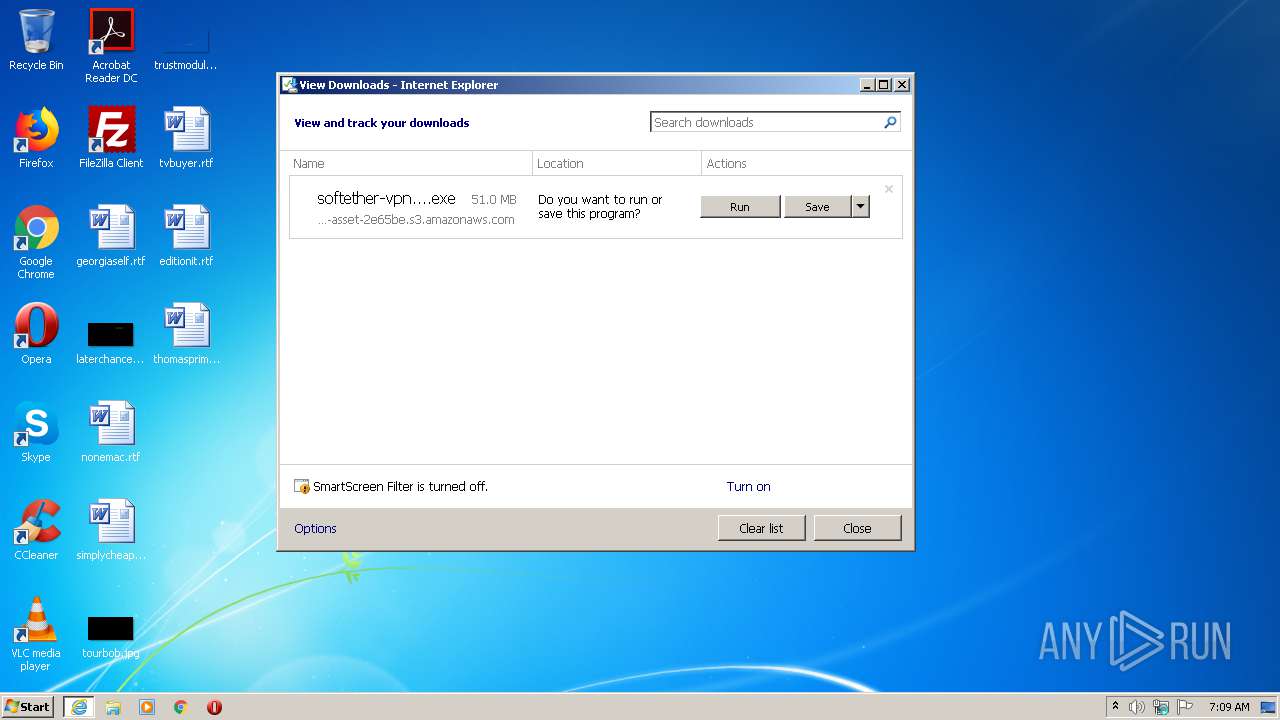
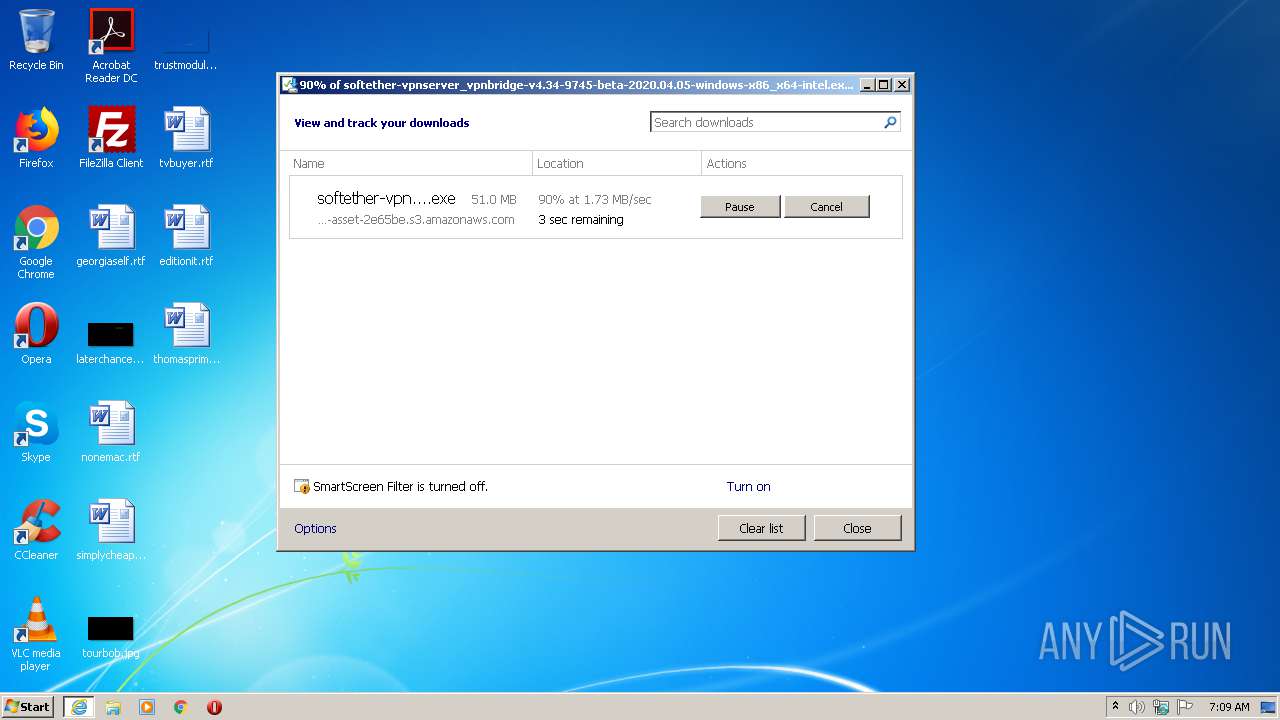
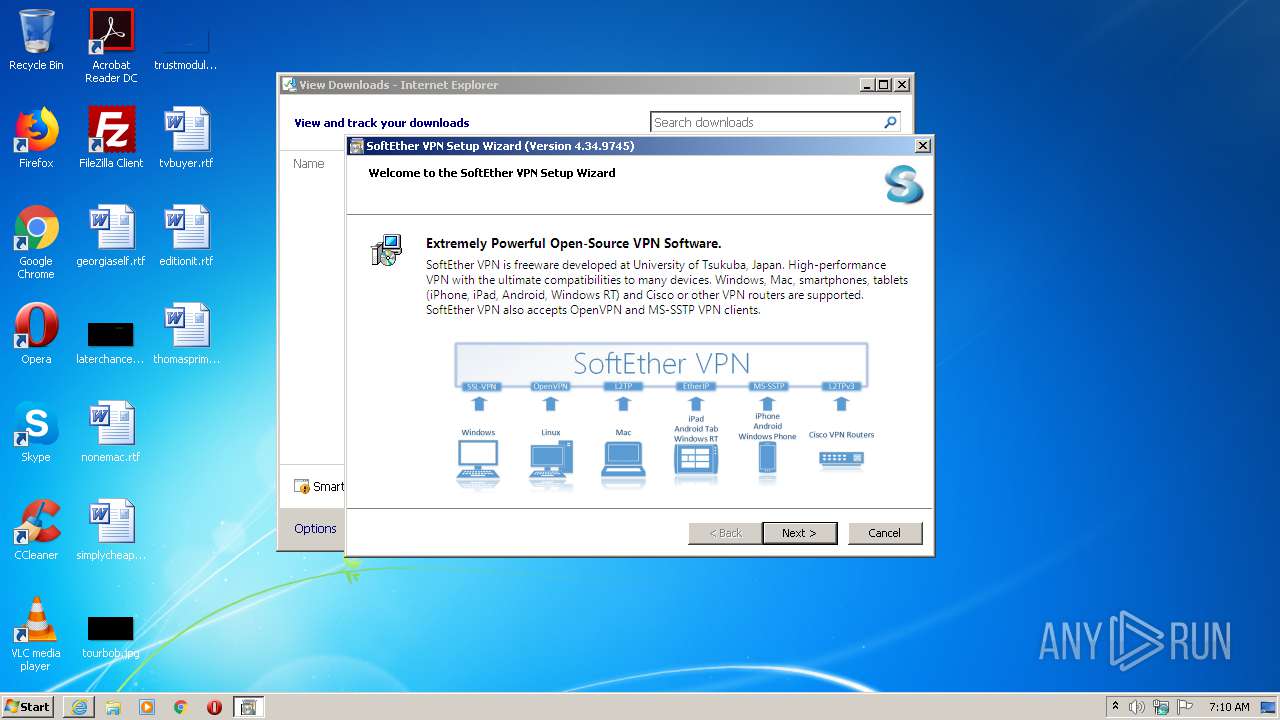
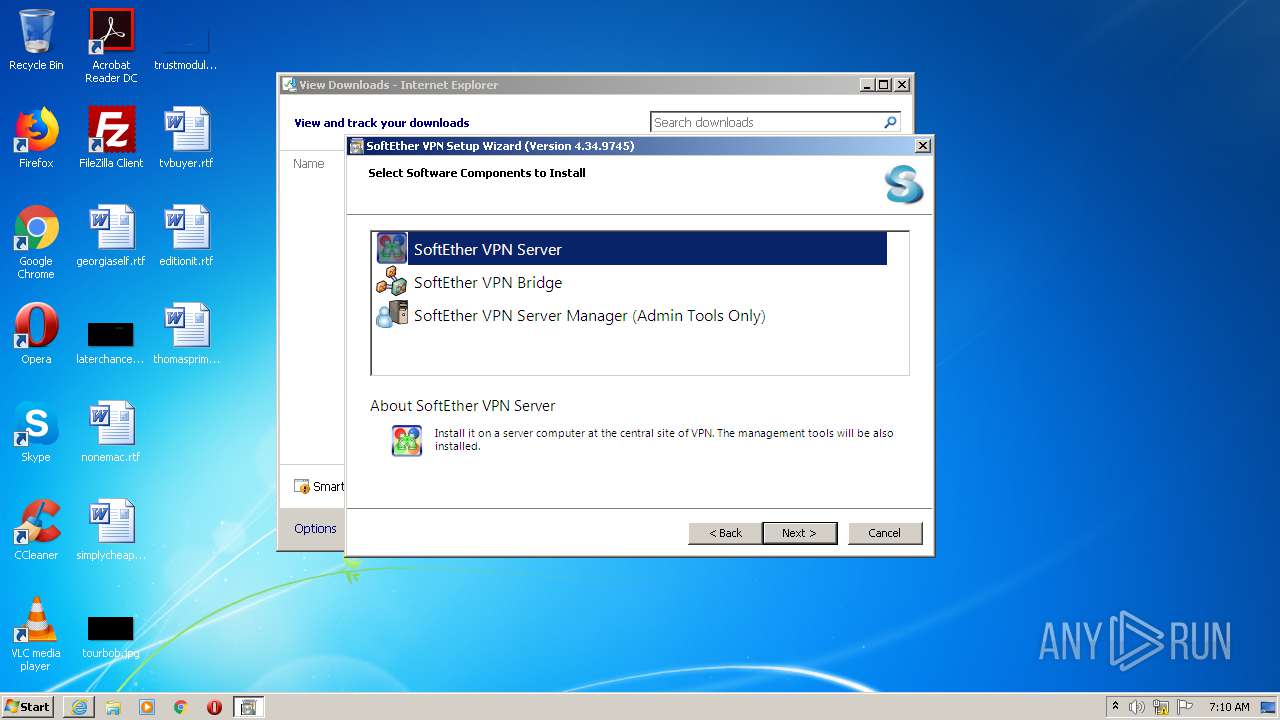
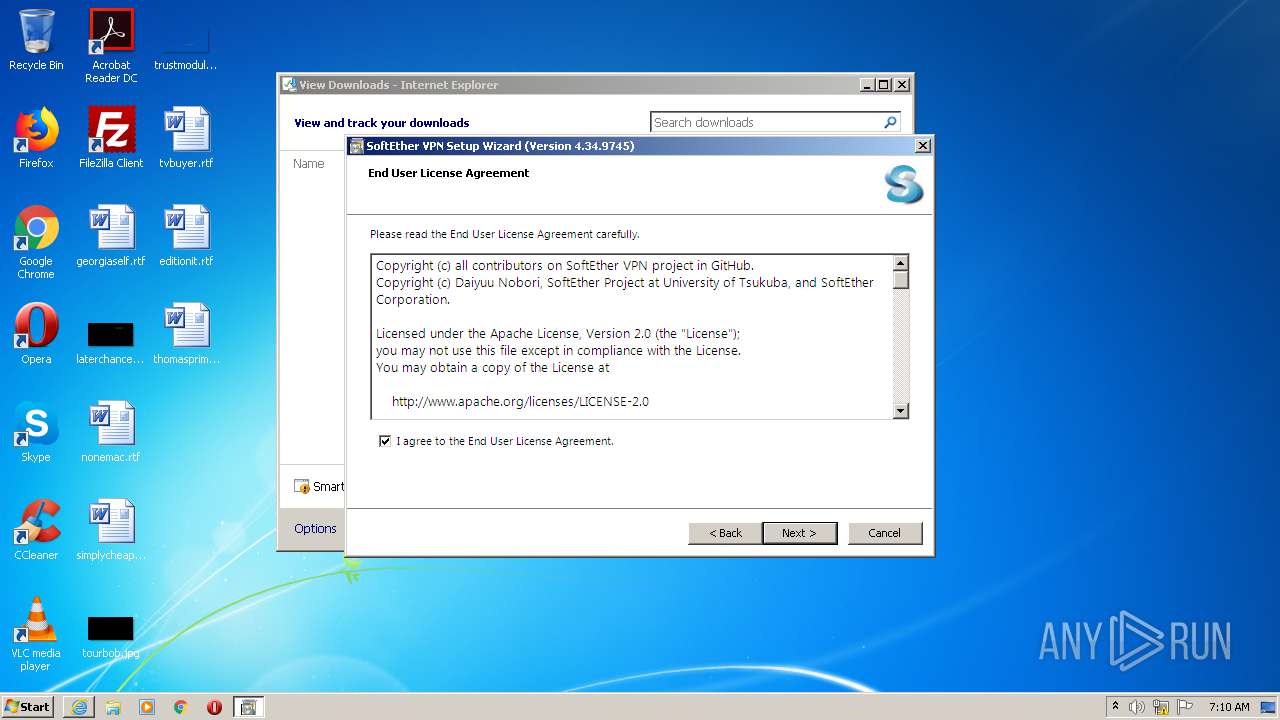
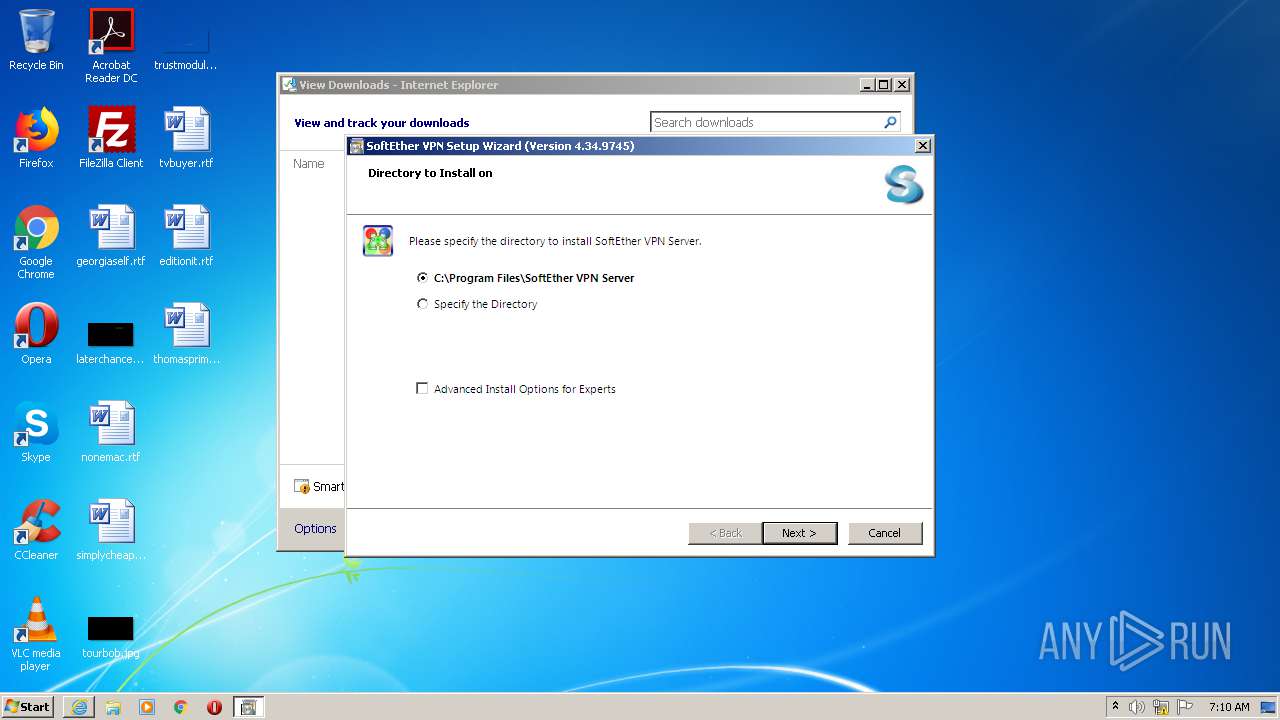
| URL: | https://github.com/SoftEtherVPN/SoftEtherVPN_Stable/releases/download/v4.34-9745-beta/softether-vpnserver_vpnbridge-v4.34-9745-beta-2020.04.05-windows-x86_x64-intel.exe |
| Full analysis: | https://app.any.run/tasks/a919fd29-aa49-41b3-a427-1593b9b855a3 |
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2020, 06:09:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0E62E7C4DC9A233B71871FC3EE39479B |
| SHA1: | 716FB6589099F2B455E8F728D2414092D7A24CAF |
| SHA256: | 522688D7F1839A2F3BBA49AAD58347355871AE5DBDD0CEB74771BFB92C8C99D0 |
| SSDEEP: | 3:N8tEdBNetDNWNhrkCAIgHN0S+AOKWTRiRIiIgZVhRLRJ8xLmn:2urNwskLVURbMZVX8xLc |
MALICIOUS
Loads dropped or rewritten executable
- vpnsetup.exe (PID: 784)
- vpnsetup.exe (PID: 3276)
- windanr.exe (PID: 2176)
- iexplore.exe (PID: 2592)
- DllHost.exe (PID: 572)
- softether-vpnserver_vpnbridge-v4.34-9745-beta-2020.04.05-windows-x86_x64-intel.exe (PID: 3344)
- DllHost.exe (PID: 3568)
- iexplore.exe (PID: 2760)
- conhost.exe (PID: 3632)
- cscript.exe (PID: 3532)
- consent.exe (PID: 3416)
- cscript.exe (PID: 3712)
- cscript.exe (PID: 3812)
- conhost.exe (PID: 3836)
- conhost.exe (PID: 2316)
- conhost.exe (PID: 1768)
- netsh.exe (PID: 2008)
- SearchProtocolHost.exe (PID: 3540)
- conhost.exe (PID: 3192)
- netsh.exe (PID: 3412)
- conhost.exe (PID: 2856)
- vpnserver.exe (PID: 2460)
- SearchFilterHost.exe (PID: 2692)
- wmiprvse.exe (PID: 3900)
- conhost.exe (PID: 3200)
- vpncmd.exe (PID: 2172)
- cscript.exe (PID: 1148)
- conhost.exe (PID: 2436)
- DllHost.exe (PID: 3788)
- netsh.exe (PID: 956)
- vpnsmgr.exe (PID: 1900)
- vpnsmgr.exe (PID: 2416)
Application was dropped or rewritten from another process
- vpnsetup.exe (PID: 784)
- vpnsetup.exe (PID: 3276)
- vpncmd.exe (PID: 2172)
- vpnserver.exe (PID: 2460)
- vpnsmgr.exe (PID: 1900)
- vpnsmgr.exe (PID: 2416)
SUSPICIOUS
Application launched itself
- vpnsetup.exe (PID: 3276)
Executable content was dropped or overwritten
- vpnsetup.exe (PID: 3276)
- softether-vpnserver_vpnbridge-v4.34-9745-beta-2020.04.05-windows-x86_x64-intel.exe (PID: 3344)
- vpnsetup.exe (PID: 784)
- vpnserver.exe (PID: 2460)
- vpncmd.exe (PID: 2172)
- vpnsmgr.exe (PID: 1900)
- vpnsmgr.exe (PID: 2416)
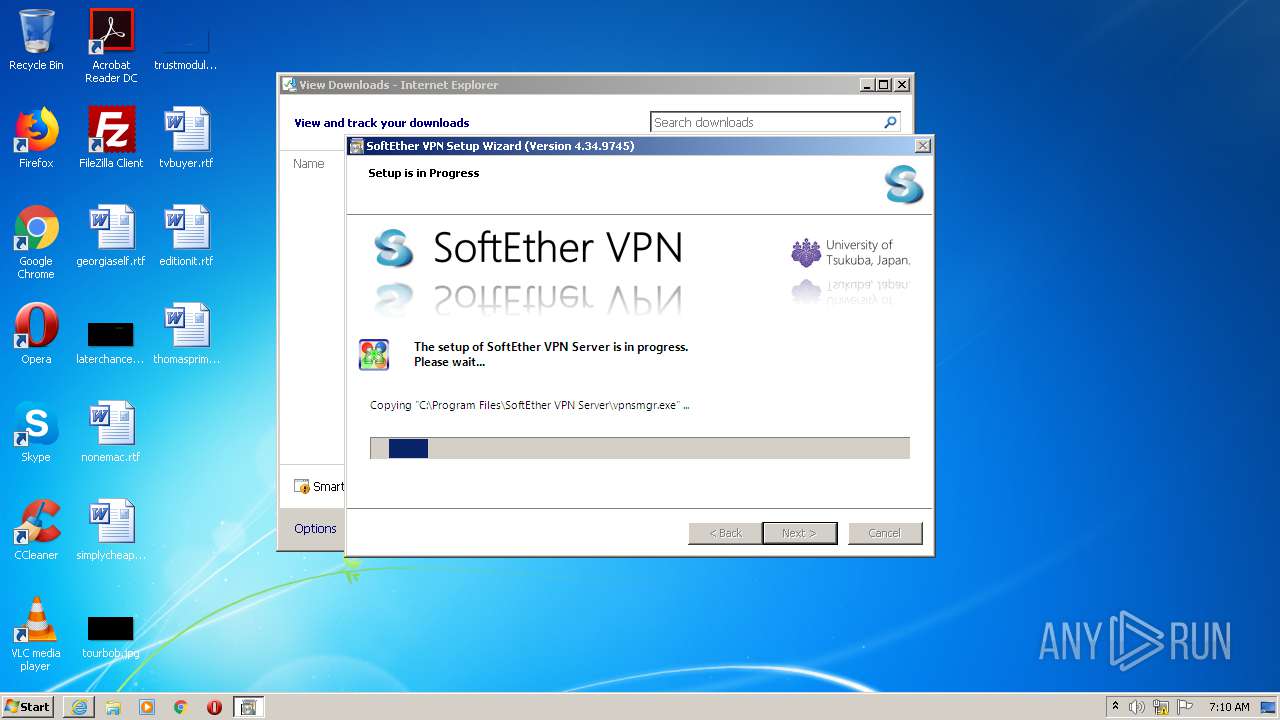
Creates files in the program directory
- vpnsetup.exe (PID: 784)
- vpnserver.exe (PID: 2460)
Executes scripts
- vpnsetup.exe (PID: 784)
- vpnserver.exe (PID: 2460)
Creates files in the Windows directory
- vpnserver.exe (PID: 2460)
- vpncmd.exe (PID: 2172)
Uses NETSH.EXE for network configuration
- vpnsetup.exe (PID: 784)
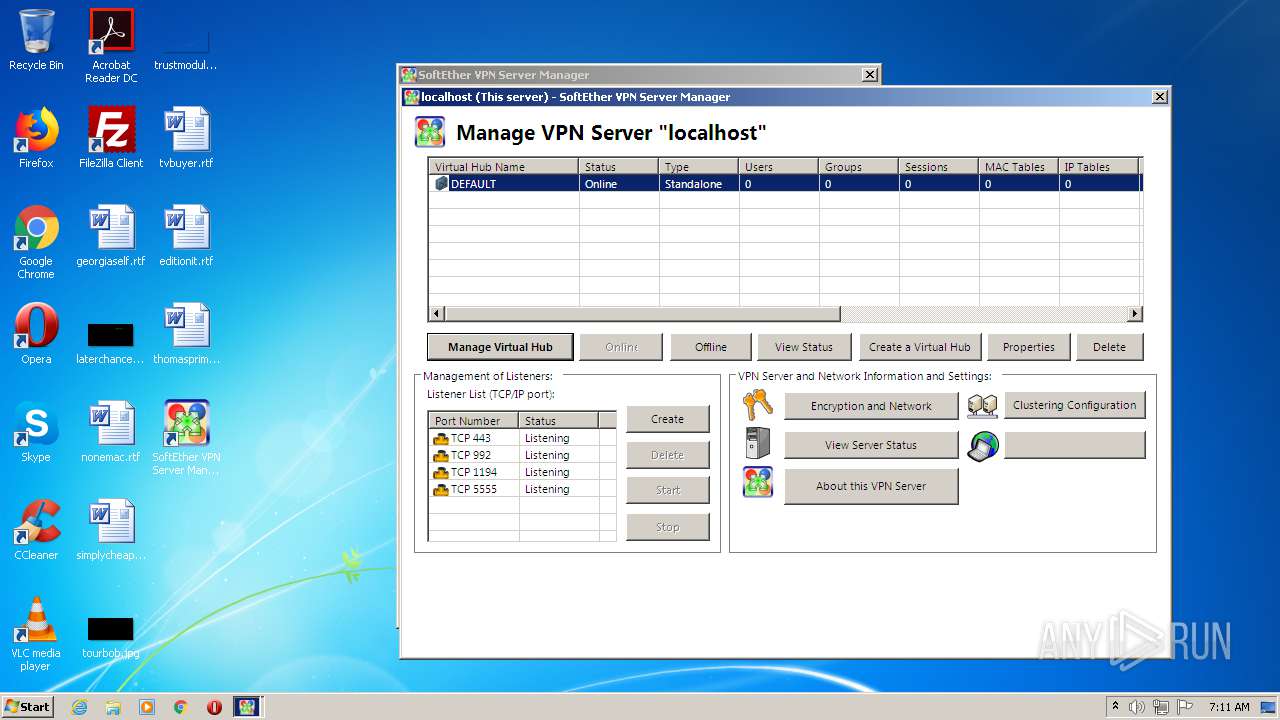
Executed as Windows Service
- vpnserver.exe (PID: 2460)
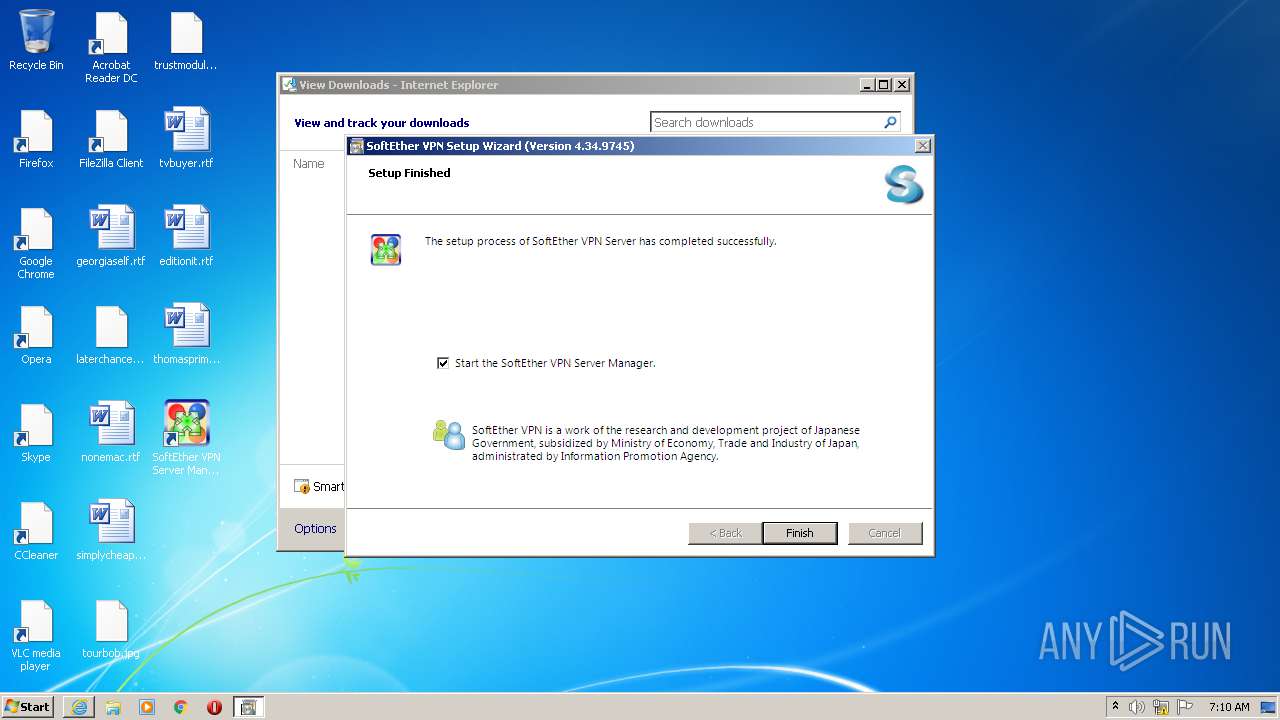
Creates a software uninstall entry
- vpnsetup.exe (PID: 784)
Creates files in the driver directory
- vpnserver.exe (PID: 2460)
Creates or modifies windows services
- vpnserver.exe (PID: 2460)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2760)
Reads Internet Cache Settings
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 2760)
Application launched itself
- iexplore.exe (PID: 2760)
Creates files in the user directory
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 2760)
Reads settings of System Certificates
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 2592)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2760)
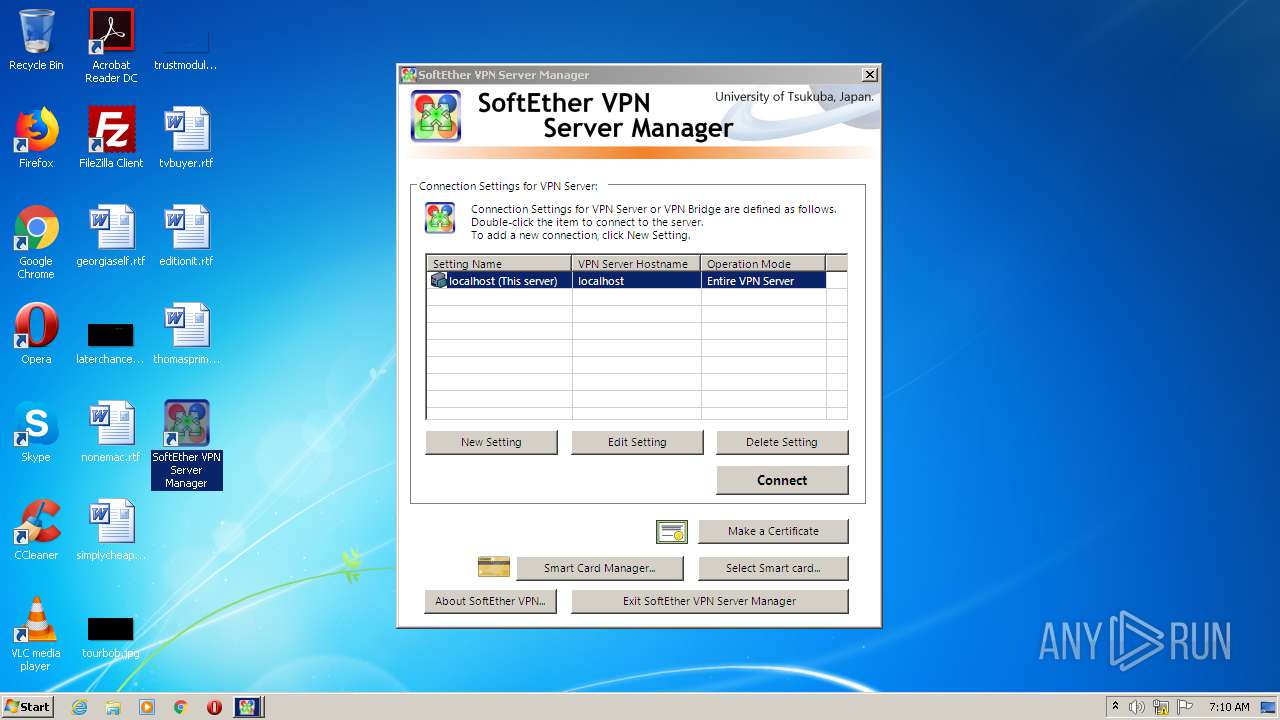
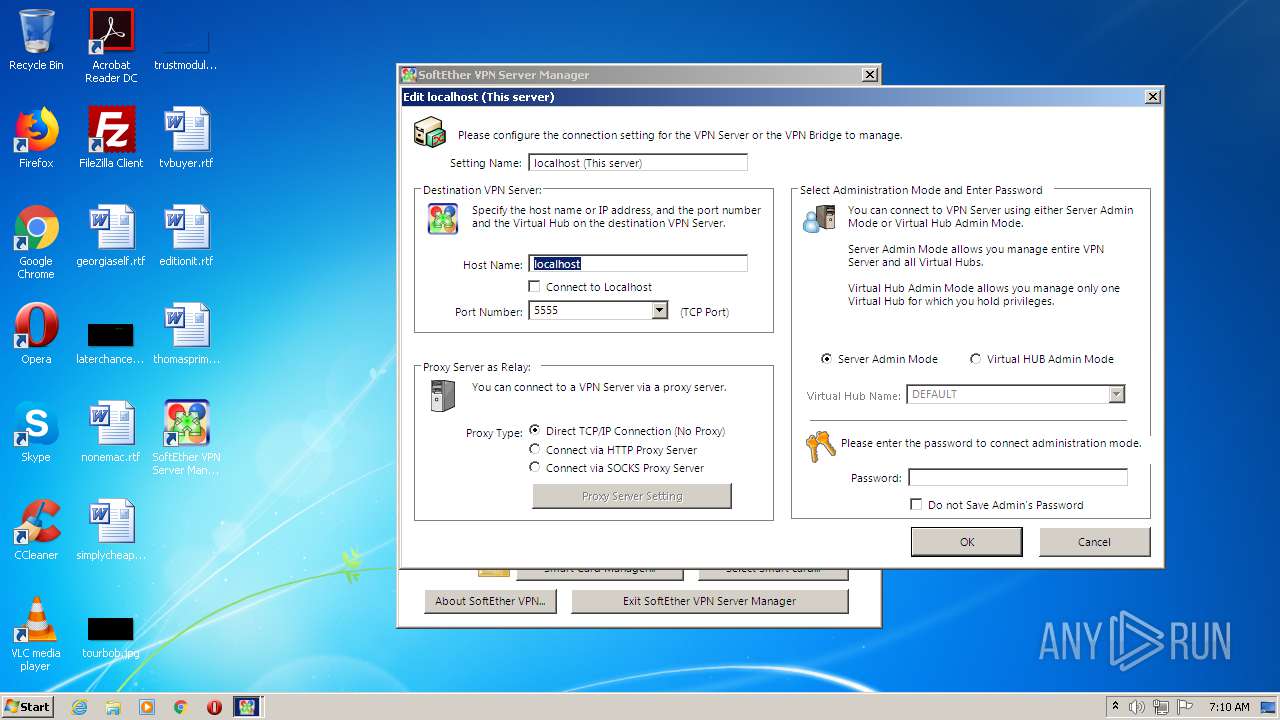
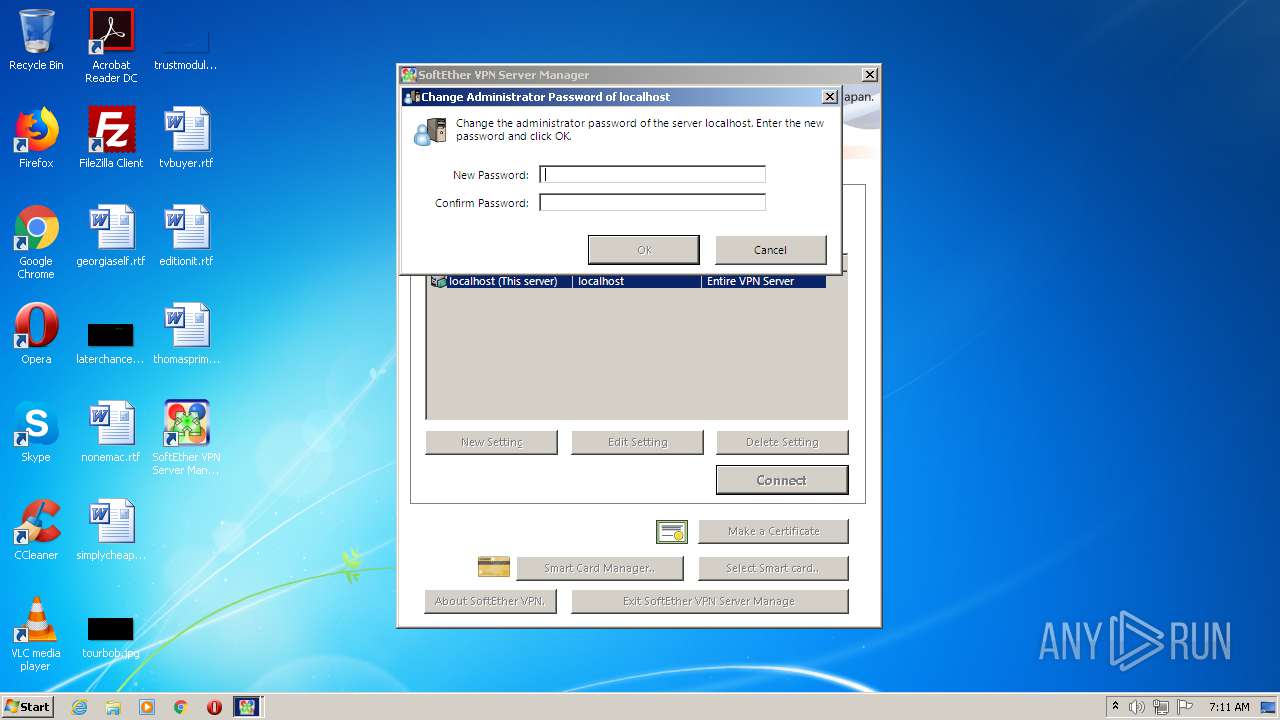
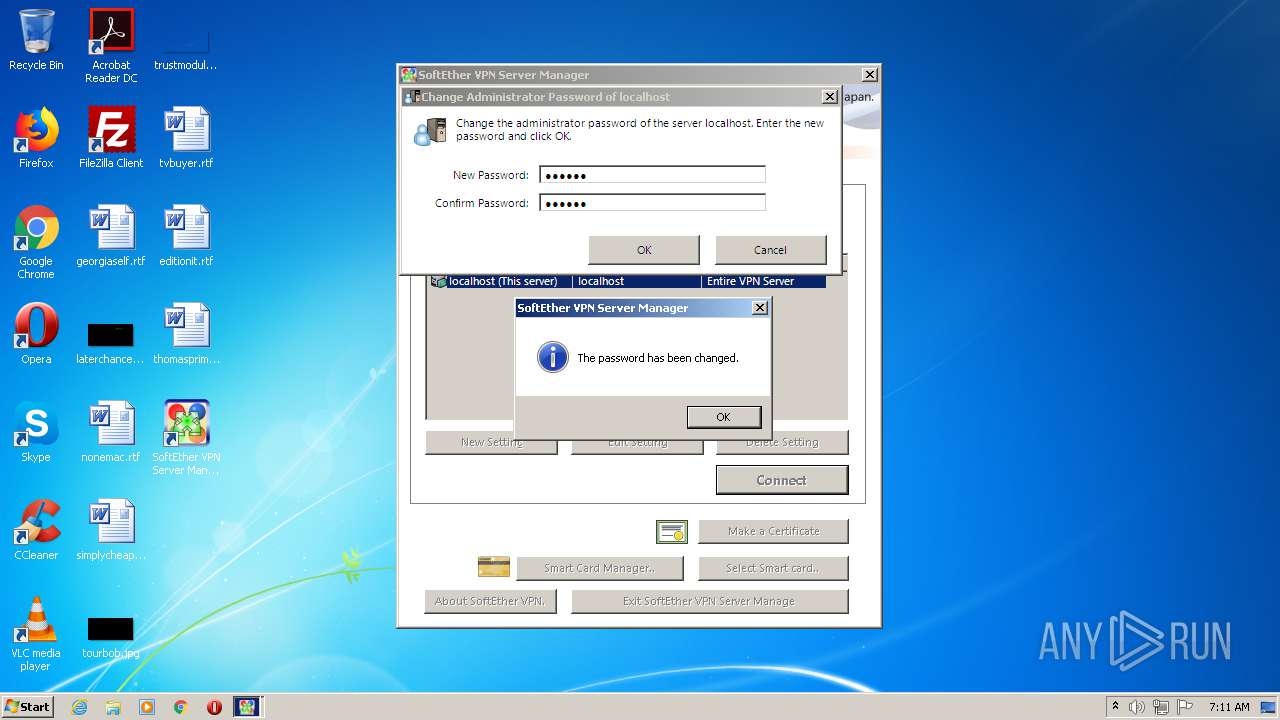
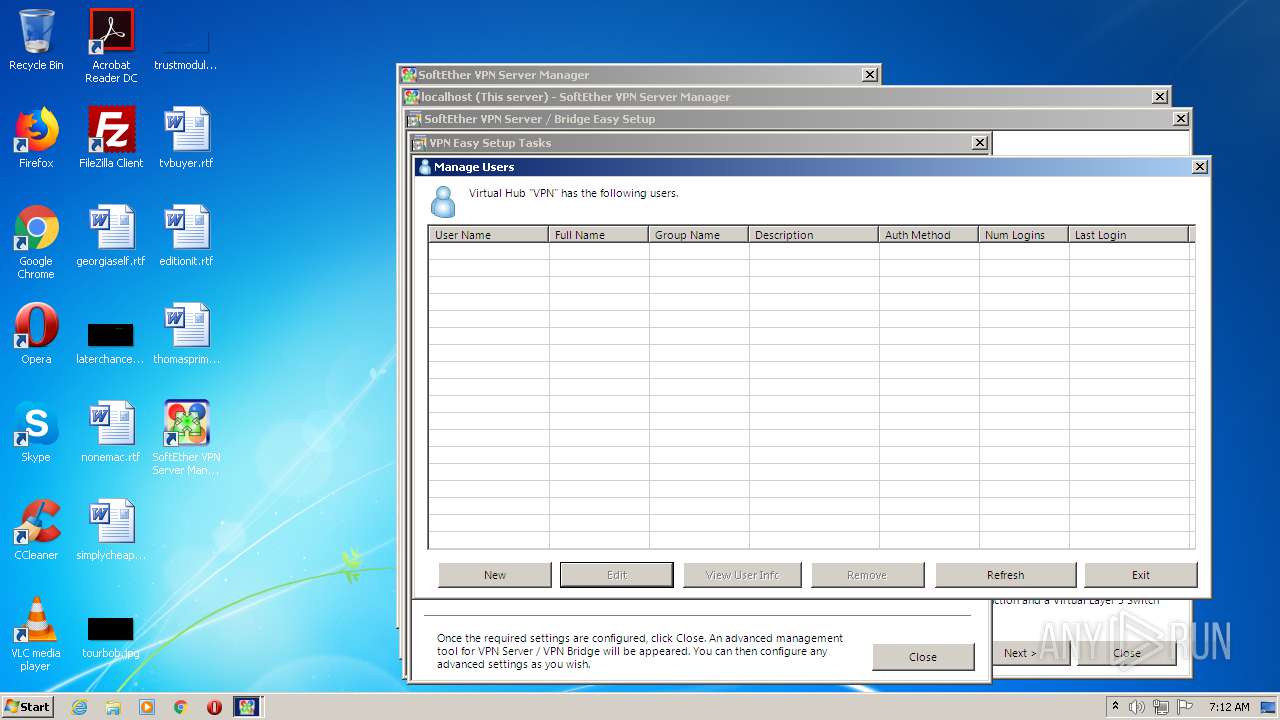
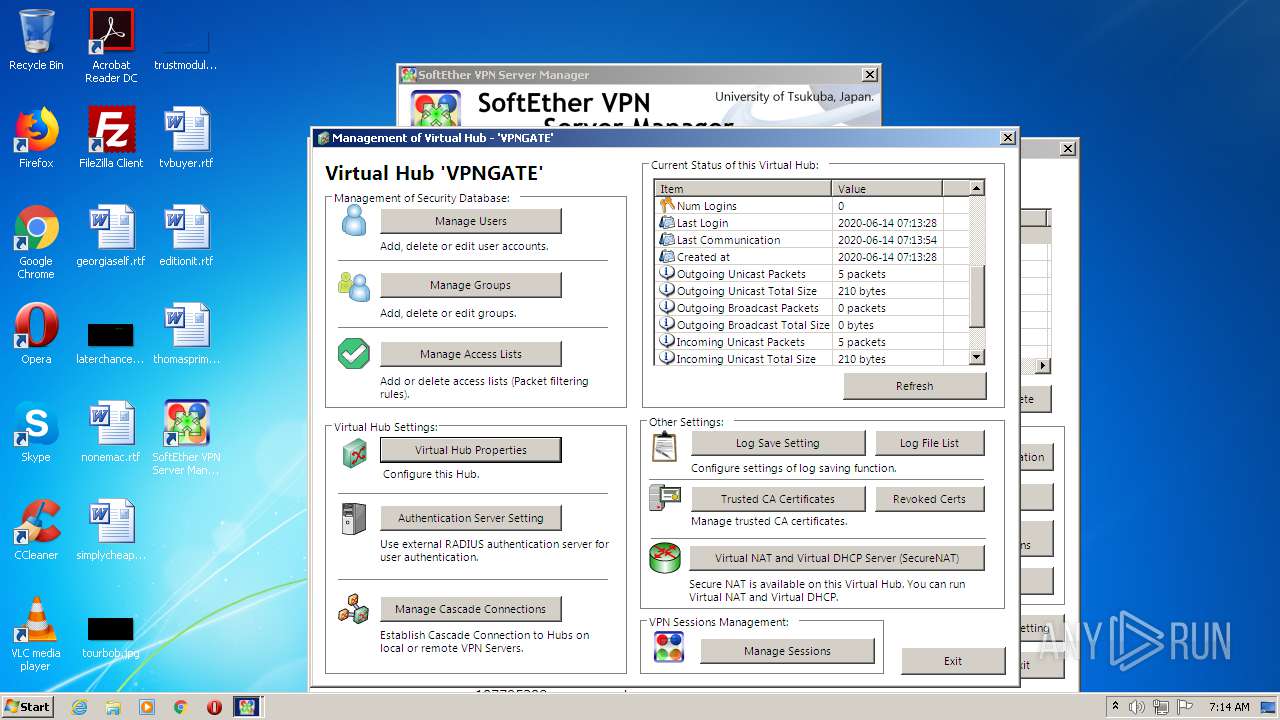
Manual execution by user
- vpnsmgr.exe (PID: 2416)
Changes settings of System certificates
- iexplore.exe (PID: 2760)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
32
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | C:\Windows\system32\DllHost.exe /Processid:{E10F6C3A-F1AE-4ADC-AA9D-2FE65525666E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 784 | "C:\Users\admin\AppData\Local\Temp\VPN_B97E\vpnsetup.exe" /CALLERSFXPATH:"C:\Users\admin\AppData\Local\Temp\VPN_B97E\installer.cache" /ISEASYINSTALLER:0 /UAC:true | C:\Users\admin\AppData\Local\Temp\VPN_B97E\vpnsetup.exe | vpnsetup.exe | ||||||||||||
User: admin Company: SoftEther VPN Project at University of Tsukuba, Japan. Integrity Level: HIGH Description: SoftEther VPN Exit code: 0 Version: 4, 34, 0, 9745 Modules
| |||||||||||||||
| 956 | C:\Windows\system32\netsh.exe int ipv4 set global taskoffload=disabled | C:\Windows\system32\netsh.exe | — | vpnsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1148 | C:\Windows\system32\cscript.exe "C:\Windows\TEMP\VPN_D223\detectvm.vbs" | C:\Windows\system32\cscript.exe | — | vpnserver.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1768 | \??\C:\Windows\system32\conhost.exe "240142421-1684388994-13189089831375192784163926841420314957785163362871286949317" | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
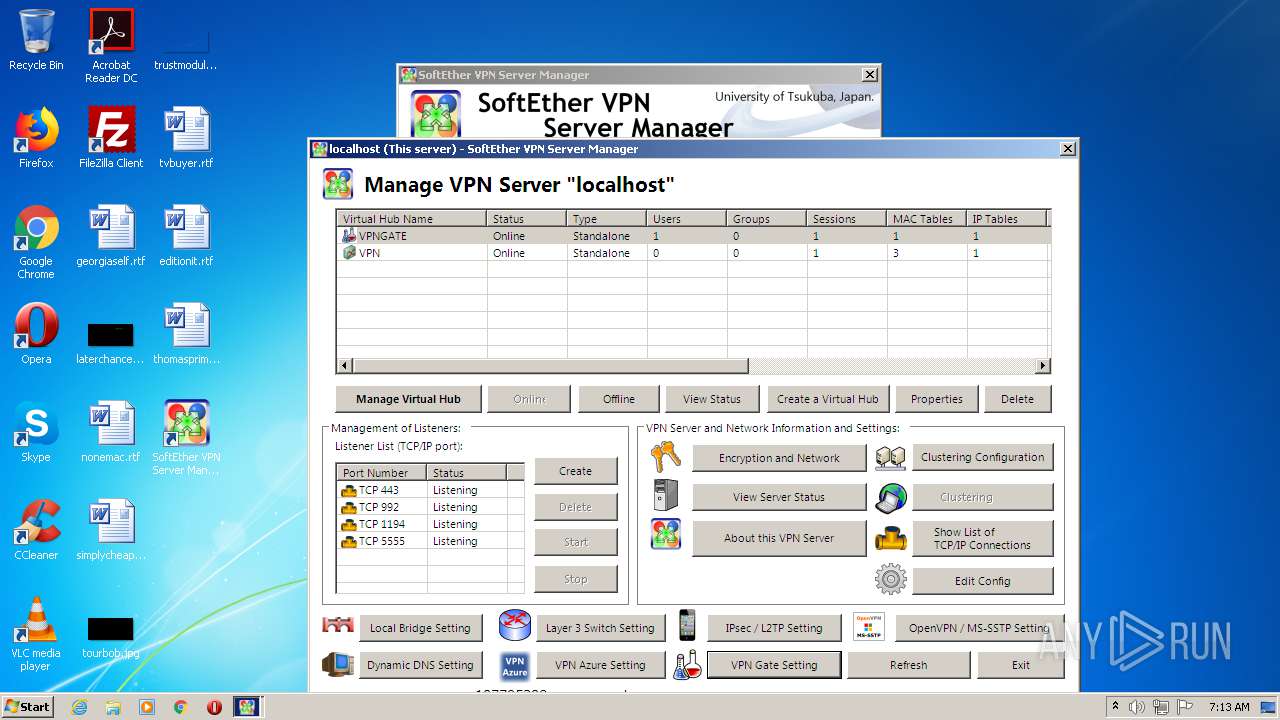
| 1900 | "C:\Program Files\SoftEther VPN Server\vpnsmgr.exe" | C:\Program Files\SoftEther VPN Server\vpnsmgr.exe | vpnsetup.exe | ||||||||||||
User: admin Company: SoftEther VPN Project at University of Tsukuba, Japan. Integrity Level: MEDIUM Description: SoftEther VPN Exit code: 0 Version: 4, 34, 0, 9745 Modules
| |||||||||||||||
| 2008 | C:\Windows\system32\netsh.exe int ipv6 set global taskoffload=disabled | C:\Windows\system32\netsh.exe | — | vpnsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | "C:\Program Files\SoftEther VPN Server\vpncmd.exe" /? | C:\Program Files\SoftEther VPN Server\vpncmd.exe | vpnsetup.exe | ||||||||||||
User: admin Company: SoftEther VPN Project at University of Tsukuba, Japan. Integrity Level: HIGH Description: SoftEther VPN Exit code: 38 Version: 4, 34, 0, 9745 Modules
| |||||||||||||||
| 2176 | "windanr.exe" | C:\Windows\system32\windanr.exe | — | q.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2316 | \??\C:\Windows\system32\conhost.exe "241946656-2445212-928030650710837574-751554801964024023624018315-1994862746" | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 203
Read events
2 368
Write events
2 638
Delete events
1 197
Modification events
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2176) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
23
Suspicious files
28
Text files
23
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF010.tmp | — | |
MD5:— | SHA256:— | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF011.tmp | — | |
MD5:— | SHA256:— | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6TQJKBGX.txt | — | |
MD5:— | SHA256:— | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\softether-vpnserver_vpnbridge-v4.34-9745-beta-2020.04.05-windows-x86_x64-intel[1].exe | — | |
MD5:— | SHA256:— | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\softether-vpnserver_vpnbridge-v4.34-9745-beta-2020.04.05-windows-x86_x64-intel.exe.laab27d.partial | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF209C8E62EE58DEA4.TMP | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\softether-vpnserver_vpnbridge-v4.34-9745-beta-2020.04.05-windows-x86_x64-intel.exe.laab27d.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\softether-vpnserver_vpnbridge-v4.34-9745-beta-2020.04.05-windows-x86_x64-intel.exe | — | |
MD5:— | SHA256:— | |||
| 3344 | softether-vpnserver_vpnbridge-v4.34-9745-beta-2020.04.05-windows-x86_x64-intel.exe | C:\Users\admin\AppData\Local\Temp\VPN_B97E\hamcore.se2 | — | |
MD5:— | SHA256:— | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_B00CE8D5D4CF0E959CFDB61F636A135D | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
31
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2760 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2592 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAVXyAsoJoOhewoRRJMpa3k%3D | US | der | 471 b | whitelisted |
2592 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
2592 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
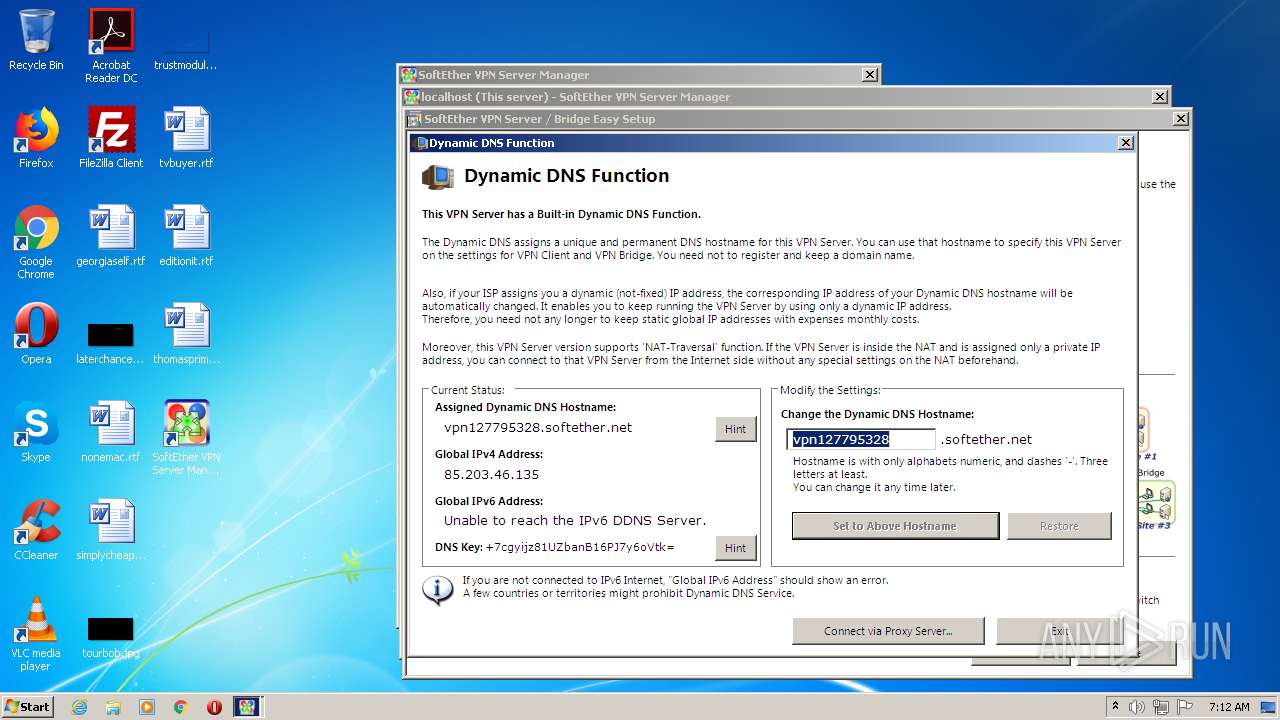
2460 | vpnserver.exe | GET | 200 | 130.158.75.46:80 | http://get-my-ip.ddns.softether-network.net/ddns/getmyip.ashx?v=16055165538354434927 | JP | text | 16 b | unknown |
2592 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2460 | vpnserver.exe | GET | 200 | 130.158.75.46:80 | http://get-my-ip.ddns.softether-network.net/ddns/getmyip.ashx?v=3203182232104812052 | JP | text | 16 b | unknown |
2760 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2592 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAVXyAsoJoOhewoRRJMpa3k%3D | US | der | 471 b | whitelisted |
2460 | vpnserver.exe | GET | 200 | 130.158.75.46:80 | http://get-my-ip.ddns.softether-network.net/ddns/getmyip.ashx?v=11656837889484078807 | JP | text | 16 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | iexplore.exe | 140.82.118.3:443 | github.com | — | US | malicious |
2592 | iexplore.exe | 52.217.44.172:443 | github-production-release-asset-2e65be.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
2592 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2760 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
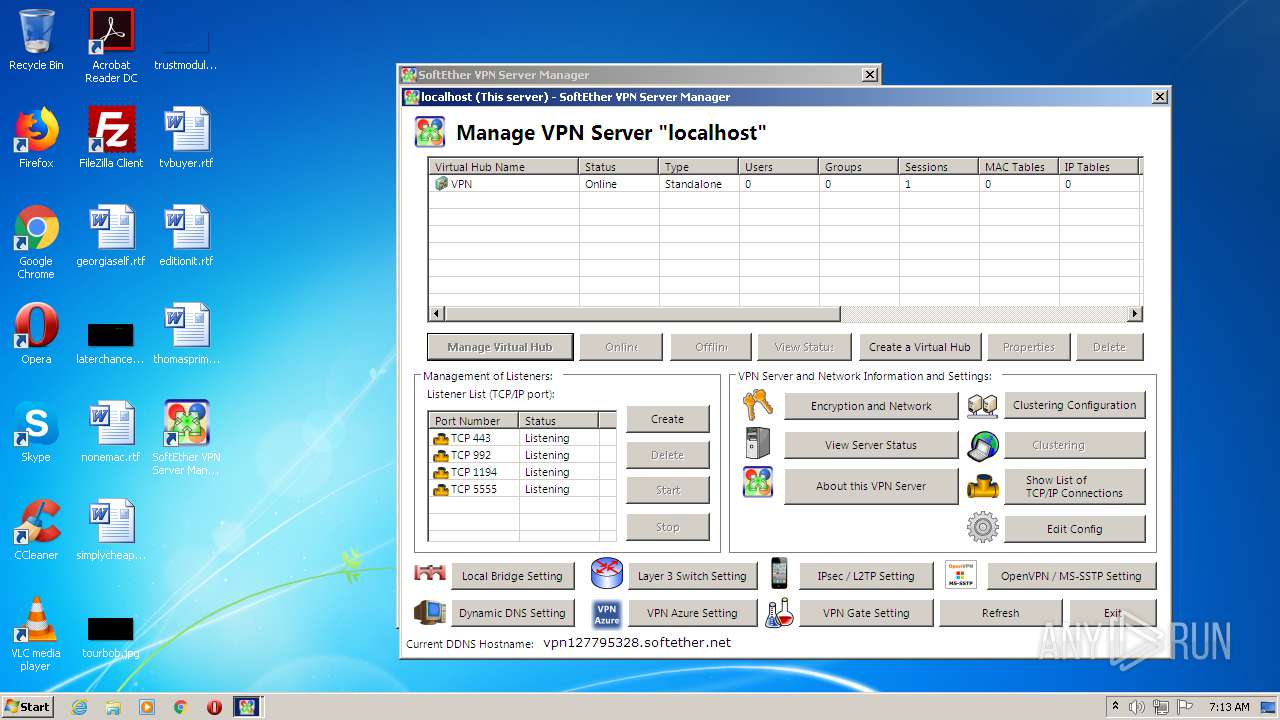
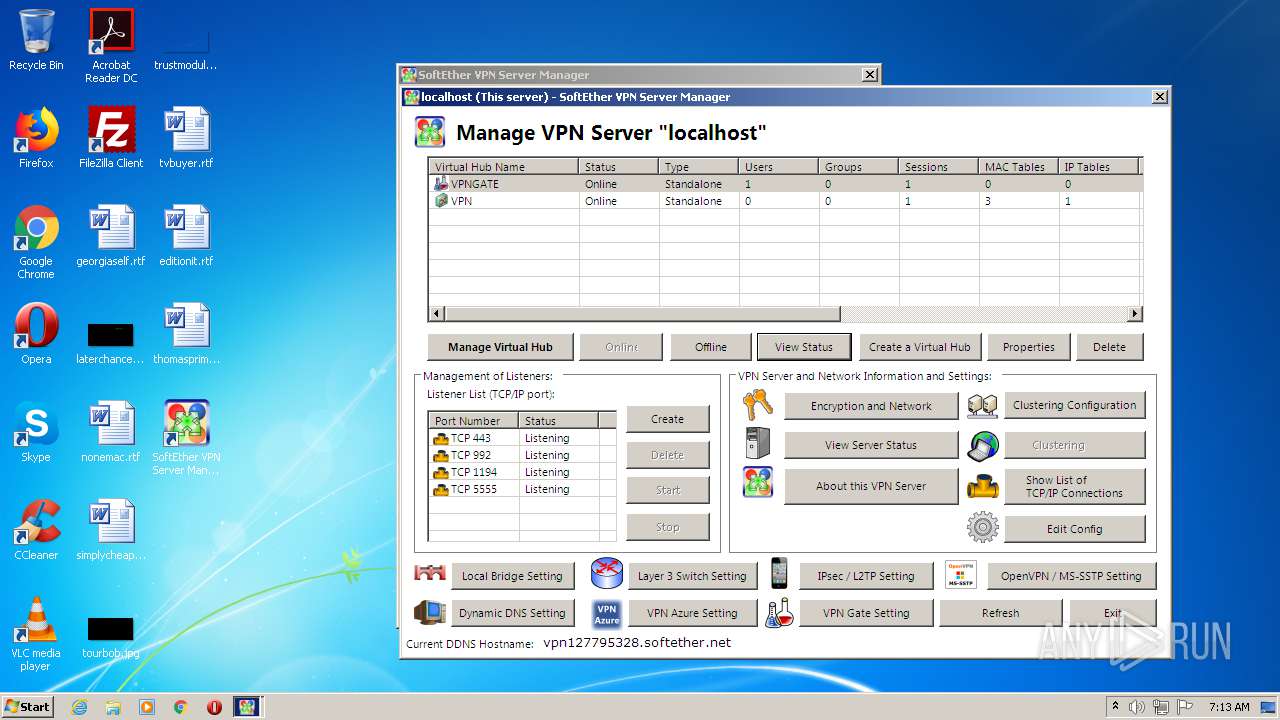
1900 | vpnsmgr.exe | 130.158.6.62:443 | update-check.softether-network.net | University of Tsukuba | JP | unknown |
2760 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2416 | vpnsmgr.exe | 130.158.6.62:443 | update-check.softether-network.net | University of Tsukuba | JP | unknown |
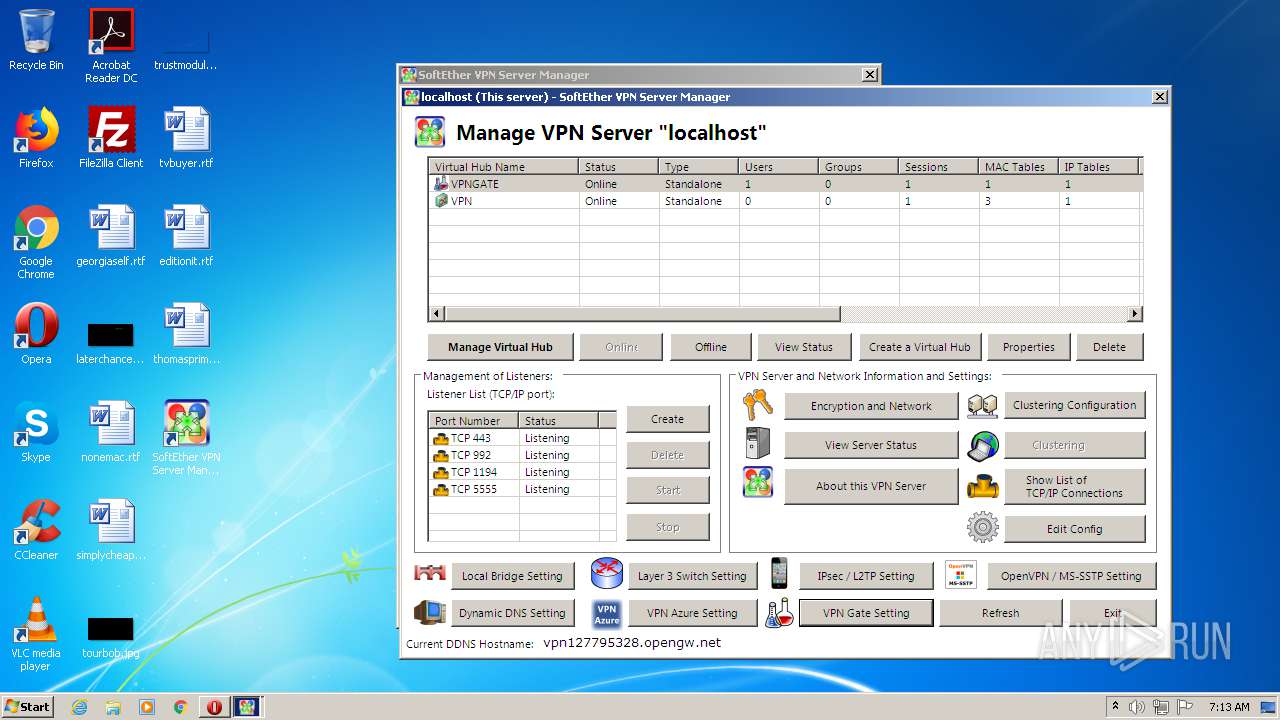
2460 | vpnserver.exe | 130.158.6.116:5004 | x5.xe.servers.nat-traversal.softether-network.net | University of Tsukuba | JP | unknown |
— | — | 2.16.186.26:80 | www.msftncsi.com | Akamai International B.V. | — | whitelisted |
— | — | 130.158.6.113:5004 | xc.x8.servers.nat-traversal.softether-network.net | University of Tsukuba | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
github-production-release-asset-2e65be.s3.amazonaws.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
update-check.softether-network.net |
| unknown |
keepalive.softether.org |
| unknown |
x6.x5.servers.ddns.softether-network.net |
| unknown |
x5.xe.servers.nat-traversal.softether-network.net |
| unknown |