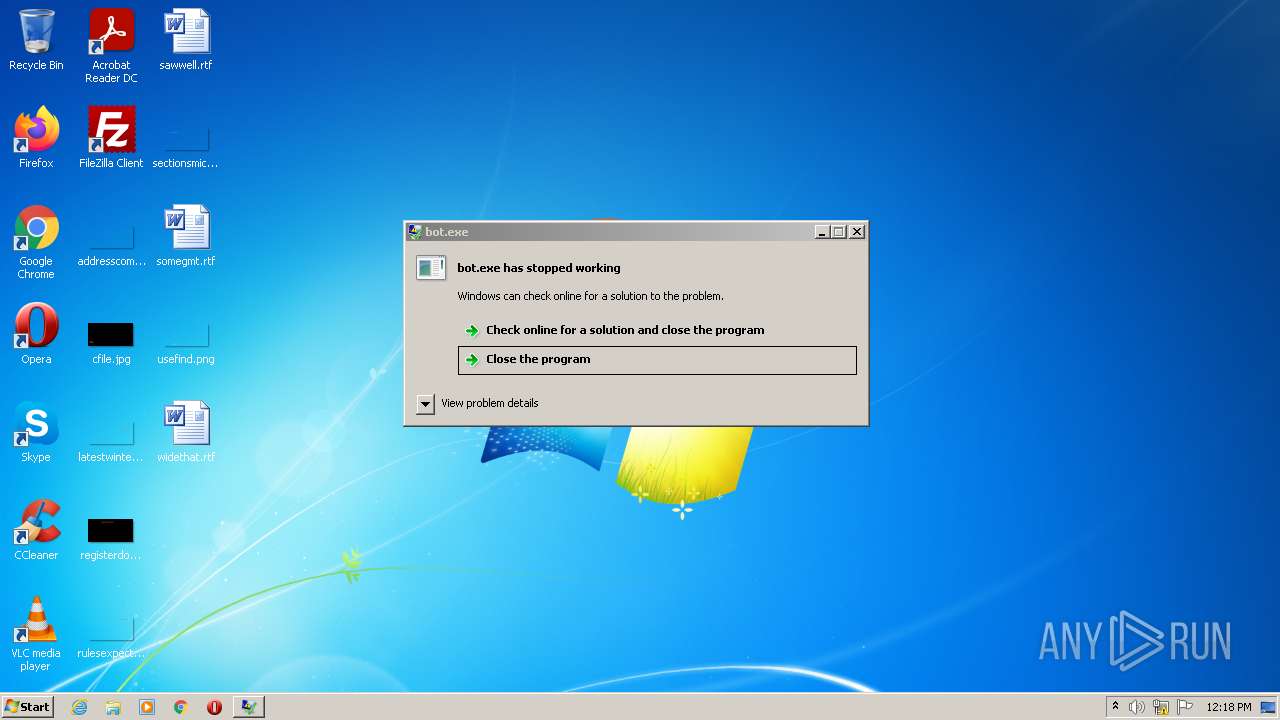
MALICIOUS
OSKI detected by memory dumps
- bot.exe (PID: 1036)
VIDAR was detected
- bot.exe (PID: 1036)
SUSPICIOUS
Reads the computer name
- bot.exe (PID: 1036)
Checks supported languages
- bot.exe (PID: 1036)
Reads the cookies of Google Chrome
- bot.exe (PID: 1036)
Creates files in the program directory
- bot.exe (PID: 1036)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
oski
(PID) Process(1036) bot.exe
C262.77.159.212
RC4 Key056139954853430408
ID1BEF0A57BE110FD467A
other (204)w
system.txt
System ---------------------------------------------------
Windows: %s
Bit: %s
User: %s
Computer Name: %s
System Language: %s
Machine ID: %s
GUID: %s
Domain Name: %s
Workgroup: %s
Keyboard Languages: %s
Hardware -------------------------------------------------
Processor: %s
Logical processors: %d
Videocard: %s
Display: %s
RAM: %s
Laptop: %s
Time -----------------------------------------------------
Local: %s
Zone: %s
Network --------------------------------------------------
IP: IP?
Country: Country?
Installed Softwrare --------------------------------------
%s\\*
.
%s\\%s
%s
C:\\ProgramData\\
.exe
:Zone.Identifier
[ZoneTransfer] ZoneId=2
%s/1.jpg
%s/2.jpg
%s/3.jpg
%s/4.jpg
%s/5.jpg
%s/6.jpg
%s/7.jpg
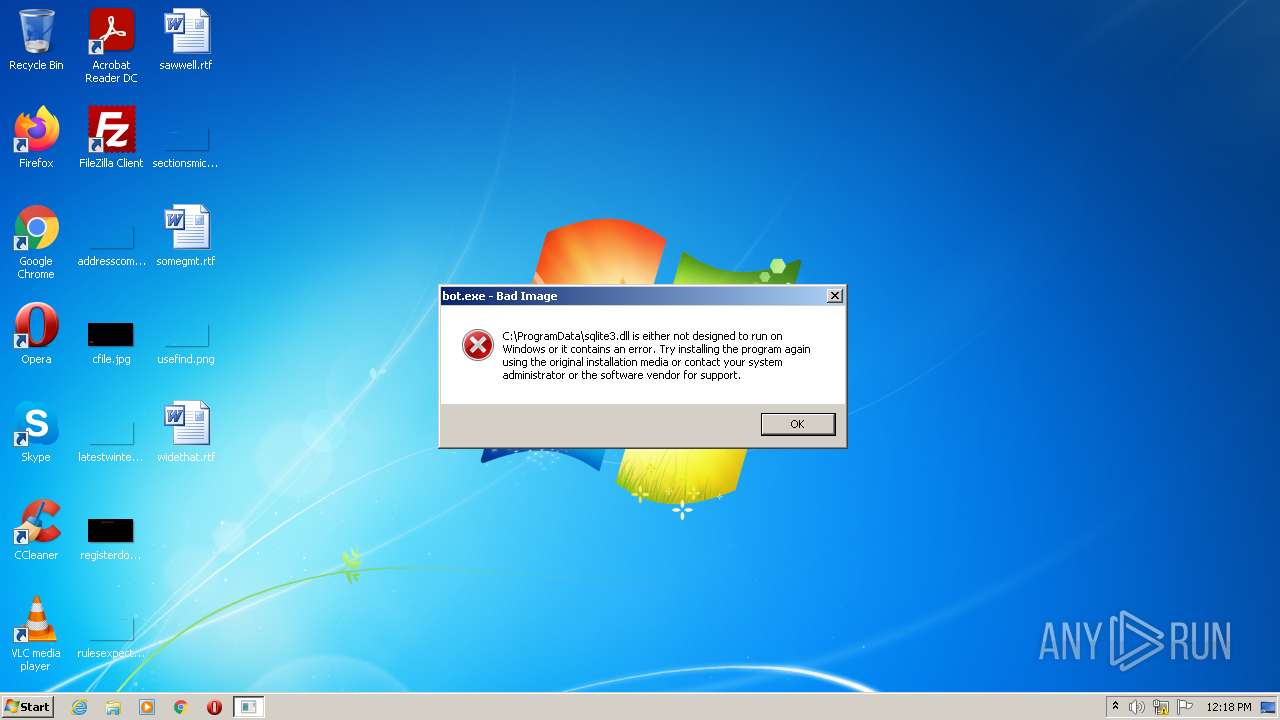
C:\\ProgramData\\sqlite3.dll
C:\\ProgramData\\freebl3.dll
C:\\ProgramData\\mozglue.dll
C:\\ProgramData\\msvcp140.dll
C:\\ProgramData\\nss3.dll
C:\\ProgramData\\softokn3.dll
C:\\ProgramData\\vcruntime140.dll
_%s.zip
\\cookies
\\autofill
\\cc
file
%s/main.php
APPDATA
LOCALAPPDATA
USERPROFILE
JohnDoe
HAL9TH
sqlite3.dll
sqlite3_open
sqlite3_prepare_v2
sqlite3_step
sqlite3_column_text
sqlite3_finalize
sqlite3_close
sqlite3_column_bytes
sqlite3_column_blob
\"os_crypt\":{\"encrypted_key\":\"
\"}
PATH
PATH=
NSS_Init
NSS_Shutdown
PK11_GetInternalKeySlot
PK11_FreeSlot
PK11_Authenticate
PK11SDR_Decrypt
vaultcli.dll
VaultOpenVault
VaultCloseVault
VaultEnumerateItems
VaultGetItem
VaultFree
passwords.txt
a+
r
PROF: UNK
PROF: %s
SOFT: %s
HOST: %s
USER: %s
PASS:
PASS: %s
%s\\Mozilla\\Firefox\\profiles.ini
\\logins.json
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
guid
\\temp
cookies\\%s_%s.txt
%s %s %s %s %s %s %s
CARD: %s NAME: %s DATE: %s/%s
cc\\%s_%s.txt
autofill\\%s_%s.txt
%s %s
SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies
SELECT origin_url, username_value, password_value FROM logins
SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies
SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards
SELECT fieldname, value FROM moz_formhistory
SELECT name, value FROM autofill
TRUE
FALSE
..\\profiles.ini
%s\\*
\\Local State
Login Data
Cookies
Web Data
cookies.sqlite
logins.json
formhistory.sqlite
\\Opera Software\\Opera Stable\\
Opera
\\Google\\Chrome\\User Data
Google Chrome
\\Chromium\\User Data
Chromium
\\Kometa\\User Data
Kometa
\\Amigo\\User Data
Amigo
\\Torch\\User Data
Torch
\\Orbitum\\User Data
Orbitum
\\Comodo\\Dragon\\User Data
Comodo Dragon
\\Nichrome\\User Data
Nichrome
\\Maxthon5\\Users
Maxthon5
\\Sputnik\\User Data
Sputnik
\\Epic Privacy Browser\\User Data
EPB
\\Vivaldi\\User Data
Vivaldi
\\CocCoc\\Browser\\User Data
CocCoc Browser
\\uCozMedia\\Uran\\User Data
Uran Browser
\\QIP Surf\\User Data
QIP Surf
\\CentBrowser\\User Data
Cent
\\Elements Browser\\User Data
Elements Browser
\\TorBro\\Profile
TorBro
\\CryptoTab Browser\\User Data
CryptoTab
\\BraveSoftware\\Brave-Browser\\User Data
Brave
\\Mozilla\\Firefox\\Profiles\\
Mozilla Firefox
\\Moonchild Productions\\Pale Moon\\Profiles\\
Pale Moon
\\Waterfox\\Profiles\\
Waterfox
\\8pecxstudios\\Cyberfox\\Profiles\\
Cyberfox
\\NETGATE Technologies\\BlackHawk\\Profiles\\
BlackHawk
\\Mozilla\\icecat\\Profiles\\
IceCat
\\K-Meleon\\
KMeleon
\\Thunderbird\\Profiles\\
Thunderbird
HARDWARE\\DESCRIPTION\\System\\CentralProcessor\\0
ProcessorNameString
kernel32.dll
%d MB
Unk
SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion
ProductName
x64
x86
SOFTWARE\\Microsoft\\Cryptography
MachineGuid
%d/%d/%d %d:%d:%d
%d_%d_%d_%d_%d_%d
UTC%d
DISPLAY
%dx%d
SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Uninstall
DisplayName
DisplayVersion
%s%d
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x717b |
| UninitializedDataSize: | - |
| InitializedDataSize: | 62976 |
| CodeSize: | 154112 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2020:07:17 19:15:13+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jul-2020 17:15:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 17-Jul-2020 17:15:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00025923 | 0x00025A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43763 |
.rdata | 0x00027000 | 0x00008178 | 0x00008200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.81575 |
.data | 0x00030000 | 0x00004428 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.45347 |
.reloc | 0x00035000 | 0x00002C9A | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.63855 |
Imports
KERNEL32.dll |
NETAPI32.dll |
USER32.dll |
Total processes
36
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | "C:\Users\admin\AppData\Local\Temp\bot.exe" | C:\Users\admin\AppData\Local\Temp\bot.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
oski(PID) Process(1036) bot.exe C262.77.159.212 RC4 Key056139954853430408 ID1BEF0A57BE110FD467A other (204)w system.txt System --------------------------------------------------- Windows: %s Bit: %s User: %s Computer Name: %s System Language: %s Machine ID: %s GUID: %s Domain Name: %s Workgroup: %s Keyboard Languages: %s Hardware ------------------------------------------------- Processor: %s Logical processors: %d Videocard: %s Display: %s RAM: %s Laptop: %s Time ----------------------------------------------------- Local: %s Zone: %s Network -------------------------------------------------- IP: IP? Country: Country? Installed Softwrare -------------------------------------- %s\\* . %s\\%s %s C:\\ProgramData\\ .exe :Zone.Identifier [ZoneTransfer] ZoneId=2 %s/1.jpg %s/2.jpg %s/3.jpg %s/4.jpg %s/5.jpg %s/6.jpg %s/7.jpg C:\\ProgramData\\sqlite3.dll C:\\ProgramData\\freebl3.dll C:\\ProgramData\\mozglue.dll C:\\ProgramData\\msvcp140.dll C:\\ProgramData\\nss3.dll C:\\ProgramData\\softokn3.dll C:\\ProgramData\\vcruntime140.dll _%s.zip \\cookies \\autofill \\cc file %s/main.php APPDATA LOCALAPPDATA USERPROFILE JohnDoe HAL9TH sqlite3.dll sqlite3_open sqlite3_prepare_v2 sqlite3_step sqlite3_column_text sqlite3_finalize sqlite3_close sqlite3_column_bytes sqlite3_column_blob \"os_crypt\":{\"encrypted_key\":\" \"} PATH PATH= NSS_Init NSS_Shutdown PK11_GetInternalKeySlot PK11_FreeSlot PK11_Authenticate PK11SDR_Decrypt vaultcli.dll VaultOpenVault VaultCloseVault VaultEnumerateItems VaultGetItem VaultFree passwords.txt a+ r PROF: UNK PROF: %s SOFT: %s HOST: %s USER: %s PASS: PASS: %s %s\\Mozilla\\Firefox\\profiles.ini \\logins.json formSubmitURL usernameField encryptedUsername encryptedPassword guid \\temp cookies\\%s_%s.txt %s %s %s %s %s %s %s CARD: %s NAME: %s DATE: %s/%s cc\\%s_%s.txt autofill\\%s_%s.txt %s %s SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies SELECT origin_url, username_value, password_value FROM logins SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards SELECT fieldname, value FROM moz_formhistory SELECT name, value FROM autofill TRUE FALSE ..\\profiles.ini %s\\* \\Local State Login Data Cookies Web Data cookies.sqlite logins.json formhistory.sqlite \\Opera Software\\Opera Stable\\ Opera \\Google\\Chrome\\User Data Google Chrome \\Chromium\\User Data Chromium \\Kometa\\User Data Kometa \\Amigo\\User Data Amigo \\Torch\\User Data Torch \\Orbitum\\User Data Orbitum \\Comodo\\Dragon\\User Data Comodo Dragon \\Nichrome\\User Data Nichrome \\Maxthon5\\Users Maxthon5 \\Sputnik\\User Data Sputnik \\Epic Privacy Browser\\User Data EPB \\Vivaldi\\User Data Vivaldi \\CocCoc\\Browser\\User Data CocCoc Browser \\uCozMedia\\Uran\\User Data Uran Browser \\QIP Surf\\User Data QIP Surf \\CentBrowser\\User Data Cent \\Elements Browser\\User Data Elements Browser \\TorBro\\Profile TorBro \\CryptoTab Browser\\User Data CryptoTab \\BraveSoftware\\Brave-Browser\\User Data Brave \\Mozilla\\Firefox\\Profiles\\ Mozilla Firefox \\Moonchild Productions\\Pale Moon\\Profiles\\ Pale Moon \\Waterfox\\Profiles\\ Waterfox \\8pecxstudios\\Cyberfox\\Profiles\\ Cyberfox \\NETGATE Technologies\\BlackHawk\\Profiles\\ BlackHawk \\Mozilla\\icecat\\Profiles\\ IceCat \\K-Meleon\\ KMeleon \\Thunderbird\\Profiles\\ Thunderbird HARDWARE\\DESCRIPTION\\System\\CentralProcessor\\0 ProcessorNameString kernel32.dll %d MB Unk SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion ProductName x64 x86 SOFTWARE\\Microsoft\\Cryptography MachineGuid %d/%d/%d %d:%d:%d %d_%d_%d_%d_%d_%d UTC%d DISPLAY %dx%d SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Uninstall DisplayName DisplayVersion %s%d | |||||||||||||||
Total events
314
Read events
294
Write events
20
Delete events
0
Modification events
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1036) bot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1036 | bot.exe | C:\ProgramData\sqlite3.dll | html | |
MD5:1B7C22A214949975556626D7217E9A39 | SHA256:340C8464C2007CE3F80682E15DFAFA4180B641D53C14201B929906B7B0284D87 | |||
| 1036 | bot.exe | C:\ProgramData\605281709068304\temp | sqlite | |
MD5:B8E63E7225C9F4E0A81371F29D6456D8 | SHA256:35A6919CE60EA8E0A44934F8B267BDE2C5A063C2E32F22D34724F168C43150C8 | |||
| 1036 | bot.exe | C:\ProgramData\msvcp140.dll | html | |
MD5:1B7C22A214949975556626D7217E9A39 | SHA256:340C8464C2007CE3F80682E15DFAFA4180B641D53C14201B929906B7B0284D87 | |||
| 1036 | bot.exe | C:\ProgramData\freebl3.dll | html | |
MD5:1B7C22A214949975556626D7217E9A39 | SHA256:340C8464C2007CE3F80682E15DFAFA4180B641D53C14201B929906B7B0284D87 | |||
| 1036 | bot.exe | C:\ProgramData\nss3.dll | html | |
MD5:1B7C22A214949975556626D7217E9A39 | SHA256:340C8464C2007CE3F80682E15DFAFA4180B641D53C14201B929906B7B0284D87 | |||
| 1036 | bot.exe | C:\ProgramData\softokn3.dll | html | |
MD5:1B7C22A214949975556626D7217E9A39 | SHA256:340C8464C2007CE3F80682E15DFAFA4180B641D53C14201B929906B7B0284D87 | |||
| 1036 | bot.exe | C:\ProgramData\mozglue.dll | html | |
MD5:1B7C22A214949975556626D7217E9A39 | SHA256:340C8464C2007CE3F80682E15DFAFA4180B641D53C14201B929906B7B0284D87 | |||
| 1036 | bot.exe | C:\ProgramData\vcruntime140.dll | html | |
MD5:1B7C22A214949975556626D7217E9A39 | SHA256:340C8464C2007CE3F80682E15DFAFA4180B641D53C14201B929906B7B0284D87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
3
DNS requests
1
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1036 | bot.exe | POST | 404 | 62.77.159.212:80 | http://62.77.159.212/6.jpg | HU | html | 123 b | malicious |
1036 | bot.exe | POST | 404 | 62.77.159.212:80 | http://62.77.159.212/2.jpg | HU | html | 123 b | malicious |
1036 | bot.exe | POST | 404 | 62.77.159.212:80 | http://62.77.159.212/1.jpg | HU | html | 123 b | malicious |
1036 | bot.exe | POST | 404 | 62.77.159.212:80 | http://62.77.159.212/4.jpg | HU | html | 123 b | malicious |
1036 | bot.exe | POST | 404 | 62.77.159.212:80 | http://62.77.159.212/3.jpg | HU | html | 123 b | malicious |
1036 | bot.exe | POST | 404 | 62.77.159.212:80 | http://62.77.159.212/5.jpg | HU | html | 123 b | malicious |
1036 | bot.exe | POST | 404 | 62.77.159.212:80 | http://62.77.159.212/7.jpg | HU | html | 123 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1036 | bot.exe | 62.77.159.212:80 | — | Infotechna Ltd. | HU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1036 | bot.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
1036 | bot.exe | A Network Trojan was detected | ET TROJAN Vidar/Arkei/Megumin/Oski Stealer HTTP POST Pattern |
1036 | bot.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
1036 | bot.exe | A Network Trojan was detected | ET TROJAN Vidar/Arkei/Megumin/Oski Stealer HTTP POST Pattern |
1036 | bot.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
1036 | bot.exe | A Network Trojan was detected | ET TROJAN Vidar/Arkei/Megumin/Oski Stealer HTTP POST Pattern |
1036 | bot.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
1036 | bot.exe | A Network Trojan was detected | ET TROJAN Vidar/Arkei/Megumin/Oski Stealer HTTP POST Pattern |
1036 | bot.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
1036 | bot.exe | A Network Trojan was detected | ET TROJAN Vidar/Arkei/Megumin/Oski Stealer HTTP POST Pattern |